| File name: | ed7b275f-7e7b-4fa9-9abf-676847530890 |
| Full analysis: | https://app.any.run/tasks/1b9f0380-0b5f-49dc-a239-0a77ae4267ae |
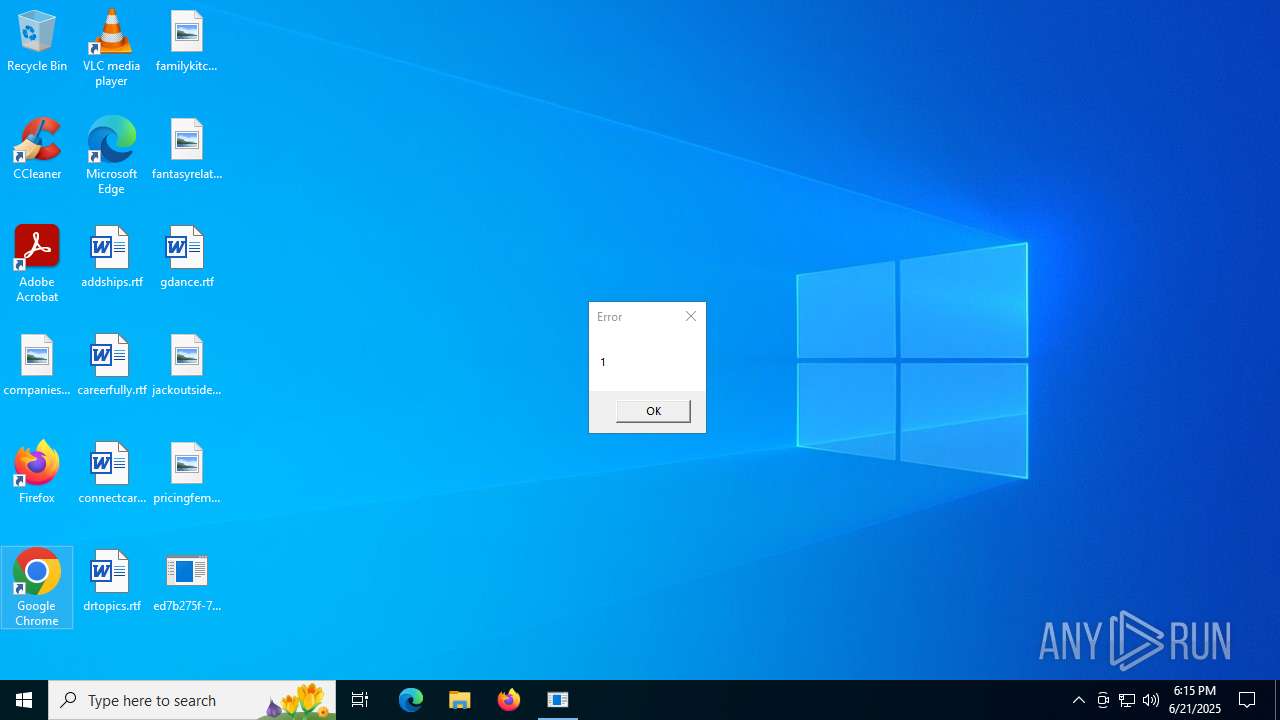
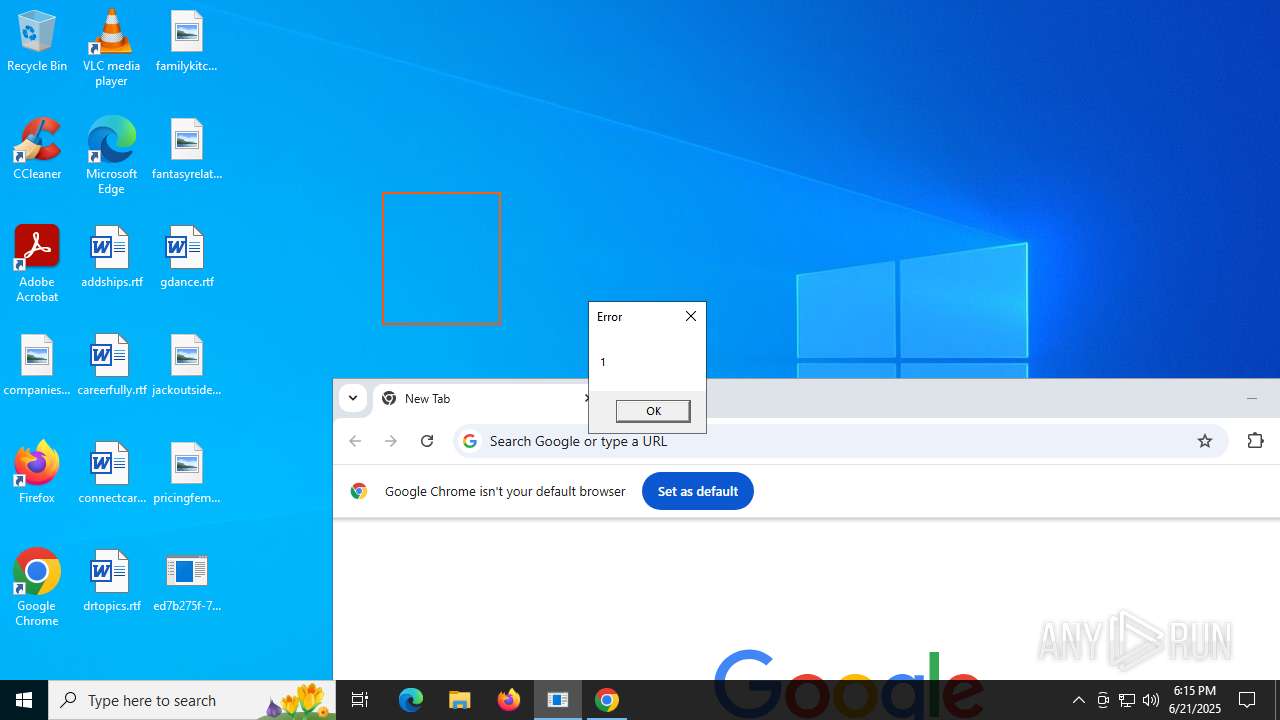
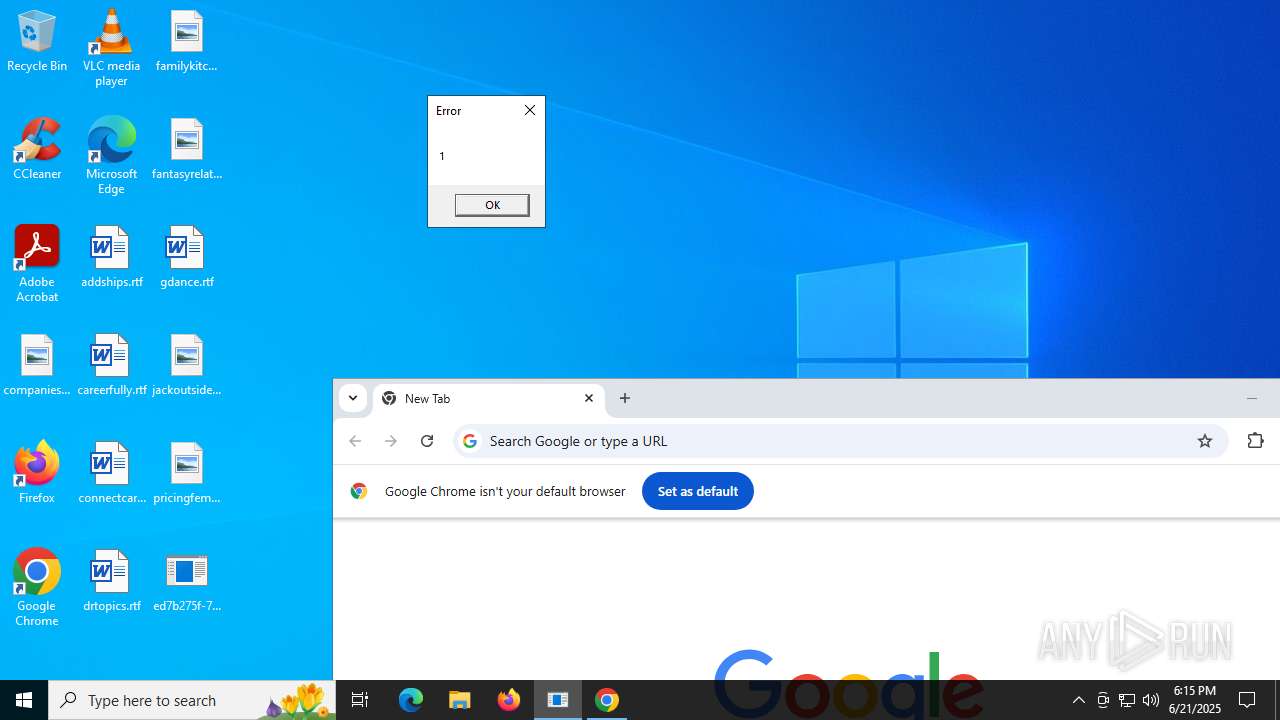
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 18:15:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 5 sections |
| MD5: | 946E3834E36523E8AE07CB2FEEA9B734 |
| SHA1: | C6CA80816B8E1DF667C5D49F60C554B6622C5522 |
| SHA256: | F224739A2013952F37140737874E91777EBED4E12354260856F703BDCDF22AF4 |
| SSDEEP: | 24576:VilbG5ebt9nXzuCH/BiuKkICXYYB1Yctp7VGLVmhqC4:VilbG5ebzXzuCH/Biu3IoYYB1Yctp7Ve |
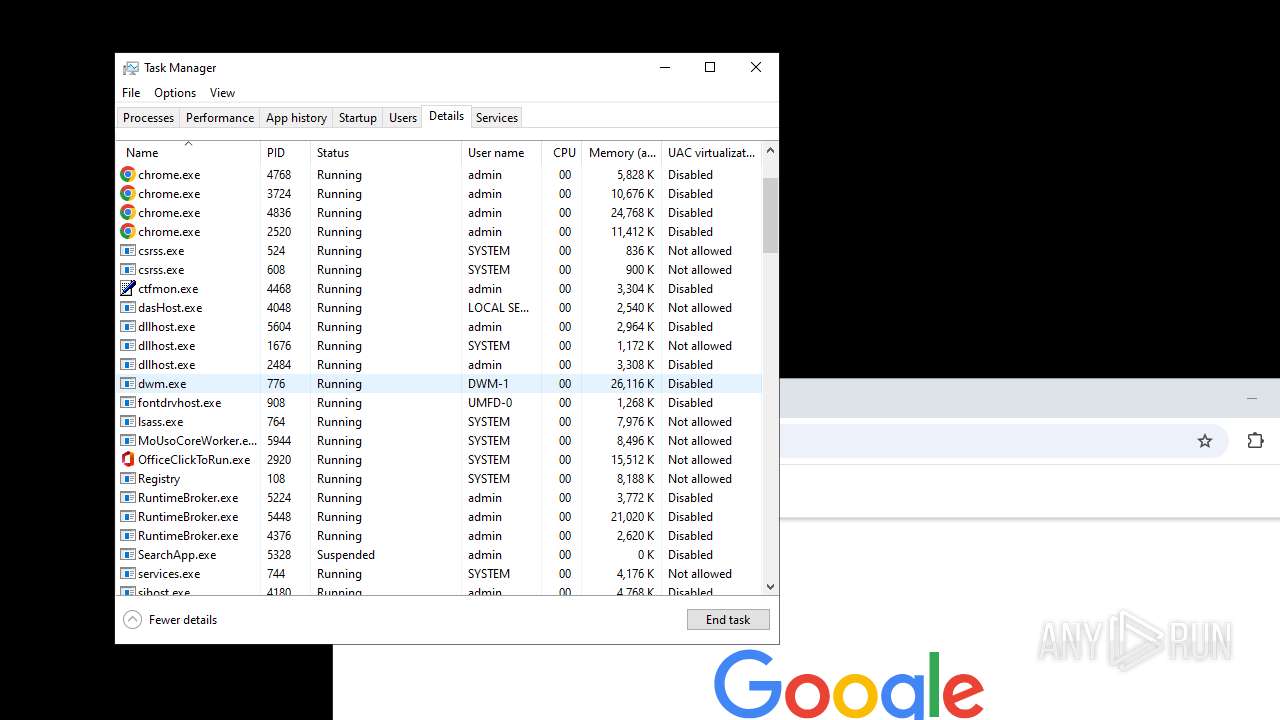
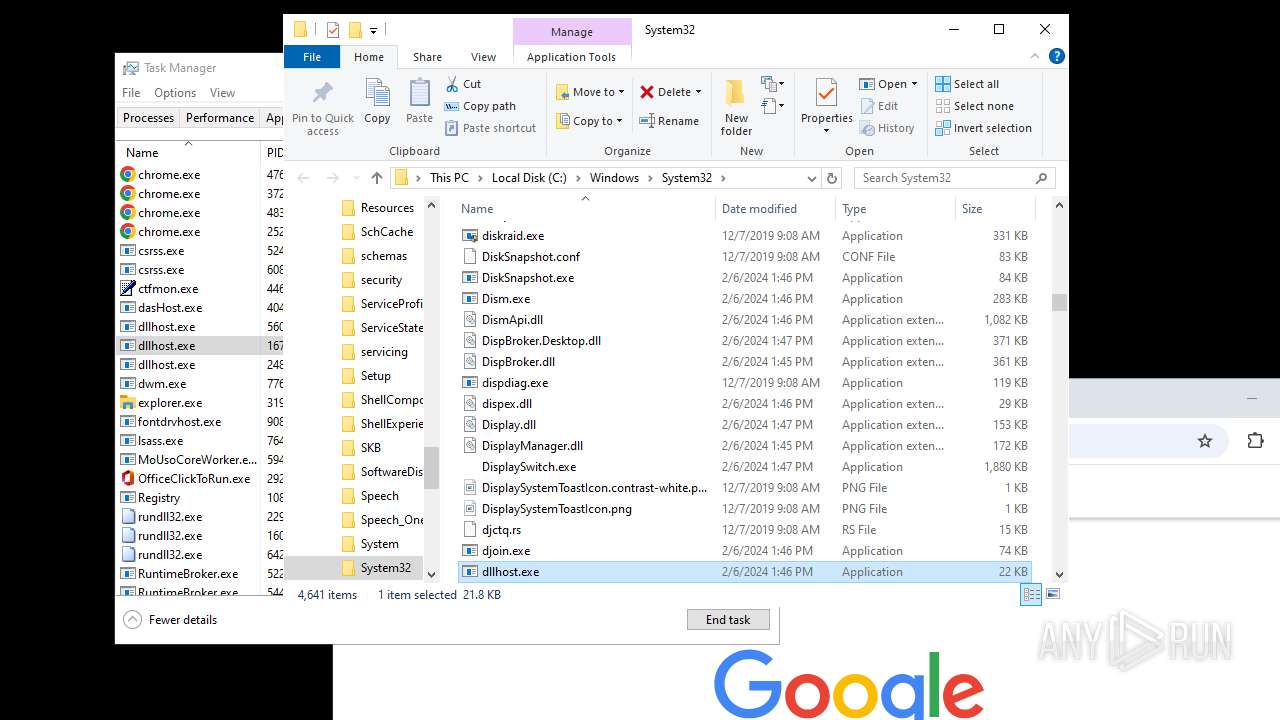
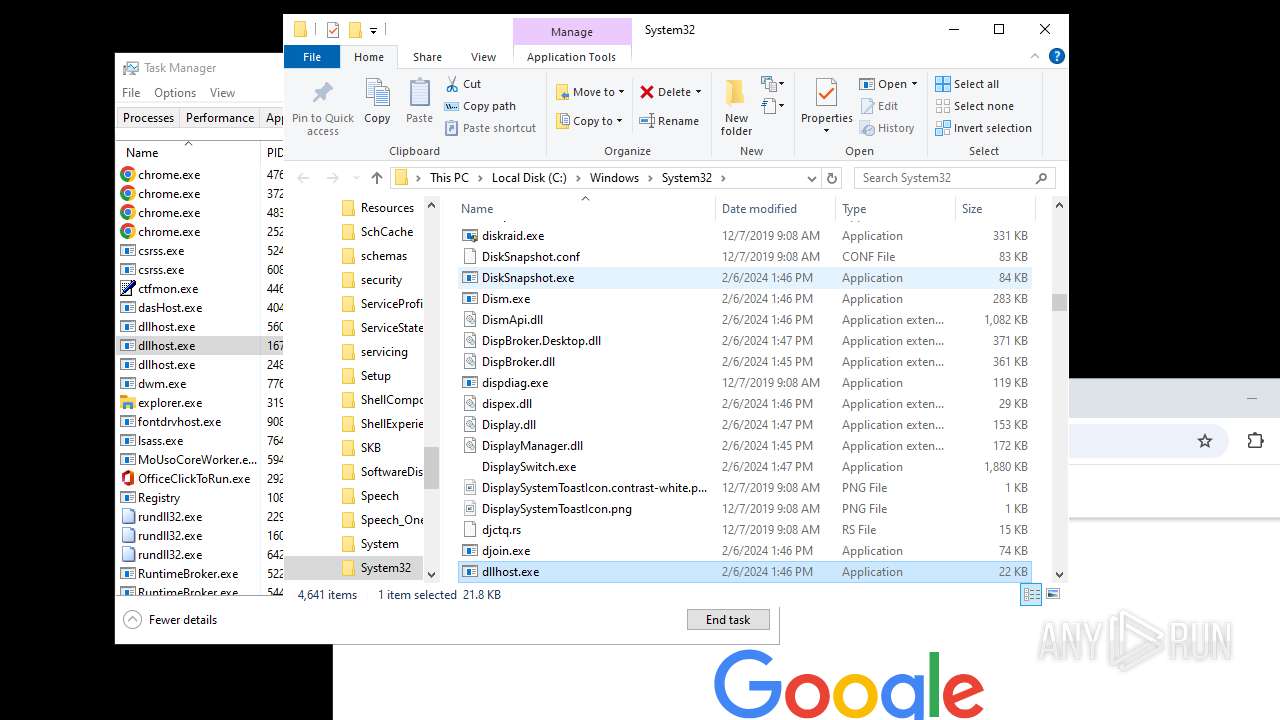
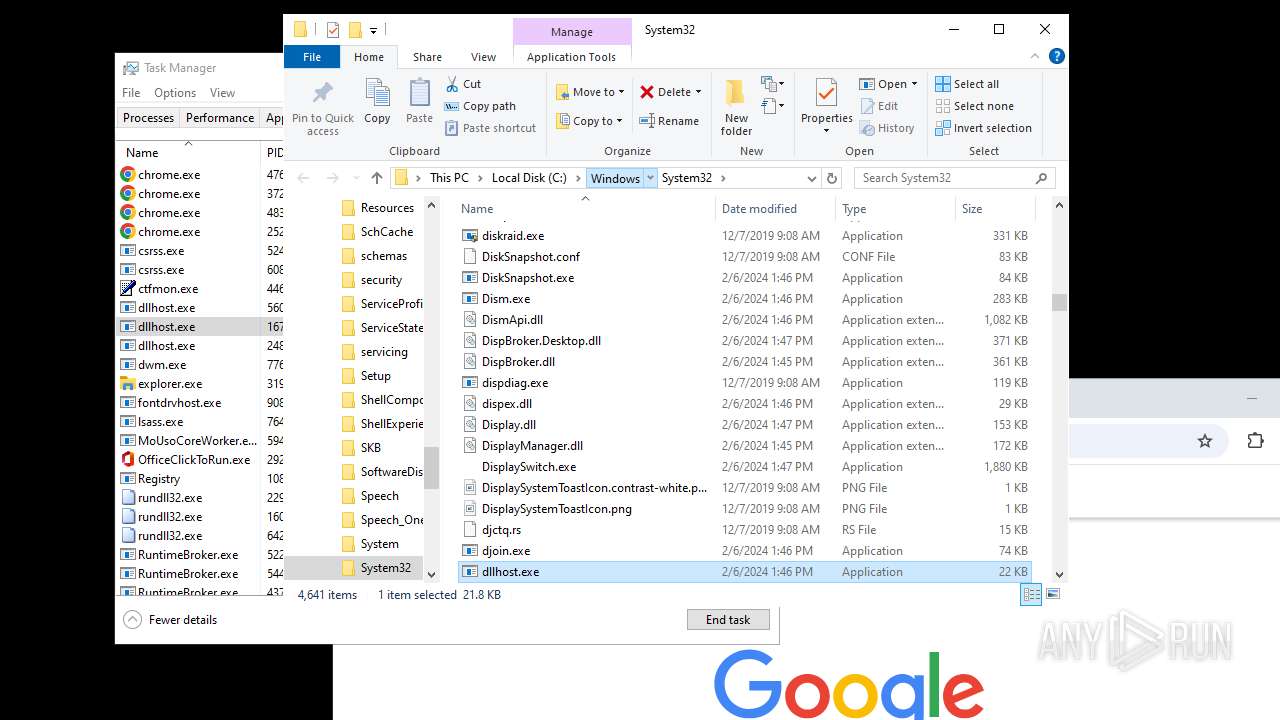
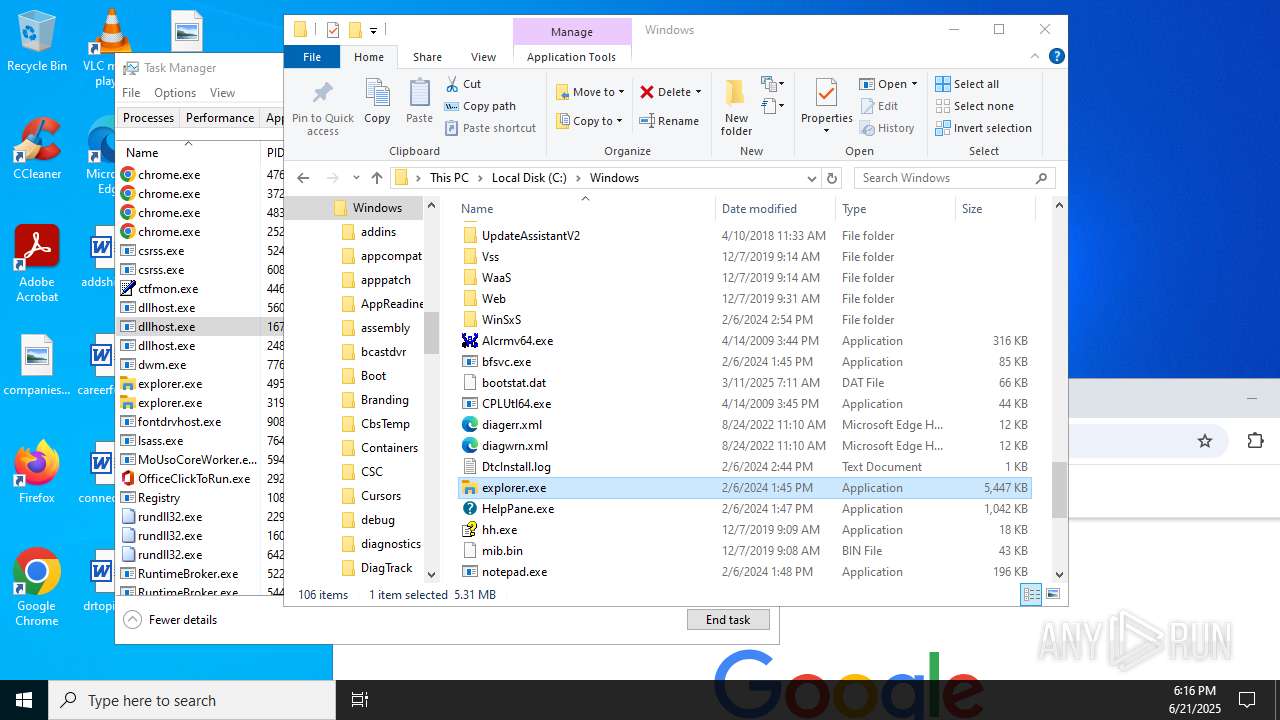
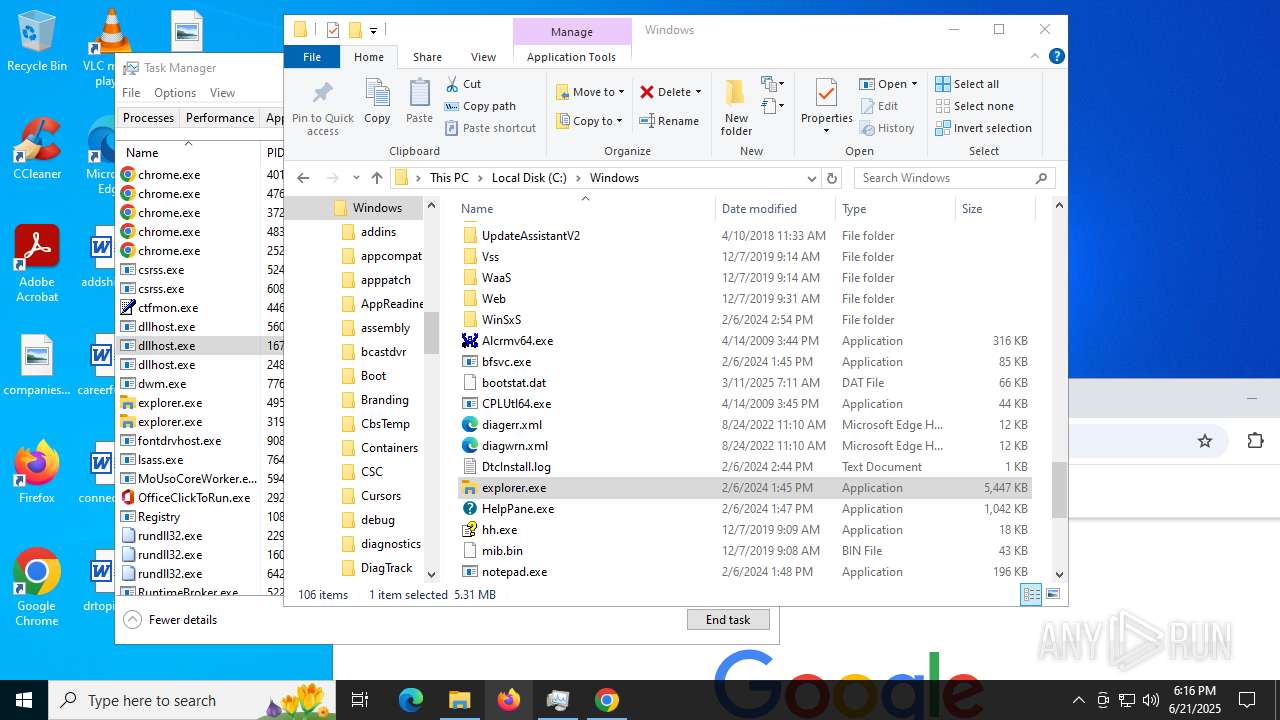
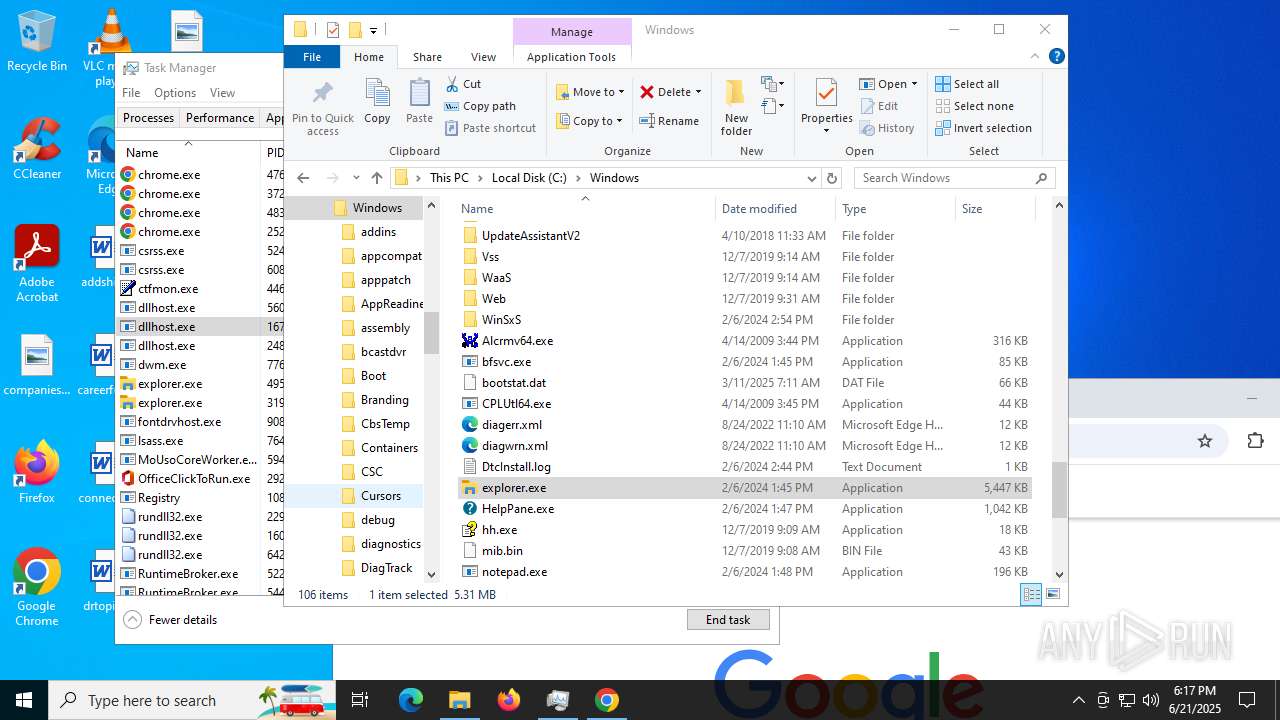
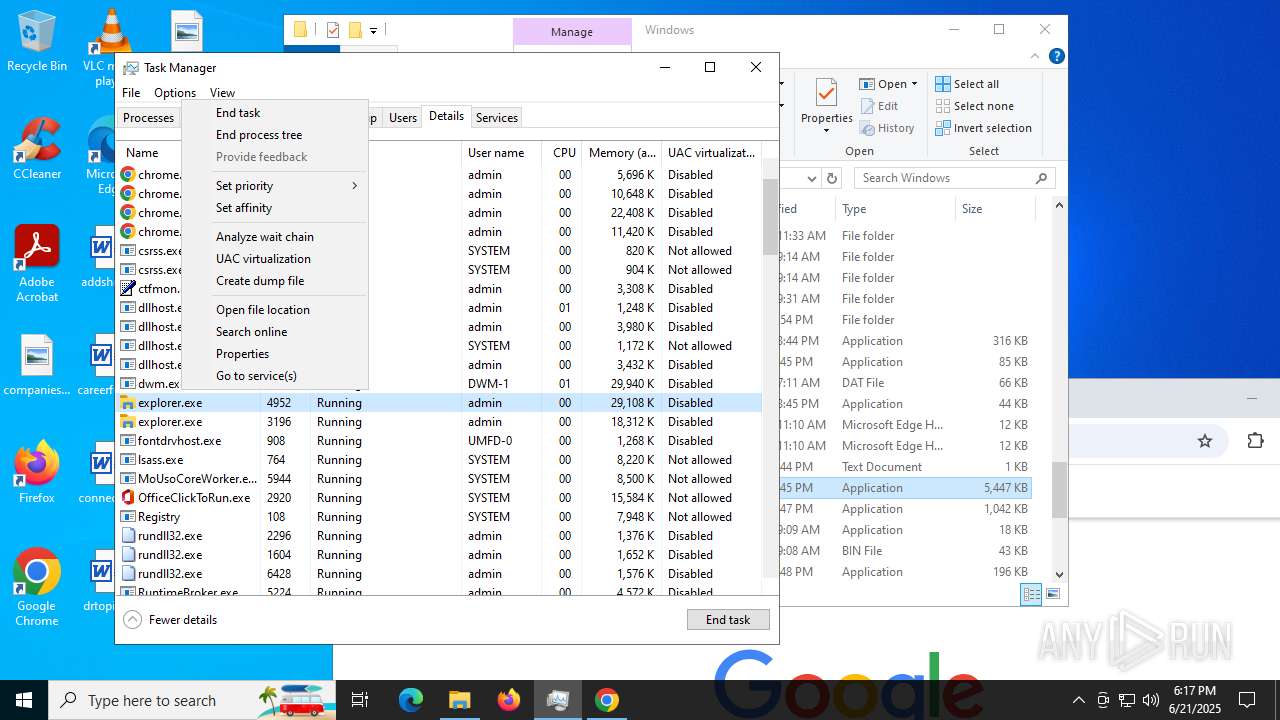
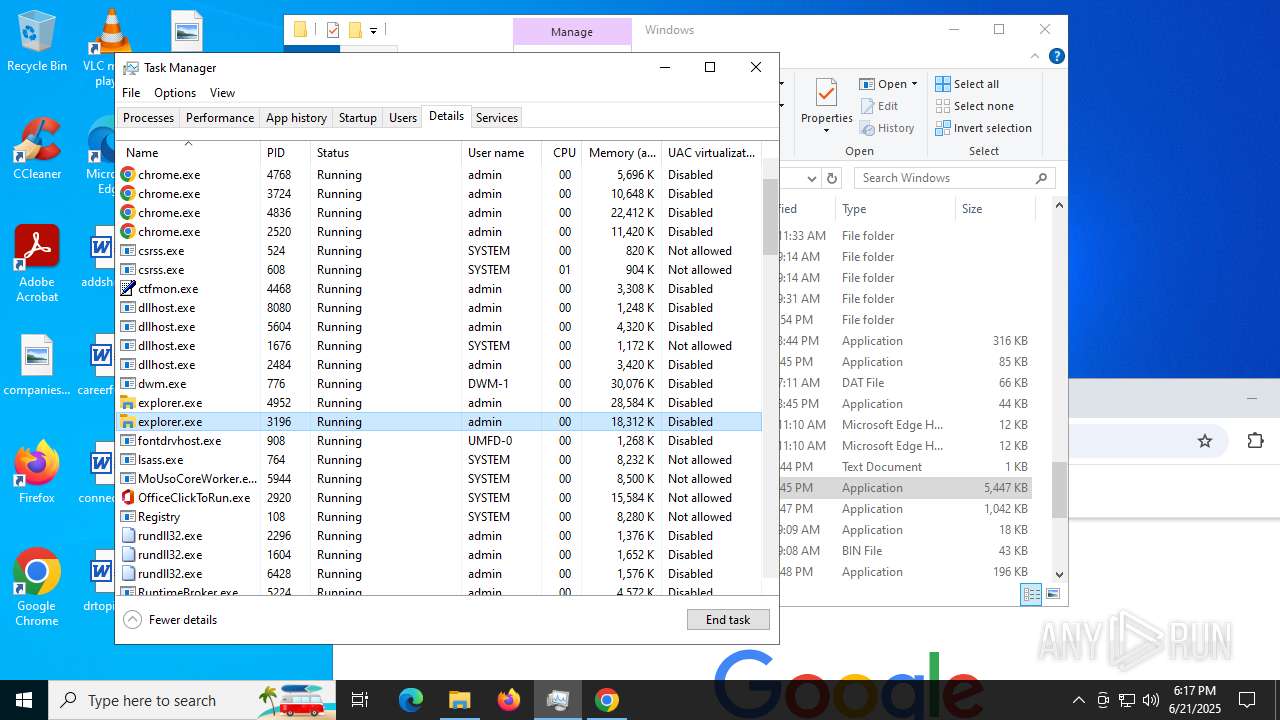
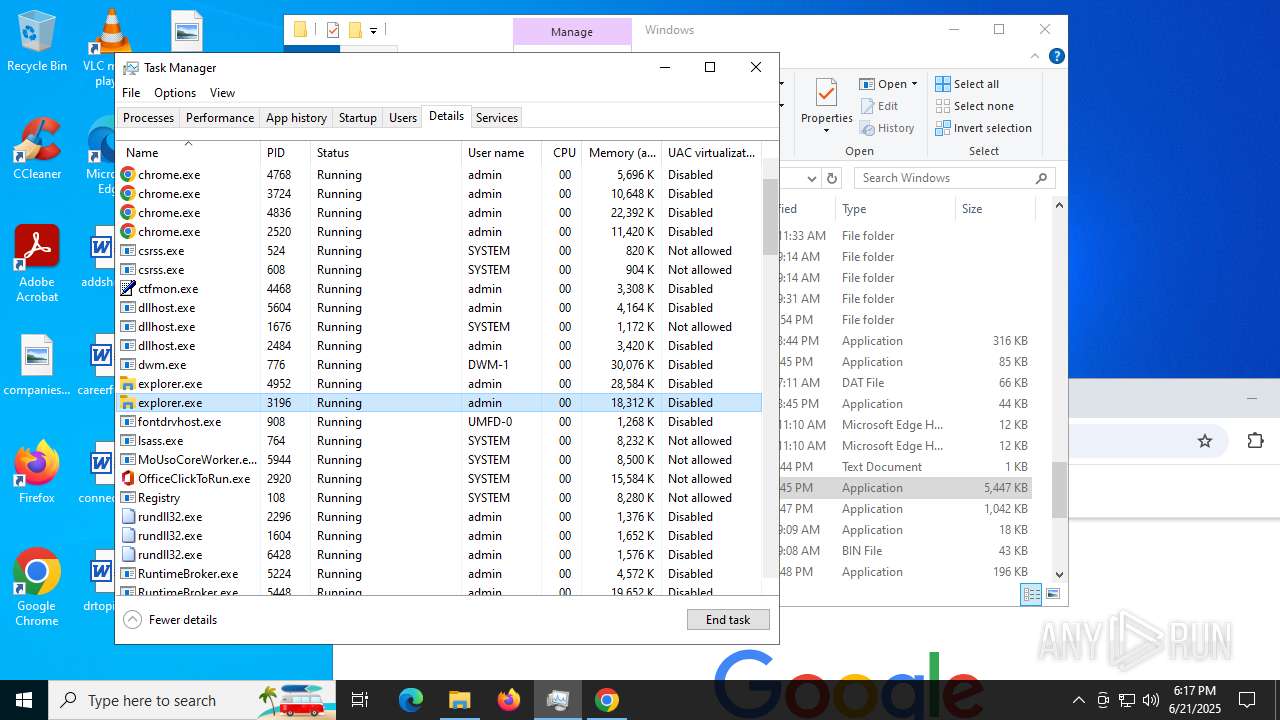
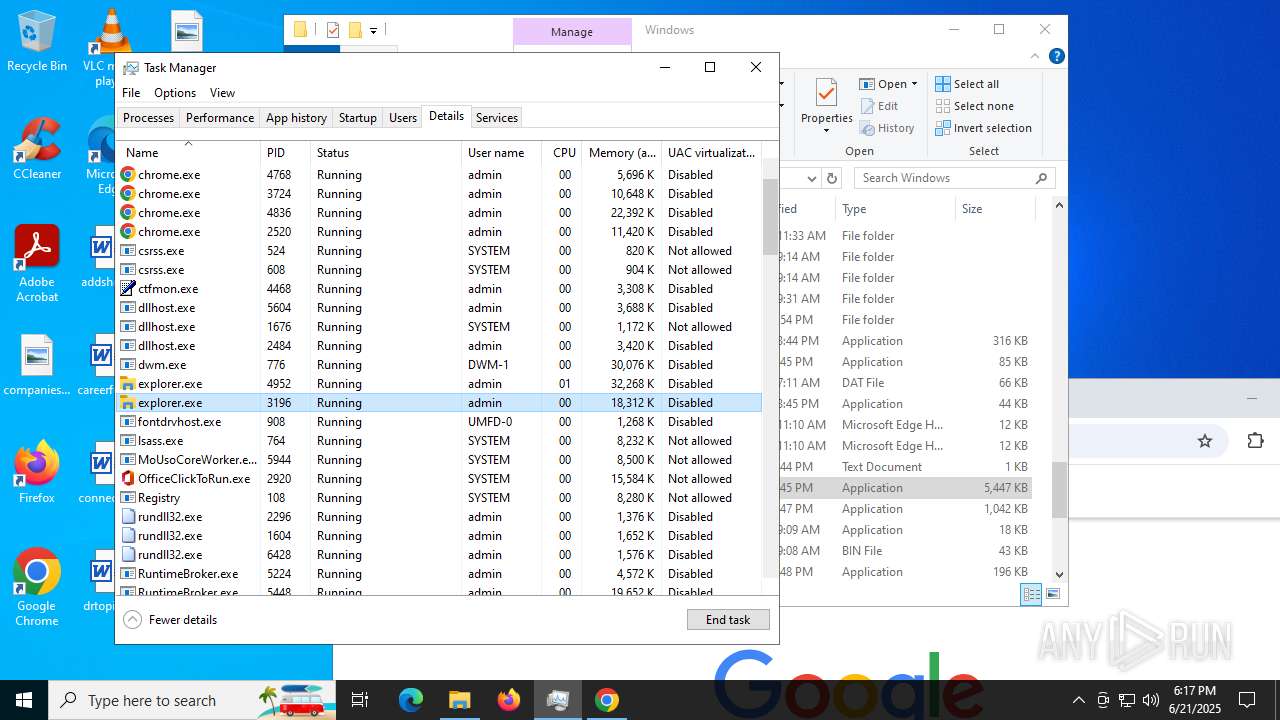
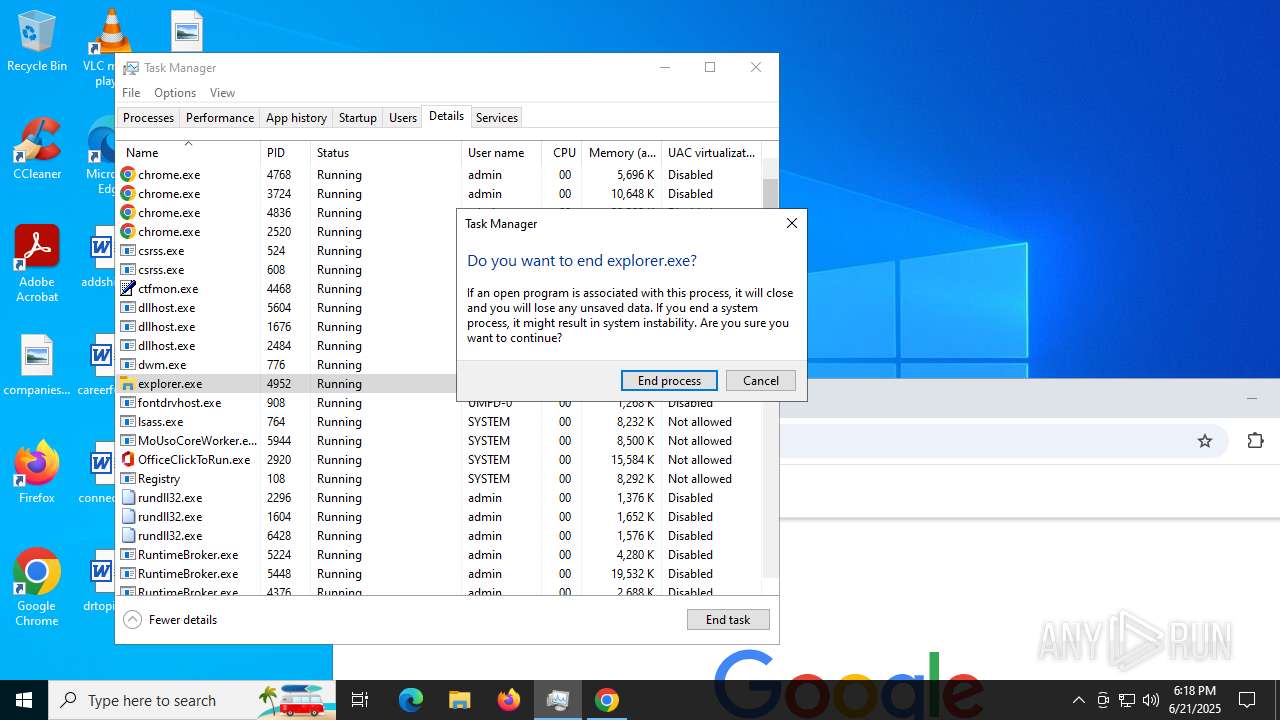
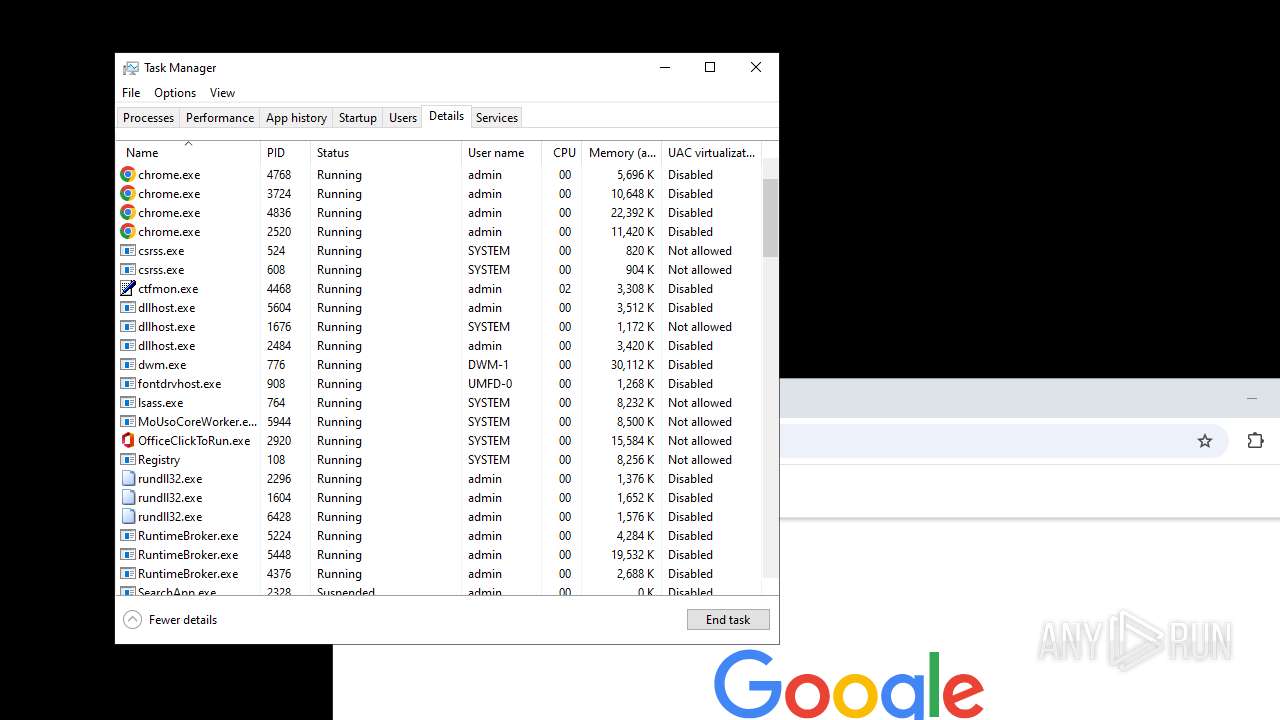
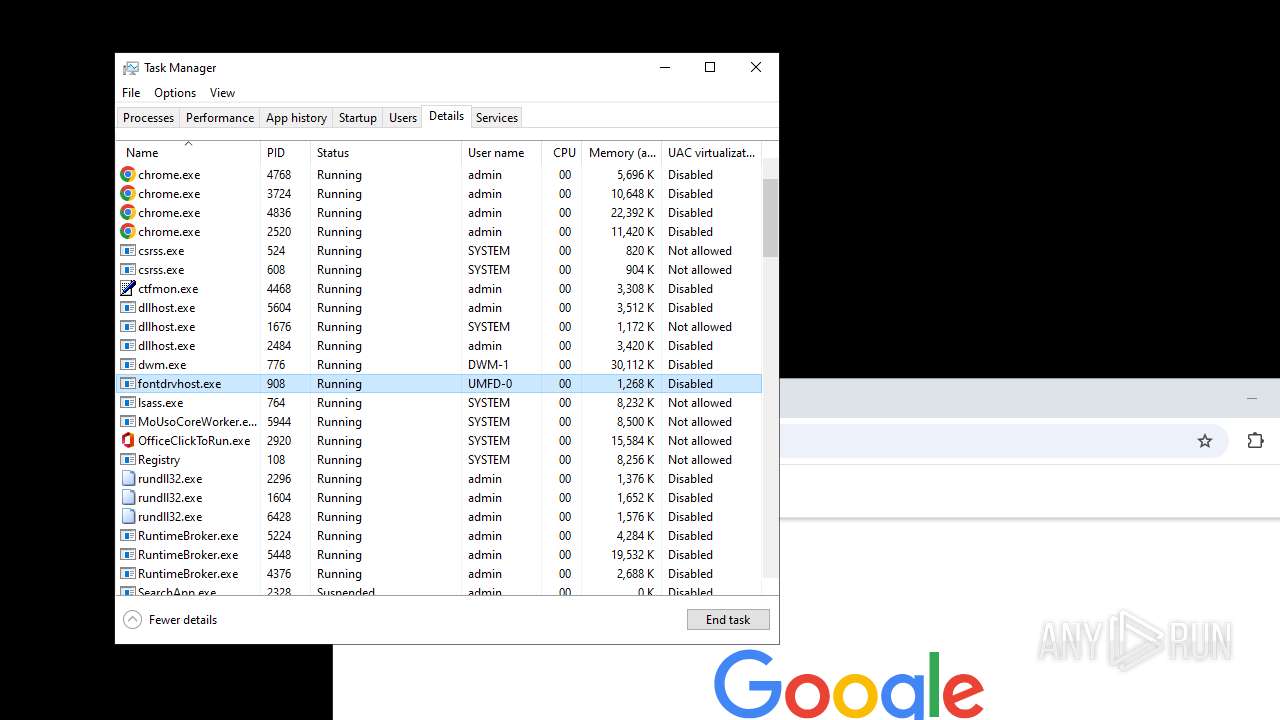
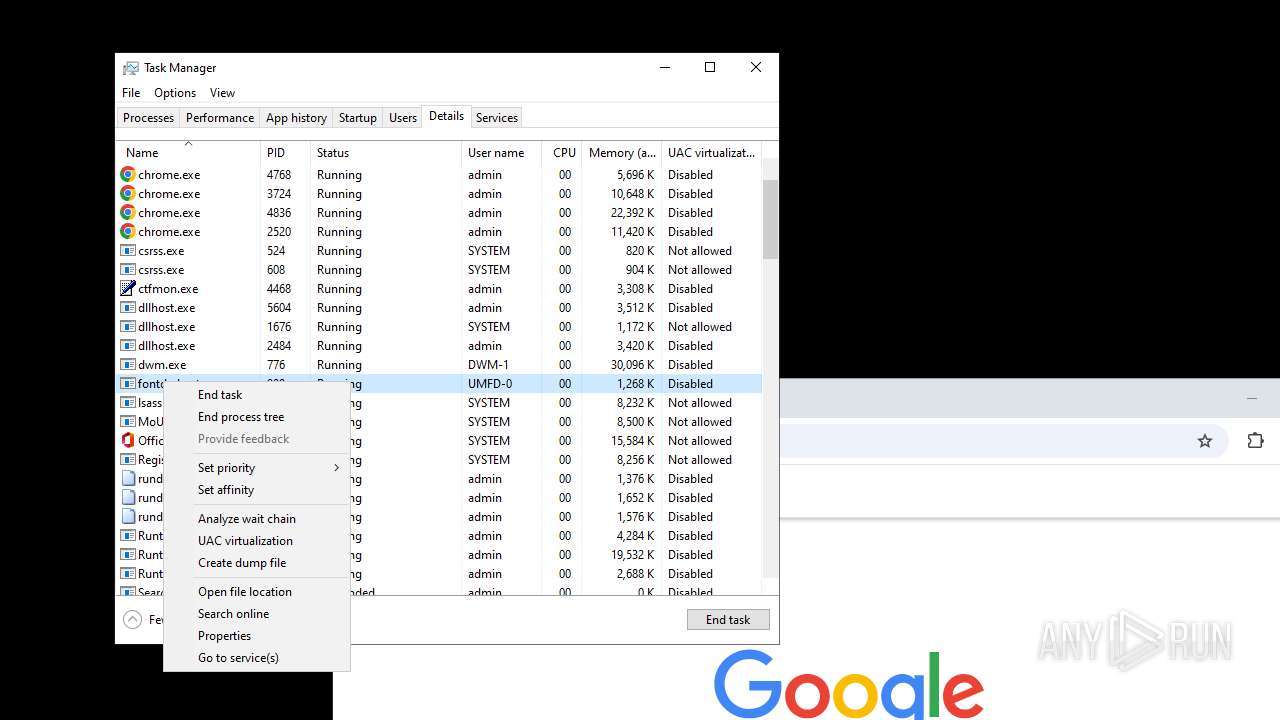
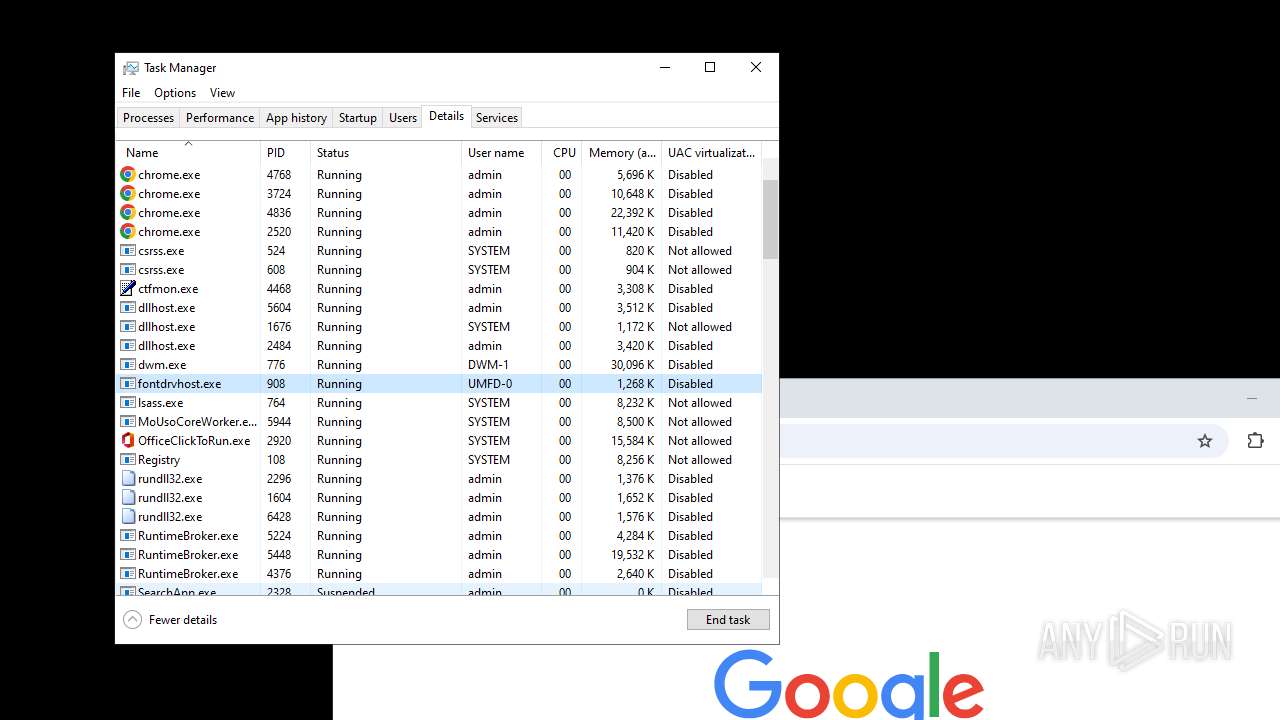
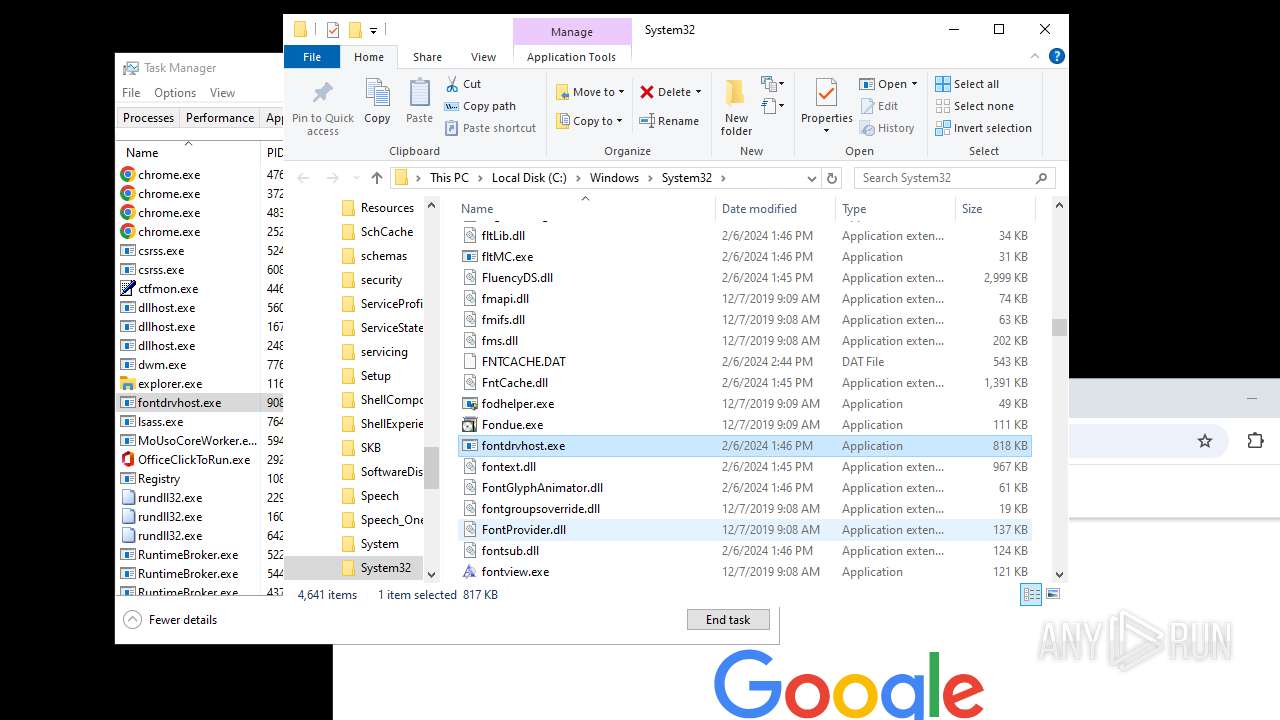
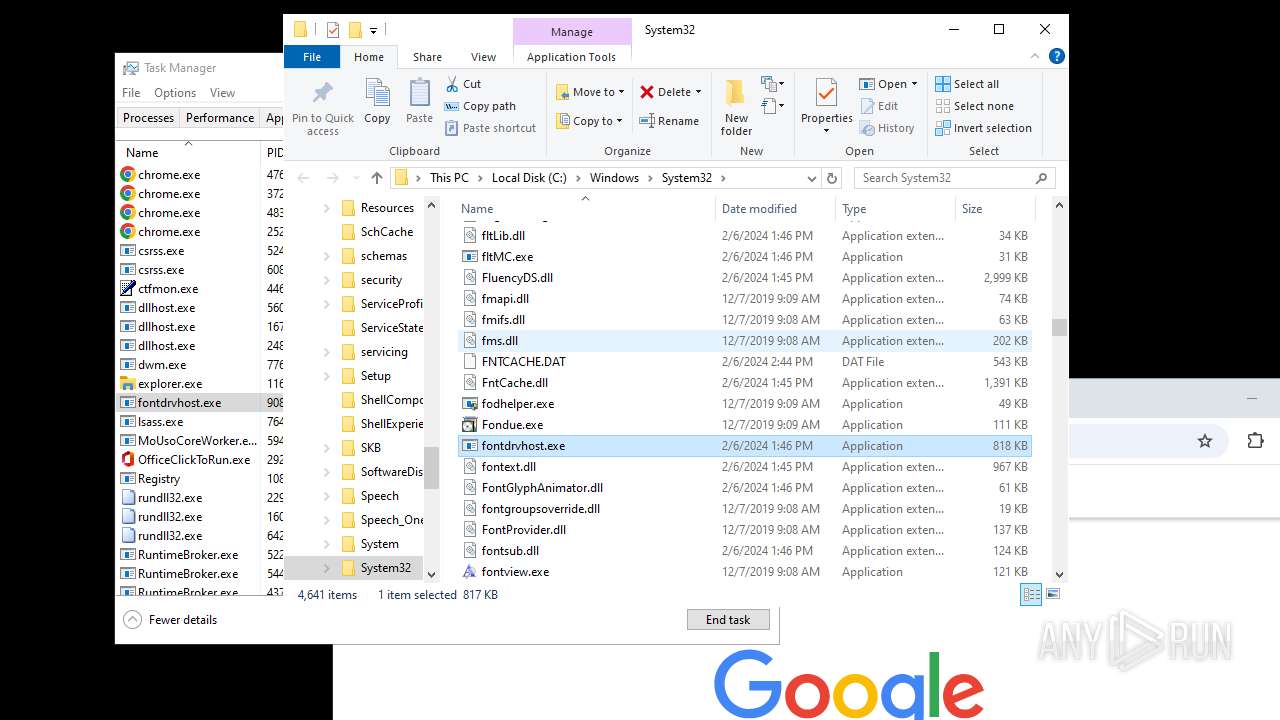
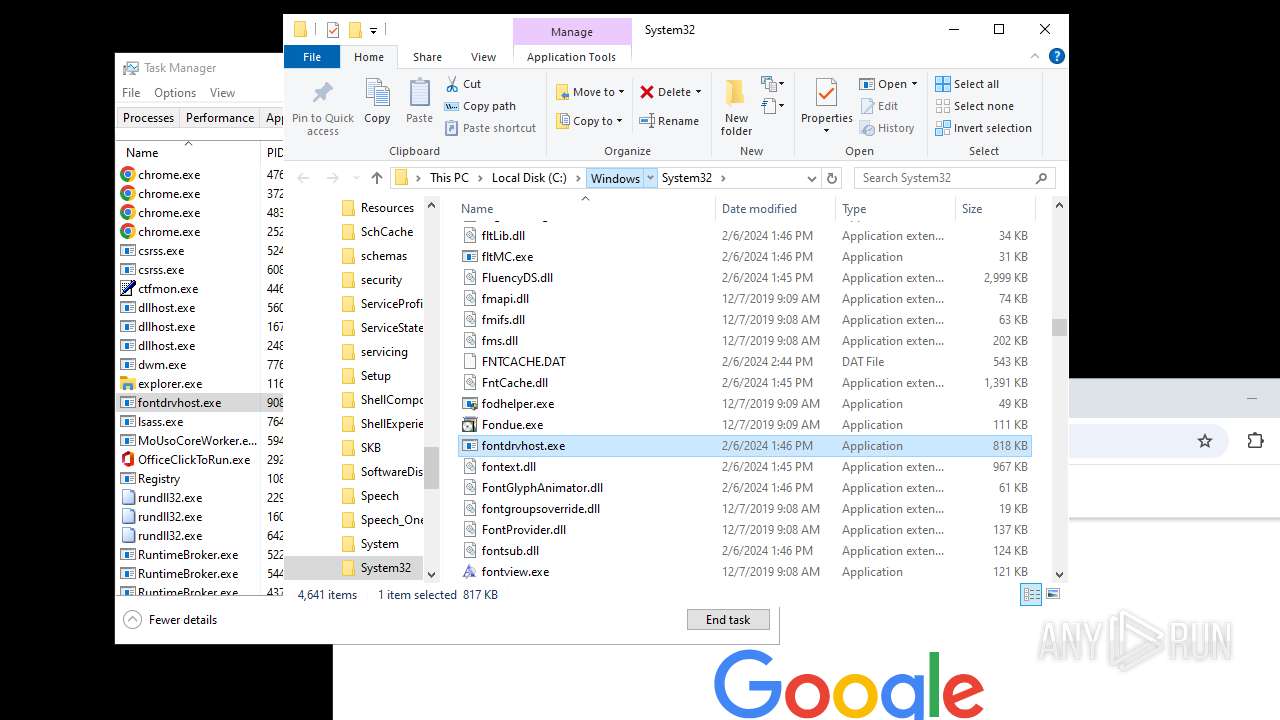
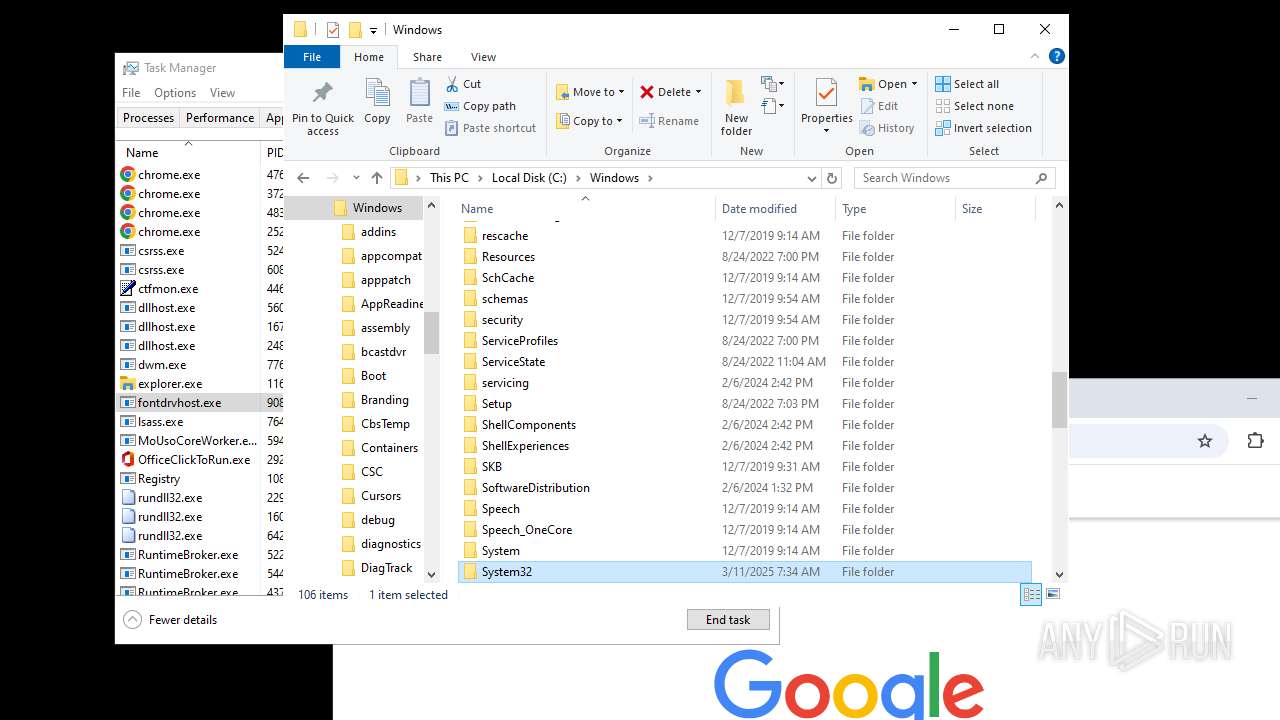
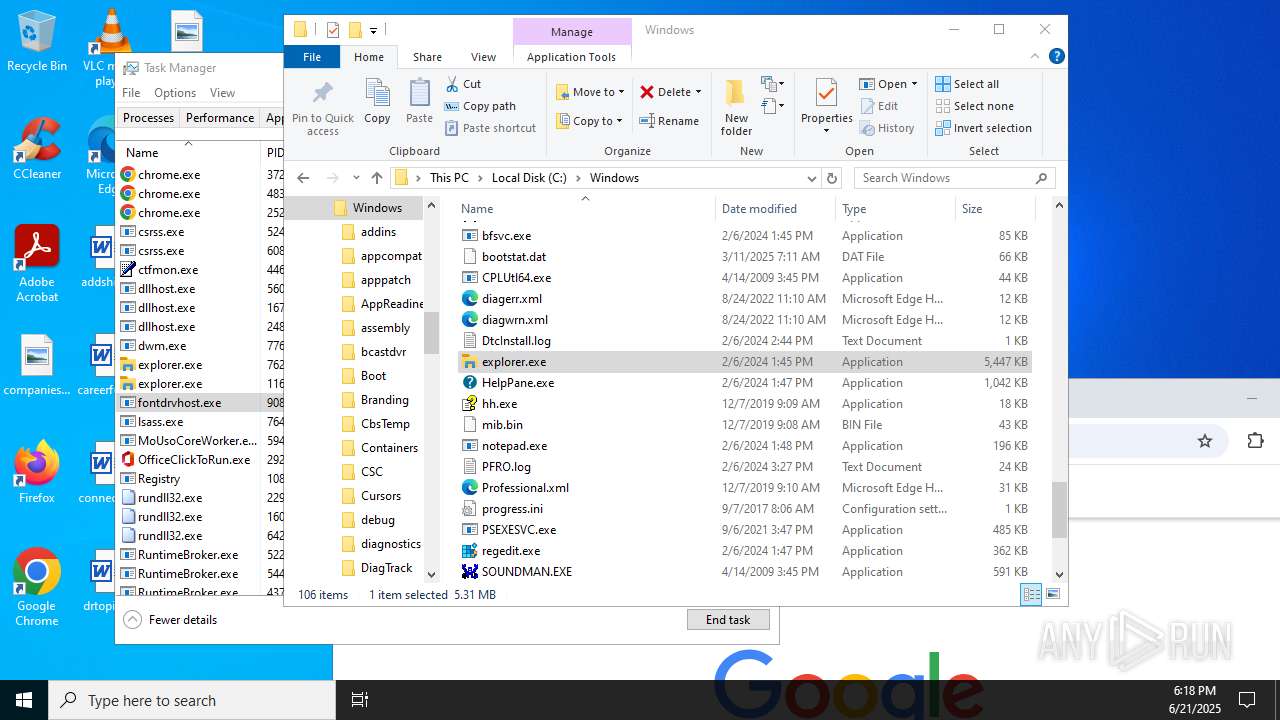
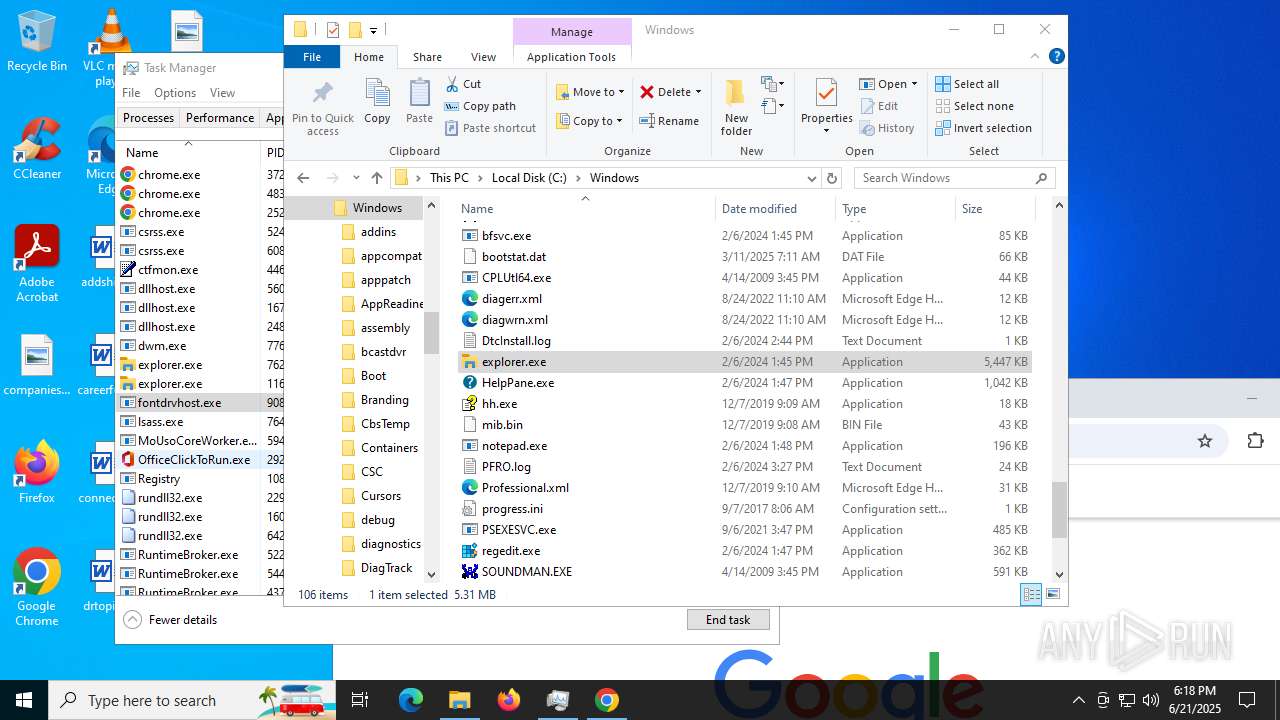
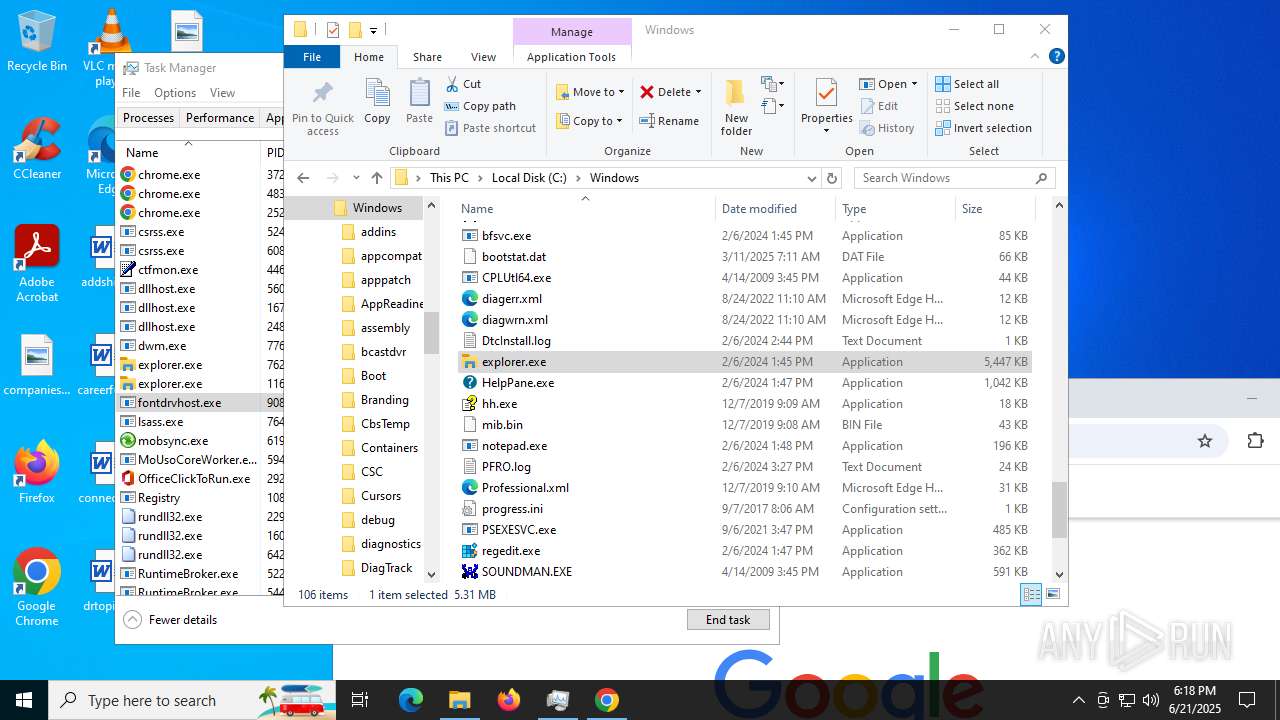
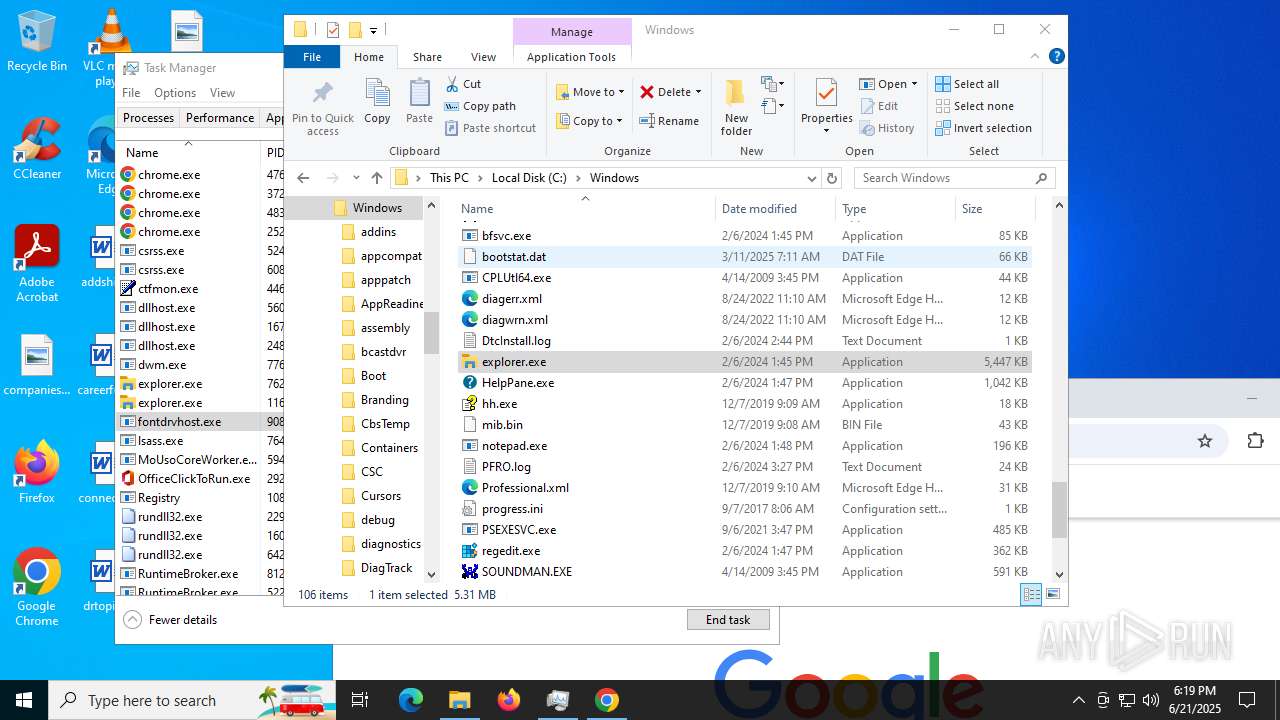
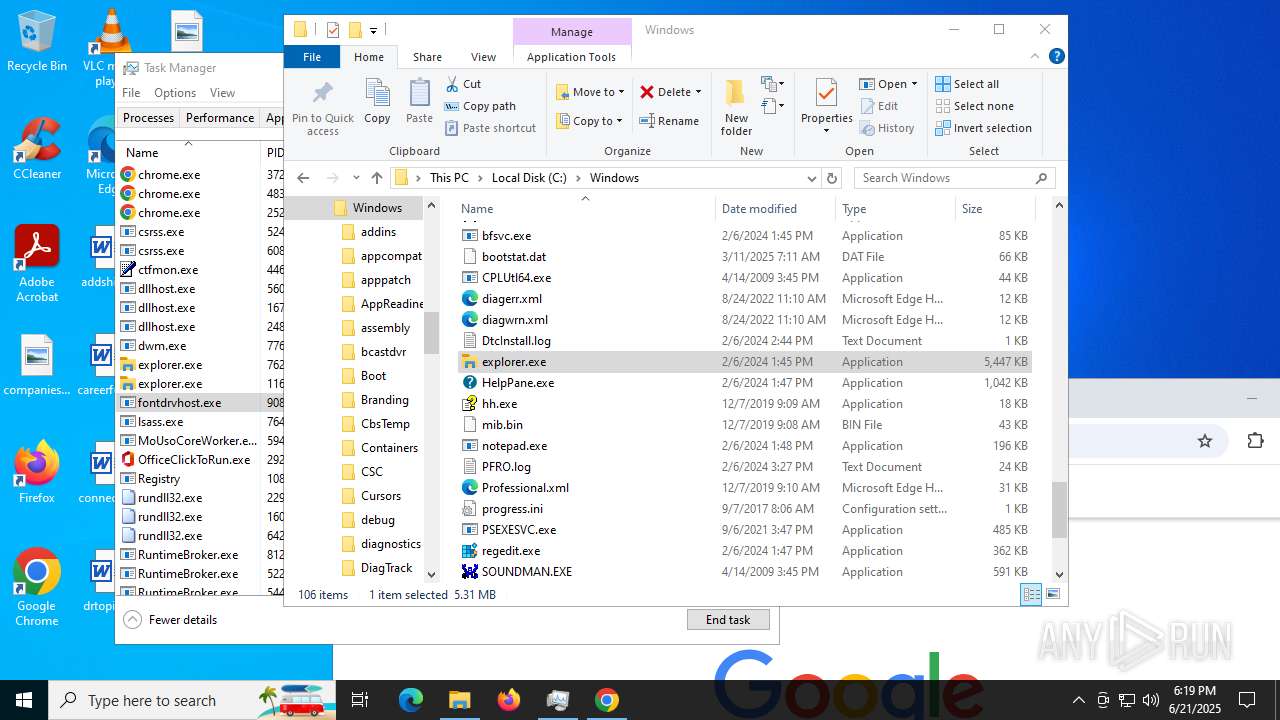
MALICIOUS
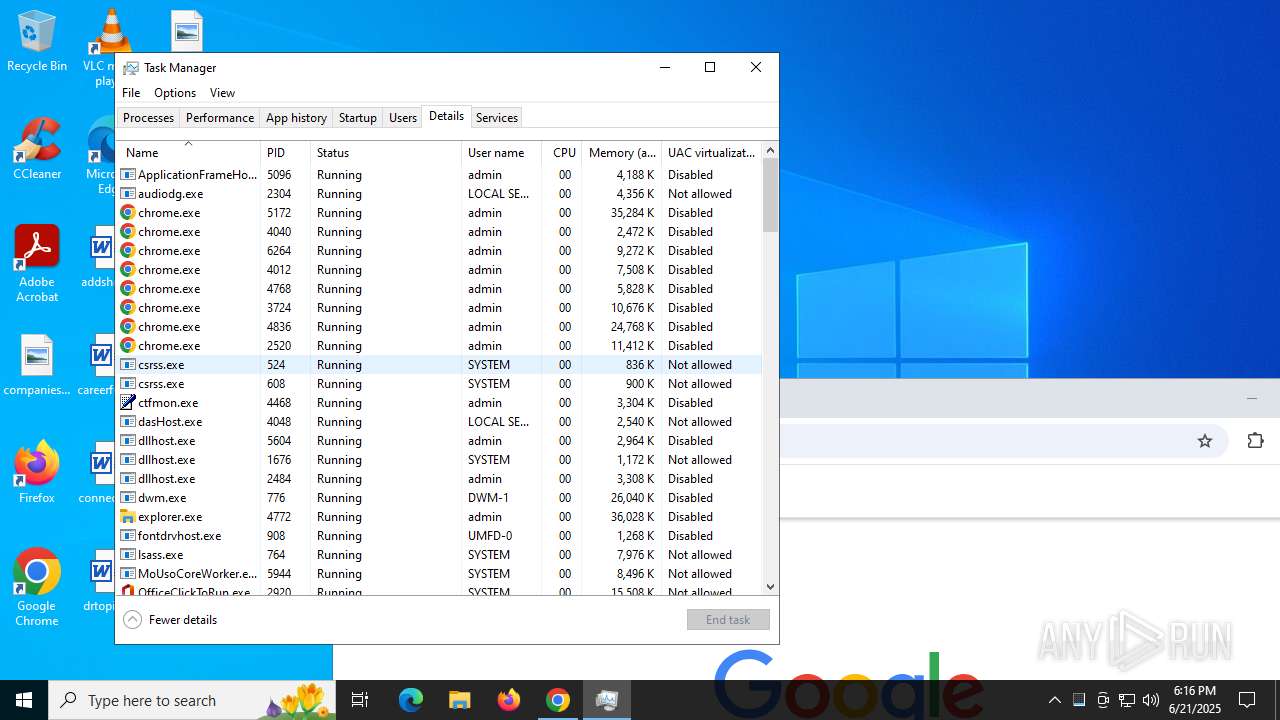
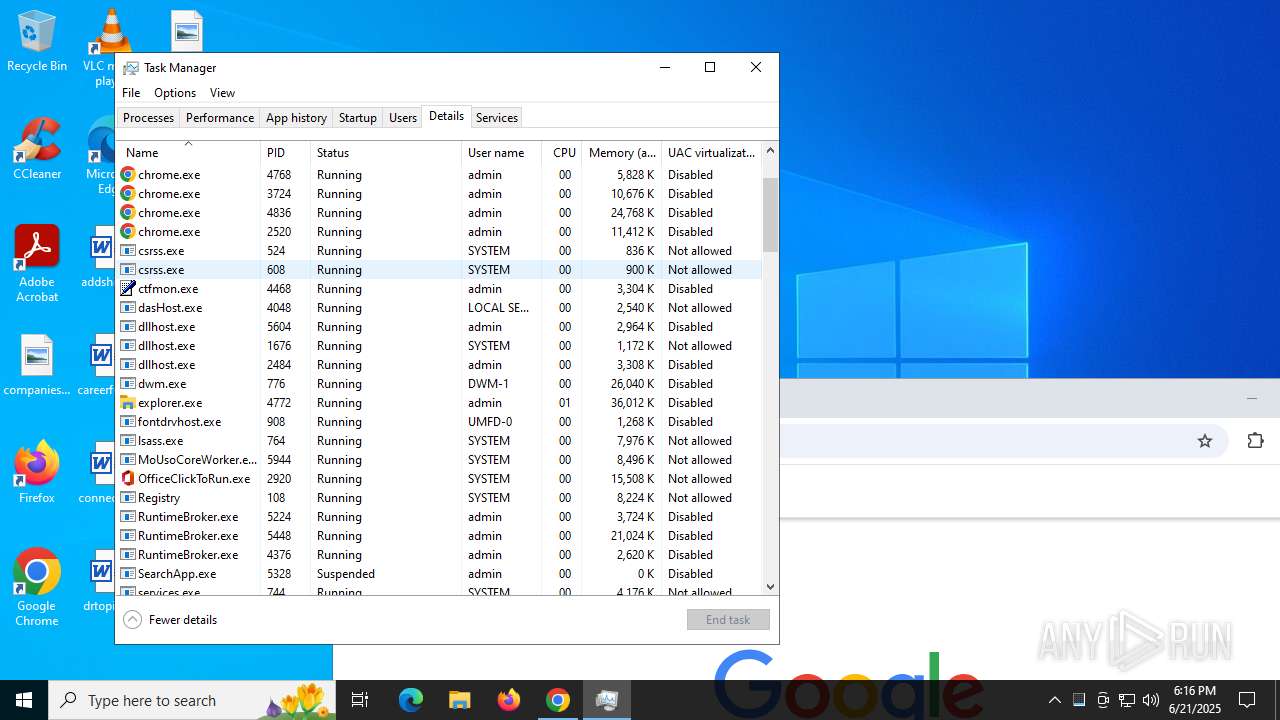
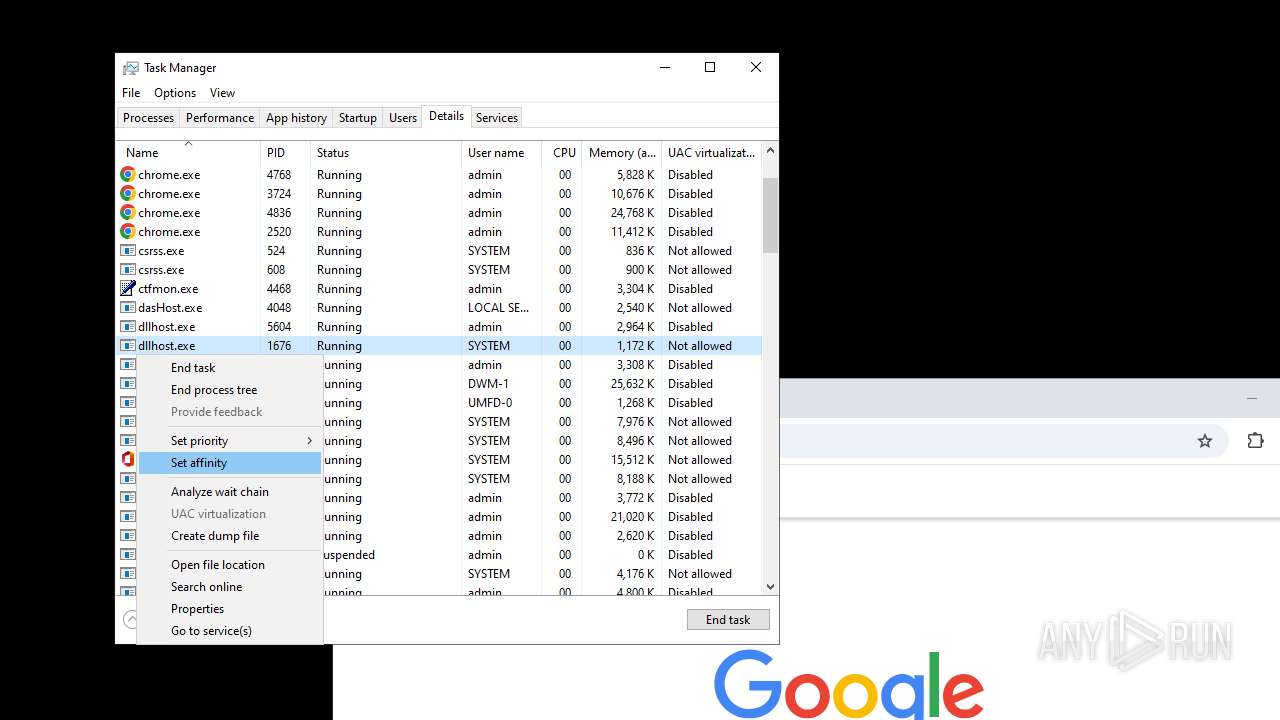
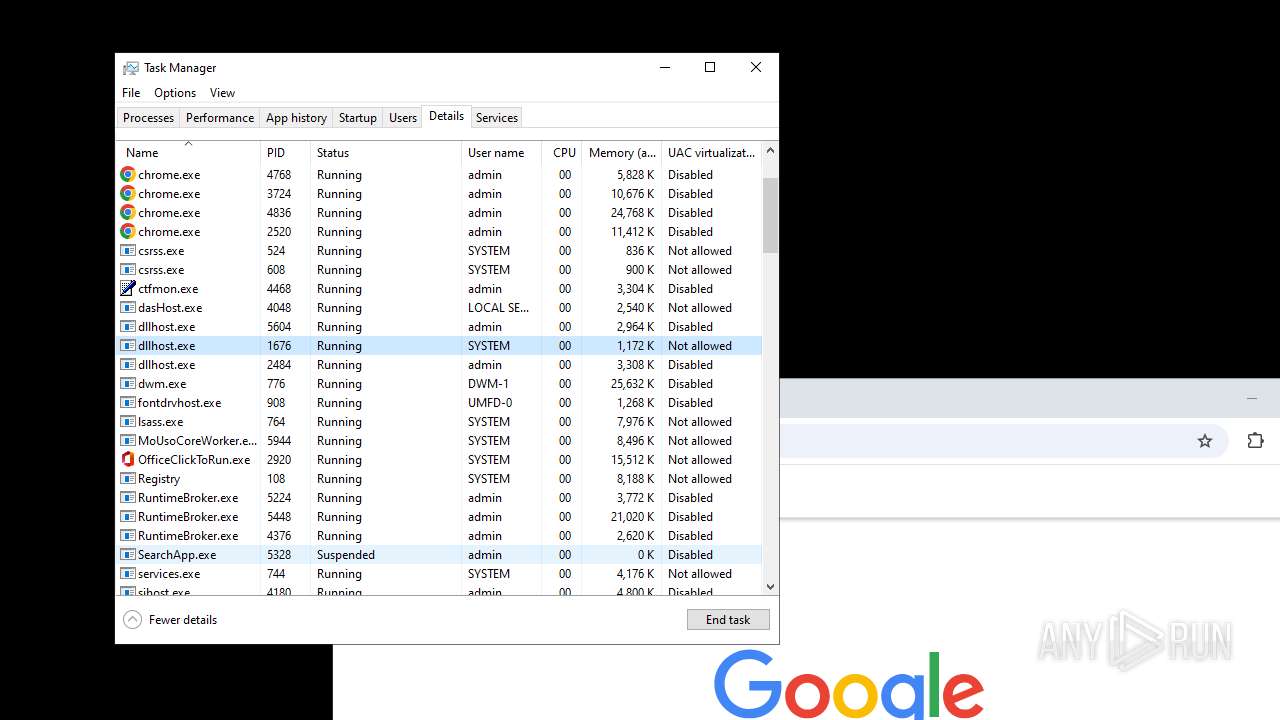
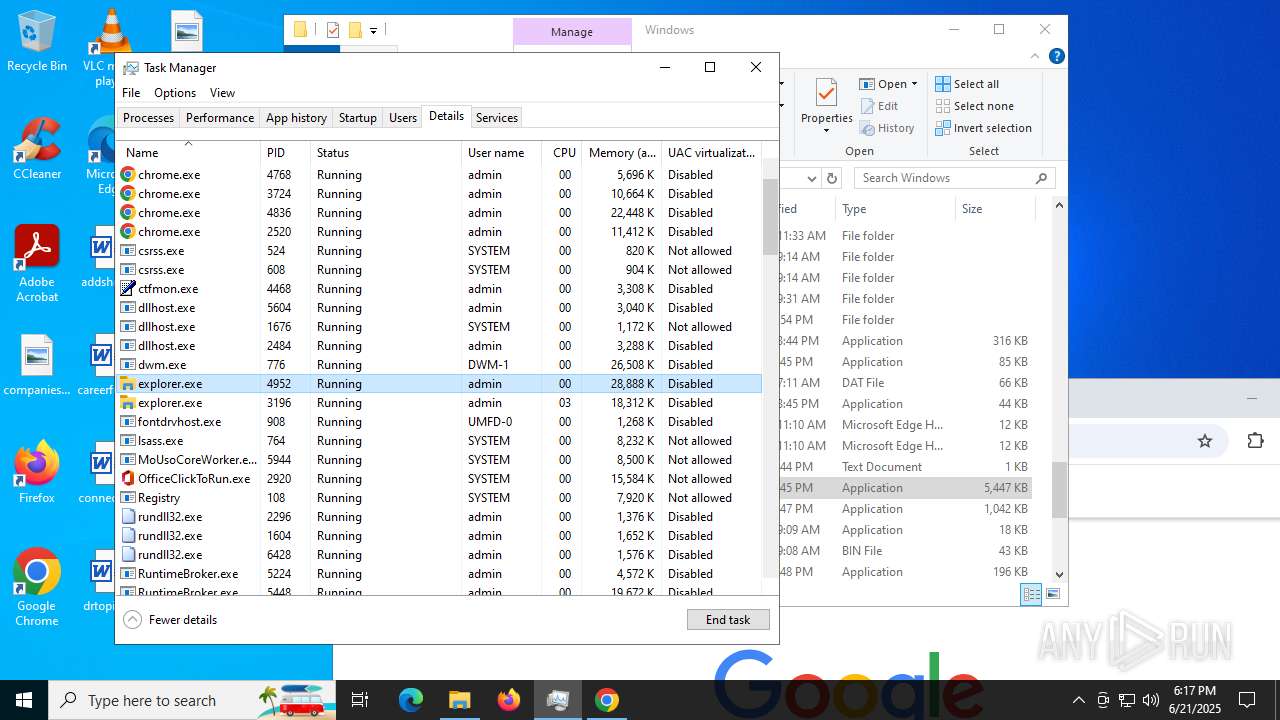
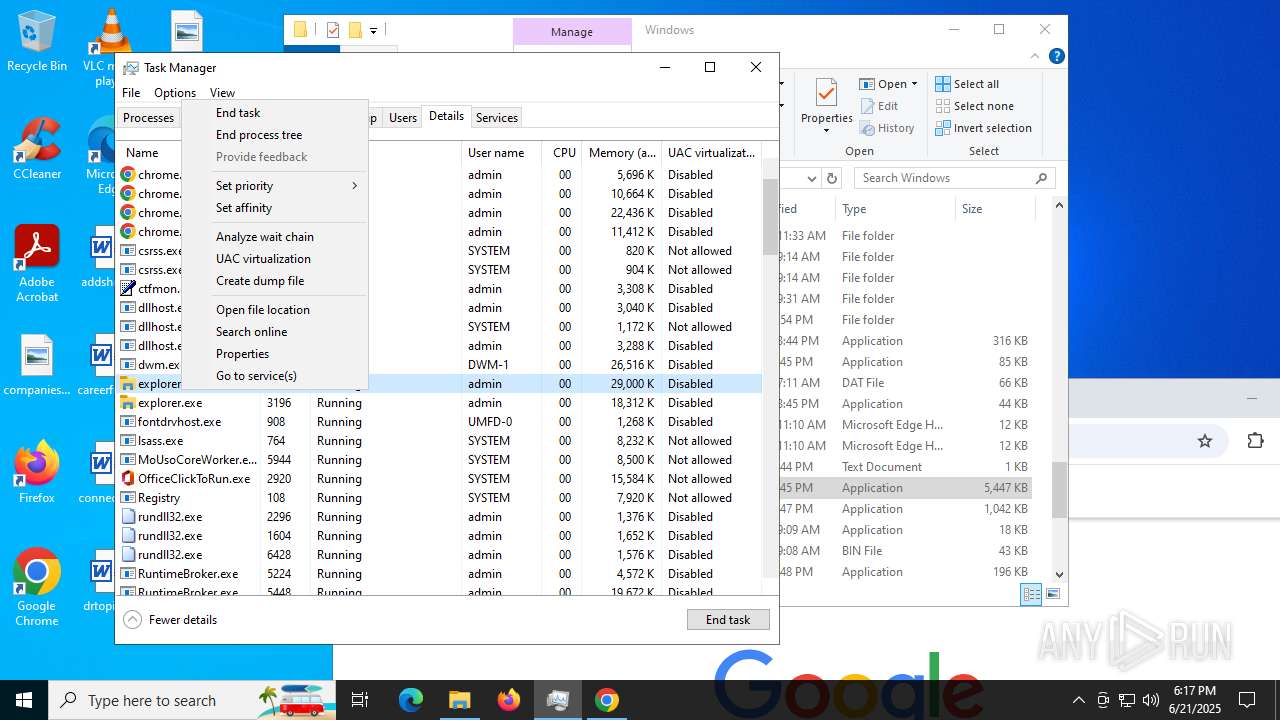
Application was injected by another process
- sihost.exe (PID: 4180)
- svchost.exe (PID: 4204)
- svchost.exe (PID: 4248)
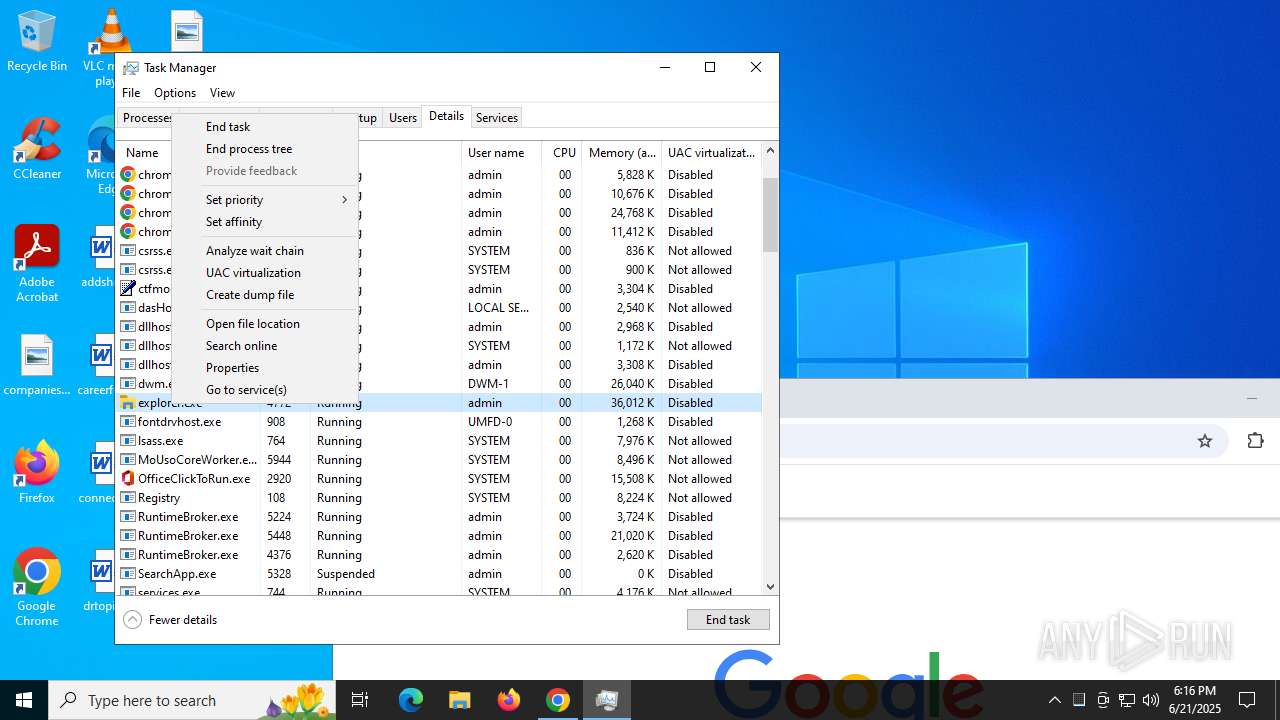
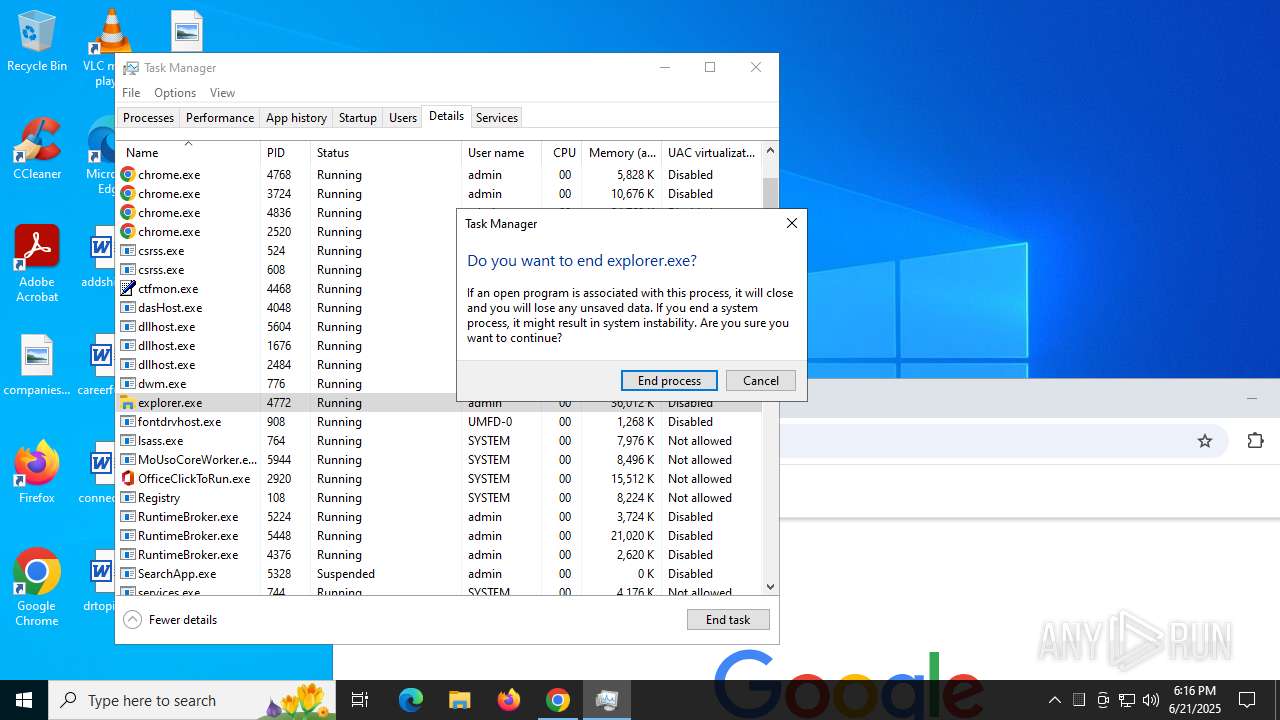
- explorer.exe (PID: 4772)
- svchost.exe (PID: 5048)
- StartMenuExperienceHost.exe (PID: 5160)
- RuntimeBroker.exe (PID: 5224)
- SearchApp.exe (PID: 5328)
- RuntimeBroker.exe (PID: 5448)
- dllhost.exe (PID: 5604)
- RuntimeBroker.exe (PID: 4376)
- ApplicationFrameHost.exe (PID: 5096)
- UserOOBEBroker.exe (PID: 5936)
- svchost.exe (PID: 6984)
- dllhost.exe (PID: 2484)
- TextInputHost.exe (PID: 2772)
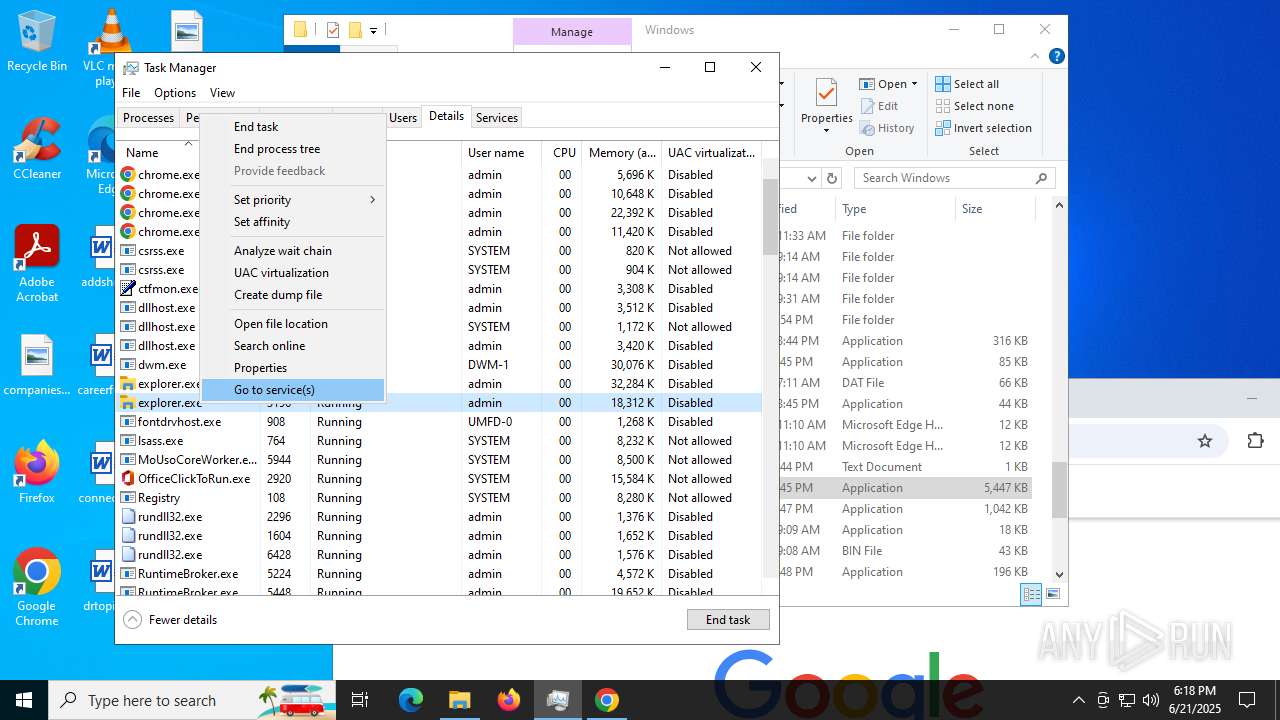
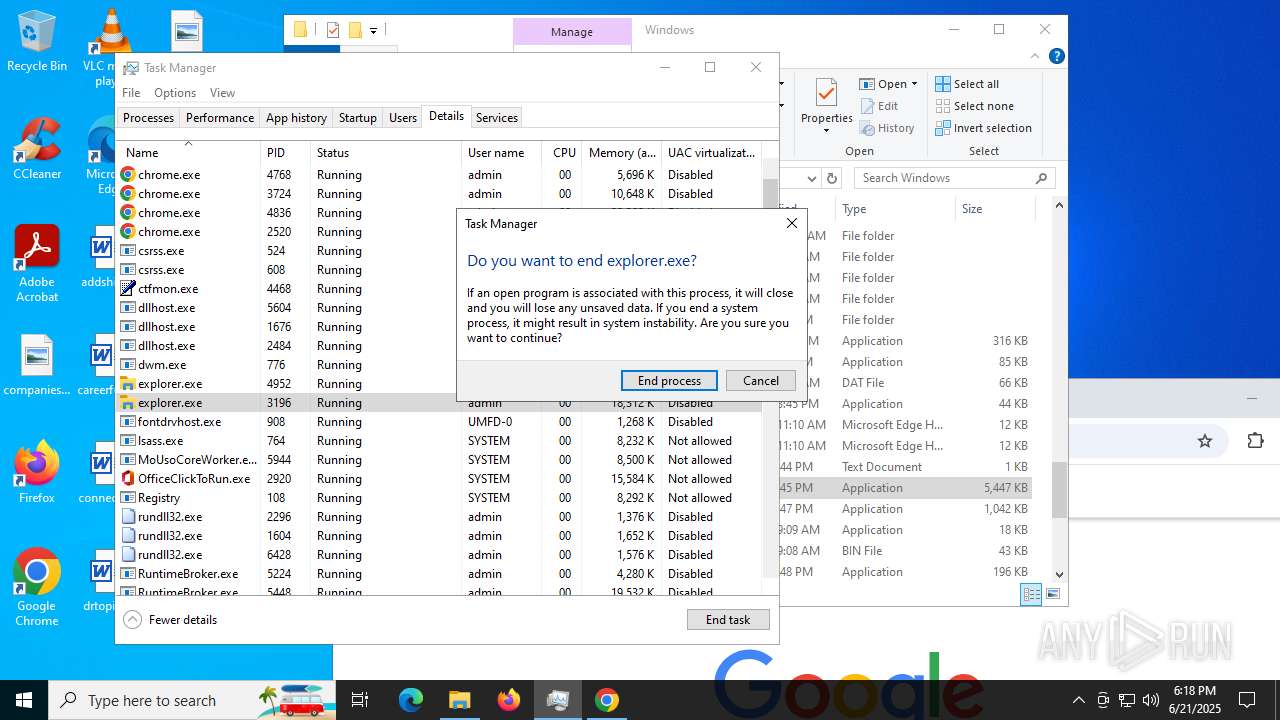
Runs injected code in another process
- ed7b275f-7e7b-4fa9-9abf-676847530890.exe (PID: 5300)
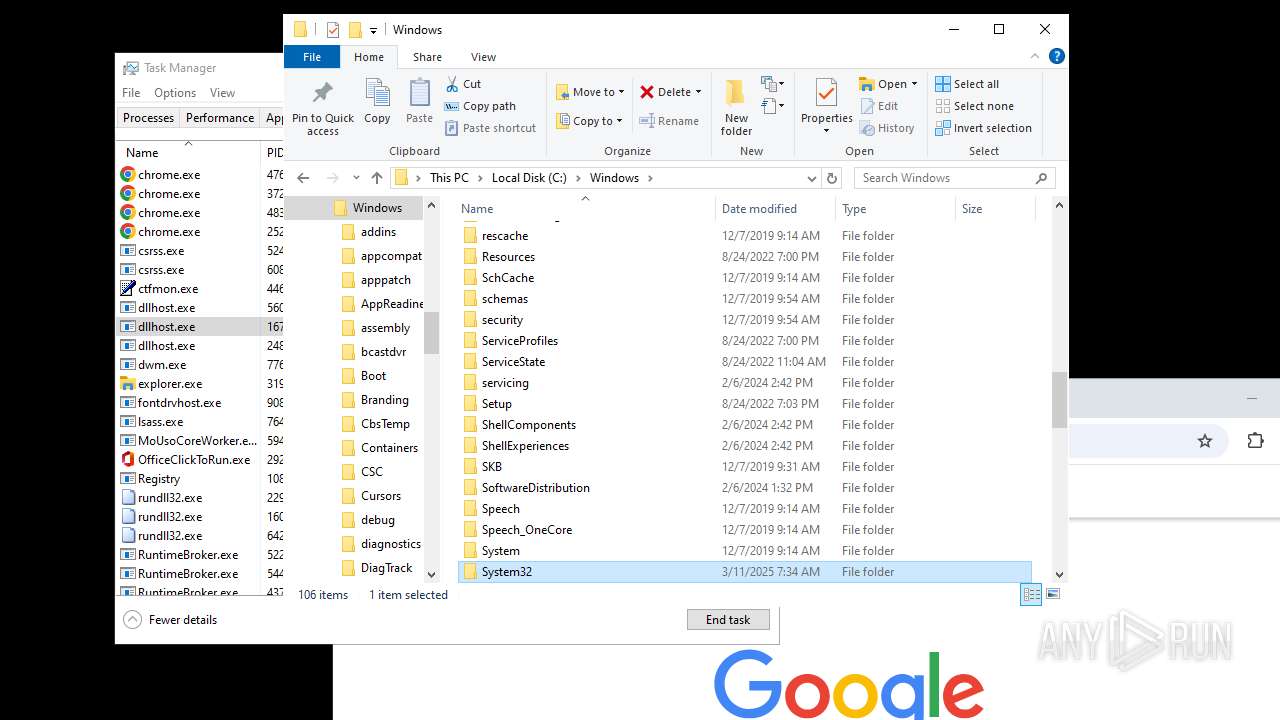
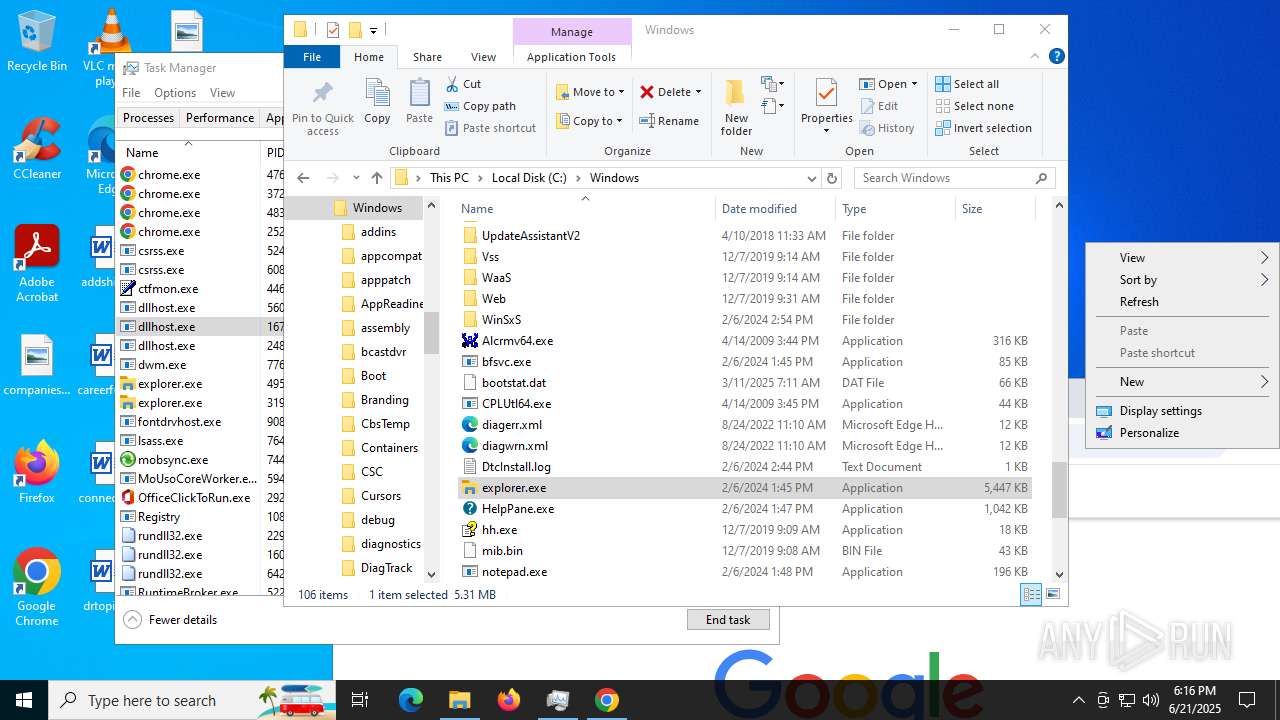
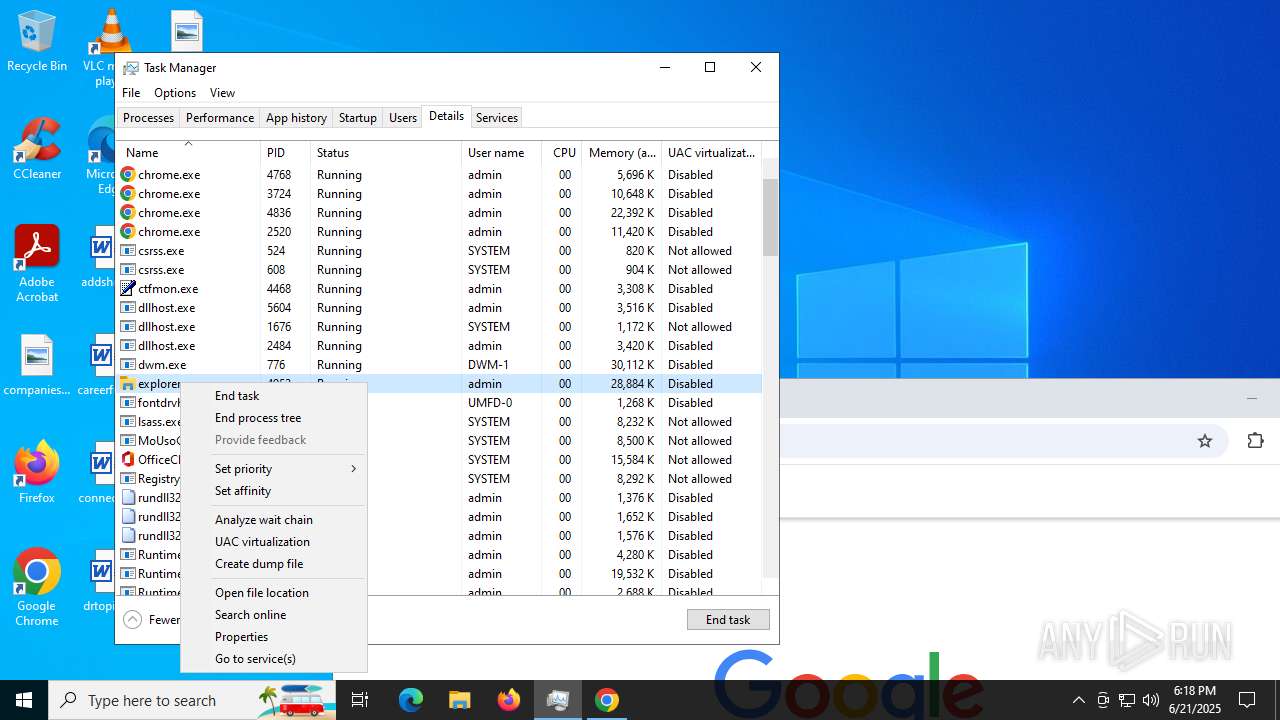
Changes the autorun value in the registry
- ed7b275f-7e7b-4fa9-9abf-676847530890.exe (PID: 5300)
- explorer.exe (PID: 4772)
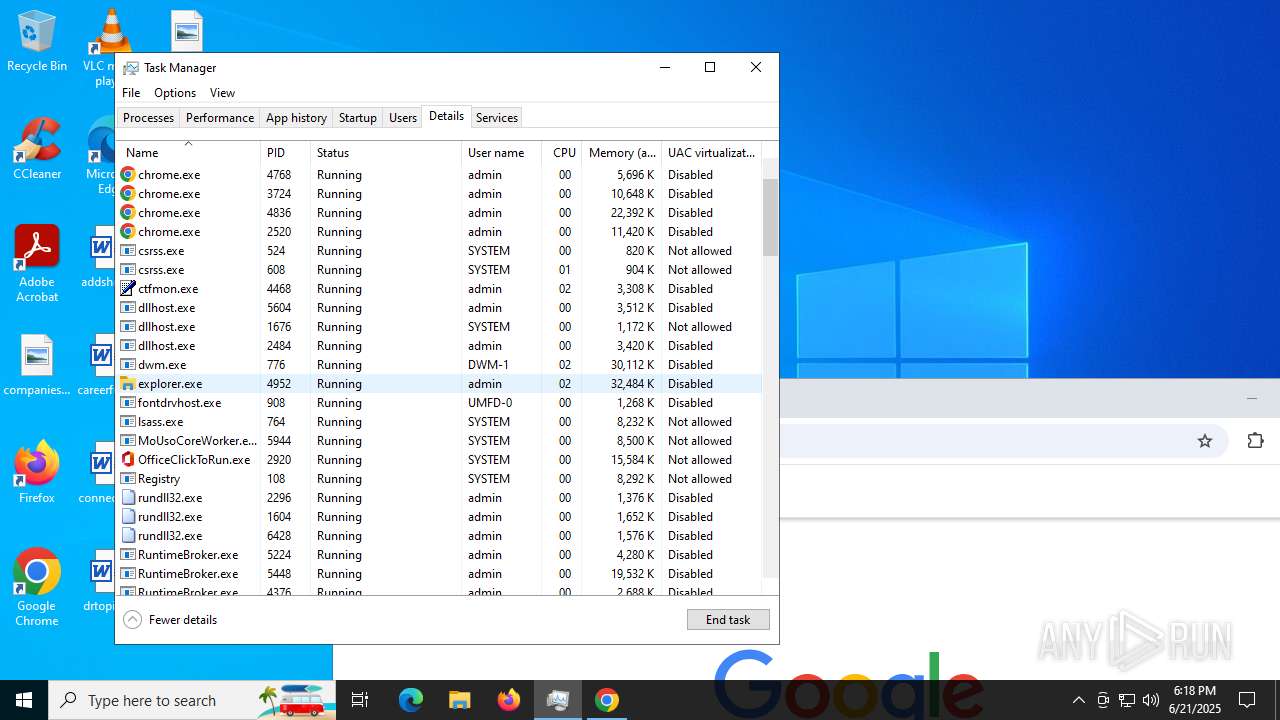
- explorer.exe (PID: 3196)
- explorer.exe (PID: 1160)
DIAMOTRIX has been detected (SURICATA)
- explorer.exe (PID: 4772)
- explorer.exe (PID: 3196)
- explorer.exe (PID: 1160)
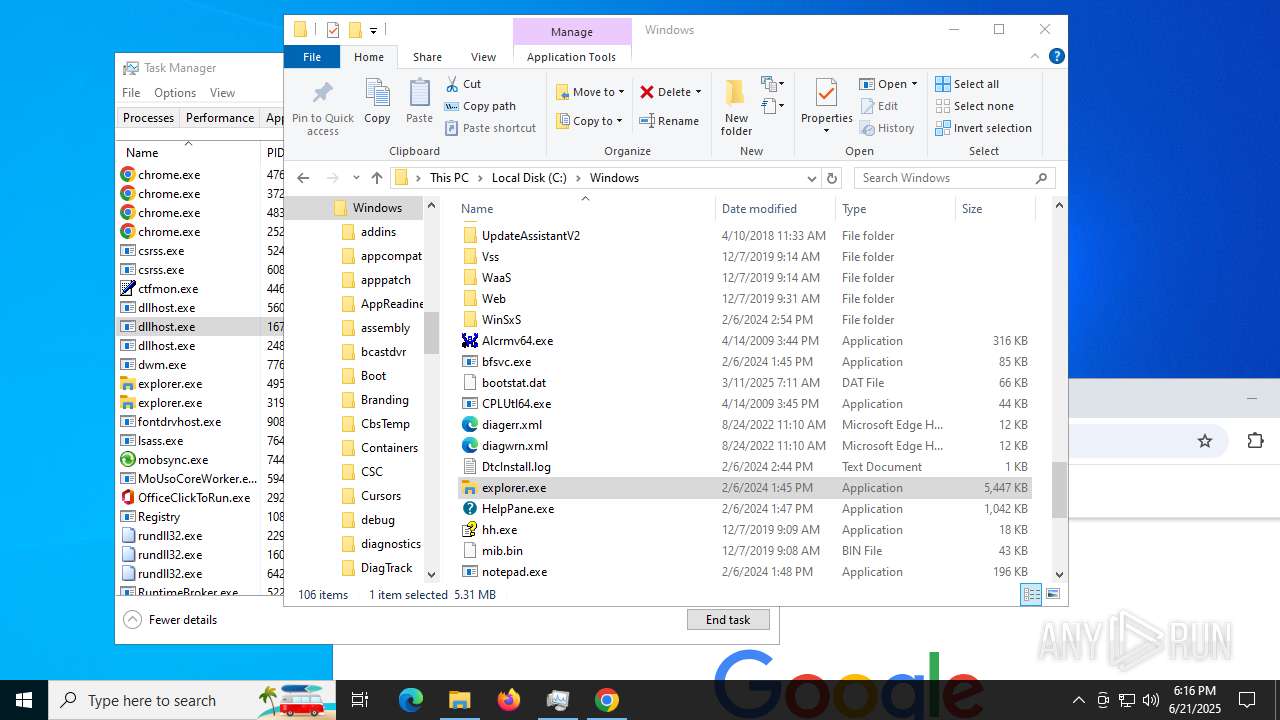
SUSPICIOUS
Found regular expressions for crypto-addresses (YARA)
- ed7b275f-7e7b-4fa9-9abf-676847530890.exe (PID: 5300)
- explorer.exe (PID: 4952)
- explorer.exe (PID: 7628)
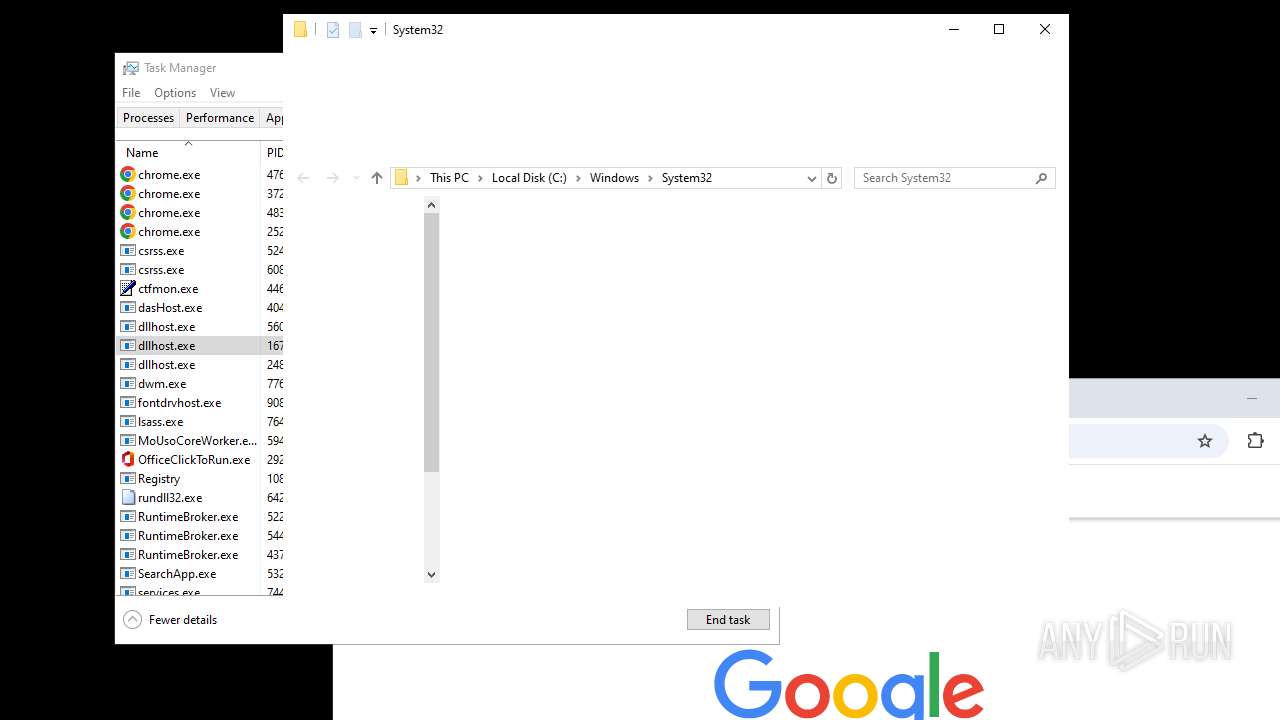
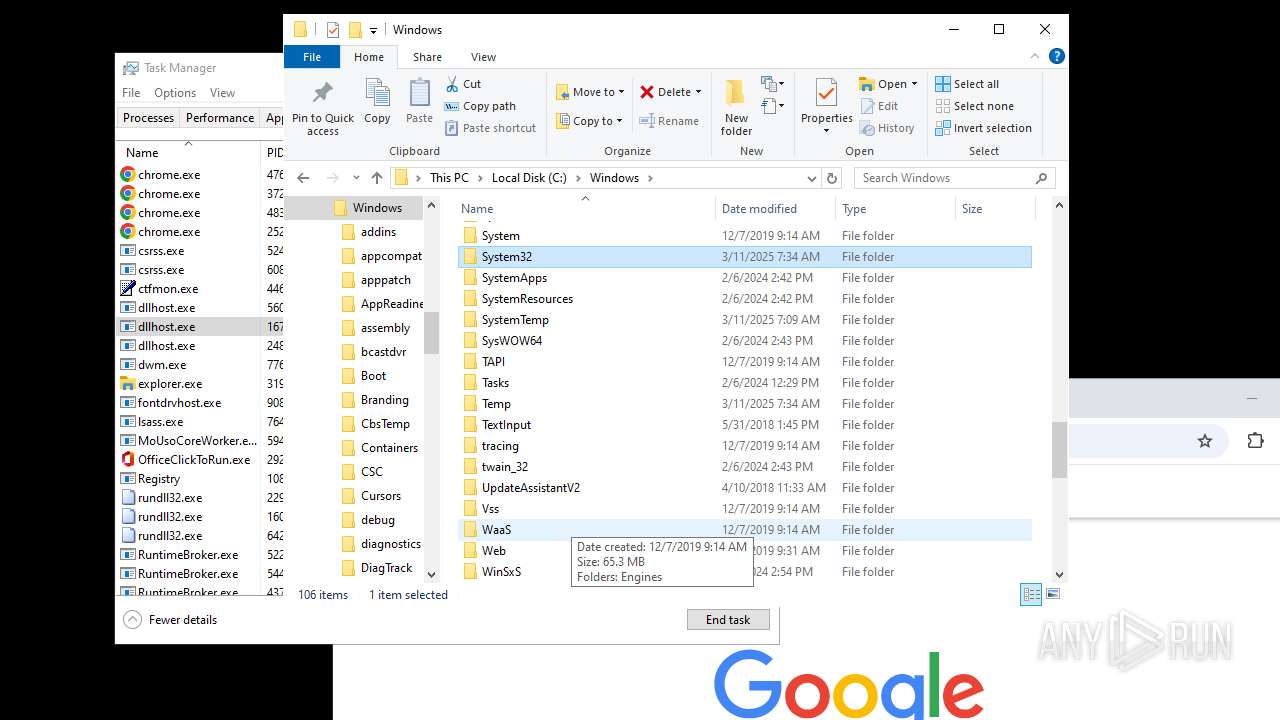
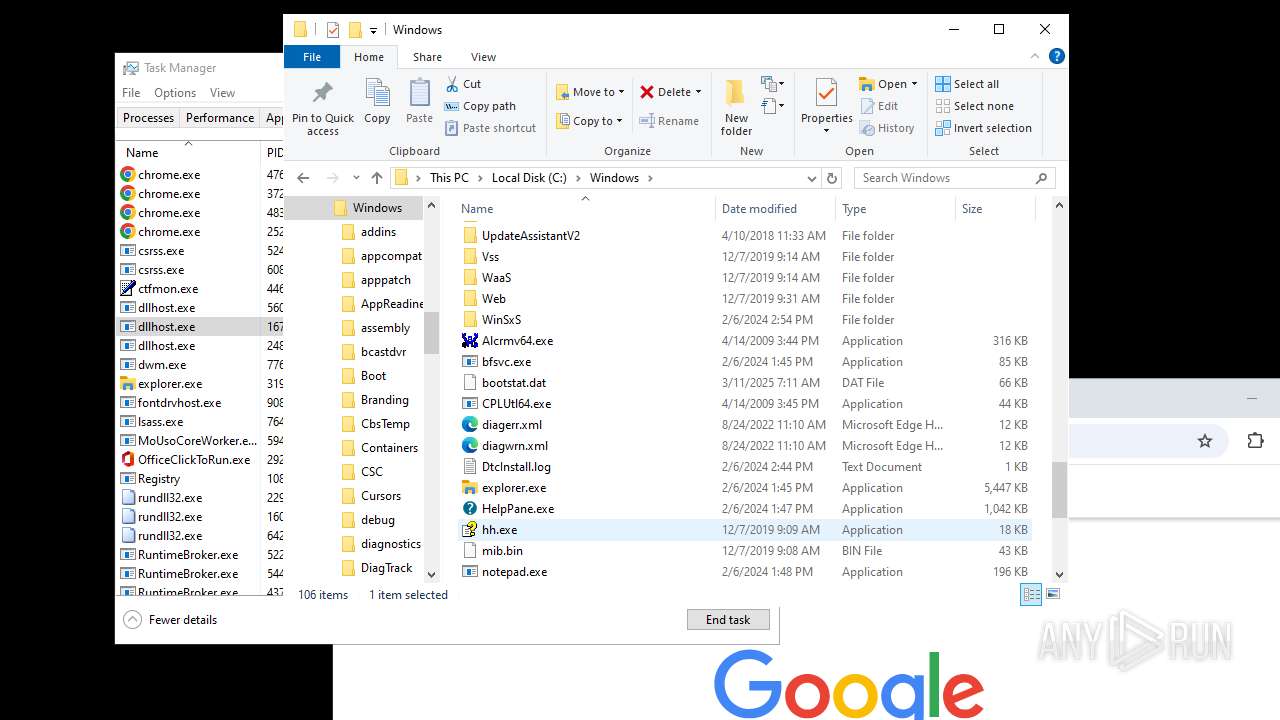
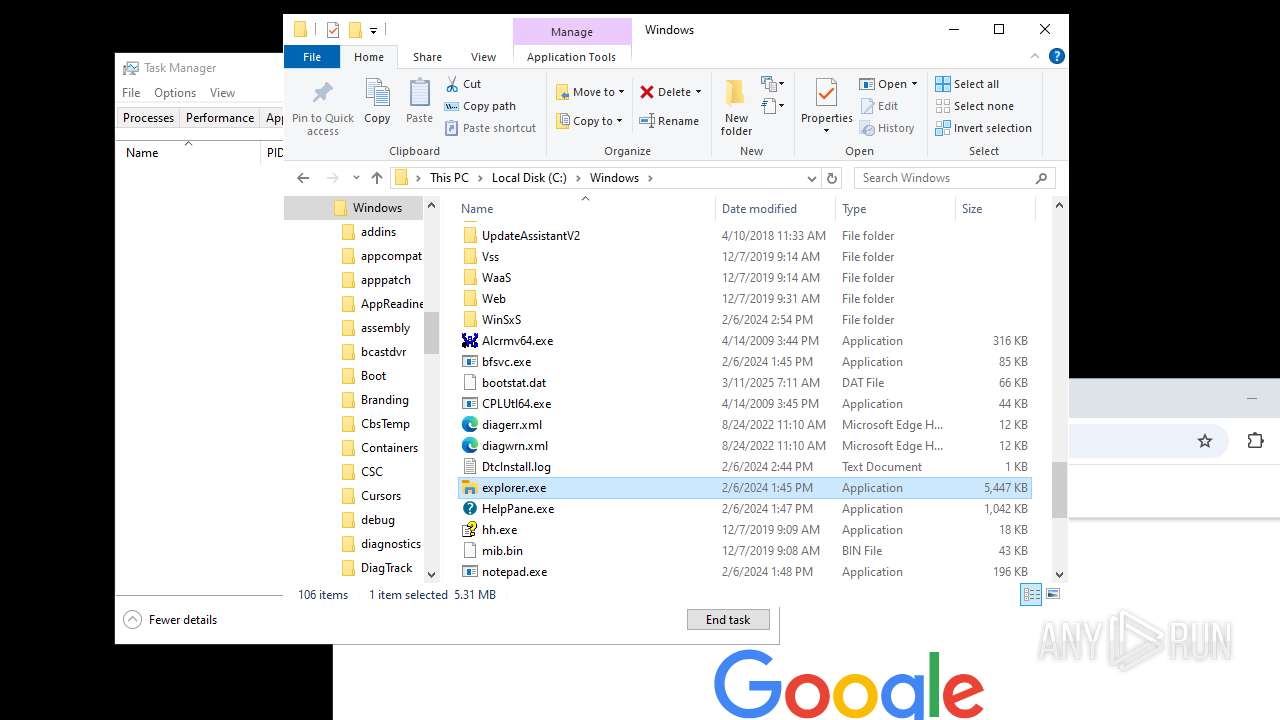
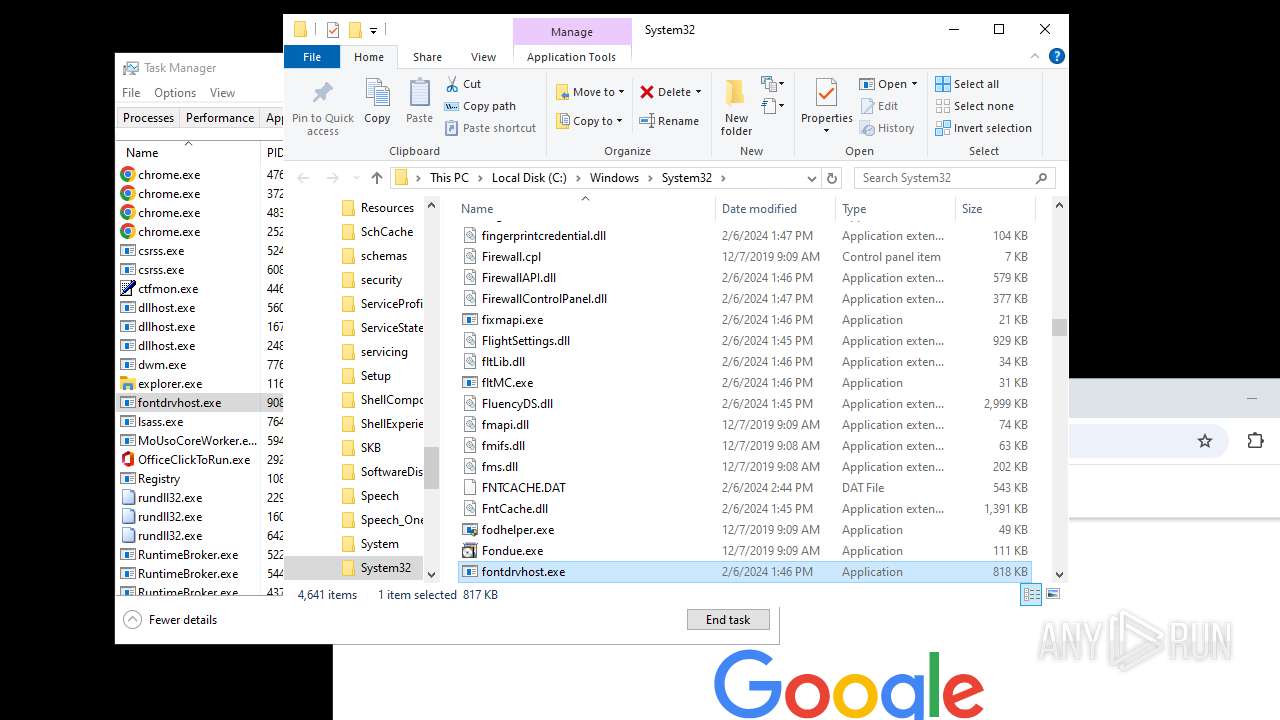
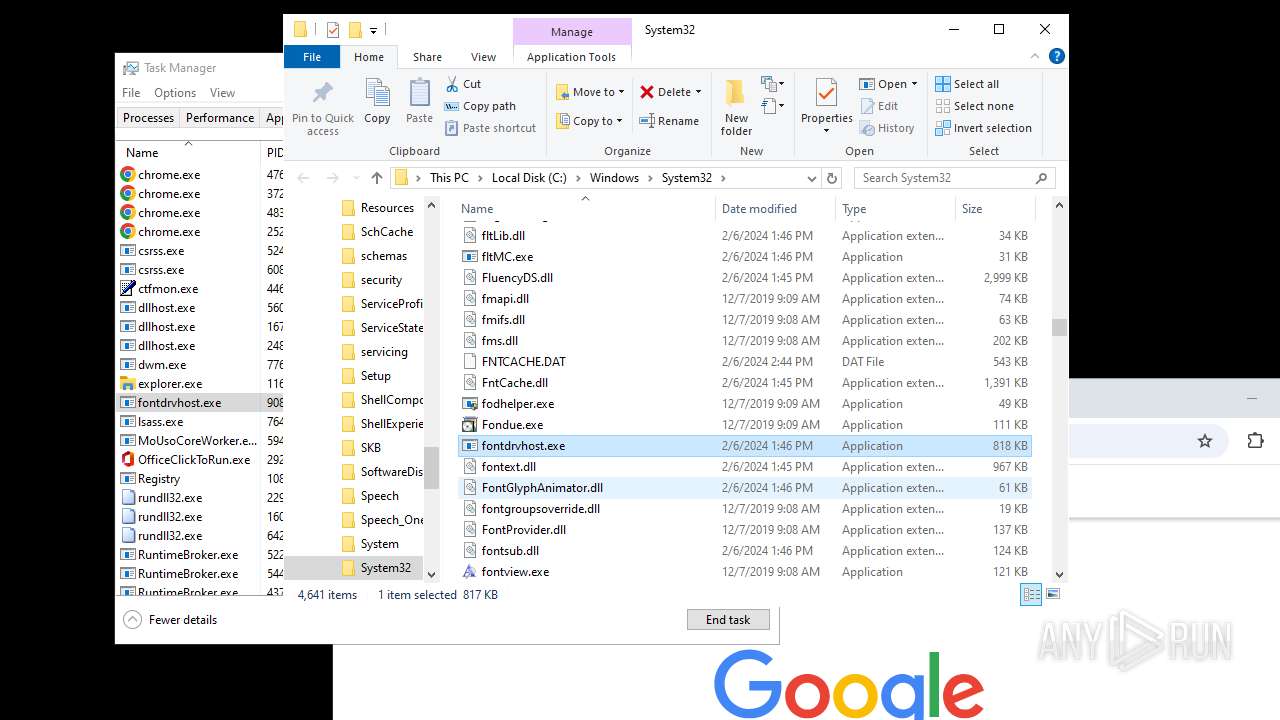
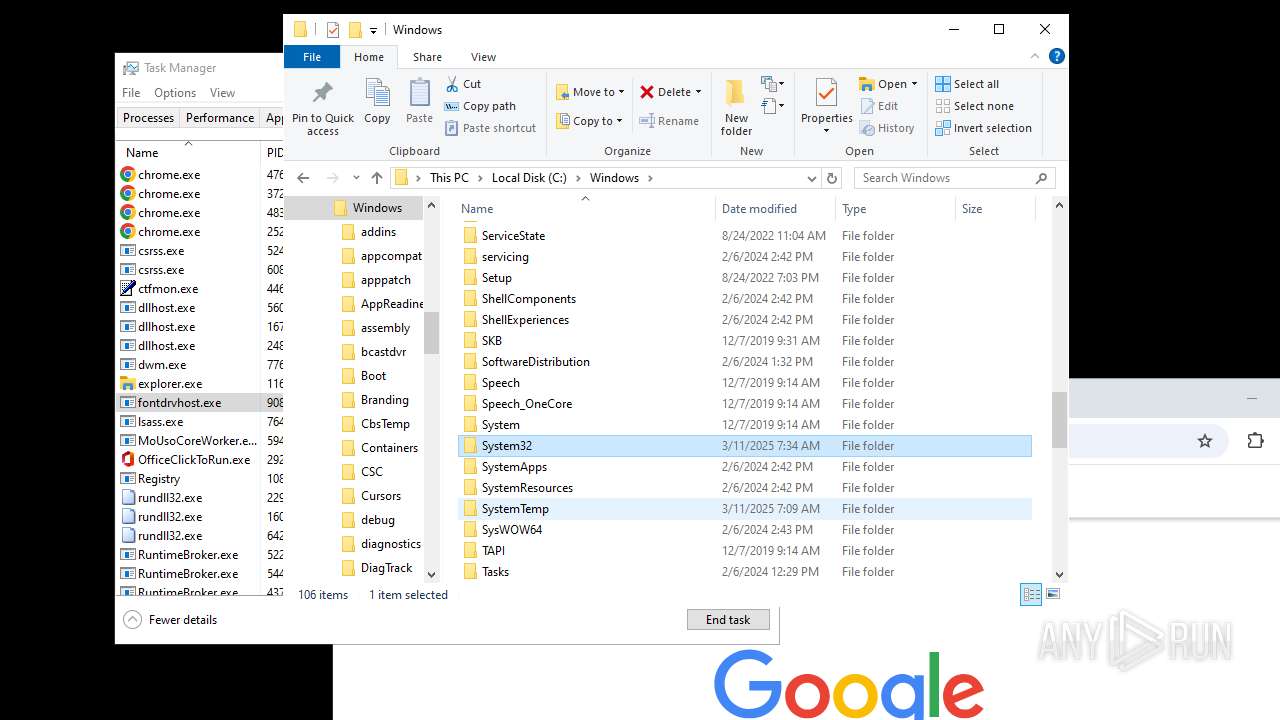
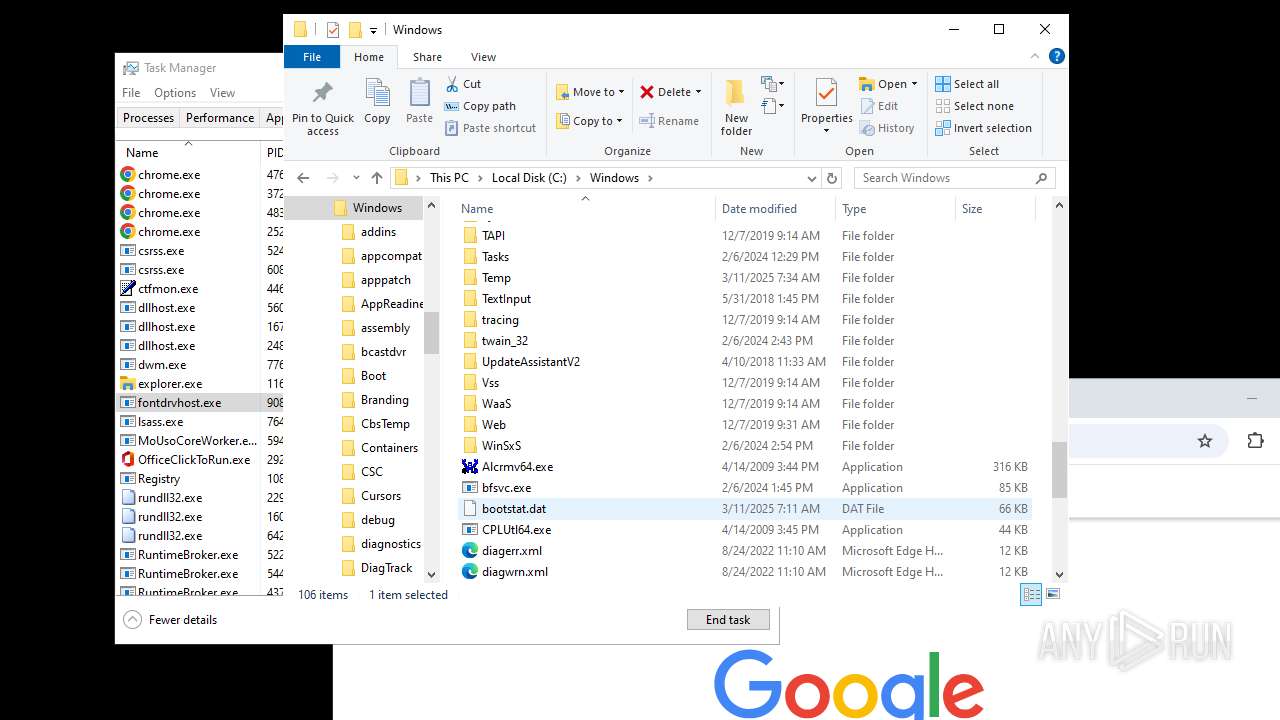
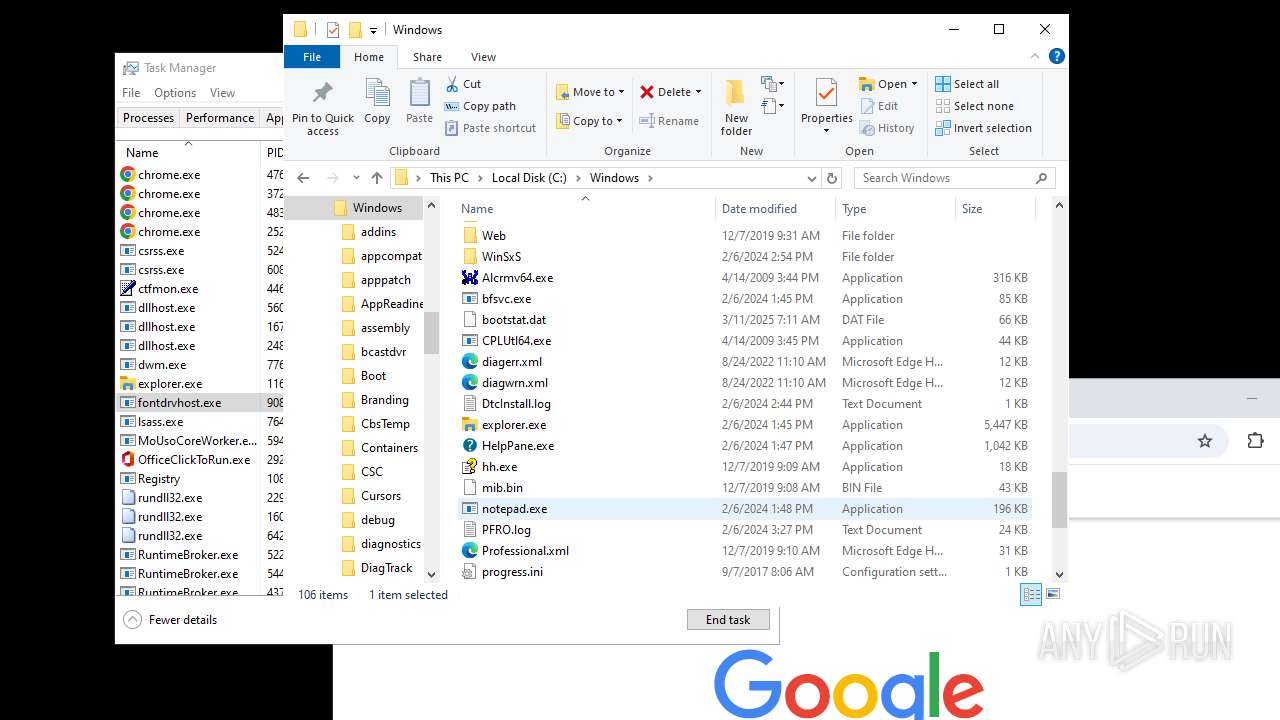
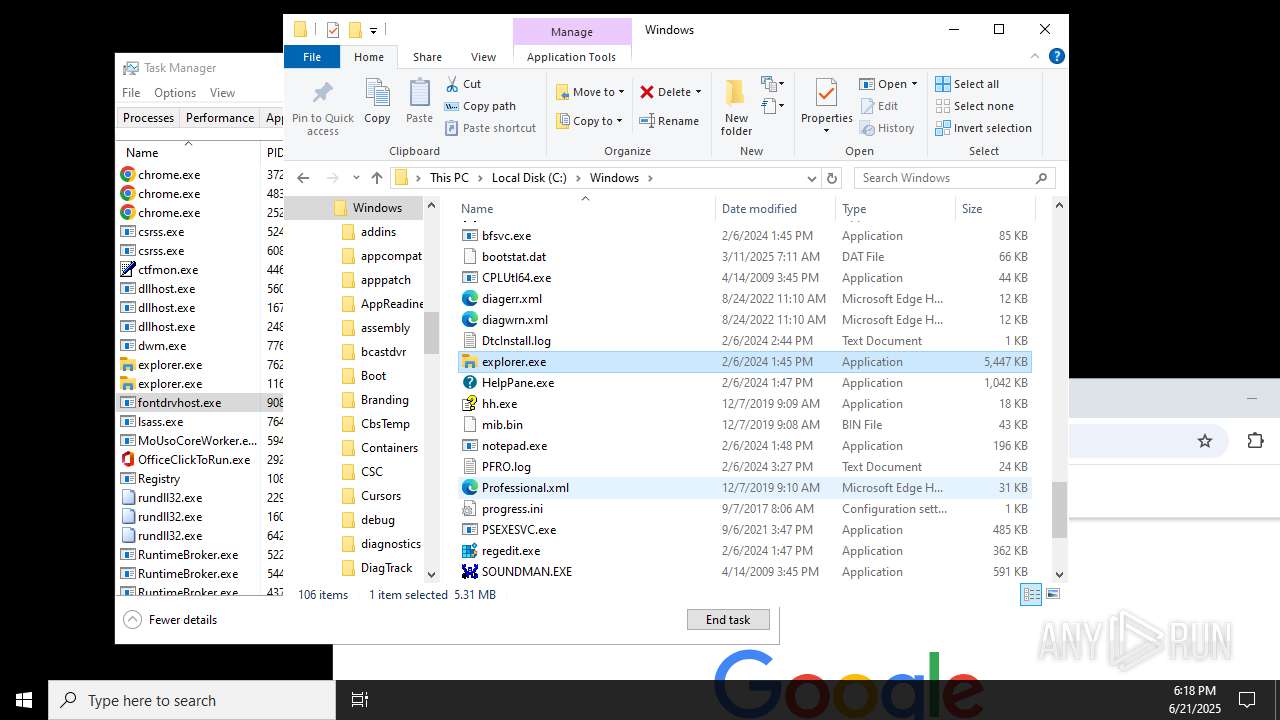
Executable content was dropped or overwritten
- ed7b275f-7e7b-4fa9-9abf-676847530890.exe (PID: 5300)
Connects to the server without a host name
- explorer.exe (PID: 4772)
- explorer.exe (PID: 3196)
- explorer.exe (PID: 1160)
Application launched itself
- explorer.exe (PID: 3196)
- explorer.exe (PID: 1160)
Reads security settings of Internet Explorer
- StartMenuExperienceHost.exe (PID: 6352)
- StartMenuExperienceHost.exe (PID: 7760)
Reads the date of Windows installation
- StartMenuExperienceHost.exe (PID: 6352)
- SearchApp.exe (PID: 2328)
- StartMenuExperienceHost.exe (PID: 7760)
- SearchApp.exe (PID: 3668)
Creates file in the systems drive root
- explorer.exe (PID: 3196)
- explorer.exe (PID: 1160)
INFO
Reads the computer name
- ed7b275f-7e7b-4fa9-9abf-676847530890.exe (PID: 5300)
- TextInputHost.exe (PID: 7080)
- StartMenuExperienceHost.exe (PID: 6352)
- SearchApp.exe (PID: 2328)
- StartMenuExperienceHost.exe (PID: 7760)
- SearchApp.exe (PID: 3668)
- TextInputHost.exe (PID: 3756)
Checks supported languages
- ed7b275f-7e7b-4fa9-9abf-676847530890.exe (PID: 5300)
- TextInputHost.exe (PID: 7080)
- StartMenuExperienceHost.exe (PID: 6352)
- SearchApp.exe (PID: 2328)
- TextInputHost.exe (PID: 3756)
- SearchApp.exe (PID: 3668)
- StartMenuExperienceHost.exe (PID: 7760)
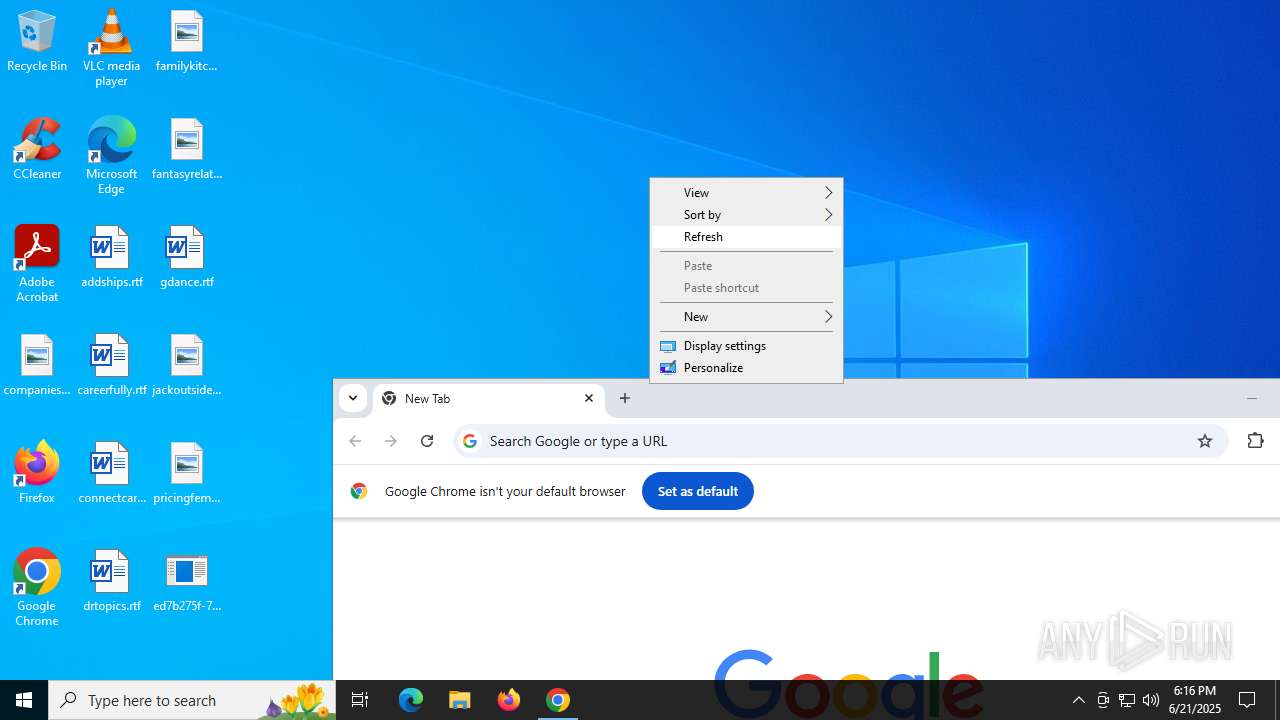
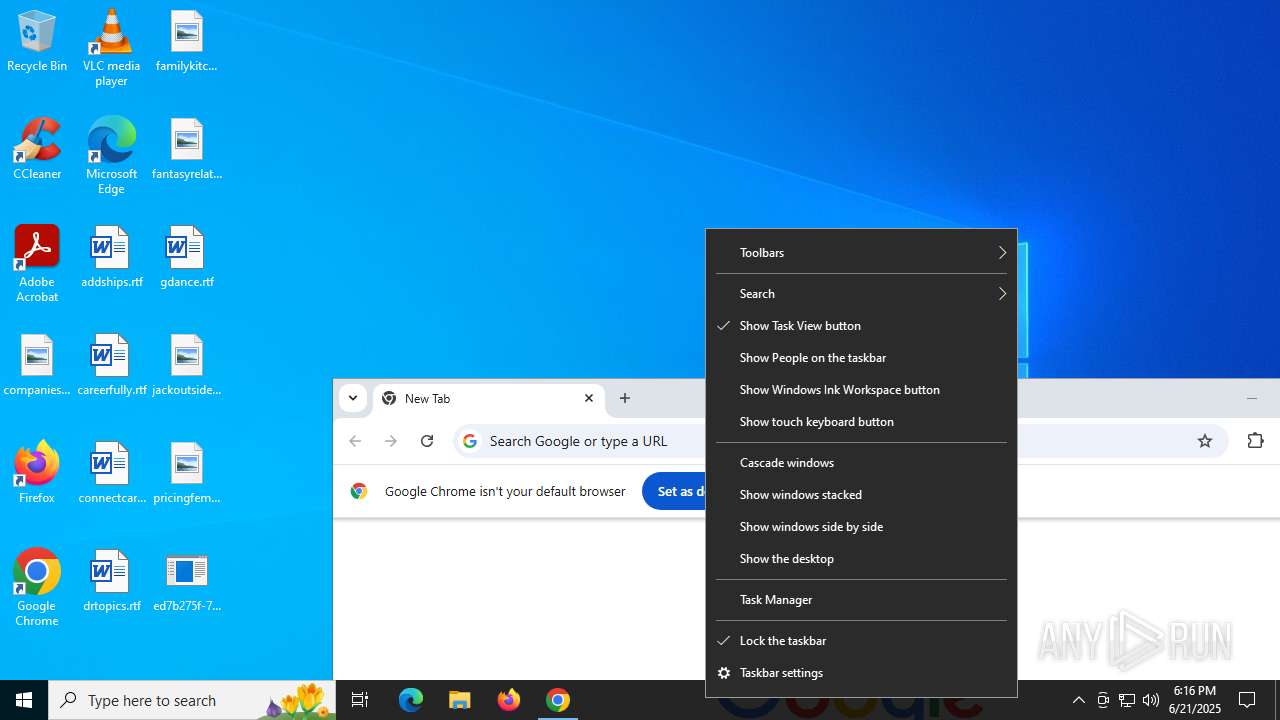
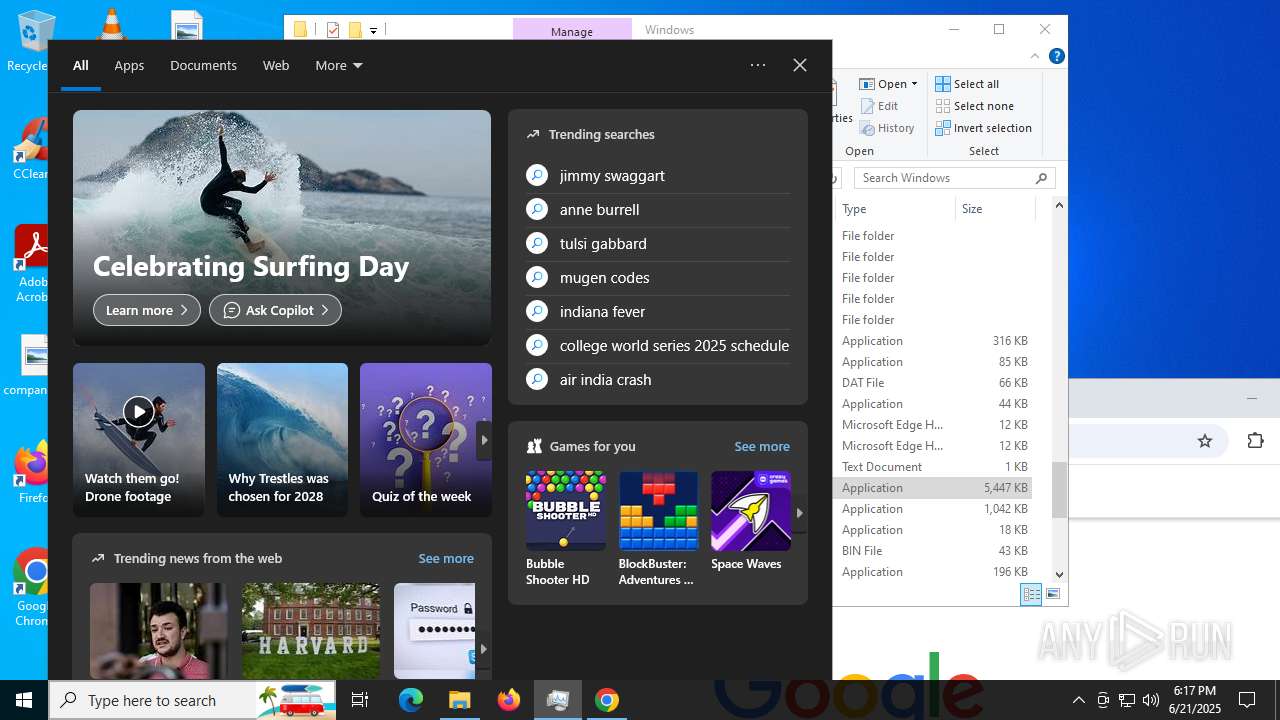
Manual execution by a user
- chrome.exe (PID: 5172)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4772)
- Taskmgr.exe (PID: 7156)
- explorer.exe (PID: 3196)
- explorer.exe (PID: 4952)
- RuntimeBroker.exe (PID: 5224)
- explorer.exe (PID: 1160)
- explorer.exe (PID: 7628)
- RuntimeBroker.exe (PID: 5448)
Application launched itself
- chrome.exe (PID: 5172)
Reads the machine GUID from the registry
- ed7b275f-7e7b-4fa9-9abf-676847530890.exe (PID: 5300)
- StartMenuExperienceHost.exe (PID: 5160)
- TextInputHost.exe (PID: 2772)
- SearchApp.exe (PID: 2328)
- SearchApp.exe (PID: 3668)
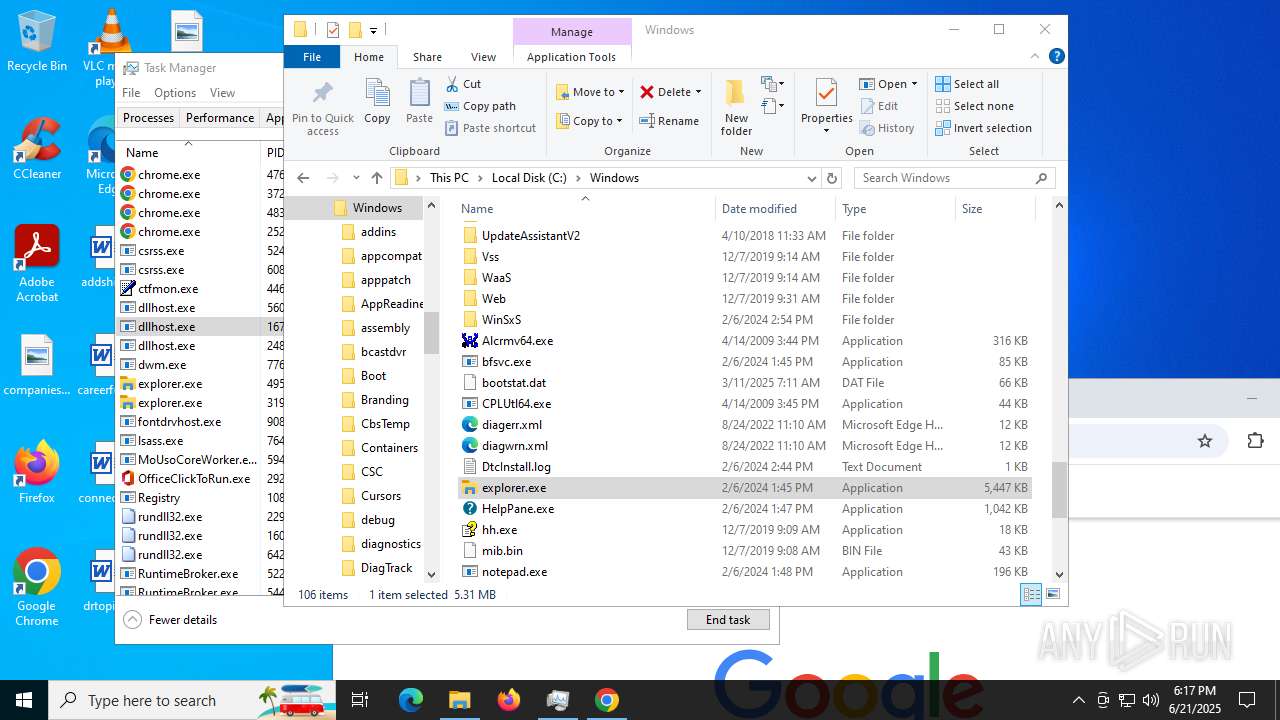
Creates files in the program directory
- ed7b275f-7e7b-4fa9-9abf-676847530890.exe (PID: 5300)
Checks proxy server information
- explorer.exe (PID: 4772)
- explorer.exe (PID: 4952)
- SearchApp.exe (PID: 2328)
- explorer.exe (PID: 3196)
- slui.exe (PID: 4192)
- explorer.exe (PID: 1160)
- SearchApp.exe (PID: 3668)
- explorer.exe (PID: 7628)
Launching a file from a Registry key
- ed7b275f-7e7b-4fa9-9abf-676847530890.exe (PID: 5300)
- explorer.exe (PID: 4772)
- explorer.exe (PID: 3196)
- explorer.exe (PID: 1160)
Process checks computer location settings
- StartMenuExperienceHost.exe (PID: 6352)
- SearchApp.exe (PID: 2328)
- SearchApp.exe (PID: 3668)
- StartMenuExperienceHost.exe (PID: 7760)
Reads the software policy settings
- SearchApp.exe (PID: 2328)
- slui.exe (PID: 4192)
- SearchApp.exe (PID: 3668)
Creates files or folders in the user directory
- explorer.exe (PID: 4952)
- dllhost.exe (PID: 5604)
- explorer.exe (PID: 7628)
Reads Environment values
- SearchApp.exe (PID: 2328)
- SearchApp.exe (PID: 3668)
Executable content was dropped or overwritten
- chrome.exe (PID: 7528)
The sample compiled with english language support
- chrome.exe (PID: 7528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:21 18:08:52+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 55808 |
| InitializedDataSize: | 541184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1e78 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
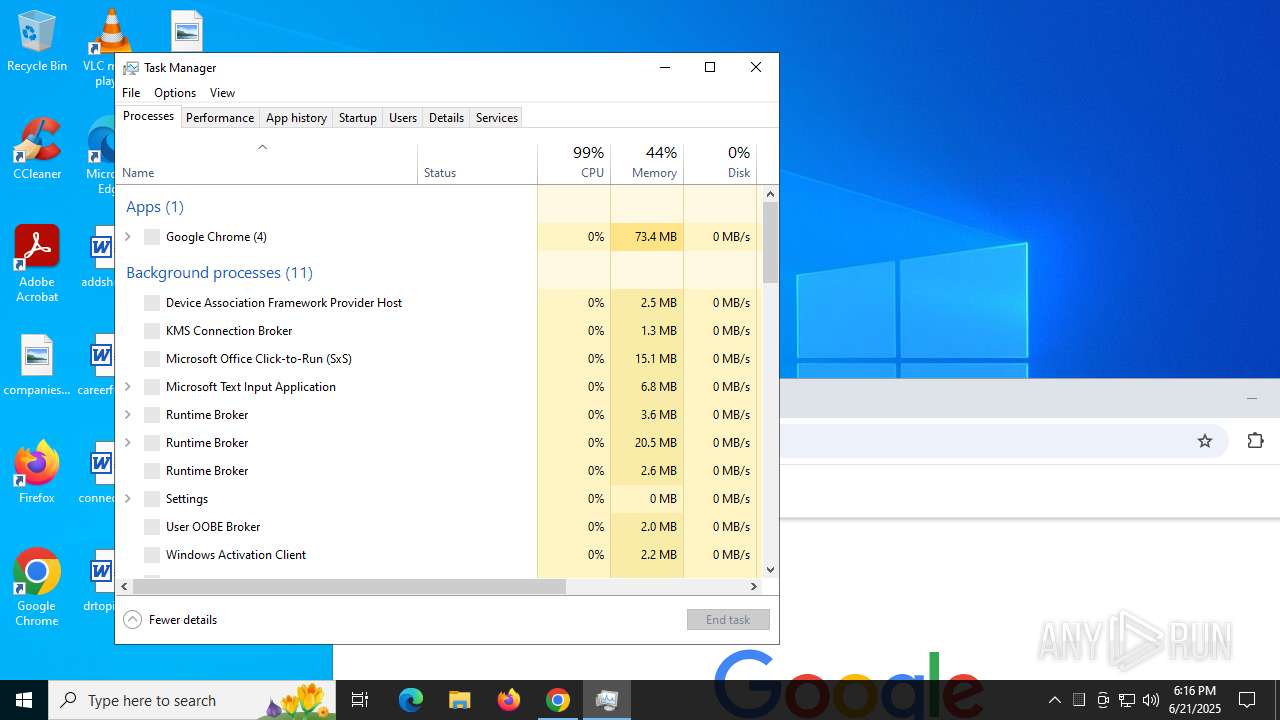
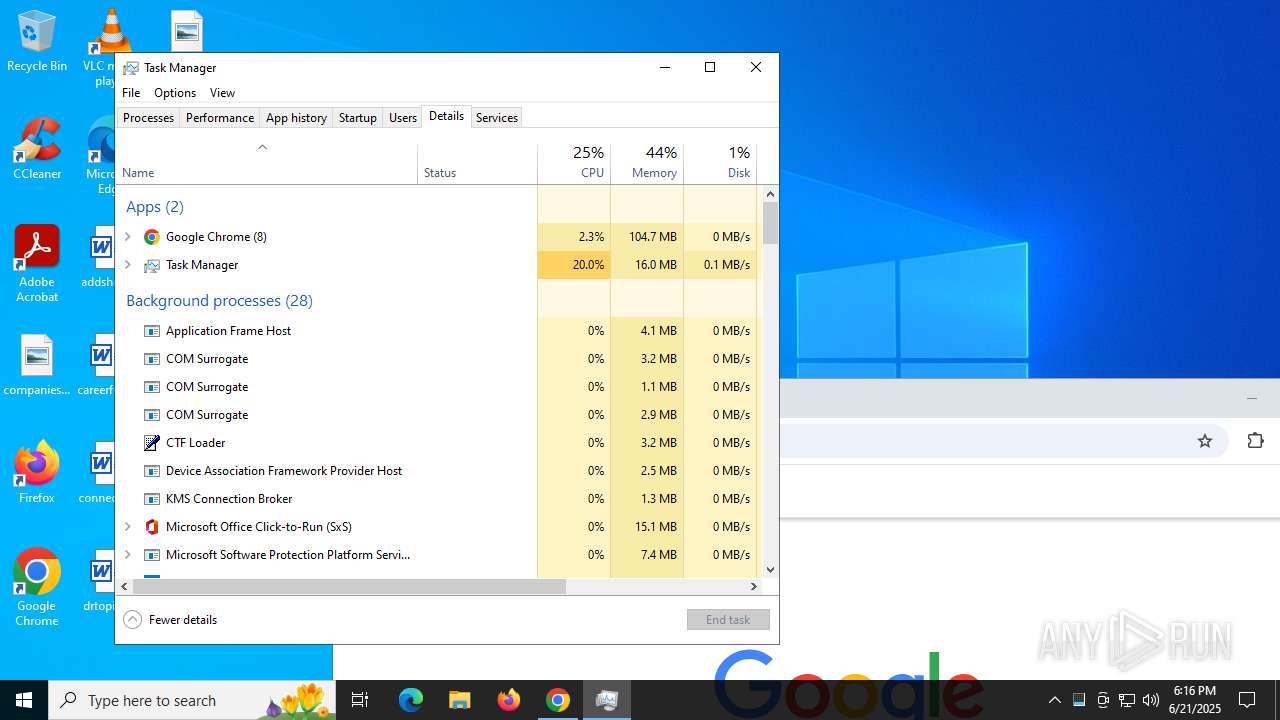
Total processes
183
Monitored processes
53
Malicious processes
6
Suspicious processes
15
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1160 | C:\WINDOWS\explorer.exe /factory,{682159d9-c321-47ca-b3f1-30e36b2ec8b9} -Embedding | C:\Windows\explorer.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1604 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2296 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {3eef301f-b596-4c0b-bd92-013beafce793} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2328 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Exit code: 1 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2484 | C:\WINDOWS\system32\DllHost.exe /Processid:{973D20D7-562D-44B9-B70B-5A0F49CCDF3F} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=4356,i,6736442332276124669,13451980843930724059,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4584 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2772 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Exit code: 1 Version: 123.26505.0.0 Modules
| |||||||||||||||
| 2792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4988,i,6736442332276124669,13451980843930724059,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5016 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3196 | C:\WINDOWS\explorer.exe /factory,{682159d9-c321-47ca-b3f1-30e36b2ec8b9} -Embedding | C:\Windows\explorer.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3668 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
101 684
Read events
100 852
Write events
778
Delete events
54
Modification events
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000C0332 |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010012000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C000000190000000000000063006F006D00700061006E0069006500730072006500670069006F006E0061006C002E006A00700067003E002000200000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C0000001000000000000000610064006400730068006900700073002E007200740066003E002000200000001300000000000000630061007200650065007200660075006C006C0079002E007200740066003E00200020000000120000000000000063006F006E006E006500630074006300610072002E007200740066003E0020002000000010000000000000006400720074006F0070006900630073002E007200740066003E002000200000001500000000000000660061006D0069006C0079006B00690074006300680065006E002E0070006E0067003E002000200000001800000000000000660061006E007400610073007900720065006C006100740069006F006E0073002E006A00700067003E002000200000000E000000000000006700640061006E00630065002E007200740066003E0020002000000013000000000000006A00610063006B006F007500740073006900640065002E0070006E0067003E002000200000001500000000000000700072006900630069006E006700660065006D0061006C0065002E006A00700067003E002000200000002C00000000000000650064003700620032003700350066002D0037006500370062002D0034006600610039002D0039006100620066002D003600370036003800340037003500330030003800390030002E006500780065003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000001200000000000000000000000000000000000000803F0000004008000000803F000040400900000000000000404003000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D0000000040000000400E0000000040000040400F0000000040000080401000000000000000803F01000000000000000040020000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F0700000000400000A0401100 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconNameVersion |
Value: 1 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: B8F6566800000000 | |||
| (PID) Process: | (5172) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5172) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5172) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000001102BA |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
| (PID) Process: | (5172) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5172) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
12
Suspicious files
199
Text files
212
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF17acab.TMP | — | |
MD5:— | SHA256:— | |||
| 5172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF17acba.TMP | — | |
MD5:— | SHA256:— | |||
| 5172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF17acba.TMP | — | |
MD5:— | SHA256:— | |||
| 5172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17acba.TMP | — | |
MD5:— | SHA256:— | |||
| 5172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF17acba.TMP | — | |
MD5:— | SHA256:— | |||
| 5172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
77
DNS requests
52
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3936 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.10:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4012 | chrome.exe | GET | 200 | 142.250.185.110:80 | http://clients2.google.com/time/1/current?cup2key=8:f-pKo-FPnP31rK2aLQ3m4st0oyi_IaE3eSi--qkeE_4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
5692 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5692 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4772 | explorer.exe | POST | 200 | 194.38.21.76:80 | http://194.38.21.76/diamo/post.php | unknown | — | — | malicious |
4804 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
4804 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
4804 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2468 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
3936 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3936 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.24.77.10:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4772 | explorer.exe | A Network Trojan was detected | ET MALWARE Diamotrix Clipper POST Request M1 |
4772 | explorer.exe | A Network Trojan was detected | ET MALWARE Diamotrix POST Request M3 |
3196 | explorer.exe | A Network Trojan was detected | ET MALWARE Diamotrix Clipper POST Request M1 |
3196 | explorer.exe | A Network Trojan was detected | ET MALWARE Diamotrix POST Request M3 |
1160 | explorer.exe | A Network Trojan was detected | ET MALWARE Diamotrix Clipper POST Request M1 |