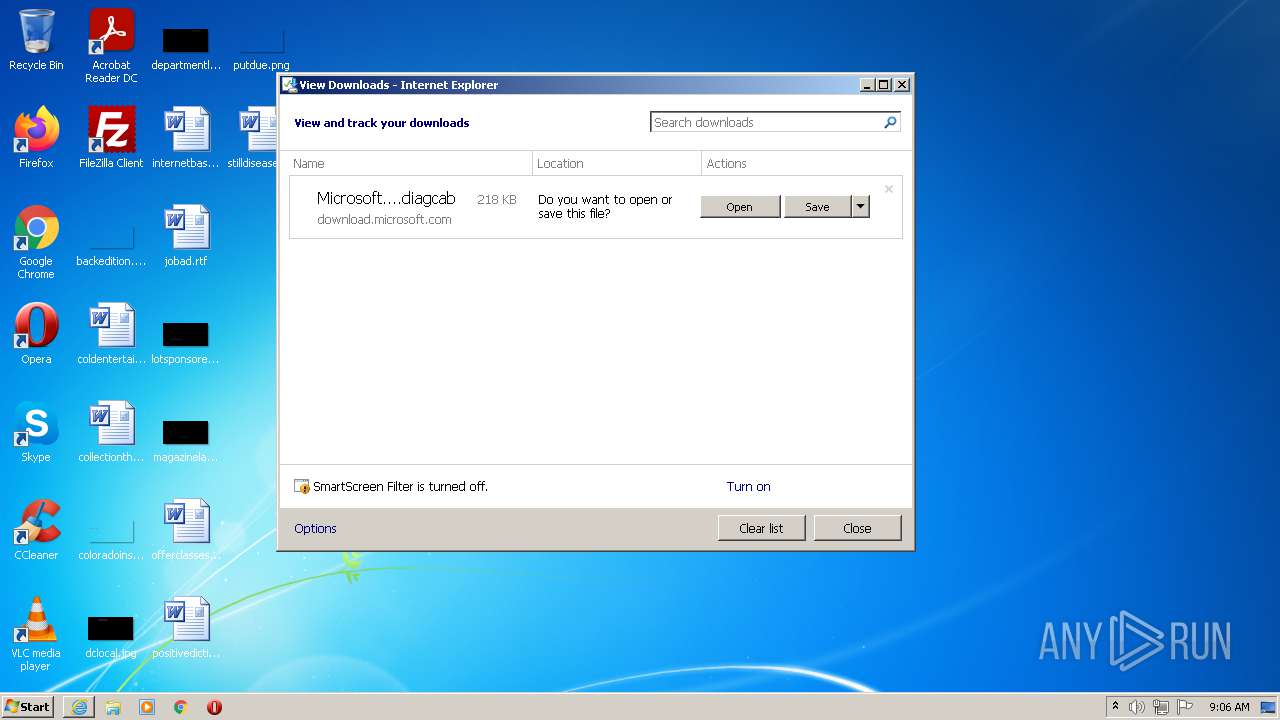
| URL: | https://download.microsoft.com/download/7/E/9/7E9188C0-2511-4B01-8B4E-0A641EC2F600/MicrosoftProgram_Install_and_Uninstall.meta.diagcab |
| Full analysis: | https://app.any.run/tasks/7cc04995-2fc8-464b-a29a-d52d669cc515 |
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2021, 08:05:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8745935352C37AF4DC2BA9D639AEE225 |
| SHA1: | 683906968C58FAD341A0AA52CCD4AC809EBC8414 |
| SHA256: | F1E392A7AF30AB01410DCBF5485FD3B0A430F75F5D39457B988218198CC4337C |
| SSDEEP: | 3:N8SElyKRtR8LSOcYd5XBUI34UgmXvr3uTXuZzXrWBM3:2SKTD8mOH54UjabutyM3 |
MALICIOUS
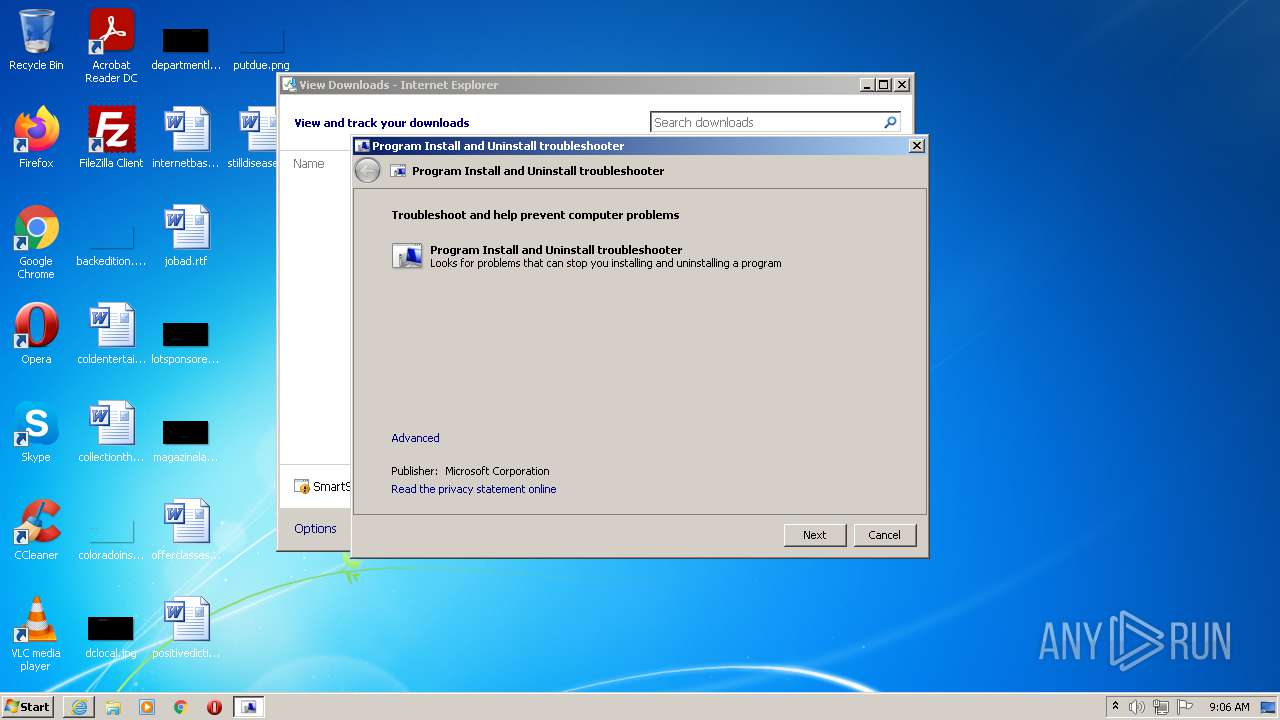
Drops executable file immediately after starts
- msdt.exe (PID: 2844)
- msdt.exe (PID: 3588)
- csc.exe (PID: 2820)
- csc.exe (PID: 392)
- csc.exe (PID: 2712)
- csc.exe (PID: 424)
- csc.exe (PID: 1148)
- csc.exe (PID: 3664)
- csc.exe (PID: 3908)
- csc.exe (PID: 2636)
- csc.exe (PID: 3048)
- csc.exe (PID: 3440)
Starts Visual C# compiler
- sdiagnhost.exe (PID: 2276)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2660)
Application launched itself
- msdt.exe (PID: 2844)
Creates files in the Windows directory
- msdt.exe (PID: 3588)
- sdiagnhost.exe (PID: 2276)
Executable content was dropped or overwritten
- msdt.exe (PID: 3588)
- csc.exe (PID: 392)
- csc.exe (PID: 2820)
- csc.exe (PID: 2712)
- csc.exe (PID: 424)
- csc.exe (PID: 1148)
- csc.exe (PID: 3664)
- csc.exe (PID: 3440)
- msdt.exe (PID: 2844)
- csc.exe (PID: 3908)
- csc.exe (PID: 2636)
- csc.exe (PID: 3048)
Executed via COM
- sdiagnhost.exe (PID: 2276)
- DllHost.exe (PID: 3964)
- DllHost.exe (PID: 3960)
Checks supported languages
- csc.exe (PID: 2820)
- cvtres.exe (PID: 2656)
- cvtres.exe (PID: 3748)
- csc.exe (PID: 392)
- cvtres.exe (PID: 3192)
- csc.exe (PID: 2712)
- csc.exe (PID: 424)
- cvtres.exe (PID: 340)
- csc.exe (PID: 1148)
- cvtres.exe (PID: 2052)
- csc.exe (PID: 3664)
- cvtres.exe (PID: 528)
- csc.exe (PID: 3440)
- cvtres.exe (PID: 1768)
- csc.exe (PID: 3908)
- cvtres.exe (PID: 2788)
- cvtres.exe (PID: 2948)
- csc.exe (PID: 2636)
- csc.exe (PID: 3048)
- cvtres.exe (PID: 588)
Drops a file with a compile date too recent
- csc.exe (PID: 2820)
- csc.exe (PID: 392)
- csc.exe (PID: 2712)
- csc.exe (PID: 424)
- csc.exe (PID: 1148)
- csc.exe (PID: 3664)
- csc.exe (PID: 3440)
- csc.exe (PID: 3908)
- csc.exe (PID: 2636)
- csc.exe (PID: 3048)
Drops a file that was compiled in debug mode
- csc.exe (PID: 2820)
- csc.exe (PID: 392)
- csc.exe (PID: 2712)
- csc.exe (PID: 424)
- csc.exe (PID: 1148)
- csc.exe (PID: 3664)
- csc.exe (PID: 3440)
- csc.exe (PID: 3908)
- csc.exe (PID: 2636)
- csc.exe (PID: 3048)
Executed as Windows Service
- vssvc.exe (PID: 2080)
Reads Environment values
- vssvc.exe (PID: 2080)
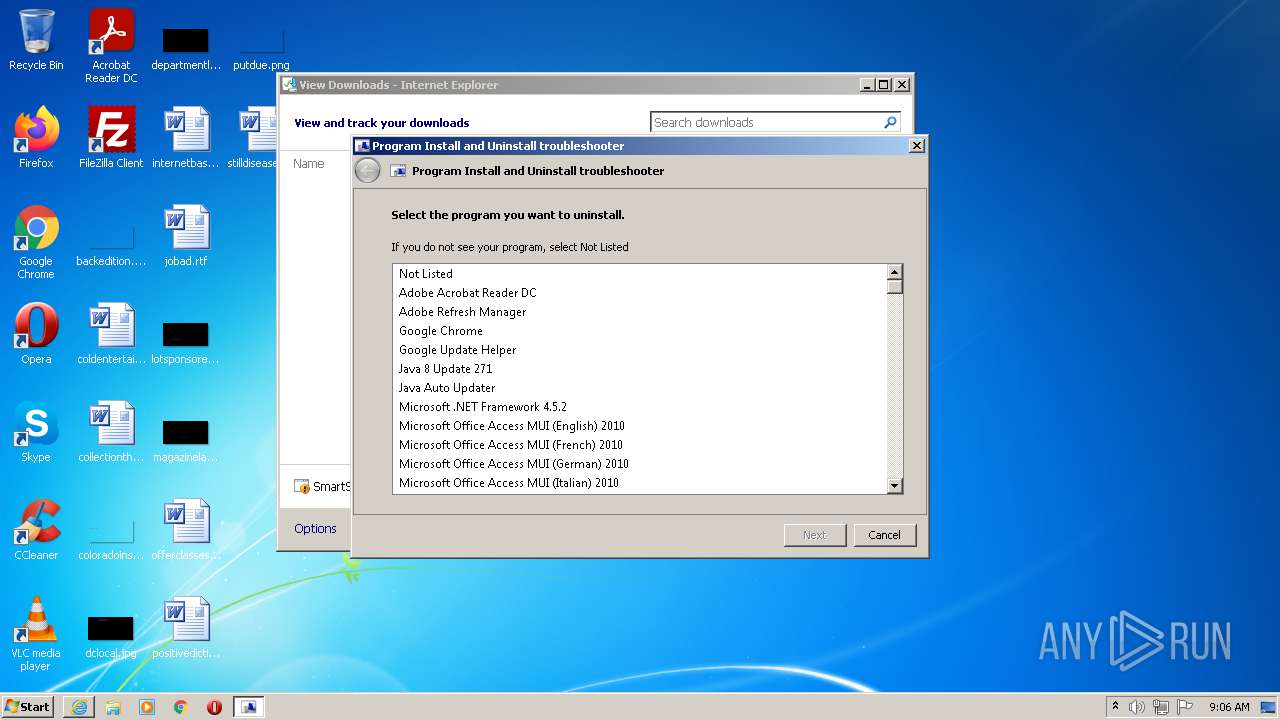
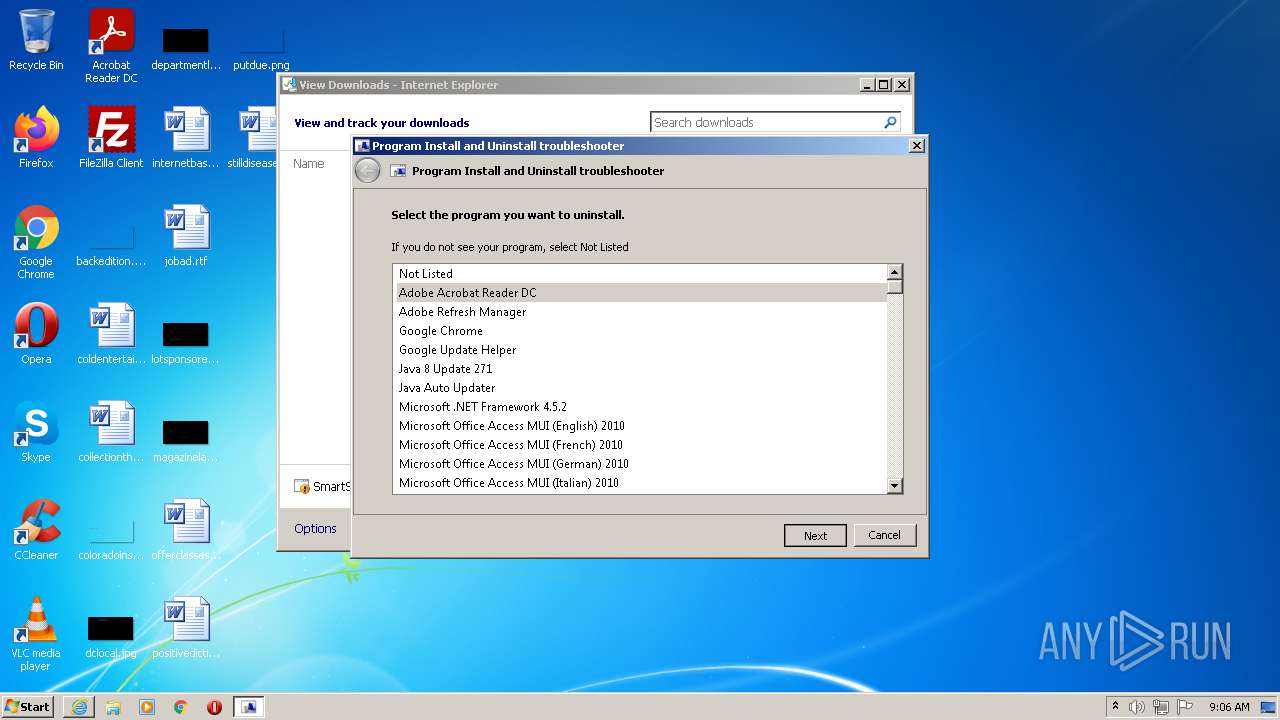
Searches for installed software
- DllHost.exe (PID: 3964)
INFO
Checks supported languages
- iexplore.exe (PID: 2968)
- msdt.exe (PID: 2844)
- iexplore.exe (PID: 2660)
- msdt.exe (PID: 3588)
- sdiagnhost.exe (PID: 2276)
- DllHost.exe (PID: 3960)
- DllHost.exe (PID: 3964)
- vssvc.exe (PID: 2080)
Changes internet zones settings
- iexplore.exe (PID: 2968)
Reads the computer name
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 2660)
- msdt.exe (PID: 2844)
- msdt.exe (PID: 3588)
- sdiagnhost.exe (PID: 2276)
- DllHost.exe (PID: 3960)
- DllHost.exe (PID: 3964)
- vssvc.exe (PID: 2080)
Application launched itself
- iexplore.exe (PID: 2968)
Checks Windows Trust Settings
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 2660)
- msdt.exe (PID: 2844)
- sdiagnhost.exe (PID: 2276)
- msdt.exe (PID: 3588)
Reads settings of System Certificates
- iexplore.exe (PID: 2968)
- iexplore.exe (PID: 2660)
- msdt.exe (PID: 2844)
- msdt.exe (PID: 3588)
- sdiagnhost.exe (PID: 2276)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2968)
Reads the date of Windows installation
- iexplore.exe (PID: 2968)
Reads internet explorer settings
- iexplore.exe (PID: 2660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
29
Malicious processes
4
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES11B7.tmp" "c:\Users\admin\AppData\Local\Temp\CSC11B6.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft� Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 392 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\9z25enp0.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 424 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\fi4ie8k3.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 528 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES1291.tmp" "c:\Users\admin\AppData\Local\Temp\CSC1290.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft� Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 588 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES1437.tmp" "c:\Users\admin\AppData\Local\Temp\CSC1436.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft� Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1148 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\04soctpk.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 1768 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES12FF.tmp" "c:\Users\admin\AppData\Local\Temp\CSC12FE.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft� Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2052 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES1224.tmp" "c:\Users\admin\AppData\Local\Temp\CSC1223.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft� Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2080 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2276 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
34 813
Read events
34 595
Write events
218
Delete events
0
Modification events
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 35399040 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30906760 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 335564352 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30906760 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
92
Suspicious files
10
Text files
203
Unknown types
116
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{4929B4C6-057B-11EC-A146-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF801BFC7160C6CCFD.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2660 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\MicrosoftProgram_Install_and_Uninstall.meta[1].diagcab | compressed | |
MD5:051742480645B325FD409537566541B5 | SHA256:0F1936FF1BC22D6233C8C2AFCA62E3F234CF2E57B84220E4D2666D53F7374DE5 | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFF884ECC9A017F84F.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\MicrosoftProgram_Install_and_Uninstall.meta.diagcab.hio7g71.partial:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2844 | msdt.exe | C:\Users\admin\AppData\Local\Temp\msdt\_A91C20F2-CF2F-4316-B6D9-1E005931D948_\cabpkg\DiagPackage.cat | cat | |
MD5:2913255678D8EC7977016992C69160A0 | SHA256:D8E3C911B98094A7AFB783DE5DCAE54860259F720FC035FD3854B26C8107E7A2 | |||
| 2968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
12
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1672 | svchost.exe | GET | 304 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?ed53382d525bee76 | US | — | — | whitelisted |
1672 | svchost.exe | GET | 304 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ee0438397e8fdef2 | US | — | — | whitelisted |
2968 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2968 | iexplore.exe | GET | 200 | 2.16.186.26:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?161ece0b70517f48 | unknown | compressed | 4.70 Kb | whitelisted |
2968 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2968 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2660 | iexplore.exe | 2.18.233.19:443 | download.microsoft.com | Akamai International B.V. | — | whitelisted |
— | — | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2968 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2660 | iexplore.exe | 2.16.186.26:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2968 | iexplore.exe | 2.16.186.26:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2968 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|