| File name: | VolcanoUpdater.exe |
| Full analysis: | https://app.any.run/tasks/71a4bac9-2d7c-47ae-a295-628c57f53e84 |
| Verdict: | Malicious activity |
| Analysis date: | July 07, 2025, 11:11:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 14 sections |
| MD5: | BA317846710D02A8CACEDFE474ED781A |
| SHA1: | F9E425C55B5DB03CBE4F726C10563EF4952E8D50 |
| SHA256: | F2C84F5BA3B30EE992E63129721BC22C0FED27FCACE7D19AD7C9887E4C1B7821 |
| SSDEEP: | 98304:ryOfn7B1giIdckwirGiCqyFqwbxMqbMuZQQDuw/pYIJUZst8XJ3wAMic5fh2DF8P:2kZ+K75MmH |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the BIOS version
- VolcanoUpdater.exe (PID: 6724)
- VolcanoUI.exe (PID: 6140)
Reads security settings of Internet Explorer
- VolcanoUpdater.exe (PID: 6724)
Executable content was dropped or overwritten
- VolcanoUpdater.exe (PID: 6724)
- VolcanoUI.exe (PID: 6140)
Reads the date of Windows installation
- VolcanoUpdater.exe (PID: 6724)
Process drops legitimate windows executable
- VolcanoUI.exe (PID: 6140)
INFO
Checks supported languages
- VolcanoUpdater.exe (PID: 6724)
- VolcanoUI.exe (PID: 6140)
Create files in a temporary directory
- VolcanoUpdater.exe (PID: 6724)
- VolcanoUI.exe (PID: 6140)
Process checks computer location settings
- VolcanoUpdater.exe (PID: 6724)
Reads the computer name
- VolcanoUpdater.exe (PID: 6724)
- VolcanoUI.exe (PID: 6140)
The sample compiled with english language support
- VolcanoUI.exe (PID: 6140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:14 20:29:47+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.38 |
| CodeSize: | 801280 |
| InitializedDataSize: | 262656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7e3058 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
135
Monitored processes
3
Malicious processes
2
Suspicious processes
0
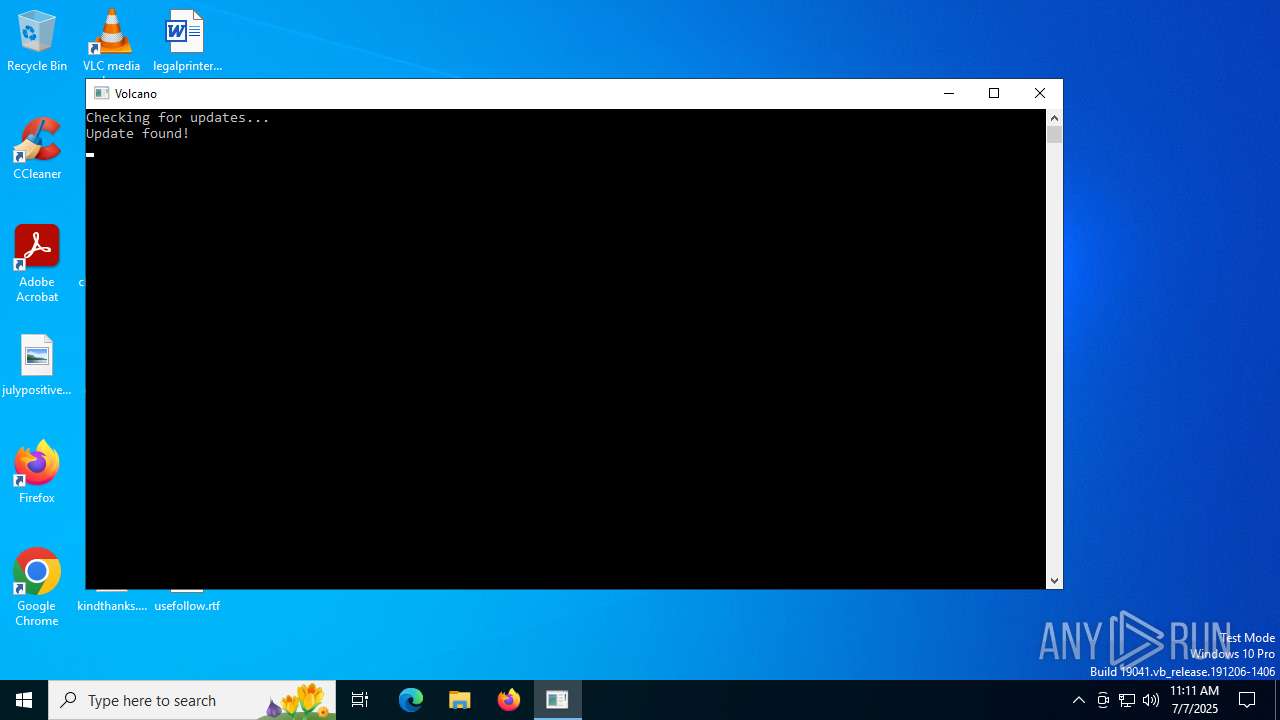
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6140 | "C:\Users\admin\AppData\Local\Temp\VolcanoUI.exe" | C:\Users\admin\AppData\Local\Temp\VolcanoUI.exe | VolcanoUpdater.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6524 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | VolcanoUpdater.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6724 | "C:\Users\admin\AppData\Local\Temp\VolcanoUpdater.exe" | C:\Users\admin\AppData\Local\Temp\VolcanoUpdater.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 309
Read events
1 309
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
16
Text files
74
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6724 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\version.txt | text | |
MD5:3823114D99249BC029749AEA158C1936 | SHA256:310F7F2C311B30A7E54C7FCEE7DD4E16A182729C4FBD94EE8187E5ED93CA9DEE | |||
| 6724 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\temp | compressed | |
MD5:6898A8C1F03981BE0FE2ACDDCBC9EEFC | SHA256:9E036CAC52B086B9840F6380456E24E8574C0FE7DA45867E373C091F06EB44CA | |||
| 6724 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\luau-lifter.exe | executable | |
MD5:F1246A49C8183FCFAC4D7669A6C50881 | SHA256:F5AD37B2293814CE33149CA8D8BF1D673AE0C8F3CB025D7B83954EB0E68E631D | |||
| 6724 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\abap-BrgZPUOV.js | text | |
MD5:5E0865606680E6D5AB5FAAE672097932 | SHA256:A3E2A241DA83C7AA80836ACE9FB3B2A242F458FF917DF9F19363F2E6430DD059 | |||
| 6724 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\cameligo-BFG1Mk7z.js | text | |
MD5:E9D40B956B6BEC8A5BFFD0D94552B2F8 | SHA256:CC50FE6B6738380FDC2D31D1A2FE210EA67CB19A5F6ABBF91E0AD3A08491A1E5 | |||
| 6724 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\dart-CFKIUWau.js | text | |
MD5:0E5BB107380566D808DCACF9F19E5E1B | SHA256:34F1EC79D69827427121963C5C96CD7F9CC97B7042C812367343E9AD60B546B4 | |||
| 6724 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\csharp-dUCx_-0o.js | text | |
MD5:5616EF1623A707EDDFB5641341DB735E | SHA256:DE87D1D2BDCEC69C9A9AB2CE355B9BC638BAC7E4078D303DF89DADCB85F58846 | |||
| 6724 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\csp-5Rap-vPy.js | text | |
MD5:8CB672DB7B68FE7F3F7DFCB05AE388A5 | SHA256:C413FA2B83B1A0B1AF76E822721C4A429163B7BCD477B4DEEBD41F7C4E4C8A20 | |||
| 6724 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\codicon-DCmgc-ay.ttf | ttf | |
MD5:CB7F0A51C106A33FB4ABAB8C454373D8 | SHA256:0F1D5219934E96E83B8DB162D60B4D8C09B5DE1E7D38031CBAFE4A3C0F2889C9 | |||
| 6724 | VolcanoUpdater.exe | C:\Users\admin\AppData\Local\Temp\bin\page\assets\css-D3h14YRZ.js | text | |
MD5:387BF345843B2BE9BA90A6FBA1DE584E | SHA256:55CD0C924635240191C8189F4A500720E61EEE267EB2093474BF686AE5820EA6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
16
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
764 | lsass.exe | GET | 200 | 142.250.185.195:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 142.250.185.195:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2612 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4860 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6724 | VolcanoUpdater.exe | 104.21.48.1:443 | file.volcano.best | CLOUDFLARENET | — | malicious |
764 | lsass.exe | 142.250.185.195:80 | c.pki.goog | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6140 | VolcanoUI.exe | 104.21.48.1:443 | file.volcano.best | CLOUDFLARENET | — | malicious |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
file.volcano.best |
| malicious |
c.pki.goog |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
Process | Message |
|---|---|
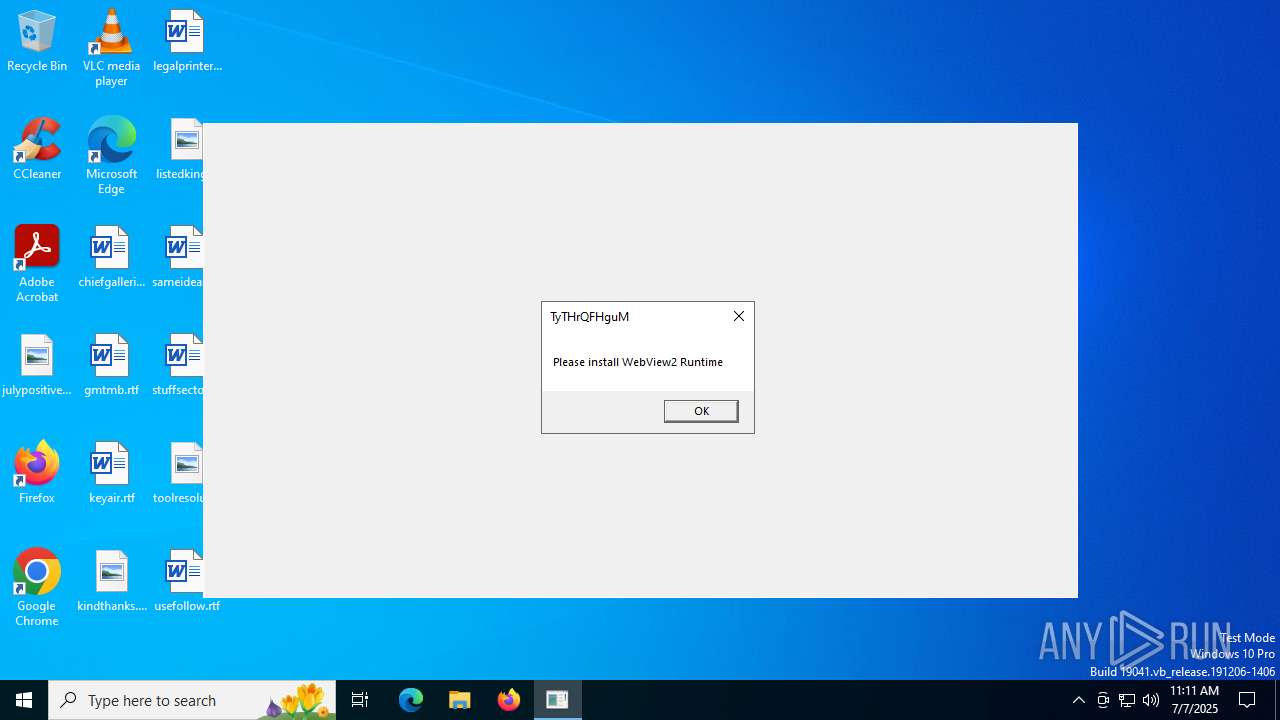
VolcanoUI.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
VolcanoUI.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|