| File name: | you-get-0.4.985-win32.exe |
| Full analysis: | https://app.any.run/tasks/14a49910-9394-4d2d-b951-95f59d6a35cd |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 00:58:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 8FC83220258965FB31D3385B83A1AF43 |
| SHA1: | A50409FAEB5B0DDD77935331FE832C2AD2335864 |
| SHA256: | F2A72D3927A73081A8DF7C36424BE5183692198BE25B1547A8200AA36215DDBD |
| SSDEEP: | 196608:afxY4Txyv5Oi2QG33kWOE30GX925D4gYQIp:WY485OilikWVEGX9gYQIp |
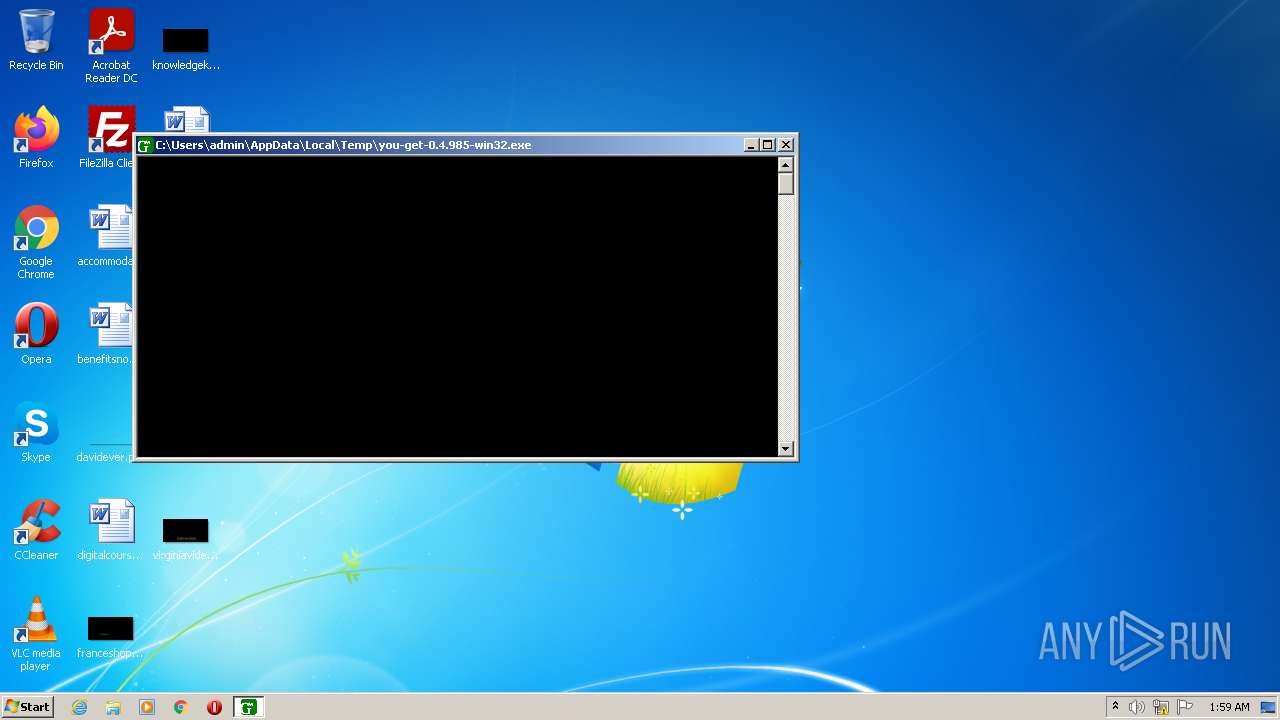
MALICIOUS
Drops executable file immediately after starts
- you-get-0.4.985-win32.exe (PID: 3412)
Loads dropped or rewritten executable
- you-get-0.4.985-win32.exe (PID: 1088)
SUSPICIOUS
Drops a file with a compile date too recent
- you-get-0.4.985-win32.exe (PID: 3412)
Checks supported languages
- you-get-0.4.985-win32.exe (PID: 3412)
- you-get-0.4.985-win32.exe (PID: 1088)
Reads the computer name
- you-get-0.4.985-win32.exe (PID: 1088)
Reads Environment values
- you-get-0.4.985-win32.exe (PID: 1088)
Application launched itself
- you-get-0.4.985-win32.exe (PID: 3412)
Loads Python modules
- you-get-0.4.985-win32.exe (PID: 1088)
Executable content was dropped or overwritten
- you-get-0.4.985-win32.exe (PID: 3412)
INFO
Dropped object may contain Bitcoin addresses
- you-get-0.4.985-win32.exe (PID: 3412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 1970-Jan-02 10:28:52 |
| TLS Callbacks: | 2 callback(s) detected. |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 8 |
| TimeDateStamp: | 1970-Jan-02 10:28:52 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 39332 | 39424 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.11465 |
.data | 45056 | 52 | 512 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.584487 |
.rdata | 49152 | 18624 | 18944 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.99351 |
.bss | 69632 | 50696 | 0 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.idata | 122880 | 2940 | 3072 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0676 |
.CRT | 126976 | 52 | 512 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.271114 |
.tls | 131072 | 32 | 512 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.175526 |
.rsrc | 135168 | 73208 | 73216 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.56322 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 1.91924 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 2.23123 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
2 | 6.05629 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.5741 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 7.95079 | 37019 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.29119 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
msvcrt.dll |
Total processes
35
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1088 | "C:\Users\admin\AppData\Local\Temp\you-get-0.4.985-win32.exe" | C:\Users\admin\AppData\Local\Temp\you-get-0.4.985-win32.exe | — | you-get-0.4.985-win32.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3412 | "C:\Users\admin\AppData\Local\Temp\you-get-0.4.985-win32.exe" | C:\Users\admin\AppData\Local\Temp\you-get-0.4.985-win32.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
163
Read events
163
Write events
0
Delete events
0
Modification events
Executable files
57
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3412 | you-get-0.4.985-win32.exe | C:\Users\admin\AppData\Local\Temp\_MEI34122\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 3412 | you-get-0.4.985-win32.exe | C:\Users\admin\AppData\Local\Temp\_MEI34122\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 3412 | you-get-0.4.985-win32.exe | C:\Users\admin\AppData\Local\Temp\_MEI34122\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 3412 | you-get-0.4.985-win32.exe | C:\Users\admin\AppData\Local\Temp\_MEI34122\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 3412 | you-get-0.4.985-win32.exe | C:\Users\admin\AppData\Local\Temp\_MEI34122\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
| 3412 | you-get-0.4.985-win32.exe | C:\Users\admin\AppData\Local\Temp\_MEI34122\MSVCR100.dll | executable | |
MD5:32FC1A3BFD9BEDBF2DD73D65B40C2034 | SHA256:DA591987A11586D48E7B2F59A08D94C78E44DCBDD40DA1CE721C30E499088336 | |||
| 3412 | you-get-0.4.985-win32.exe | C:\Users\admin\AppData\Local\Temp\_MEI34122\_hashlib.cp35-win32.pyd | executable | |
MD5:3C41F5FDD84874BB85413F00E49B7D11 | SHA256:380211A68208AE646198F34C3B7C13D43AE5A3E5C337D1871B8E62DC7F334ABA | |||
| 3412 | you-get-0.4.985-win32.exe | C:\Users\admin\AppData\Local\Temp\_MEI34122\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:00D8B4BED48A1BB8A0451B967A902977 | SHA256:568D7F8551D8B4199DB3359D5145BC4CB01D6D2F1347547F47967EB06A45C3B5 | |||
| 3412 | you-get-0.4.985-win32.exe | C:\Users\admin\AppData\Local\Temp\_MEI34122\api-ms-win-core-file-l2-1-0.dll | executable | |
MD5:534483B0F4A1924B1AE6D7E66B4A4926 | SHA256:C1BCA1BB524C5AE3D877A099F469B6FC34288BAB26AE7A7F4FC47CD869F4958D | |||
| 3412 | you-get-0.4.985-win32.exe | C:\Users\admin\AppData\Local\Temp\_MEI34122\api-ms-win-core-handle-l1-1-0.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report