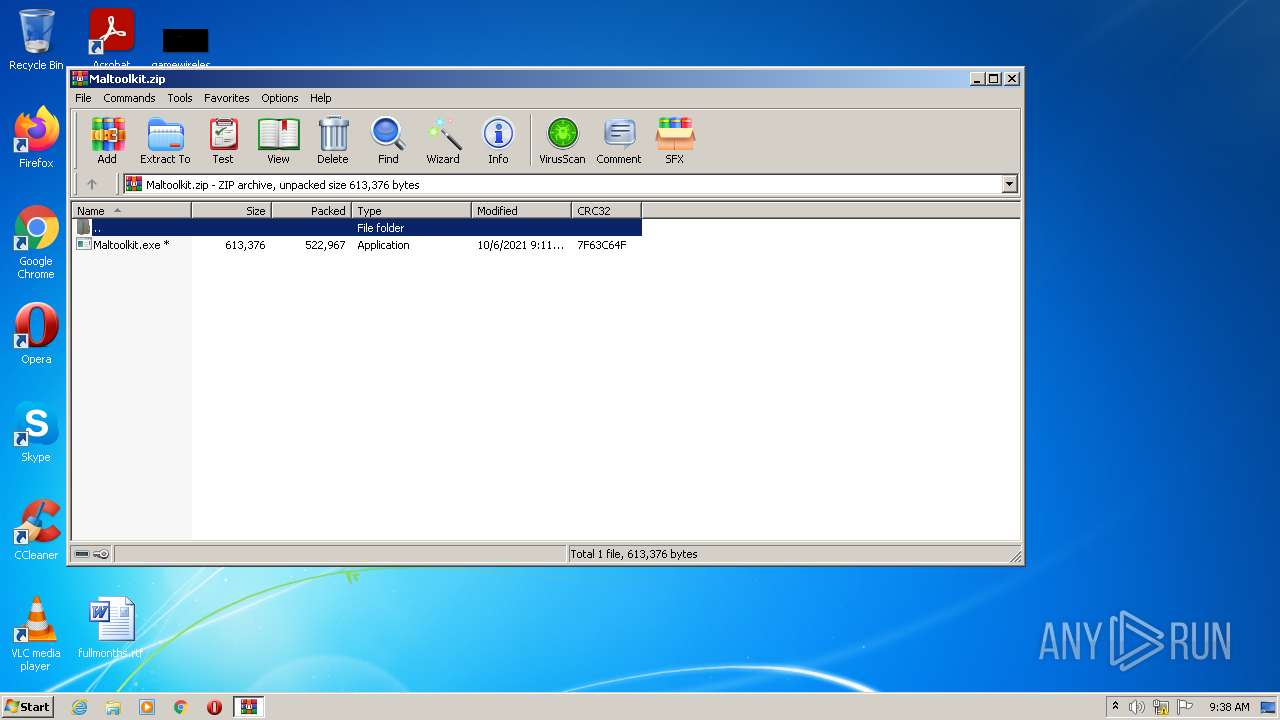
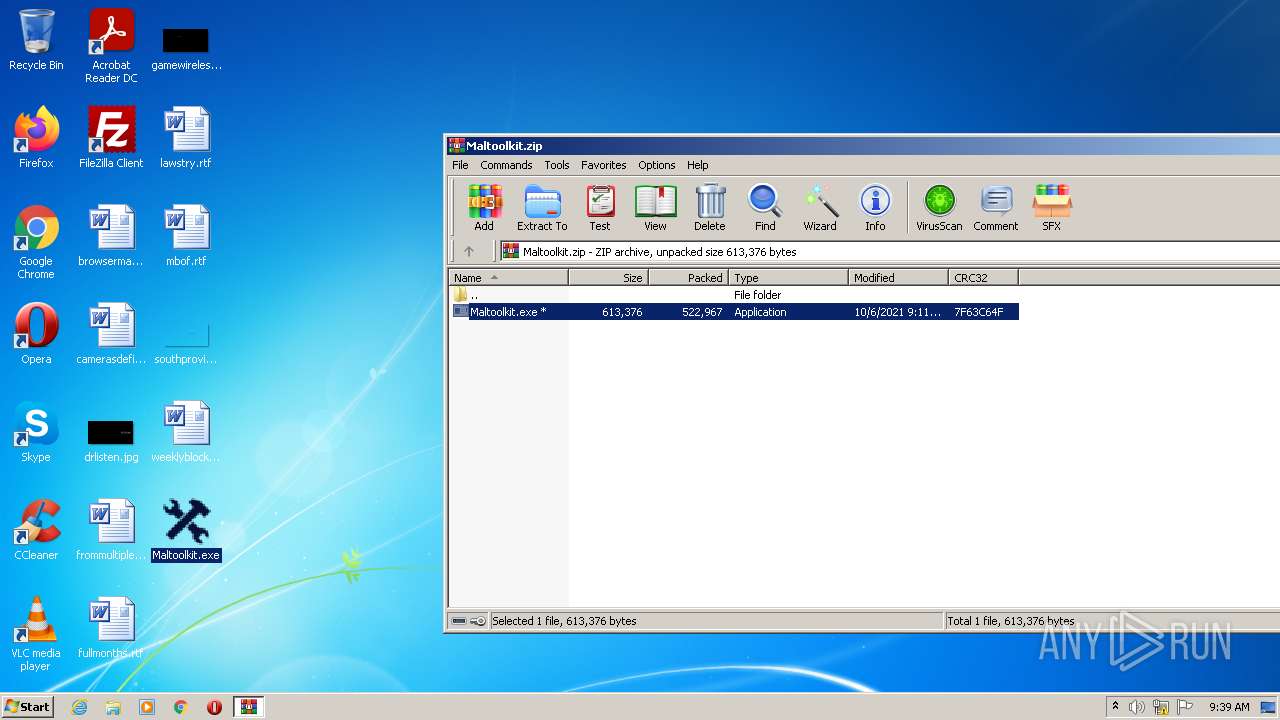
| File name: | Maltoolkit.zip |
| Full analysis: | https://app.any.run/tasks/b09dd8ab-2729-4ae5-bf0e-76501a8fbba8 |
| Verdict: | Malicious activity |
| Analysis date: | February 25, 2022, 09:38:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 1AF0EDA61692DEE4EFFC5FC35AD66B76 |
| SHA1: | 2A633D155A0BC21B38DDCBB2BDD63F688426D9A7 |
| SHA256: | F257D6C0DEFEDF6386D2446C59E19D830A97F9B909AFFB411C60E3A18FD1E5CF |
| SSDEEP: | 6144:XXLd4nKz7D0+JAAyEP089PaMluholIyiLeAo8AwFsqJgQmjyPtMUXEK2fa5UJ43u:x4nOgGFyMNlDiLxNAw1gQpK5a5CyTciq |
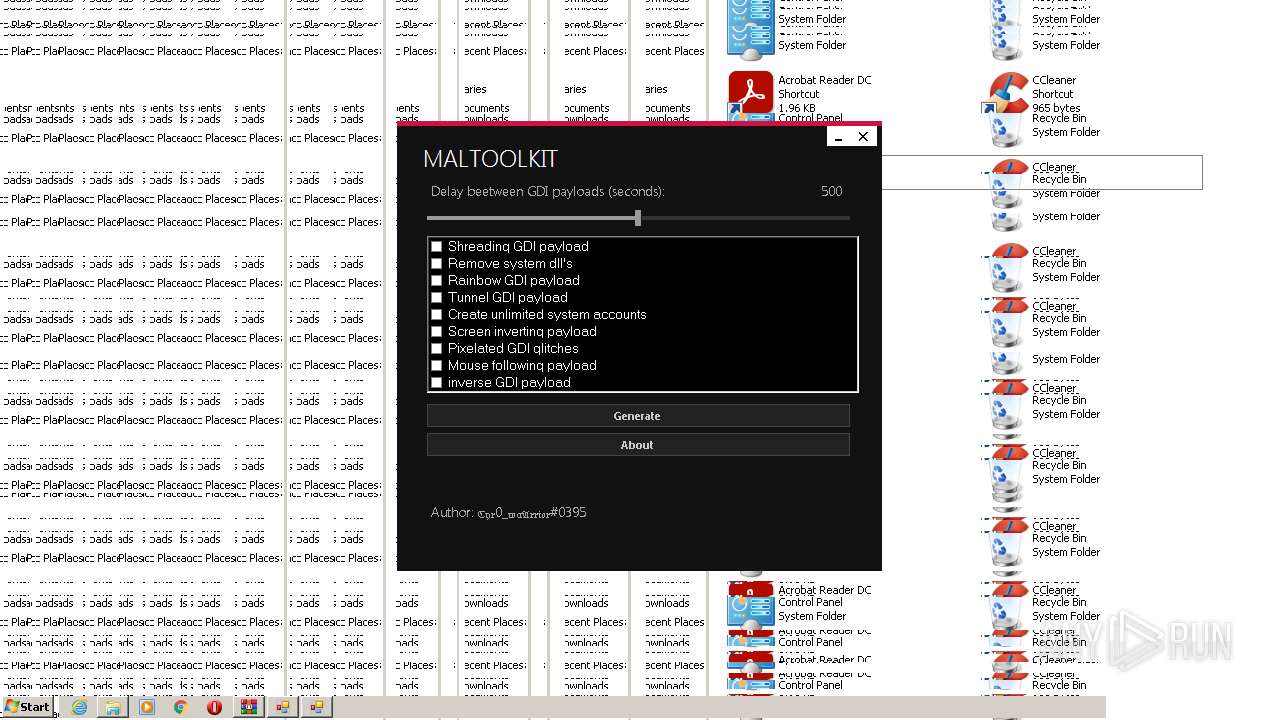
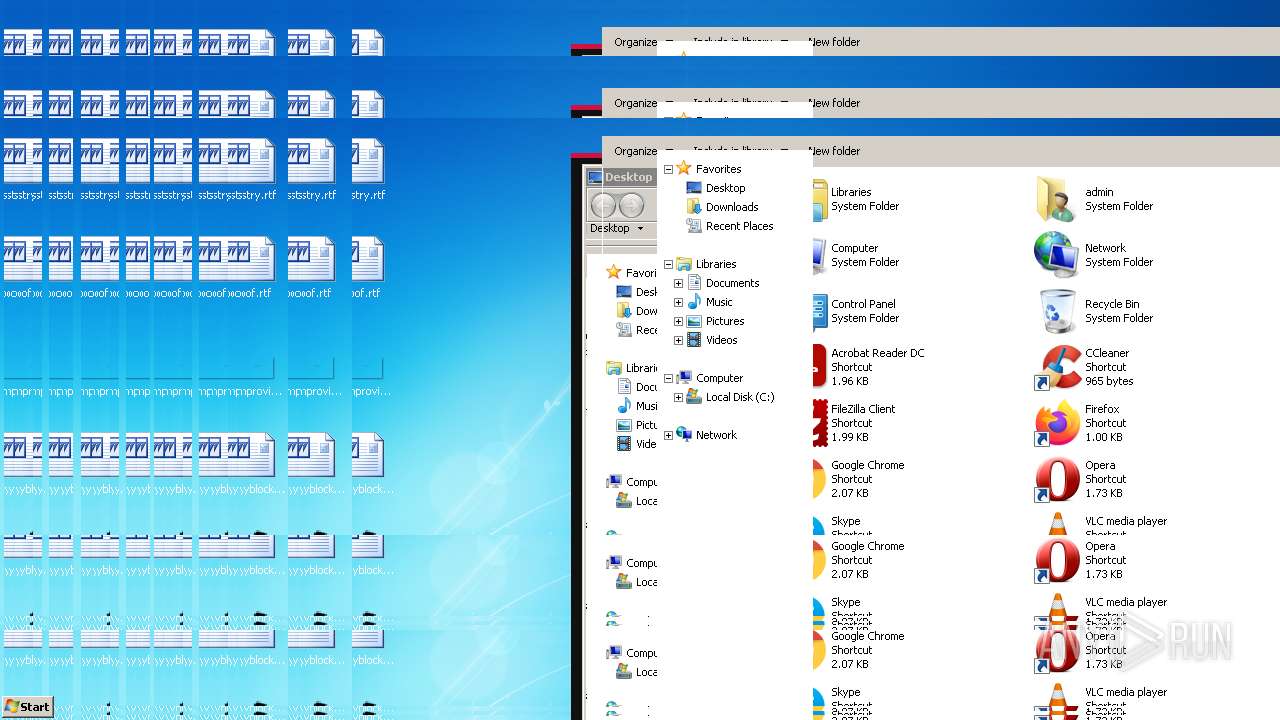
MALICIOUS
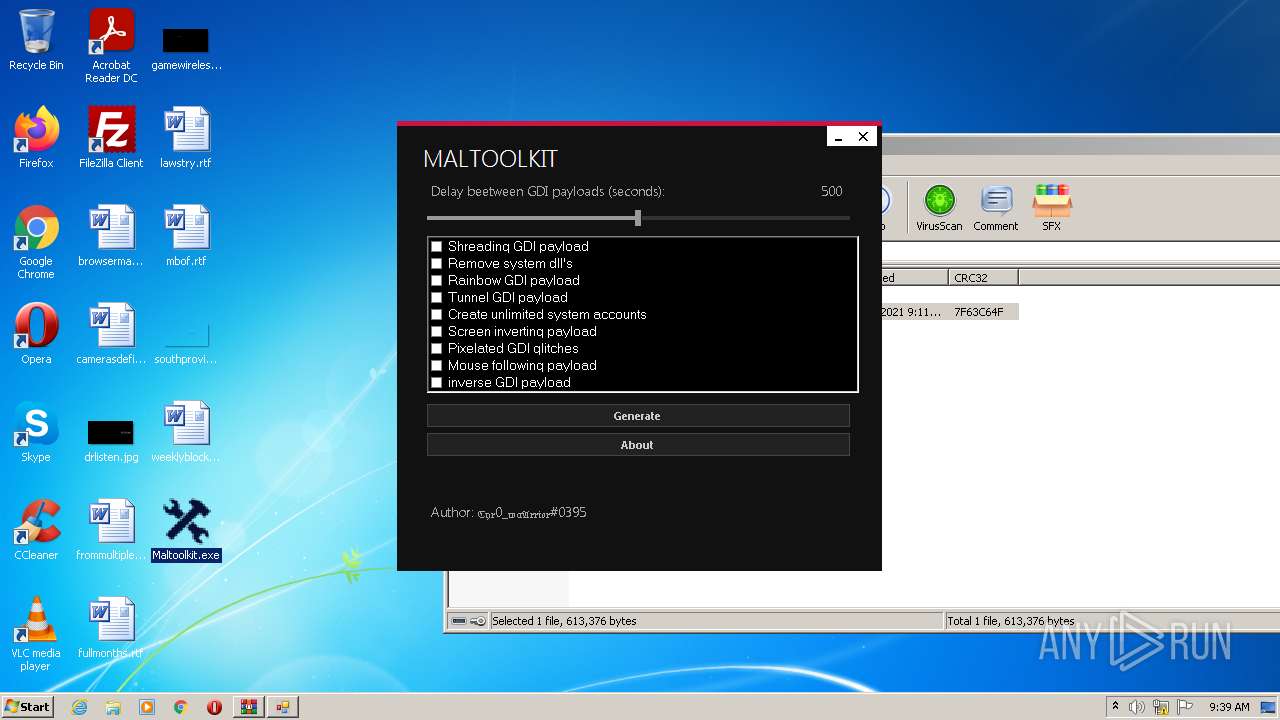
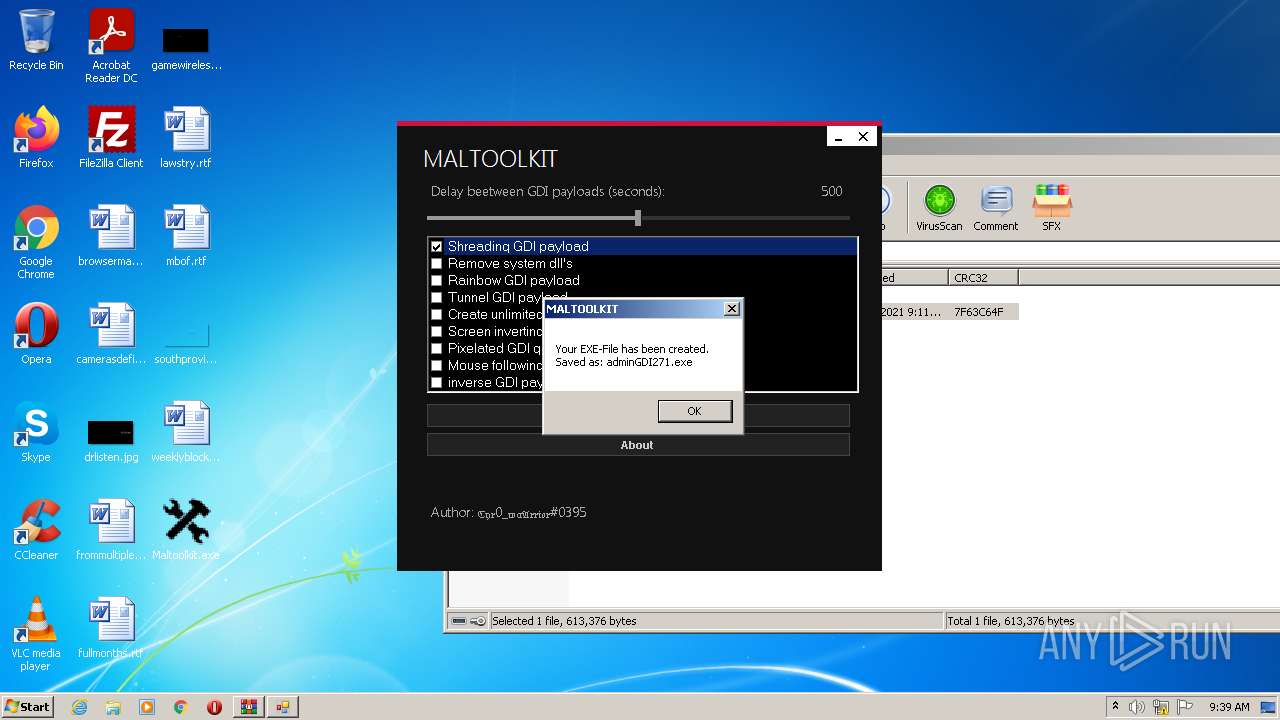
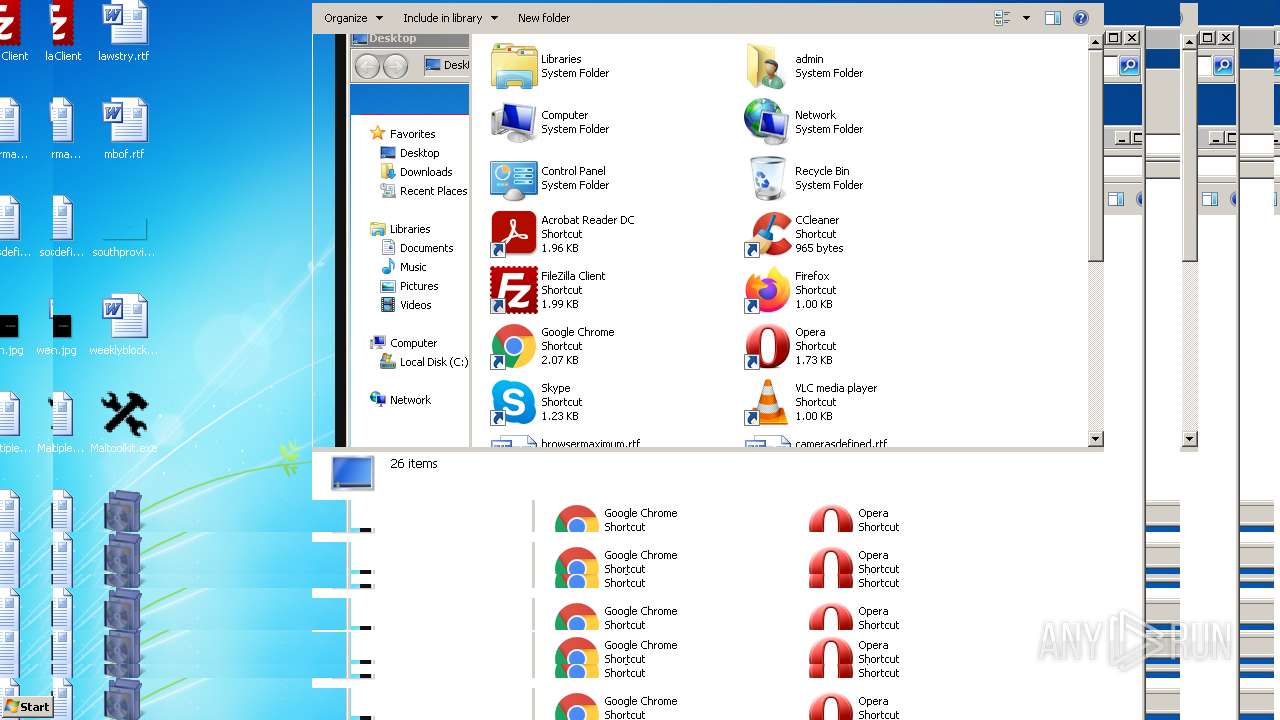
Application was dropped or rewritten from another process
- Maltoolkit.exe (PID: 3664)
- Maltoolkit.exe (PID: 3936)
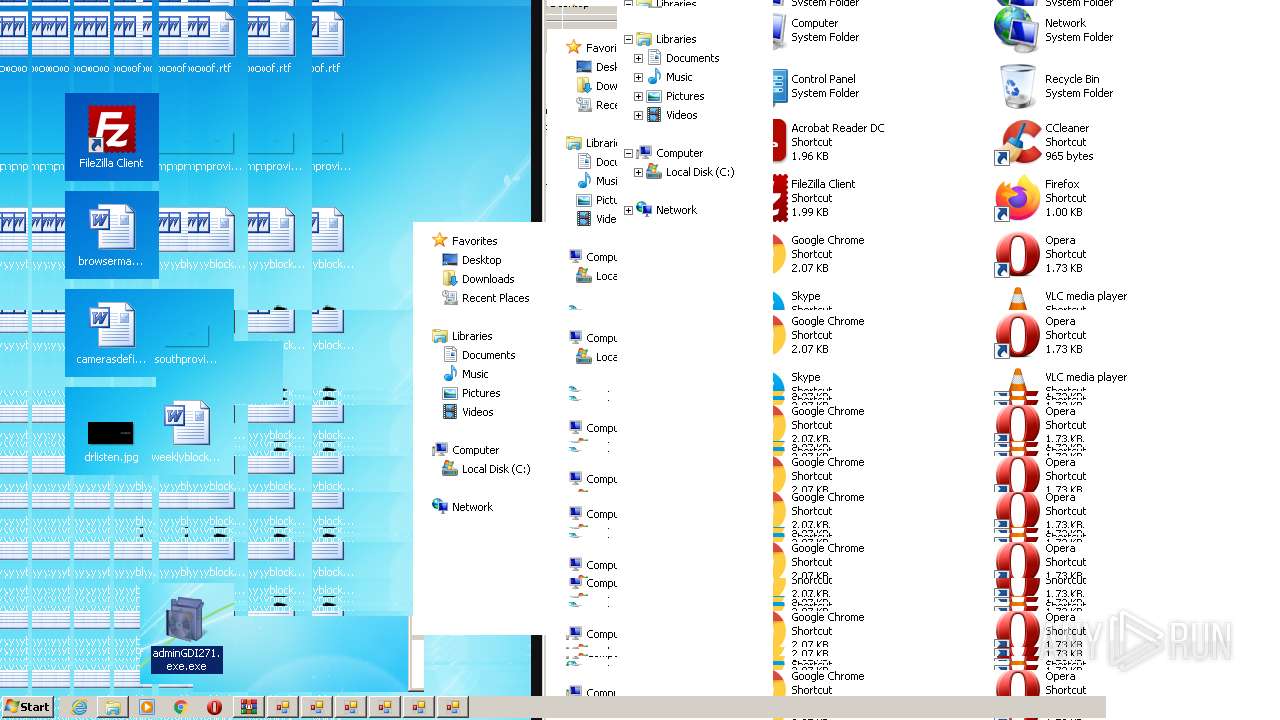
- adminGDI271.exe.exe (PID: 2180)
- Maltoolkit.exe (PID: 3608)
- adminGDI271.exe.exe (PID: 1936)
- adminGDI271.exe.exe (PID: 3068)
- adminGDI271.exe.exe (PID: 2840)
- Maltoolkit.exe (PID: 3008)
- adminGDI271.exe.exe (PID: 2252)
- Maltoolkit.exe (PID: 2352)
- Maltoolkit.exe (PID: 2092)
- adminGDI271.exe.exe (PID: 328)
- Maltoolkit.exe (PID: 2880)
Runs app for hidden code execution
- Maltoolkit.exe (PID: 3664)
Drops executable file immediately after starts
- adminGDI271.exe.exe (PID: 2180)
- adminGDI271.exe.exe (PID: 3068)
- adminGDI271.exe.exe (PID: 1936)
- adminGDI271.exe.exe (PID: 2840)
- adminGDI271.exe.exe (PID: 2252)
- adminGDI271.exe.exe (PID: 328)
SUSPICIOUS
Reads the computer name
- Maltoolkit.exe (PID: 3664)
- WinRAR.exe (PID: 3560)
- Maltoolkit.exe (PID: 3936)
- Maltoolkit.exe (PID: 3608)
- Maltoolkit.exe (PID: 2352)
- Maltoolkit.exe (PID: 3008)
- Maltoolkit.exe (PID: 2092)
- Maltoolkit.exe (PID: 2880)
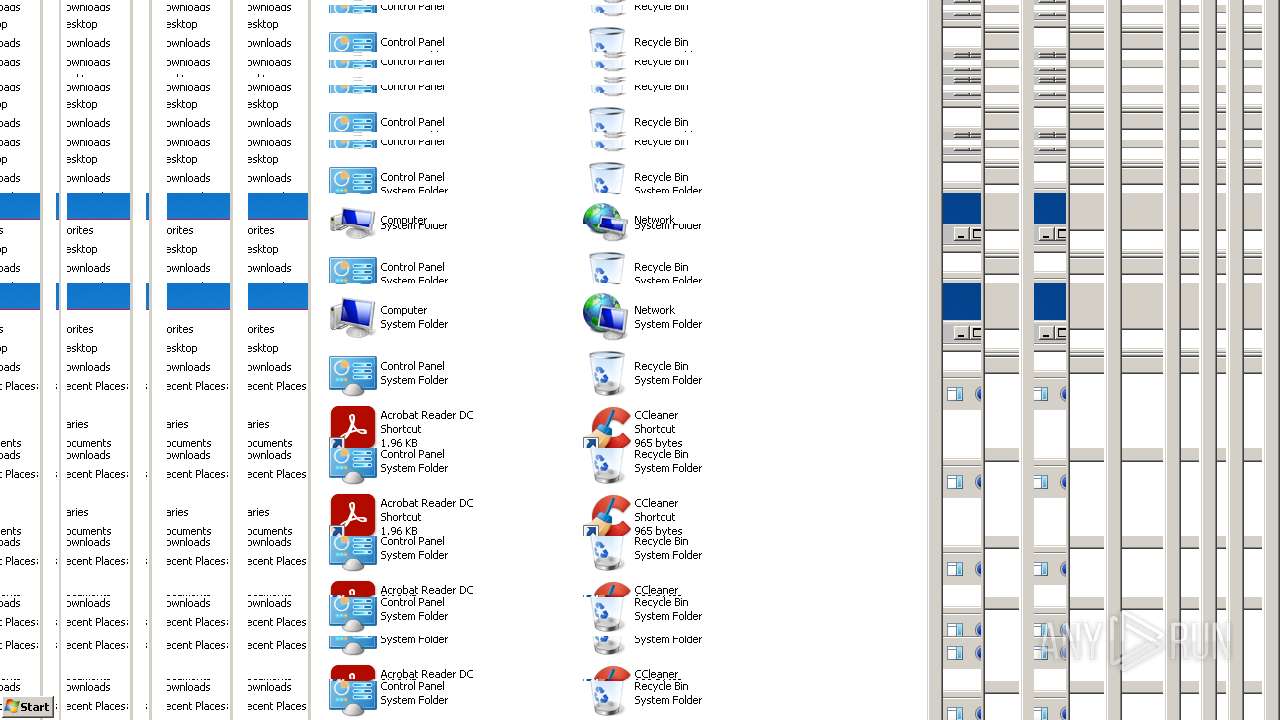
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3560)
- adminGDI271.exe.exe (PID: 2180)
- iexpress.exe (PID: 300)
- adminGDI271.exe.exe (PID: 3068)
- adminGDI271.exe.exe (PID: 2840)
- adminGDI271.exe.exe (PID: 1936)
- adminGDI271.exe.exe (PID: 2252)
- adminGDI271.exe.exe (PID: 328)
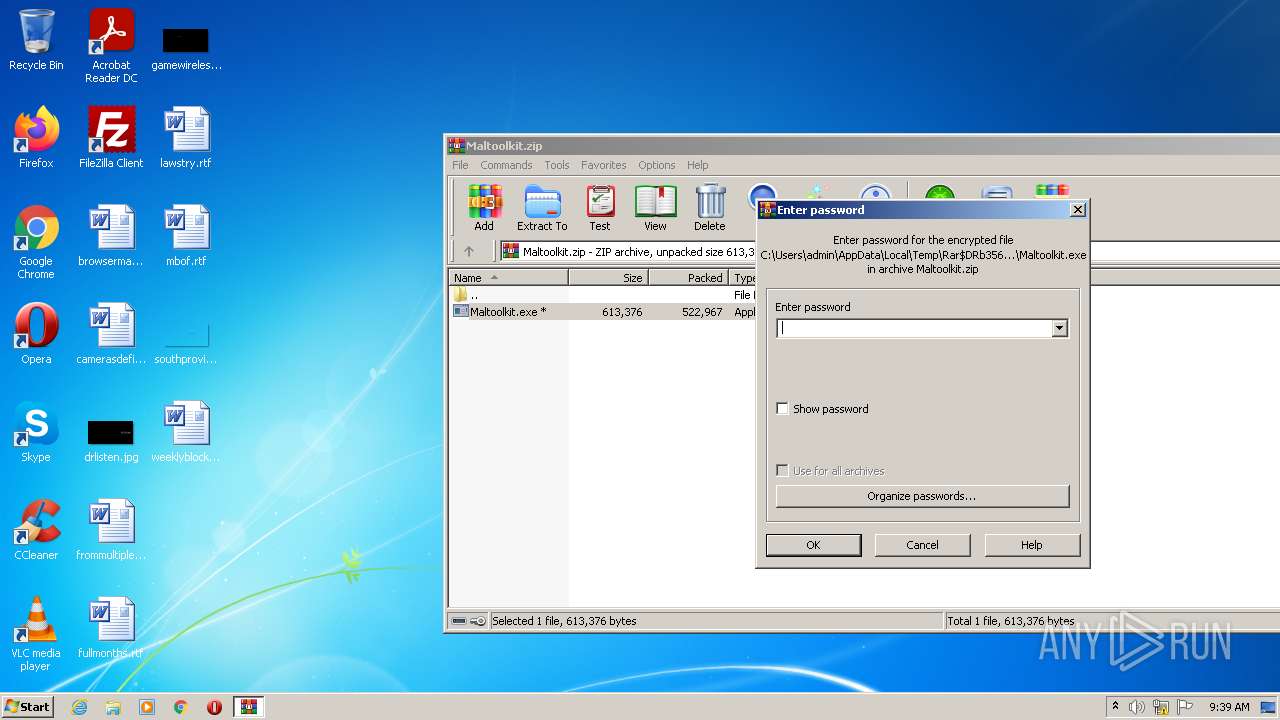
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3560)
- adminGDI271.exe.exe (PID: 2180)
- iexpress.exe (PID: 300)
- adminGDI271.exe.exe (PID: 1936)
- adminGDI271.exe.exe (PID: 3068)
- adminGDI271.exe.exe (PID: 2840)
- adminGDI271.exe.exe (PID: 328)
- adminGDI271.exe.exe (PID: 2252)
Checks supported languages
- WinRAR.exe (PID: 3560)
- Maltoolkit.exe (PID: 3664)
- cmd.exe (PID: 1640)
- cmd.exe (PID: 3688)
- Maltoolkit.exe (PID: 3936)
- adminGDI271.exe.exe (PID: 2180)
- cmd.exe (PID: 2688)
- Maltoolkit.exe (PID: 3608)
- adminGDI271.exe.exe (PID: 1936)
- adminGDI271.exe.exe (PID: 3068)
- Maltoolkit.exe (PID: 2352)
- adminGDI271.exe.exe (PID: 2840)
- cmd.exe (PID: 2872)
- Maltoolkit.exe (PID: 3008)
- cmd.exe (PID: 2532)
- adminGDI271.exe.exe (PID: 2252)
- cmd.exe (PID: 4016)
- Maltoolkit.exe (PID: 2092)
- adminGDI271.exe.exe (PID: 328)
- Maltoolkit.exe (PID: 2880)
- cmd.exe (PID: 2340)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3560)
- adminGDI271.exe.exe (PID: 2180)
- adminGDI271.exe.exe (PID: 3068)
- adminGDI271.exe.exe (PID: 2840)
- adminGDI271.exe.exe (PID: 1936)
- adminGDI271.exe.exe (PID: 2252)
- adminGDI271.exe.exe (PID: 328)
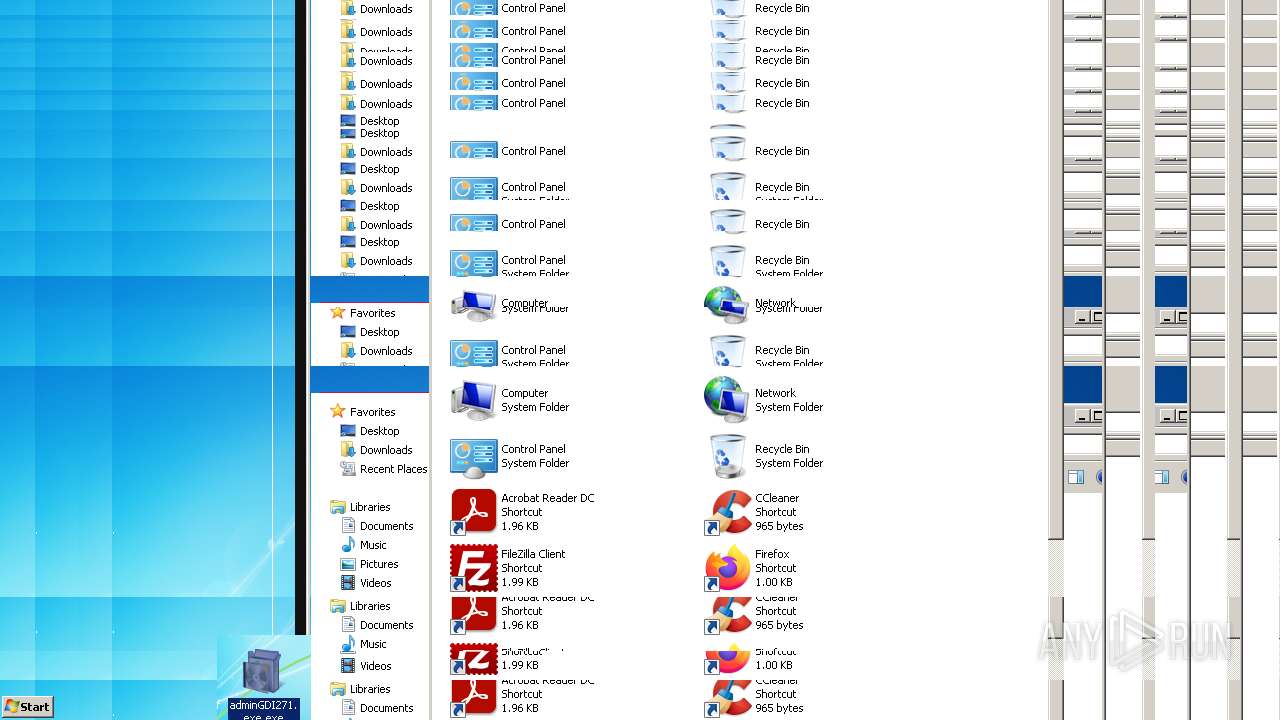
Starts CMD.EXE for commands execution
- Maltoolkit.exe (PID: 3664)
- adminGDI271.exe.exe (PID: 2180)
- adminGDI271.exe.exe (PID: 1936)
- adminGDI271.exe.exe (PID: 3068)
- adminGDI271.exe.exe (PID: 2840)
- adminGDI271.exe.exe (PID: 2252)
- adminGDI271.exe.exe (PID: 328)
Creates files in the Windows directory
- Maltoolkit.exe (PID: 3664)
INFO
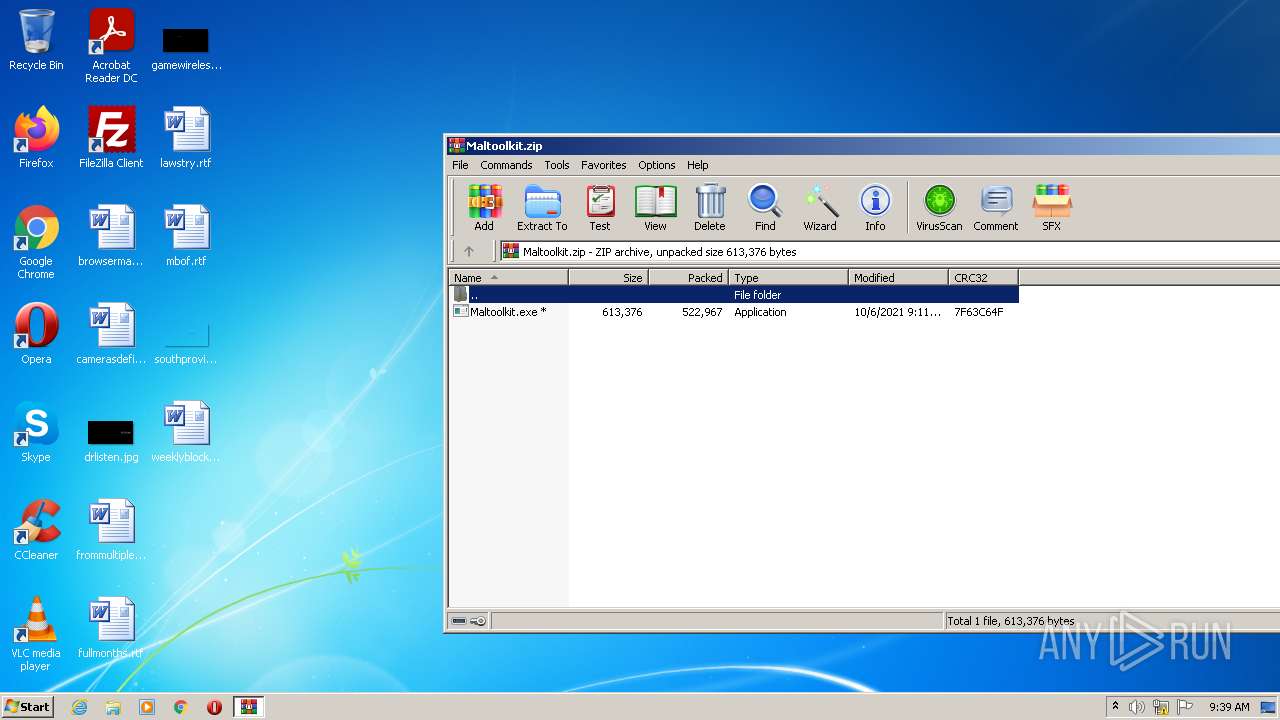
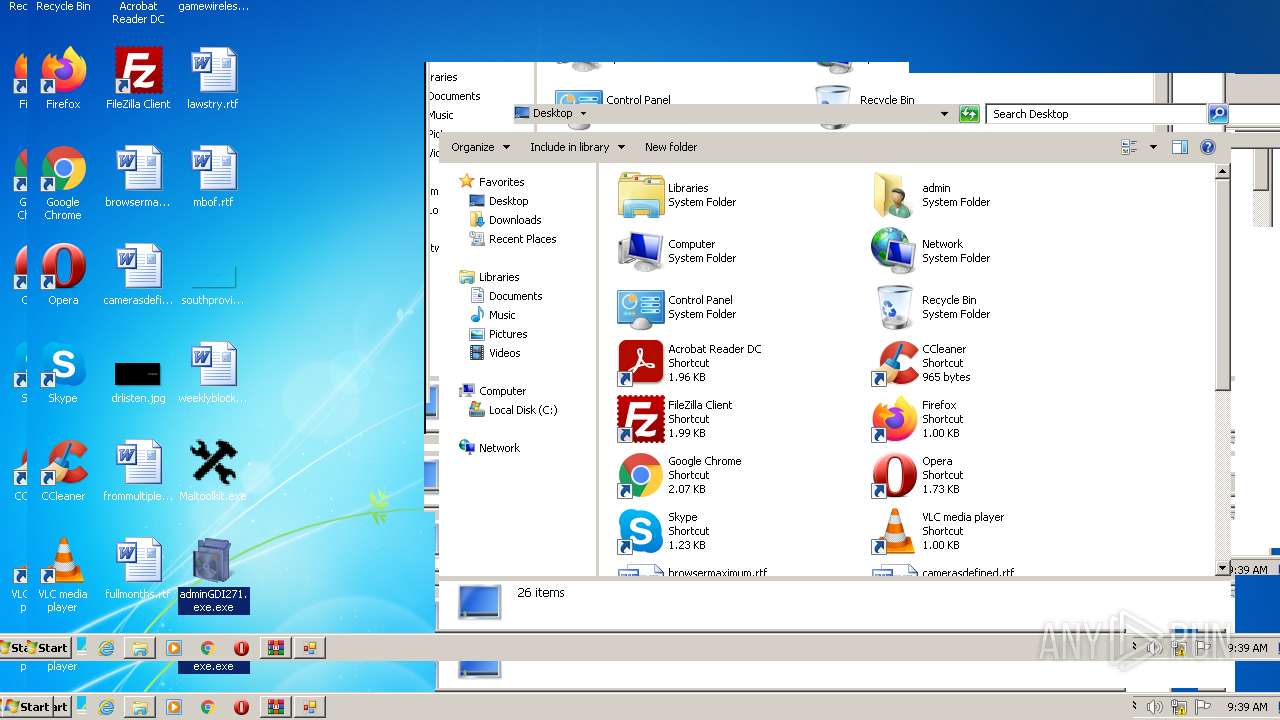
Manual execution by user
- Maltoolkit.exe (PID: 3664)
- adminGDI271.exe.exe (PID: 3068)
- adminGDI271.exe.exe (PID: 2180)
- adminGDI271.exe.exe (PID: 1936)
- adminGDI271.exe.exe (PID: 2840)
- adminGDI271.exe.exe (PID: 2252)
- adminGDI271.exe.exe (PID: 328)
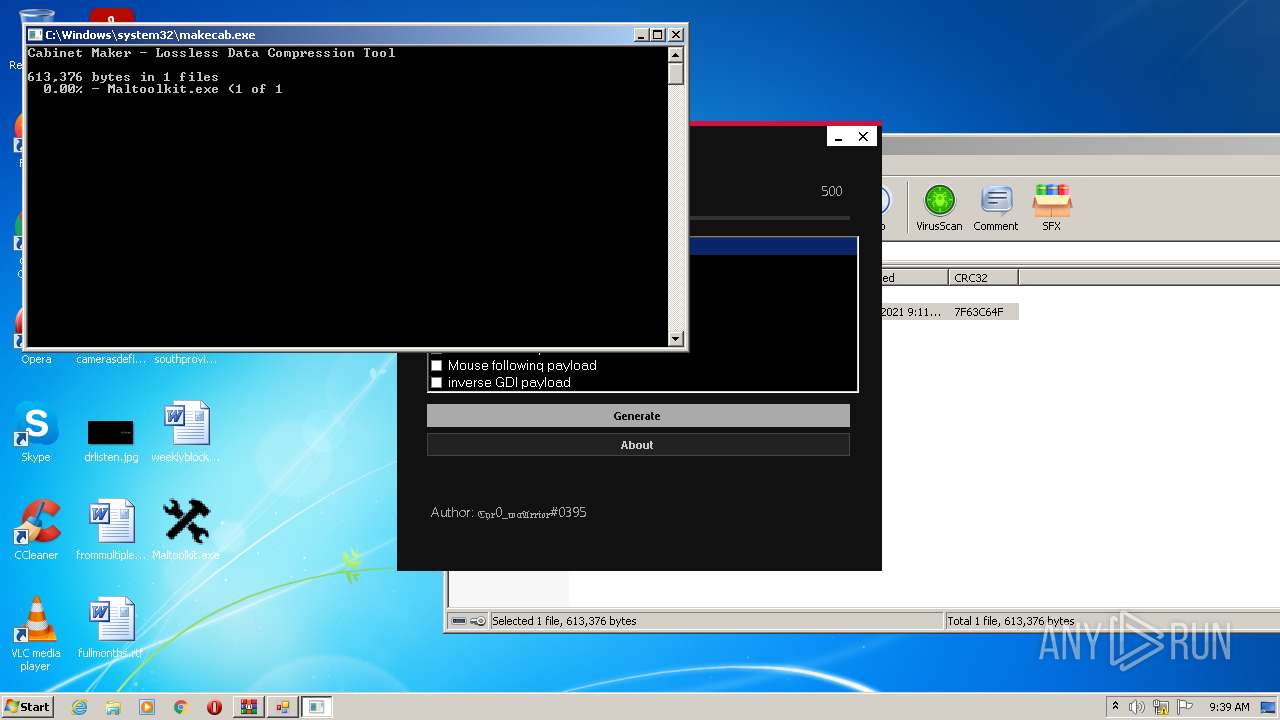
Checks supported languages
- iexpress.exe (PID: 300)
- makecab.exe (PID: 2560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | Maltoolkit.exe |
|---|---|
| ZipUncompressedSize: | 613376 |
| ZipCompressedSize: | 522967 |
| ZipCRC: | 0x7f63c64f |
| ZipModifyDate: | 2021:10:06 11:11:12 |
| ZipCompression: | Unknown (99) |
| ZipBitFlag: | 0x0009 |
| ZipRequiredVersion: | 20 |
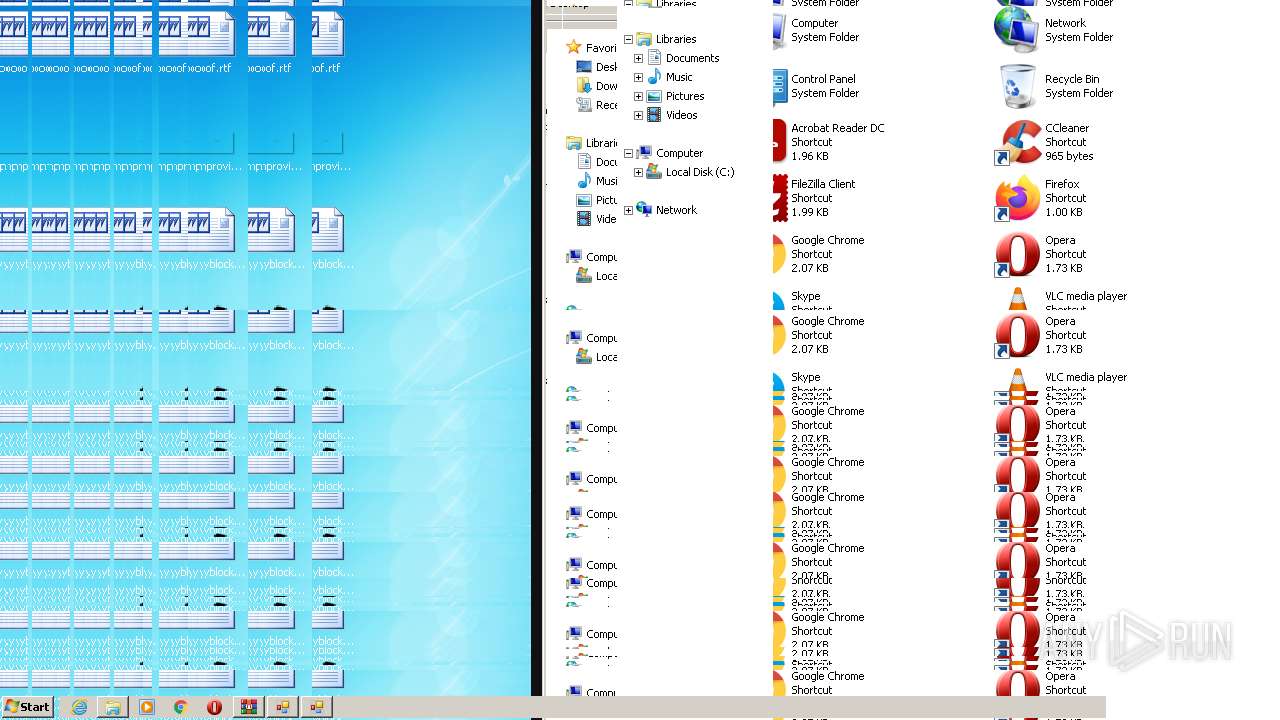
Total processes
67
Monitored processes
23
Malicious processes
8
Suspicious processes
6
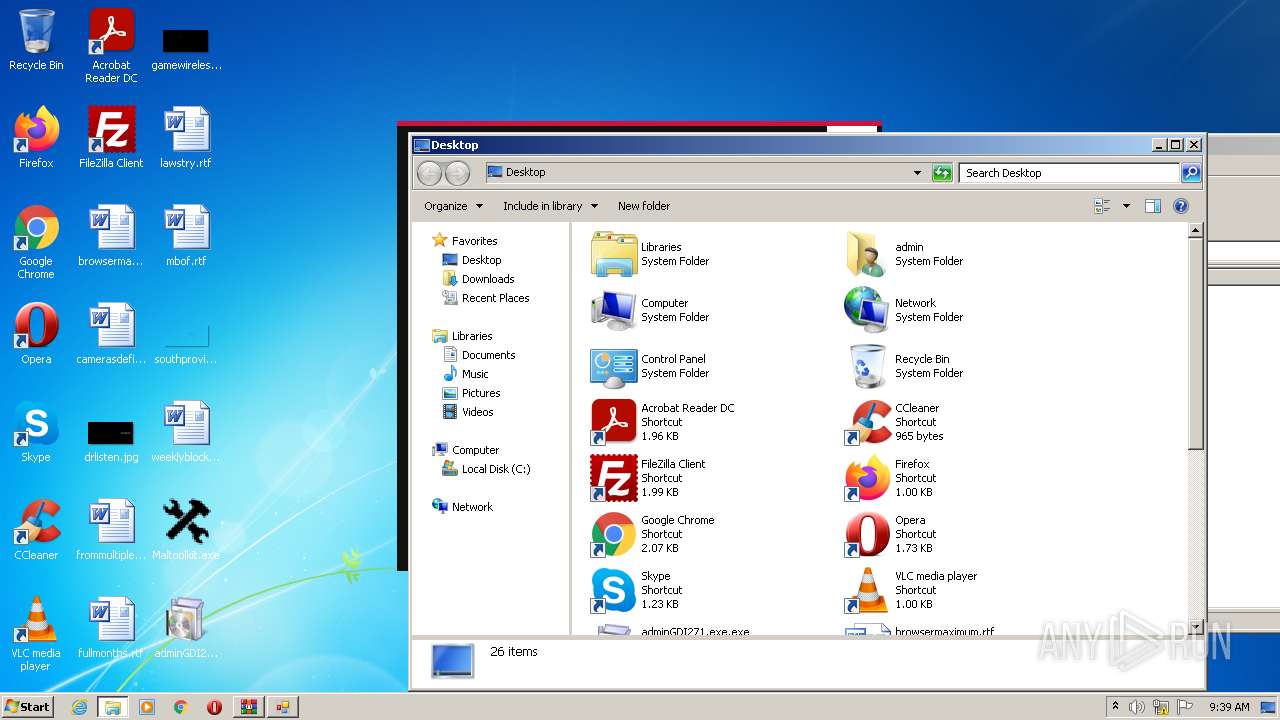
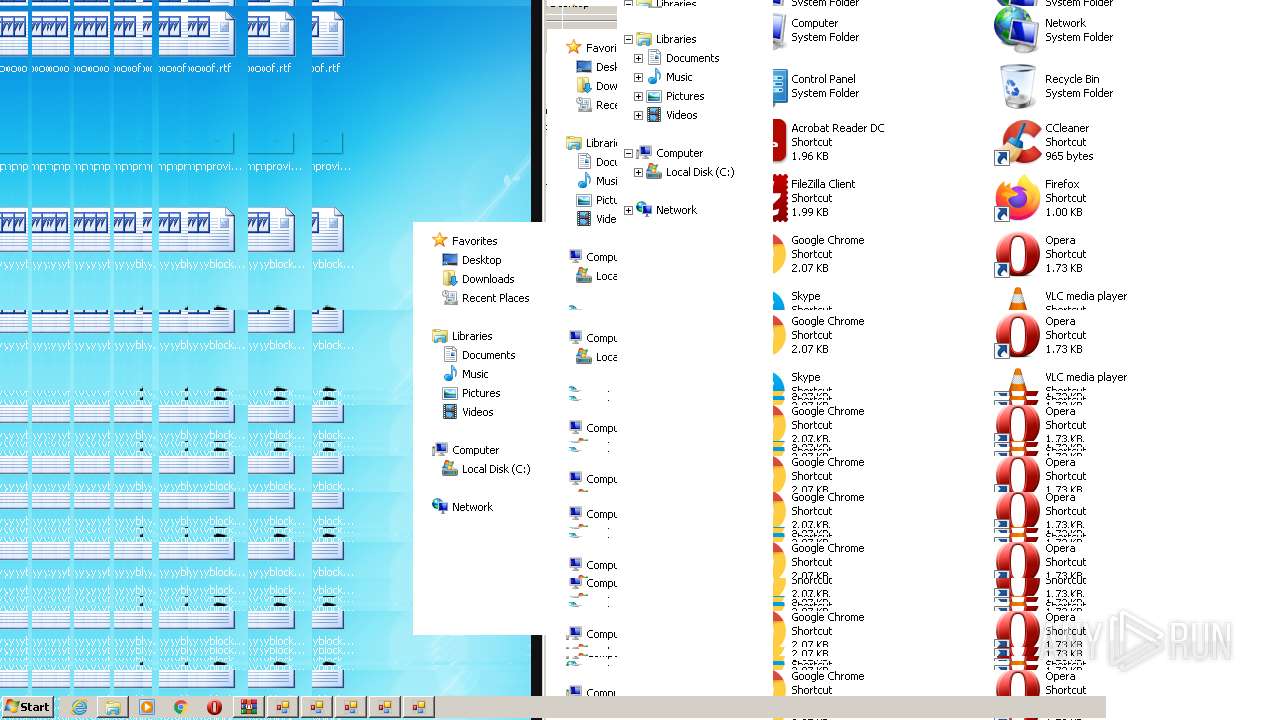
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | iexpress /N C:\Users\admin\AppData\Local\Temp\\optionfile.SED | C:\Windows\system32\iexpress.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Wizard Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 328 | "C:\Users\admin\Desktop\adminGDI271.exe.exe" | C:\Users\admin\Desktop\adminGDI271.exe.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1640 | "cmd.exe" | C:\Windows\system32\cmd.exe | — | Maltoolkit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1936 | "C:\Users\admin\Desktop\adminGDI271.exe.exe" | C:\Users\admin\Desktop\adminGDI271.exe.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2092 | Maltoolkit.exe --shreadinggdipayload500 | C:\Users\admin\AppData\Local\Temp\IXP003.TMP\Maltoolkit.exe | — | cmd.exe | |||||||||||
User: admin Company: MALWAREMAN Integrity Level: MEDIUM Description: Maltoolkit Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2180 | "C:\Users\admin\Desktop\adminGDI271.exe.exe" | C:\Users\admin\Desktop\adminGDI271.exe.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2252 | "C:\Users\admin\Desktop\adminGDI271.exe.exe" | C:\Users\admin\Desktop\adminGDI271.exe.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2340 | cmd /c Maltoolkit.exe --shreadinggdipayload500 | C:\Windows\system32\cmd.exe | — | adminGDI271.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2352 | Maltoolkit.exe --shreadinggdipayload500 | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\Maltoolkit.exe | — | cmd.exe | |||||||||||
User: admin Company: MALWAREMAN Integrity Level: MEDIUM Description: Maltoolkit Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2532 | cmd /c Maltoolkit.exe --shreadinggdipayload500 | C:\Windows\system32\cmd.exe | — | adminGDI271.exe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 759
Read events
1 748
Write events
11
Delete events
0
Modification events
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Maltoolkit.zip | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3560) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
10
Suspicious files
9
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2560 | makecab.exe | C:\Users\admin\Desktop\~adminGDI271.exe_LAYOUT.INF | binary | |
MD5:— | SHA256:— | |||
| 300 | iexpress.exe | C:\Users\admin\Desktop\~adminGDI271.exe.DDF | binary | |
MD5:— | SHA256:— | |||
| 3664 | Maltoolkit.exe | C:\Users\admin\AppData\Local\Temp\optionfile.SED | binary | |
MD5:— | SHA256:— | |||
| 2560 | makecab.exe | C:\Users\admin\Desktop\~adminGDI271.exe.CAB | compressed | |
MD5:— | SHA256:— | |||
| 2560 | makecab.exe | C:\Users\admin\AppData\Local\Temp\inf_2560_3 | text | |
MD5:— | SHA256:— | |||
| 2560 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_2560_8 | binary | |
MD5:— | SHA256:— | |||
| 2560 | makecab.exe | C:\Users\admin\Desktop\~adminGDI271.exe.RPT | text | |
MD5:— | SHA256:— | |||
| 2560 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_2560_6 | binary | |
MD5:— | SHA256:— | |||
| 2560 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_2560_5 | binary | |
MD5:29B1745E465A8BC3D4B8984B7FE0E36D | SHA256:891414EC318A8B972064CDD311E23036A7592326CBA452C91DB14F1E74F60618 | |||
| 2560 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_2560_7 | binary | |
MD5:F99F4932E2CA7EF3A0AC7F40F1C5E71D | SHA256:E93C2AE196EAE3E4C4E01D9411A4A6ED2DBC10F7DC1F6E800DAD5422A571840C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report