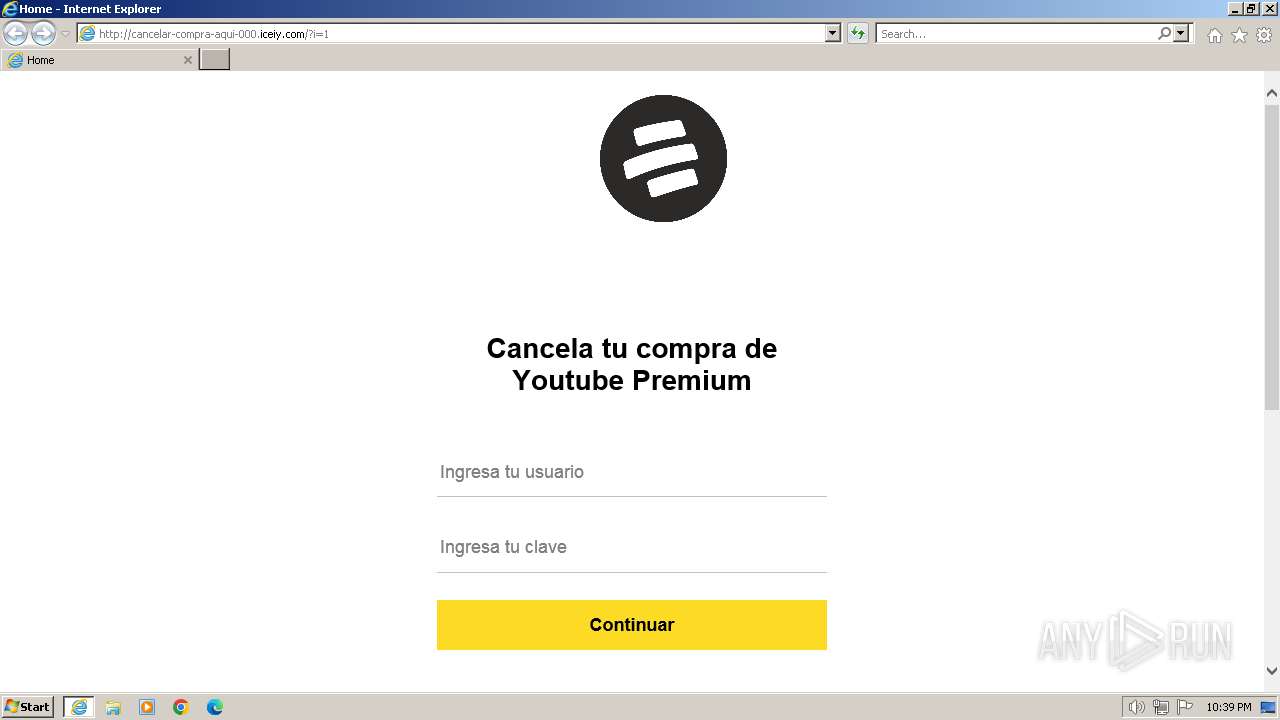
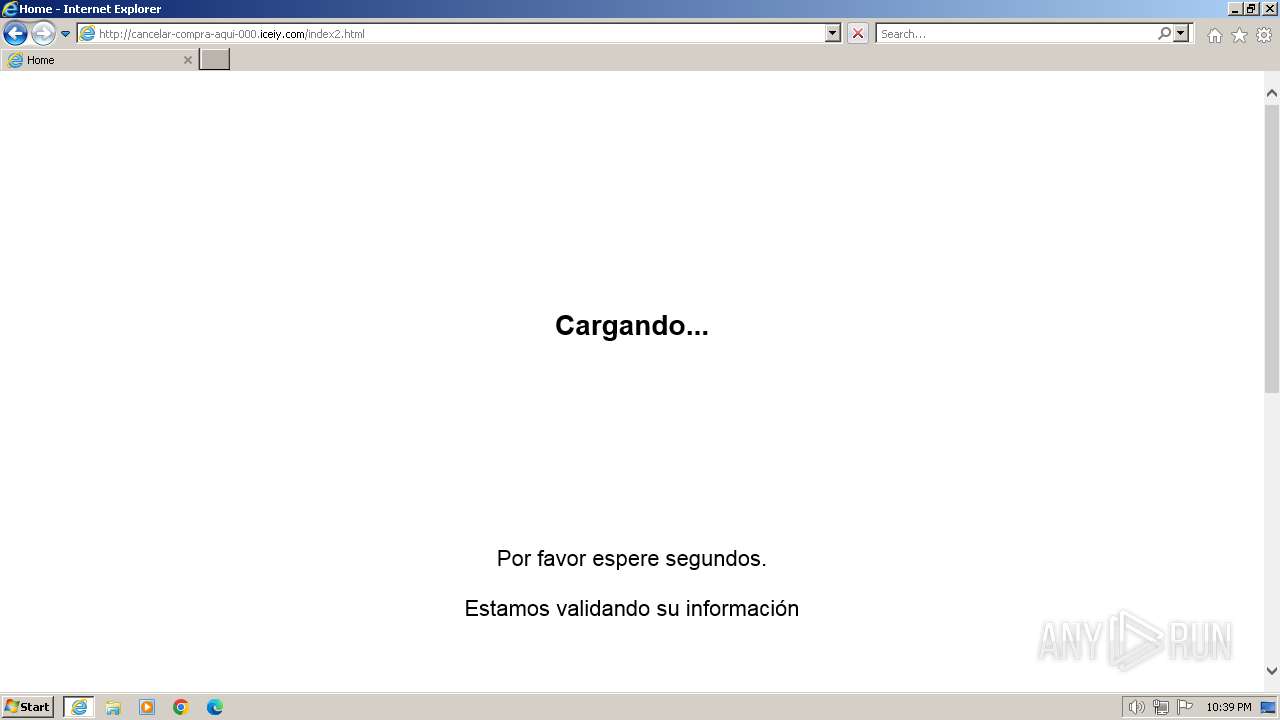
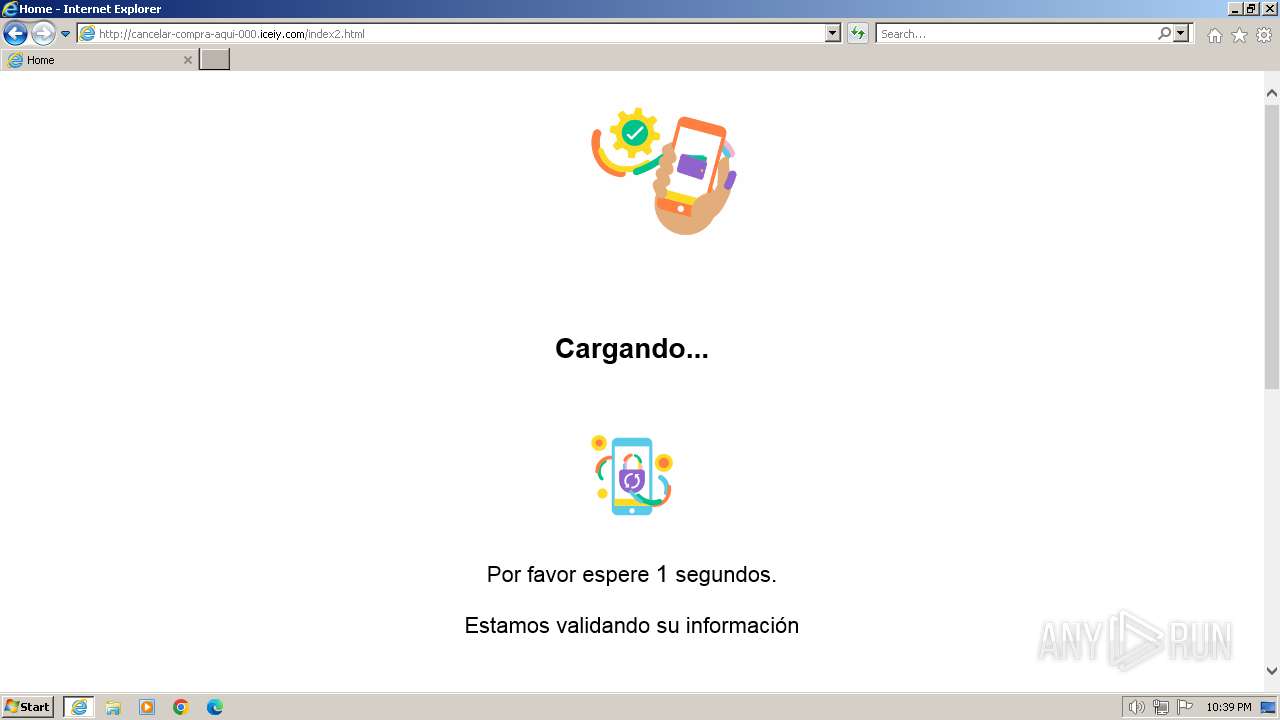
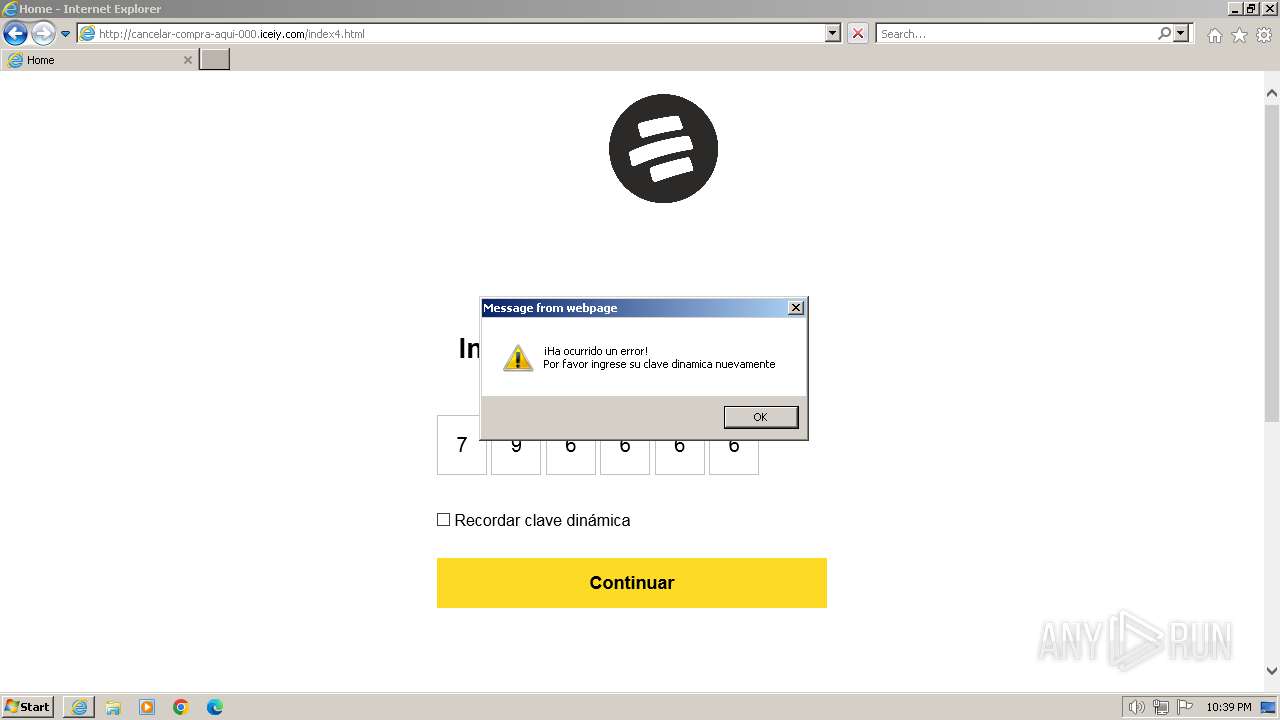
| URL: | cancelar-compra-aqui-000.iceiy.com/ |
| Full analysis: | https://app.any.run/tasks/bf92f6e2-5cd6-49da-b4b0-f8f0a14bc611 |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2024, 22:38:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1422A946839AF11AA6CEE37A124361B4 |
| SHA1: | 42575C40783B94ECAF269E6E1BEC9B4C5A3BED9D |
| SHA256: | F2A5D22702D06228473053658B905B2BD4B9D02EE2D6AA4434FC295BE1A059D2 |
| SSDEEP: | 3:HZ2zEUZIVLMcw:HAEUIJw |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2040 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Internet Explorer\iexplore.exe" "cancelar-compra-aqui-000.iceiy.com/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
19 237
Read events
19 168
Write events
67
Delete events
2
Modification events
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2040) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
46
Text files
22
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 392 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:3B8718BD7867F0D32922FC6EB112E52F | SHA256:0DA3F6452B91947ED4AD5E11A34CB348A7DA0276E2EE8F8F27D5F3B3987DD1BD | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\HSW3ANKI.htm | html | |
MD5:8934BC81E73EE977948E529E66D189E0 | SHA256:2C1DA8ED62394F674D88522BDBE23EB6EDB97262511352AF98C2574FC0E62B40 | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\C4XYTWOR.txt | text | |
MD5:C0FA9548E9856331809F175513F92832 | SHA256:2B4E2CF26A19A2D2994B321099021B6867168FC84CFB847BEA46250821484888 | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\main[1].css | text | |
MD5:3B9195B36F73EDD0DBDECB586F03BEDF | SHA256:B5D9C6CCC6F8719760801DD385BB455E4F16537D5AC17F2059CA0702383677E2 | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\XV9KCFAY.htm | html | |
MD5:533FEF8E9E626DE3FC9792C120C69979 | SHA256:1C8E4ADFF6709E42B0111451F5F989519479B805EED3A8A7E247B478E35A2A4F | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\saxes[1].js | text | |
MD5:7FF9ED3DC689A0330BE25F5BCBC2327E | SHA256:148B2782FCDF9D7536577C787359607F9AC63CC0322A5059613CEC944C258556 | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:2A07E721CE75014F856C462D39B0D1C2 | SHA256:58B01F08123532C052A1218B7AF877A170DEF4245BF910BA4DB72072626317EB | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:AC89A852C2AAA3D389B2D2DD312AD367 | SHA256:0B720E19270C672F9B6E0EC40B468AC49376807DE08A814573FE038779534F45 | |||
| 392 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A16C6C16D94F76E0808C087DFC657D99_625B6A317EF9FBF256D00704E8512DA8 | binary | |
MD5:9663097D24D67B627AF76B8E33A6CB56 | SHA256:1F84E4549B97236262B8D3B99FD74B52AA13B7D90076731DC54551F2329FA6E0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
61
DNS requests
29
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
392 | iexplore.exe | GET | 200 | 185.27.134.223:80 | http://cancelar-compra-aqui-000.iceiy.com/ | GB | html | 845 b | unknown |
392 | iexplore.exe | GET | 200 | 185.27.134.223:80 | http://cancelar-compra-aqui-000.iceiy.com/?i=1 | GB | html | 3.29 Kb | unknown |
392 | iexplore.exe | GET | 200 | 185.27.134.223:80 | http://cancelar-compra-aqui-000.iceiy.com/bootstrap.min.css | GB | — | — | unknown |
392 | iexplore.exe | GET | 200 | 185.27.134.223:80 | http://cancelar-compra-aqui-000.iceiy.com/util.css | GB | text | 81.8 Kb | unknown |
392 | iexplore.exe | GET | 200 | 185.27.134.223:80 | http://cancelar-compra-aqui-000.iceiy.com/main.css | GB | text | 13.3 Kb | unknown |
392 | iexplore.exe | GET | 200 | 185.27.134.223:80 | http://cancelar-compra-aqui-000.iceiy.com/saxes.js | GB | text | 4.62 Kb | unknown |
392 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0a8775331b03f167 | GB | compressed | 4.66 Kb | unknown |
392 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7f4ae261cec090e7 | GB | compressed | 4.66 Kb | unknown |
392 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | unknown |
392 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
392 | iexplore.exe | 185.27.134.223:80 | cancelar-compra-aqui-000.iceiy.com | Wildcard UK Limited | GB | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
392 | iexplore.exe | 172.217.18.10:443 | ajax.googleapis.com | GOOGLE | US | whitelisted |
392 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
392 | iexplore.exe | 142.250.186.35:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
392 | iexplore.exe | 169.62.185.103:443 | www.bancolombia.com | SOFTLAYER | US | unknown |
2040 | iexplore.exe | 104.126.37.171:443 | www.bing.com | Akamai International B.V. | DE | unknown |
2040 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cancelar-compra-aqui-000.iceiy.com |
| unknown |
ajax.googleapis.com |
| whitelisted |
www.bancolombia.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
392 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
392 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
392 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup SSL Cert Observed (ipinfo .io) |
392 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup SSL Cert Observed (ipinfo .io) |
392 | iexplore.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
392 | iexplore.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
392 | iexplore.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
392 | iexplore.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
1080 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |