| File name: | WBS LearnSpace 3D.exe.zs |
| Full analysis: | https://app.any.run/tasks/fcb033f2-280a-4bec-86e1-a9cfbb2a9898 |
| Verdict: | Malicious activity |
| Analysis date: | March 26, 2020, 11:41:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9707D75A2CA1B67A416A85E702209C2B |
| SHA1: | A7892BDBDA8426EAD027409CAB20B97AF08A88B6 |
| SHA256: | F2C748E927F193B978199505853816C35DDBE840F4C556ADC6598FD391B807D4 |
| SSDEEP: | 98304:p8zKeIxq7HrFHI7kphejaAV+YL4XlNRjZBOQFuUBvAwkx6:TubpoReAVJkVOophW6 |
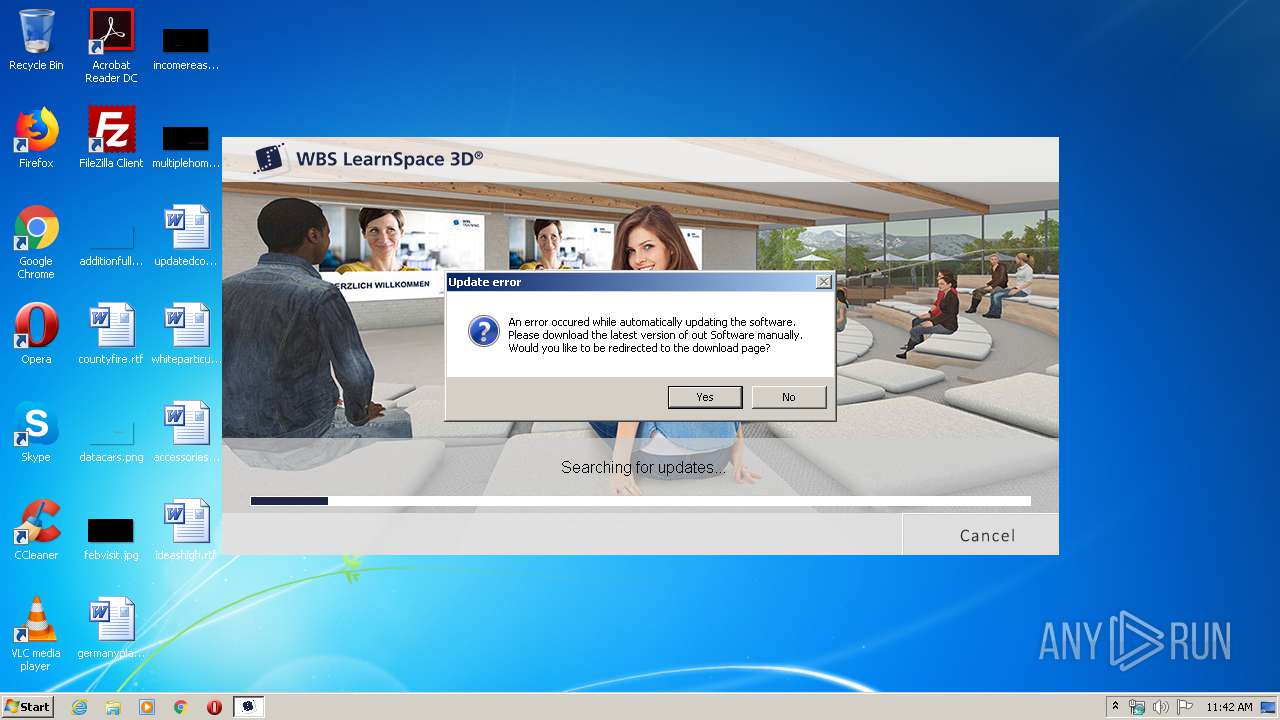
MALICIOUS
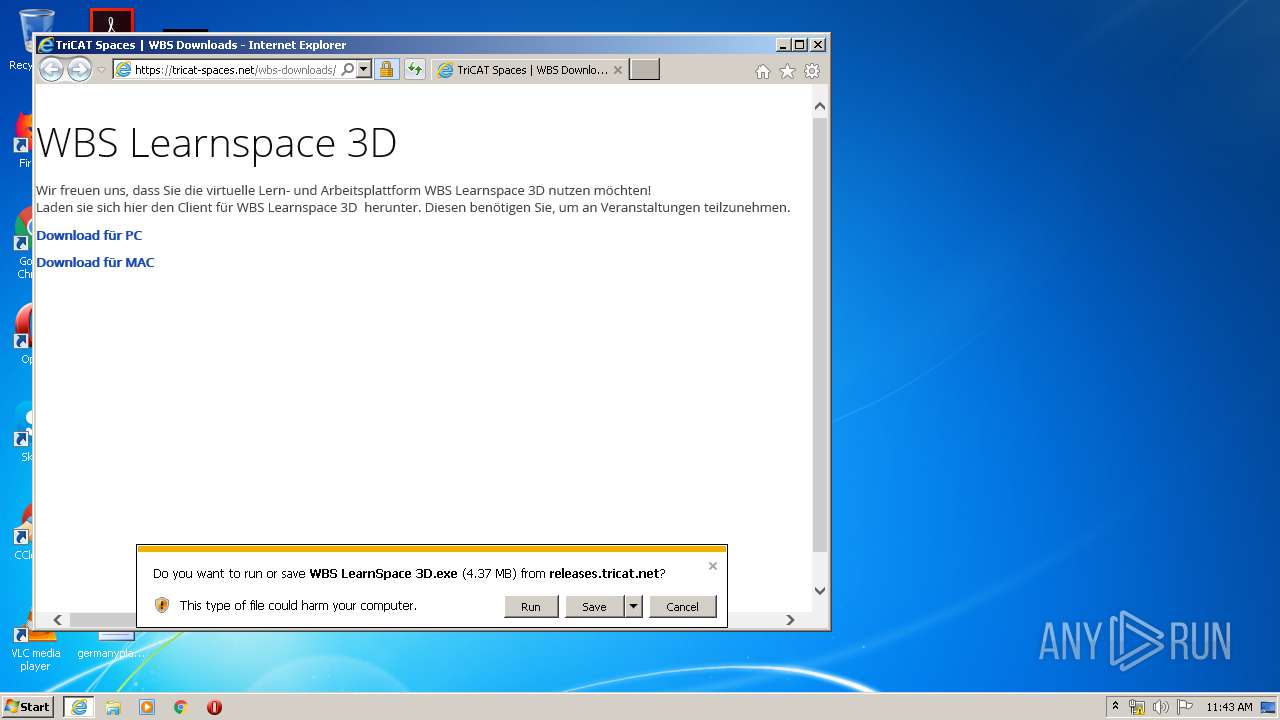
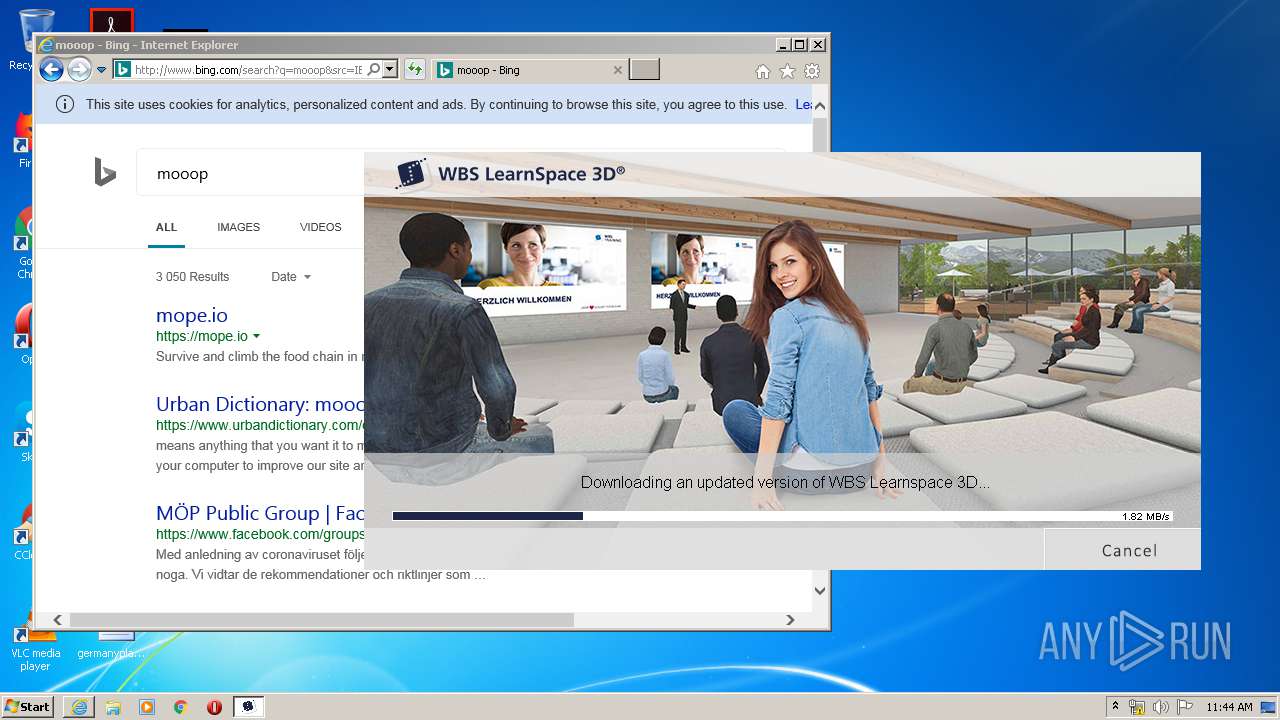
Application was dropped or rewritten from another process
- WBS LearnSpace 3D.exe (PID: 3824)
SUSPICIOUS
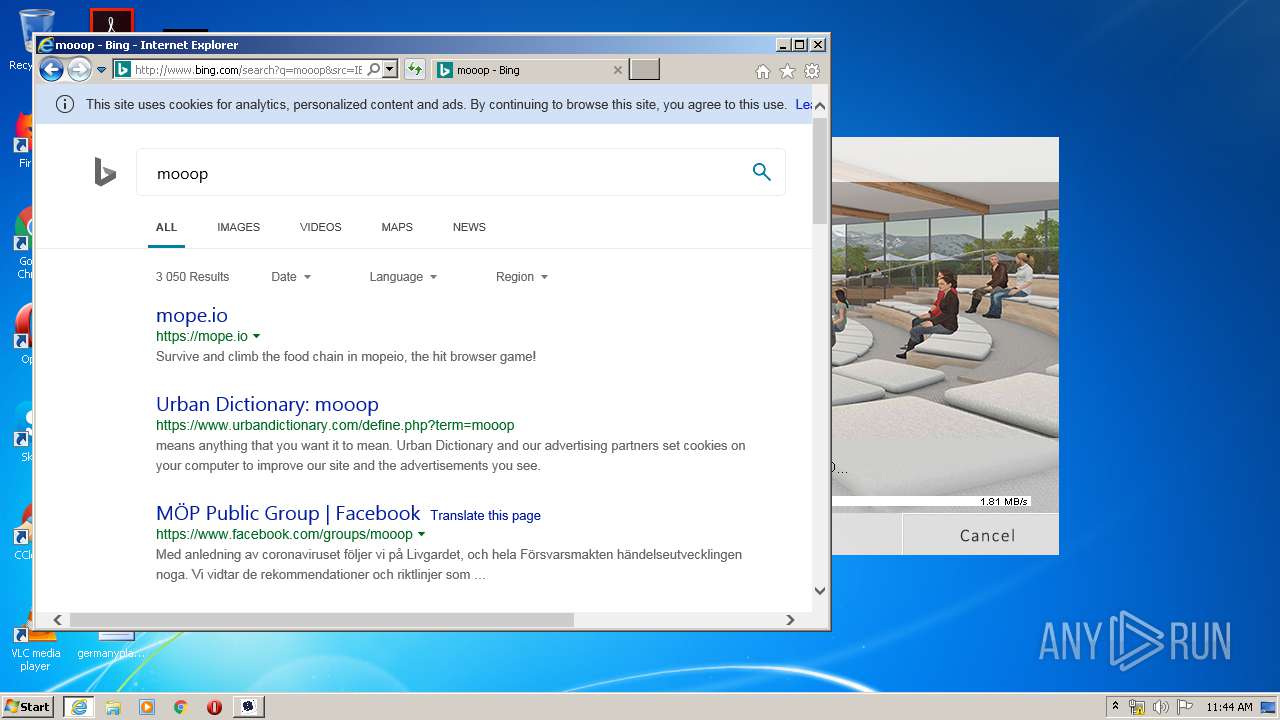
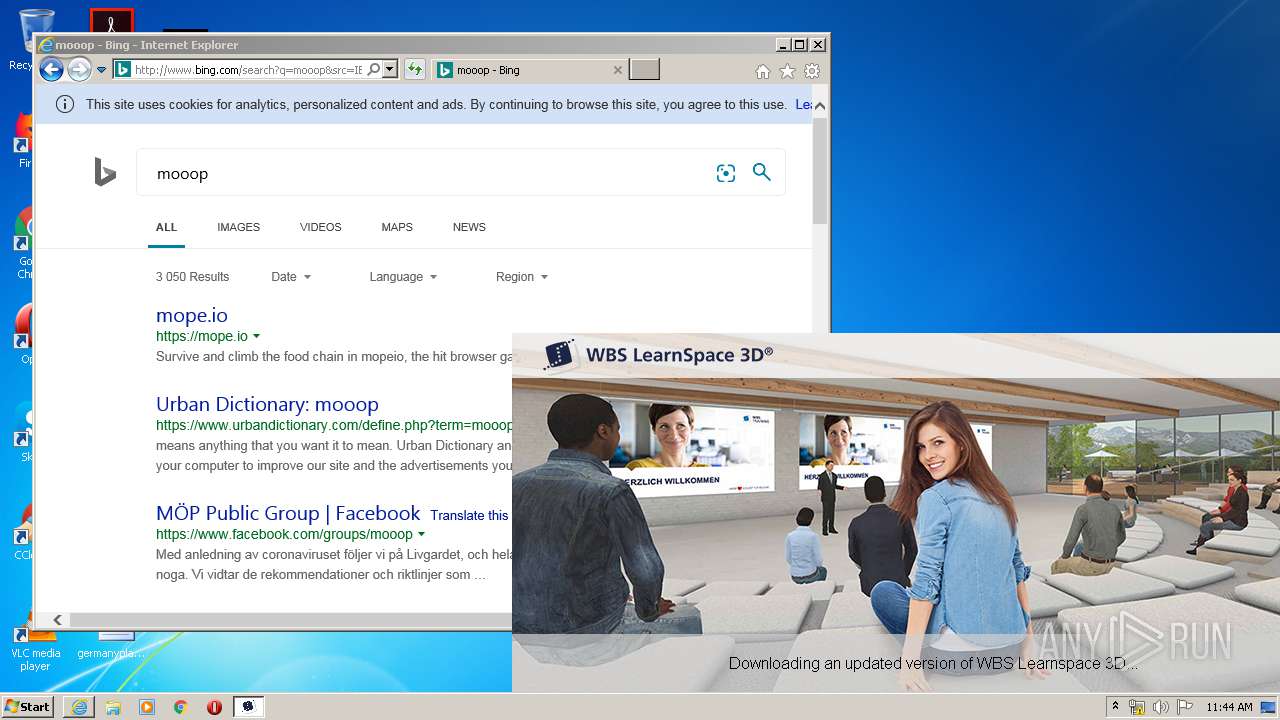
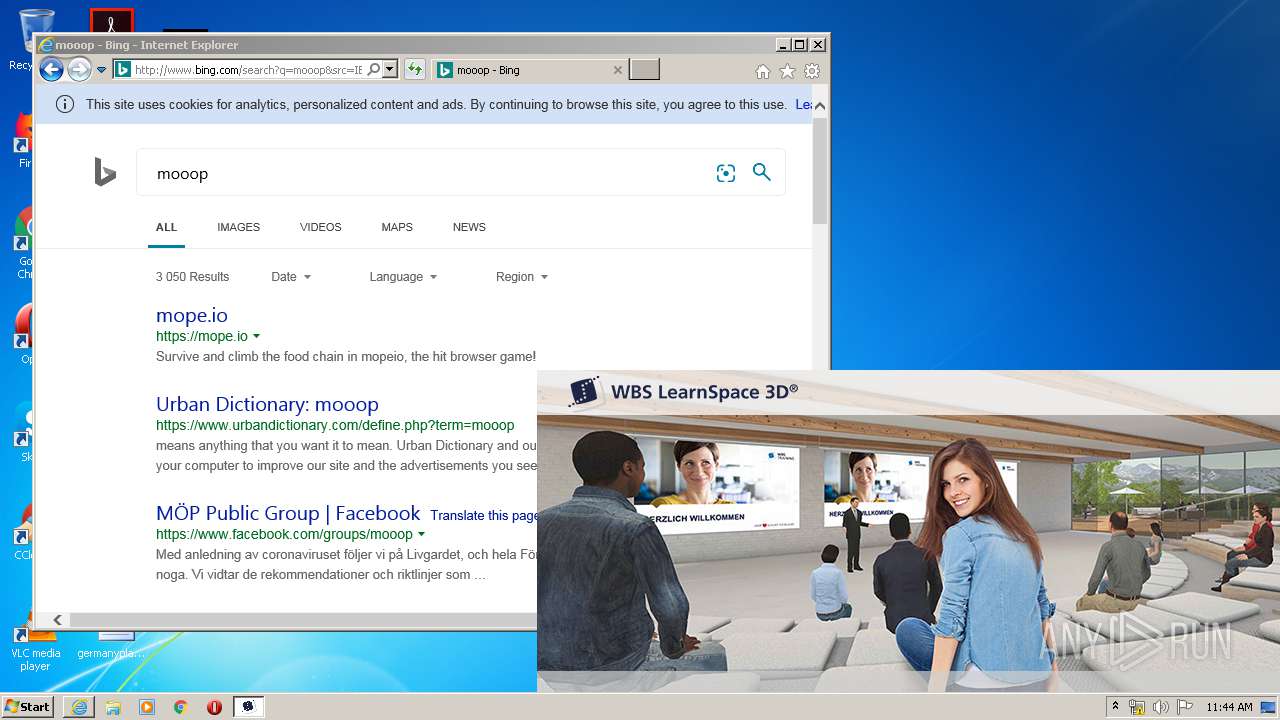
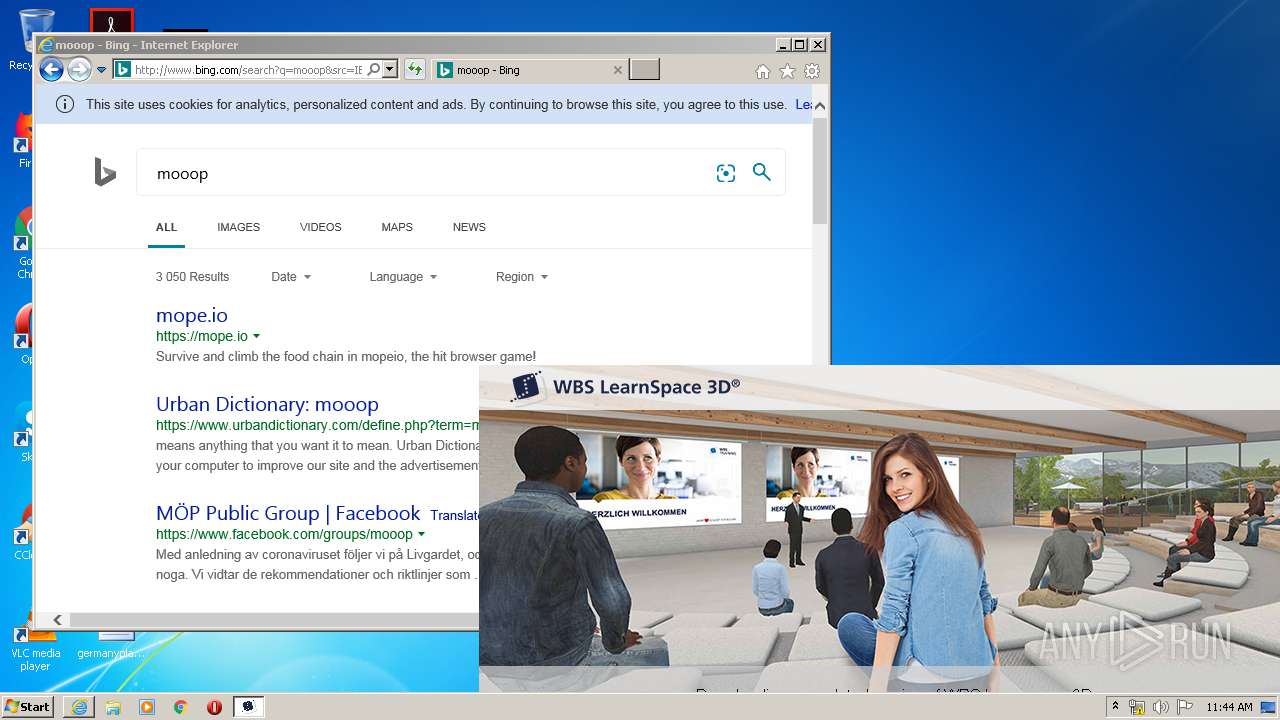
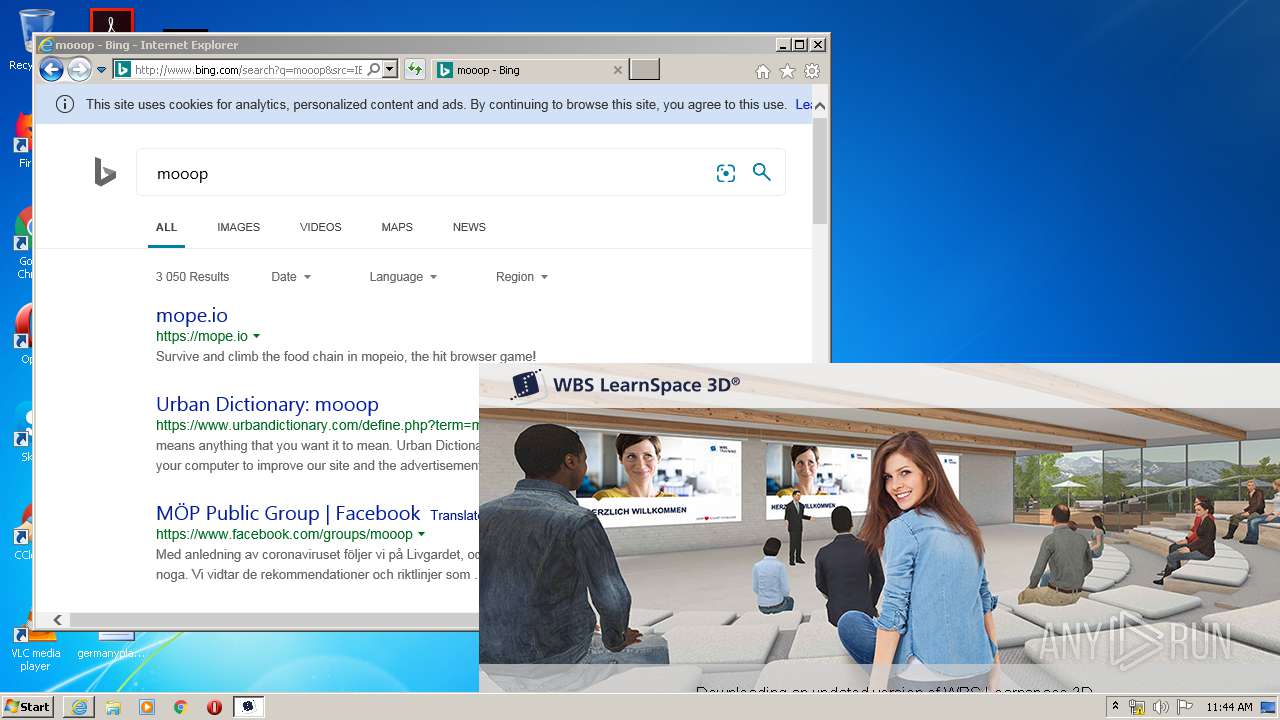
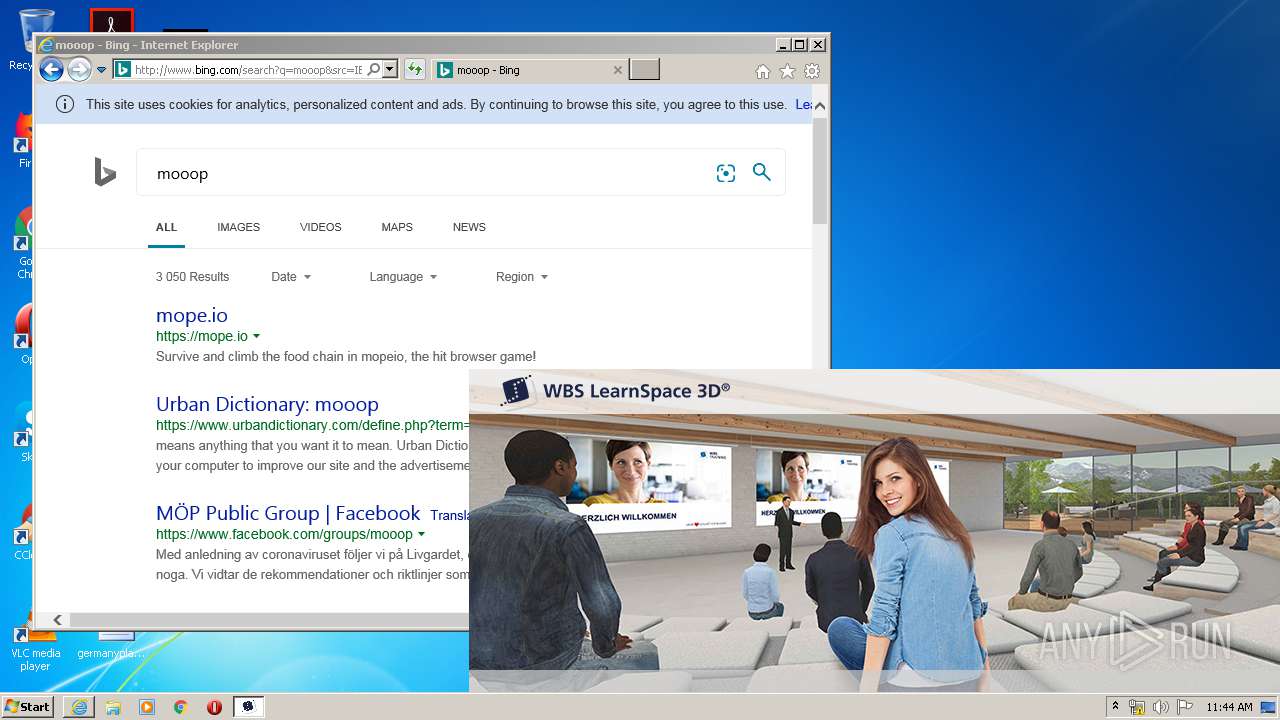
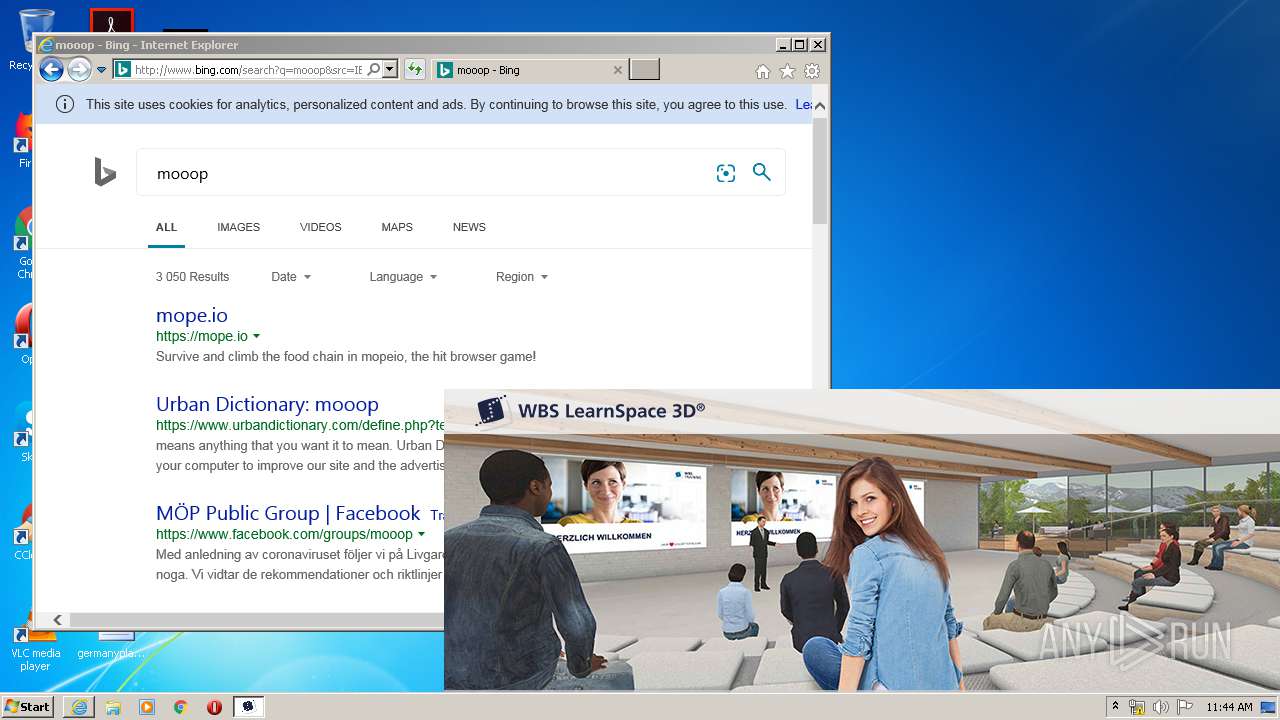
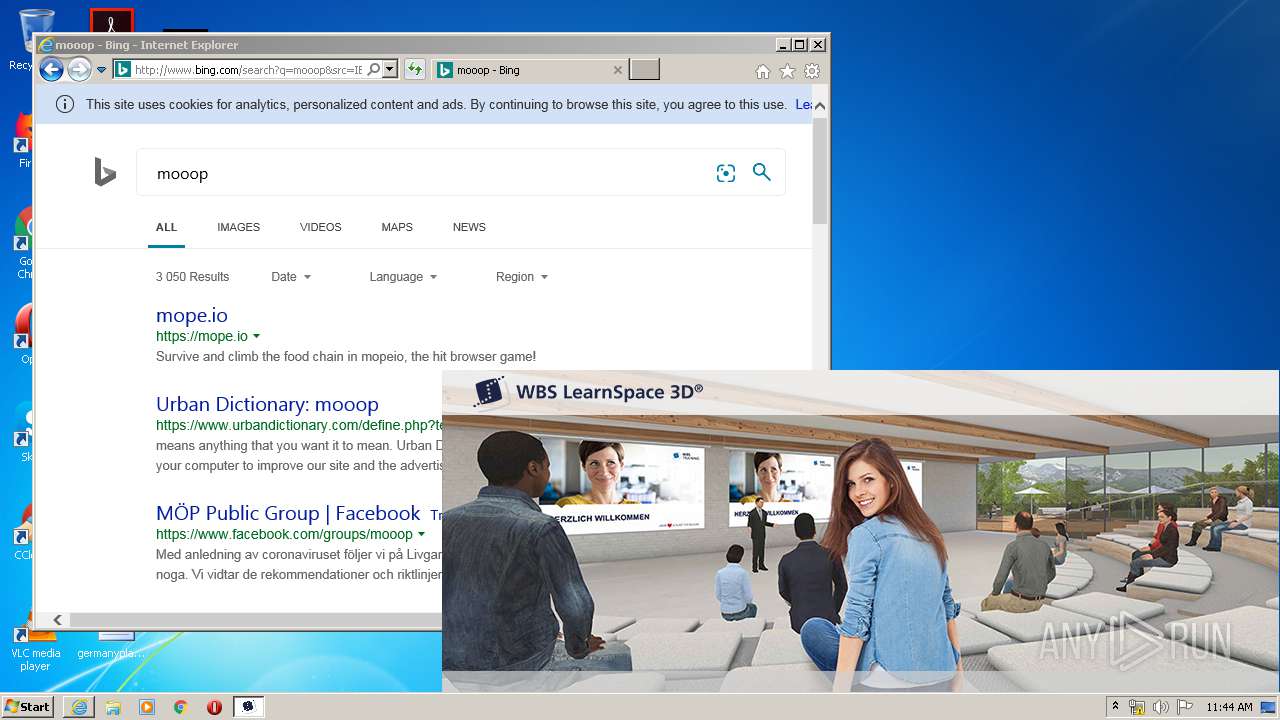
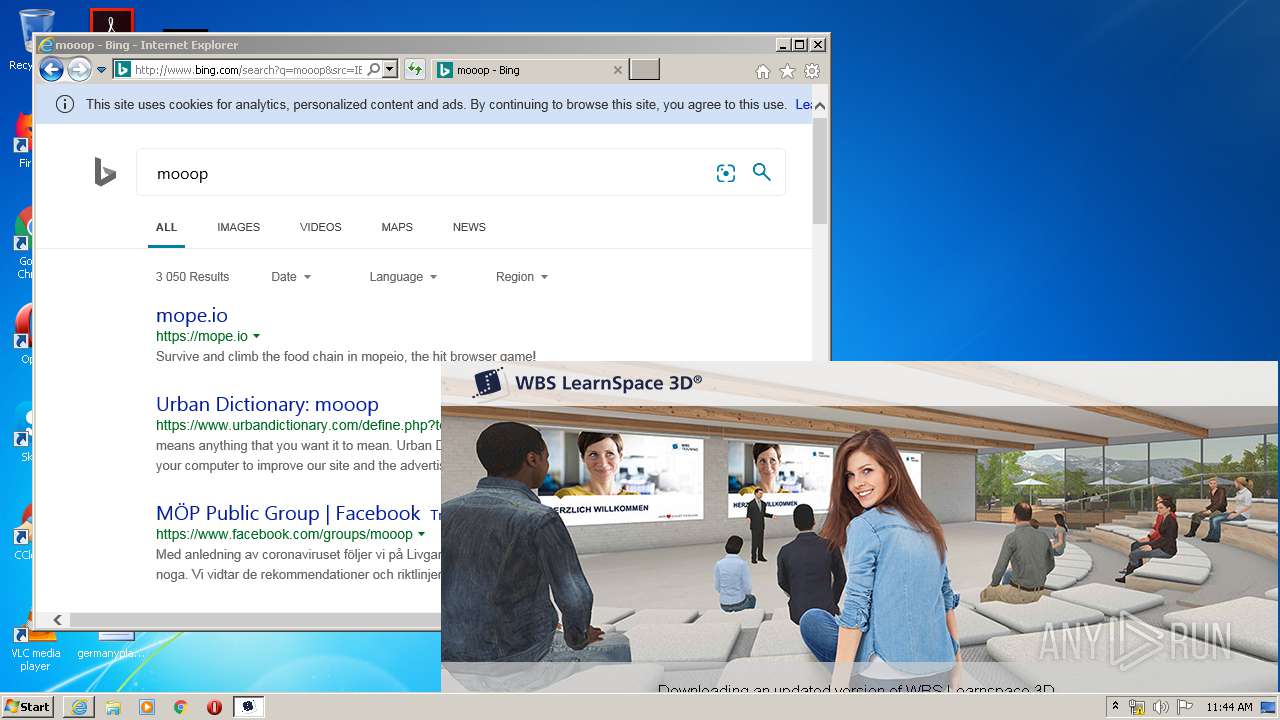
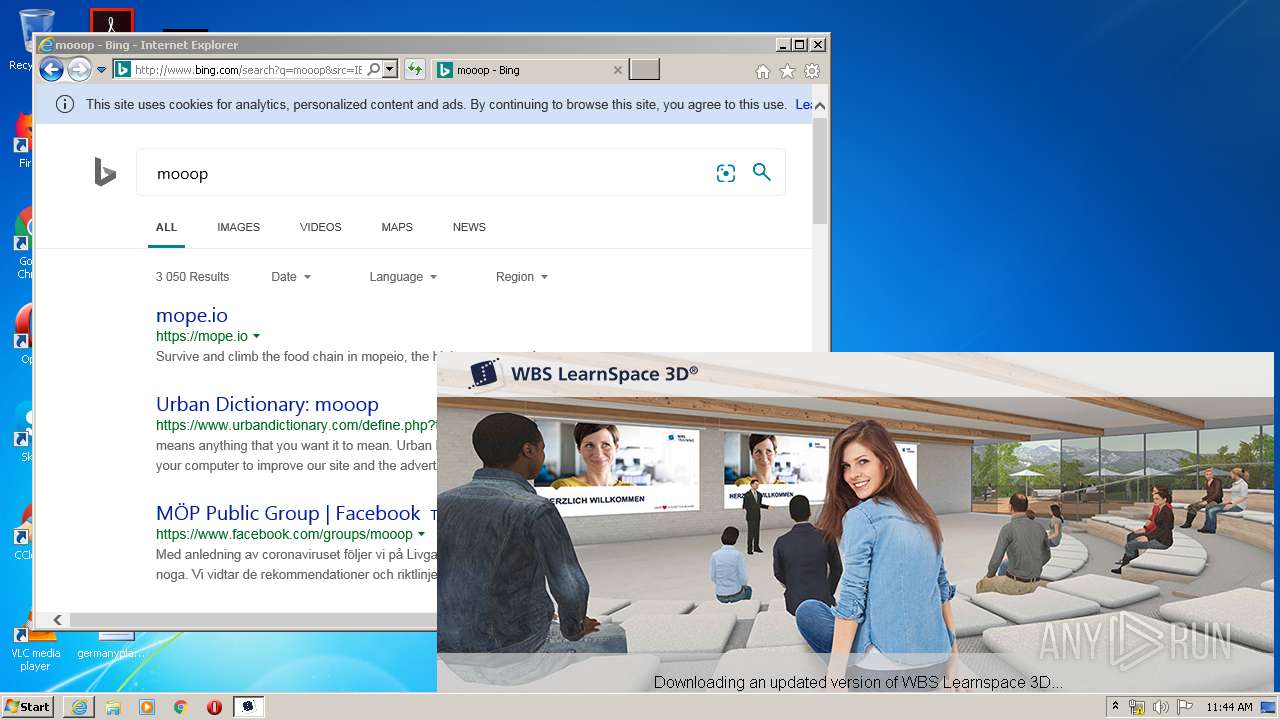
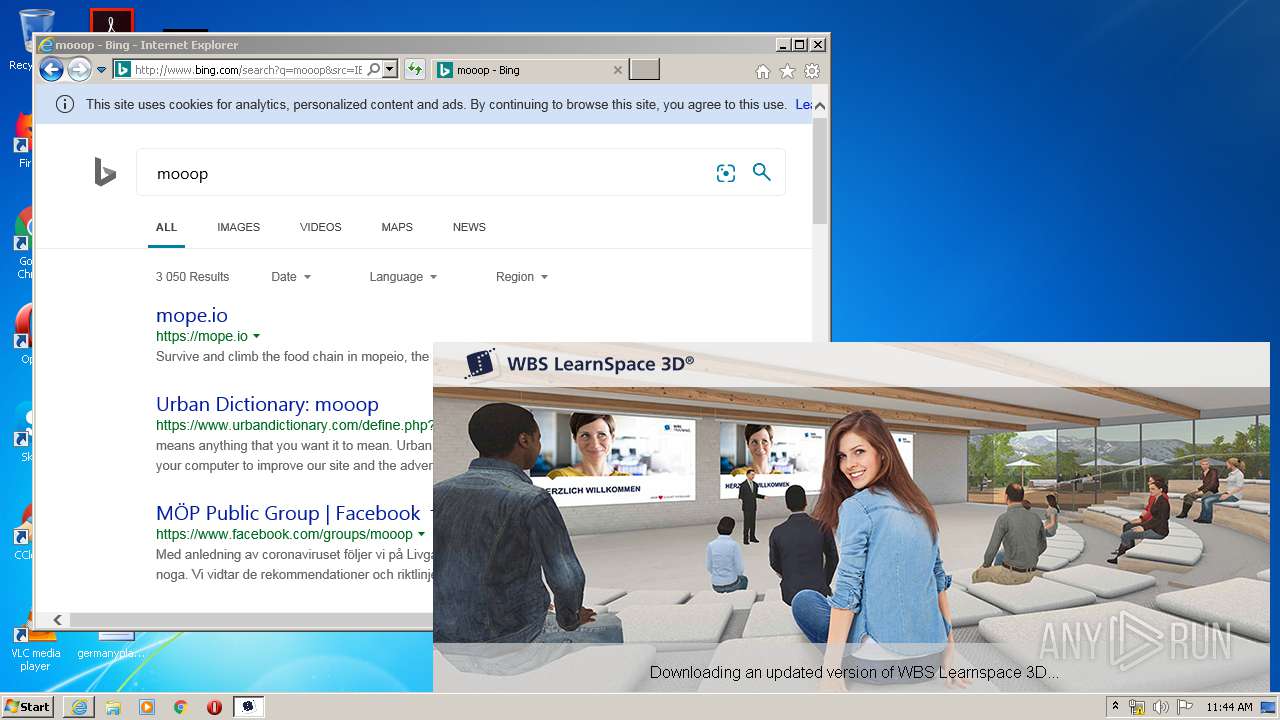
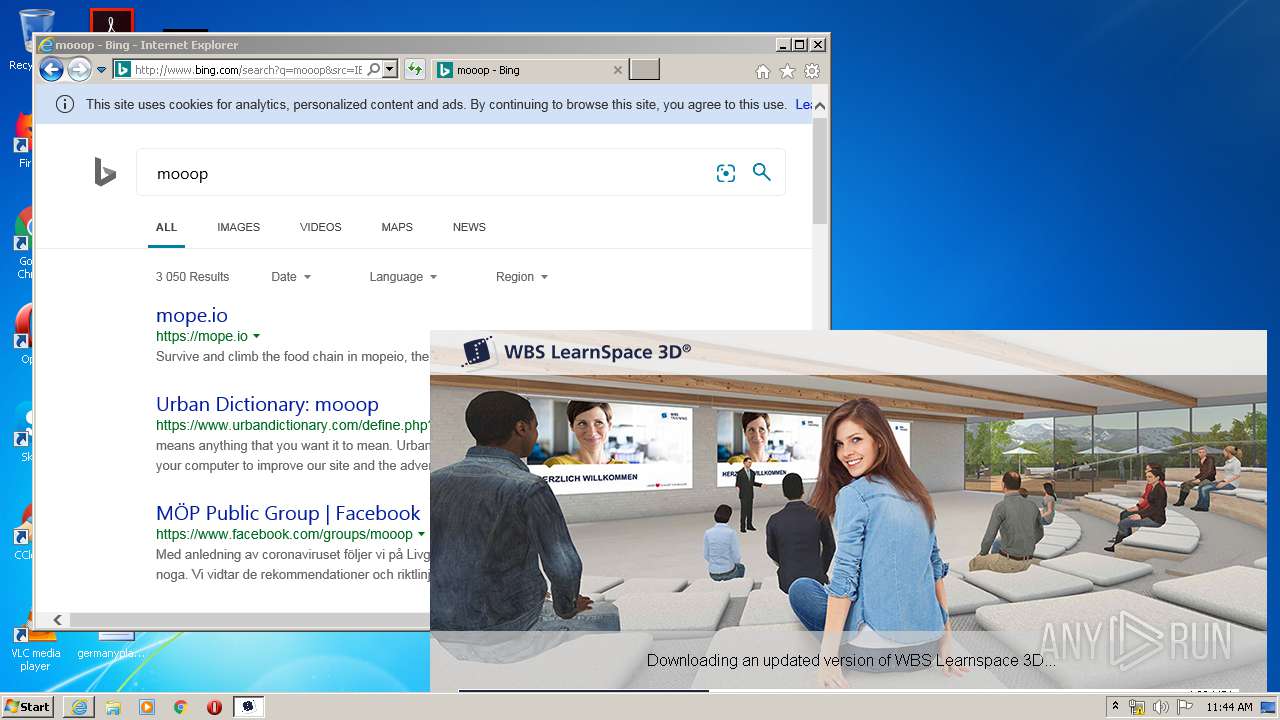
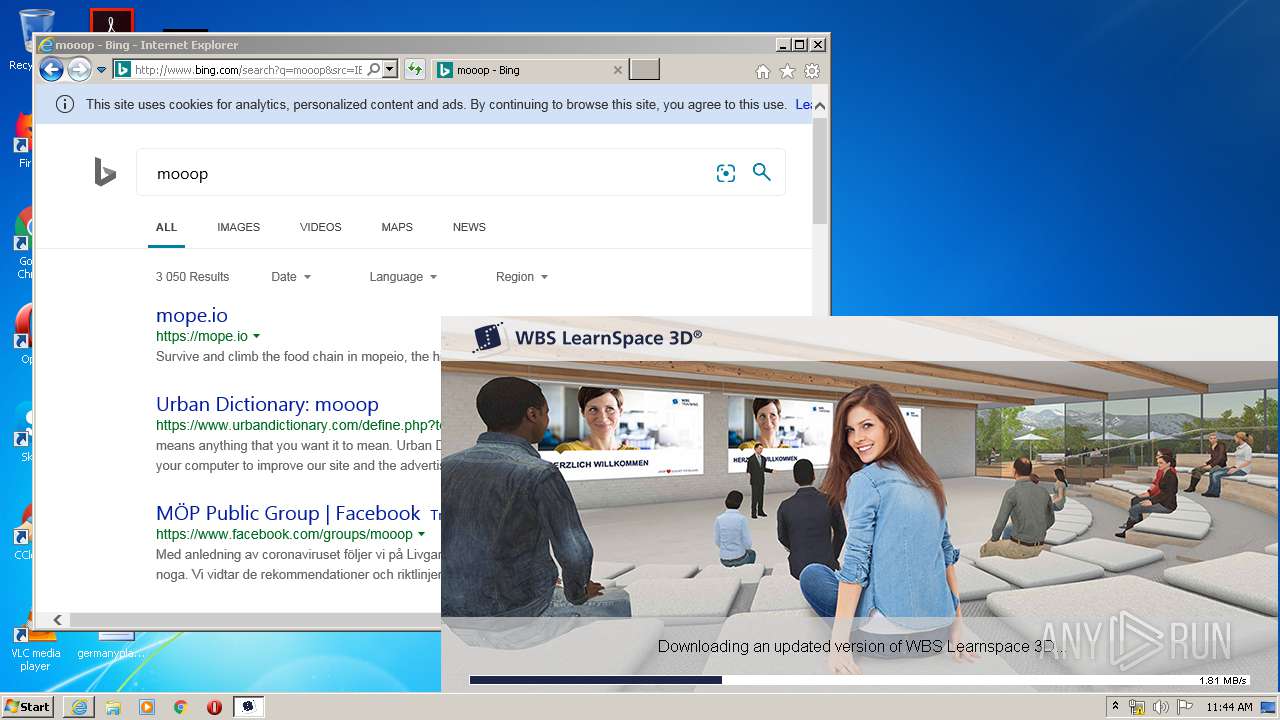
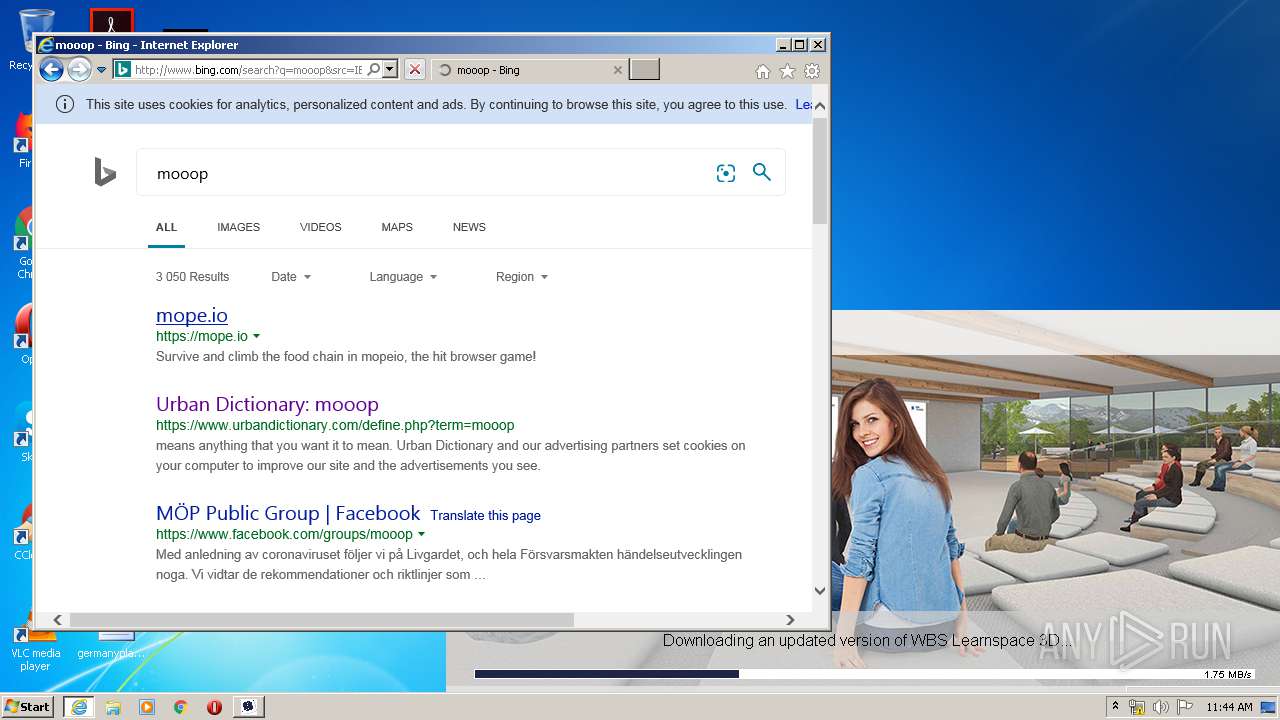
Starts Internet Explorer
- WBS LearnSpace 3D.exe.zs.exe (PID: 3484)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3316)
- iexplore.exe (PID: 3320)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3316)
Reads Internet Cache Settings
- iexplore.exe (PID: 3316)
- iexplore.exe (PID: 3320)
Application launched itself
- iexplore.exe (PID: 3316)
Reads internet explorer settings
- iexplore.exe (PID: 3320)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3316)
Creates files in the user directory
- iexplore.exe (PID: 3316)
- iexplore.exe (PID: 3320)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3320)
Reads settings of System Certificates
- iexplore.exe (PID: 3316)
- iexplore.exe (PID: 3320)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3316)
Changes settings of System certificates
- iexplore.exe (PID: 3316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:10:15 16:18:48+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.14 |
| CodeSize: | 2745856 |
| InitializedDataSize: | 1934336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x242144 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2018.10.15.9282 |
| ProductVersionNumber: | 1.0.0.9282 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | German |
| CharacterSet: | Unicode |
| CompanyName: | TriCAT GmbH |
| FileDescription: | Learnspace 3D |
| FileVersion: | 2018.10.15.9282 |
| InternalName: | TriCAT Launcher |
| LegalCopyright: | Copyright TriCAT GmbH, 2017. All rights reserved. |
| OriginalFileName: | VirtuelleFirma.exe |
| ProductName: | Learnspace 3D |
| ProductVersion: | 1.0.0.9282 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Oct-2018 14:18:48 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | TriCAT GmbH |
| FileDescription: | Learnspace 3D |
| FileVersion: | 2018.10.15.9282 |
| InternalName: | TriCAT Launcher |
| LegalCopyright: | Copyright TriCAT GmbH, 2017. All rights reserved. |
| OriginalFilename: | VirtuelleFirma.exe |
| ProductName: | Learnspace 3D |
| ProductVersion: | 1.0.0.9282 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000148 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Oct-2018 14:18:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0029E4B2 | 0x0029E600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64191 |
.rdata | 0x002A0000 | 0x000B3A64 | 0x000B3C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.52331 |
.data | 0x00354000 | 0x0001AADC | 0x0000FC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.38169 |
.rsrc | 0x0036F000 | 0x000D79A0 | 0x000D7A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.06112 |
.reloc | 0x00447000 | 0x000320B4 | 0x00032200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.60053 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11563 | 794 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.02695 | 308 | UNKNOWN | German - Germany | RT_CURSOR |
3 | 2.74274 | 180 | UNKNOWN | German - Germany | RT_CURSOR |
4 | 2.34038 | 308 | UNKNOWN | German - Germany | RT_CURSOR |
5 | 2.34004 | 308 | UNKNOWN | German - Germany | RT_CURSOR |
6 | 2.51649 | 308 | UNKNOWN | German - Germany | RT_CURSOR |
7 | 2.45401 | 308 | UNKNOWN | German - Germany | RT_CURSOR |
8 | 2.34864 | 308 | UNKNOWN | German - Germany | RT_CURSOR |
9 | 2.34505 | 308 | UNKNOWN | German - Germany | RT_CURSOR |
10 | 2.34864 | 308 | UNKNOWN | German - Germany | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
PSAPI.DLL |
Total processes
42
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
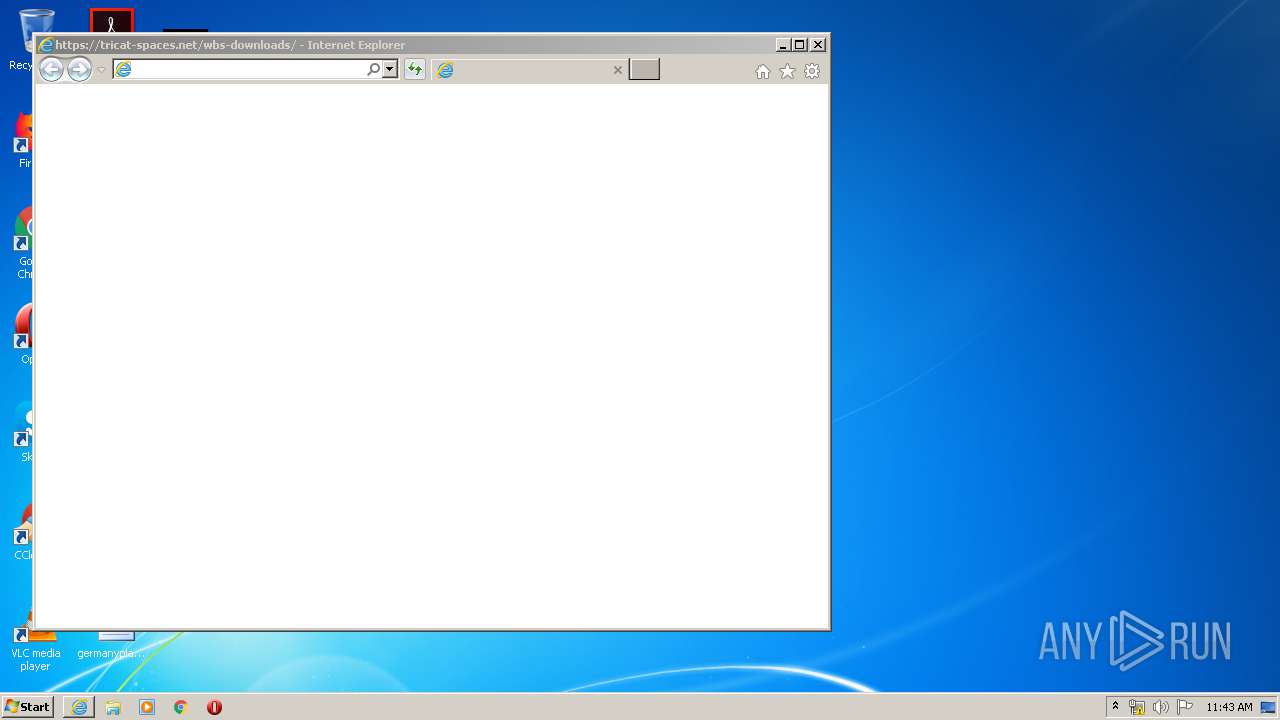
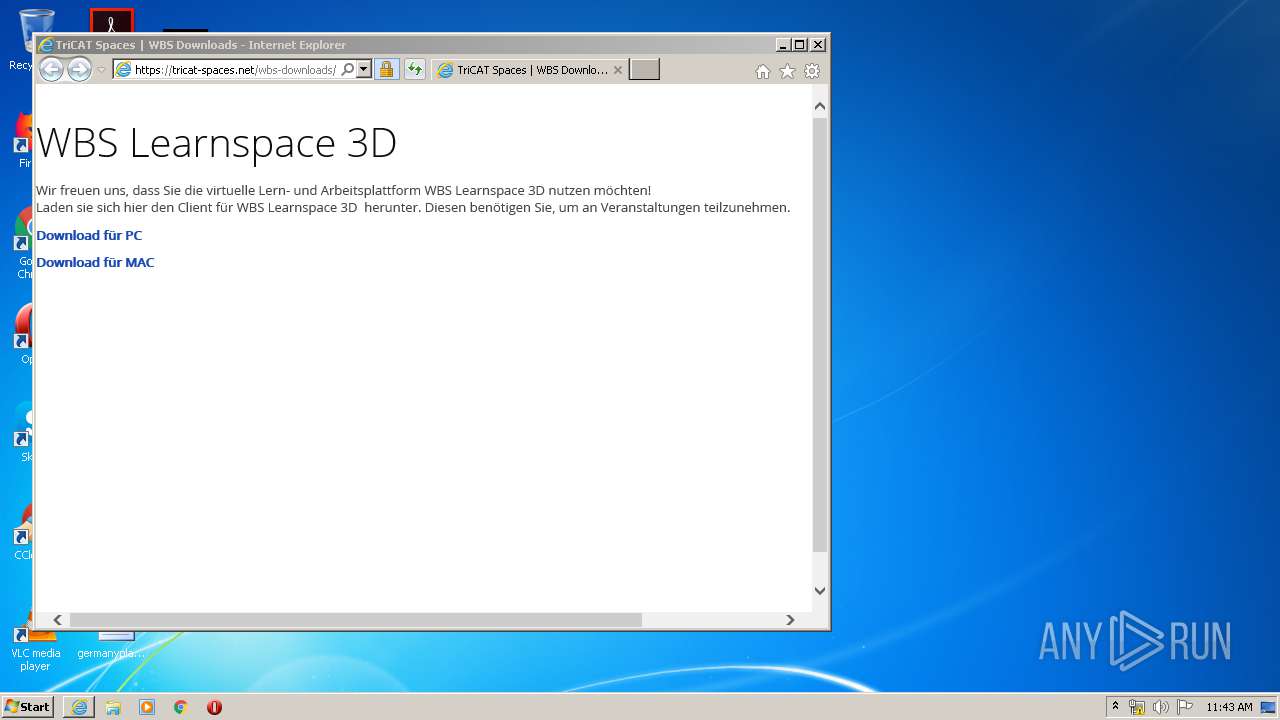
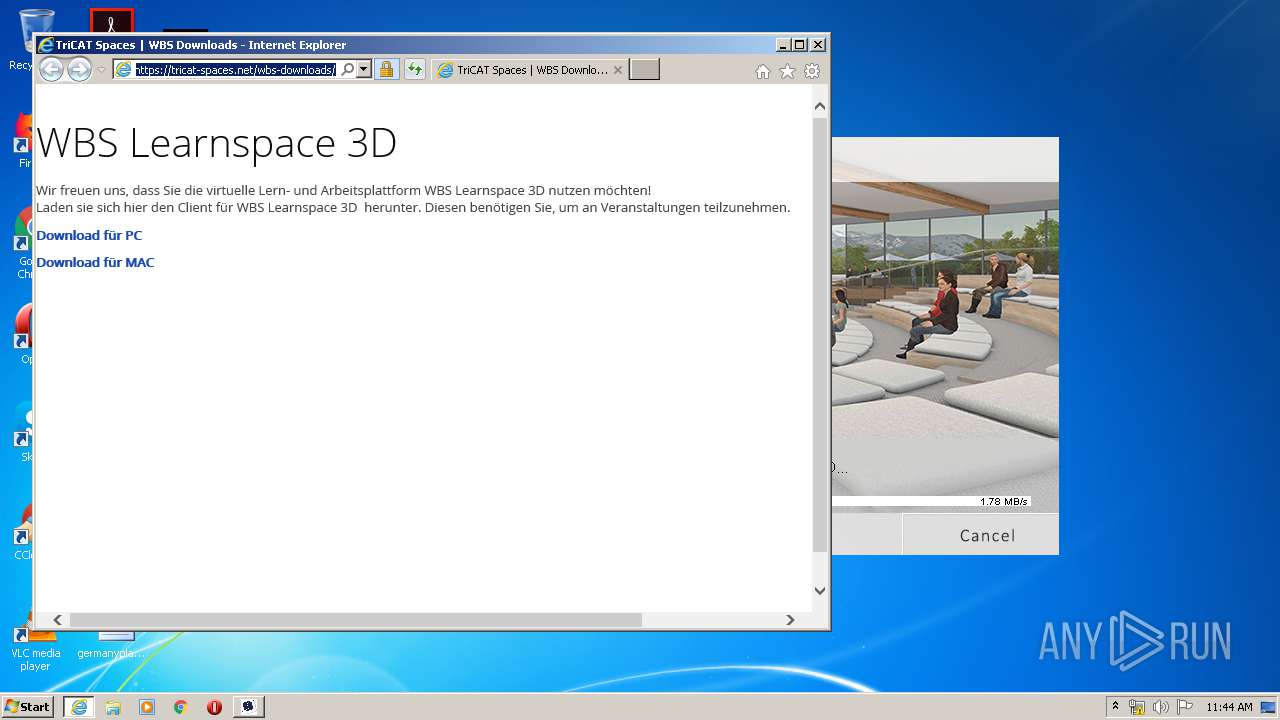
| 3316 | "C:\Program Files\Internet Explorer\iexplore.exe" https://tricat-spaces.net/wbs-downloads/ | C:\Program Files\Internet Explorer\iexplore.exe | WBS LearnSpace 3D.exe.zs.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3320 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3316 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3484 | "C:\Users\admin\AppData\Local\Temp\WBS LearnSpace 3D.exe.zs.exe" | C:\Users\admin\AppData\Local\Temp\WBS LearnSpace 3D.exe.zs.exe | explorer.exe | ||||||||||||
User: admin Company: TriCAT GmbH Integrity Level: MEDIUM Description: Learnspace 3D Exit code: 0 Version: 2018.10.15.9282 Modules
| |||||||||||||||
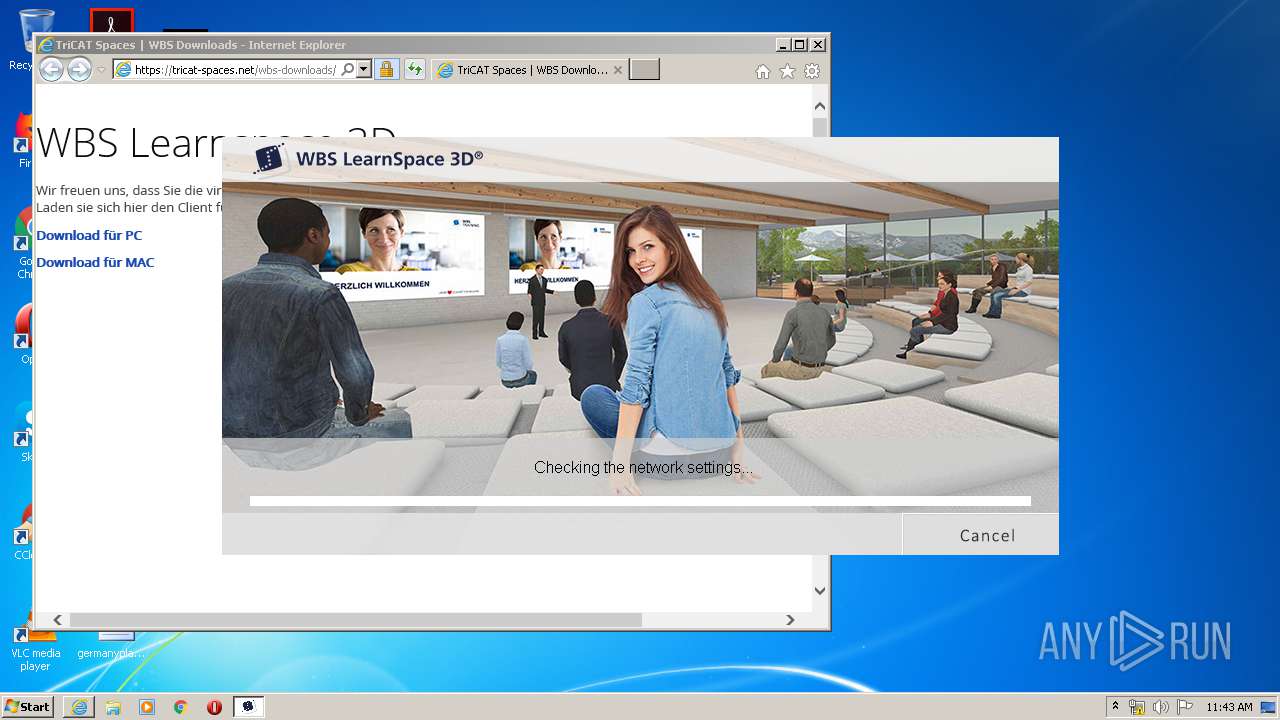
| 3824 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\WBS LearnSpace 3D.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\WBS LearnSpace 3D.exe | iexplore.exe | ||||||||||||
User: admin Company: TriCAT GmbH Integrity Level: MEDIUM Description: WBS Learnspace 3D Exit code: 0 Version: 2019.10.29.13901 Modules
| |||||||||||||||
Total events
7 837
Read events
1 702
Write events
4 125
Delete events
2 010
Modification events
| (PID) Process: | (3484) WBS LearnSpace 3D.exe.zs.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3484) WBS LearnSpace 3D.exe.zs.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: WBS LearnSpace 3D.exe.zs.exe | |||
| (PID) Process: | (3484) WBS LearnSpace 3D.exe.zs.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 010000000000000088FAD5B86303D601 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3403218548 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30802787 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3316) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
3
Suspicious files
304
Text files
222
Unknown types
149
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3320 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab473E.tmp | — | |
MD5:— | SHA256:— | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar473F.tmp | — | |
MD5:— | SHA256:— | |||
| 3316 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3316 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\WBS LearnSpace 3D.exe.hl9lzik.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 3316 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabE1A9.tmp | — | |
MD5:— | SHA256:— | |||
| 3316 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarE1AA.tmp | — | |
MD5:— | SHA256:— | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_427CDB1C9AAC2BAE6B426DB11F126FA2 | der | |
MD5:— | SHA256:— | |||
| 3316 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verE303.tmp | — | |
MD5:— | SHA256:— | |||
| 3320 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3484 | WBS LearnSpace 3D.exe.zs.exe | C:\Users\admin\AppData\Local\Temp\TriCAT\WBS\live\spaces.cfg | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
235
TCP/UDP connections
353
DNS requests
159
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
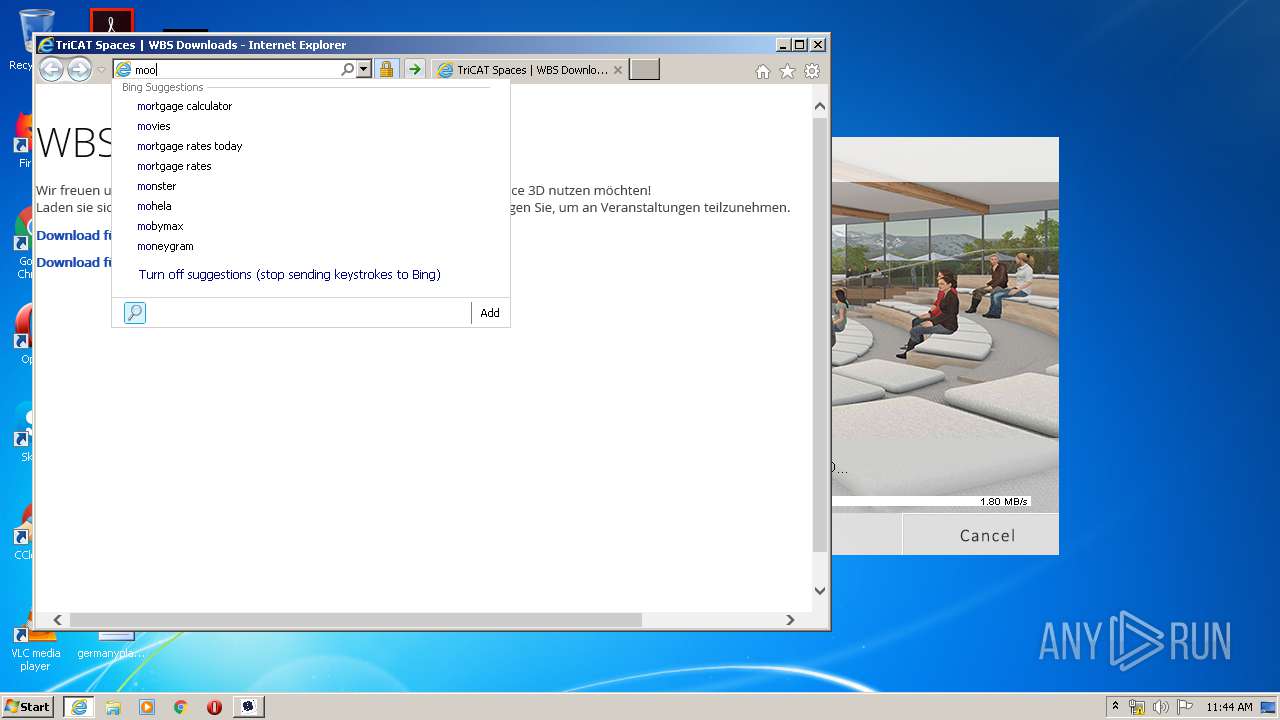
3320 | iexplore.exe | GET | — | 13.107.47.80:80 | http://api.bing.com/qsml.aspx?query=m&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
3320 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAkO6MXeW%2Fpi0q4v9wl8SFc%3D | US | der | 471 b | whitelisted |
3316 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3316 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3316 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
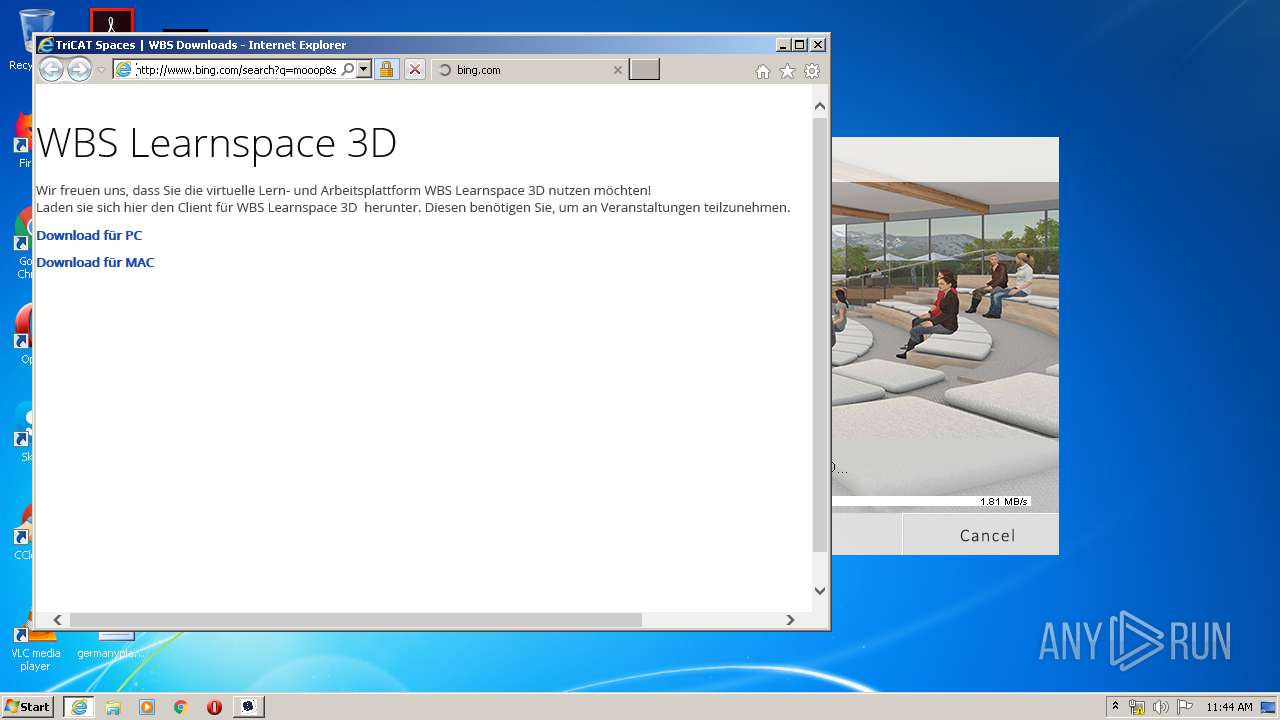
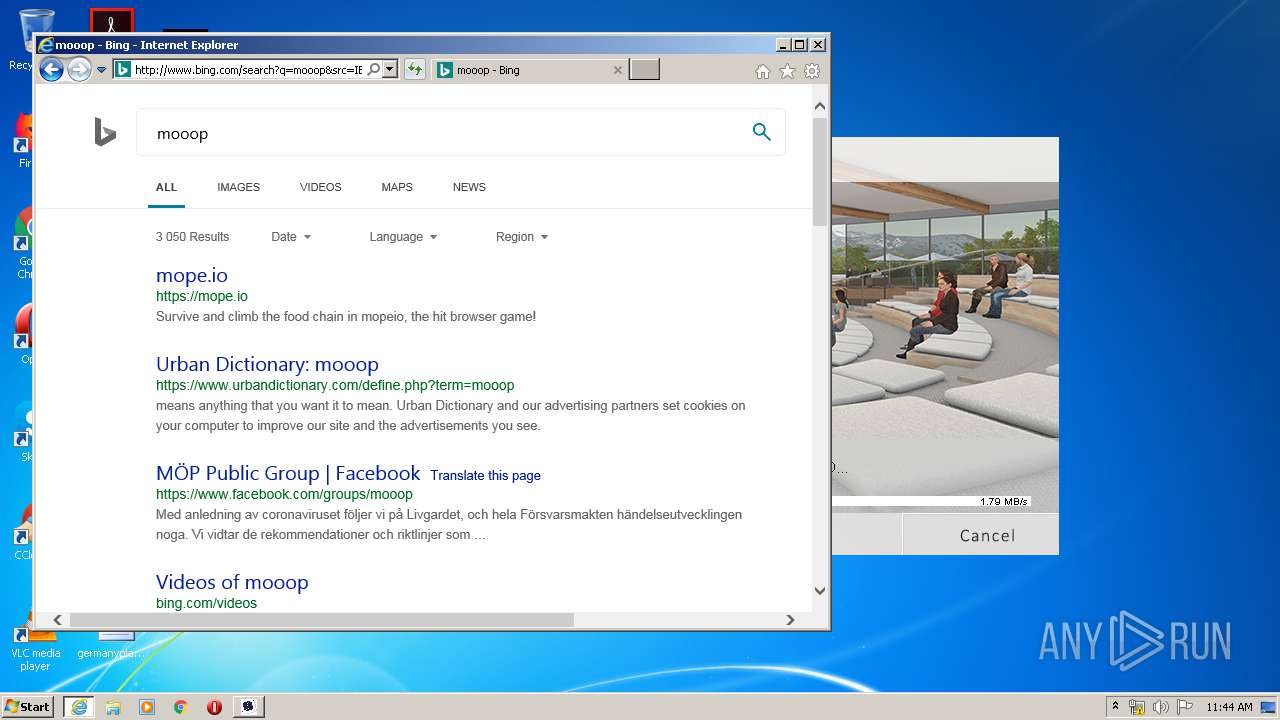
3320 | iexplore.exe | GET | 200 | 13.107.47.80:80 | http://api.bing.com/qsml.aspx?query=mooo&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 217 b | whitelisted |
3320 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAkO6MXeW%2Fpi0q4v9wl8SFc%3D | US | der | 471 b | whitelisted |
3320 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/5g/cj,nj/e9a4690d/d42920eb.js?bu=EochpSHNINEgqQXgIOIgtSHkIPAg9CCjIaEhliH0H4wfkR-GIA | US | text | 5.38 Kb | whitelisted |
3320 | iexplore.exe | GET | 200 | 13.107.47.80:80 | http://api.bing.com/qsml.aspx?query=mo&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 233 b | whitelisted |
3320 | iexplore.exe | GET | 200 | 13.107.47.80:80 | http://api.bing.com/qsml.aspx?query=moo&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 210 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3484 | WBS LearnSpace 3D.exe.zs.exe | 88.198.176.205:443 | tricat.net | Hetzner Online GmbH | DE | suspicious |
3320 | iexplore.exe | 88.198.176.205:443 | tricat.net | Hetzner Online GmbH | DE | suspicious |
3320 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3316 | iexplore.exe | 88.198.176.205:443 | tricat.net | Hetzner Online GmbH | DE | suspicious |
3316 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3316 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3316 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3824 | WBS LearnSpace 3D.exe | 88.198.176.205:443 | tricat.net | Hetzner Online GmbH | DE | suspicious |
3824 | WBS LearnSpace 3D.exe | 176.9.109.240:443 | 3dwelt.wbsag.de | Hetzner Online GmbH | DE | unknown |
3824 | WBS LearnSpace 3D.exe | 78.47.101.207:443 | updatemirror1.learnspace3d.de | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tricat.net |
| suspicious |
stats.tricat-spaces.net |
| suspicious |
releases.tricat.net |
| suspicious |
dns.msftncsi.com |
| shared |
tricat-spaces.net |
| suspicious |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
WBS LearnSpace 3D.exe.zs.exe | 11:42:23 - Filename: WBS LearnSpace 3D.exe.zs.exe
|
WBS LearnSpace 3D.exe.zs.exe | 11:42:23 - Commandline: "C:\Users\admin\AppData\Local\Temp\WBS LearnSpace 3D.exe.zs.exe"
|
WBS LearnSpace 3D.exe.zs.exe | 11:42:23 - Old process ID: 0
|
WBS LearnSpace 3D.exe.zs.exe | |
WBS LearnSpace 3D.exe.zs.exe | 11:42:23 - Init english
|
WBS LearnSpace 3D.exe.zs.exe | 11:42:23 - Filename: WBS LearnSpace 3D.exe.zs.exe
|
WBS LearnSpace 3D.exe.zs.exe | 11:42:23 - ######### NEW LOG #########
|
WBS LearnSpace 3D.exe.zs.exe | 11:42:23 - Updated proxy list, found the following entries:
|
WBS LearnSpace 3D.exe.zs.exe | 11:42:23 - Start checking Proxies
|
WBS LearnSpace 3D.exe.zs.exe | 11:42:23 - No working HTTPS Proxy found, checking direct connection
|