| File name: | nigga.exe |
| Full analysis: | https://app.any.run/tasks/b35c1525-3e63-4d55-9145-a201601aaaa1 |
| Verdict: | Malicious activity |
| Analysis date: | April 19, 2025, 06:42:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | 762BFA9DECD5B9F39ED459E397D01CB9 |
| SHA1: | D01F0A59E1F967B970CFE8EBB2F5822494BBFC10 |
| SHA256: | F27C556F68DC0FD4DE0D8028FDE345B2BBDB2A081FB3756C7A5BA18834CFAE46 |
| SSDEEP: | 98304:Sxb2xVJoMZqeLnc1ZaDPHUFK/uXbQh2U0ntDx8Kup3Qj8mtkjC+MH0QNdJx69XzX:7gKFg5TyYVNUfunUDy |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- nigga.exe (PID: 7588)
Process drops python dynamic module
- nigga.exe (PID: 7588)
The process drops C-runtime libraries
- nigga.exe (PID: 7588)
Loads Python modules
- nigga.exe (PID: 7652)
Process drops legitimate windows executable
- nigga.exe (PID: 7588)
Application launched itself
- nigga.exe (PID: 7588)
INFO
Reads the computer name
- nigga.exe (PID: 7588)
- nigga.exe (PID: 7652)
Checks supported languages
- nigga.exe (PID: 7588)
- nigga.exe (PID: 7652)
Checks proxy server information
- nigga.exe (PID: 7652)
- slui.exe (PID: 9780)
PyInstaller has been detected (YARA)
- nigga.exe (PID: 7588)
Create files in a temporary directory
- nigga.exe (PID: 7588)
The sample compiled with english language support
- nigga.exe (PID: 7588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:19 06:21:48+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 178688 |
| InitializedDataSize: | 153600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc380 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
124
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7588 | "C:\Users\admin\Desktop\nigga.exe" | C:\Users\admin\Desktop\nigga.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7596 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | nigga.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7652 | "C:\Users\admin\Desktop\nigga.exe" | C:\Users\admin\Desktop\nigga.exe | nigga.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 9780 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
152 753
Read events
152 753
Write events
0
Delete events
0
Modification events
Executable files
22
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7588 | nigga.exe | C:\Users\admin\AppData\Local\Temp\_MEI75882\_ssl.pyd | executable | |
MD5:CE19076F6B62292ED66FD06E5BA67BBA | SHA256:21CA71B2C1766FC68734CB3D1E7C2C0439B86BCFB95E00B367C5FD48C59E617C | |||
| 7588 | nigga.exe | C:\Users\admin\AppData\Local\Temp\_MEI75882\VCRUNTIME140_1.dll | executable | |
MD5:68156F41AE9A04D89BB6625A5CD222D4 | SHA256:82A2F9AE1E6146AE3CB0F4BC5A62B7227E0384209D9B1AEF86BBCC105912F7CD | |||
| 7588 | nigga.exe | C:\Users\admin\AppData\Local\Temp\_MEI75882\certifi\cacert.pem | text | |
MD5:234D271ECB91165AAEC148AD6326DD39 | SHA256:C55B21F907F7F86D48ADD093552FB5651749FF5F860508CCBB423D6C1FBD80C7 | |||
| 7588 | nigga.exe | C:\Users\admin\AppData\Local\Temp\_MEI75882\_wmi.pyd | executable | |
MD5:E3213CF44340D7B4CB65F7231A65E3A4 | SHA256:AB87FE4B0CF5B2B17901905EA86367B9756C44845EB463E77435648F0F719354 | |||
| 7588 | nigga.exe | C:\Users\admin\AppData\Local\Temp\_MEI75882\_queue.pyd | executable | |
MD5:59C05030E47BDE800AD937CCB98802D8 | SHA256:E4956834DF819C1758D17C1C42A152306F7C0EA7B457CA24CE2F6466A6CB1CAA | |||
| 7588 | nigga.exe | C:\Users\admin\AppData\Local\Temp\_MEI75882\charset_normalizer\md.cp313-win_amd64.pyd | executable | |
MD5:480B5EB45AF69A315BD2C3B1B34459D1 | SHA256:1F8A5173D8BFE6C569E81C738B830800307ED4586D2AE9AC5CC13A468C6E1892 | |||
| 7588 | nigga.exe | C:\Users\admin\AppData\Local\Temp\_MEI75882\_lzma.pyd | executable | |
MD5:3E73BC69EFB418E76D38BE5857A77027 | SHA256:6F48E7EBA363CB67F3465A6C91B5872454B44FC30B82710DFA4A4489270CE95C | |||
| 7588 | nigga.exe | C:\Users\admin\AppData\Local\Temp\_MEI75882\_socket.pyd | executable | |
MD5:69C4A9A654CF6D1684B73A431949B333 | SHA256:8DAEFAFF53E6956F5AEA5279A7C71F17D8C63E2B0D54031C3B9E82FCB0FB84DB | |||
| 7588 | nigga.exe | C:\Users\admin\AppData\Local\Temp\_MEI75882\libcrypto-3.dll | executable | |
MD5:123AD0908C76CCBA4789C084F7A6B8D0 | SHA256:4E5D5D20D6D31E72AB341C81E97B89E514326C4C861B48638243BDF0918CFA43 | |||
| 7588 | nigga.exe | C:\Users\admin\AppData\Local\Temp\_MEI75882\charset_normalizer\md__mypyc.cp313-win_amd64.pyd | executable | |
MD5:501B867C424A8E3A41A9BE4AB22DBEED | SHA256:437CEB75E7BC7C72C9090558397EF3598B0BC7BC499434AF5827028083D300CA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
50 088
DNS requests
24
Threats
2 498
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
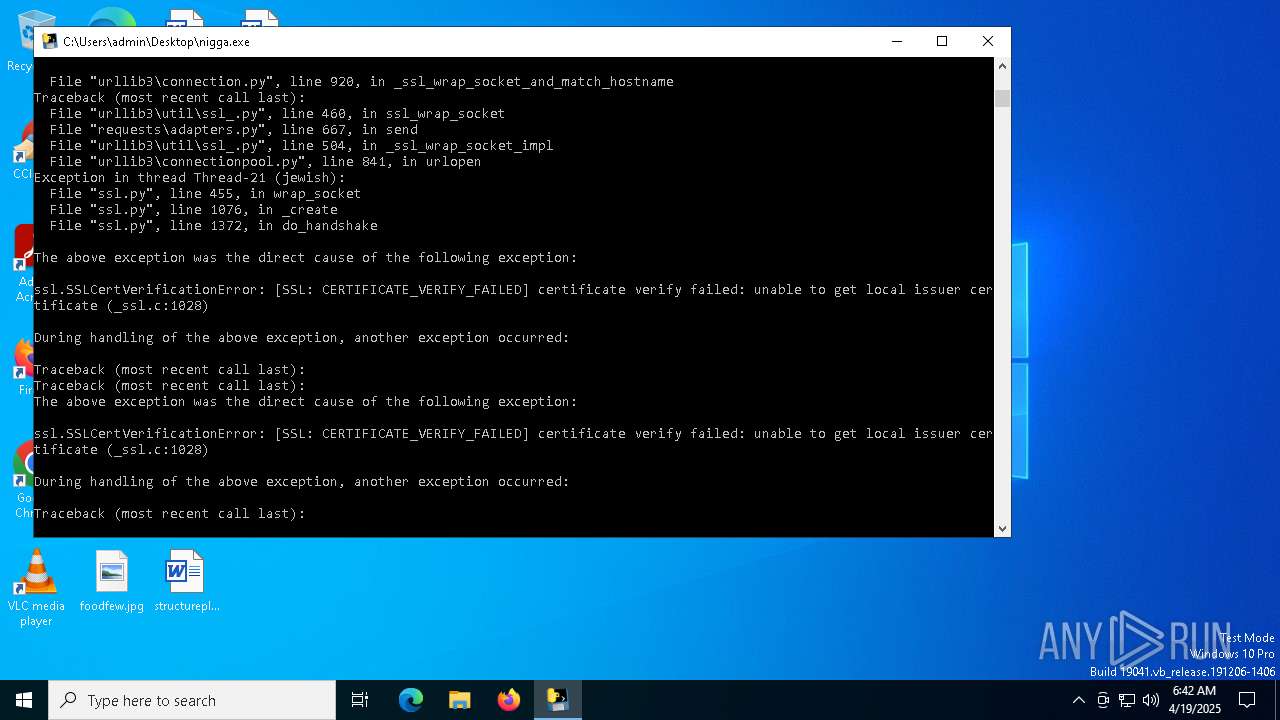
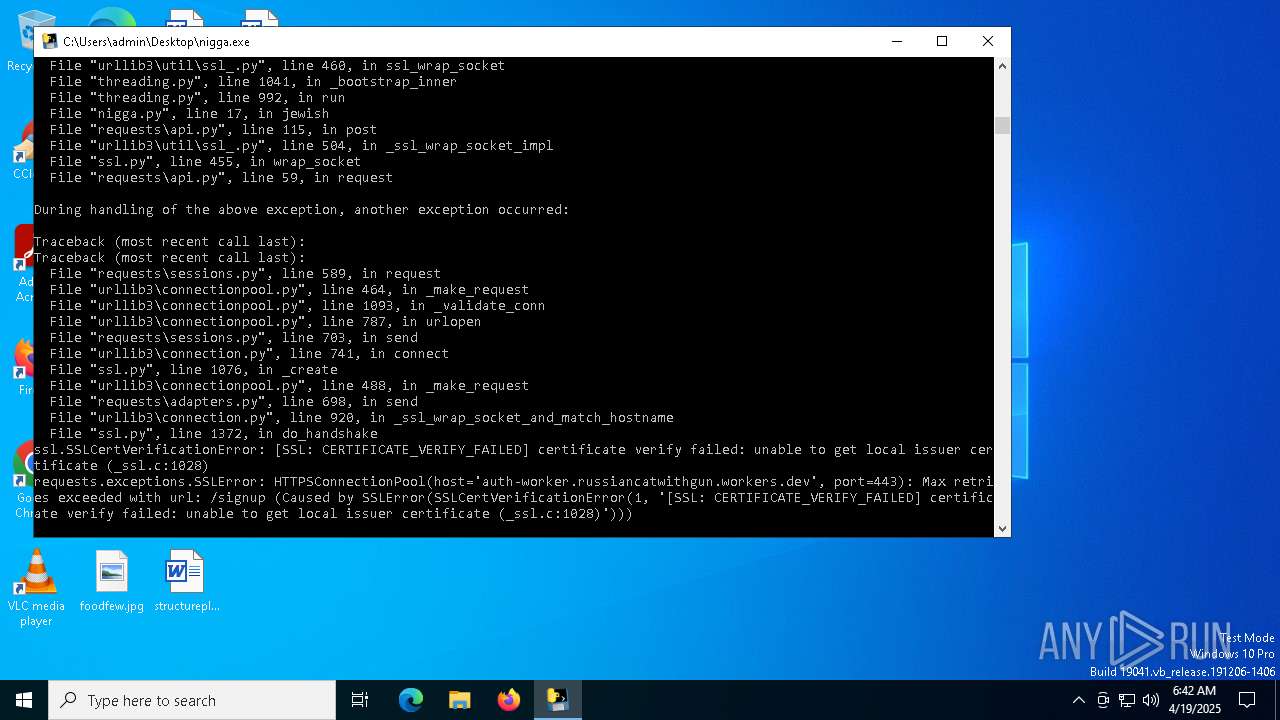
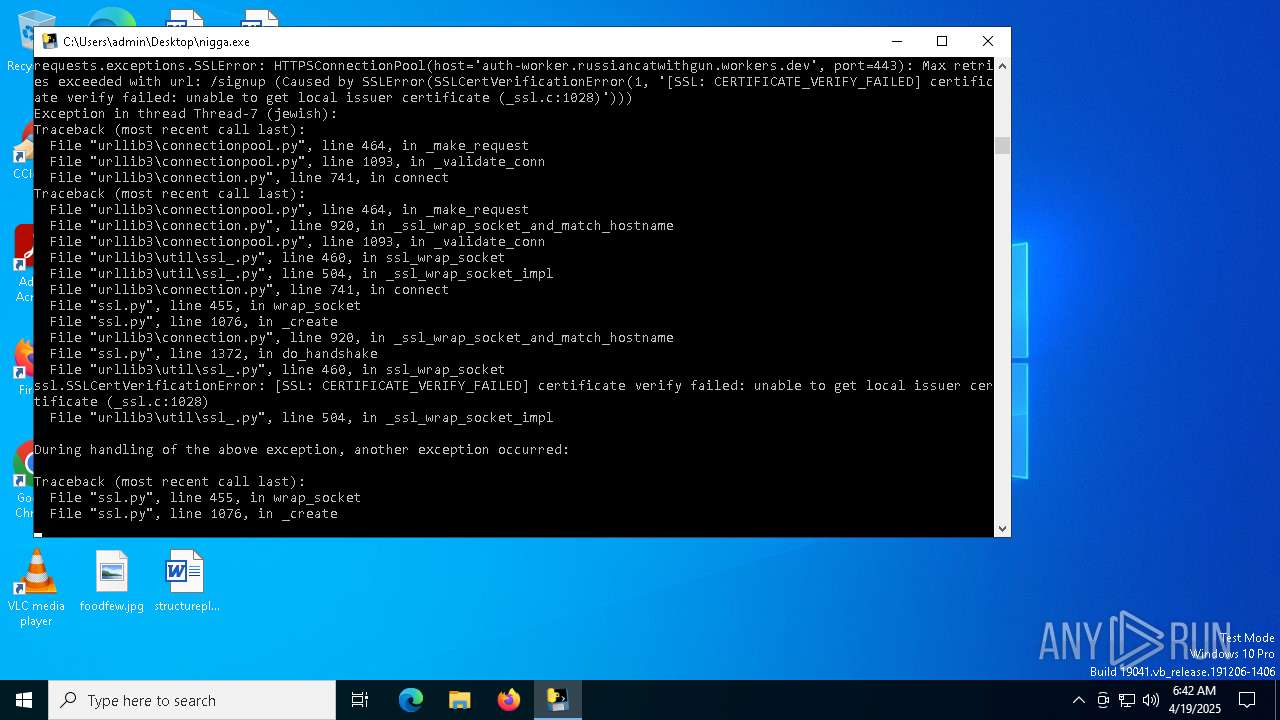
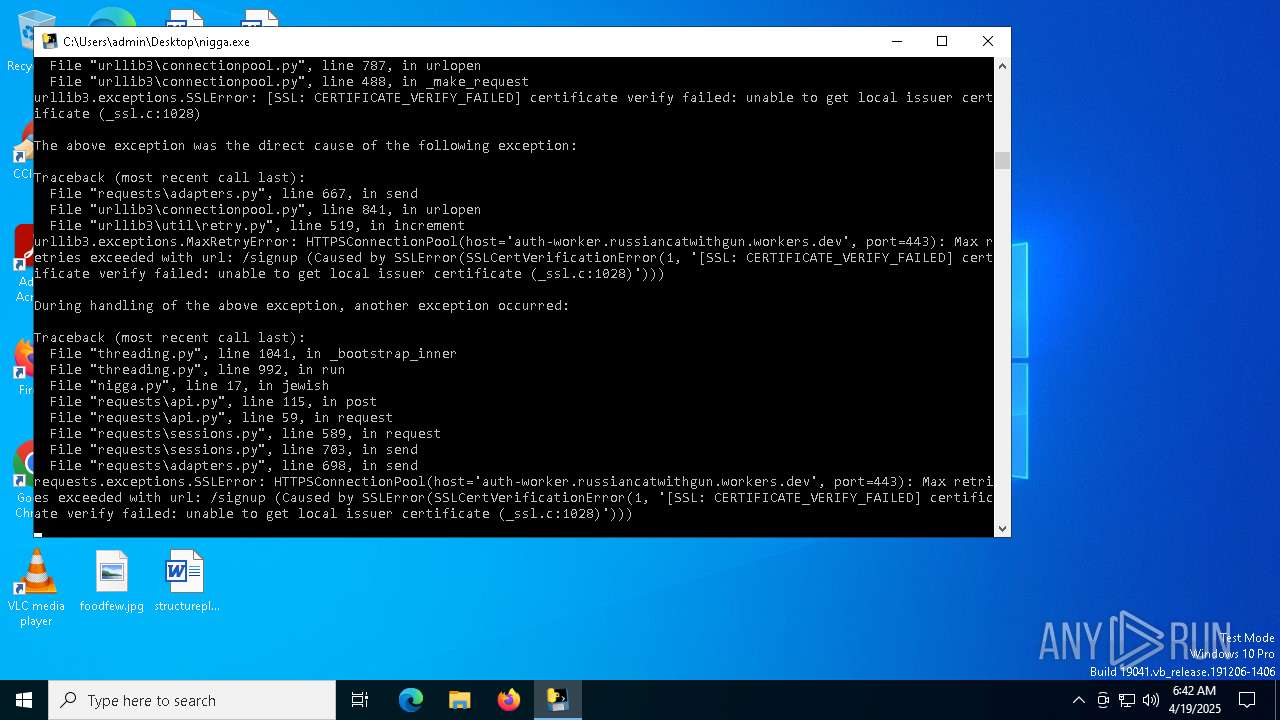
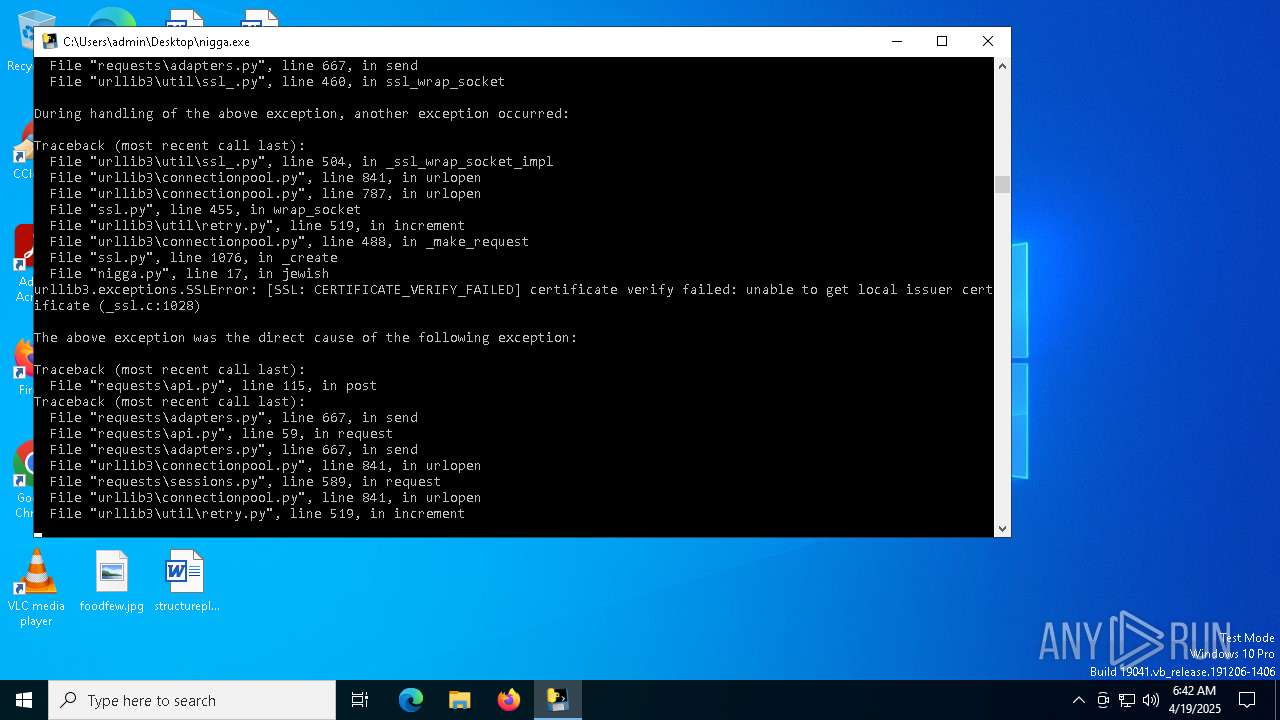
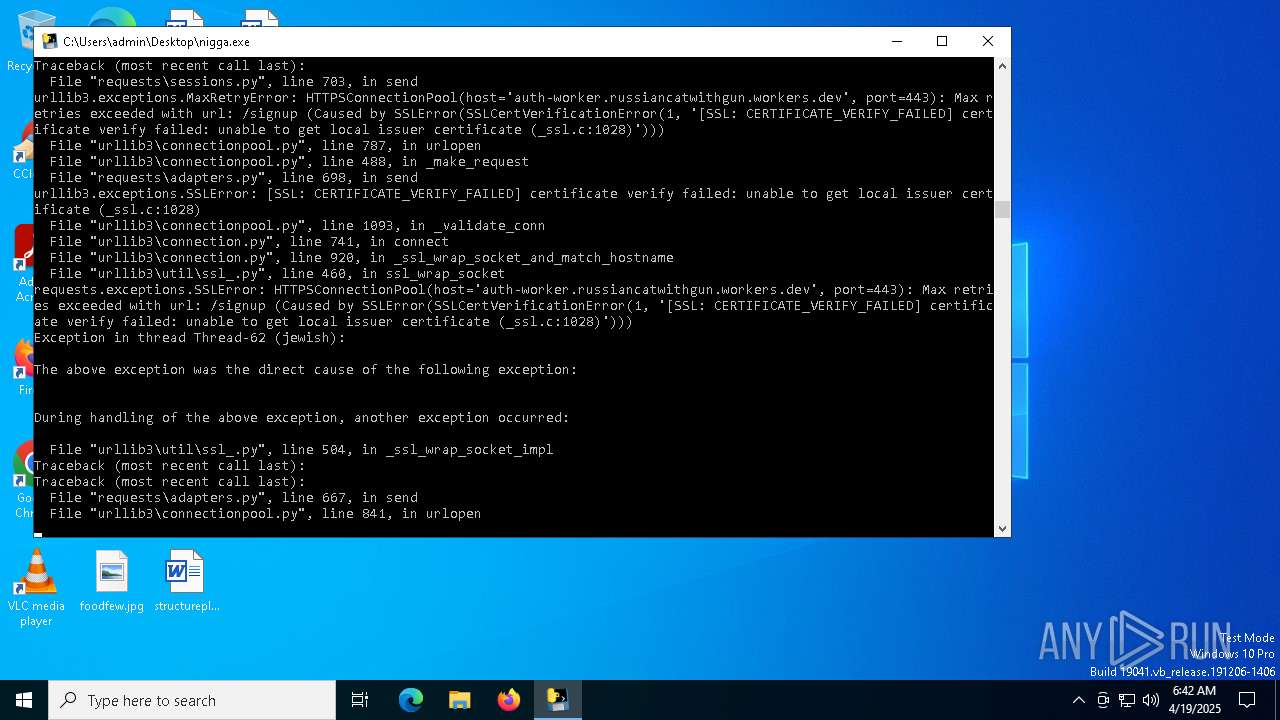
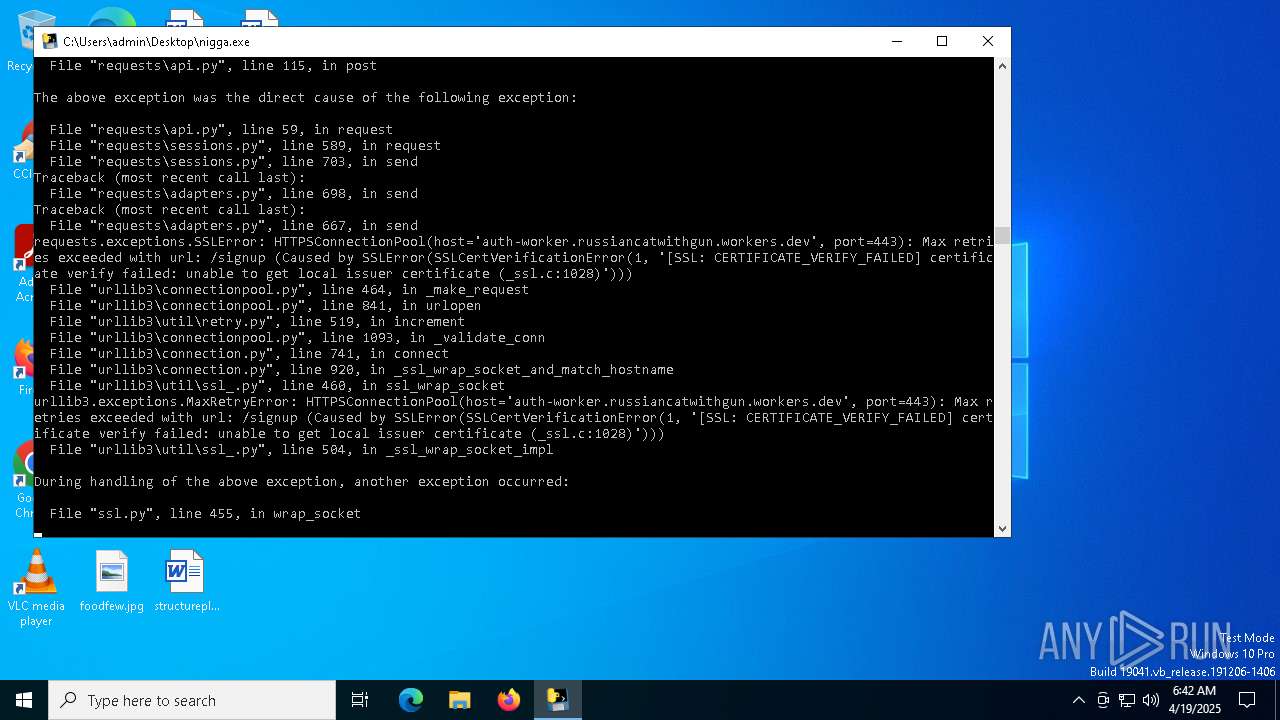
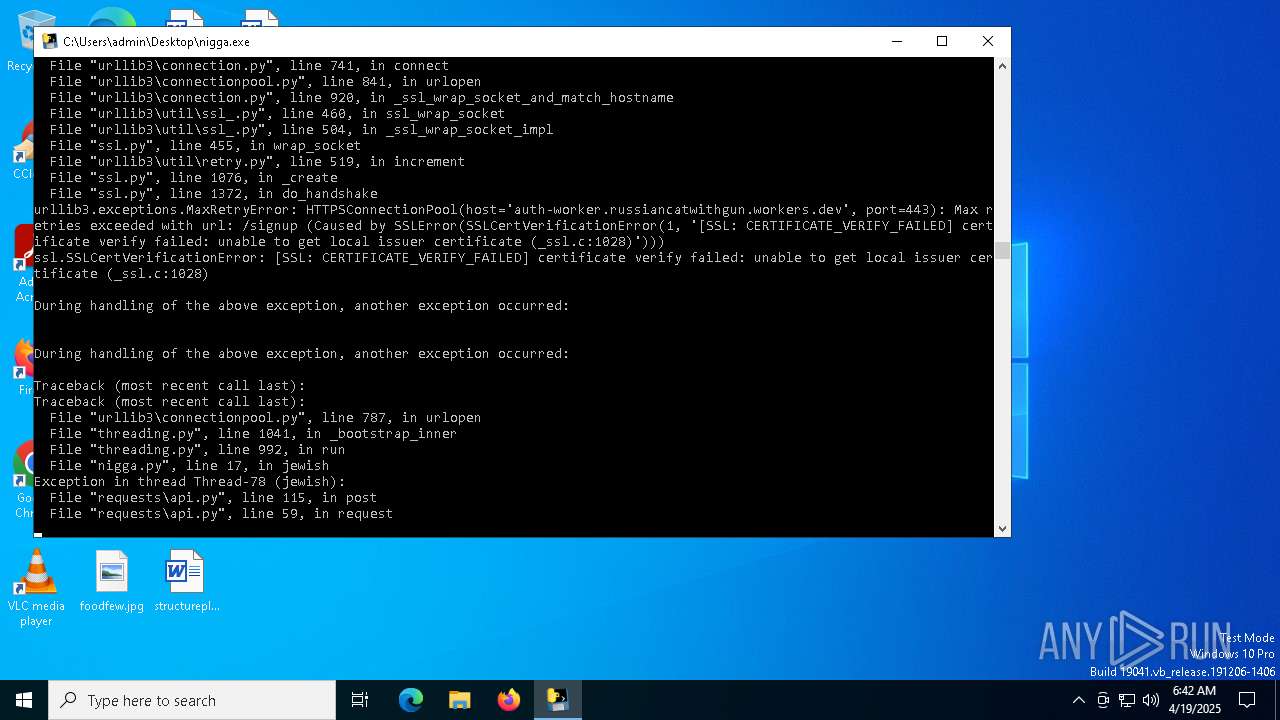
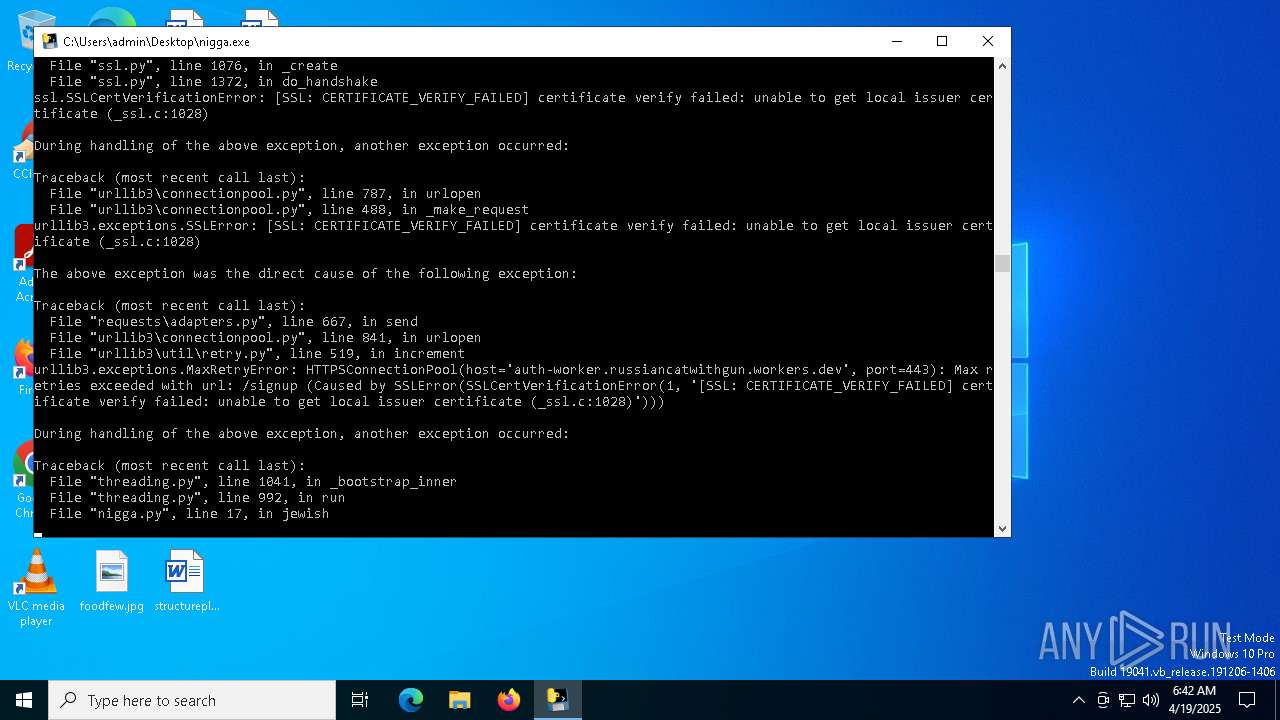
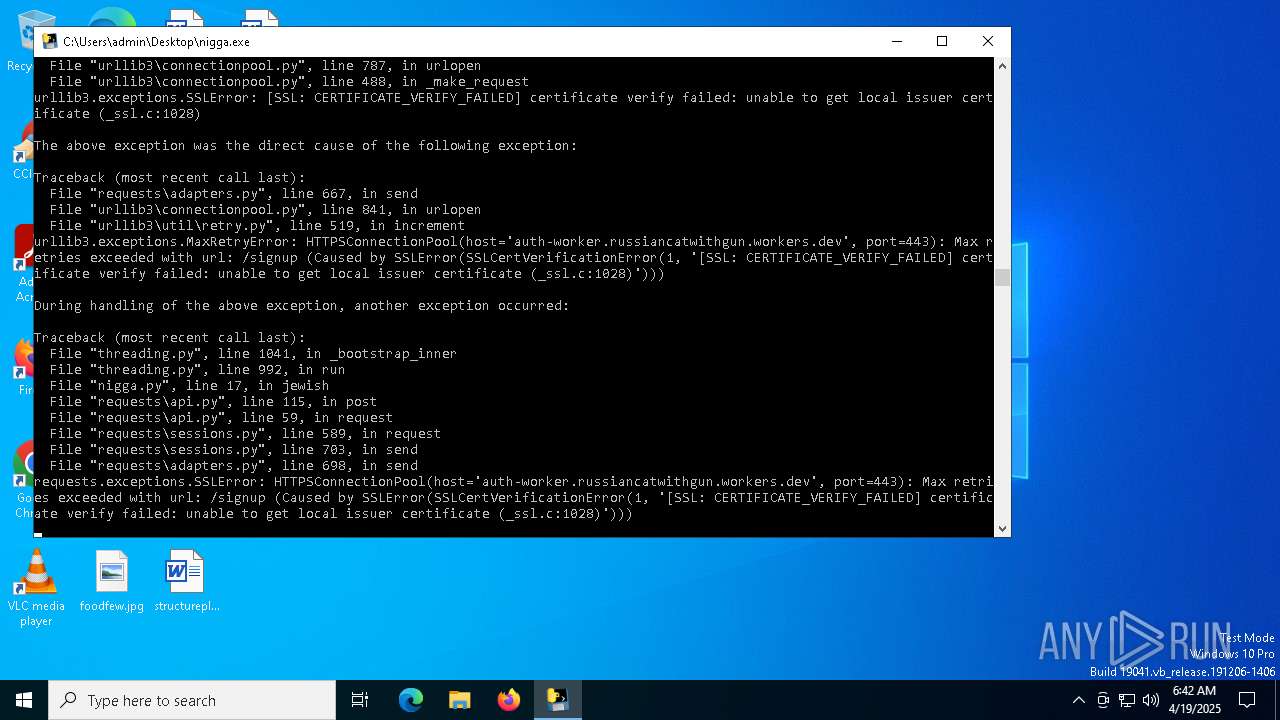
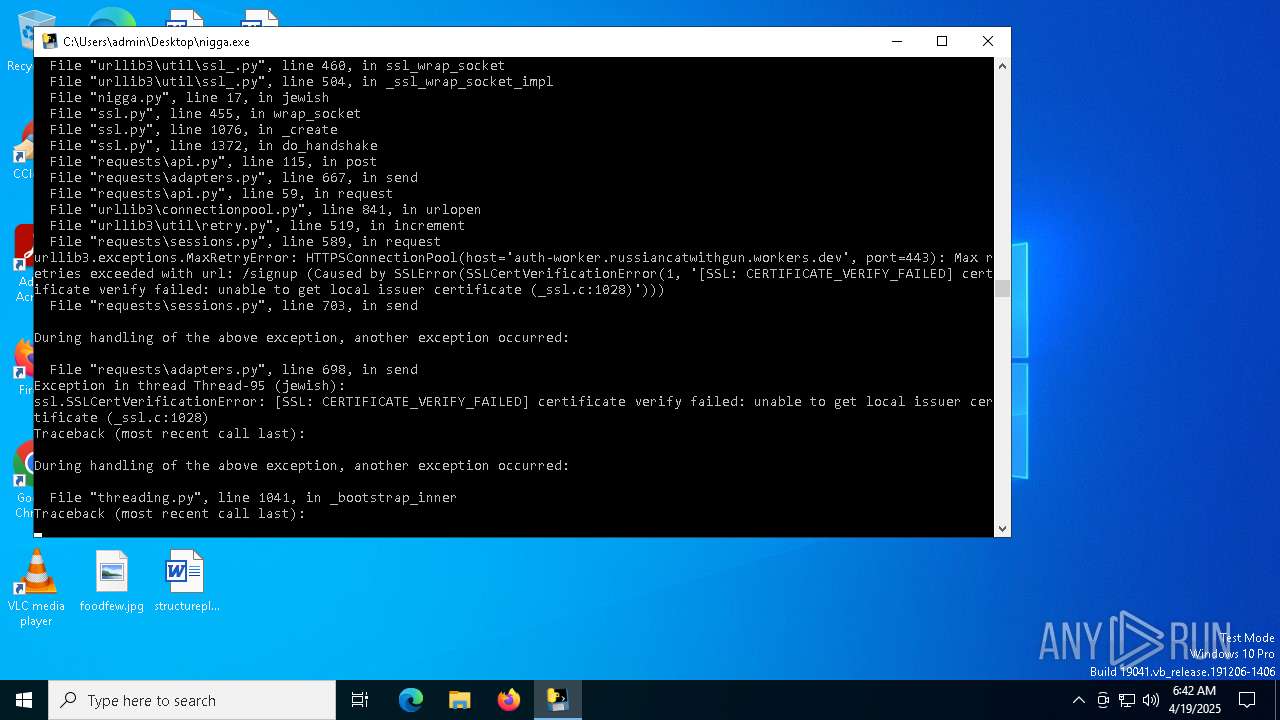
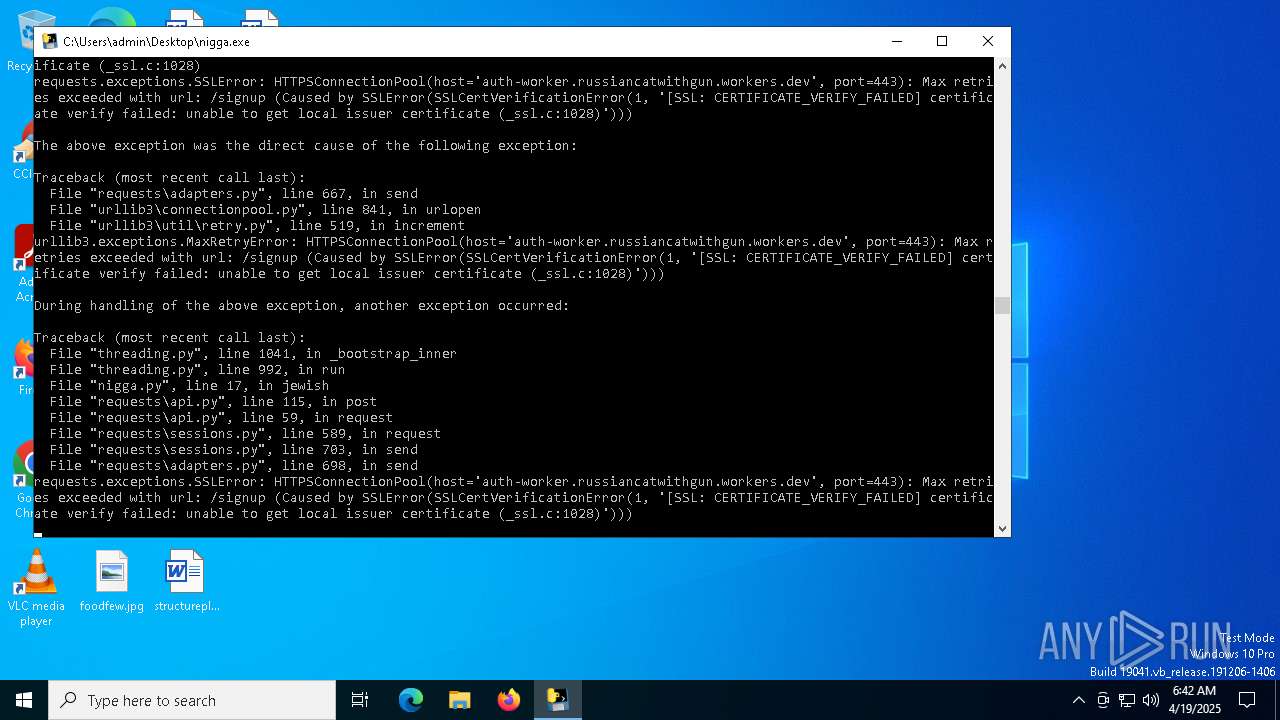
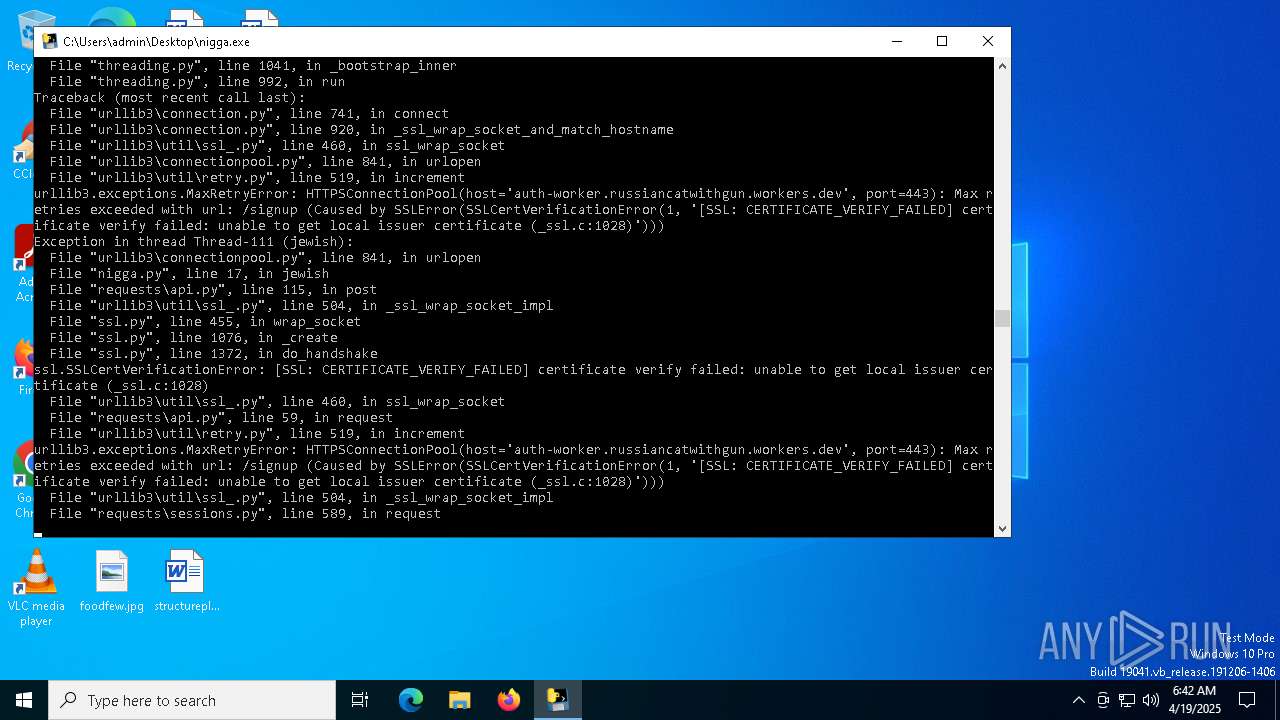
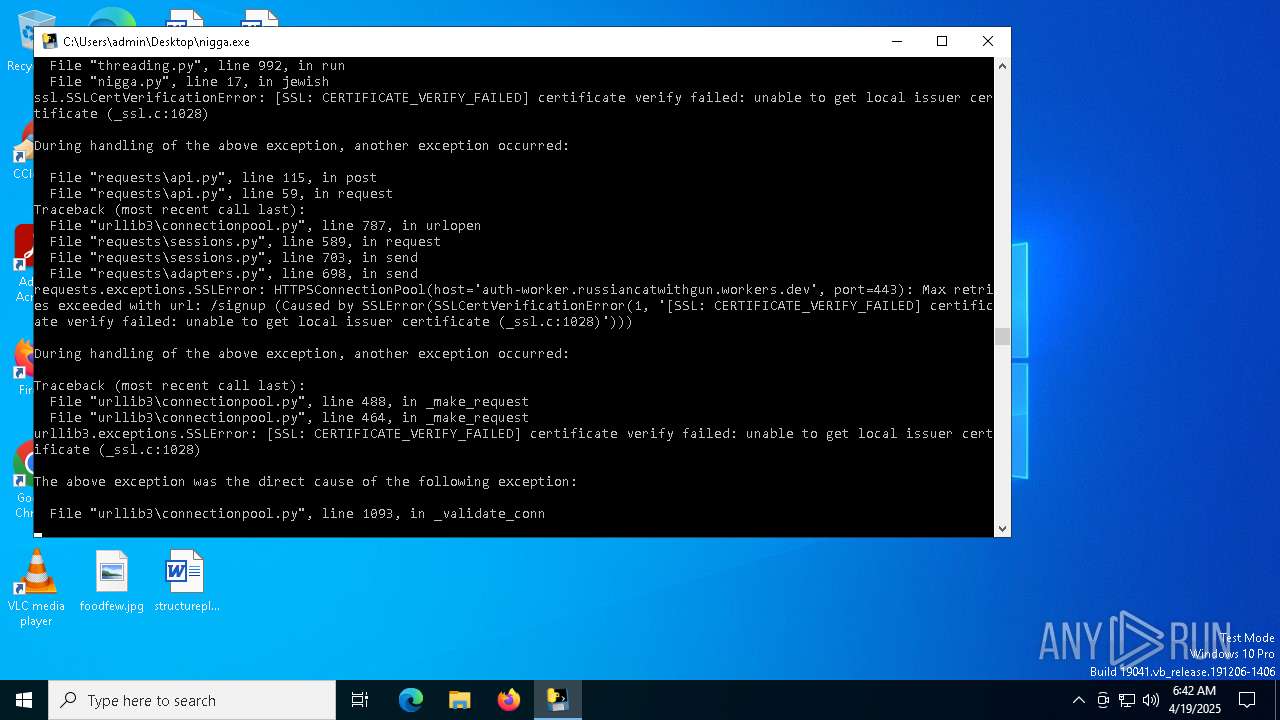
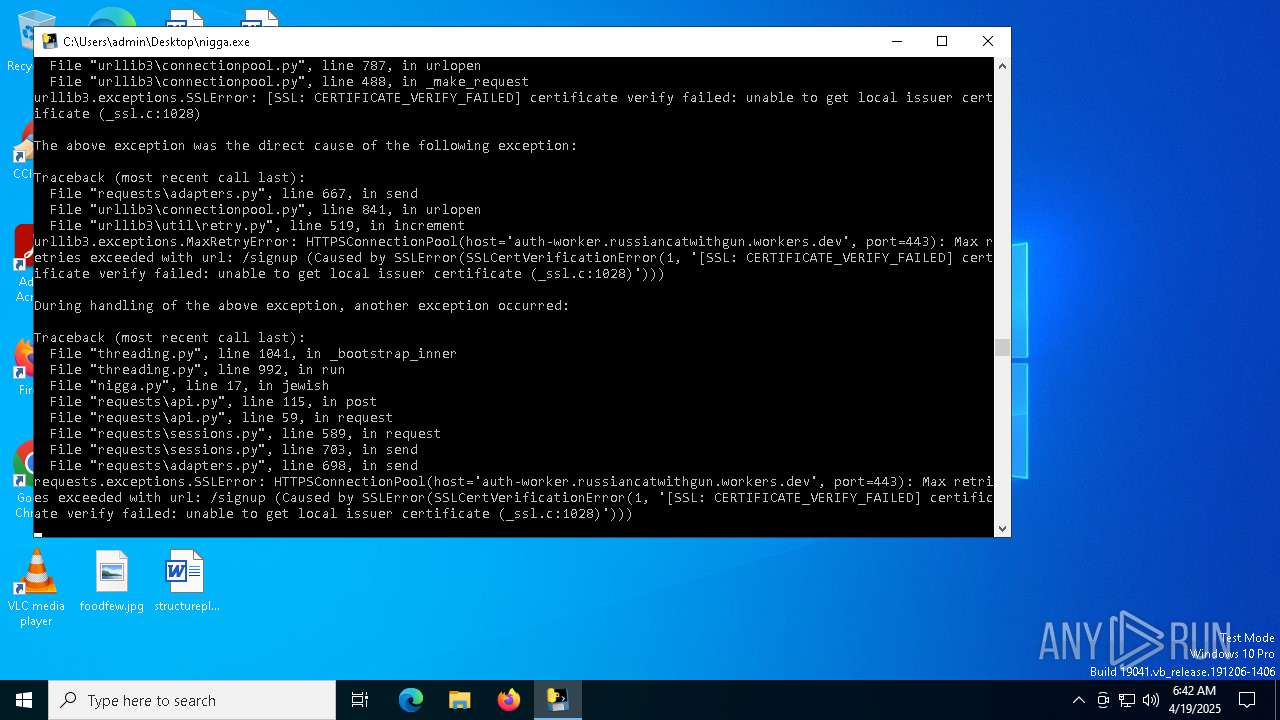
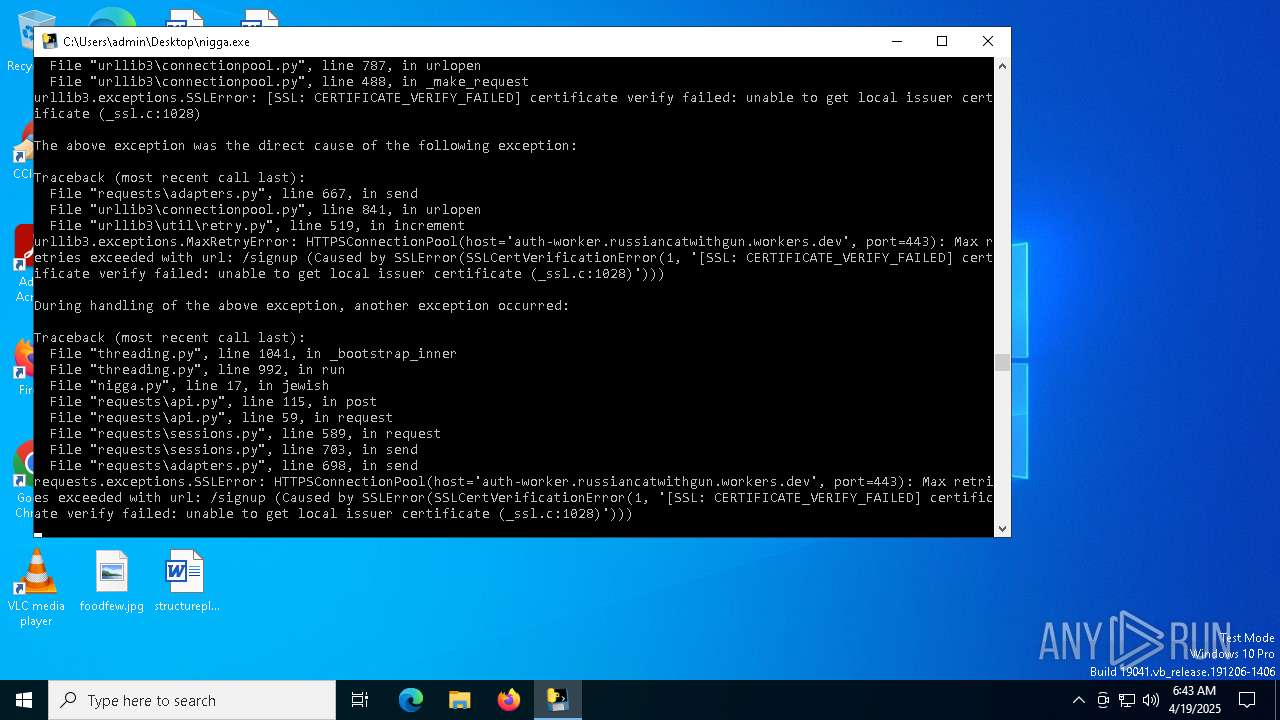
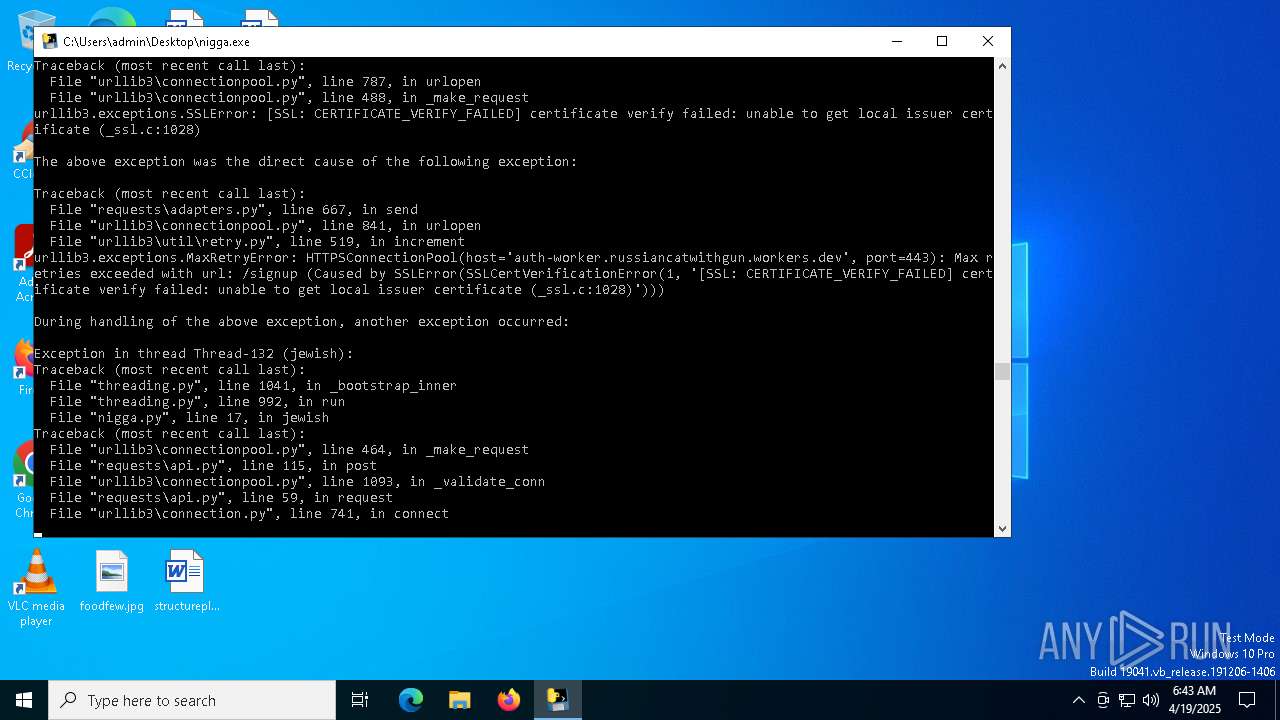
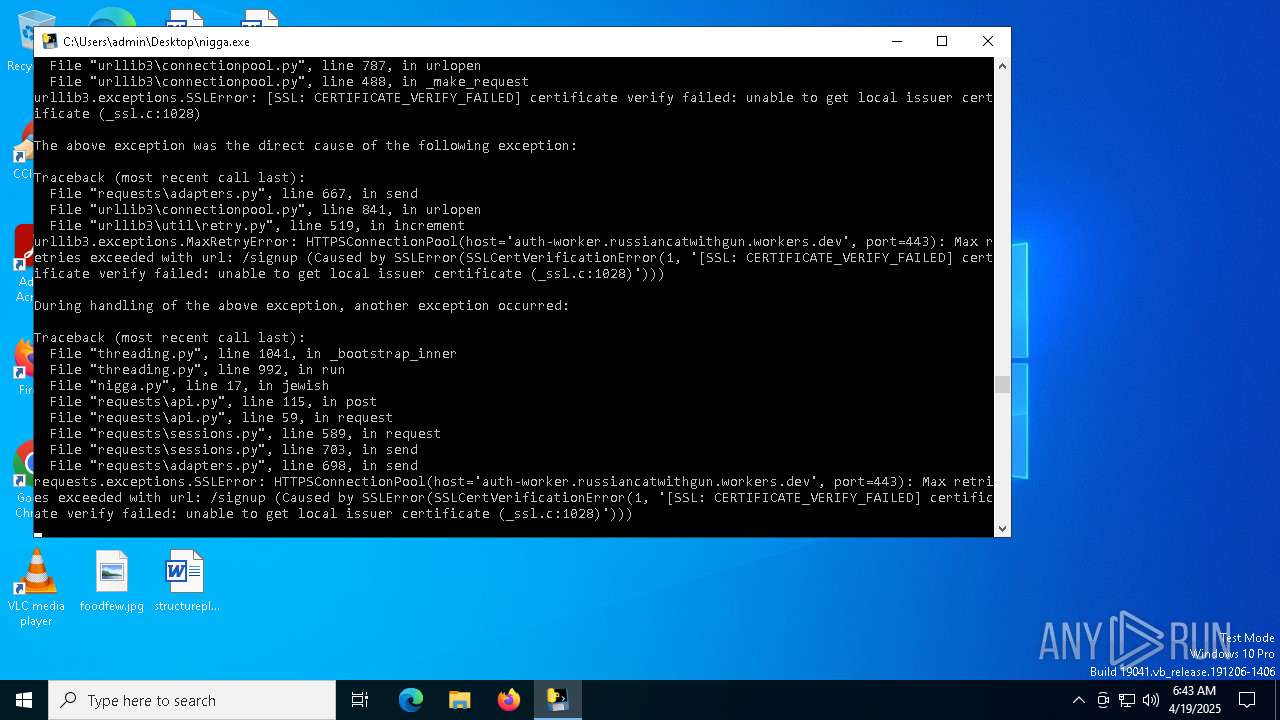
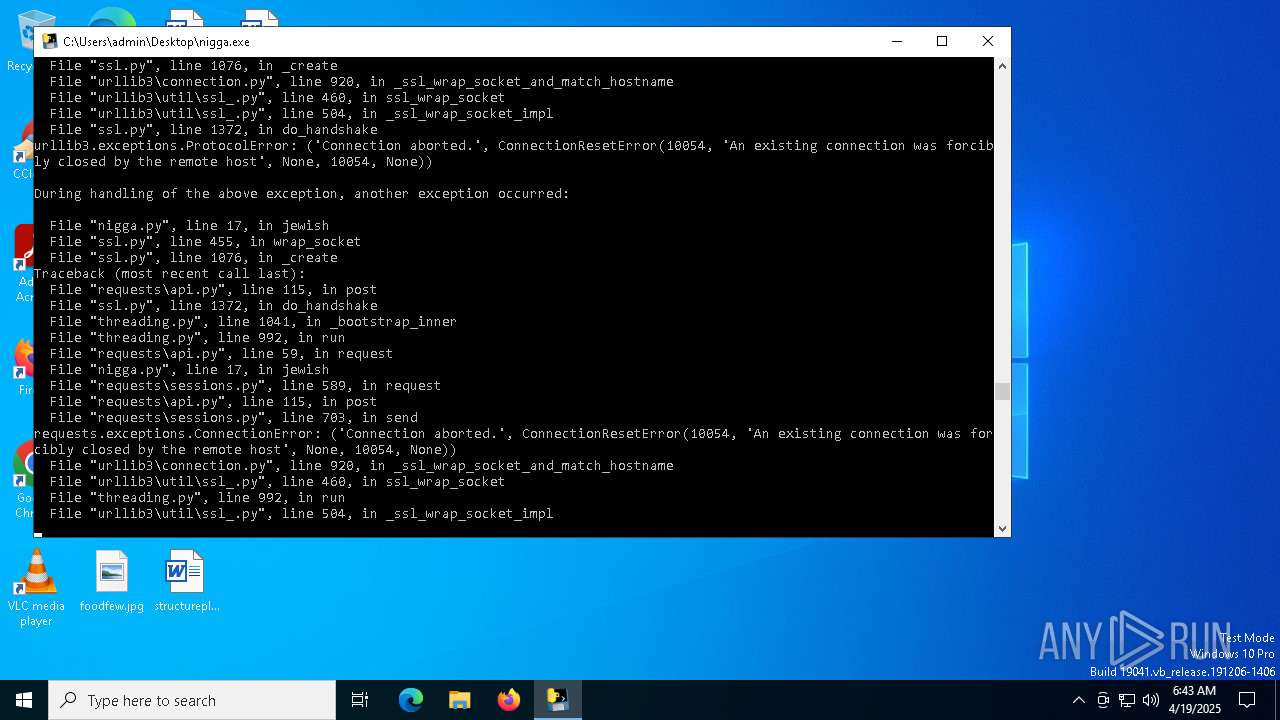
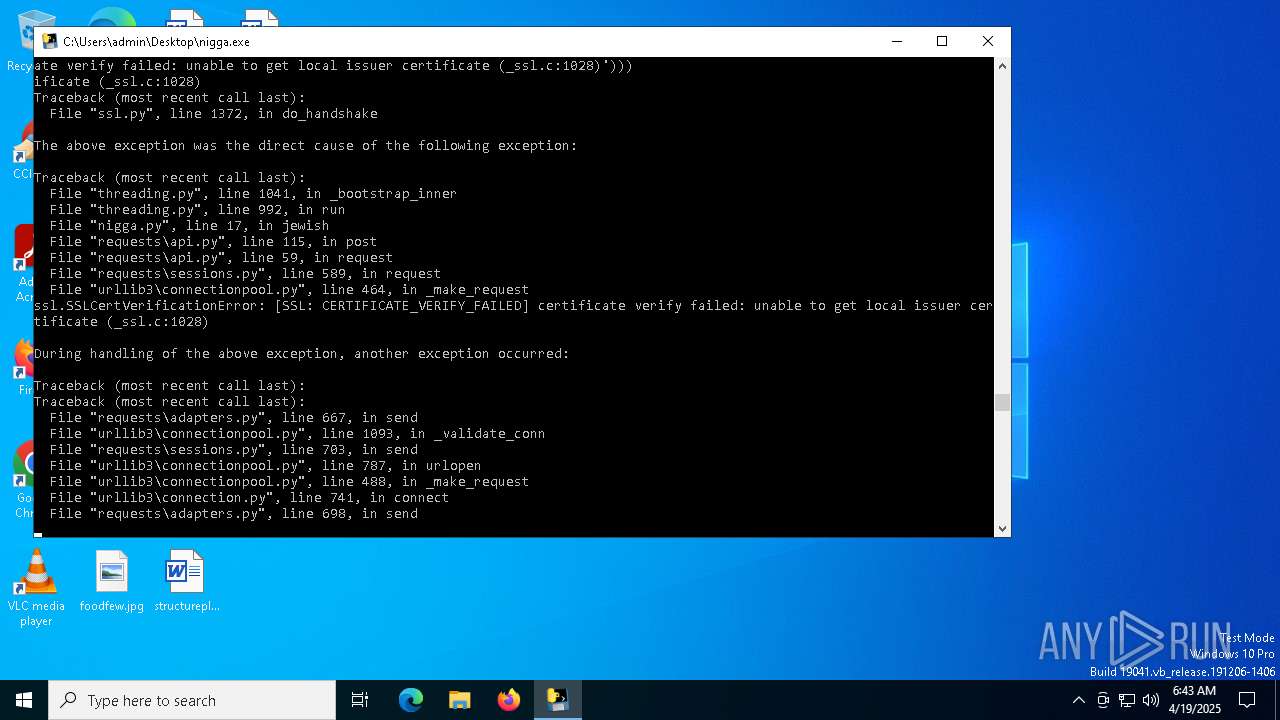
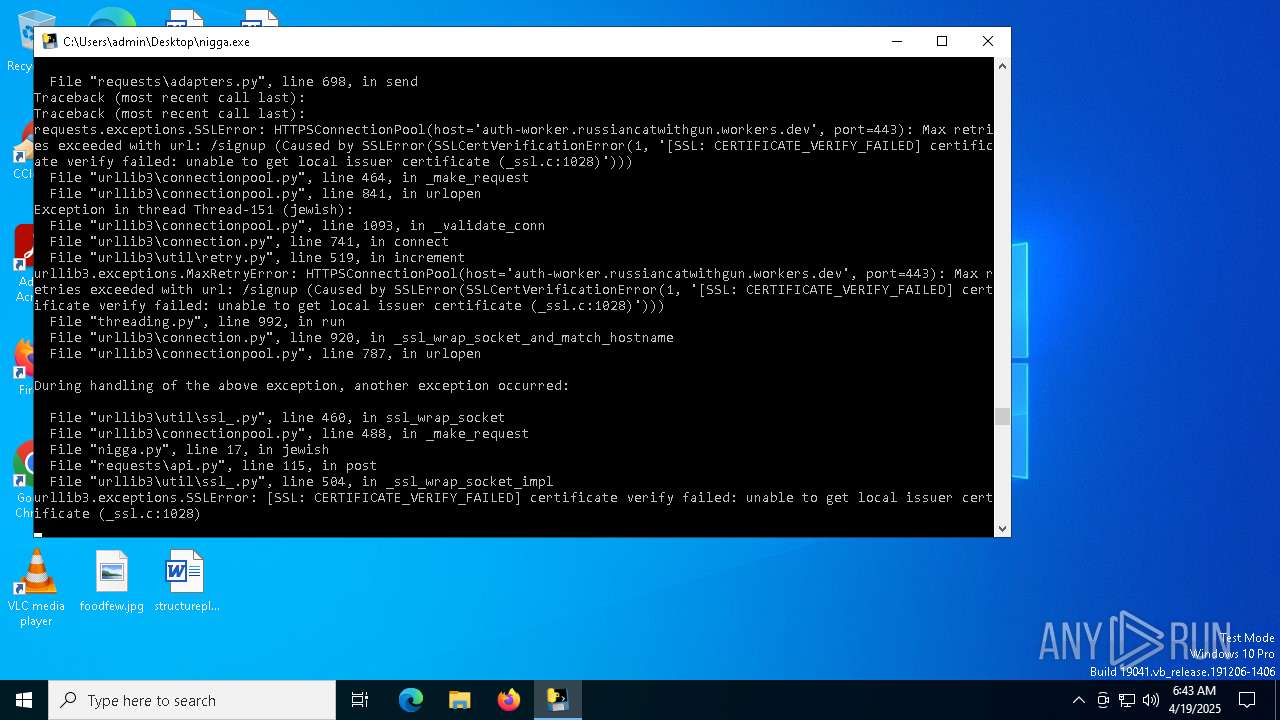
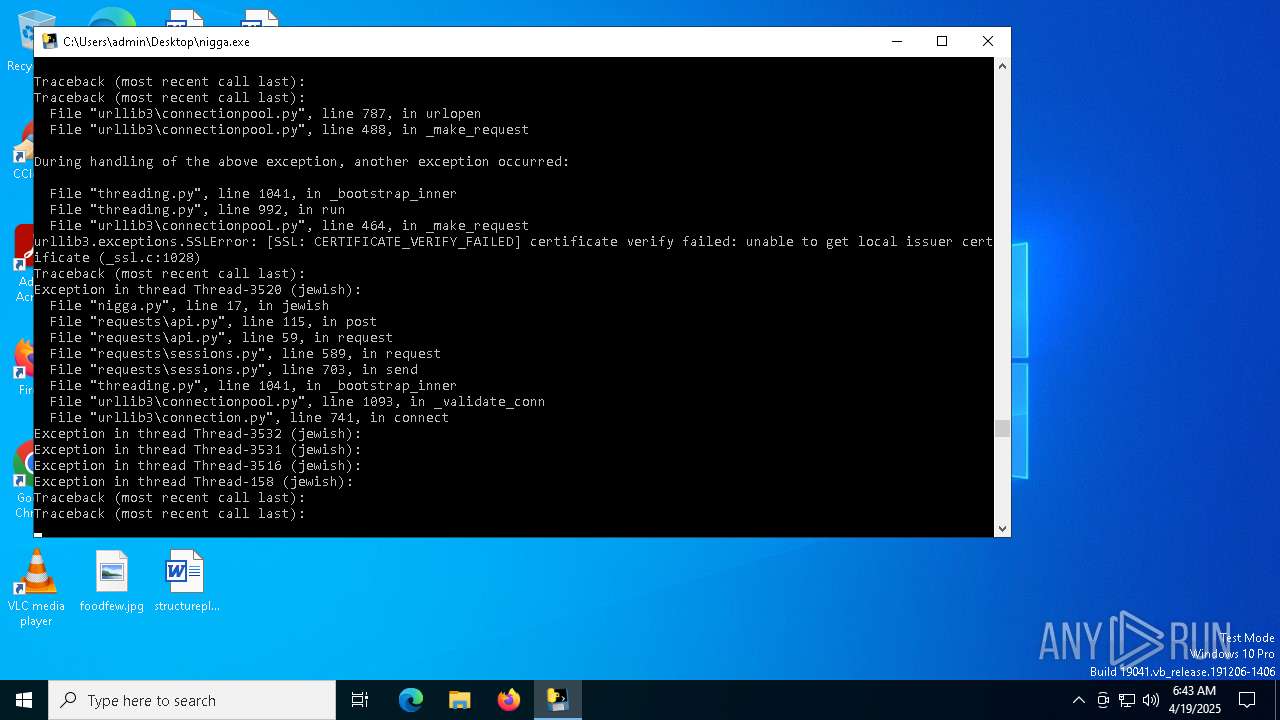
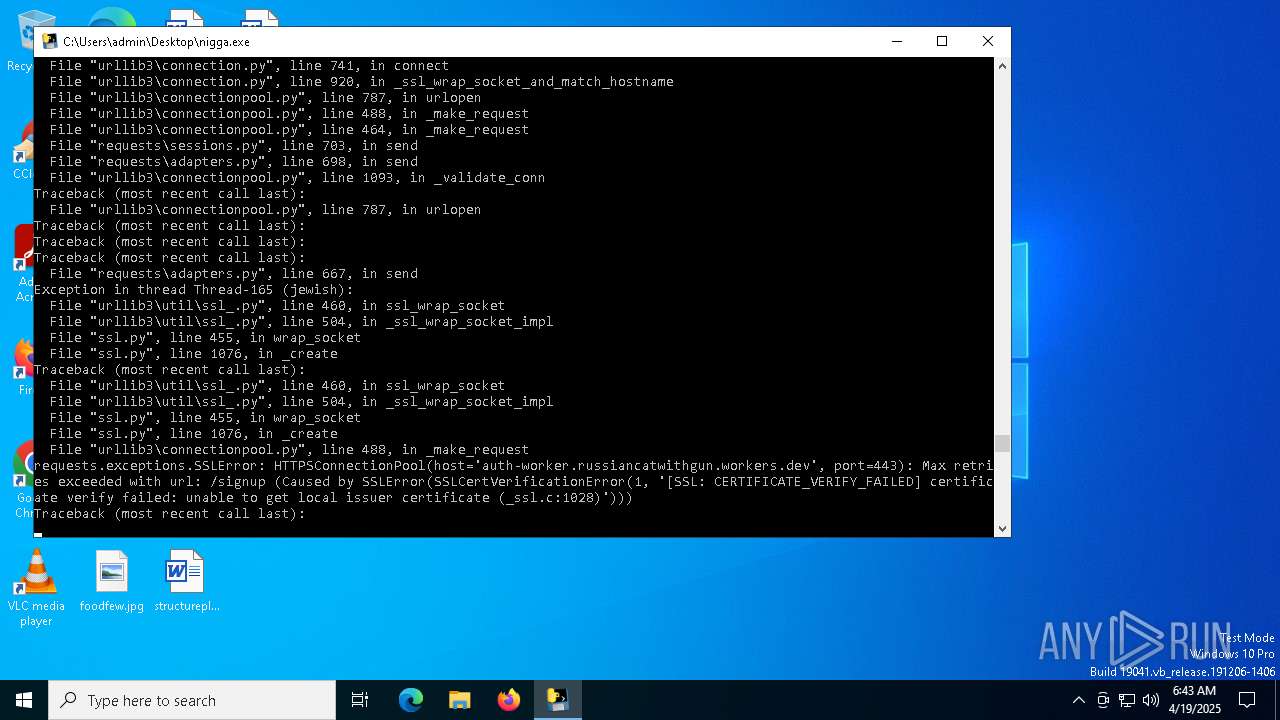
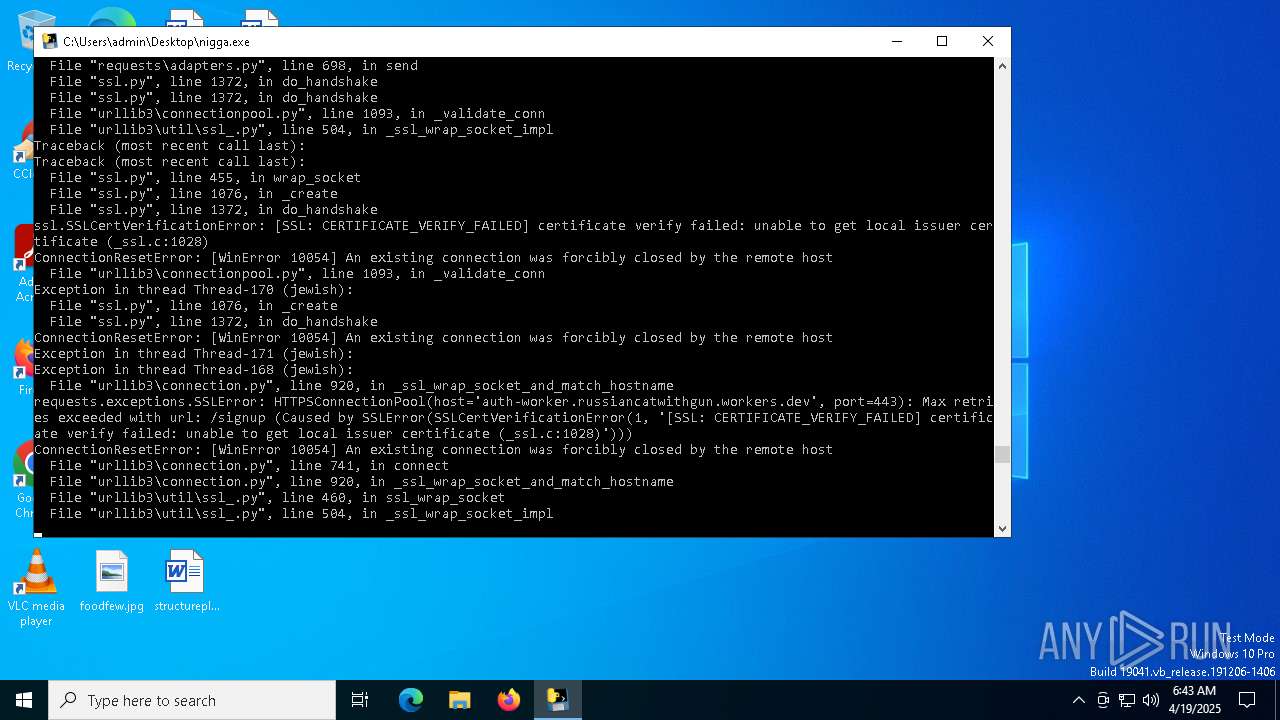
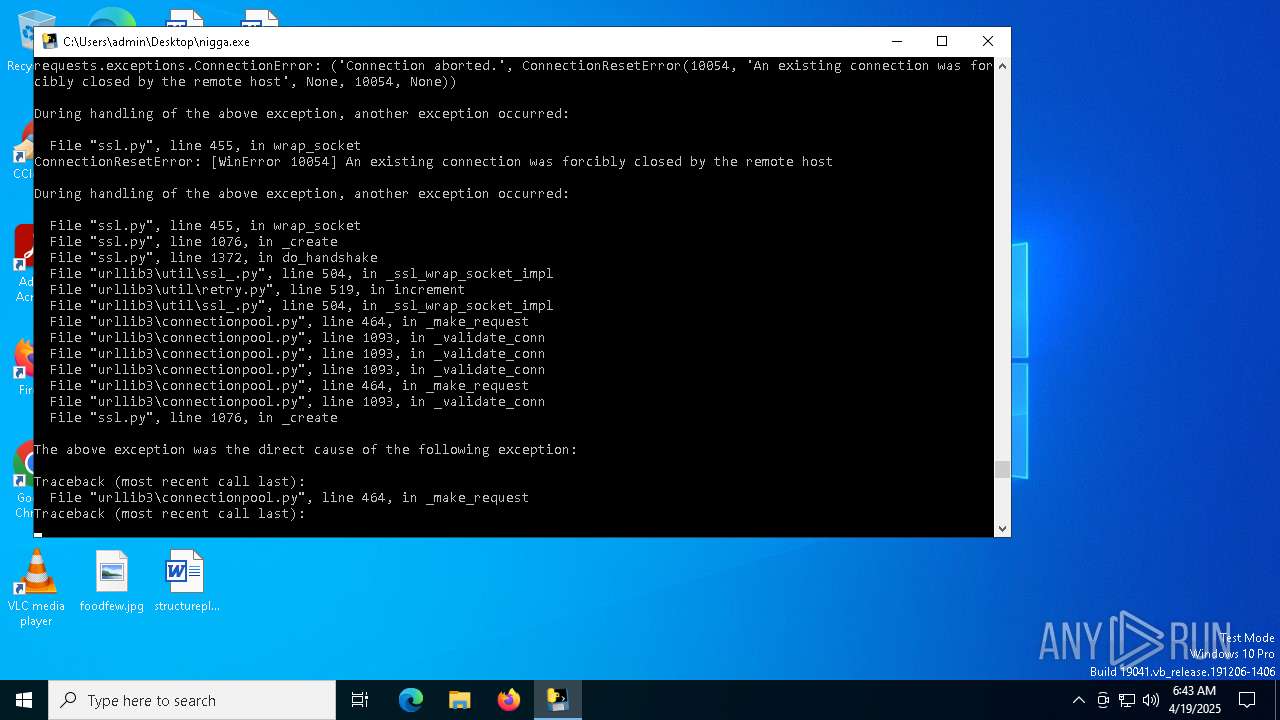
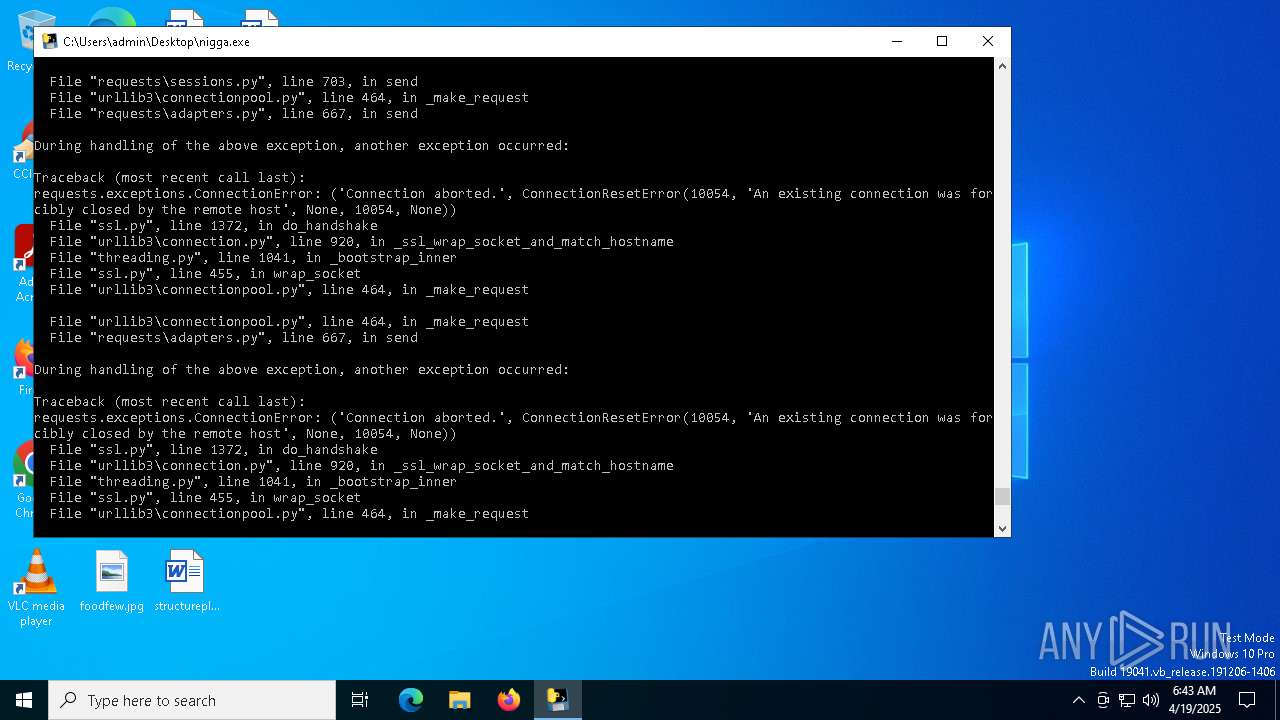
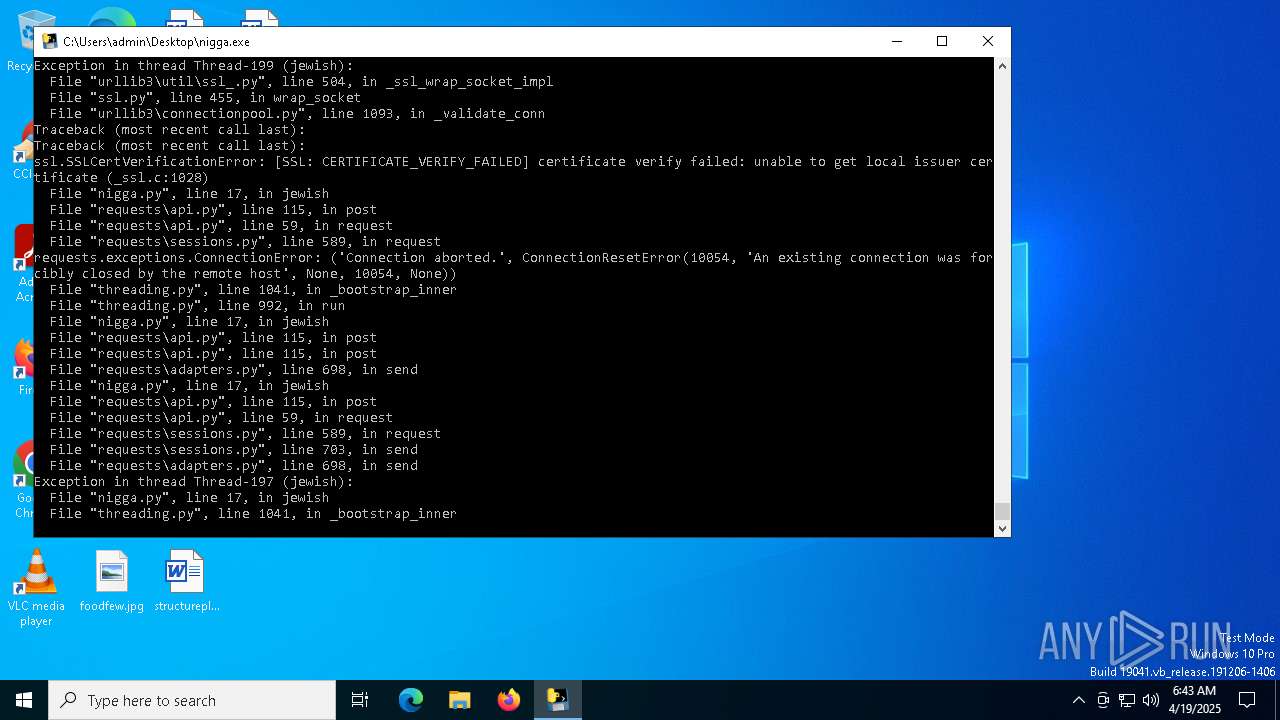
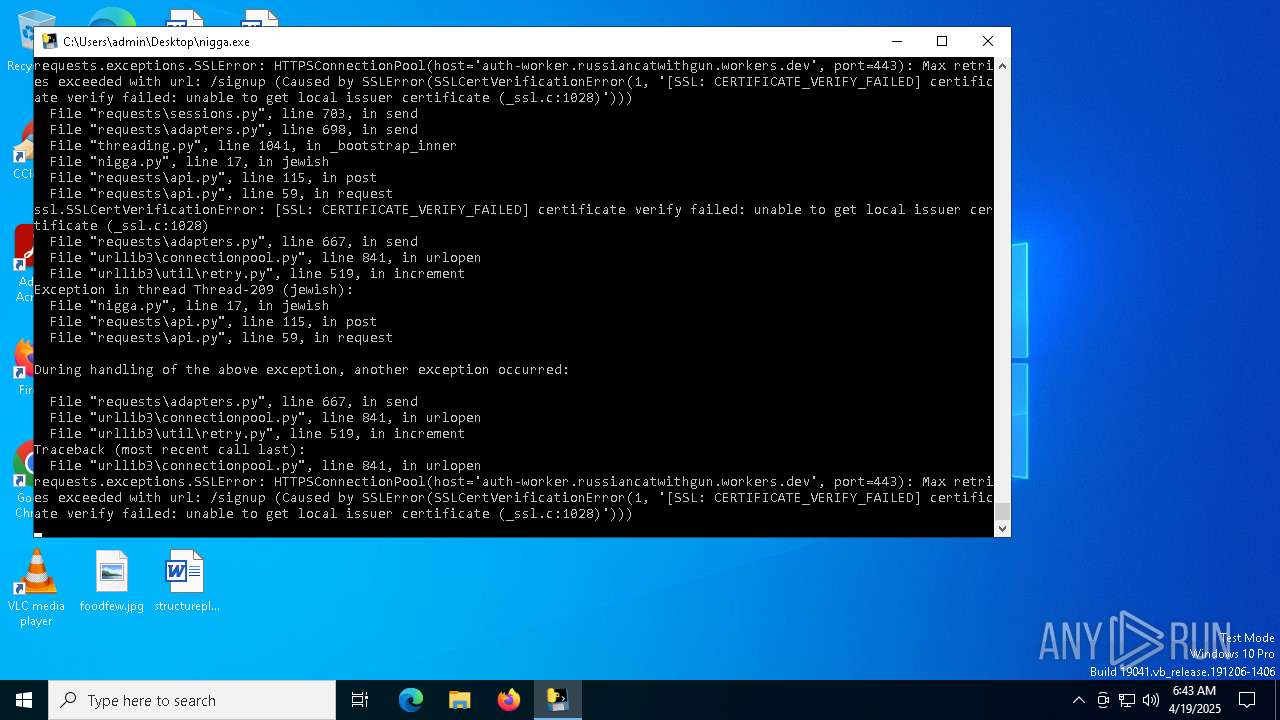
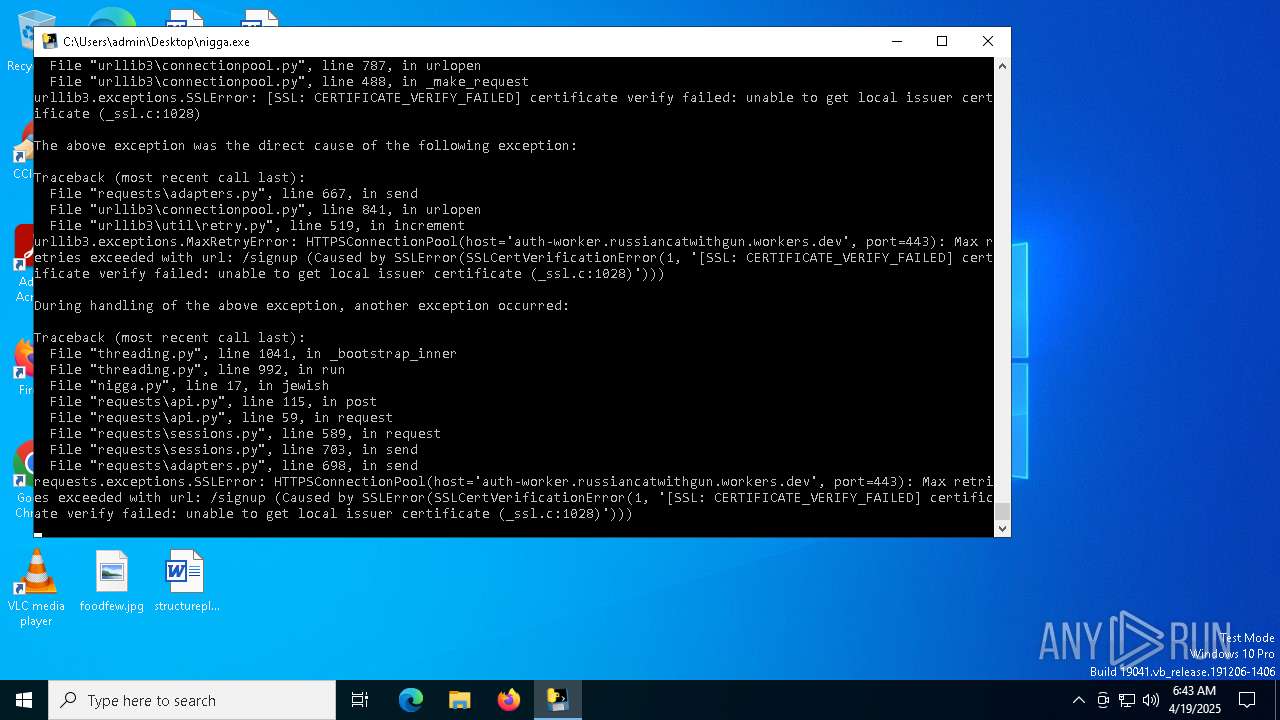
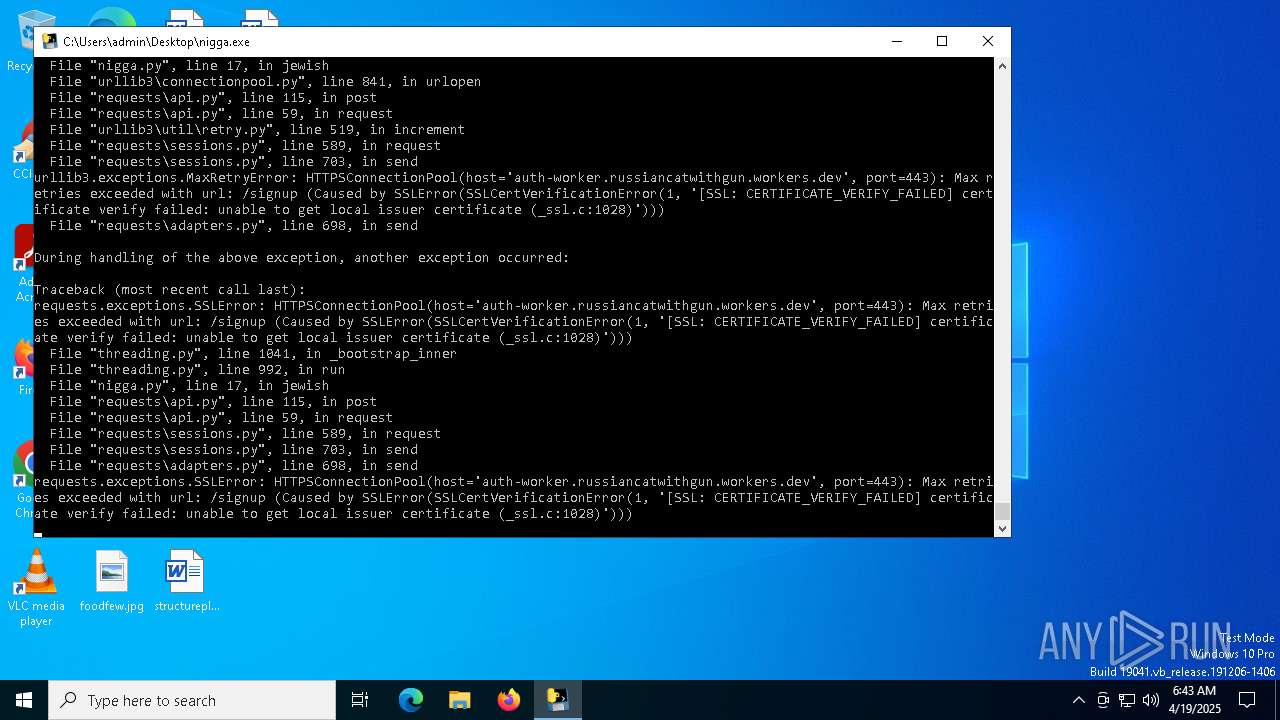
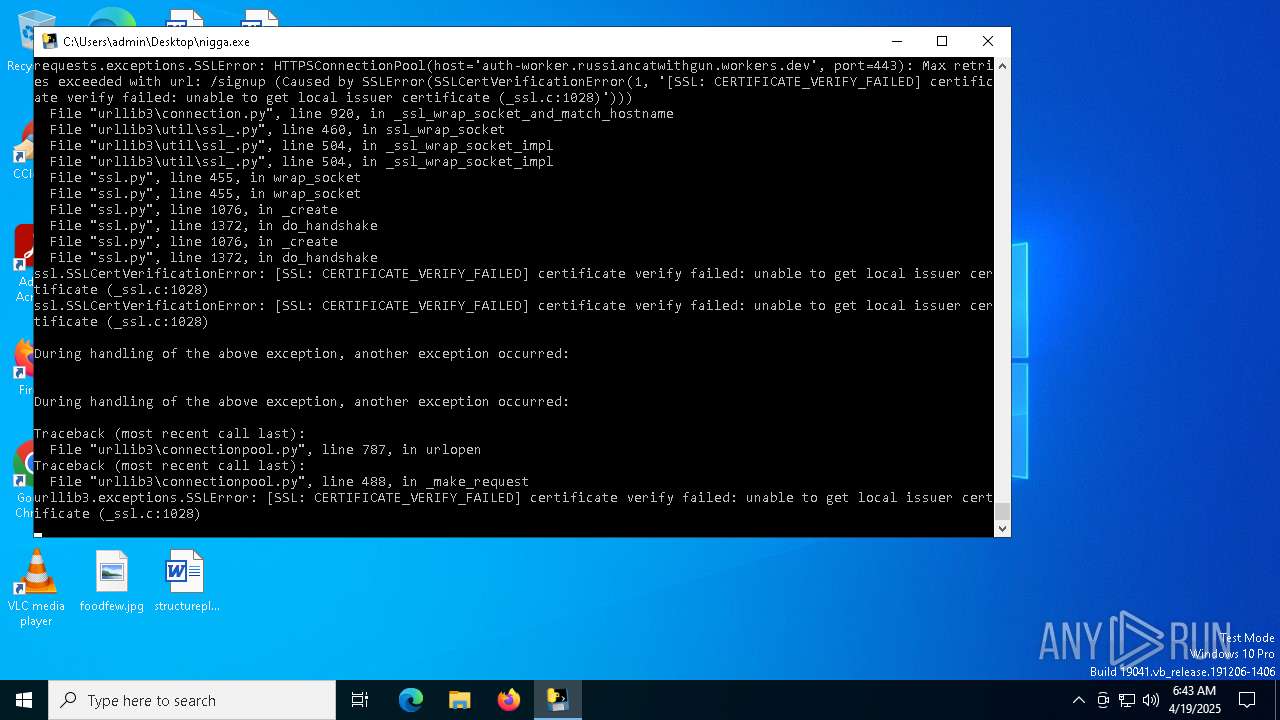
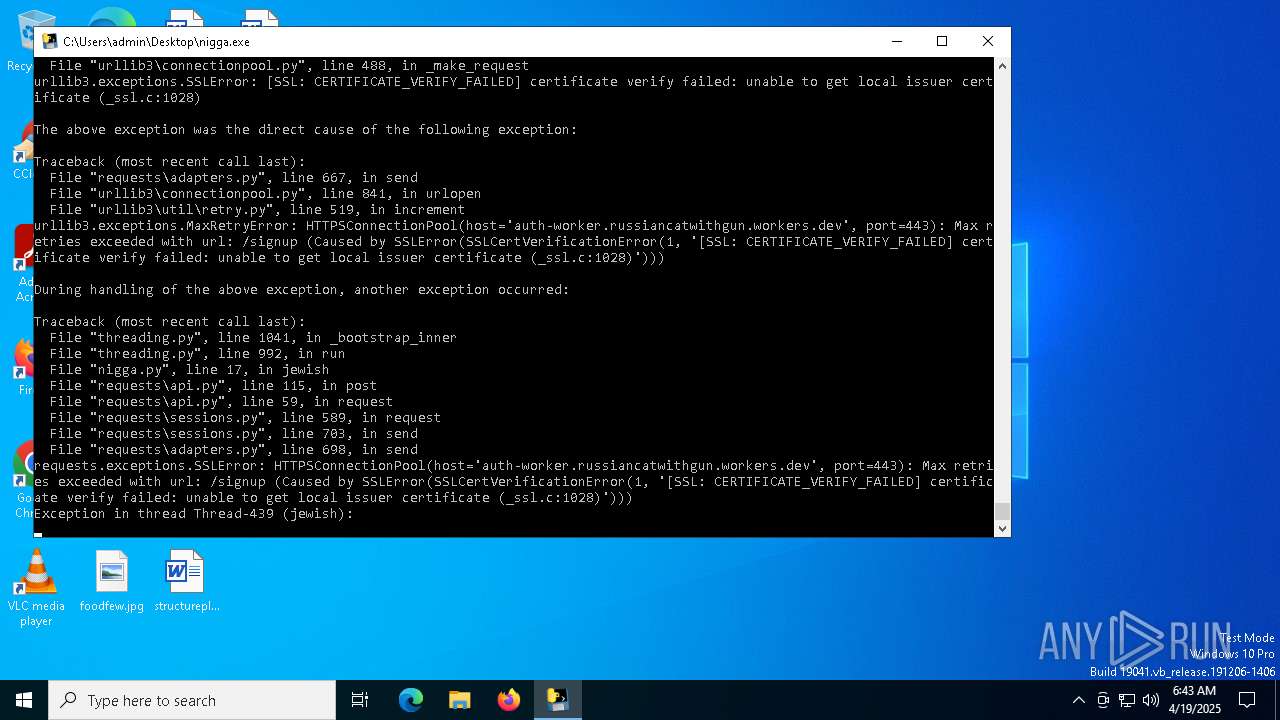
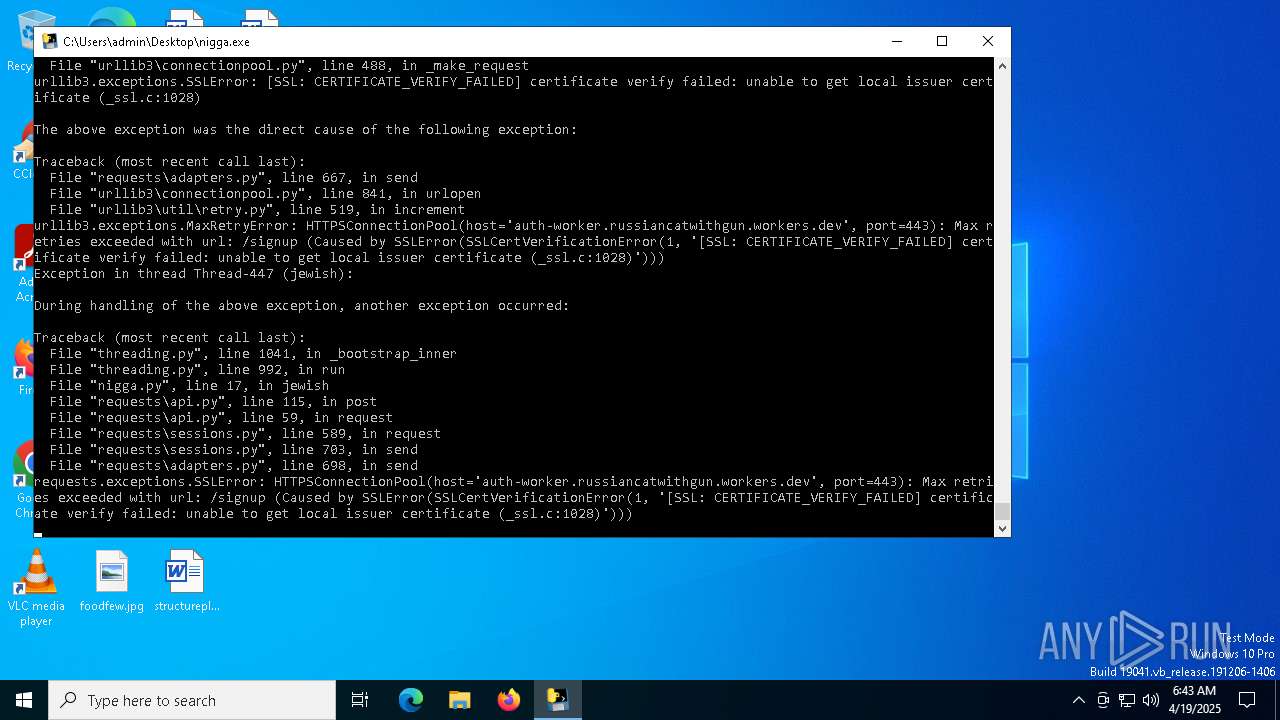
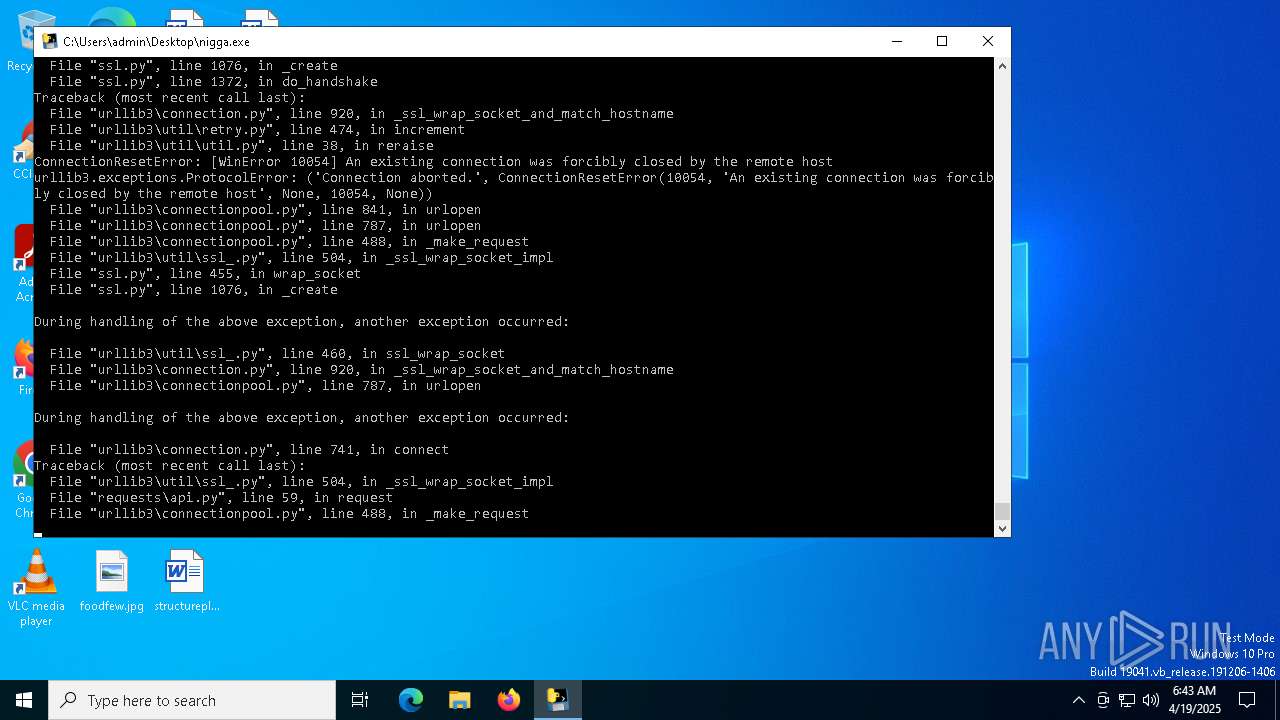
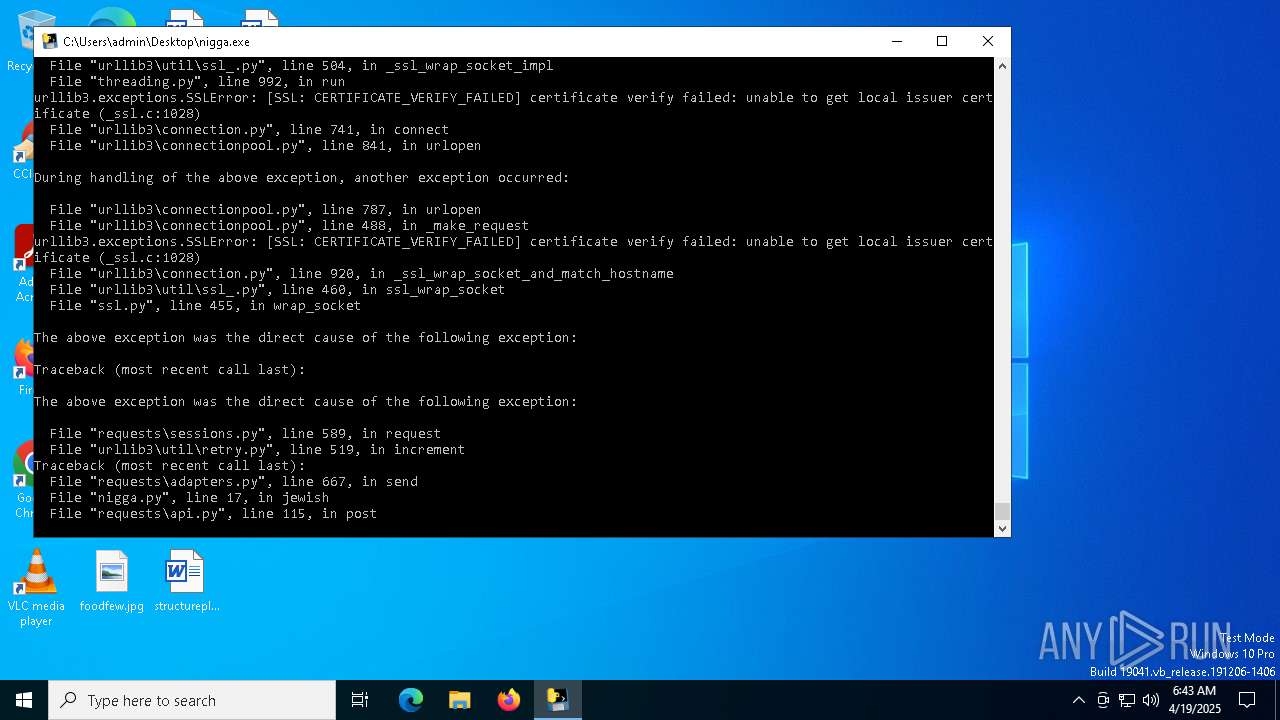
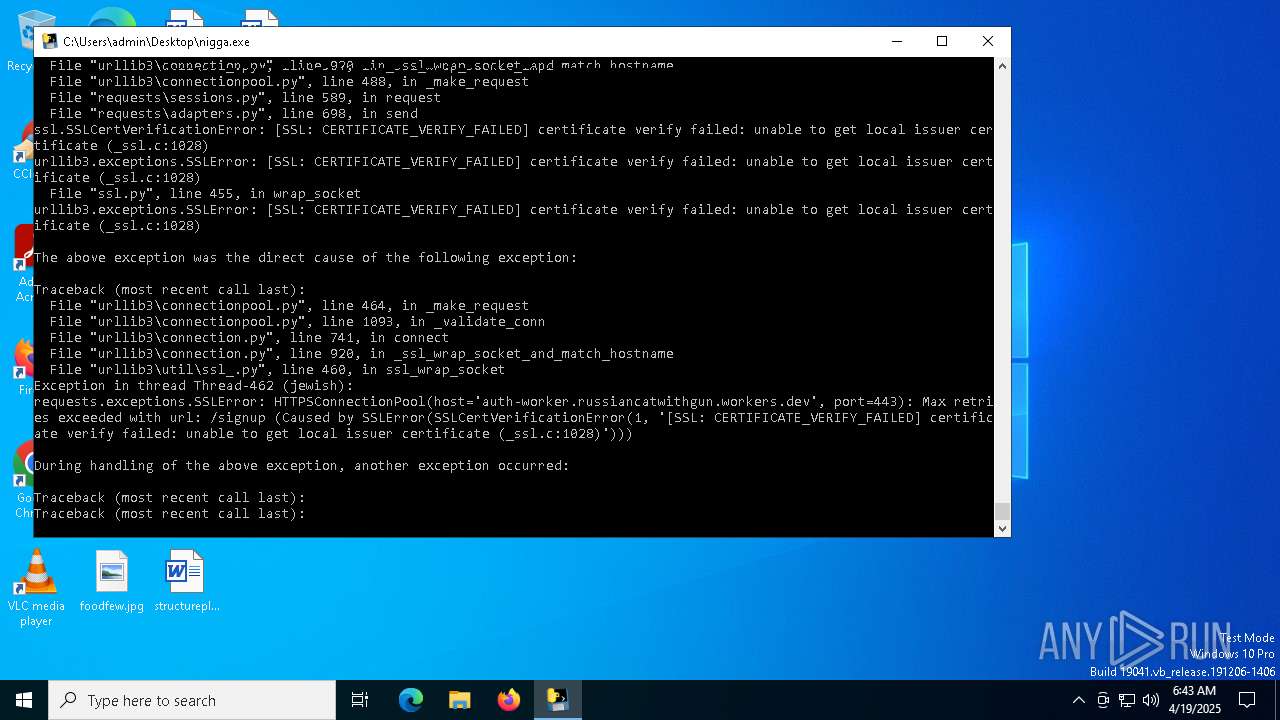
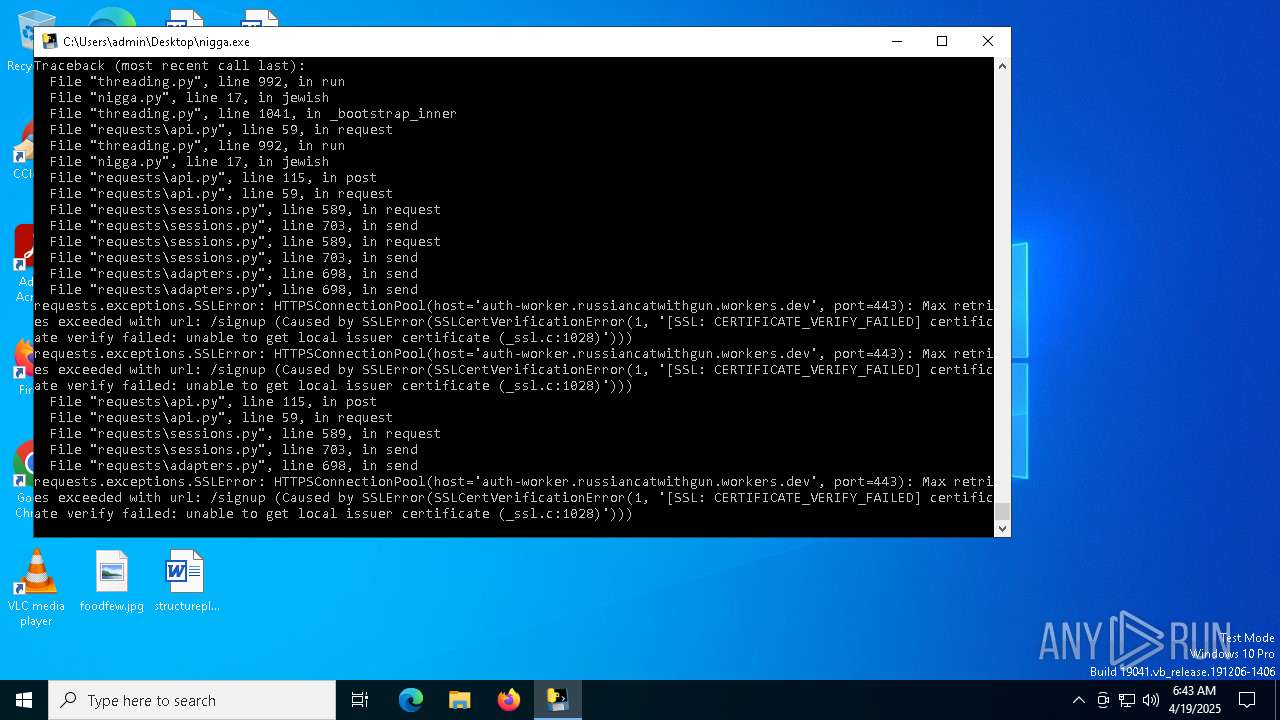
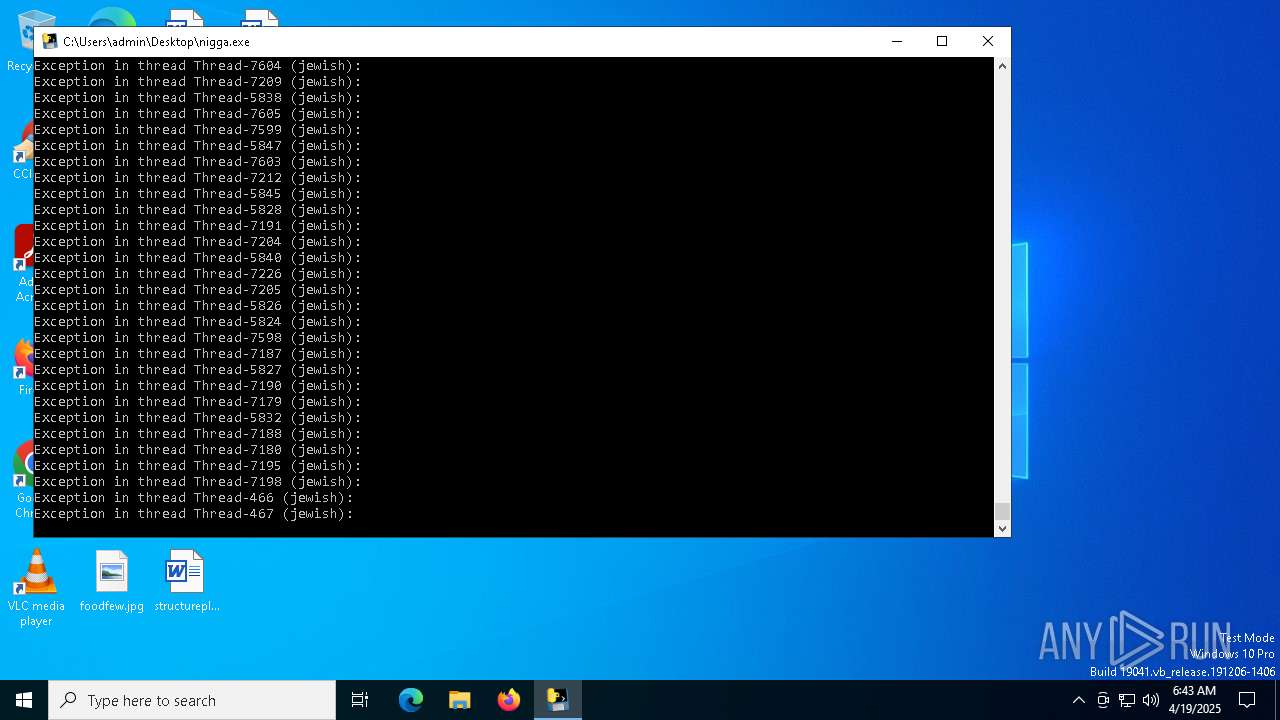
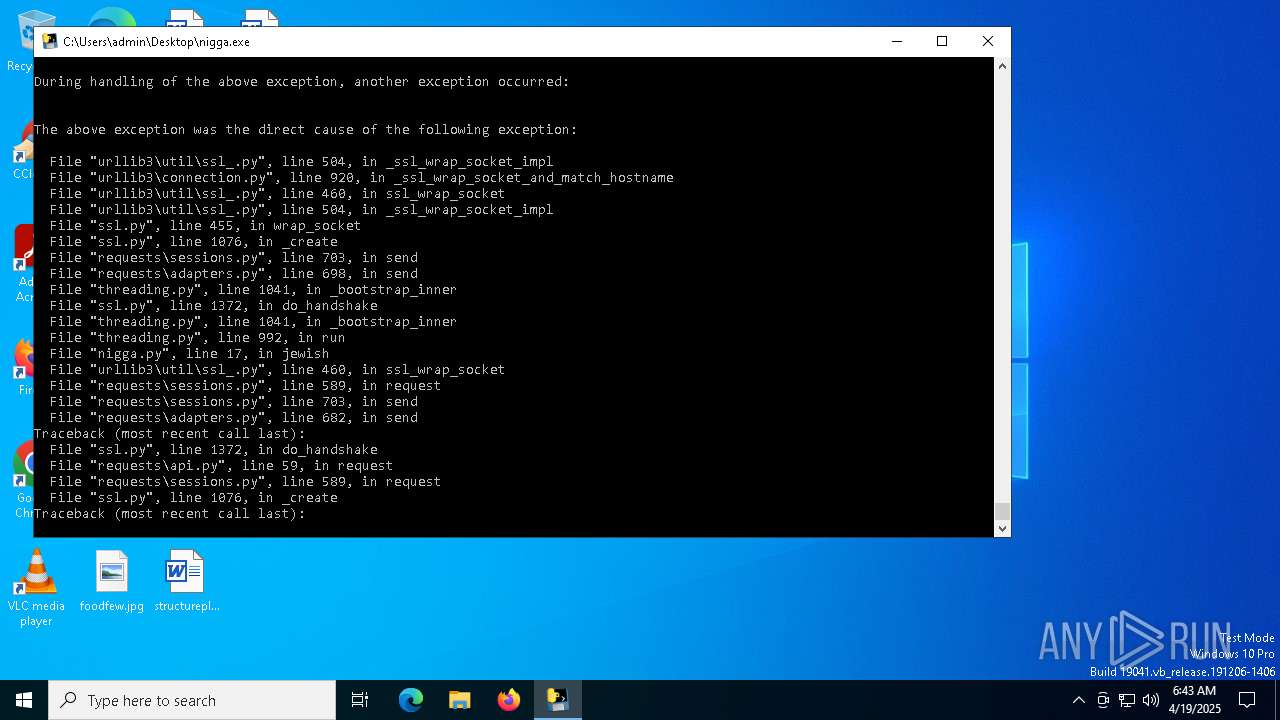
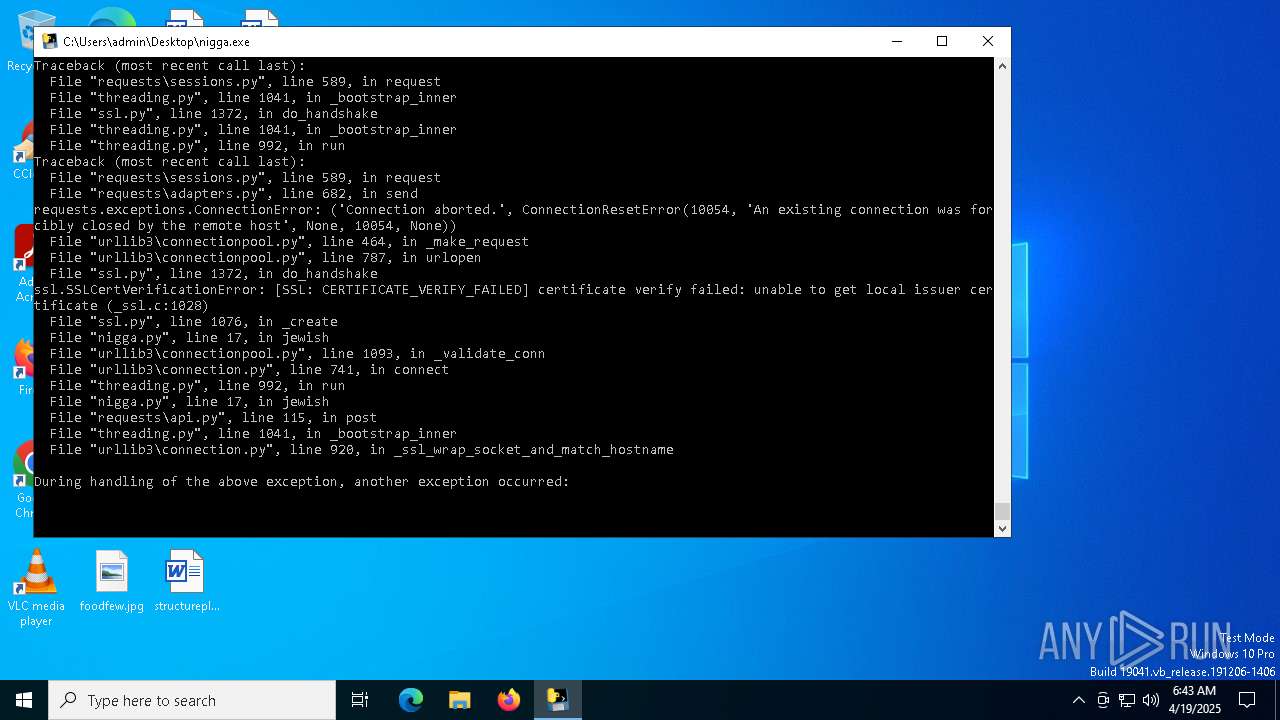
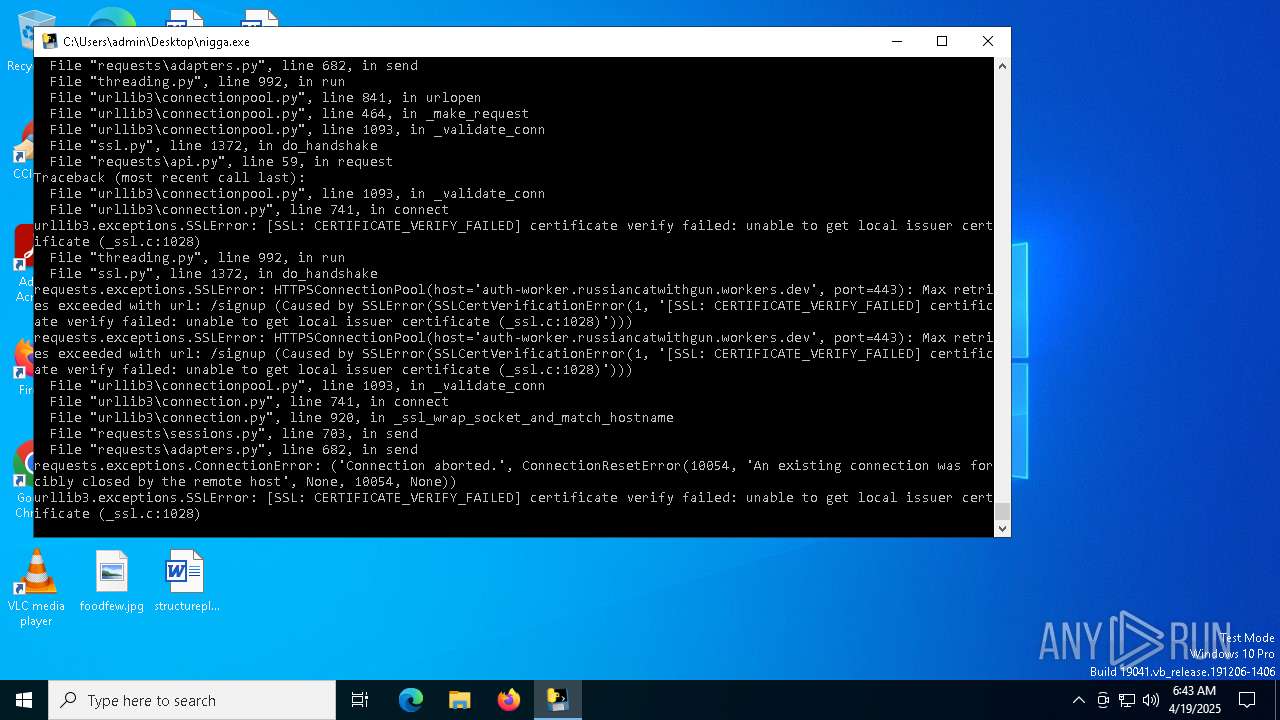
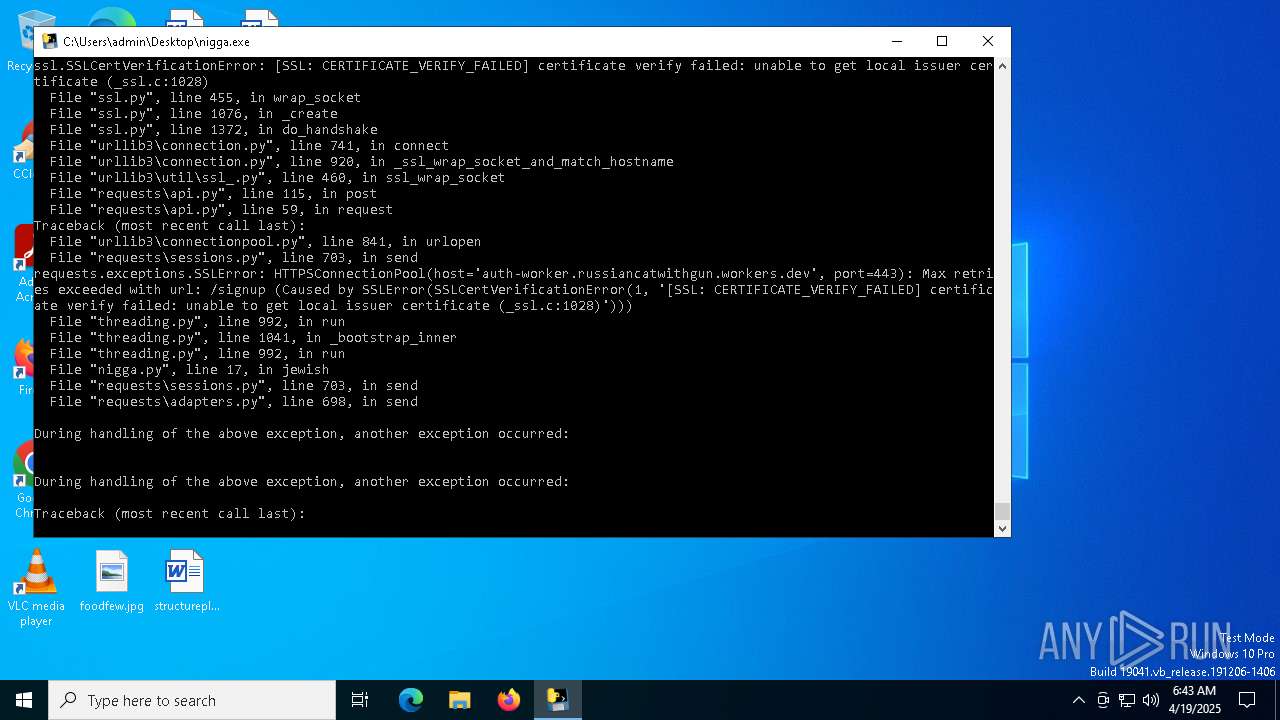
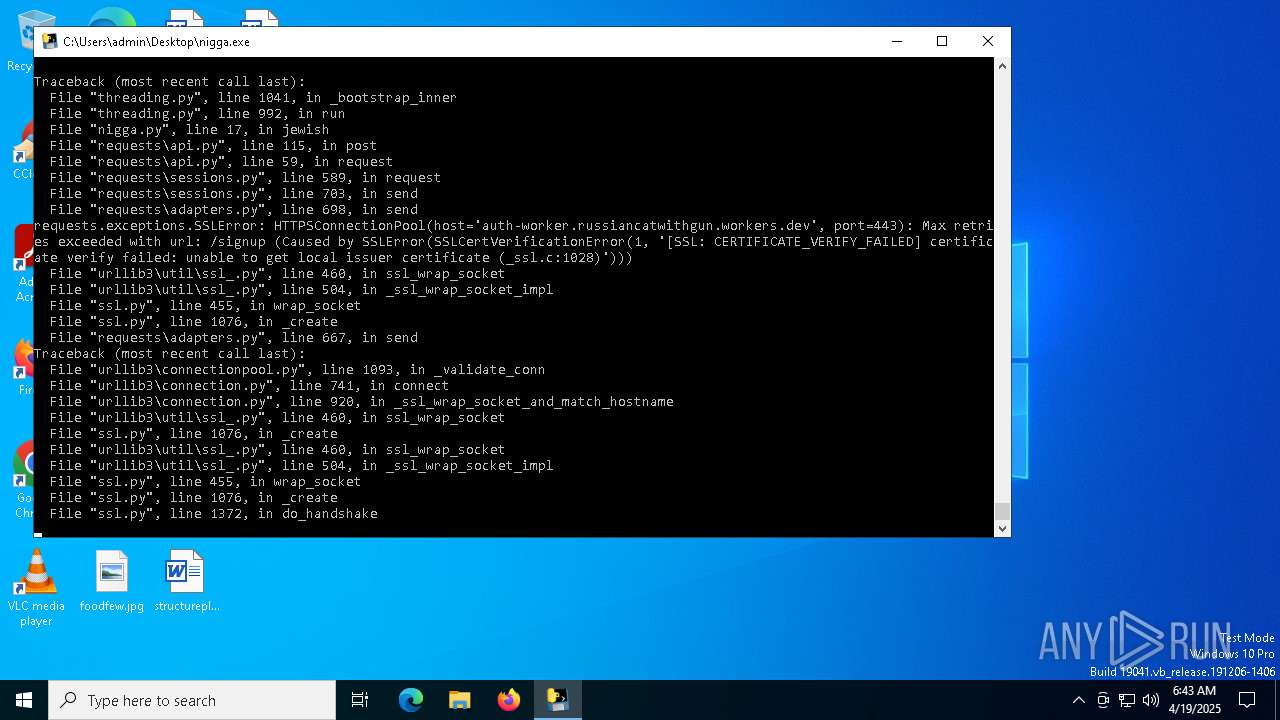
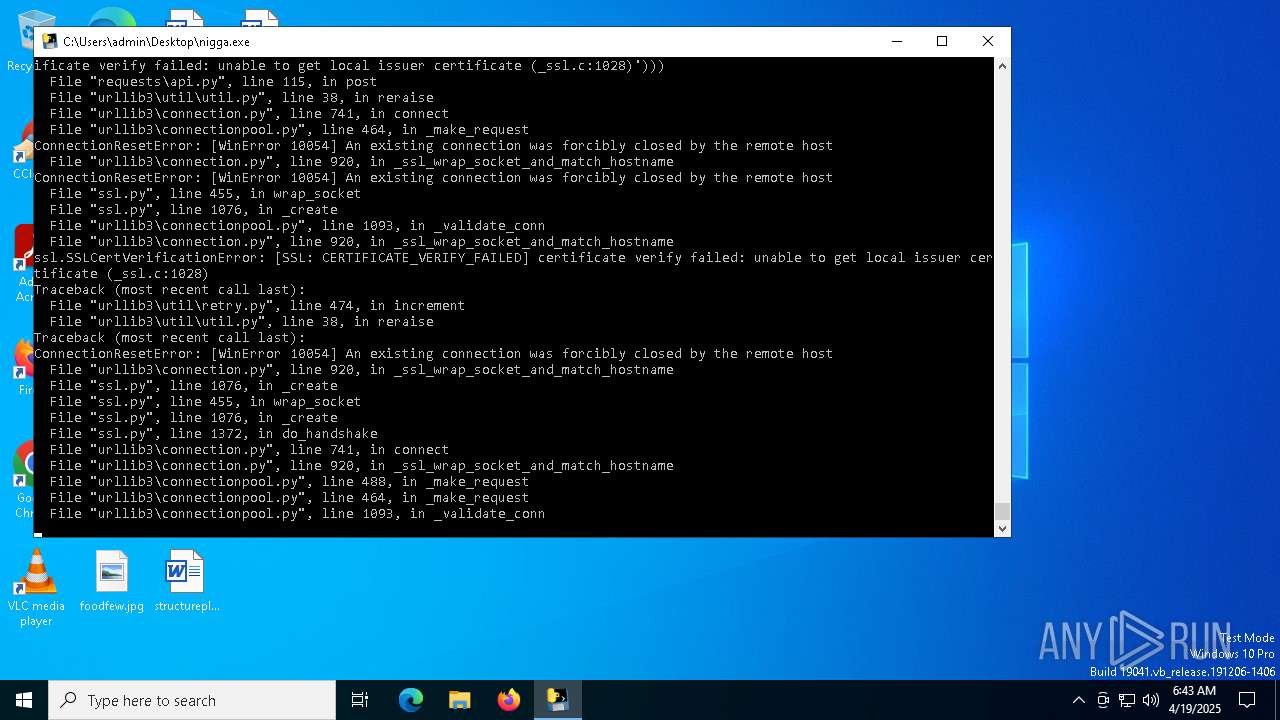
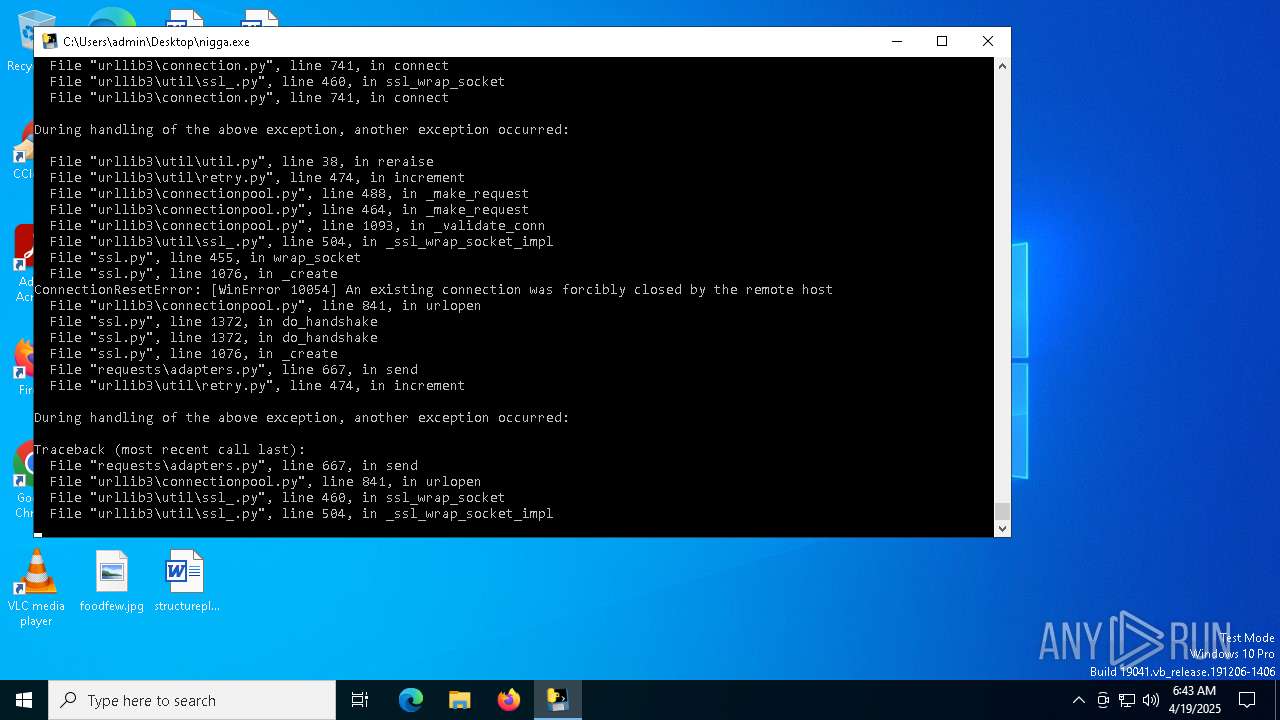
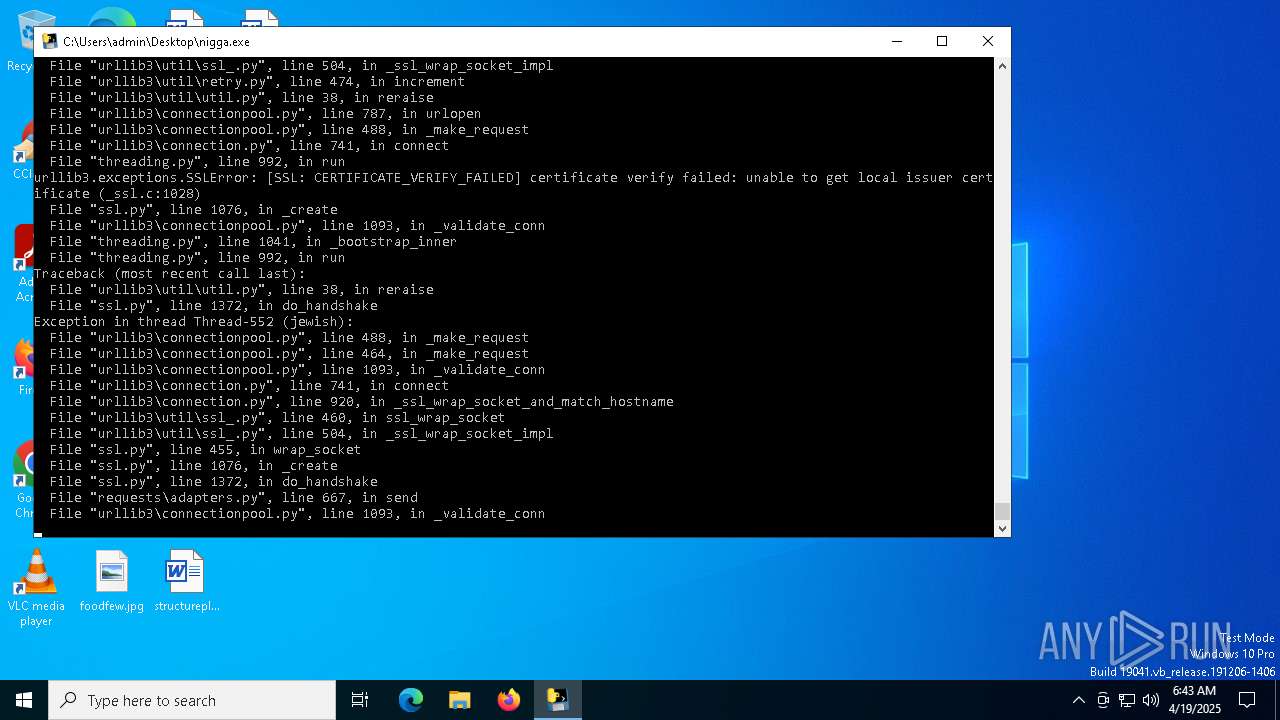
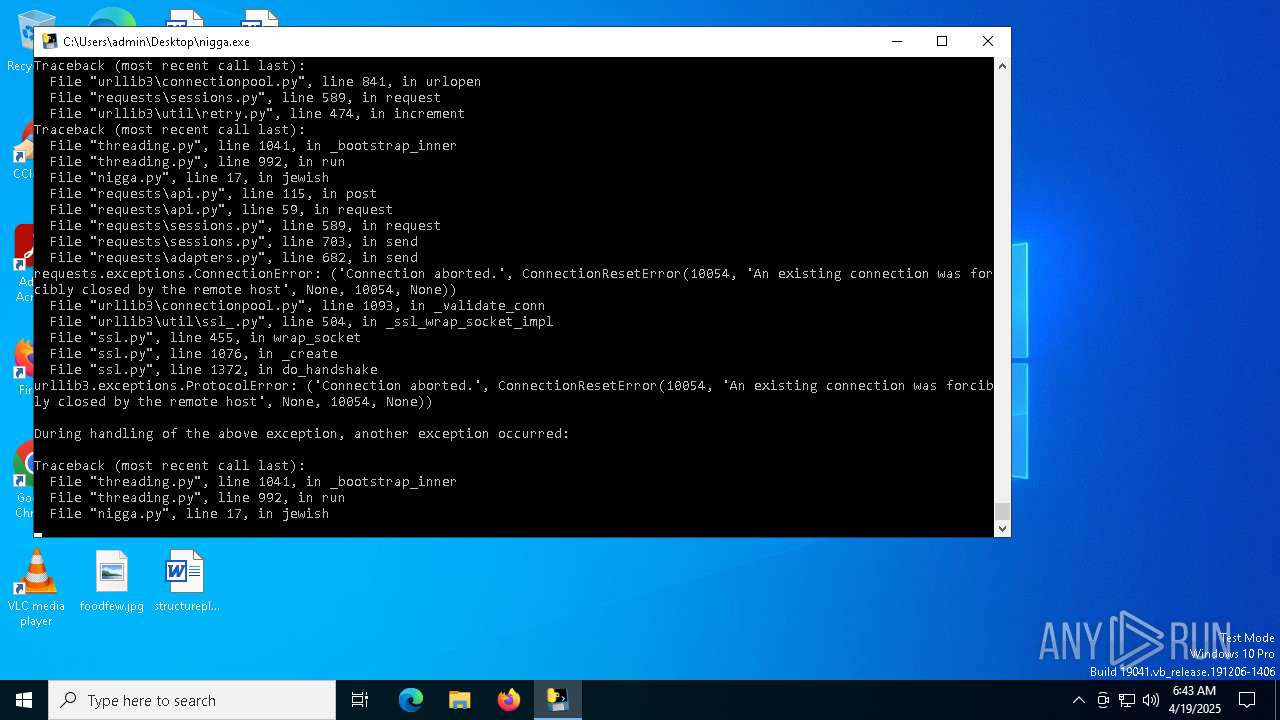
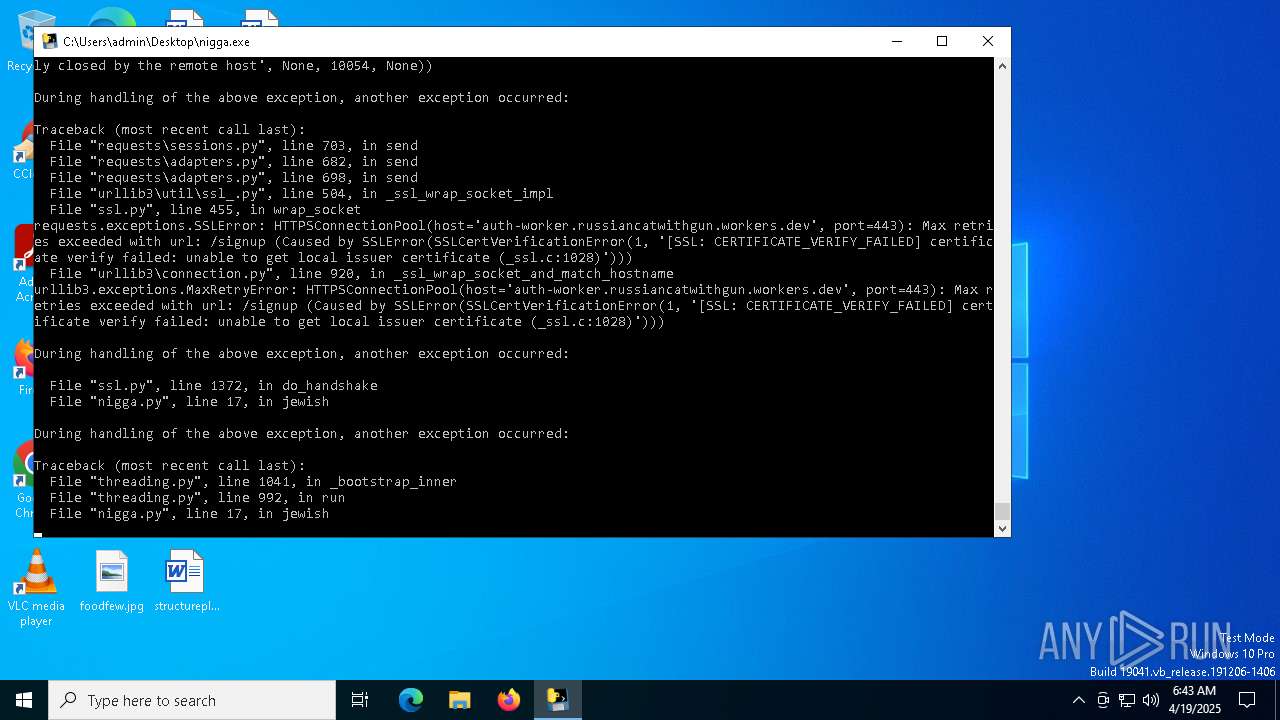
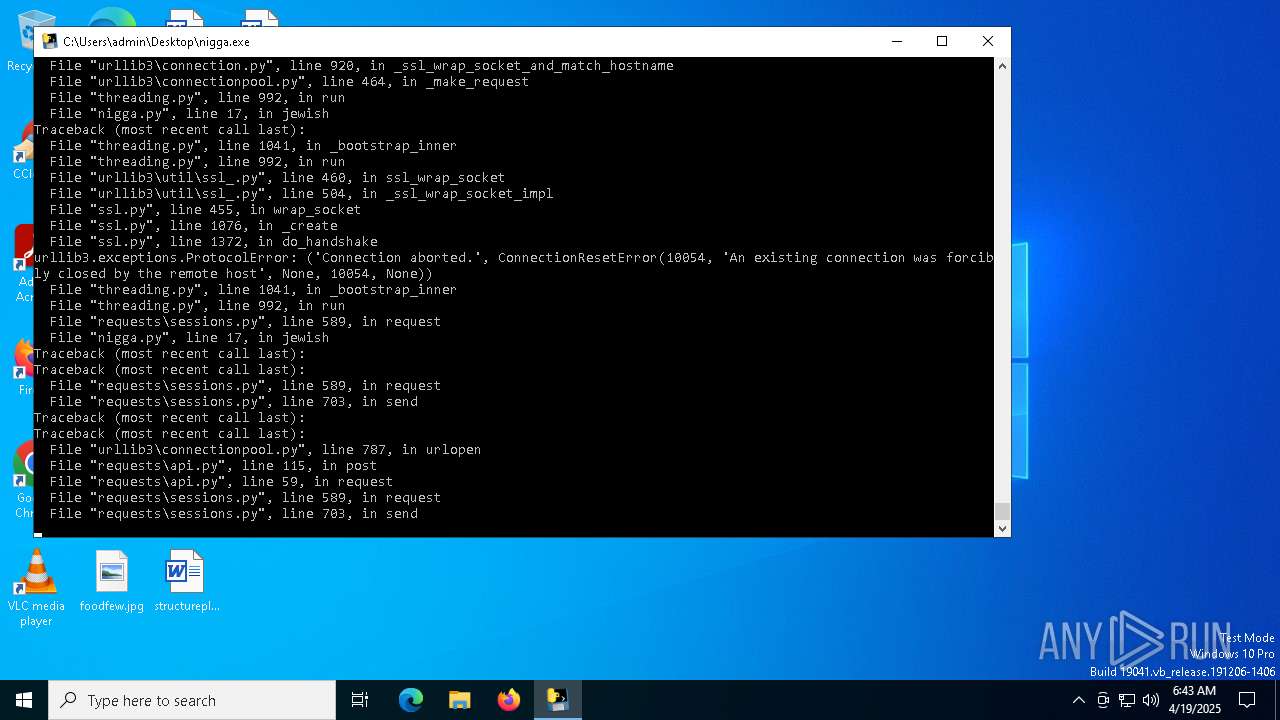
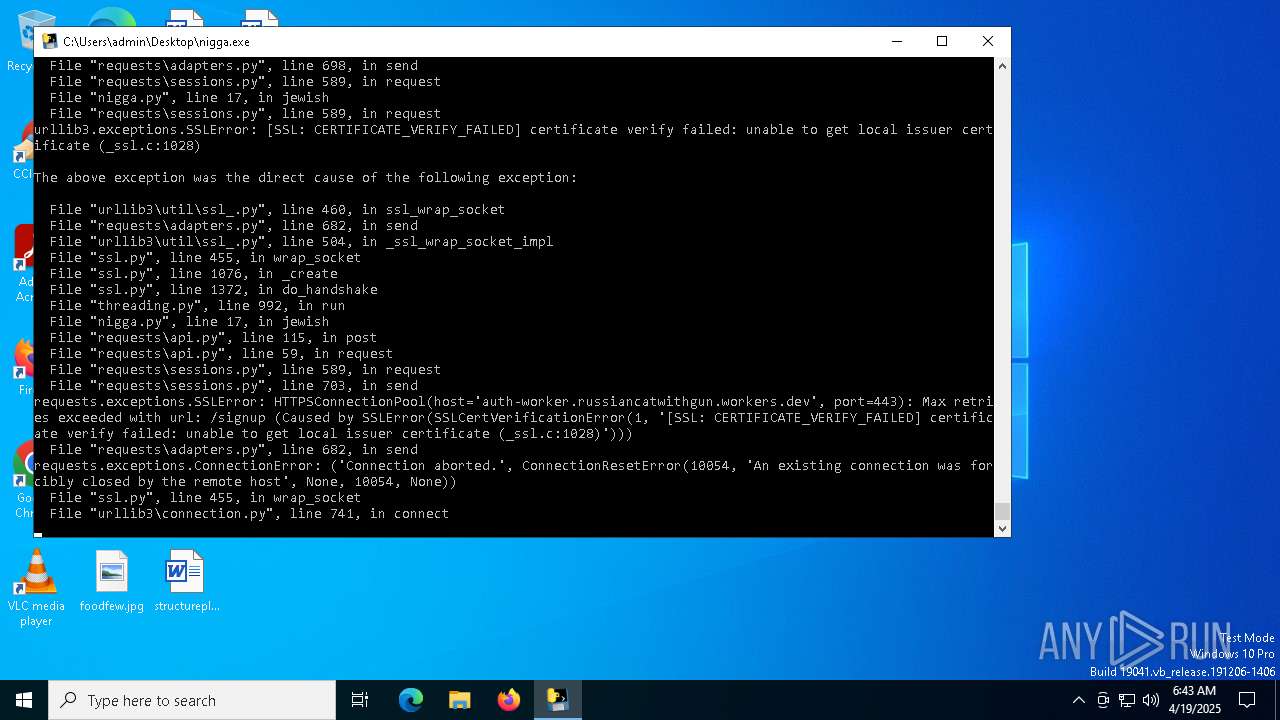
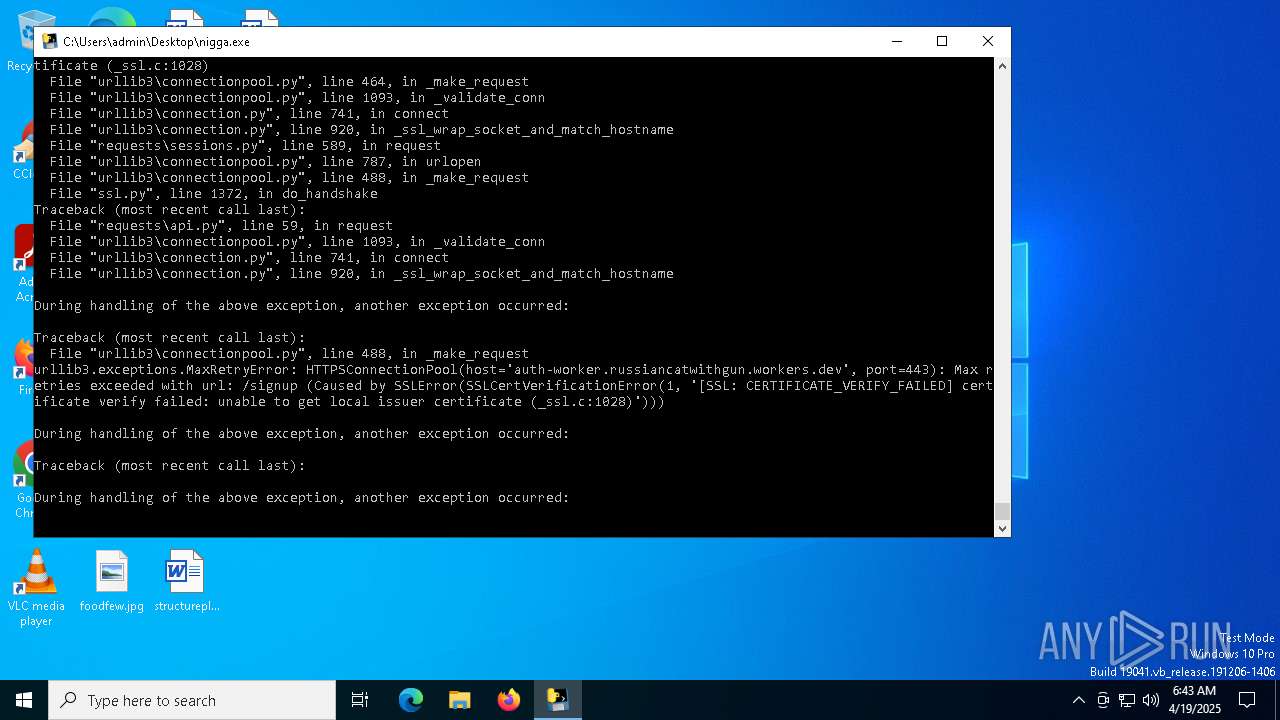
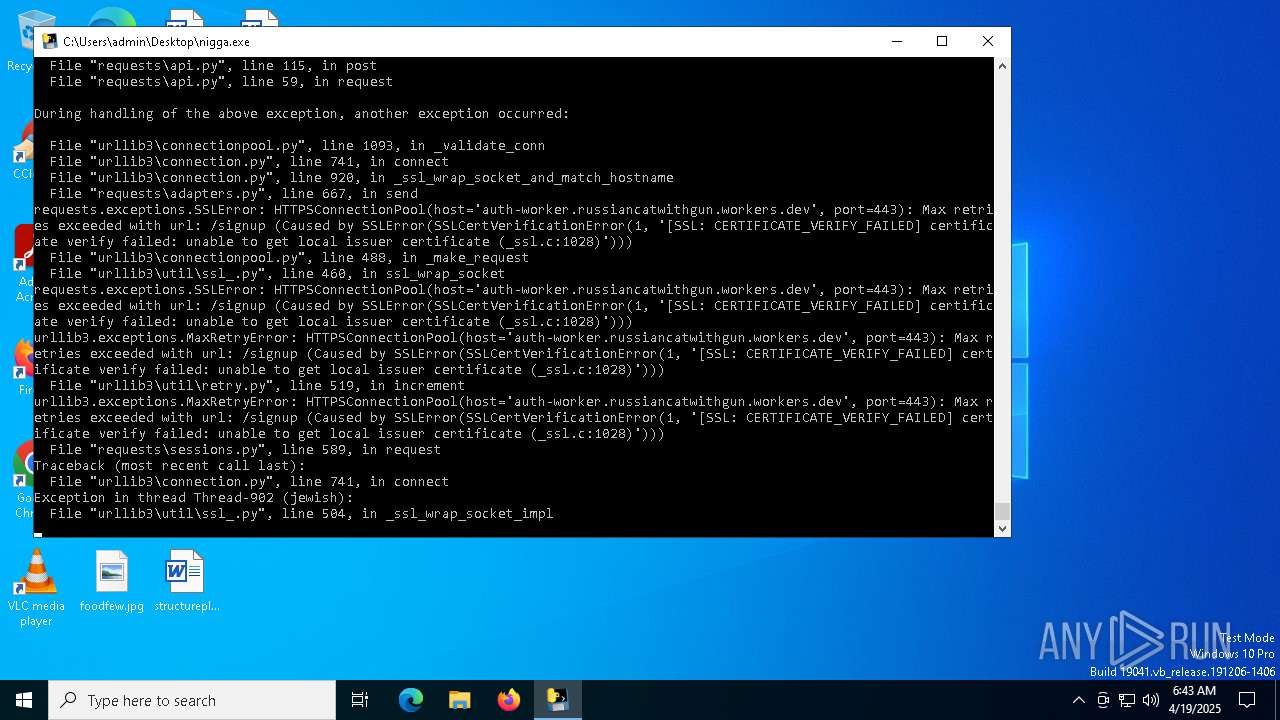
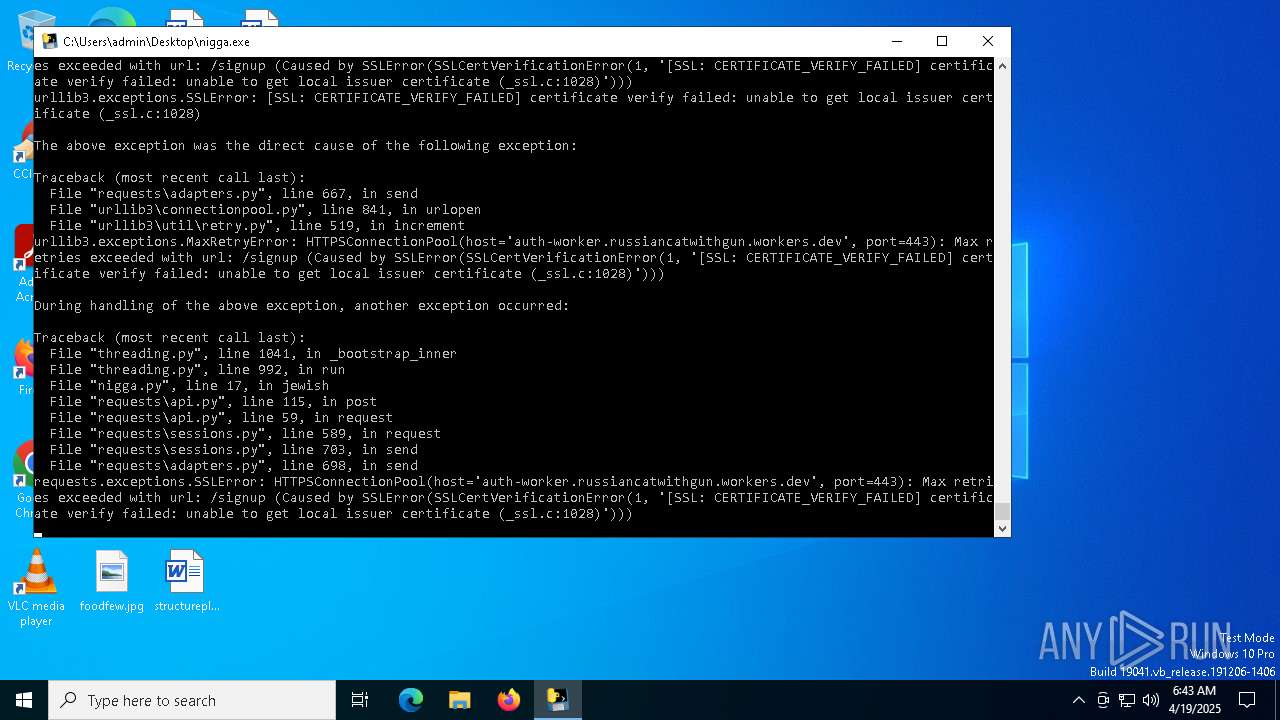
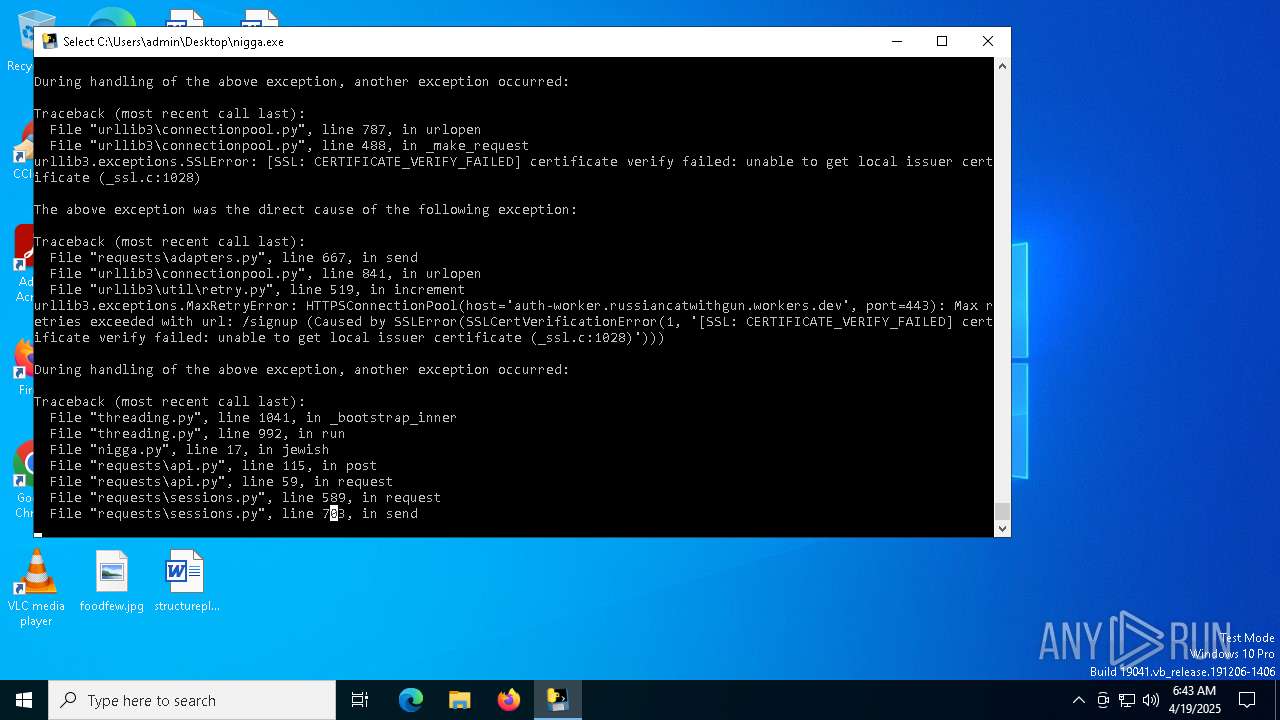
7652 | nigga.exe | 104.21.16.1:443 | auth-worker.russiancatwithgun.workers.dev | CLOUDFLARENET | — | shared |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
21788 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7652 | nigga.exe | 104.21.112.1:443 | auth-worker.russiancatwithgun.workers.dev | CLOUDFLARENET | — | shared |
7652 | nigga.exe | 104.21.96.1:443 | auth-worker.russiancatwithgun.workers.dev | CLOUDFLARENET | — | shared |
7456 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
auth-worker.russiancatwithgun.workers.dev |
| shared |
slscr.update.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] DNS Query to Cloudflare Worker App |
2196 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Cloudflare workers.dev Domain |
7652 | nigga.exe | Misc activity | ET INFO Observed Cloudflare workers.dev Domain in TLS SNI |
7652 | nigga.exe | Misc activity | ET INFO Observed Cloudflare workers.dev Domain in TLS SNI |
7652 | nigga.exe | Misc activity | ET INFO Observed Cloudflare workers.dev Domain in TLS SNI |
7652 | nigga.exe | Misc activity | ET INFO Observed Cloudflare workers.dev Domain in TLS SNI |
7652 | nigga.exe | Misc activity | ET INFO Observed Cloudflare workers.dev Domain in TLS SNI |
7652 | nigga.exe | Misc activity | ET INFO Observed Cloudflare workers.dev Domain in TLS SNI |
7652 | nigga.exe | Misc activity | ET INFO Observed Cloudflare workers.dev Domain in TLS SNI |
7652 | nigga.exe | Misc activity | ET INFO Observed Cloudflare workers.dev Domain in TLS SNI |