| File name: | datadecrypt.exe |
| Full analysis: | https://app.any.run/tasks/37719108-51f9-4b29-b722-2b186f8a6c7b |
| Verdict: | Malicious activity |
| Analysis date: | January 28, 2024, 03:19:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5960D101C8170B432F93387B96927AF7 |
| SHA1: | 8D7E349C22A11F76FC13E9EDC50E25067766EF66 |
| SHA256: | F23542F7EE78D204034CB11A48C97B04E447FC17535133414DA453FADD4738CB |
| SSDEEP: | 98304:ODQPohs2E6S1RNJ31LawGx8lh6fPEXPYKzUyvtHLjAJ7MY2E8OiJW8VUvOZK3k+m:EhBgZLdOw |
MALICIOUS
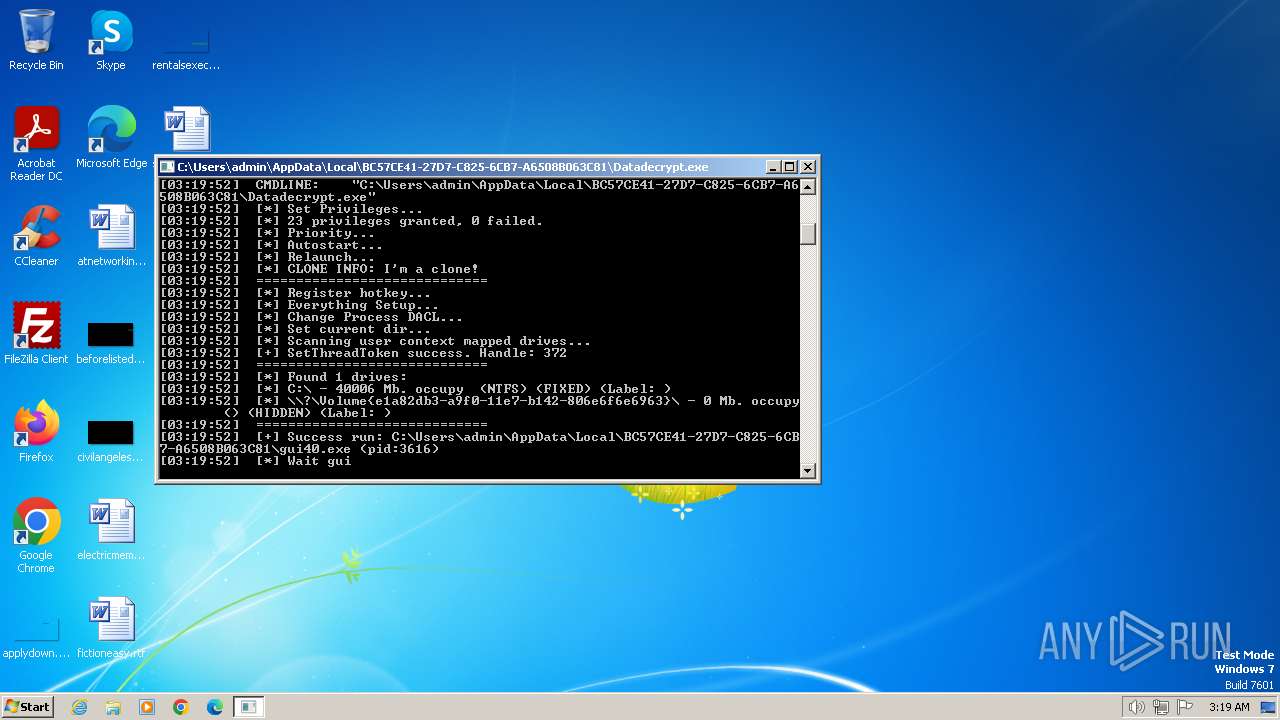
Drops the executable file immediately after the start
- datadecrypt.exe (PID: 2640)
- 7za.exe (PID: 680)
- datadecrypt.exe (PID: 2240)
- Datadecrypt.exe (PID: 956)
Known privilege escalation attack
- dllhost.exe (PID: 2208)
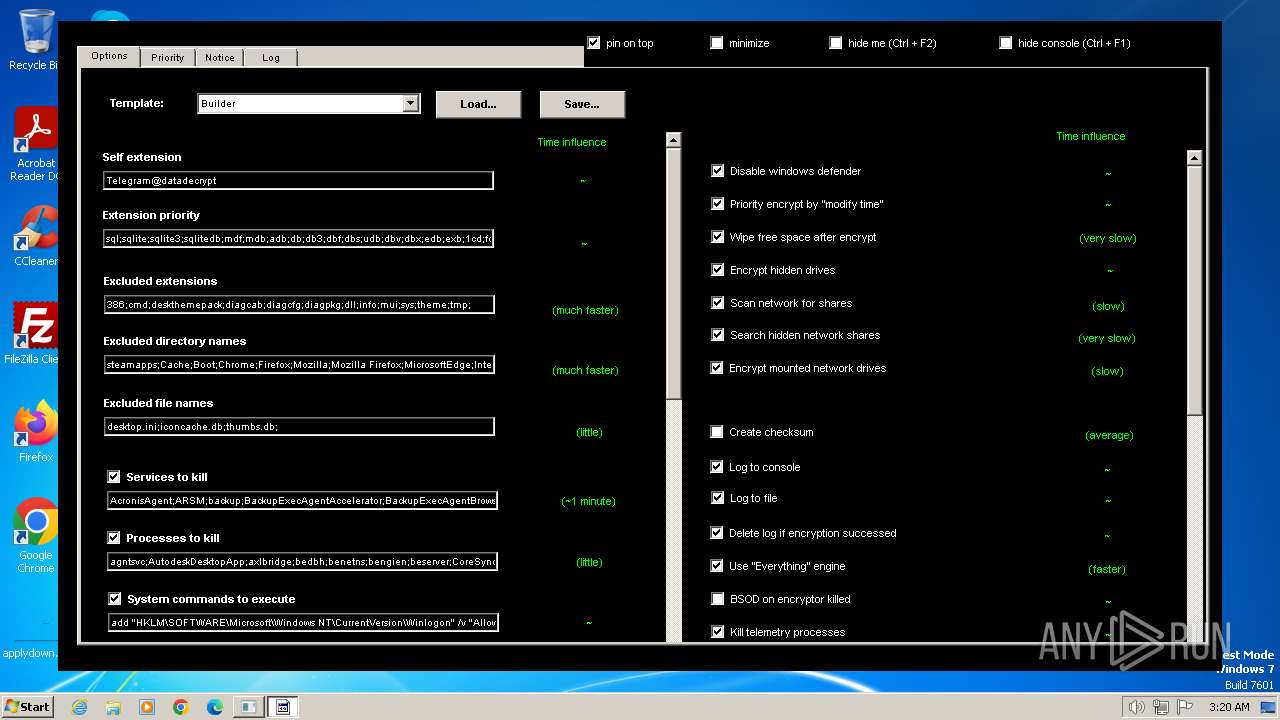
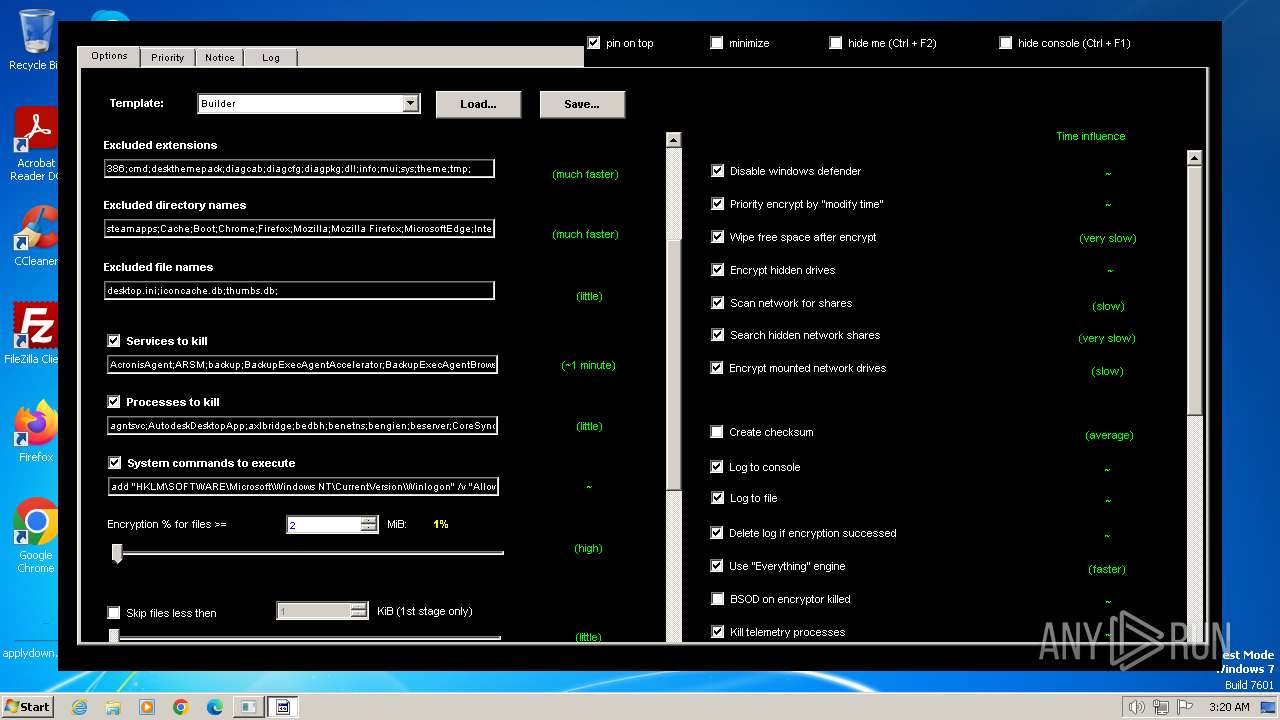
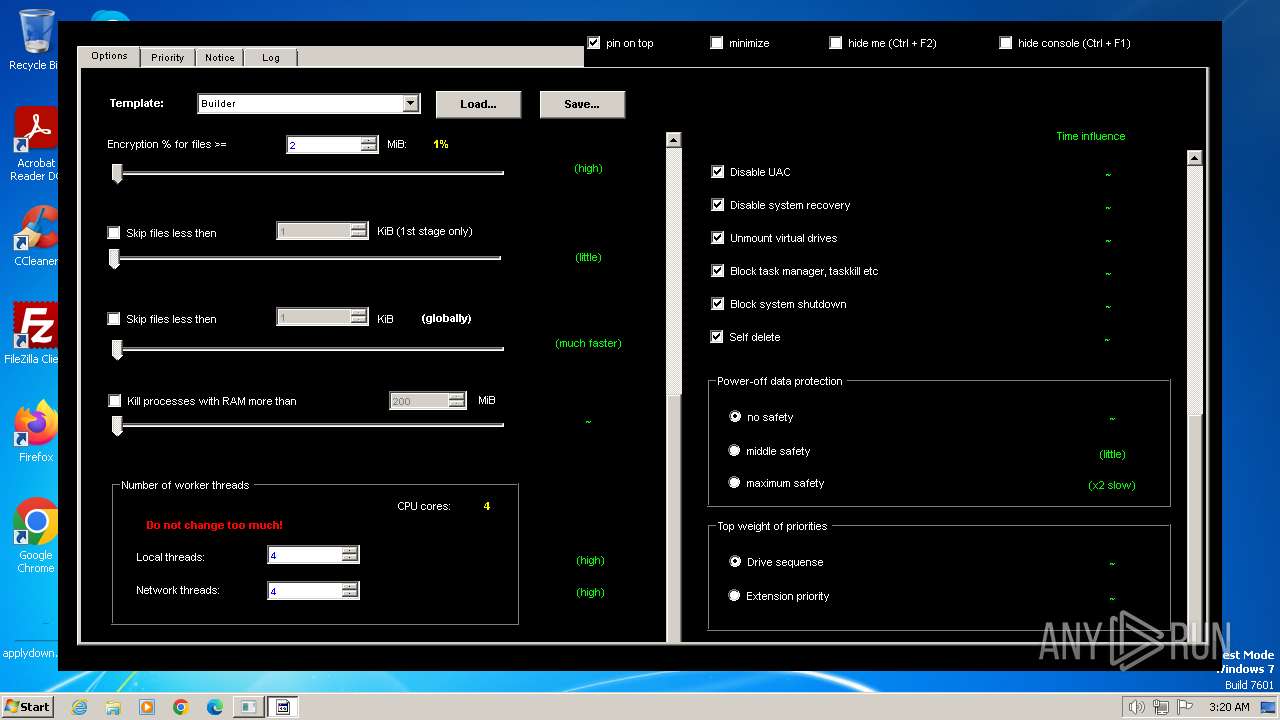
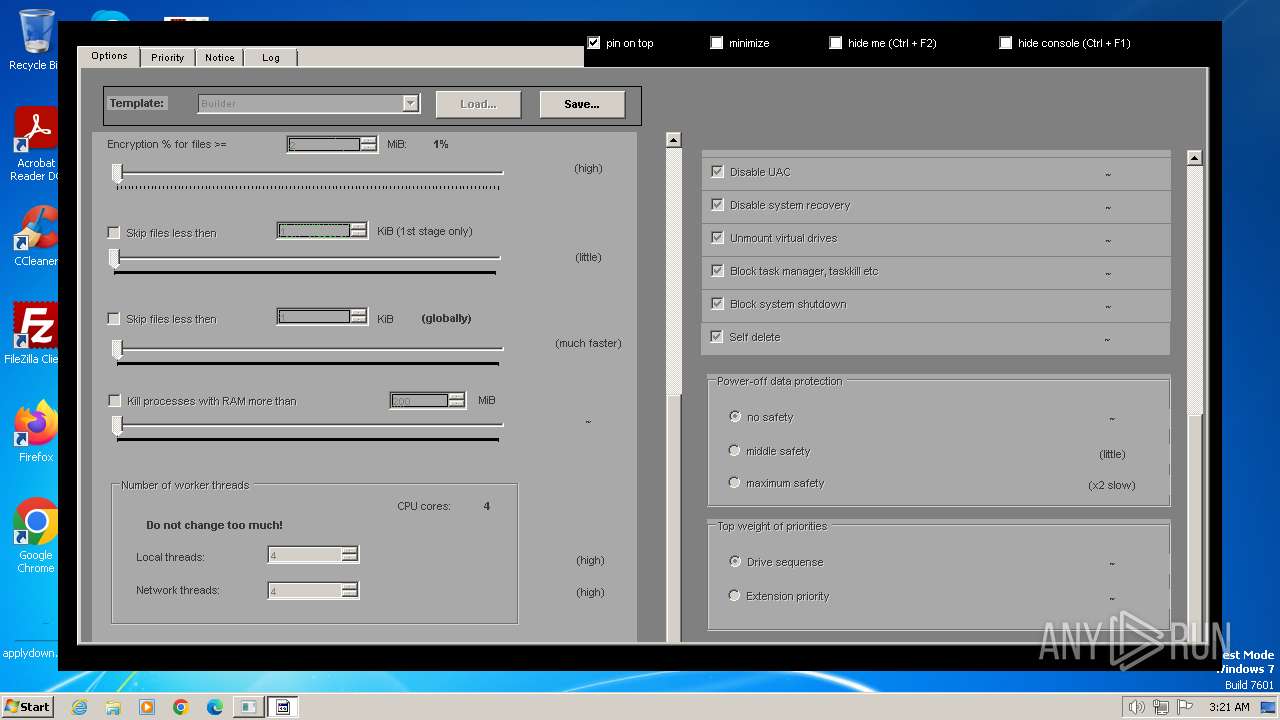
Disables Windows Defender
- DC.exe (PID: 2528)
- DC.exe (PID: 3572)
Creates or modifies Windows services
- DC.exe (PID: 2528)
- DC.exe (PID: 3572)
UAC/LUA settings modification
- Datadecrypt.exe (PID: 956)
Bypass execution policy to execute commands
- powershell.exe (PID: 292)
- powershell.exe (PID: 3904)
- powershell.exe (PID: 3656)
Changes powershell execution policy (Bypass)
- Datadecrypt.exe (PID: 956)
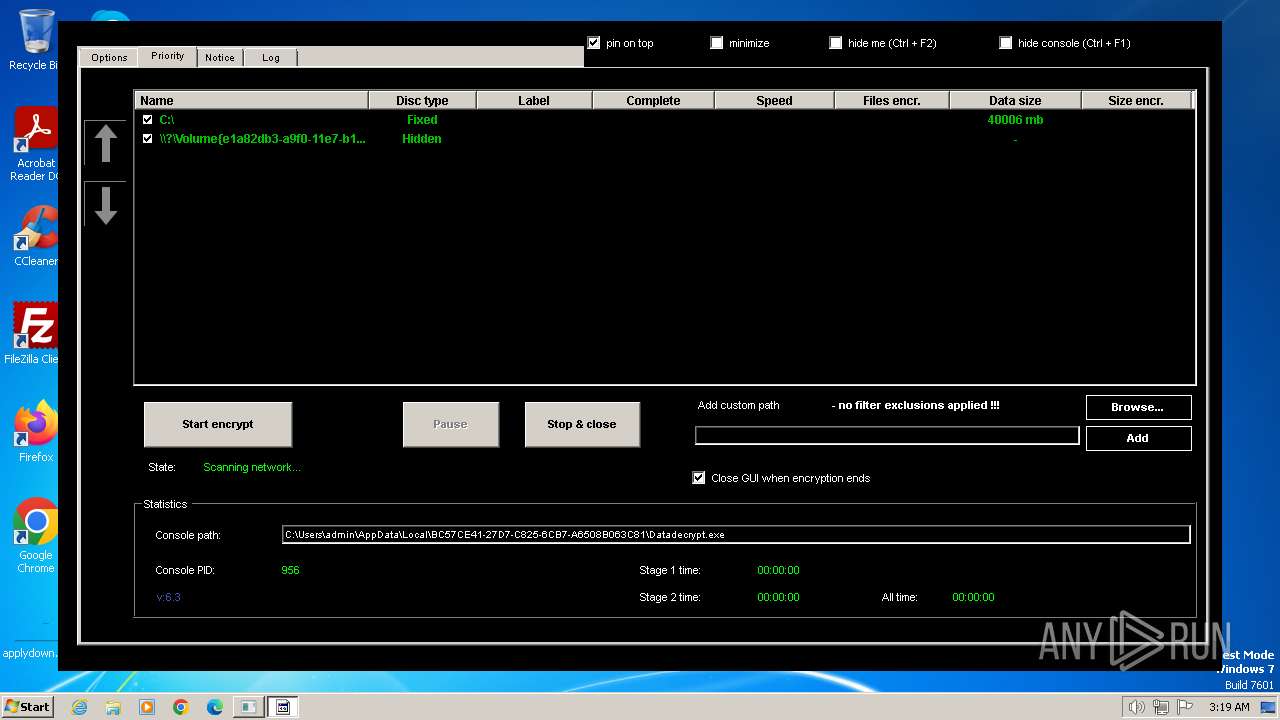
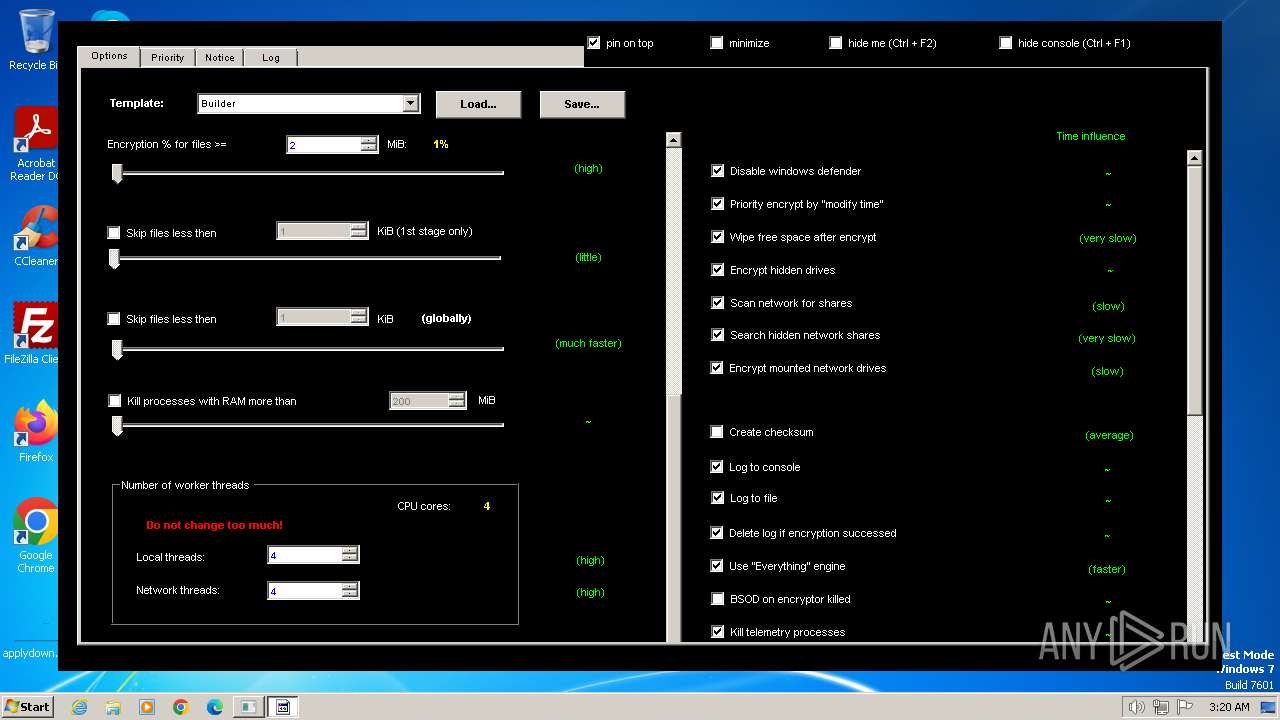
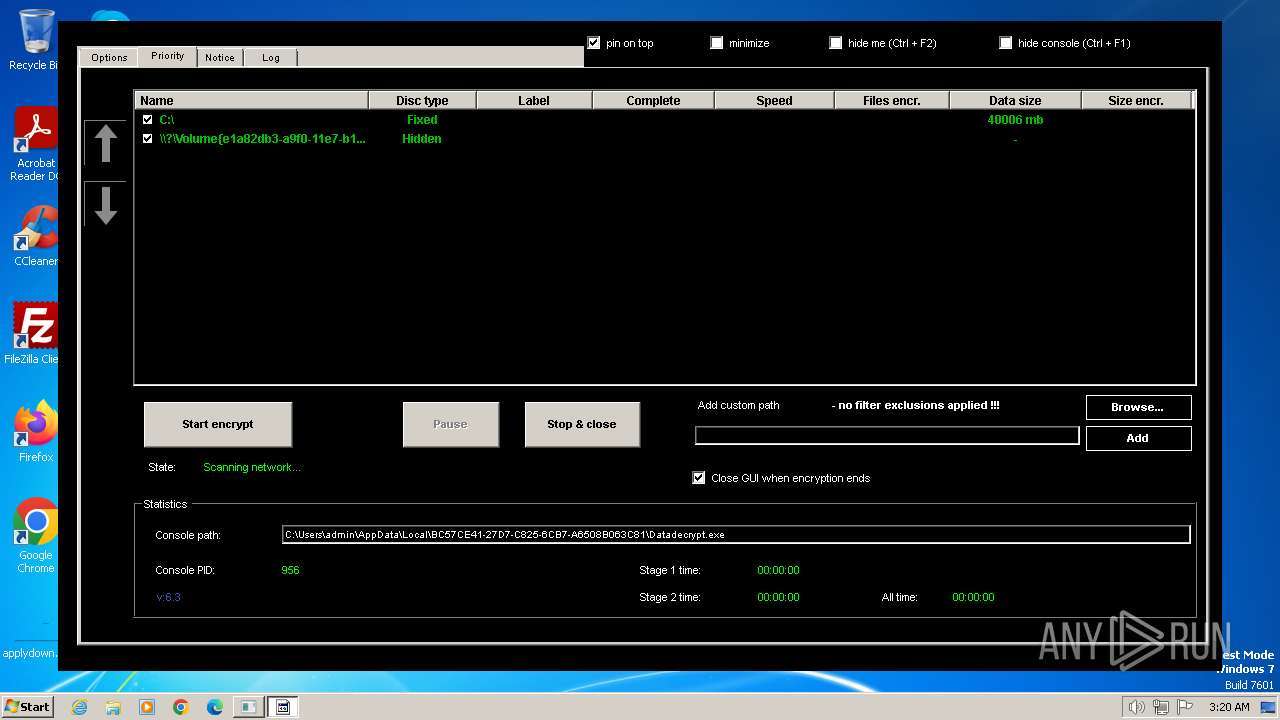
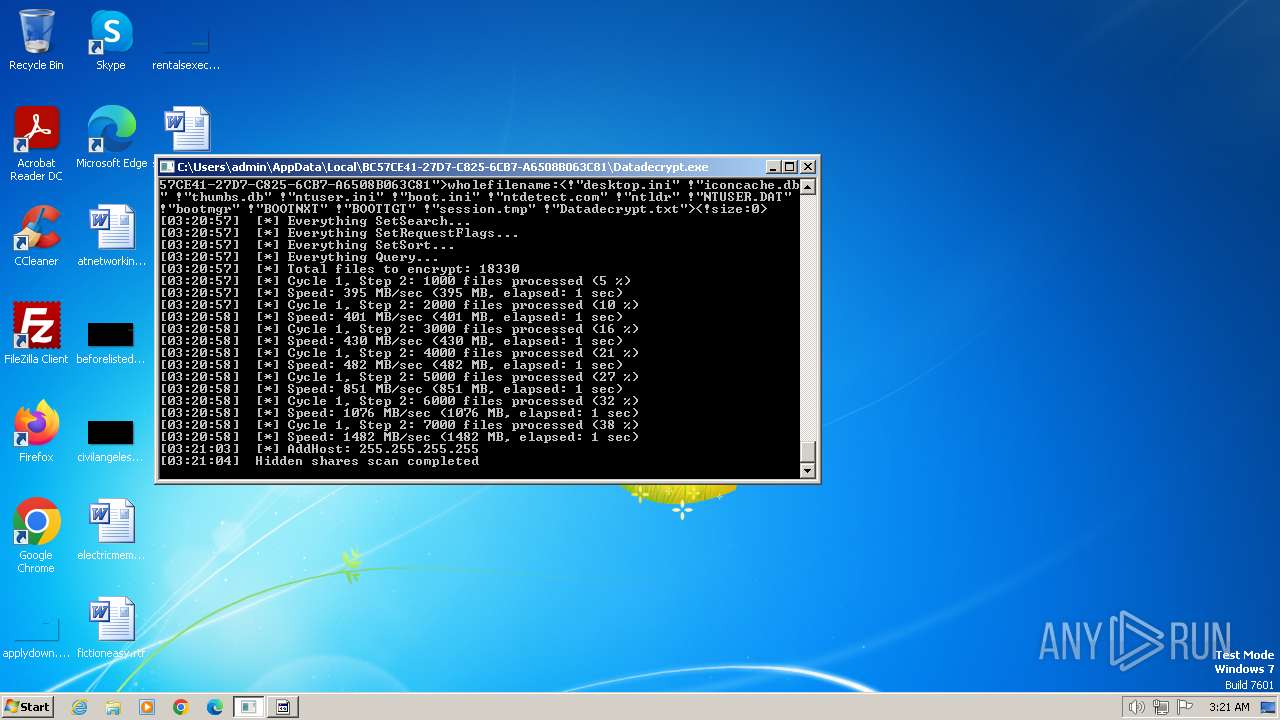
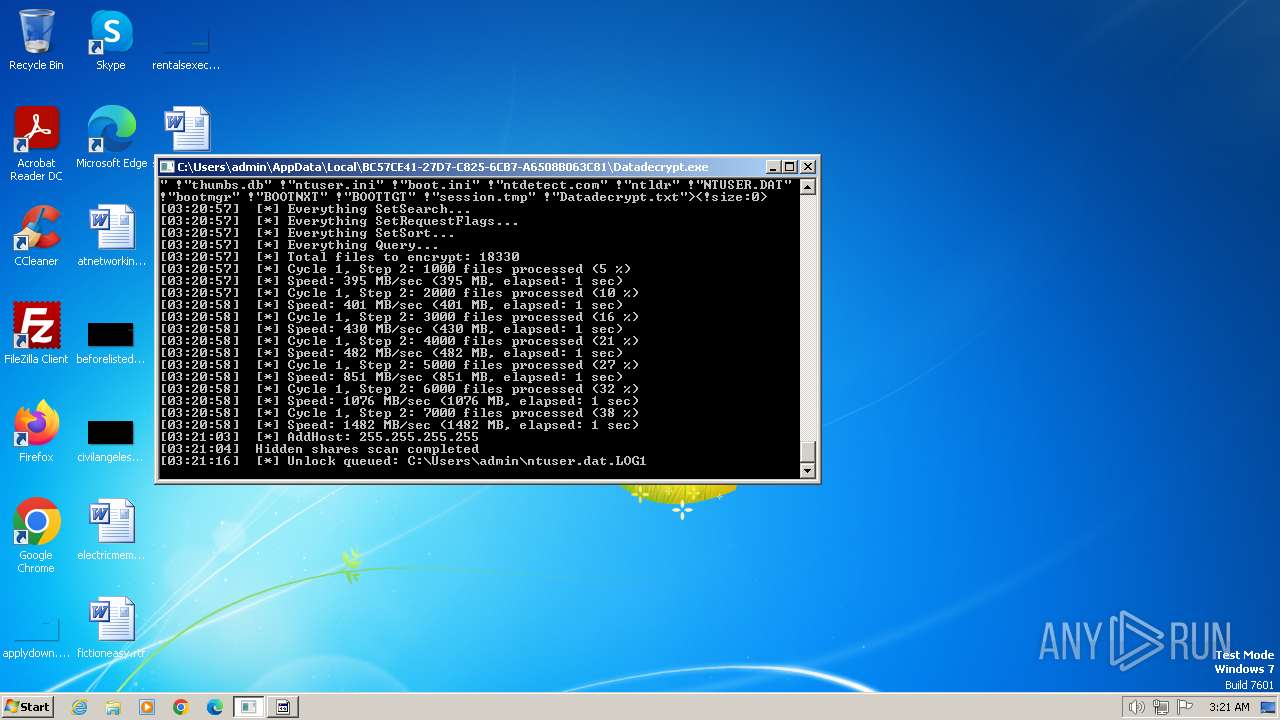
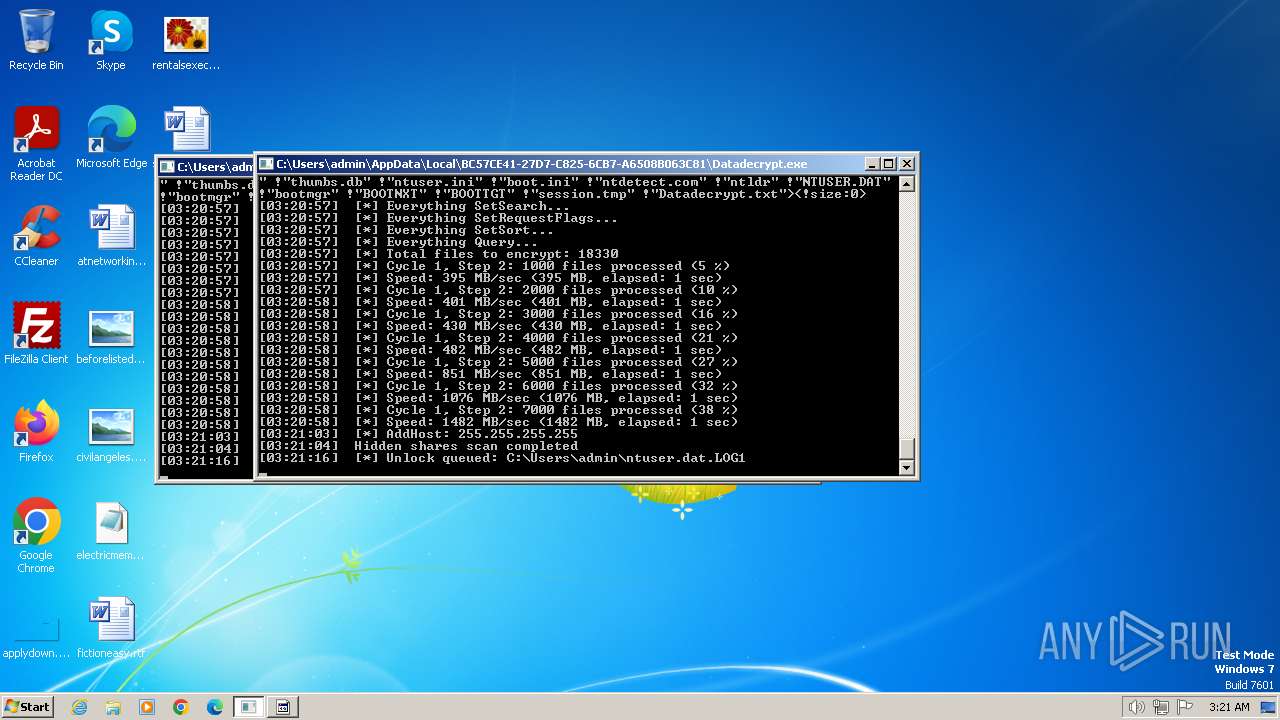
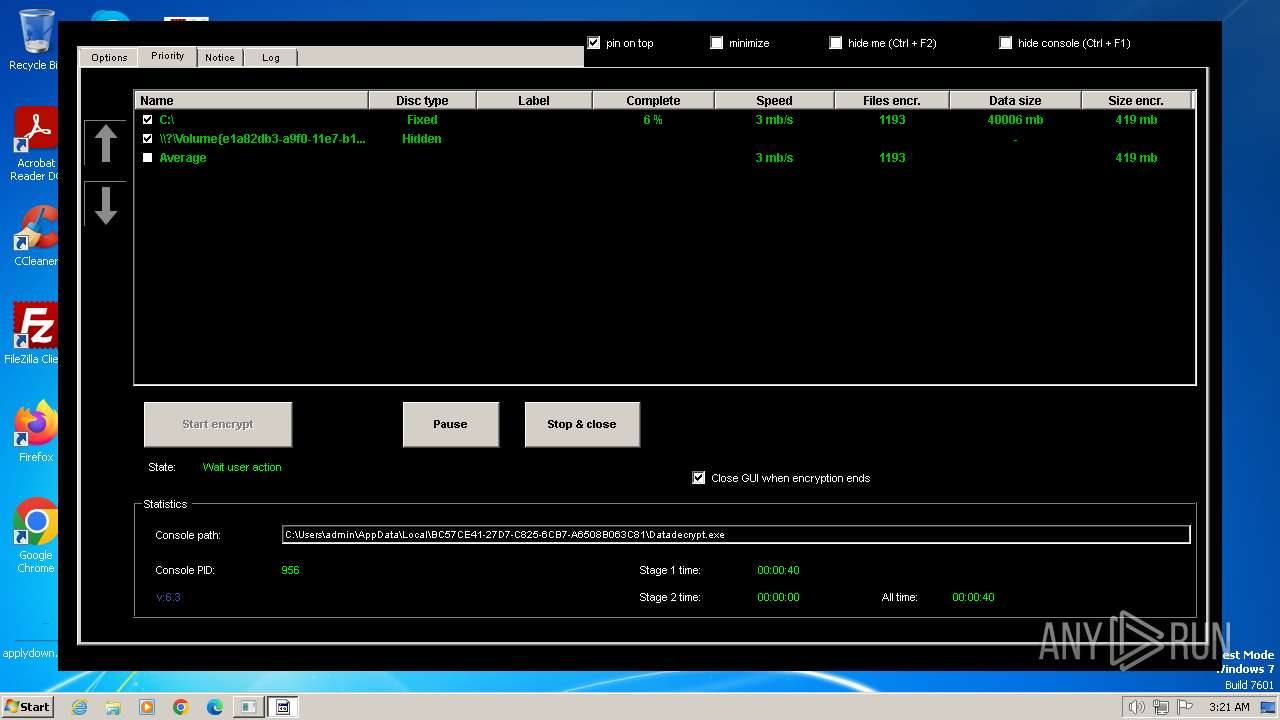
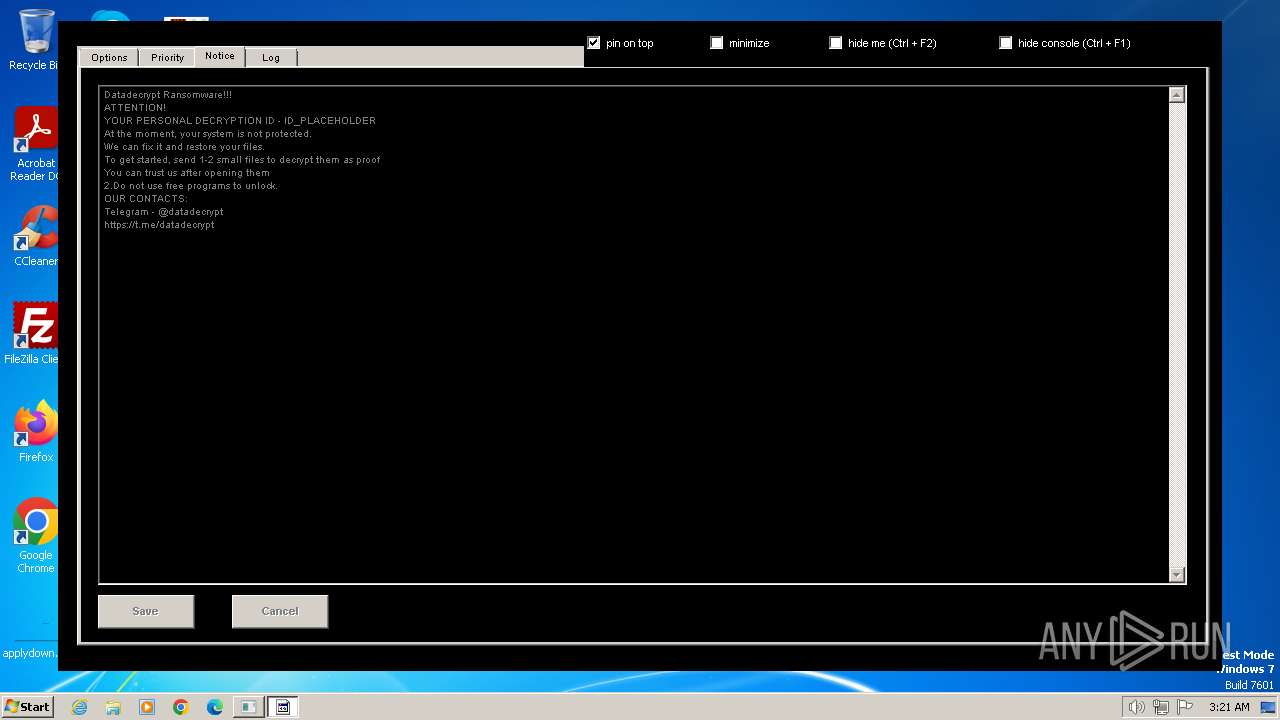
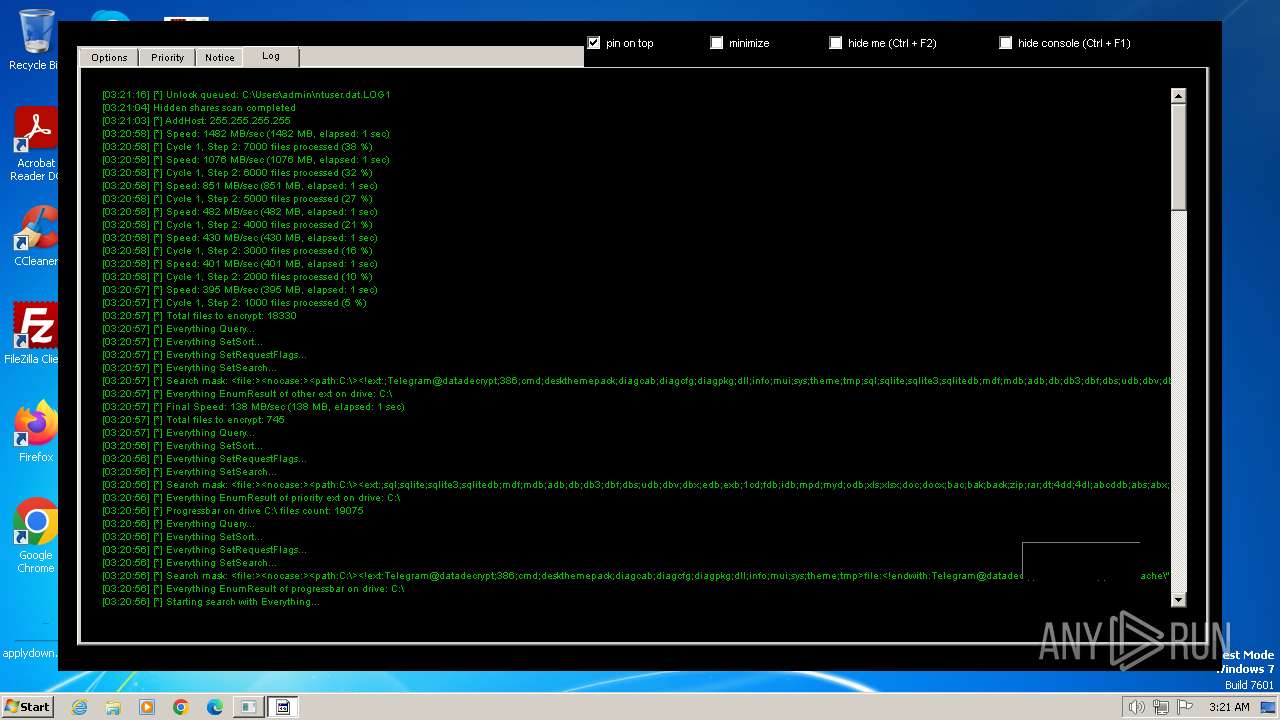
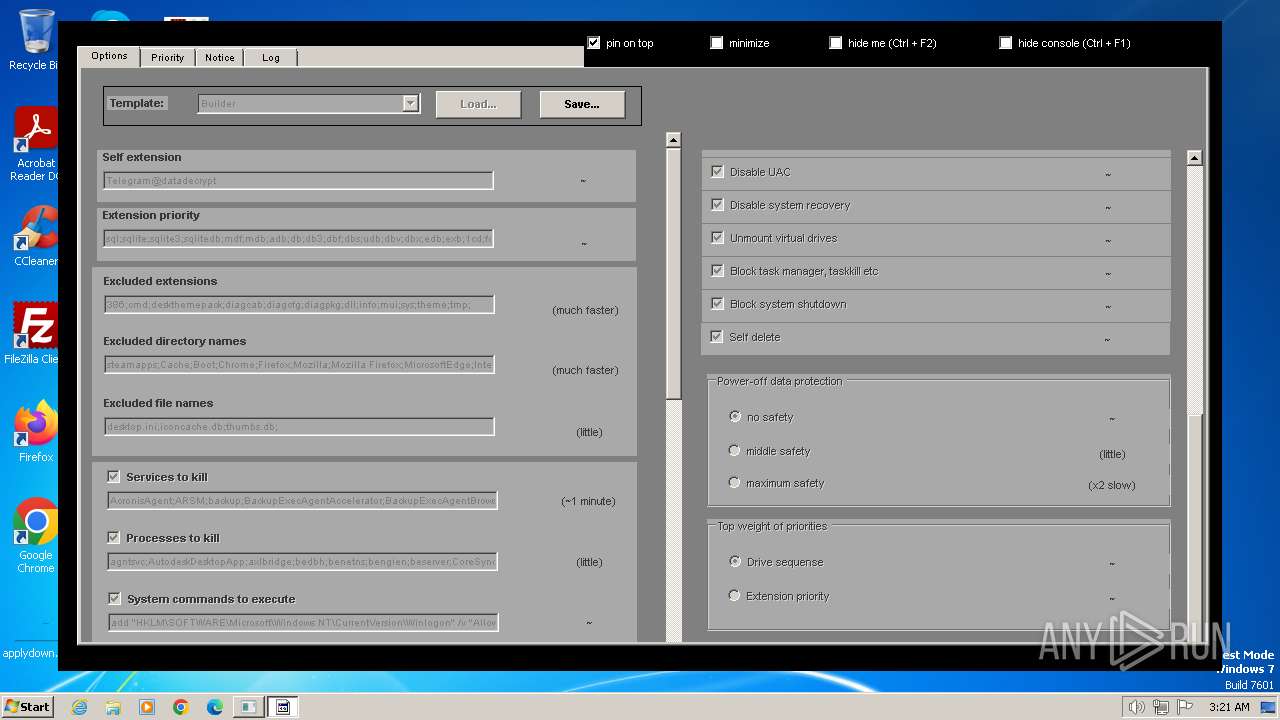
Renames files like ransomware
- Datadecrypt.exe (PID: 956)
Actions looks like stealing of personal data
- Datadecrypt.exe (PID: 956)
SUSPICIOUS
Executable content was dropped or overwritten
- datadecrypt.exe (PID: 2640)
- 7za.exe (PID: 680)
- datadecrypt.exe (PID: 2240)
- Datadecrypt.exe (PID: 956)
Drops 7-zip archiver for unpacking
- datadecrypt.exe (PID: 2640)
- datadecrypt.exe (PID: 2240)
Reads the Internet Settings
- datadecrypt.exe (PID: 2640)
- powershell.exe (PID: 3656)
- powershell.exe (PID: 292)
- powershell.exe (PID: 3904)
Starts CMD.EXE for commands execution
- datadecrypt.exe (PID: 2640)
- Datadecrypt.exe (PID: 956)
Executing commands from ".cmd" file
- datadecrypt.exe (PID: 2640)
Application launched itself
- Datadecrypt.exe (PID: 956)
- DC.exe (PID: 2528)
The executable file from the user directory is run by the CMD process
- DC.exe (PID: 2528)
Creates or modifies Windows services
- Datadecrypt.exe (PID: 956)
Uses powercfg.exe to modify the power settings
- Datadecrypt.exe (PID: 956)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 292)
- powershell.exe (PID: 3656)
- powershell.exe (PID: 3904)
Process drops legitimate windows executable
- Datadecrypt.exe (PID: 956)
Executes as Windows Service
- systray.exe (PID: 2244)
Starts POWERSHELL.EXE for commands execution
- Datadecrypt.exe (PID: 956)
INFO
Checks supported languages
- datadecrypt.exe (PID: 2640)
- 7za.exe (PID: 2560)
- 7za.exe (PID: 680)
- datadecrypt.exe (PID: 2240)
- gui40.exe (PID: 3616)
- Everything.exe (PID: 2248)
- Datadecrypt.exe (PID: 2544)
- Datadecrypt.exe (PID: 2556)
- DC.exe (PID: 2528)
- Datadecrypt.exe (PID: 956)
- DC.exe (PID: 3572)
- Datadecrypt.exe (PID: 3136)
Reads the computer name
- datadecrypt.exe (PID: 2640)
- 7za.exe (PID: 2560)
- 7za.exe (PID: 680)
- datadecrypt.exe (PID: 2240)
- Datadecrypt.exe (PID: 956)
- gui40.exe (PID: 3616)
- Everything.exe (PID: 2248)
- DC.exe (PID: 3572)
- DC.exe (PID: 2528)
- Datadecrypt.exe (PID: 3136)
- Datadecrypt.exe (PID: 2544)
- Datadecrypt.exe (PID: 2556)
Create files in a temporary directory
- 7za.exe (PID: 680)
- datadecrypt.exe (PID: 2640)
- DC.exe (PID: 2528)
Creates files or folders in the user directory
- datadecrypt.exe (PID: 2240)
- Datadecrypt.exe (PID: 956)
- gui40.exe (PID: 3616)
Checks transactions between databases Windows and Oracle
- datadecrypt.exe (PID: 2240)
Reads the machine GUID from the registry
- datadecrypt.exe (PID: 2240)
- gui40.exe (PID: 3616)
Reads mouse settings
- DC.exe (PID: 2528)
- DC.exe (PID: 3572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:31 01:38:51+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 101888 |
| InitializedDataSize: | 87040 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1942f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
101
Monitored processes
34
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | powershell.exe -ExecutionPolicy Bypass "Get-VM | Stop-VM" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Datadecrypt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 560 | powercfg.exe -SETDCVALUEINDEX 8c5e7fda-e8bf-4a96-9a85-a6e23a8c635c 4f971e89-eebd-4455-a8de-9e59040e7347 96996bc0-ad50-47ec-923b-6f41874dd9eb 0 | C:\Windows\System32\powercfg.exe | — | Datadecrypt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 680 | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\7za.exe" x -y -p2683527442232016684 Everything64.dll | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\7za.exe | datadecrypt.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console Exit code: 0 Version: 21.06 Modules
| |||||||||||||||
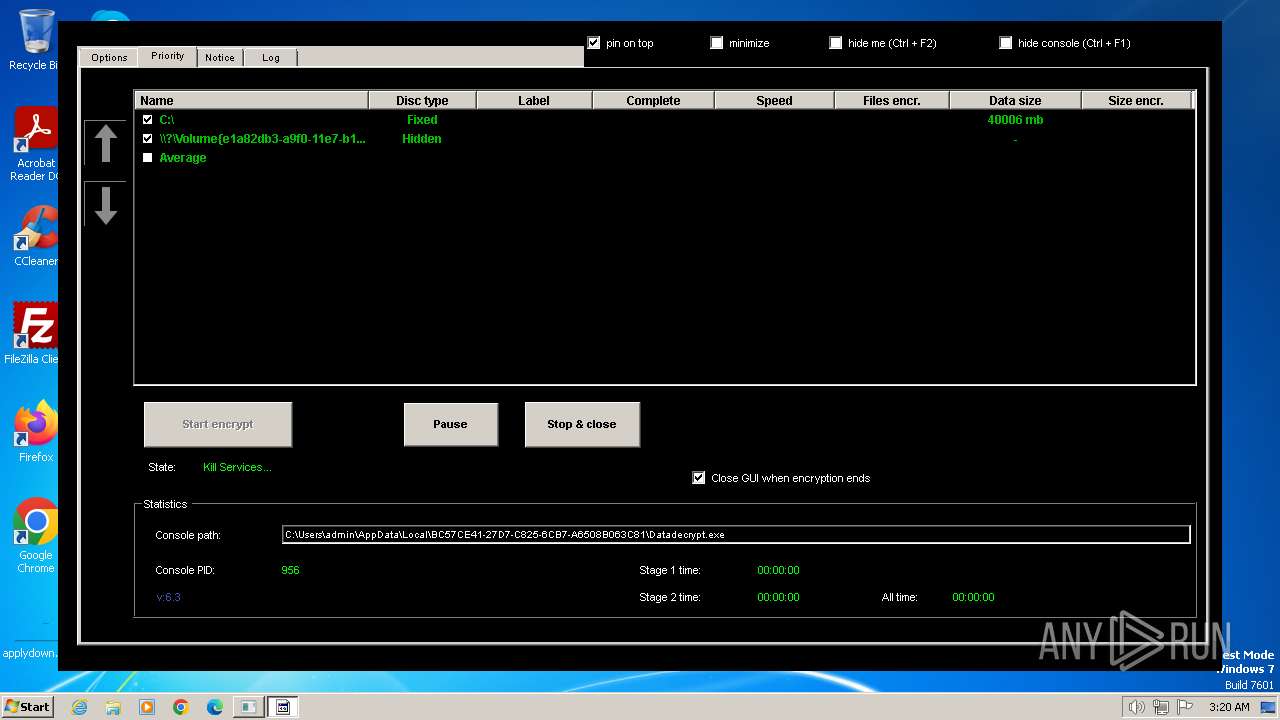
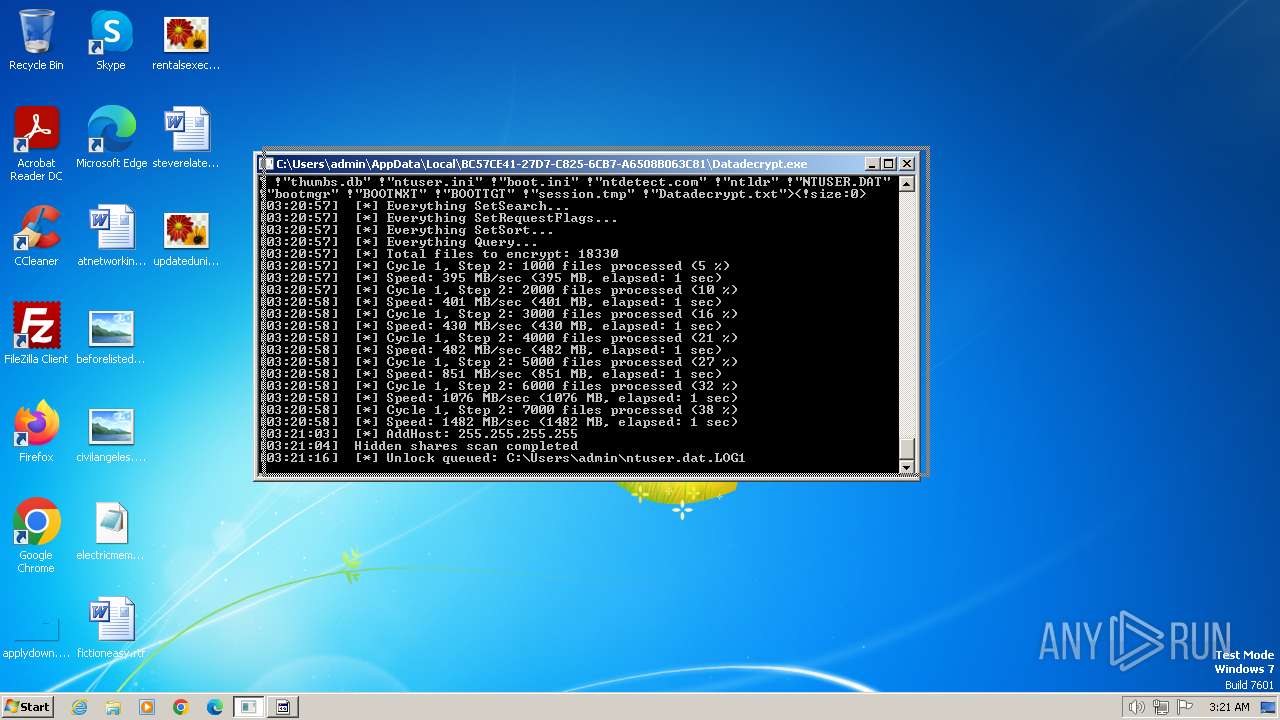
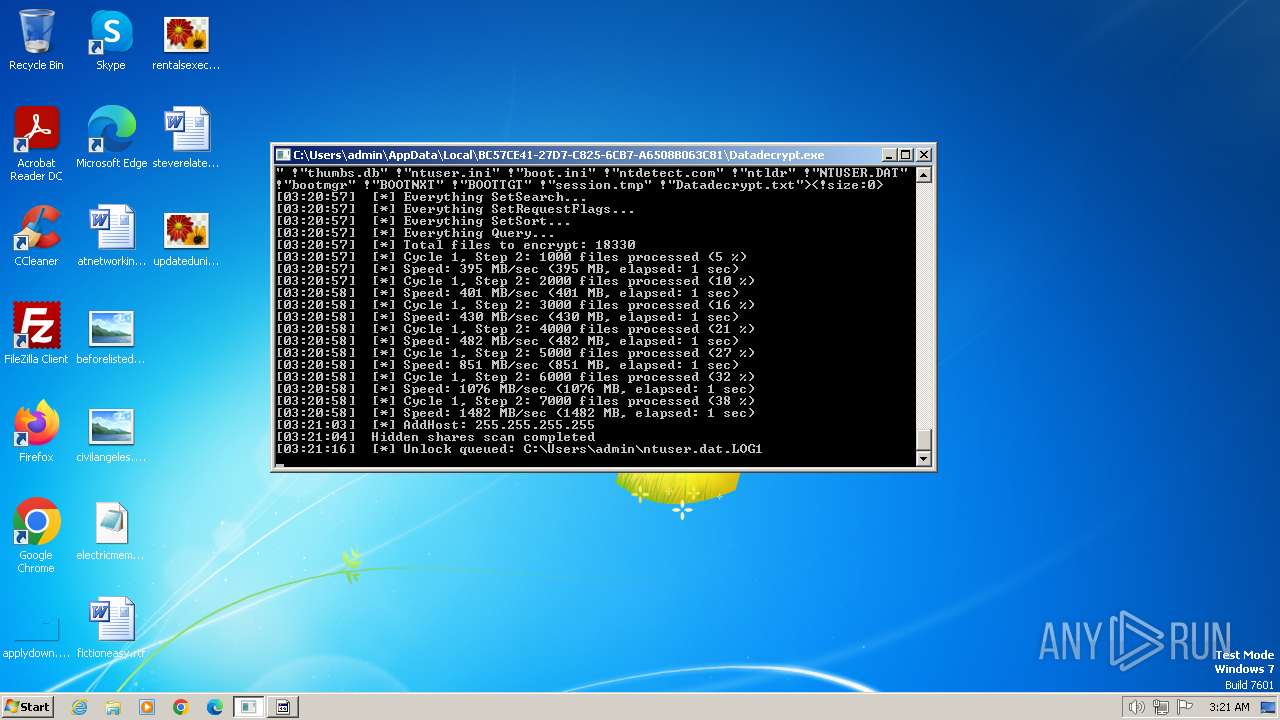
| 956 | "C:\Users\admin\AppData\Local\BC57CE41-27D7-C825-6CB7-A6508B063C81\Datadecrypt.exe" | C:\Users\admin\AppData\Local\BC57CE41-27D7-C825-6CB7-A6508B063C81\Datadecrypt.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 968 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\7ZSfx000.cmd" " | C:\Windows\System32\cmd.exe | — | datadecrypt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2208 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2240 | "C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\datadecrypt.exe" | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\datadecrypt.exe | datadecrypt.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2244 | C:\Windows\System32\Systray.exe C:\Windows\system32\SearchIndexer.exe /Embedding | C:\Windows\System32\systray.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Systray .exe stub Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2248 | "C:\Users\admin\AppData\Local\BC57CE41-27D7-C825-6CB7-A6508B063C81\Everything.exe" -startup | C:\Users\admin\AppData\Local\BC57CE41-27D7-C825-6CB7-A6508B063C81\Everything.exe | — | Datadecrypt.exe | |||||||||||
User: admin Company: voidtools Integrity Level: HIGH Description: Everything Exit code: 0 Version: 1.4.1.1015 Modules
| |||||||||||||||
| 2528 | DC.exe /D | C:\Users\admin\AppData\Local\BC57CE41-27D7-C825-6CB7-A6508B063C81\DC.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
4 842
Read events
4 776
Write events
60
Delete events
6
Modification events
| (PID) Process: | (2640) datadecrypt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2640) datadecrypt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2640) datadecrypt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2640) datadecrypt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2208) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2208) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2208) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2208) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (956) Datadecrypt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (956) Datadecrypt.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\SDRSVC |
| Operation: | write | Name: | Start |
Value: 3 | |||
Executable files
89
Suspicious files
2 249
Text files
377
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 680 | 7za.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Everything2.ini | text | |
MD5:51014C0C06ACDD80F9AE4469E7D30A9E | SHA256:89AD2164717BD5F5F93FBB4CEBF0EFEB473097408FDDFC7FC7B924D790514DC5 | |||
| 2640 | datadecrypt.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\7za.exe | executable | |
MD5:B93EB0A48C91A53BDA6A1A074A4B431E | SHA256:AB15A9B27EE2D69A8BC8C8D1F5F40F28CD568F5CBB28D36ED938110203F8D142 | |||
| 680 | 7za.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\gui40.exe | executable | |
MD5:57850A4490A6AFD1EF682EB93EA45E65 | SHA256:31FEFF32D23728B39ED813C1E7DC5FE6A87DCD4D10AA995446A8C5EB5DA58615 | |||
| 680 | 7za.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\xdel.exe | executable | |
MD5:803DF907D936E08FBBD06020C411BE93 | SHA256:E8EAA39E2ADFD49AB69D7BB8504CCB82A902C8B48FBC256472F36F41775E594C | |||
| 2640 | datadecrypt.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Everything.exe | executable | |
MD5:C44487CE1827CE26AC4699432D15B42A | SHA256:4C83E46A29106AFBAF5279029D102B489D958781764289B61AB5B618A4307405 | |||
| 2240 | datadecrypt.exe | C:\Users\admin\AppData\Local\BC57CE41-27D7-C825-6CB7-A6508B063C81\DC.exe | executable | |
MD5:AC34BA84A5054CD701EFAD5DD14645C9 | SHA256:C576F7F55C4C0304B290B15E70A638B037DF15C69577CD6263329C73416E490E | |||
| 2640 | datadecrypt.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Everything32.dll | executable | |
MD5:3B03324537327811BBBAFF4AAFA4D75B | SHA256:8CAE8A9740D466E17F16481E68DE9CBD58265863C3924D66596048EDFD87E880 | |||
| 2240 | datadecrypt.exe | C:\Users\admin\AppData\Local\BC57CE41-27D7-C825-6CB7-A6508B063C81\Everything2.ini | text | |
MD5:51014C0C06ACDD80F9AE4469E7D30A9E | SHA256:89AD2164717BD5F5F93FBB4CEBF0EFEB473097408FDDFC7FC7B924D790514DC5 | |||
| 2640 | datadecrypt.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Everything64.dll | compressed | |
MD5:6BEAABDCEBD1819DD160B0137B8D68E0 | SHA256:0DA80DFFC602B64B17F47A1B82F38F75A2222234D83FFDA4131F8AD3AE99682E | |||
| 2240 | datadecrypt.exe | C:\Users\admin\AppData\Local\BC57CE41-27D7-C825-6CB7-A6508B063C81\7za.exe | executable | |
MD5:B93EB0A48C91A53BDA6A1A074A4B431E | SHA256:AB15A9B27EE2D69A8BC8C8D1F5F40F28CD568F5CBB28D36ED938110203F8D142 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
267
DNS requests
0
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
— | — | 192.168.100.190:49169 | — | — | — | unknown |
— | — | 192.168.100.190:49170 | — | — | — | unknown |
956 | Datadecrypt.exe | 192.168.1.2:445 | — | — | — | unknown |
— | — | 192.168.100.190:49172 | — | — | — | unknown |
— | — | 192.168.100.190:49173 | — | — | — | unknown |
— | — | 192.168.100.190:49174 | — | — | — | unknown |
— | — | 192.168.100.190:49175 | — | — | — | unknown |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
956 | Datadecrypt.exe | Misc activity | ET SCAN Behavioral Unusual Port 445 traffic Potential Scan or Infection |