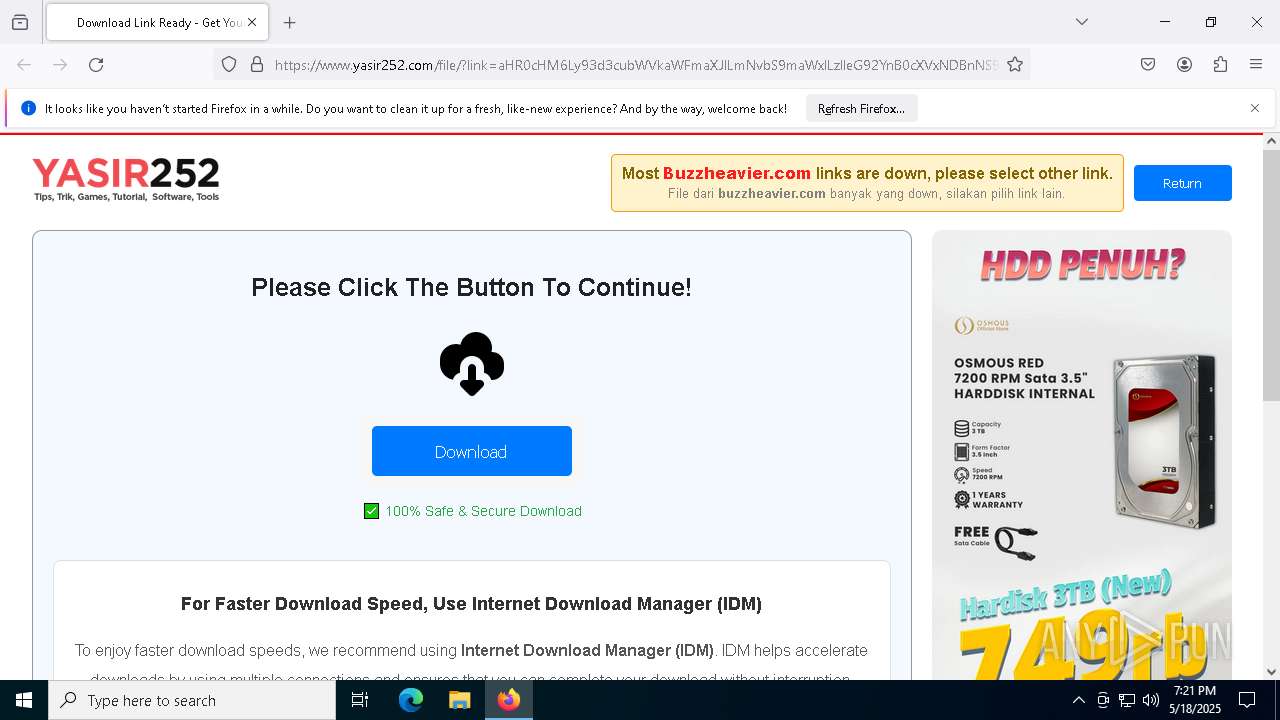
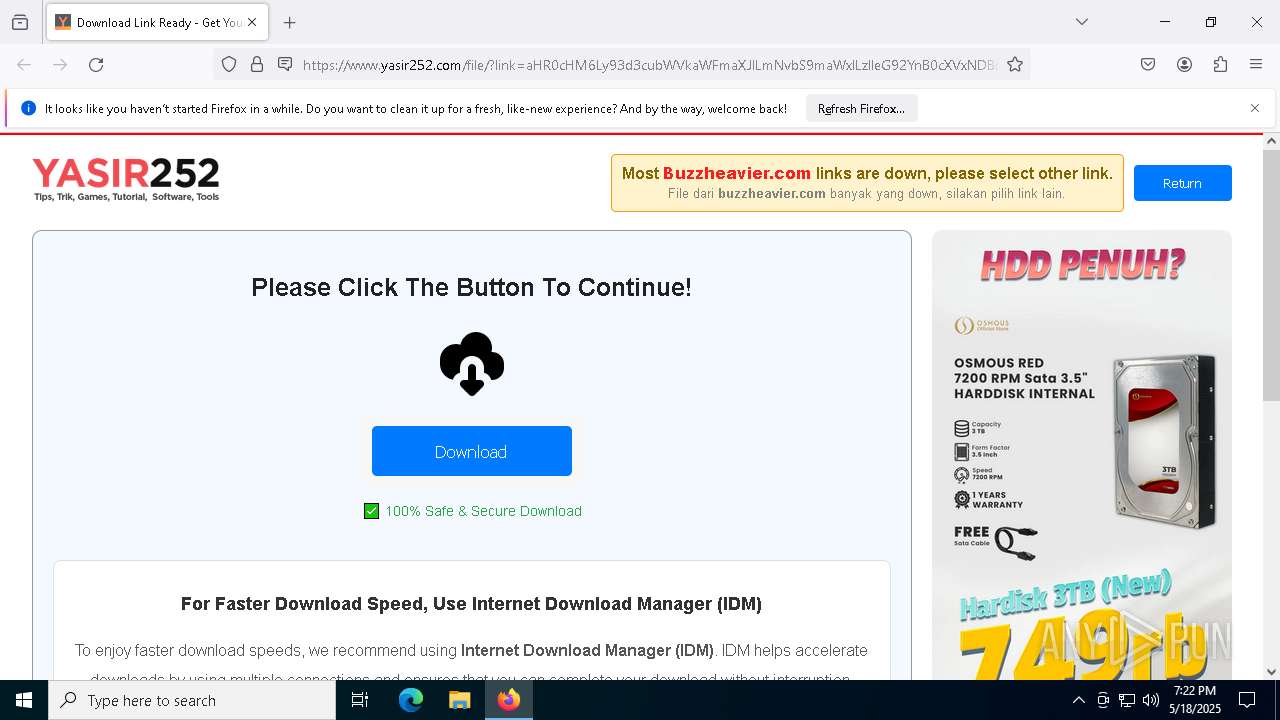
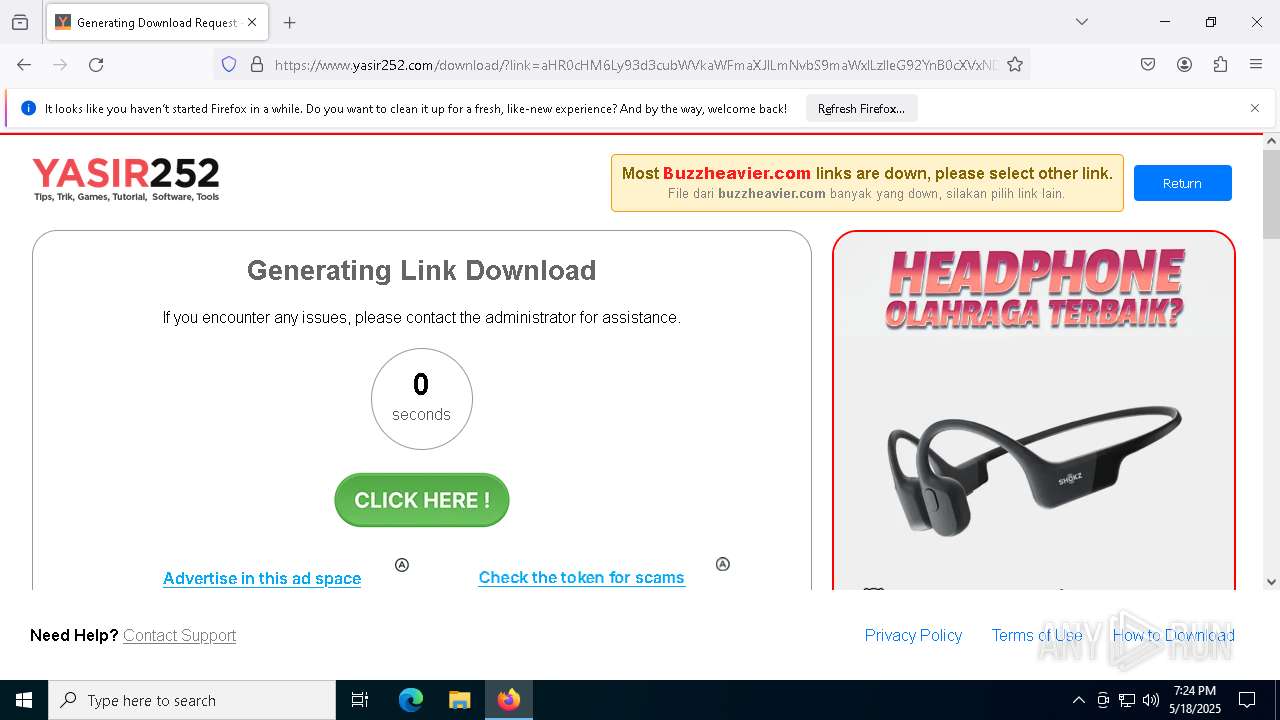
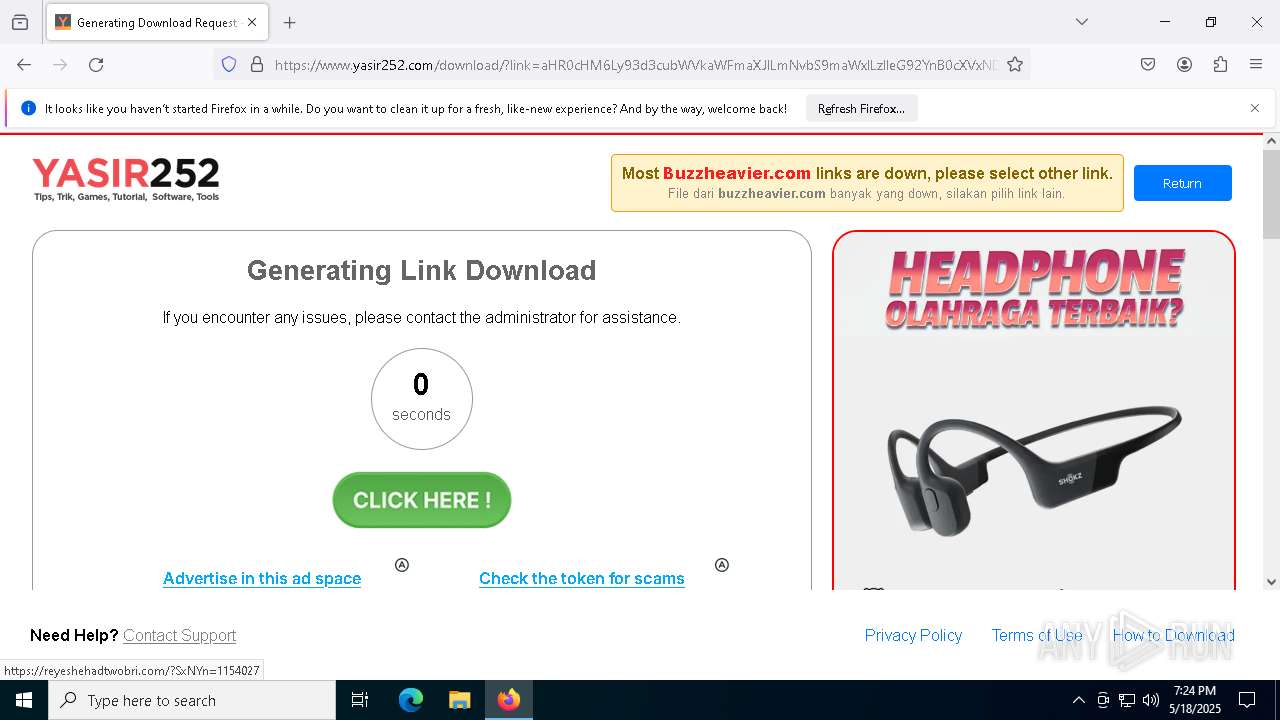
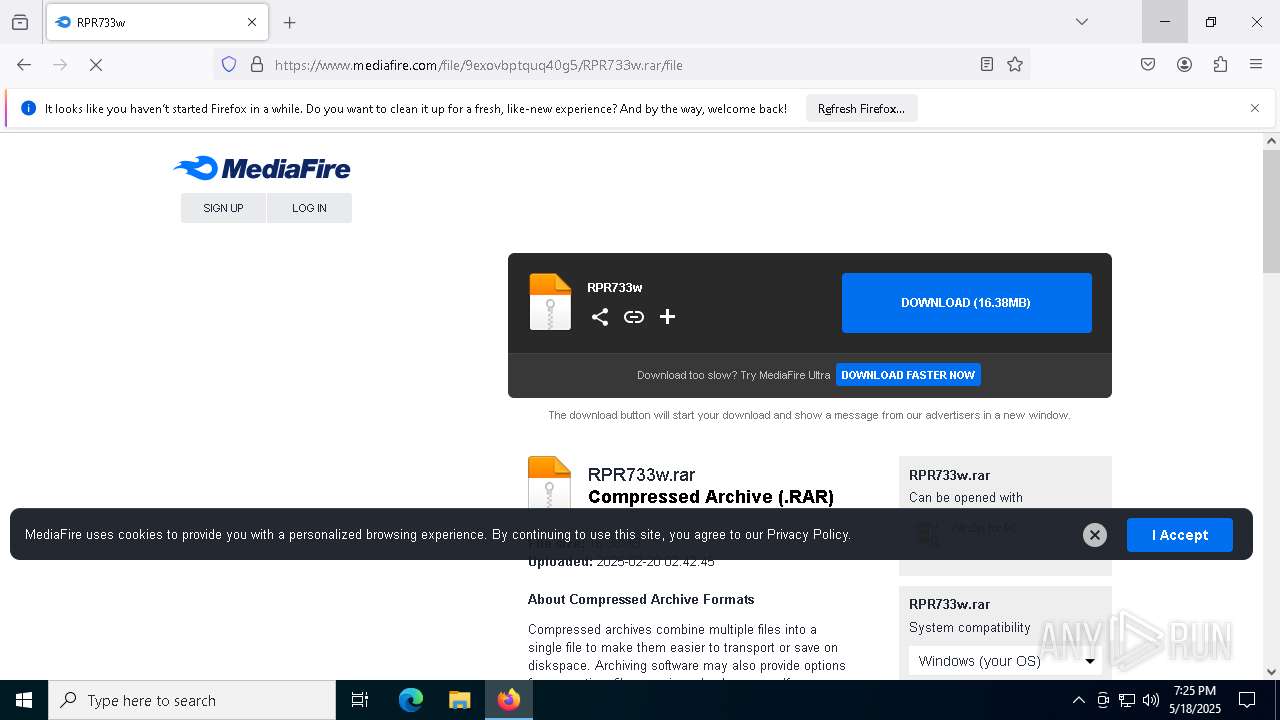
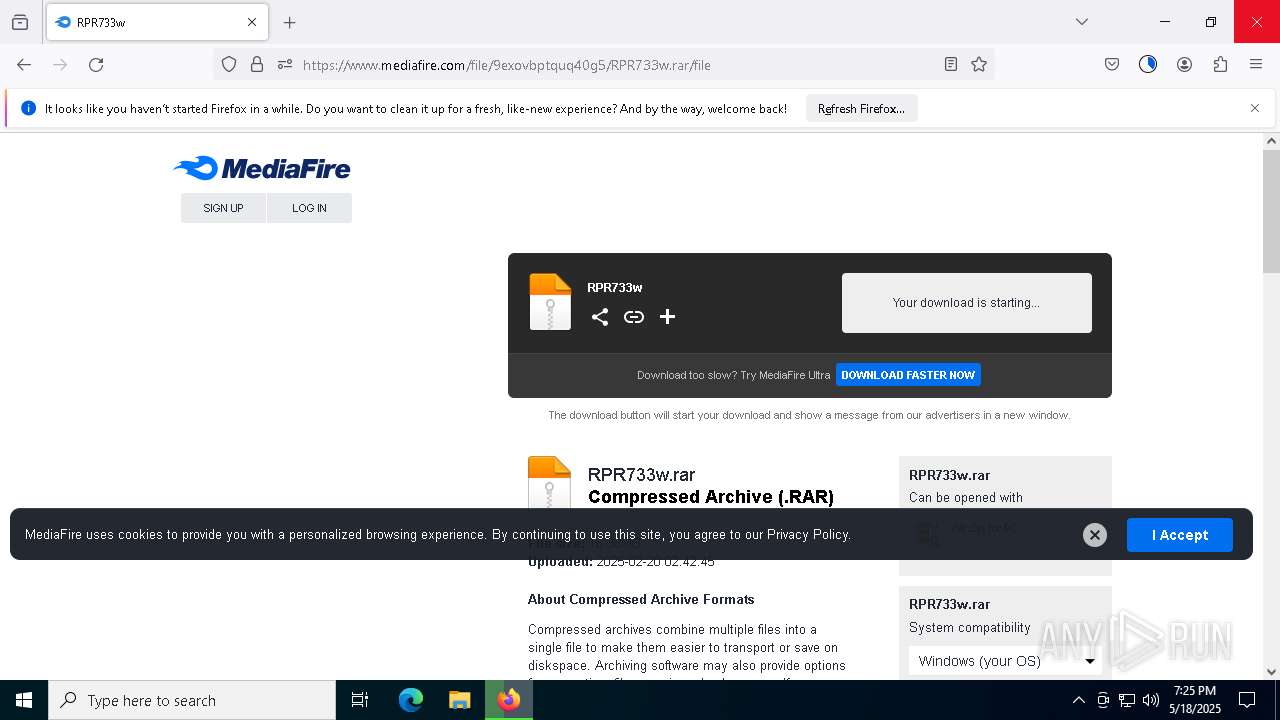
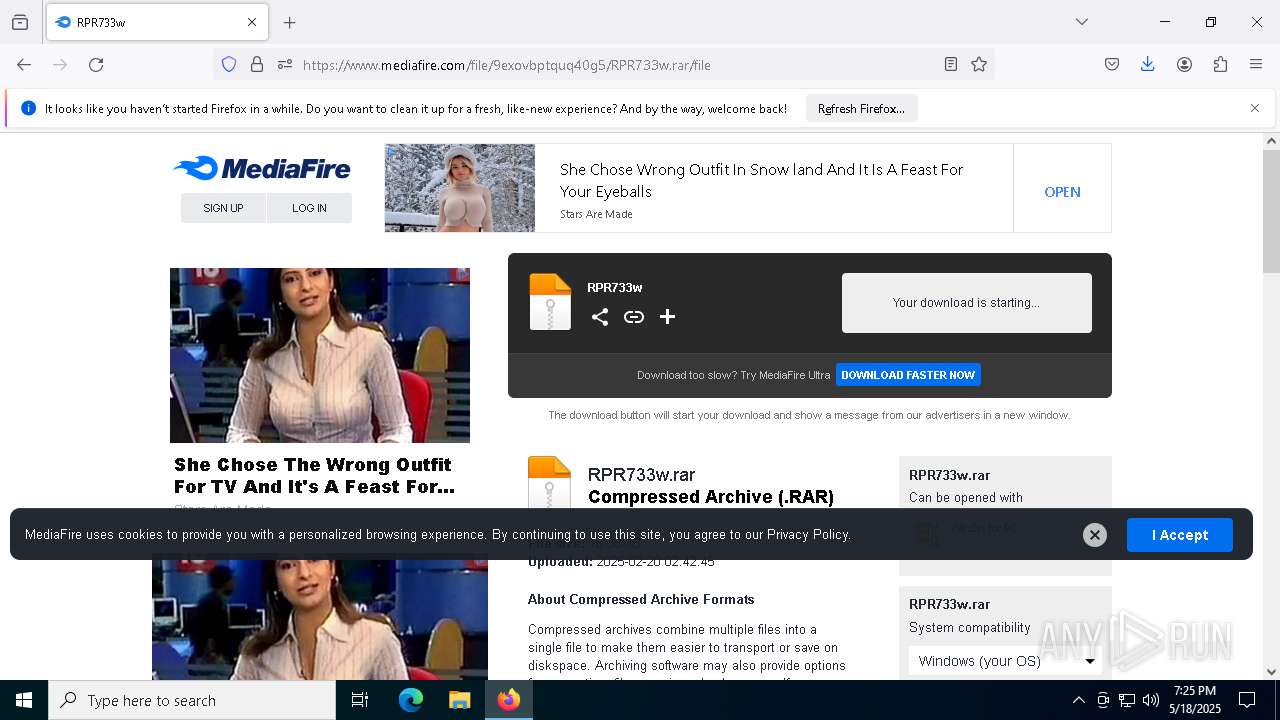
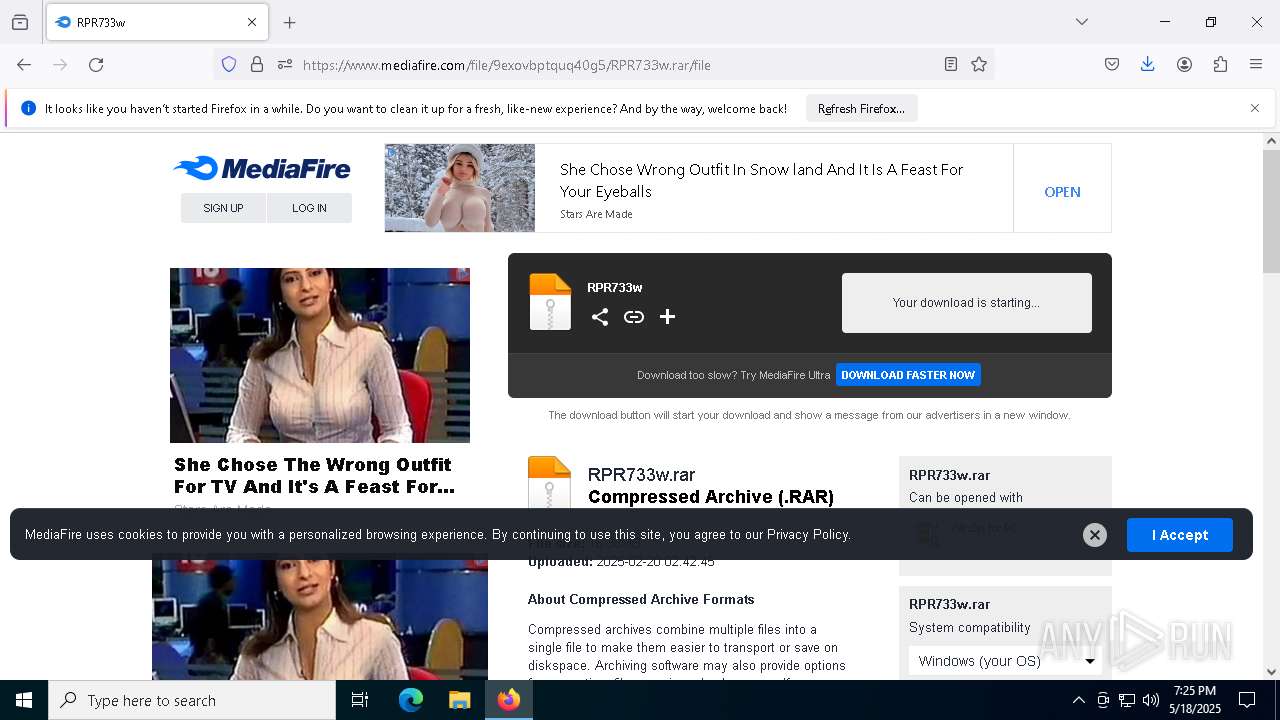
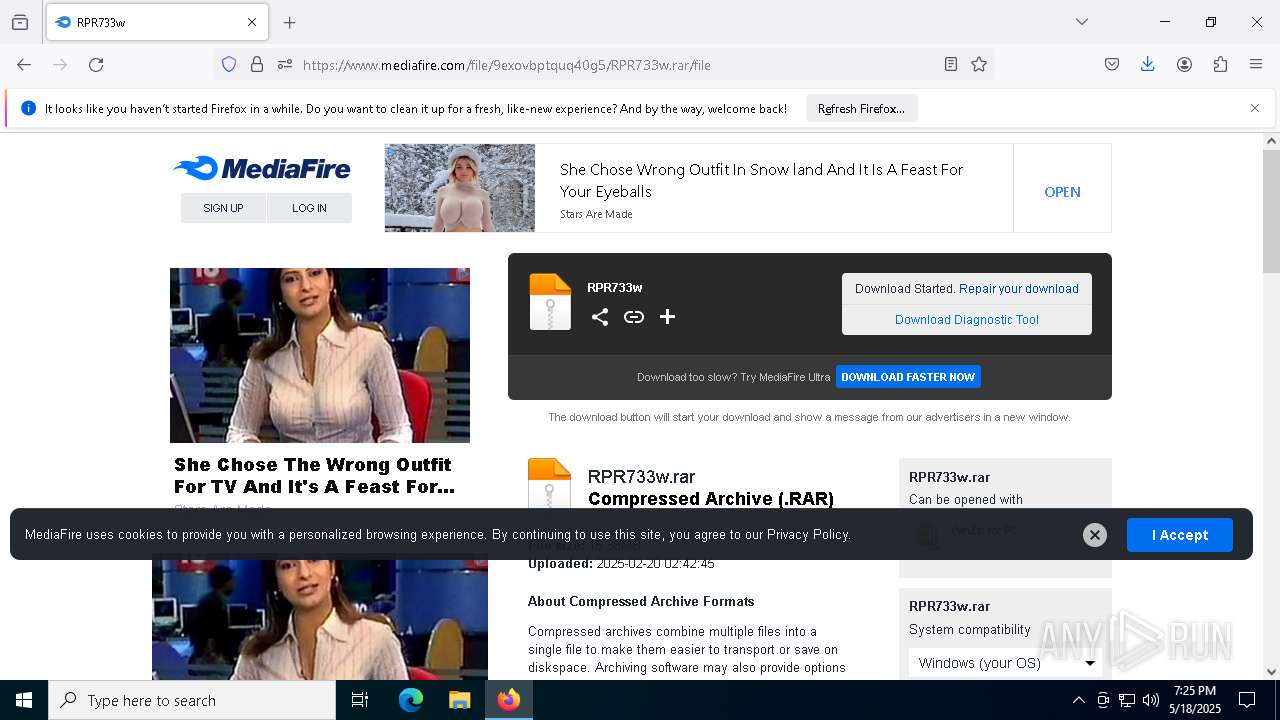
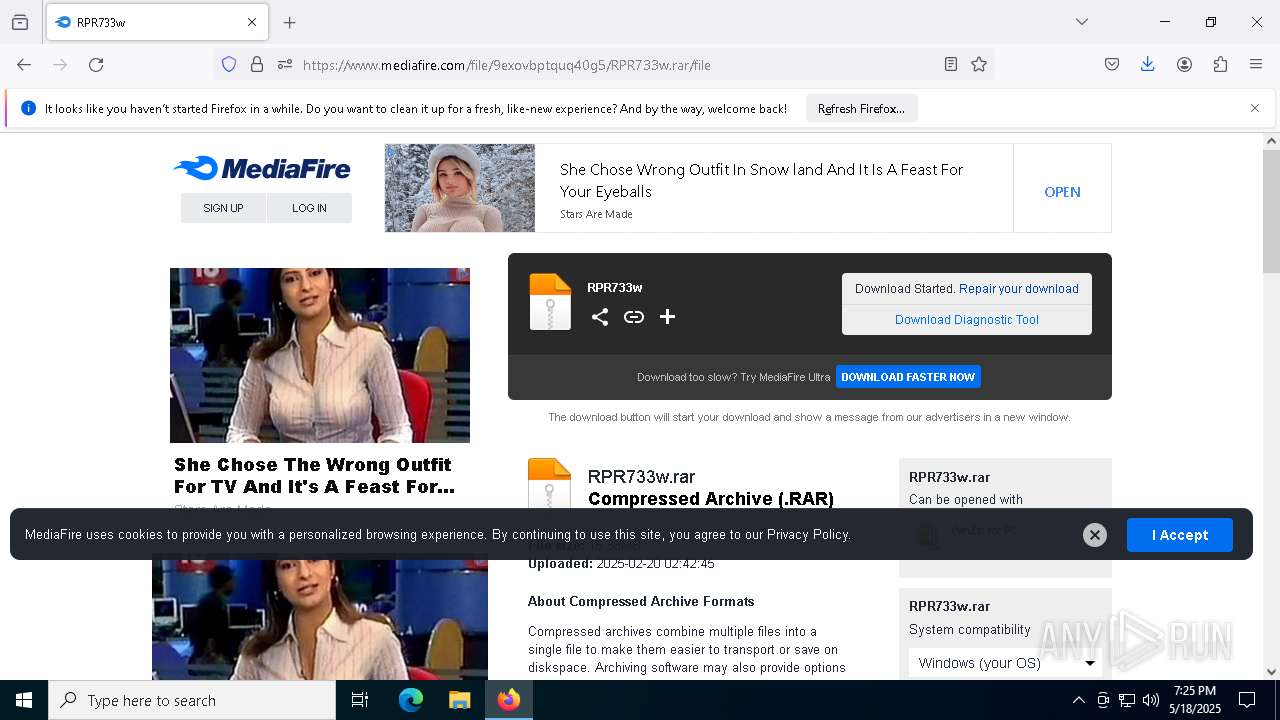
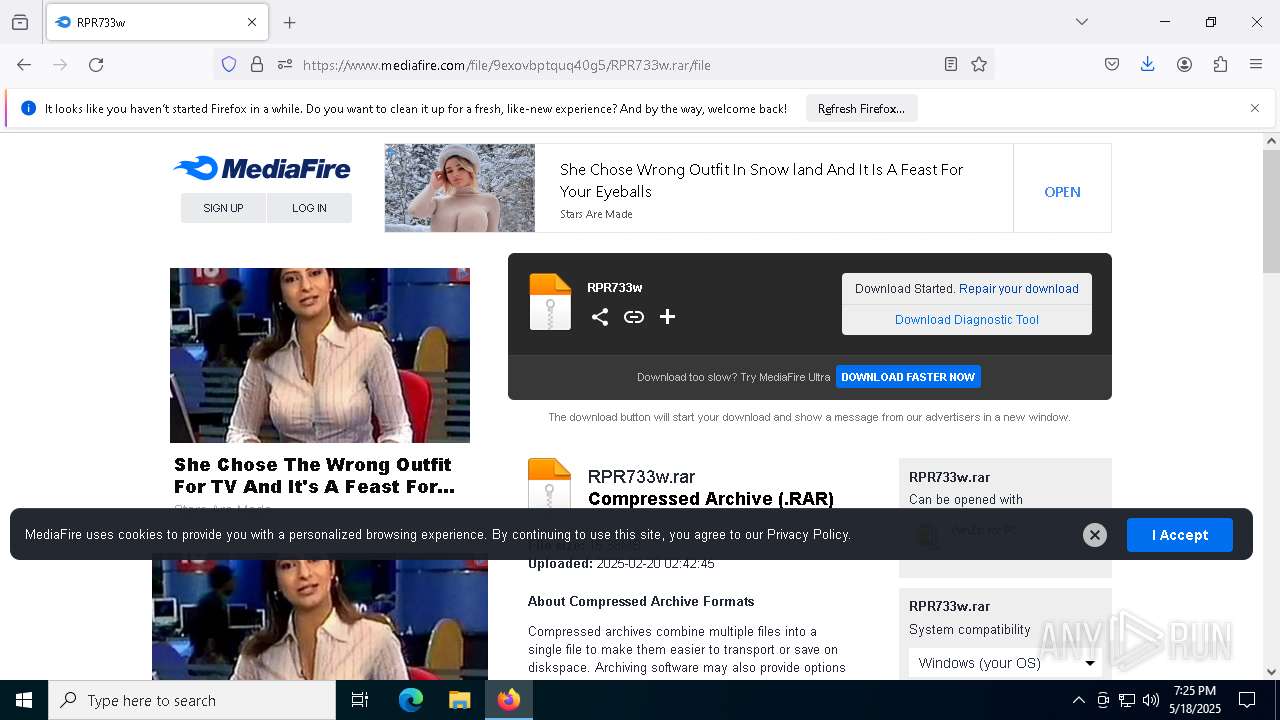
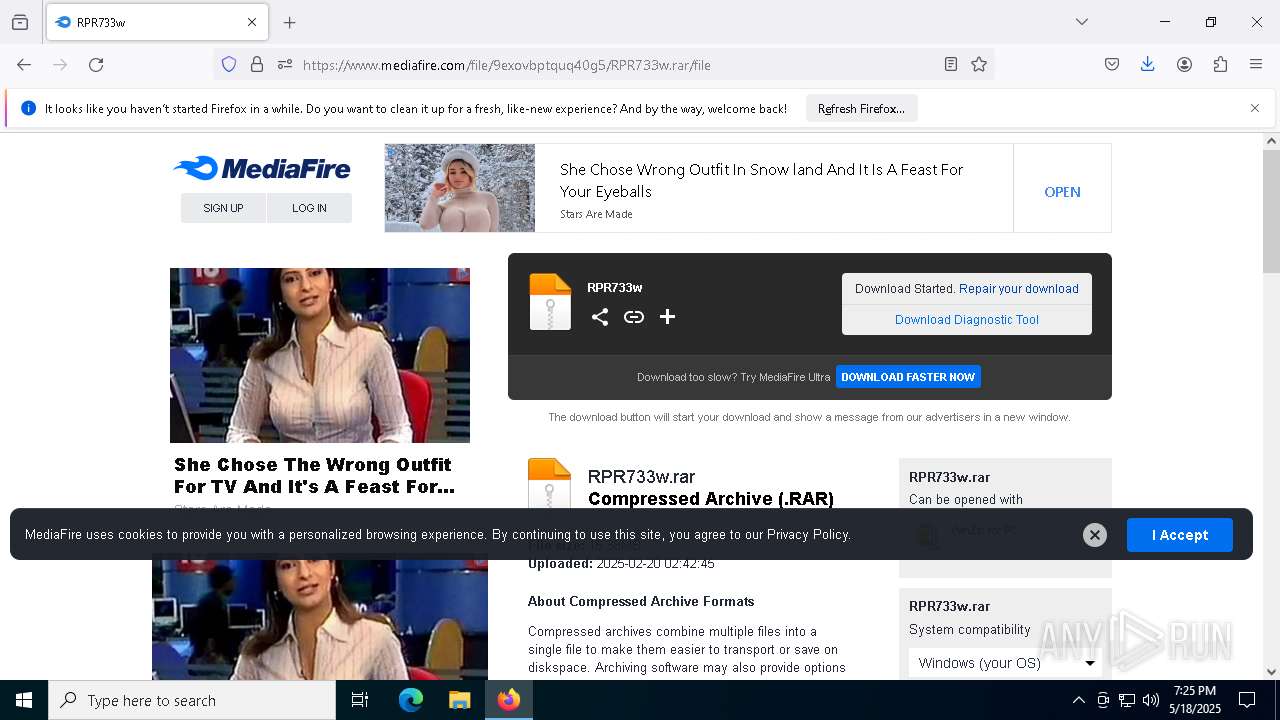
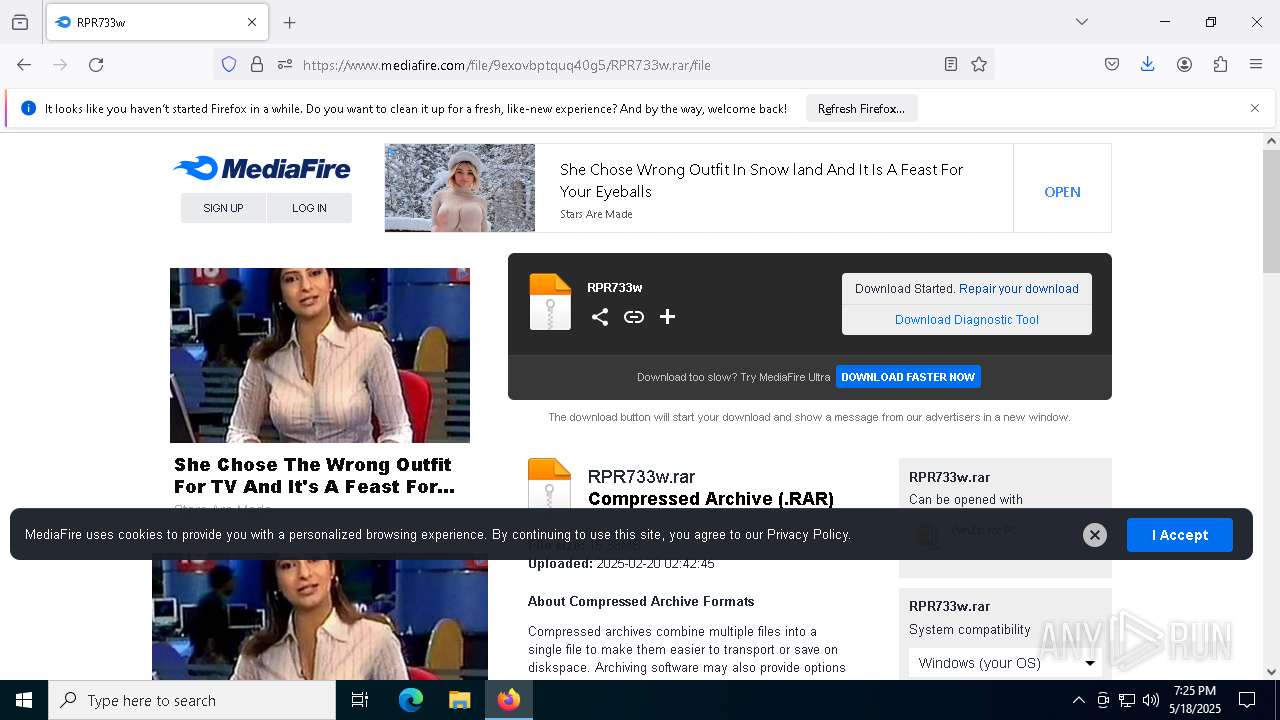
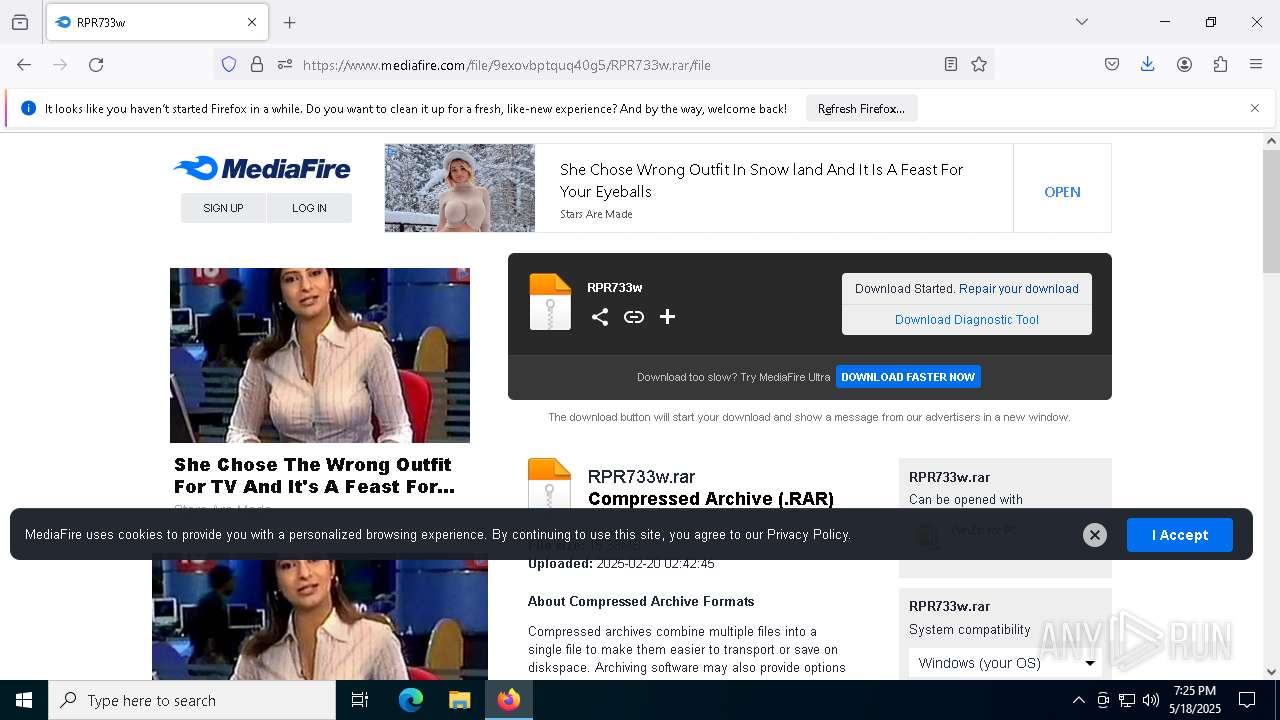
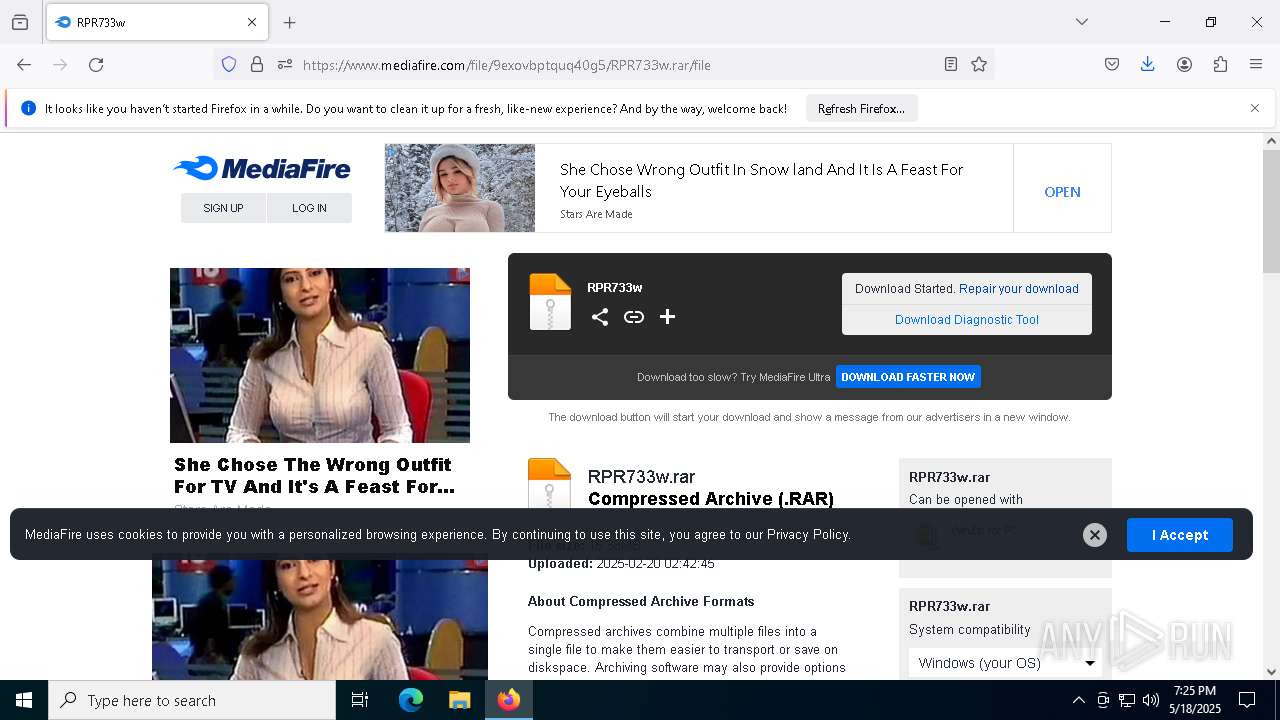
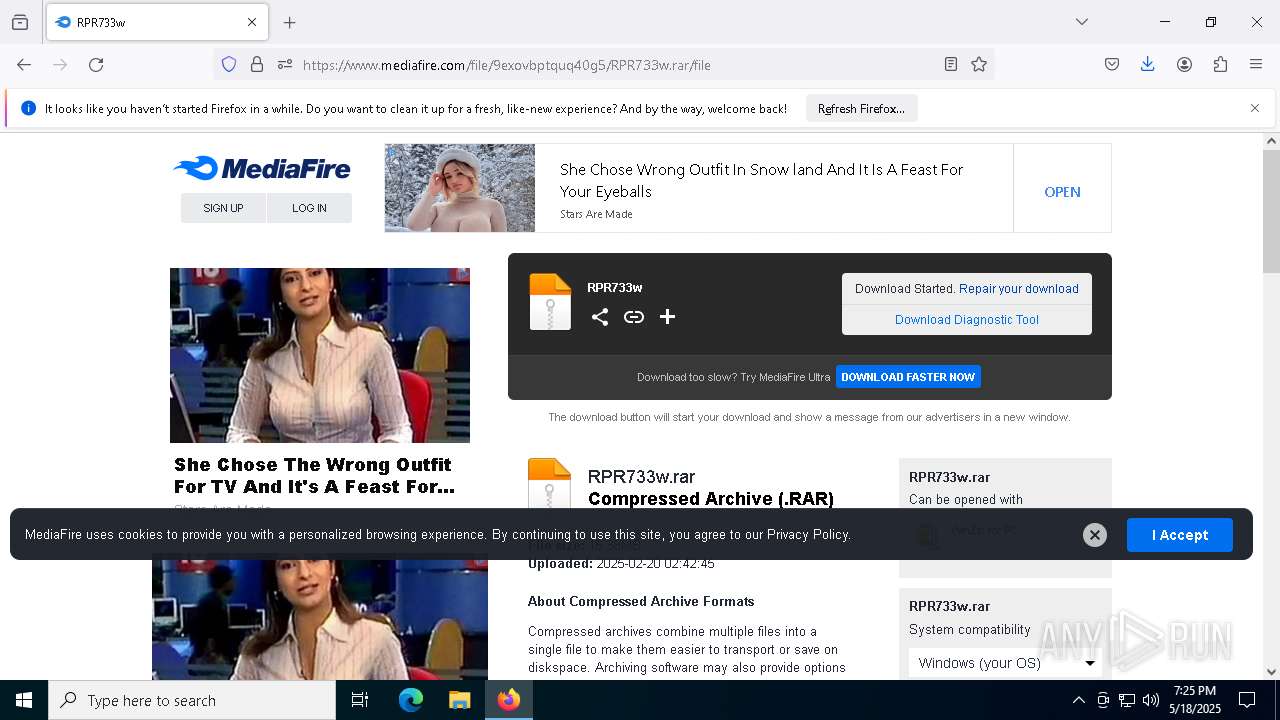
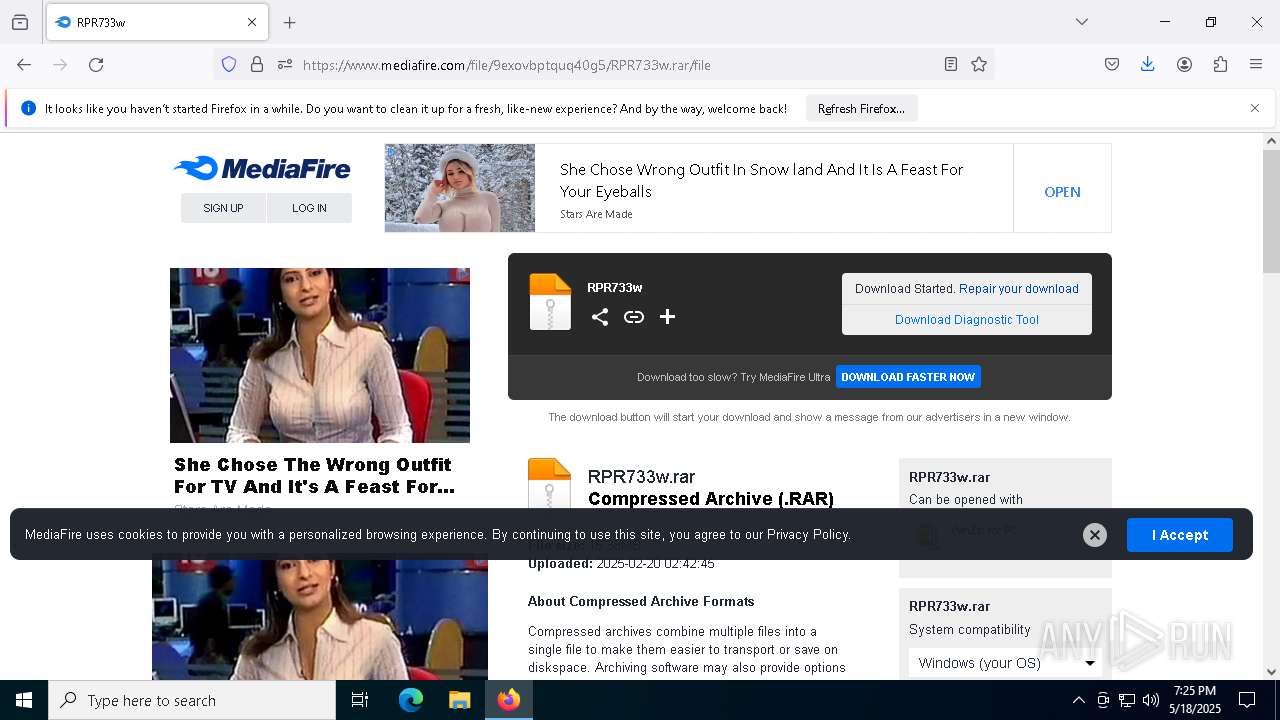
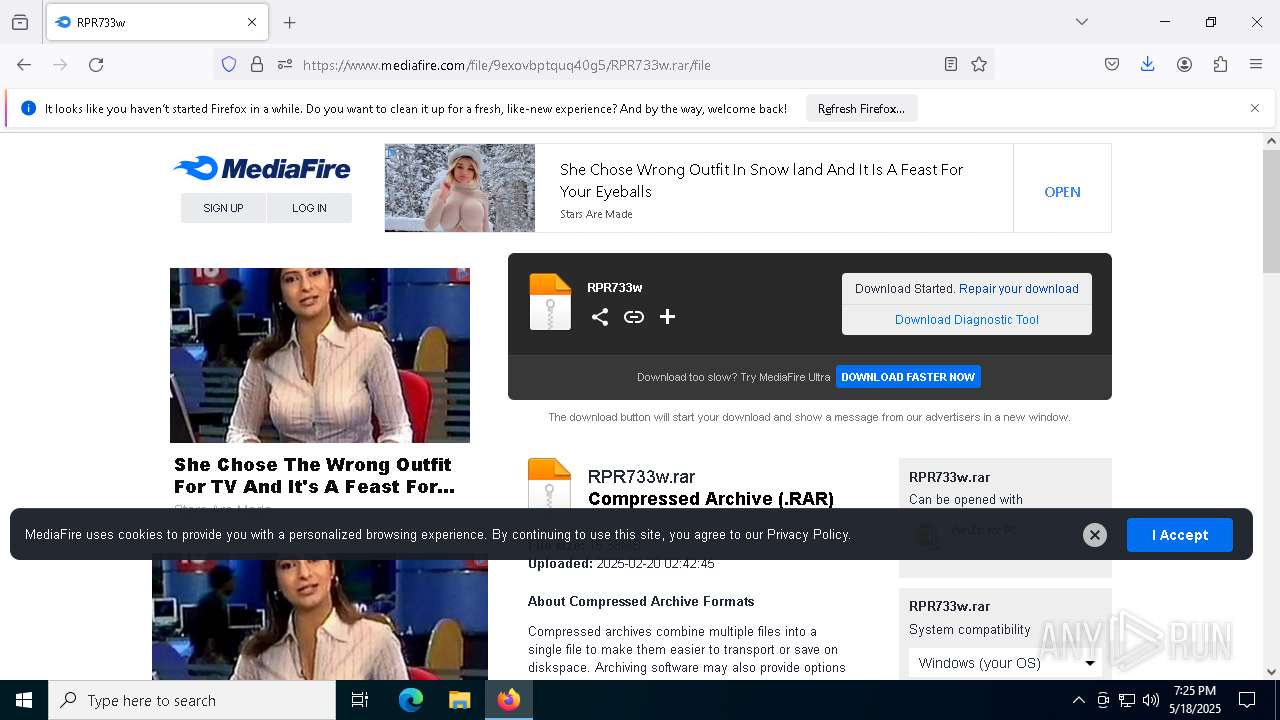
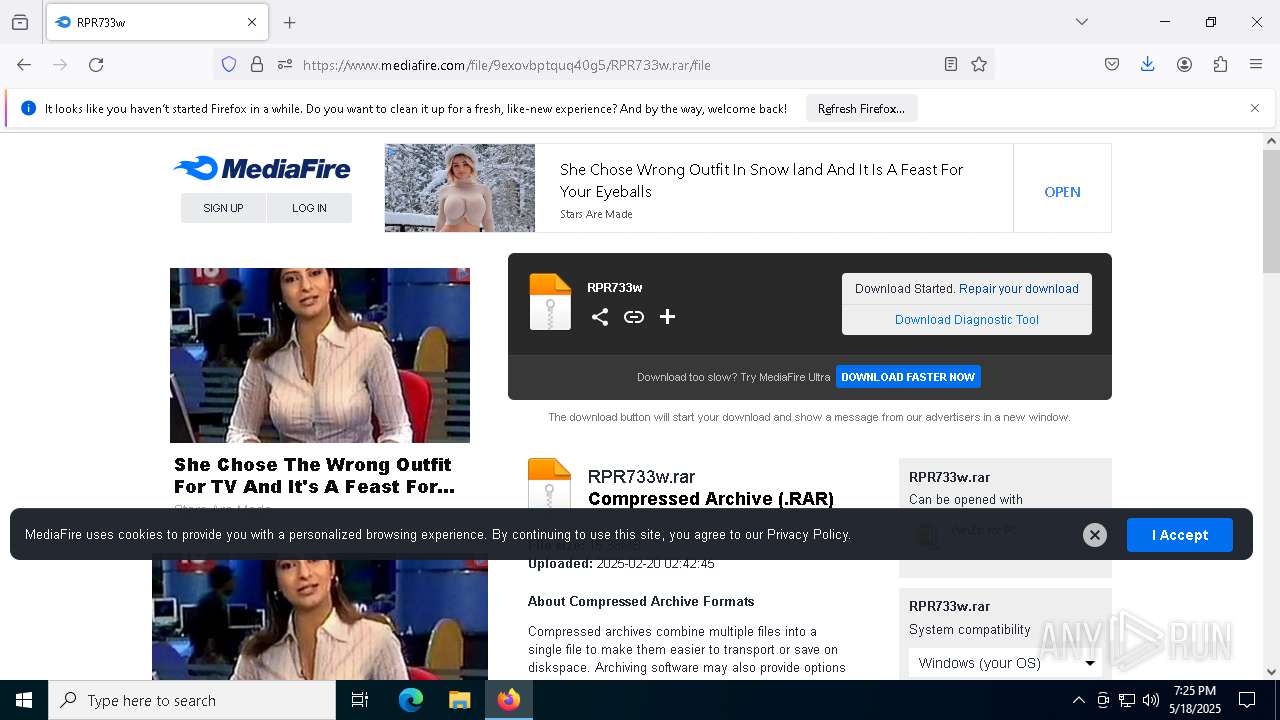
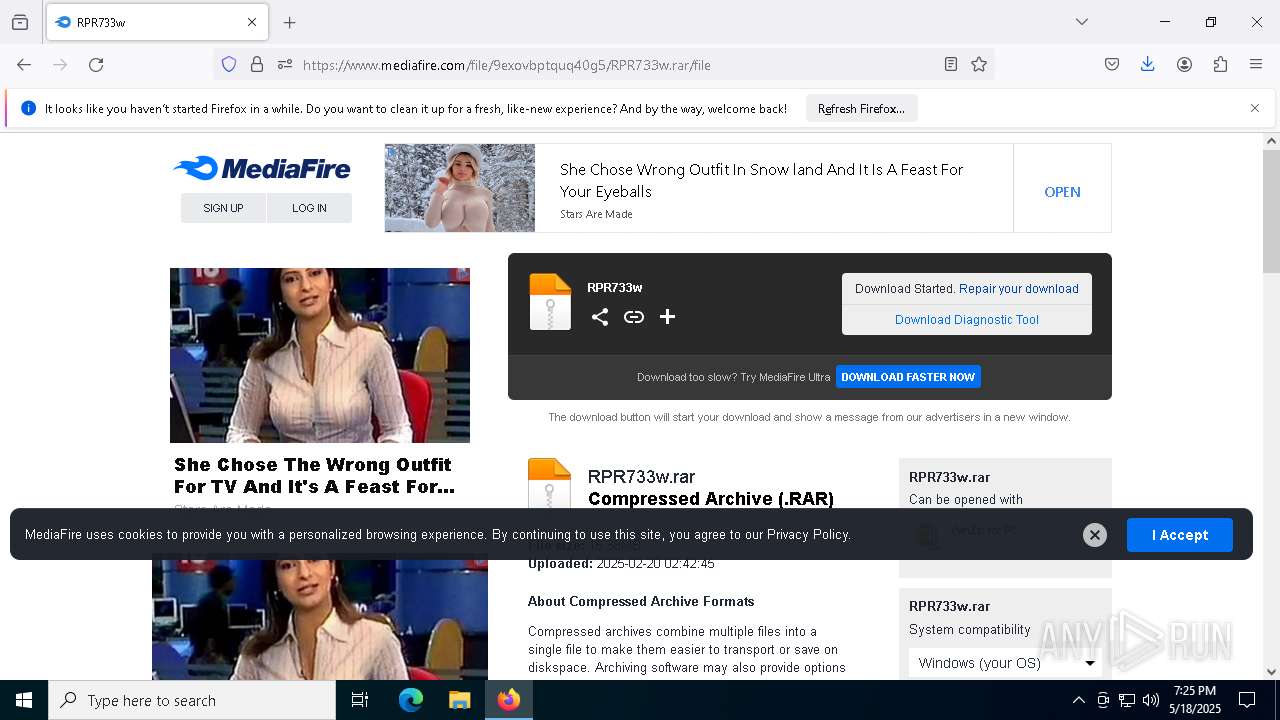
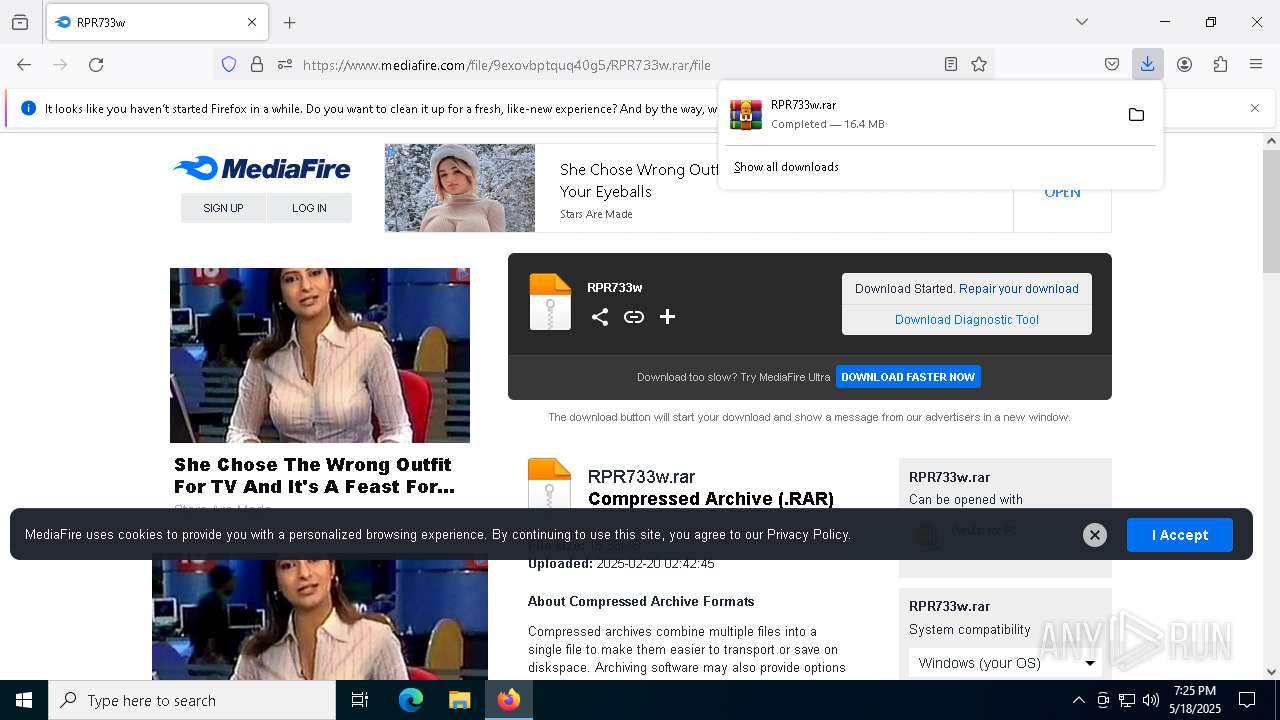
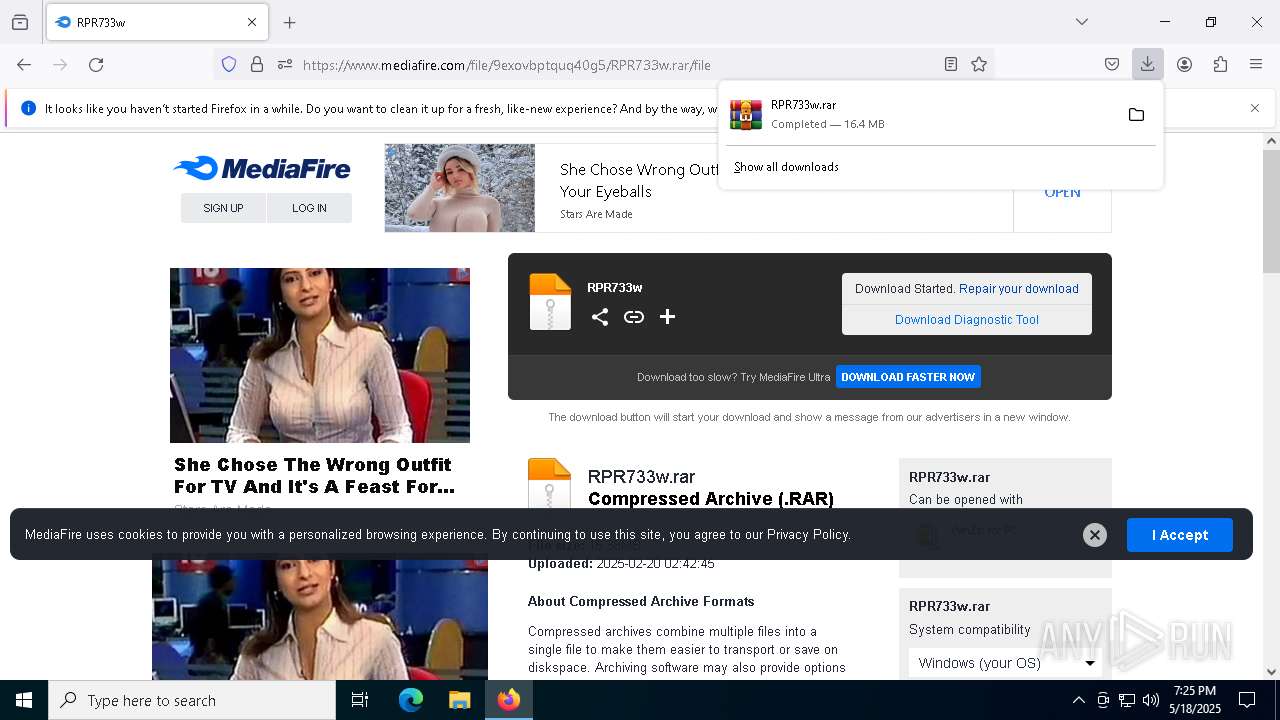
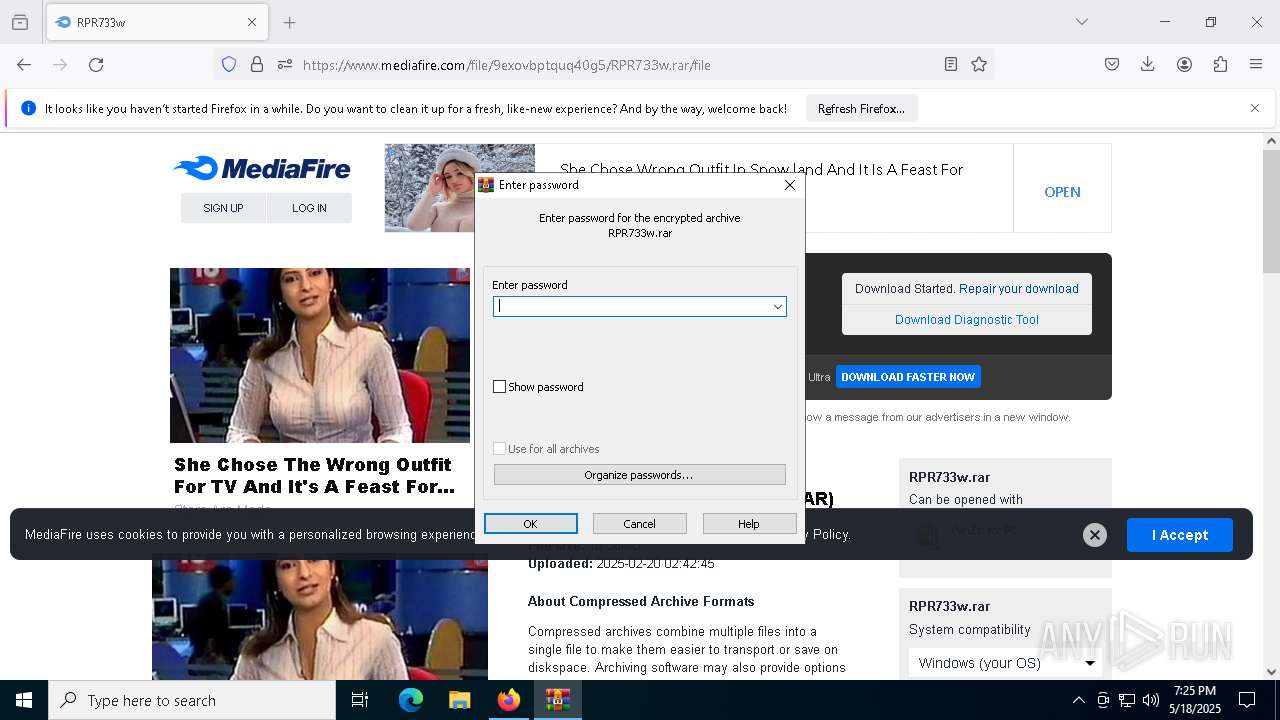
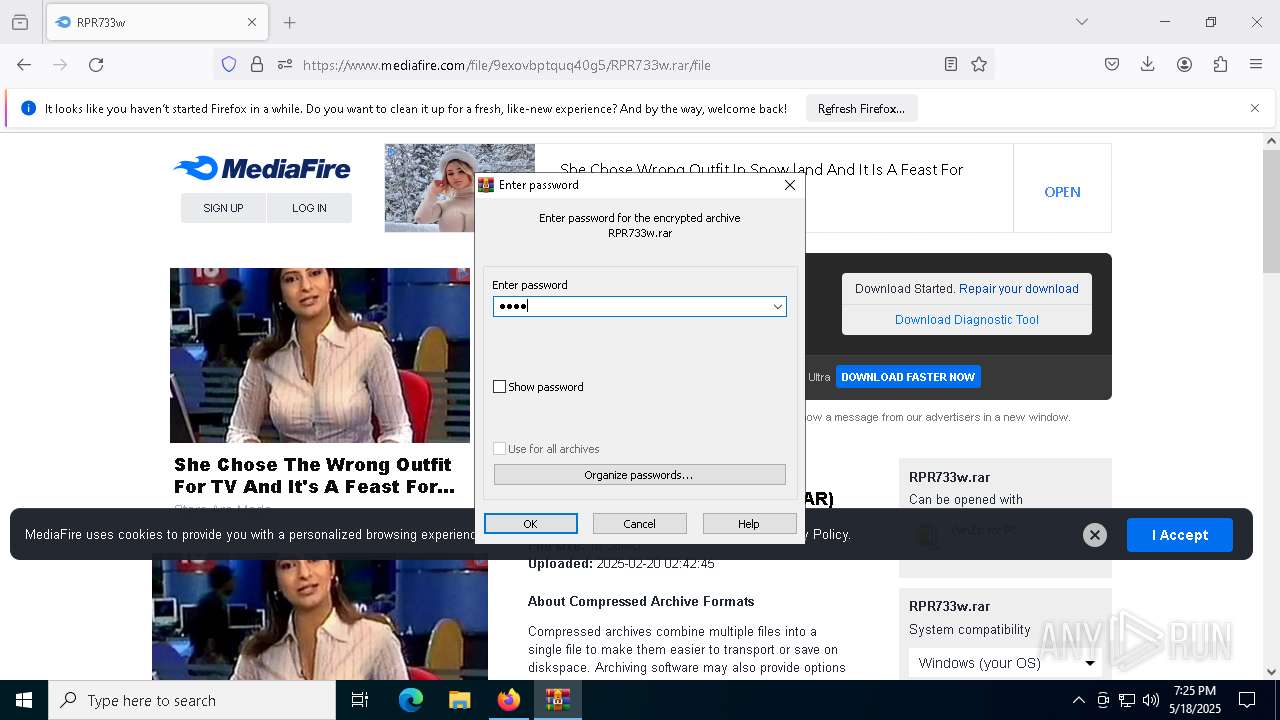
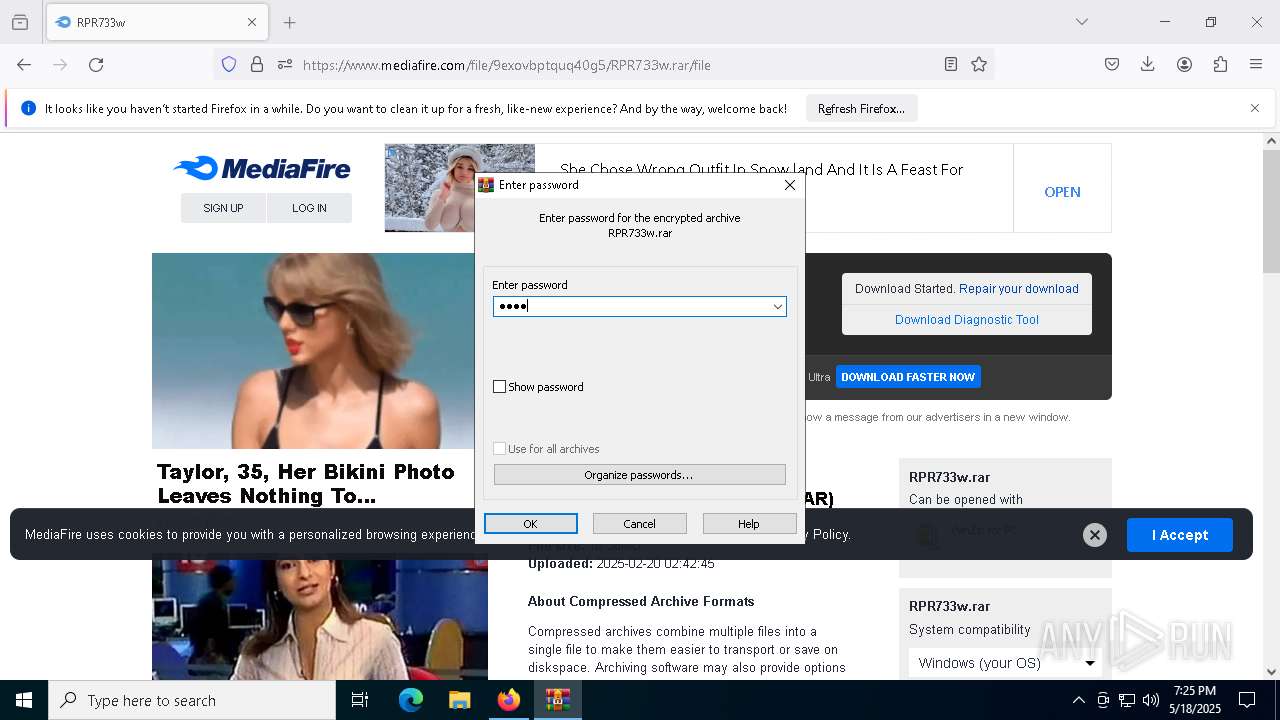
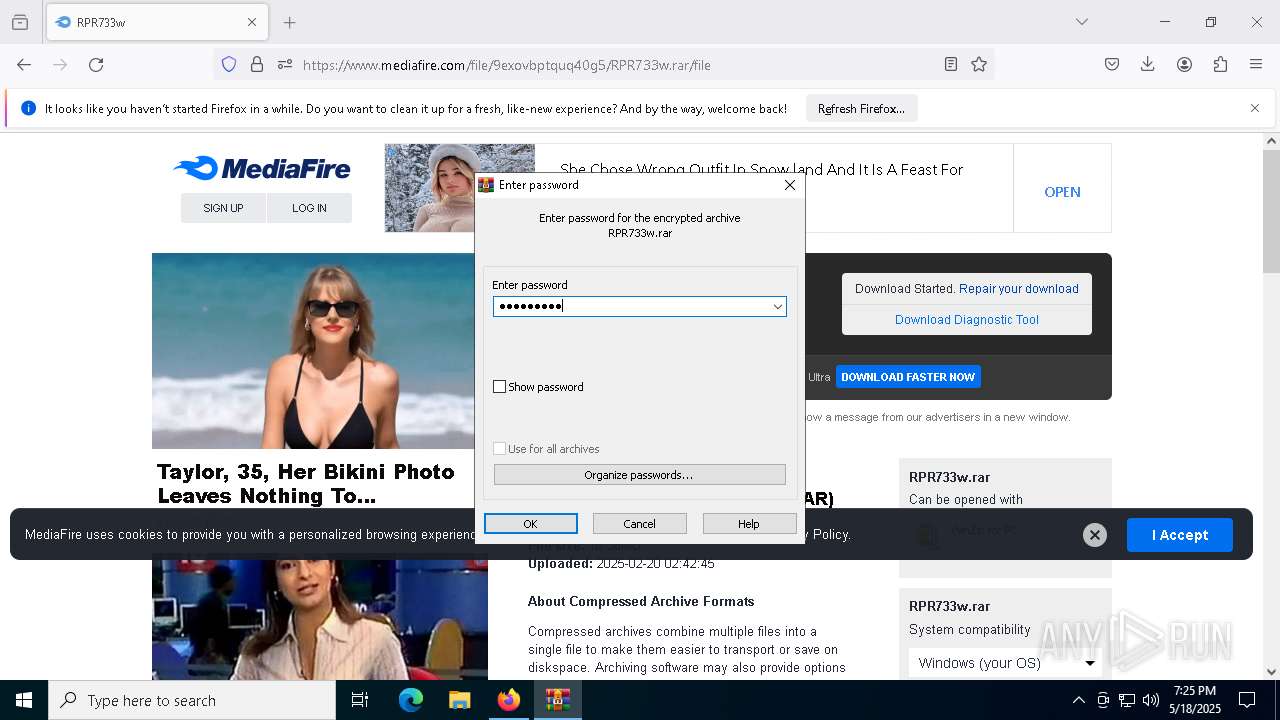
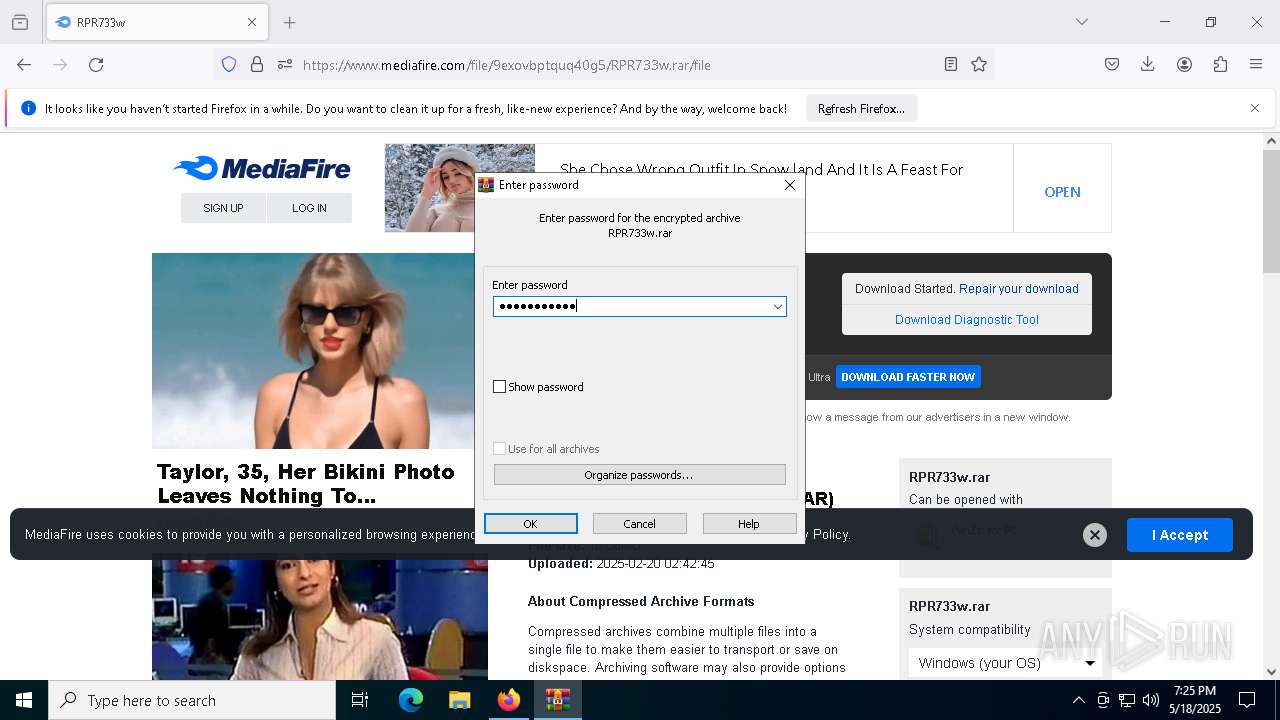
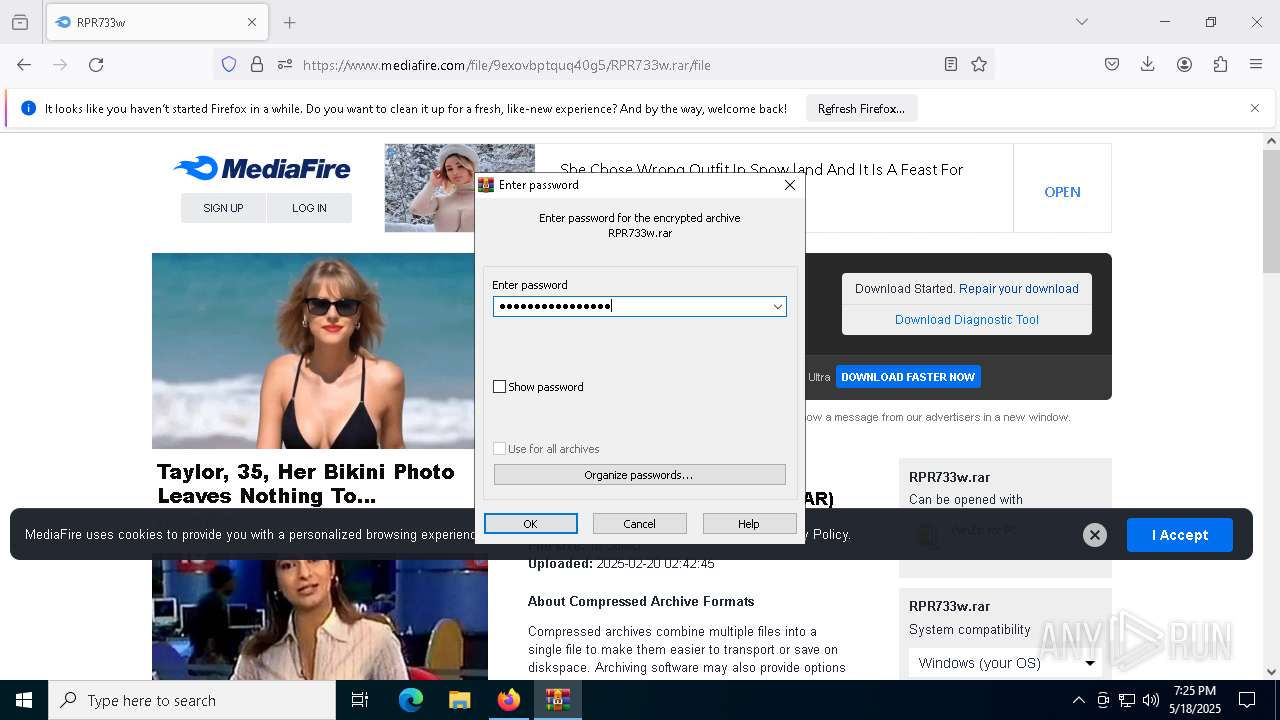
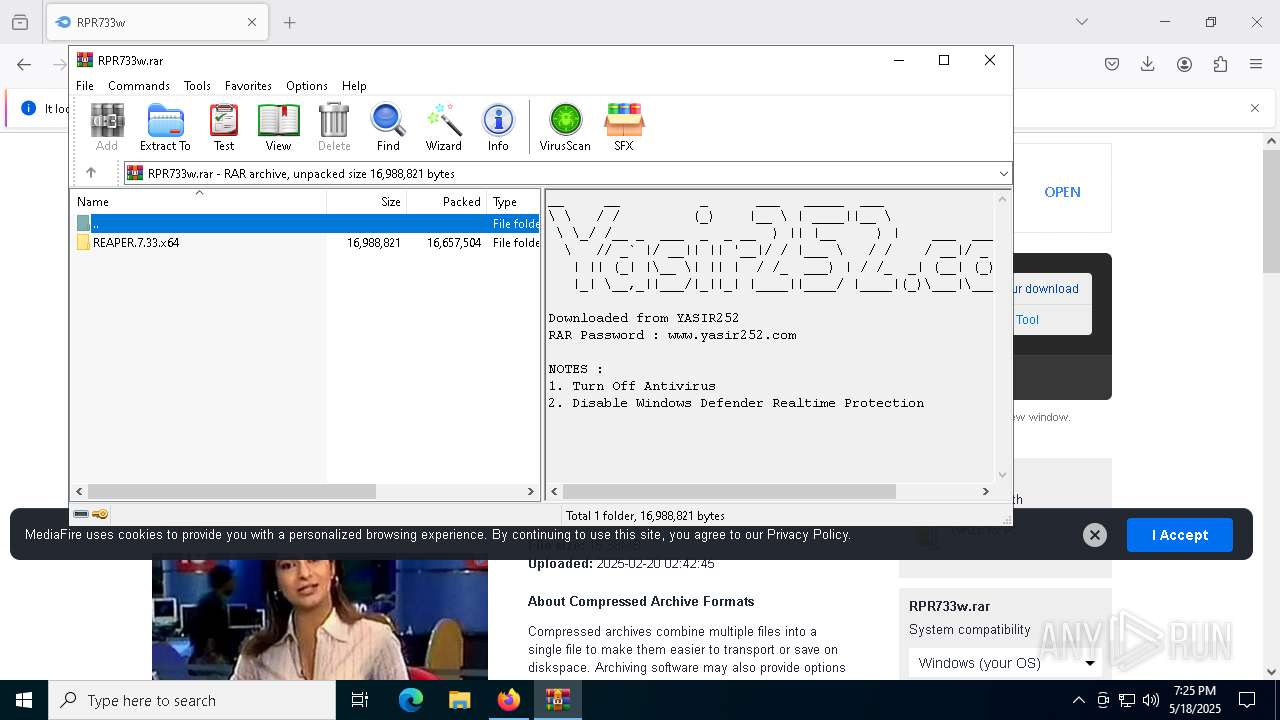
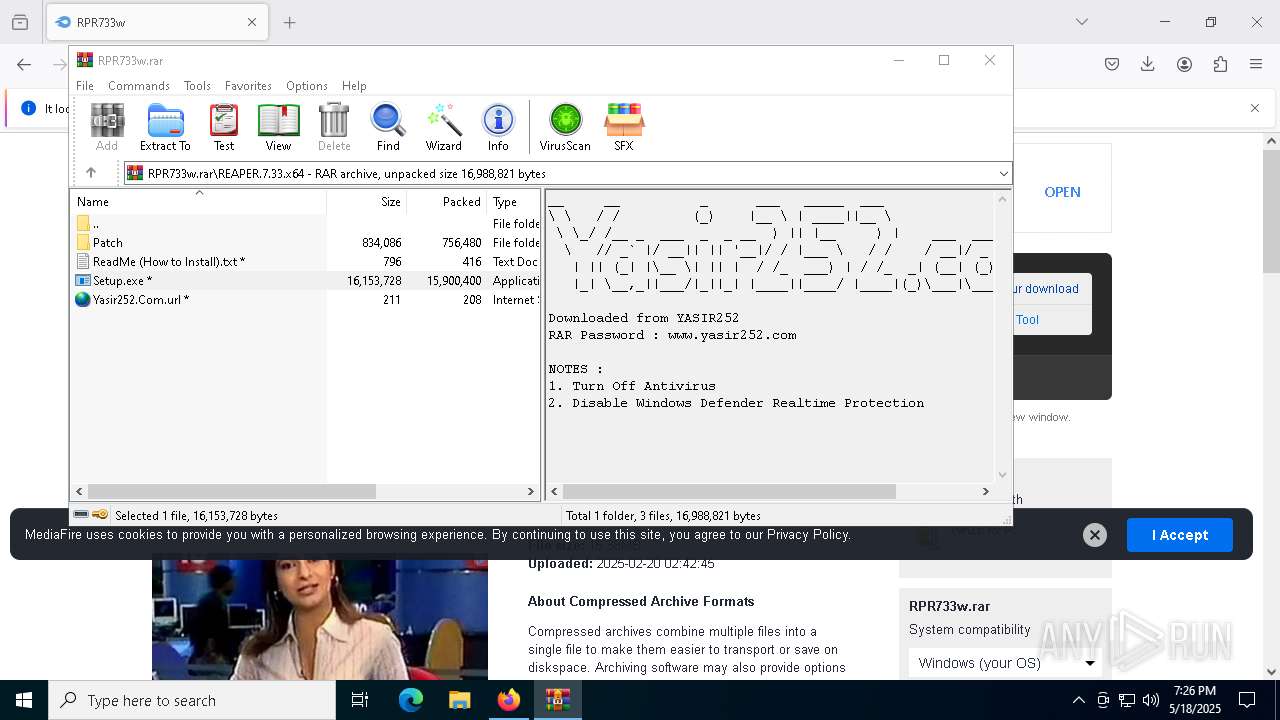
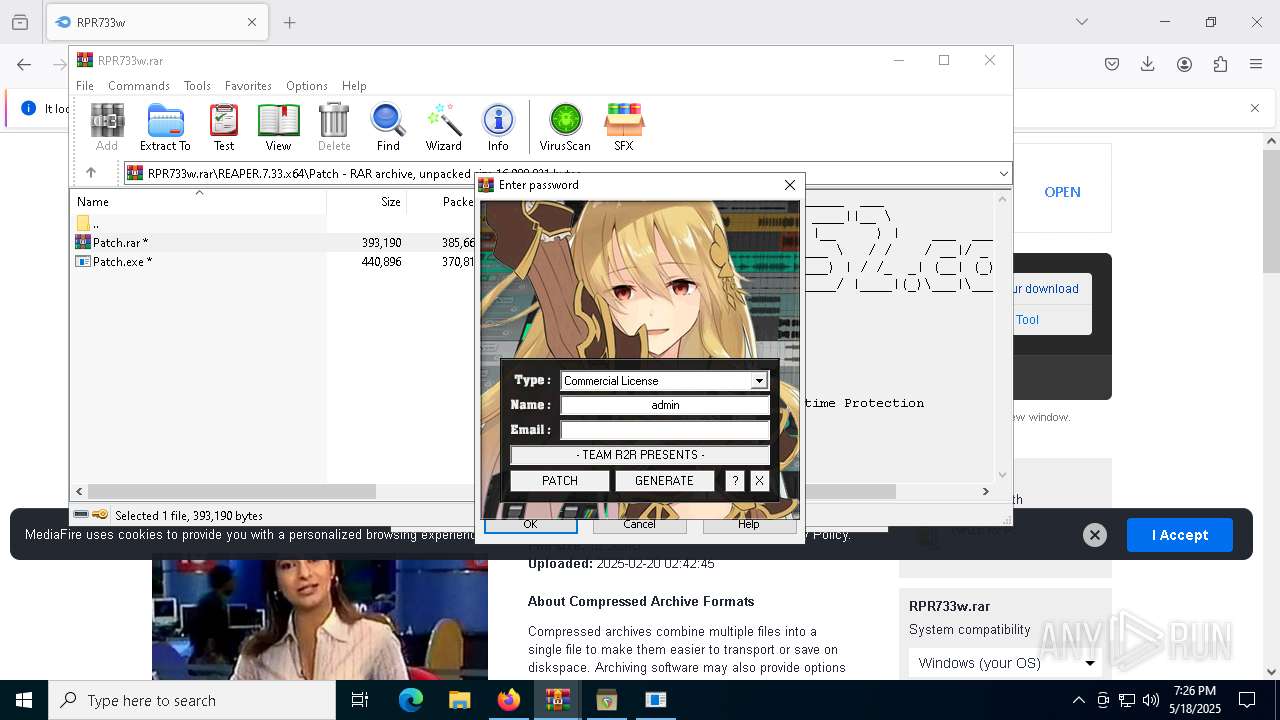
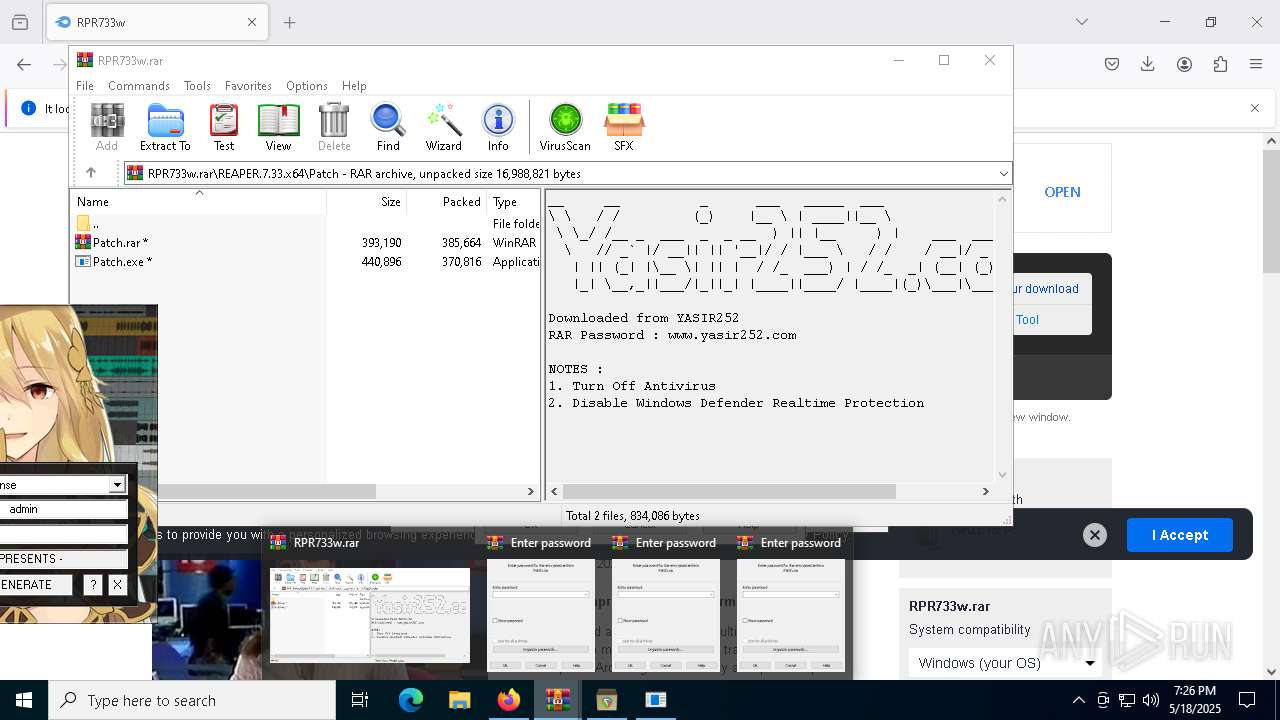
| URL: | https://www.yasir252.com/file/?link=aHR0cHM6Ly93d3cubWVkaWFmaXJlLmNvbS9maWxlLzlleG92YnB0cXVxNDBnNS9SUFI3MzN3LnJhci9maWxl |
| Full analysis: | https://app.any.run/tasks/f8b7fa58-739a-4d16-8fb2-eaf05aa098f4 |
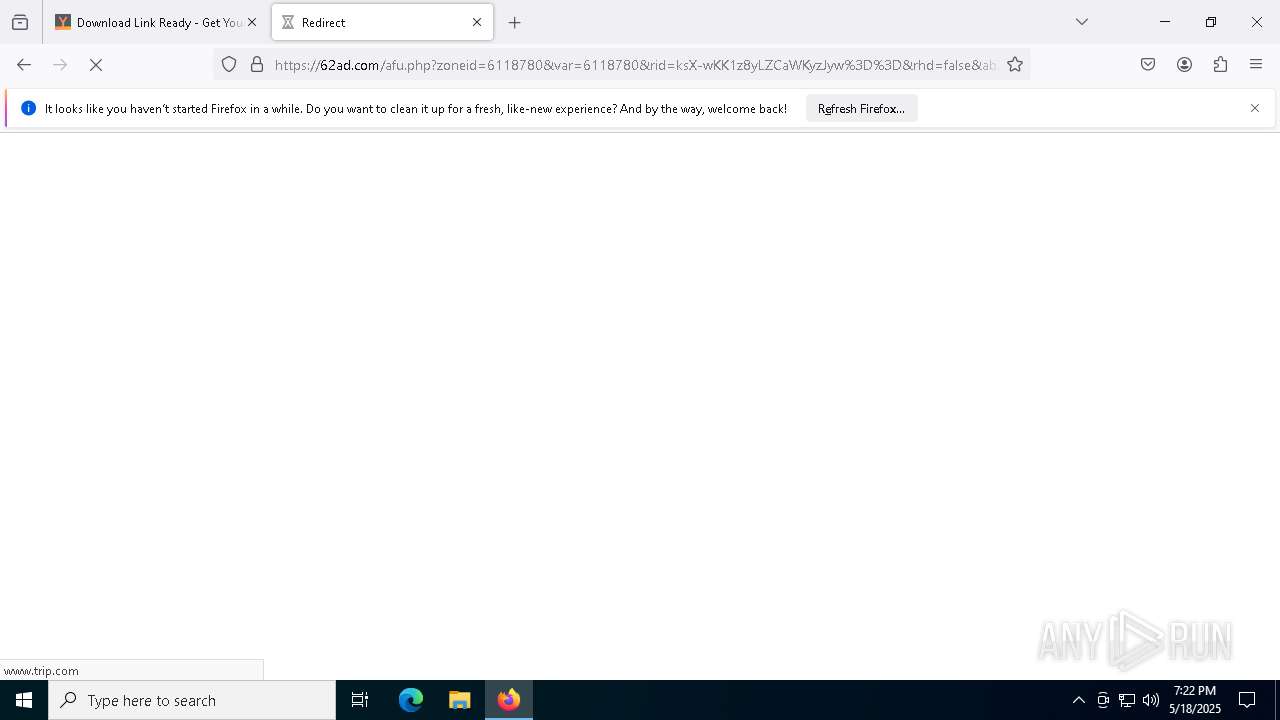
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 19:21:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E20DAF44900B6B98E9D3FA0CF955F640 |
| SHA1: | BF1FB2E226EF73FF825CA8411675B50B178ED69A |
| SHA256: | F1EED4D3C07802F78A7E6A5F72135332E68B1C0E5069A565B2537FA51E27CE83 |
| SSDEEP: | 3:N8DSL1yxoaC6DcOPBGQ9bpIn75yLphJAicqe5iczoWpb2IEmn:2OLWhpe75yLOSe8/W1vEm |
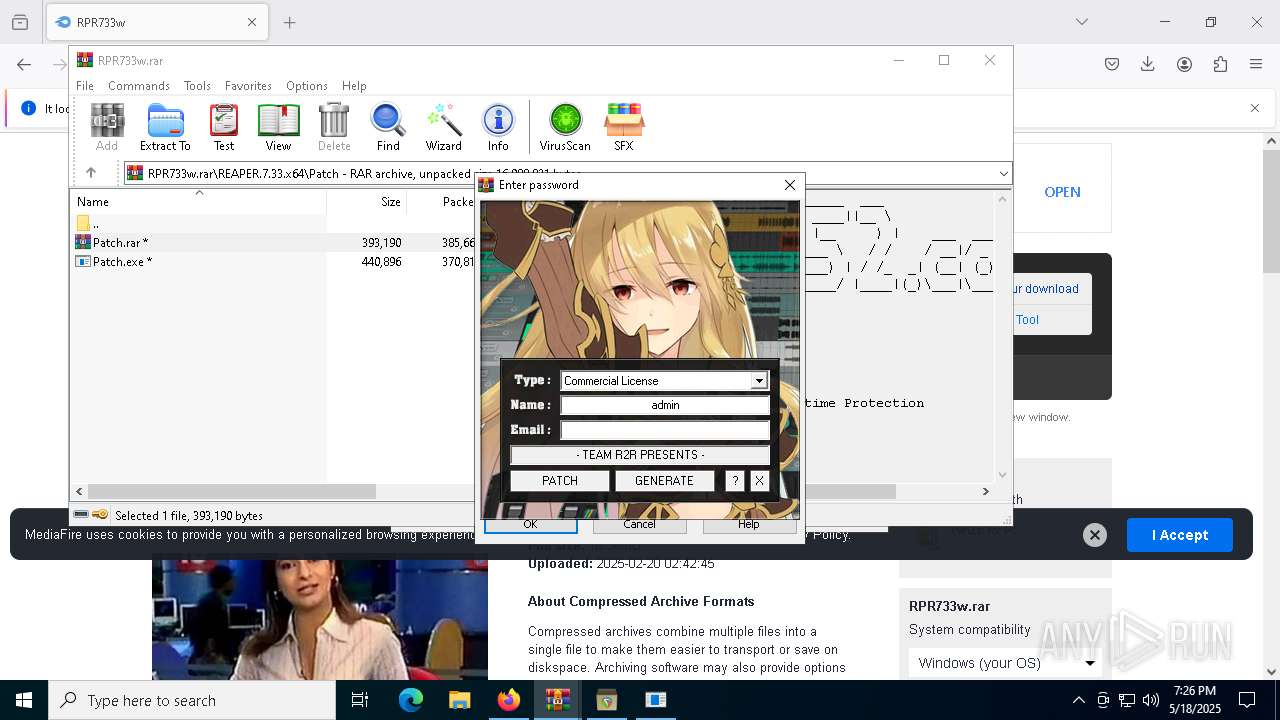
MALICIOUS
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
Connecting to InterPlanetary File System domains
- firefox.exe (PID: 7308)
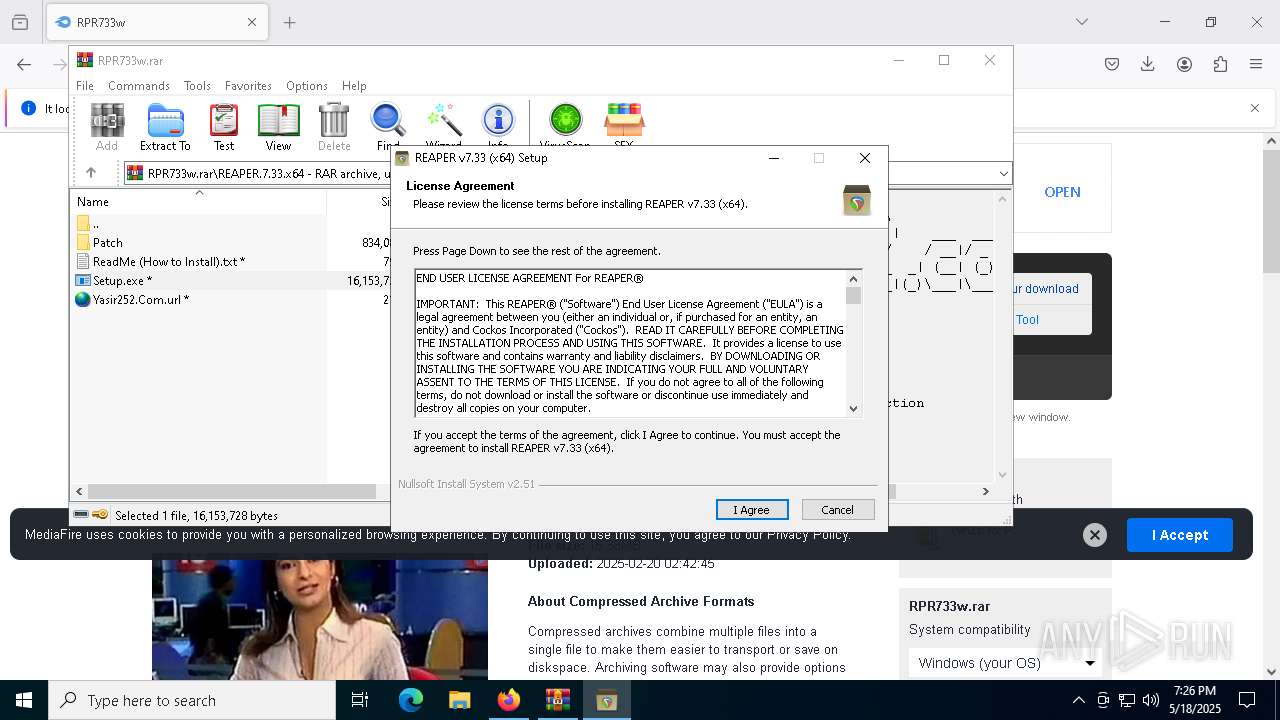
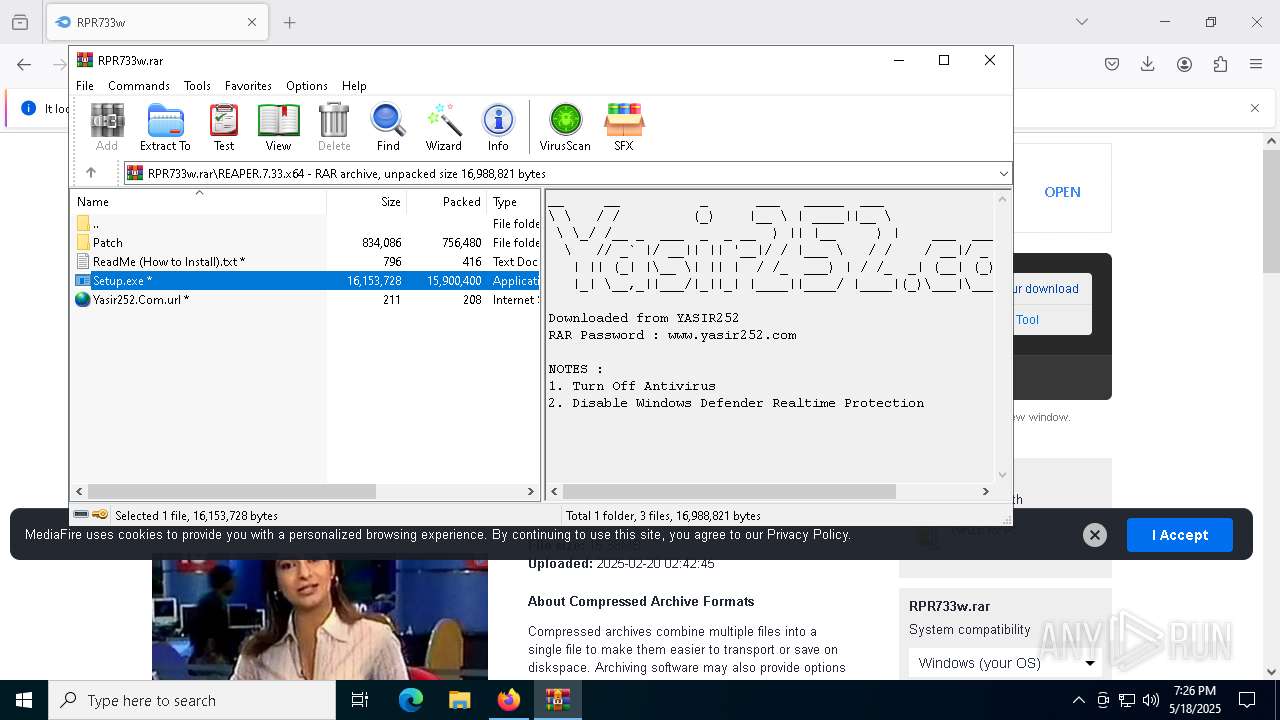
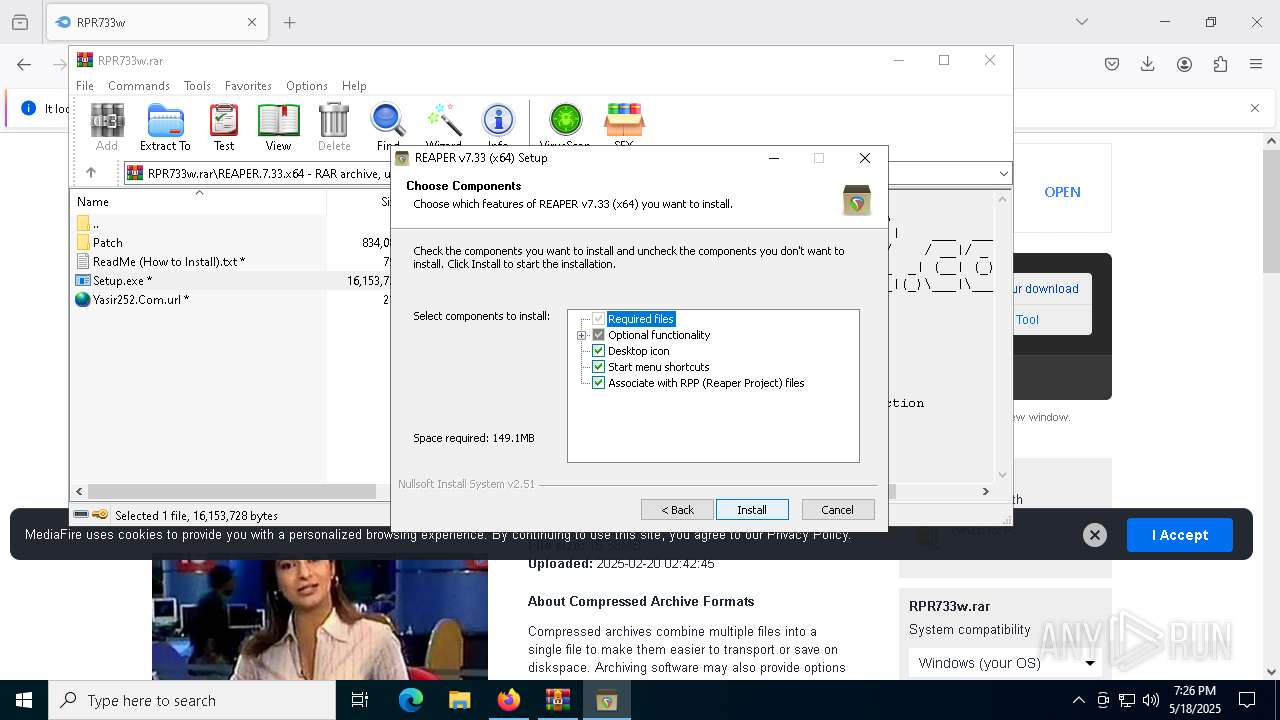
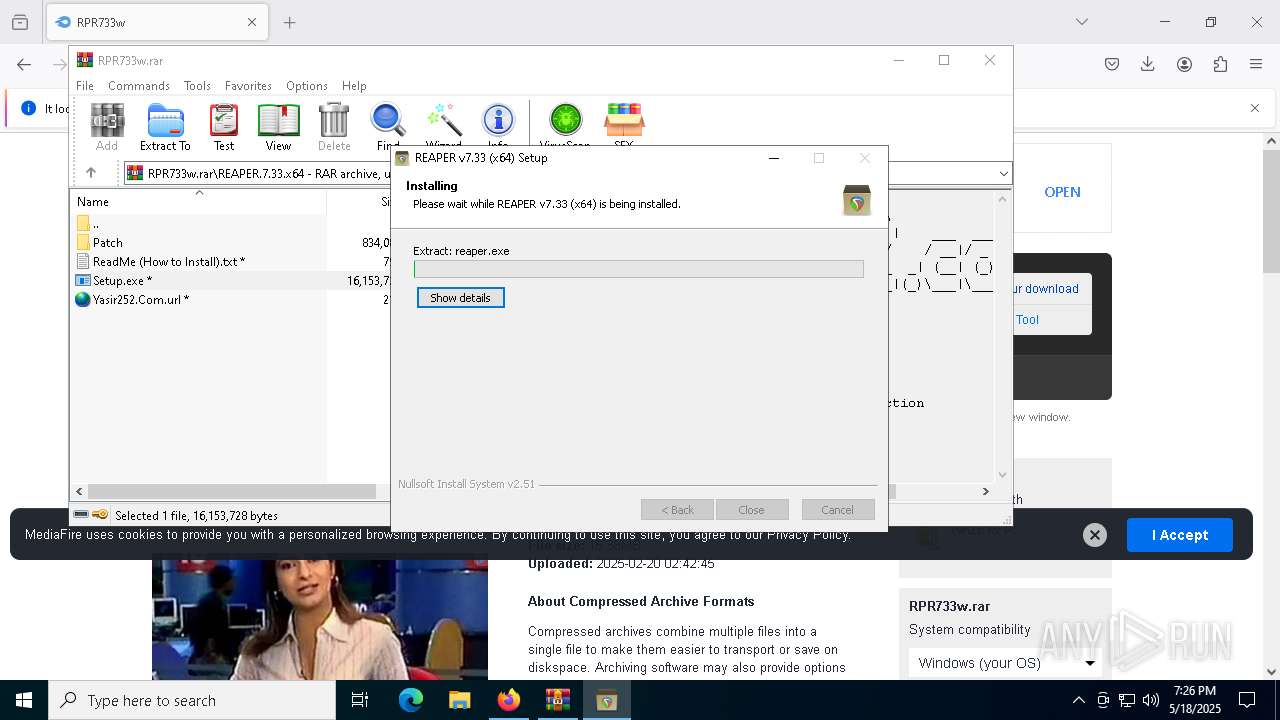
Executing a file with an untrusted certificate
- Setup.exe (PID: 5256)
- Setup.exe (PID: 4448)
- Setup.exe (PID: 9184)
SUSPICIOUS
Potential Corporate Privacy Violation
- firefox.exe (PID: 7308)
Malware-specific behavior (creating "System.dll" in Temp)
- Setup.exe (PID: 5256)
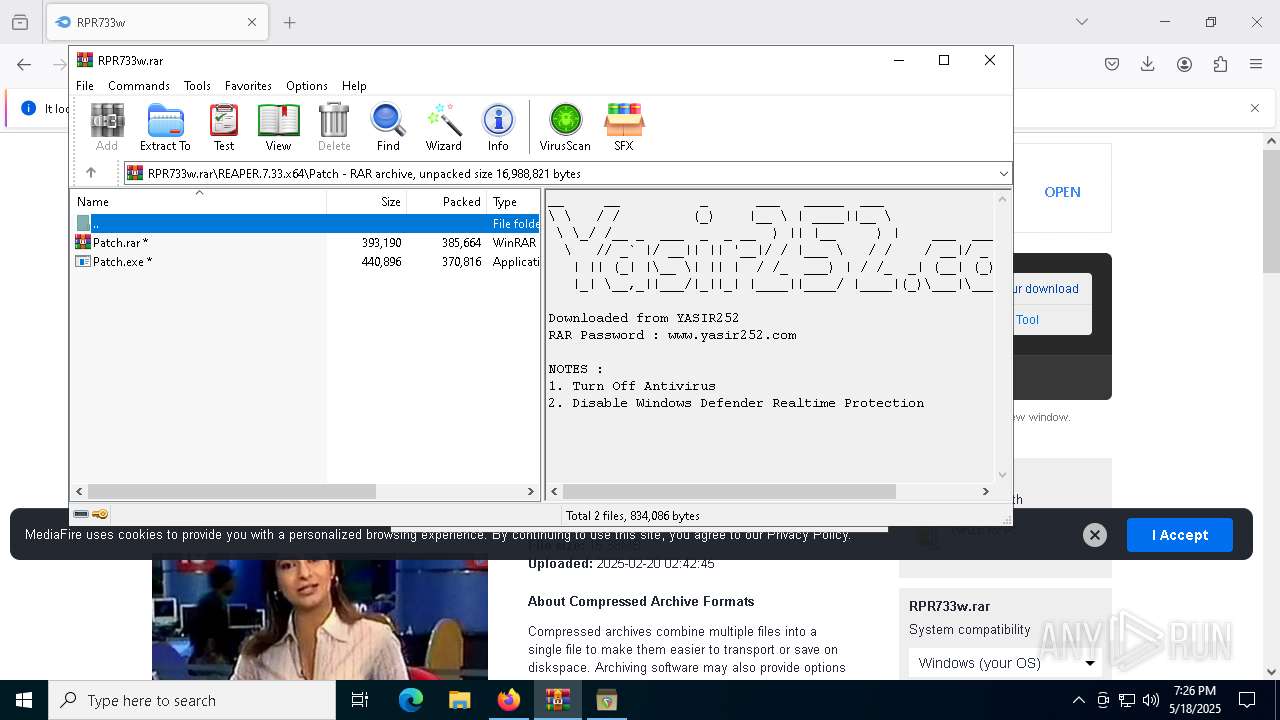
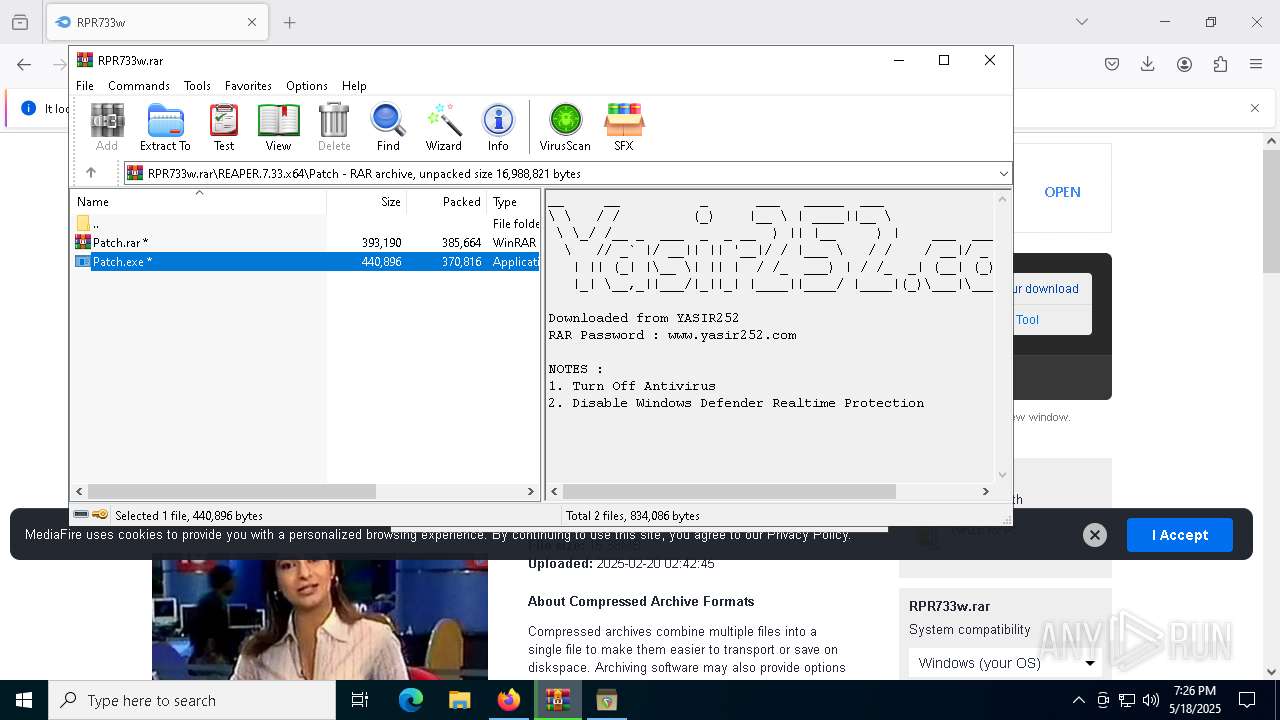
Executable content was dropped or overwritten
- Patch.exe (PID: 8732)
- Setup.exe (PID: 9184)
- Setup.exe (PID: 4448)
- Setup.exe (PID: 5256)
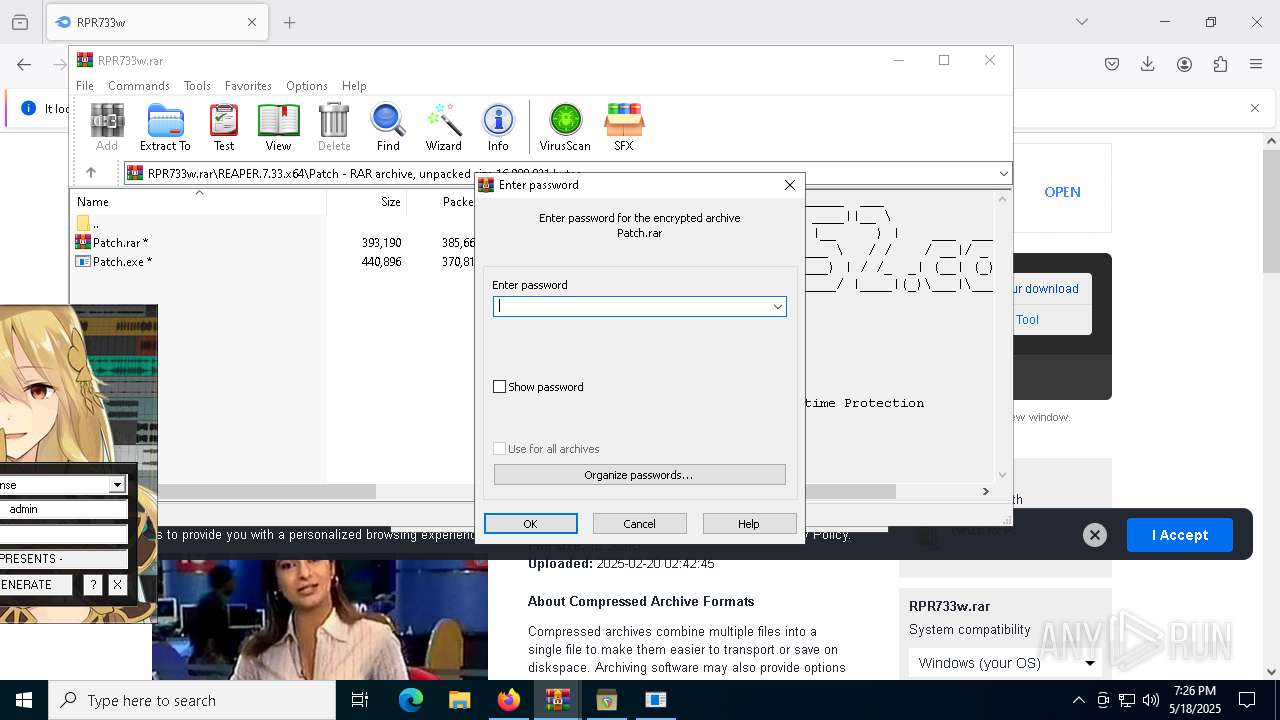
Application launched itself
- WinRAR.exe (PID: 6044)
- Setup.exe (PID: 4448)
- Setup.exe (PID: 5256)
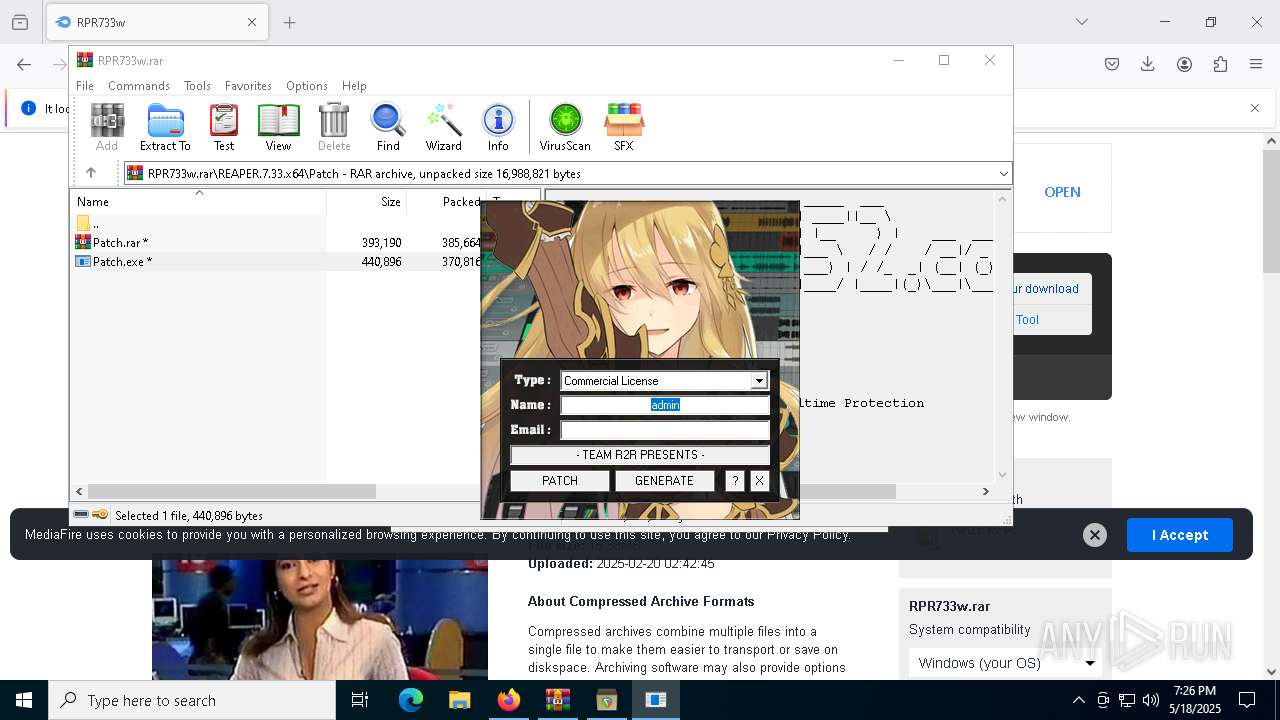
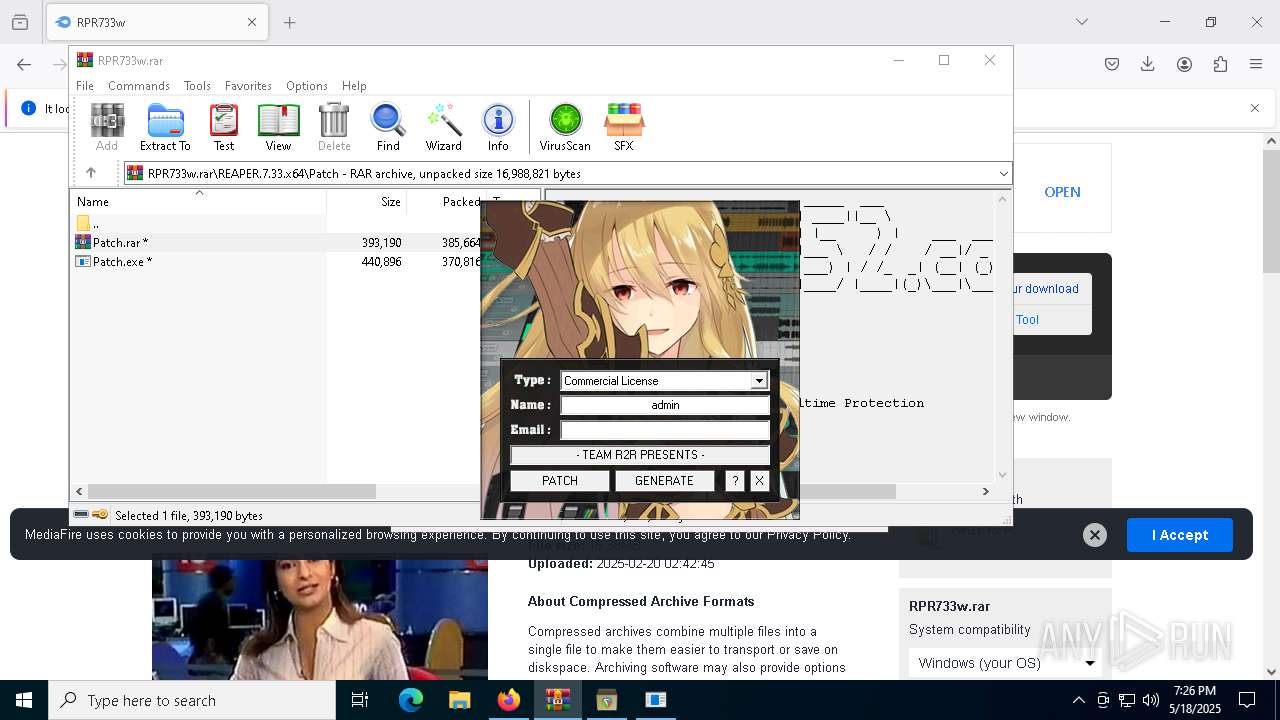
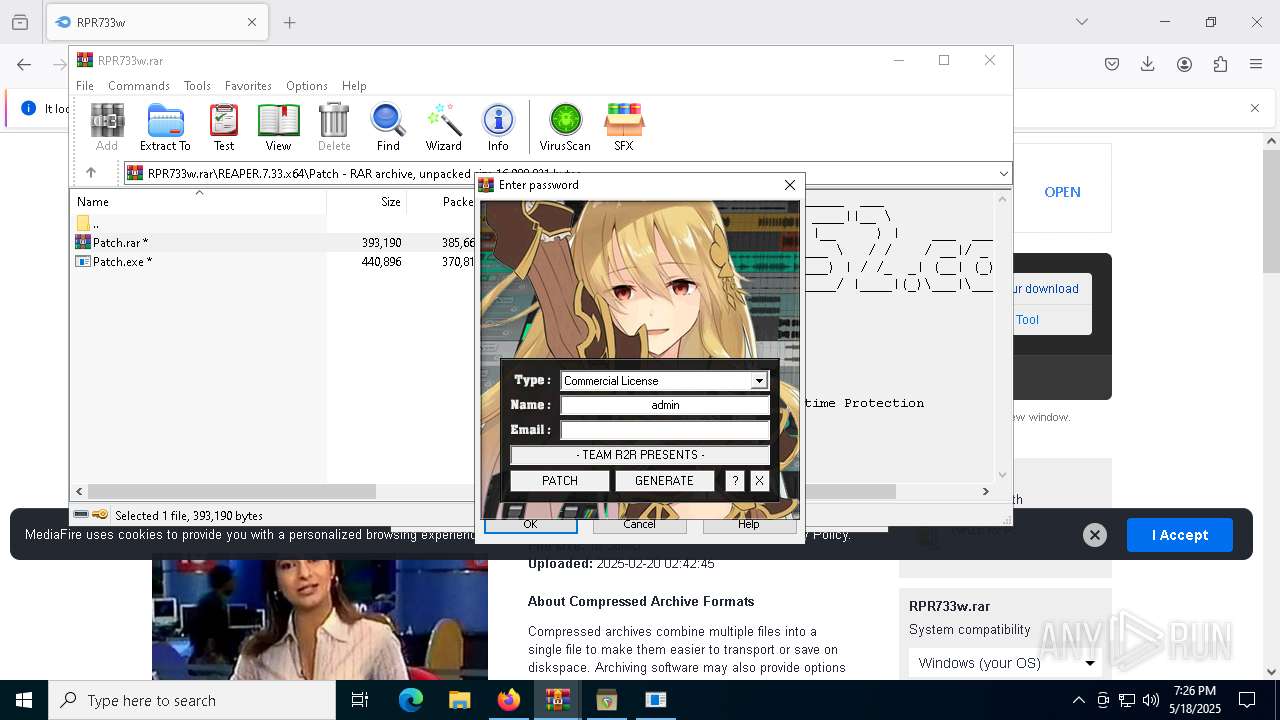
There is functionality for taking screenshot (YARA)
- Setup.exe (PID: 4448)
- Setup.exe (PID: 9184)
- Patch.exe (PID: 8732)
INFO
Application launched itself
- firefox.exe (PID: 7308)
- firefox.exe (PID: 7288)
Reads the software policy settings
- slui.exe (PID: 8416)
- slui.exe (PID: 1128)
Checks proxy server information
- slui.exe (PID: 1128)
Executable content was dropped or overwritten
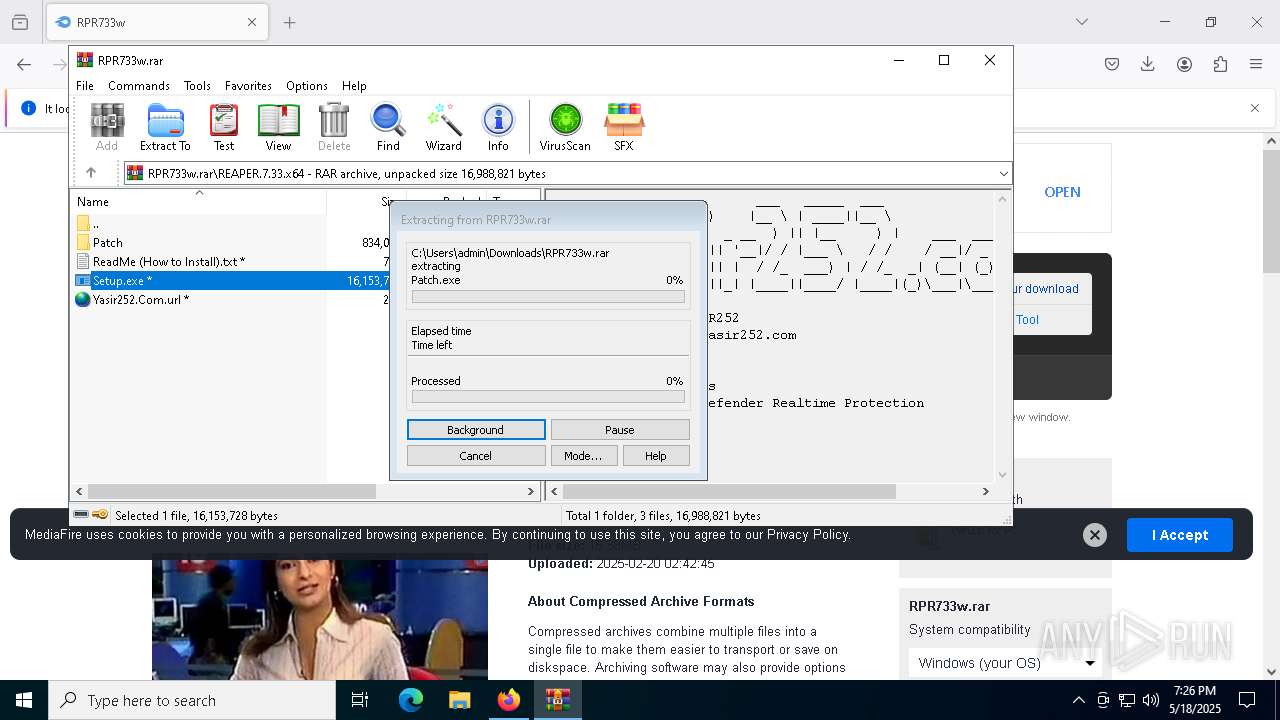
- WinRAR.exe (PID: 6044)
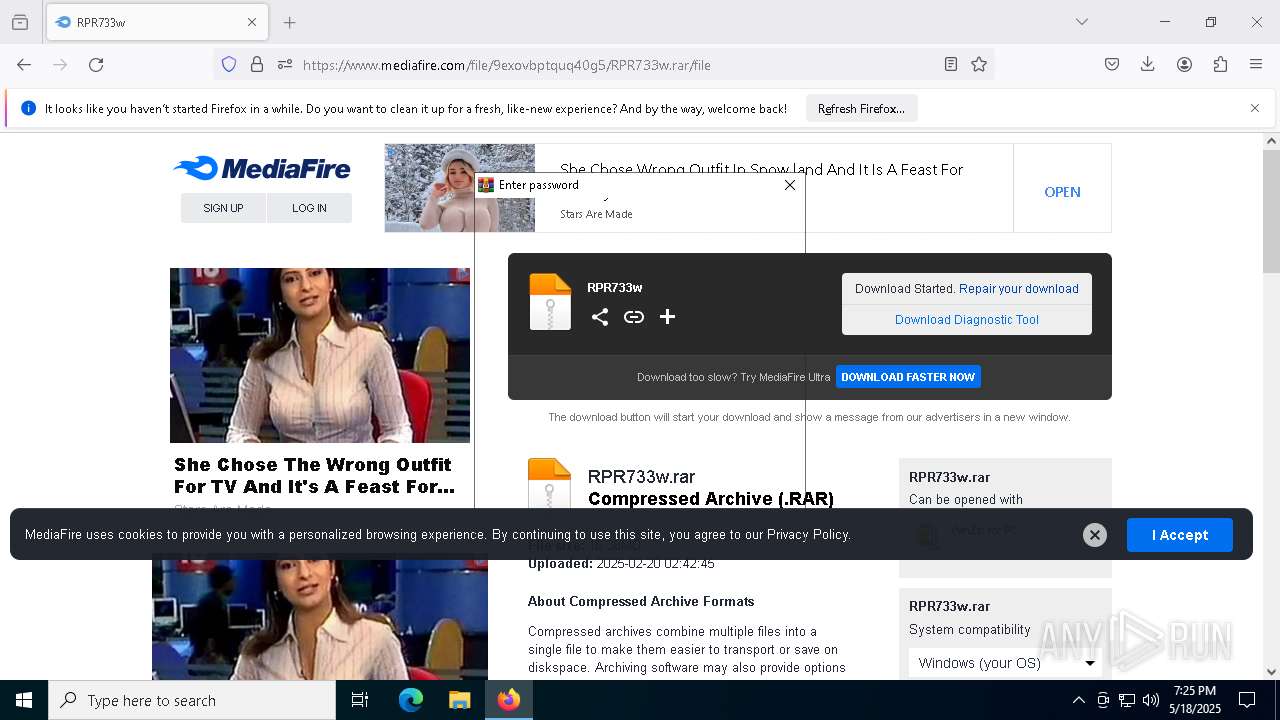
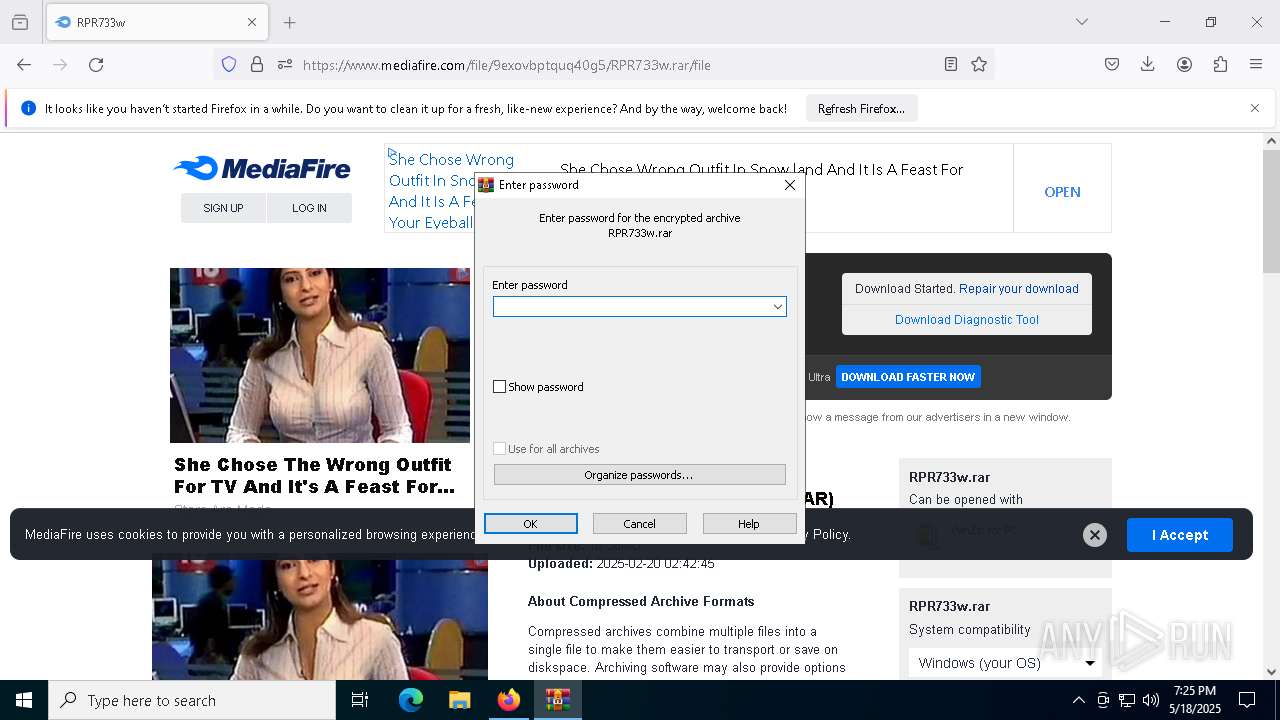
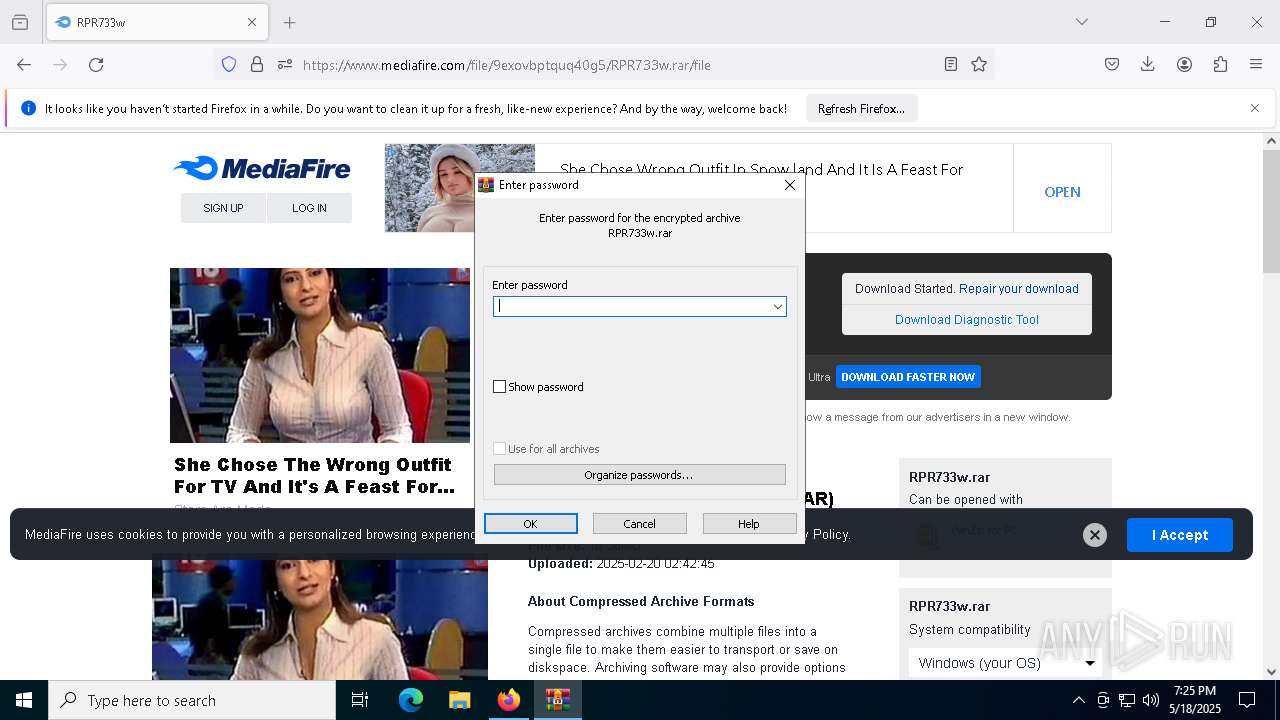
Manual execution by a user
- WinRAR.exe (PID: 6044)
The sample compiled with english language support
- Setup.exe (PID: 9184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
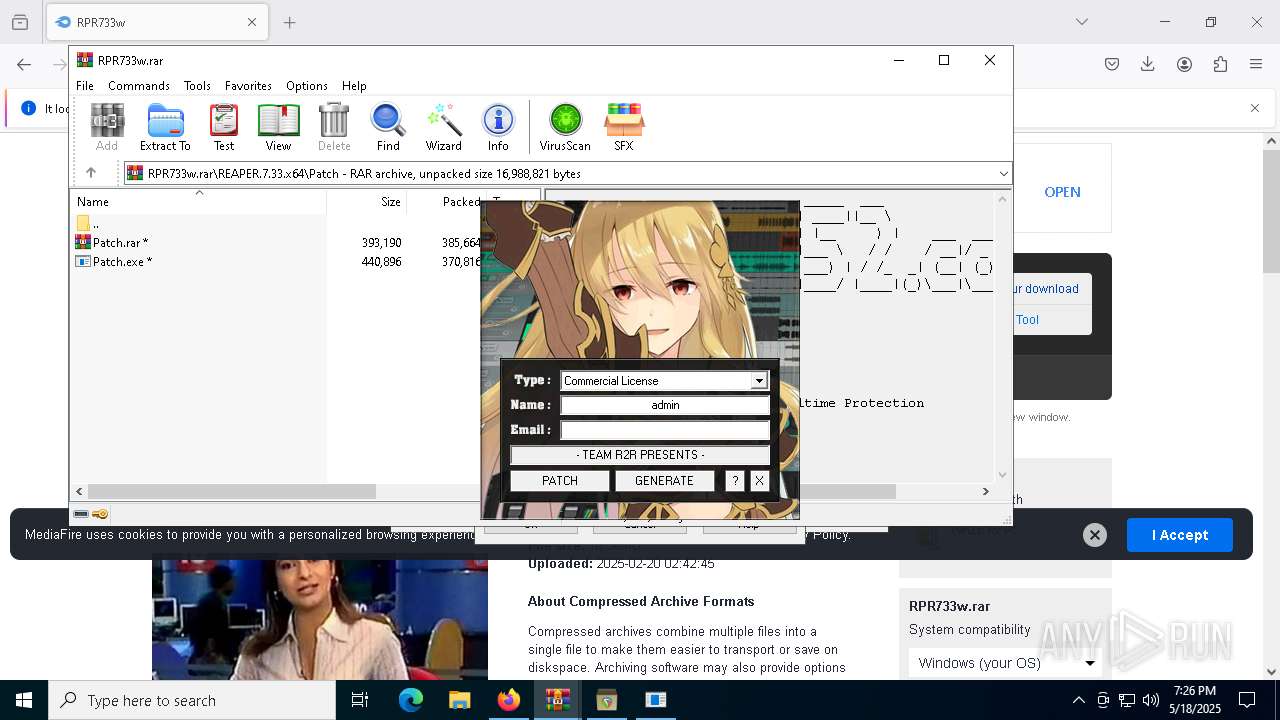
Total processes
185
Monitored processes
51
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | C:\Users\admin\AppData\Local\Temp\keygen.exe | C:\Users\admin\AppData\Local\Temp\keygen.exe | — | Patch.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1128 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3768 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5708 -childID 14 -isForBrowser -prefsHandle 4172 -prefMapHandle 4036 -prefsLen 31642 -prefMapSize 244583 -jsInitHandle 1376 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {db265331-422b-4006-afec-53e3ec5ab9cf} 7308 "\\.\pipe\gecko-crash-server-pipe.7308" 1bad76dc850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 4164 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=7252 -childID 29 -isForBrowser -prefsHandle 7428 -prefMapHandle 7180 -prefsLen 31684 -prefMapSize 244583 -jsInitHandle 1376 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {3ceb0c42-5ba8-4ad2-8c9f-606342652978} 7308 "\\.\pipe\gecko-crash-server-pipe.7308" 1bad76dcbd0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4300 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIb6044.19205\Patch.rar | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.91.0 Modules
| |||||||||||||||
| 4448 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=7104 -childID 19 -isForBrowser -prefsHandle 6908 -prefMapHandle 6384 -prefsLen 31642 -prefMapSize 244583 -jsInitHandle 1376 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {ac25e0a4-12c4-407c-89fc-c9bed52a3c81} 7308 "\\.\pipe\gecko-crash-server-pipe.7308" 1bad84cd850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
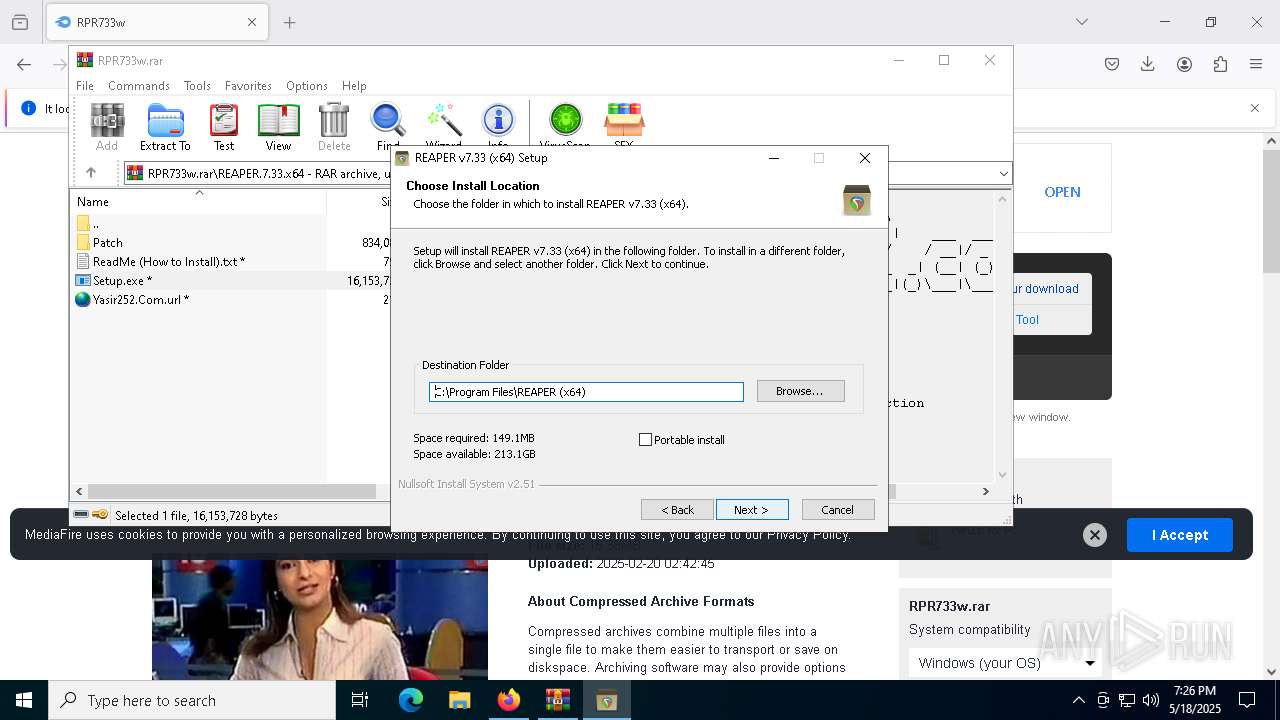
| 4448 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb6044.17036\REAPER.7.33.x64\Setup.exe" /SKIP2 /ADMIN /D=C:\Program Files\REAPER (x64) | C:\Users\admin\AppData\Local\Temp\Rar$EXb6044.17036\REAPER.7.33.x64\Setup.exe | Setup.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4724 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=7920 -childID 28 -isForBrowser -prefsHandle 7772 -prefMapHandle 7760 -prefsLen 31684 -prefMapSize 244583 -jsInitHandle 1376 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {c77b1934-231f-4b51-b04e-273bdfa56991} 7308 "\\.\pipe\gecko-crash-server-pipe.7308" 1bad84cda10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5256 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb6044.17036\REAPER.7.33.x64\Setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb6044.17036\REAPER.7.33.x64\Setup.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
46 469
Read events
46 441
Write events
28
Delete events
0
Modification events
| (PID) Process: | (7308) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\RPR733w.rar | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6044) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
61
Suspicious files
635
Text files
874
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7308 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7308 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7308 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7308 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7308 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7308 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 7308 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 7308 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 7308 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7308 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
142
TCP/UDP connections
490
DNS requests
527
Threats
39
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7308 | firefox.exe | POST | — | 142.250.186.99:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7308 | firefox.exe | POST | 200 | 142.250.186.99:80 | http://o.pki.goog/s/wr3/3H4 | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.161:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.161:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7308 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7308 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7308 | firefox.exe | POST | 200 | 184.24.77.79:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7308 | firefox.exe | POST | 200 | 142.250.186.99:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.161:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.161:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7308 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
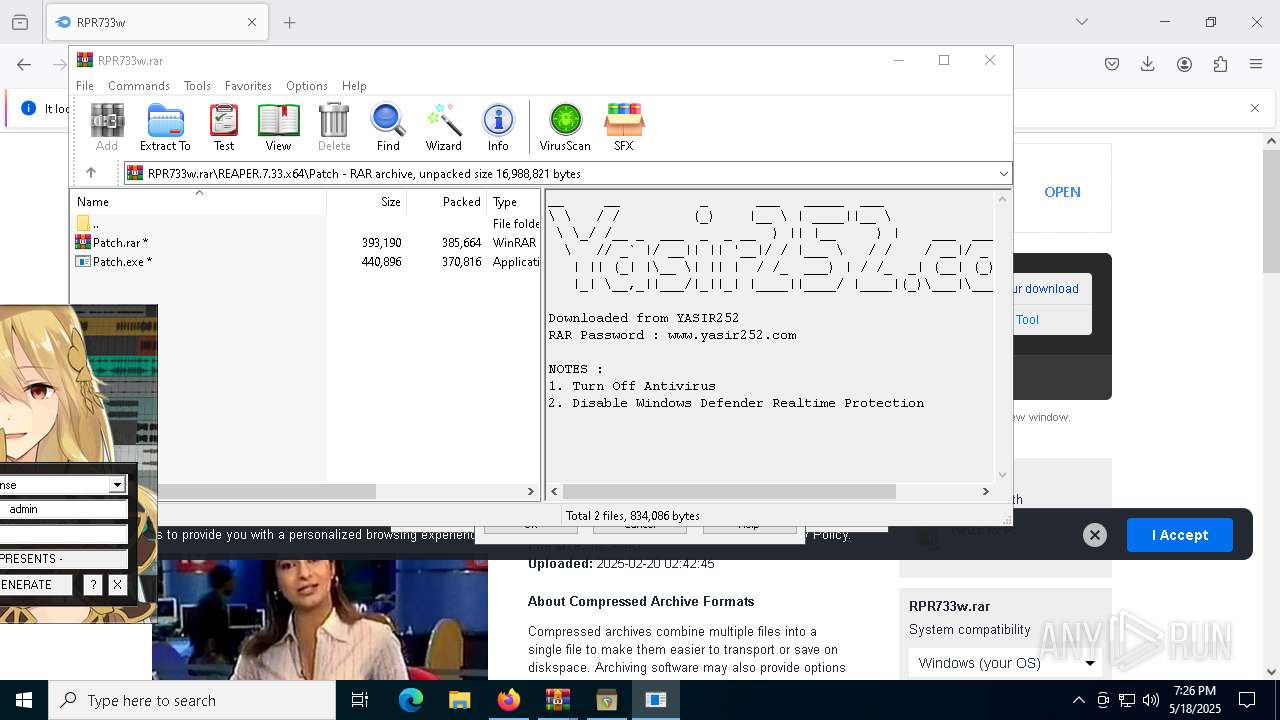
7308 | firefox.exe | 178.128.90.9:443 | www.yasir252.com | DIGITALOCEAN-ASN | SG | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
www.yasir252.com |
| unknown |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (aiharsoreersu .net) |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (aiharsoreersu .net) |
2196 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (aiharsoreersu .net) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING Peer-to-Peer File Sharing Service Domain in DNS Lookup (ipfs .io) |
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING Peer-to-Peer File Sharing Service Domain in DNS Lookup (ipfs .io) |
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING Peer-to-Peer File Sharing Service Domain in DNS Lookup (ipfs .io) |
7308 | firefox.exe | Potentially Bad Traffic | ET FILE_SHARING Observed Peer-to-Peer File Sharing Service Domain (ipfs .io in TLS SNI) |