| File name: | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.7z |
| Full analysis: | https://app.any.run/tasks/150132dd-b1e5-4f81-9534-b4c1fd090f6c |
| Verdict: | Malicious activity |
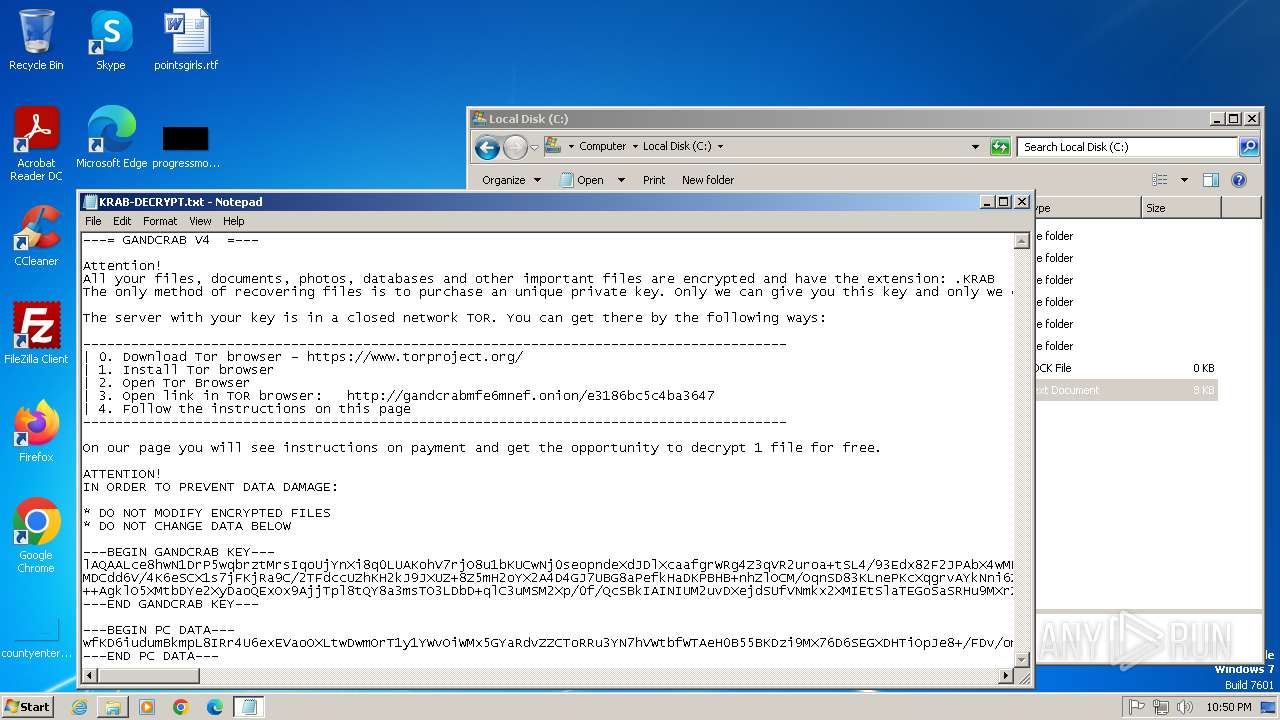
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | April 29, 2025, 21:49:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
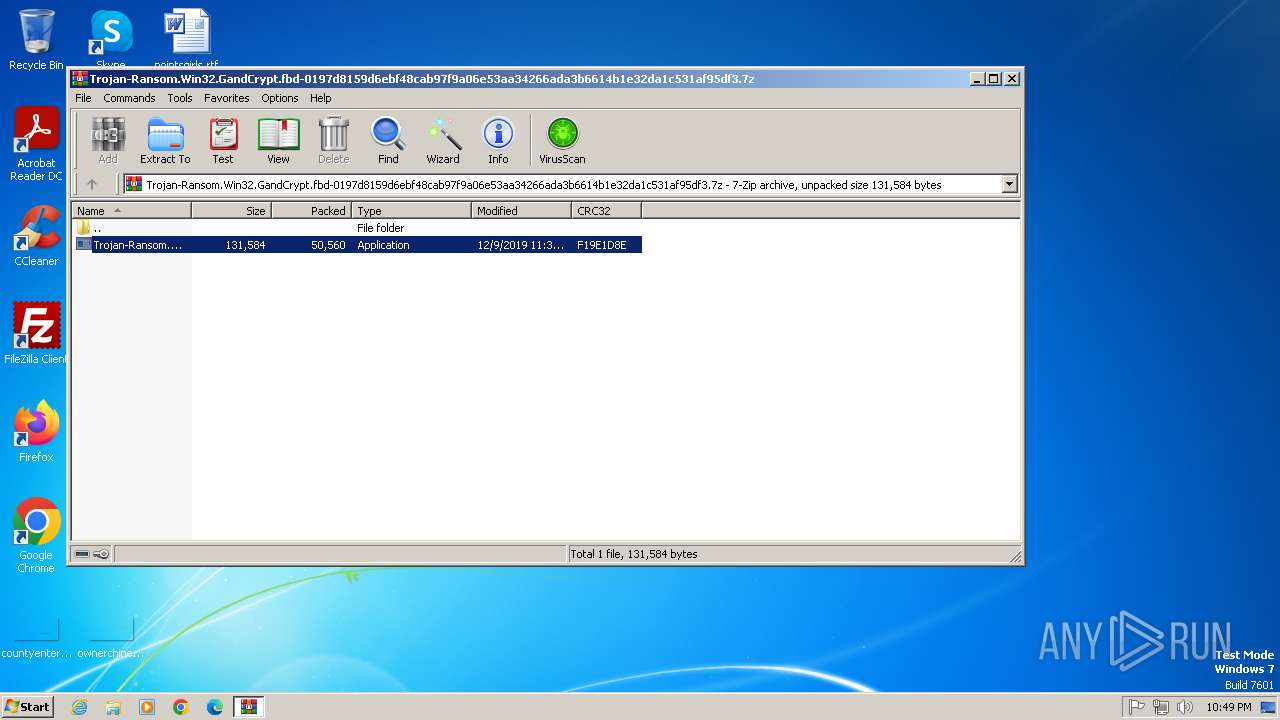
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | CFB9CBD272136D9046812A56C4333F15 |
| SHA1: | 020B037E18AF5FE49B87F318E7F98A94B06182A6 |
| SHA256: | F2C63AB7DBC9F330F2CF27CD671E67DB97D48F5401BF8701C089EB5564F0FAFA |
| SSDEEP: | 1536:RCPZ0QlmG+2DzTagLMz3OQnw2dyDNcMrNXx:RsZZd+WygLMKQFyplrNXx |
MALICIOUS
GANDCRAB mutex has been found
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
GandCrab keys are found
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Writes a file to the Word startup folder
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Renames files like ransomware
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
SUSPICIOUS
Reads security settings of Internet Explorer
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Reads settings of System Certificates
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Adds/modifies Windows certificates
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Reads the Internet Settings
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
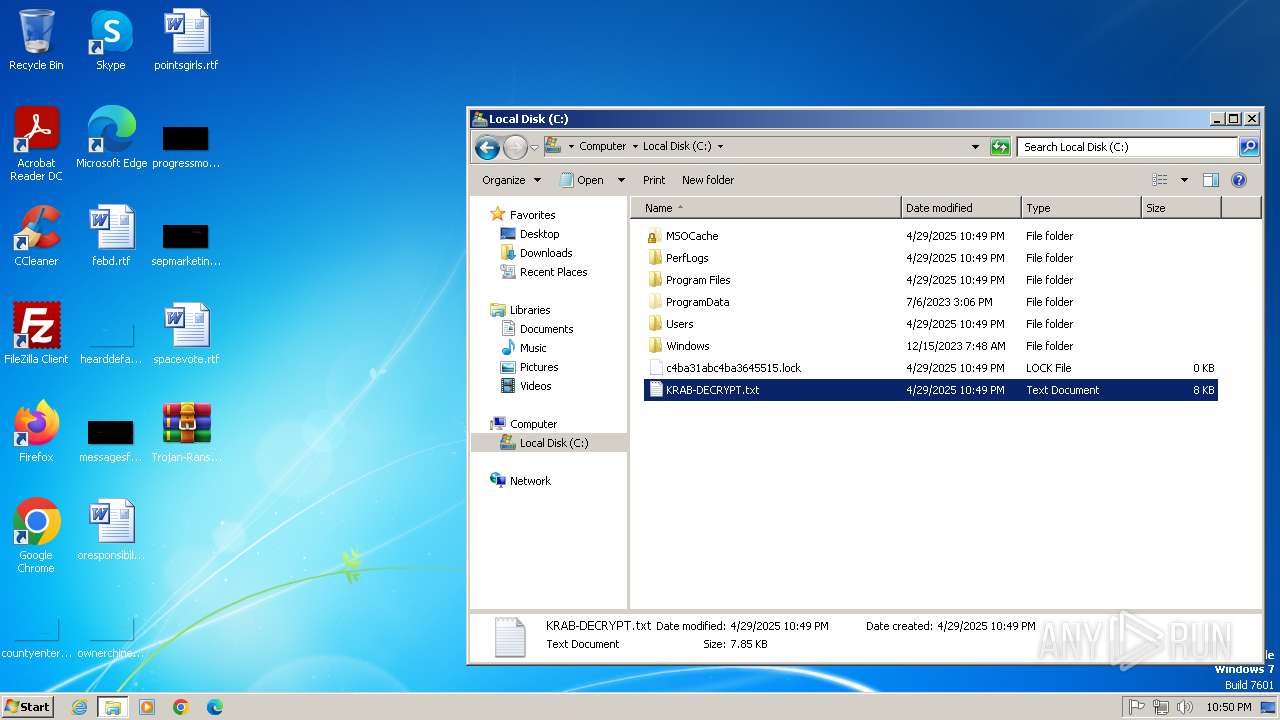
Creates file in the systems drive root
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Reads browser cookies
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
INFO
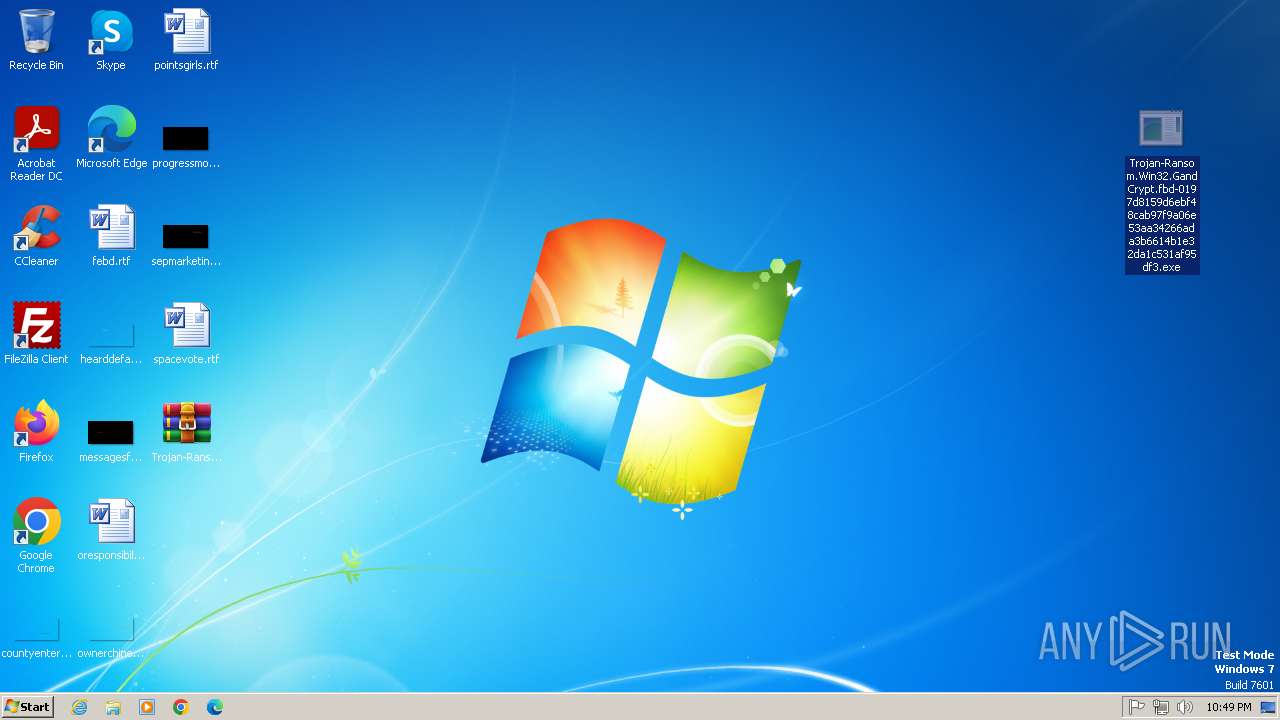
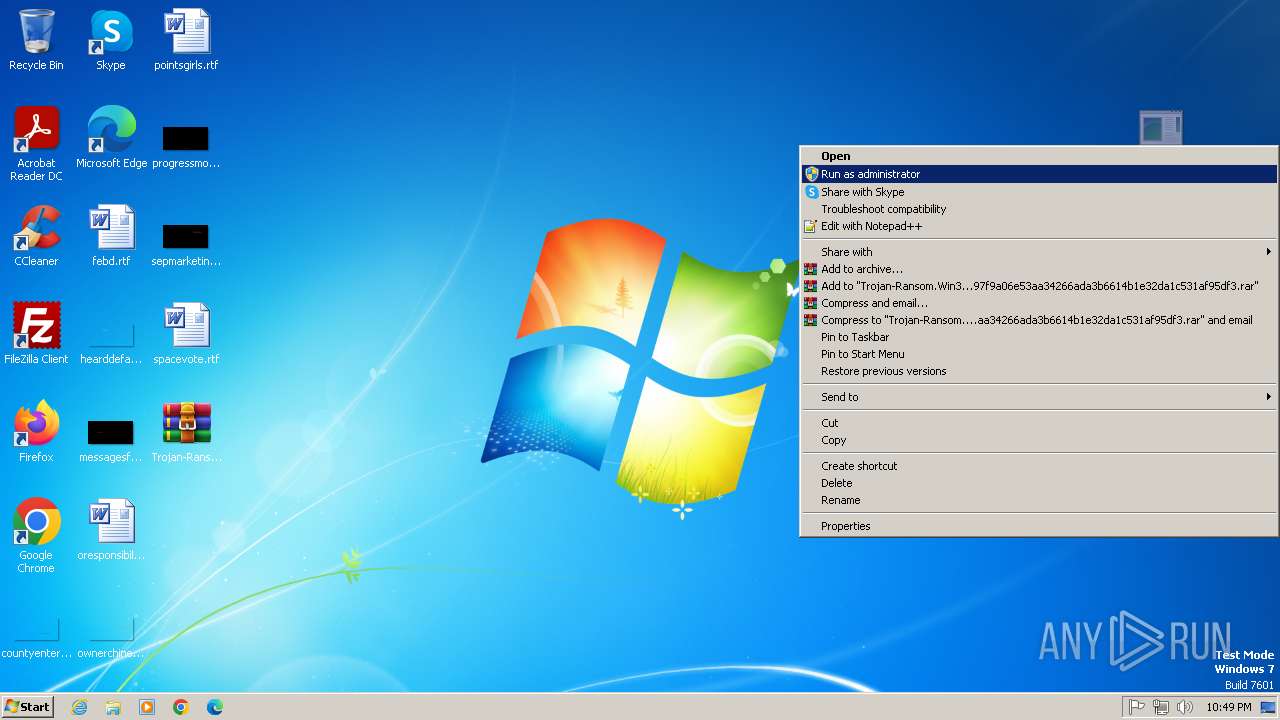
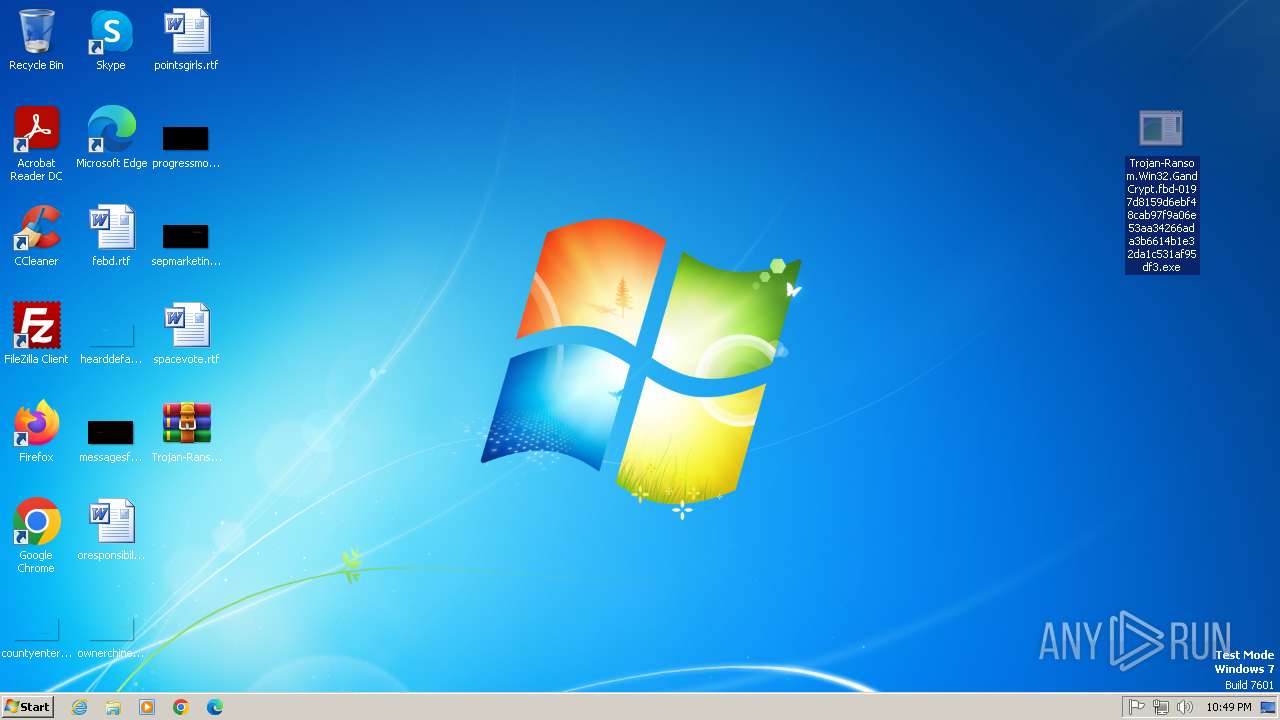
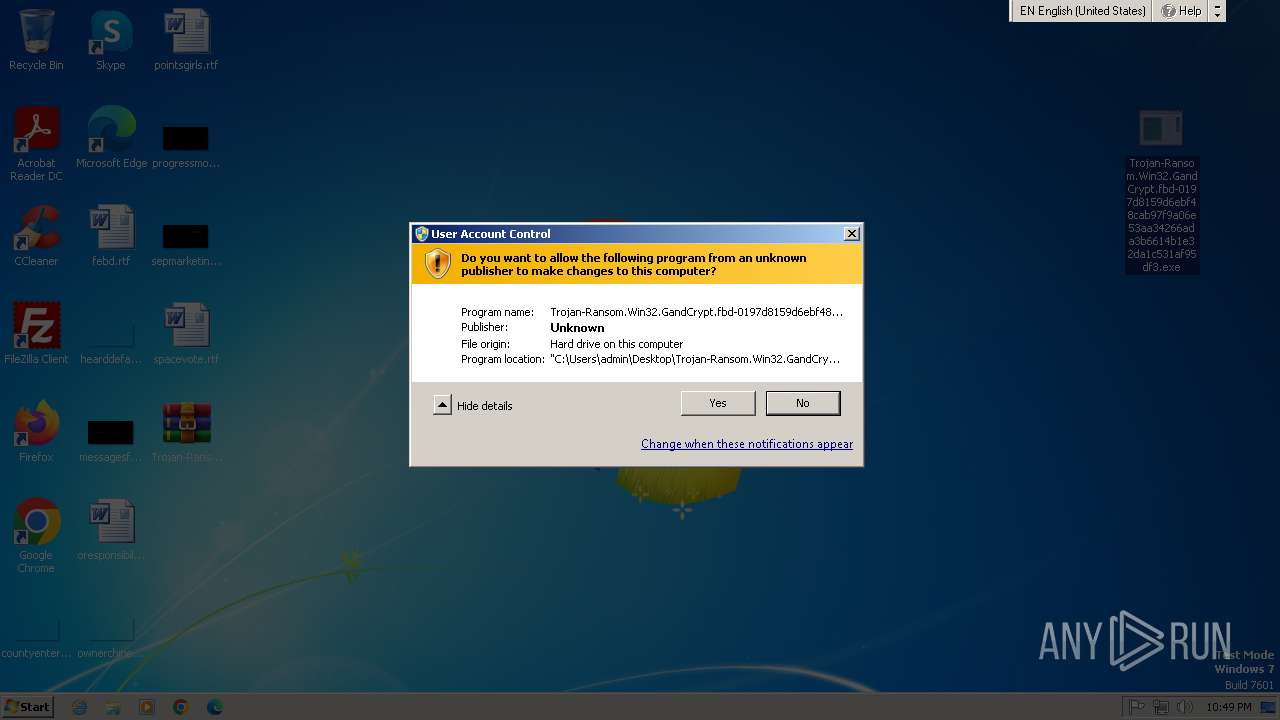
Manual execution by a user
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
- explorer.exe (PID: 2436)
- notepad.exe (PID: 3296)
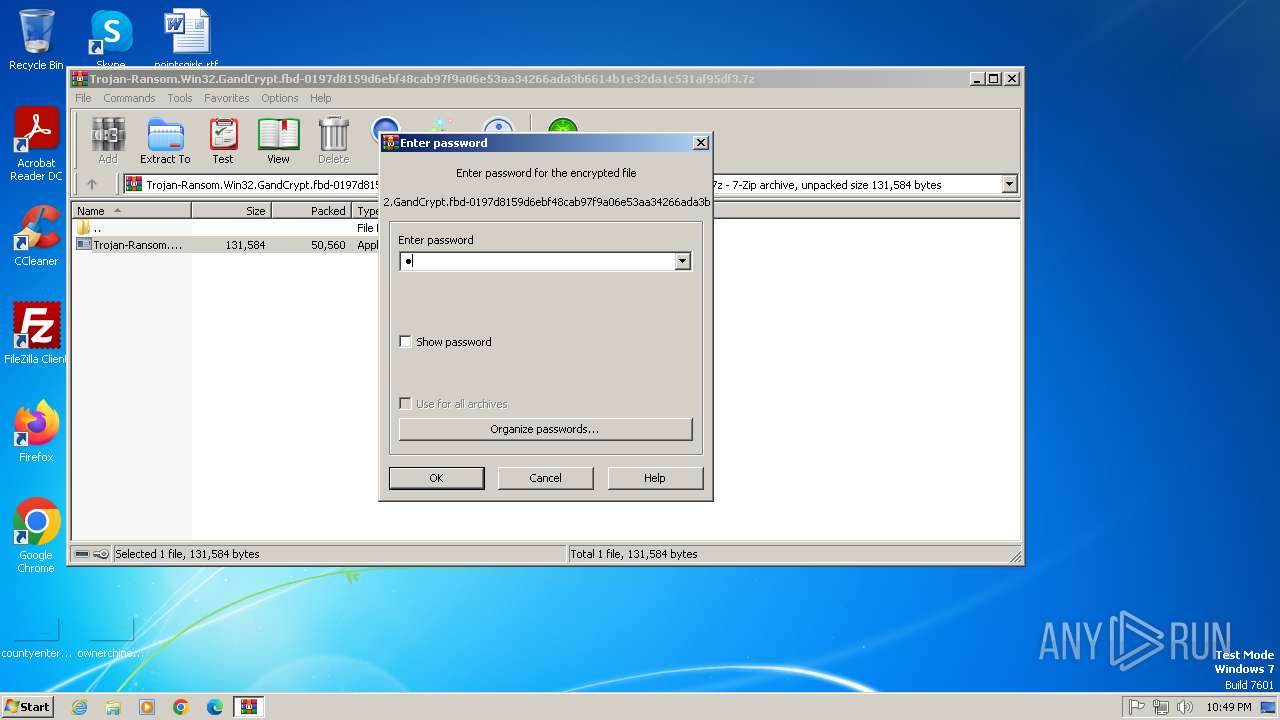
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2848)
Reads CPU info
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Reads Environment values
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Reads product name
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Reads the machine GUID from the registry
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Checks proxy server information
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Checks supported languages
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Reads the software policy settings
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Reads the computer name
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Creates files or folders in the user directory
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Creates files in the program directory
- Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe (PID: 2100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2019:12:09 23:38:54+00:00 |
| ArchivedFileName: | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe |
Total processes
44
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1080 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2100 | "C:\Users\admin\Desktop\Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe" | C:\Users\admin\Desktop\Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 2436 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
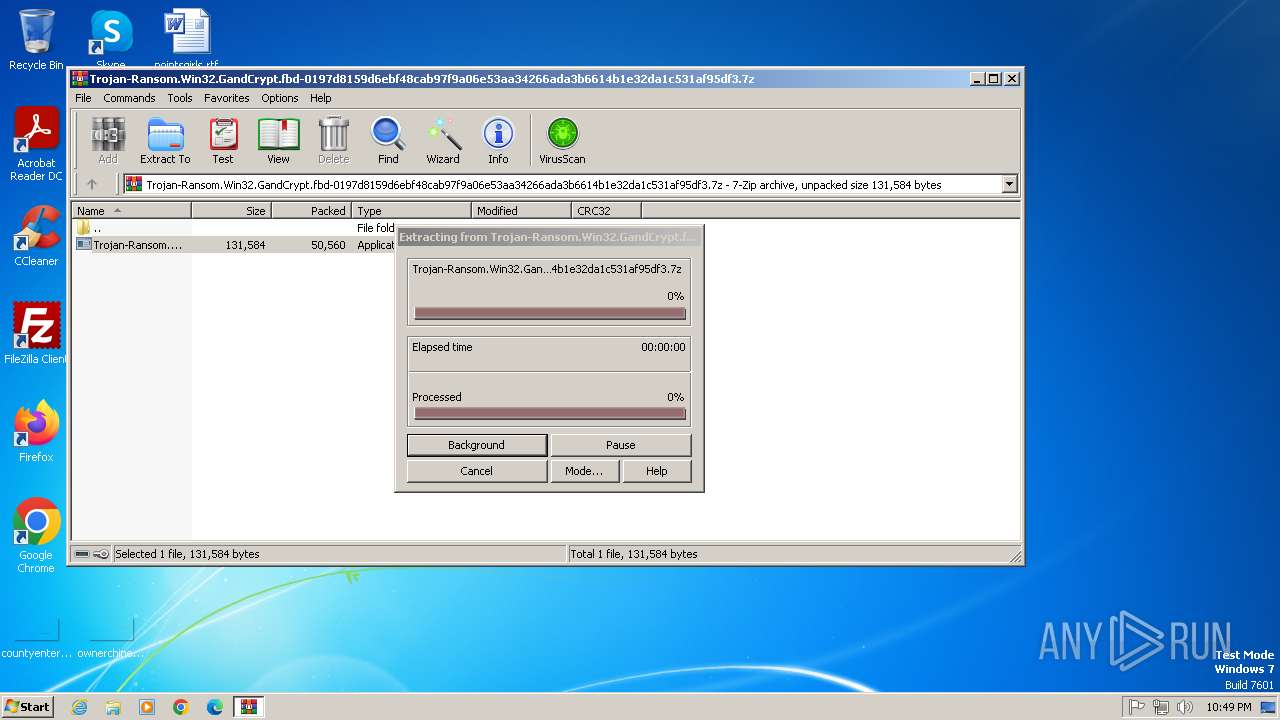
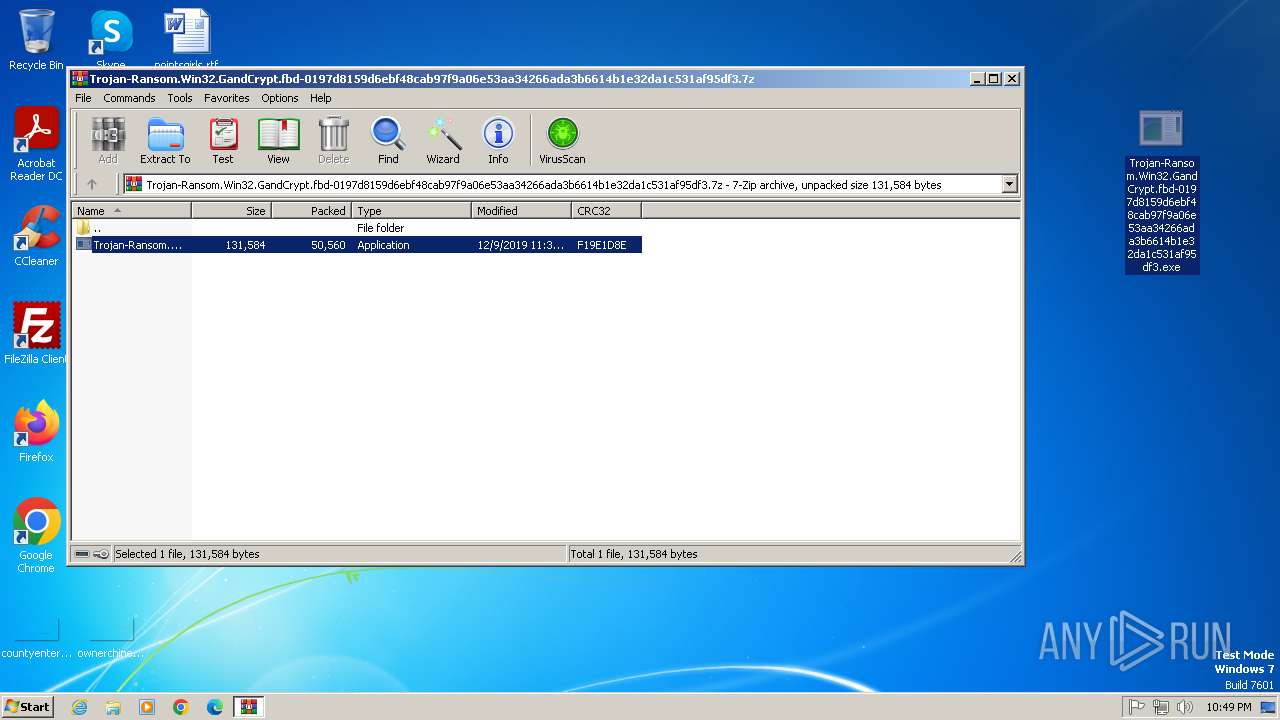
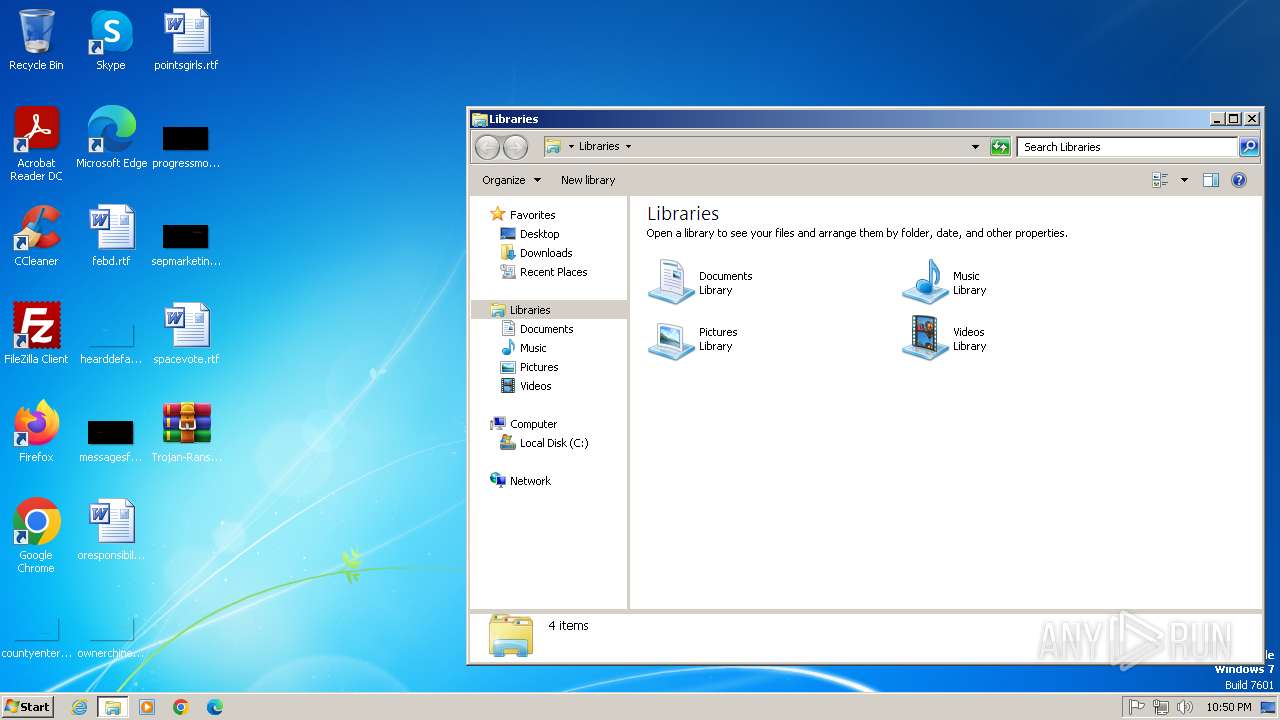
| 2848 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3296 | "C:\Windows\system32\NOTEPAD.EXE" C:\KRAB-DECRYPT.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
30 739
Read events
30 649
Write events
79
Delete events
11
Modification events
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1080) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkList\Nla\Cache\Intranet |
| Operation: | write | Name: | {4040CF00-1B3E-486A-B407-FA14C56B6FC0} |
Value: D4DA6D39D73C | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.7z | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2848) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
5
Suspicious files
1 258
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | C:\KRAB-DECRYPT.txt | binary | |
MD5:4A5756CC6D2605A6FAE5F37E5EC11444 | SHA256:808ECD51B8C19F4F4B2122F71CC5B8E5602381DDEB0D52F6BFA77895FE292733 | |||
| 2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | C:\Users\KRAB-DECRYPT.txt | binary | |
MD5:4A5756CC6D2605A6FAE5F37E5EC11444 | SHA256:808ECD51B8C19F4F4B2122F71CC5B8E5602381DDEB0D52F6BFA77895FE292733 | |||
| 1080 | svchost.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp\Cab4706.tmp | compressed | |
MD5:77B20B5CD41BC6BB475CCA3F91AE6E3C | SHA256:5511A9B9F9144ED7BDE4CCB074733B7C564D918D2A8B10D391AFC6BE5B3B1509 | |||
| 2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim | — | |
MD5:— | SHA256:— | |||
| 2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.KRAB | — | |
MD5:— | SHA256:— | |||
| 2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:77B20B5CD41BC6BB475CCA3F91AE6E3C | SHA256:5511A9B9F9144ED7BDE4CCB074733B7C564D918D2A8B10D391AFC6BE5B3B1509 | |||
| 2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:6917486A5FB084C0793ECC4E2465FC55 | SHA256:F846E42A8C0CF775FDF86337F6182D2C8816A549781424045F545900EF7DAC46 | |||
| 2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:9ADEDD06815AFEA84088681D4B60F48B | SHA256:08B9D1BEE50A765DB66B960DFB1277ADE9D7B0829EE161AF51457D7C20E36611 | |||
| 1080 | svchost.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp\Tar4707.tmp | binary | |
MD5:91A1B89AA7A488DBB204DBB4767F1F21 | SHA256:F6BE95C88C20EF82EE8A6878E16F9ECD77300BC1905EB826592A0DD41AD1C0F8 | |||
| 2848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2848.17271\Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | executable | |
MD5:1B8FF7D0B6204A4597463055204F8180 | SHA256:0197D8159D6EBF48CAB97F9A06E53AA34266ADA3B6614B1E32DA1C531AF95DF3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
14
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | GET | 301 | 104.21.63.109:80 | http://www.macartegrise.eu/ | unknown | — | — | malicious |
2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | GET | 200 | 23.50.131.200:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0545c25b84bbf84a | unknown | — | — | whitelisted |
2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | GET | 200 | 172.217.16.131:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | GET | 200 | 172.217.16.131:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | GET | 301 | 104.21.63.109:80 | http://www.macartegrise.eu/ | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | 104.21.63.109:80 | www.macartegrise.eu | CLOUDFLARENET | — | malicious |
2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | 104.21.63.109:443 | www.macartegrise.eu | CLOUDFLARENET | — | malicious |
2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | 23.50.131.200:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | 172.217.16.131:80 | c.pki.goog | GOOGLE | US | whitelisted |
2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | 34.136.111.81:80 | www.poketeg.com | GOOGLE-CLOUD-PLATFORM | US | malicious |
2100 | Trojan-Ransom.Win32.GandCrypt.fbd-0197d8159d6ebf48cab97f9a06e53aa34266ada3b6614b1e32da1c531af95df3.exe | 34.132.102.6:80 | www.poketeg.com | GOOGLE-CLOUD-PLATFORM | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.billerimpex.com |
| whitelisted |
www.macartegrise.eu |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
c.pki.goog |
| whitelisted |
www.poketeg.com |
| malicious |
dns.msftncsi.com |
| whitelisted |