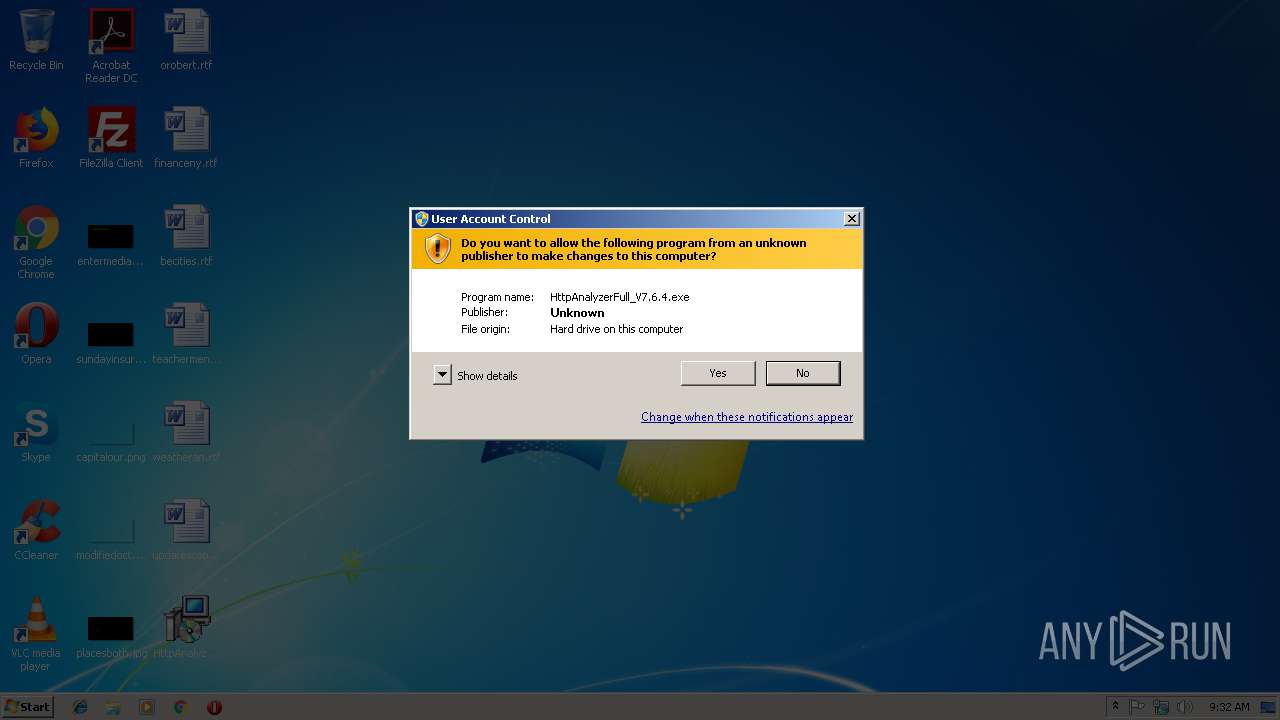
| File name: | HttpAnalyzerFull_V7.6.4.exe |
| Full analysis: | https://app.any.run/tasks/5a5a43b8-3cc0-4a18-b0c6-8fc334855cab |
| Verdict: | Malicious activity |
| Analysis date: | December 21, 2018, 09:31:58 |
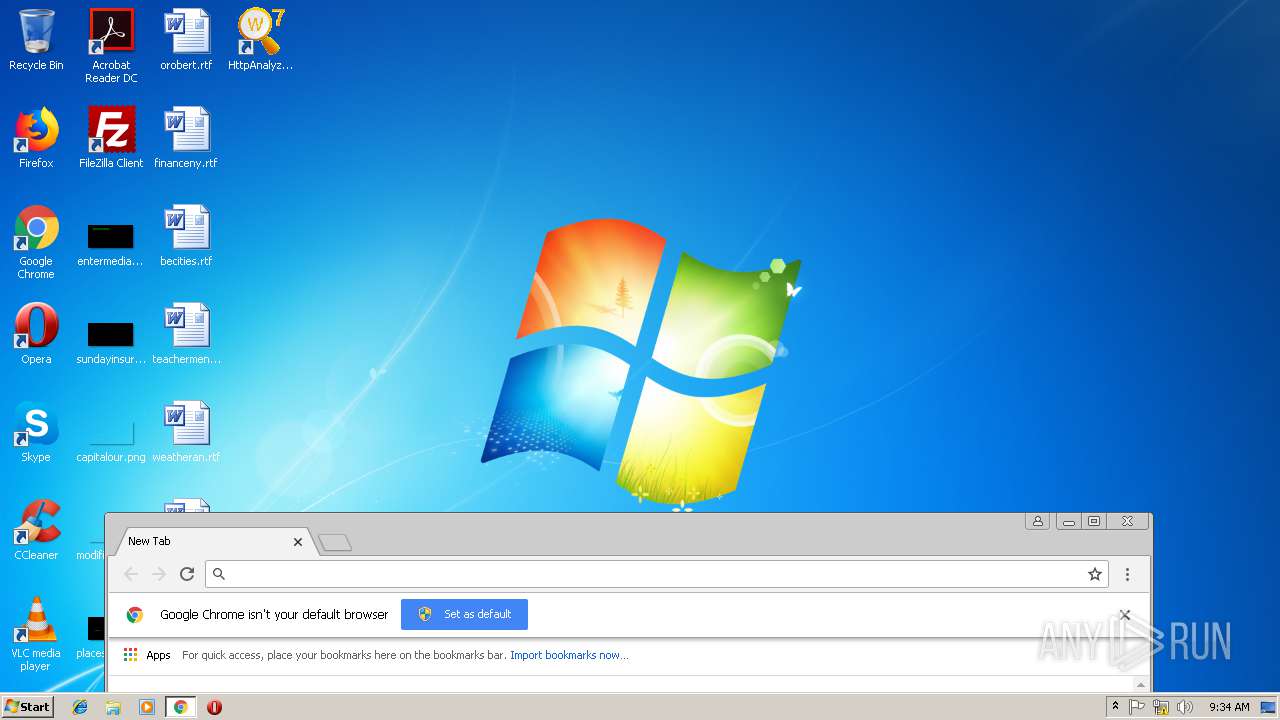
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DE9C9EFE330FAA044AA39BB46D5CBFBF |
| SHA1: | 507C5362B6C272A3469E407DC9B61BEEC3151214 |
| SHA256: | F25541DEE8F859B62C642D2E6E835C247900B5BC94A00CDBC4D894BAB83796DD |
| SSDEEP: | 196608:zlV8V9+oPxvNRtiexPhNOk1C/moCgrlbej1GGzaA6aIHf9LdrNjL:zzCpxvNRLxpNnVoElzr7I/9v |
MALICIOUS
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3836)
- regsvr32.exe (PID: 2852)
- nfregdrv.exe (PID: 2840)
- netFilterService.exe (PID: 2992)
- netFilterService.exe (PID: 3196)
Registers / Runs the DLL via REGSVR32.EXE
- HttpAnalyzerFull_V7.6.4.tmp (PID: 2916)
Changes settings of System certificates
- CertMgr.exe (PID: 4080)
- netFilterService.exe (PID: 2992)
Application was dropped or rewritten from another process
- nfregdrv.exe (PID: 2840)
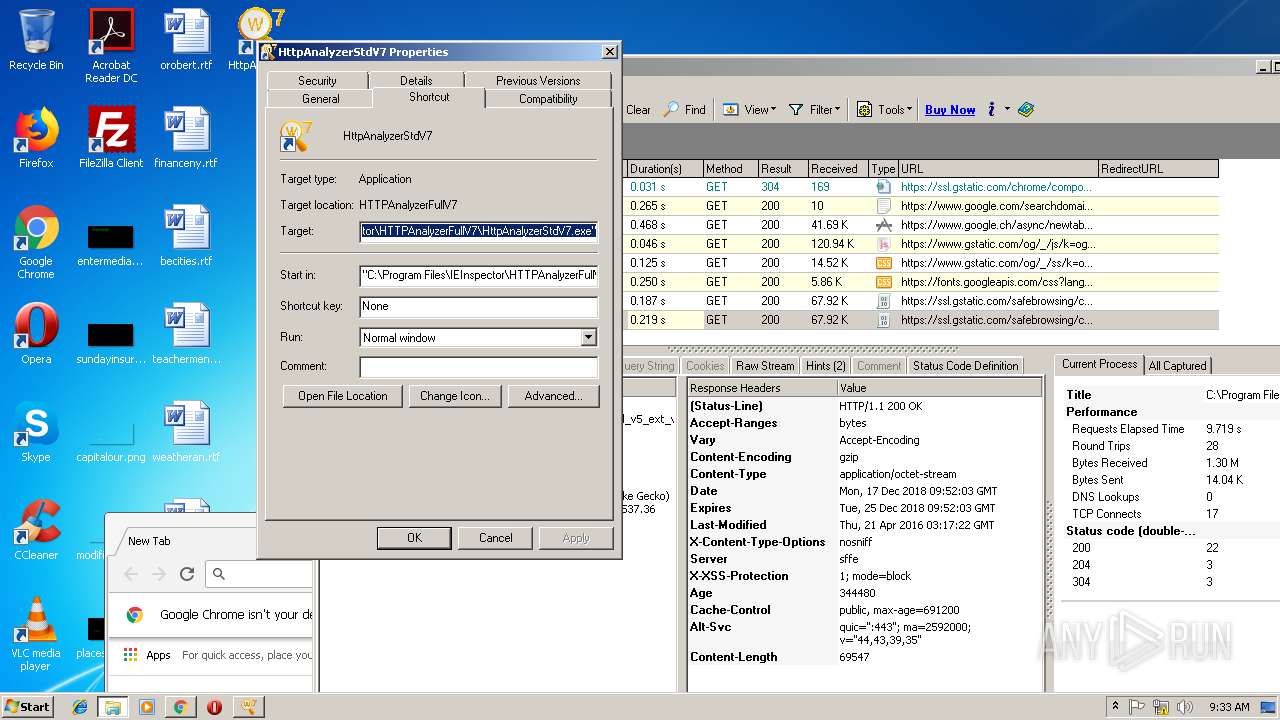
- HttpAnalyzerStdV7.exe (PID: 3576)
- FixPathDataType.exe (PID: 1228)
- CertMgr.exe (PID: 4080)
- HttpAnalyzerStdV7.exe (PID: 2880)
- netFilterService.exe (PID: 3196)
- netFilterService.exe (PID: 2992)
SUSPICIOUS
Executable content was dropped or overwritten
- HttpAnalyzerFull_V7.6.4.exe (PID: 3892)
- HttpAnalyzerFull_V7.6.4.exe (PID: 2280)
- HttpAnalyzerFull_V7.6.4.tmp (PID: 2916)
Creates COM task schedule object
- HttpAnalyzerFull_V7.6.4.tmp (PID: 2916)
- regsvr32.exe (PID: 3836)
- regsvr32.exe (PID: 2852)
Creates files in the driver directory
- HttpAnalyzerFull_V7.6.4.tmp (PID: 2916)
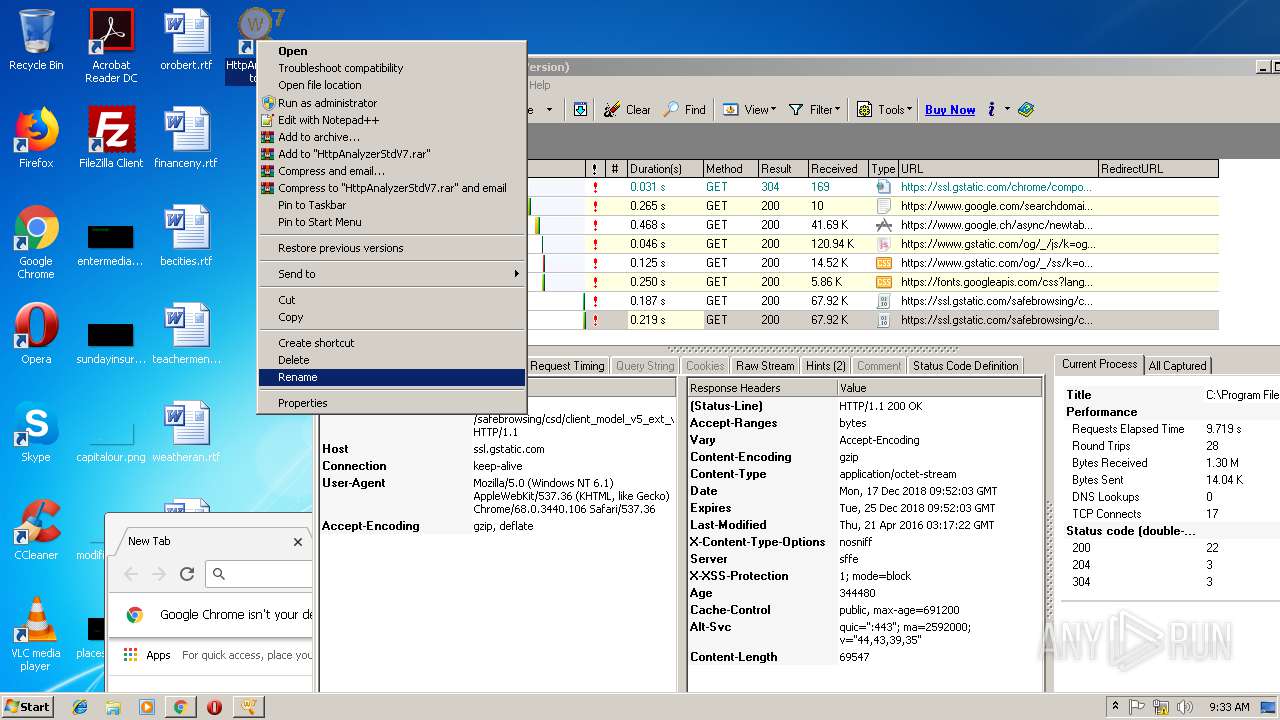
Modifies the open verb of a shell class
- HttpAnalyzerFull_V7.6.4.tmp (PID: 2916)
Creates files in the Windows directory
- HttpAnalyzerFull_V7.6.4.tmp (PID: 2916)
Creates files in the program directory
- netFilterService.exe (PID: 2992)
INFO
Application was dropped or rewritten from another process
- HttpAnalyzerFull_V7.6.4.tmp (PID: 2828)
- HttpAnalyzerFull_V7.6.4.tmp (PID: 2916)
Creates files in the program directory
- HttpAnalyzerFull_V7.6.4.tmp (PID: 2916)
Creates a software uninstall entry
- HttpAnalyzerFull_V7.6.4.tmp (PID: 2916)
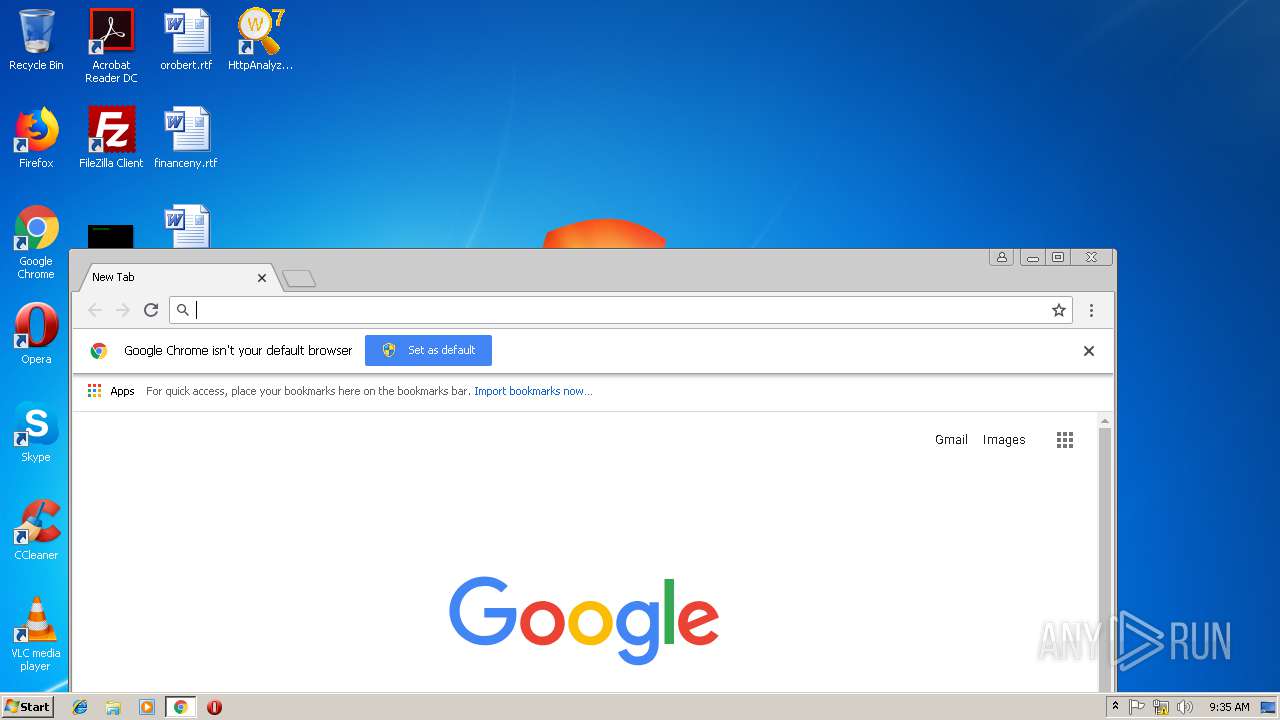
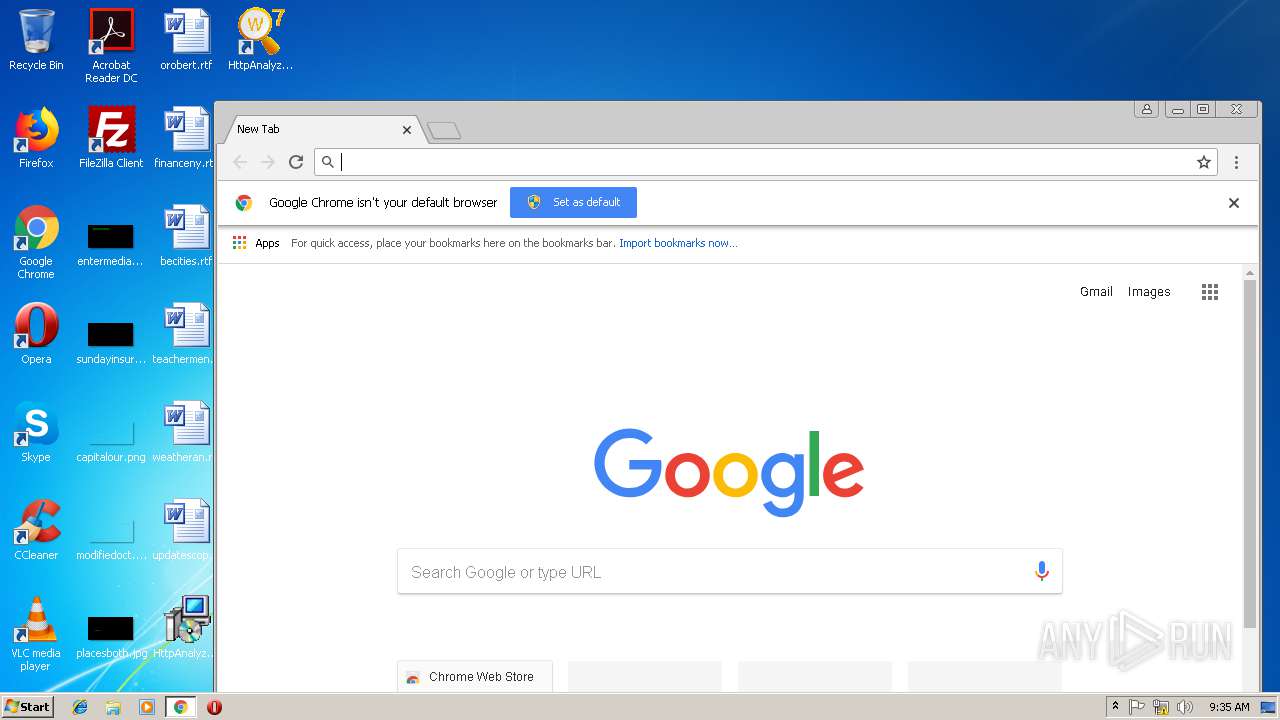
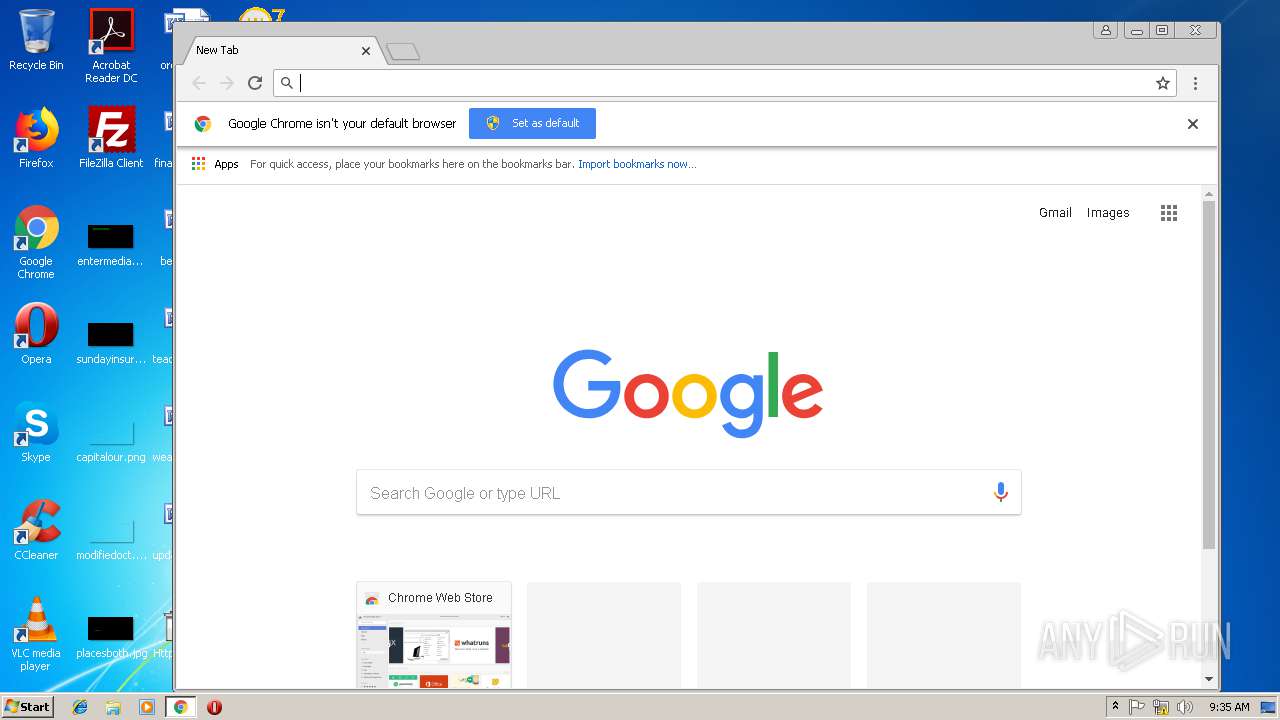
Application launched itself
- chrome.exe (PID: 2584)
Reads settings of System Certificates
- chrome.exe (PID: 2584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41472 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaa98 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.6.4.0 |
| ProductVersionNumber: | 7.6.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
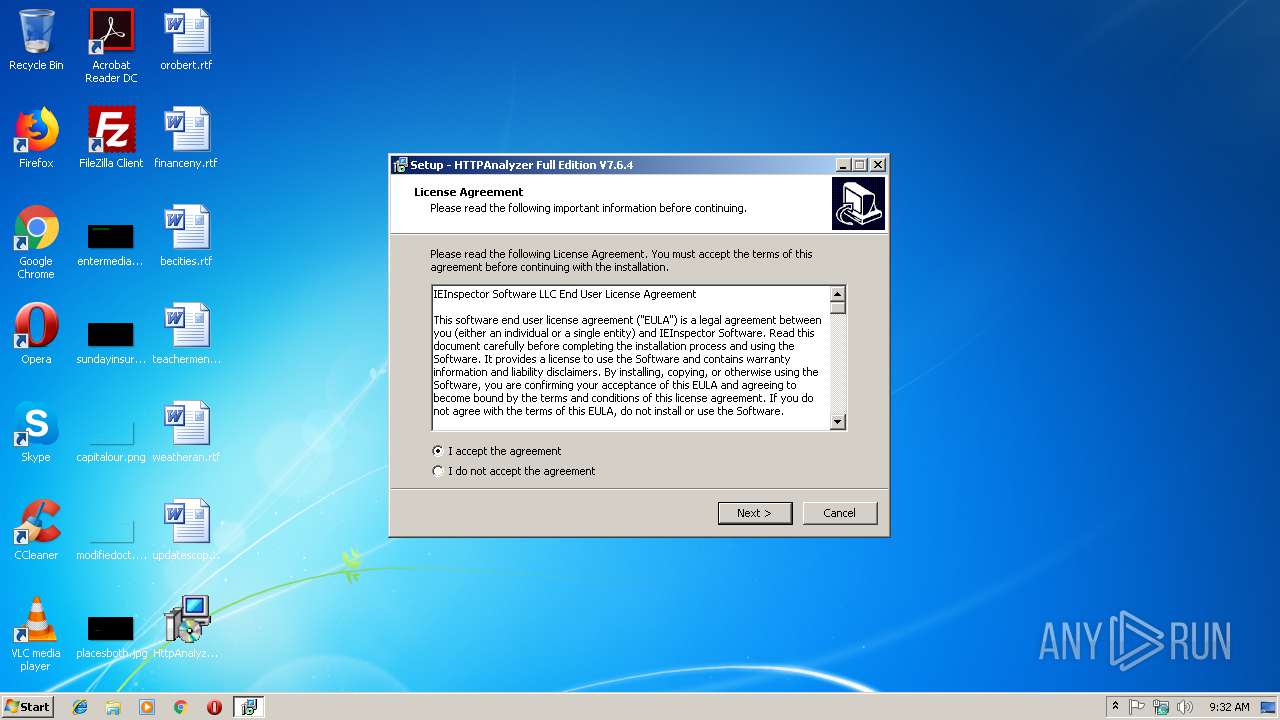
| CompanyName: | IEInspector Software |
| FileDescription: | HTTP Analyzer Full V7.6.4 |
| FileVersion: | 7.6.4 |
| LegalCopyright: | IEInspector Software |
| ProductName: | HTTPAnalyzer Full Edition V7.6.4 |
| ProductVersion: | 7.6.4 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | IEInspector Software |
| FileDescription: | HTTP Analyzer Full V7.6.4 |
| FileVersion: | 7.6.4 |
| LegalCopyright: | IEInspector Software |
| ProductName: | HTTPAnalyzer Full Edition V7.6.4 |
| ProductVersion: | 7.6.4 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000A1D0 | 0x0000A200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64375 |
DATA | 0x0000C000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74012 |
BSS | 0x0000D000 | 0x00000E94 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000E000 | 0x0000097C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48608 |
.tls | 0x0000F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00010000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 0x00011000 | 0x0000091C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00012000 | 0x00002C00 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.60624 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
62
Monitored processes
25
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1228 | "C:\Program Files\IEInspector\HTTPAnalyzerFullV7\FixPathDataType.exe" | C:\Program Files\IEInspector\HTTPAnalyzerFullV7\FixPathDataType.exe | — | HttpAnalyzerFull_V7.6.4.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=892,6078443524381580957,16099771478991707837,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=731DD4F147E03D14C4A9AC284E169CF3 --mojo-platform-channel-handle=1456 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=892,6078443524381580957,16099771478991707837,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8CA32C6319CC25A46CA7558865896BB5 --mojo-platform-channel-handle=520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=892,6078443524381580957,16099771478991707837,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=362927965DA3D60BC68490E067AFEDD5 --mojo-platform-channel-handle=3808 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2280 | "C:\Users\admin\Desktop\HttpAnalyzerFull_V7.6.4.exe" /SPAWNWND=$10122 /NOTIFYWND=$50108 | C:\Users\admin\Desktop\HttpAnalyzerFull_V7.6.4.exe | HttpAnalyzerFull_V7.6.4.tmp | ||||||||||||
User: admin Company: IEInspector Software Integrity Level: HIGH Description: HTTP Analyzer Full V7.6.4 Exit code: 0 Version: 7.6.4 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=892,6078443524381580957,16099771478991707837,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=8853FADA0ABA384CCE48BC02A93490AF --mojo-platform-channel-handle=864 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f4d00b0,0x6f4d00c0,0x6f4d00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2828 | "C:\Users\admin\AppData\Local\Temp\is-ASR2O.tmp\HttpAnalyzerFull_V7.6.4.tmp" /SL5="$50108,9802854,57856,C:\Users\admin\Desktop\HttpAnalyzerFull_V7.6.4.exe" | C:\Users\admin\AppData\Local\Temp\is-ASR2O.tmp\HttpAnalyzerFull_V7.6.4.tmp | — | HttpAnalyzerFull_V7.6.4.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2840 | "C:\Program Files\IEInspector\HTTPAnalyzerFullV7\nfregdrv.exe" netfilter_v76 | C:\Program Files\IEInspector\HTTPAnalyzerFullV7\nfregdrv.exe | — | HttpAnalyzerFull_V7.6.4.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
2 064
Read events
1 014
Write events
1 040
Delete events
10
Modification events
| (PID) Process: | (2916) HttpAnalyzerFull_V7.6.4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 640B000017F2D91A1099D401 | |||
| (PID) Process: | (2916) HttpAnalyzerFull_V7.6.4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: D7416F3C28125D31C21A82F8C5D97BE66884DC236DF58ADEADF9DB1532890959 | |||
| (PID) Process: | (2916) HttpAnalyzerFull_V7.6.4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2916) HttpAnalyzerFull_V7.6.4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\IEInspector\HTTPAnalyzerFullV7\IEHTTPAnalyzerV7.dll | |||
| (PID) Process: | (2916) HttpAnalyzerFull_V7.6.4.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: EFCD94A77F730140CB42E366755176C9878918927E16850F585A4652E3A235AC | |||
| (PID) Process: | (2916) HttpAnalyzerFull_V7.6.4.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Program Files\IEInspector\HTTPAnalyzerFullV7\HTTPAnalyzer.tlb |
Value: 1 | |||
| (PID) Process: | (2916) HttpAnalyzerFull_V7.6.4.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Program Files\IEInspector\HTTPAnalyzerFullV7\IEInspectorBHO.dll |
Value: 1 | |||
| (PID) Process: | (2916) HttpAnalyzerFull_V7.6.4.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.halog |
| Operation: | write | Name: | |
Value: IEInspector.HTTPAnalyzer.NativeLogFile | |||
| (PID) Process: | (2916) HttpAnalyzerFull_V7.6.4.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\IEInspector.HTTPAnalyzer.NativeLogFile |
| Operation: | write | Name: | |
Value: HTTPAnalyzer Log File | |||
| (PID) Process: | (2916) HttpAnalyzerFull_V7.6.4.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\IEInspector.HTTPAnalyzer.NativeLogFile\Shell\Open\Command |
| Operation: | write | Name: | |
Value: "C:\Program Files\IEInspector\HTTPAnalyzerFullV7\HTTPAnalyzerStdV7.exe" "%1" | |||
Executable files
26
Suspicious files
82
Text files
99
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2916 | HttpAnalyzerFull_V7.6.4.tmp | C:\Program Files\IEInspector\HTTPAnalyzerFullV7\is-QA4FI.tmp | — | |
MD5:— | SHA256:— | |||
| 2916 | HttpAnalyzerFull_V7.6.4.tmp | C:\Program Files\IEInspector\HTTPAnalyzerFullV7\is-RD6OG.tmp | — | |
MD5:— | SHA256:— | |||
| 2916 | HttpAnalyzerFull_V7.6.4.tmp | C:\Program Files\IEInspector\HTTPAnalyzerFullV7\is-89FOG.tmp | — | |
MD5:— | SHA256:— | |||
| 2916 | HttpAnalyzerFull_V7.6.4.tmp | C:\Program Files\IEInspector\HTTPAnalyzerFullV7\is-IIOON.tmp | — | |
MD5:— | SHA256:— | |||
| 2916 | HttpAnalyzerFull_V7.6.4.tmp | C:\Program Files\IEInspector\HTTPAnalyzerFullV7\is-NKPR1.tmp | — | |
MD5:— | SHA256:— | |||
| 2916 | HttpAnalyzerFull_V7.6.4.tmp | C:\Program Files\IEInspector\HTTPAnalyzerFullV7\is-IABCR.tmp | — | |
MD5:— | SHA256:— | |||
| 2916 | HttpAnalyzerFull_V7.6.4.tmp | C:\Program Files\IEInspector\HTTPAnalyzerFullV7\is-KT853.tmp | — | |
MD5:— | SHA256:— | |||
| 2916 | HttpAnalyzerFull_V7.6.4.tmp | C:\Program Files\IEInspector\HTTPAnalyzerFullV7\is-C6OQM.tmp | — | |
MD5:— | SHA256:— | |||
| 2916 | HttpAnalyzerFull_V7.6.4.tmp | C:\Program Files\IEInspector\HTTPAnalyzerFullV7\is-LHOJU.tmp | — | |
MD5:— | SHA256:— | |||
| 2916 | HttpAnalyzerFull_V7.6.4.tmp | C:\Program Files\IEInspector\HTTPAnalyzerFullV7\is-Q6TKD.tmp | — | |
MD5:— | SHA256:— | |||
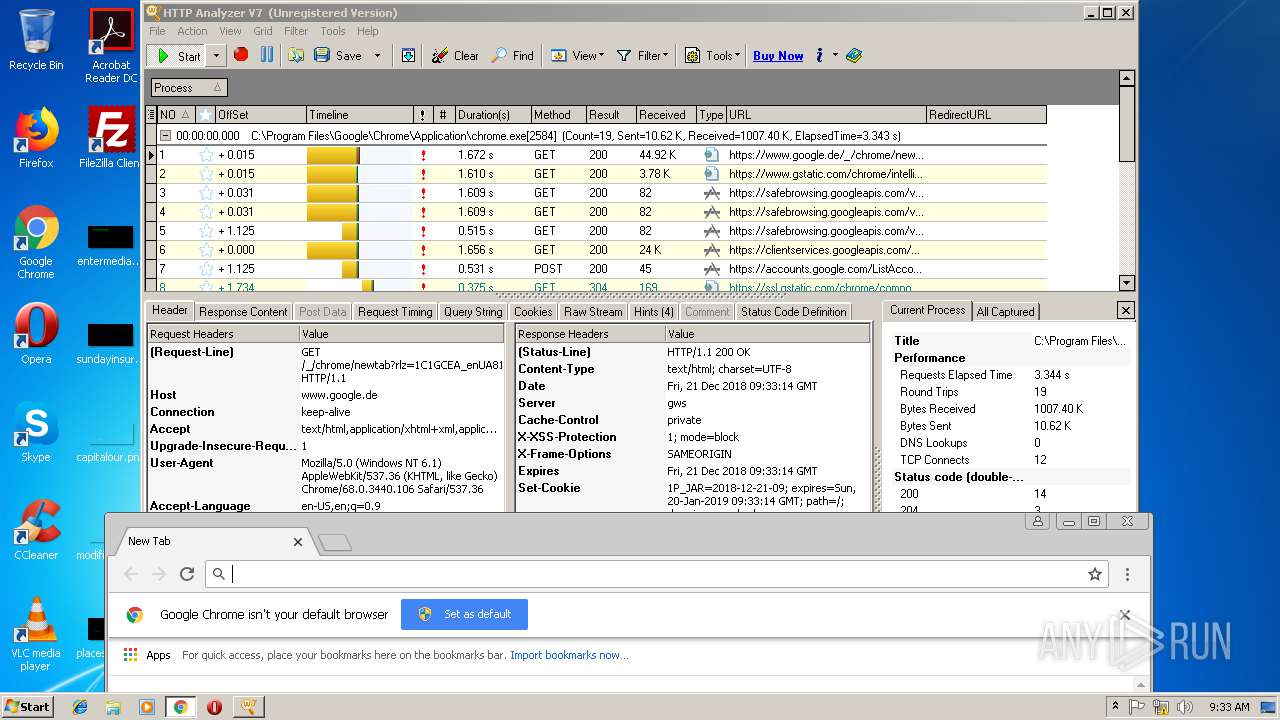
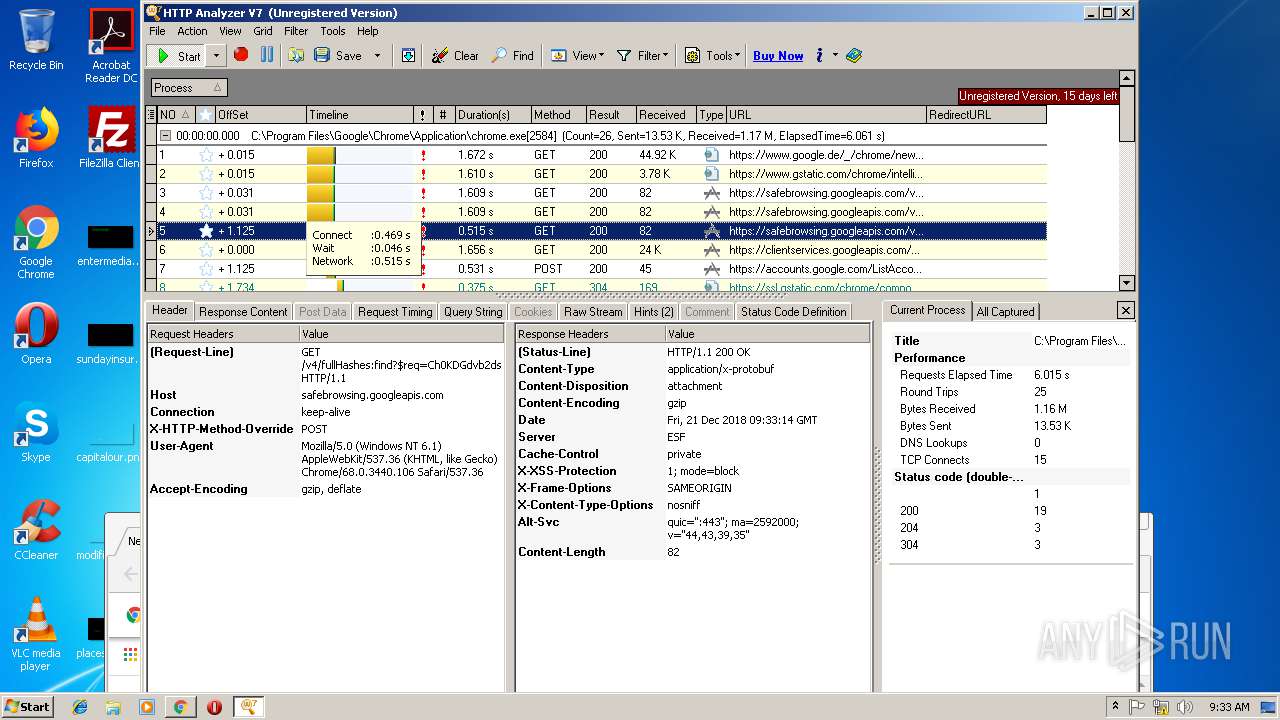
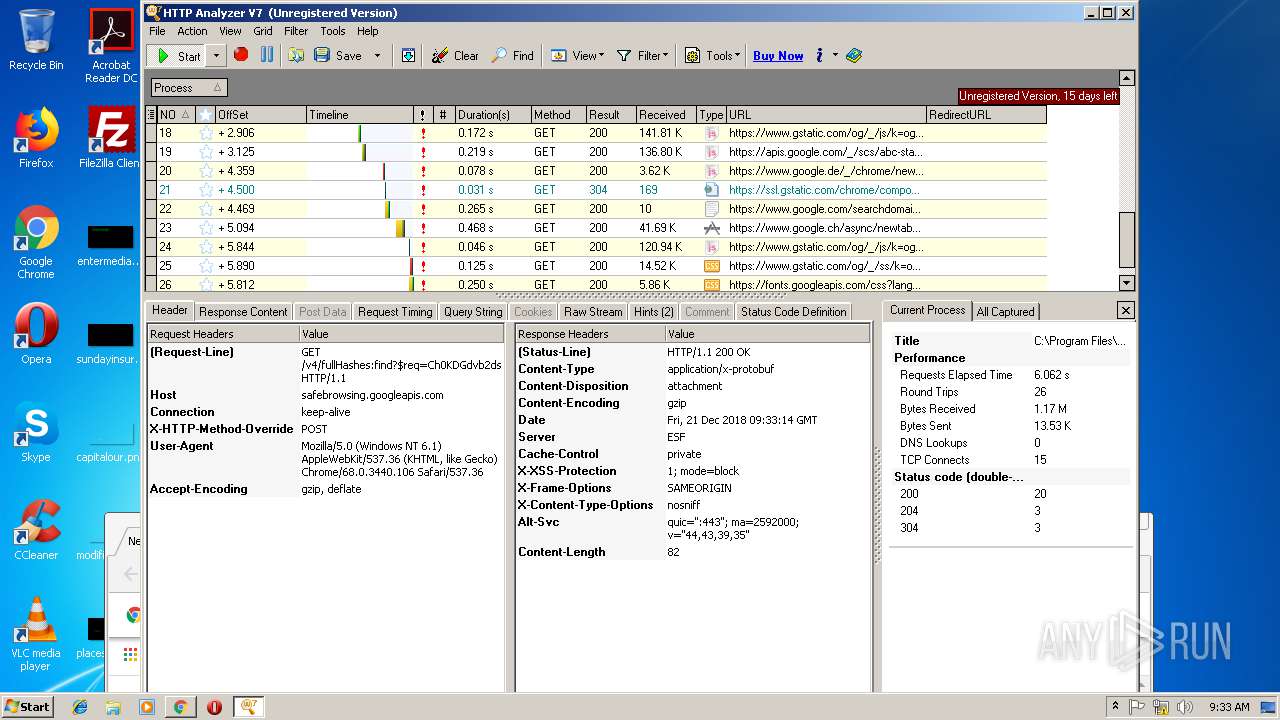
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
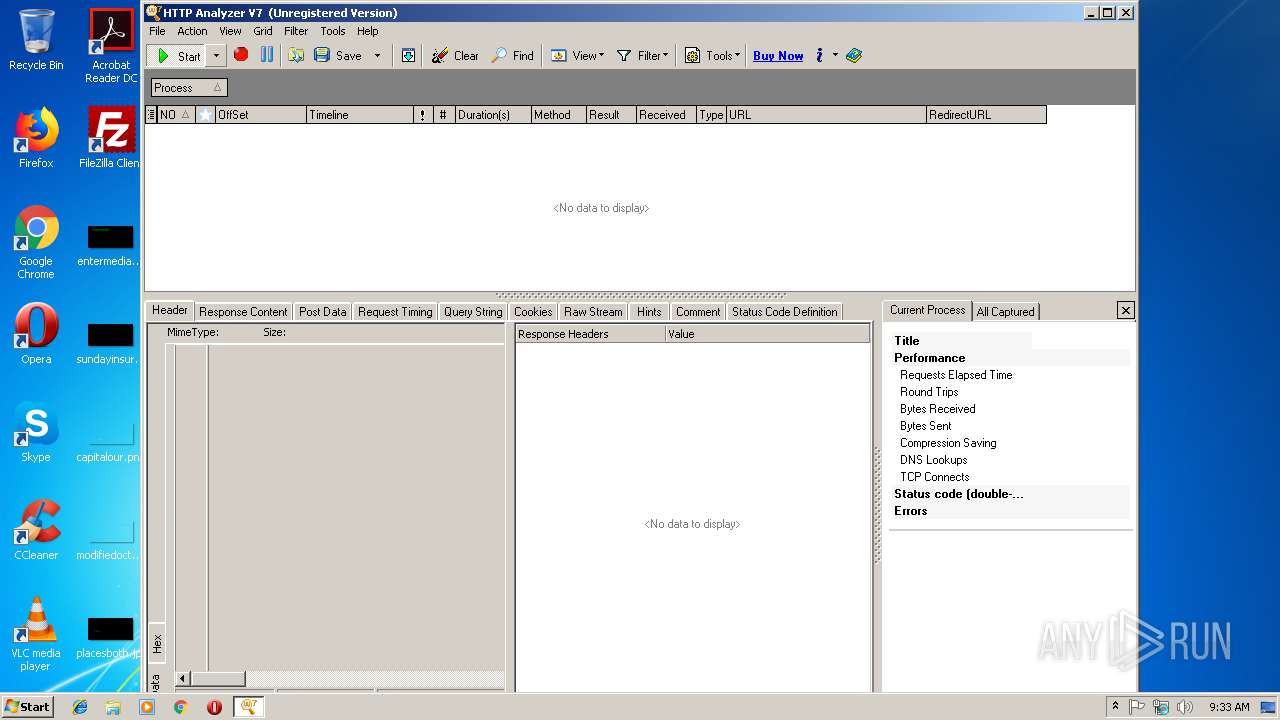
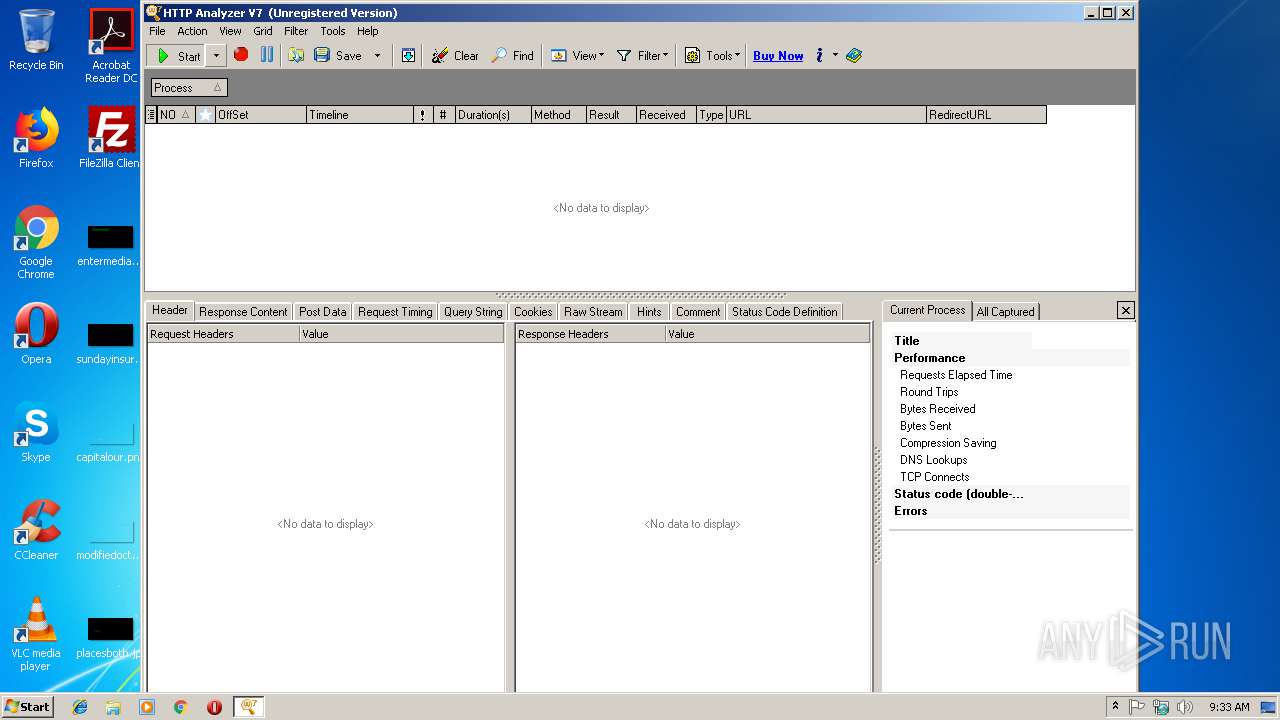
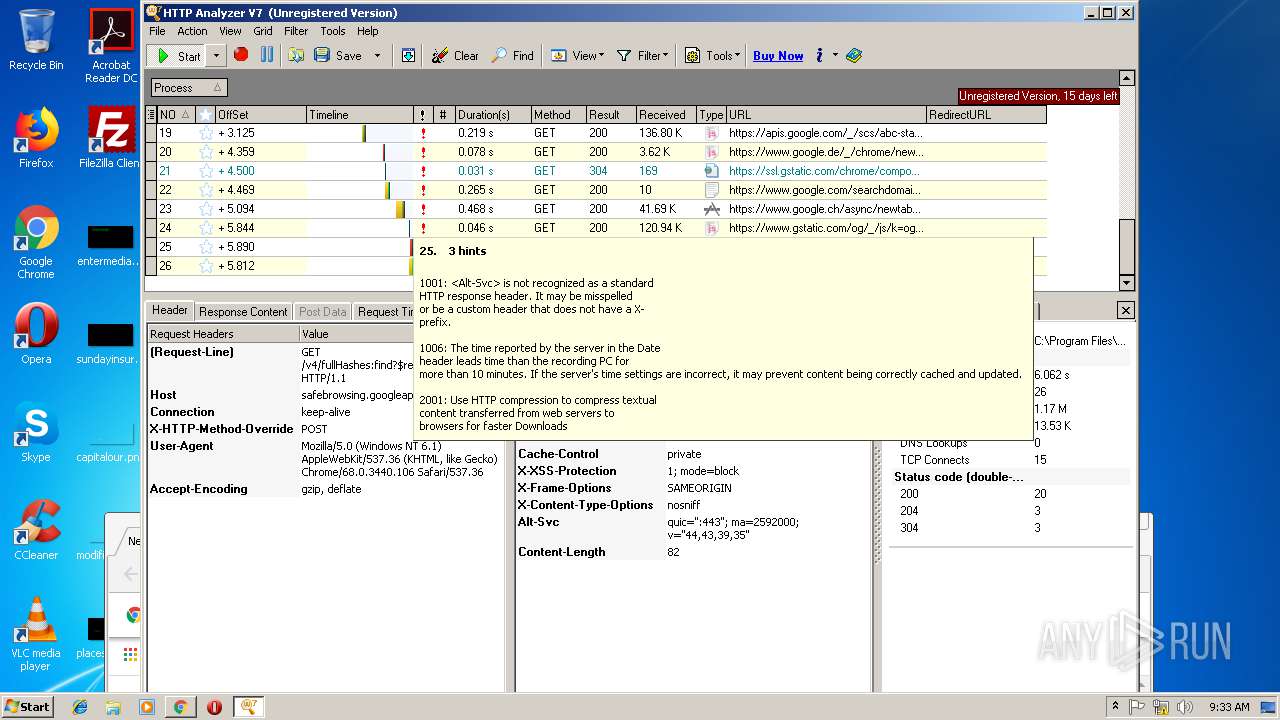
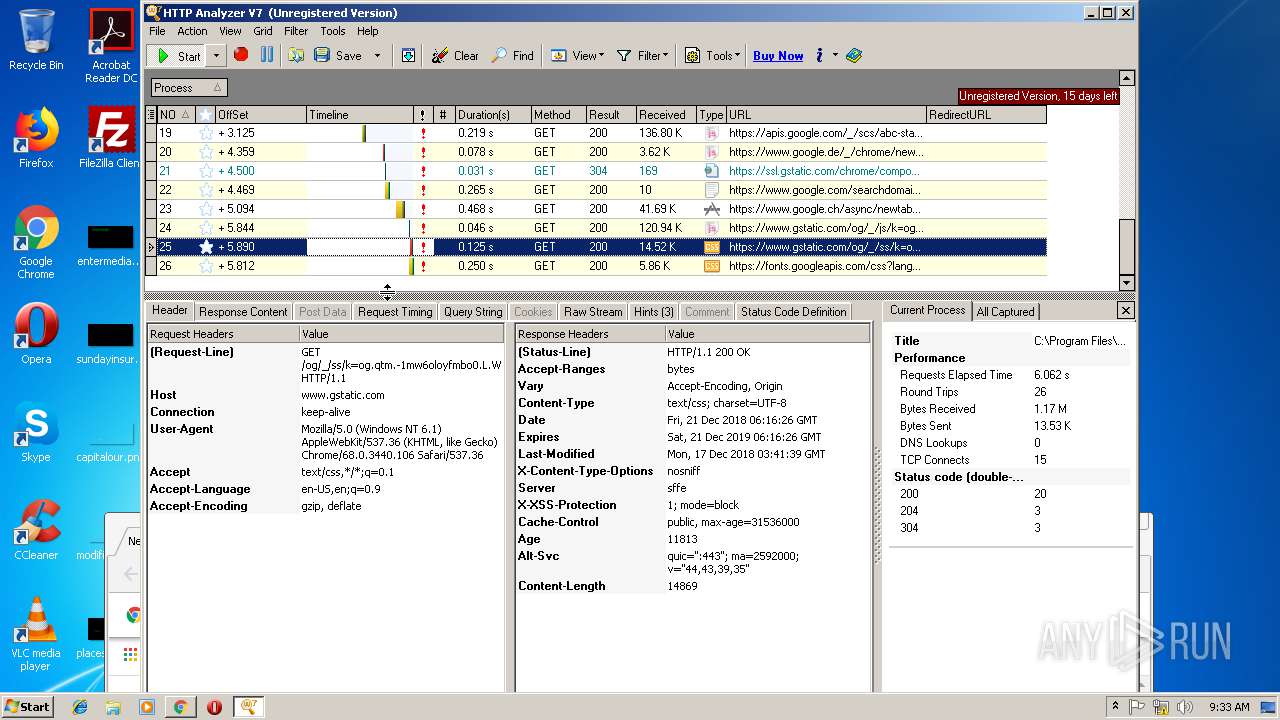
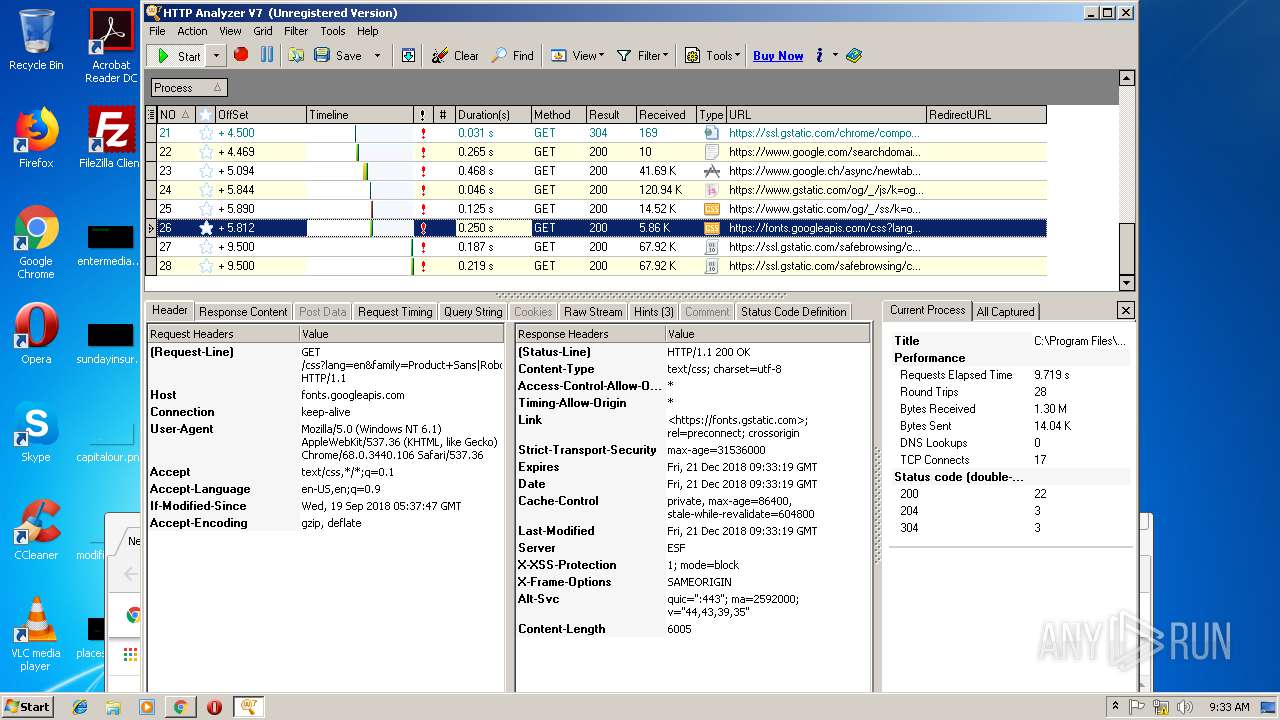
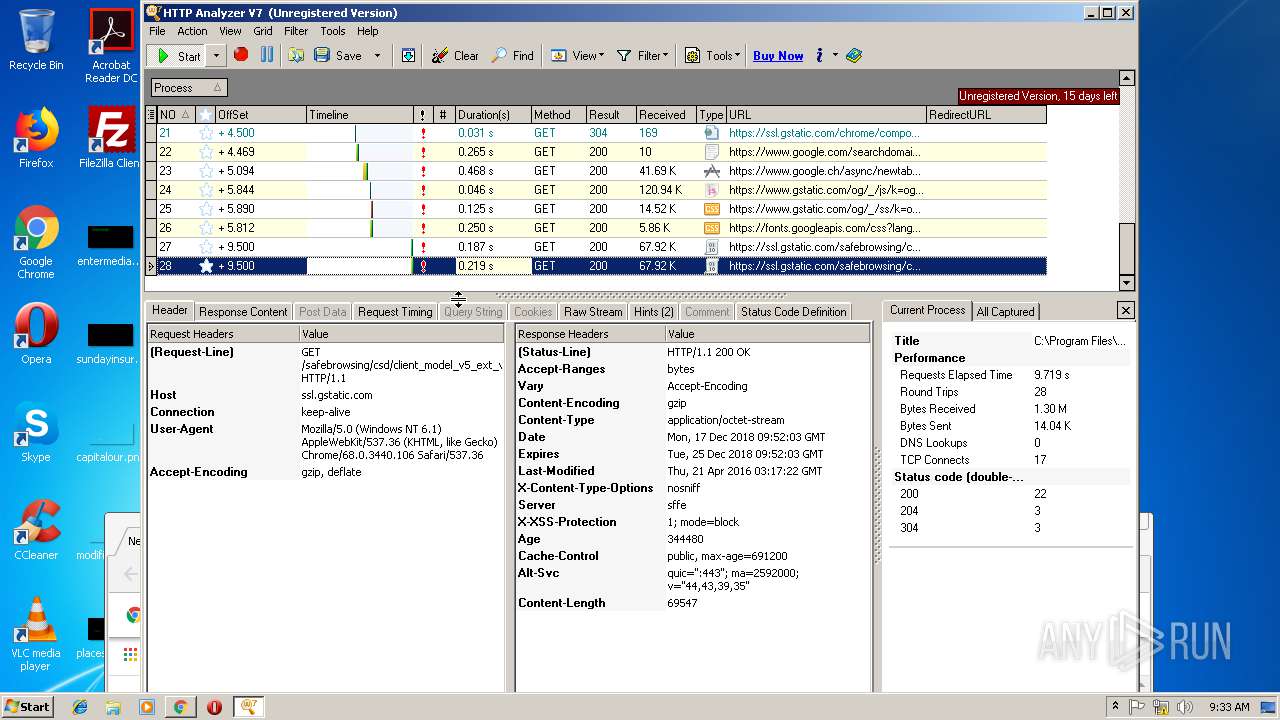
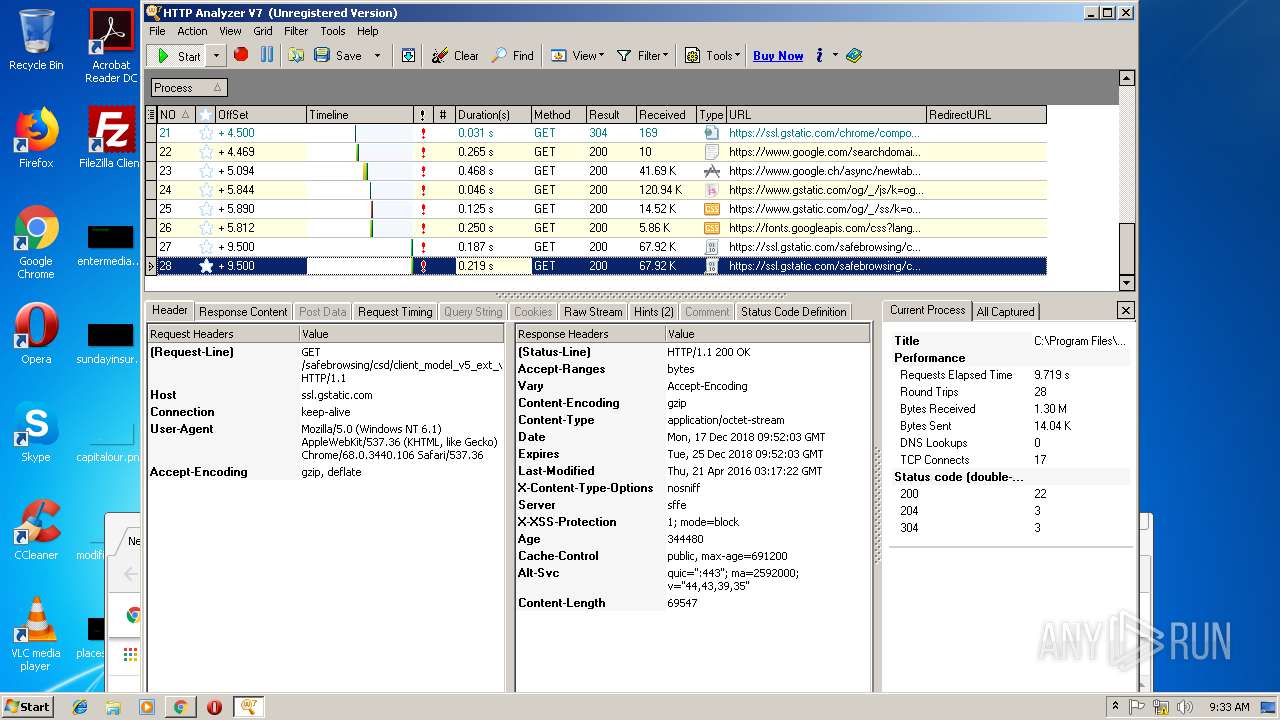
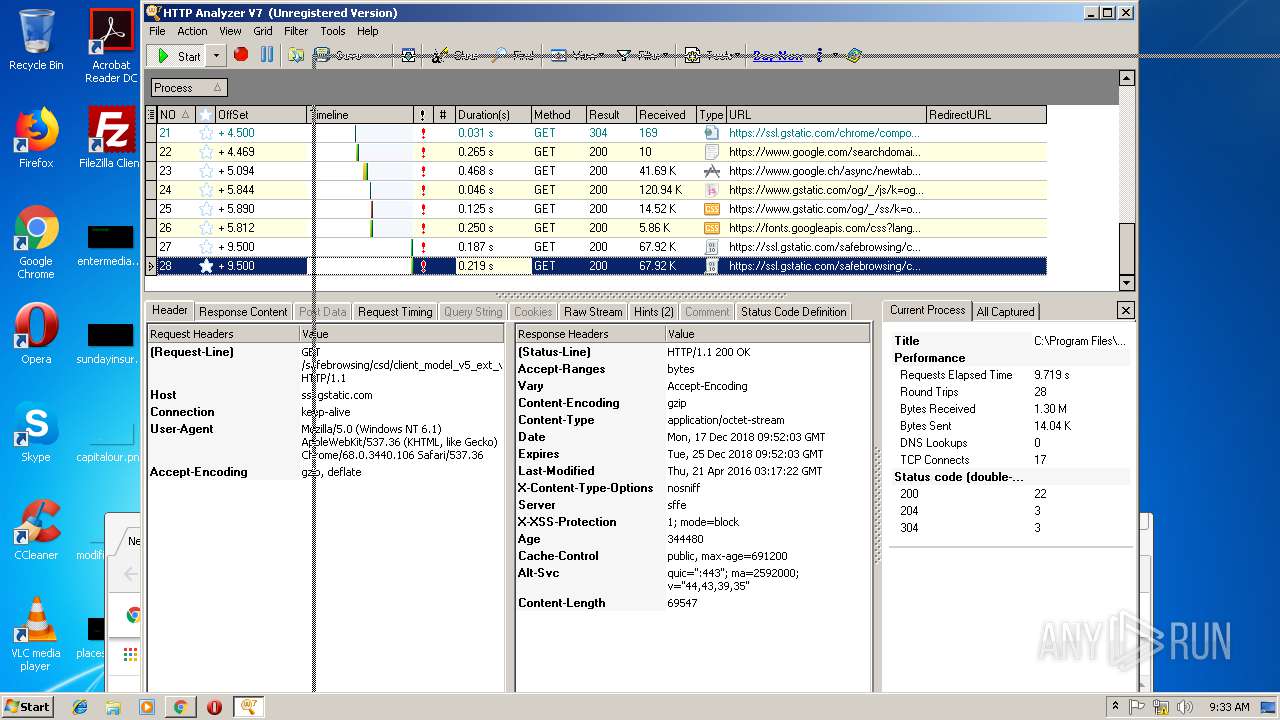
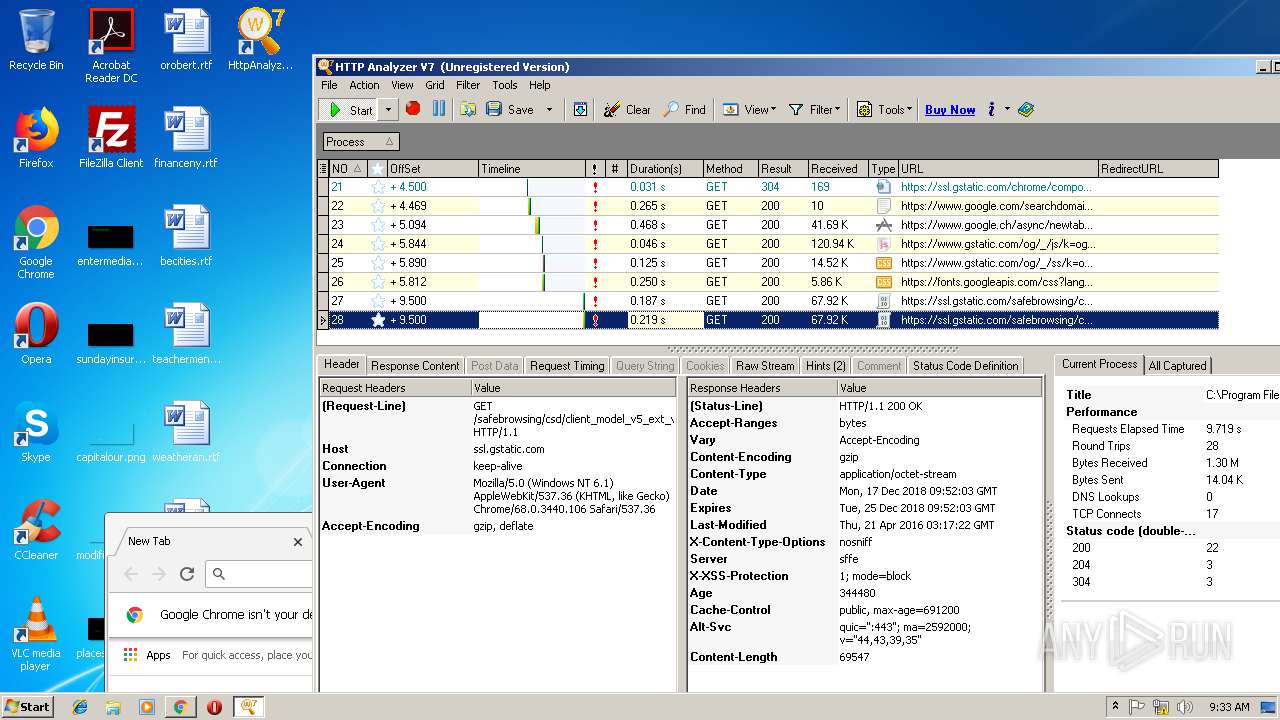
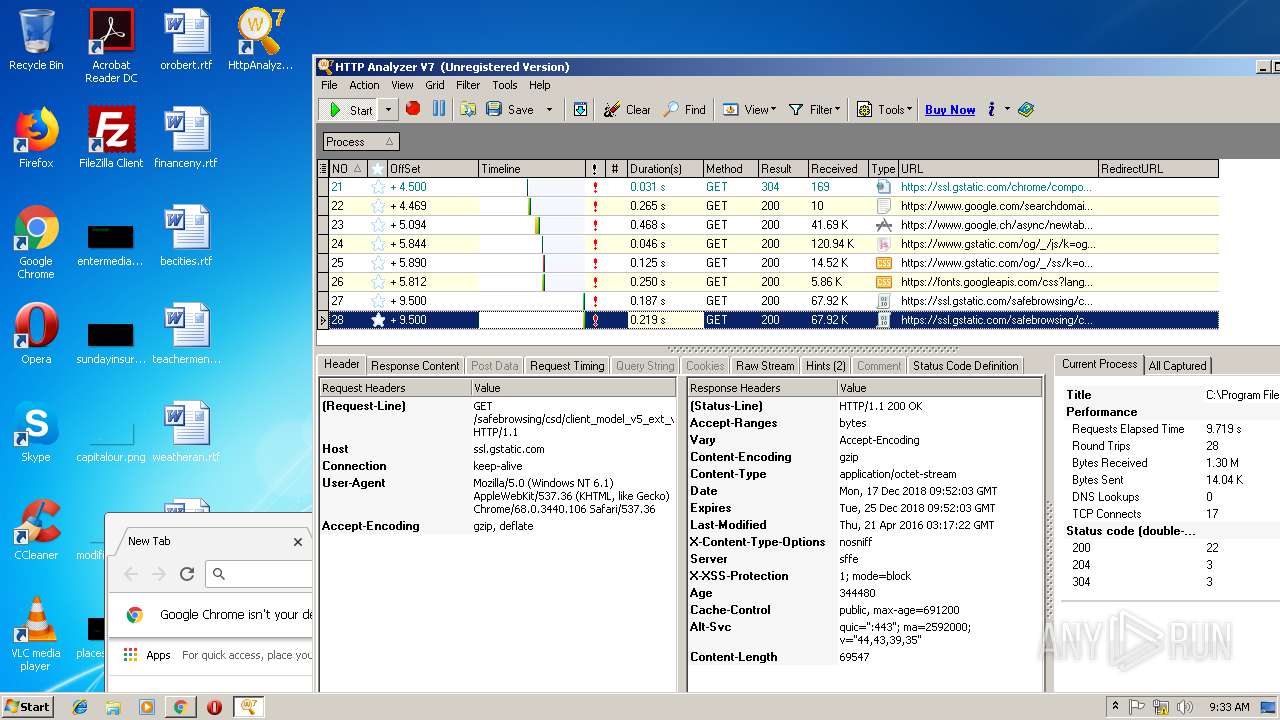
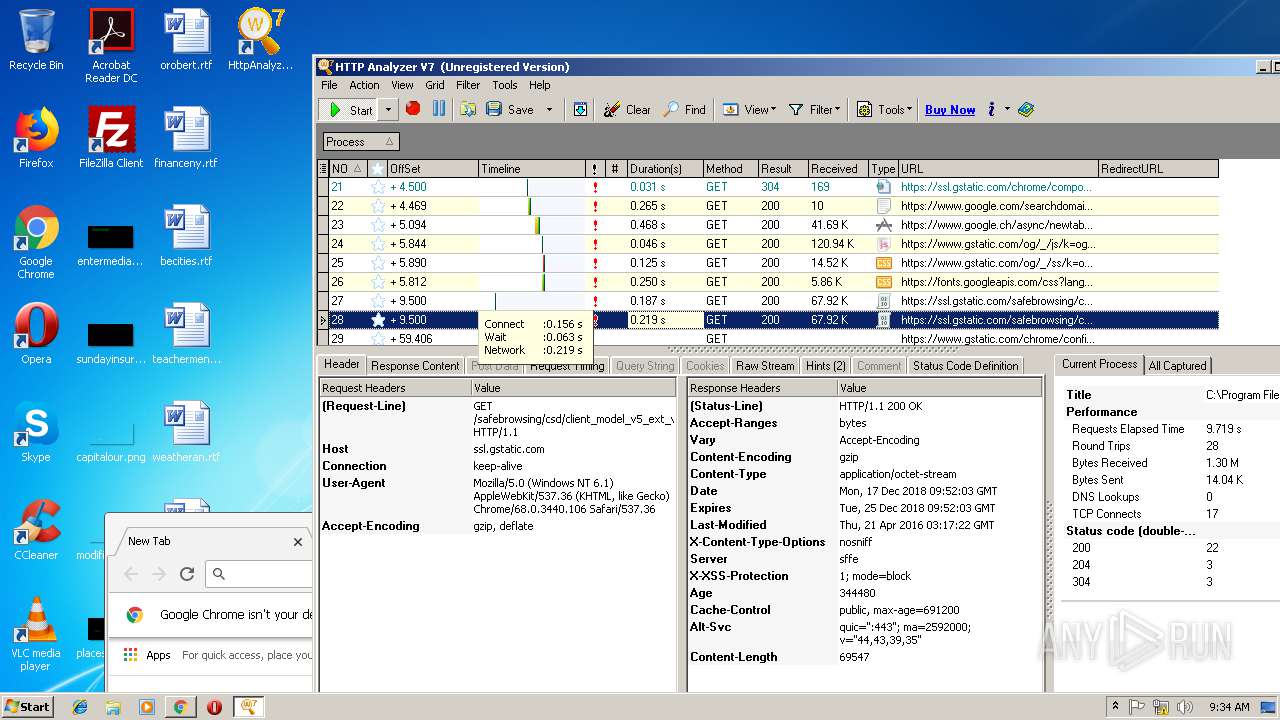
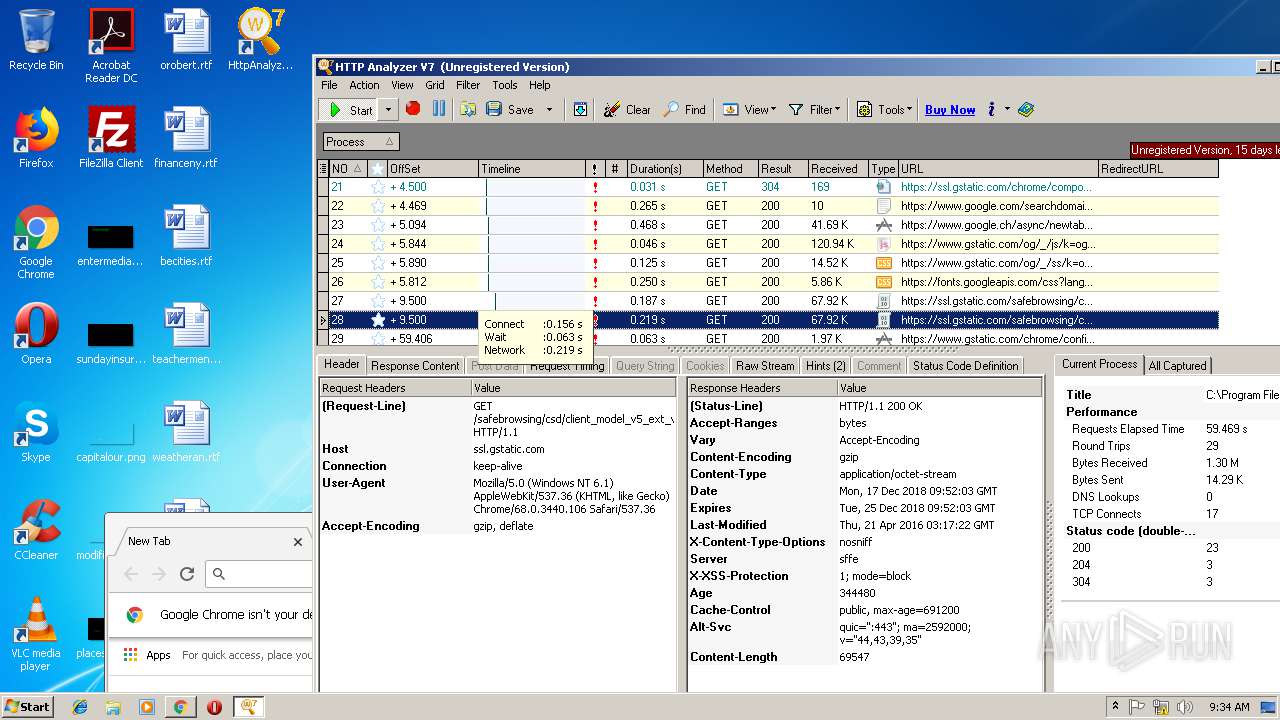
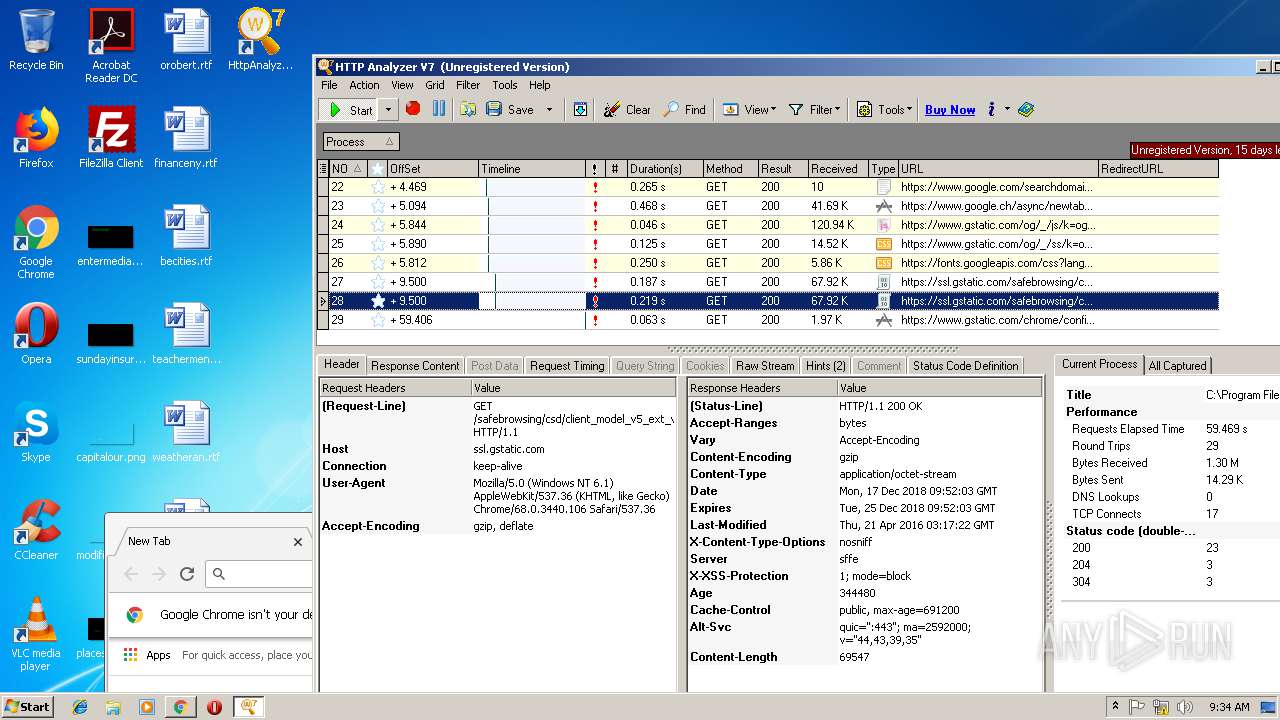
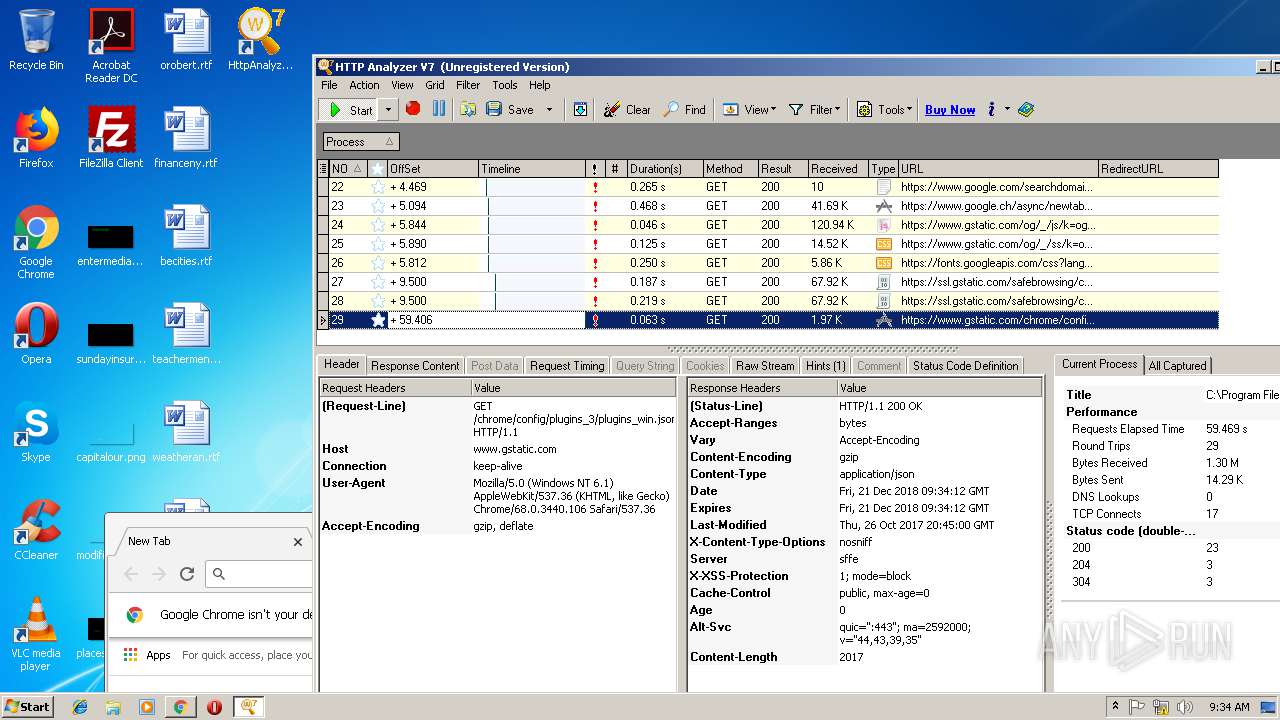
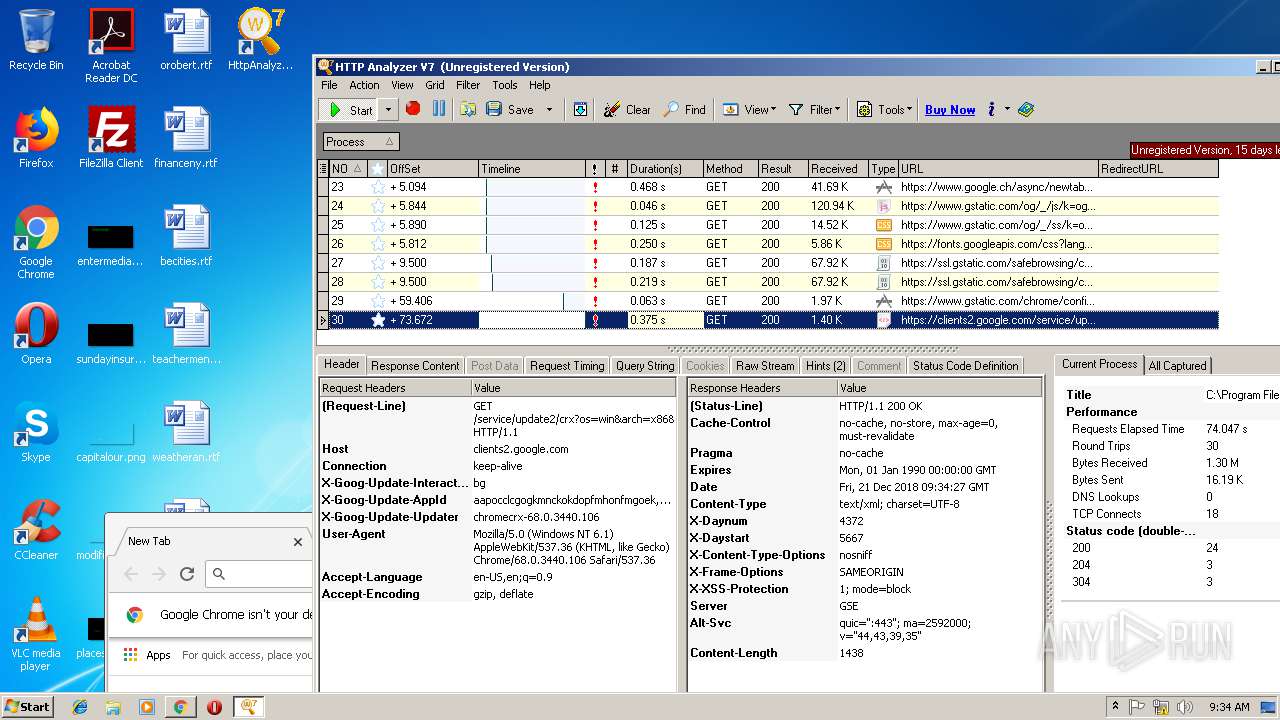
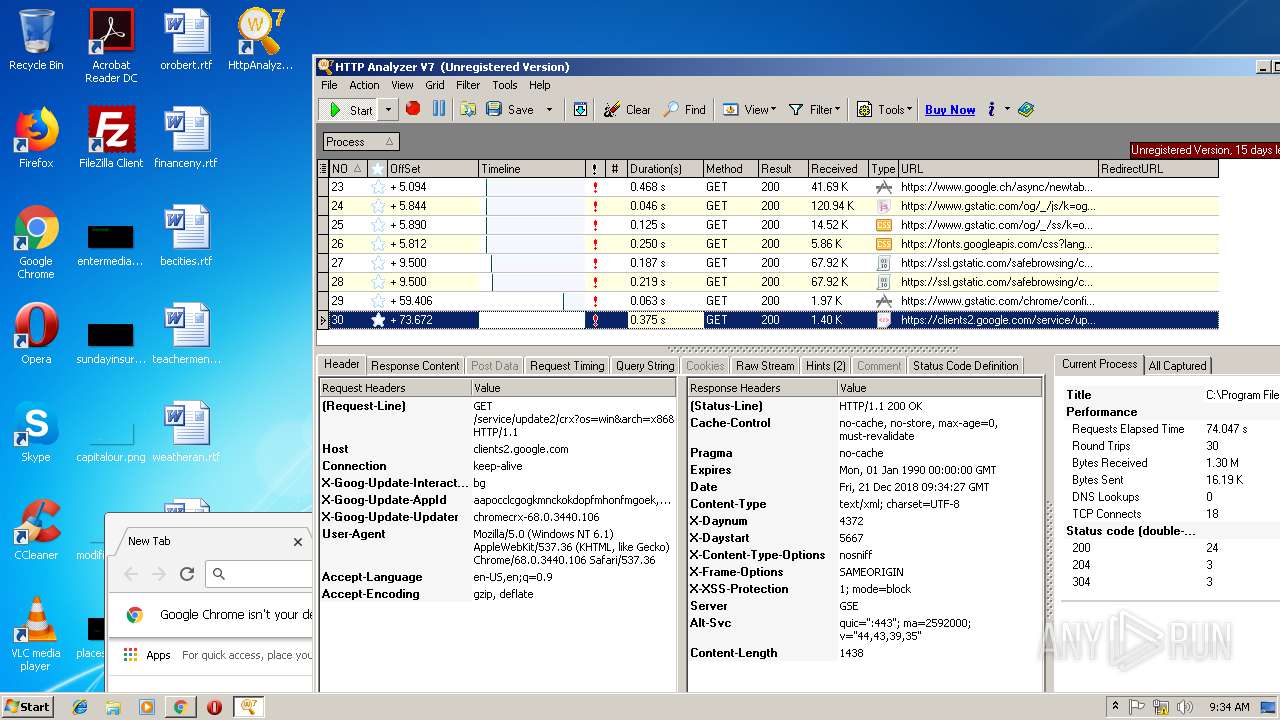
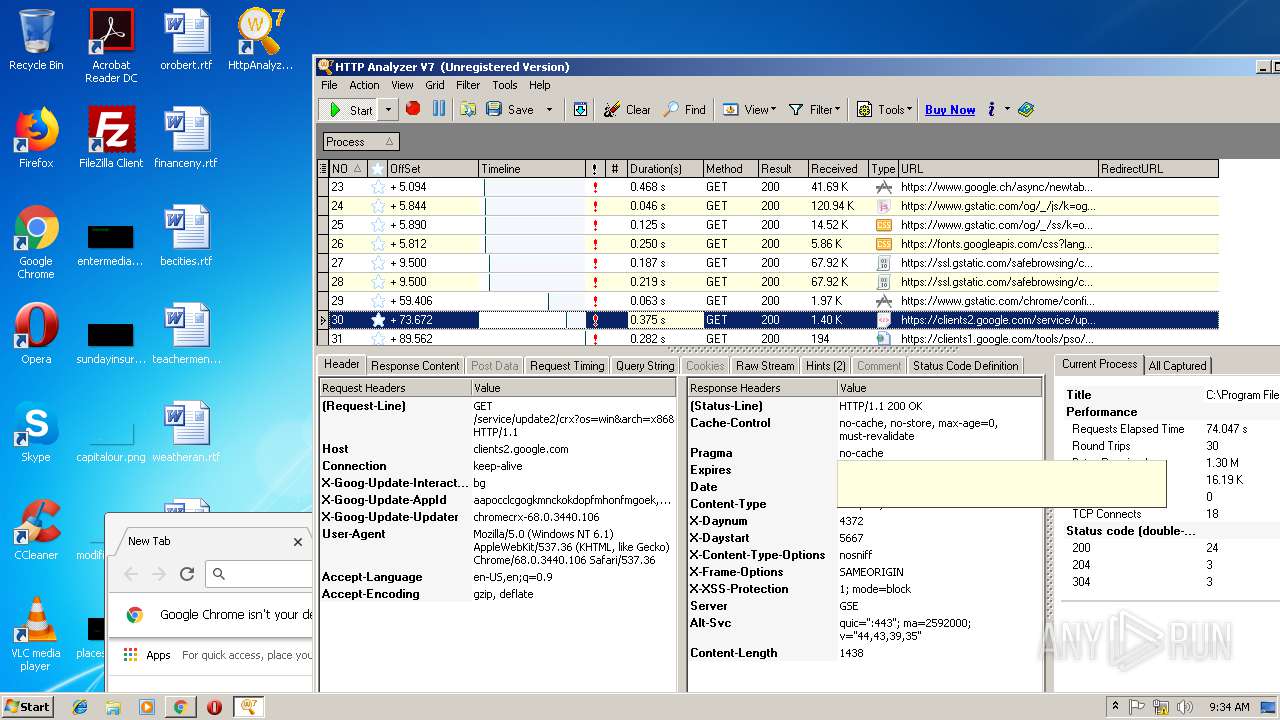
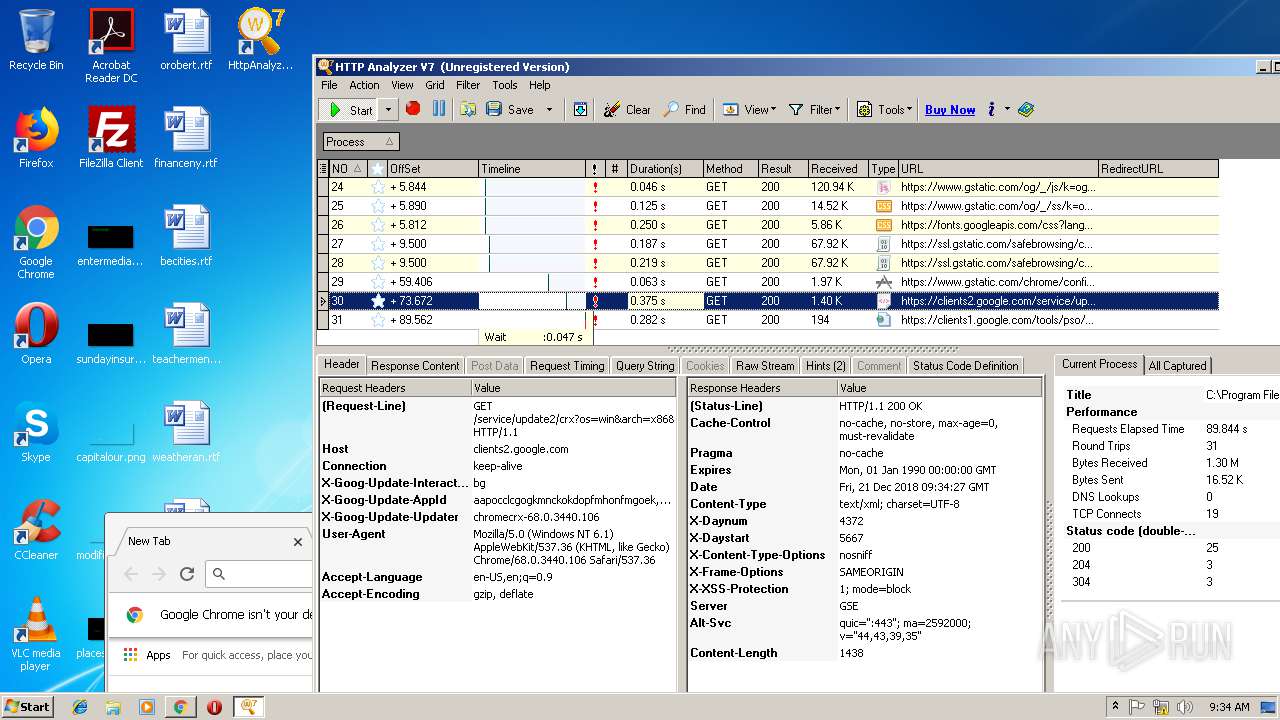
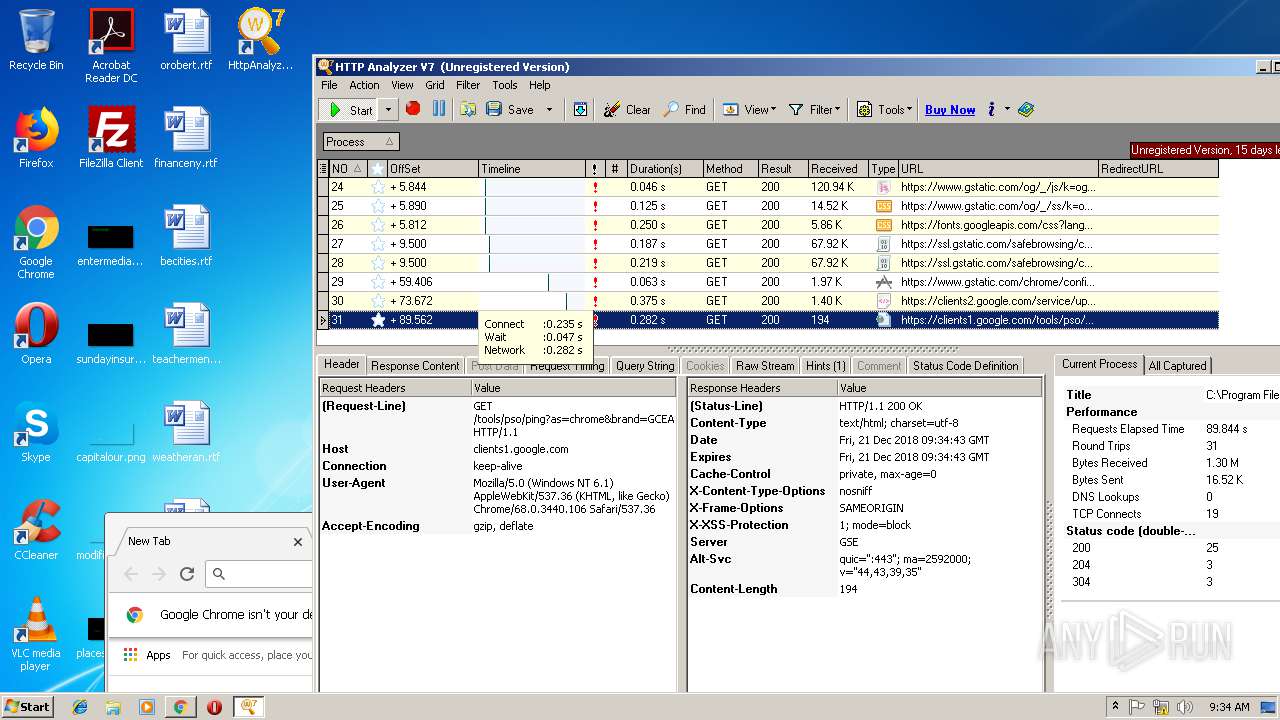
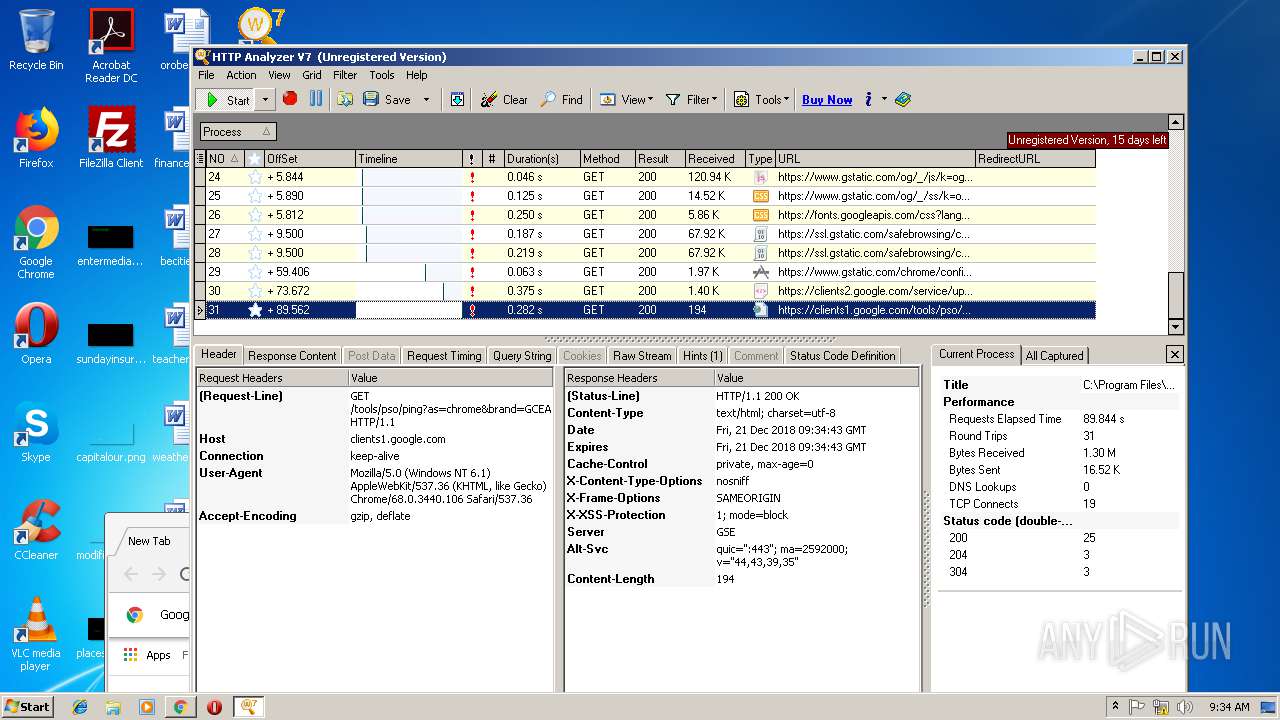
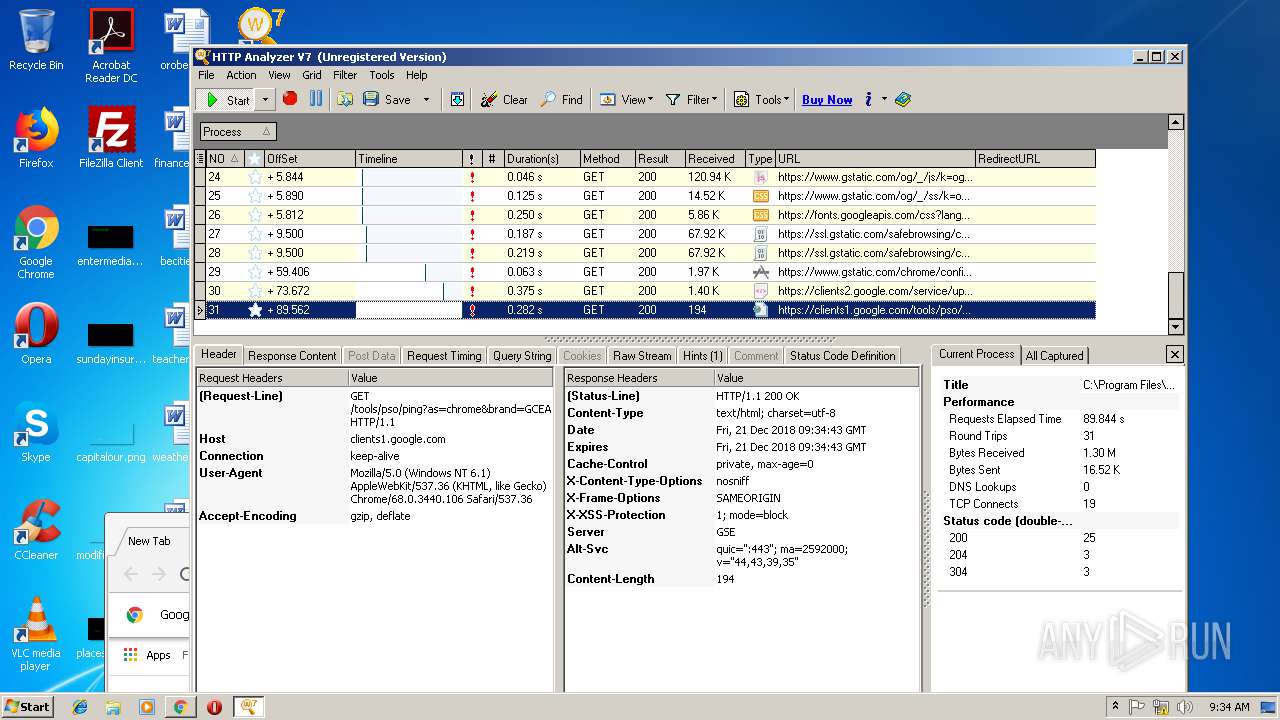
HTTP(S) requests
0
TCP/UDP connections
23
DNS requests
13
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2584 | chrome.exe | 216.58.205.238:443 | apis.google.com | Google Inc. | US | whitelisted |
2584 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
2584 | chrome.exe | 172.217.18.99:443 | www.google.ch | Google Inc. | US | whitelisted |
2584 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2584 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2584 | chrome.exe | 216.58.207.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
2584 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2584 | chrome.exe | 172.217.16.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2584 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2584 | chrome.exe | 216.58.207.35:443 | www.google.de | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.ch |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: FixTaskModalDialog |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: FixTaskModalDialog |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: AppDeActivateZOrderFix |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: ControlResizeFix |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: ActionListAVFix |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: ObjAutoDEPFix |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: ObjAutoDEPFix |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: CmdShowMinimizeFir |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: CmdShowMinimizeFix |
HttpAnalyzerStdV7.exe | VCLFixPack patch installed: MDIChildFocusFix |