| File name: | DeathPlus.exe |
| Full analysis: | https://app.any.run/tasks/3c0f942a-8753-4a61-bb09-15e71297b20c |
| Verdict: | Malicious activity |
| Analysis date: | October 26, 2024, 12:06:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sections |
| MD5: | F0ECDCCB410A0F4E01CD6D41A52D56B2 |
| SHA1: | 23D1452A0FA794D6EE03B786DD4CF9EC189904CE |
| SHA256: | F23233BFFB08FCBBDA8237FECE95003BEA1453466150BE0EB0B2F0860A34B72E |
| SSDEEP: | 98304:TgTYVfYa4uckN1T6ZbyeC/xij1A+LEew5/19SOGqSWqlz1Ymh5uC7o+vIeKJVJ:aNickN1T6Fyx/g/E75/19SOGLWqlBNhE |
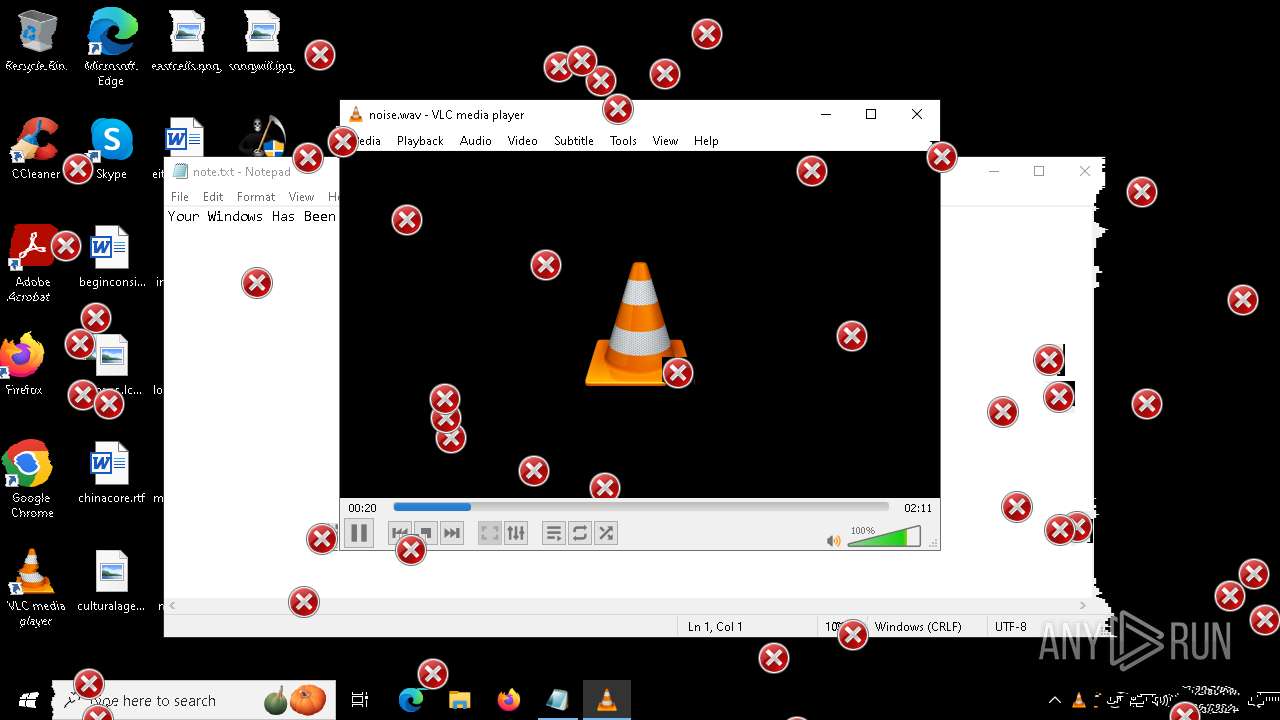
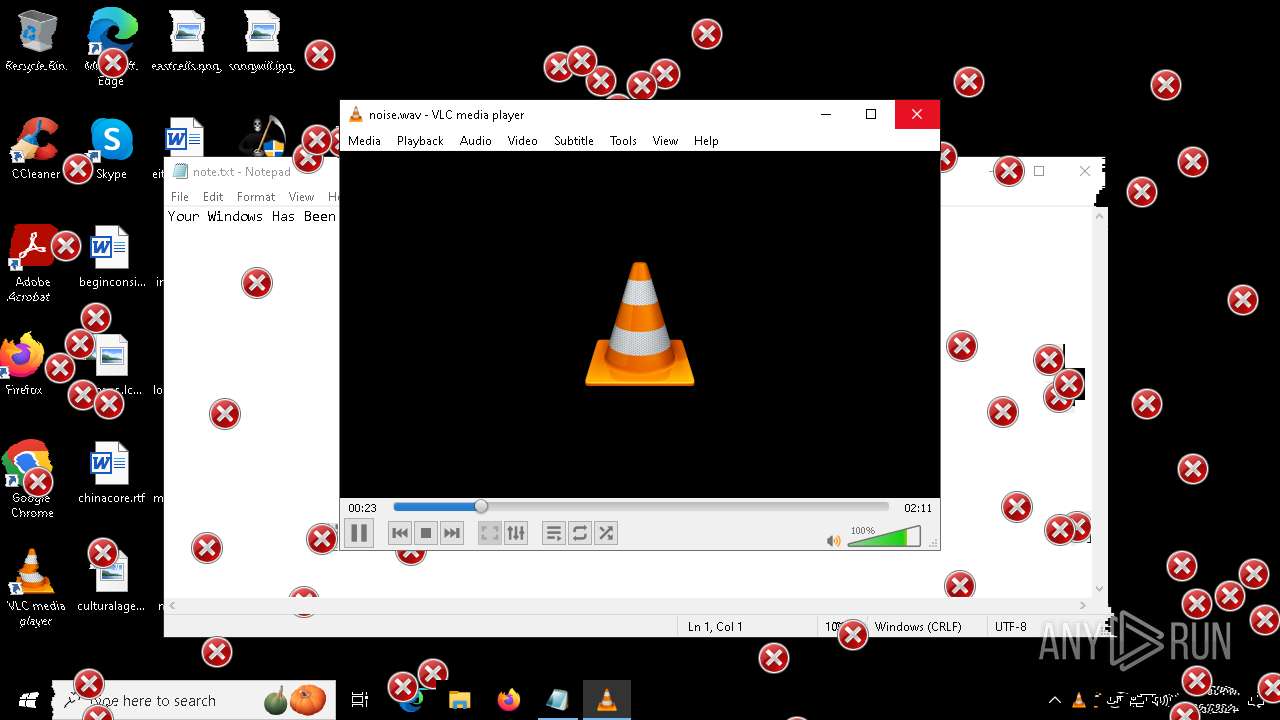
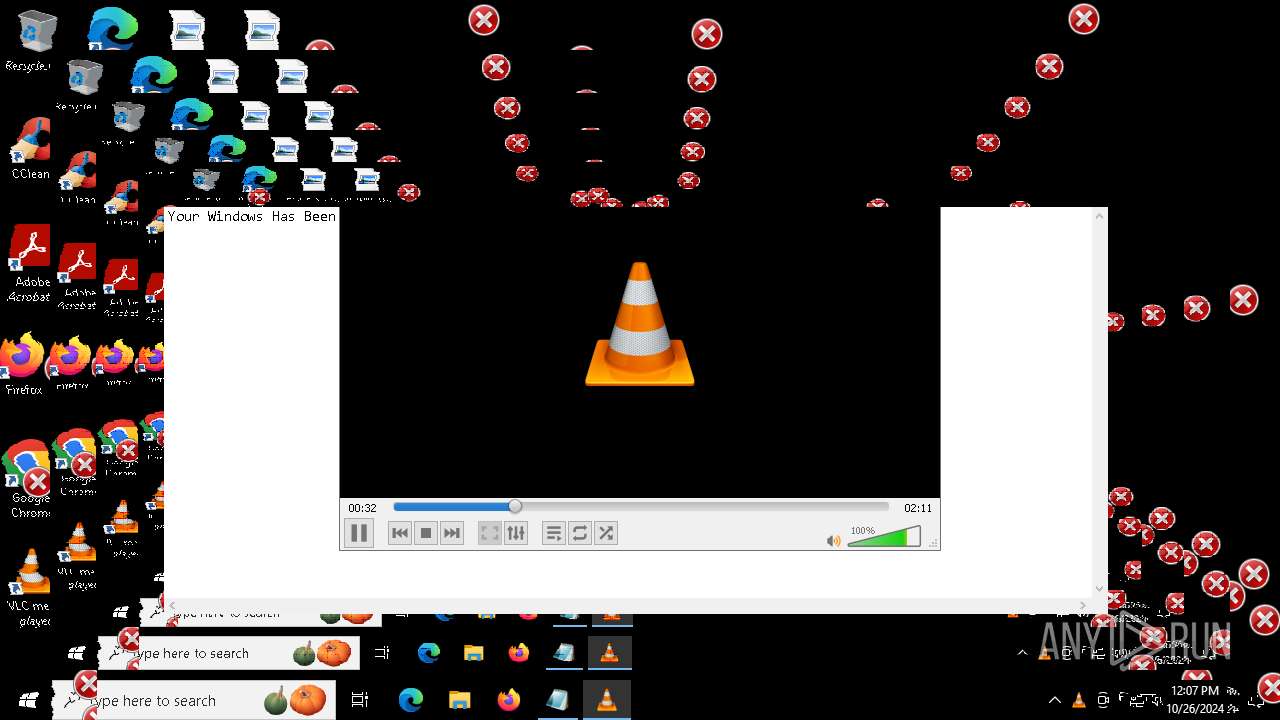
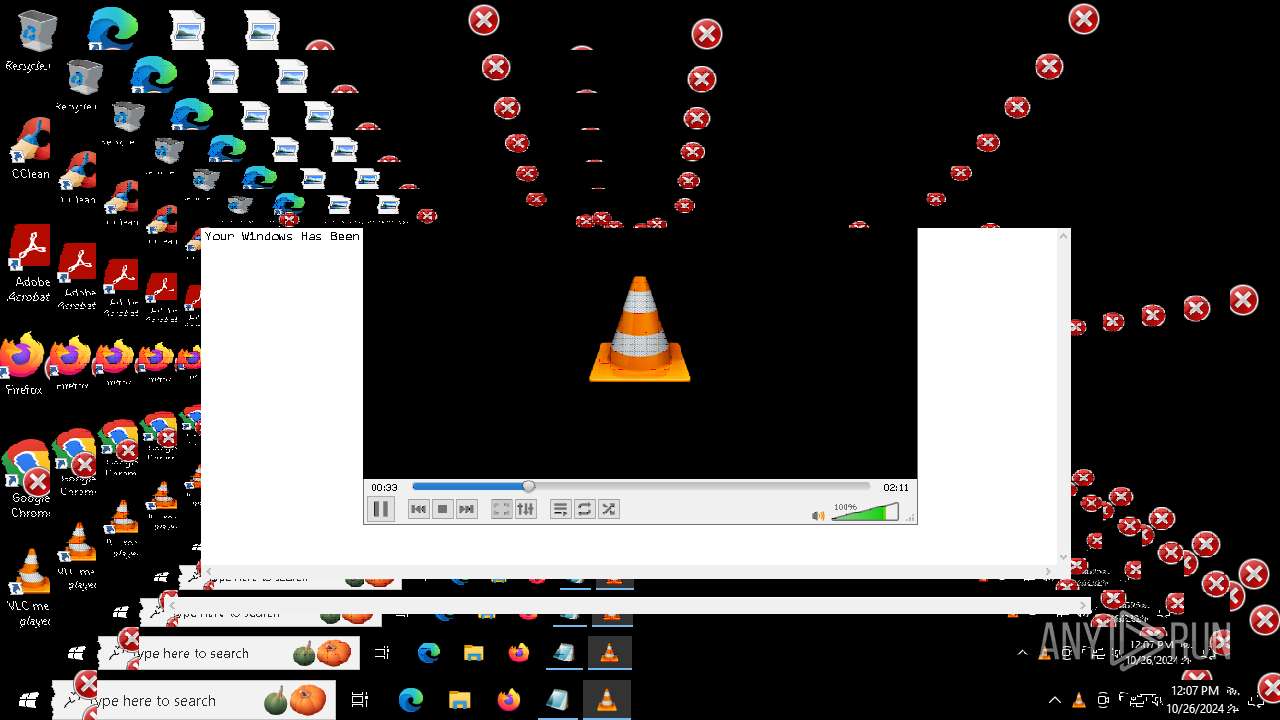
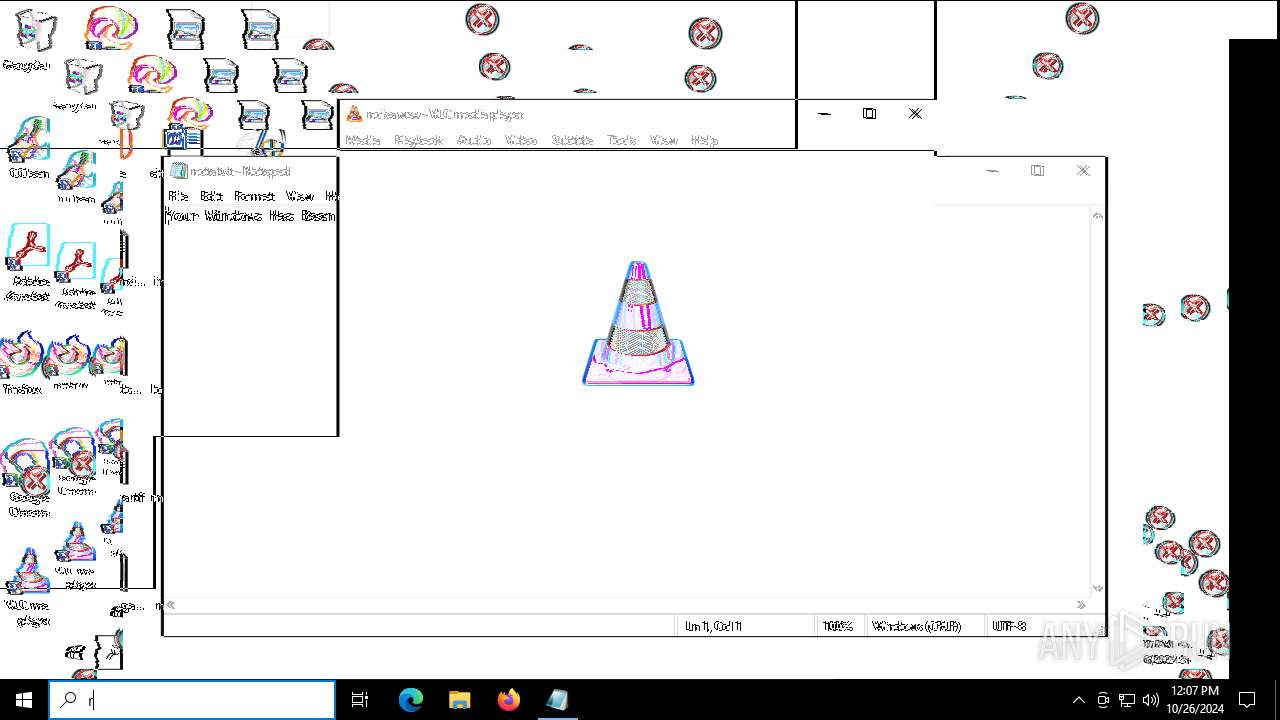
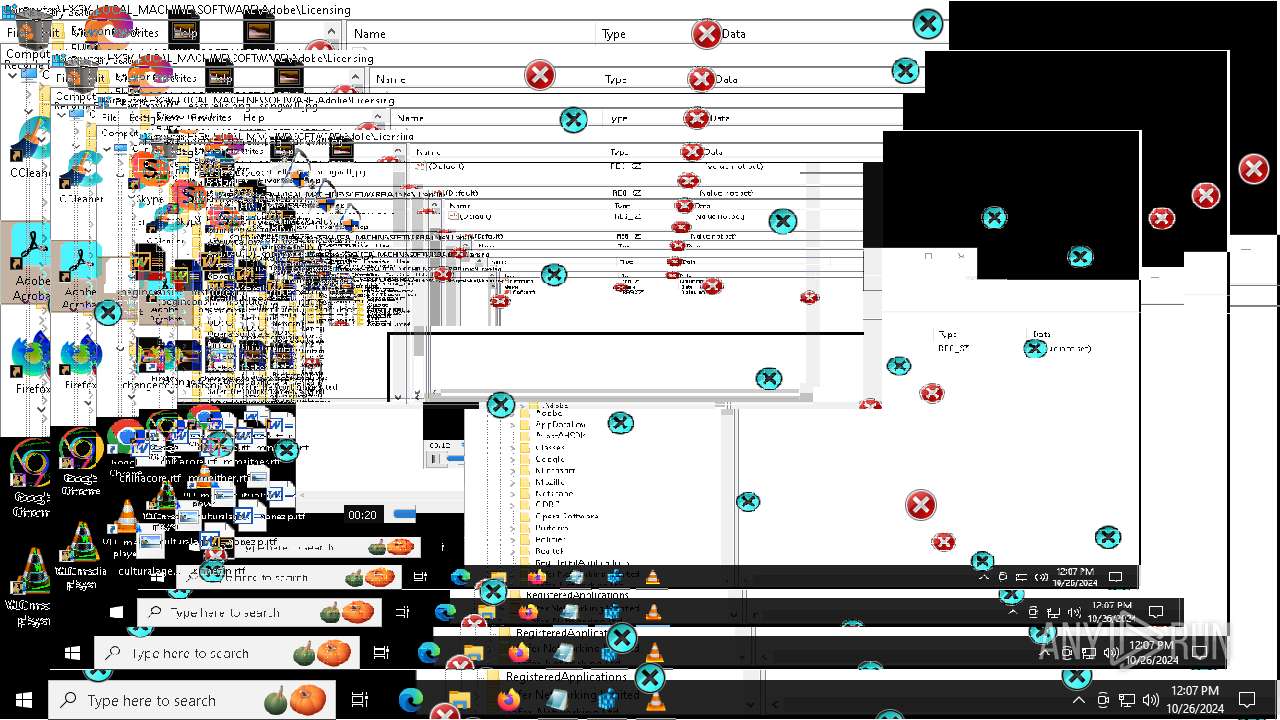
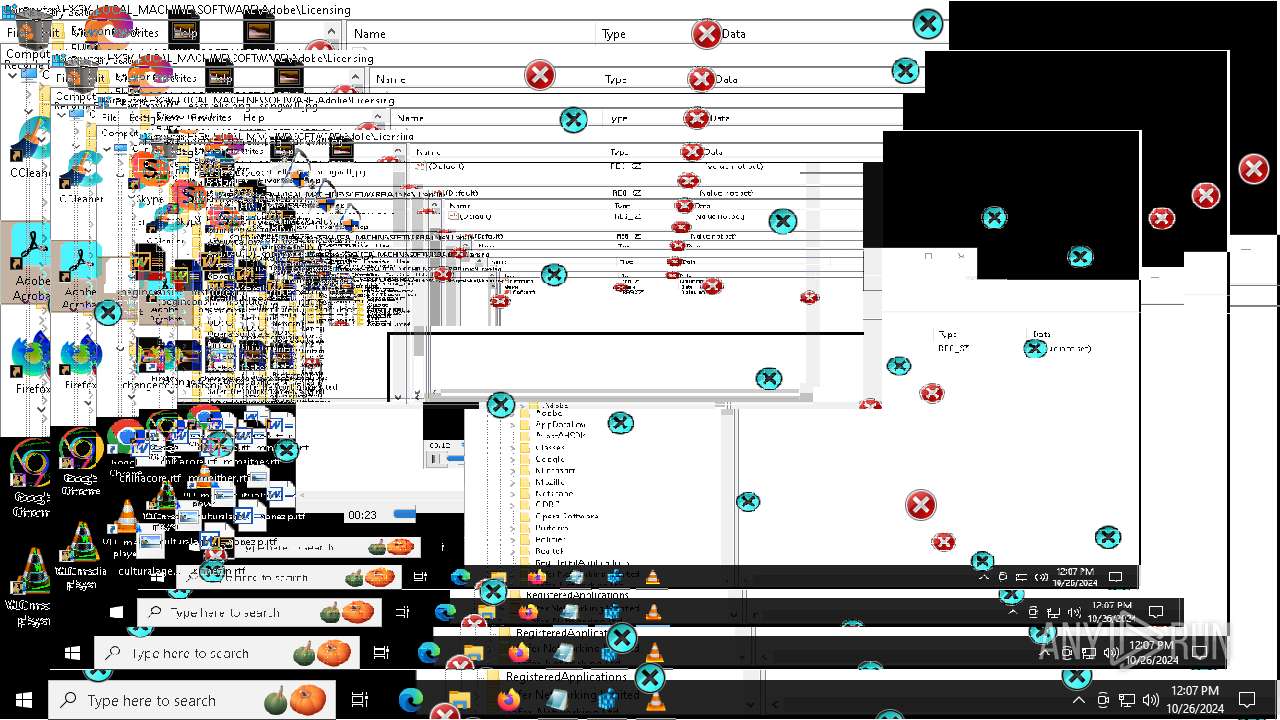
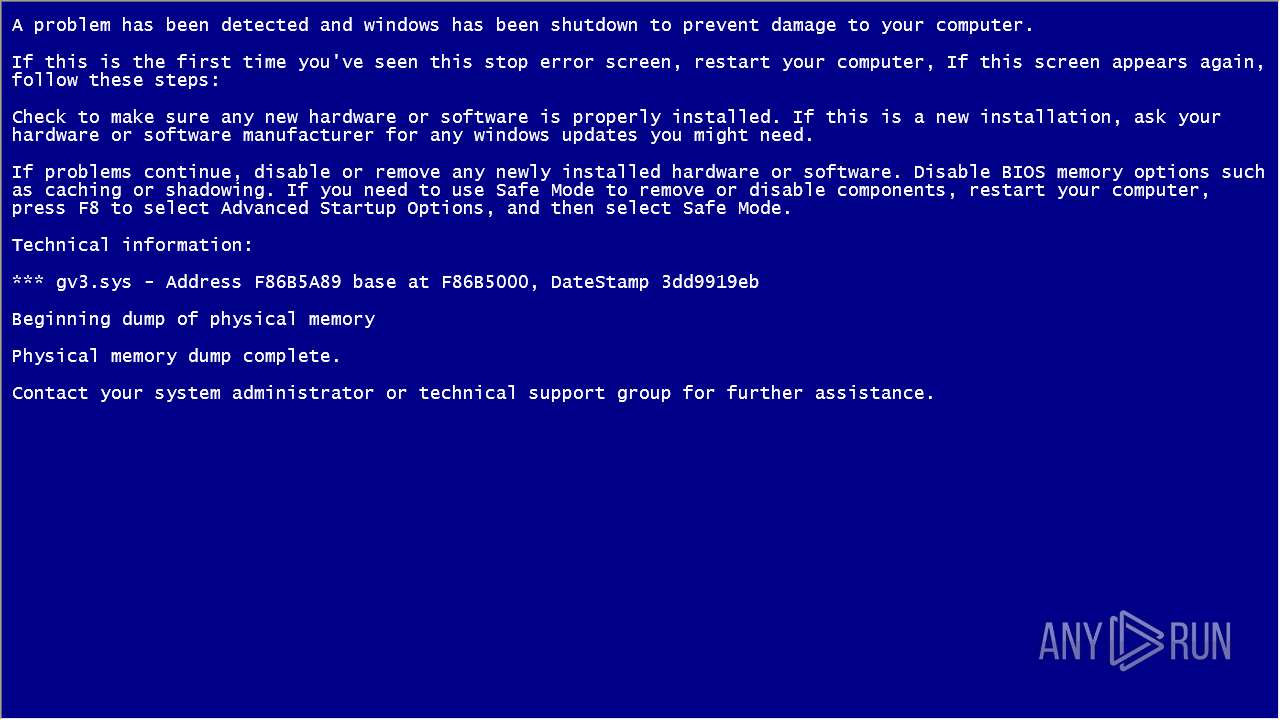
MALICIOUS
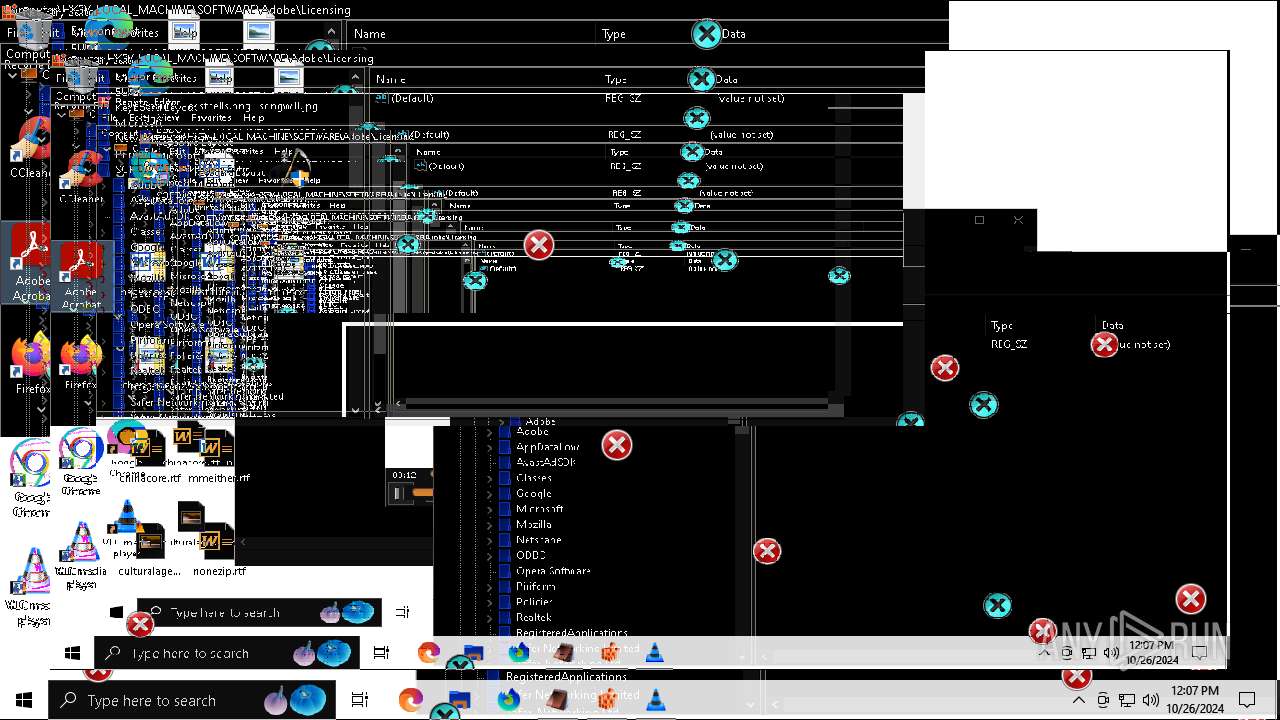
Changes the autorun value in the registry
- MBRKiller.exe (PID: 1184)
Uses Task Scheduler to run other applications
- MBRKiller.exe (PID: 1184)
SUSPICIOUS
Executable content was dropped or overwritten
- DeathPlus.exe (PID: 6668)
Reads security settings of Internet Explorer
- DeathPlus.exe (PID: 6668)
- ShellExperienceHost.exe (PID: 1880)
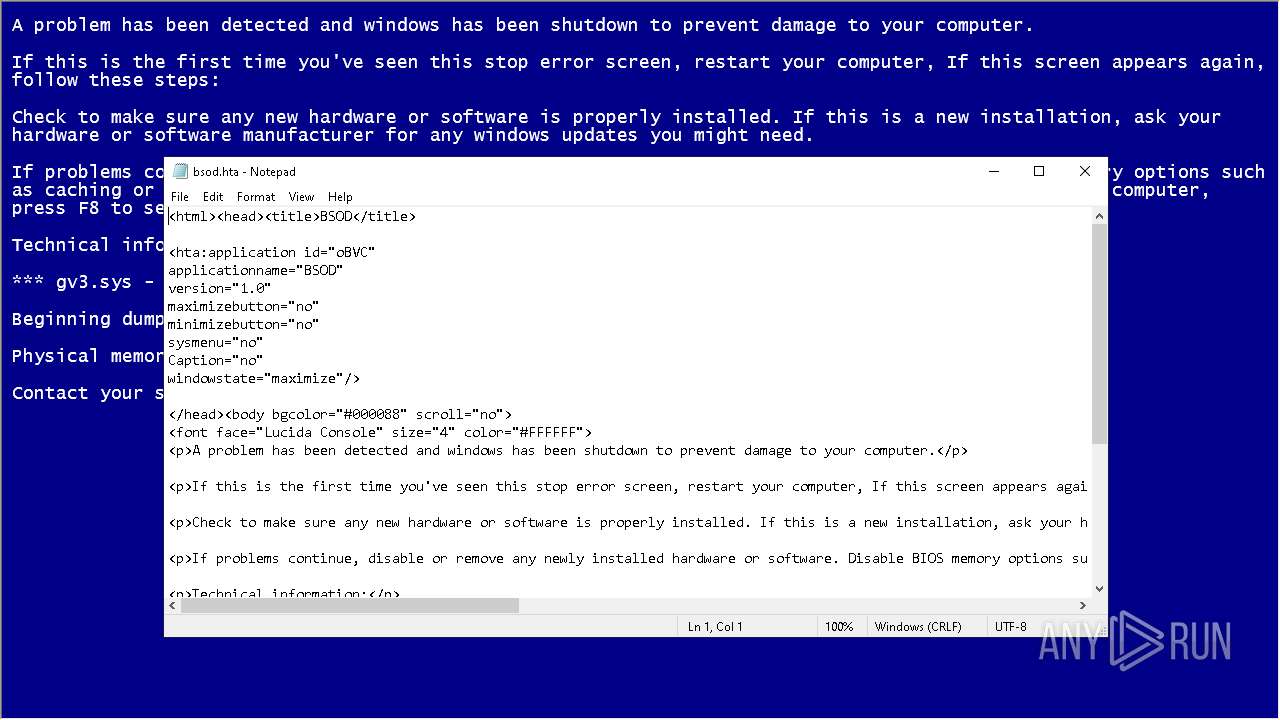
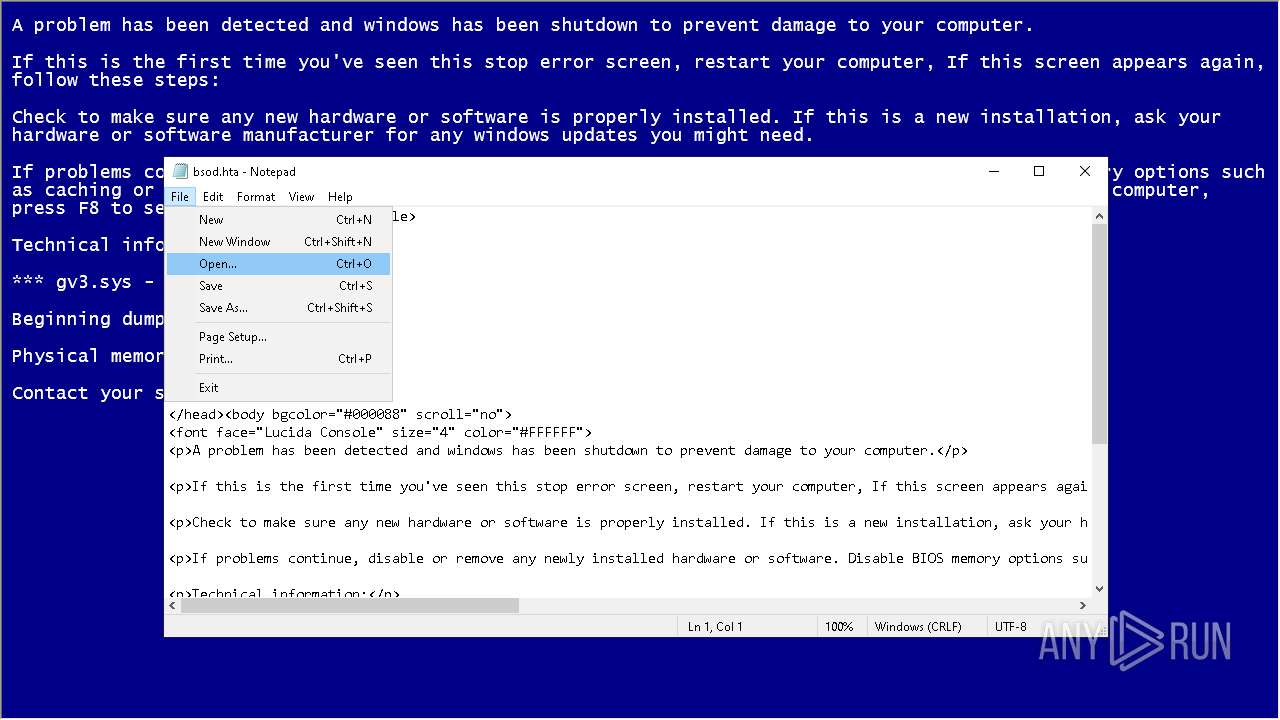
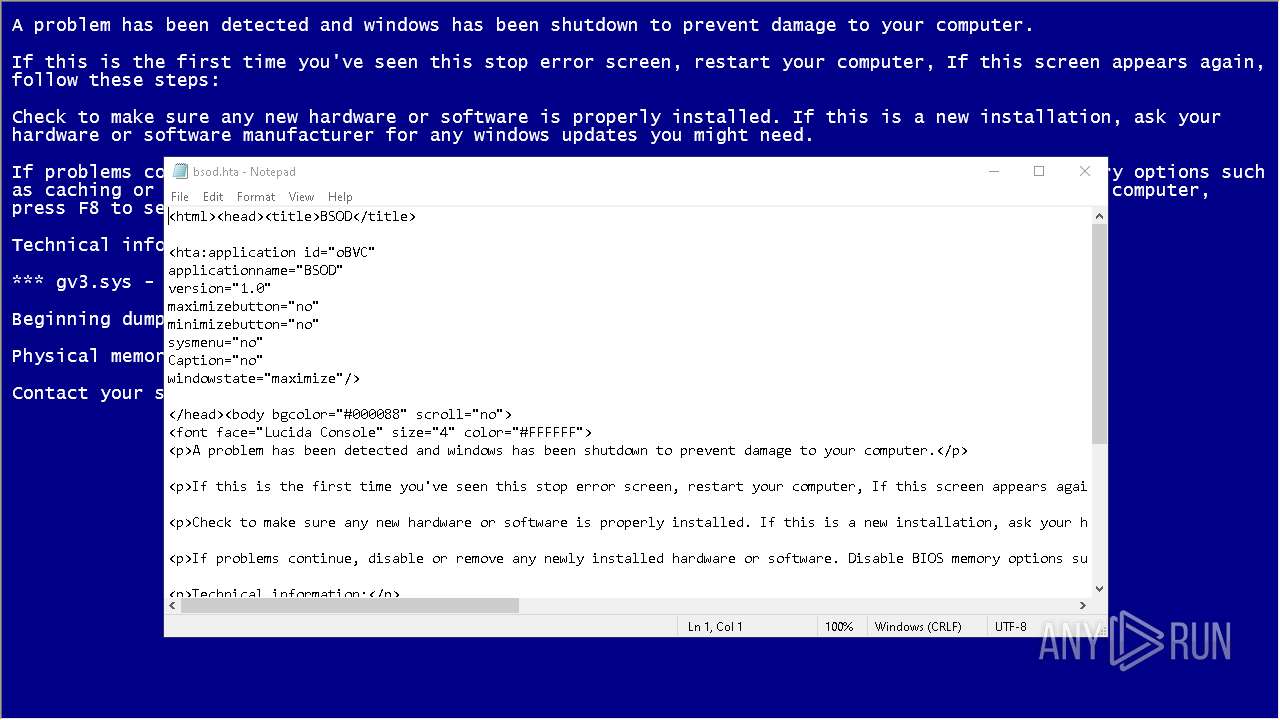
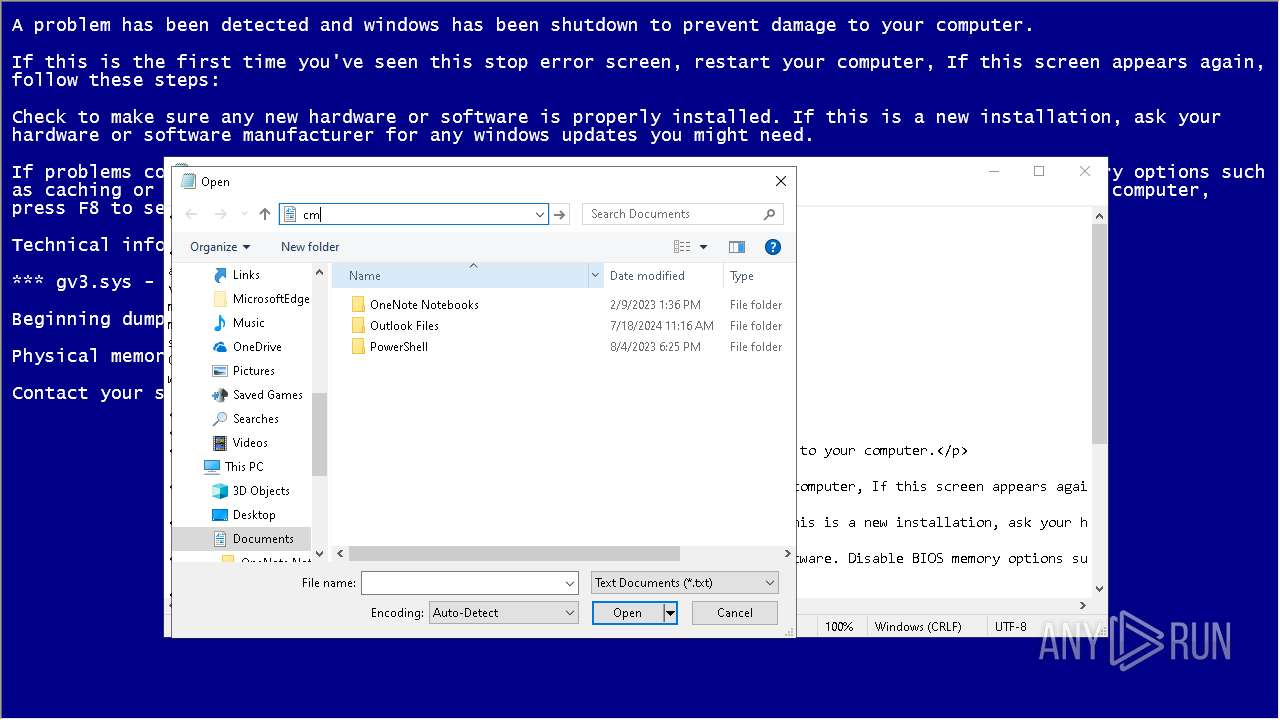
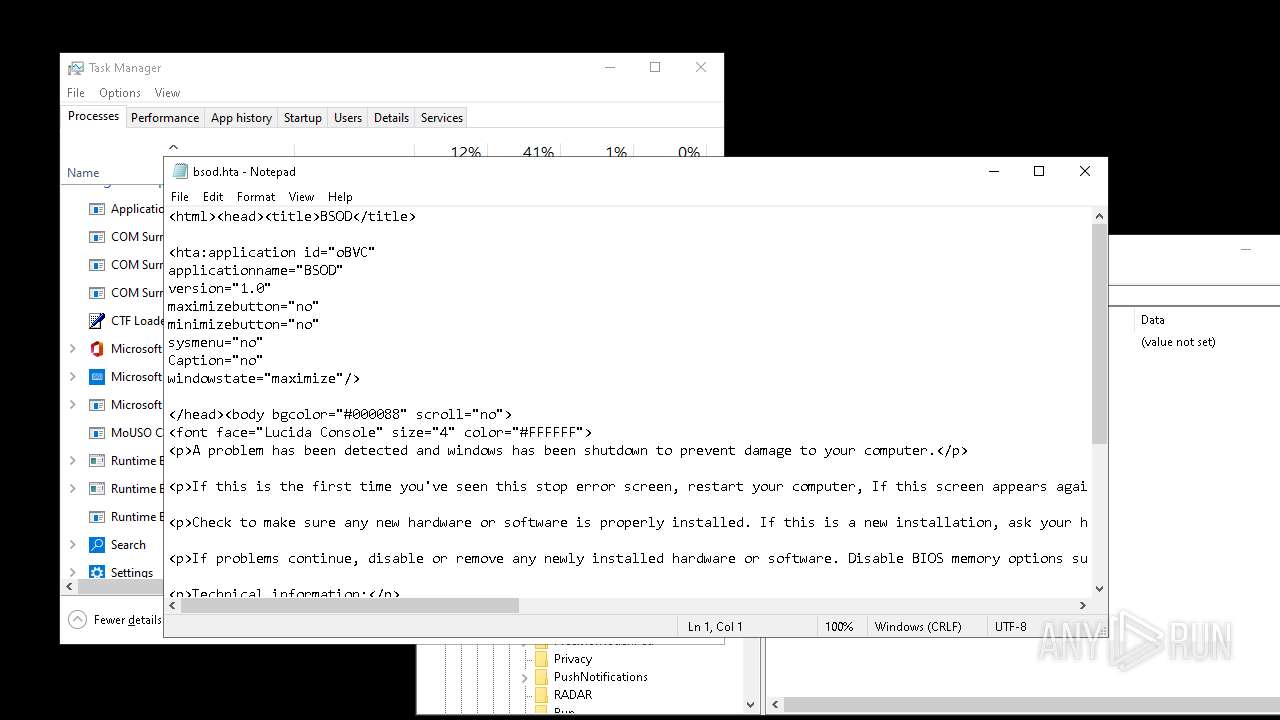
Executing commands from a ".bat" file
- DeathPlus.exe (PID: 6668)
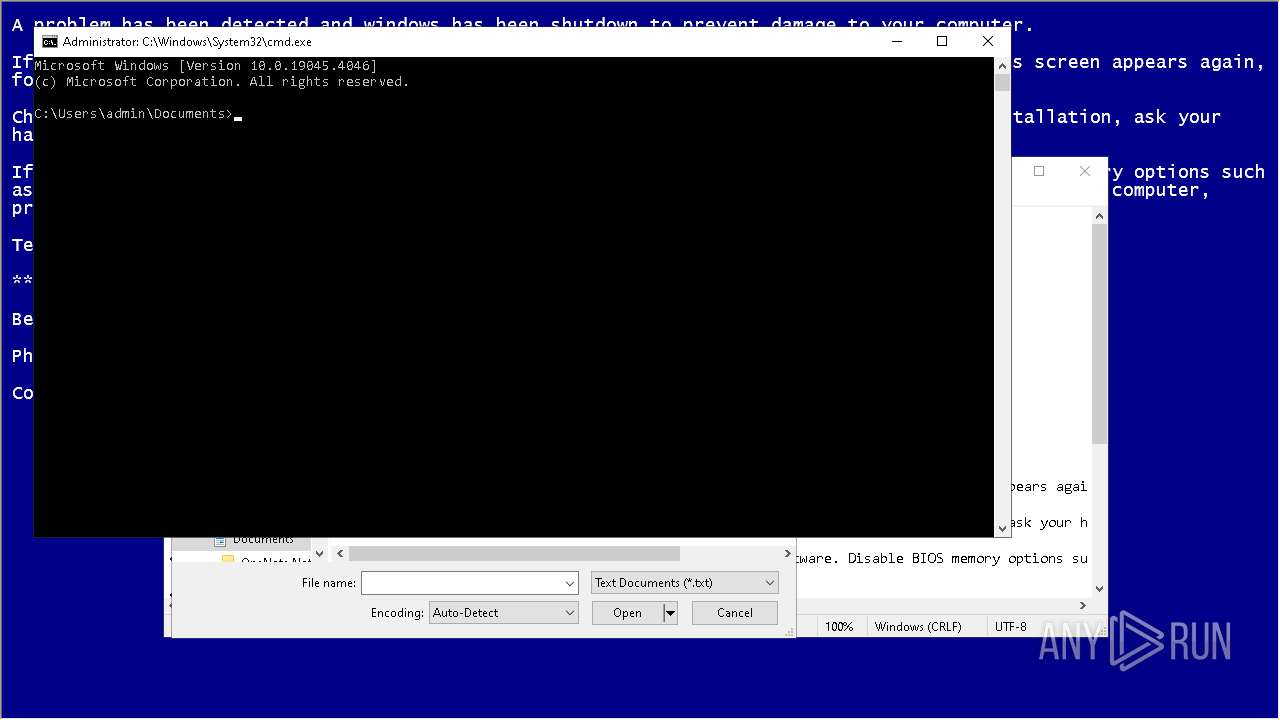
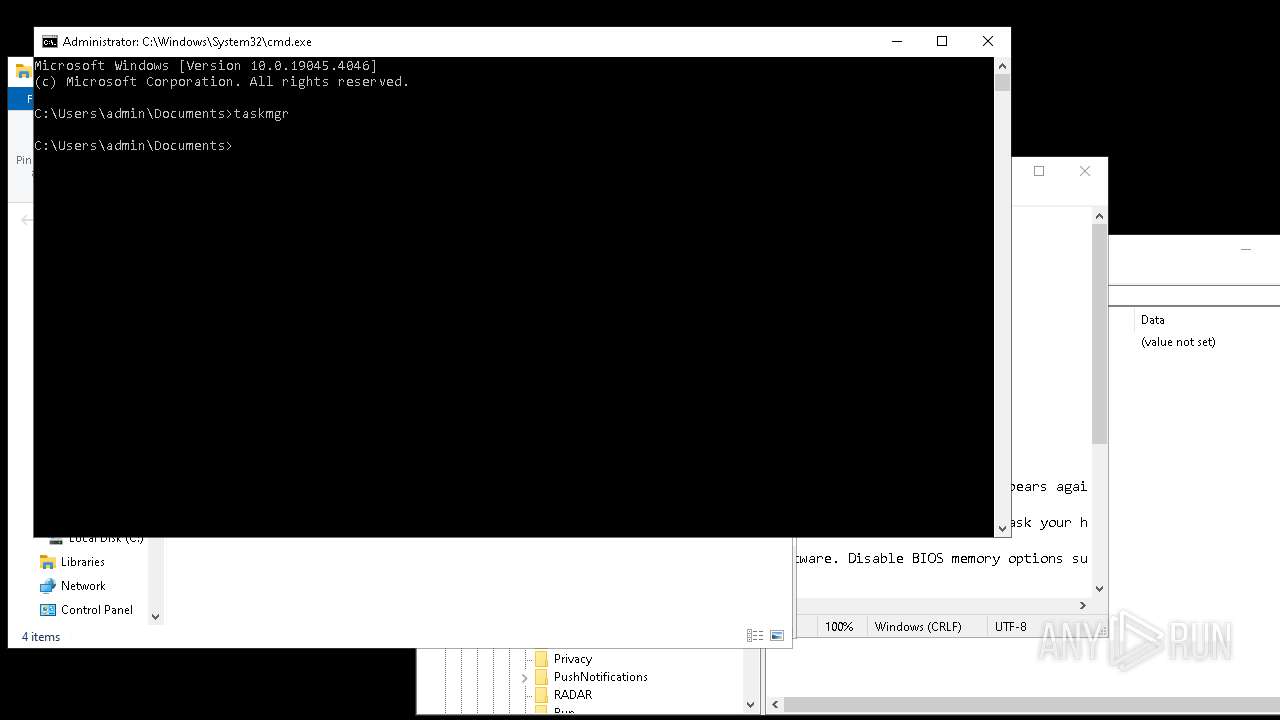
Starts CMD.EXE for commands execution
- DeathPlus.exe (PID: 6668)
- notepad.exe (PID: 6204)
The executable file from the user directory is run by the CMD process
- MBRKiller.exe (PID: 1184)
- CLWCP.exe (PID: 3792)
- waves.exe (PID: 7208)
- icons.exe (PID: 7528)
- tunnel.exe (PID: 8168)
- BitBlt.exe (PID: 6200)
- icons.exe (PID: 3860)
- scream.exe (PID: 3972)
- scream.exe (PID: 8132)
- CLWCP.exe (PID: 7540)
- scream.exe (PID: 8152)
- scream.exe (PID: 1792)
- scream.exe (PID: 8128)
- scream.exe (PID: 7108)
- scream.exe (PID: 7004)
- tunnel.exe (PID: 7852)
- scream.exe (PID: 3852)
- scream.exe (PID: 4080)
- scream.exe (PID: 2784)
- scream.exe (PID: 6752)
- scream.exe (PID: 6808)
- scream.exe (PID: 4584)
- scream.exe (PID: 3844)
- scream.exe (PID: 7000)
- scream.exe (PID: 2888)
- scream.exe (PID: 6772)
- scream.exe (PID: 916)
- scream.exe (PID: 1184)
- scream.exe (PID: 3008)
- CLWCP.exe (PID: 6000)
- BitBlt.exe (PID: 6628)
- icons.exe (PID: 6756)
- tunnel.exe (PID: 7320)
- inv.exe (PID: 204)
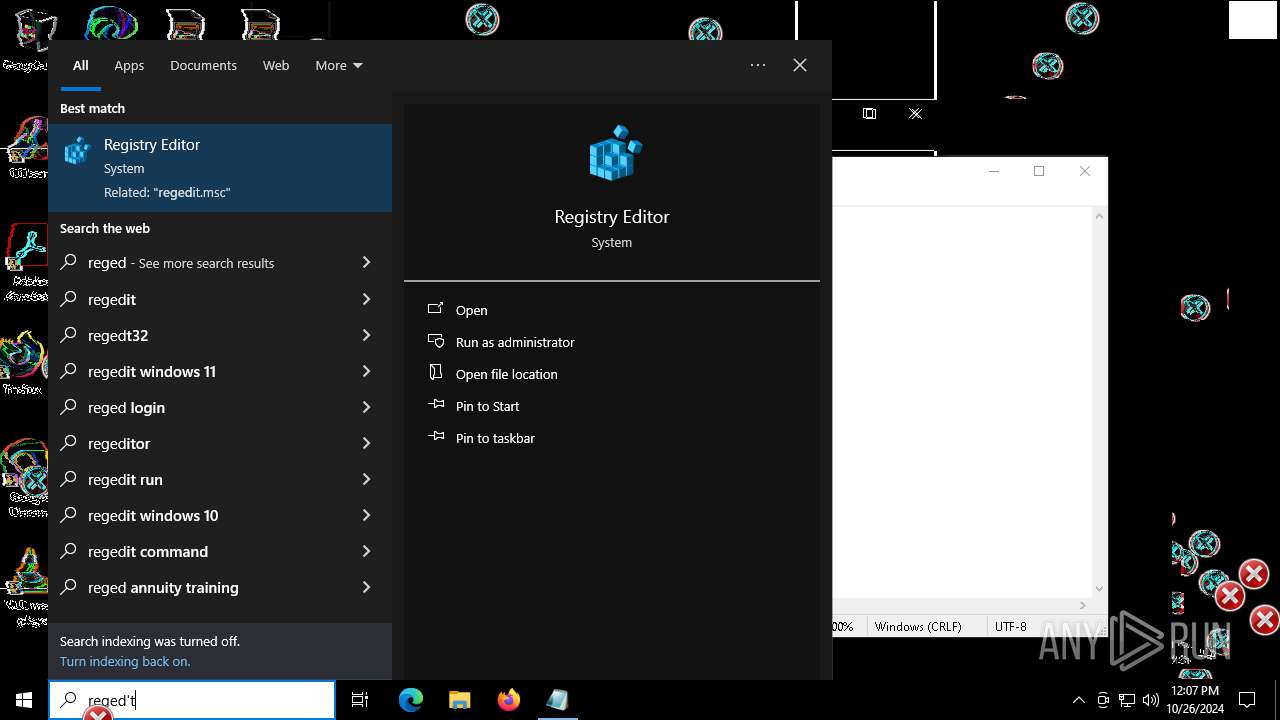
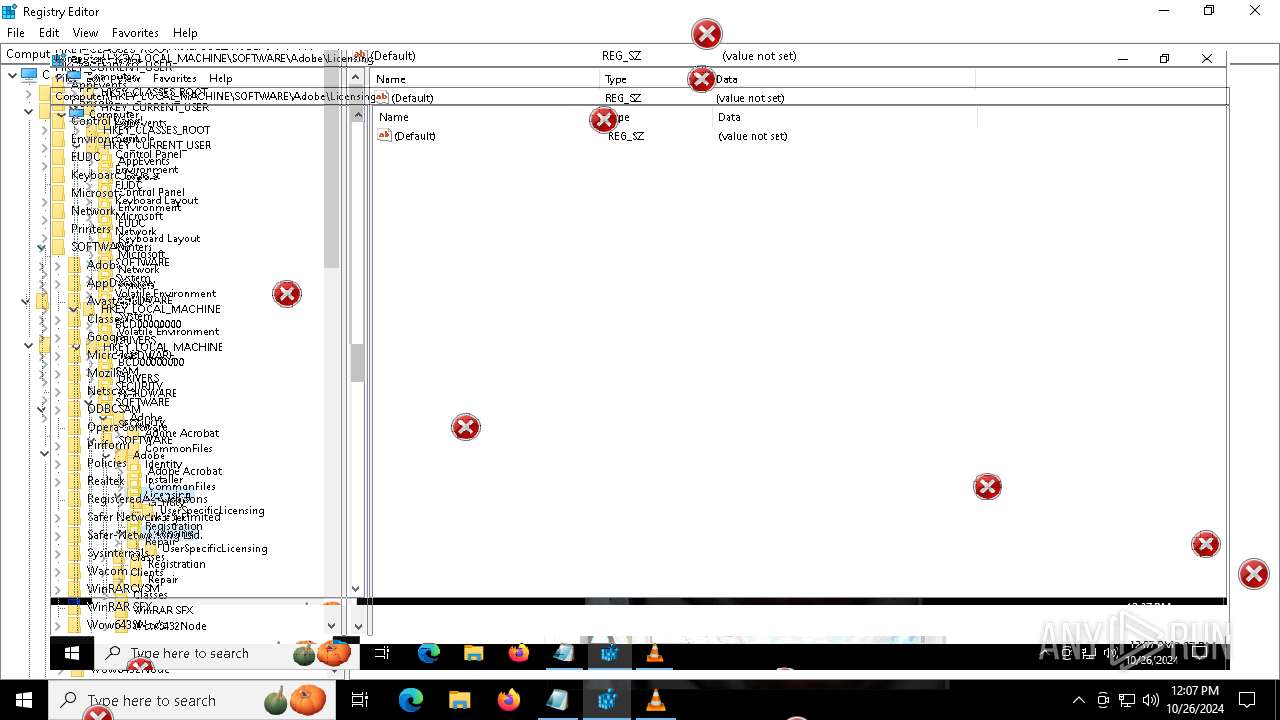
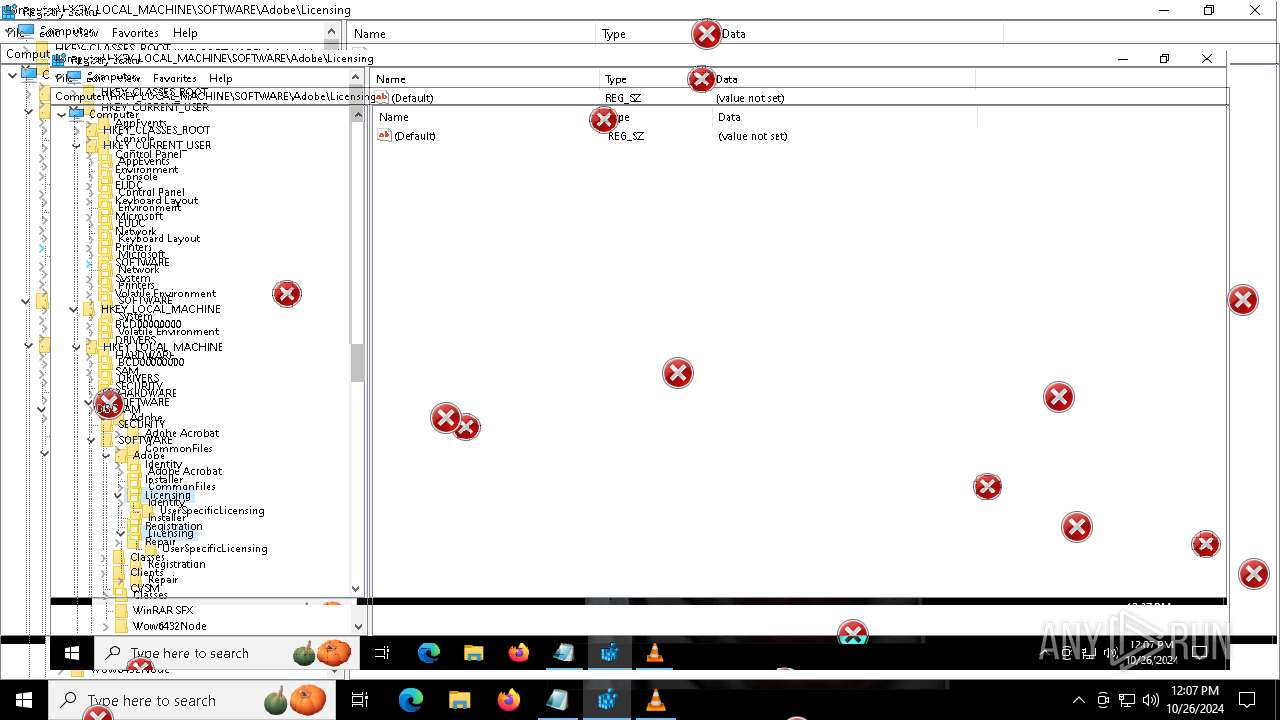
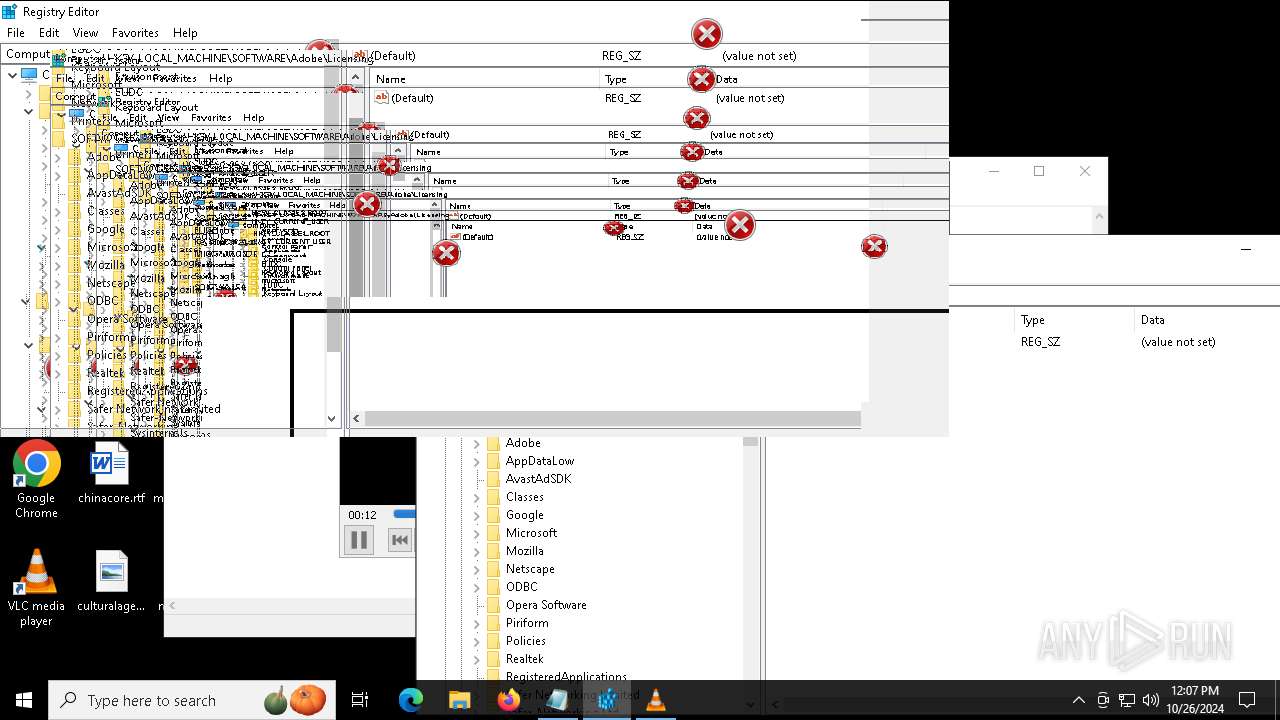
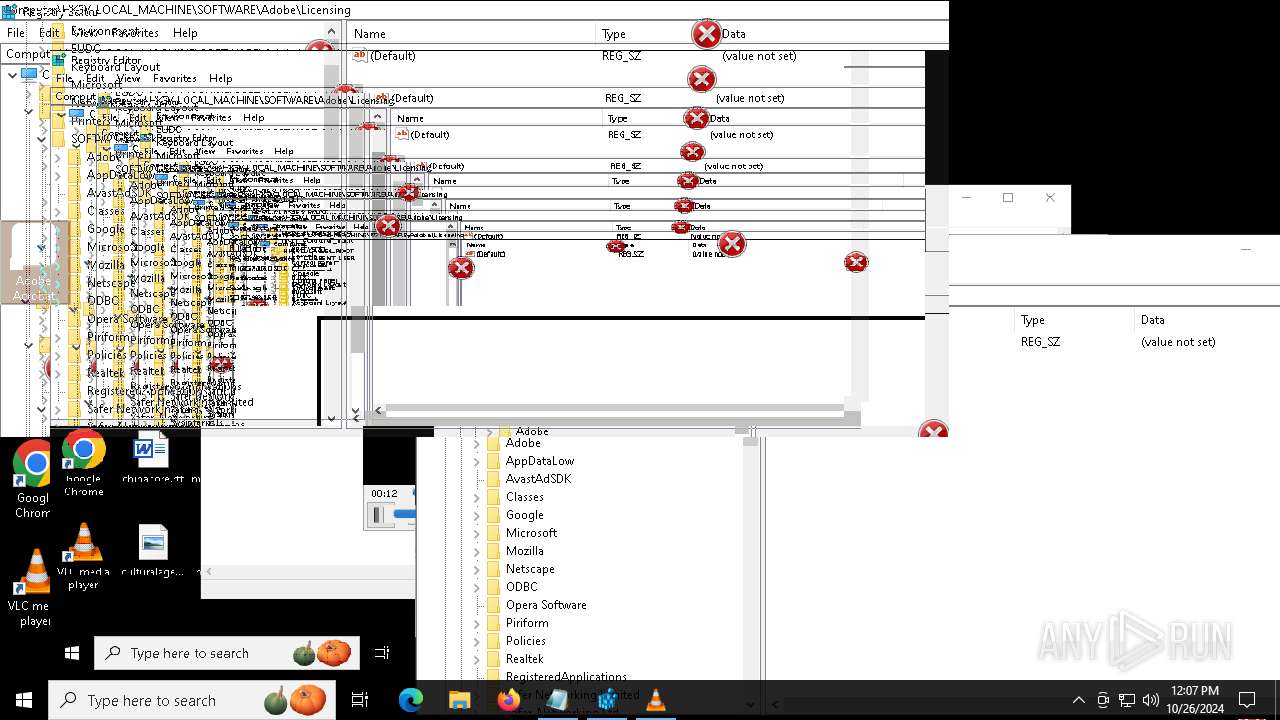
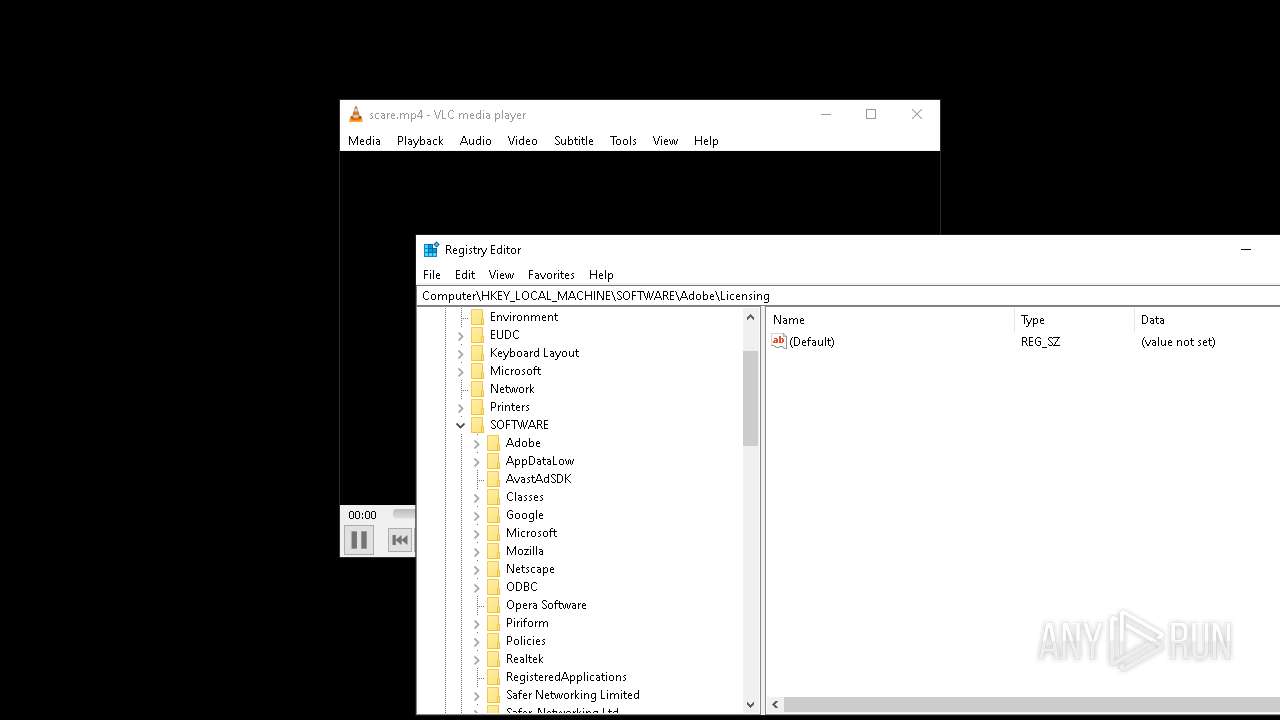
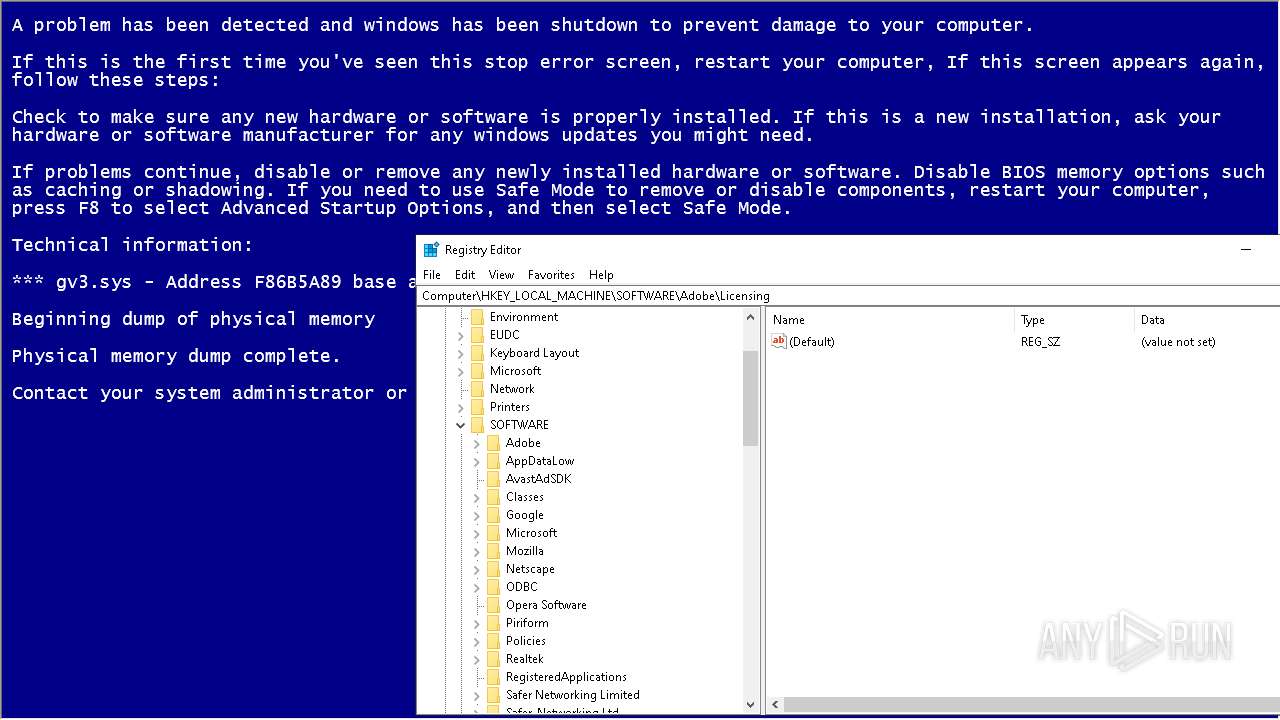
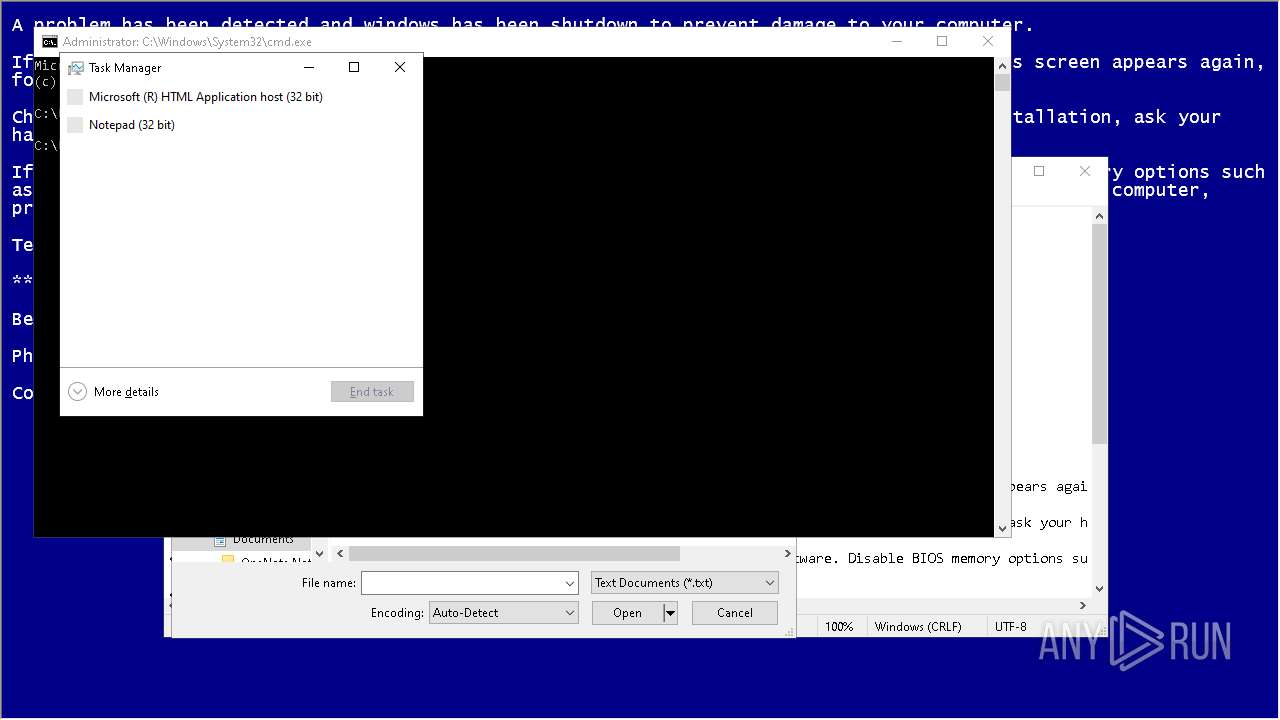
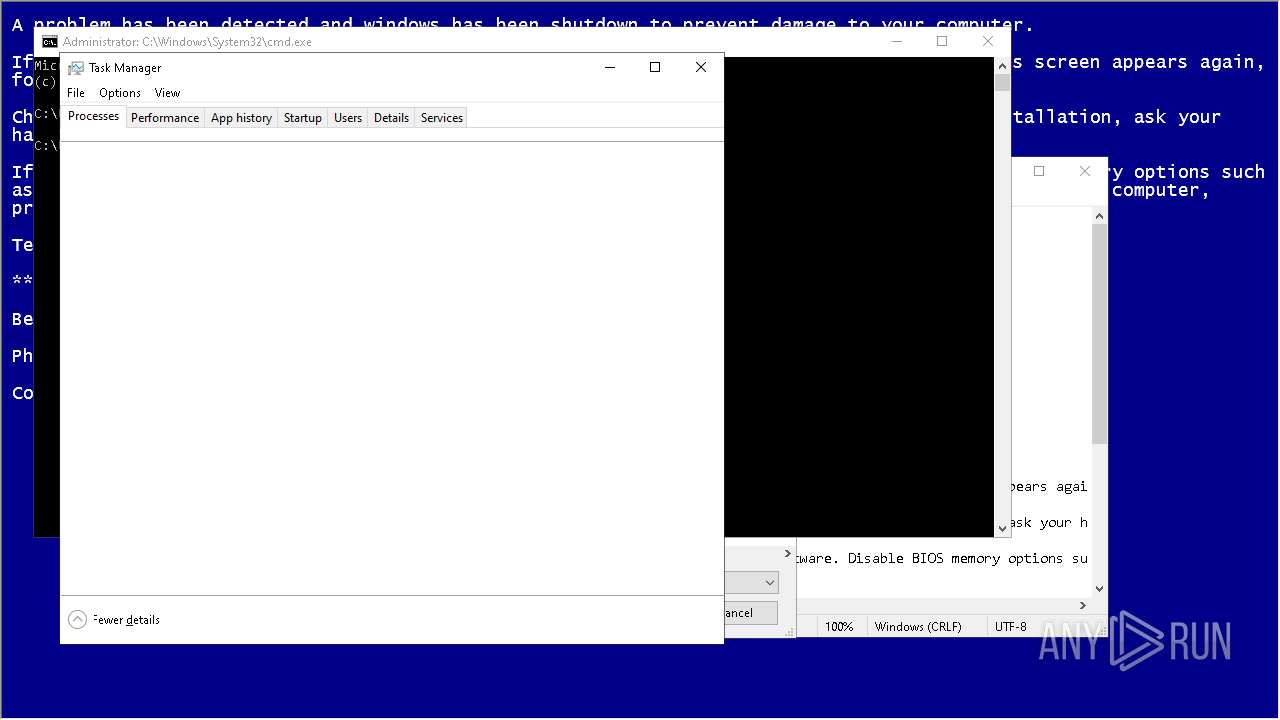
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2648)
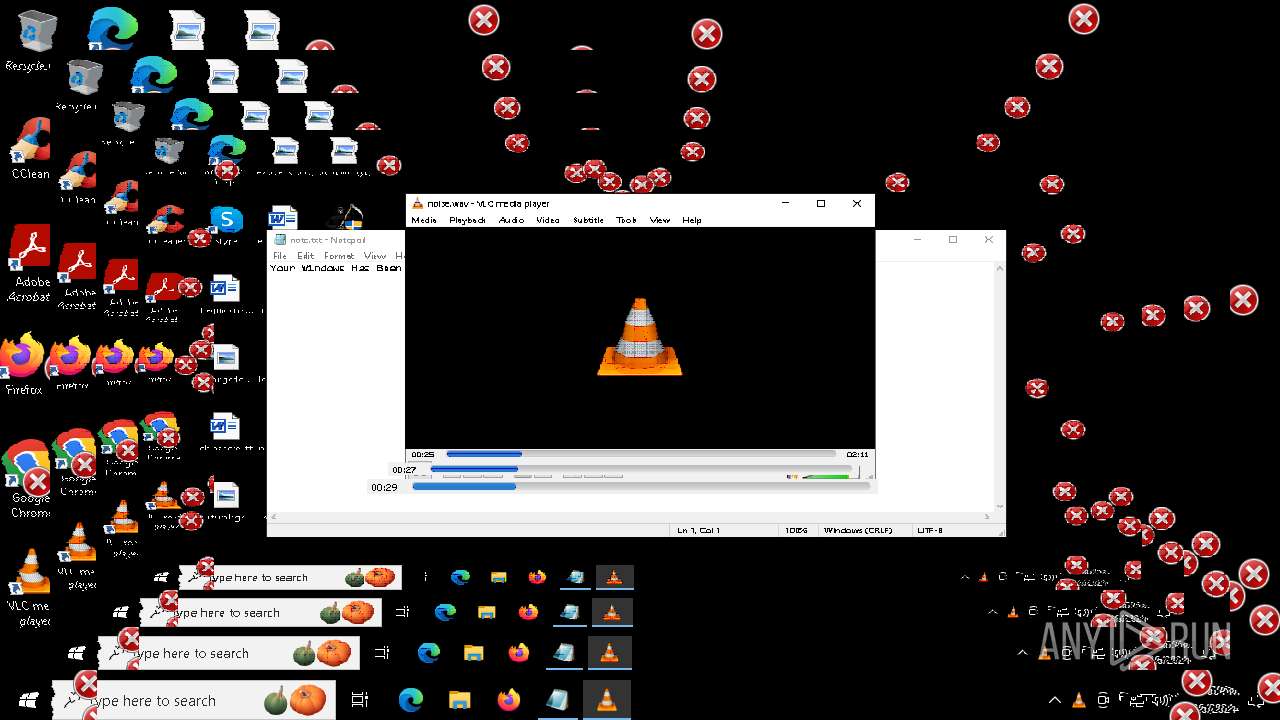
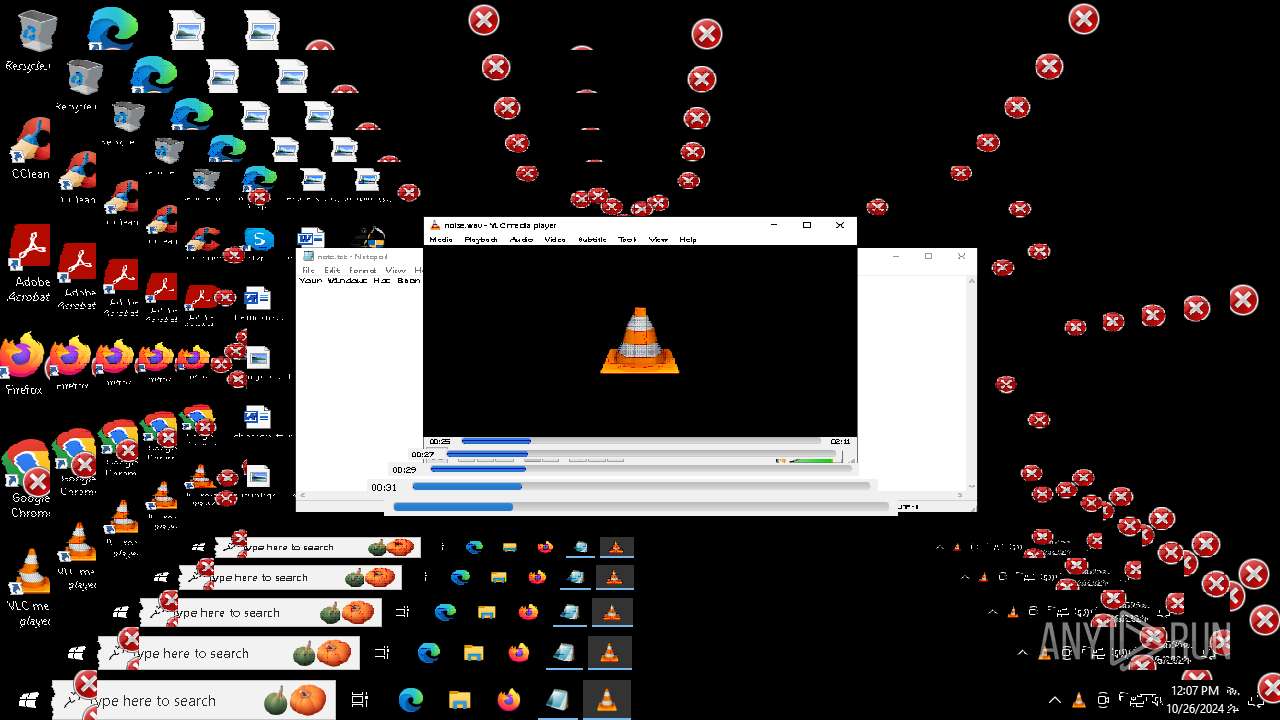
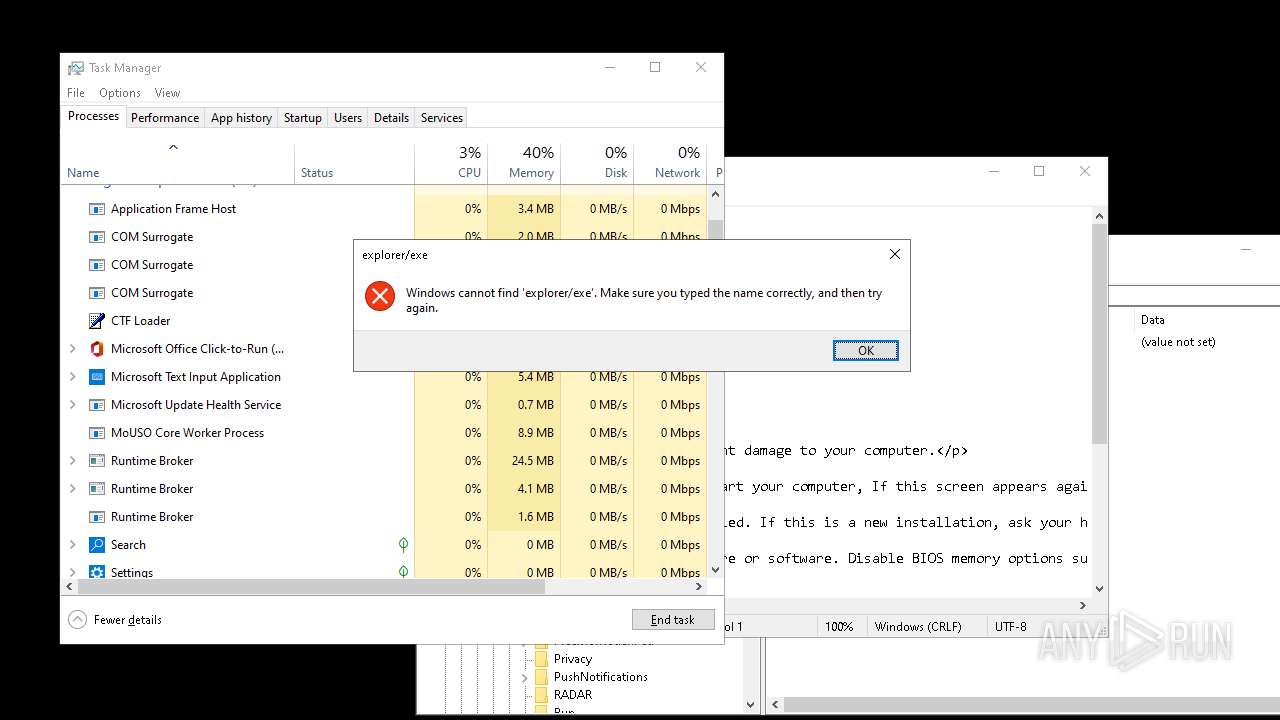
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2648)
Probably fake Windows Update
- schtasks.exe (PID: 3580)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2648)
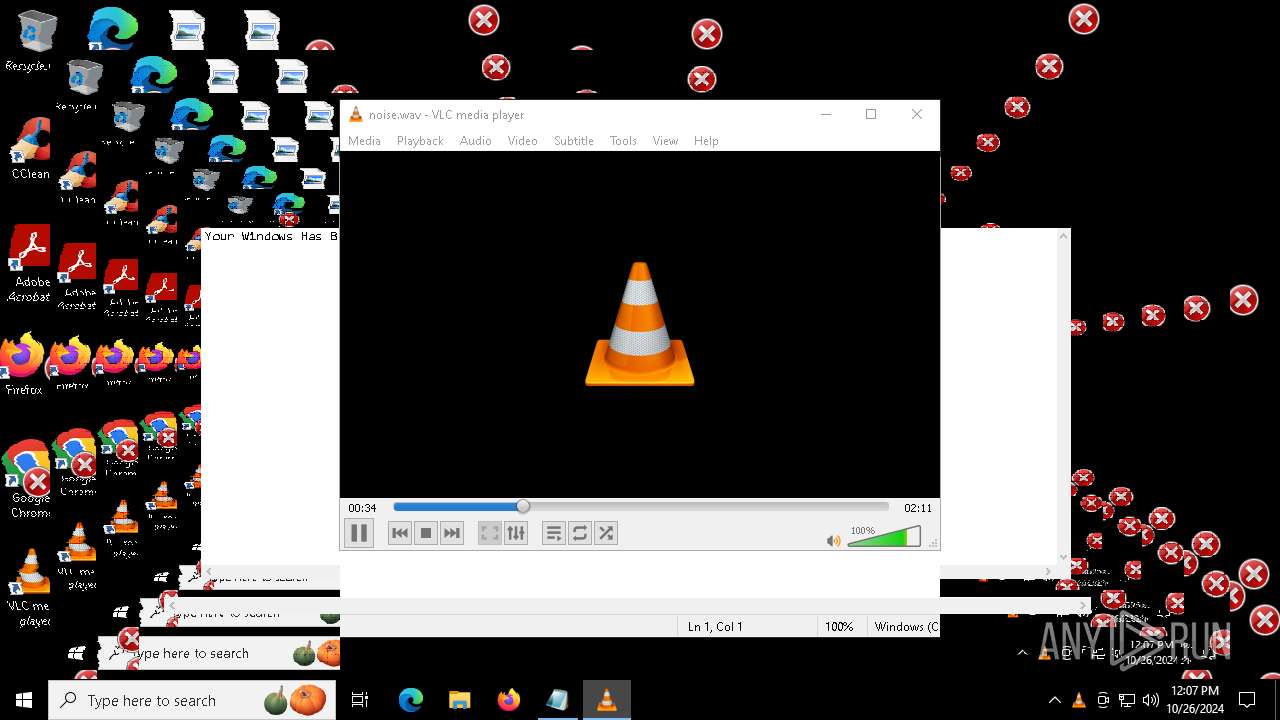
There is functionality for taking screenshot (YARA)
- vlc.exe (PID: 2928)
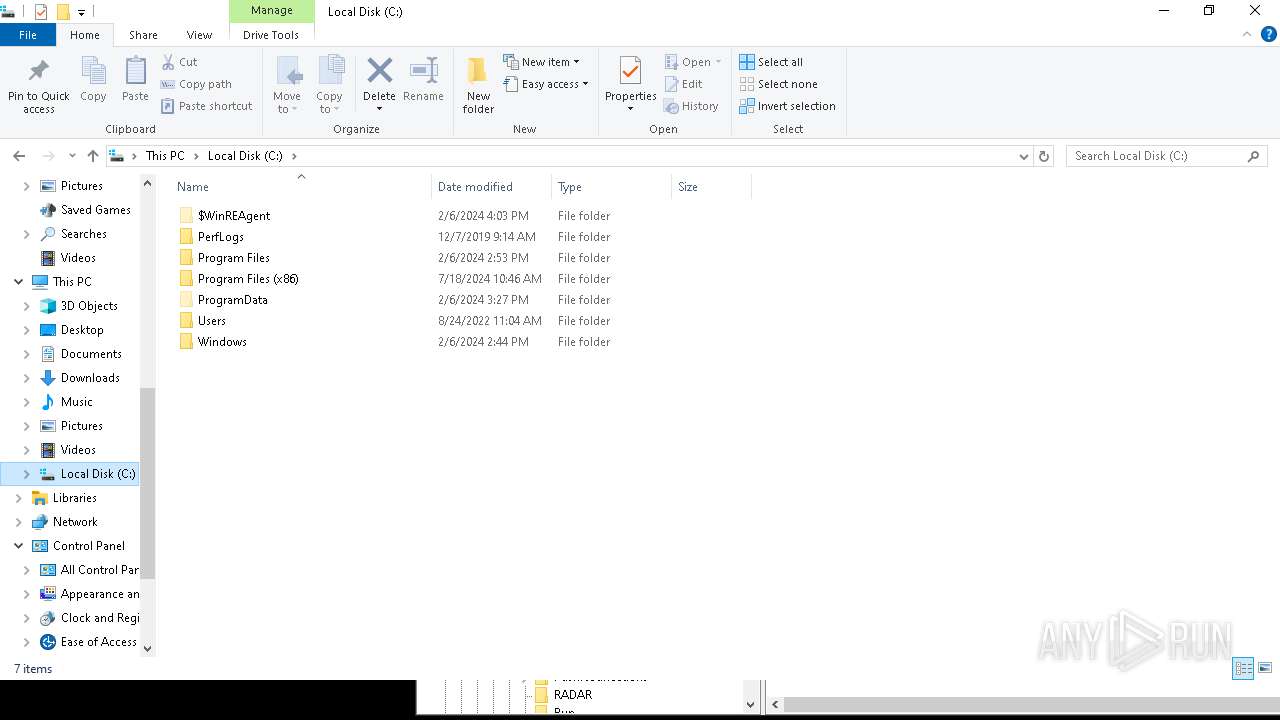
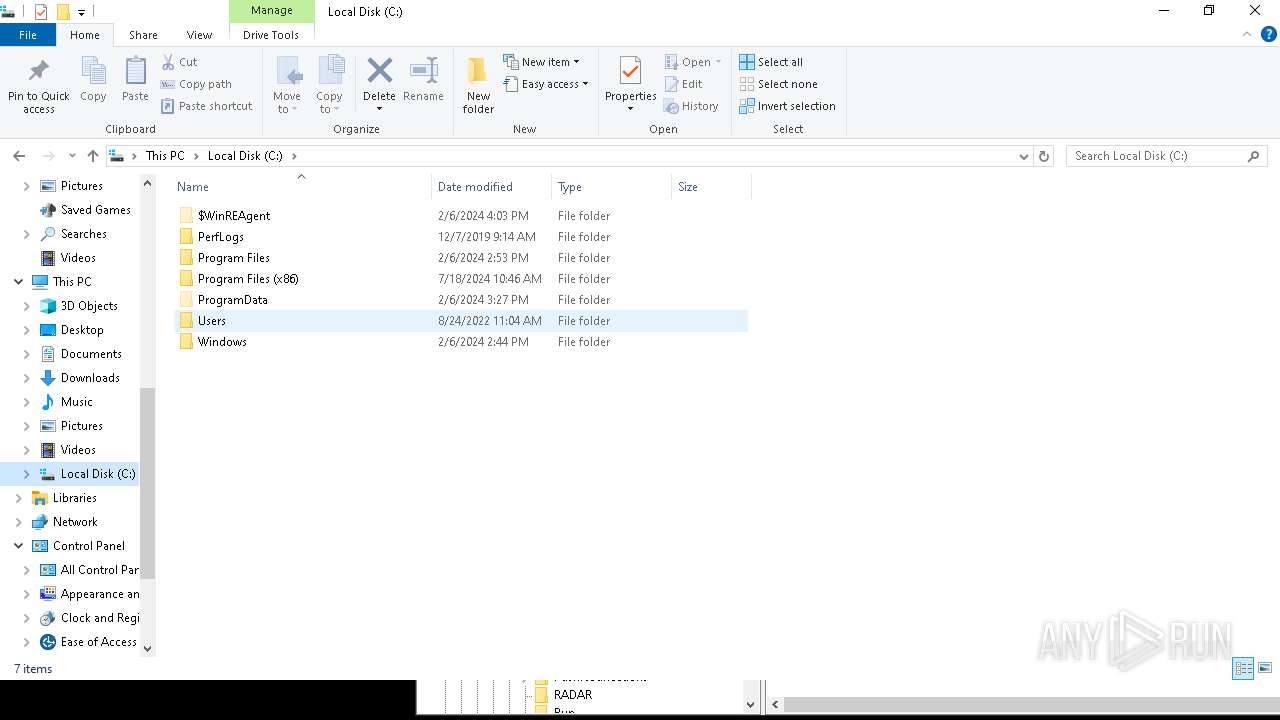
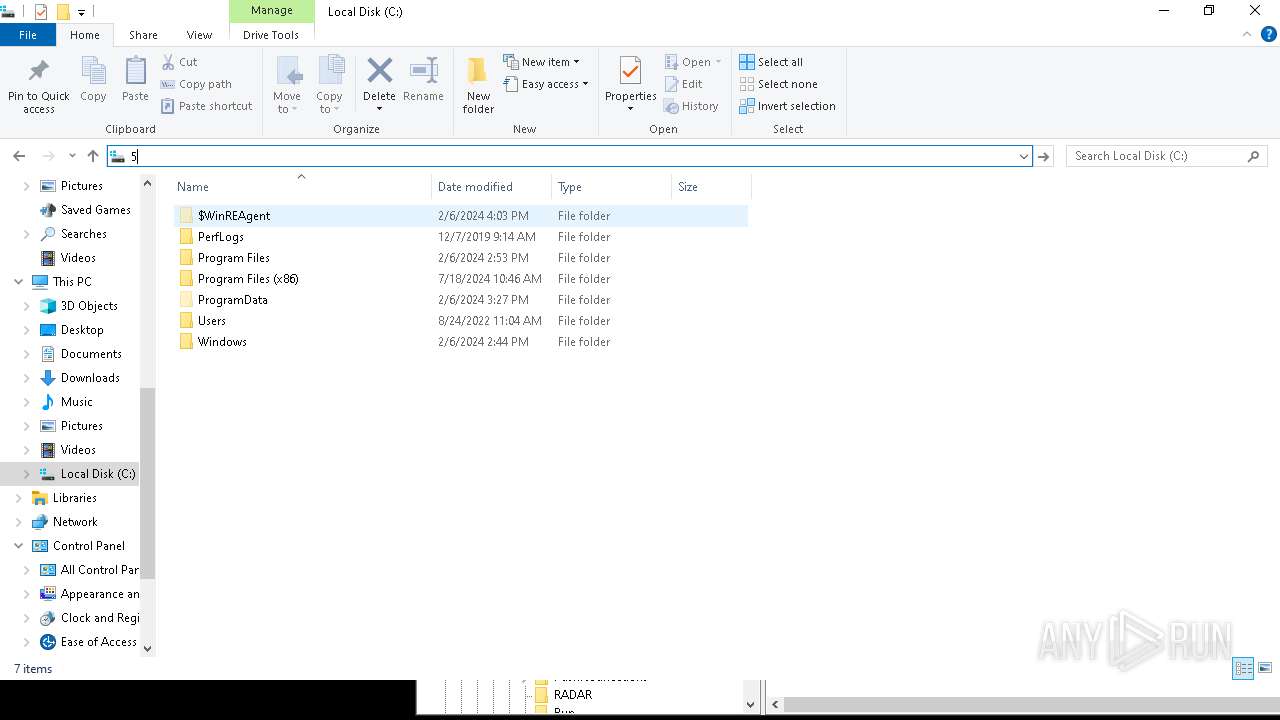
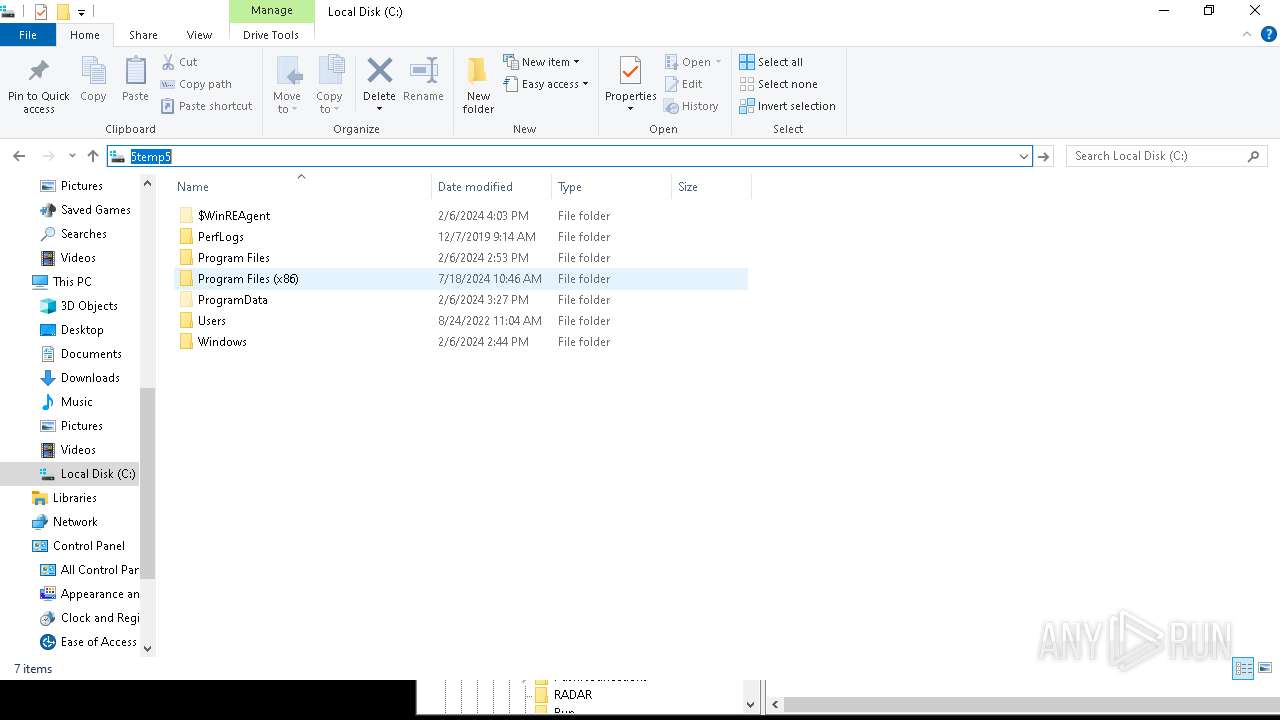
Creates file in the systems drive root
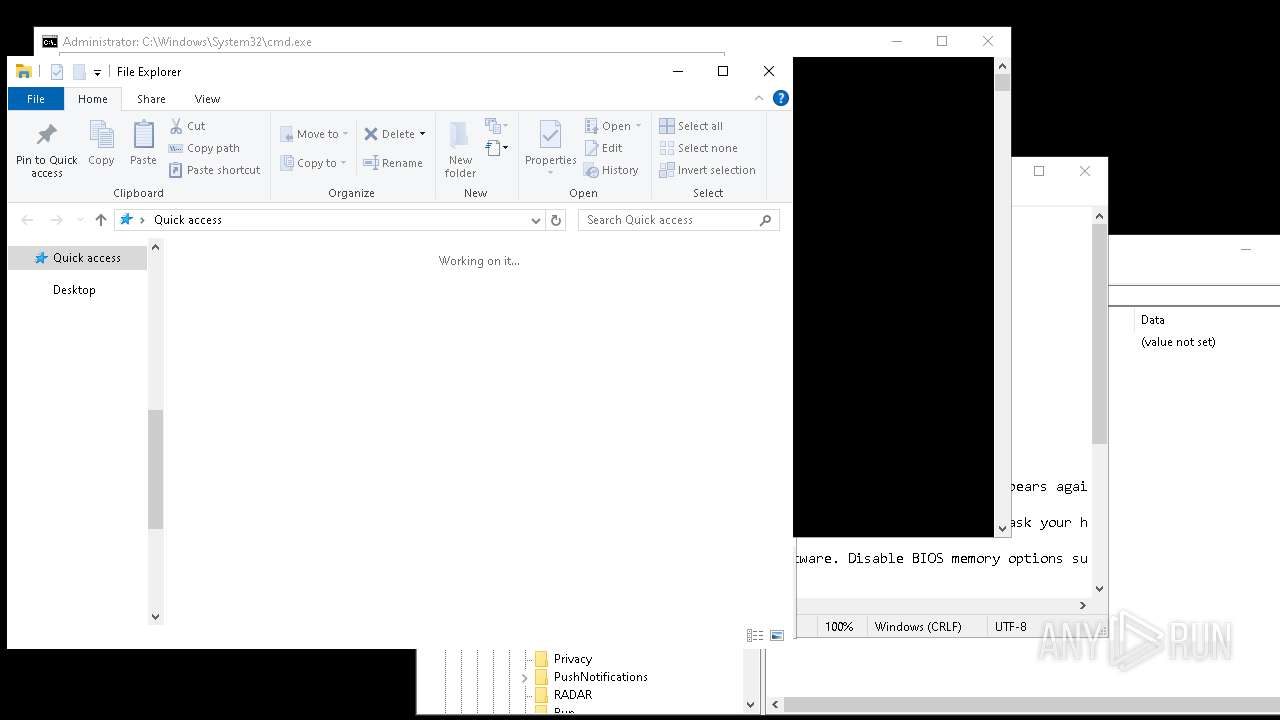
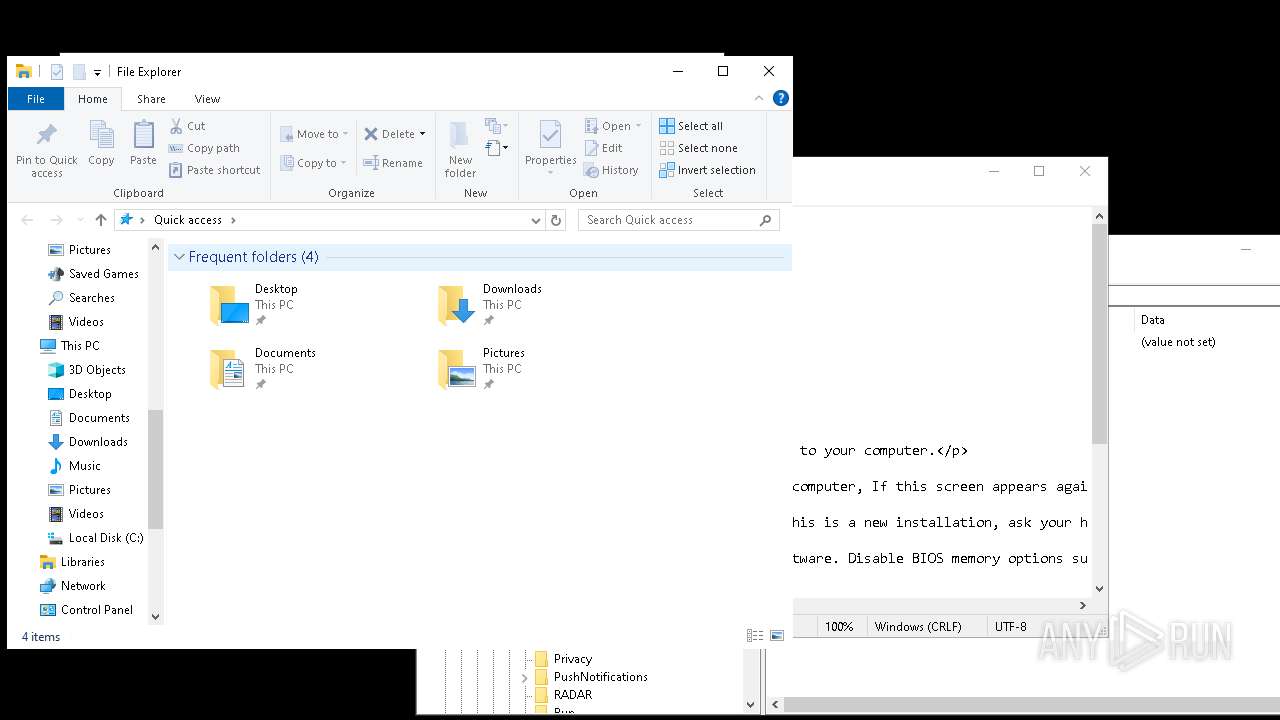
- explorer.exe (PID: 8048)
SMB connection has been detected (probably for file transfer)
- explorer.exe (PID: 8048)
INFO
Checks supported languages
- DeathPlus.exe (PID: 6668)
- MBRKiller.exe (PID: 1184)
- vlc.exe (PID: 2928)
- CLWCP.exe (PID: 3792)
- waves.exe (PID: 7208)
- tunnel.exe (PID: 8168)
- icons.exe (PID: 7528)
- ShellExperienceHost.exe (PID: 1880)
- BitBlt.exe (PID: 6200)
- scream.exe (PID: 8152)
- tunnel.exe (PID: 7852)
- CLWCP.exe (PID: 7540)
- scream.exe (PID: 8128)
- scream.exe (PID: 3972)
- scream.exe (PID: 7108)
- icons.exe (PID: 3860)
- scream.exe (PID: 7004)
- scream.exe (PID: 8132)
- scream.exe (PID: 3852)
- scream.exe (PID: 6752)
- scream.exe (PID: 4080)
- scream.exe (PID: 6808)
- scream.exe (PID: 1792)
- scream.exe (PID: 2784)
- scream.exe (PID: 4584)
- scream.exe (PID: 2888)
- scream.exe (PID: 1184)
- scream.exe (PID: 3844)
- scream.exe (PID: 3008)
- scream.exe (PID: 7000)
- scream.exe (PID: 916)
- scream.exe (PID: 6772)
- CLWCP.exe (PID: 6000)
- vlc.exe (PID: 7404)
- icons.exe (PID: 6756)
- BitBlt.exe (PID: 6628)
- tunnel.exe (PID: 7320)
- inv.exe (PID: 204)
- vlc.exe (PID: 2632)
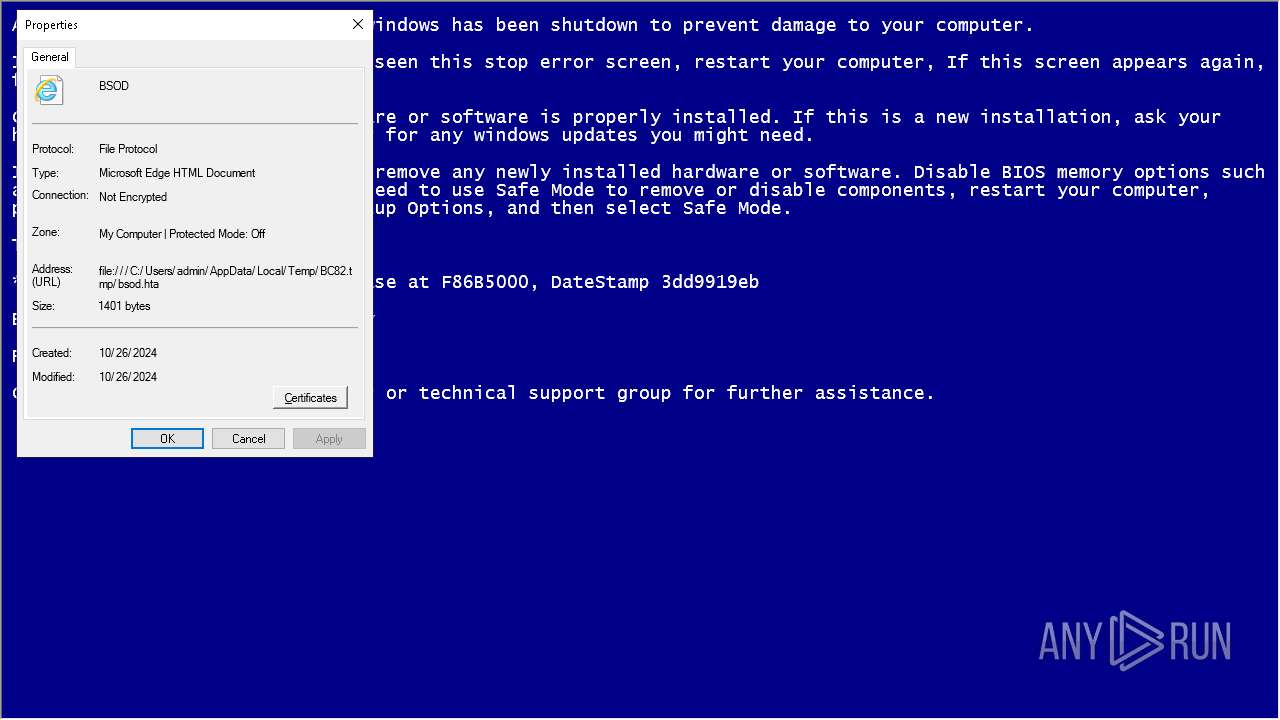
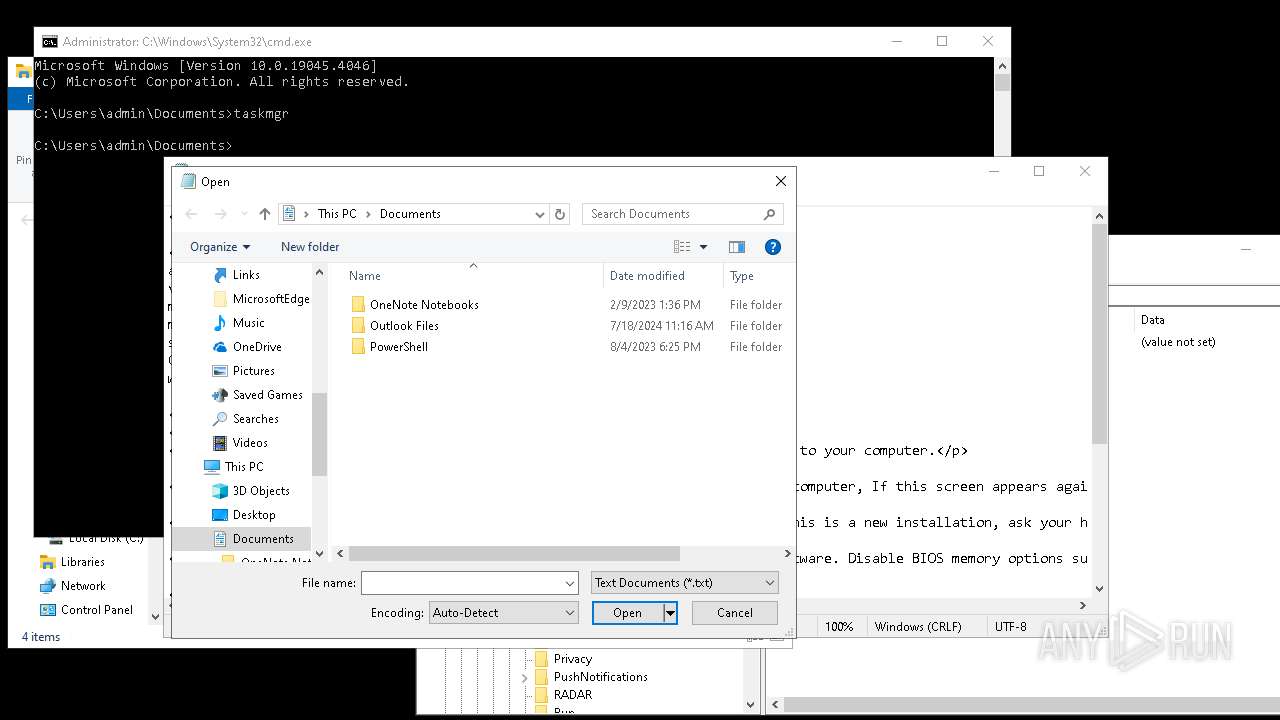
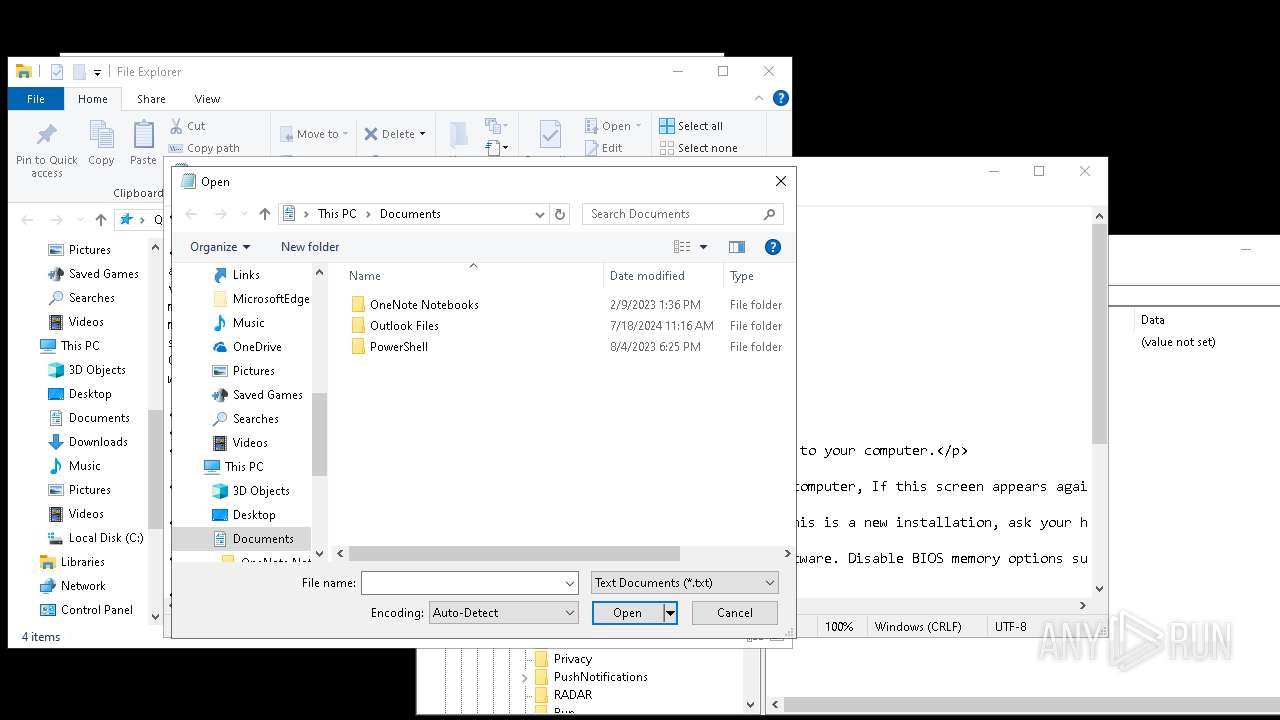
Create files in a temporary directory
- DeathPlus.exe (PID: 6668)
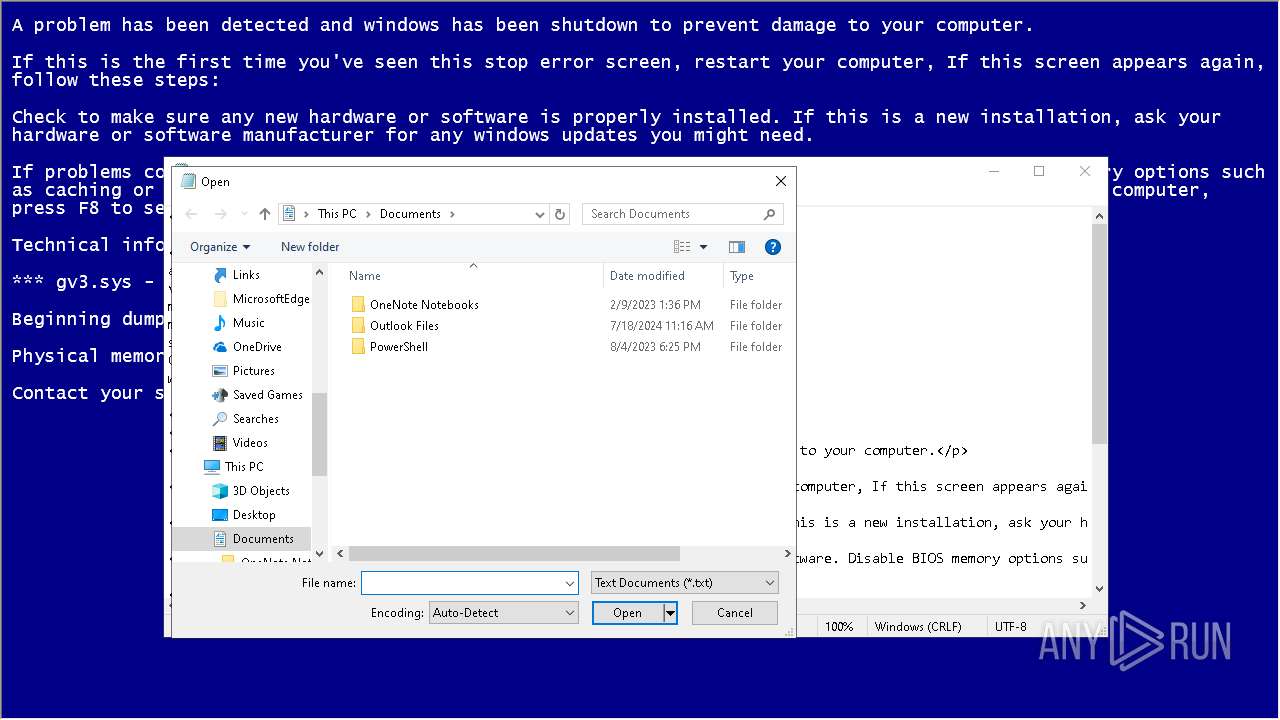
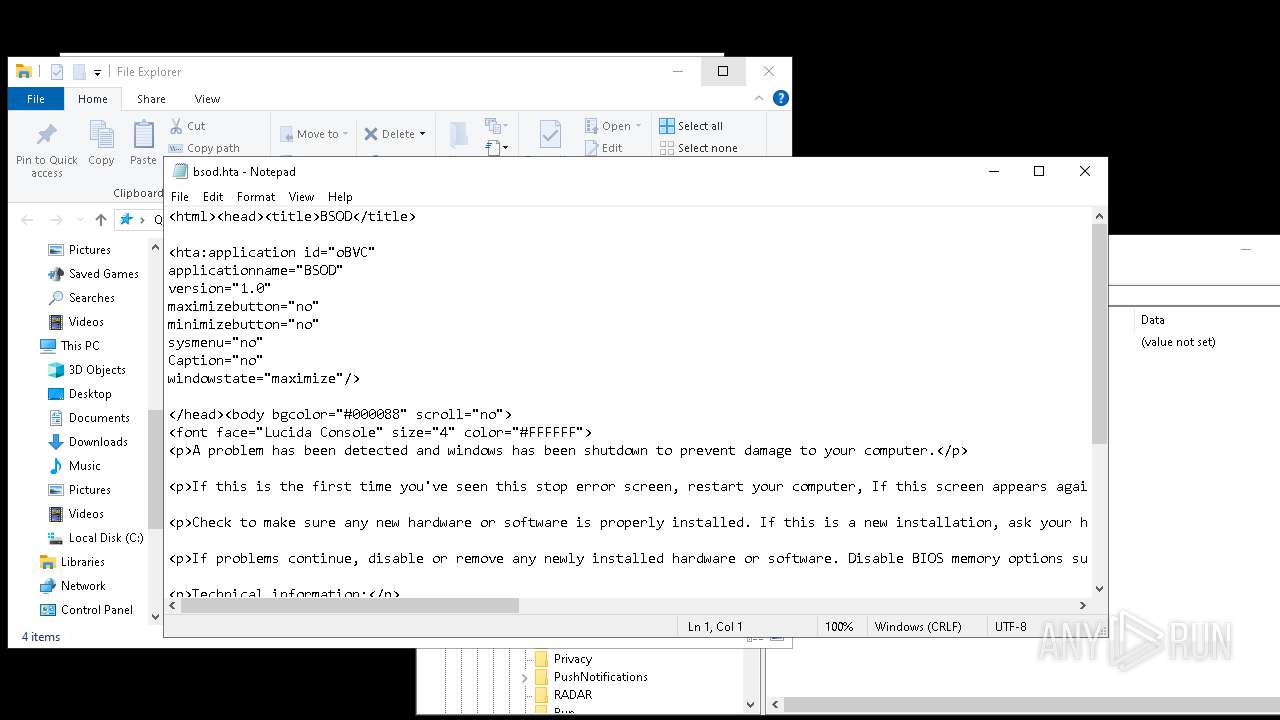
The process uses the downloaded file
- DeathPlus.exe (PID: 6668)
- cmd.exe (PID: 2648)
- mshta.exe (PID: 5976)
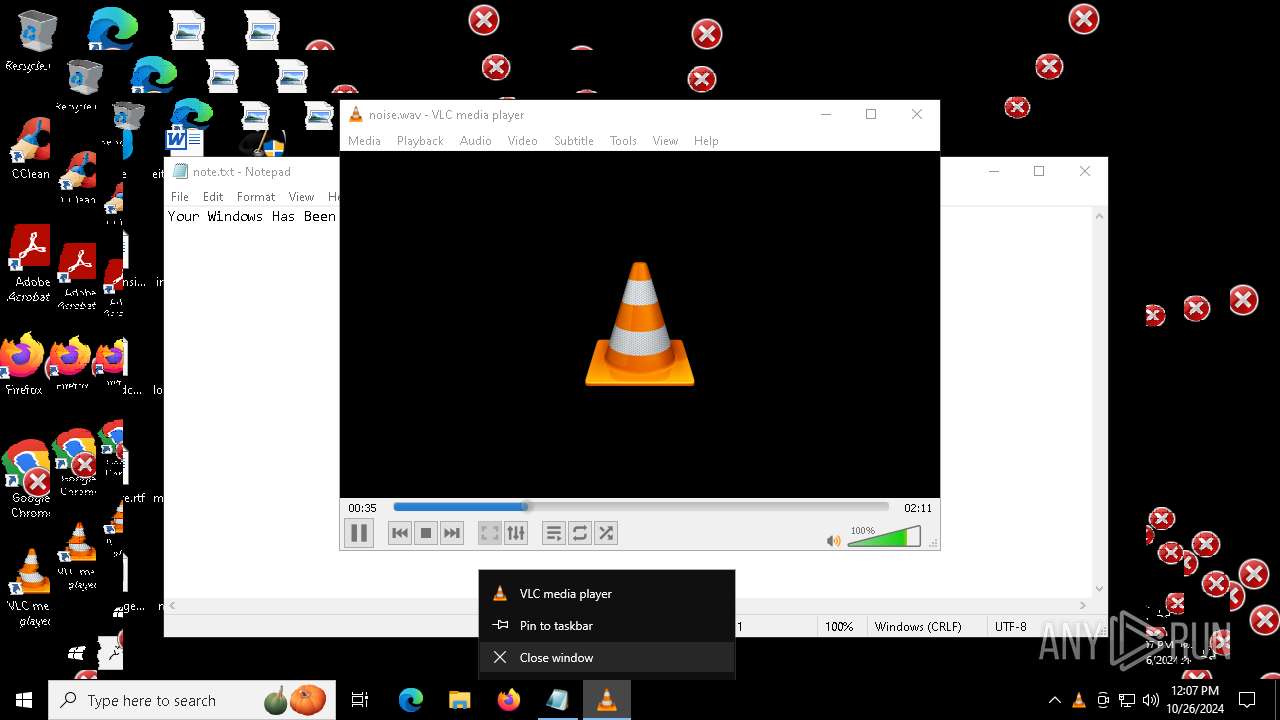
- notepad.exe (PID: 6204)
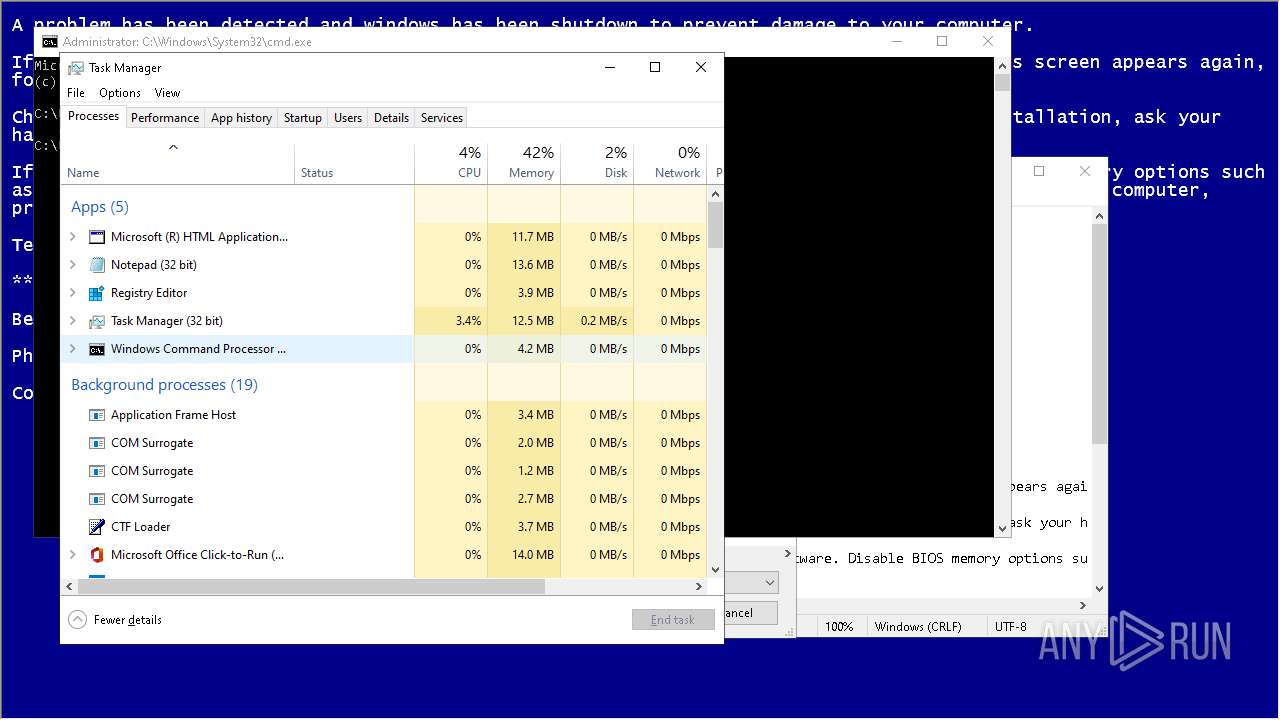
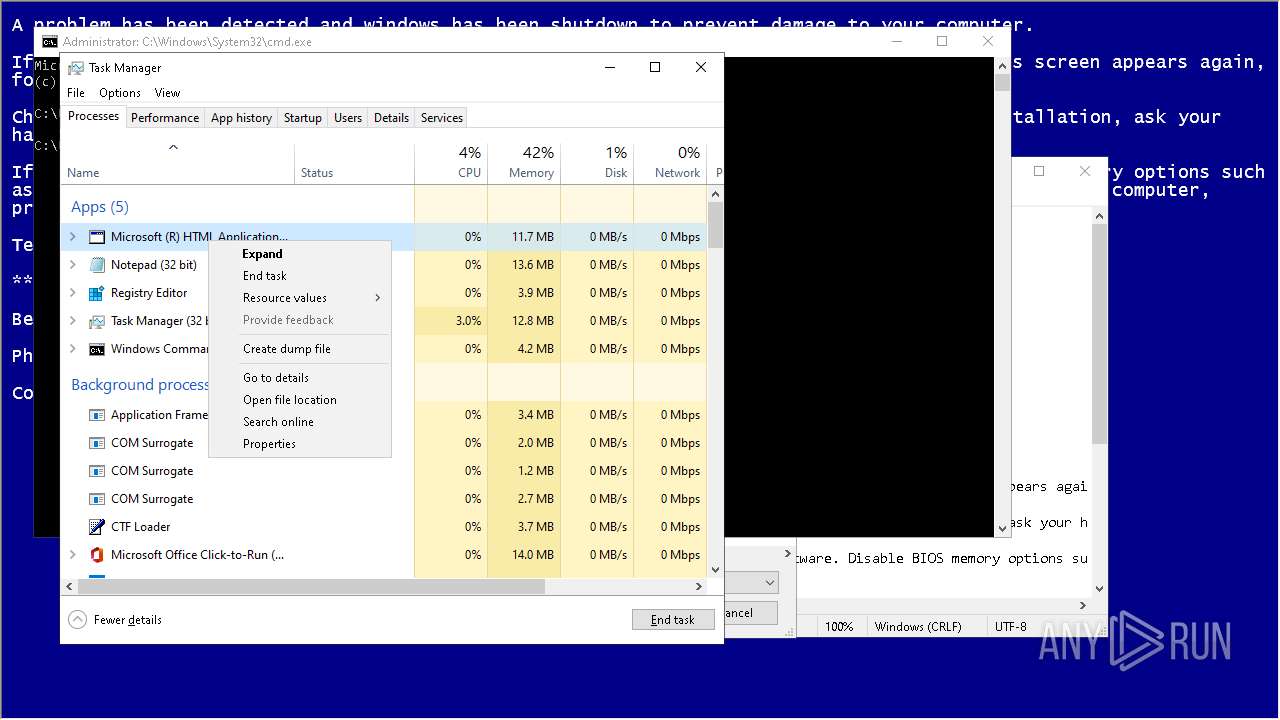
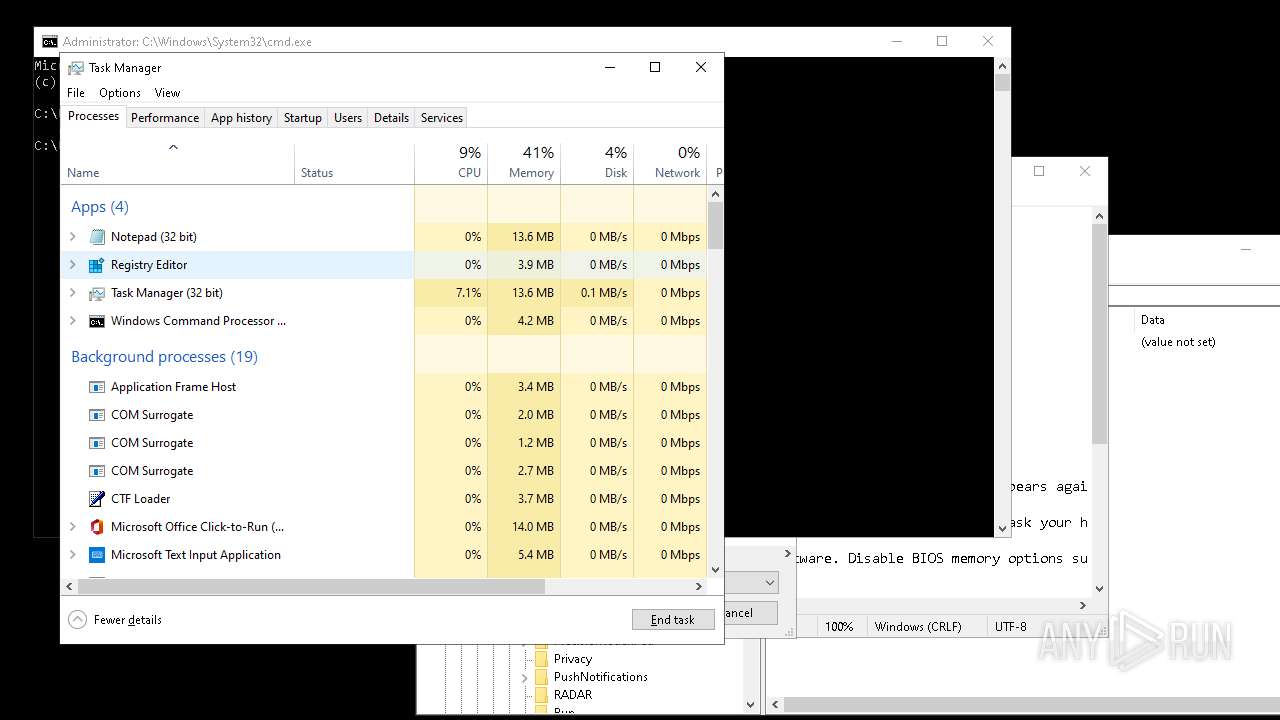
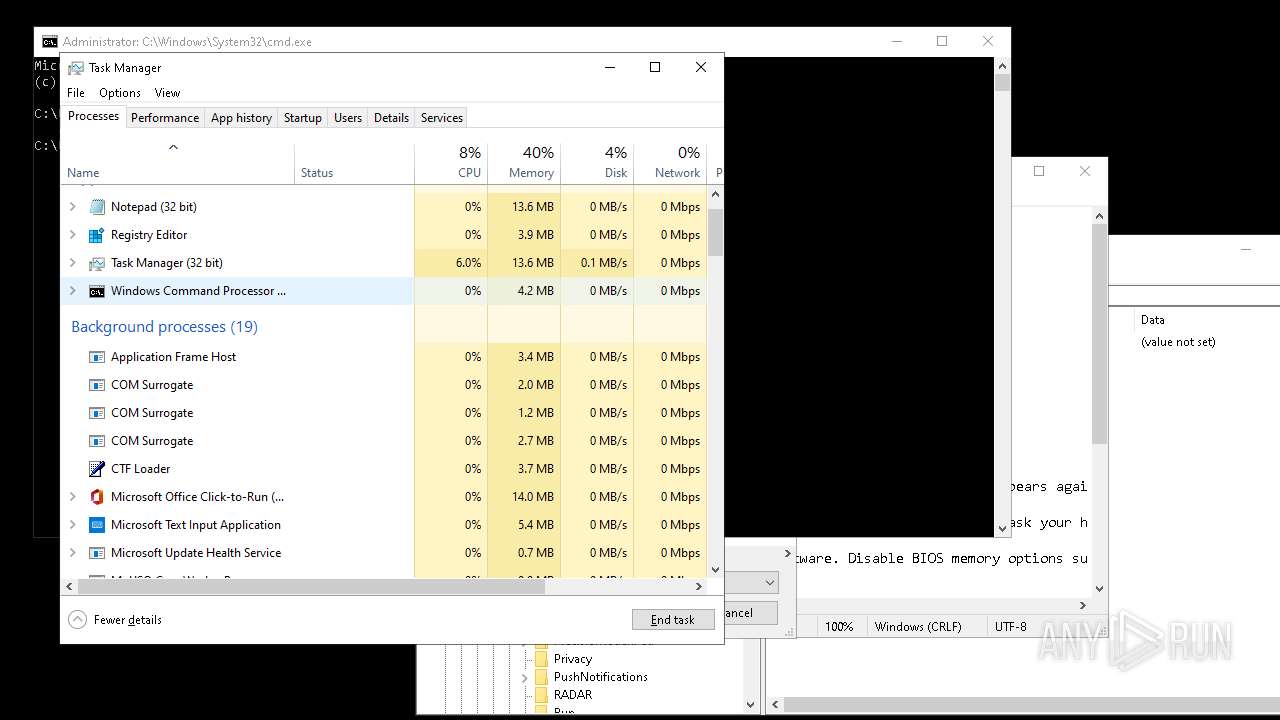
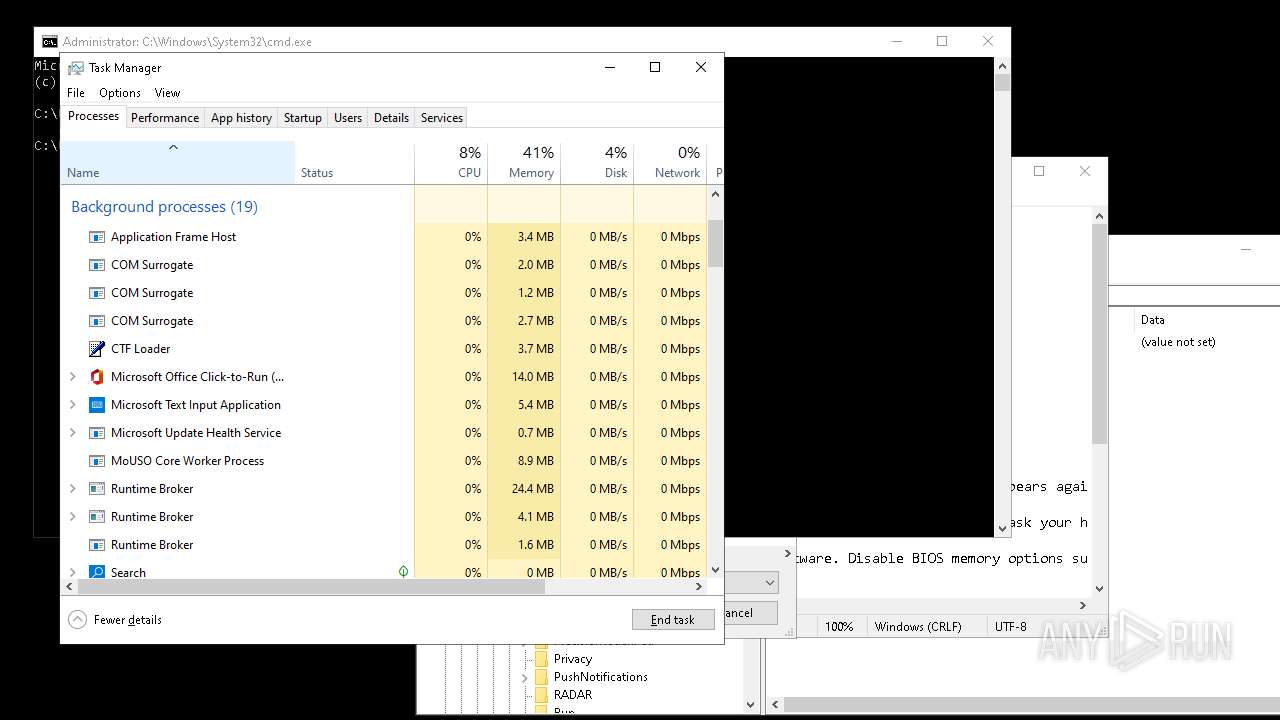
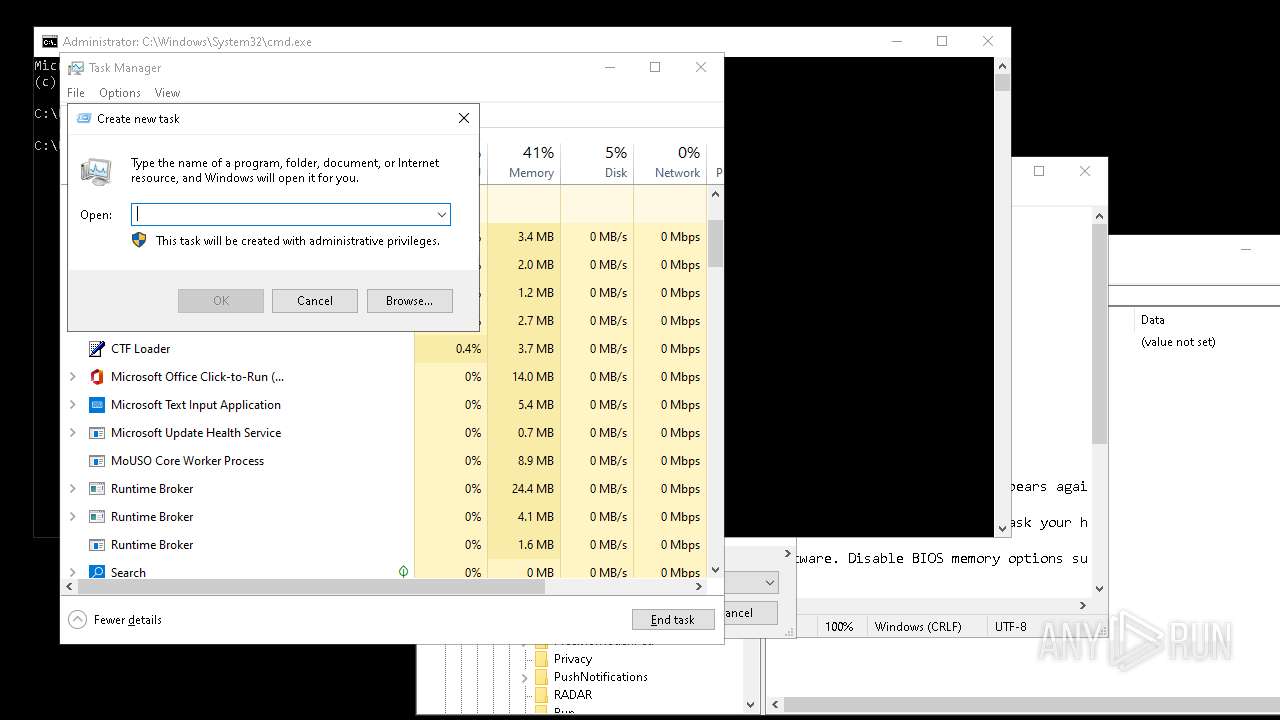
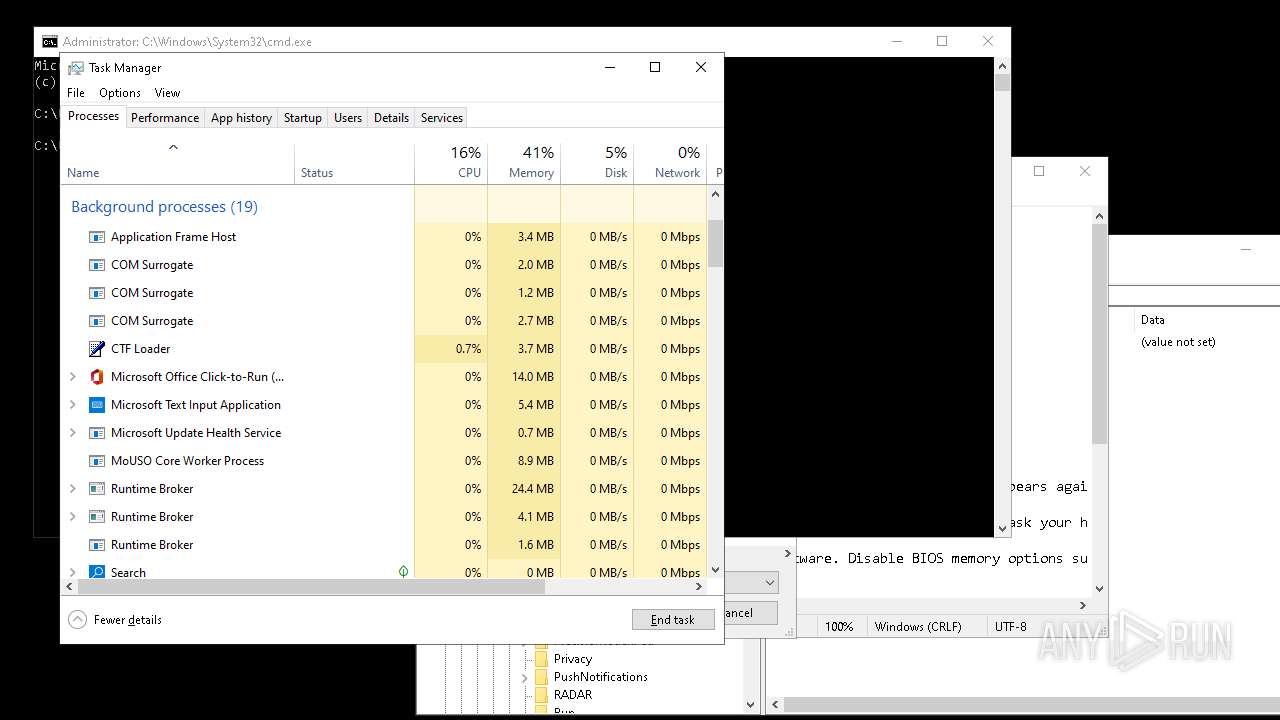
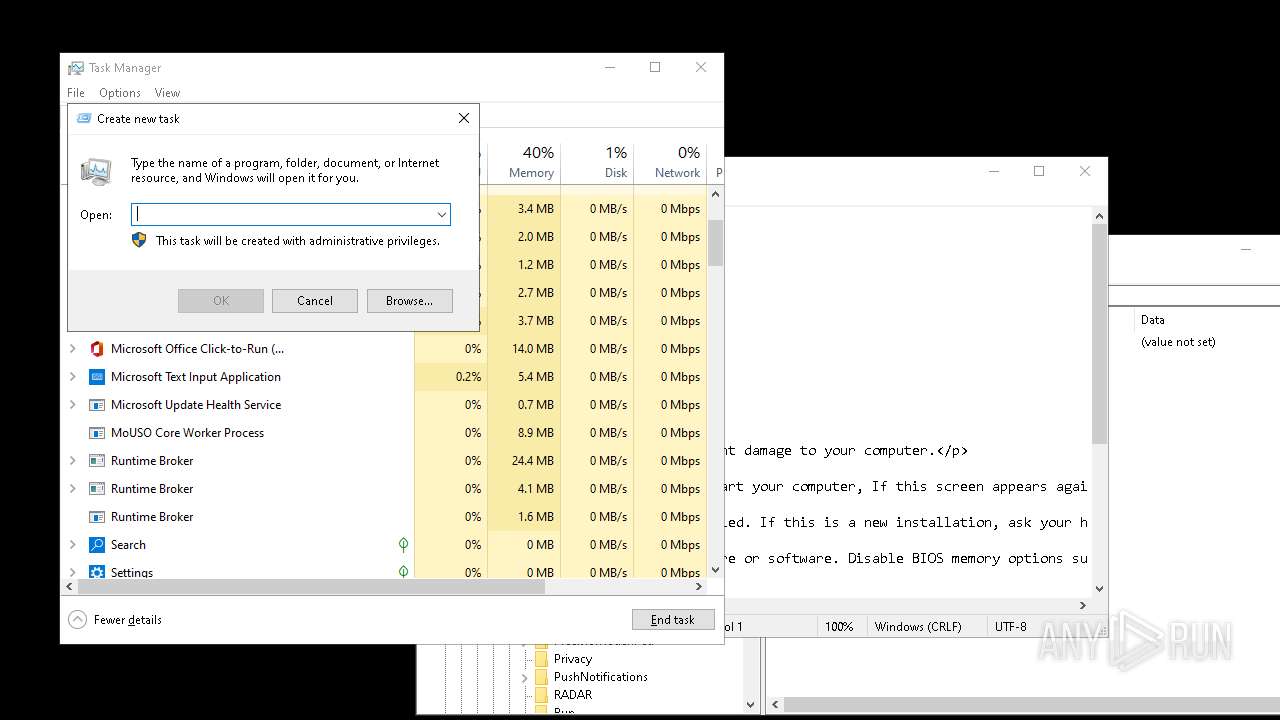
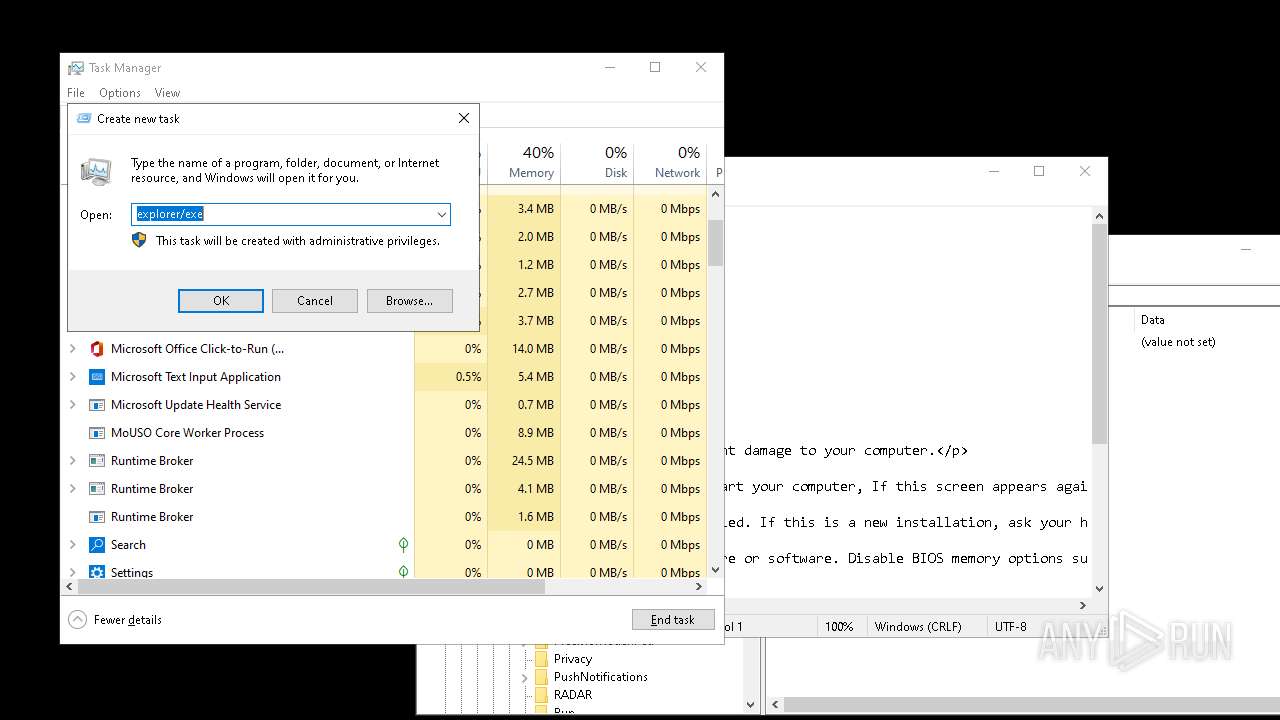
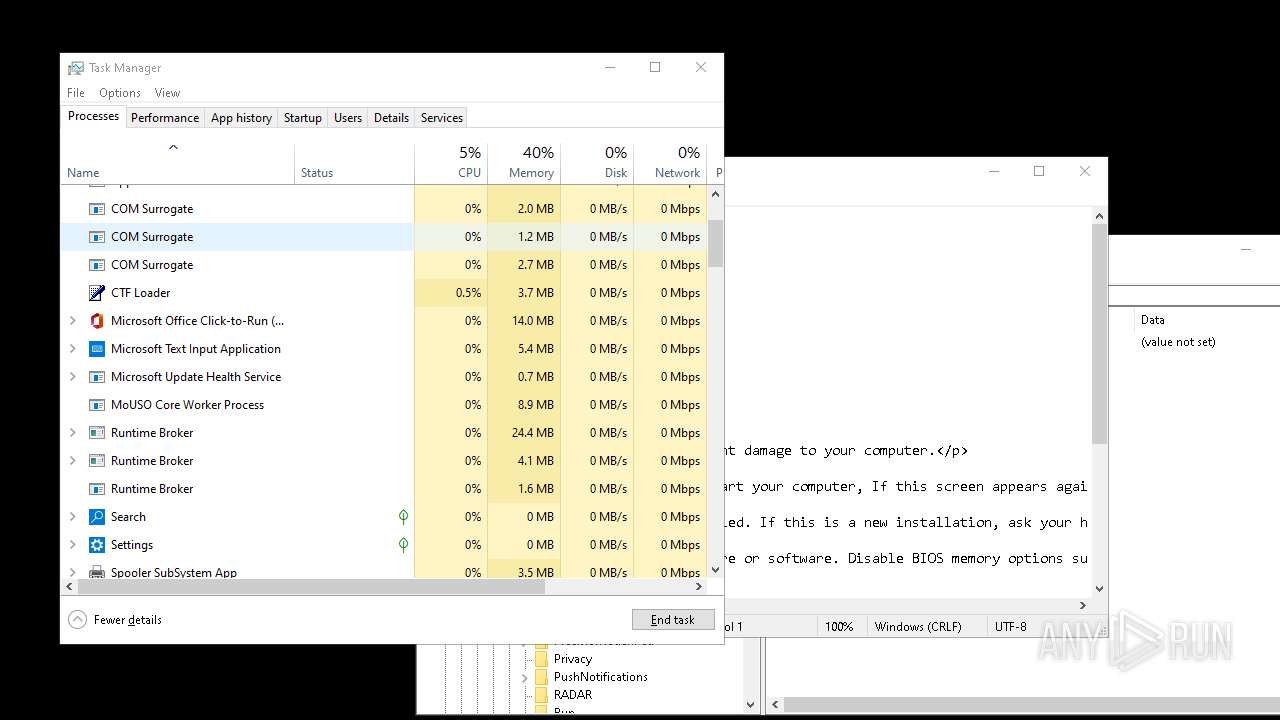
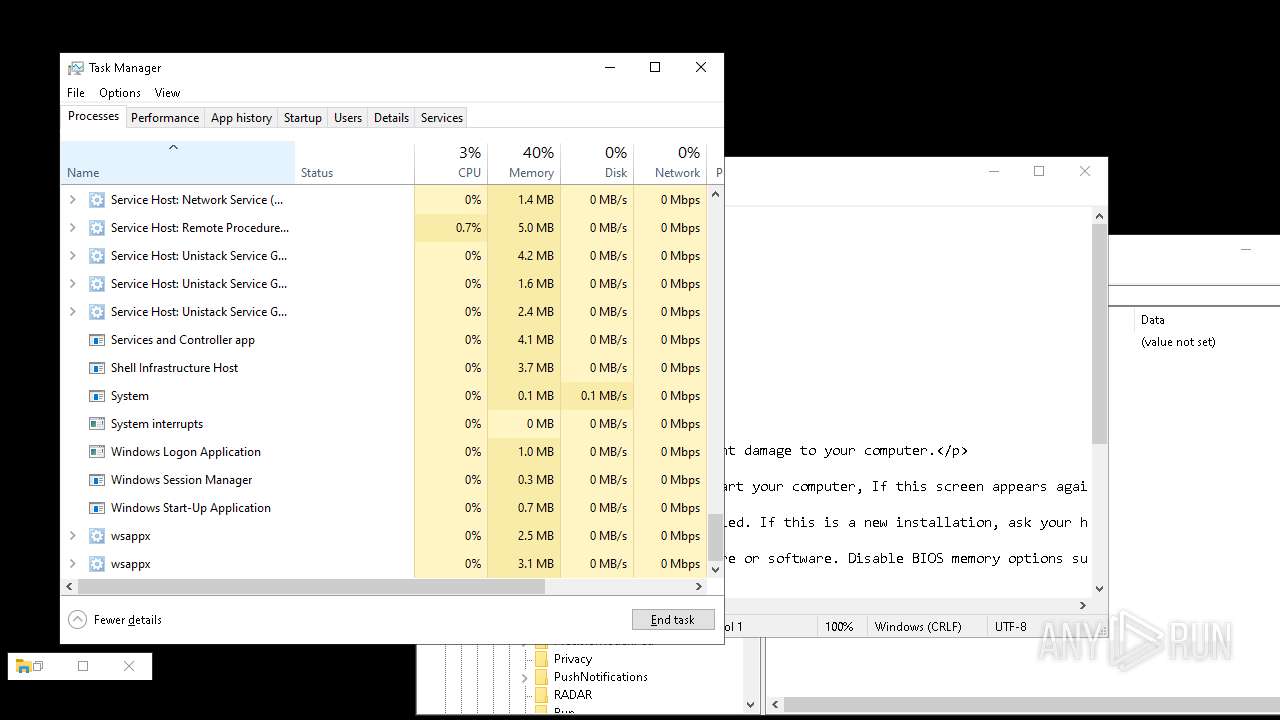
- Taskmgr.exe (PID: 4340)
Process checks computer location settings
- DeathPlus.exe (PID: 6668)
Reads the computer name
- DeathPlus.exe (PID: 6668)
- ShellExperienceHost.exe (PID: 1880)
- vlc.exe (PID: 2928)
- scream.exe (PID: 8152)
- scream.exe (PID: 8128)
- scream.exe (PID: 7108)
- scream.exe (PID: 3972)
- scream.exe (PID: 8132)
- scream.exe (PID: 7004)
- scream.exe (PID: 1792)
- scream.exe (PID: 3852)
- scream.exe (PID: 4080)
- scream.exe (PID: 6752)
- scream.exe (PID: 6808)
- scream.exe (PID: 3844)
- scream.exe (PID: 2784)
- scream.exe (PID: 7000)
- scream.exe (PID: 1184)
- scream.exe (PID: 916)
- scream.exe (PID: 4584)
- scream.exe (PID: 3008)
- scream.exe (PID: 2888)
- scream.exe (PID: 6772)
- vlc.exe (PID: 7404)
Sends debugging messages
- vlc.exe (PID: 2928)
- ShellExperienceHost.exe (PID: 1880)
- vlc.exe (PID: 7404)
- vlc.exe (PID: 2632)
Reads security settings of Internet Explorer
- notepad.exe (PID: 3740)
- notepad.exe (PID: 6204)
- Taskmgr.exe (PID: 4340)
- explorer.exe (PID: 8048)
UPX packer has been detected
- DeathPlus.exe (PID: 6668)
The process uses Lua
- vlc.exe (PID: 2928)
Manual execution by a user
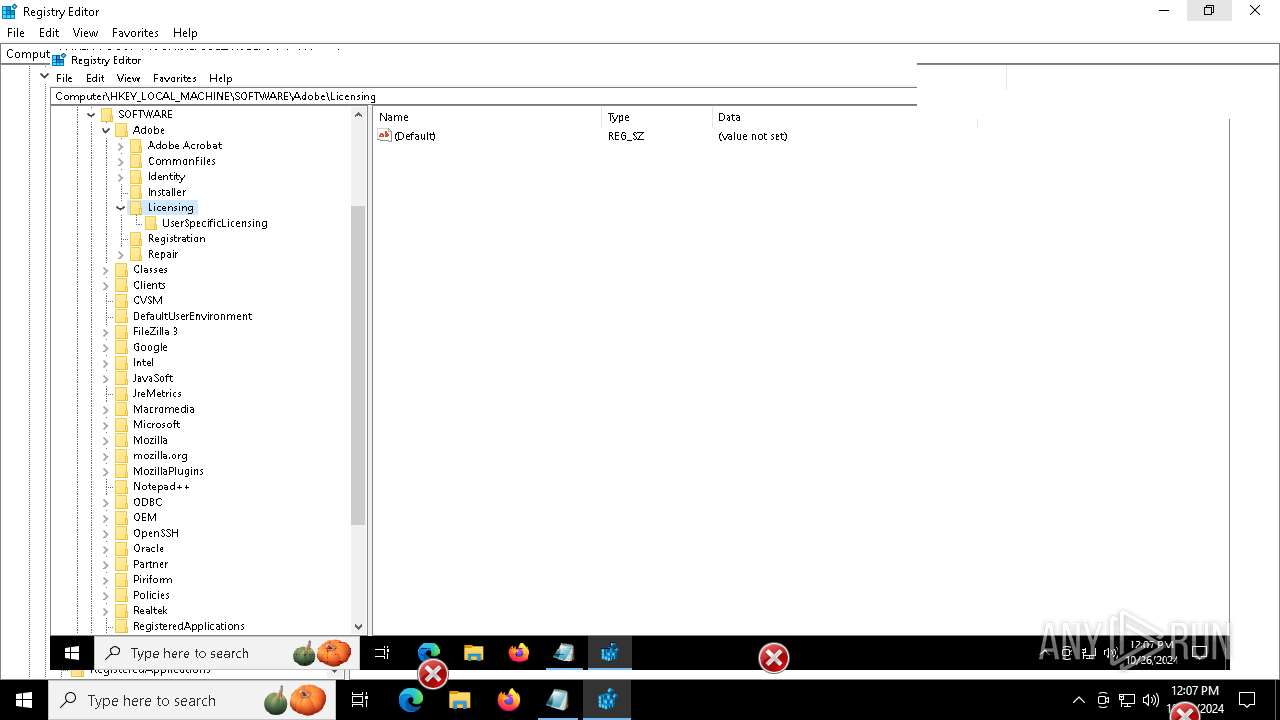
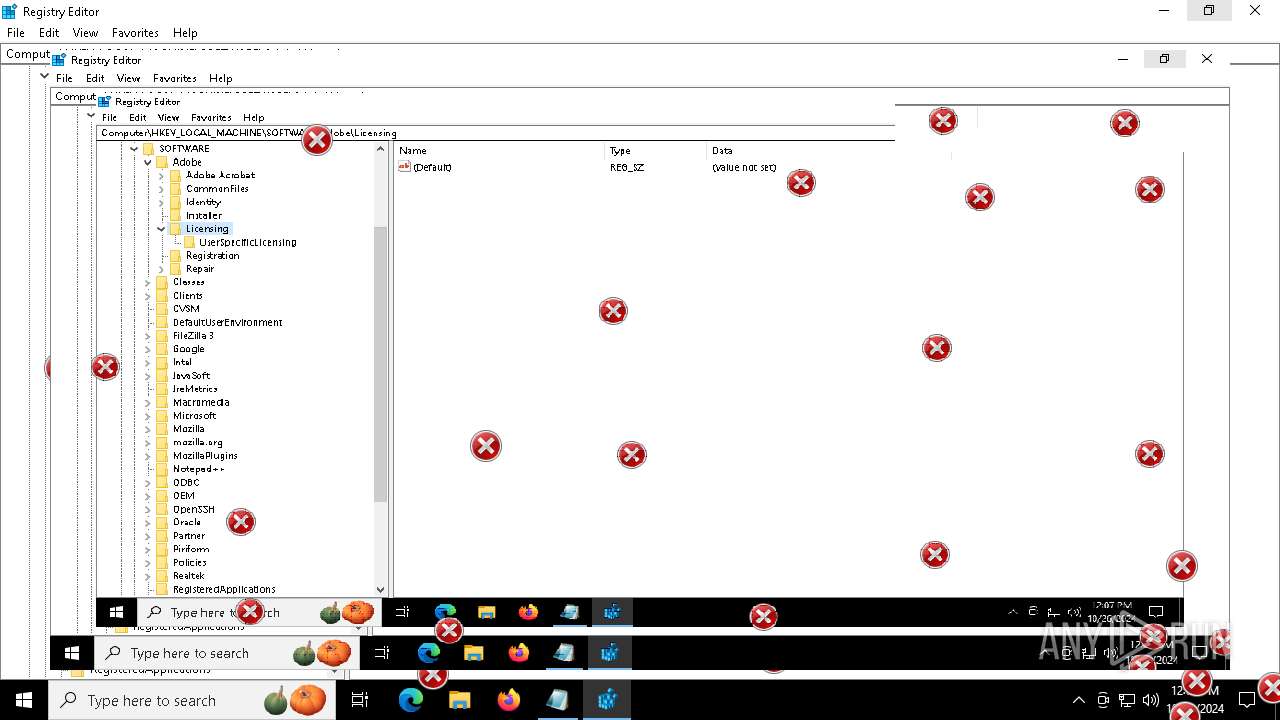
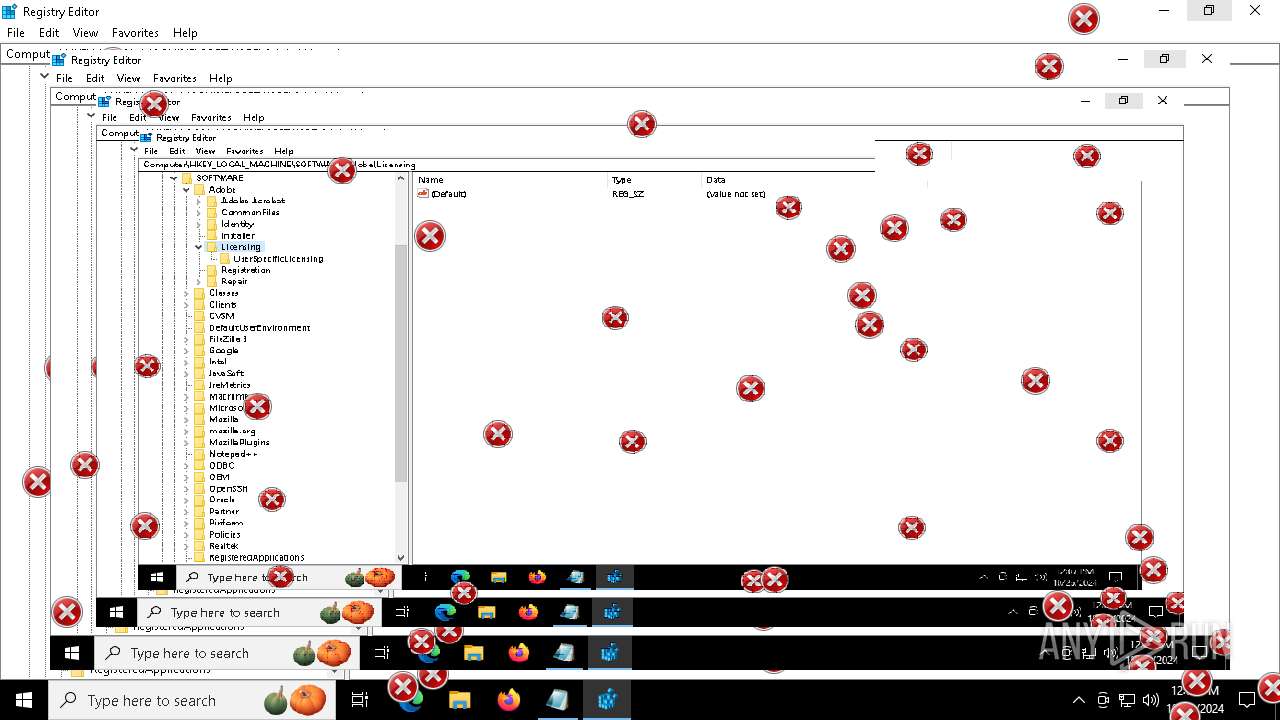
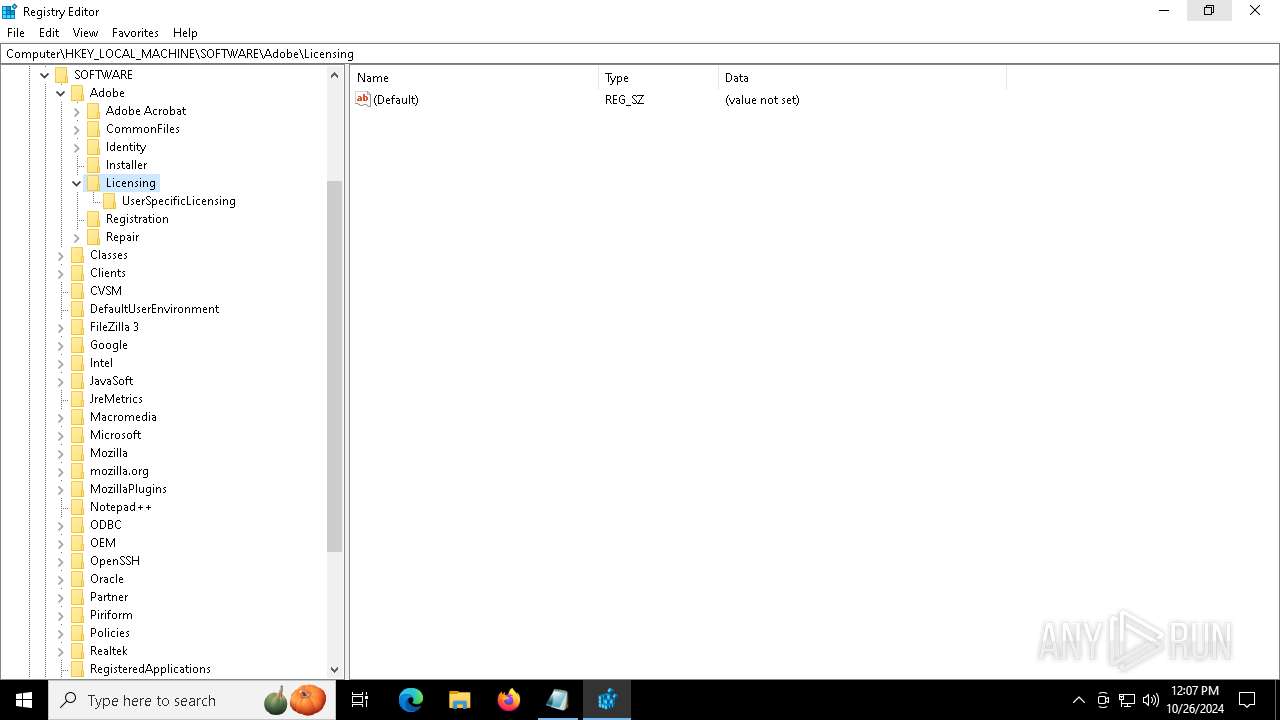
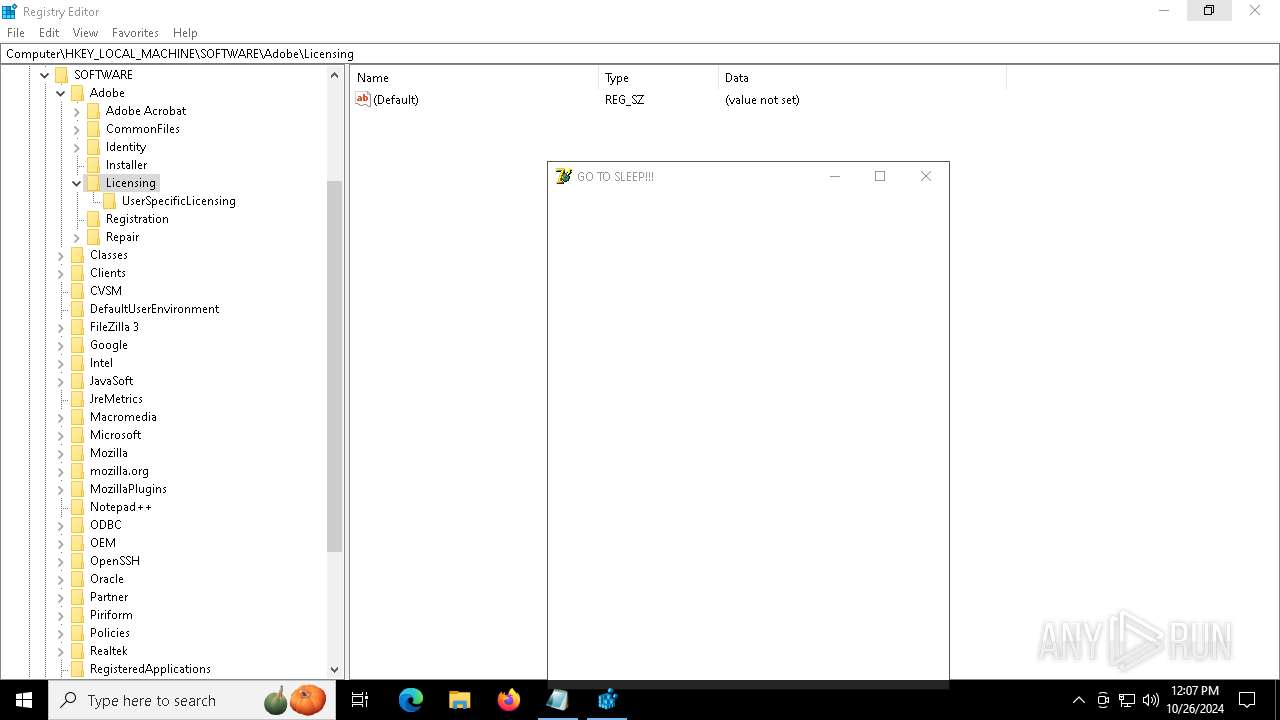
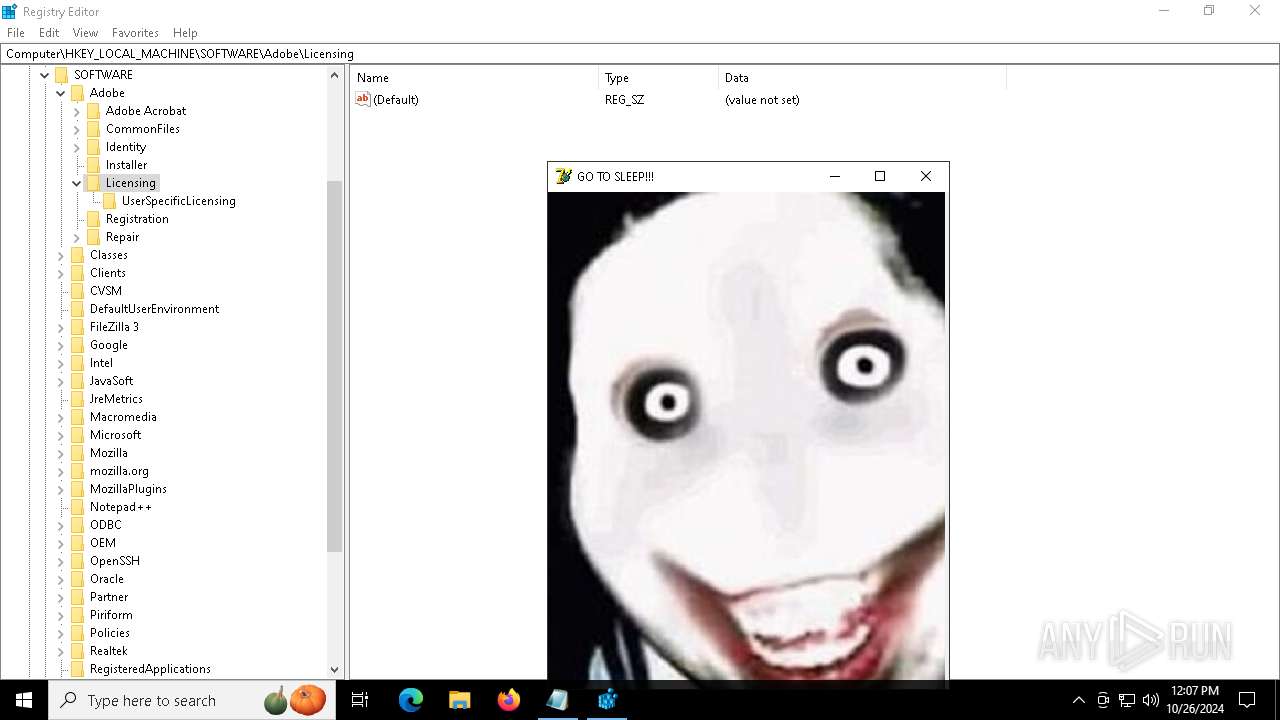
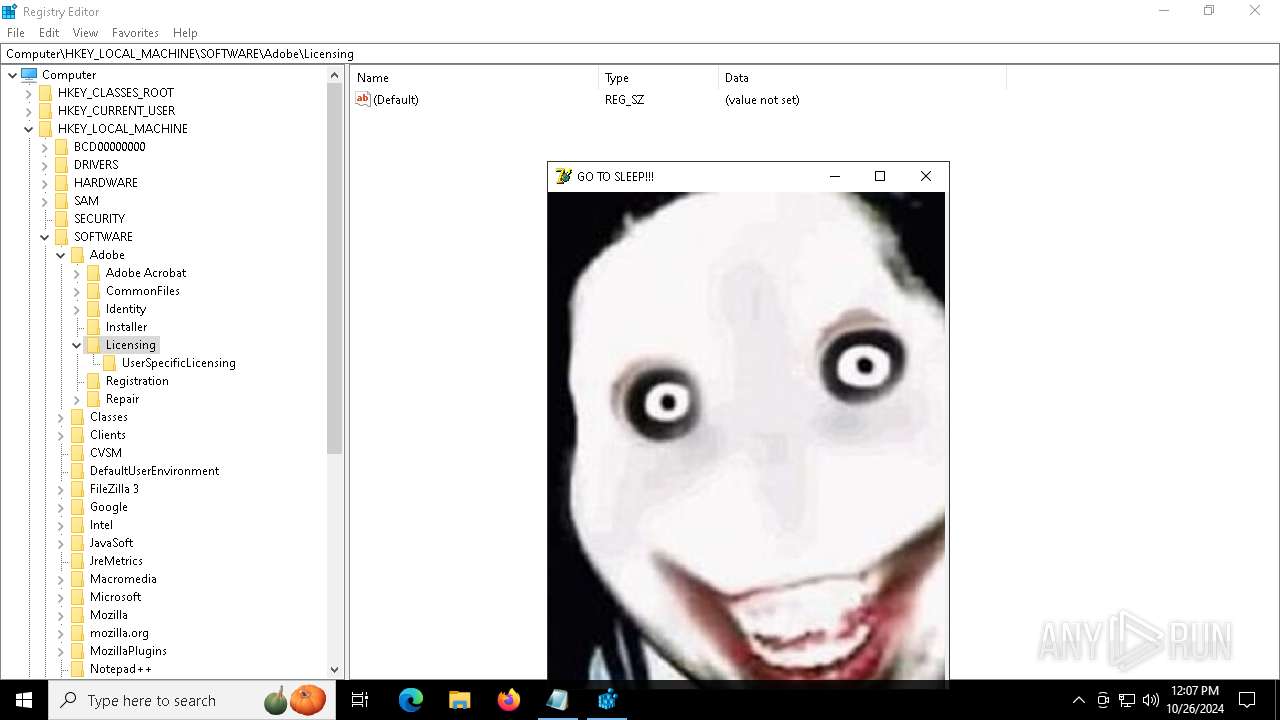
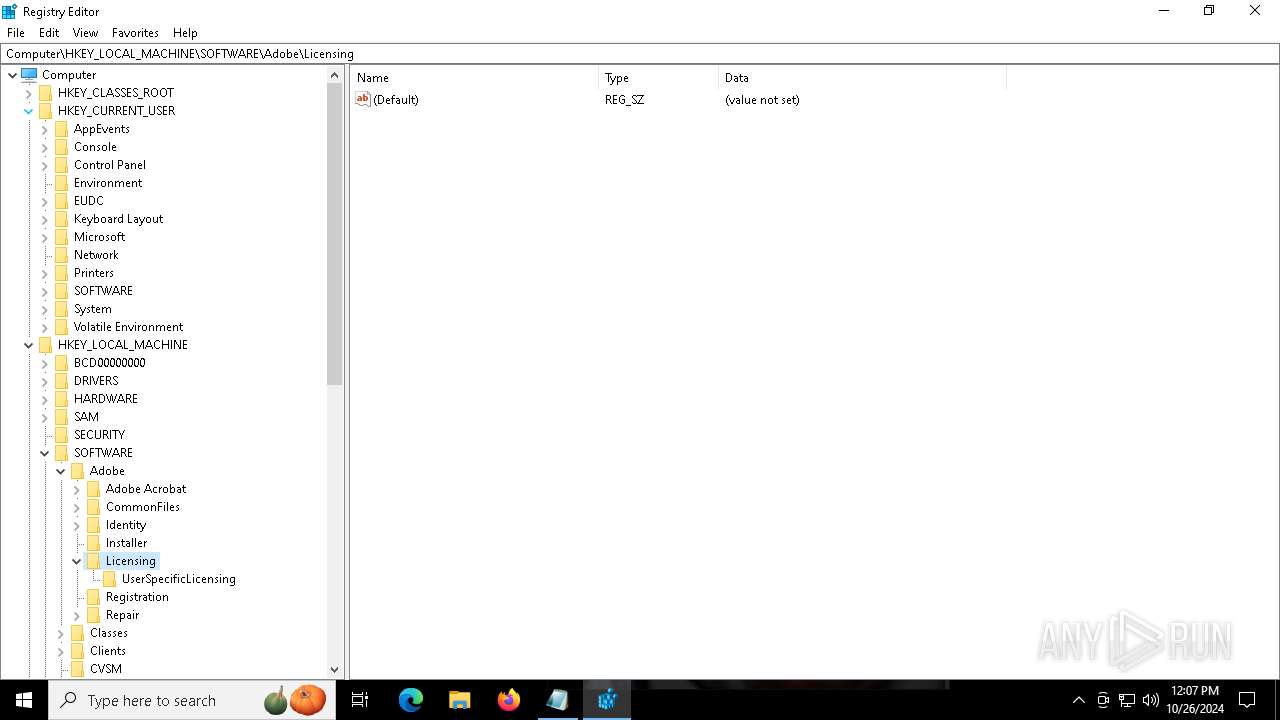
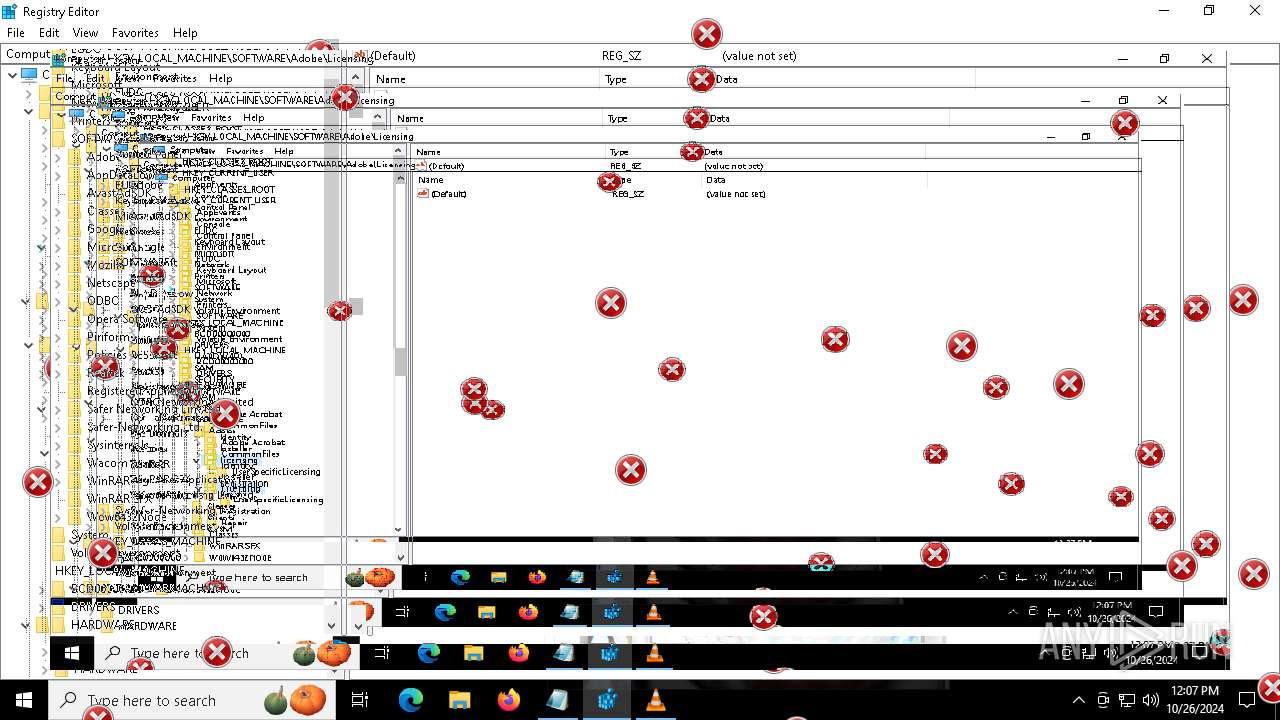
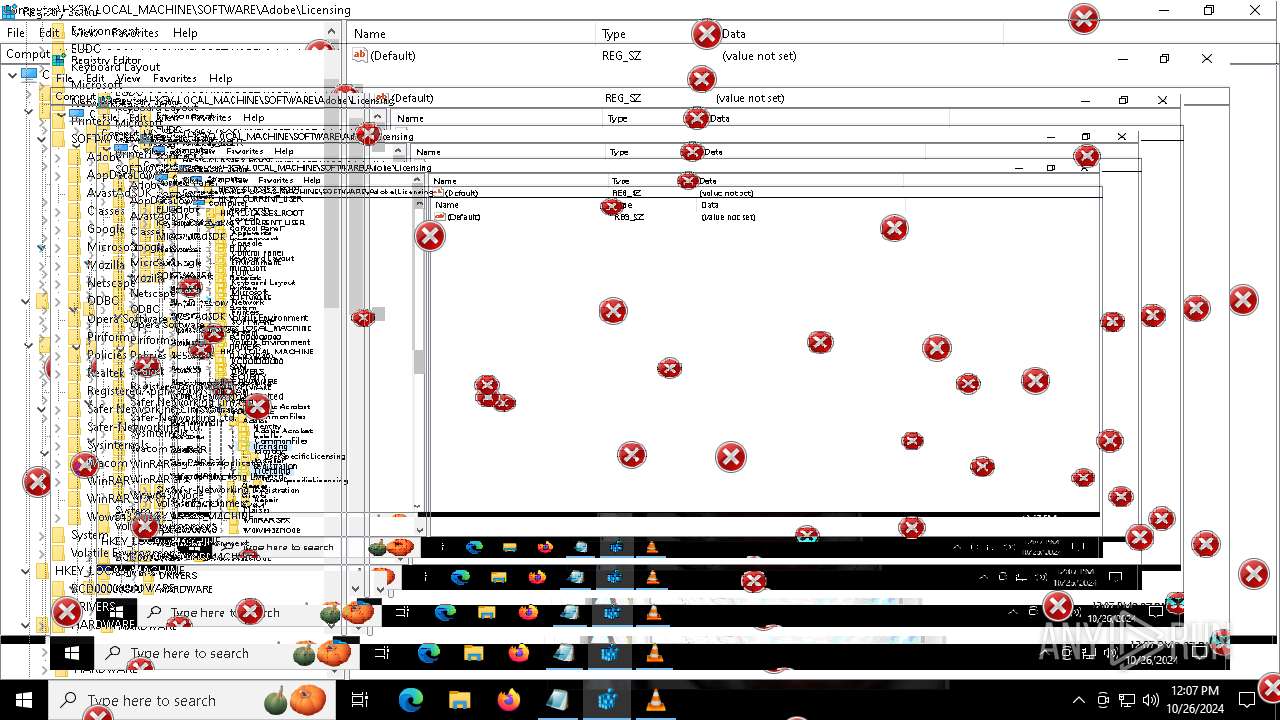
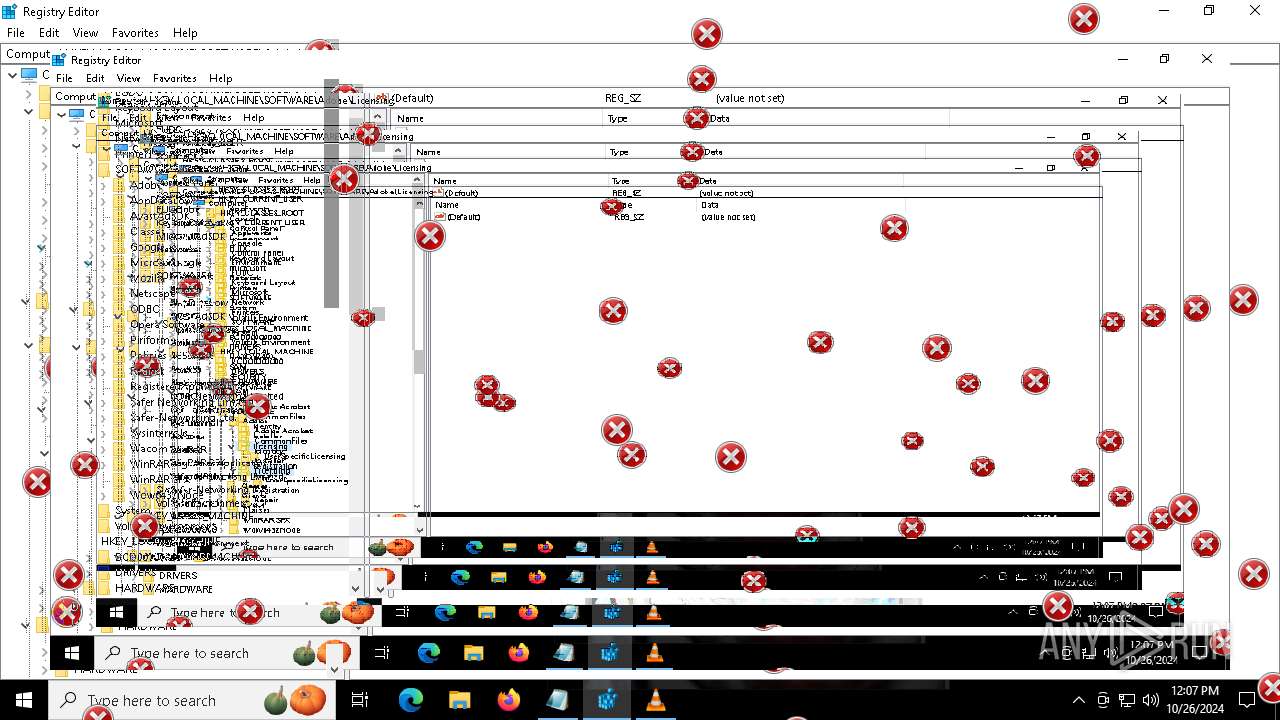
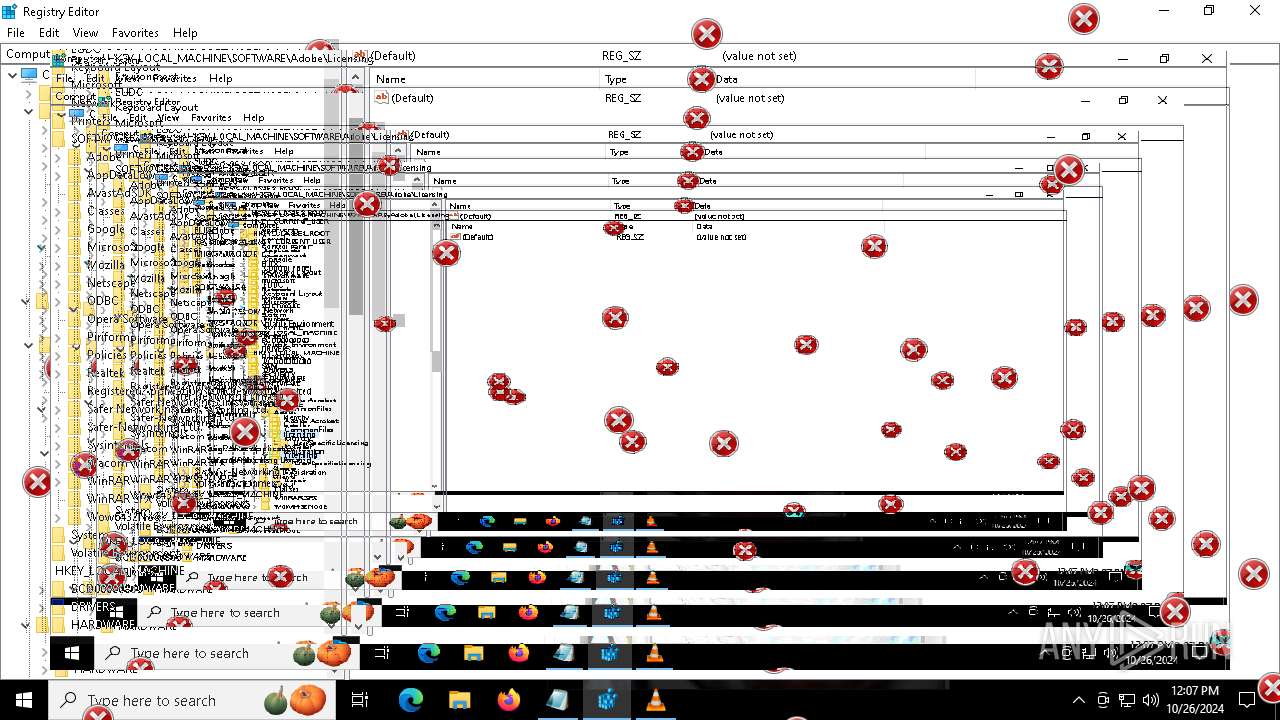
- regedit.exe (PID: 7884)
- regedit.exe (PID: 616)
Reads the software policy settings
- slui.exe (PID: 8000)
- slui.exe (PID: 7908)
Reads Internet Explorer settings
- mshta.exe (PID: 5976)
Creates files or folders in the user directory
- Taskmgr.exe (PID: 4340)
Checks proxy server information
- slui.exe (PID: 7908)
- mshta.exe (PID: 5976)
- explorer.exe (PID: 8048)
Application launched itself
- msedge.exe (PID: 5616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:08 13:12:07+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 5767168 |
| InitializedDataSize: | 200704 |
| UninitializedDataSize: | 29433856 |
| EntryPoint: | 0x2191930 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug, Pre-release, Private build |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileDescription: | Do not run this on Real PC |
| FileVersion: | 1,0,0,0 |
| ProductName: | DeathPlus |
| ProductVersion: | 1,0,0,0 |
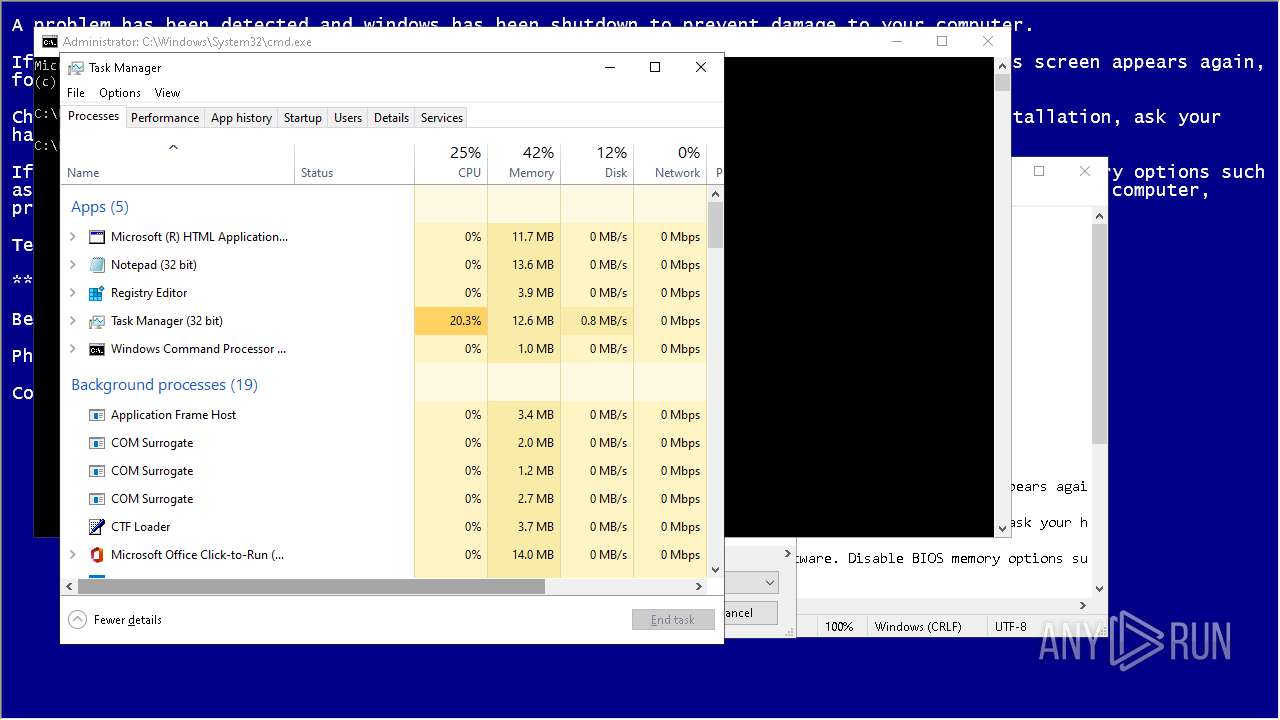
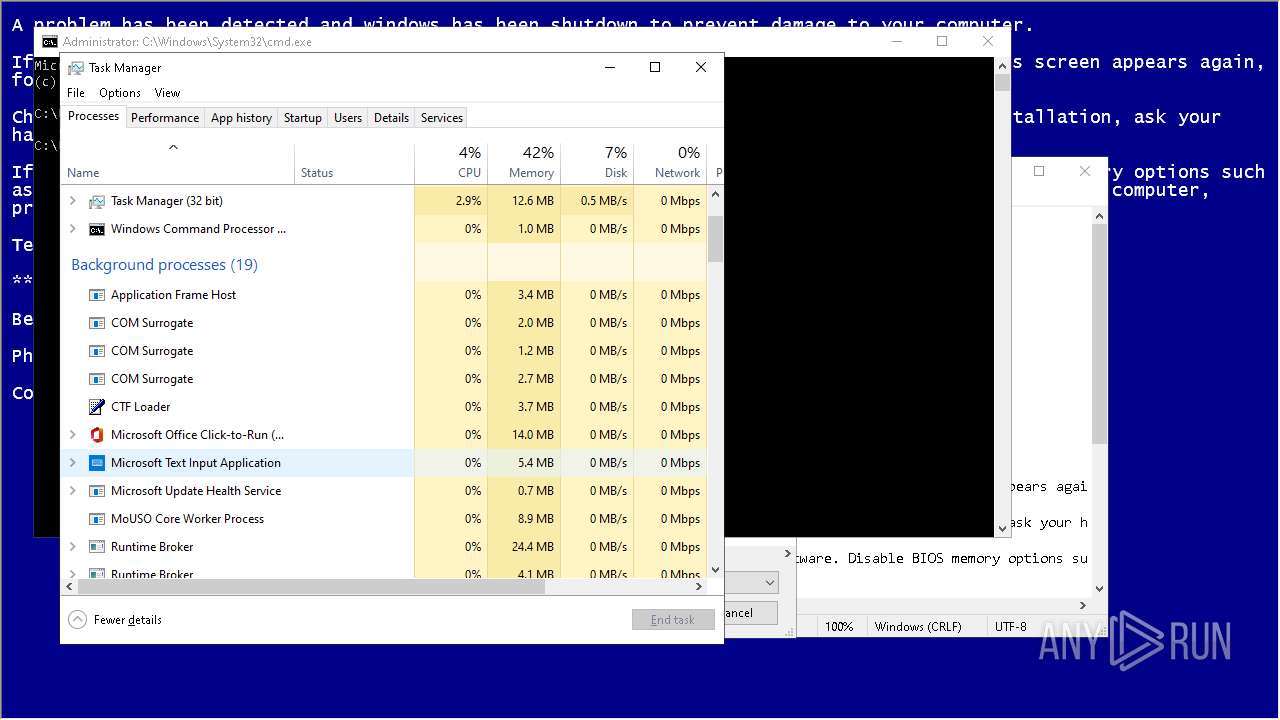
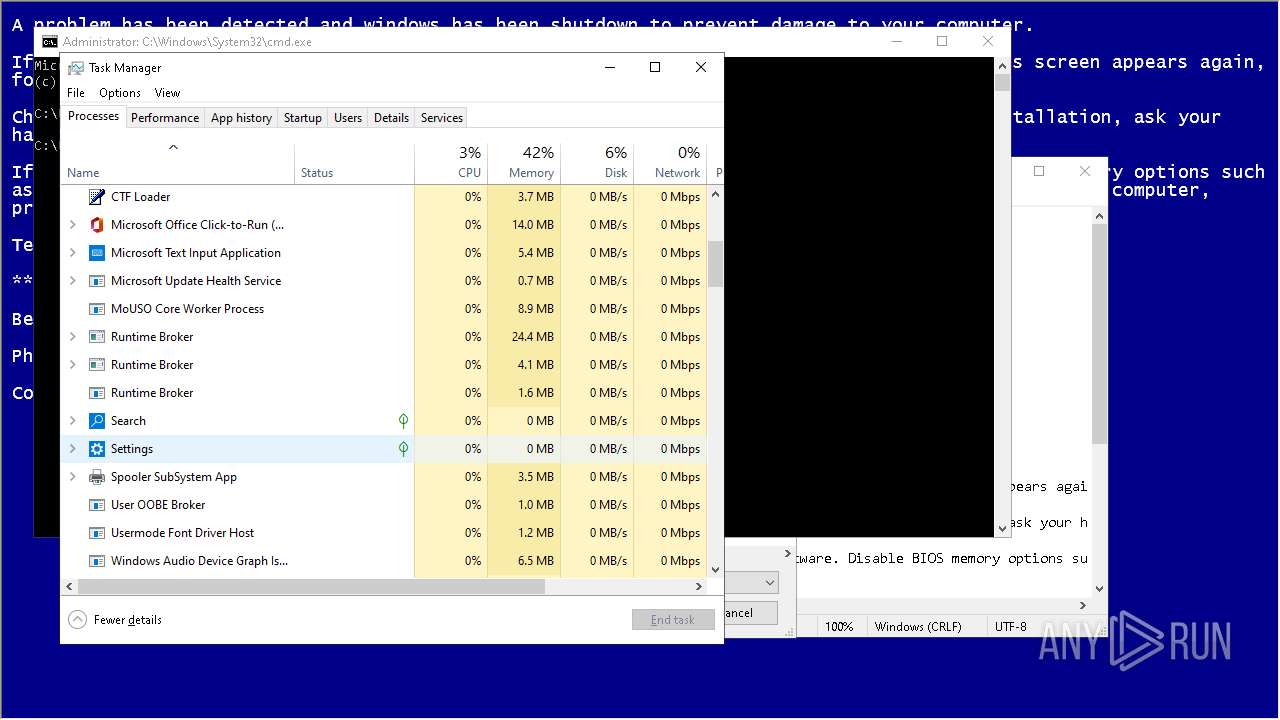
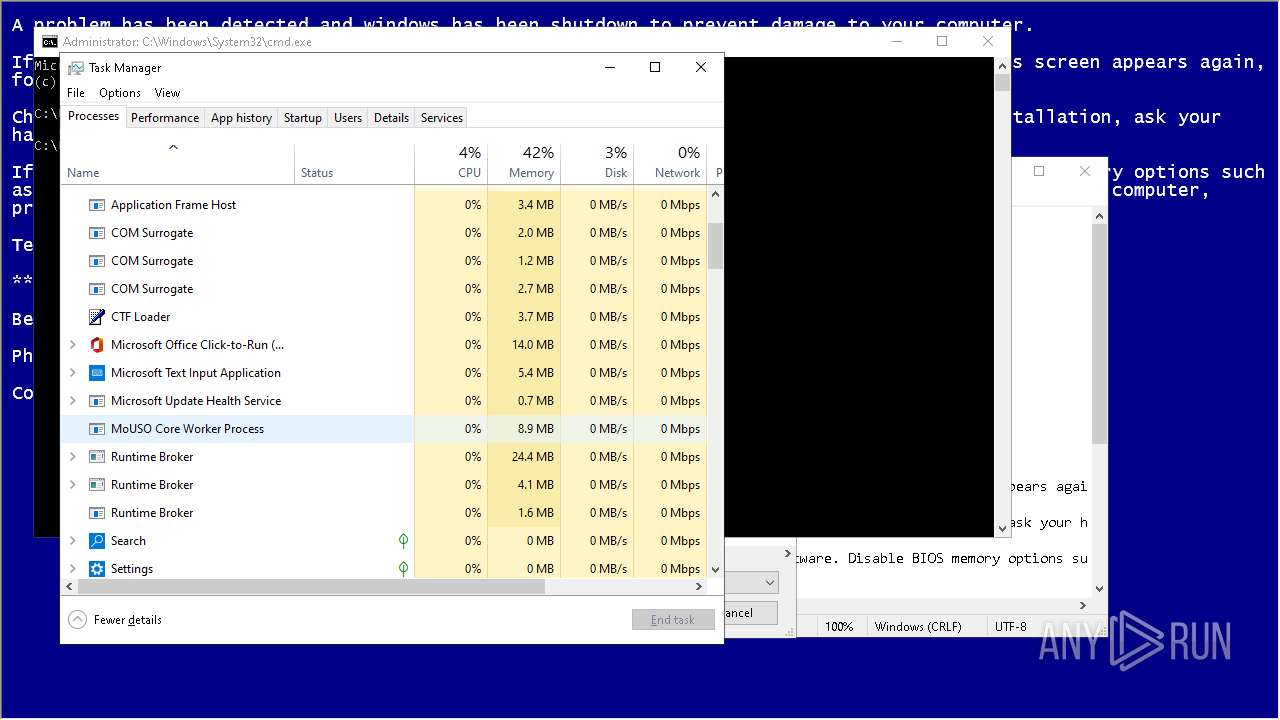
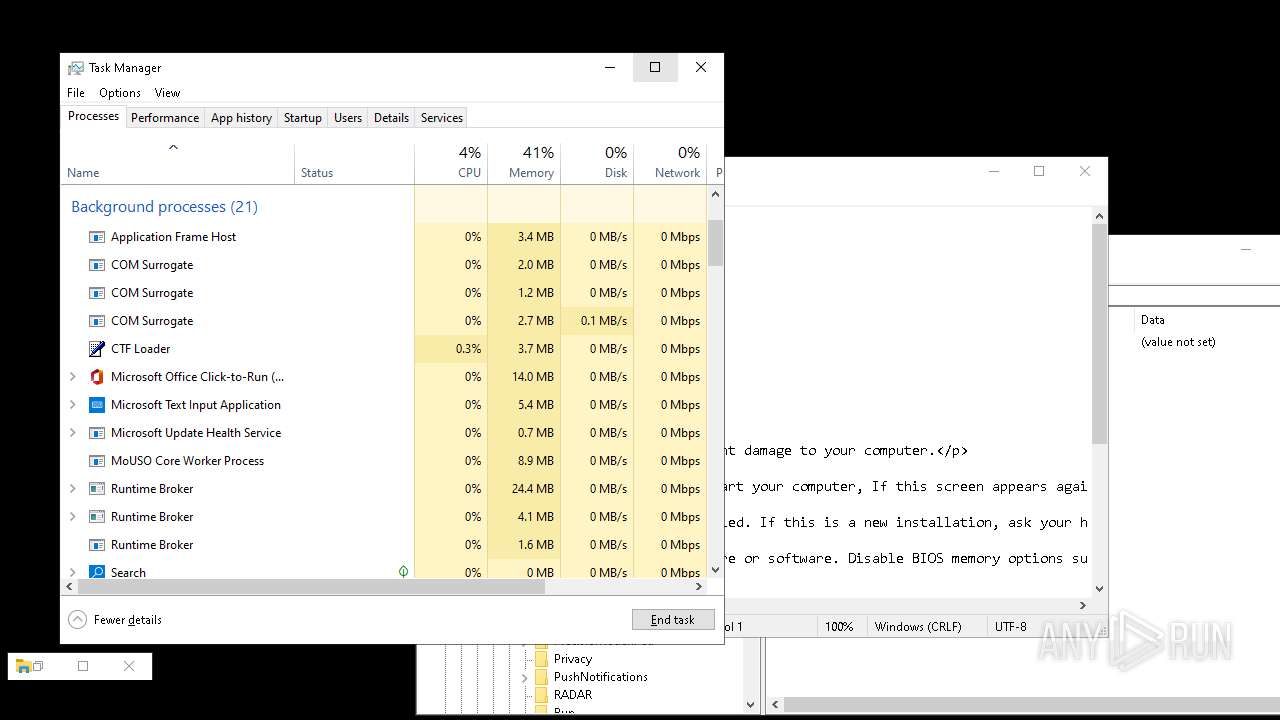
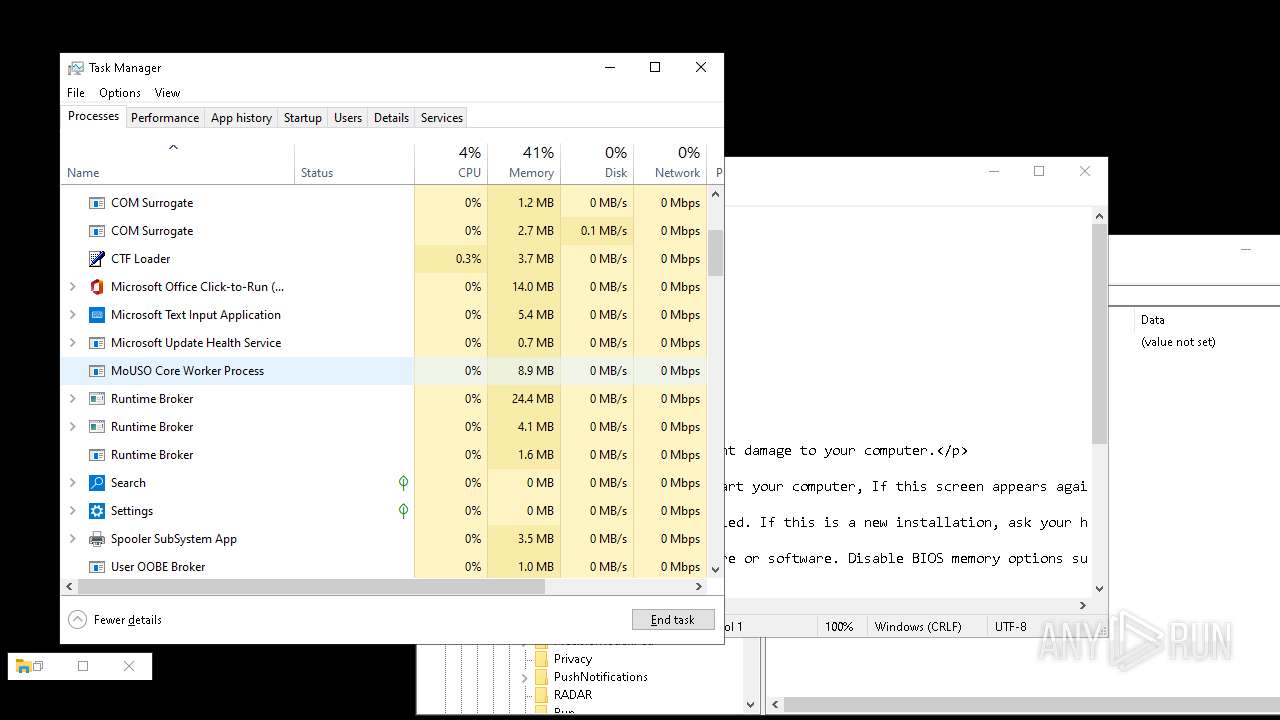
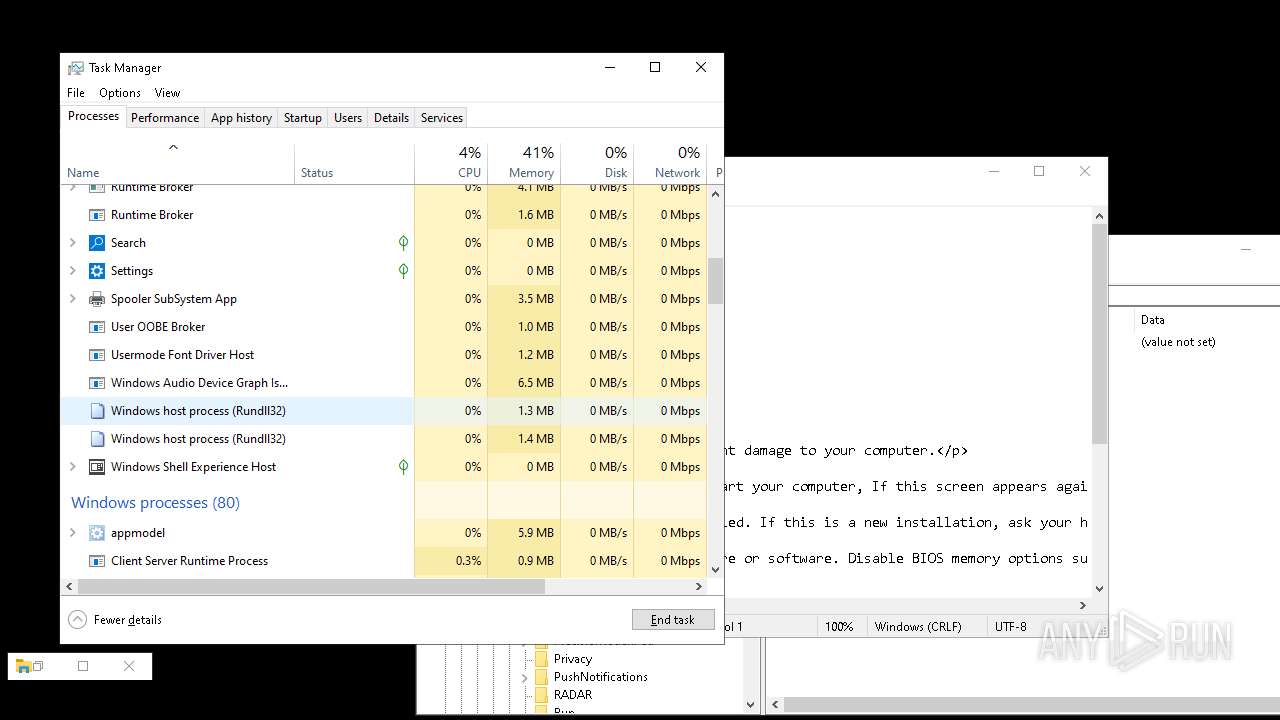
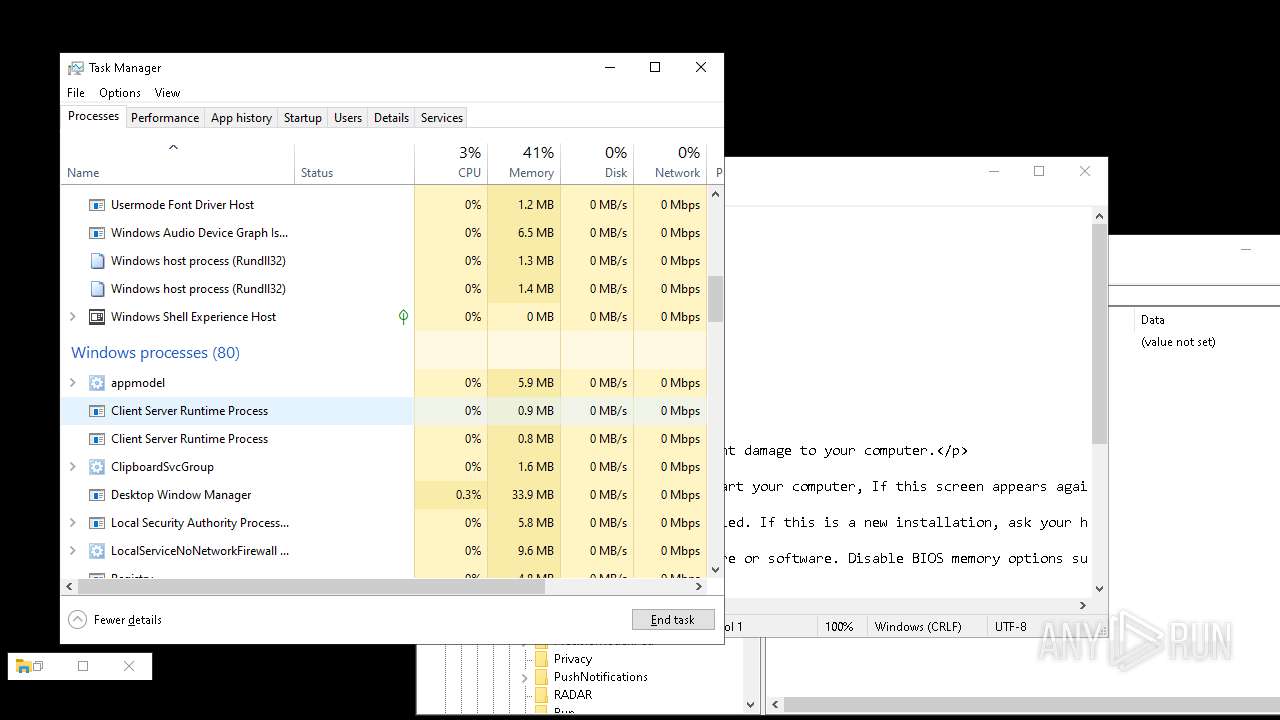
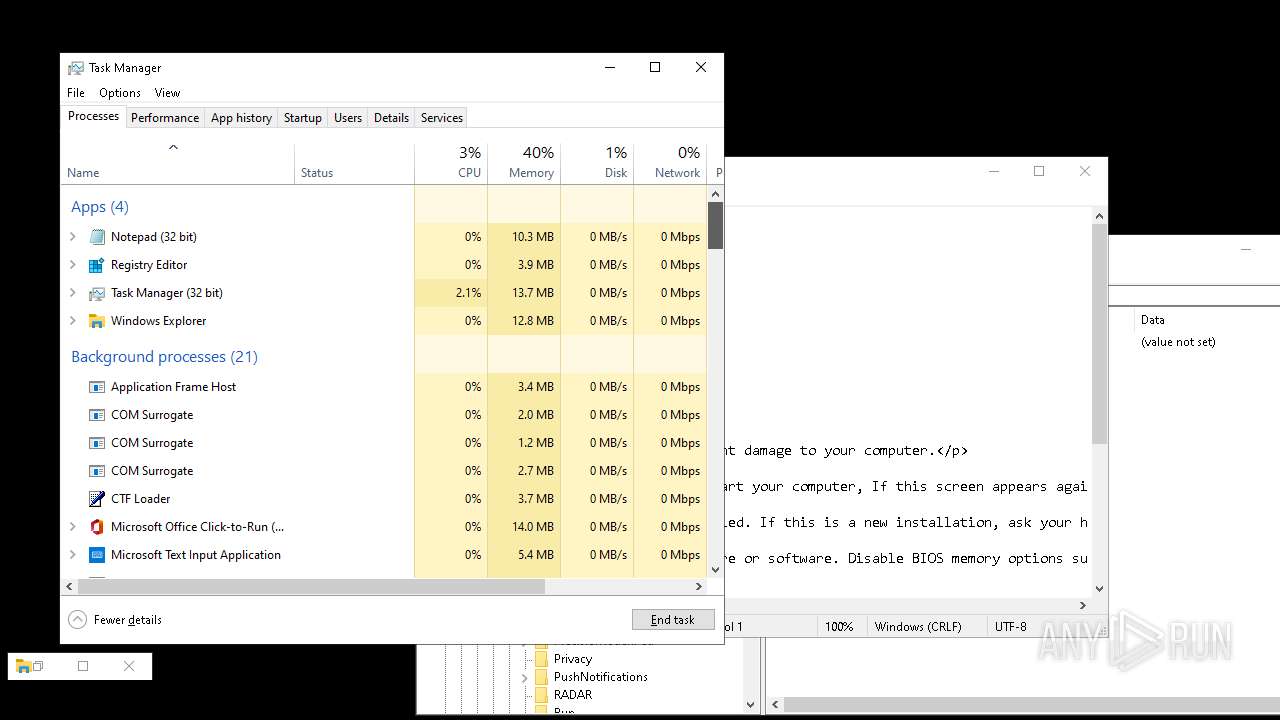
Total processes
271
Monitored processes
123
Malicious processes
3
Suspicious processes
0
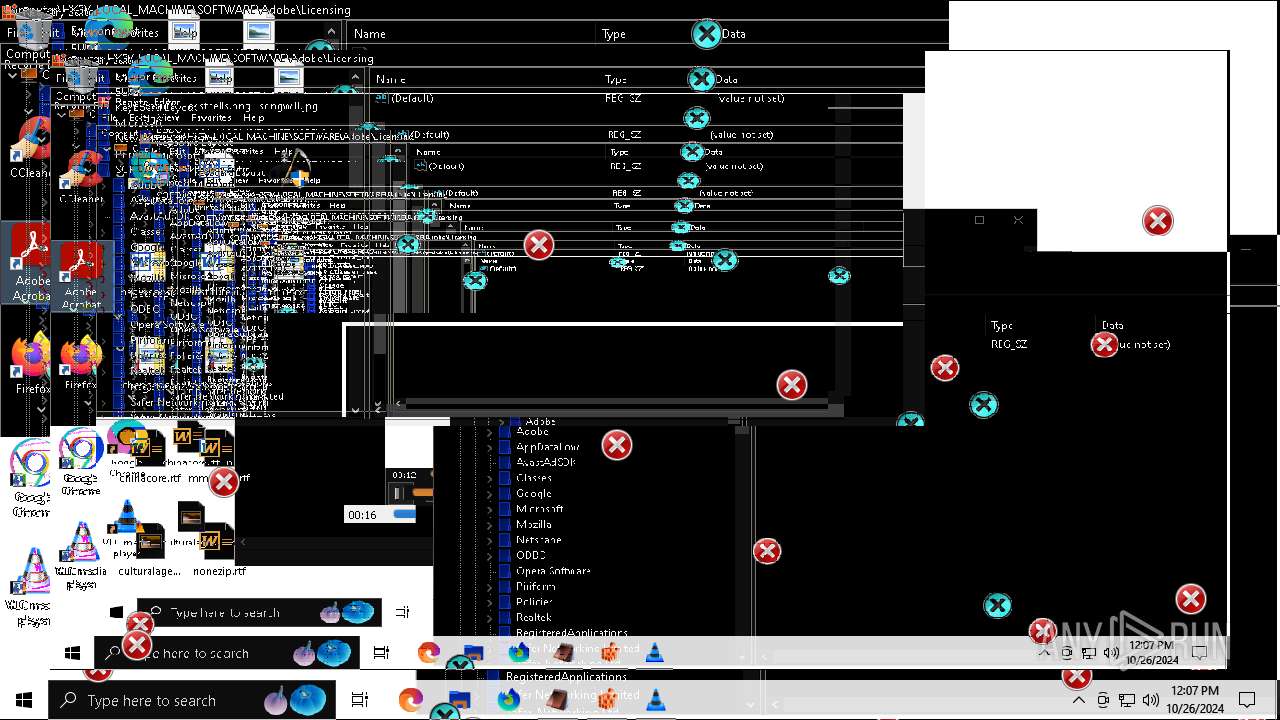
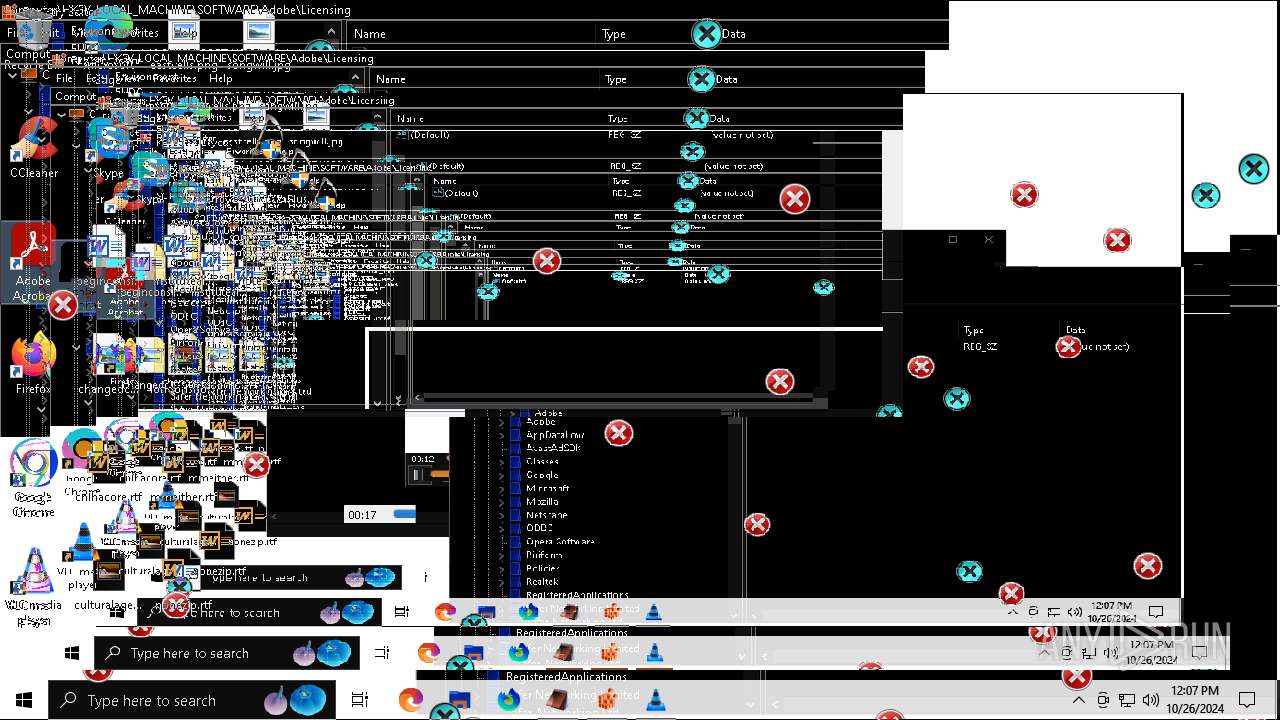
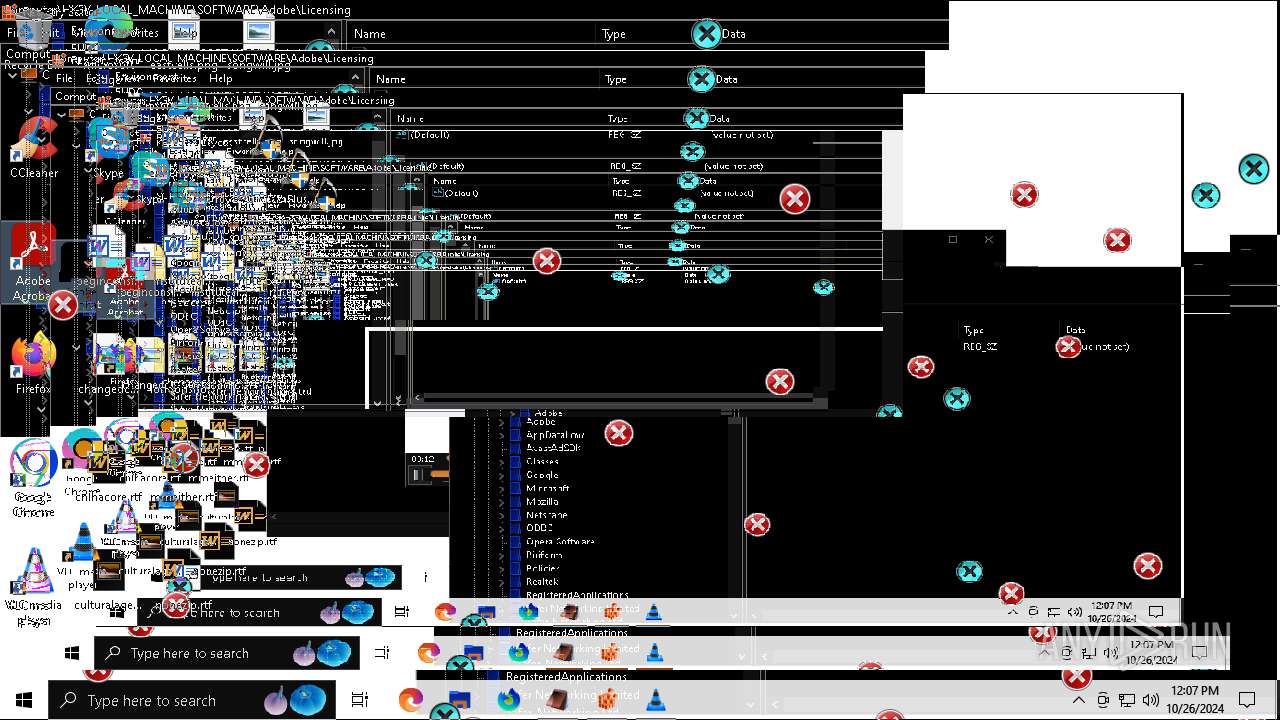
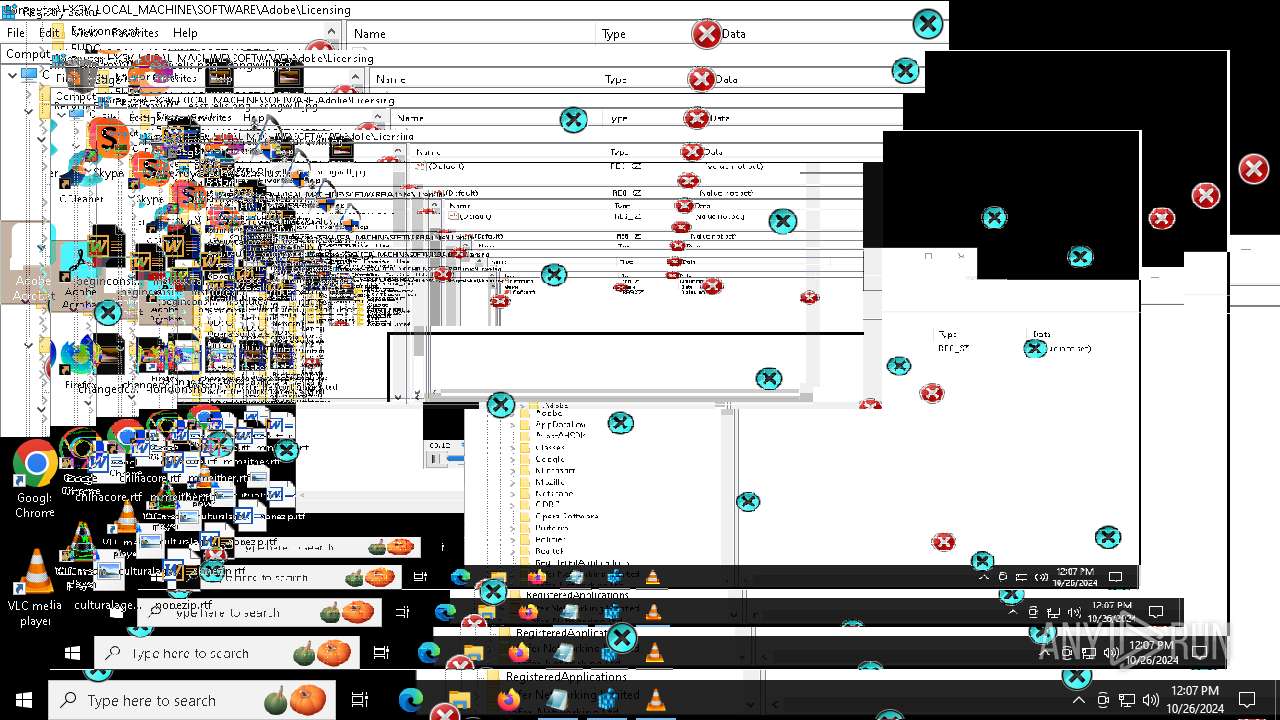
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | inv.exe | C:\Users\admin\AppData\Local\Temp\BC82.tmp\inv.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 616 | "C:\WINDOWS\regedit.exe" | C:\Windows\regedit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 784 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6216 --field-trial-handle=2416,i,10426291150575895777,5433951827364817736,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 916 | scream.exe | C:\Users\admin\AppData\Local\Temp\BC82.tmp\scream.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 944 | taskkill /f /im explorer.exe | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | timeout 5 /nobreak | C:\Windows\SysWOW64\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | MBRKiller.exe | C:\Users\admin\AppData\Local\Temp\BC82.tmp\MBRKiller.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1184 | scream.exe | C:\Users\admin\AppData\Local\Temp\BC82.tmp\scream.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1252 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=5164 --field-trial-handle=2416,i,10426291150575895777,5433951827364817736,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1792 | scream.exe | C:\Users\admin\AppData\Local\Temp\BC82.tmp\scream.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
Total events
32 317
Read events
32 150
Write events
140
Delete events
27
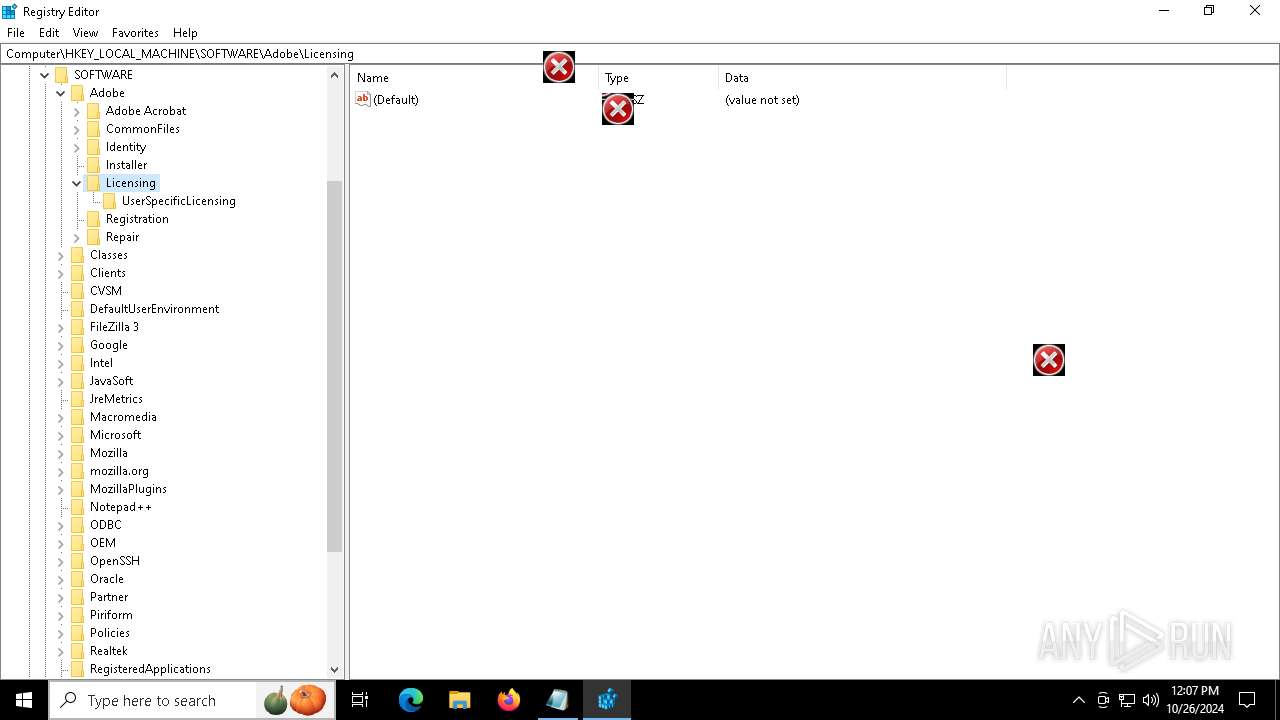
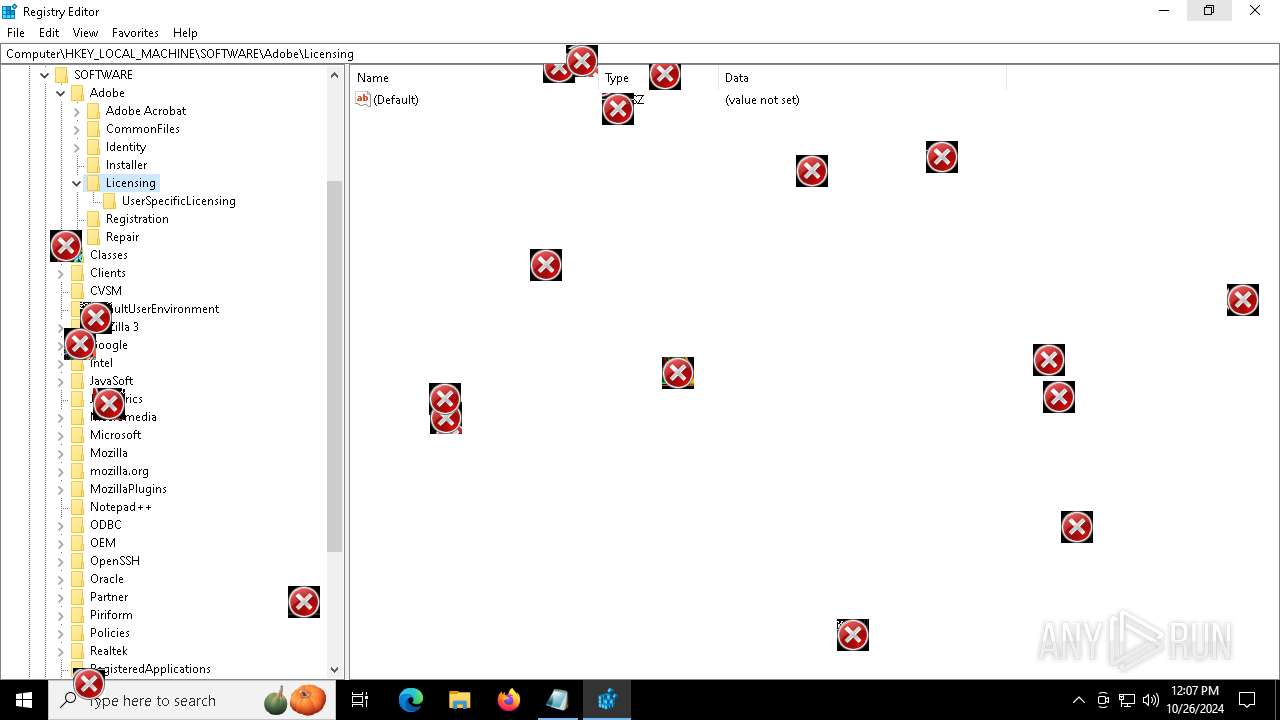
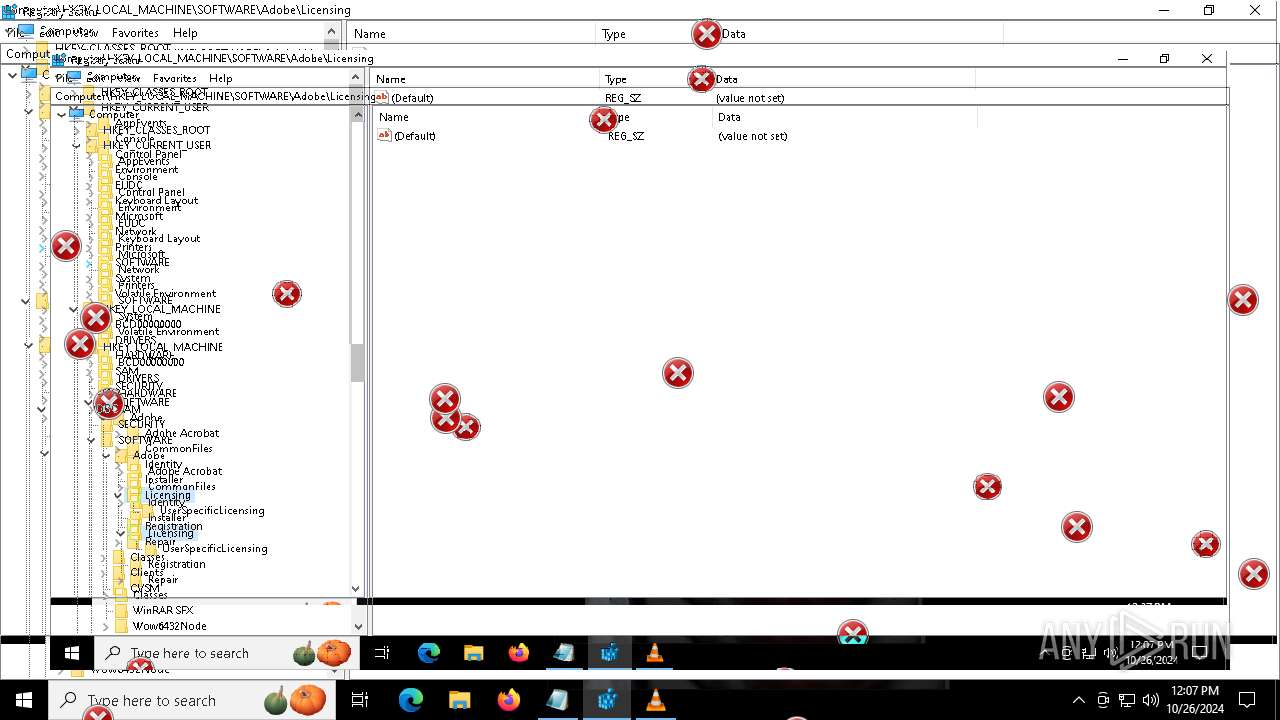
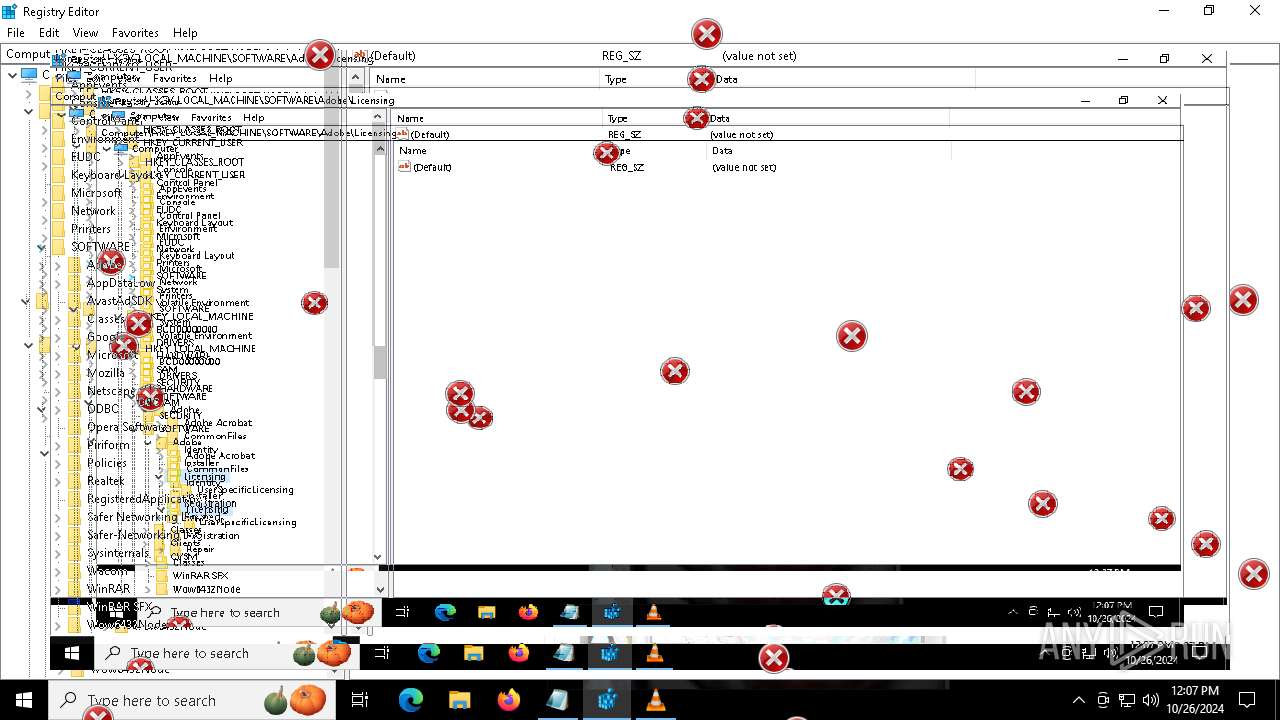
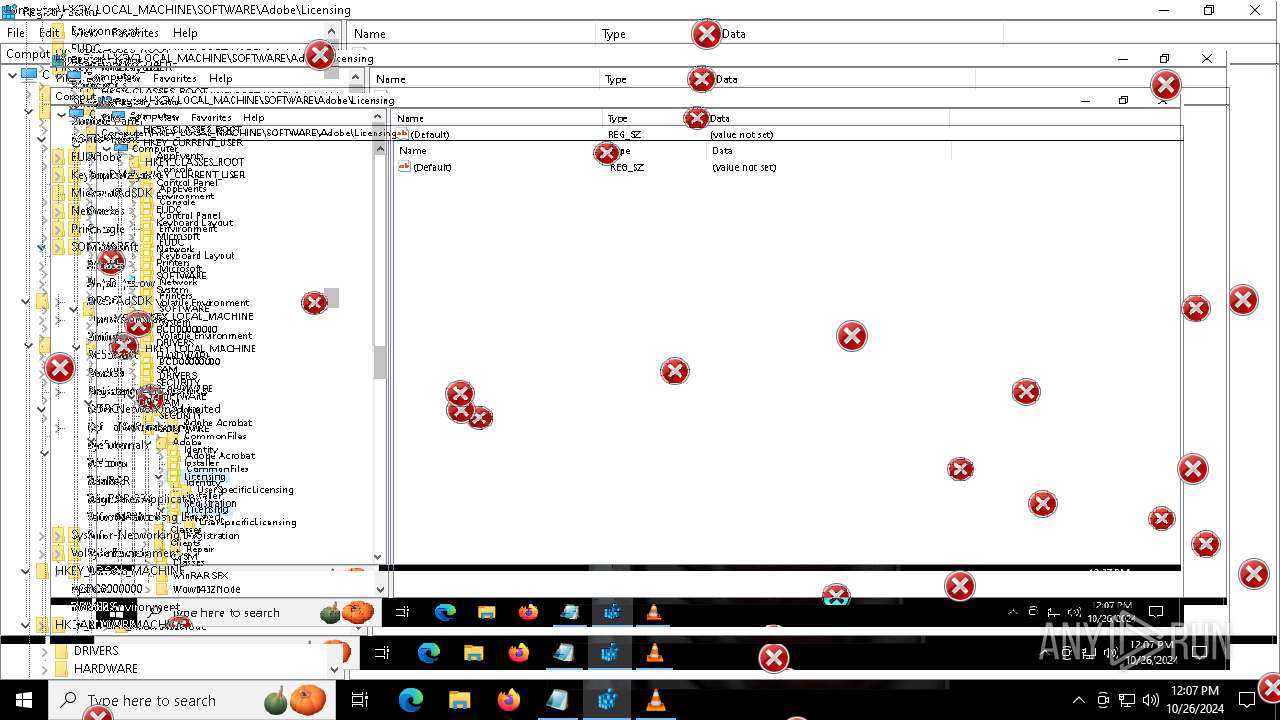
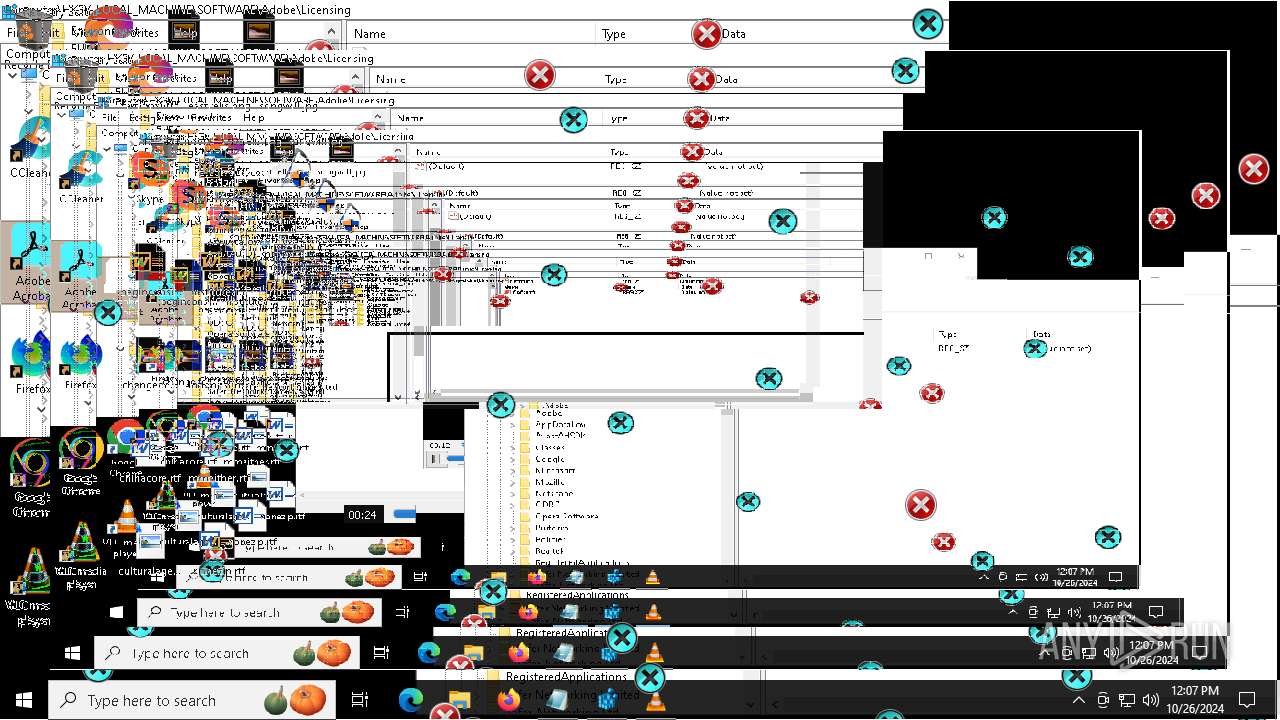
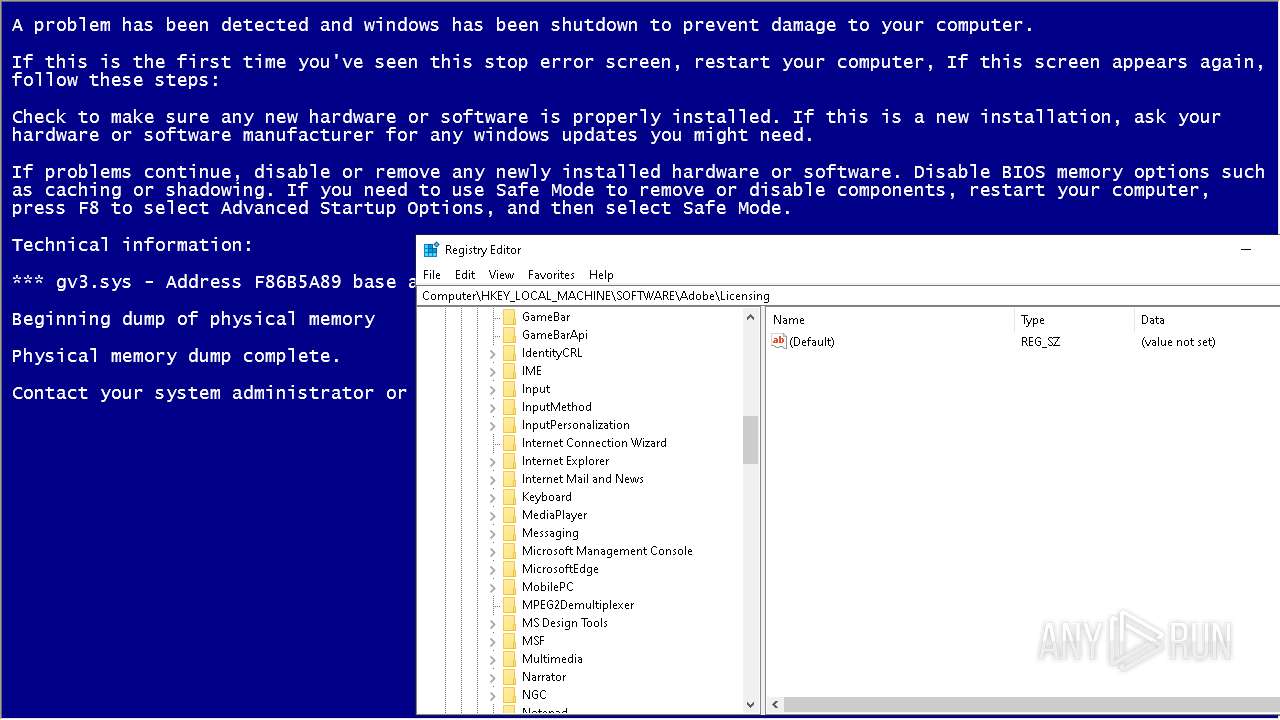
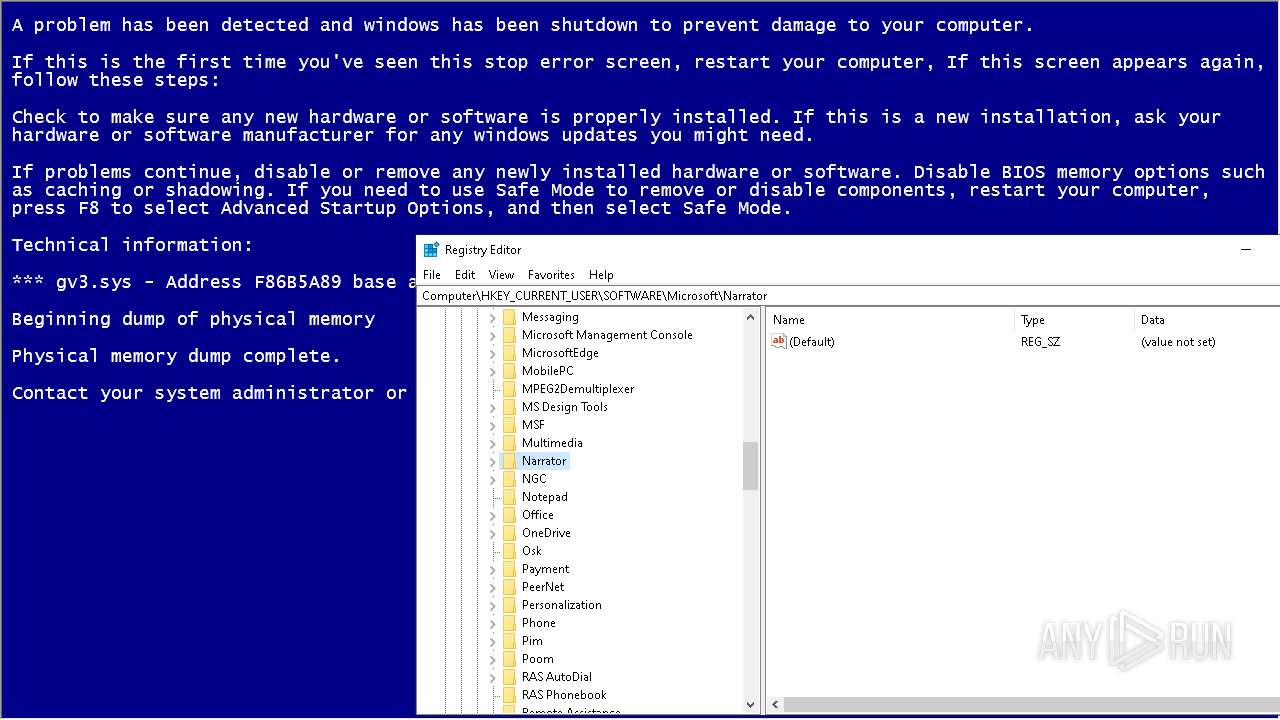
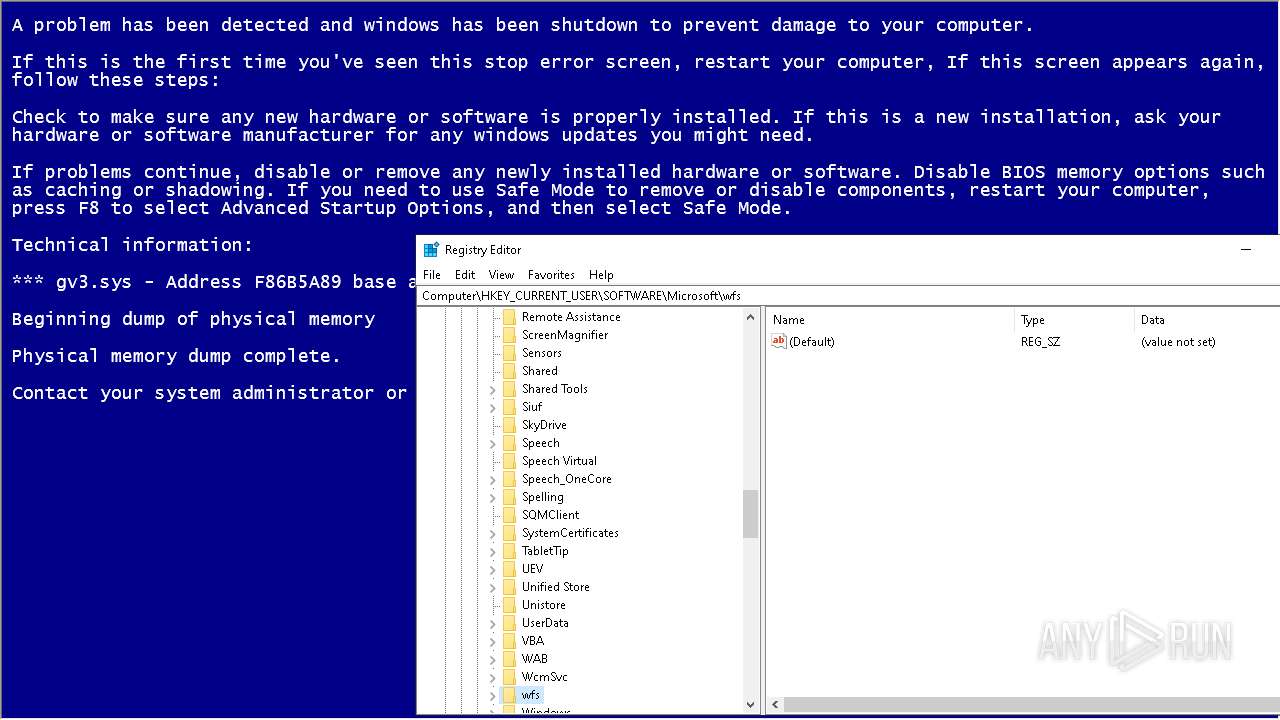
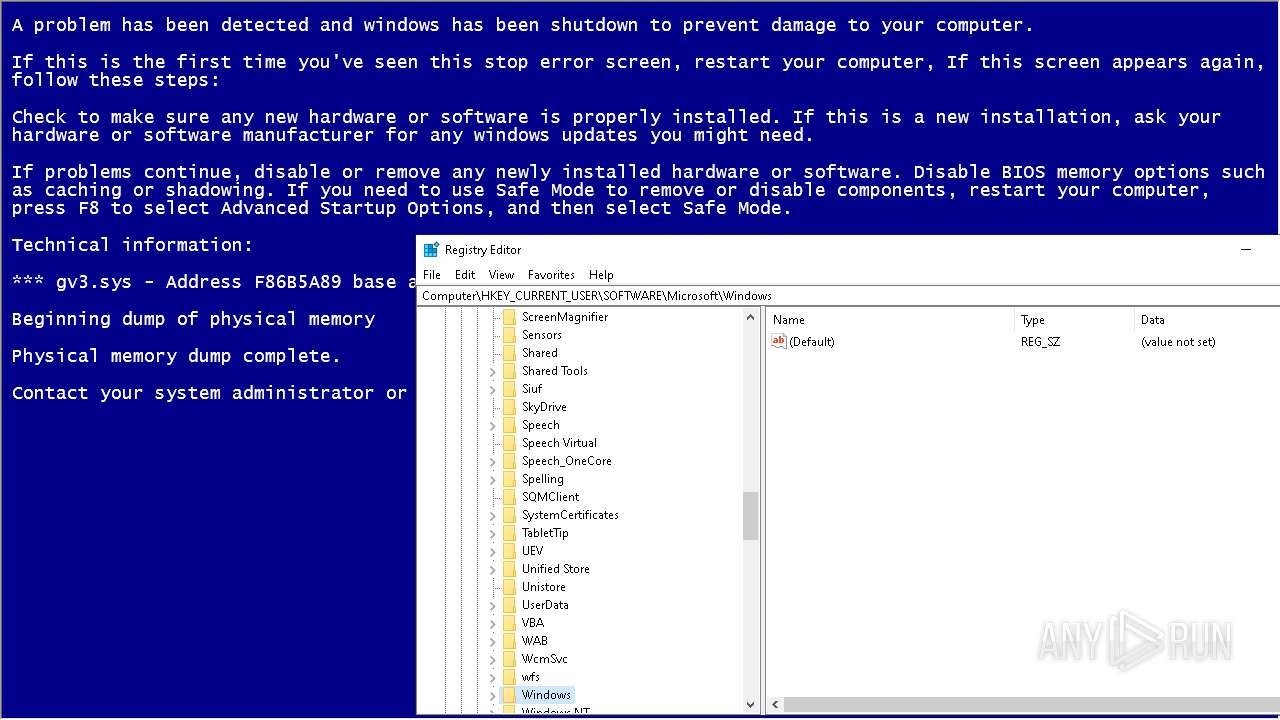
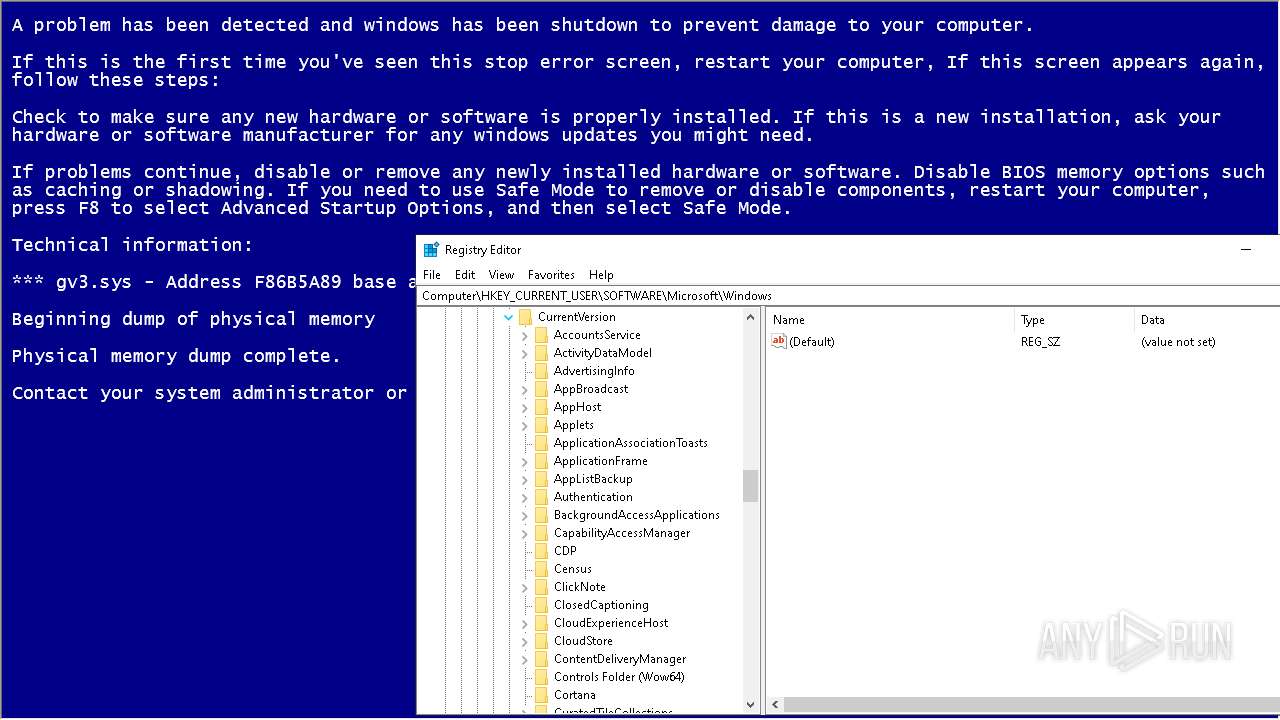
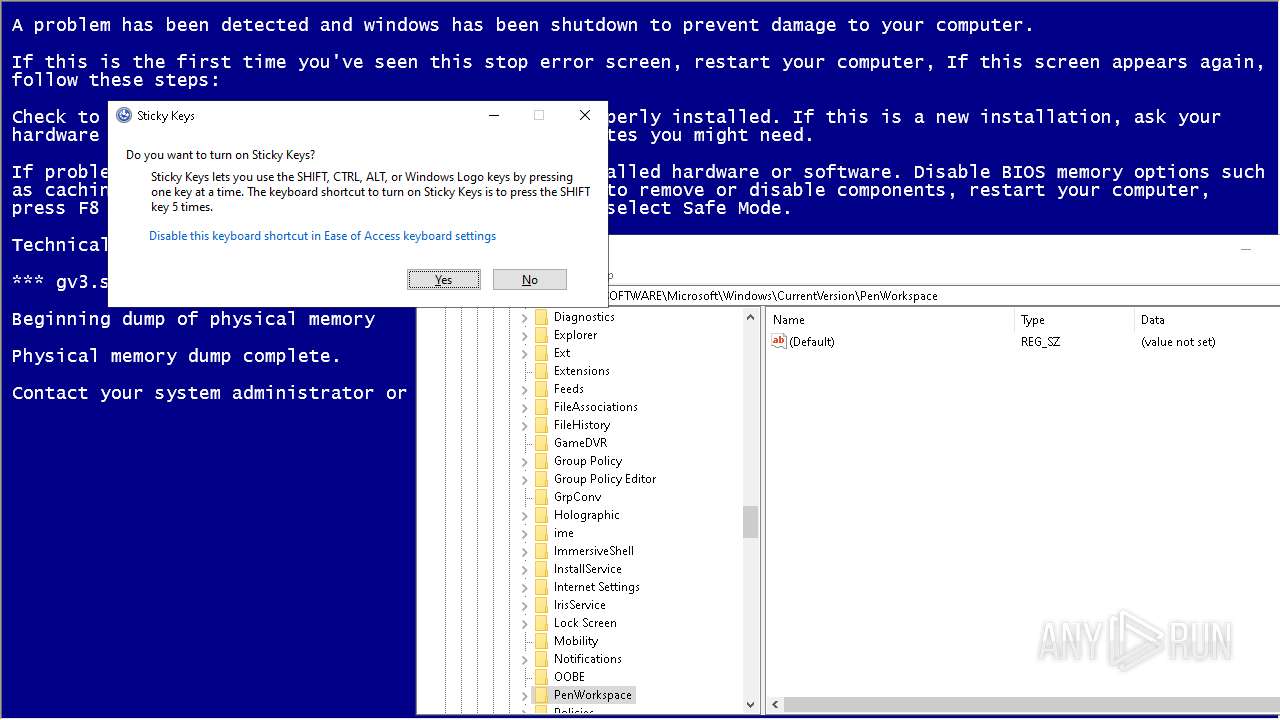
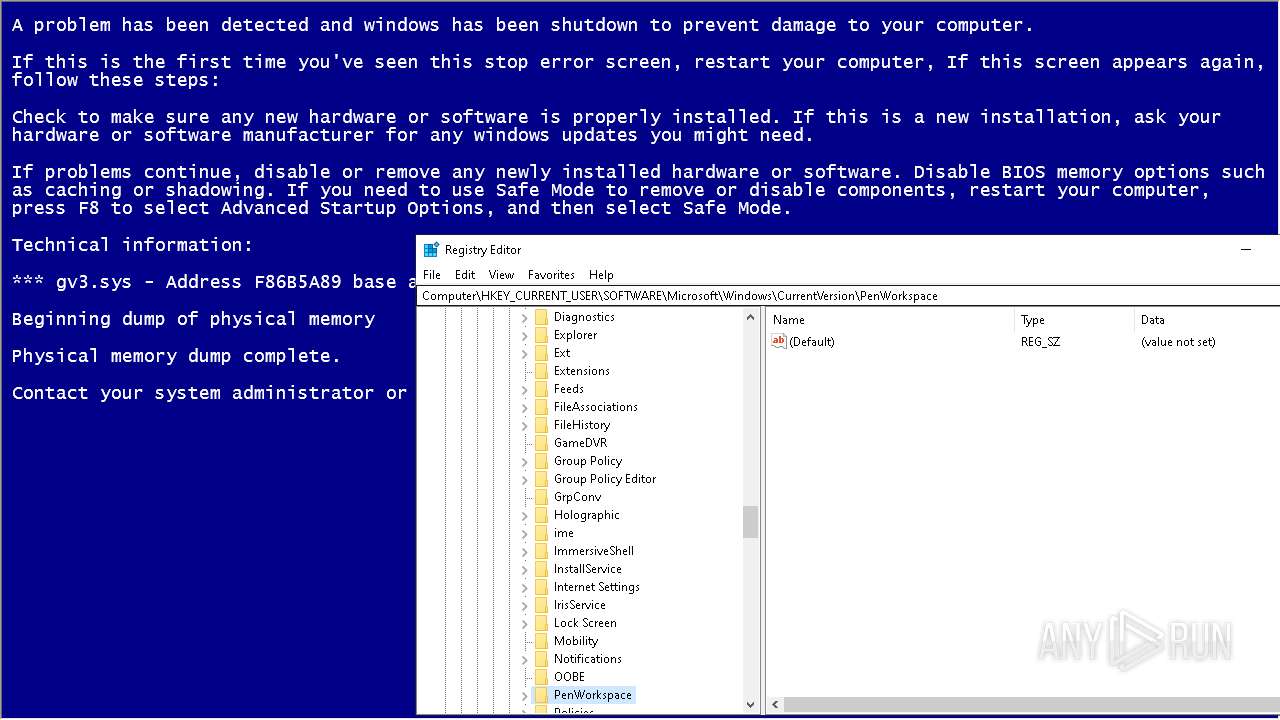
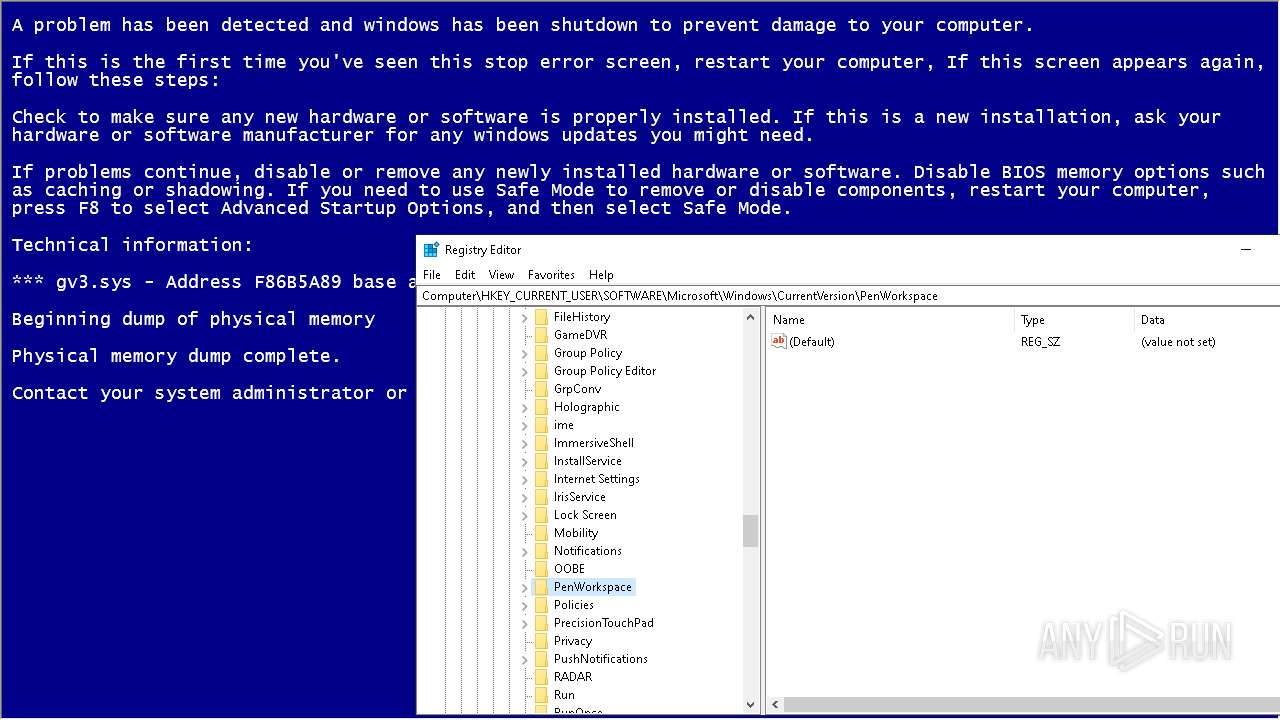
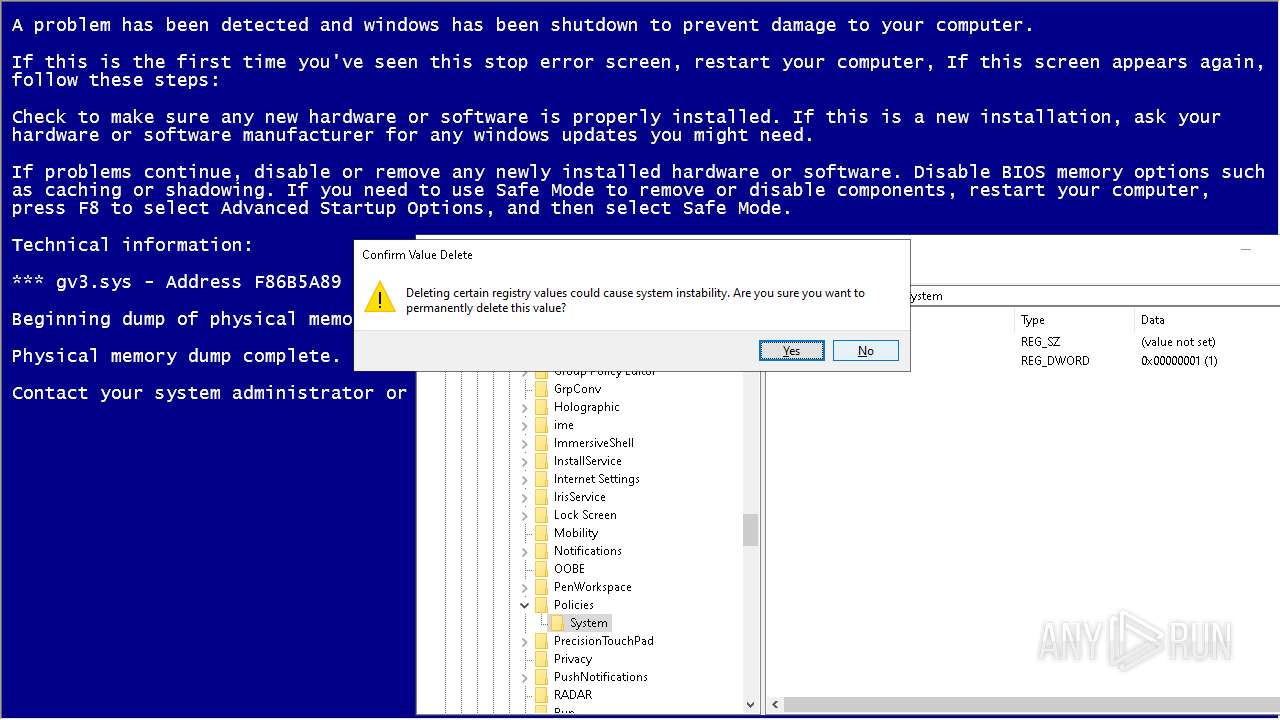
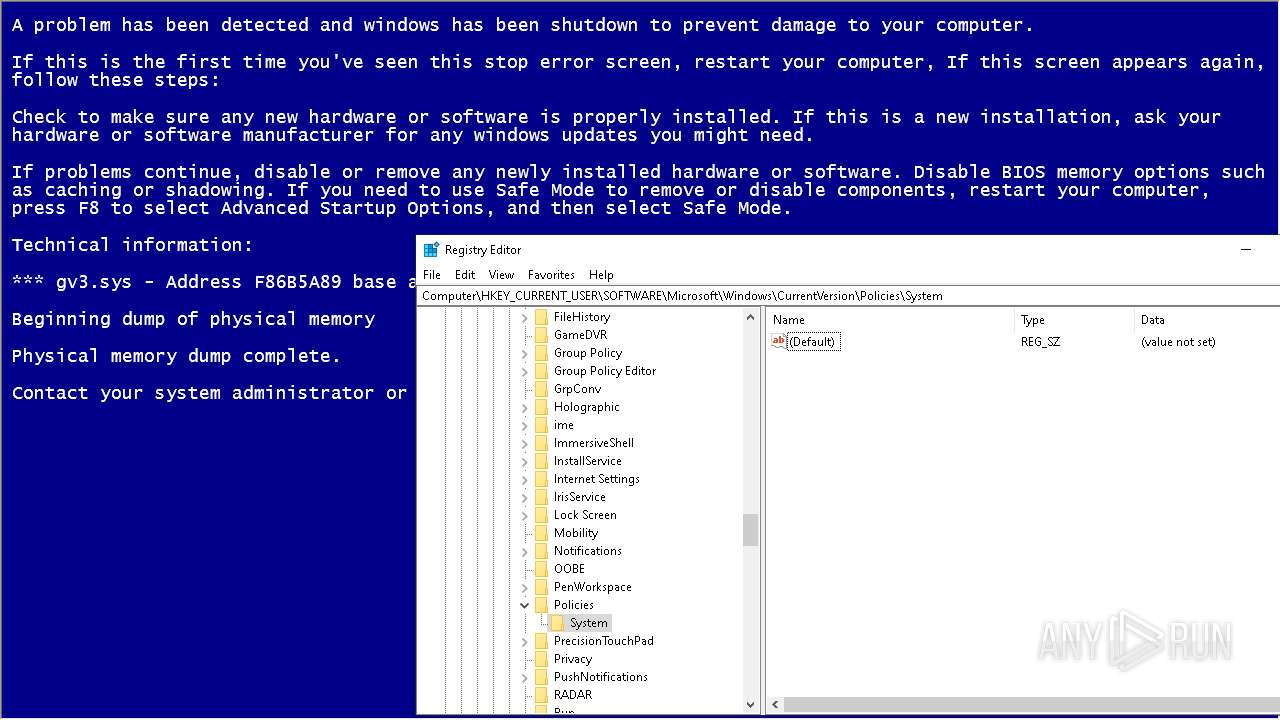
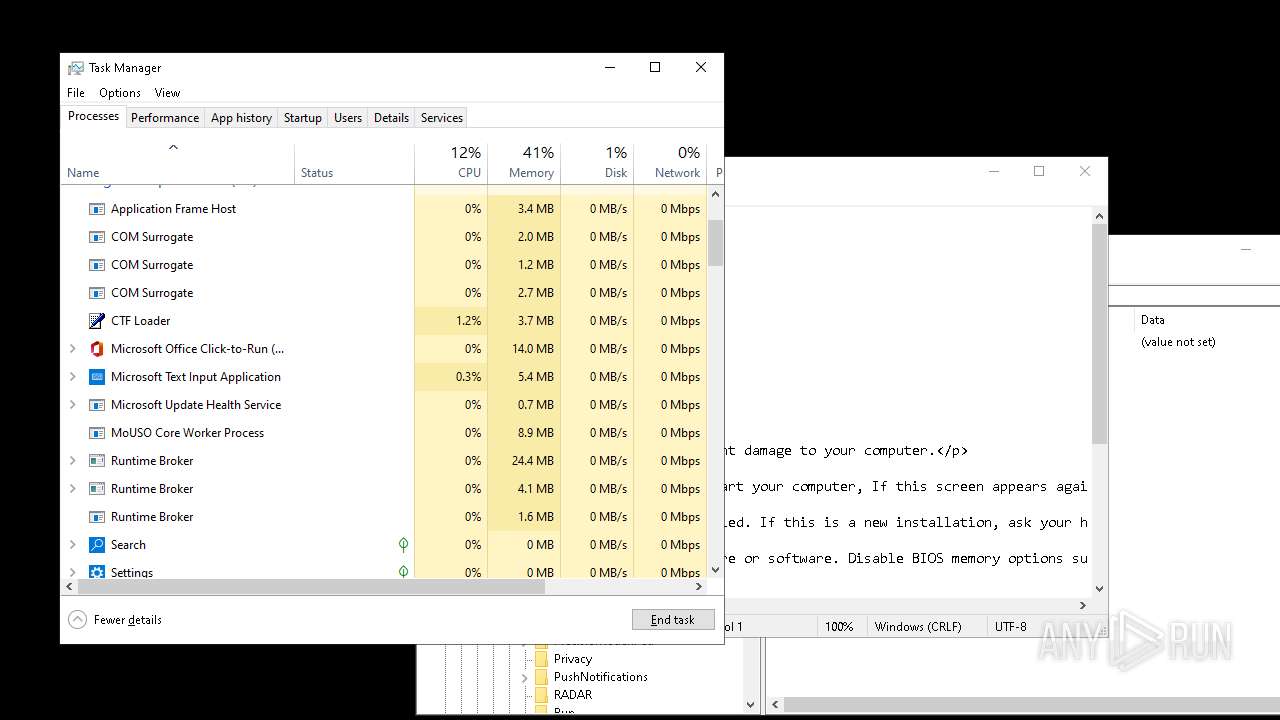
Modification events
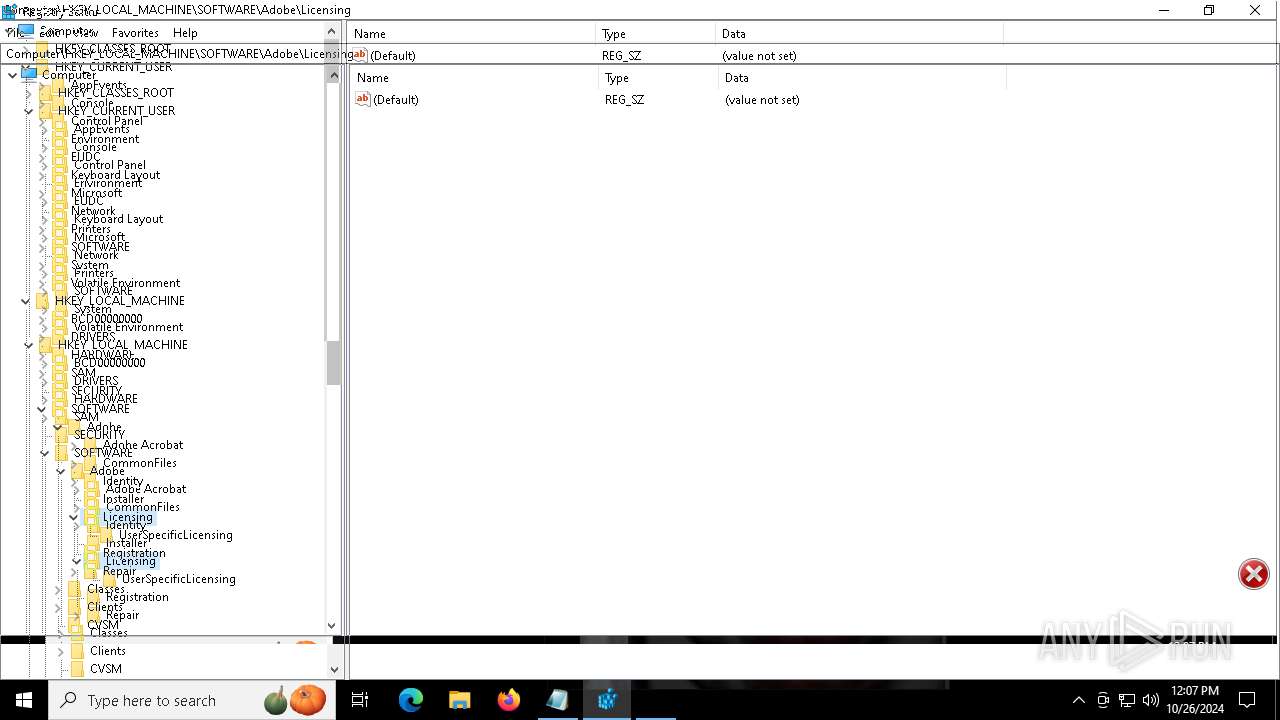
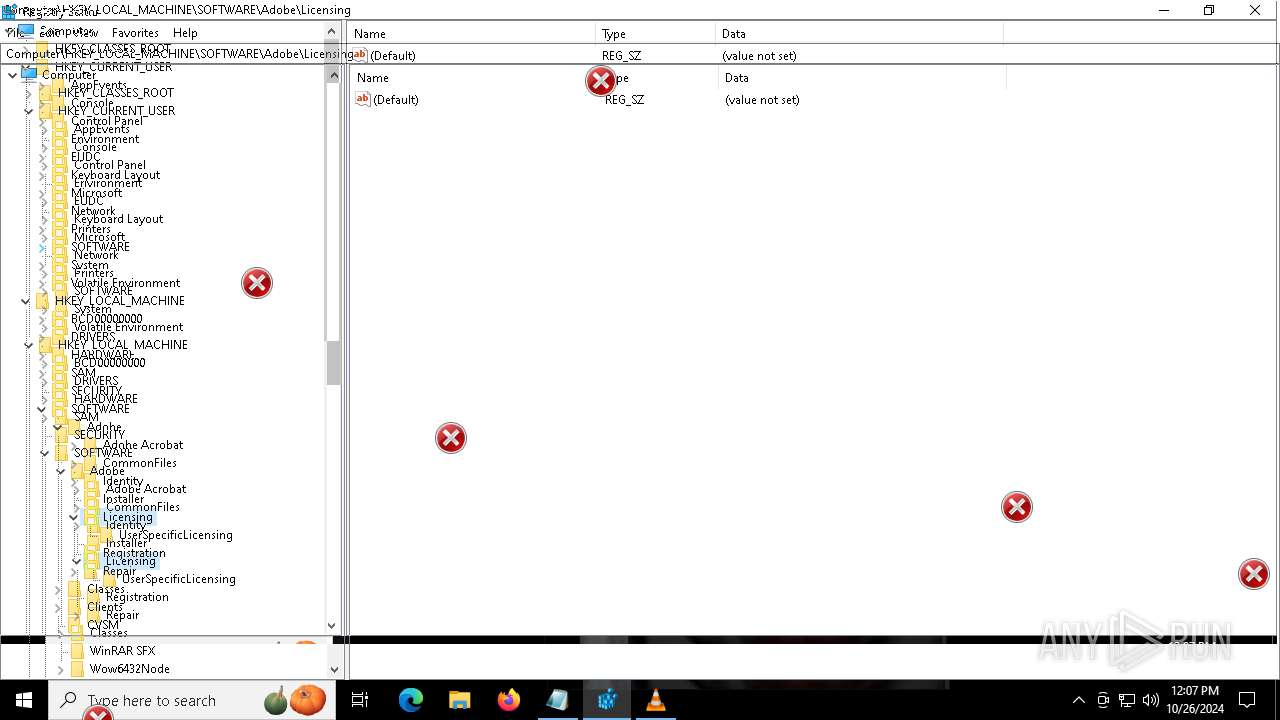
| (PID) Process: | (6340) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
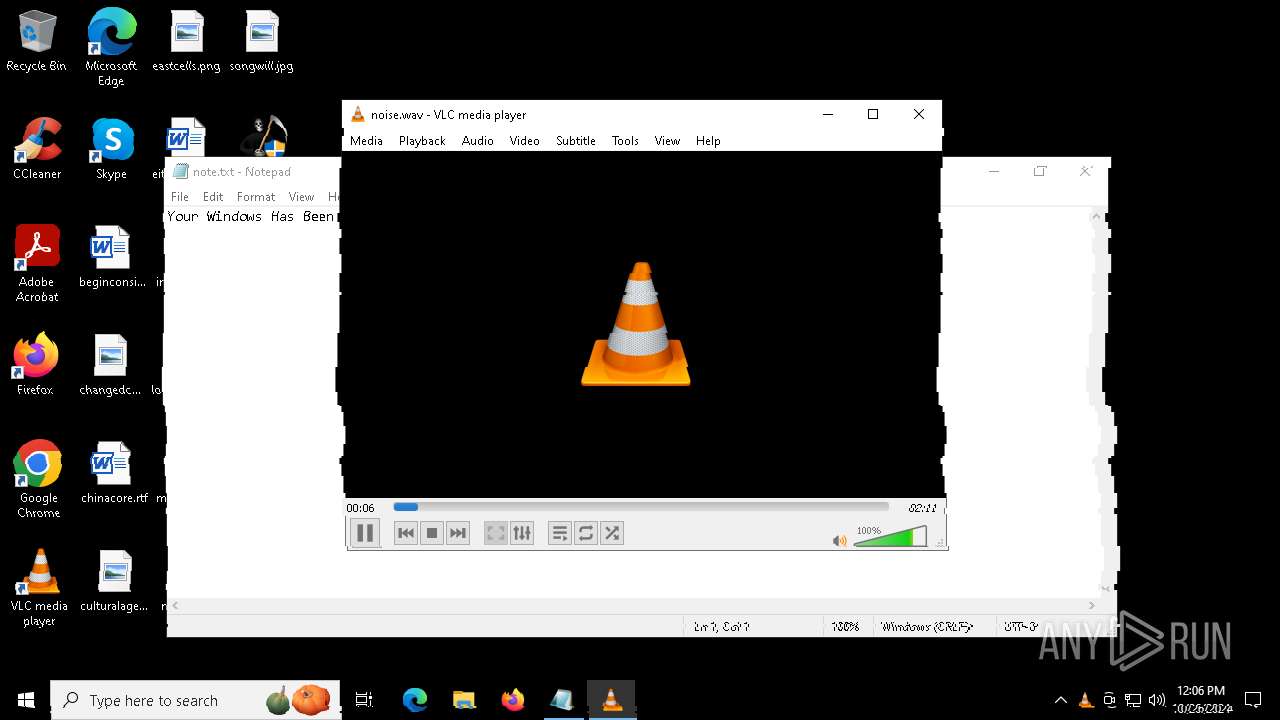
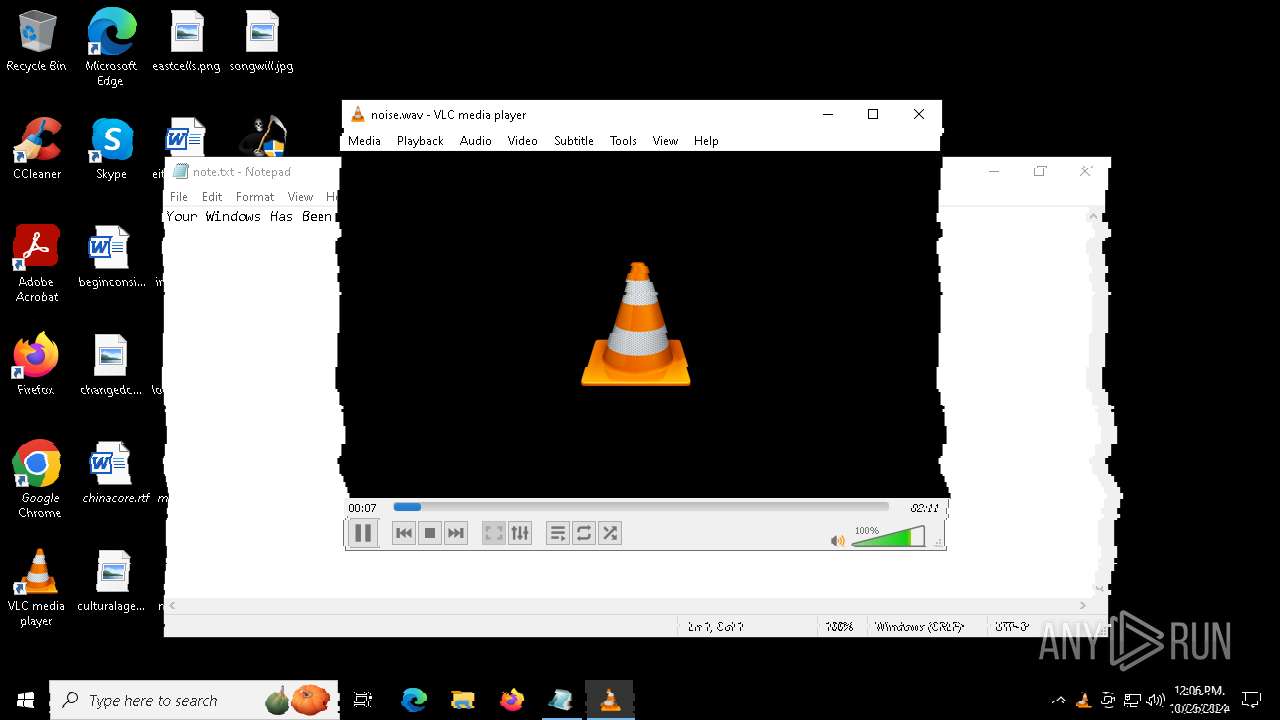
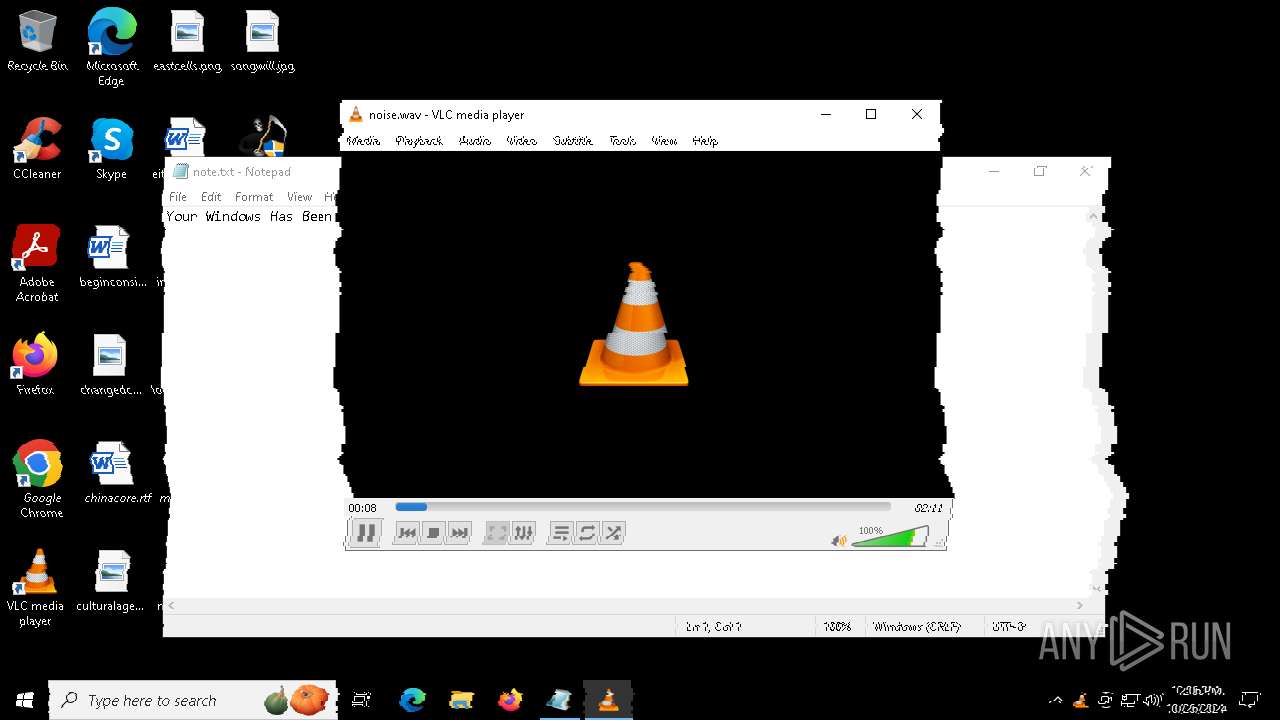
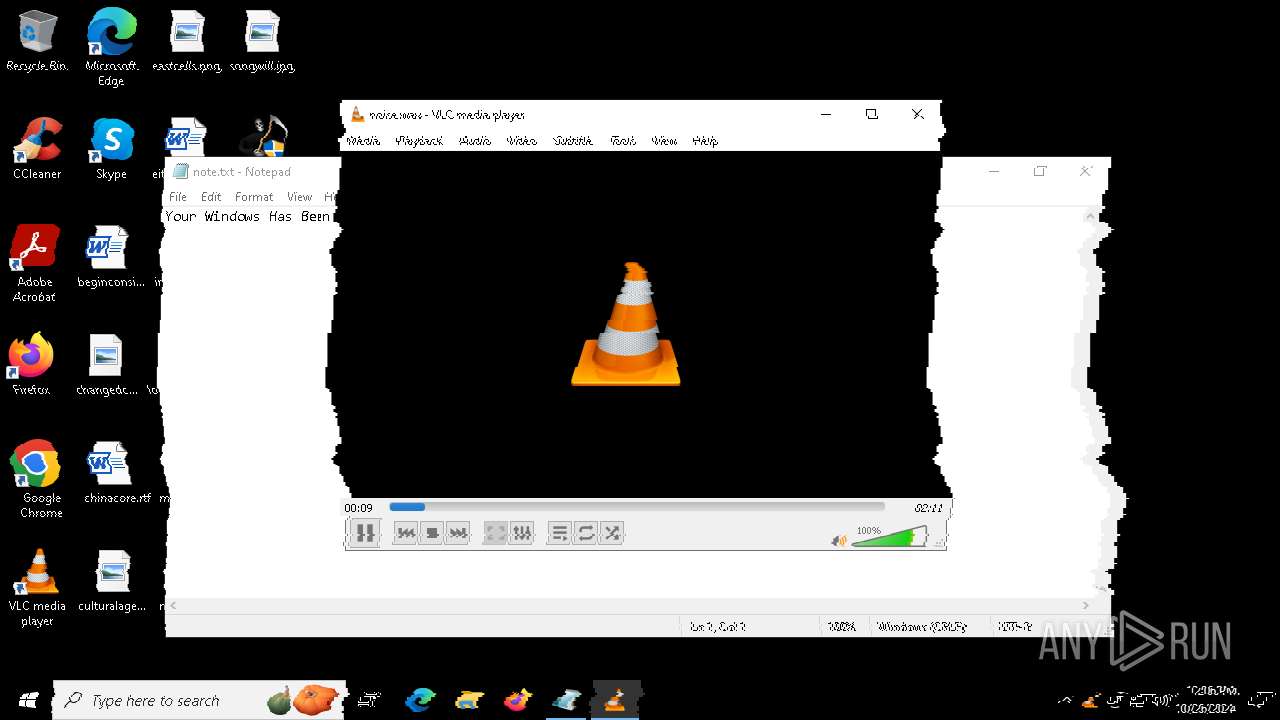
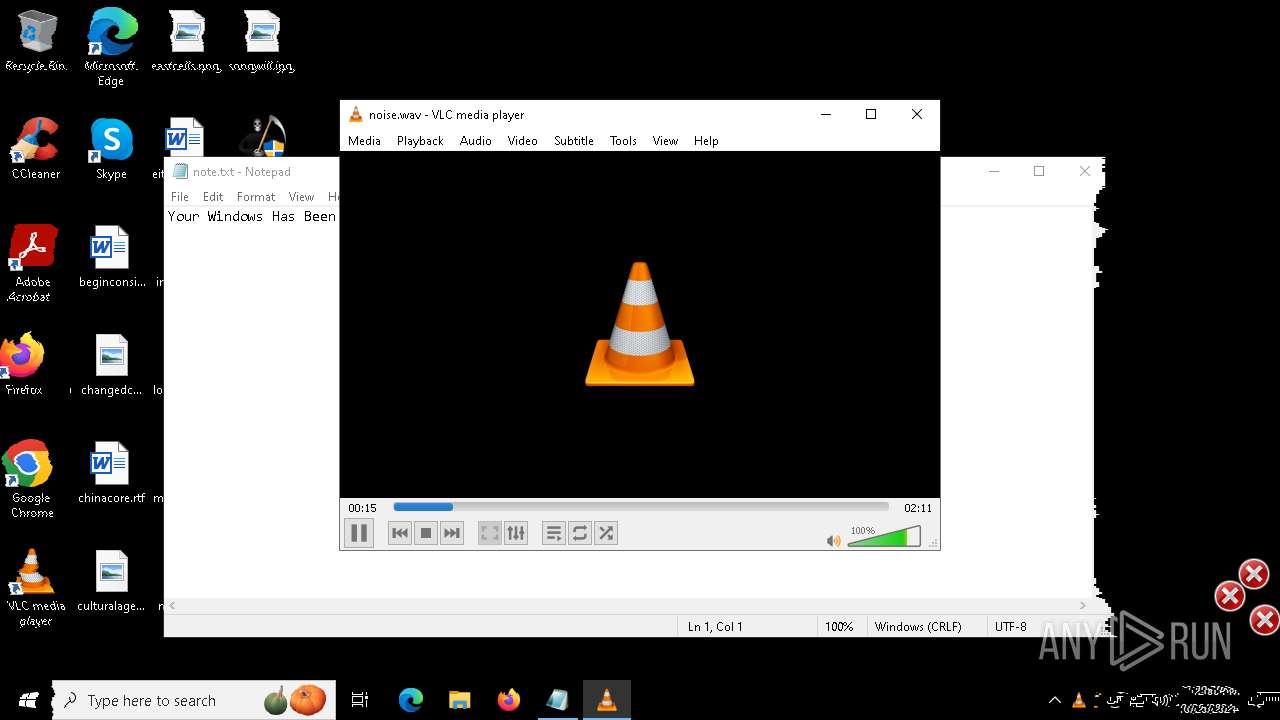
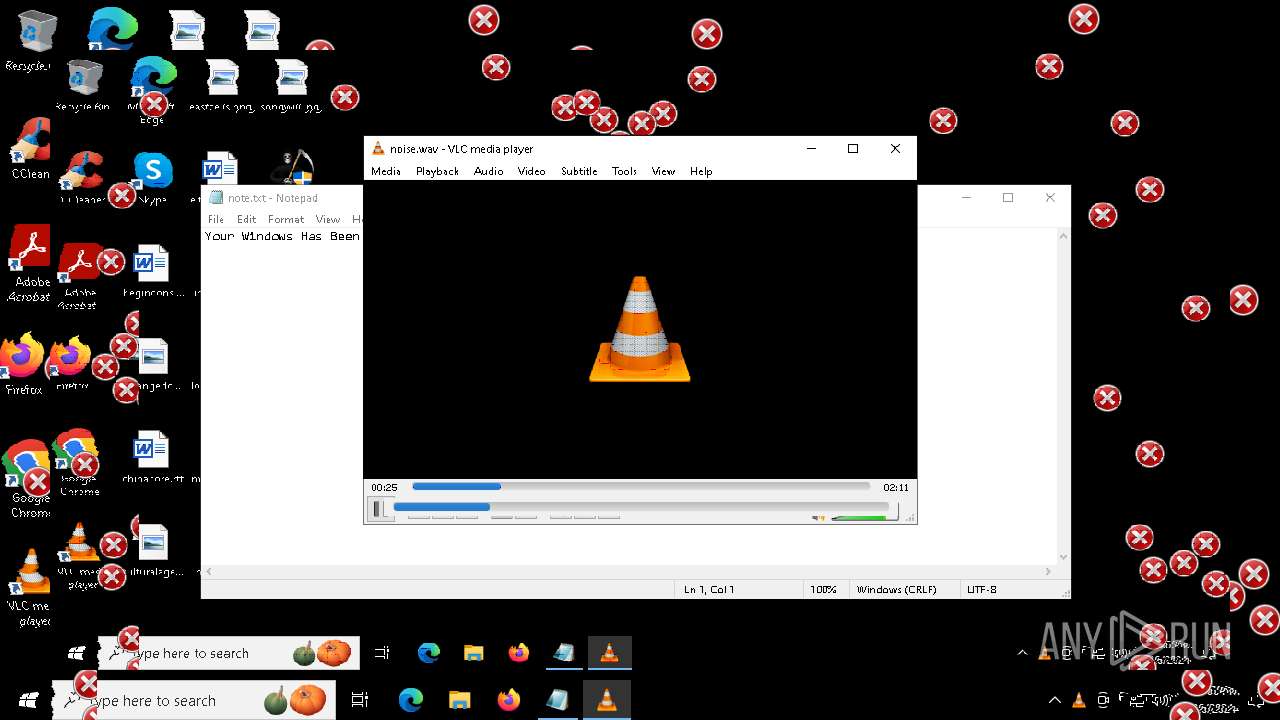
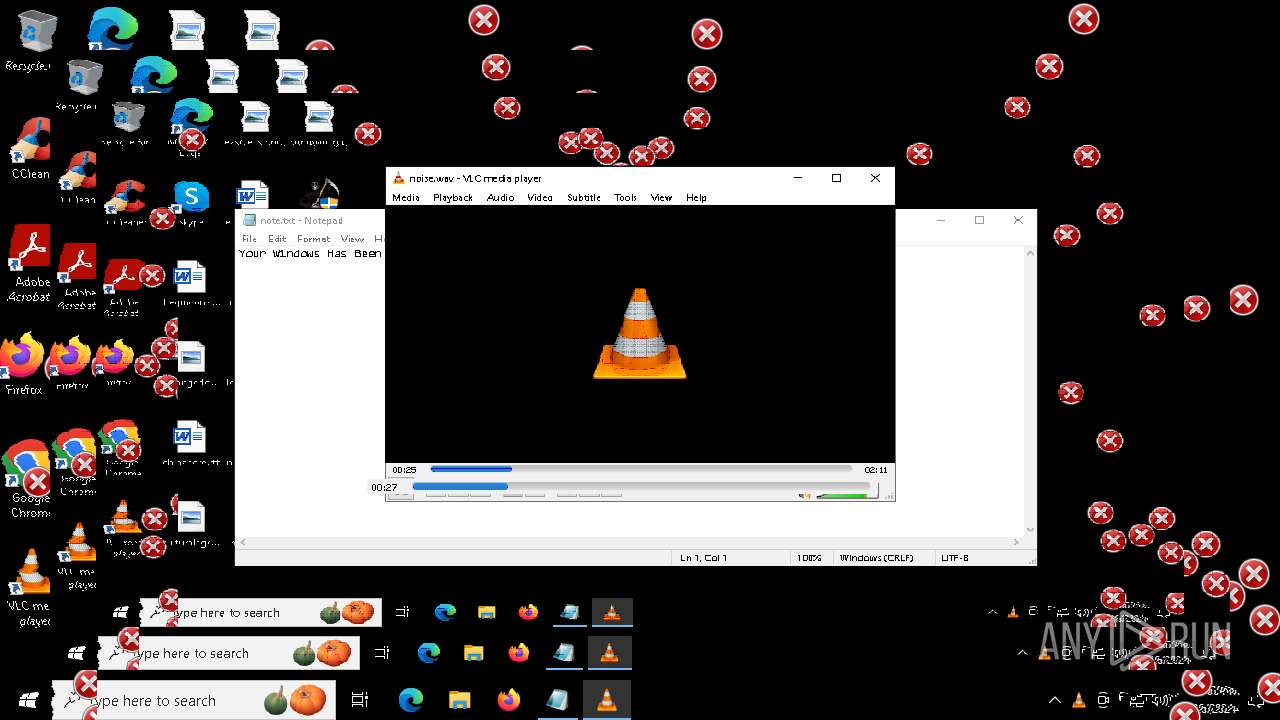
| (PID) Process: | (2648) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.wav\OpenWithProgids |
| Operation: | write | Name: | VLC.wav |
Value: | |||
| (PID) Process: | (2648) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {E46787A1-4629-4423-A693-BE1F003B2742} {886D8EEB-8CF2-4446-8D02-CDBA1DBDCF99} 0xFFFF |
Value: 0100000000000000182D397B9F27DB01 | |||
| (PID) Process: | (2648) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.txt\OpenWithProgids |
| Operation: | write | Name: | txtfile |
Value: | |||
| (PID) Process: | (1184) MBRKiller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Windows Update |
Value: | |||
| (PID) Process: | (1184) MBRKiller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Update |
Value: C:\Users\admin\AppData\Local\Temp\BC82.tmp\MBRKiller.exe | |||
| (PID) Process: | (1184) MBRKiller.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Windows Update |
Value: C:\Users\admin\AppData\Local\Temp\BC82.tmp\MBRKiller.exe | |||
| (PID) Process: | (6500) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | delete value | Name: | WallPaper |
Value: fnaf.bmp | |||
| (PID) Process: | (2648) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.mp4\OpenWithProgids |
| Operation: | write | Name: | VLC.mp4 |
Value: | |||
| (PID) Process: | (2648) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {F81B1B56-7613-4EE4-BC05-1FAB5DE5C07E} {886D8EEB-8CF2-4446-8D02-CDBA1DBDCF99} 0xFFFF |
Value: 010000000000000072C4CEBB9F27DB01 | |||
Executable files
15
Suspicious files
29
Text files
44
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6668 | DeathPlus.exe | C:\Users\admin\AppData\Local\Temp\BC82.tmp\fnaf.bmp | — | |
MD5:— | SHA256:— | |||
| 6668 | DeathPlus.exe | C:\Users\admin\AppData\Local\Temp\BC82.tmp\clown.bmp | — | |
MD5:— | SHA256:— | |||
| 1184 | MBRKiller.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 2928 | vlc.exe | — | ||
MD5:— | SHA256:— | |||
| 6668 | DeathPlus.exe | C:\Users\admin\AppData\Local\Temp\BC82.tmp\DeathPlus.bat | text | |
MD5:892F11B37E59D1BB0D8ACCD66402E12D | SHA256:AB473B1B6AE32BCB465DDDBD0A8079A12611BD7A2AF5DF45367A0AA6764E3E8A | |||
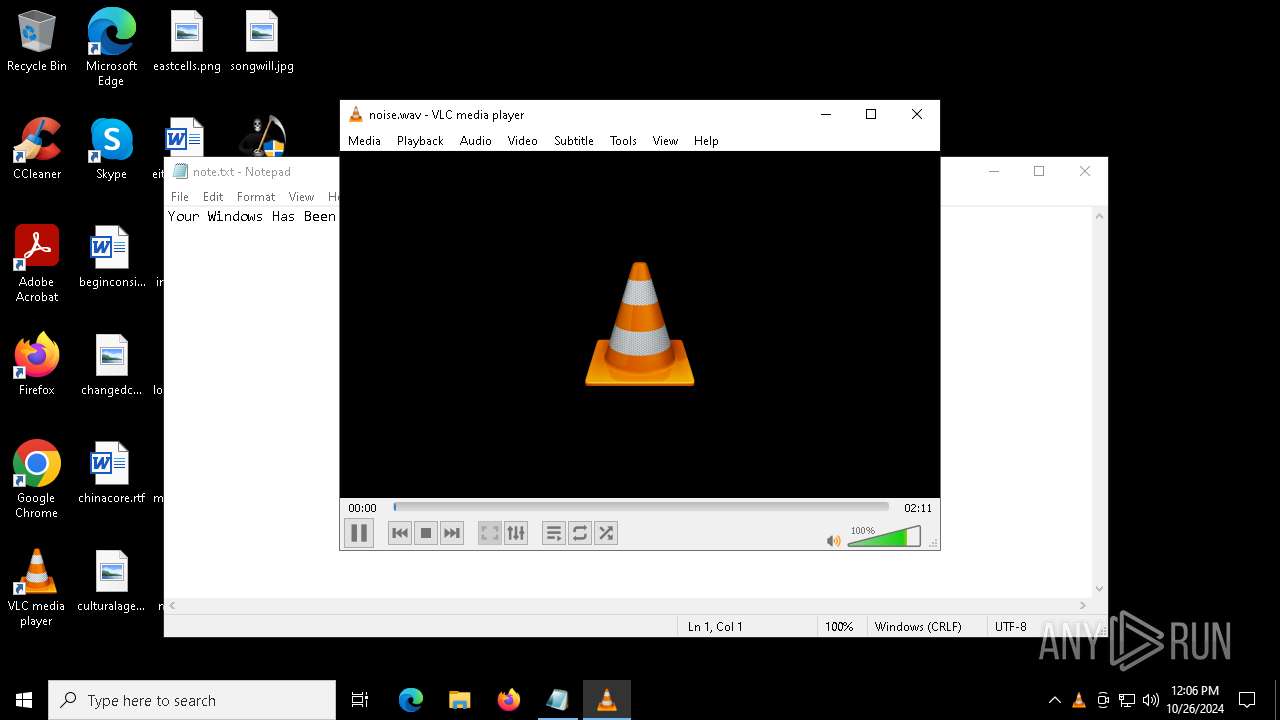
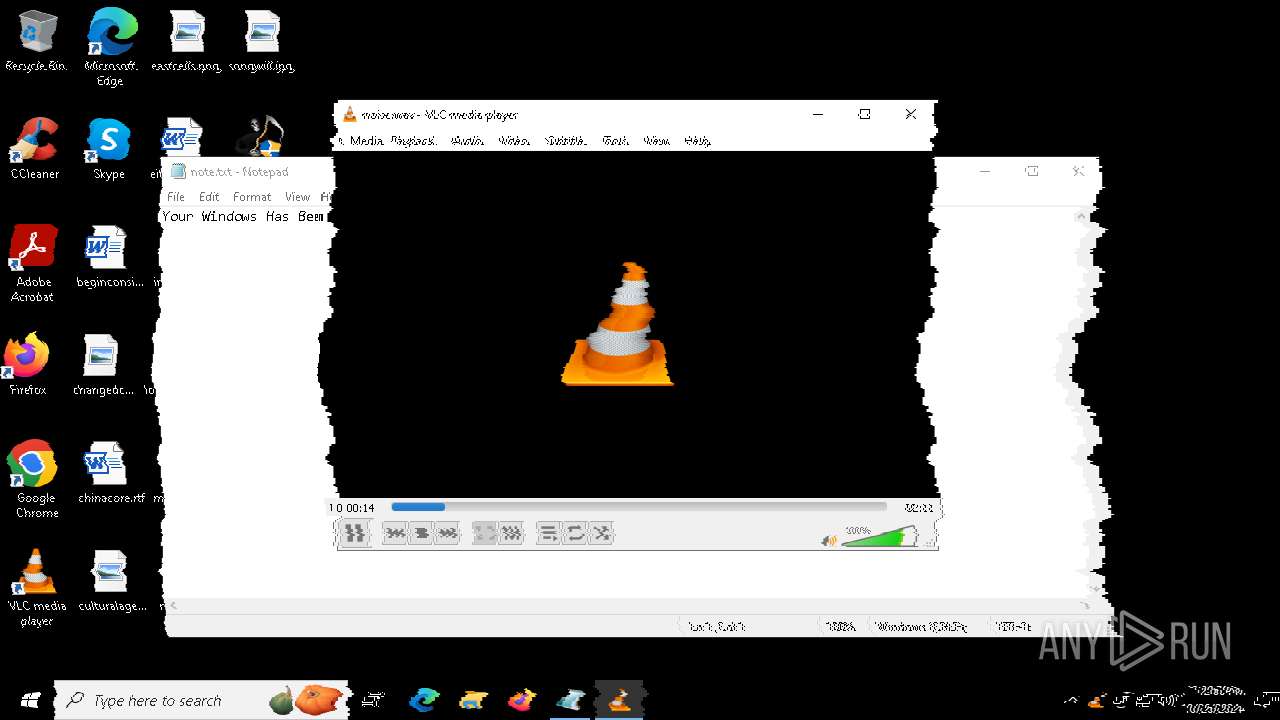
| 6668 | DeathPlus.exe | C:\Users\admin\AppData\Local\Temp\BC82.tmp\noise.wav | wav | |
MD5:6FB3826CE933E7748E14CB31D1E50A74 | SHA256:81EB82AC1911503143BBAA44646CFEDE618A0807E9DCCCEF09F1DEB4D8700CE4 | |||
| 6668 | DeathPlus.exe | C:\Users\admin\AppData\Local\Temp\BC82.tmp\scream.exe | executable | |
MD5:CBF06517A75EEE73FF7A614981384457 | SHA256:AE5252BE8CAD37A12F70F94751F5A9DB15866A6C395DC5EBA505ECB05D414A9A | |||
| 6668 | DeathPlus.exe | C:\Users\admin\AppData\Local\Temp\BC82.tmp\CLWCP.exe | executable | |
MD5:E62EE6F1EFC85CB36D62AB779DB6E4EC | SHA256:13B4EC59785A1B367EFB691A3D5C86EB5AAF1CA0062521C4782E1BAAC6633F8A | |||
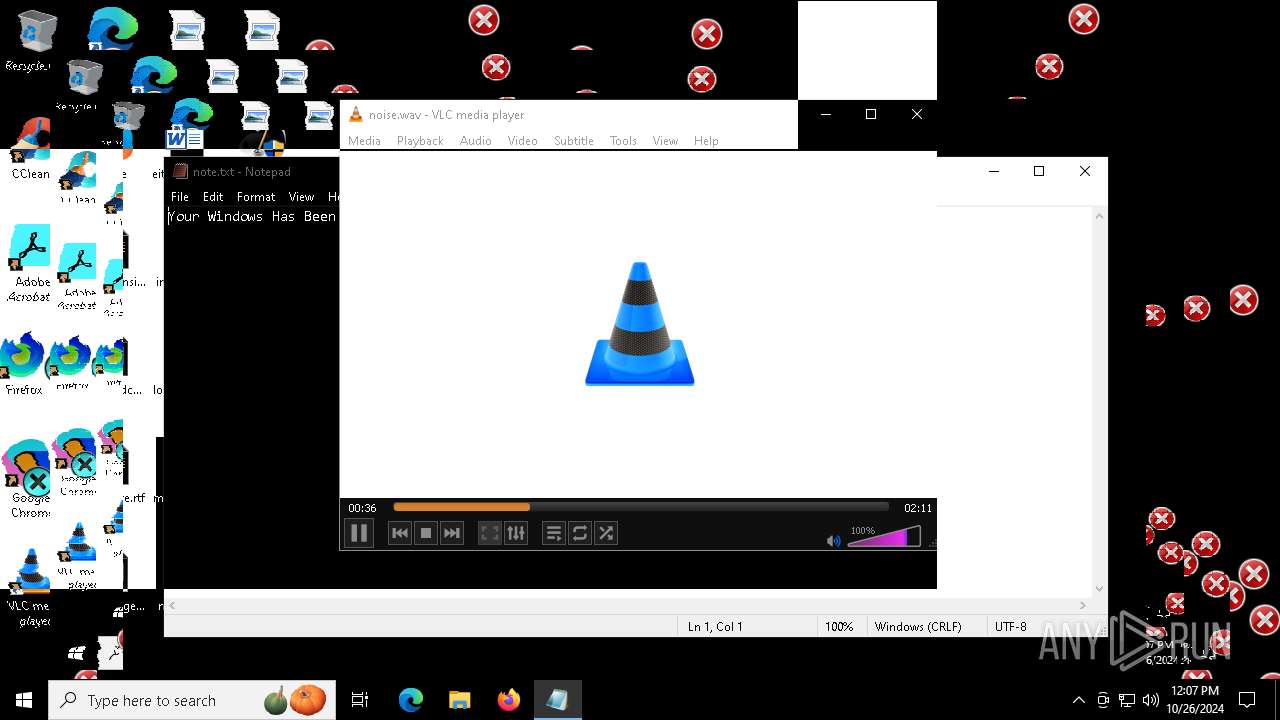
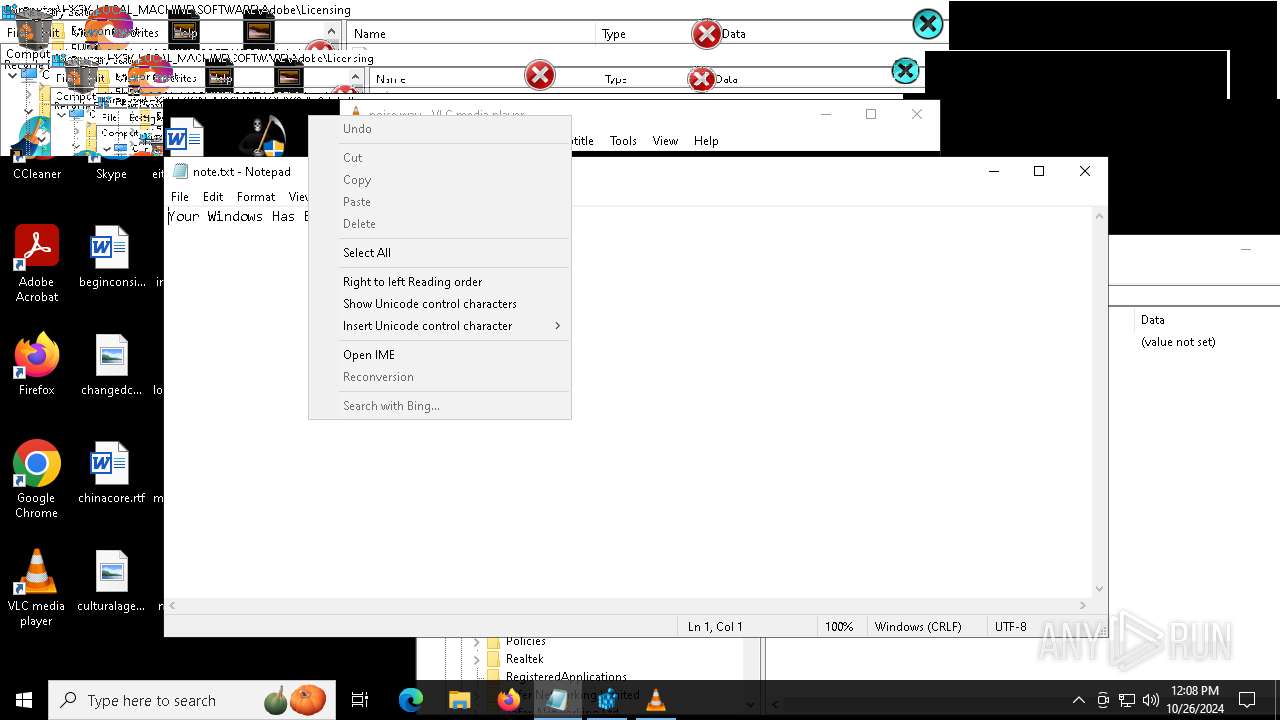
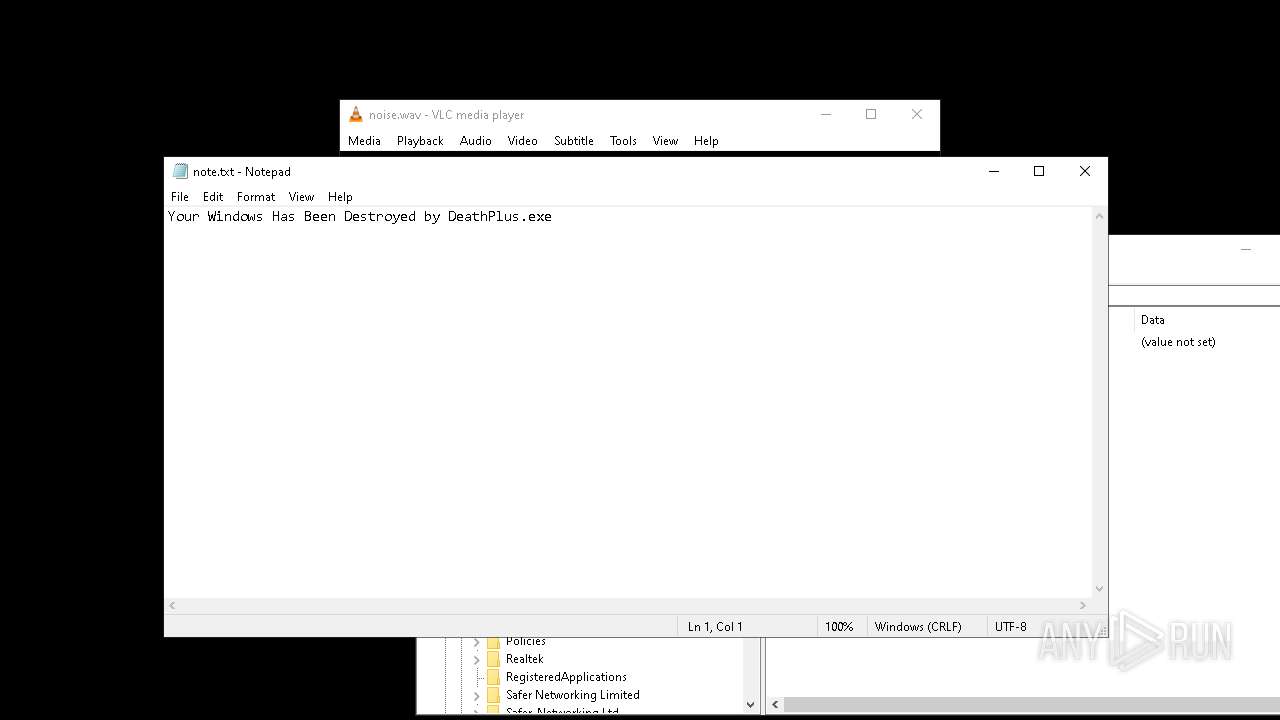
| 2648 | cmd.exe | C:\Users\admin\Desktop\note.txt | text | |
MD5:3420DDCB4BC853F482F42850BEE72490 | SHA256:343BA8F566AD4135B22CC7C63680AD0215DBC6D96398B9E7B4F032F9D2F03E57 | |||
| 6668 | DeathPlus.exe | C:\Users\admin\AppData\Local\Temp\BC82.tmp\MBRKiller.exe | executable | |
MD5:6C3D5092B6515B57C144BDCFCD641D13 | SHA256:DF3416733483B30D3E0725EC07CAEA190176D4305F93EEB3CACCE84802EA8E01 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
64
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2076 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6888 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
8052 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8052 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4836 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 2.16.110.195:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2076 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2076 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4360 | SearchApp.exe | 2.23.209.161:443 | th.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
Process | Message |
|---|---|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=x86_64-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=x86_64-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x64/contrib/x86_64-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc debug: plug-ins loaded: 494 modules
|