| File name: | injector.exe |
| Full analysis: | https://app.any.run/tasks/c63bf564-d4cb-4b6a-887f-b3aa9aac53f4 |
| Verdict: | Malicious activity |
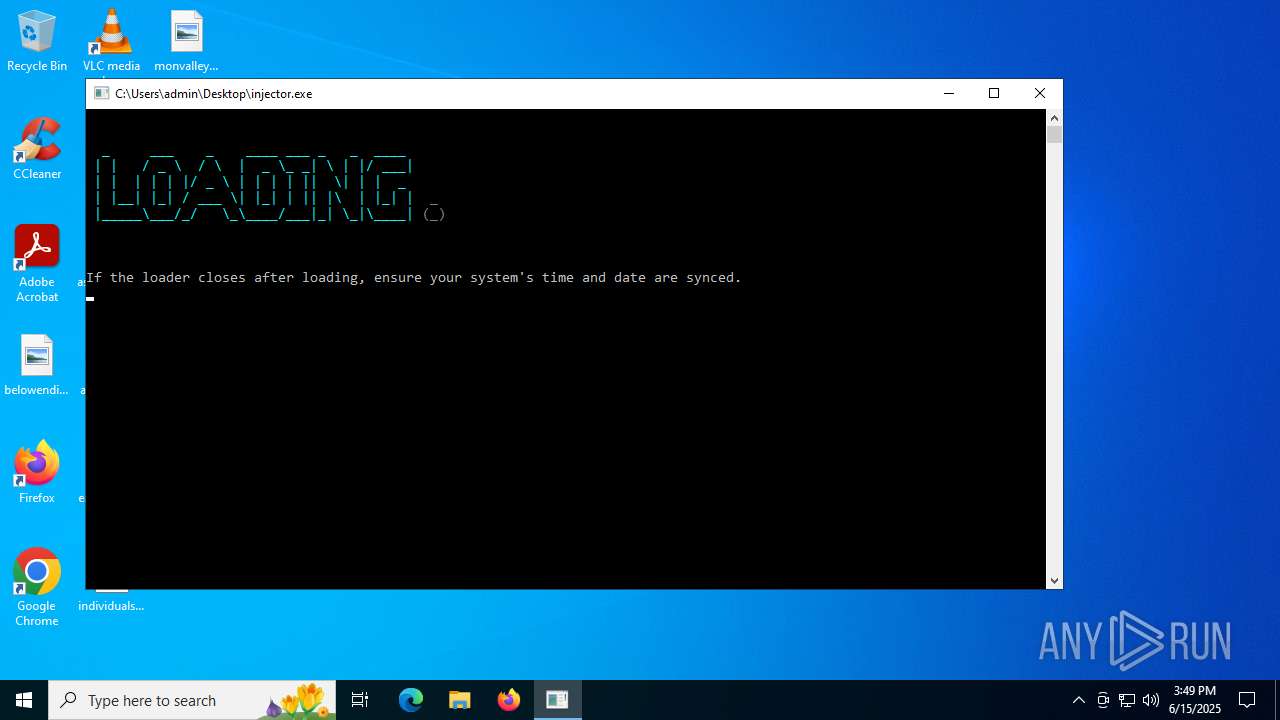
| Analysis date: | June 15, 2025, 15:49:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 8 sections |
| MD5: | 0E74F2FB53A7654D0562701283A4CBC2 |
| SHA1: | 0447A08818F1D8C2899789049577E3174754C91A |
| SHA256: | F28707DDFCC349795D2EA8D2813090B487B778205F7C2C67E3A98FD757546108 |
| SSDEEP: | 98304:IOvPzicW18BkZaBfysOf3RhB1K5Tm/JpBQm03Y4j0SPhSSFiytHIgmoao1n8MFEt:xcvTlz |
MALICIOUS
Uses TASKKILL.EXE to kill security tools
- cmd.exe (PID: 2220)
- cmd.exe (PID: 416)
- cmd.exe (PID: 6216)
- cmd.exe (PID: 1752)
XORed URL has been found (YARA)
- loader.exe (PID: 1508)
- injector.exe (PID: 3864)
SUSPICIOUS
Execution of CURL command
- injector.exe (PID: 3864)
Executable content was dropped or overwritten
- curl.exe (PID: 2464)
Starts CMD.EXE for commands execution
- injector.exe (PID: 3864)
- loader.exe (PID: 1508)
The executable file from the user directory is run by the CMD process
- loader.exe (PID: 1508)
Hides command output
- cmd.exe (PID: 6380)
- cmd.exe (PID: 2220)
- cmd.exe (PID: 416)
- cmd.exe (PID: 3836)
- cmd.exe (PID: 3580)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 4216)
- cmd.exe (PID: 6216)
- cmd.exe (PID: 4120)
- cmd.exe (PID: 1752)
- cmd.exe (PID: 2296)
- cmd.exe (PID: 1800)
- cmd.exe (PID: 6900)
- cmd.exe (PID: 4576)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6380)
- cmd.exe (PID: 4120)
Starts SC.EXE for service management
- cmd.exe (PID: 3836)
- cmd.exe (PID: 2296)
Stops a currently running service
- sc.exe (PID: 1180)
- sc.exe (PID: 1700)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 6656)
- cmd.exe (PID: 4216)
- cmd.exe (PID: 3580)
- cmd.exe (PID: 6900)
- cmd.exe (PID: 4576)
- cmd.exe (PID: 1800)
Reads security settings of Internet Explorer
- loader.exe (PID: 1508)
INFO
Checks supported languages
- injector.exe (PID: 3864)
- curl.exe (PID: 2464)
- loader.exe (PID: 1508)
Execution of CURL command
- cmd.exe (PID: 7052)
Reads the computer name
- curl.exe (PID: 2464)
- loader.exe (PID: 1508)
Create files in a temporary directory
- injector.exe (PID: 3864)
- curl.exe (PID: 2464)
Checks proxy server information
- loader.exe (PID: 1508)
VMProtect protector has been detected
- injector.exe (PID: 3864)
- loader.exe (PID: 1508)
Creates files or folders in the user directory
- loader.exe (PID: 1508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:24 16:12:14+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 62976 |
| InitializedDataSize: | 31232 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6f704c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
179
Monitored processes
42
Malicious processes
3
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 416 | C:\WINDOWS\system32\cmd.exe /c taskkill /f /im HTTPDebuggerSvc.exe >nul 2>&1 | C:\Windows\System32\cmd.exe | — | loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | taskkill /FI "IMAGENAME eq cheatengine*" /IM * /F /T | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | sc stop HTTPDebuggerPro | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | reg delete HKLM\System\CurrentControlSet\Services\NPF /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1508 | C:\Users\admin\AppData\Local\Temp\\loader.exe | C:\Users\admin\AppData\Local\Temp\loader.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1652 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | injector.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1688 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | injector.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1700 | sc stop HTTPDebuggerPro | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | C:\WINDOWS\system32\cmd.exe /c taskkill /f /im HTTPDebuggerSvc.exe >nul 2>&1 | C:\Windows\System32\cmd.exe | — | loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1800 | C:\WINDOWS\system32\cmd.exe /c taskkill /FI "IMAGENAME eq processhacker*" /IM * /F /T >nul 2>&1 | C:\Windows\System32\cmd.exe | — | loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 163
Read events
2 160
Write events
3
Delete events
0
Modification events
| (PID) Process: | (1508) loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1508) loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1508) loader.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2464 | curl.exe | C:\Users\admin\AppData\Local\Temp\loader.exe | executable | |
MD5:F12B34356CDFD5B1164ED7C7EF210E2A | SHA256:A2973FA7592CA856417FC7BB60FDE7959A36B663B91AD02580071F3D447B1464 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
40
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2520 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1508 | loader.exe | GET | 200 | 142.250.186.100:80 | http://www.google.com/ | unknown | — | — | whitelisted |
2620 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2620 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1488 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2464 | curl.exe | 75.2.43.161:443 | maticsky.net | AMAZON-02 | US | unknown |
2336 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2520 | svchost.exe | 40.126.31.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2520 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1508 | loader.exe | 142.250.186.100:80 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
maticsky.net |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
Process | Message |
|---|---|
loader.exe | ReFo Security |
loader.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
loader.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
loader.exe | ReFo Security |
loader.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
loader.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
loader.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
loader.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
loader.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
loader.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |