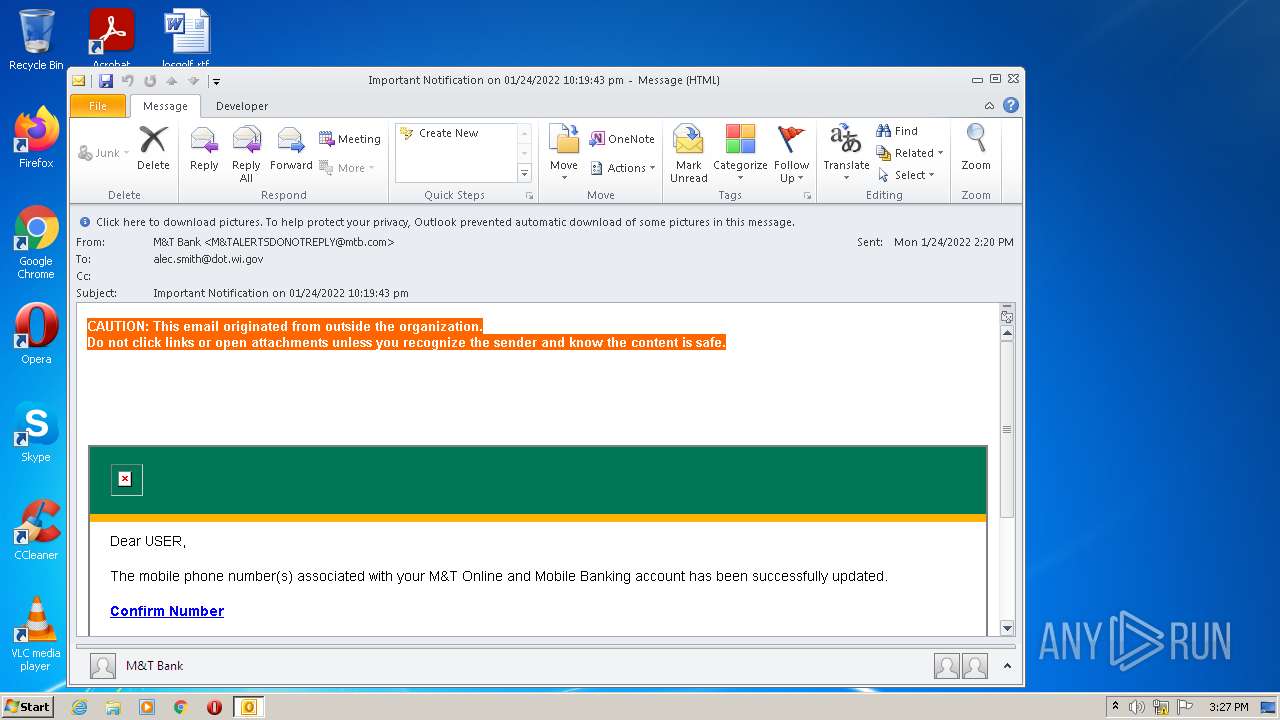
| File name: | uploads_0823d948-0ef4-4a05-9b7f-6ca45c998bb0.eml |
| Full analysis: | https://app.any.run/tasks/8678d80a-500a-4942-9f5a-b33b9e01476c |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 15:27:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 07713F85989EF2B91DA38F5E9EDBC0A1 |
| SHA1: | 68CB3248A33C5FCF8919F39EF0C339662748F513 |
| SHA256: | F2D8AA2EB9996F5D8CDCAA9828619F49A5821E54DFF0636AA5ECD679A5108CA4 |
| SSDEEP: | 192:tetO7tf1F5Dj/fMGINzQGnM+D542/Ue3gzSh6WmPTGGudwCLXvJPPnXE5L9cFNUt:t3/NImGMO5zUazh6fPTruwCLqL9csRB |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- OUTLOOK.EXE (PID: 276)
Reads the computer name
- OUTLOOK.EXE (PID: 276)
Searches for installed software
- OUTLOOK.EXE (PID: 276)
Creates files in the user directory
- OUTLOOK.EXE (PID: 276)
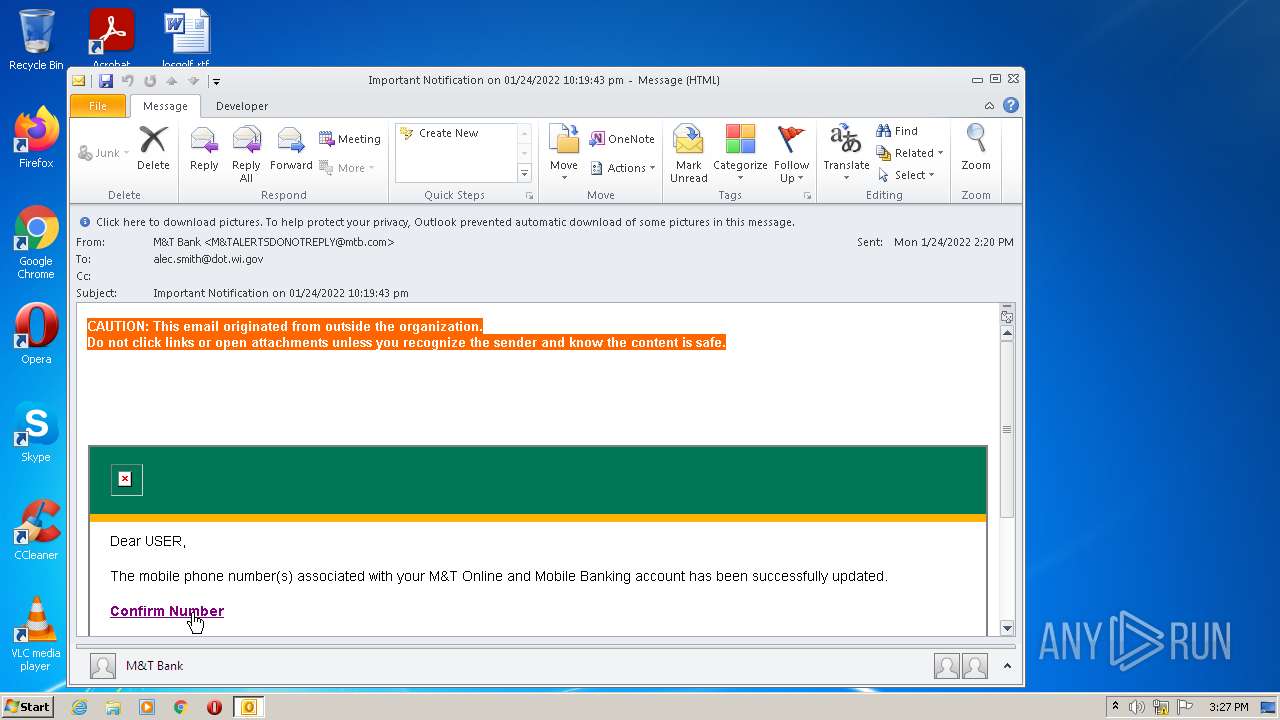
Starts Internet Explorer
- OUTLOOK.EXE (PID: 276)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3284)
- iexplore.exe (PID: 3036)
INFO
Reads the computer name
- iexplore.exe (PID: 1256)
- iexplore.exe (PID: 3284)
- iexplore.exe (PID: 3036)
Changes internet zones settings
- iexplore.exe (PID: 1256)
Reads settings of System Certificates
- iexplore.exe (PID: 3036)
- iexplore.exe (PID: 1256)
- iexplore.exe (PID: 3284)
Checks Windows Trust Settings
- iexplore.exe (PID: 1256)
- iexplore.exe (PID: 3284)
- iexplore.exe (PID: 3036)
Reads internet explorer settings
- iexplore.exe (PID: 3036)
- iexplore.exe (PID: 3284)
Checks supported languages
- iexplore.exe (PID: 3284)
- iexplore.exe (PID: 1256)
- iexplore.exe (PID: 3036)
Creates files in the user directory
- iexplore.exe (PID: 3284)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 276)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1256)
Changes settings of System certificates
- iexplore.exe (PID: 1256)
Application launched itself
- iexplore.exe (PID: 1256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\uploads_0823d948-0ef4-4a05-9b7f-6ca45c998bb0.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
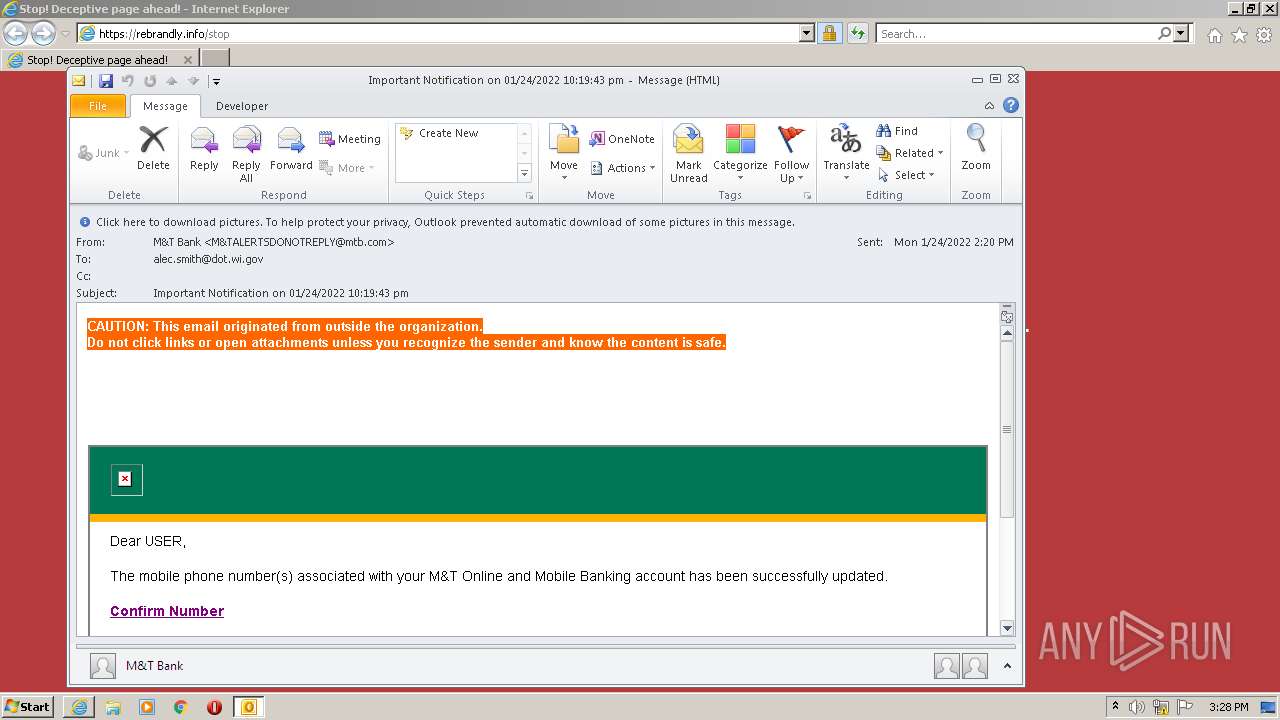
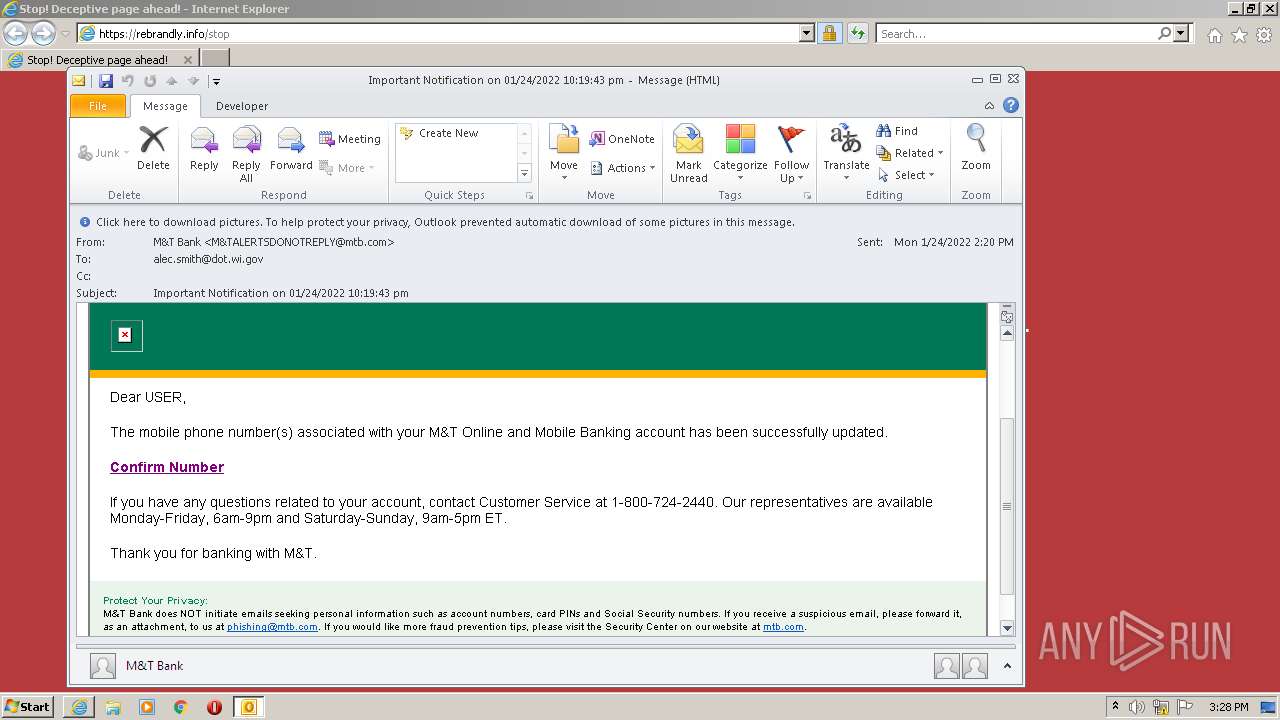
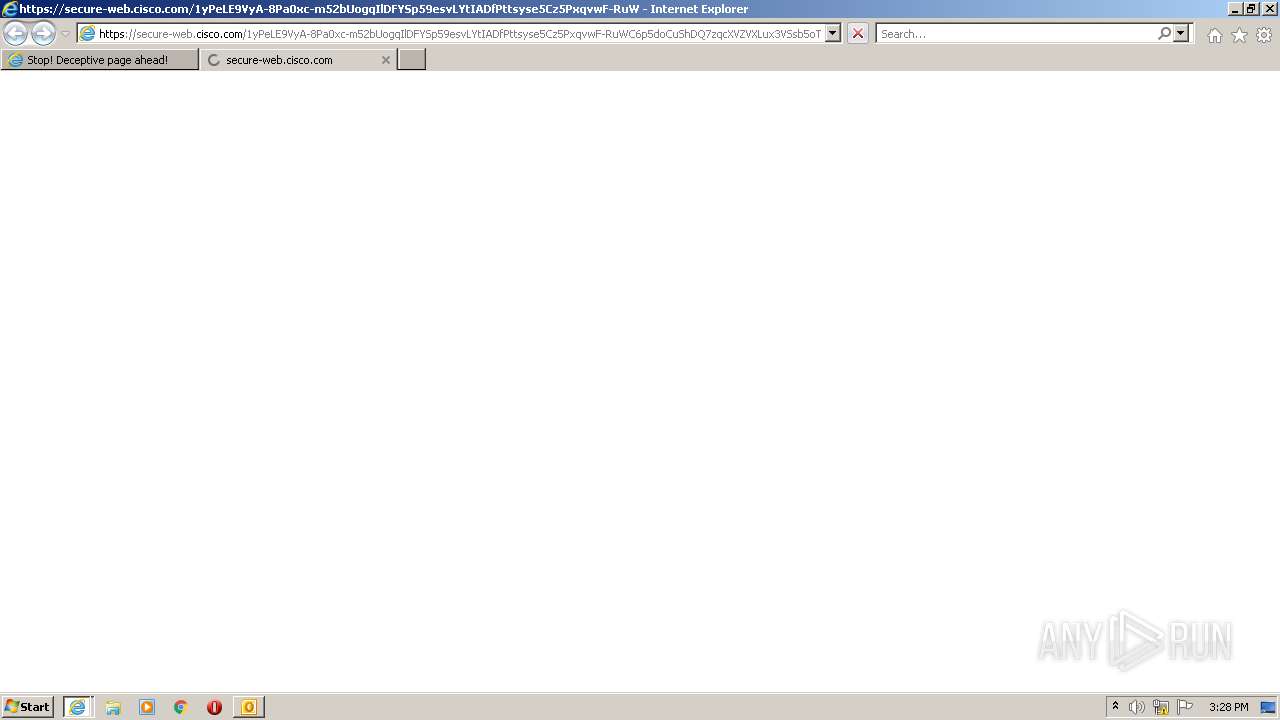
| 1256 | "C:\Program Files\Internet Explorer\iexplore.exe" https://secure-web.cisco.com/1JDJn4g0wA7iBi7K15tg4EJATDb2hVUWegUzILsiSHd4ZD-5hcC2jGBlhr8dzxTFEjMwro_e-JK4-IHp-aP3_sTUYJZvMaeMLUlQkdfV6MI9IABQyHeKBlgBr7Md8GzOce0HuhPYfZ_NUl16OlcTDfyczHciRHoPeUW0lyNEsYm7ZCwmQBMUUHHnRLBagTK11cJOfYaOgil6h9bFs9p86KsJUZT_y_wjRRtQKb56Zy2l9XyT0Hlcp5DEVVLltux81iIN2ItFz1wZQOUrokA7ipH2uwGdf9vDp6V58Wduz_5odhSbJEZAbxfqQCiXDTs7-/https%3A%2F%2Frebrand.ly%2Focnzbx9 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3036 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1256 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3284 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1256 CREDAT:3413259 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
22 903
Read events
22 094
Write events
787
Delete events
22
Modification events
| (PID) Process: | (276) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (276) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (276) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (276) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (276) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (276) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (276) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (276) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (276) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (276) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
36
Text files
124
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 276 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRE2D2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 276 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 276 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 276 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6CFED4E1A8866BE87BE17622BFB4D726_FBADB8F7FD7B56EE191ACF24A8989D94 | der | |
MD5:— | SHA256:— | |||
| 3036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6CFED4E1A8866BE87BE17622BFB4D726_FBADB8F7FD7B56EE191ACF24A8989D94 | binary | |
MD5:— | SHA256:— | |||
| 3036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\263821BCA2CBC5EA0B25012F05788322_41310C887E59D4EB5B8FD9D3DCA2C98D | binary | |
MD5:— | SHA256:— | |||
| 3036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\263821BCA2CBC5EA0B25012F05788322_41310C887E59D4EB5B8FD9D3DCA2C98D | der | |
MD5:— | SHA256:— | |||
| 3036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
| 3036 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
137
DNS requests
48
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
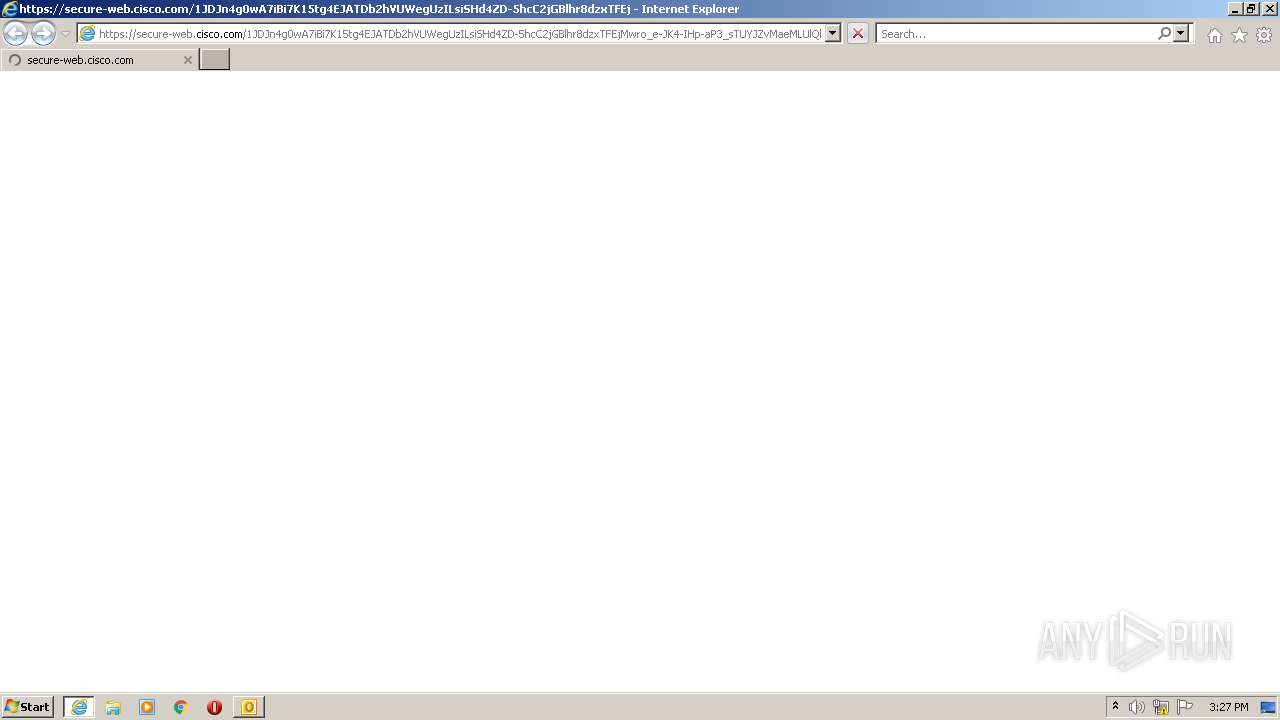
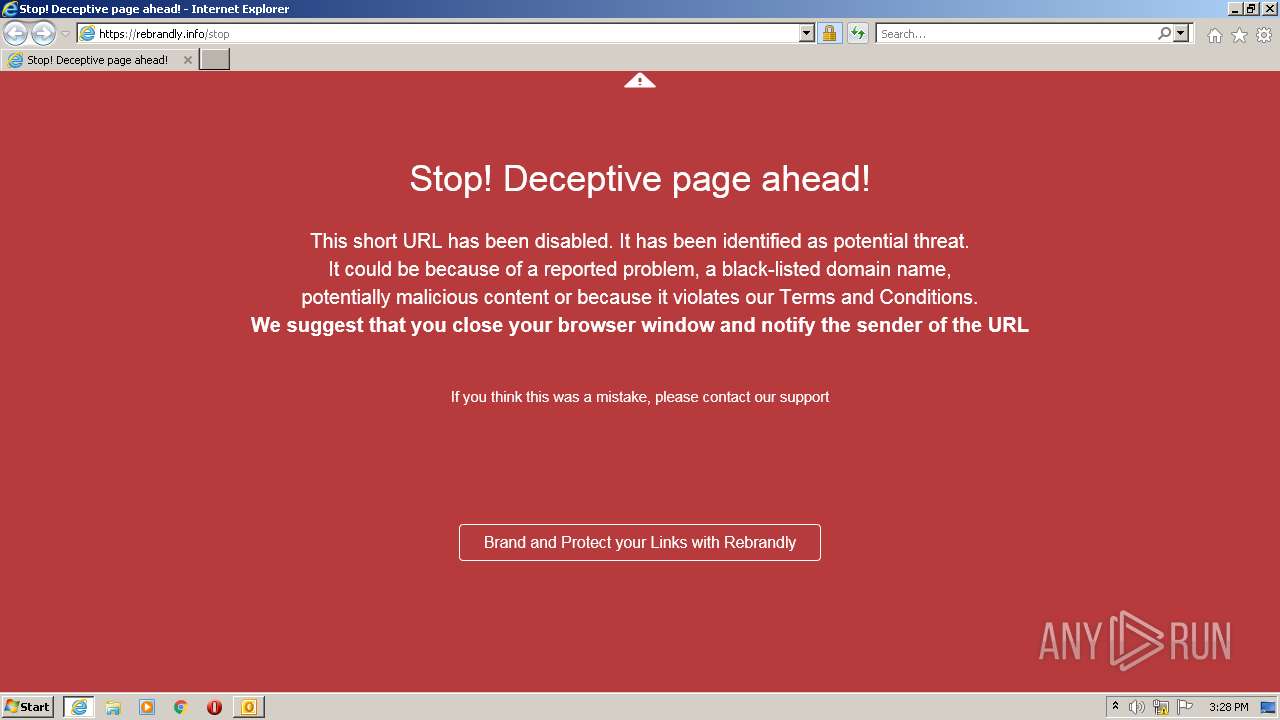
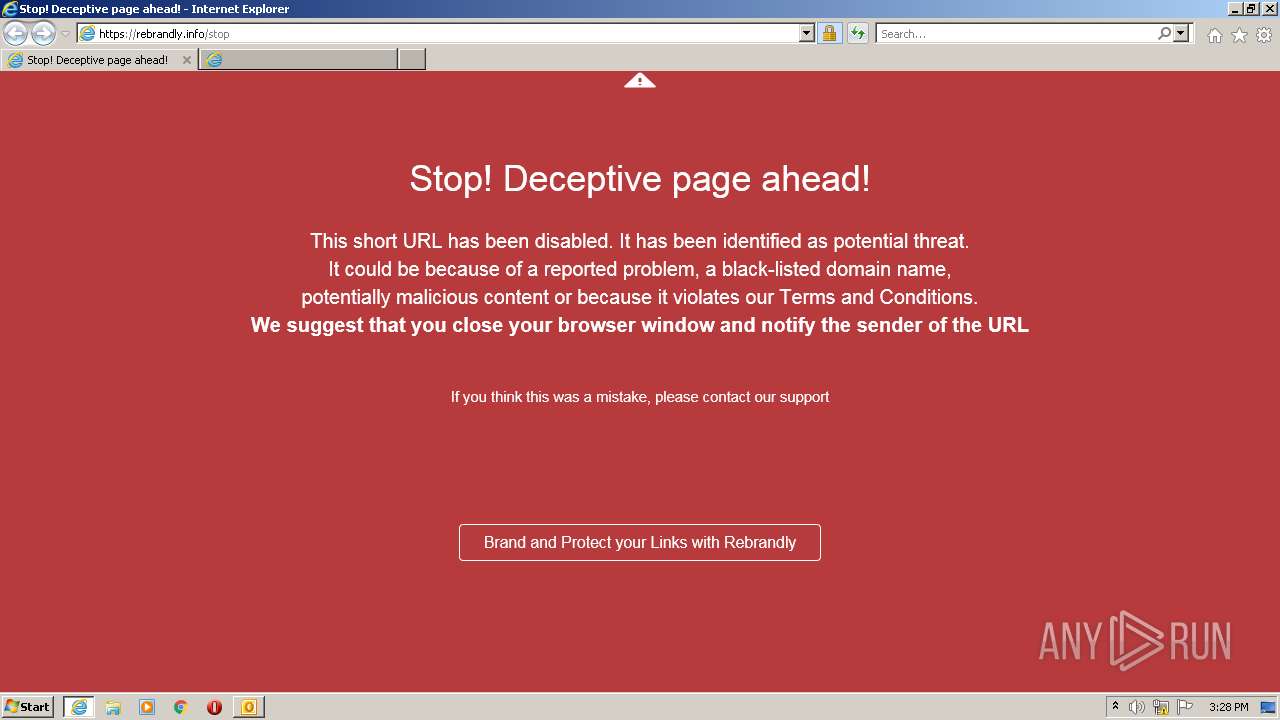
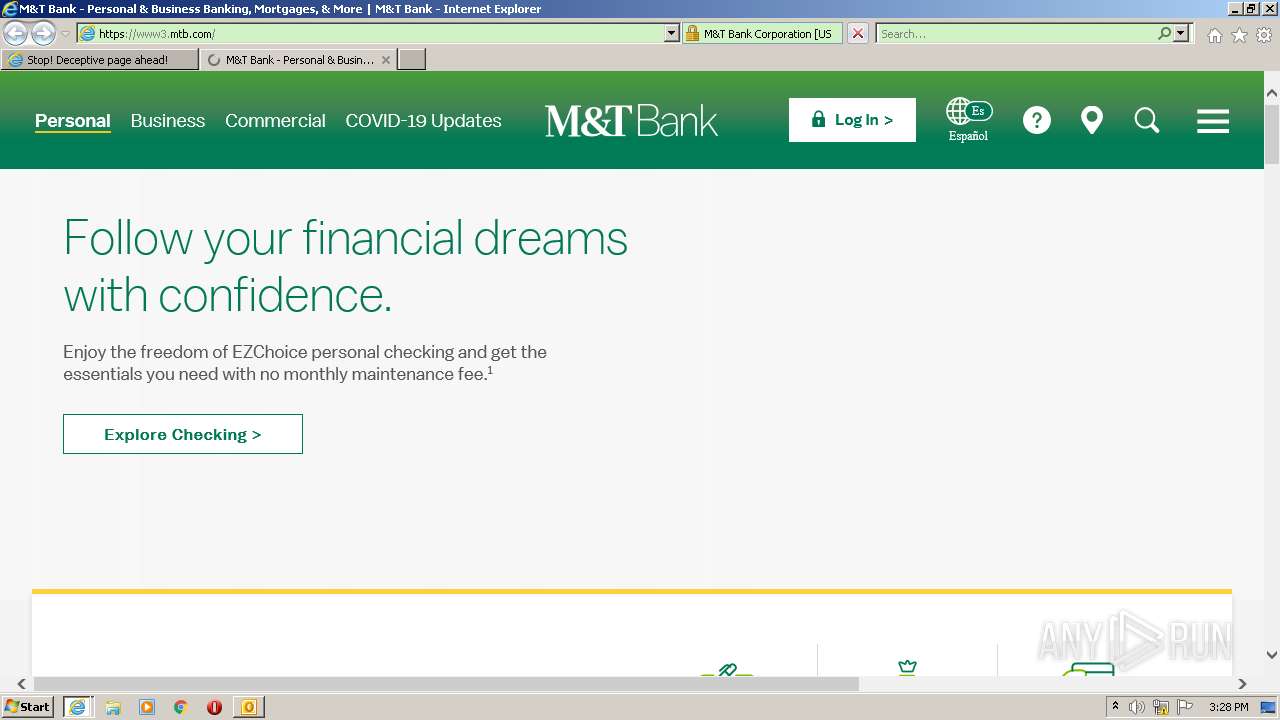
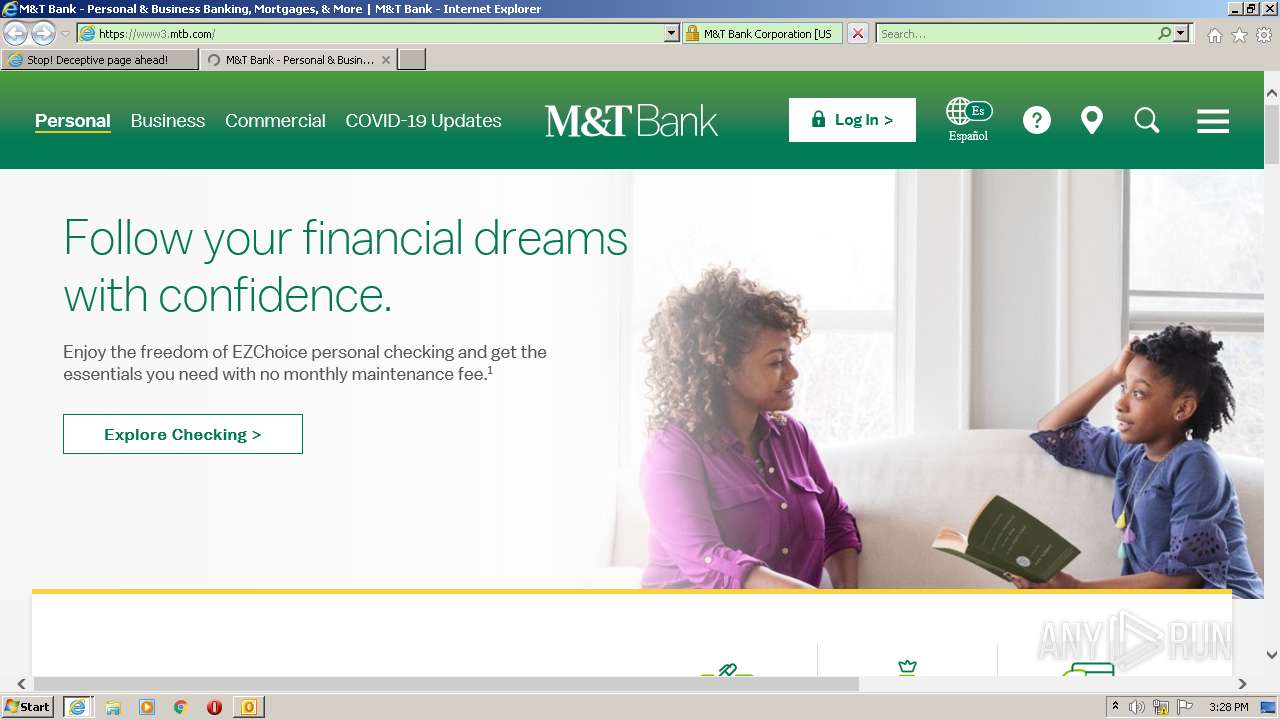
3036 | iexplore.exe | GET | 301 | 3.232.178.176:80 | http://rebrand.ly/ocnzbx9?rb.routing.mode=proxy&rb.routing.signature=902563 | US | — | — | whitelisted |
3036 | iexplore.exe | GET | 200 | 143.204.101.123:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3036 | iexplore.exe | GET | 200 | 192.35.177.23:80 | http://commercial.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTULRG8NAnkG2vMiFulhUophWOf2gQUibibtp7t%2B7DGvQ3sZ048o5KdLfkCEEABfOt6GkOKldoRYnQ%2BdUA%3D | US | der | 1.71 Kb | whitelisted |
3284 | iexplore.exe | GET | 200 | 104.89.37.9:80 | http://ocsp.entrust.net/MEUwQzBBMD8wPTAJBgUrDgMCGgUABBQsSqZpWQuWOxHU9pAda%2B7Lf6V20AQUaJDkZ6SmU4DHhmak8fdLQ%2FuEvW0CBFHTQEQ%3D | NL | der | 1.53 Kb | whitelisted |
3284 | iexplore.exe | GET | 200 | 104.89.37.9:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEDfrSfs9WeX5aWamCH1j0vs%3D | NL | der | 1.55 Kb | whitelisted |
3284 | iexplore.exe | GET | 200 | 104.89.37.9:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEB3aH4WmIdt0rI%2Fecl6gDKA%3D | NL | der | 1.55 Kb | whitelisted |
3036 | iexplore.exe | GET | 200 | 143.204.101.42:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3284 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEAPcXPipNqNLgWgvPi2Uwnc%3D | US | der | 471 b | whitelisted |
1256 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3284 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEALlWXxgIC%2BNSLF2h2cDq%2Bk%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3036 | iexplore.exe | 146.112.255.69:443 | secure-web.cisco.com | OpenDNS, LLC | — | suspicious |
— | — | 146.112.255.69:443 | secure-web.cisco.com | OpenDNS, LLC | — | suspicious |
3036 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3036 | iexplore.exe | 3.232.178.176:80 | rebrand.ly | — | US | unknown |
— | — | 143.204.98.84:443 | rebrandly.info | — | US | suspicious |
3036 | iexplore.exe | 143.204.101.123:80 | o.ss2.us | — | US | malicious |
276 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
1256 | iexplore.exe | 143.204.98.84:443 | rebrandly.info | — | US | suspicious |
3036 | iexplore.exe | 54.84.168.233:80 | rebrand.ly | Amazon.com, Inc. | US | unknown |
1256 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
secure-web.cisco.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
commercial.ocsp.identrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
rebrand.ly |
| whitelisted |
rebrandly.info |
| whitelisted |
o.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |