| File name: | jmmaster.exe |
| Full analysis: | https://app.any.run/tasks/fb78c611-b125-44fb-b34d-2a5f14633a25 |
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2019, 15:13:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, InnoSetup self-extracting archive |
| MD5: | A2F5ED2EE63ADAB3C7F9C91D9E5DC83A |
| SHA1: | 9CC4BA05F7DEC72B38399D1CFB904F8C16468D46 |
| SHA256: | F2A334E64A86B41CFDACF56442860BE5C43C5776F392E2756AD3E8FABDAC5E97 |
| SSDEEP: | 24576:yDq7GAbr6NTSTi8jTNGaGrQu/+0gyrIo9cpaxU4VFFjgwO5hwKkuuczoScFLXzP3:yDkfTcaHu20gyrIbkG46w+wKkccSaLXD |
MALICIOUS
Changes the autorun value in the registry
- SaveNowInst.exe (PID: 3292)
- whinstaller.exe (PID: 3400)
Application was dropped or rewritten from another process
- SaveNow.exe (PID: 2936)
- INSA0A9.tmp (PID: 2596)
- whinstaller.exe (PID: 3400)
- whAgent.exe (PID: 3608)
- jmm.exe (PID: 2392)
Loads dropped or rewritten executable
- INSA0A9.tmp (PID: 2596)
- whAgent.exe (PID: 3608)
SUSPICIOUS
Creates files in the Windows directory
- INSA0A9.tmp (PID: 2596)
- whinstaller.exe (PID: 3400)
Creates a software uninstall entry
- INSA0A9.tmp (PID: 2596)
- whinstaller.exe (PID: 3400)
Executable content was dropped or overwritten
- SaveNowInst.exe (PID: 3292)
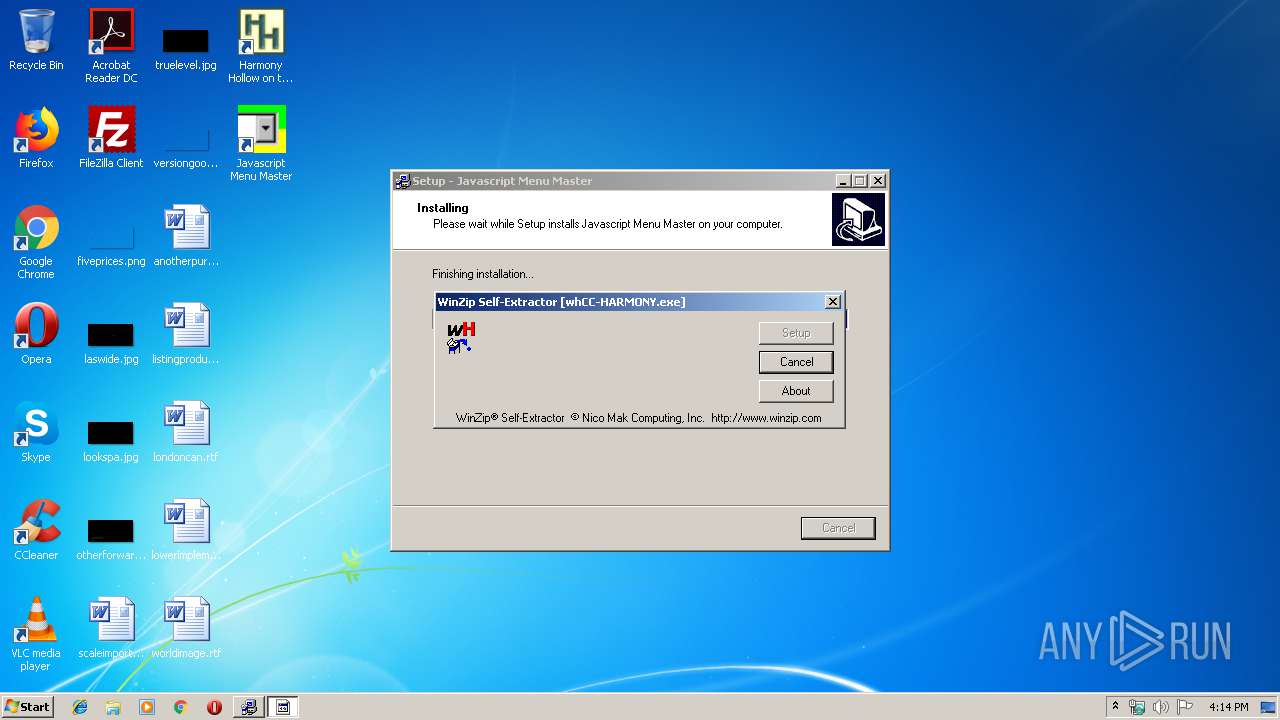
- whCC-HARMONY.exe (PID: 3460)
- whinstaller.exe (PID: 3400)
- INSA0A9.tmp (PID: 2596)
- jmmaster.exe (PID: 3600)
Creates files in the program directory
- whinstaller.exe (PID: 3400)
- INSA0A9.tmp (PID: 2596)
Starts application with an unusual extension
- jmmaster.exe (PID: 3600)
Reads internet explorer settings
- SaveNow.exe (PID: 2936)
Removes files from Windows directory
- whinstaller.exe (PID: 3400)
Creates COM task schedule object
- whAgent.exe (PID: 3608)
INFO
Creates files in the program directory
- SaveNowInst.exe (PID: 3292)
Creates a software uninstall entry
- SaveNowInst.exe (PID: 3292)
Application was dropped or rewritten from another process
- whCC-HARMONY.exe (PID: 3460)
- SaveNowInst.exe (PID: 3292)
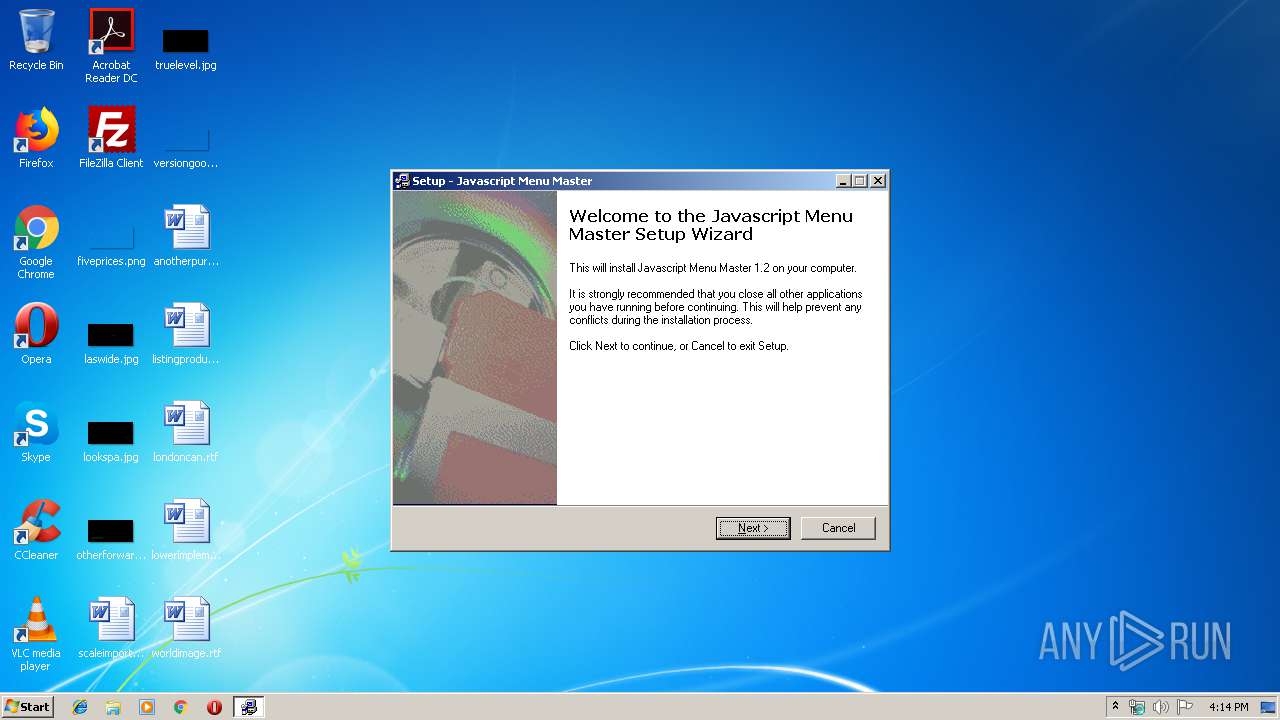
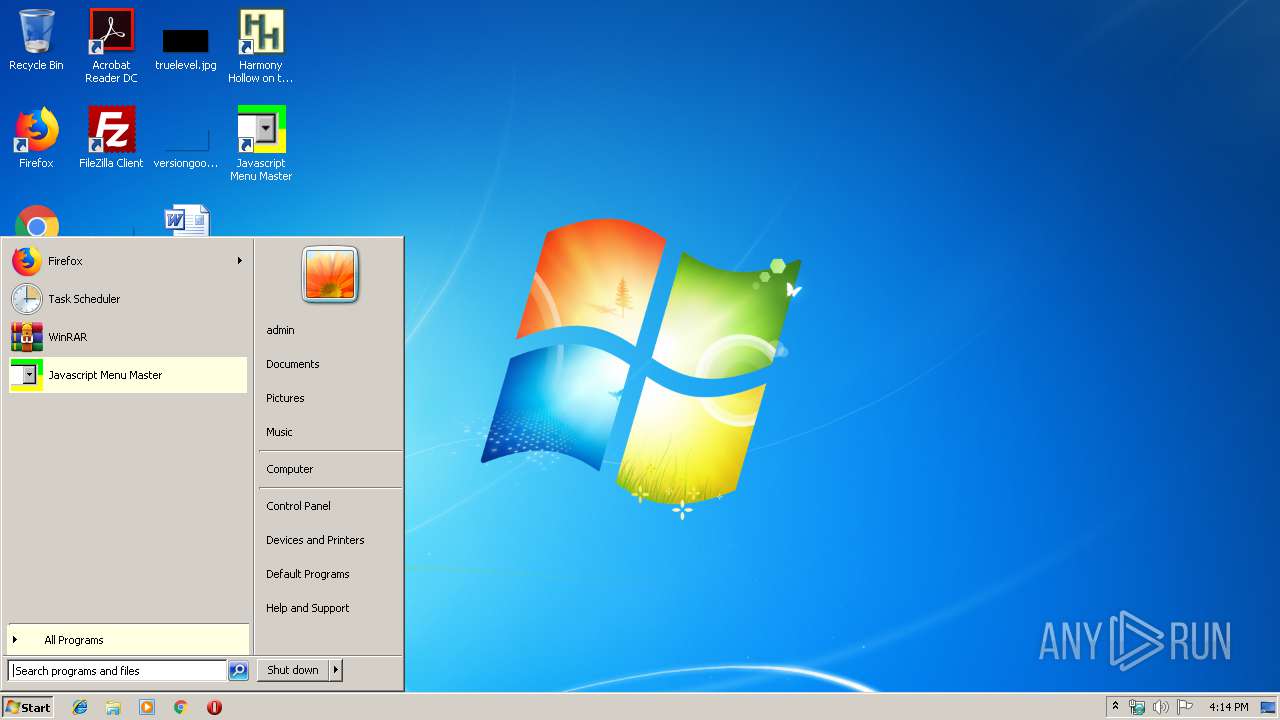
Manual execution by user
- jmm.exe (PID: 2392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (82.8) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.7) |
| .exe | | | Win32 Executable (generic) (3.4) |
| .exe | | | Generic Win/DOS Executable (1.5) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 46592 |
| InitializedDataSize: | 15872 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xbf34 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000B58C | 0x0000B600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49832 |
DATA | 0x0000D000 | 0x000017DC | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.28334 |
BSS | 0x0000F000 | 0x00001174 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00011000 | 0x00000762 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.55225 |
.tls | 0x00012000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00013000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.210826 |
.reloc | 0x00014000 | 0x00000840 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00015000 | 0x00001200 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.66089 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.49889 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 3.17623 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
MAINICON | 2.42968 | 34 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
45
Monitored processes
10
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
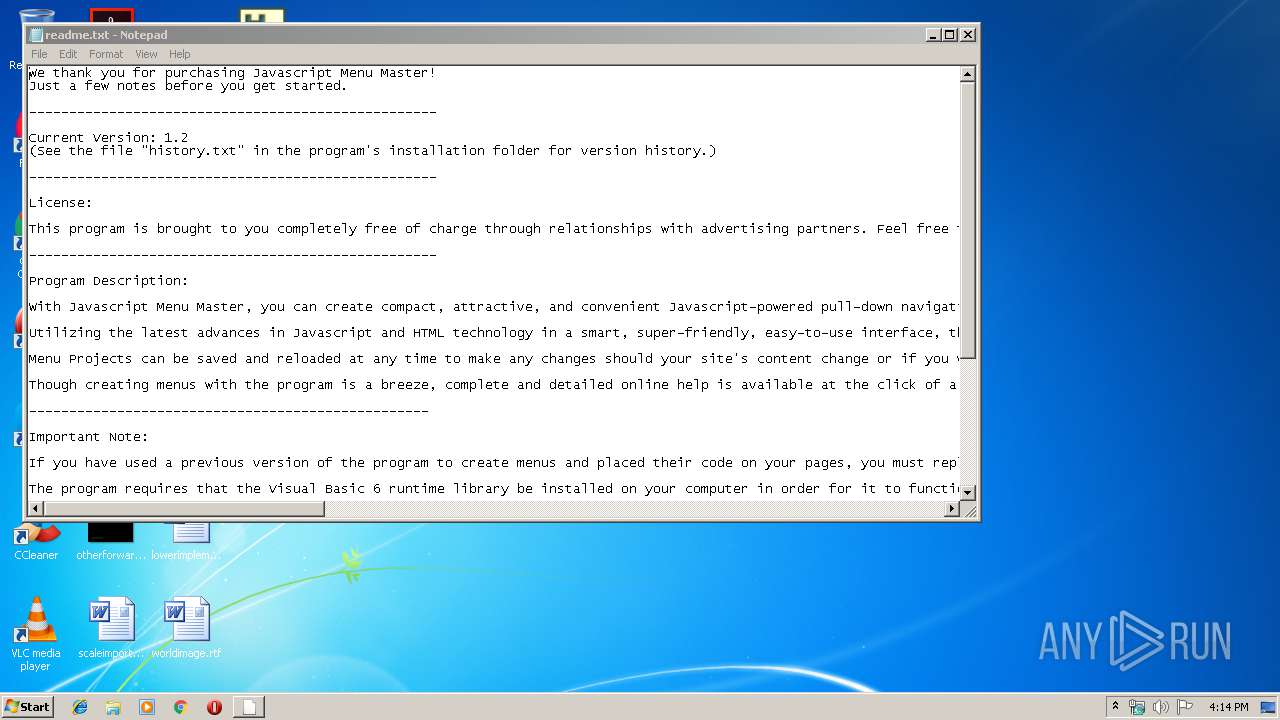
| 2184 | "C:\Windows\system32\NOTEPAD.EXE" C:\Program Files\Javascript Menu Master\readme.txt | C:\Windows\system32\NOTEPAD.EXE | — | INSA0A9.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
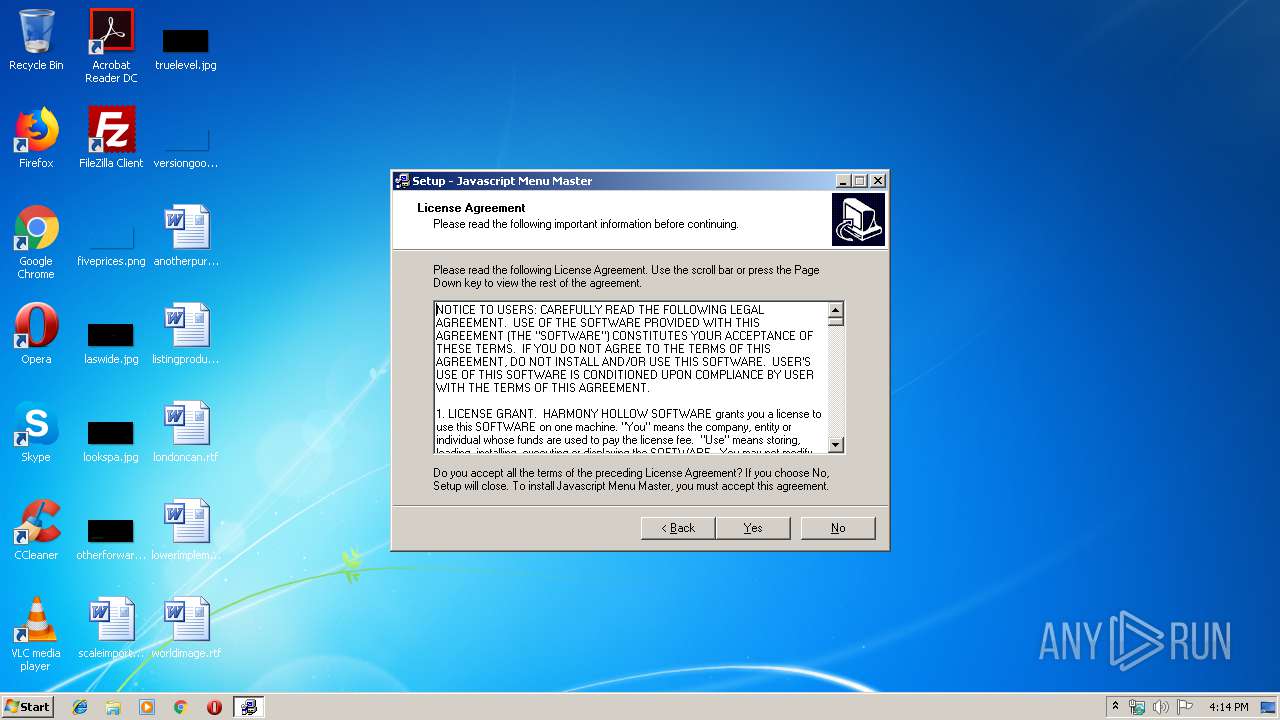
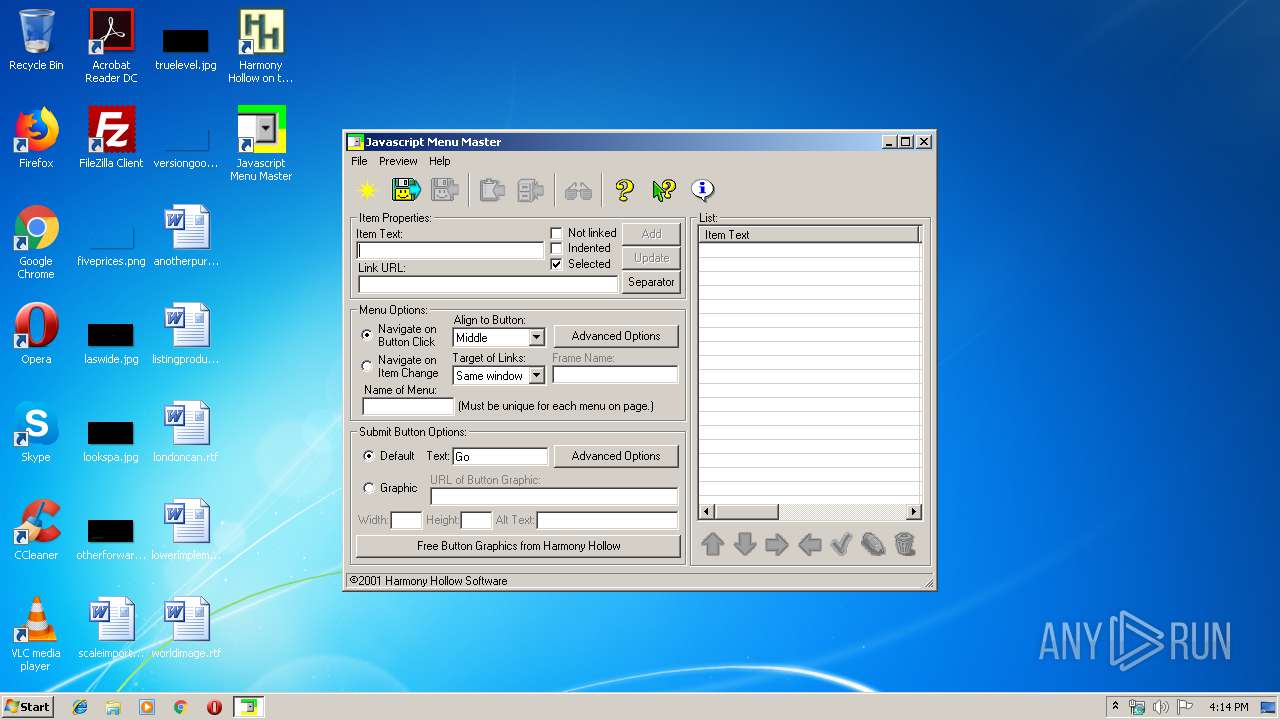
| 2392 | "C:\Program Files\Javascript Menu Master\jmm.exe" | C:\Program Files\Javascript Menu Master\jmm.exe | — | explorer.exe | |||||||||||
User: admin Company: Harmony Hollow, Inc. Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2596 | C:\Users\admin\AppData\Local\Temp\INSA0A9.tmp /SL3 $30134 C:\Users\admin\AppData\Local\Temp\jmmaster.exe 1376779 1380189 60928 | C:\Users\admin\AppData\Local\Temp\INSA0A9.tmp | jmmaster.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2936 | "C:\Program Files\SaveNow\SaveNow.exe" | C:\Program Files\SaveNow\SaveNow.exe | — | SaveNowInst.exe | |||||||||||
User: admin Company: WhenU.com, Inc. Integrity Level: HIGH Description: SaveNow Exit code: 0 Version: 1, 4, 0, 1 Modules
| |||||||||||||||
| 3184 | "C:\Users\admin\AppData\Local\Temp\jmmaster.exe" | C:\Users\admin\AppData\Local\Temp\jmmaster.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3292 | C:\Users\admin\AppData\Local\Temp\is-1POIQ.tmp\SaveNowInst.exe http://app.whenu.com/Offers?url=HHLW0701 | C:\Users\admin\AppData\Local\Temp\is-1POIQ.tmp\SaveNowInst.exe | INSA0A9.tmp | ||||||||||||
User: admin Company: WhenU.com, Inc. Integrity Level: HIGH Description: SaveNow Setup Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
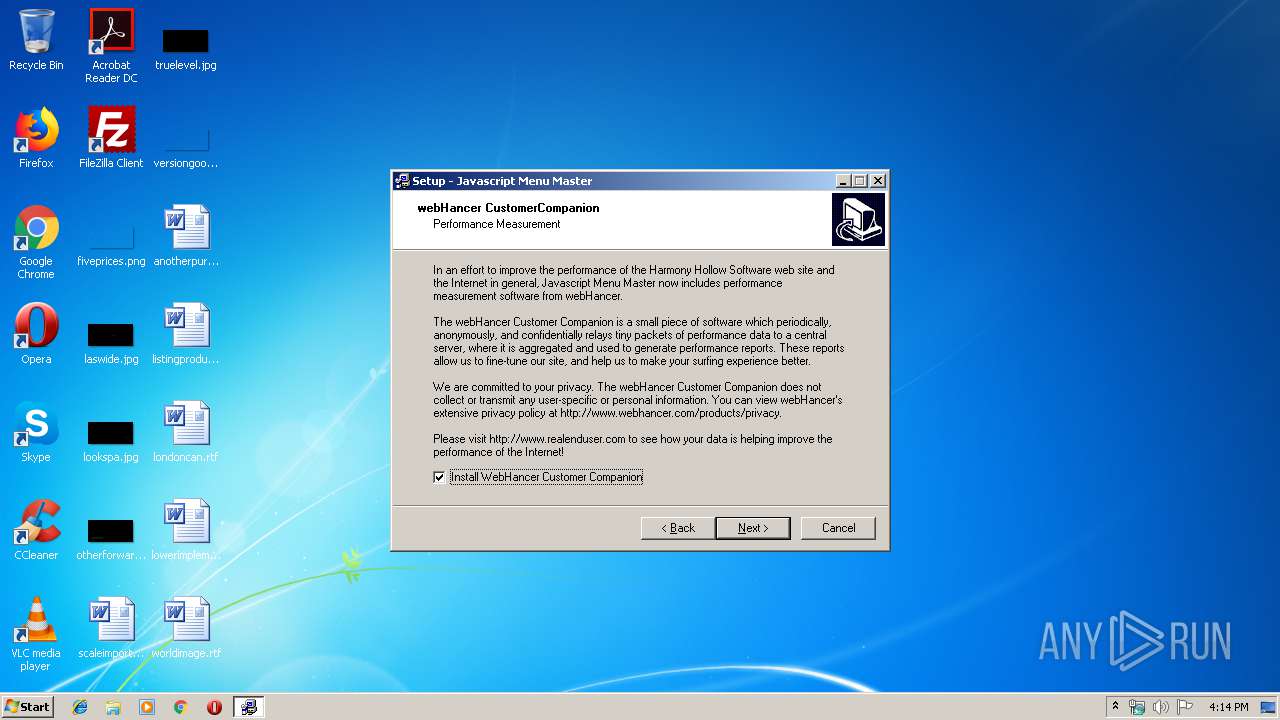
| 3400 | .\whinstaller.exe /silent | C:\Users\admin\AppData\Local\Temp\WZSD90F.tmp\whinstaller.exe | whCC-HARMONY.exe | ||||||||||||
User: admin Company: webHancer Corporation Integrity Level: HIGH Description: webHancer Installer Exit code: 0 Version: 1.8.1 Modules
| |||||||||||||||
| 3460 | C:\Users\admin\AppData\Local\Temp\is-1POIQ.tmp\whCC-HARMONY.exe | C:\Users\admin\AppData\Local\Temp\is-1POIQ.tmp\whCC-HARMONY.exe | INSA0A9.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3600 | "C:\Users\admin\AppData\Local\Temp\jmmaster.exe" | C:\Users\admin\AppData\Local\Temp\jmmaster.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3608 | whAgent.exe C:\PROGRA~1\WEBHAN~1\ | C:\Program Files\webHancer\programs\whAgent.exe | whinstaller.exe | ||||||||||||
User: admin Company: webHancer Corporation Integrity Level: HIGH Description: webHancer Customer Companion Exit code: 0 Version: 2.1.4 Modules
| |||||||||||||||
Total events
1 787
Read events
1 687
Write events
99
Delete events
1
Modification events
| (PID) Process: | (3292) SaveNowInst.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (3292) SaveNowInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WhenU\SaveNow |
| Operation: | write | Name: | db_local_update |
Value: 0 | |||
| (PID) Process: | (3292) SaveNowInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WhenU\SaveNow |
| Operation: | write | Name: | db_script_update |
Value: 992992724 | |||
| (PID) Process: | (3292) SaveNowInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WhenU\SaveNow |
| Operation: | write | Name: | InstallDir |
Value: C:\Program Files\SaveNow | |||
| (PID) Process: | (3292) SaveNowInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WhenU\SaveNow |
| Operation: | write | Name: | pats_url |
Value: http://a1964.g.akamai.net/f/1964/2730/1h/app.whenu.com/OffersData | |||
| (PID) Process: | (3292) SaveNowInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WhenU\SaveNow |
| Operation: | write | Name: | script_url |
Value: http://a1964.g.akamai.net/f/1964/2730/1h/web.whenu.com/offscript2.html | |||
| (PID) Process: | (3292) SaveNowInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WhenU\SaveNow |
| Operation: | write | Name: | update_url |
Value: http://a1964.g.akamai.net/f/1964/2730/1d/web.whenu.com/savenowupdate.exe | |||
| (PID) Process: | (3292) SaveNowInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WhenU\SaveNow |
| Operation: | write | Name: | Version |
Value: 1.4 | |||
| (PID) Process: | (3292) SaveNowInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SaveNow |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\SaveNow\SaveNow.exe,-0 | |||
| (PID) Process: | (3292) SaveNowInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\SaveNow |
| Operation: | write | Name: | DisplayName |
Value: SaveNow | |||
Executable files
24
Suspicious files
2
Text files
97
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2596 | INSA0A9.tmp | C:\Program Files\Javascript Menu Master\is-V945H.tmp | — | |
MD5:— | SHA256:— | |||
| 2596 | INSA0A9.tmp | C:\Windows\system32\is-LEN9C.tmp | — | |
MD5:— | SHA256:— | |||
| 2596 | INSA0A9.tmp | C:\Windows\is-LKSRQ.tmp | — | |
MD5:— | SHA256:— | |||
| 2596 | INSA0A9.tmp | C:\Windows\is-6DUK6.tmp | — | |
MD5:— | SHA256:— | |||
| 2596 | INSA0A9.tmp | C:\Program Files\Javascript Menu Master\is-FICRB.tmp | — | |
MD5:— | SHA256:— | |||
| 2596 | INSA0A9.tmp | C:\Program Files\Javascript Menu Master\is-E1N1B.tmp | — | |
MD5:— | SHA256:— | |||
| 2596 | INSA0A9.tmp | C:\Program Files\Javascript Menu Master\is-3M1AJ.tmp | — | |
MD5:— | SHA256:— | |||
| 2596 | INSA0A9.tmp | C:\Program Files\Javascript Menu Master\is-OLHH6.tmp | — | |
MD5:— | SHA256:— | |||
| 2596 | INSA0A9.tmp | C:\Program Files\Javascript Menu Master\is-6KQBA.tmp | — | |
MD5:— | SHA256:— | |||
| 2596 | INSA0A9.tmp | C:\Users\admin\AppData\Local\Temp\is-1POIQ.tmp\is-AR5CA.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3608 | whAgent.exe | POST | 403 | 185.53.179.29:80 | http://prime.webhancer.com/ | DE | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3608 | whAgent.exe | 185.53.179.29:80 | prime.webhancer.com | Team Internet AG | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
prime.webhancer.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3608 | whAgent.exe | A Network Trojan was detected | ET MALWARE Webhancer Data Post |