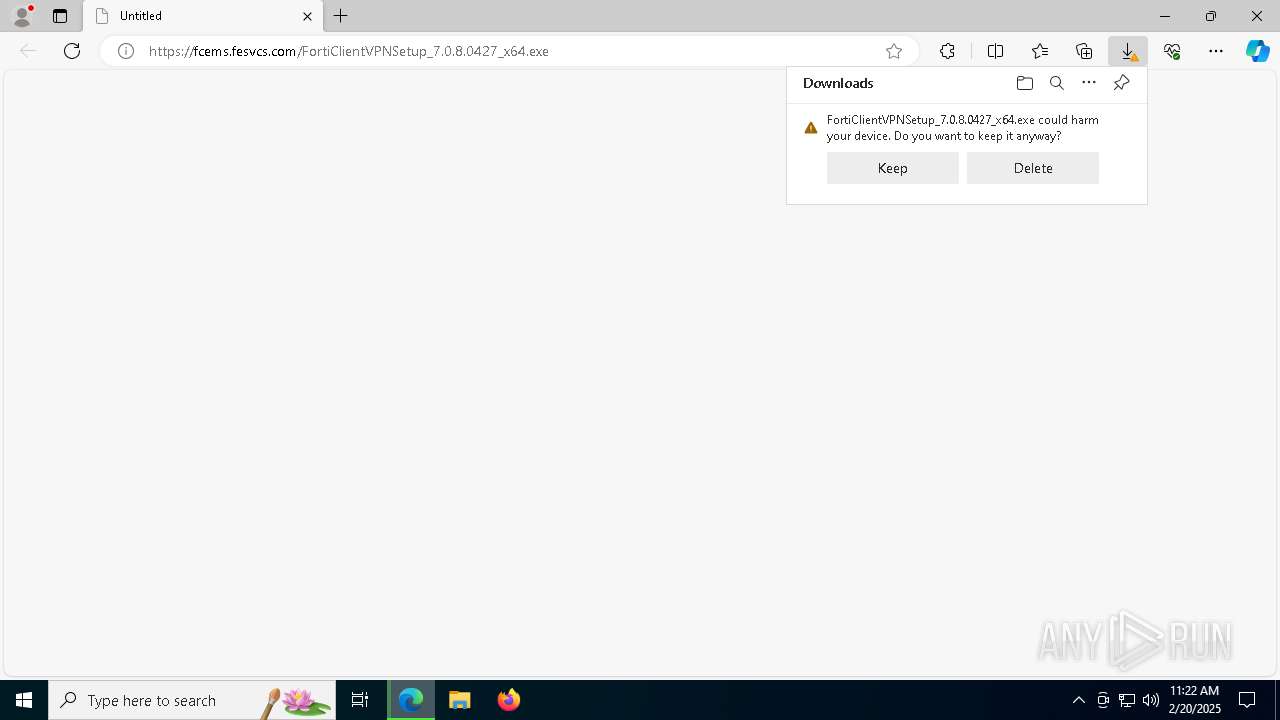
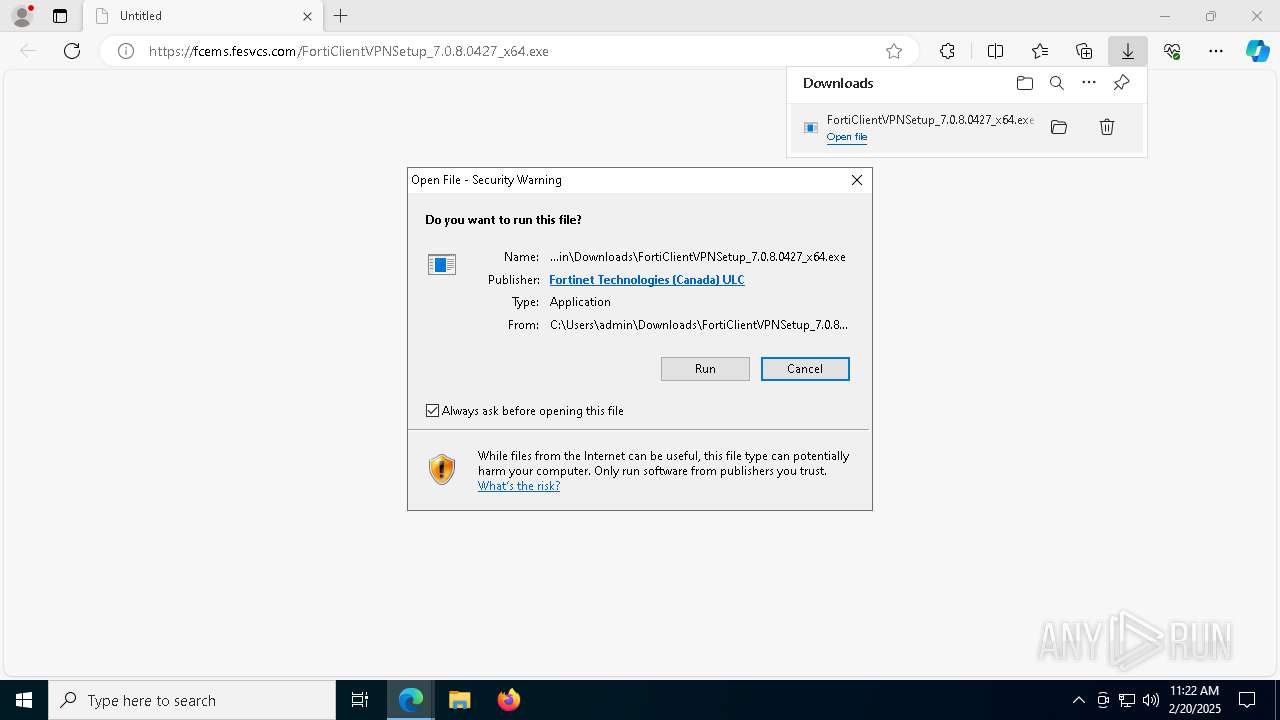
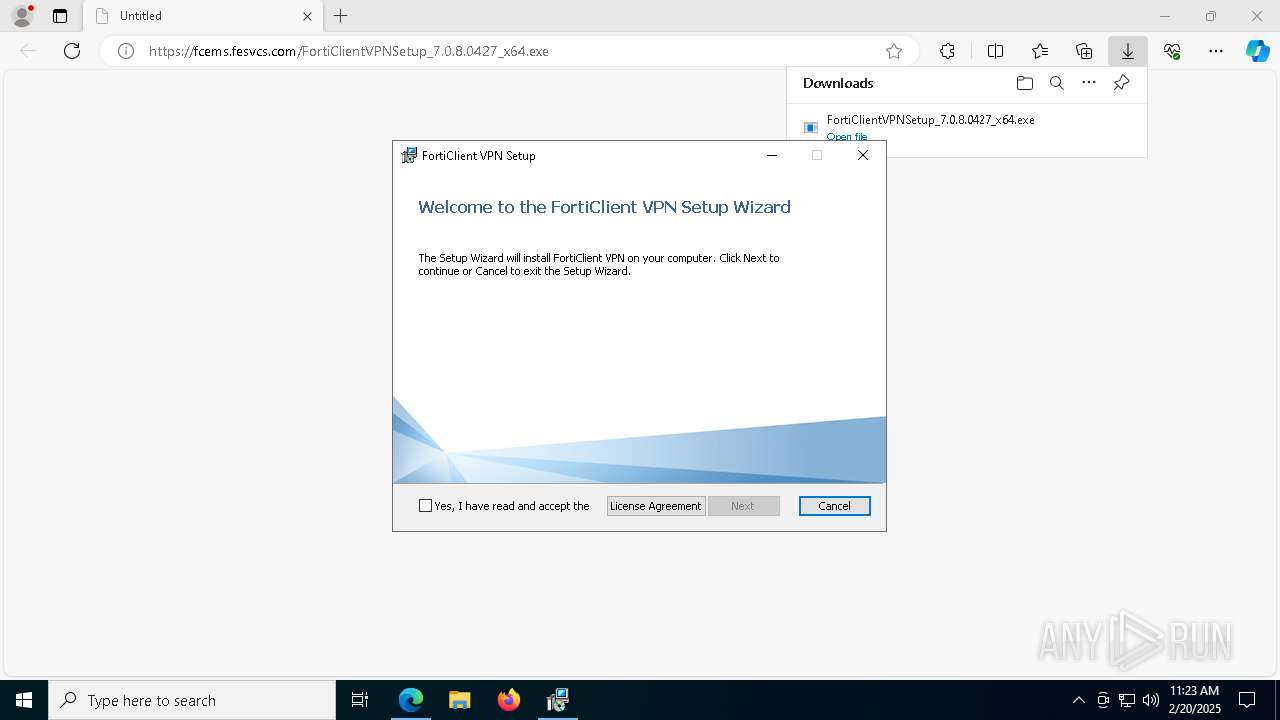
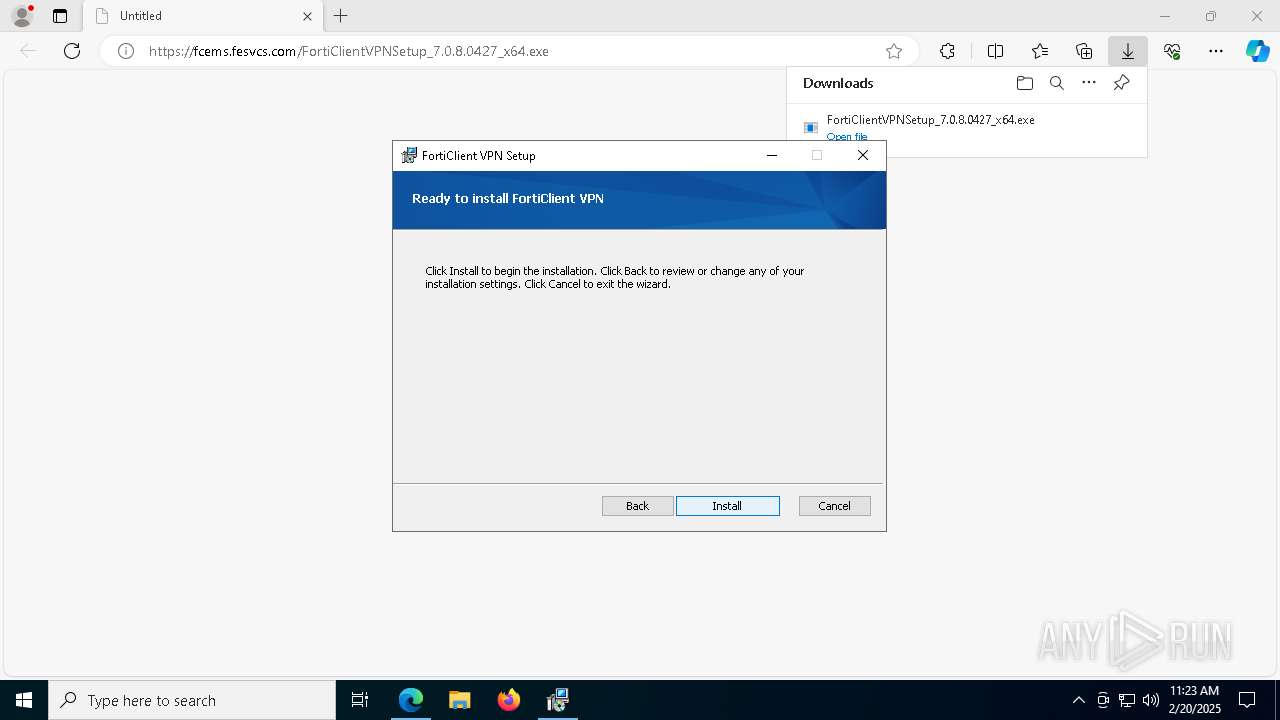
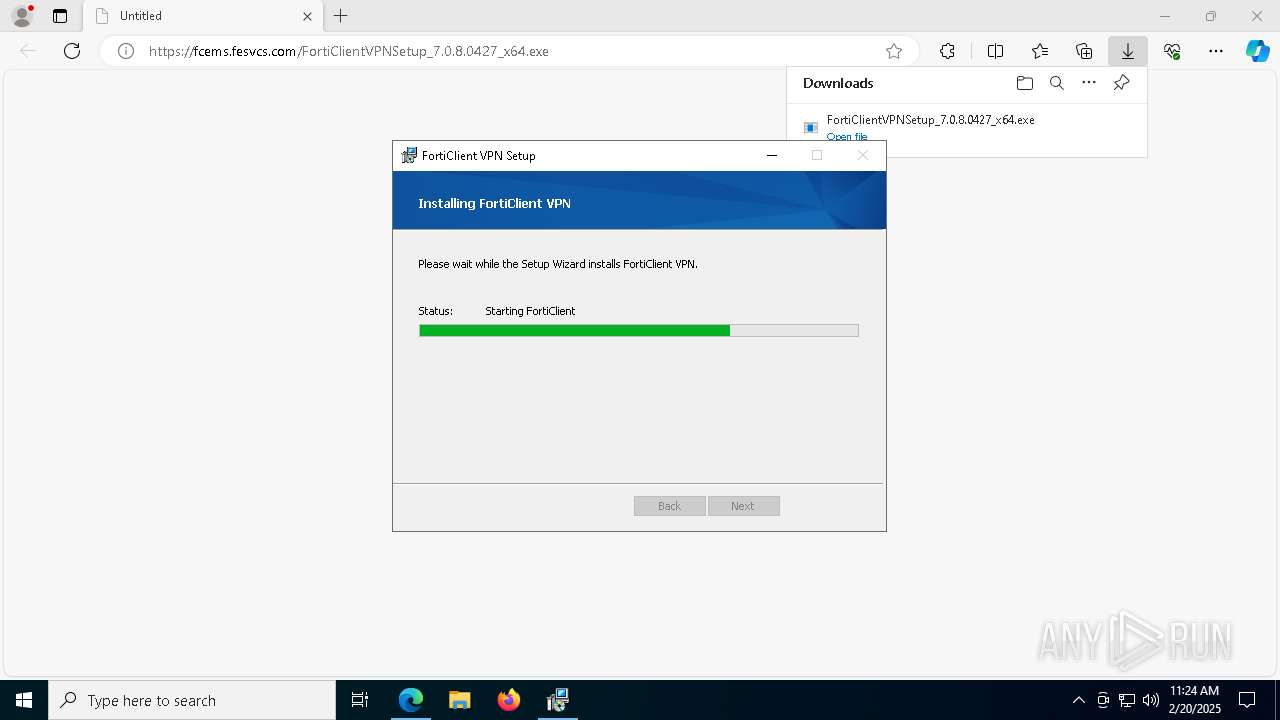
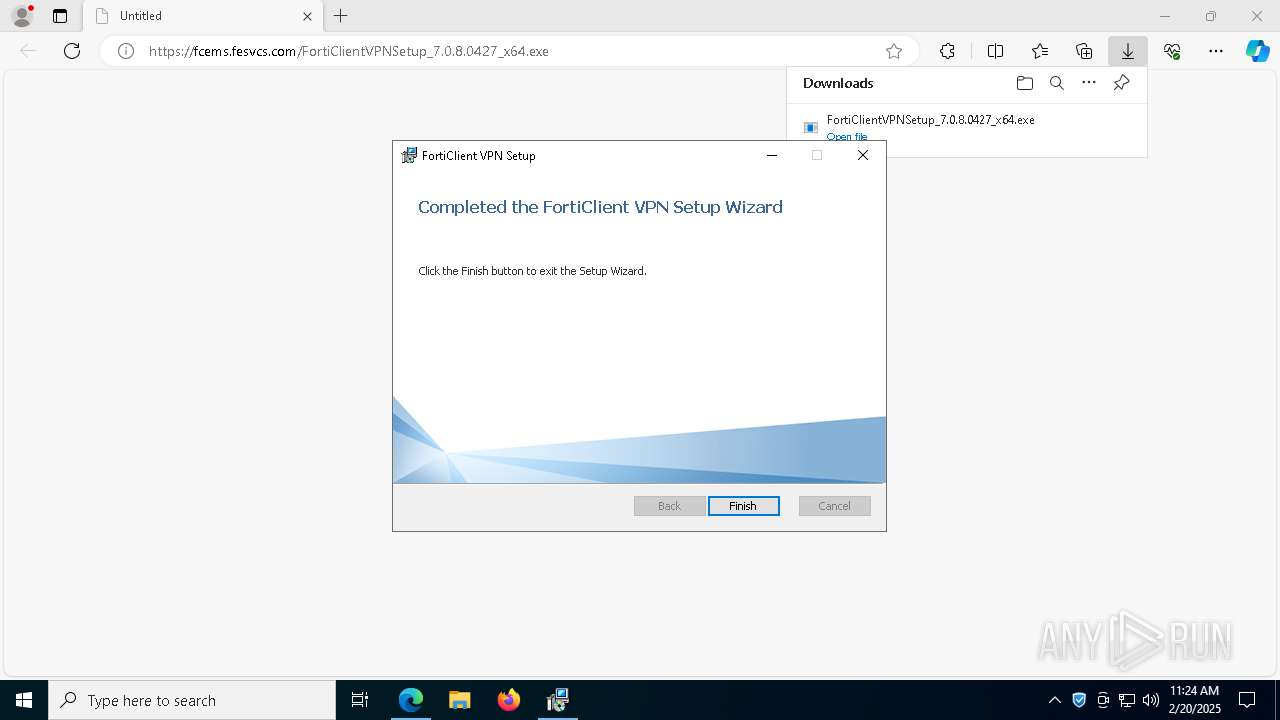
| URL: | https://fcems.fesvcs.com/FortiClientVPNSetup_7.0.8.0427_x64.exe |
| Full analysis: | https://app.any.run/tasks/fb49fff9-567b-452f-936e-d836fe8716b2 |
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2025, 11:22:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 723FA8472416D29F037335B7DEDD433A |
| SHA1: | AF817B640C266BC05A0517CB38417F786C048054 |
| SHA256: | F2818A4CAF84F757316517752889C96B11824C1D5BCFA11C2151DFF61FBA0C9B |
| SSDEEP: | 3:N85I7qIHdphyVVPU2T:25I+IHdpha22T |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- scheduler.exe (PID: 1864)
Starts NET.EXE for service management
- FortiSSLVPNdaemon.exe (PID: 7736)
- net.exe (PID: 7192)
SUSPICIOUS
Reads security settings of Internet Explorer
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 8164)
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 7260)
- scheduler.exe (PID: 1864)
- update_task.exe (PID: 2728)
- FortiTray.exe (PID: 6824)
Application launched itself
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 8164)
- FortiClient.exe (PID: 6444)
Checks Windows Trust Settings
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 7260)
- msiexec.exe (PID: 4388)
- drvinst.exe (PID: 1216)
- drvinst.exe (PID: 7380)
- drvinst.exe (PID: 7620)
- msiexec.exe (PID: 3996)
- FortiTray.exe (PID: 6824)
Reads the Windows owner or organization settings
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 7260)
- msiexec.exe (PID: 4388)
Executable content was dropped or overwritten
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 7260)
- drvinst.exe (PID: 1216)
- drvinst.exe (PID: 1328)
- drvinst.exe (PID: 7380)
- drvinst.exe (PID: 1304)
- drvinst.exe (PID: 7620)
- update_task.exe (PID: 2728)
Executes as Windows Service
- VSSVC.exe (PID: 1344)
- scheduler.exe (PID: 1864)
The process drops C-runtime libraries
- msiexec.exe (PID: 4388)
Process drops legitimate windows executable
- msiexec.exe (PID: 4388)
- update_task.exe (PID: 2728)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 4388)
- drvinst.exe (PID: 1216)
- drvinst.exe (PID: 7380)
- drvinst.exe (PID: 7620)
Creates or modifies Windows services
- drvinst.exe (PID: 1328)
- drvinst.exe (PID: 1304)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 4388)
- regsvr32.exe (PID: 6844)
- FCDBLog.exe (PID: 424)
Adds/modifies Windows certificates
- msiexec.exe (PID: 3996)
Reads the date of Windows installation
- scheduler.exe (PID: 1864)
Searches for installed software
- update_task.exe (PID: 2728)
Suspicious use of NETSH.EXE
- FortiSSLVPNdaemon.exe (PID: 7736)
Checks for external IP
- FortiSSLVPNdaemon.exe (PID: 7736)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 6312)
- msiexec.exe (PID: 4388)
- msedge.exe (PID: 4320)
Reads the computer name
- identity_helper.exe (PID: 5236)
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 8164)
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 7260)
- msiexec.exe (PID: 4388)
- msiexec.exe (PID: 5964)
- msiexec.exe (PID: 3996)
- msiexec.exe (PID: 5568)
- drvinst.exe (PID: 1216)
- drvinst.exe (PID: 1328)
- drvinst.exe (PID: 7380)
- drvinst.exe (PID: 1304)
- drvinst.exe (PID: 7620)
- scheduler.exe (PID: 1864)
- FCDBLog.exe (PID: 424)
- FCCOMInt.exe (PID: 5452)
- FortiSettings.exe (PID: 7820)
- FortiScand.exe (PID: 4164)
- FortiSSLVPNdaemon.exe (PID: 7736)
- FortiTray.exe (PID: 6824)
- update_task.exe (PID: 2728)
- FortiClient.exe (PID: 6444)
- FortiElevate.exe (PID: 4012)
- FortiClient.exe (PID: 1292)
- FortiClient.exe (PID: 6780)
- FortiClient.exe (PID: 4596)
- FortiClient.exe (PID: 6304)
Reads Environment values
- identity_helper.exe (PID: 5236)
- msiexec.exe (PID: 5568)
- msiexec.exe (PID: 5964)
- scheduler.exe (PID: 1864)
- FortiSSLVPNdaemon.exe (PID: 7736)
- FCDBLog.exe (PID: 424)
- FortiTray.exe (PID: 6824)
- update_task.exe (PID: 2728)
- FortiClient.exe (PID: 6444)
- FortiElevate.exe (PID: 4012)
- FortiClient.exe (PID: 4596)
Checks supported languages
- identity_helper.exe (PID: 5236)
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 7260)
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 8164)
- msiexec.exe (PID: 5568)
- msiexec.exe (PID: 5964)
- msiexec.exe (PID: 4388)
- msiexec.exe (PID: 3996)
- drvinst.exe (PID: 1216)
- drvinst.exe (PID: 1328)
- drvinst.exe (PID: 7380)
- drvinst.exe (PID: 1304)
- drvinst.exe (PID: 7620)
- scheduler.exe (PID: 1864)
- FortiScand.exe (PID: 4164)
- FortiSSLVPNdaemon.exe (PID: 7736)
- FCDBLog.exe (PID: 424)
- FCCOMInt.exe (PID: 5452)
- FortiSettings.exe (PID: 7820)
- FortiTray.exe (PID: 6824)
- update_task.exe (PID: 2728)
- FortiClient.exe (PID: 6444)
- FortiClient.exe (PID: 1292)
- FortiClient.exe (PID: 6780)
- FortiElevate.exe (PID: 4012)
- FortiClient.exe (PID: 4596)
- FortiClient.exe (PID: 6304)
Create files in a temporary directory
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 8164)
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 7260)
Process checks computer location settings
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 8164)
- update_task.exe (PID: 2728)
- FortiClient.exe (PID: 4596)
- FortiClient.exe (PID: 6444)
Creates files in the program directory
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 7260)
Reads the machine GUID from the registry
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 7260)
- msiexec.exe (PID: 4388)
- drvinst.exe (PID: 1216)
- drvinst.exe (PID: 7380)
- drvinst.exe (PID: 7620)
- msiexec.exe (PID: 3996)
- FortiTray.exe (PID: 6824)
Reads the software policy settings
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 7260)
- msiexec.exe (PID: 4388)
- drvinst.exe (PID: 1216)
- drvinst.exe (PID: 7380)
- drvinst.exe (PID: 7620)
- msiexec.exe (PID: 3996)
- FortiTray.exe (PID: 6824)
Application launched itself
- msedge.exe (PID: 6312)
- msiexec.exe (PID: 4388)
Manages system restore points
- SrTasks.exe (PID: 7976)
The sample compiled with english language support
- msiexec.exe (PID: 4388)
- FortiClientVPNSetup_7.0.8.0427_x64.exe (PID: 7260)
- msedge.exe (PID: 4320)
- update_task.exe (PID: 2728)
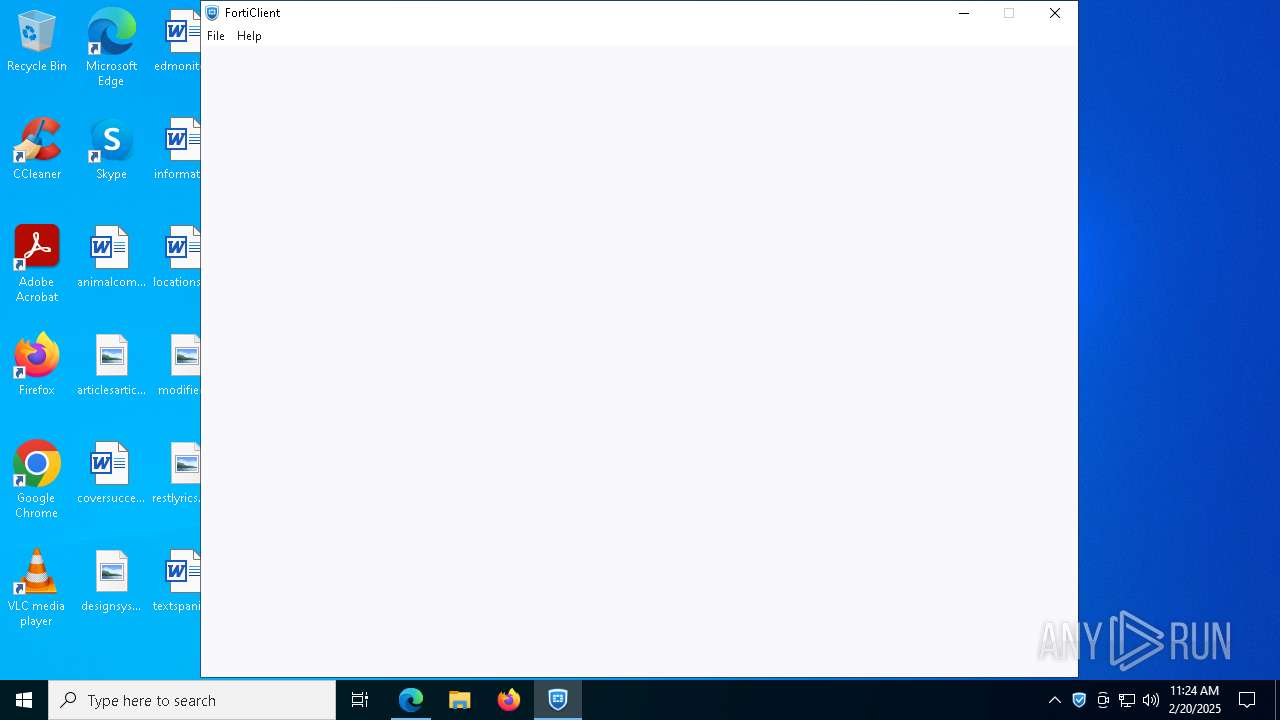
Manual execution by a user
- FortiClient.exe (PID: 6444)
Reads product name
- FortiClient.exe (PID: 6444)
- FortiClient.exe (PID: 4596)
Creates a software uninstall entry
- msiexec.exe (PID: 4388)
Checks proxy server information
- FortiClient.exe (PID: 6444)
- FortiTray.exe (PID: 6824)
Disables trace logs
- netsh.exe (PID: 7608)
- netsh.exe (PID: 5680)
- netsh.exe (PID: 7772)
- netsh.exe (PID: 7880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
233
Monitored processes
92
Malicious processes
4
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 424 | FCDBLog.exe -s FC_{73EFB30F-1CAD-4a7a-AE2E-150282B6CE25}_000011 | C:\Program Files\Fortinet\FortiClient\FCDBLog.exe | — | scheduler.exe | |||||||||||
User: SYSTEM Company: Fortinet Inc. Integrity Level: SYSTEM Description: FortiClient Logging daemon Version: 7.0.8.0427 Modules
| |||||||||||||||
| 624 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6804 --field-trial-handle=2424,i,14372344735055025538,976649728476057088,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 836 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7896 --field-trial-handle=2424,i,14372344735055025538,976649728476057088,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1216 | DrvInst.exe "4" "1" "C:\Program Files\Common Files\Fortinet\FortiClient\ftvnic\ft_vnic.inf" "9" "43d6f8a63" "00000000000001E0" "WinSta0\Default" "00000000000001F0" "208" "C:\Program Files\Common Files\Fortinet\FortiClient\ftvnic" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Fortinet\FortiClient\FortiClient.exe" --type=gpu-process --field-trial-handle=1868,6459429344267377226,9877300804982875465,131072 --enable-features=WebComponentsV0Enabled --disable-features=CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,SpareRendererForSitePerProcess --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1876 /prefetch:2 | C:\Program Files\Fortinet\FortiClient\FortiClient.exe | — | FortiClient.exe | |||||||||||
User: admin Company: Fortinet Inc. Integrity Level: LOW Description: FortiClient Console Version: 7.0.8.427 Modules
| |||||||||||||||
| 1304 | DrvInst.exe "2" "211" "ROOT\NET\0001" "C:\WINDOWS\INF\oem6.inf" "oem6.inf:3205552cbf00c145:ftsvnic.ndi:16.17.14.743:root\ftsvnic," "4219b83e7" "00000000000001FC" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | DrvInst.exe "2" "201" "ROOT\NET\0000" "C:\WINDOWS\INF\oem1.inf" "oem1.inf:3205552c47487a89:FTNT.ndi:2020.4.9.0:root\ftvnic_a," "41304937f" "00000000000000EC" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1344 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1400 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7528 --field-trial-handle=2424,i,14372344735055025538,976649728476057088,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1580 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6440 --field-trial-handle=2424,i,14372344735055025538,976649728476057088,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
54 883
Read events
53 263
Write events
1 555
Delete events
65
Modification events
| (PID) Process: | (6312) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 801E485E278D2F00 | |||
| (PID) Process: | (6312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6312) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CE4B3A5E278D2F00 | |||
| (PID) Process: | (6312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262896 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {641BFF8F-F03A-43F8-94A1-9BED5EDDC198} | |||
| (PID) Process: | (6312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262896 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2BD6B139-16EA-466A-B103-A342E691F0E3} | |||
| (PID) Process: | (6312) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: AA21565E278D2F00 | |||
| (PID) Process: | (6312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
244
Suspicious files
580
Text files
135
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF134b25.TMP | — | |
MD5:— | SHA256:— | |||
| 6312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF134b45.TMP | — | |
MD5:— | SHA256:— | |||
| 6312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF134b54.TMP | — | |
MD5:— | SHA256:— | |||
| 6312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF134b54.TMP | — | |
MD5:— | SHA256:— | |||
| 6312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF134d96.TMP | — | |
MD5:— | SHA256:— | |||
| 6312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF134af7.TMP | binary | |
MD5:DFFC82B8D23613E62A20204028CEF32F | SHA256:114690F0417A9A6B079EA8D0534F095B04467809DCA929EB0983059E1C60FB6C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
98
DNS requests
79
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7412 | svchost.exe | HEAD | 200 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b1659b48-cefd-4ce2-8568-9a30f7dc5746?P1=1740552846&P2=404&P3=2&P4=aK0XKINLnrG4WQZ%2fDC0qG4tpSZJTKseYfQUaYMx%2bkpFR%2fVc8pwXaI2tjaxL4Nohdg9n6BTvBRTM4qgfQGxygXA%3d%3d | unknown | — | — | whitelisted |
6312 | msedge.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAhi3%2F7G6TMr%2BpOy8YeGNkI%3D | unknown | — | — | whitelisted |
7412 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b1659b48-cefd-4ce2-8568-9a30f7dc5746?P1=1740552846&P2=404&P3=2&P4=aK0XKINLnrG4WQZ%2fDC0qG4tpSZJTKseYfQUaYMx%2bkpFR%2fVc8pwXaI2tjaxL4Nohdg9n6BTvBRTM4qgfQGxygXA%3d%3d | unknown | — | — | whitelisted |
7412 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b1659b48-cefd-4ce2-8568-9a30f7dc5746?P1=1740552846&P2=404&P3=2&P4=aK0XKINLnrG4WQZ%2fDC0qG4tpSZJTKseYfQUaYMx%2bkpFR%2fVc8pwXaI2tjaxL4Nohdg9n6BTvBRTM4qgfQGxygXA%3d%3d | unknown | — | — | whitelisted |
7412 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b1659b48-cefd-4ce2-8568-9a30f7dc5746?P1=1740552846&P2=404&P3=2&P4=aK0XKINLnrG4WQZ%2fDC0qG4tpSZJTKseYfQUaYMx%2bkpFR%2fVc8pwXaI2tjaxL4Nohdg9n6BTvBRTM4qgfQGxygXA%3d%3d | unknown | — | — | whitelisted |
7412 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b1659b48-cefd-4ce2-8568-9a30f7dc5746?P1=1740552846&P2=404&P3=2&P4=aK0XKINLnrG4WQZ%2fDC0qG4tpSZJTKseYfQUaYMx%2bkpFR%2fVc8pwXaI2tjaxL4Nohdg9n6BTvBRTM4qgfQGxygXA%3d%3d | unknown | — | — | whitelisted |
7412 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b1659b48-cefd-4ce2-8568-9a30f7dc5746?P1=1740552846&P2=404&P3=2&P4=aK0XKINLnrG4WQZ%2fDC0qG4tpSZJTKseYfQUaYMx%2bkpFR%2fVc8pwXaI2tjaxL4Nohdg9n6BTvBRTM4qgfQGxygXA%3d%3d | unknown | — | — | whitelisted |
2548 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2548 | svchost.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
712 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2548 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 184.86.251.10:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
6312 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6636 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6636 | msedge.exe | 13.107.246.60:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6636 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
fcems.fesvcs.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
7736 | FortiSSLVPNdaemon.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
6824 | FortiTray.exe | Misc activity | ET INFO Observed Google DNS over HTTPS Domain (dns .google in TLS SNI) |
6824 | FortiTray.exe | Misc activity | ET INFO Google DNS Over HTTPS Certificate Inbound |
Process | Message |
|---|---|
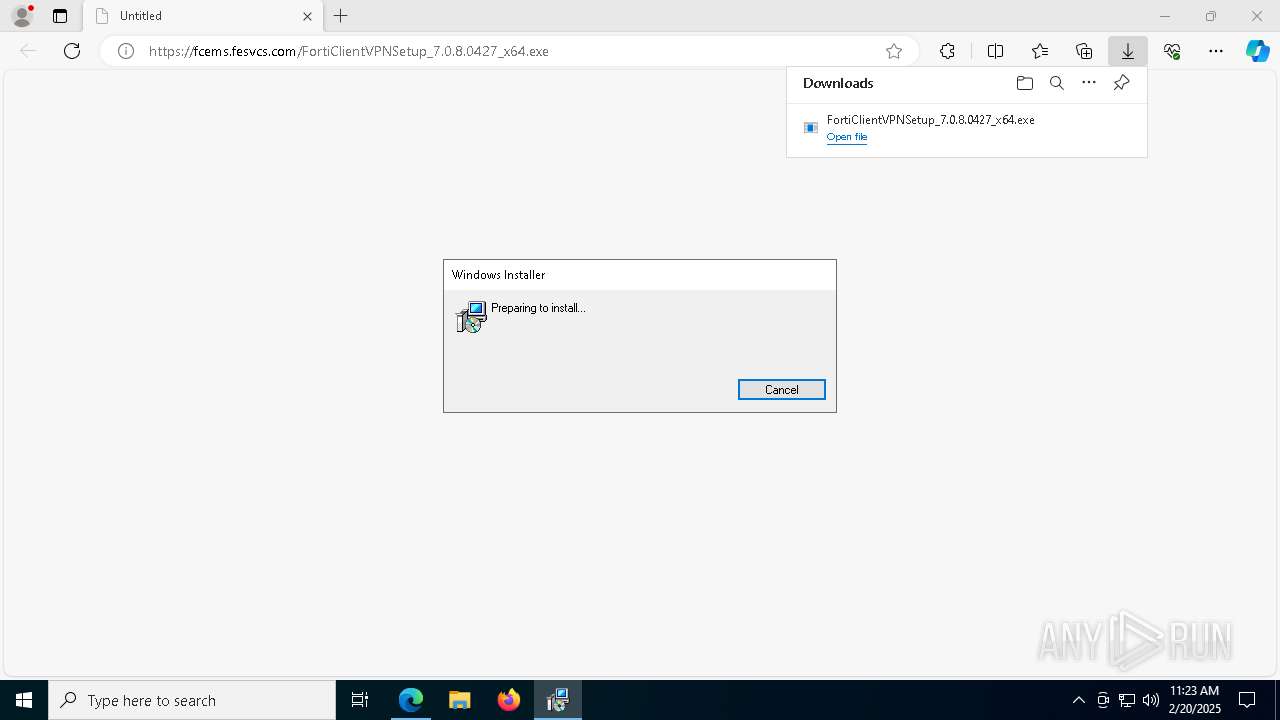
FortiClientVPNSetup_7.0.8.0427_x64.exe | Trace/s: Do Install
|
FortiClientVPNSetup_7.0.8.0427_x64.exe | Trace/s: call ProcessSetupChain
|
FortiClientVPNSetup_7.0.8.0427_x64.exe | Trace/s: Install Config
|
FortiClientVPNSetup_7.0.8.0427_x64.exe | Trace/s: MsiInstallProductW er=0 hr=0
|
FortiSSLVPNdaemon.exe | =============Close per app device ================
|