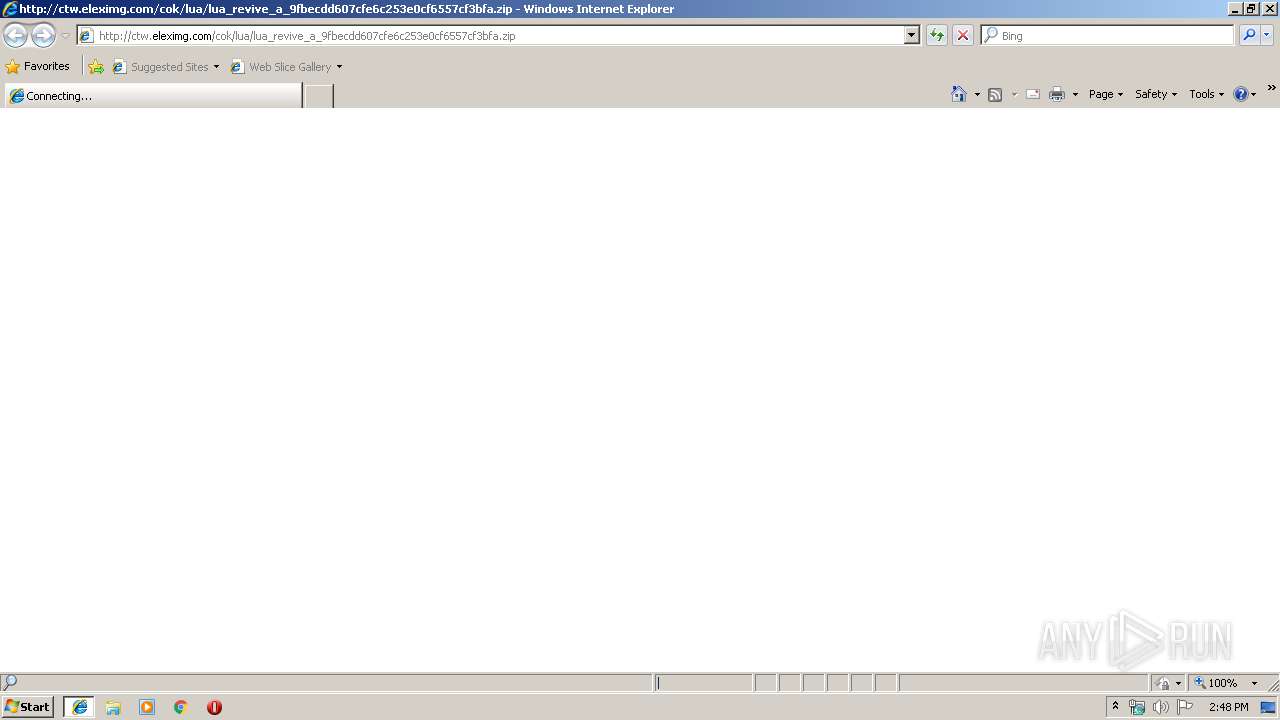
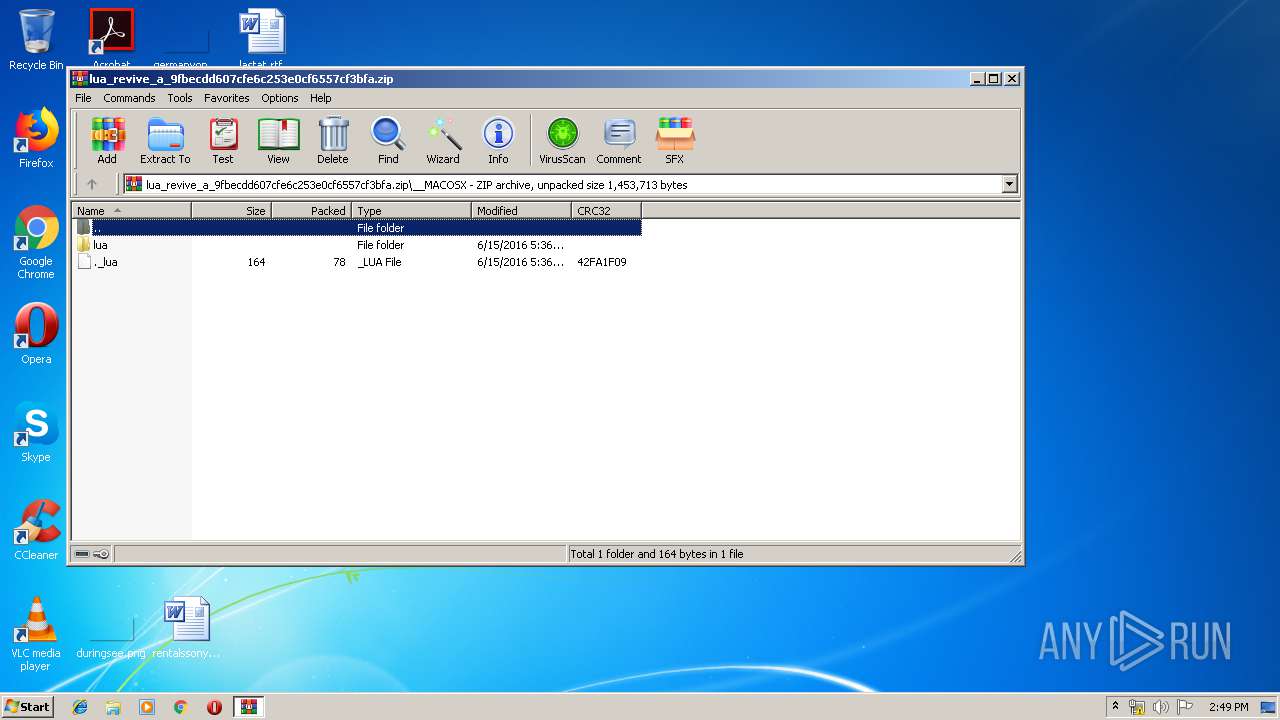
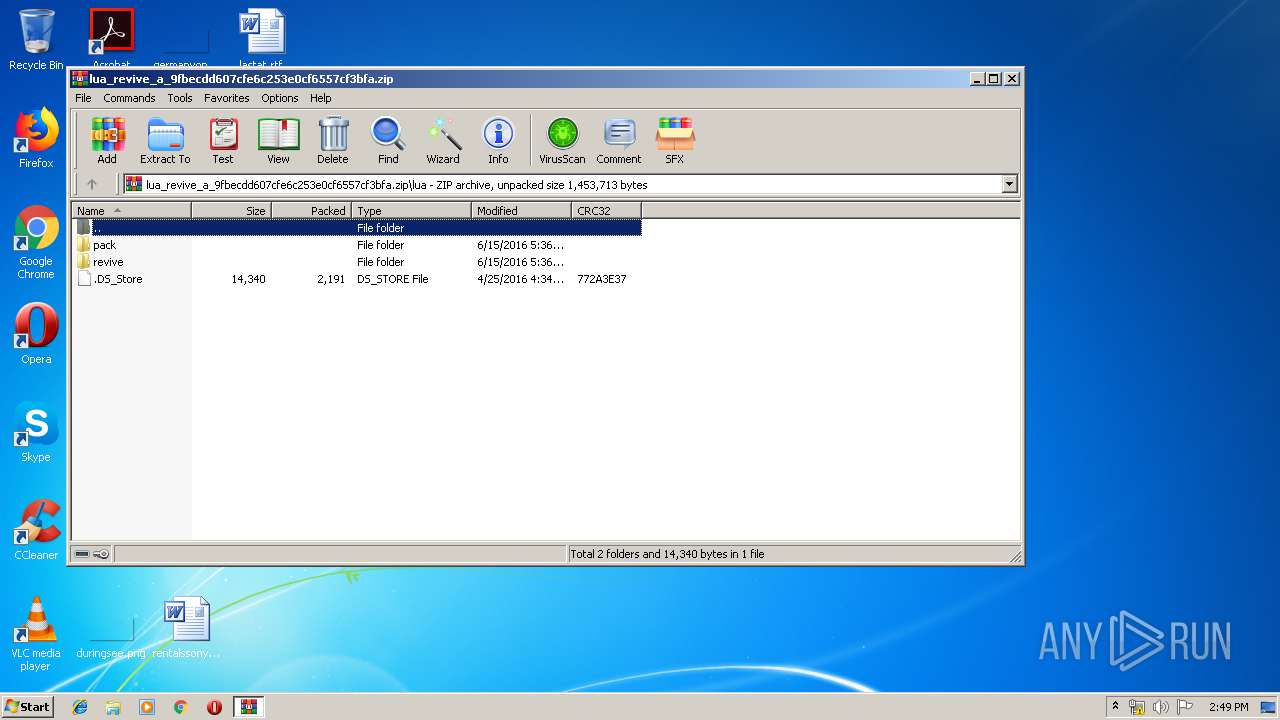
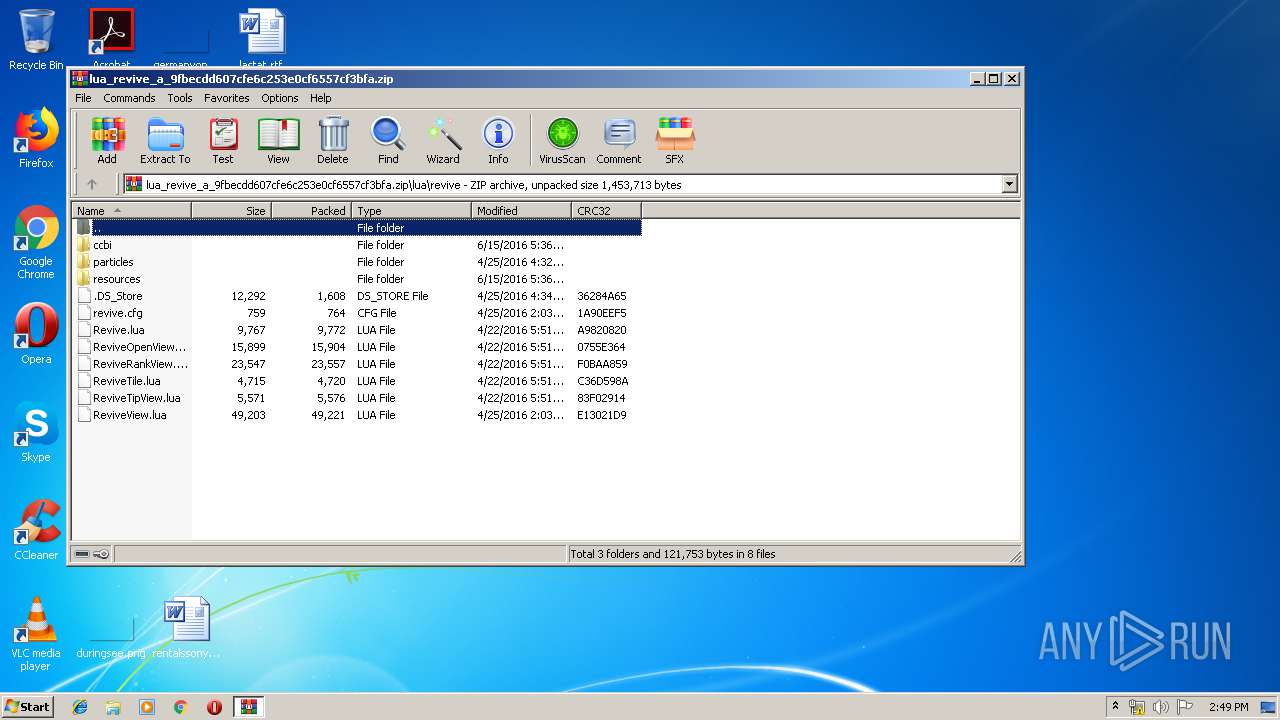
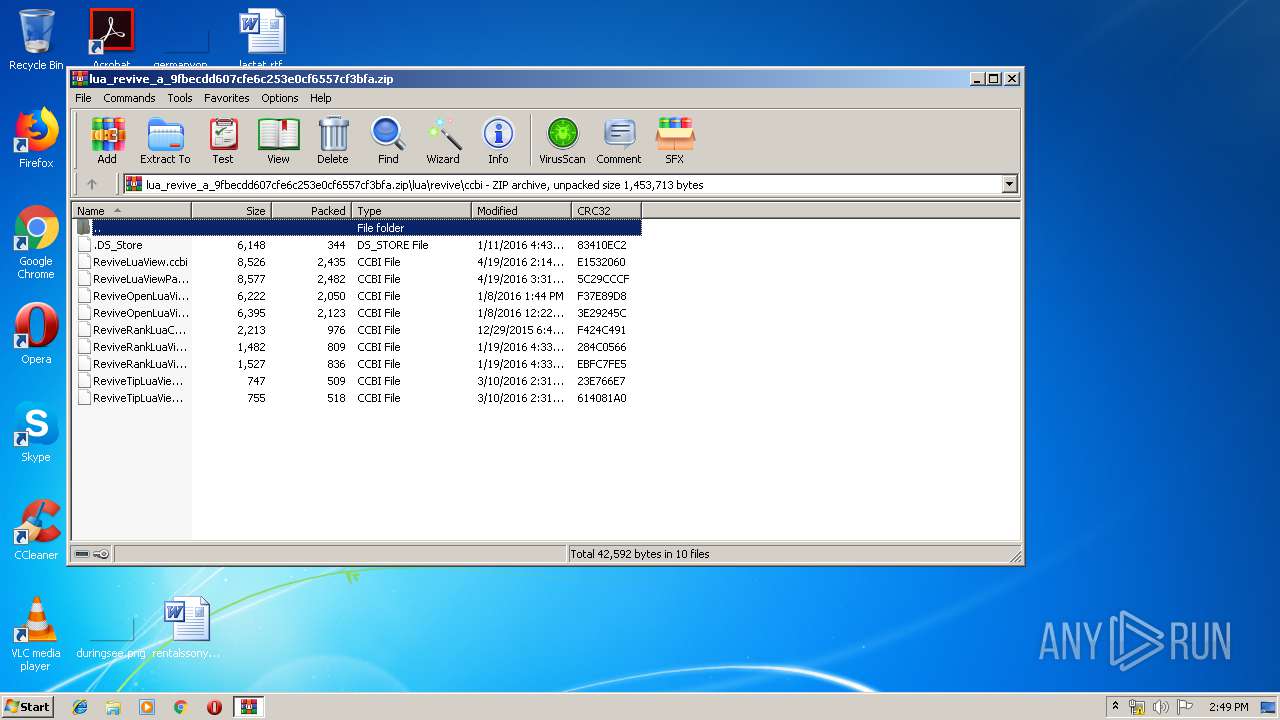
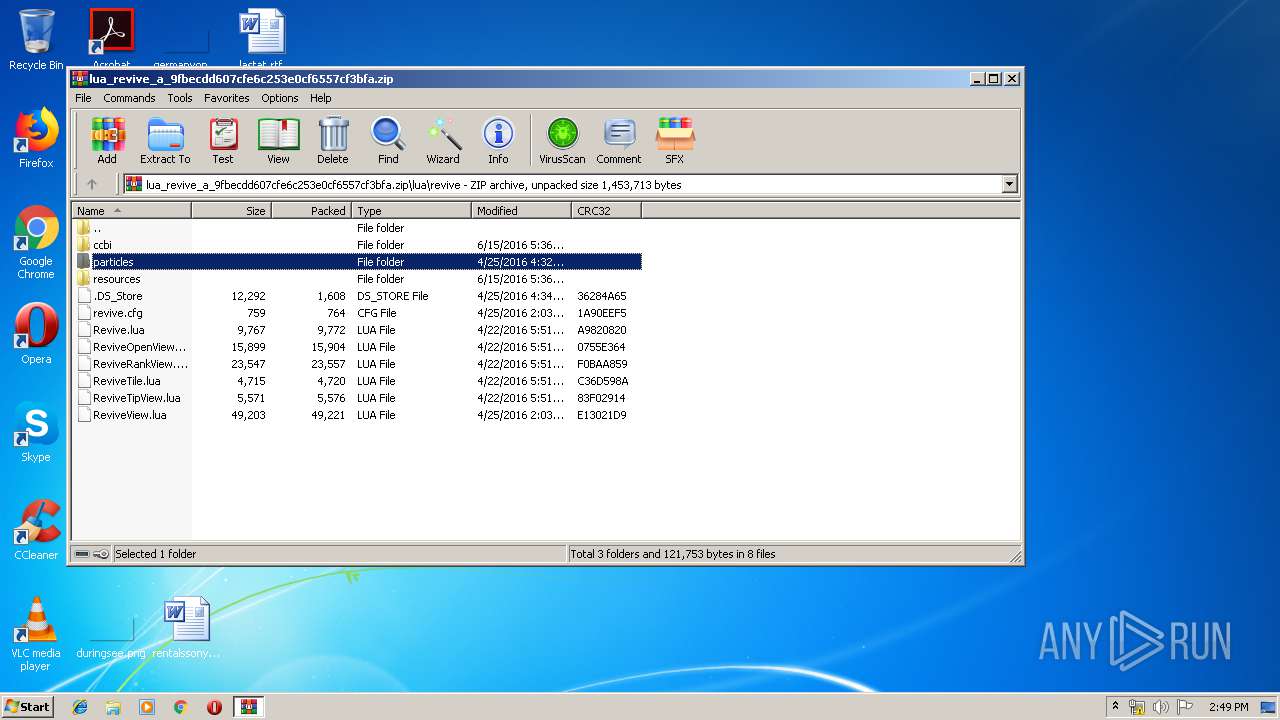
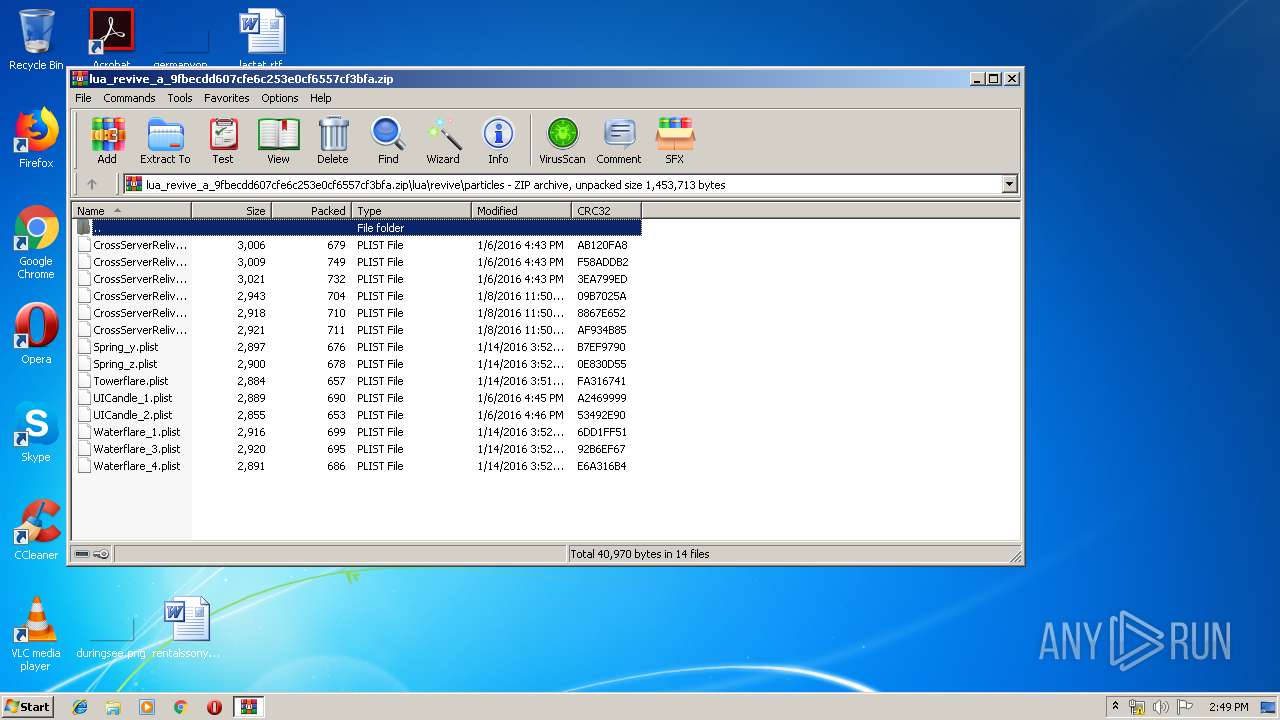
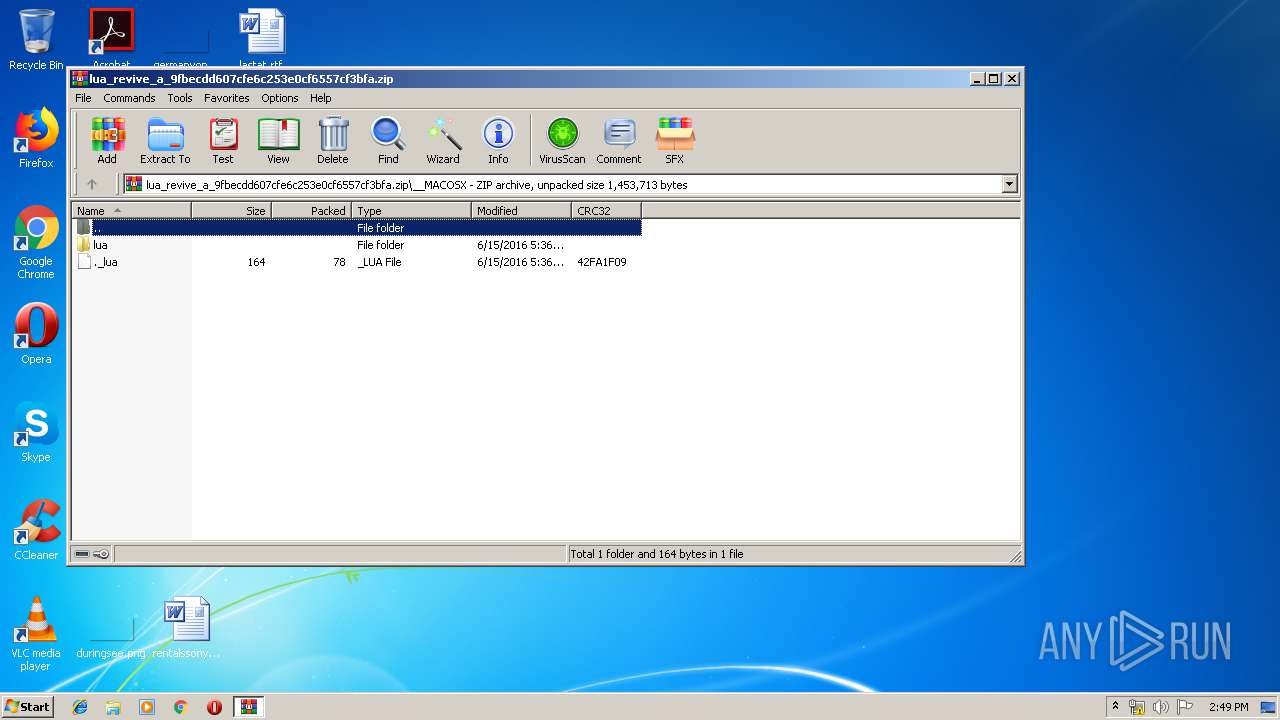
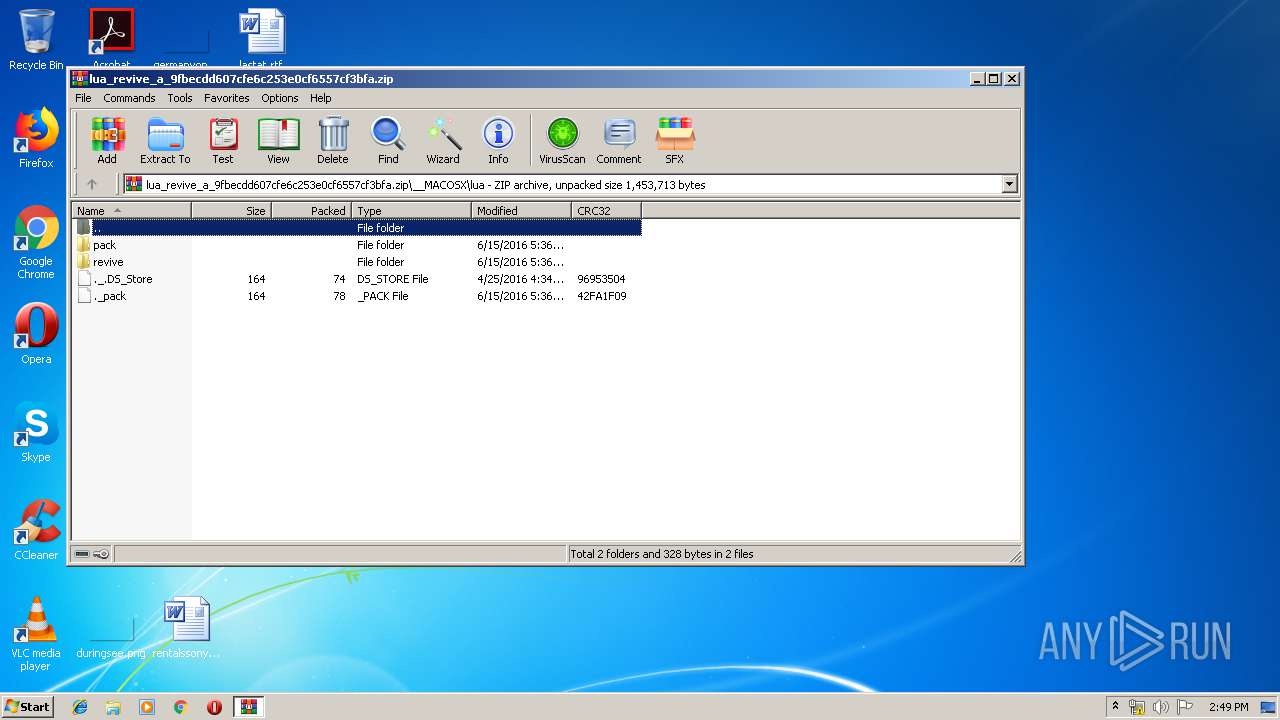
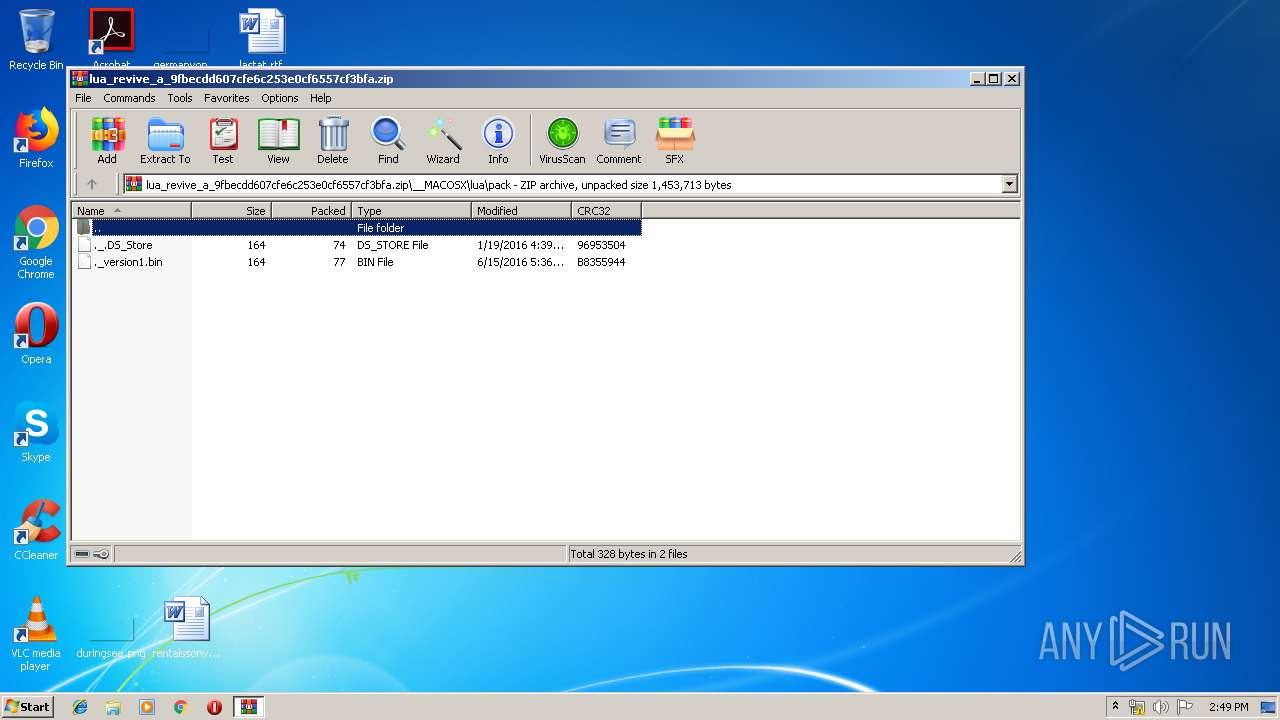
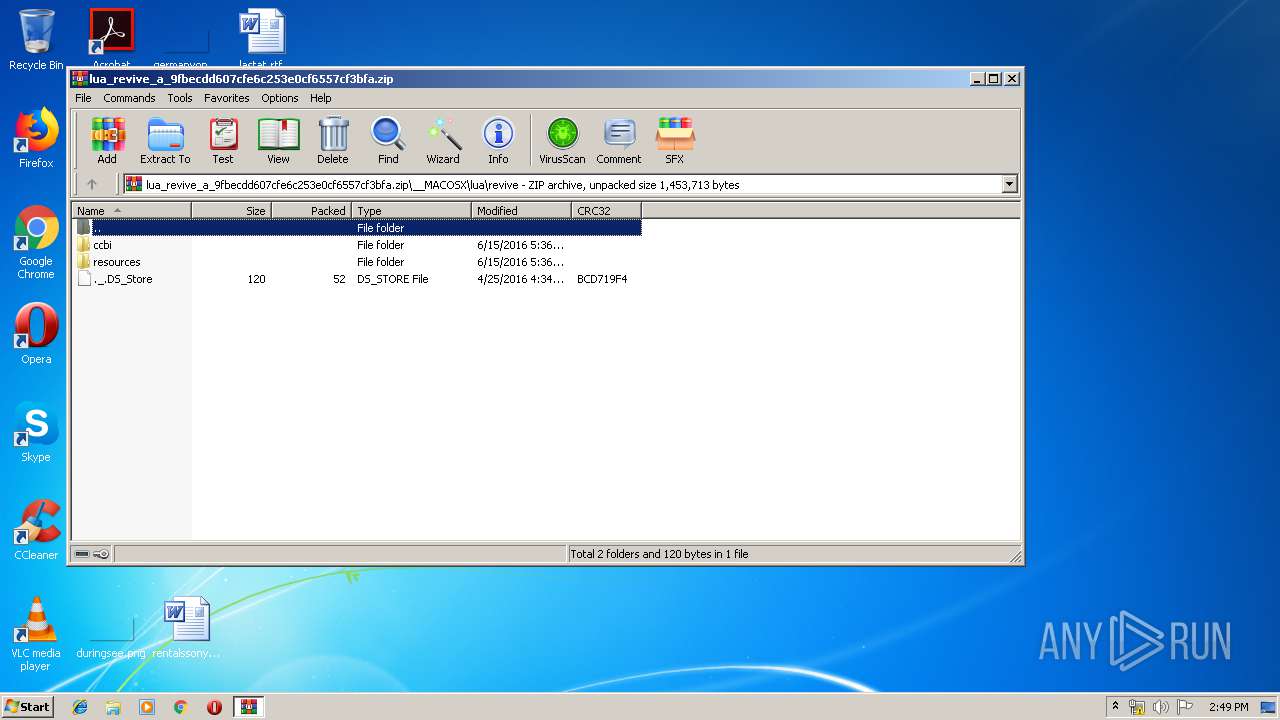
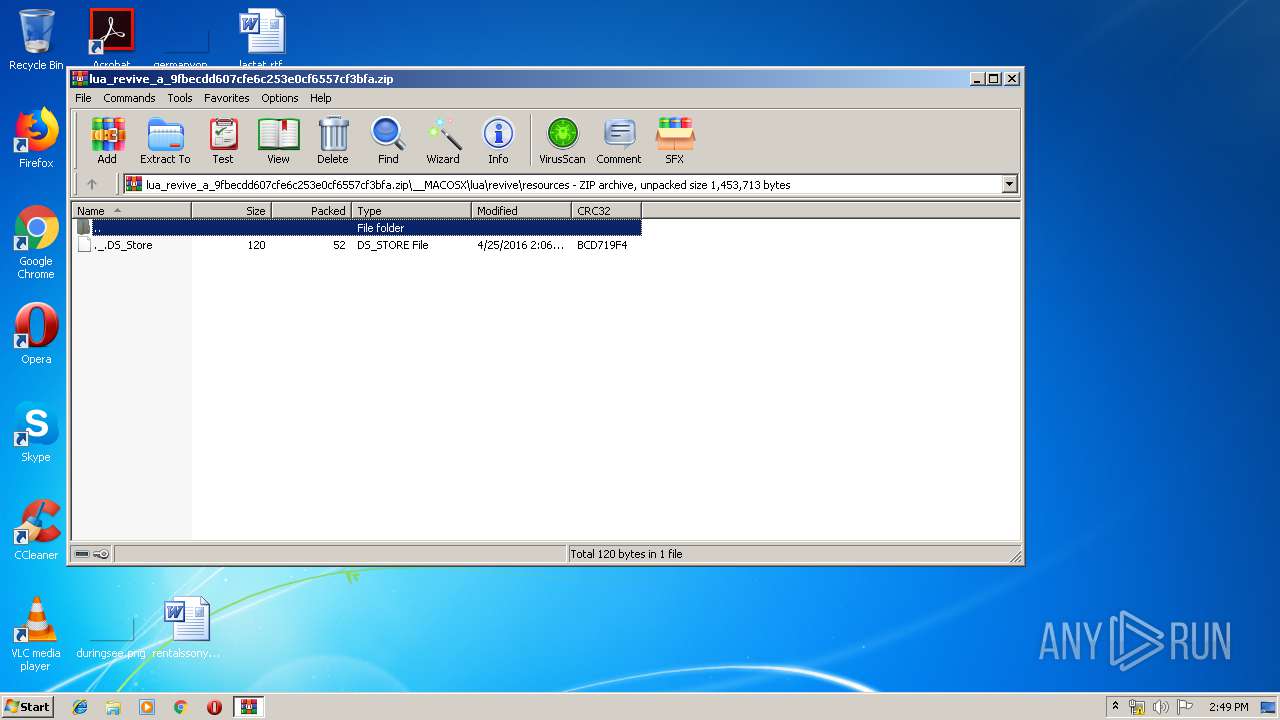
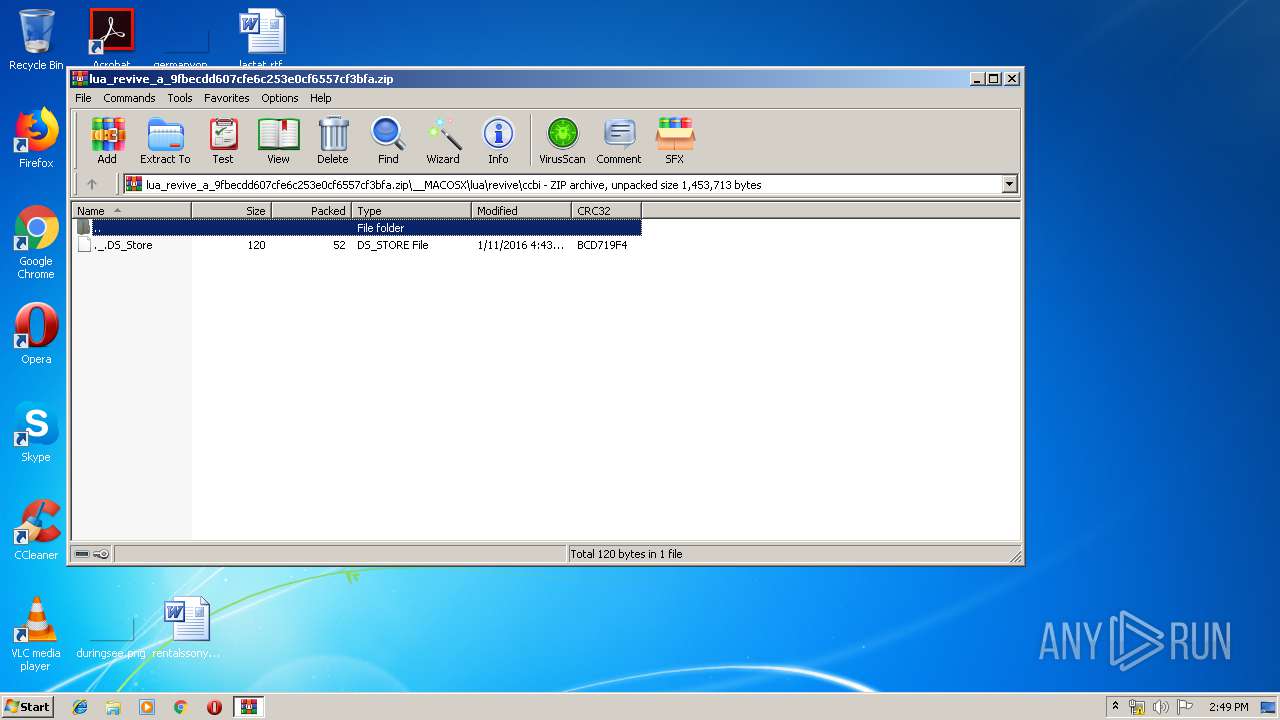
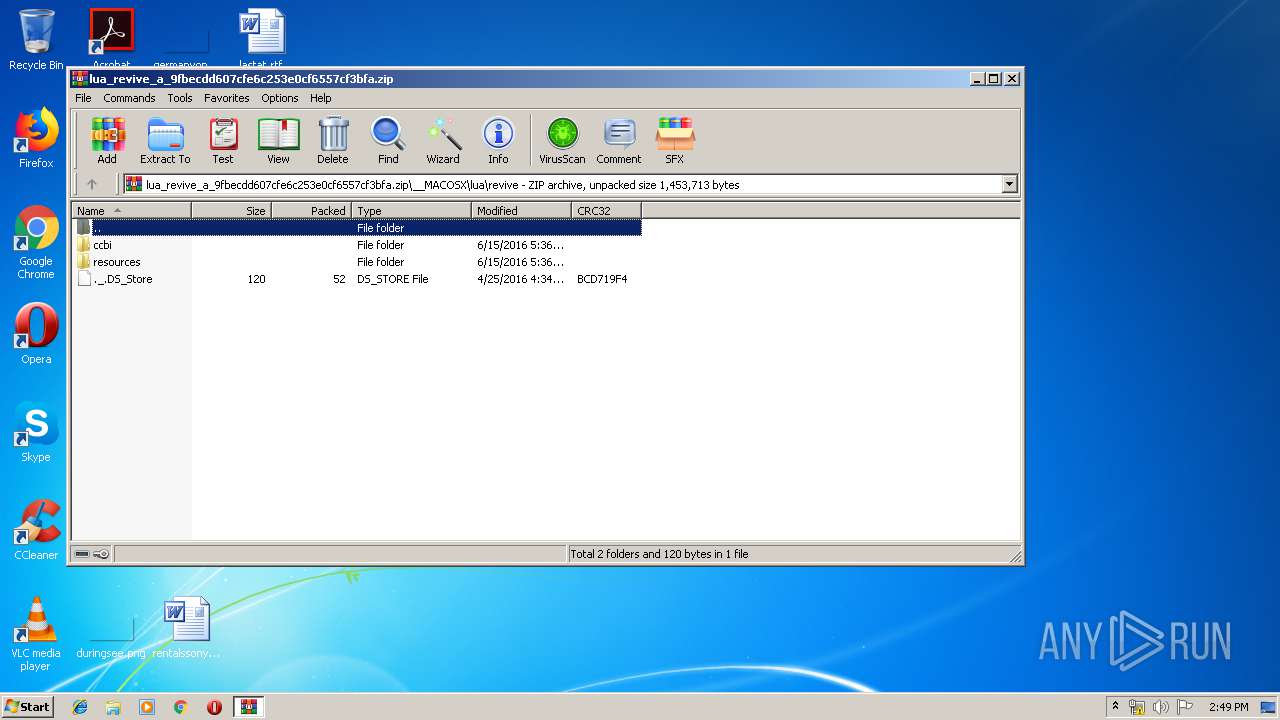
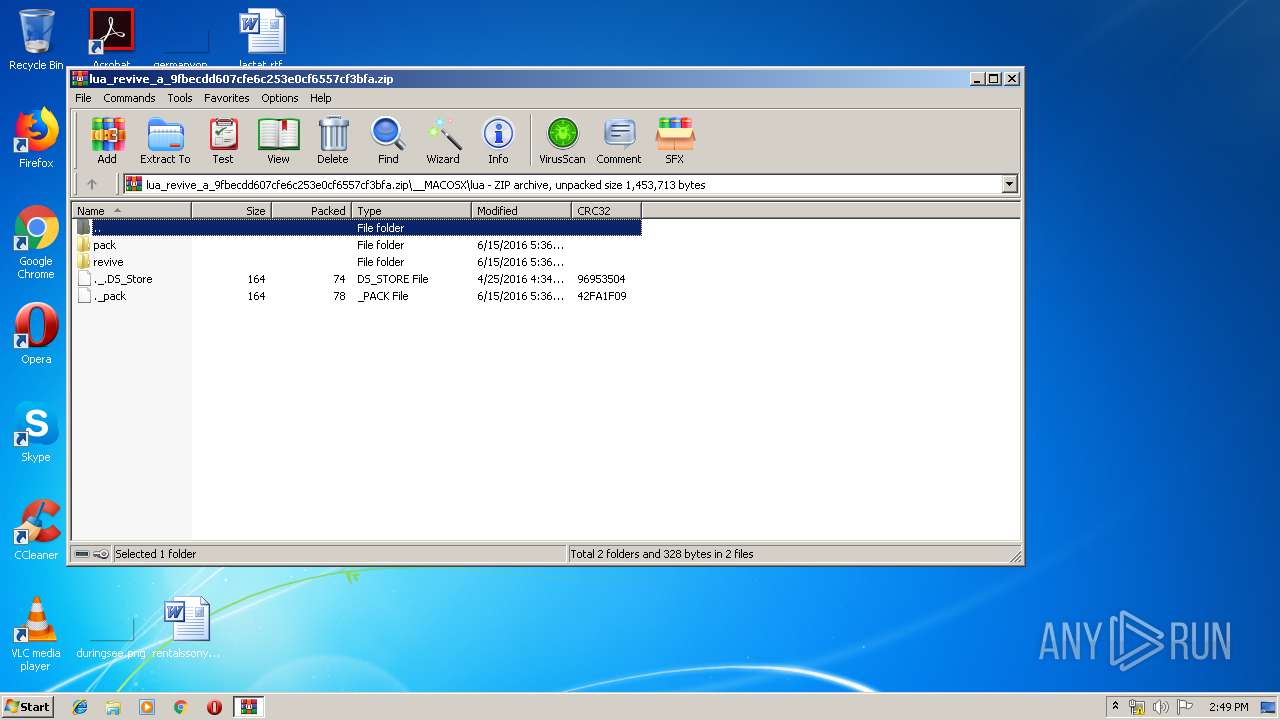
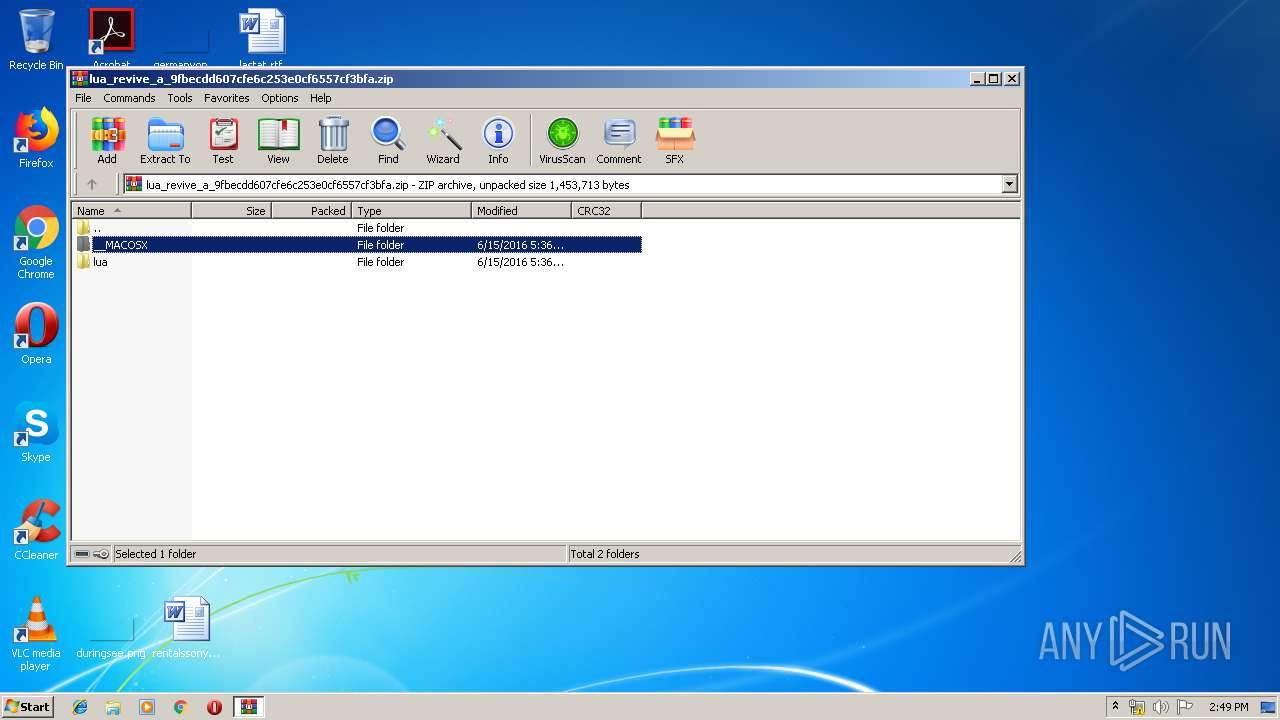
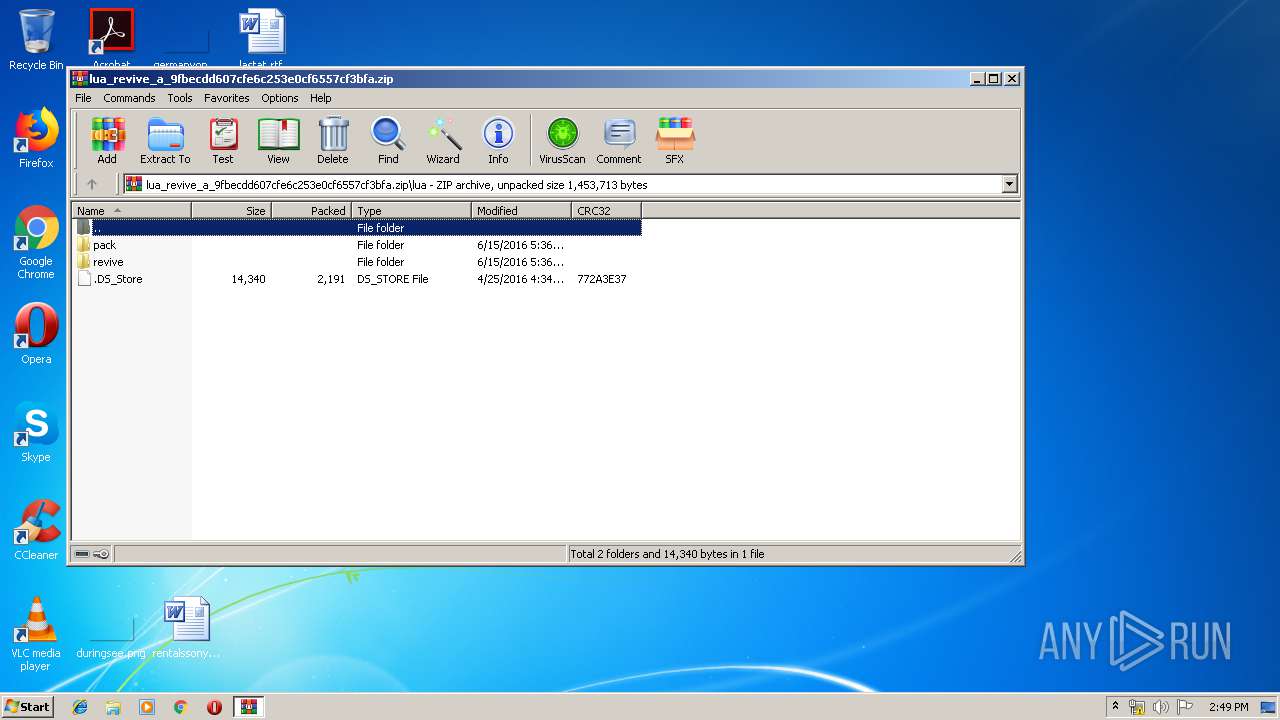
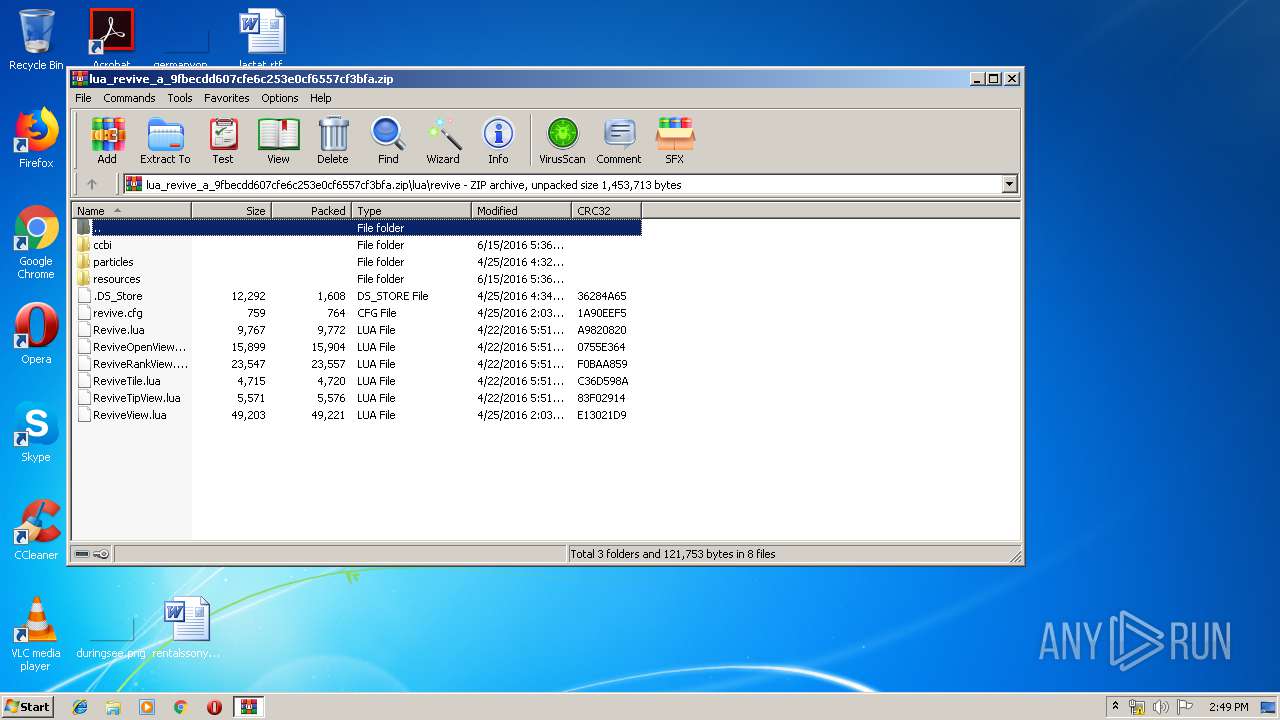
| URL: | http://ctw.eleximg.com/cok/lua/lua_revive_a_9fbecdd607cfe6c253e0cf6557cf3bfa.zip |
| Full analysis: | https://app.any.run/tasks/46ba13c6-0520-45b8-af65-b73e21808837 |
| Verdict: | No threats detected |
| Analysis date: | January 15, 2020, 14:48:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AF354A50A763DB74140BF151E1EECCBC |
| SHA1: | 40C452EAEF0FFB1E71AB3624FF1BF91022FDE00C |
| SHA256: | F2CF3C777806FEA1A3B84E894178A236CCEDD9CB614F36BF8B59A600320F22DB |
| SSDEEP: | 3:N1KdRSwAdMZIKGKOS9Xgv3DHjT21QFSPHRVn:C3Ad1dM9Xg/DDTmQoPHzn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
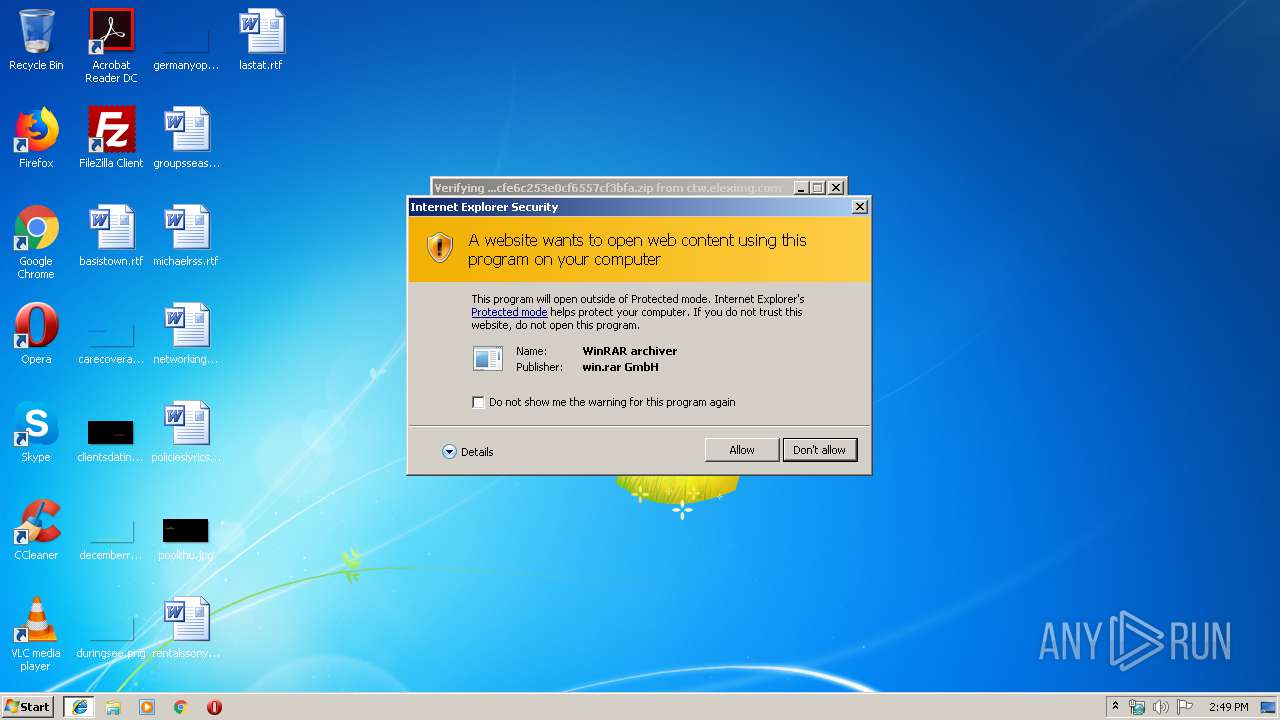
Changes internet zones settings
- iexplore.exe (PID: 2516)
Reads settings of System Certificates
- iexplore.exe (PID: 2516)
Application launched itself
- iexplore.exe (PID: 2516)
Reads Internet Cache Settings
- iexplore.exe (PID: 1416)
- iexplore.exe (PID: 2516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
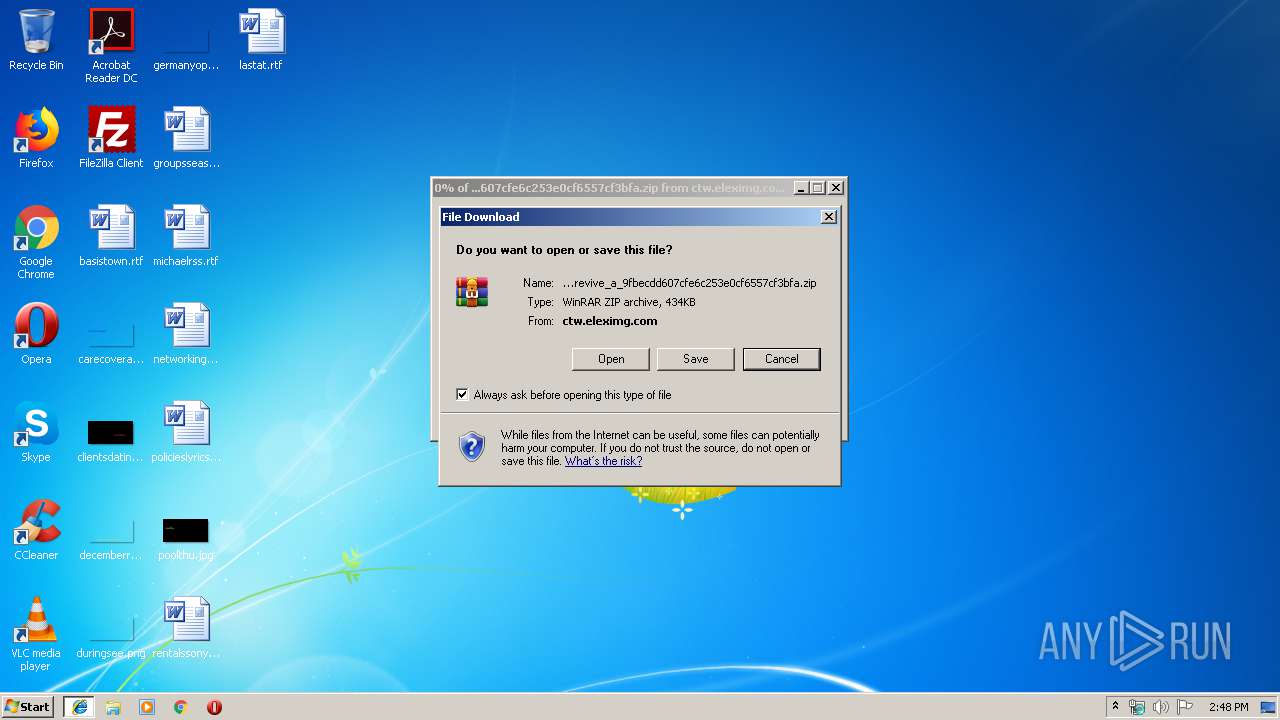
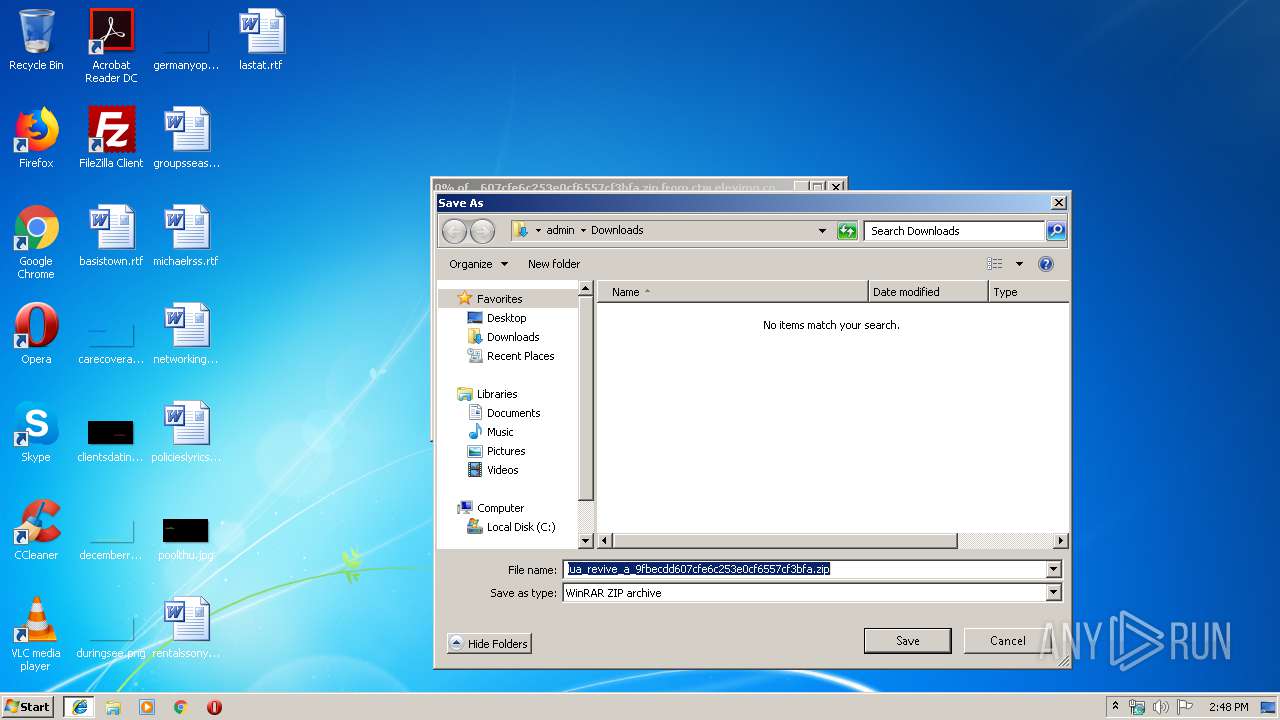
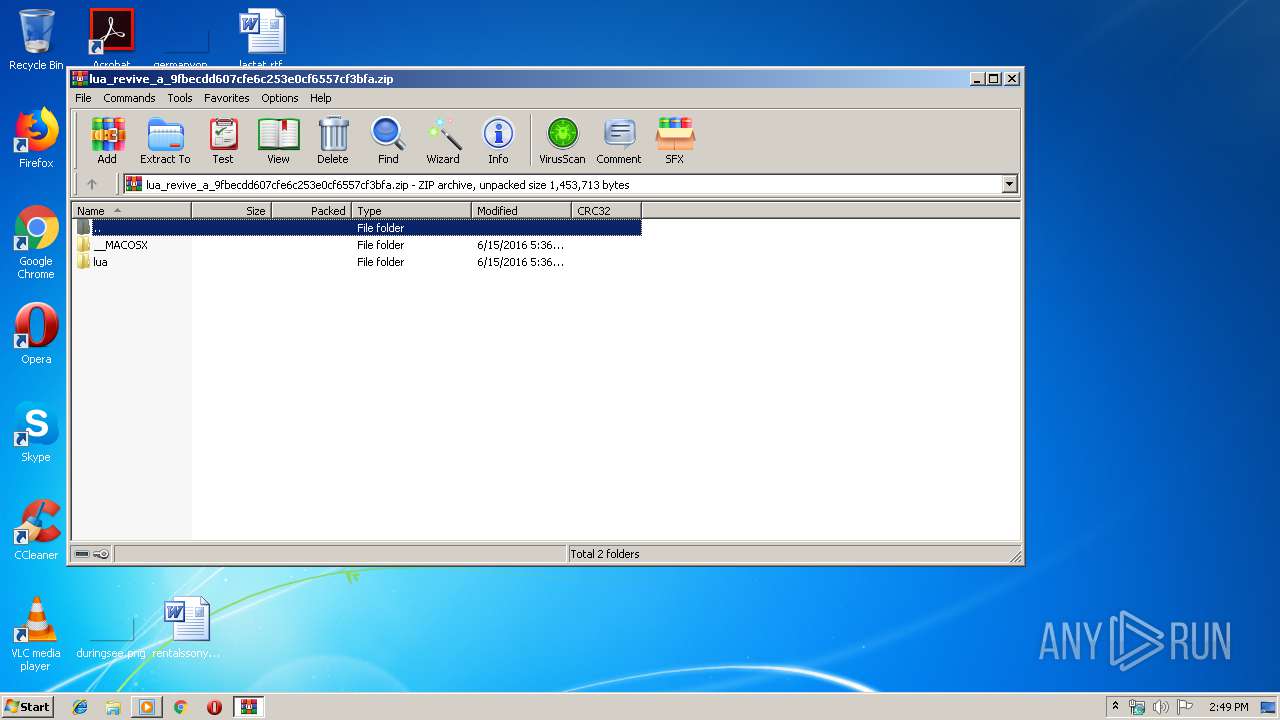
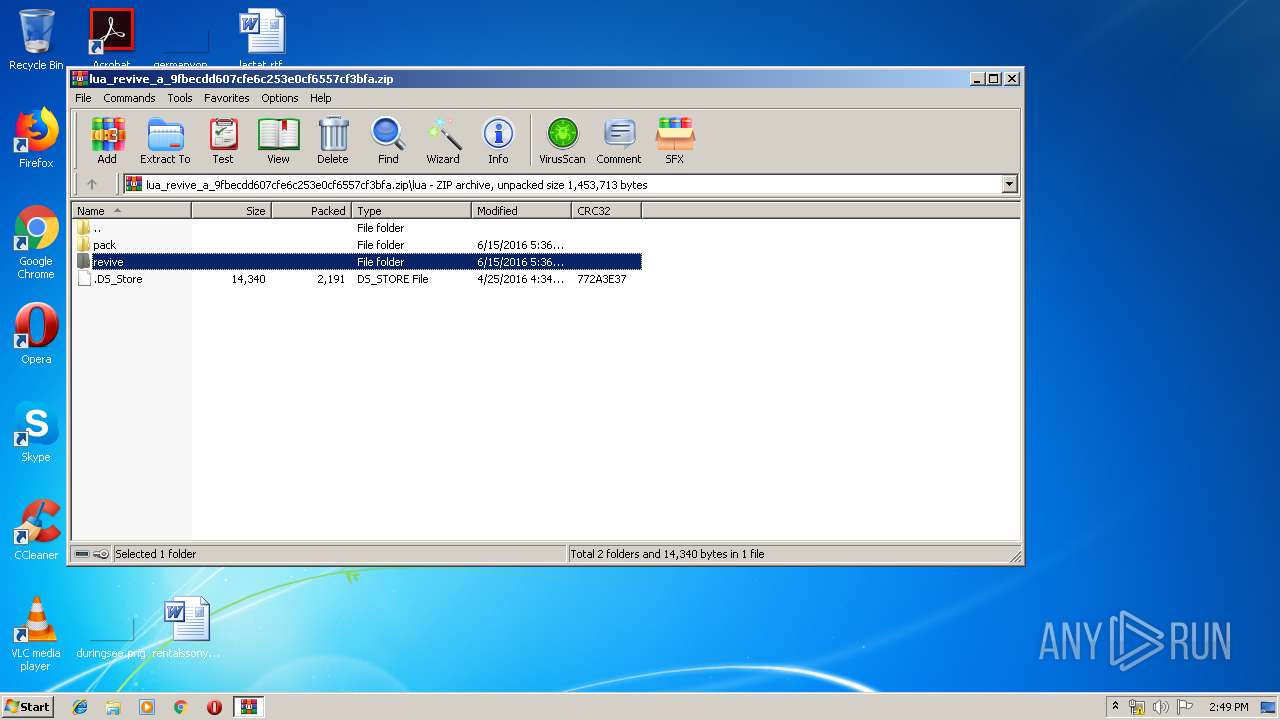
| 892 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\lua_revive_a_9fbecdd607cfe6c253e0cf6557cf3bfa.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1416 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2516 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://ctw.eleximg.com/cok/lua/lua_revive_a_9fbecdd607cfe6c253e0cf6557cf3bfa.zip" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 328
Read events
1 170
Write events
154
Delete events
4
Modification events
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {0E6F4FFD-37A6-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2516) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E407010003000F000E0030000E008C02 | |||
Executable files
0
Suspicious files
3
Text files
7
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF730BA6E397BCC963.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF58F53644E0156B30.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{0E6F4FFD-37A6-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 1416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
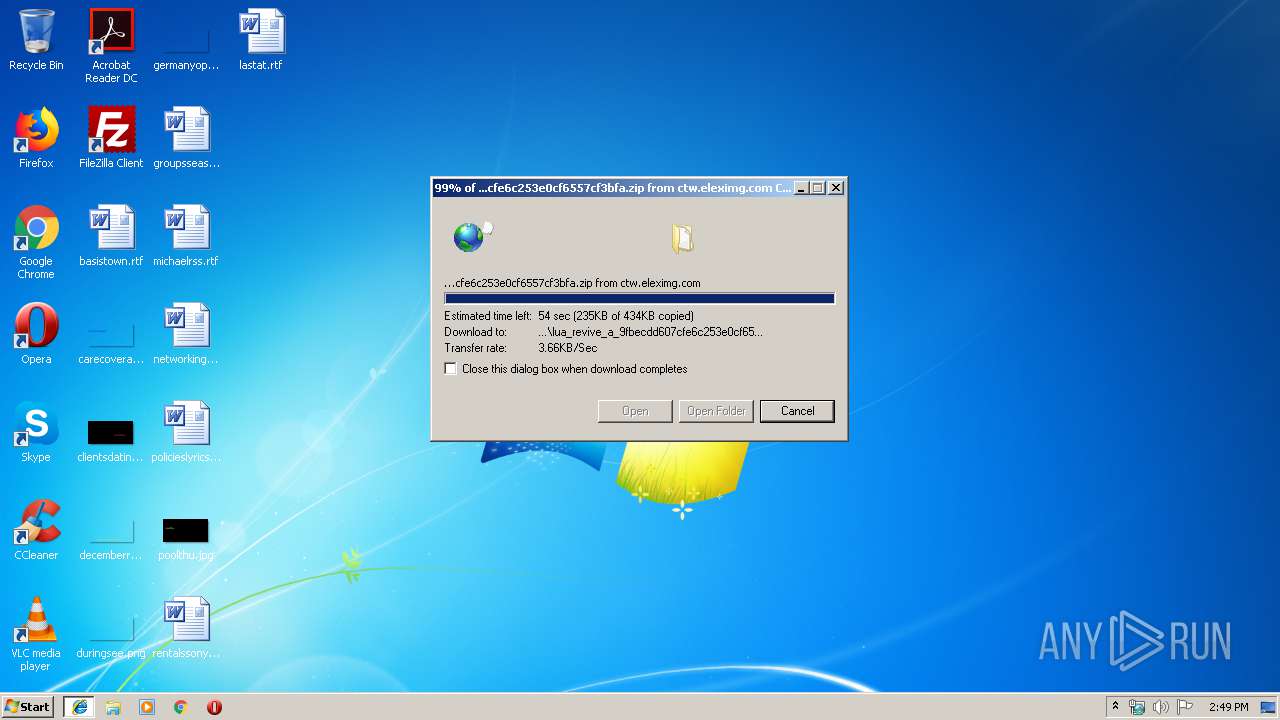
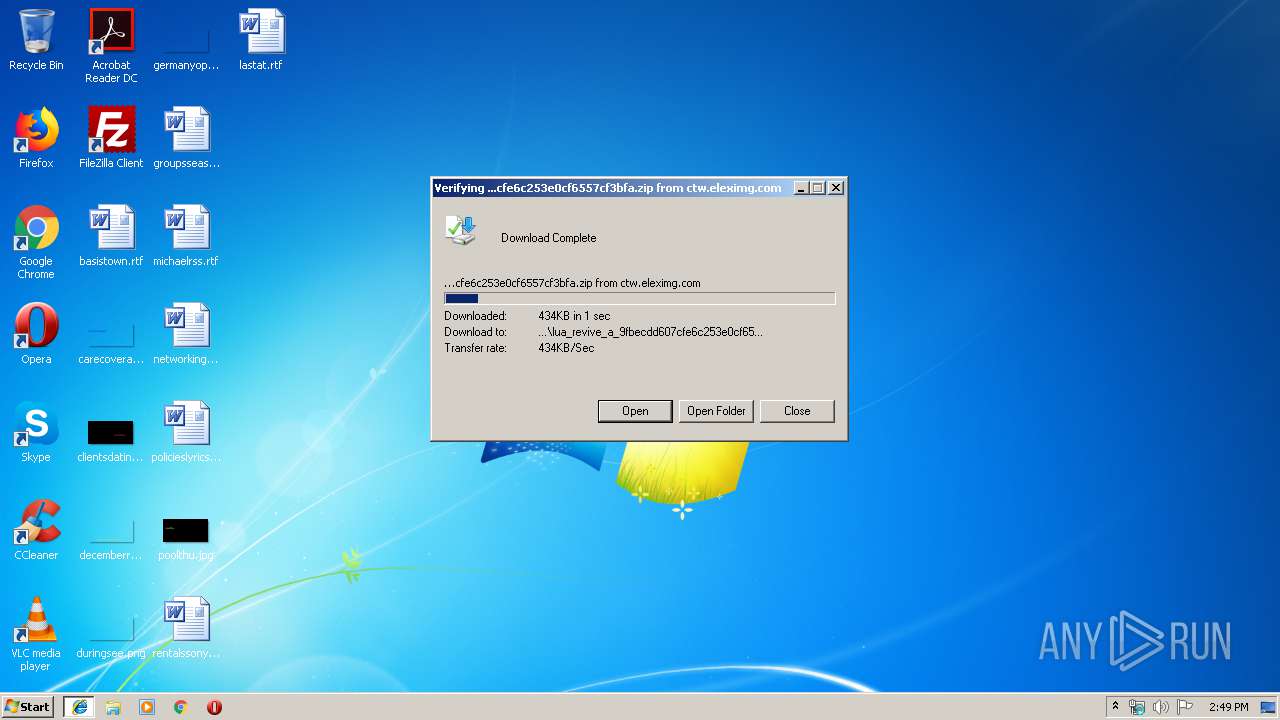
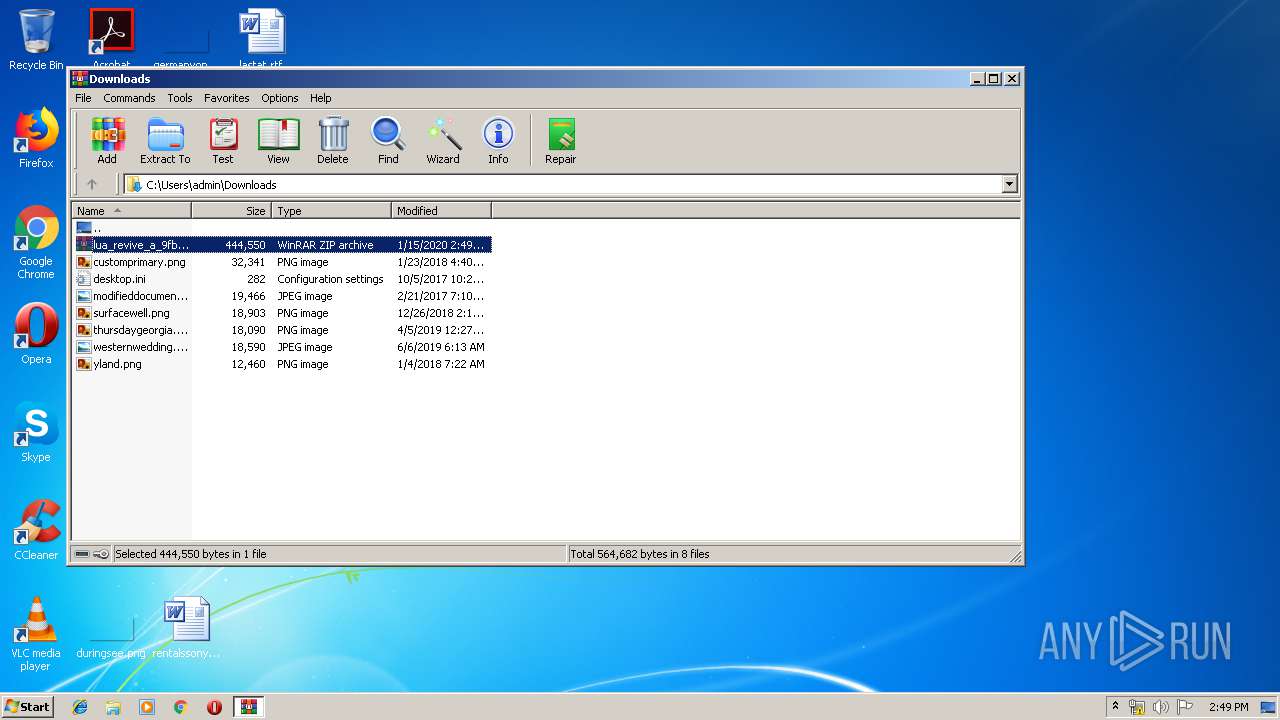
| 1416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\L9VLSA3H\lua_revive_a_9fbecdd607cfe6c253e0cf6557cf3bfa[1].zip | compressed | |
MD5:— | SHA256:— | |||
| 1416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\MSHist012020011520200116\index.dat | dat | |
MD5:— | SHA256:— | |||
| 1416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\VPVB4L6N\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 1416 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\L9VLSA3H\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1416 | iexplore.exe | GET | 200 | 2.16.186.64:80 | http://ctw.eleximg.com/cok/lua/lua_revive_a_9fbecdd607cfe6c253e0cf6557cf3bfa.zip | unknown | compressed | 434 Kb | whitelisted |
2516 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2516 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1416 | iexplore.exe | 2.16.186.64:80 | ctw.eleximg.com | Akamai International B.V. | — | whitelisted |
1416 | iexplore.exe | 2.16.186.115:80 | ctw.eleximg.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctw.eleximg.com |
| whitelisted |
www.bing.com |
| whitelisted |