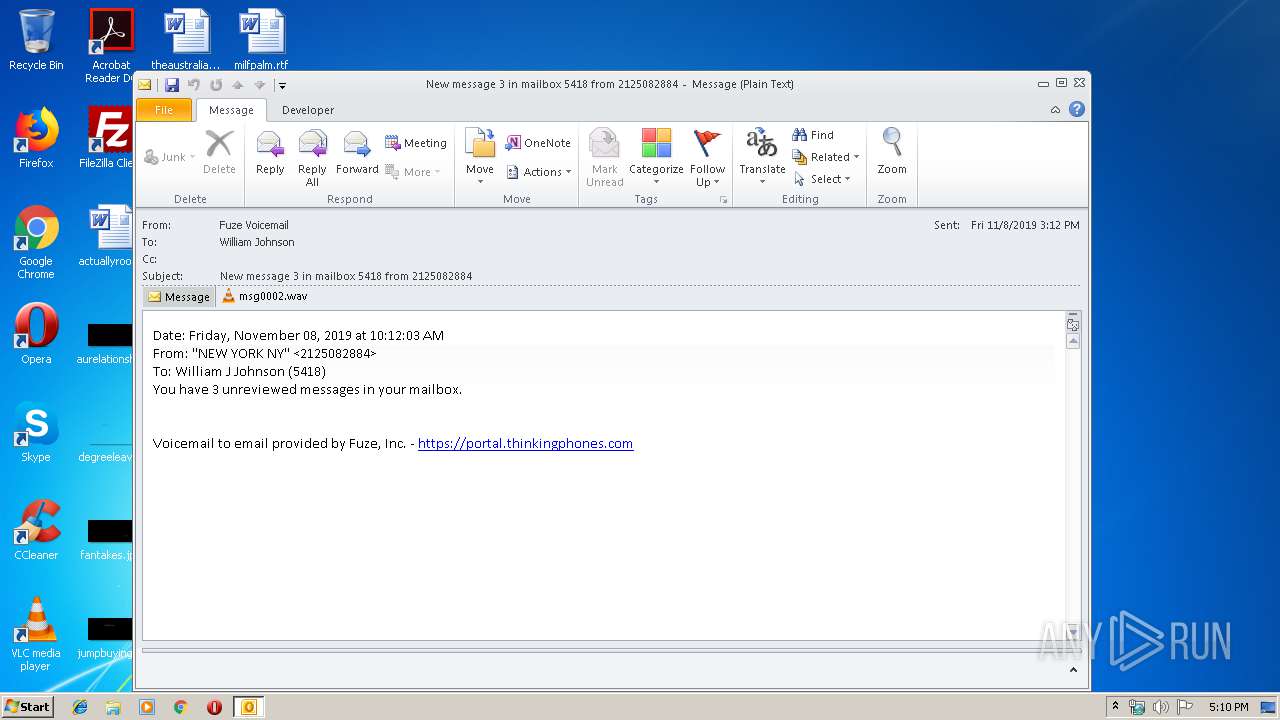
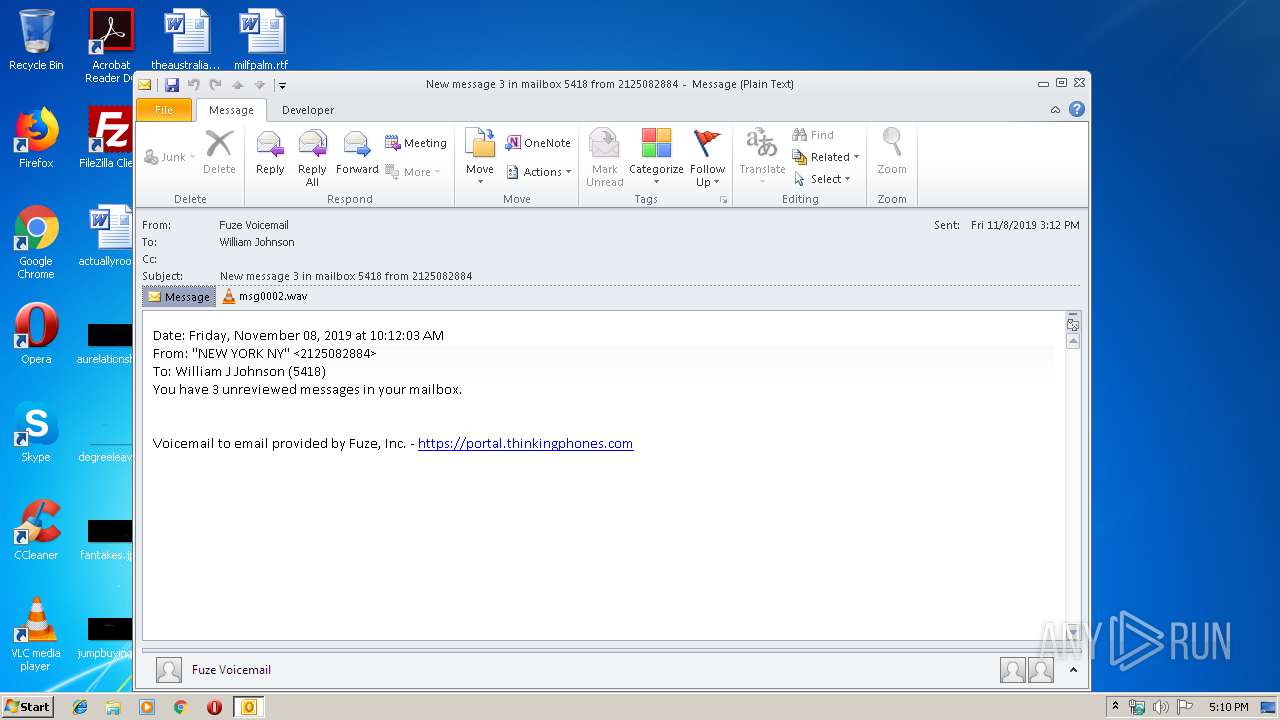
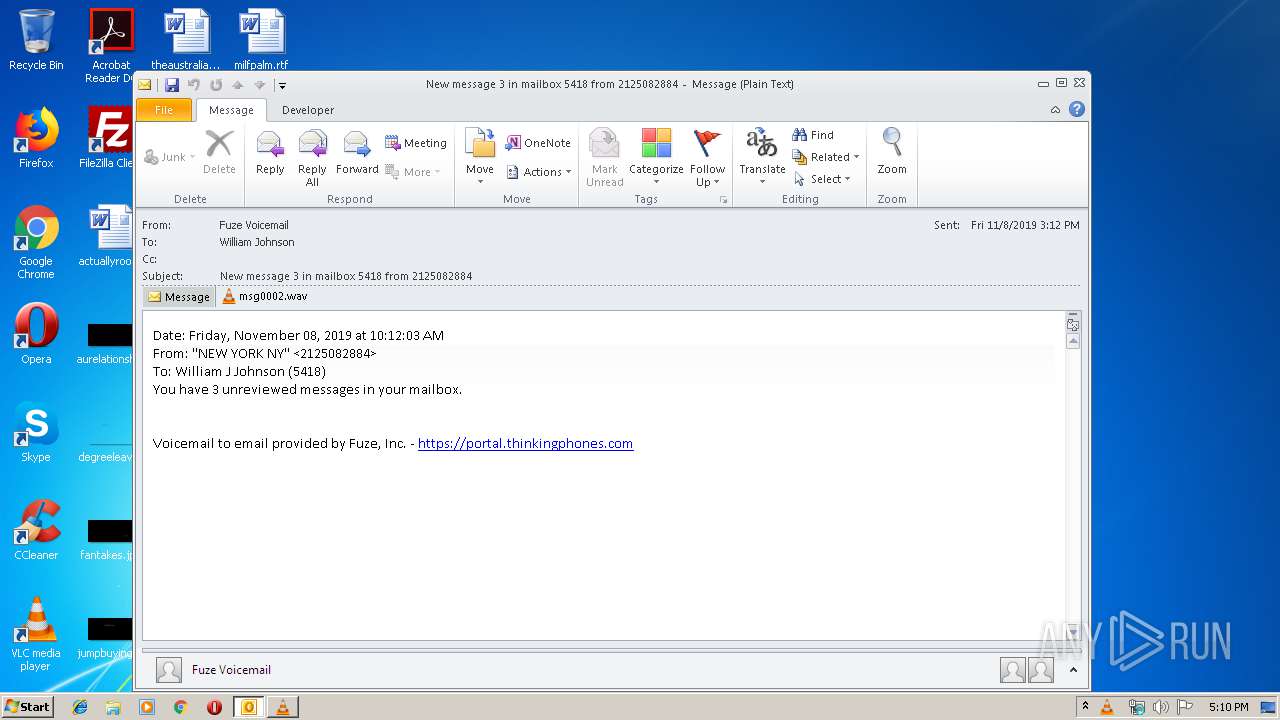
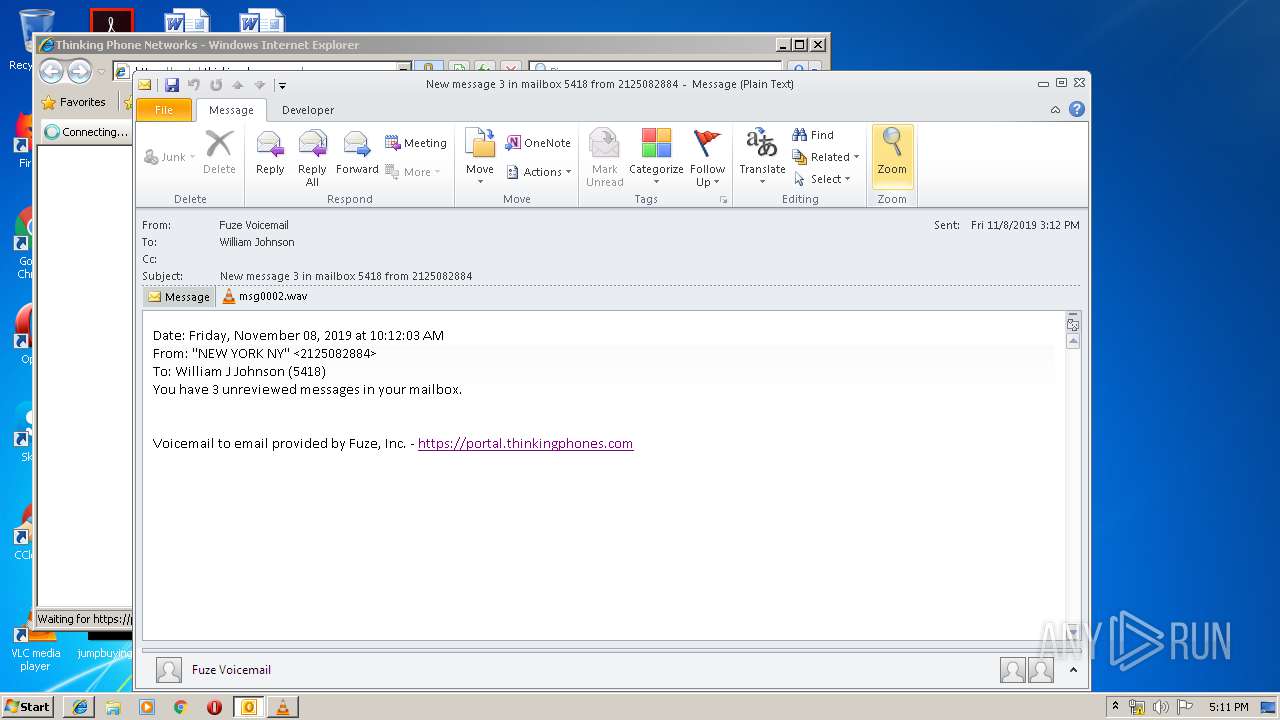
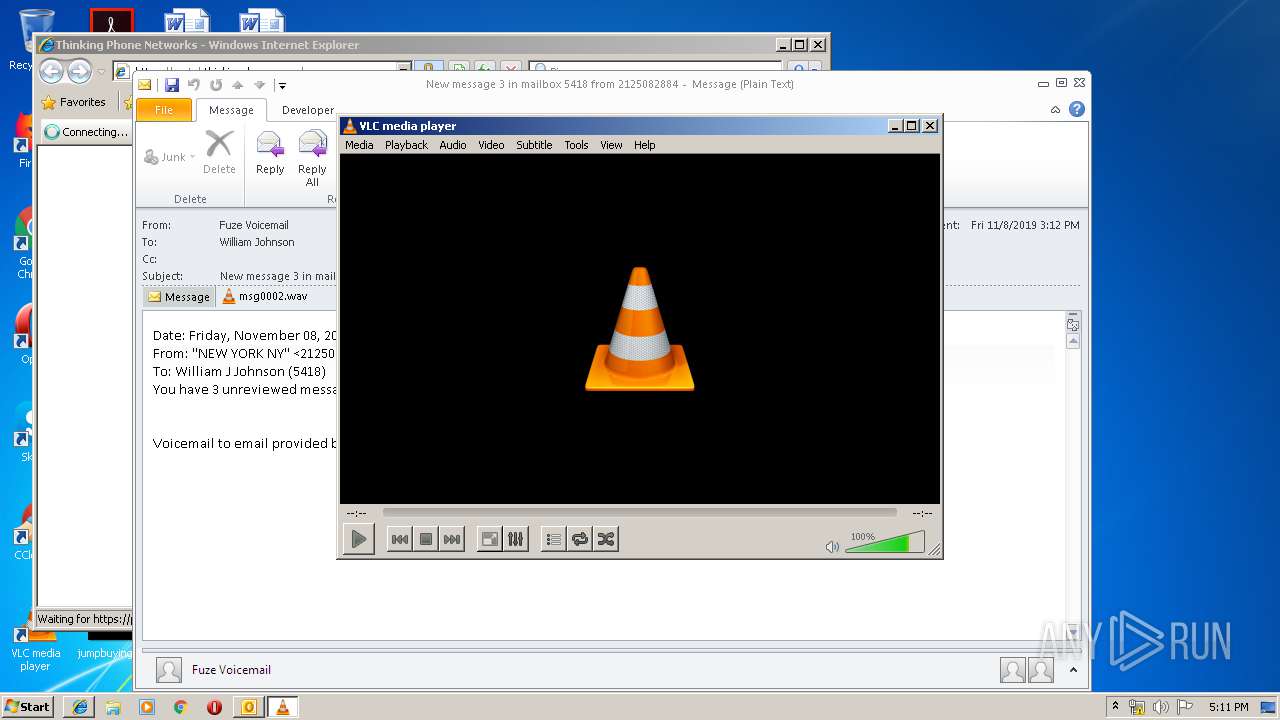
| File name: | Trojan - New message 3 in mailbox 5418 from 2125082884.msg |
| Full analysis: | https://app.any.run/tasks/5251728e-5a5e-4ec3-bc92-97b91a58b577 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2019, 17:10:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 33B60BB9BDC63D0495984F8D359CBFF7 |
| SHA1: | 61EAE5C827491158B2F5CD498D013410310DD3AD |
| SHA256: | F230C26E844C77104336F1A45EDB4CA1D306CA195B249BE0914E8324254087EE |
| SSDEEP: | 6144:Rr3SoO/7T1cbSzrDVZdOqn1Ka+6gXsDDbDZOHQ4:dSObSflOqI7efI |
MALICIOUS
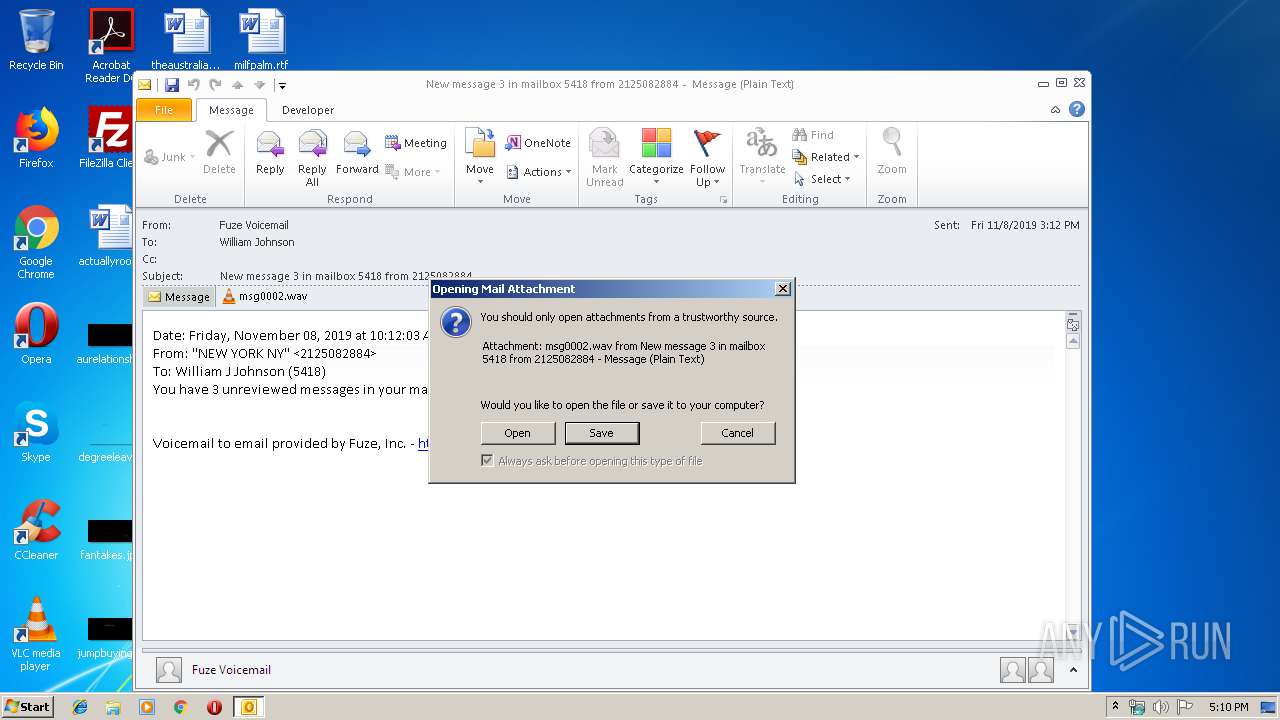
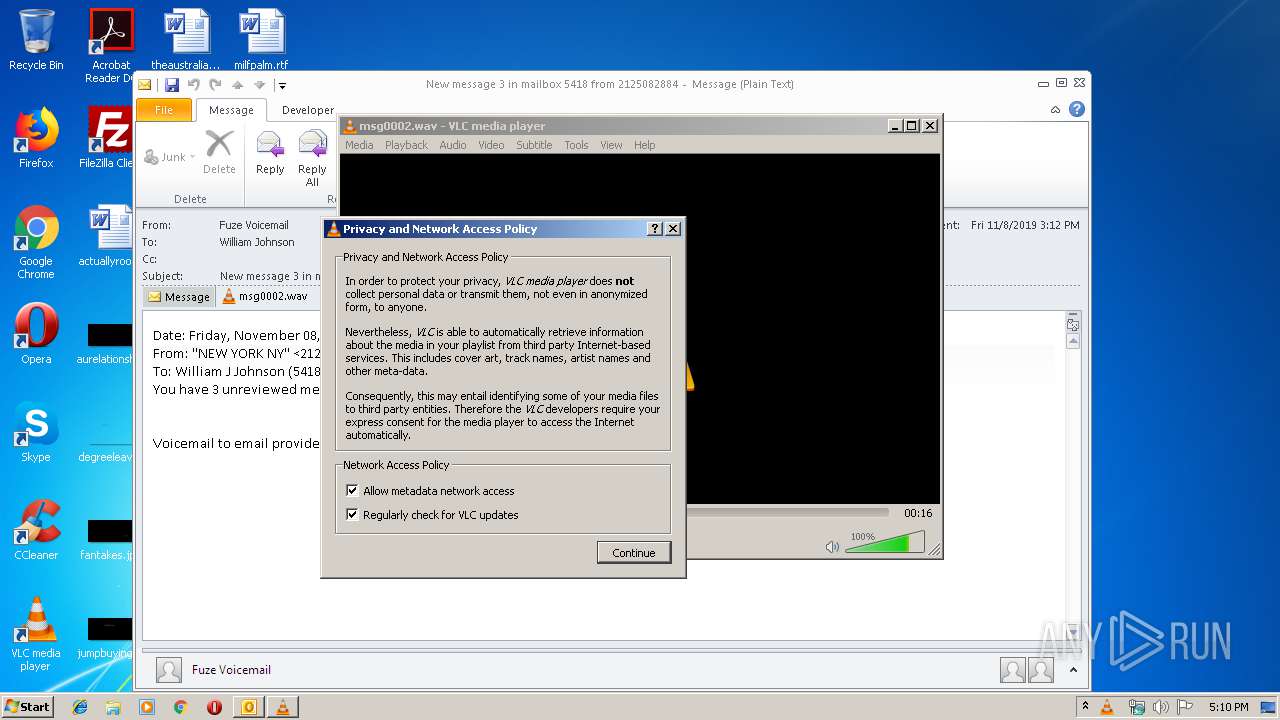
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2548)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2548)
- vlc.exe (PID: 2764)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2548)
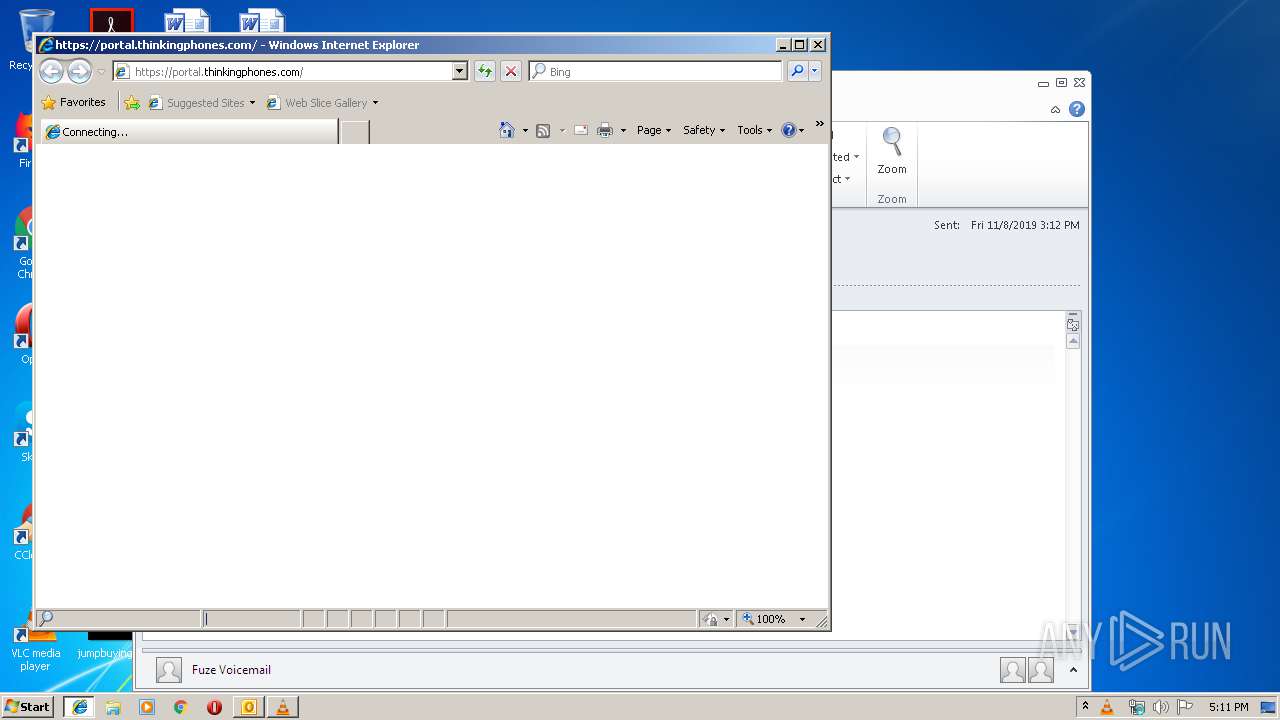
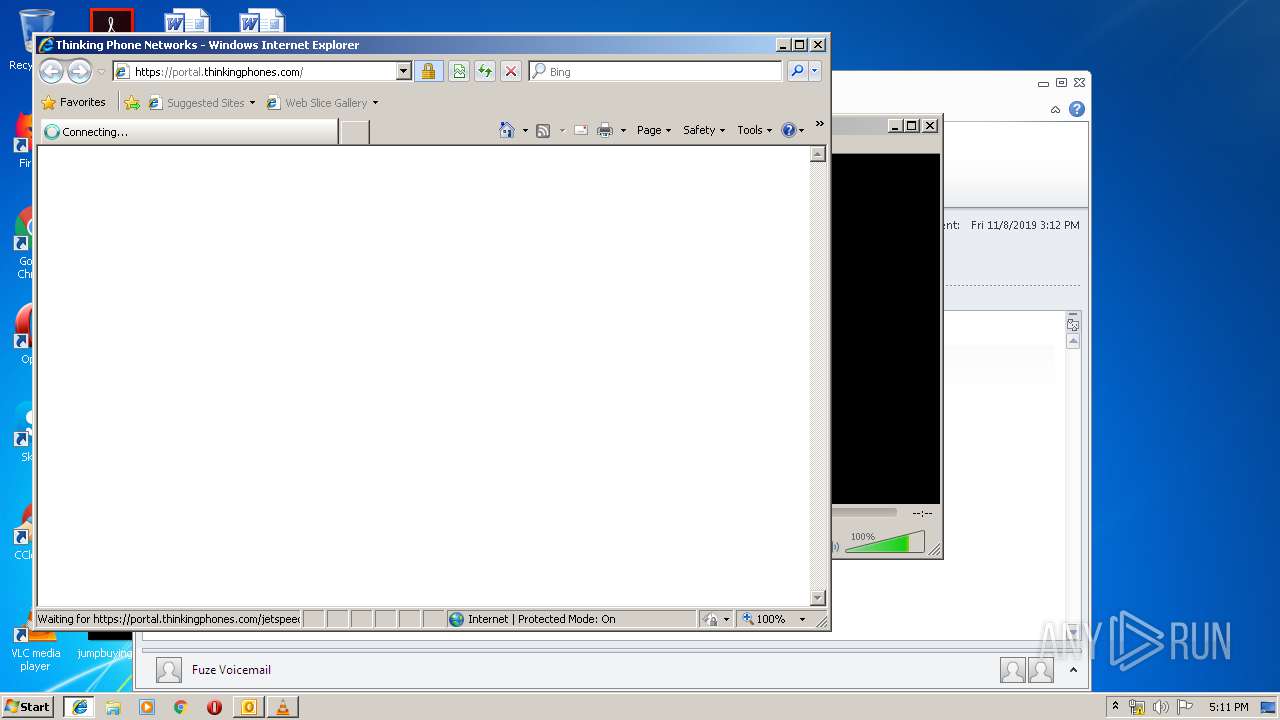
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2548)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2548)
Changes internet zones settings
- iexplore.exe (PID: 2056)
Application launched itself
- iexplore.exe (PID: 2056)
Reads internet explorer settings
- iexplore.exe (PID: 2480)
Creates files in the user directory
- iexplore.exe (PID: 2480)
Reads Internet Cache Settings
- iexplore.exe (PID: 2480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
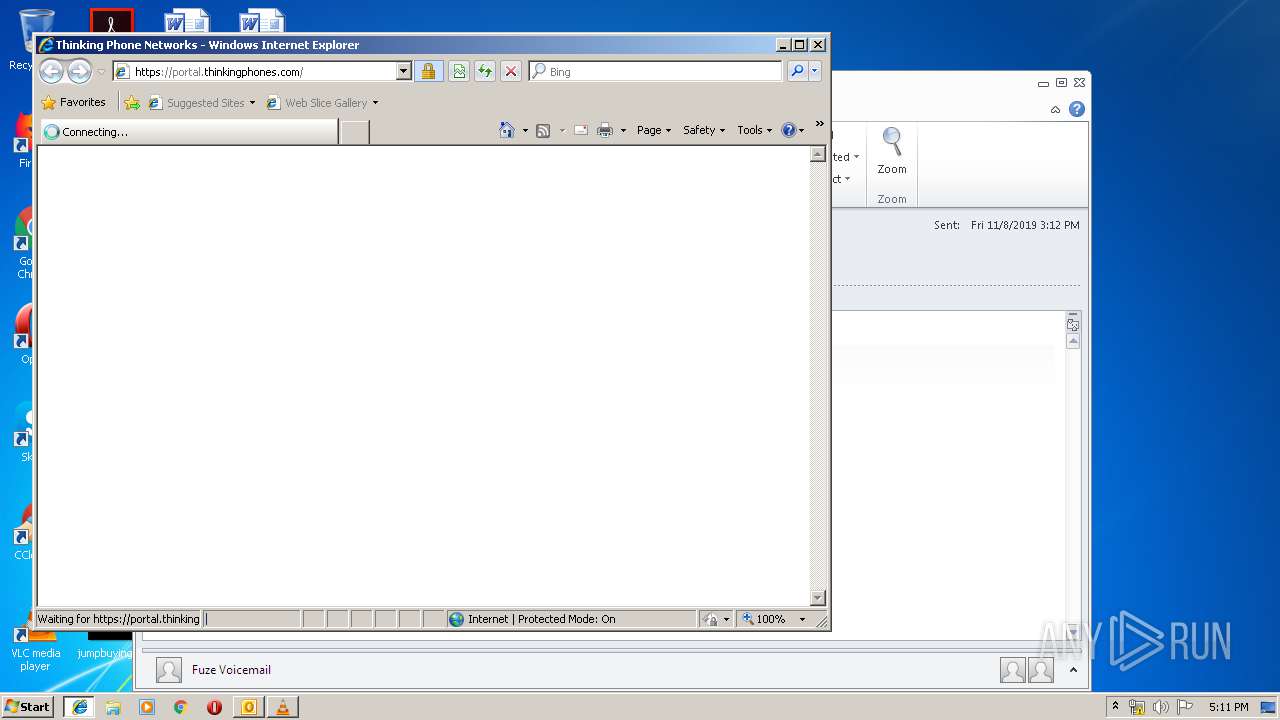
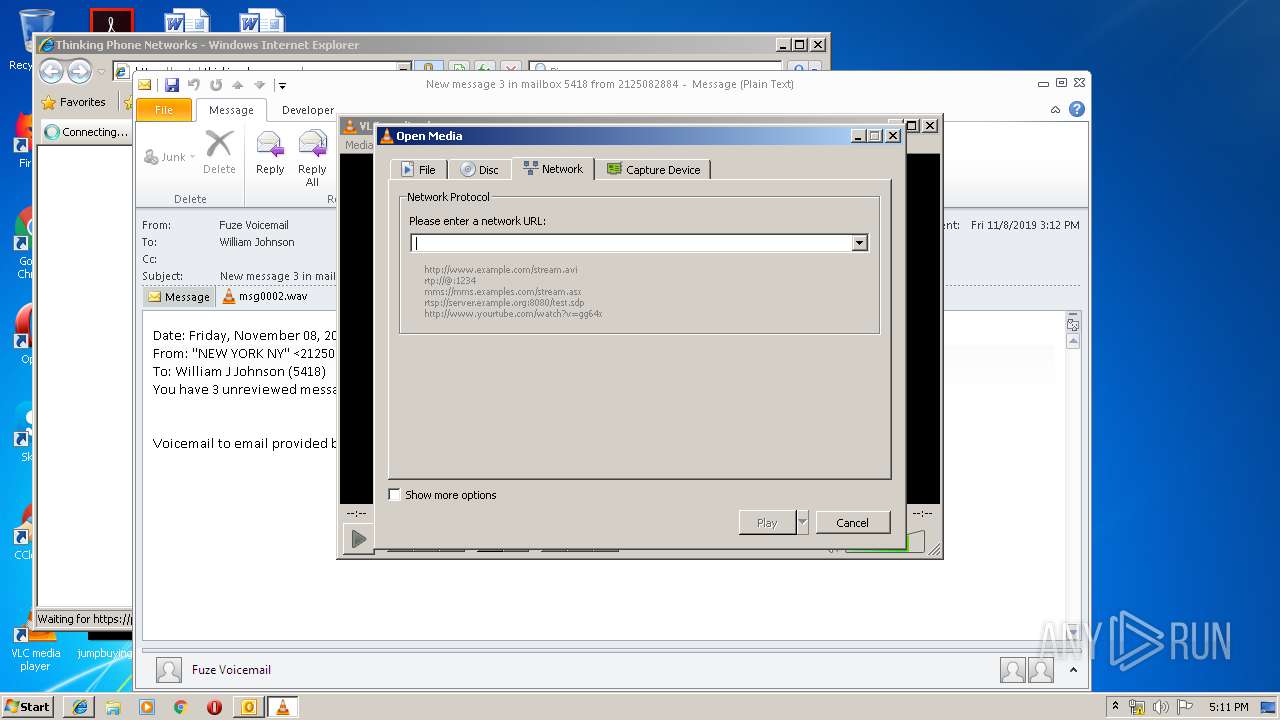
| 2056 | "C:\Program Files\Internet Explorer\iexplore.exe" https://portal.thinkingphones.com/ | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
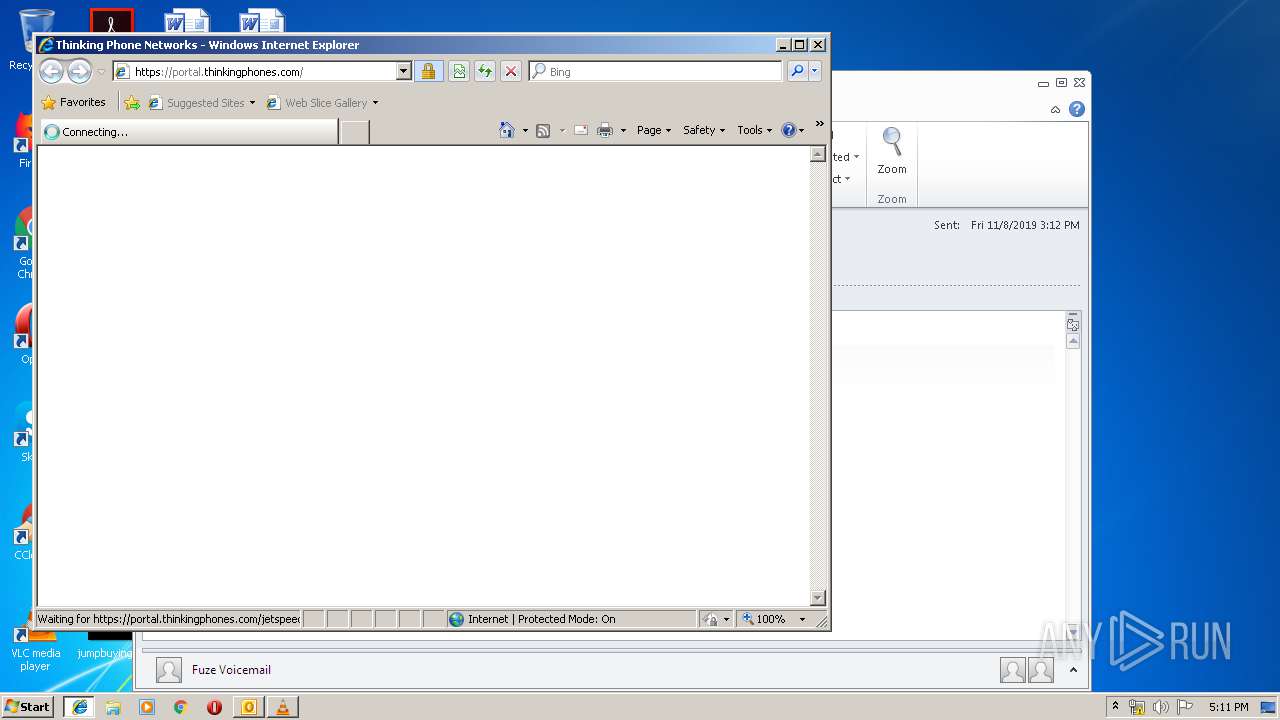
| 2480 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2056 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Trojan - New message 3 in mailbox 5418 from 2125082884.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
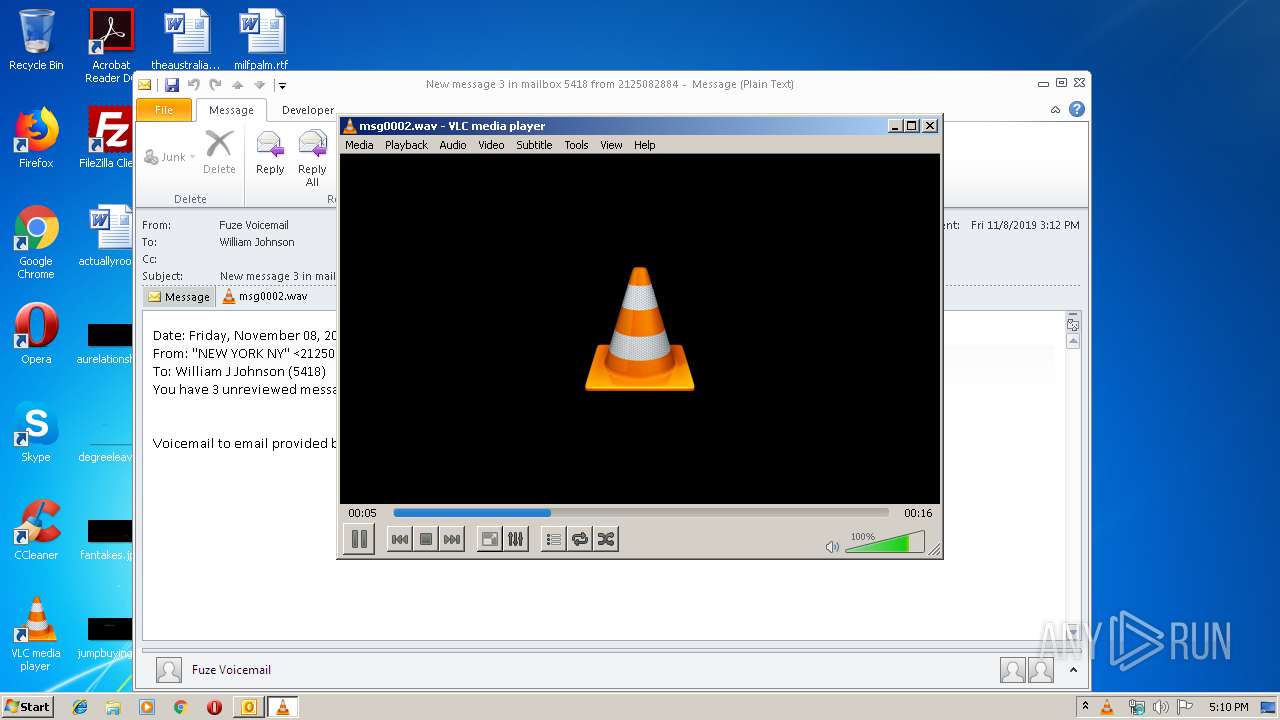
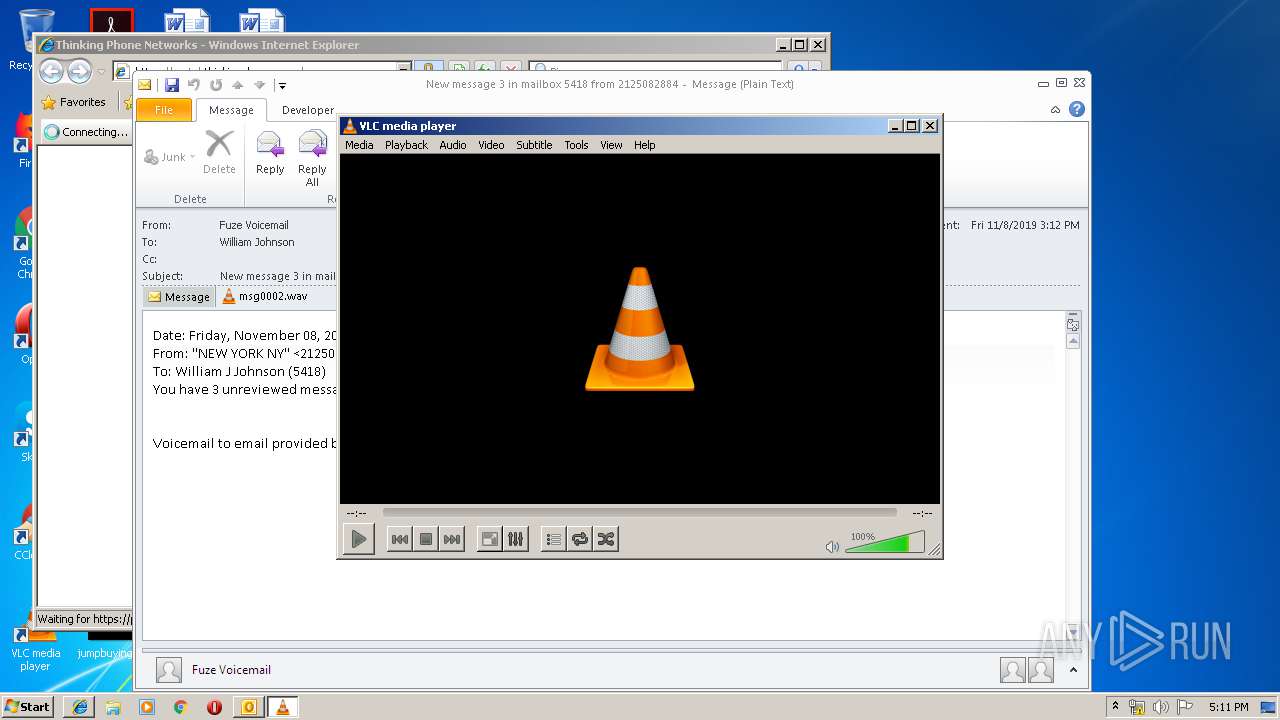
| 2764 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\GY863Z6U\msg0002.wav" | C:\Program Files\VideoLAN\VLC\vlc.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
Total events
2 603
Read events
1 978
Write events
604
Delete events
21
Modification events
| (PID) Process: | (2548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2548) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1332215988 | |||
| (PID) Process: | (2548) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources |
| Operation: | write | Name: | UISnapshot |
Value: 1033;1046;1036;1031;1040;1041;1049;3082;1042;1055 | |||
Executable files
0
Suspicious files
5
Text files
38
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2548 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA92B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2548 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\GY863Z6U\msg0002 (2).wav\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2764 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCCBB7.tmp | — | |
MD5:— | SHA256:— | |||
| 2764 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCCD1F.tmp | — | |
MD5:— | SHA256:— | |||
| 2764 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCCD30.tmp | — | |
MD5:— | SHA256:— | |||
| 2764 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCCD31.tmp | — | |
MD5:— | SHA256:— | |||
| 2764 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCCD32.tmp | — | |
MD5:— | SHA256:— | |||
| 2764 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCCD33.tmp | — | |
MD5:— | SHA256:— | |||
| 2764 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCCD34.tmp | — | |
MD5:— | SHA256:— | |||
| 2764 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCCD35.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
7
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2548 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2480 | iexplore.exe | GET | 200 | 67.26.139.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
2480 | iexplore.exe | GET | 200 | 13.224.89.196:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2056 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2548 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2056 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2480 | iexplore.exe | 3.219.213.162:443 | portal.thinkingphones.com | — | US | unknown |
2480 | iexplore.exe | 13.224.89.196:80 | x.ss2.us | — | US | unknown |
2480 | iexplore.exe | 67.26.139.254:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2480 | iexplore.exe | 35.170.241.192:443 | auth.thinkingphones.com | Amazon.com, Inc. | US | unknown |
2056 | iexplore.exe | 3.219.213.162:443 | portal.thinkingphones.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
portal.thinkingphones.com |
| unknown |
www.bing.com |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
auth.thinkingphones.com |
| unknown |
Threats
Process | Message |
|---|---|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|