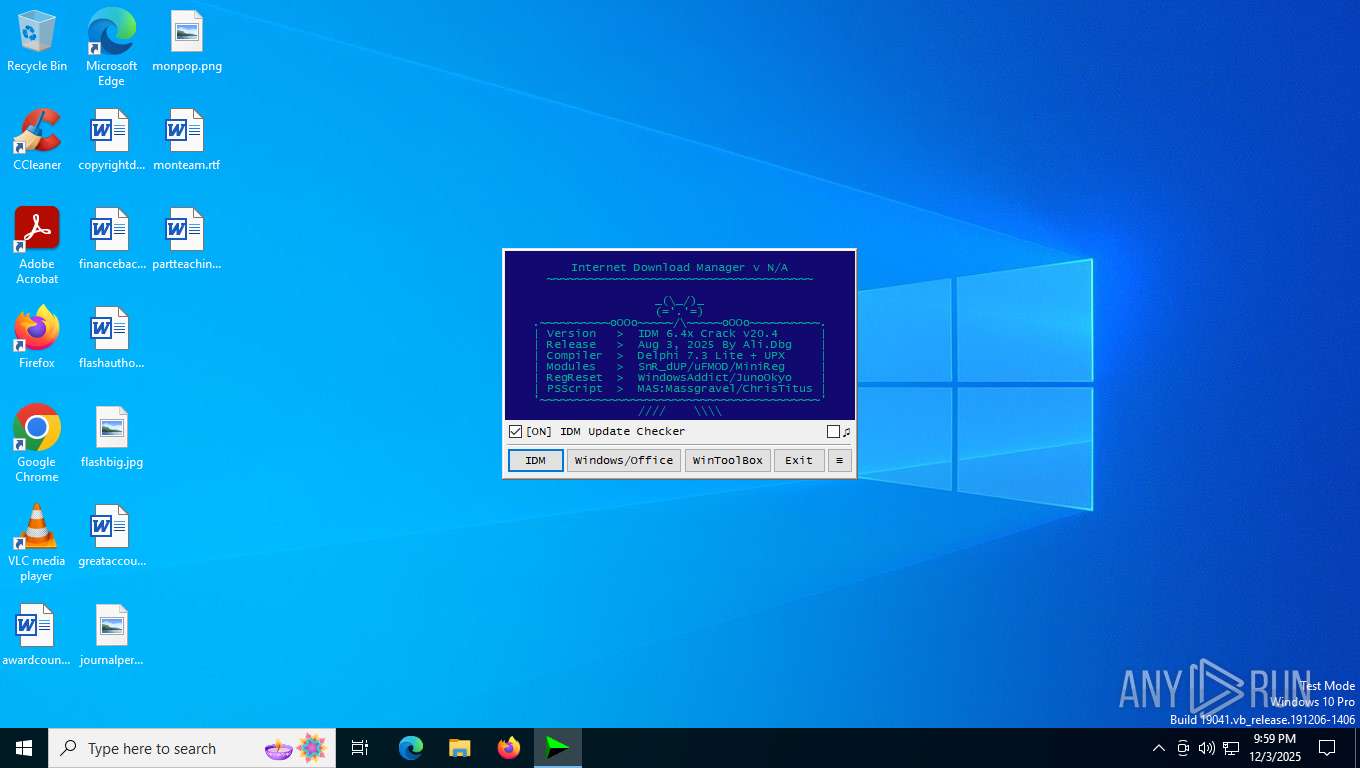
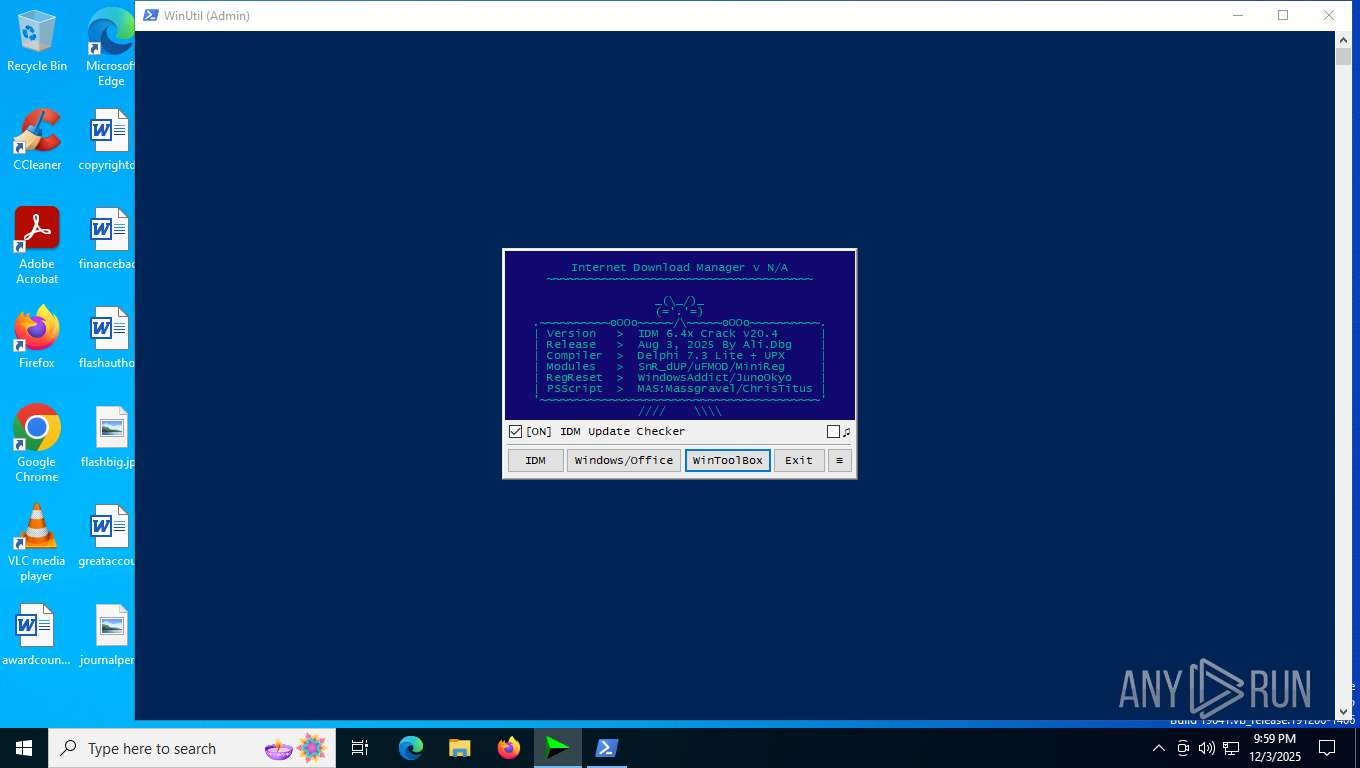
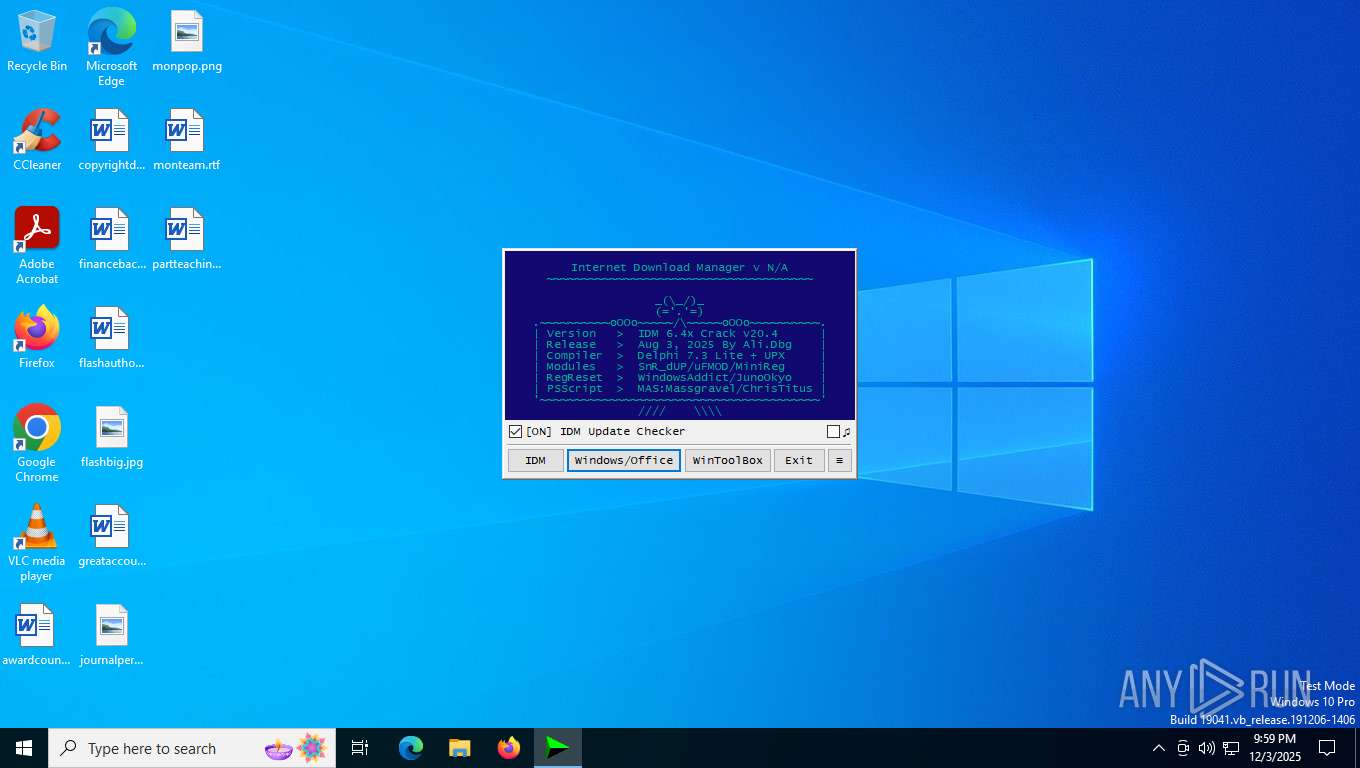
| File name: | IDM_6.4x_Crack_v20.4.exe |
| Full analysis: | https://app.any.run/tasks/64e9c1f3-5e48-42fd-8dcd-69061962a022 |
| Verdict: | Malicious activity |
| Threats: | DonutLoader is a versatile, open-source-based in-memory loader that turns .NET assemblies, executables, DLLs, and scripts into position-independent shellcode for execution entirely in RAM. Originally derived from the popular Donut tool, it enables threat actors to bypass traditional antivirus and EDR solutions by avoiding disk writes and injecting payloads directly into legitimate Windows processes. |
| Analysis date: | December 03, 2025, 21:58:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 13955B600A8D1AA1FFF5A805821259E4 |
| SHA1: | D86601200FD2CB55D49642BD96DEF60C9B0957ED |
| SHA256: | F25CFF1EEA2EE2C4001905405D674E7B7E9050A554B67A390B2777AE71A4850B |
| SSDEEP: | 1536:je+j44XYSLfuscW+yZELir92ZmyjvGVqRC4tPdUqEzGAV:je+04Xv2WtELir9uyqRJNdSzGAV |
MALICIOUS
DONUTLOADER has been found (auto)
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 2176)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 2176)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 2176)
Deletes a file (SCRIPT)
- wscript.exe (PID: 2176)
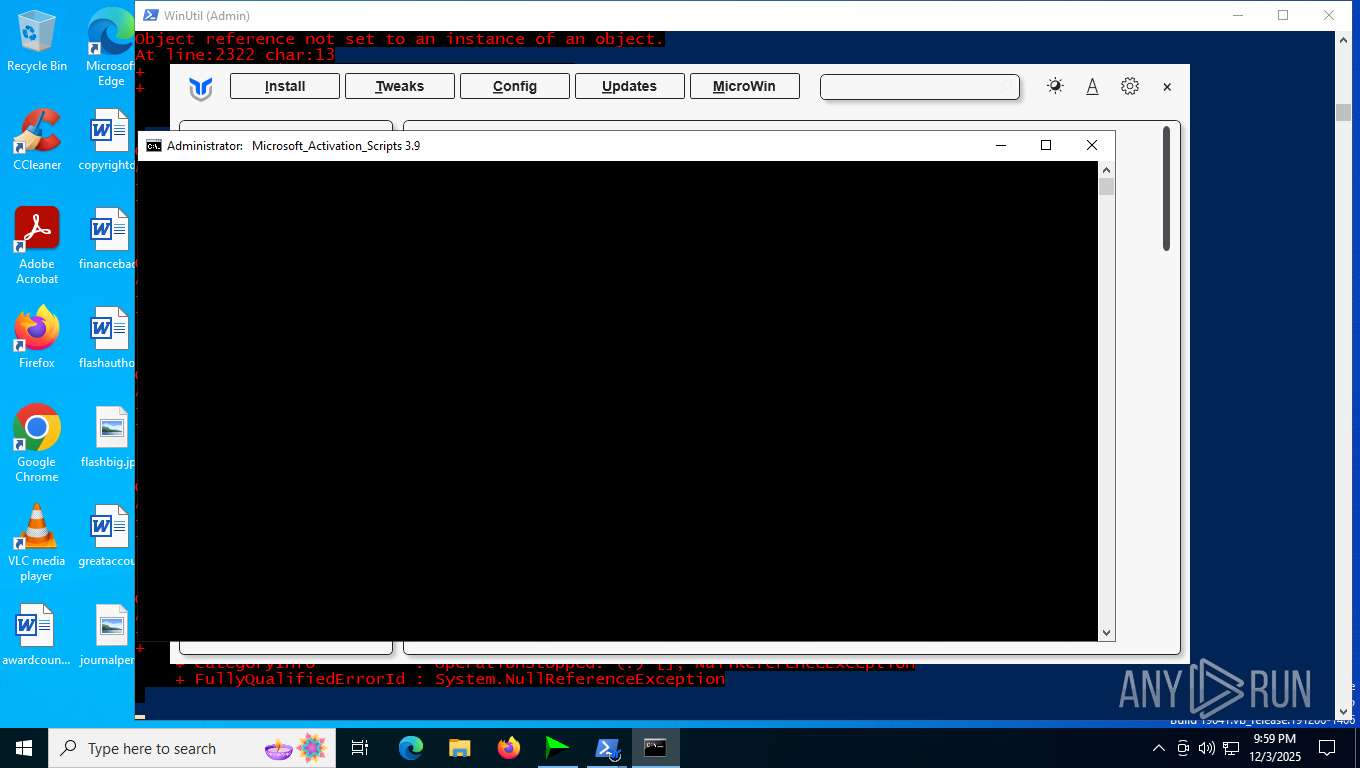
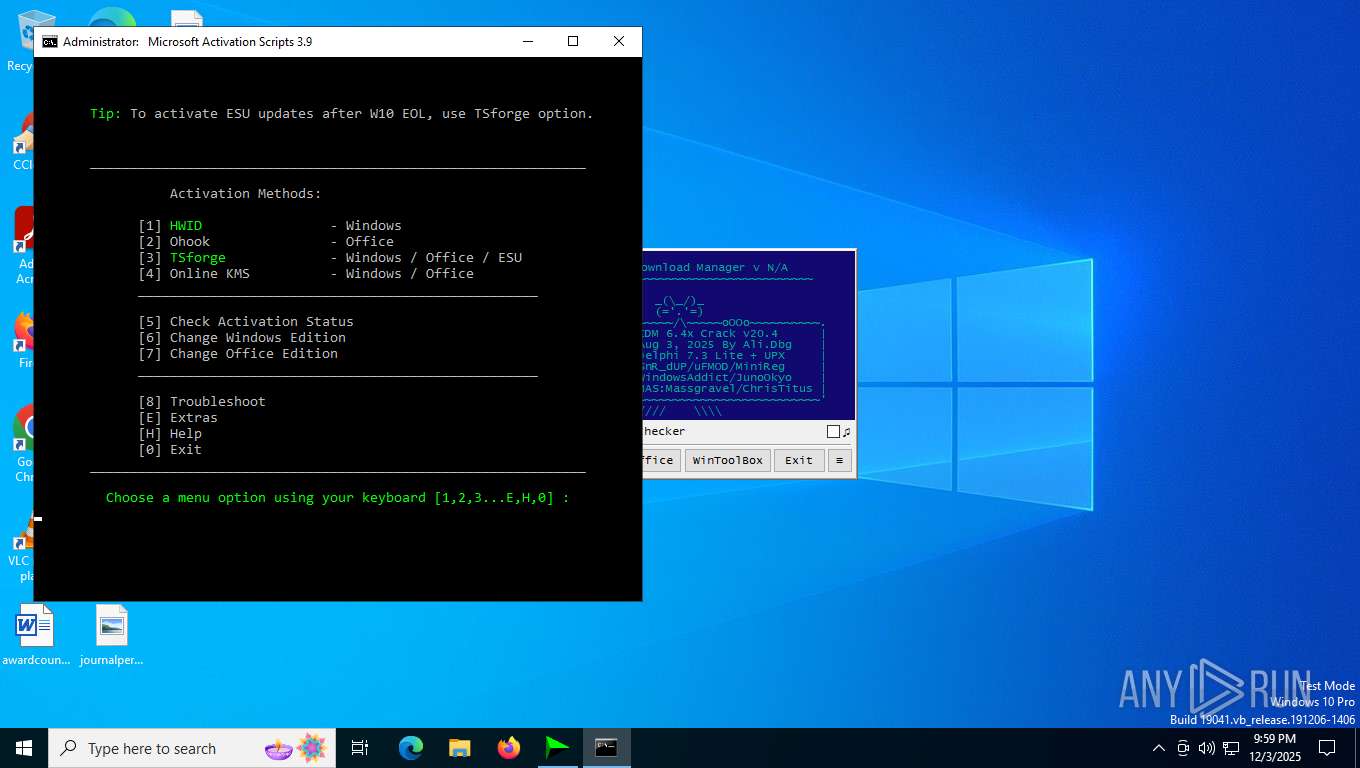
Changes powershell execution policy (Bypass)
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
- powershell.exe (PID: 8064)
- cmd.exe (PID: 4056)
Bypass execution policy to execute commands
- powershell.exe (PID: 7724)
- powershell.exe (PID: 8064)
- powershell.exe (PID: 4360)
- powershell.exe (PID: 4796)
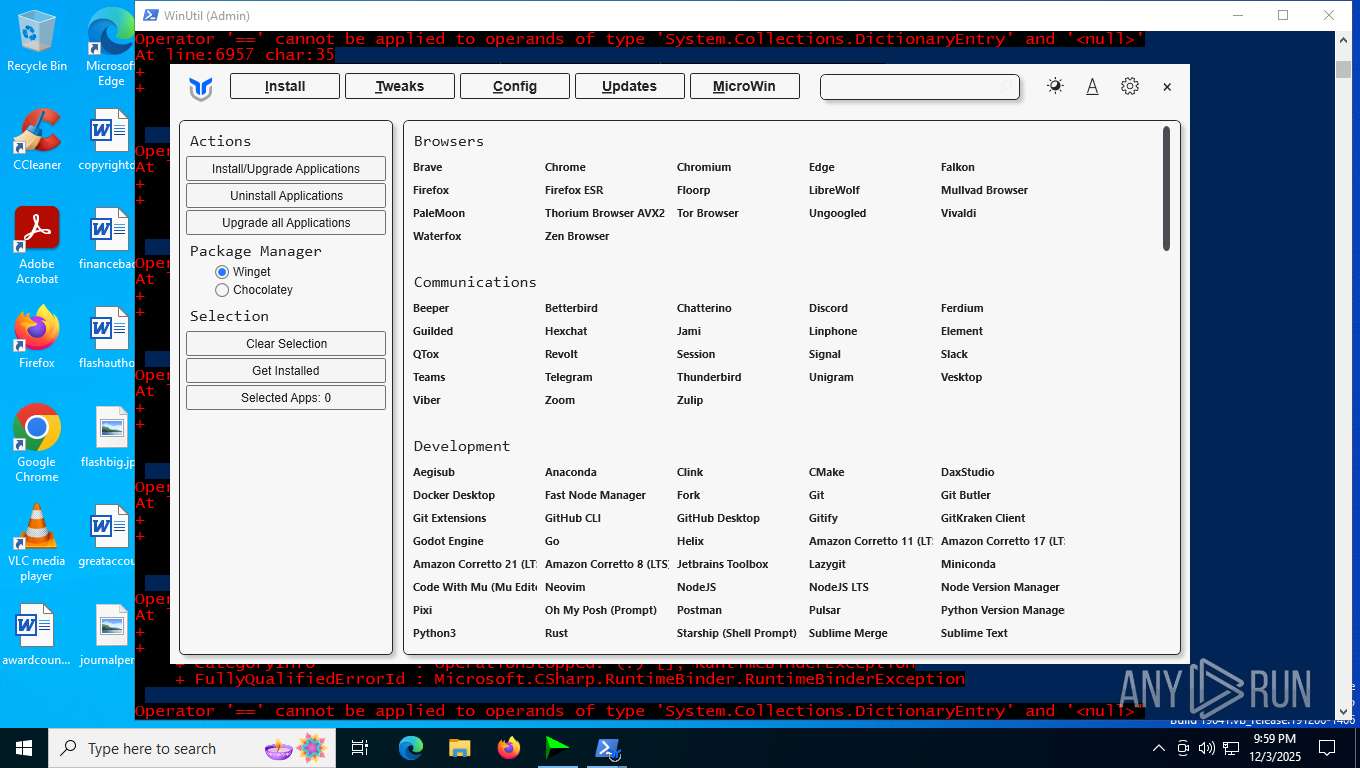
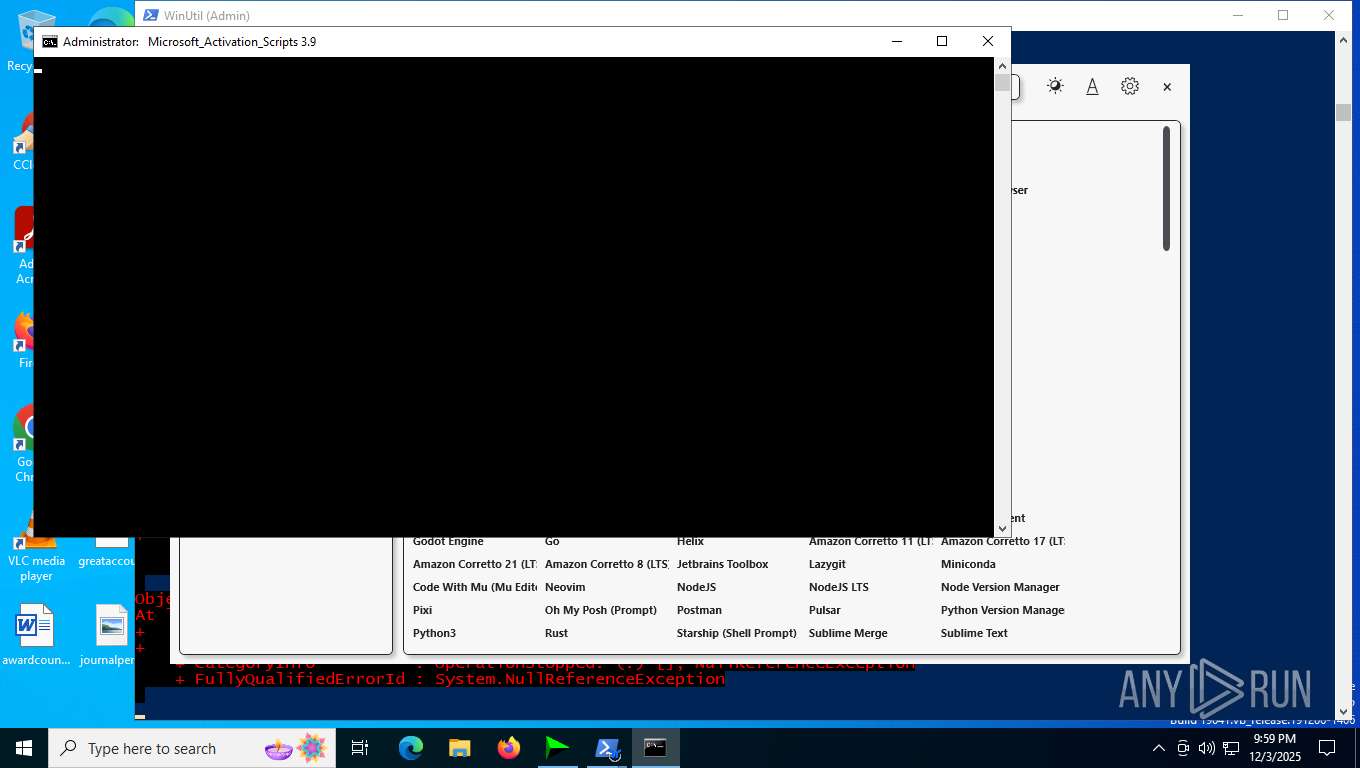
Starts Visual C# compiler
- powershell.exe (PID: 7724)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 7724)
Modifies registry (POWERSHELL)
- powershell.exe (PID: 8064)
Run PowerShell with an invisible window
- powershell.exe (PID: 4360)
- powershell.exe (PID: 4796)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2176)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 2176)
The process executes VB scripts
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 2176)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 2176)
Uses REG/REGEDIT.EXE to modify registry
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
- cmd.exe (PID: 7900)
- cmd.exe (PID: 4240)
- cmd.exe (PID: 7596)
Executing commands from a ".bat" file
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
- cmd.exe (PID: 4240)
Starts CMD.EXE for commands execution
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
- cmd.exe (PID: 4240)
- cmd.exe (PID: 2192)
- powershell.exe (PID: 4360)
- cmd.exe (PID: 7324)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 7736)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 1940)
Application launched itself
- cmd.exe (PID: 4240)
- cmd.exe (PID: 2192)
- powershell.exe (PID: 8064)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 7736)
- cmd.exe (PID: 1940)
- cmd.exe (PID: 8092)
Hides command output
- cmd.exe (PID: 7552)
- cmd.exe (PID: 7900)
- cmd.exe (PID: 2024)
- cmd.exe (PID: 4412)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 4240)
- cmd.exe (PID: 2024)
- cmd.exe (PID: 4412)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4240)
- cmd.exe (PID: 7552)
- cmd.exe (PID: 8016)
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
- powershell.exe (PID: 8064)
- cmd.exe (PID: 2024)
- cmd.exe (PID: 4412)
- cmd.exe (PID: 4056)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 4240)
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 7724)
The process bypasses the loading of PowerShell profile settings
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
- powershell.exe (PID: 8064)
- cmd.exe (PID: 2024)
- cmd.exe (PID: 4412)
- cmd.exe (PID: 4056)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 4360)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 2692)
The process hides Powershell's copyright startup banner
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
- powershell.exe (PID: 8064)
- cmd.exe (PID: 4056)
Creates a directory (POWERSHELL)
- powershell.exe (PID: 7724)
CSC.EXE is used to compile C# code
- csc.exe (PID: 7976)
Starts application with an unusual extension
- cmd.exe (PID: 4240)
Reads security settings of Internet Explorer
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
Executable content was dropped or overwritten
- csc.exe (PID: 7976)
The process executes Powershell scripts
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
- powershell.exe (PID: 8064)
- cmd.exe (PID: 4056)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 8064)
- powershell.exe (PID: 4360)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 8064)
Uses .NET C# to load dll
- powershell.exe (PID: 7724)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 4360)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 2692)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4360)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 2692)
Queries Computer System Information (Win32_ComputerSystem) (SCRIPT)
- powershell.exe (PID: 4360)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 2692)
Executing commands from ".cmd" file
- cmd.exe (PID: 7324)
- powershell.exe (PID: 4360)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 8092)
Windows service management via SC.EXE
- sc.exe (PID: 2920)
- sc.exe (PID: 7420)
Starts SC.EXE for service management
- cmd.exe (PID: 7596)
- cmd.exe (PID: 8092)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 4360)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7596)
- cmd.exe (PID: 8092)
Executes script without checking the security policy
- powershell.exe (PID: 8000)
- powershell.exe (PID: 2692)
Converts TXT file into a string
- powershell.exe (PID: 8000)
- powershell.exe (PID: 2692)
Removes files via Powershell
- powershell.exe (PID: 4796)
Manipulates environment variables
- powershell.exe (PID: 4796)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 4796)
INFO
Checks supported languages
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
- chcp.com (PID: 7400)
- cvtres.exe (PID: 8004)
- csc.exe (PID: 7976)
- mode.com (PID: 8124)
- mode.com (PID: 7564)
- mode.com (PID: 7228)
Creates files or folders in the user directory
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
Reads the computer name
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
Checks proxy server information
- wscript.exe (PID: 2176)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 8064)
- powershell.exe (PID: 4360)
Create files in a temporary directory
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
- reg.exe (PID: 8180)
- csc.exe (PID: 7976)
- cvtres.exe (PID: 8004)
Checks operating system version
- cmd.exe (PID: 4240)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 8092)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2412)
- powershell.exe (PID: 2192)
- powershell.exe (PID: 8064)
- powershell.exe (PID: 4360)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 2692)
Process checks computer location settings
- IDM_6.4x_Crack_v20.4.exe (PID: 3548)
Disables trace logs
- powershell.exe (PID: 7724)
- powershell.exe (PID: 8064)
- powershell.exe (PID: 4360)
Changes the display of characters in the console
- cmd.exe (PID: 4240)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 8064)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7724)
Reads mouse settings
- powershell.exe (PID: 7724)
Reads the machine GUID from the registry
- csc.exe (PID: 7976)
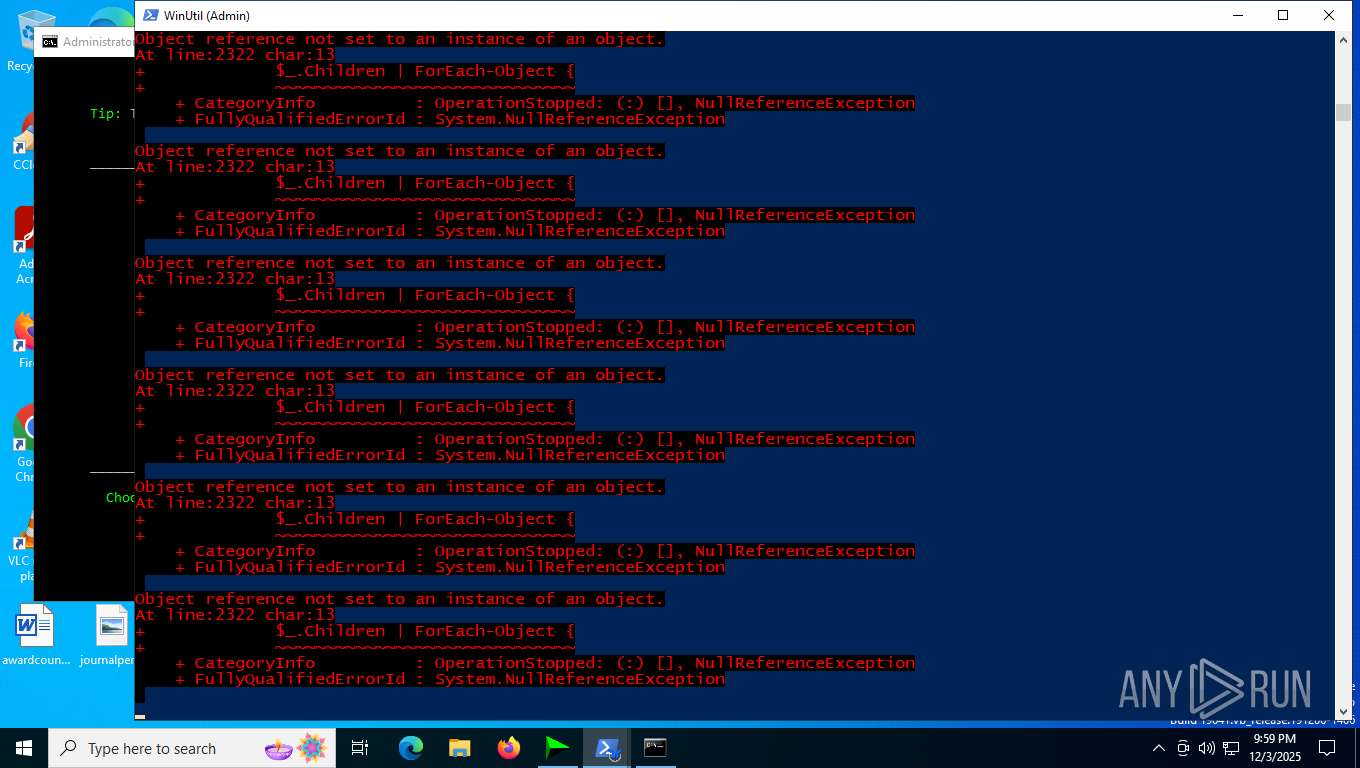
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7724)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 4360)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 2692)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 4360)
- powershell.exe (PID: 8000)
- powershell.exe (PID: 2692)
Starts MODE.COM to configure console settings
- mode.com (PID: 8124)
- mode.com (PID: 7564)
- mode.com (PID: 7228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 61440 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 188416 |
| EntryPoint: | 0x3d2b0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
284
Monitored processes
137
Malicious processes
15
Suspicious processes
1
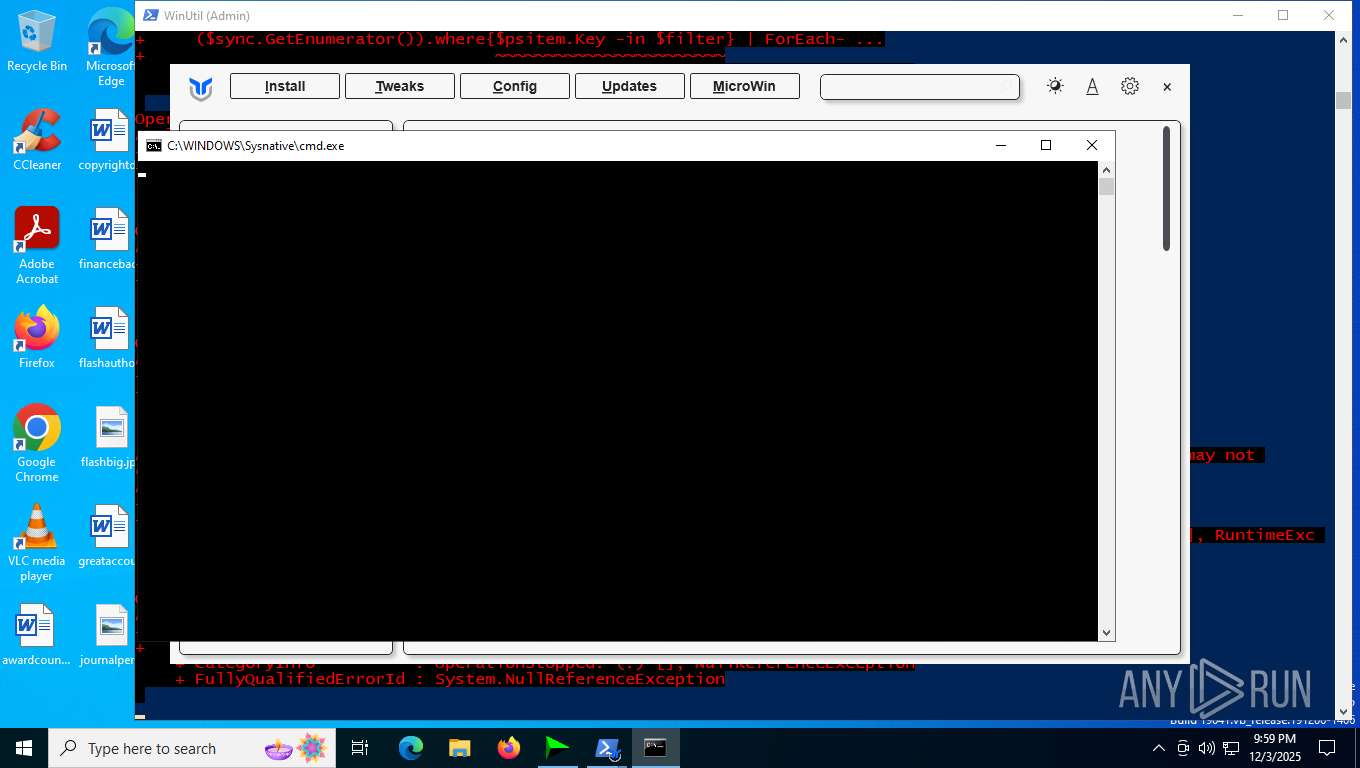
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 144 | reg.exe import C:\Users\admin\AppData\Local\Temp\IDMRegClean.reg | C:\Windows\SysWOW64\reg.exe | — | IDM_6.4x_Crack_v20.4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 144 | reg query "HKLM\SOFTWARE\Wow6432Node\Internet Download Manager" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 224 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "-el -qedit" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 272 | "C:\WINDOWS\system32\cmd.exe" /c "echo CMD is working" | C:\Windows\SysWOW64\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 476 | reg query "HKCU\Console" /v ForceV2 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | cmd | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | ping -n 1 updatecheck39.activated.win | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1664 | find /i "C:\Users\admin\AppData\Local\Temp" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1688 | reg query "HKCU\Software\DownloadManager" "/v" "scansk" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
66 266
Read events
66 208
Write events
43
Delete events
15
Modification events
| (PID) Process: | (3548) IDM_6.4x_Crack_v20.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (3548) IDM_6.4x_Crack_v20.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Wow6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (3548) IDM_6.4x_Crack_v20.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
| (PID) Process: | (3548) IDM_6.4x_Crack_v20.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
| (PID) Process: | (3548) IDM_6.4x_Crack_v20.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableCMD |
Value: 0 | |||
| (PID) Process: | (3548) IDM_6.4x_Crack_v20.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 0 | |||
| (PID) Process: | (3548) IDM_6.4x_Crack_v20.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoRun |
Value: 0 | |||
| (PID) Process: | (3548) IDM_6.4x_Crack_v20.4.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | DisallowRun |
Value: 0 | |||
| (PID) Process: | (3548) IDM_6.4x_Crack_v20.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\PowerShell |
| Operation: | write | Name: | EnableScripts |
Value: 1 | |||
| (PID) Process: | (3548) IDM_6.4x_Crack_v20.4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\PowerShell\1\ShellIds\ScriptedDiagnostics |
| Operation: | write | Name: | ExecutionPolicy |
Value: Bypass | |||
Executable files
1
Suspicious files
16
Text files
41
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3548 | IDM_6.4x_Crack_v20.4.exe | C:\Users\admin\AppData\Local\Temp\CRK_UPDT.vbs | text | |
MD5:B91C1157D6F1E605CC965D092551B307 | SHA256:92FE72CCEB630C7EFF3B2D3BED9C6969F53E5B9DFF1F481888754E59B3C76AB7 | |||
| 3548 | IDM_6.4x_Crack_v20.4.exe | C:\Users\admin\AppData\Local\Temp\IDM_UPDT.vbs | text | |
MD5:B91C1157D6F1E605CC965D092551B307 | SHA256:92FE72CCEB630C7EFF3B2D3BED9C6969F53E5B9DFF1F481888754E59B3C76AB7 | |||
| 2412 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:B462E86F762704560963BD179D53E373 | SHA256:8D461F07B16A6167CE25387F9BF4DA1A5E6836D5884CF85B612600C0F6044334 | |||
| 7268 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hkfauulp.xyn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7268 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2e204zbu.gxo.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7568 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sikhrvmq.krn.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7568 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_v1hz0xiz.wjw.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8032 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0itdbpfi.i2e.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8180 | reg.exe | C:\Windows\Temp\_Backup_HKCU_CLSID_20251203-215918499.reg | text | |
MD5:345823A0BDDB596A43415D67C9880B8A | SHA256:D9CB0467BD3FC677837C380F3A7D5C69291E001B210907FD302B3CE61FF98682 | |||
| 8180 | reg.exe | C:\Users\admin\AppData\Local\Temp\REG57D9.tmp | text | |
MD5:345823A0BDDB596A43415D67C9880B8A | SHA256:D9CB0467BD3FC677837C380F3A7D5C69291E001B210907FD302B3CE61FF98682 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
31
DNS requests
25
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2176 | wscript.exe | GET | 200 | 216.58.206.67:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
2176 | wscript.exe | GET | 200 | 216.58.206.67:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
696 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2764 | svchost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7676 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7676 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7676 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
7676 | SIHClient.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7676 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
7676 | SIHClient.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
696 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5596 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7096 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 92.123.104.16:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
2176 | wscript.exe | 188.114.96.3:443 | idm.0dy.ir | CLOUDFLARENET | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
2176 | wscript.exe | 216.58.206.67:80 | c.pki.goog | GOOGLE | US | whitelisted |
696 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
696 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
idm.0dy.ir |
| malicious |
c.pki.goog |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
— | — | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Potentially Bad Traffic | ET INFO PS1 Powershell File Request |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Check Security.Principal.WindowsBuiltInRole has been detected |
— | — | Misc activity | SUSPICIOUS [ANY.RUN] The Principal.WindowsIdentity in PS.Script has been detected |
— | — | Potentially Bad Traffic | ET ATTACK_RESPONSE PowerShell NoProfile Command Received In Powershell Stagers |