| File name: | ipmsgupd64.exe |
| Full analysis: | https://app.any.run/tasks/68718284-c135-475a-9a21-ed0d7e703ffc |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2021, 08:12:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7A081B328DCE91FFCE34BE5EEB6BA2F0 |
| SHA1: | 5CF24DCC62007D113119B1823E03170E8EF4334C |
| SHA256: | F284EDB5E1CE709E7CDBAE0AB4671722B9182AE24CC2CC044A2851D1726216E8 |
| SSDEEP: | 98304:/KuIXU8nwoRqj3Z1jjw1B7k/F4nV/EynijO71J9jzTb4m:VoLnwKAbg1B7kN4nqkijiNzb4m |
MALICIOUS
Writes to a start menu file
- ipmsgupd64.exe (PID: 1824)
Application was dropped or rewritten from another process
- IPMsg.exe (PID: 1176)
- IPMsg.exe (PID: 3332)
SUSPICIOUS
Checks supported languages
- ipmsgupd64.exe (PID: 1824)
- IPMsg.exe (PID: 1176)
- IPMsg.exe (PID: 3332)
Reads the computer name
- ipmsgupd64.exe (PID: 1824)
- IPMsg.exe (PID: 1176)
Executable content was dropped or overwritten
- ipmsgupd64.exe (PID: 1824)
Drops a file with a compile date too recent
- ipmsgupd64.exe (PID: 1824)
Reads Microsoft Outlook installation path
- IPMsg.exe (PID: 1176)
Creates a software uninstall entry
- ipmsgupd64.exe (PID: 1824)
Drops a file that was compiled in debug mode
- ipmsgupd64.exe (PID: 1824)
Creates files in the program directory
- IPMsg.exe (PID: 1176)
Creates files in the user directory
- ipmsgupd64.exe (PID: 1824)
Reads internet explorer settings
- IPMsg.exe (PID: 1176)
INFO
Checks Windows Trust Settings
- IPMsg.exe (PID: 1176)
Manual execution by user
- IPMsg.exe (PID: 3332)
Reads settings of System Certificates
- IPMsg.exe (PID: 1176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
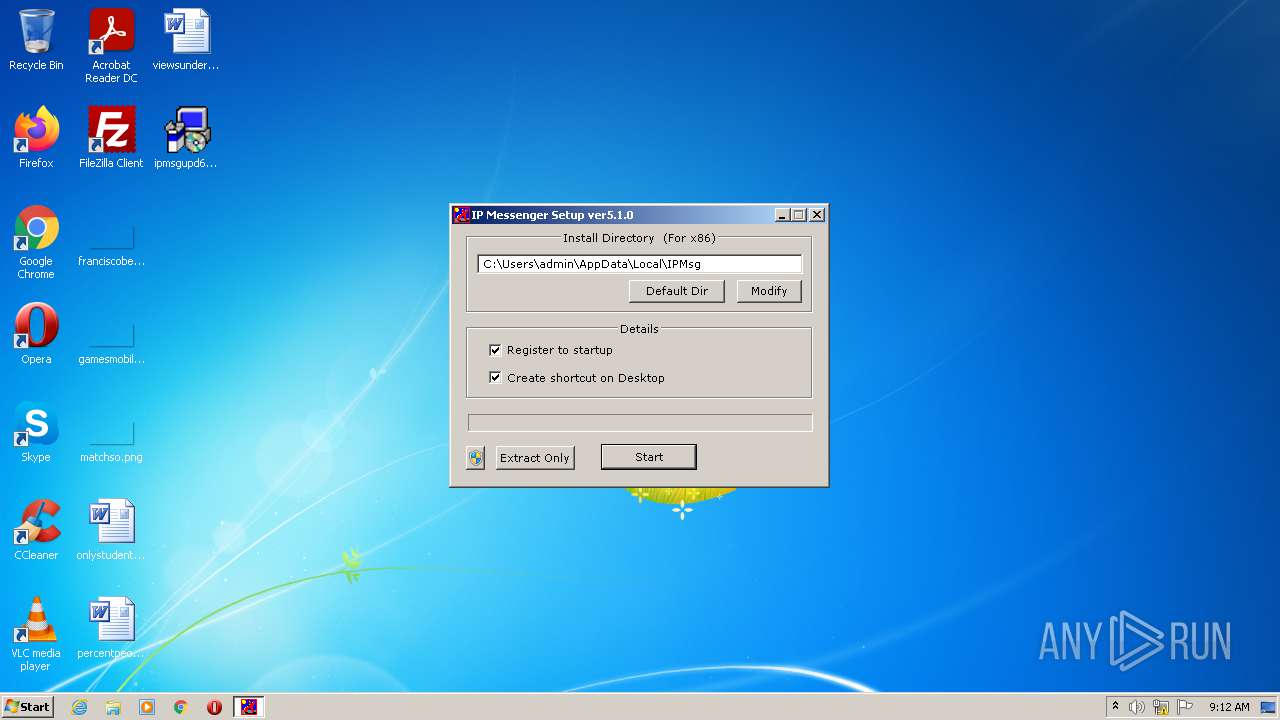
| ProductVersion: | 5.1.0.0 |
|---|---|
| ProductName: | IP Messenger |
| OriginalFileName: | install.exe |
| LegalCopyright: | Copyright(c) 2018-2021 FastCopy Lab, LLC. Copyright (c) 1996-2021 H.Shirouzu, Copyright(c) 2015-2018 Asahi Net, Inc. |
| InternalName: | チョット、いとうさん |
| FileVersion: | 5.1.0.0 |
| FileDescription: | IPMsg Installer |
| CompanyName: | FastCopy Lab, LLC. |
| Comments: | https://ipmsg.org |
| CharacterSet: | Unicode |
| LanguageCode: | Japanese |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 5.1.0.0 |
| FileVersionNumber: | 5.1.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x13318 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 114176 |
| CodeSize: | 155136 |
| LinkerVersion: | 14.16 |
| PEType: | PE32 |
| TimeStamp: | 2021:10:03 17:21:33+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Oct-2021 15:21:33 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | https://ipmsg.org |
| CompanyName: | FastCopy Lab, LLC. |
| FileDescription: | IPMsg Installer |
| FileVersion: | 5.1.0.0 |
| InternalName: | チョット、いとうさん |
| LegalCopyright: | Copyright(c) 2018-2021 FastCopy Lab, LLC. Copyright (c) 1996-2021 H.Shirouzu, Copyright(c) 2015-2018 Asahi Net, Inc. |
| OriginalFilename: | install.exe |
| ProductName: | IP Messenger |
| ProductVersion: | 5.1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 03-Oct-2021 15:21:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00025C2C | 0x00025E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57331 |
.rdata | 0x00027000 | 0x0000E142 | 0x0000E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.82848 |
.data | 0x00036000 | 0x00004E1C | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.77691 |
.rsrc | 0x0003B000 | 0x00008AE8 | 0x00008C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.69176 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.98998 | 1833 | UNKNOWN | Japanese - Japan | RT_MANIFEST |
2 | 5.24535 | 496 | UNKNOWN | Japanese - Japan | RT_STRING |
3 | 4.99144 | 518 | UNKNOWN | Japanese - Japan | RT_STRING |
4 | 3.07113 | 2216 | UNKNOWN | Japanese - Japan | RT_ICON |
5 | 2.30611 | 1736 | UNKNOWN | Japanese - Japan | RT_ICON |
6 | 2.60032 | 296 | UNKNOWN | Japanese - Japan | RT_ICON |
7 | 7.9181 | 7270 | UNKNOWN | Japanese - Japan | RT_ICON |
104 | 1.81924 | 20 | UNKNOWN | Japanese - Japan | RT_GROUP_ICON |
149 | 3.89085 | 744 | UNKNOWN | Japanese - Japan | RT_DIALOG |
150 | 3.64864 | 154 | UNKNOWN | Japanese - Japan | RT_DIALOG |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
USER32.dll (delay-loaded) |
ole32.dll |
Total processes
38
Monitored processes
3
Malicious processes
3
Suspicious processes
0
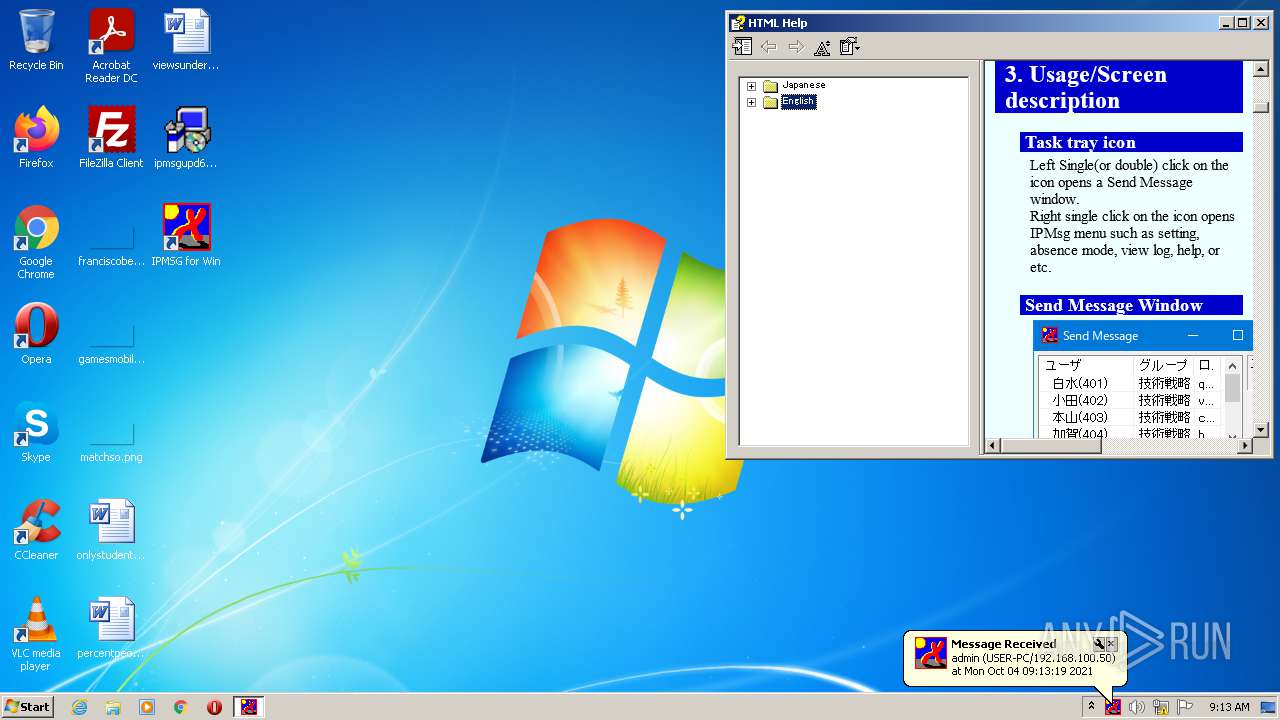
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
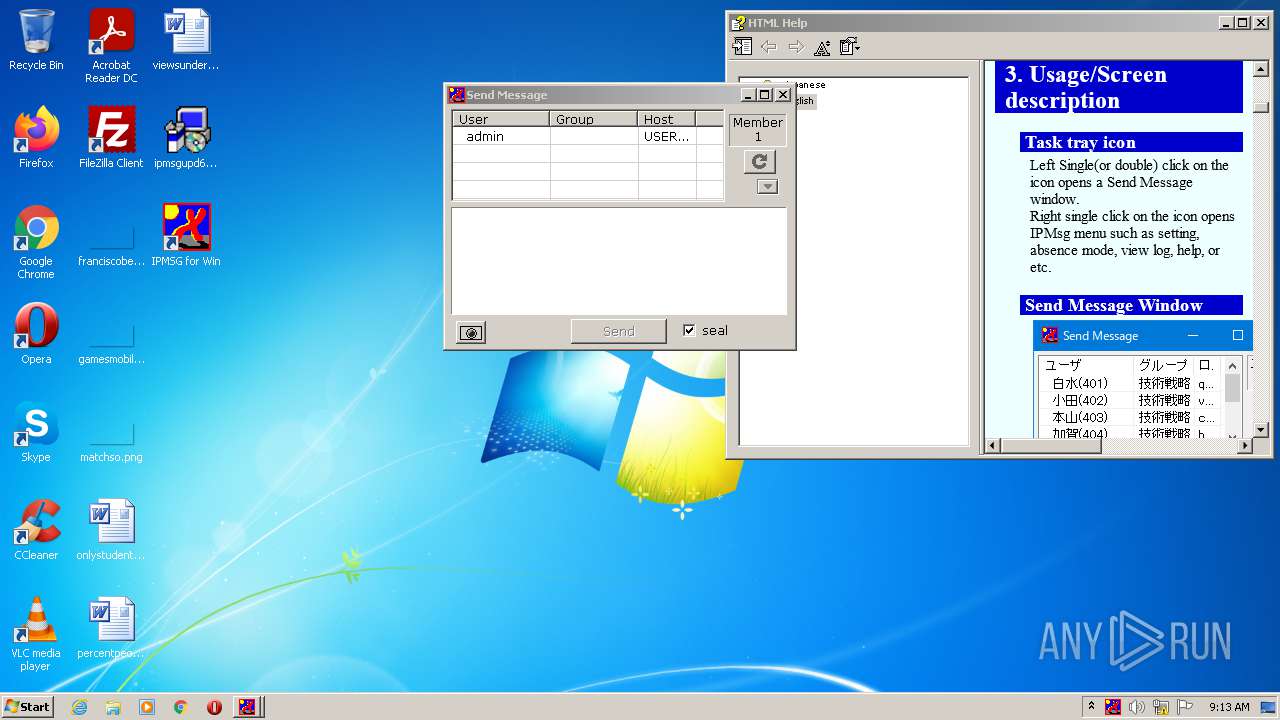
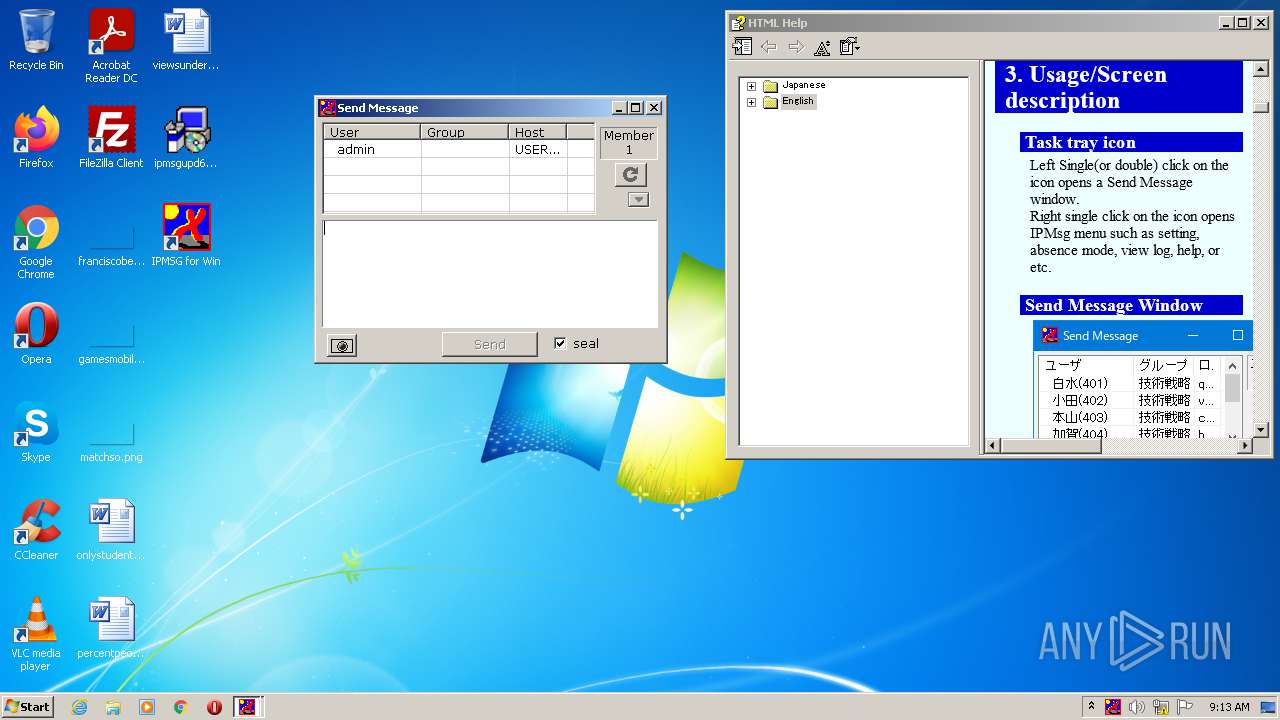
| 1176 | "C:\Users\admin\AppData\Local\IPMsg\IPMsg.exe" /FIRST_RUN | C:\Users\admin\AppData\Local\IPMsg\IPMsg.exe | ipmsgupd64.exe | ||||||||||||
User: admin Company: FastCopy Lab, LLC. Integrity Level: MEDIUM Description: IP Messenger Exit code: 0 Version: 5.1.0.0 Modules
| |||||||||||||||
| 1824 | "C:\Users\admin\Desktop\ipmsgupd64.exe" | C:\Users\admin\Desktop\ipmsgupd64.exe | Explorer.EXE | ||||||||||||
User: admin Company: FastCopy Lab, LLC. Integrity Level: MEDIUM Description: IPMsg Installer Exit code: 0 Version: 5.1.0.0 Modules
| |||||||||||||||
| 3332 | "C:\Users\admin\AppData\Local\IPMsg\IPMsg.exe" | C:\Users\admin\AppData\Local\IPMsg\IPMsg.exe | Explorer.EXE | ||||||||||||
User: admin Company: FastCopy Lab, LLC. Integrity Level: MEDIUM Description: IP Messenger Exit code: 4294967295 Version: 5.1.0.0 Modules
| |||||||||||||||
Total events
6 006
Read events
5 860
Write events
144
Delete events
2
Modification events
| (PID) Process: | (1824) ipmsgupd64.exe | Key: | HKEY_CURRENT_USER\Software\HSTools\IPMsg |
| Operation: | write | Name: | FwCheckMode |
Value: 1 | |||
| (PID) Process: | (1824) ipmsgupd64.exe | Key: | HKEY_CURRENT_USER\Software\HSTools\IPMsg |
| Operation: | write | Name: | FwCheckMode |
Value: 0 | |||
| (PID) Process: | (1824) ipmsgupd64.exe | Key: | HKEY_CURRENT_USER\Software\HSTools\IPMsg |
| Operation: | write | Name: | Path |
Value: C:\Users\admin\AppData\Local\IPMsg | |||
| (PID) Process: | (1824) ipmsgupd64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\IPMSG for Win |
| Operation: | write | Name: | DisplayName |
Value: IP Messenger for Win | |||
| (PID) Process: | (1824) ipmsgupd64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\IPMSG for Win |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\IPMsg\IPMsg.exe | |||
| (PID) Process: | (1824) ipmsgupd64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\IPMSG for Win |
| Operation: | write | Name: | UninstallString |
Value: C:\Users\admin\AppData\Local\IPMsg\uninst.exe | |||
| (PID) Process: | (1824) ipmsgupd64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\IPMSG for Win |
| Operation: | write | Name: | DisplayVersion |
Value: 5.1.0 | |||
| (PID) Process: | (1824) ipmsgupd64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\IPMSG for Win |
| Operation: | write | Name: | Publisher |
Value: H.Shirouzu & FastCopy Lab, LLC. | |||
| (PID) Process: | (1824) ipmsgupd64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\IPMSG for Win |
| Operation: | write | Name: | EstimatedSize |
Value: 3300 | |||
| (PID) Process: | (1824) ipmsgupd64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\IPMSG for Win |
| Operation: | write | Name: | HelpLink |
Value: https://ipmsg.org/help/ipmsghlp_eng.htm | |||
Executable files
4
Suspicious files
11
Text files
13
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1824 | ipmsgupd64.exe | C:\Users\admin\AppData\Local\IPMsg\uninst.exe | executable | |
MD5:— | SHA256:— | |||
| 1824 | ipmsgupd64.exe | C:\Users\admin\Desktop\IPMSG for Win.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1824 | ipmsgupd64.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\IPMSG for Win.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1824 | ipmsgupd64.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\IP Messenger for Win\Uninstall IPMSG.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1824 | ipmsgupd64.exe | C:\Users\admin\AppData\Local\IPMsg\ipcmd.exe | executable | |
MD5:— | SHA256:— | |||
| 1824 | ipmsgupd64.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\IP Messenger for Win\IPMSG for Win.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1176 | IPMsg.exe | C:\Users\admin\Documents\IPMsg\ipmsg.db-journal | binary | |
MD5:— | SHA256:— | |||
| 1824 | ipmsgupd64.exe | C:\Users\admin\AppData\Local\IPMsg\iptoast.dll | executable | |
MD5:— | SHA256:— | |||
| 1824 | ipmsgupd64.exe | C:\Users\admin\AppData\Local\IPMsg\ipmsg.chm | chm | |
MD5:— | SHA256:— | |||
| 1824 | ipmsgupd64.exe | C:\Users\admin\AppData\Local\IPMsg\ipexc.png | image | |
MD5:C5DC2D1557DBE989087BE3AB47B0AF16 | SHA256:43B56B89186FBD557B874047C580142B086BAE345CB2C0A5FC7FCE4EA2397EA4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1092 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?be438950e1a995e6 | US | — | — | whitelisted |
1176 | IPMsg.exe | GET | 200 | 2.16.186.8:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgONI56OsoEhqtGEZ9wOh7gzQg%3D%3D | unknown | der | 503 b | shared |
1176 | IPMsg.exe | GET | 200 | 104.117.200.9:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
1176 | IPMsg.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?3b74400885a4bb4f | US | compressed | 59.7 Kb | whitelisted |
1176 | IPMsg.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ed8e49bce21fb858 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1176 | IPMsg.exe | 160.16.61.55:443 | ipmsg.org | SAKURA Internet Inc. | JP | unknown |
1176 | IPMsg.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1176 | IPMsg.exe | 104.117.200.9:80 | x1.c.lencr.org | TPG Telecom Limited | US | unknown |
1176 | IPMsg.exe | 2.16.186.8:80 | r3.o.lencr.org | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ipmsg.org |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
Threats
Process | Message |
|---|---|
IPMsg.exe | 0000.01: [ 1c4]: ReplacePassArg1 /FIRST_RUN
|
IPMsg.exe | 0000.03: [ 1c4]: mscver=1916 191627045
|
IPMsg.exe | 0000.07: [ 1c4]: addr4(uni)=192.168.100.50/24 flg=1
|
IPMsg.exe | 0000.07: [ 1c4]: addr4(gw)=192.168.100.2/0
|
IPMsg.exe | 0000.07: [ 1c4]: addr4(br)=192.168.100.255/24
|
IPMsg.exe | 0000.07: [ 1c4]: Self IPv4 Addr is 192.168.100.50
|
IPMsg.exe | 0000.07: [ 1c4]: type=1 len=4 192.168.100.255/mask=24
|
IPMsg.exe | 0000.07: [ 1c4]: brlist=192.168.100.255
|
IPMsg.exe | 0002.25: [ 1c4]: sendto: addr=192.168.100.255 size=133
|
IPMsg.exe | 0002.25: [ 1c4]: GUID_MONITOR_POWER_ON=1
|