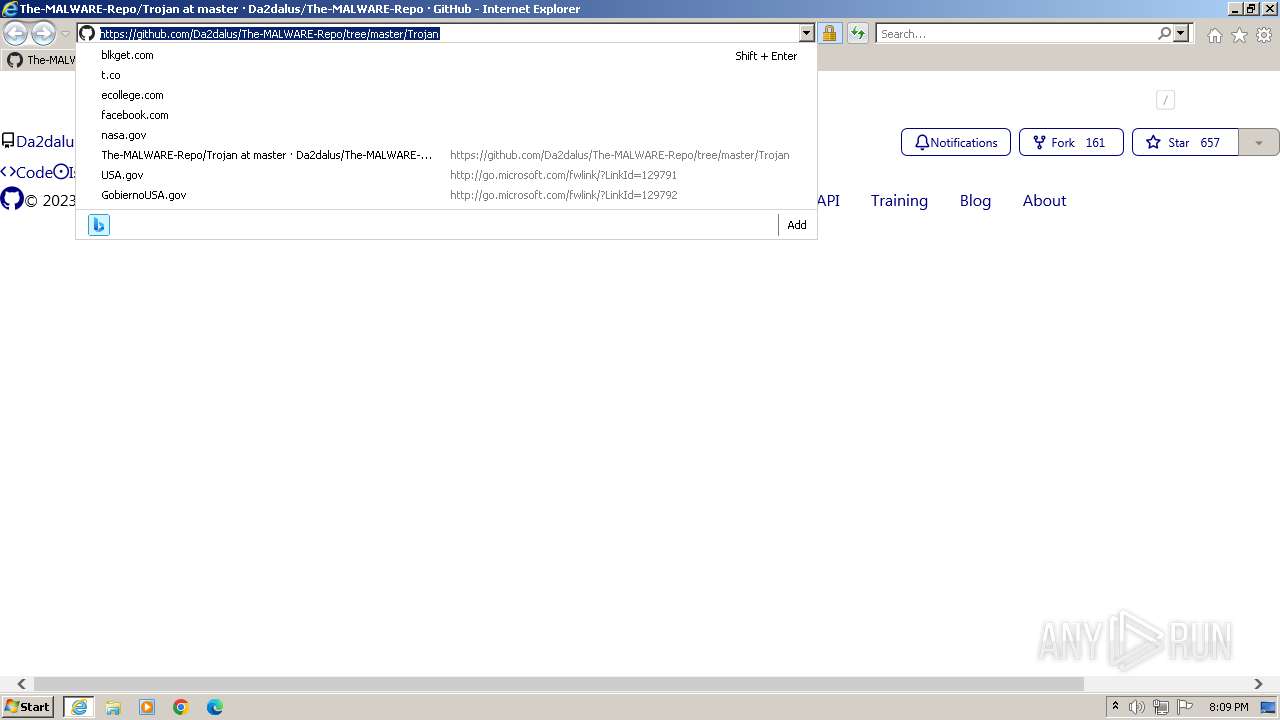
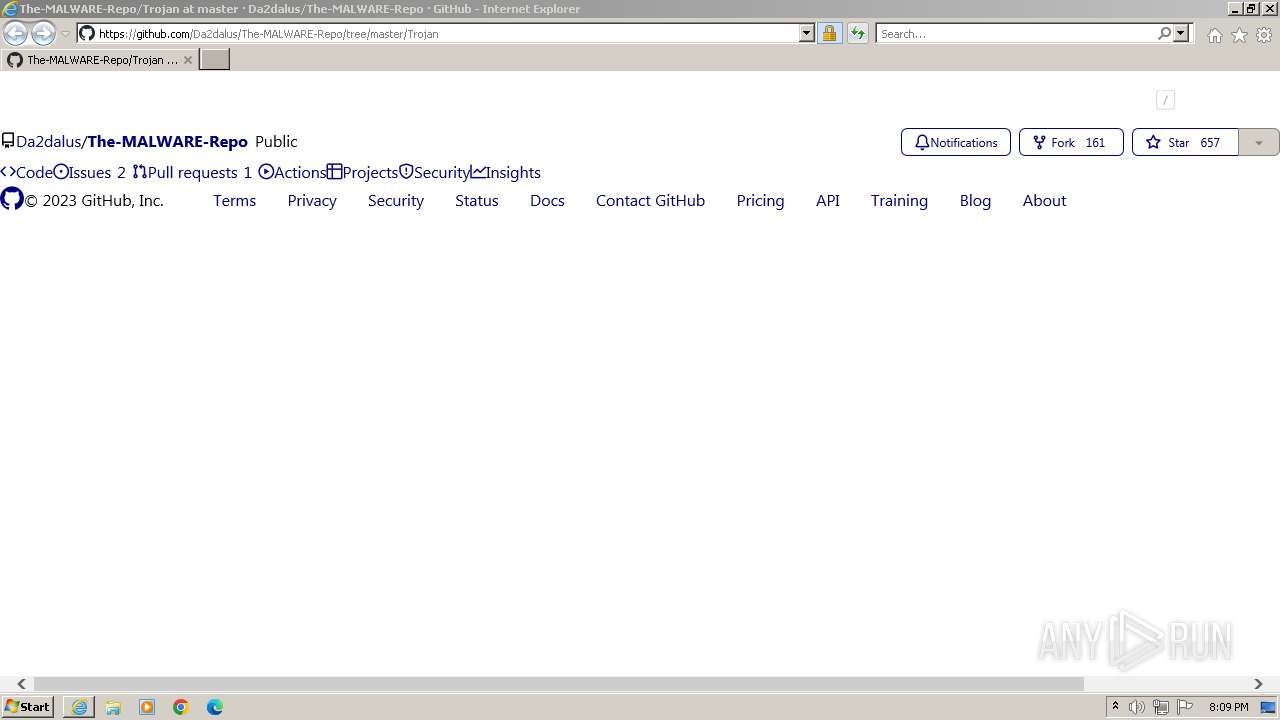
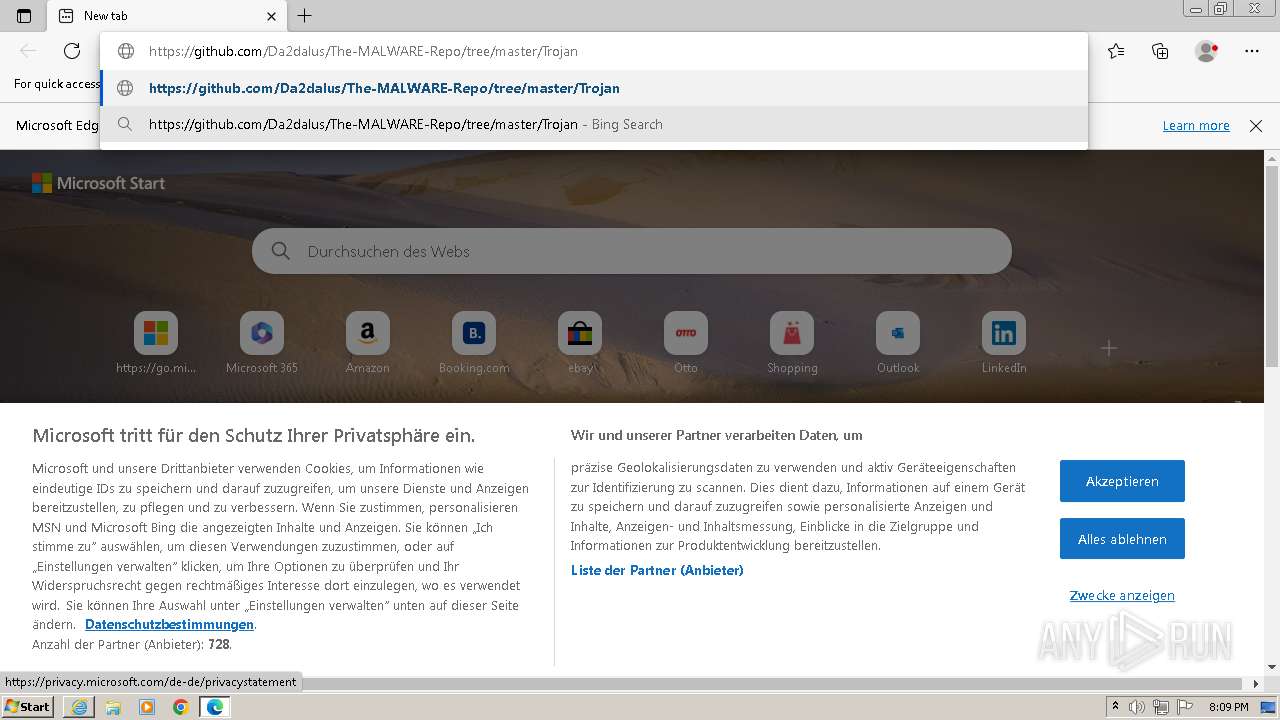
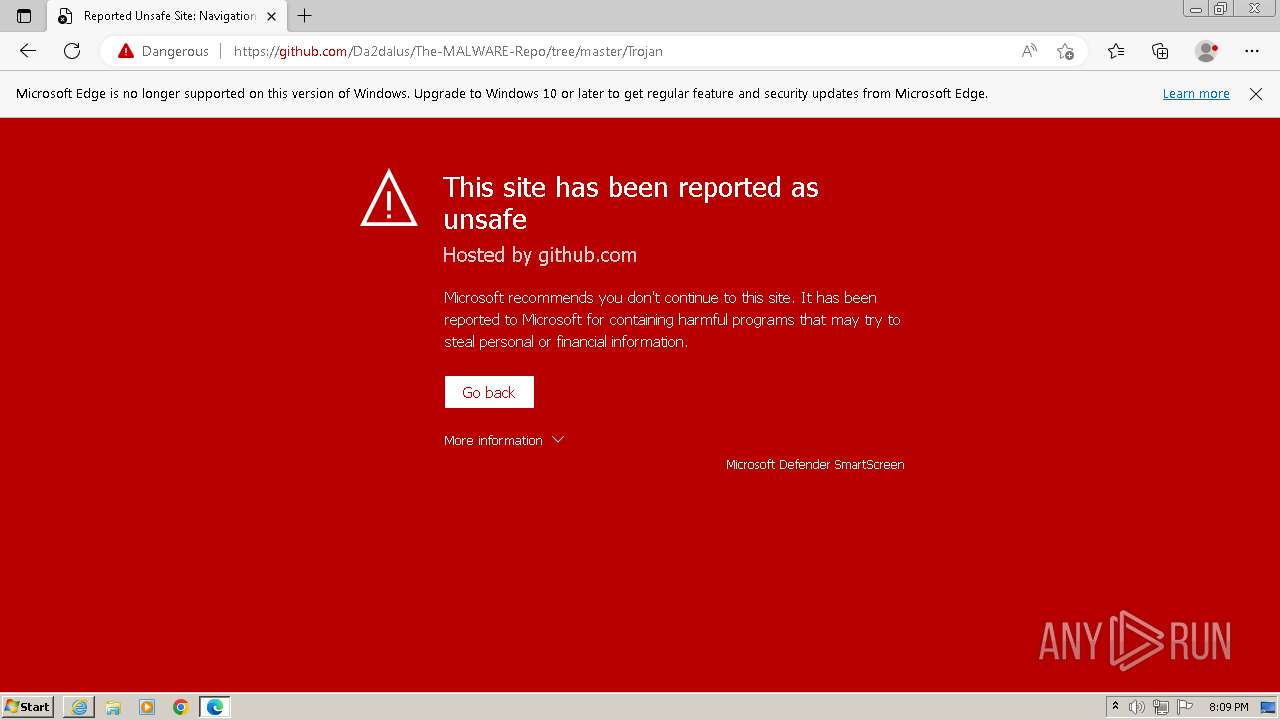
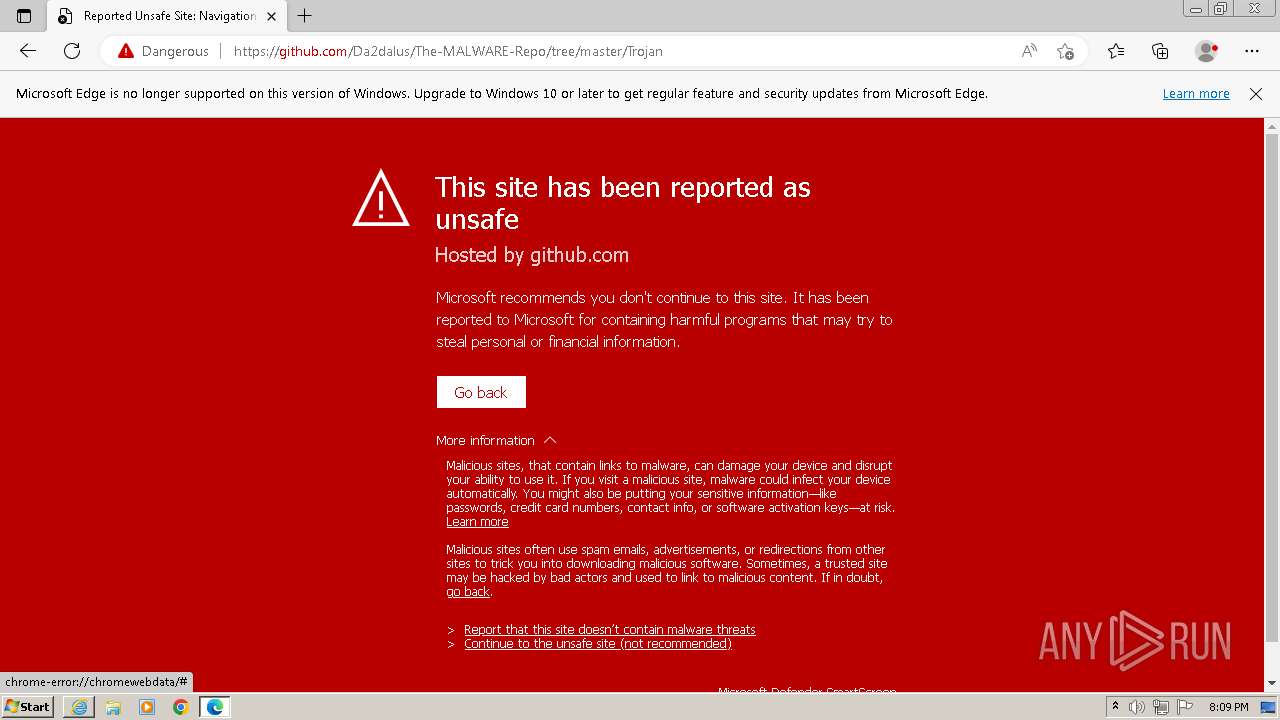
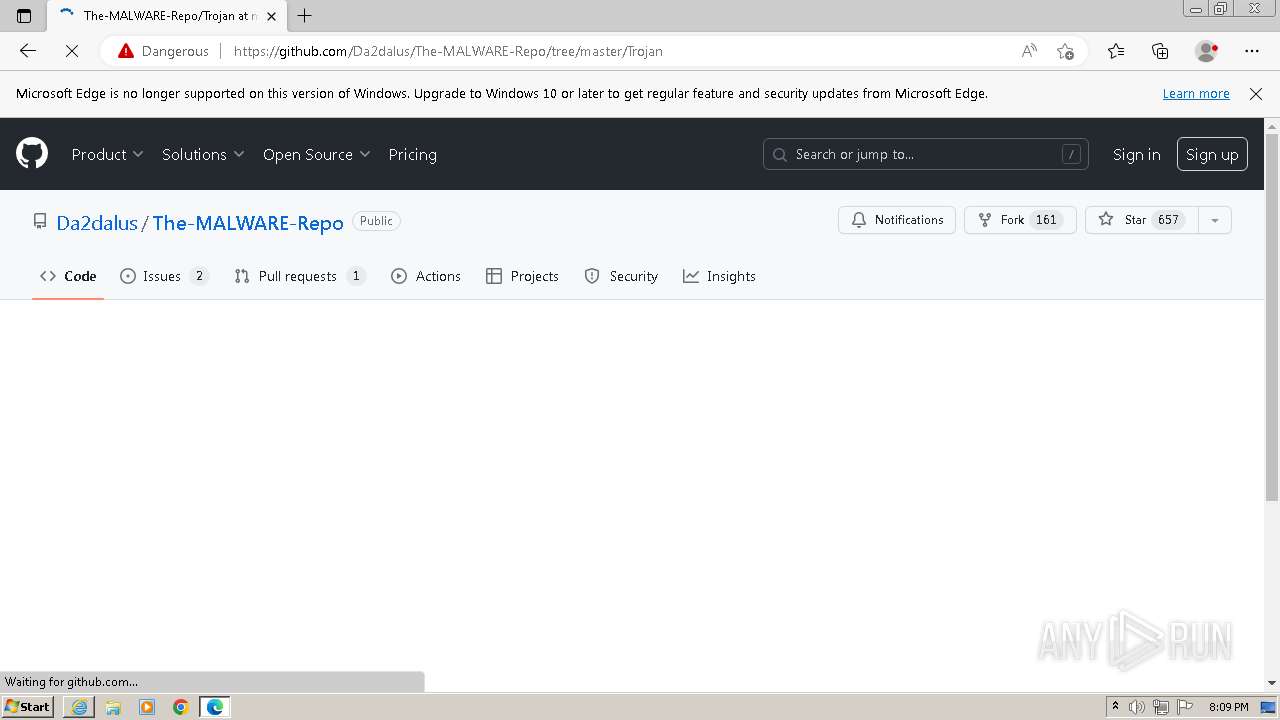
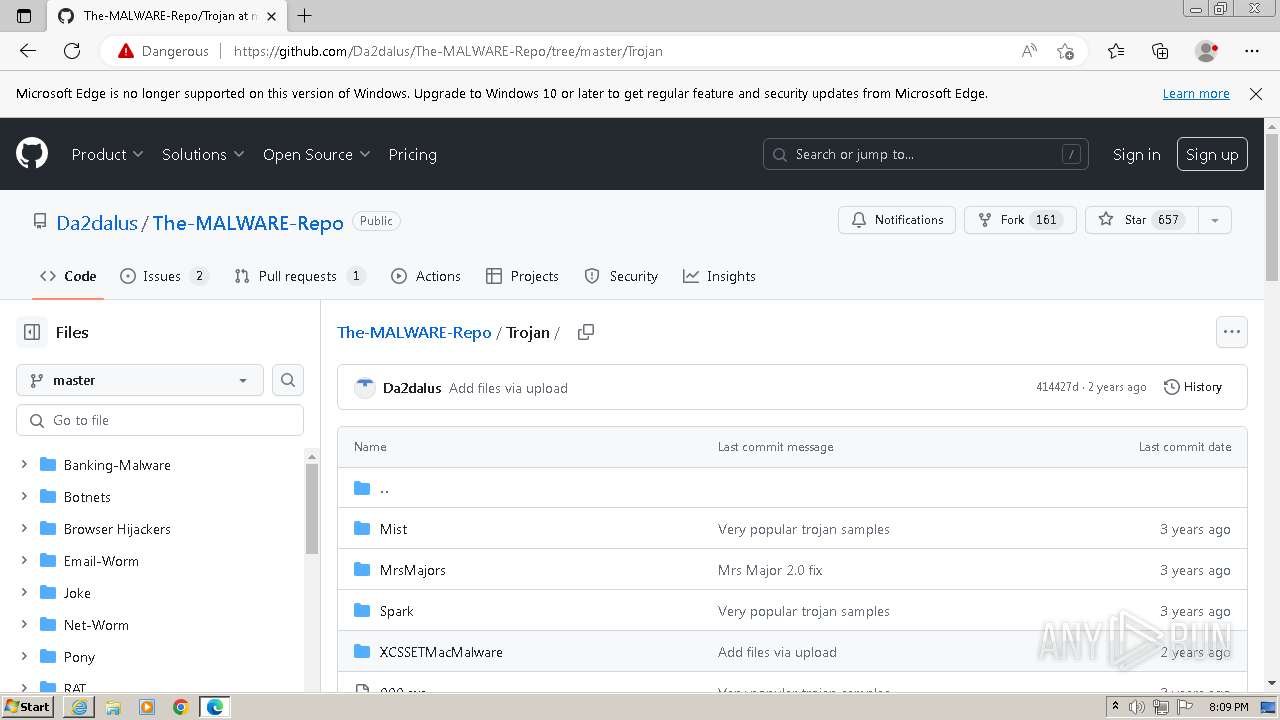
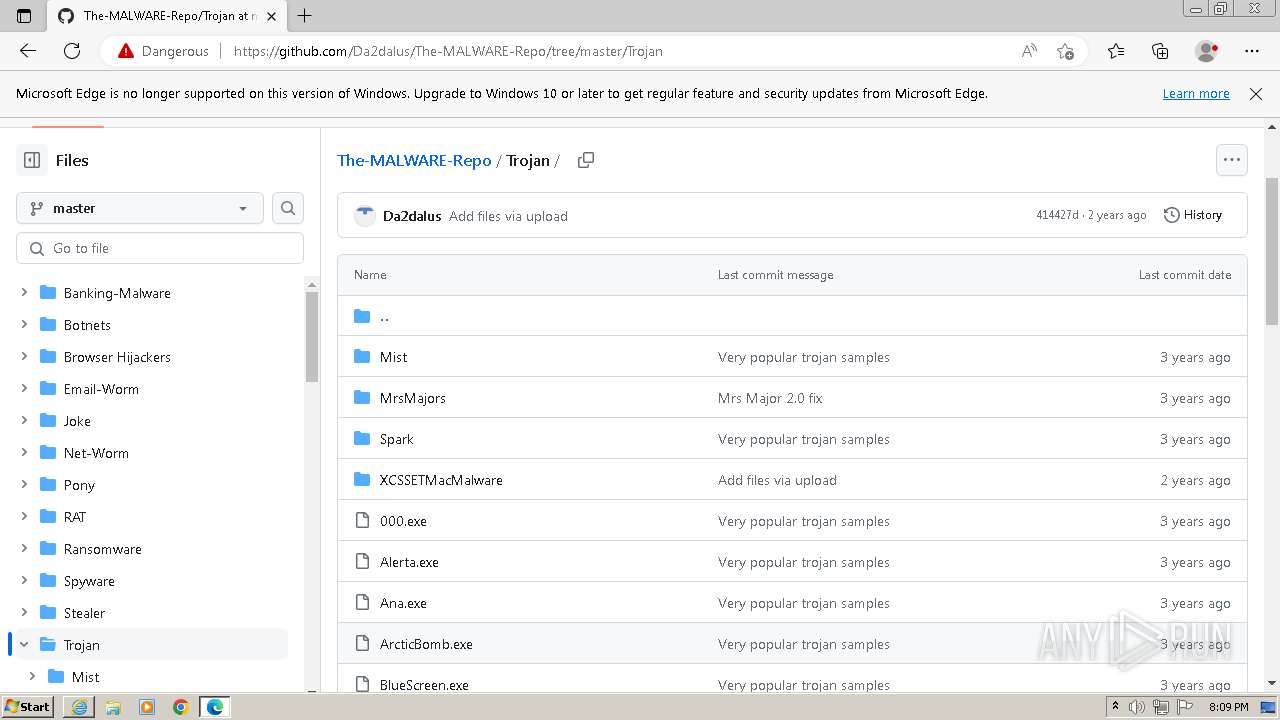
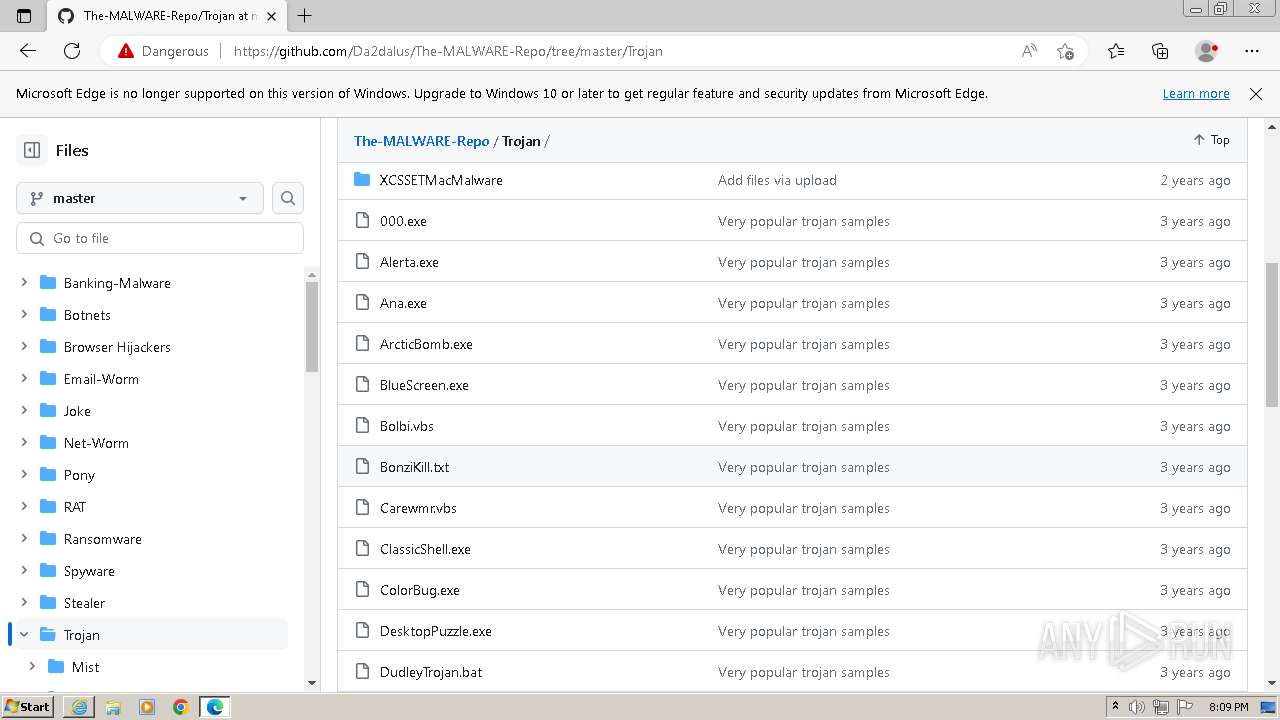
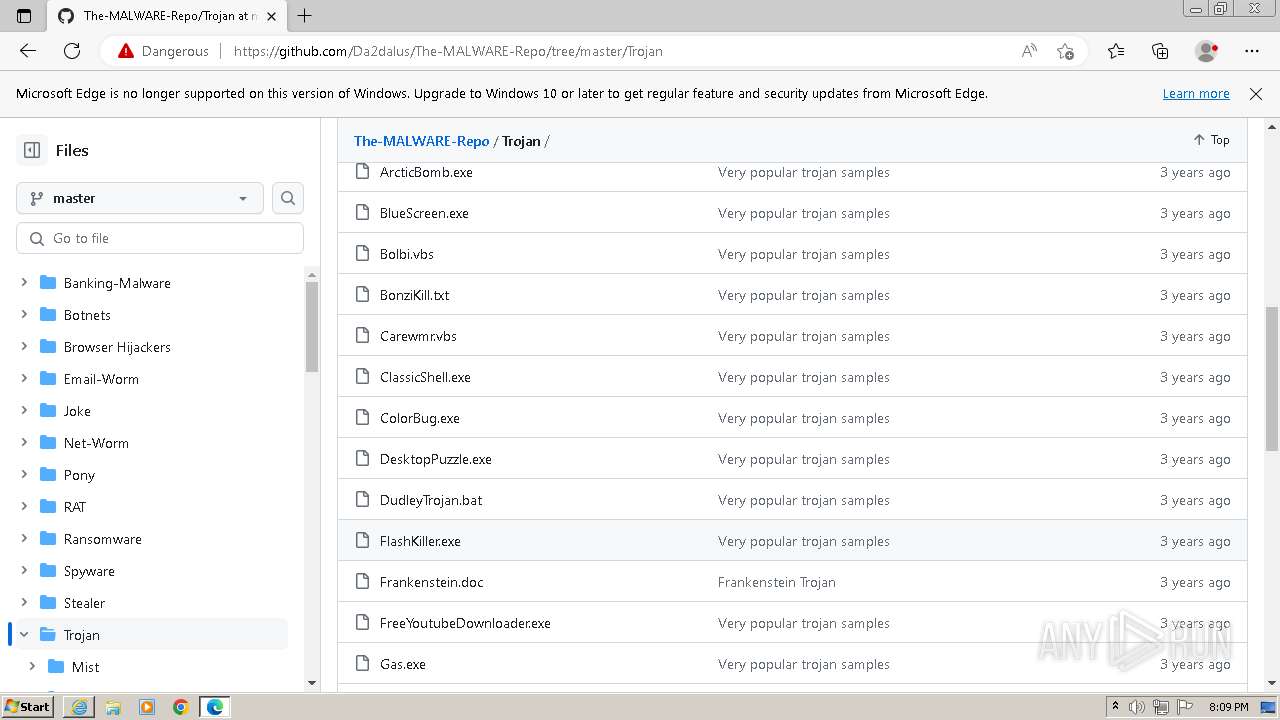
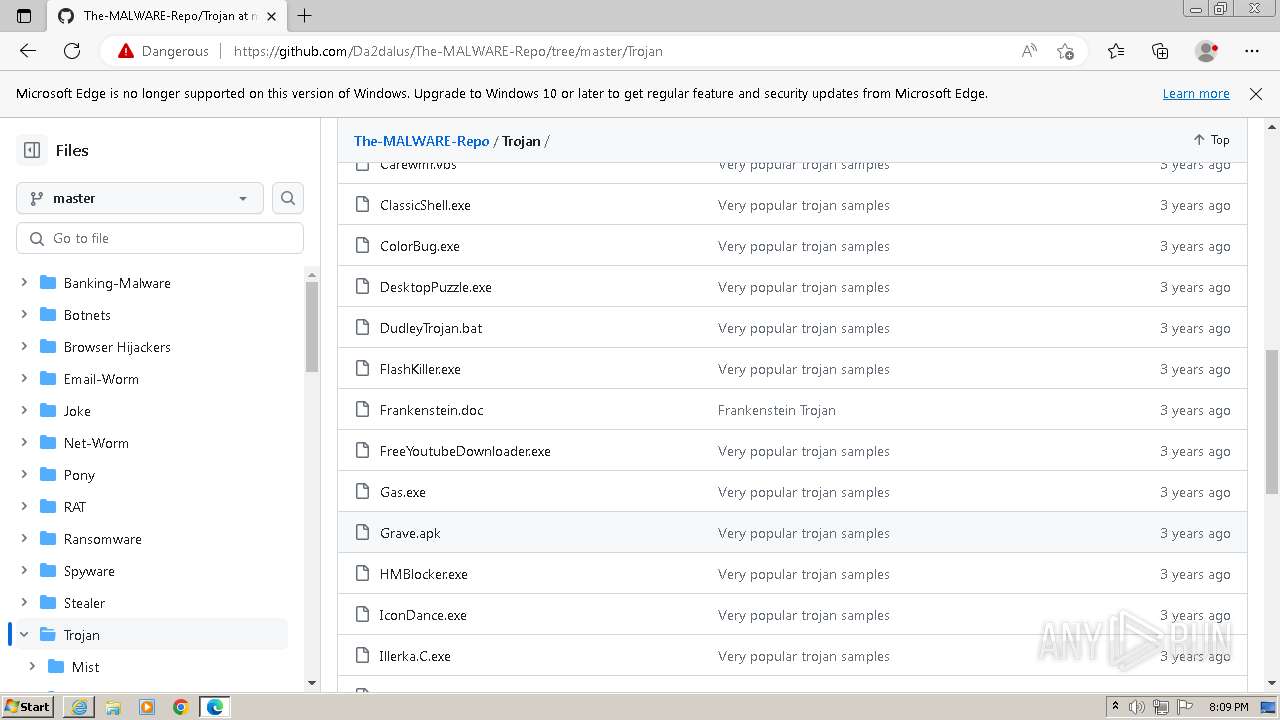
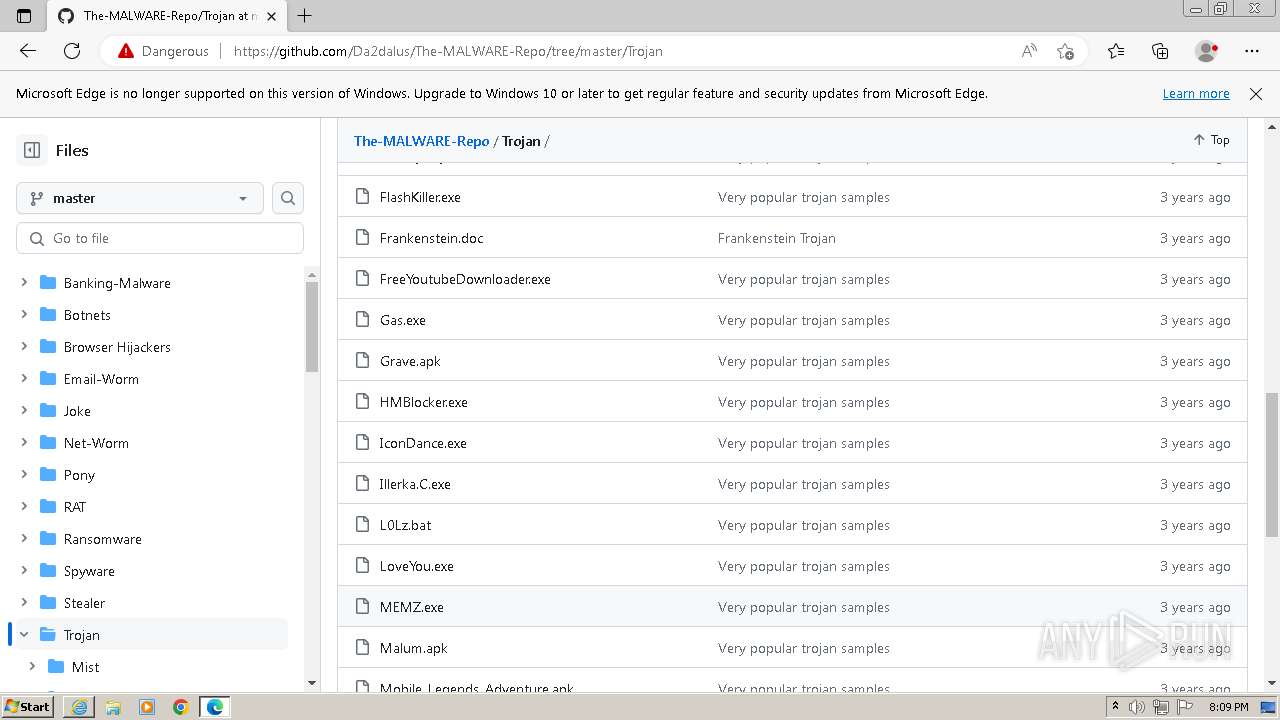
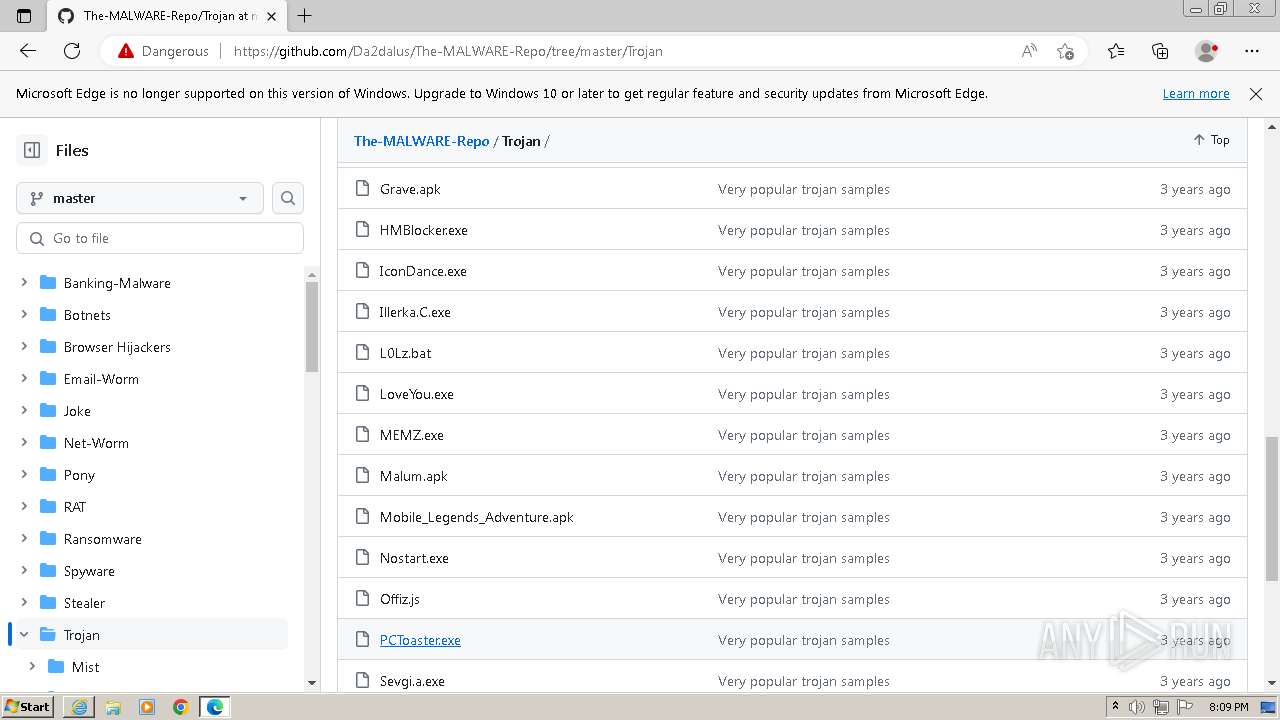
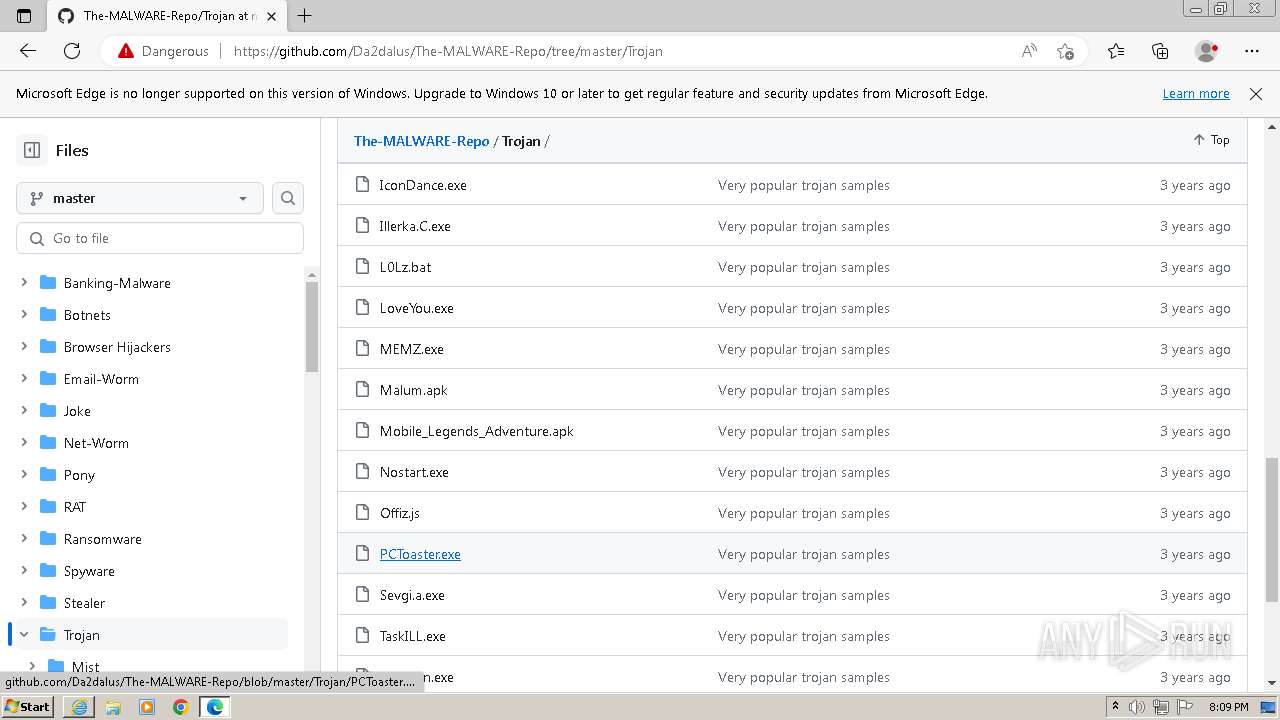
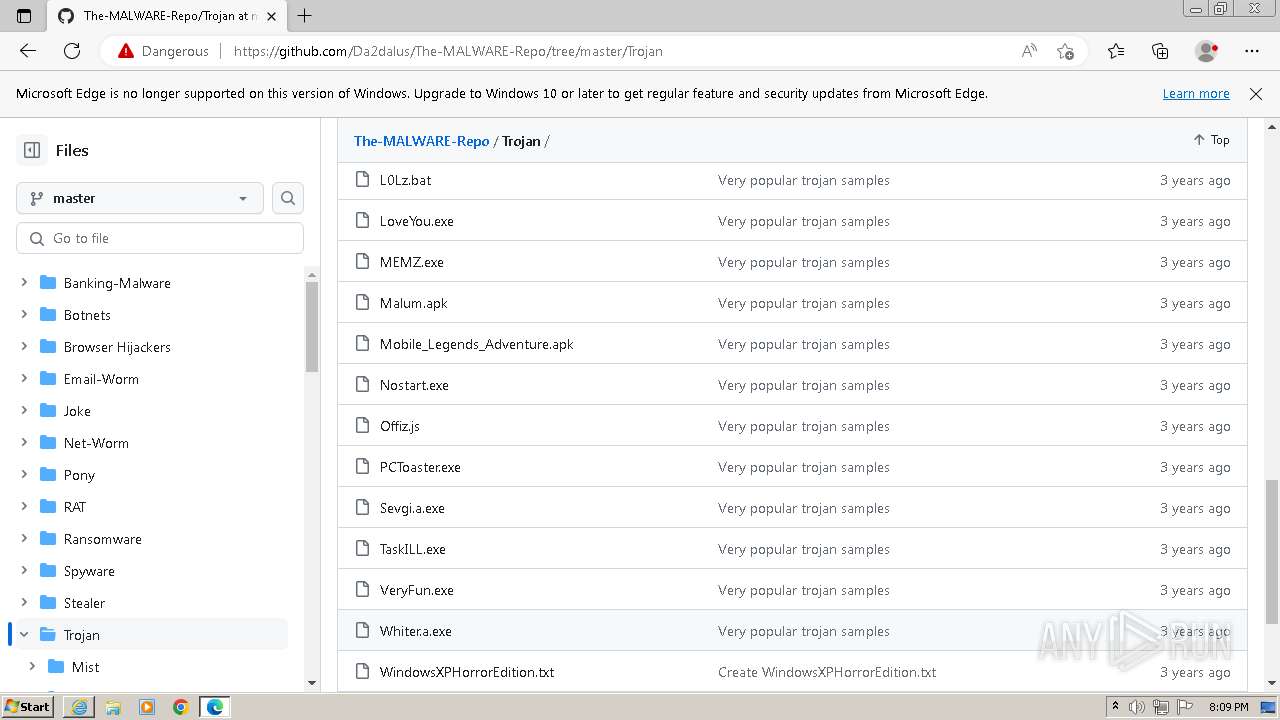
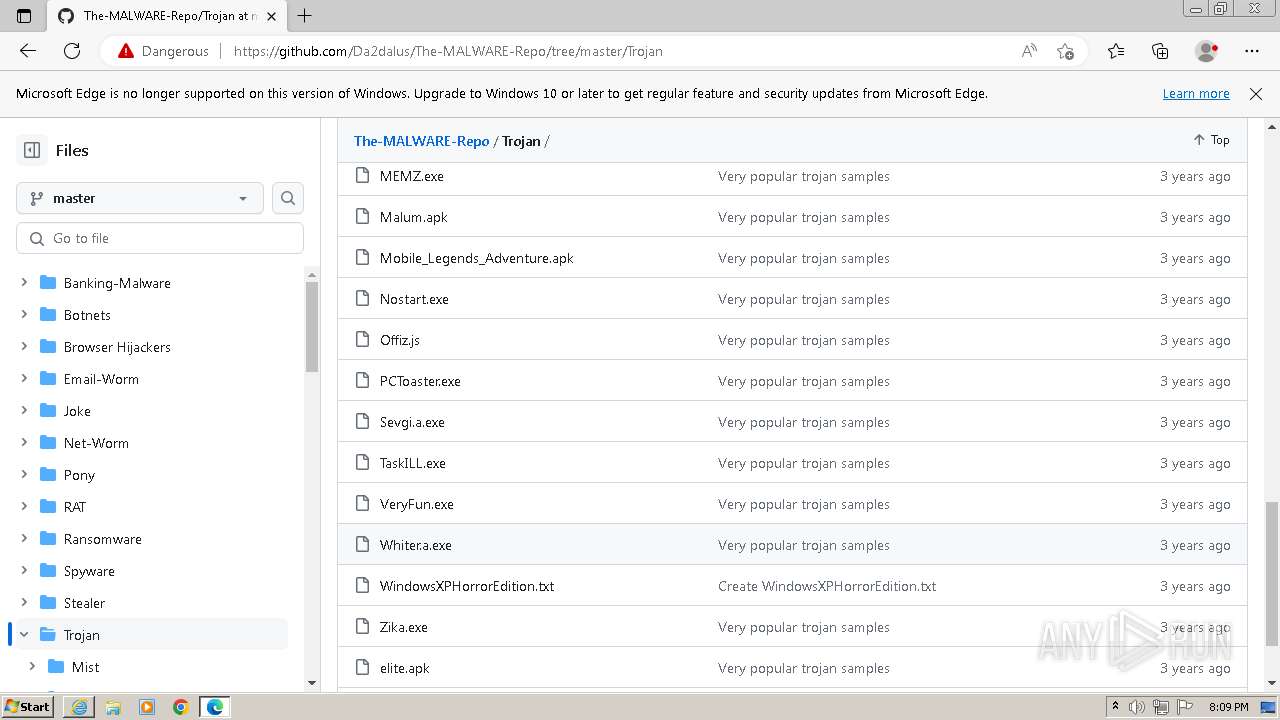
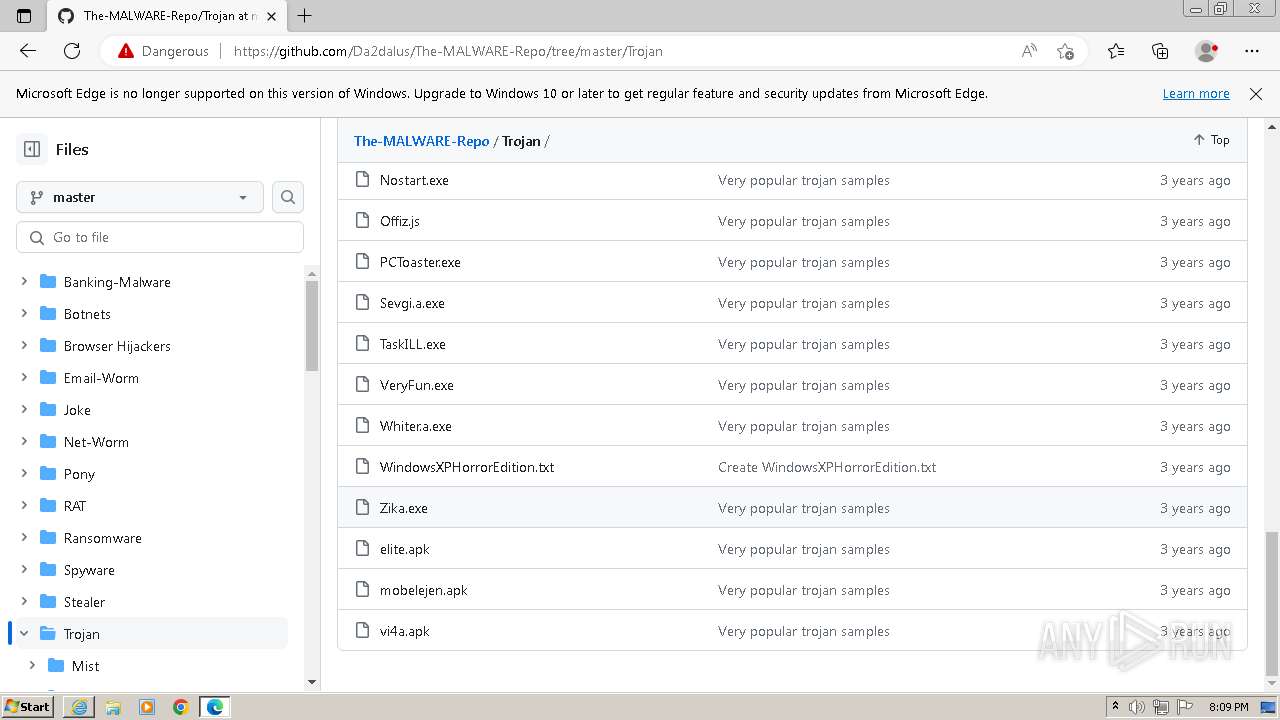
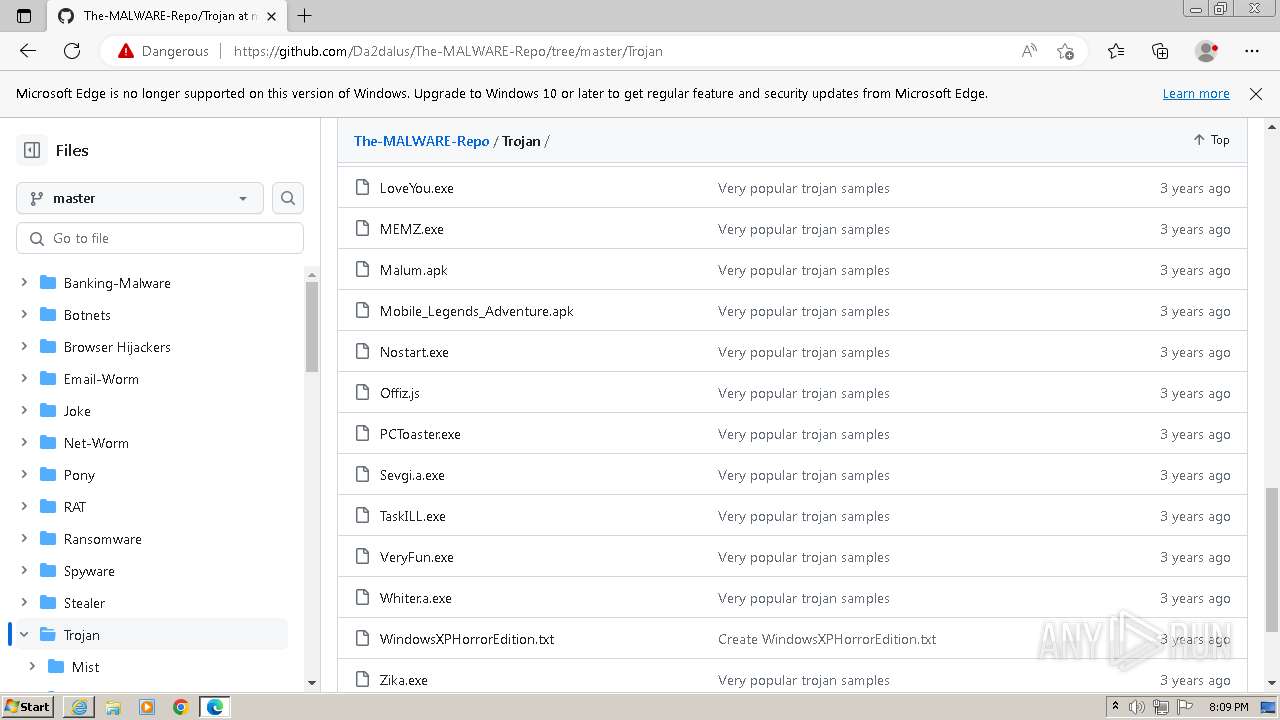
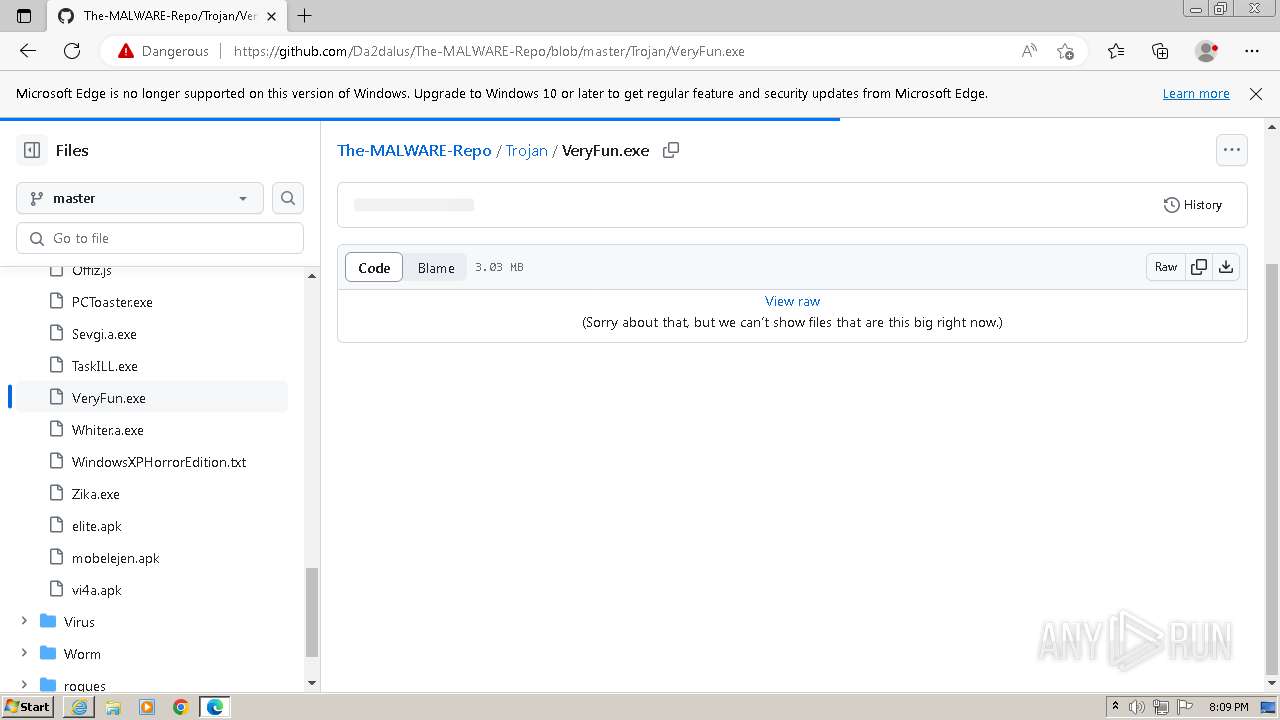
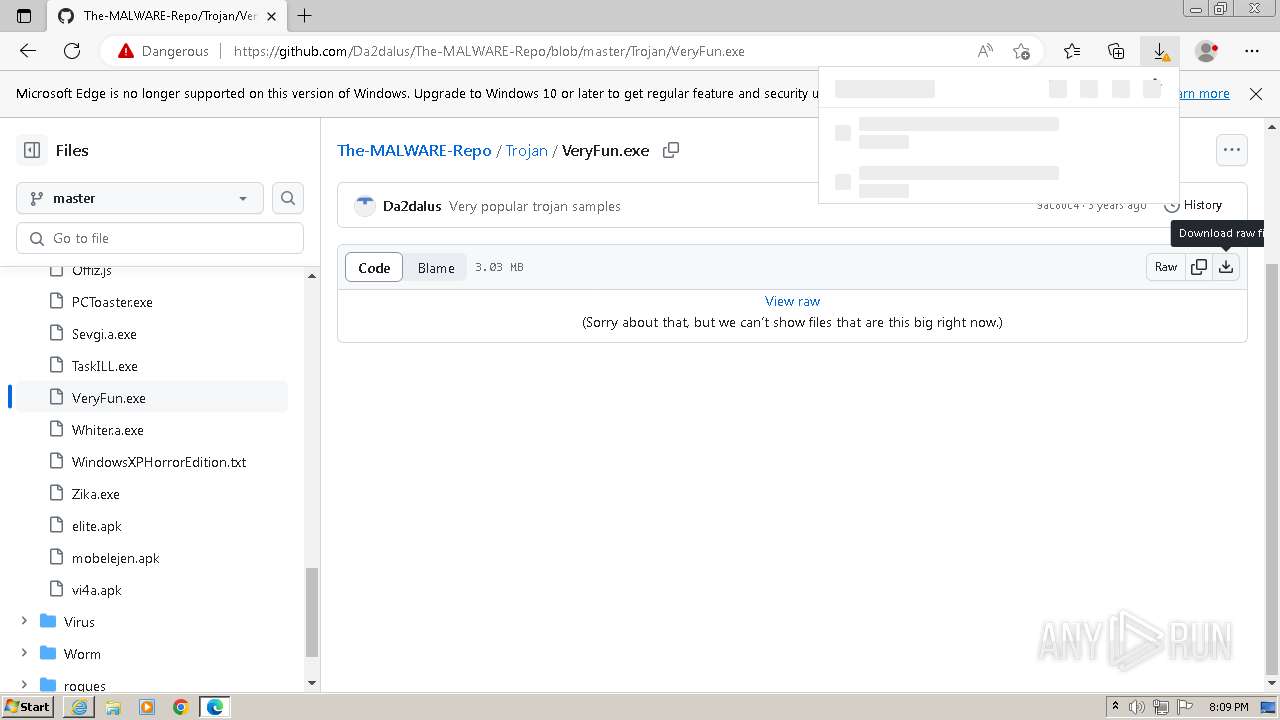
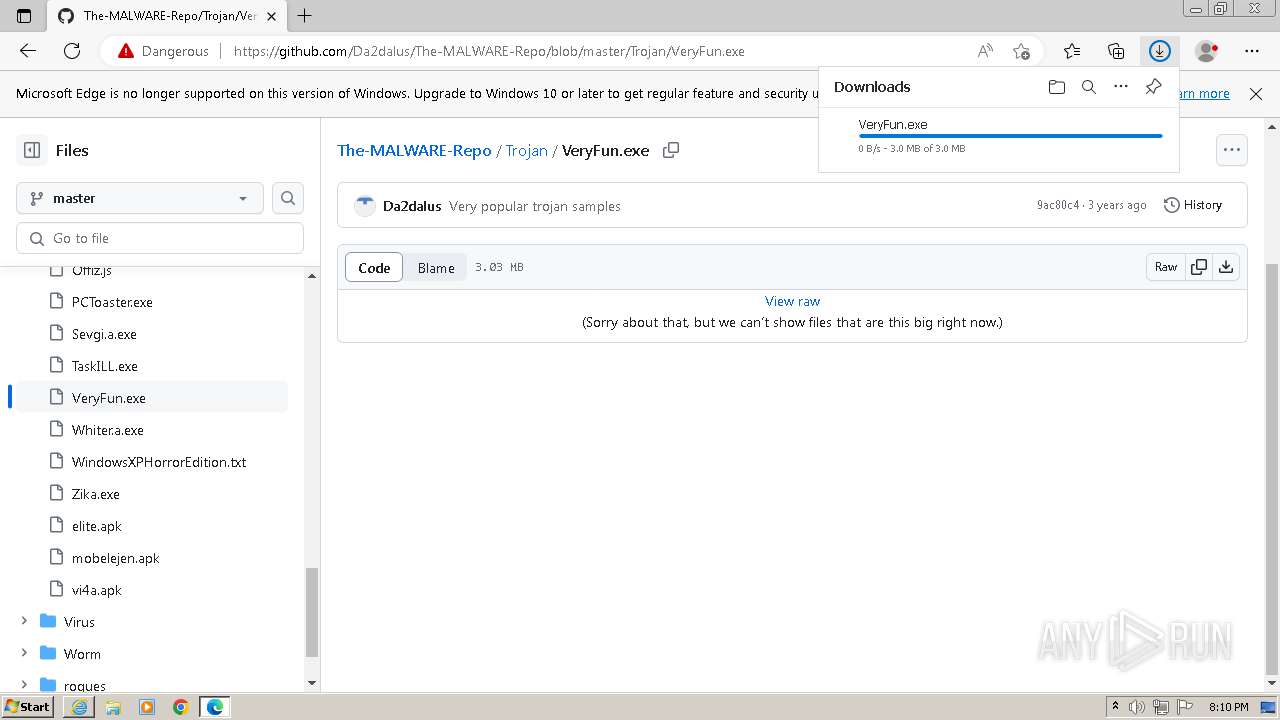
| URL: | https://github.com/Da2dalus/The-MALWARE-Repo/tree/master/Trojan |
| Full analysis: | https://app.any.run/tasks/b3e2a220-8077-4f1d-b7a6-176f2b5b6728 |
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2023, 20:08:26 |
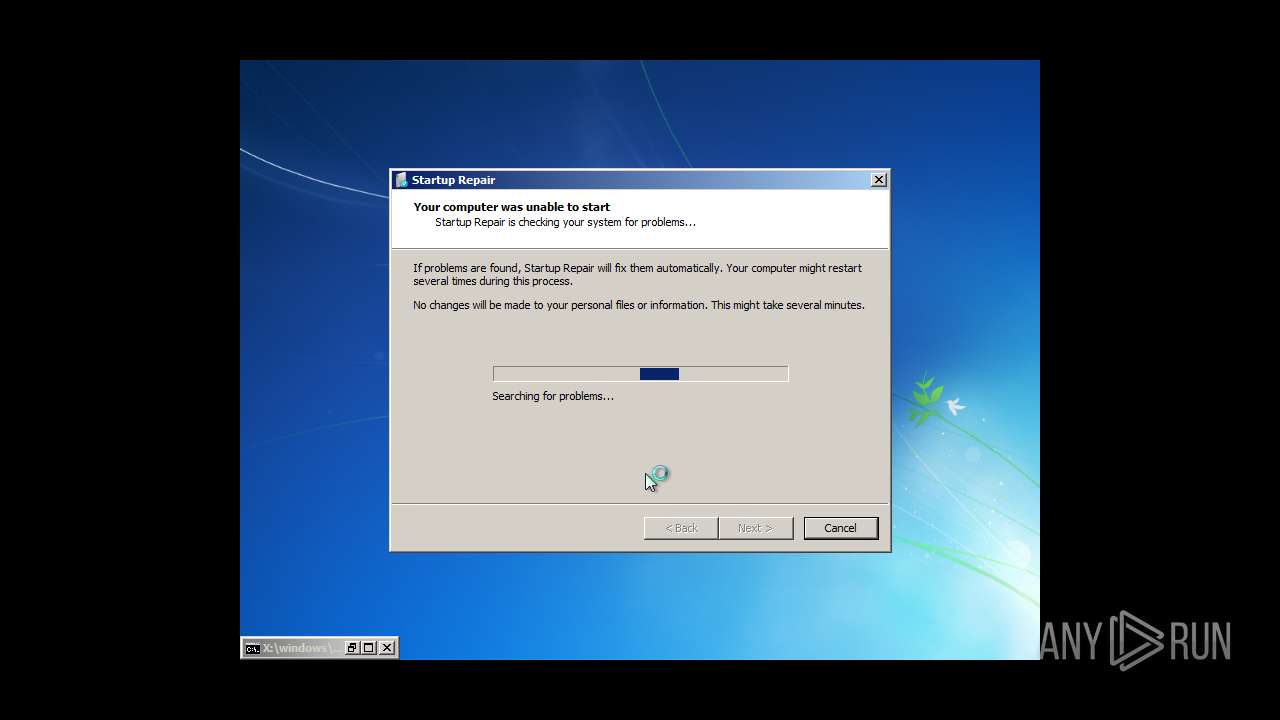
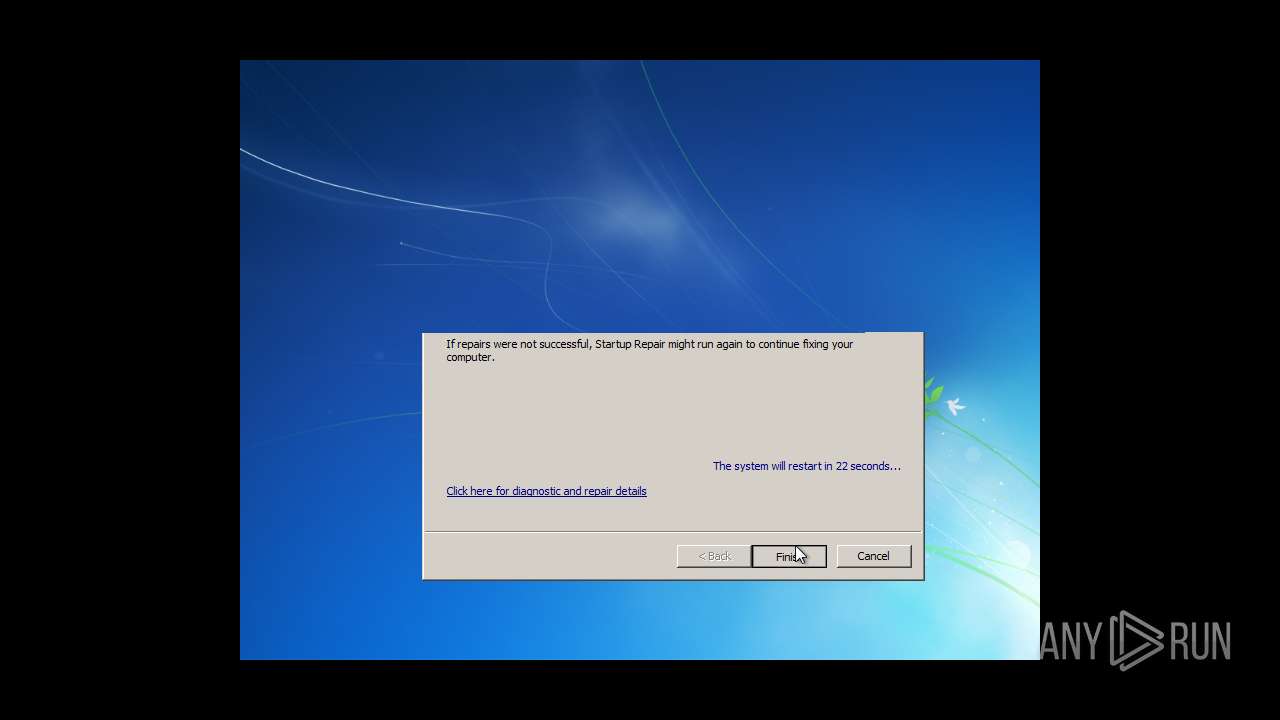
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | EF68E4D00FEC5056788BF319203F807657E22A1C |
| SHA256: | F1CF3FE7F69453813DC114EA207E6DC00FBC36D7D6D85675B50D17EE88288E58 |
| SSDEEP: | 3:N8tEdJejSOpykO3QAT+bPi:2ubYSOc9VT+bPi |
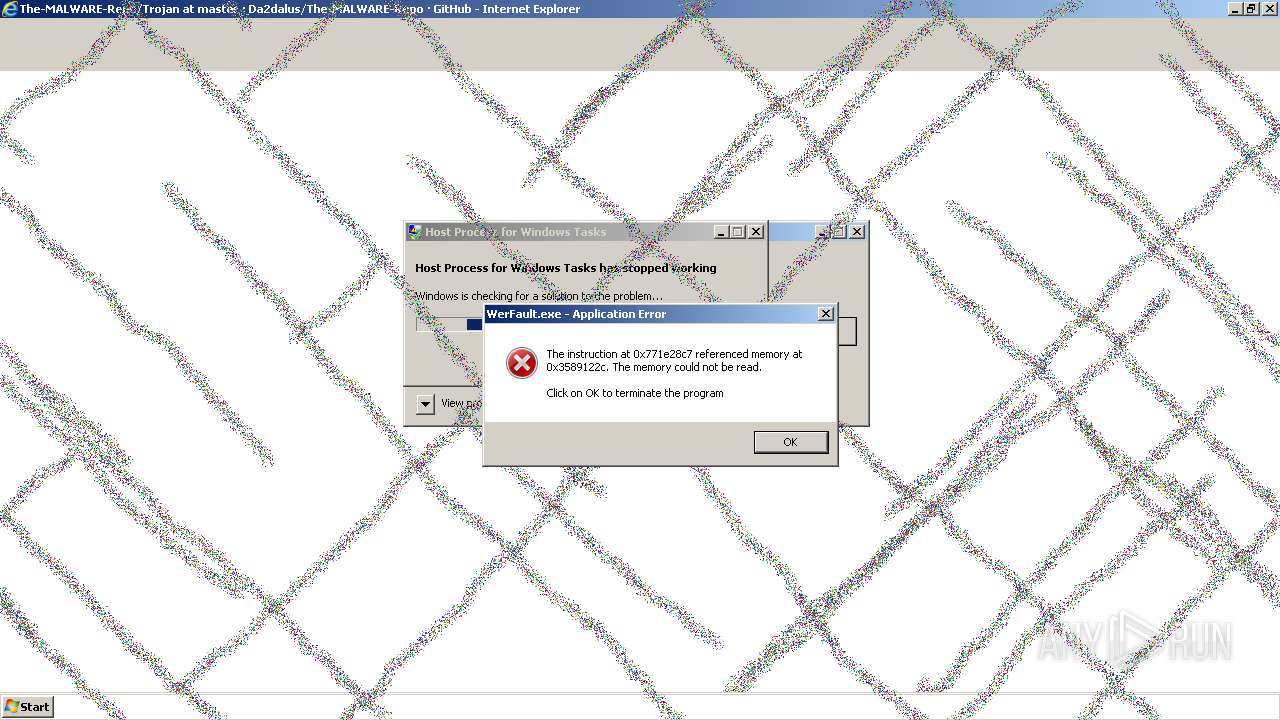
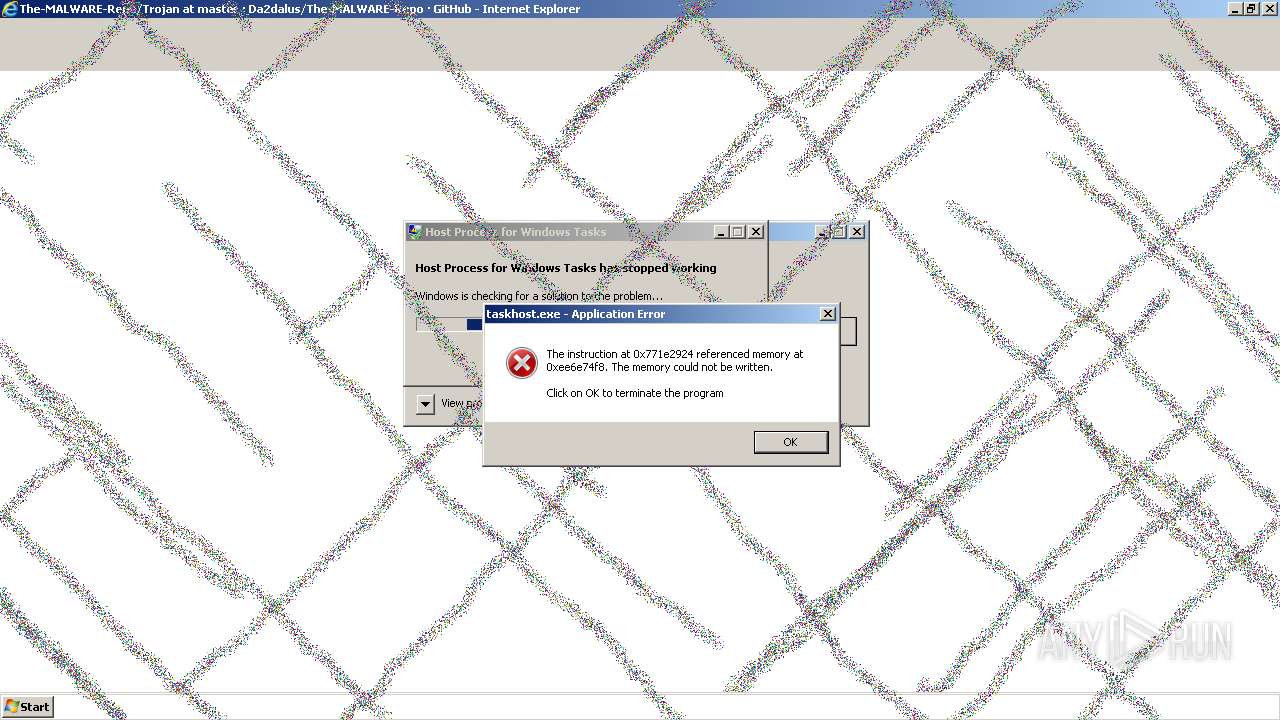
MALICIOUS
Scans artifacts that could help determine the target
- cmd.exe (PID: 2836)
Changes appearance of the Explorer extensions
- cmd.exe (PID: 2836)
Creates or modifies Windows services
- cmd.exe (PID: 2836)
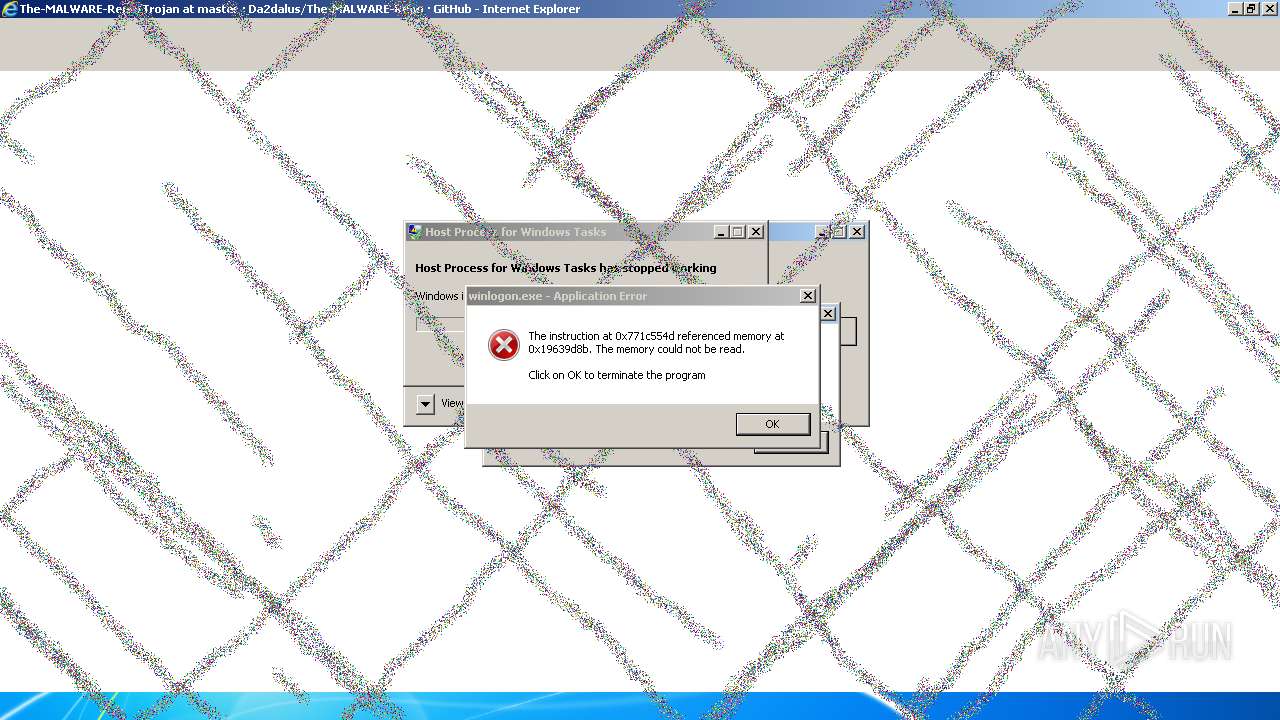
Changes the login/logoff helper path in the registry
- cmd.exe (PID: 2836)
SUSPICIOUS
Checks for the .NET to be installed
- cmd.exe (PID: 2836)
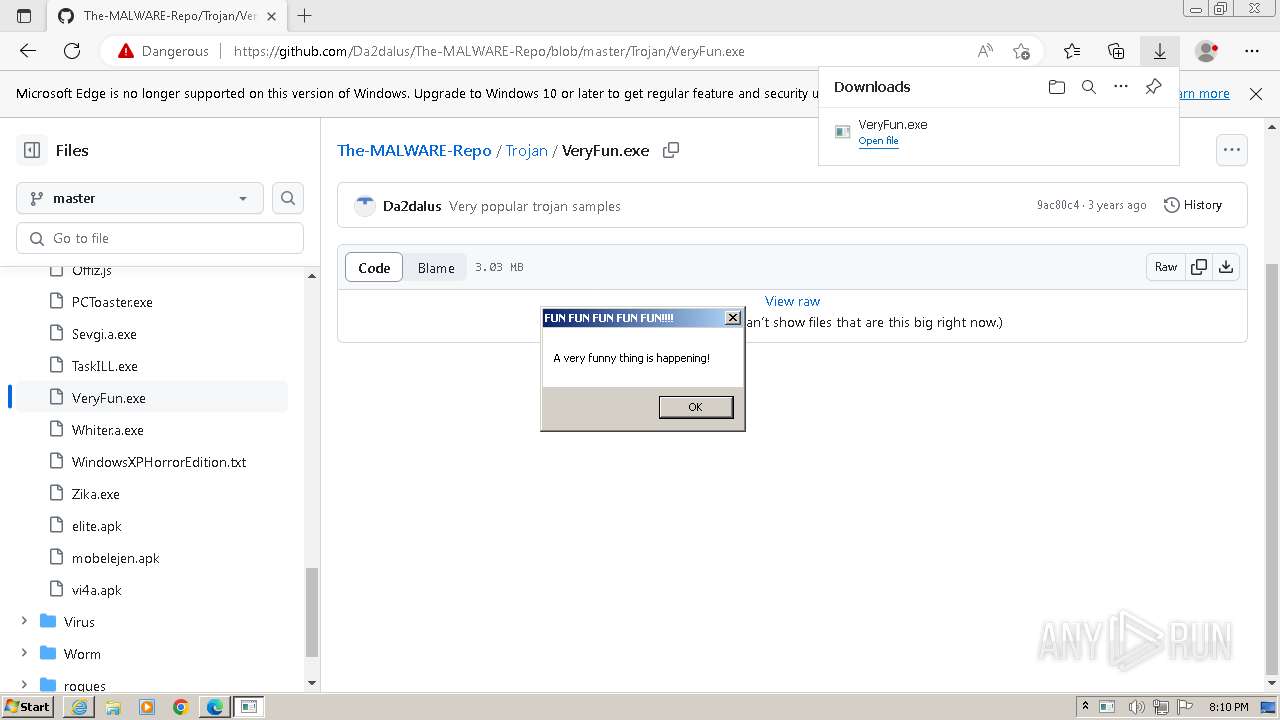
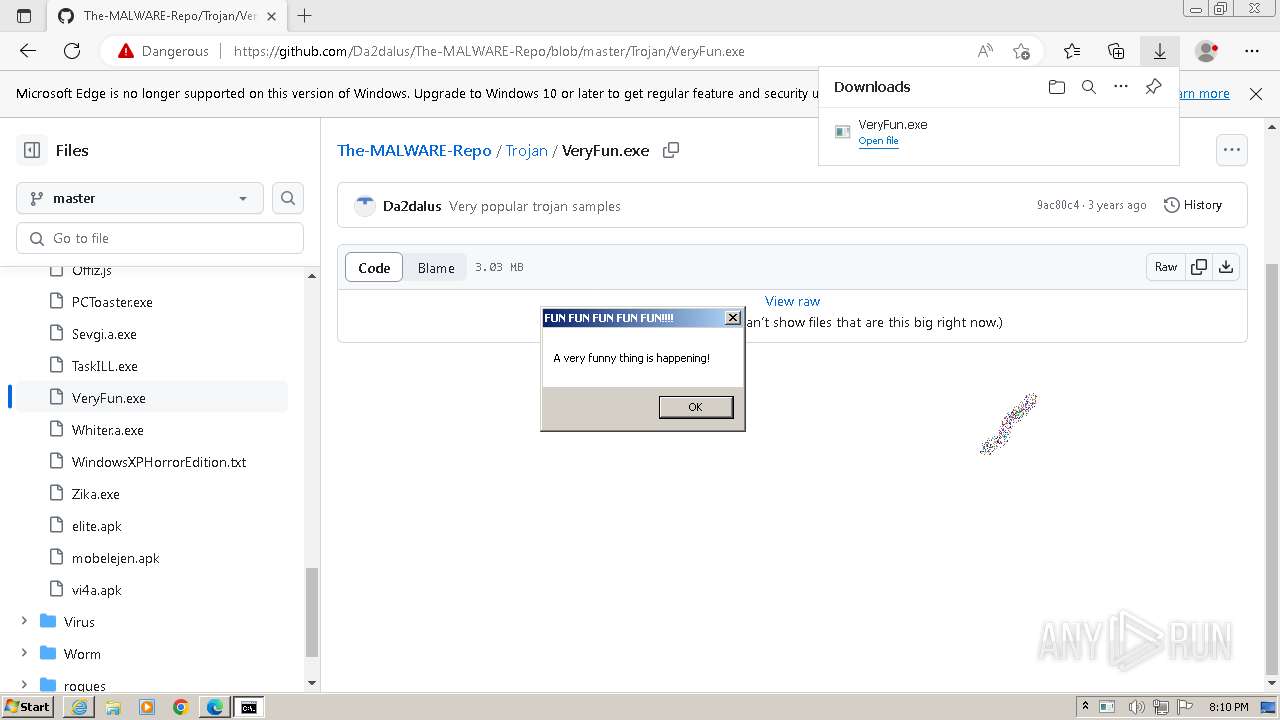
Starts CMD.EXE for commands execution
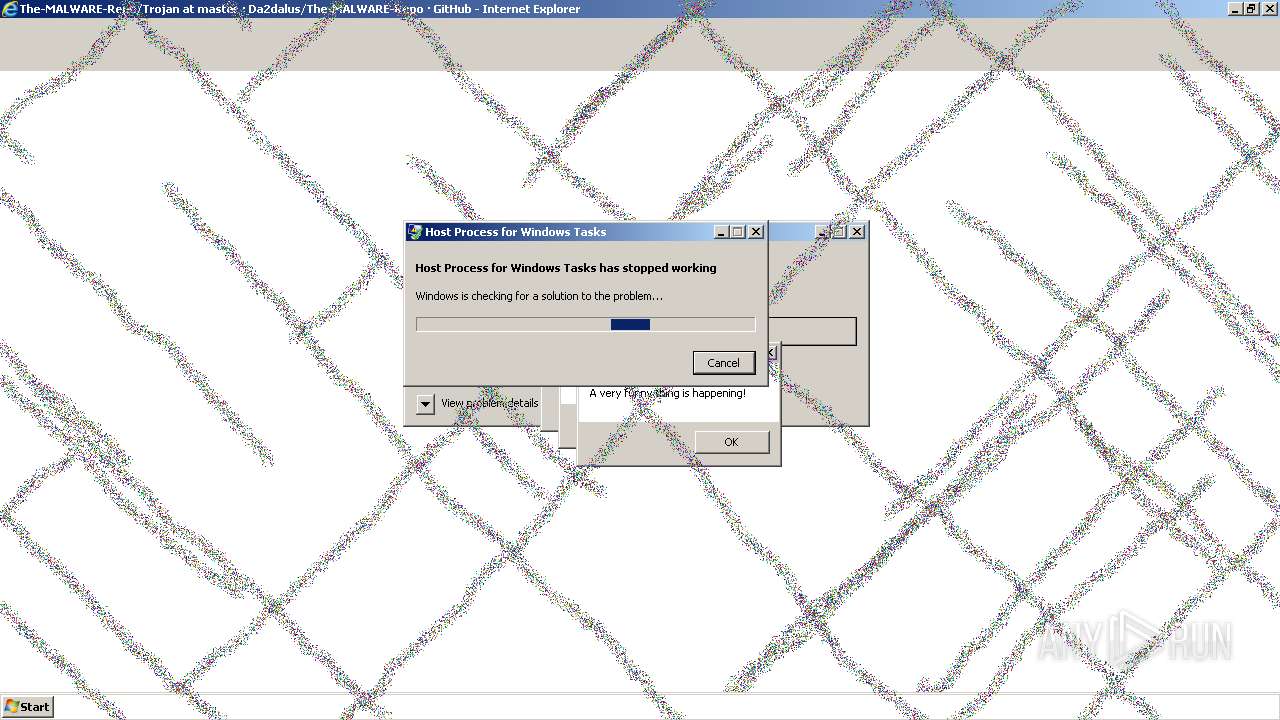
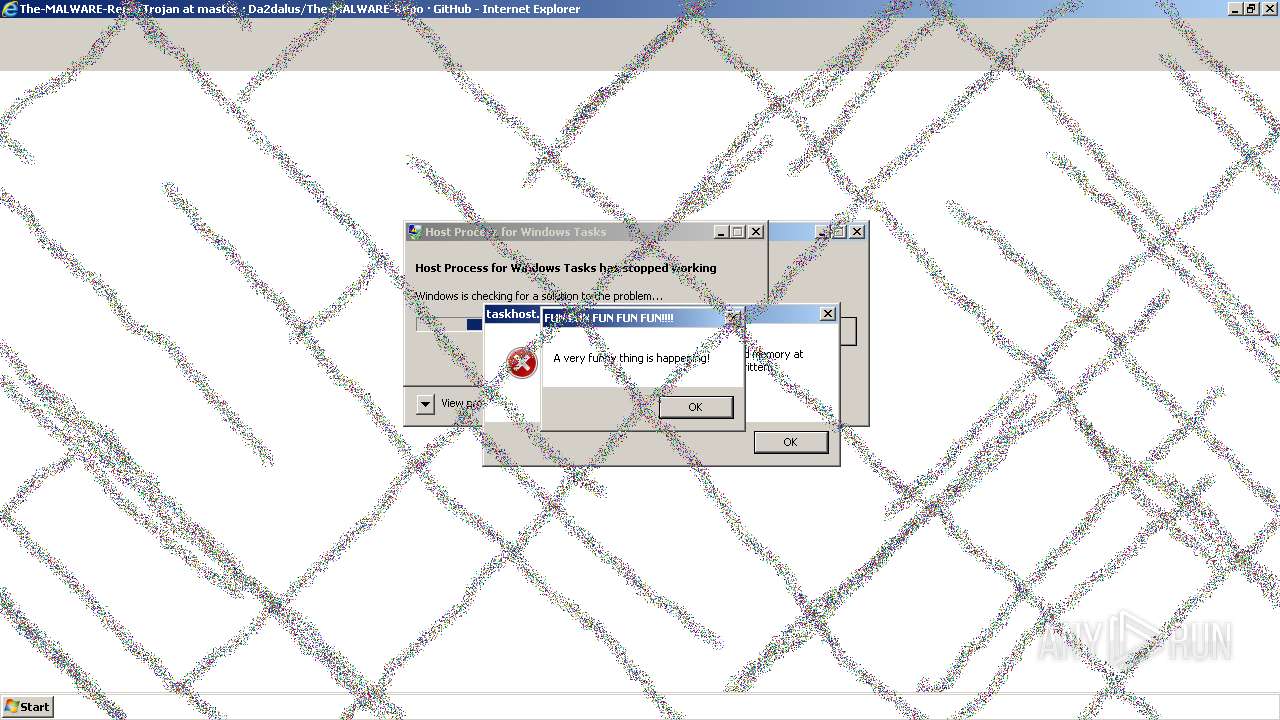
- VeryFun.exe (PID: 2176)
Reads the history of recent RDP connections
- cmd.exe (PID: 2836)
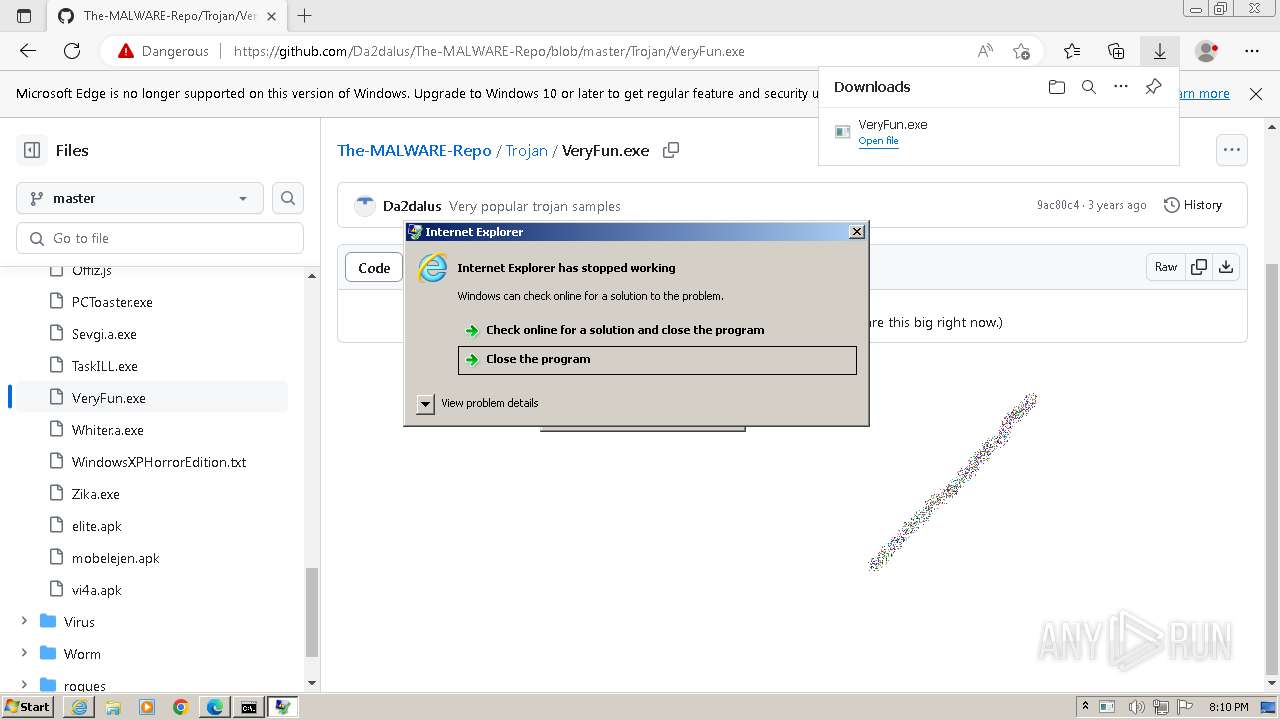
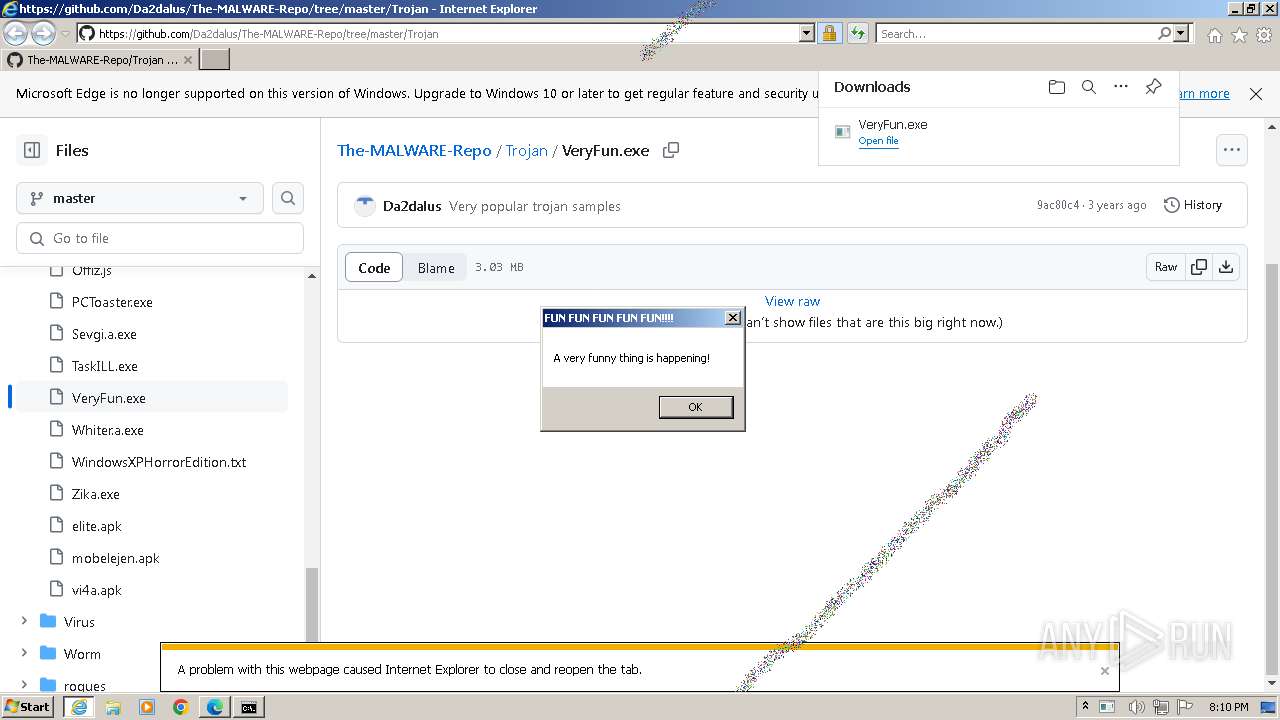
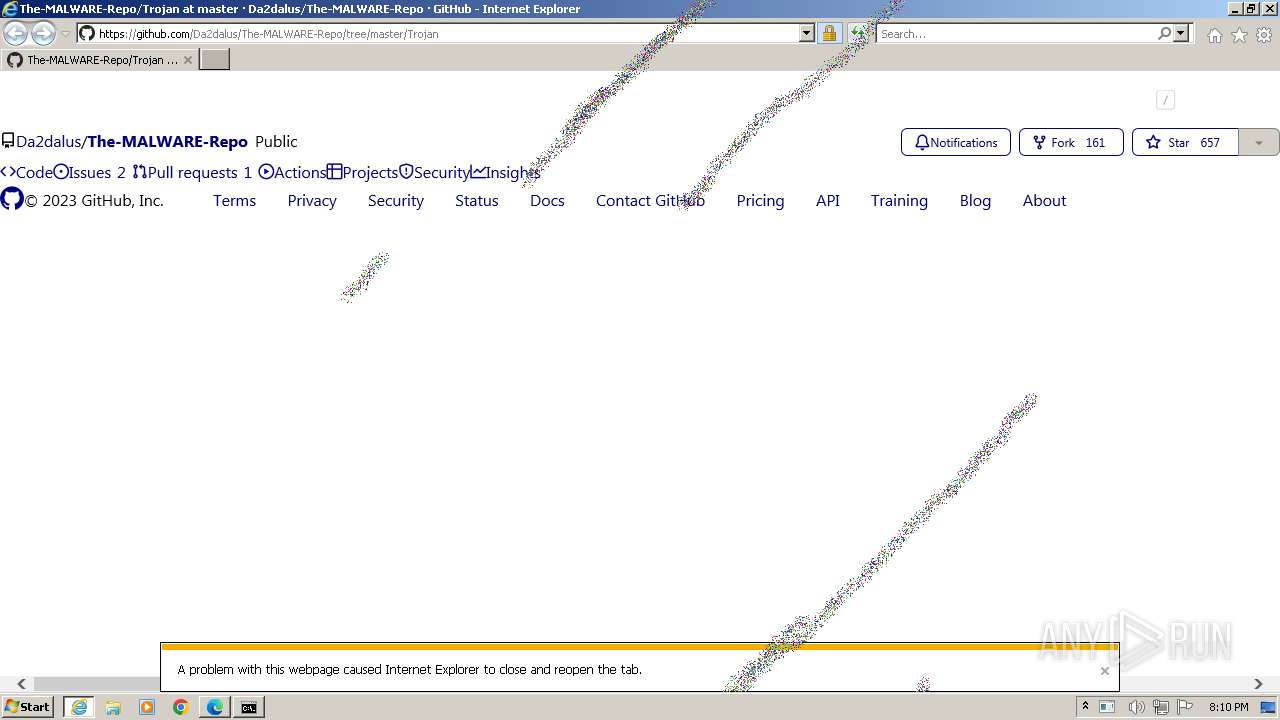
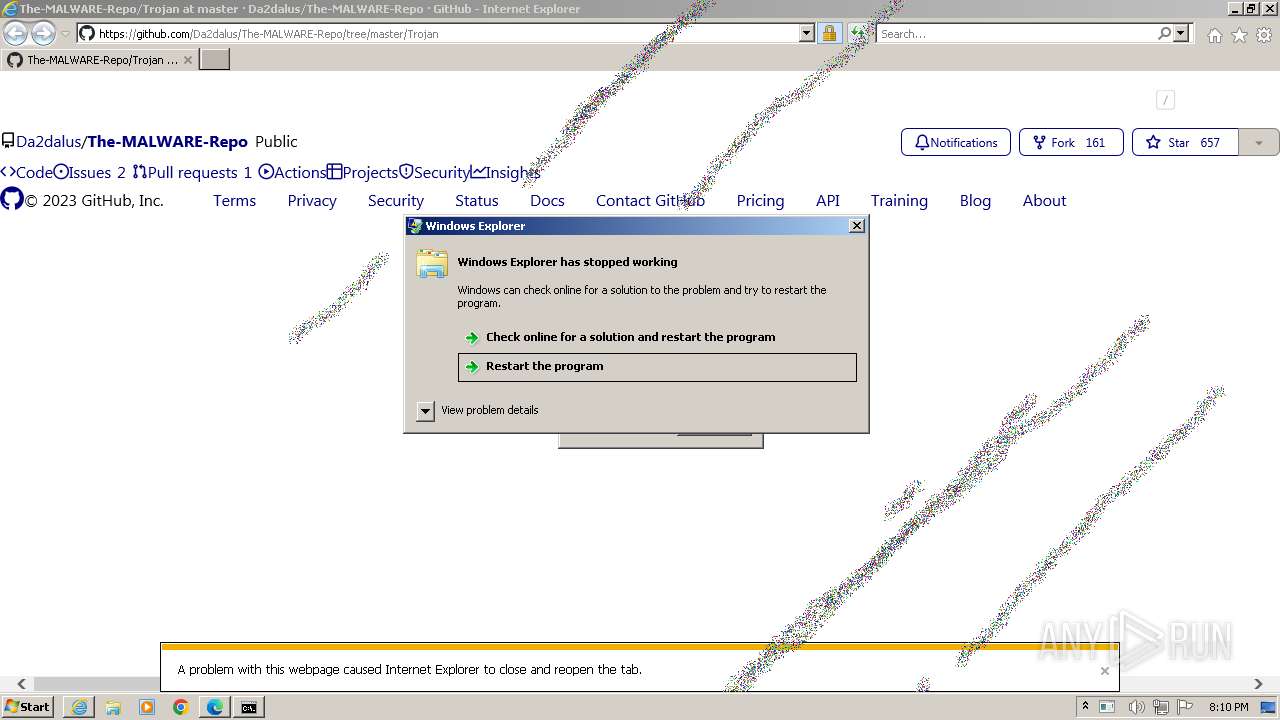
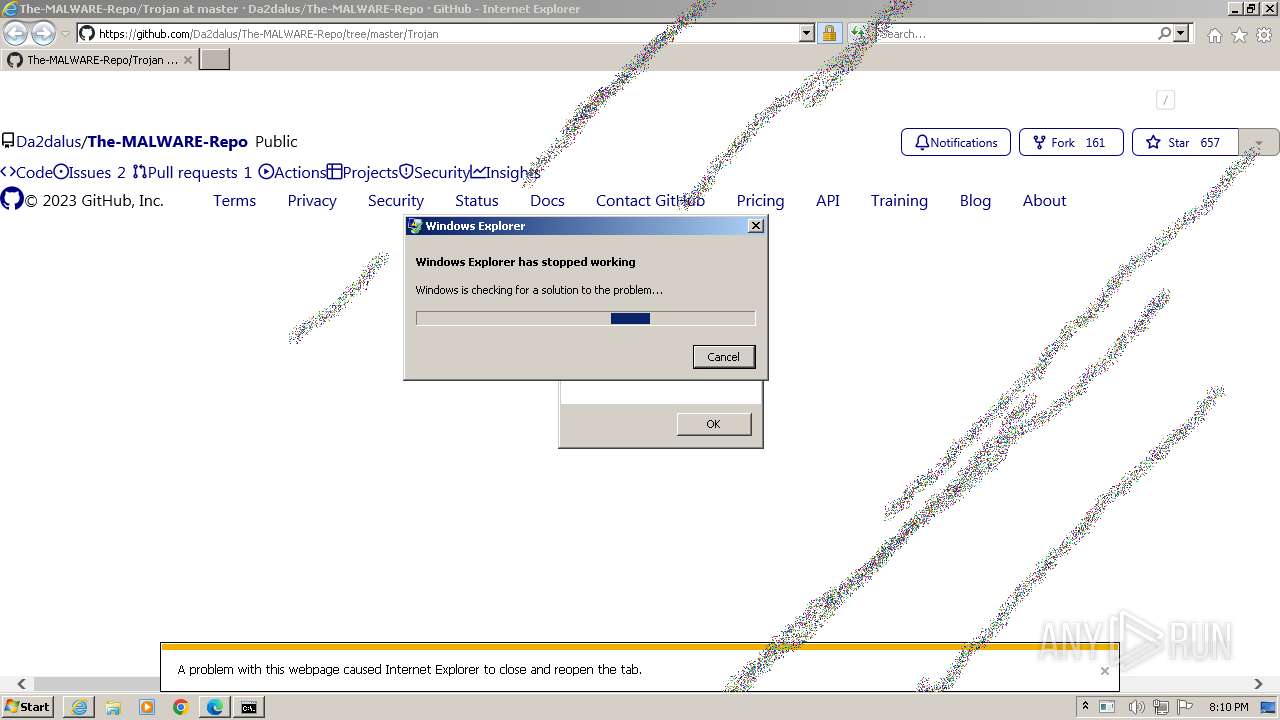
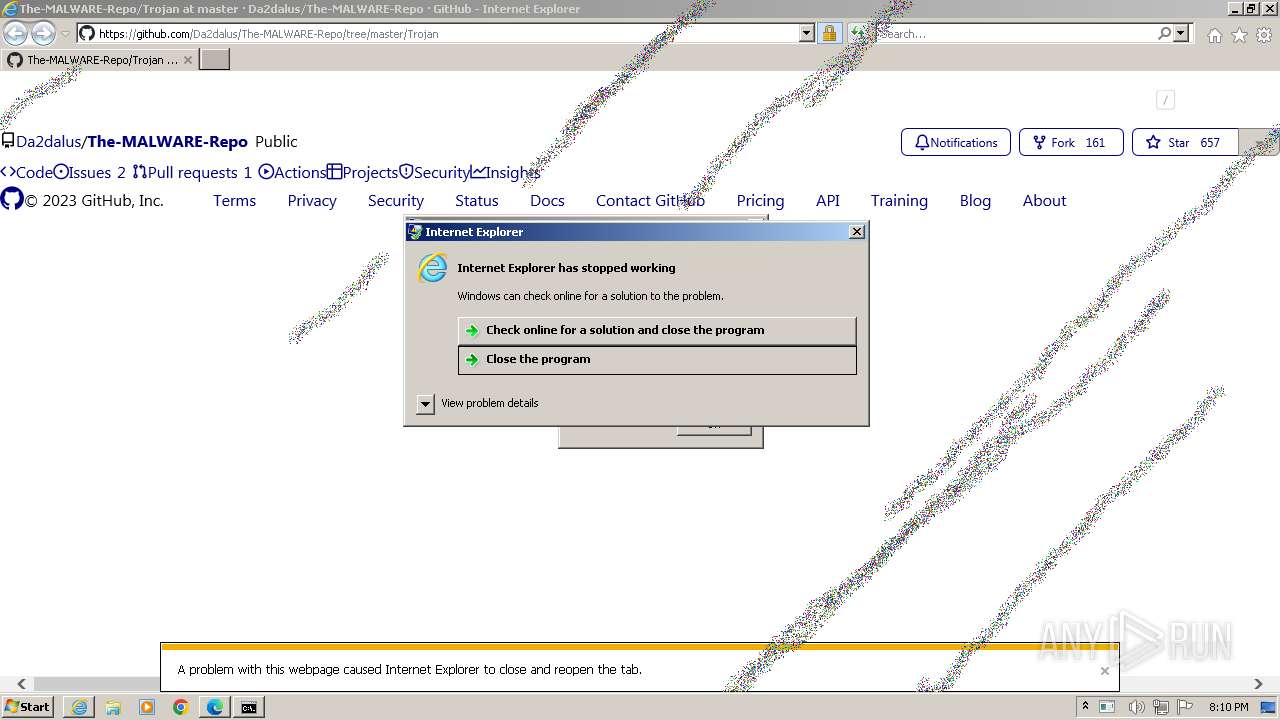
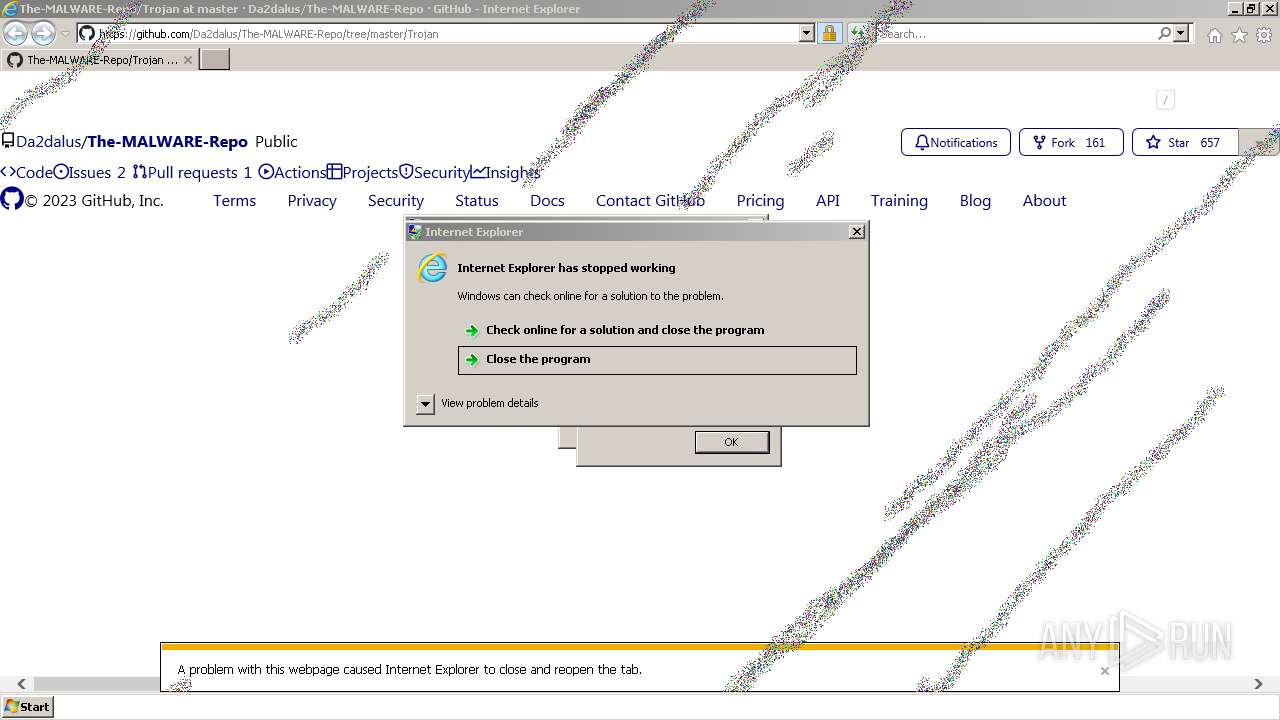
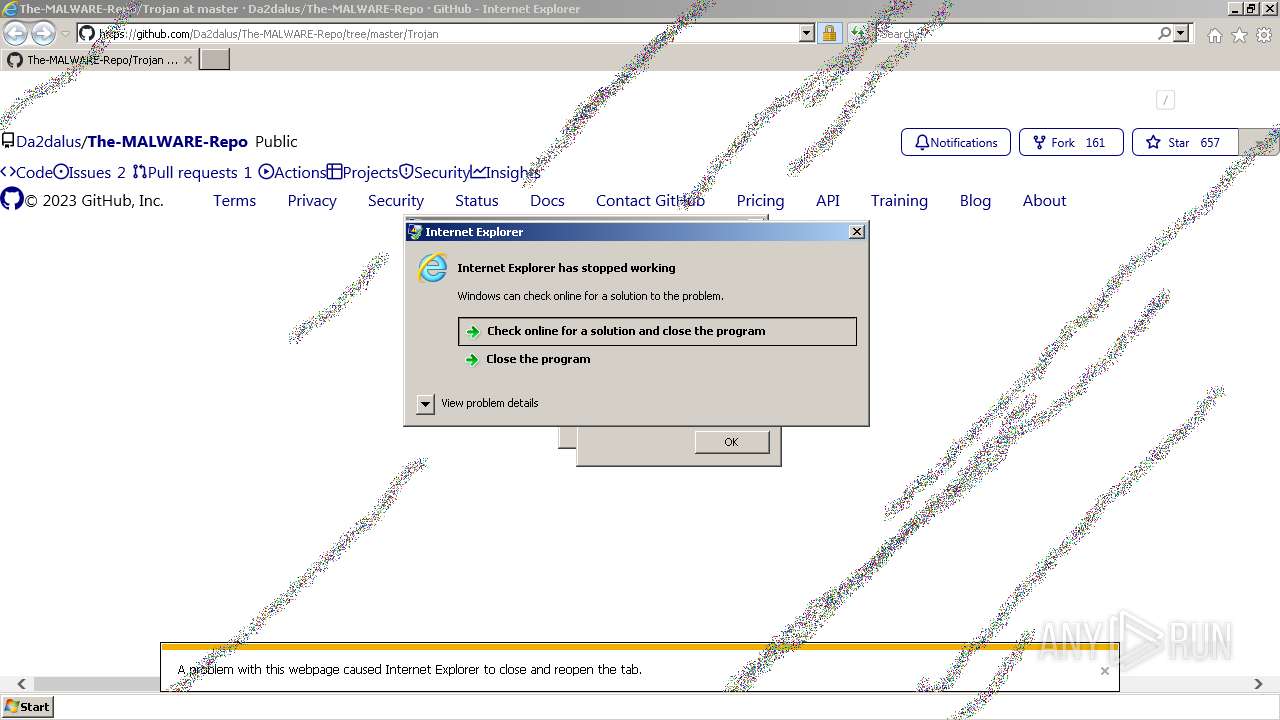
Changes the title of the Internet Explorer window
- cmd.exe (PID: 2836)
Changes default file association
- cmd.exe (PID: 2836)
Changes the Home page of Internet Explorer
- cmd.exe (PID: 2836)
Adds Netsh helper DLL
- cmd.exe (PID: 2836)
Reads the Internet Settings
- cmd.exe (PID: 2836)
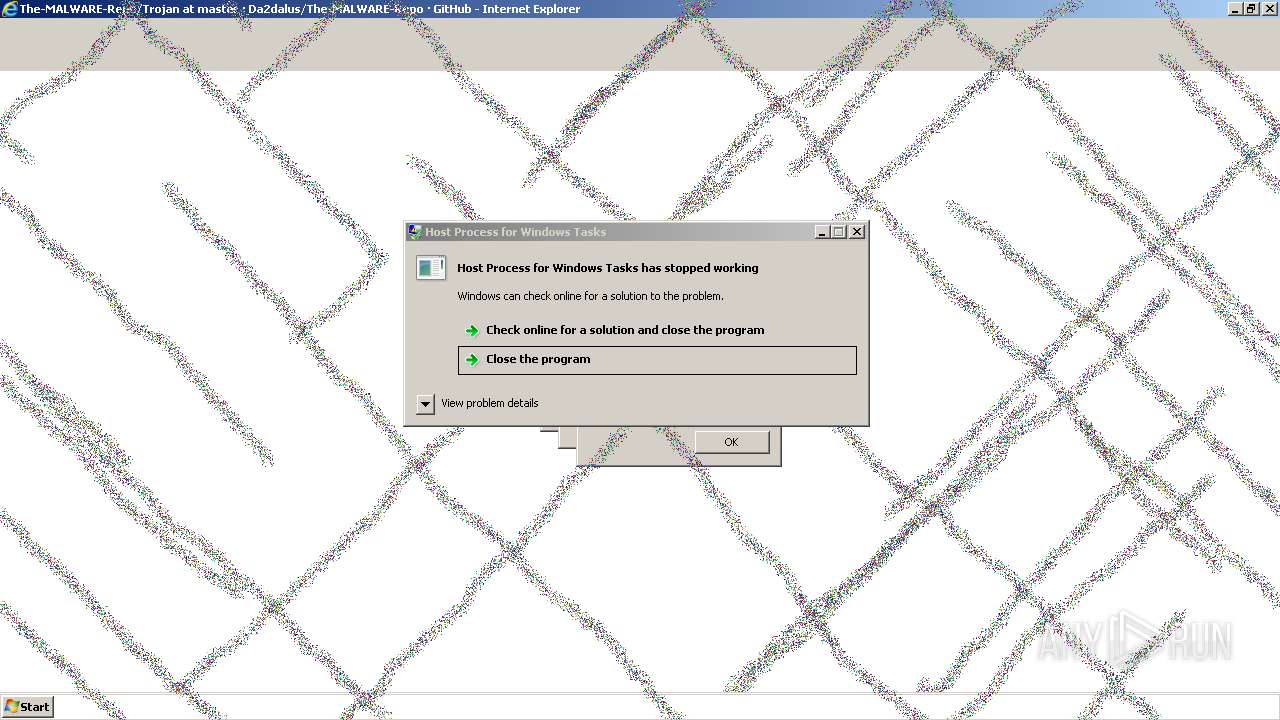
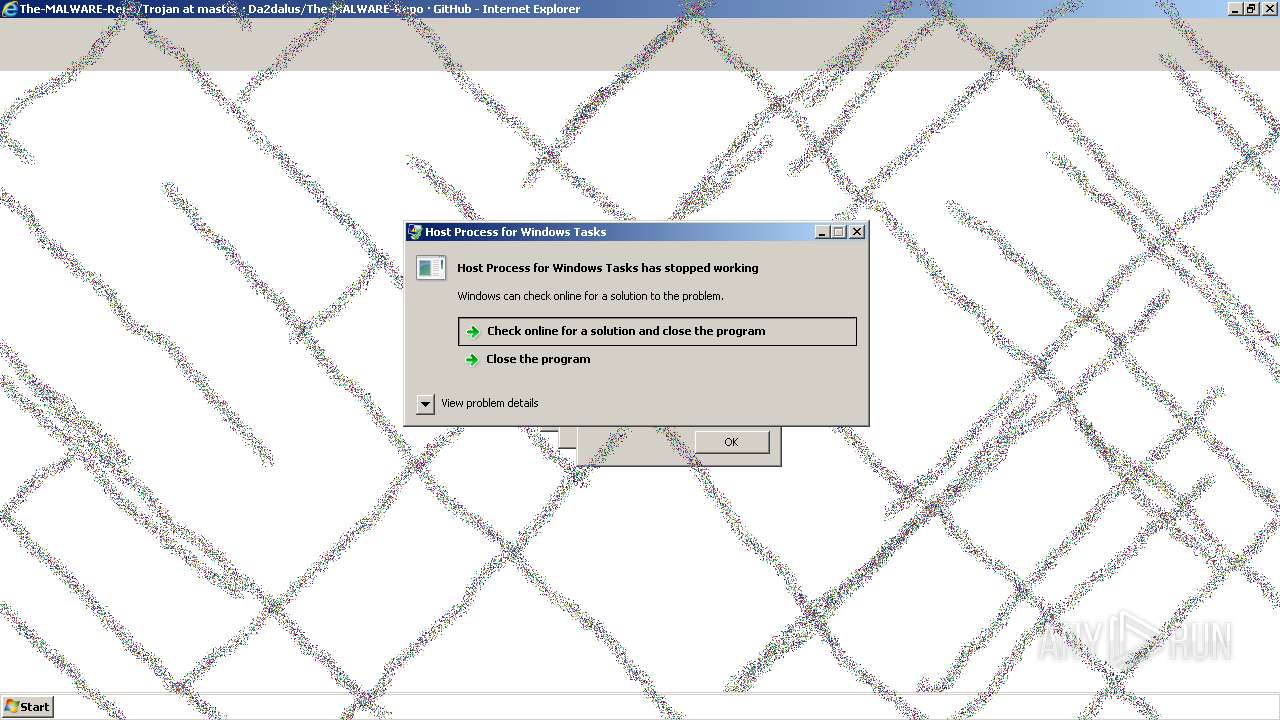
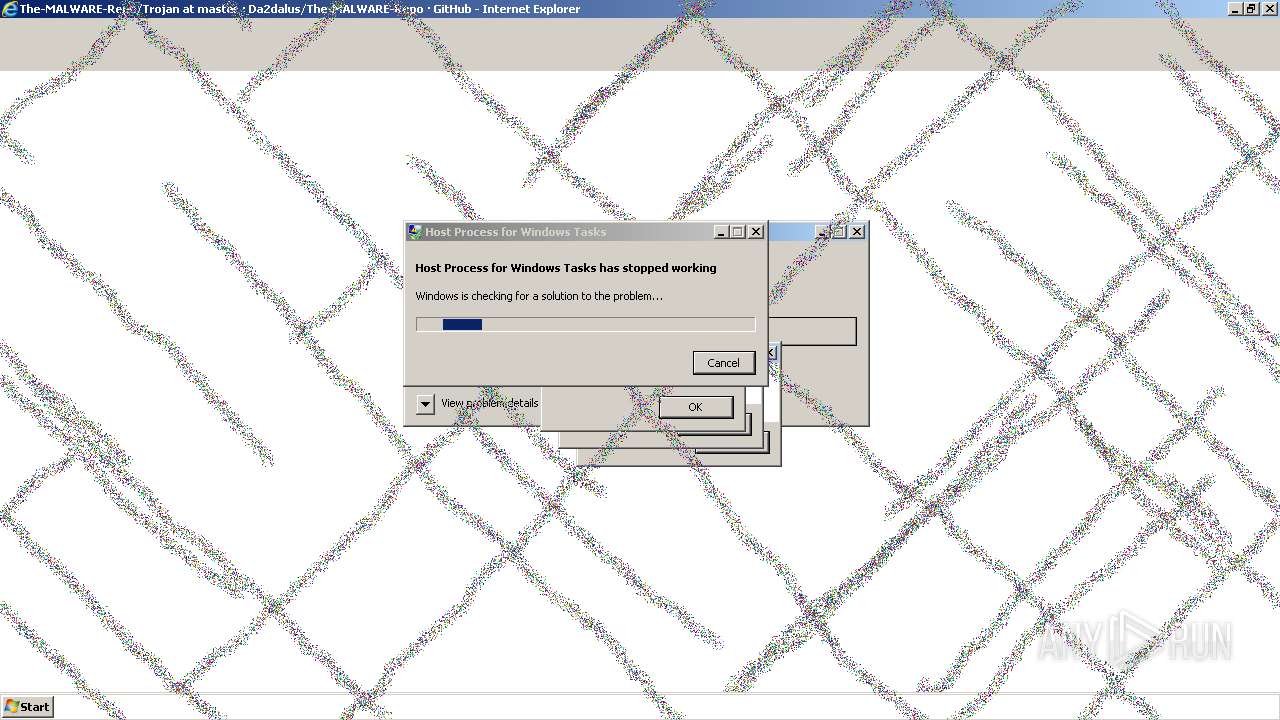
Changes the desktop background image
- cmd.exe (PID: 2836)
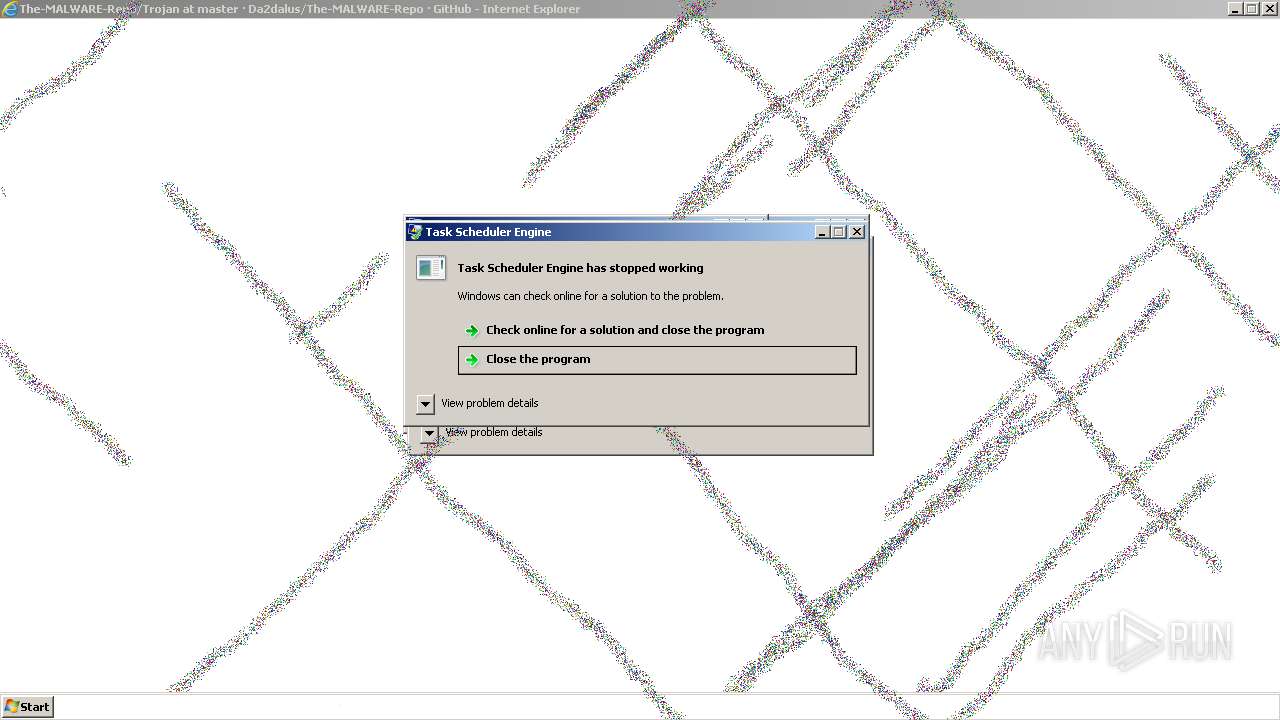
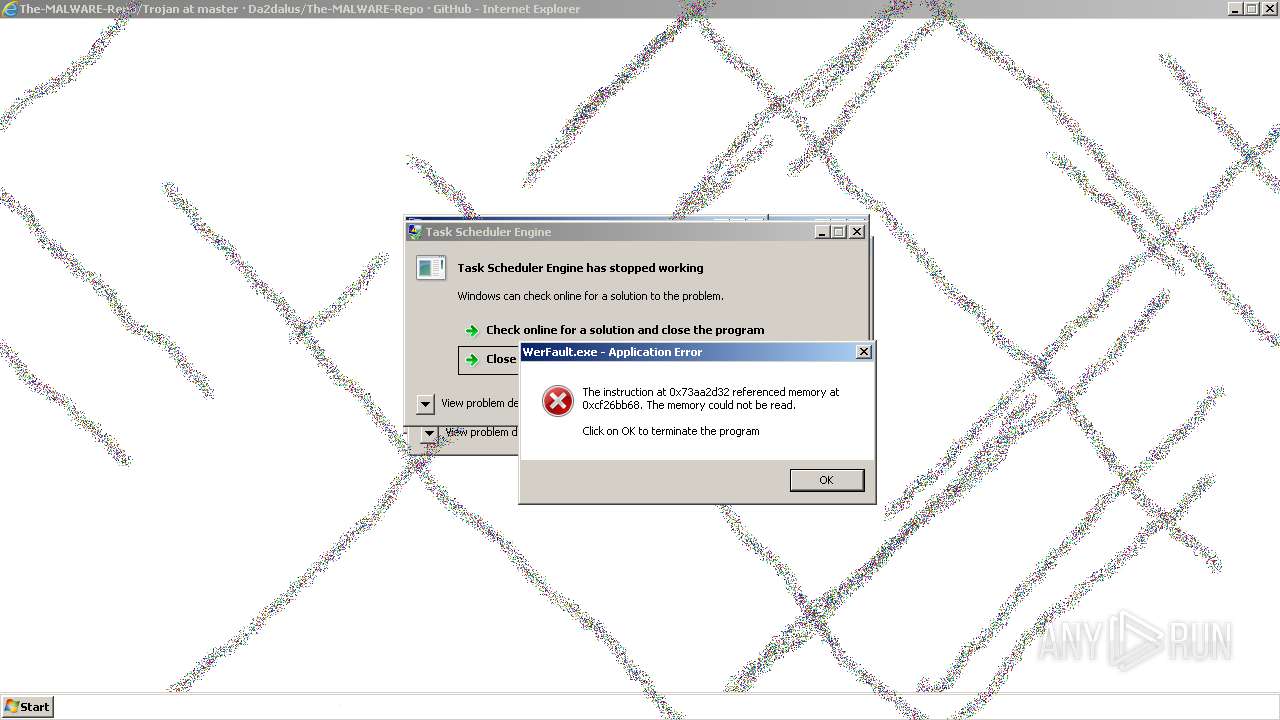
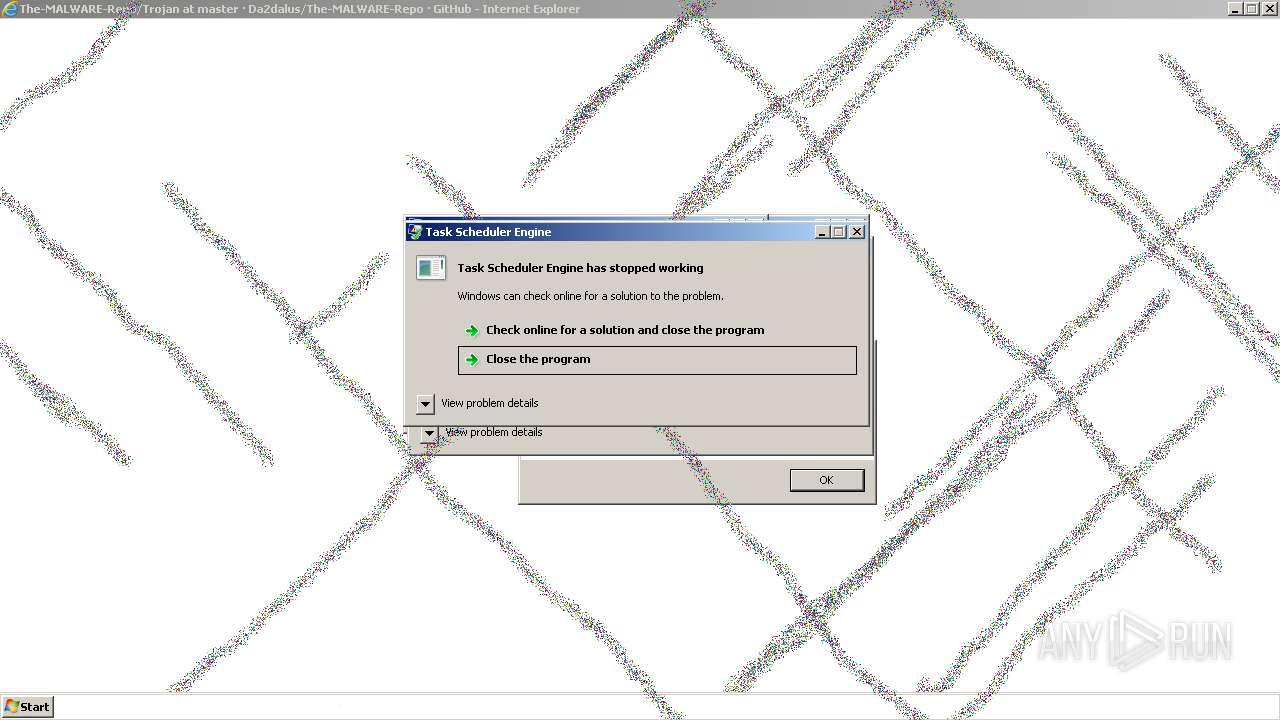
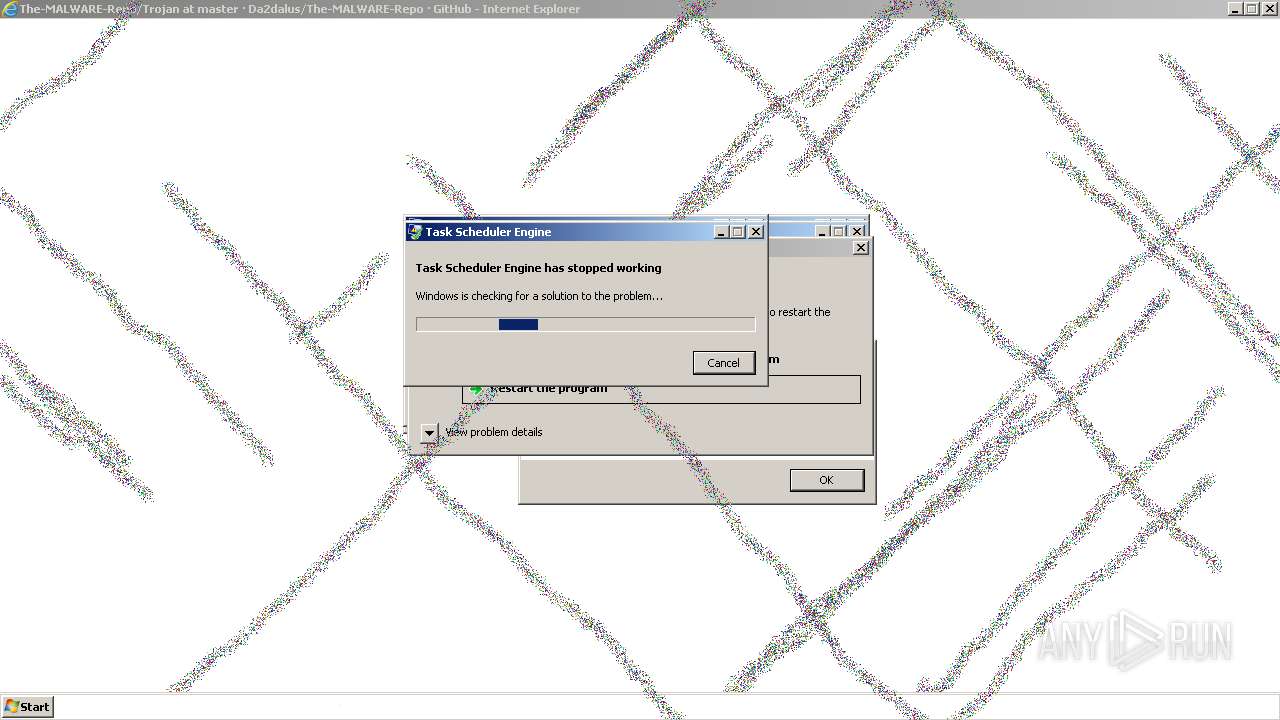
Creates/Modifies COM task schedule object
- cmd.exe (PID: 2836)
Accesses Microsoft Outlook profiles
- cmd.exe (PID: 2836)
Changes internet zones settings
- cmd.exe (PID: 2836)
Creates a software uninstall entry
- cmd.exe (PID: 2836)
Creates or modifies Windows services
- cmd.exe (PID: 2836)
INFO
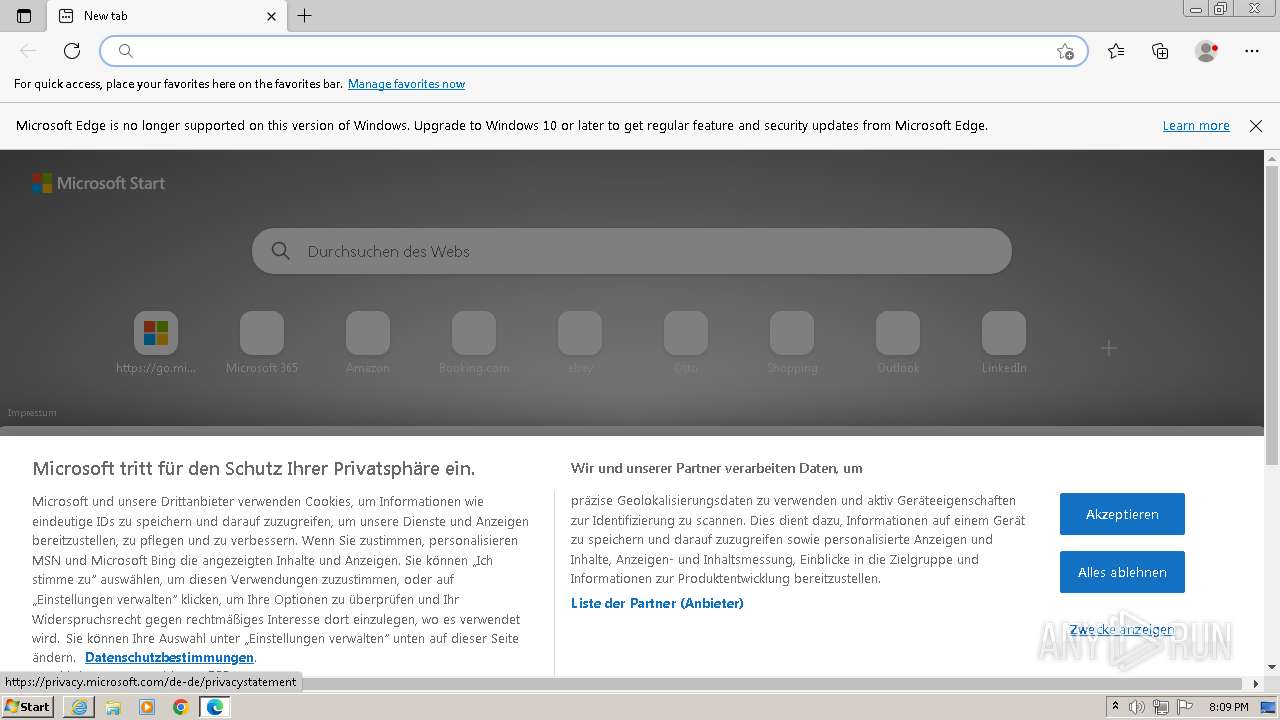
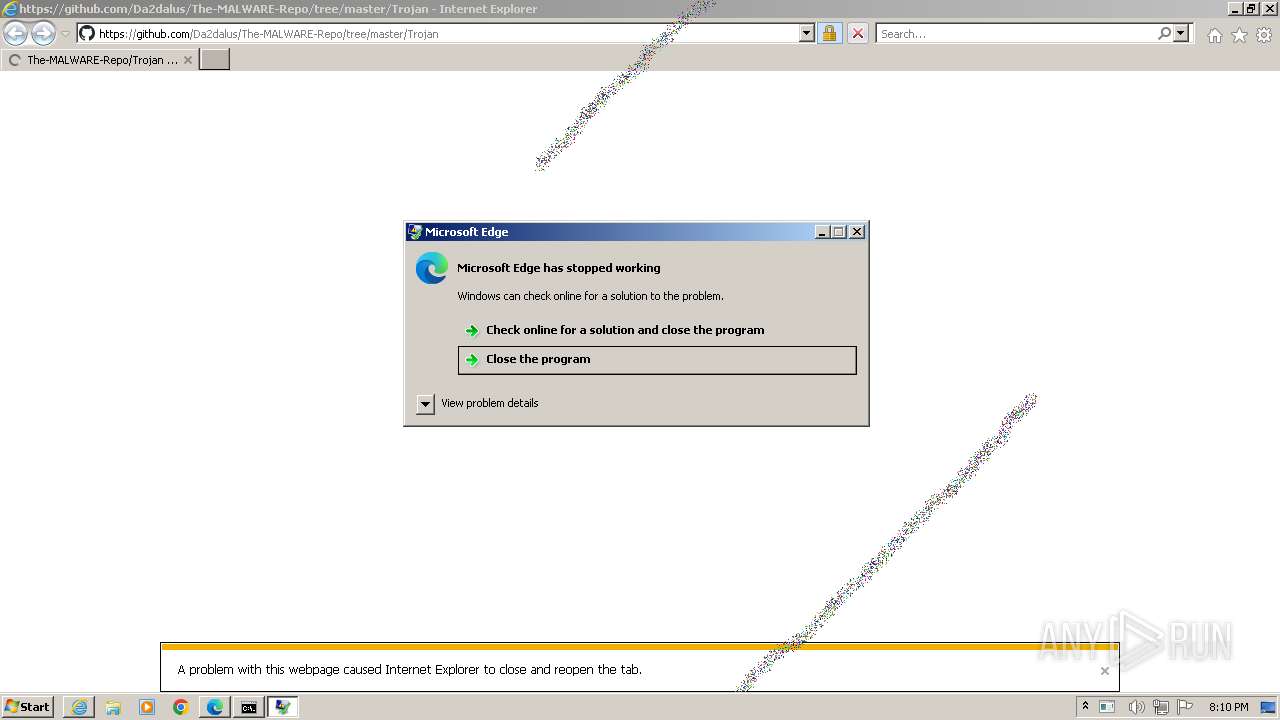
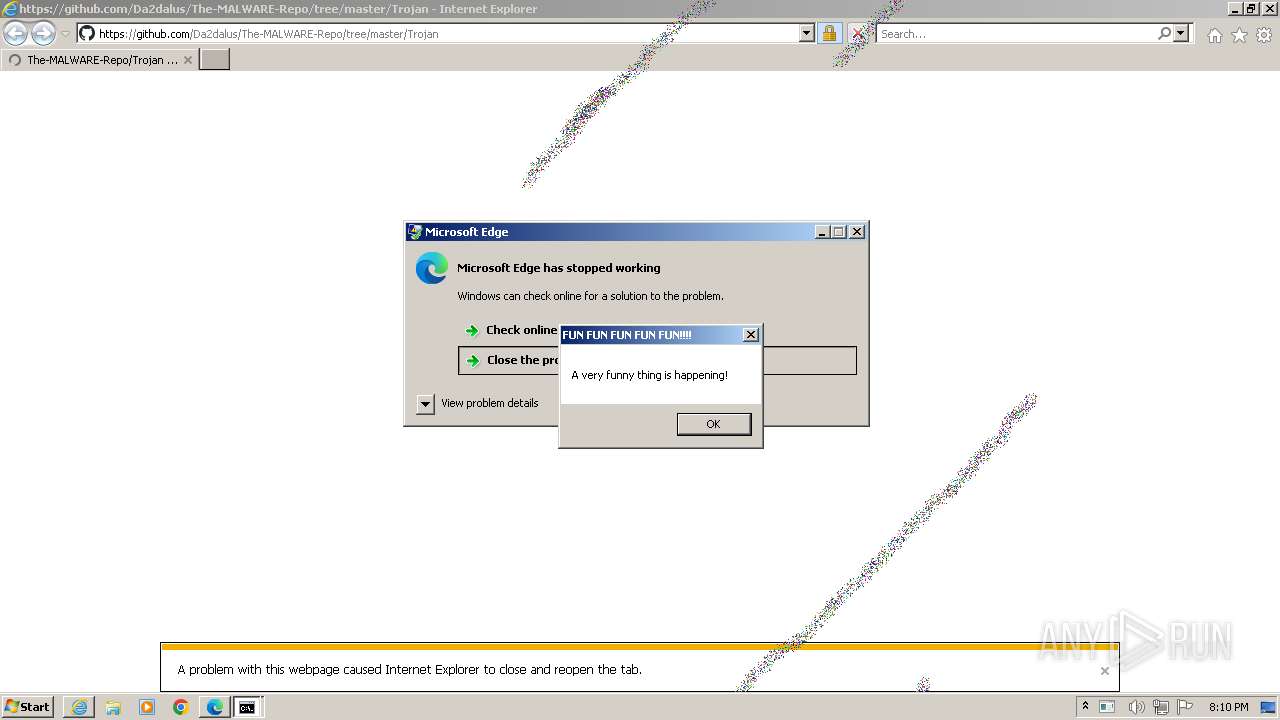
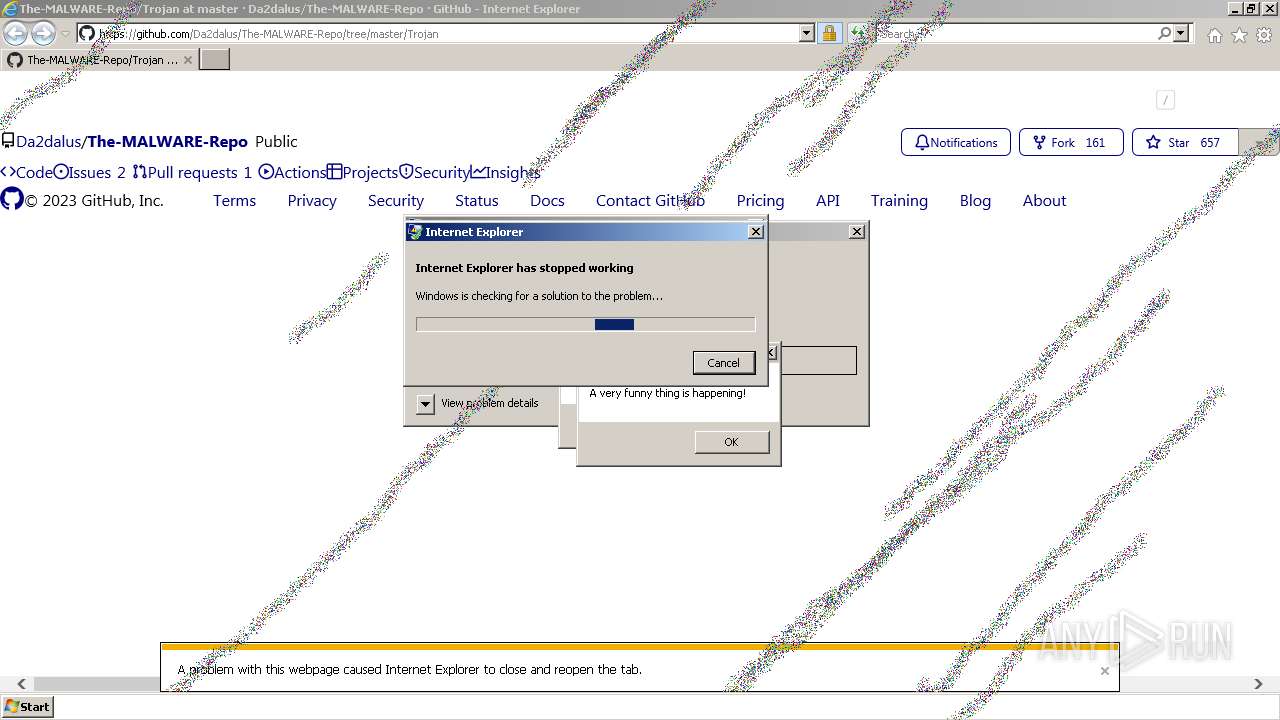
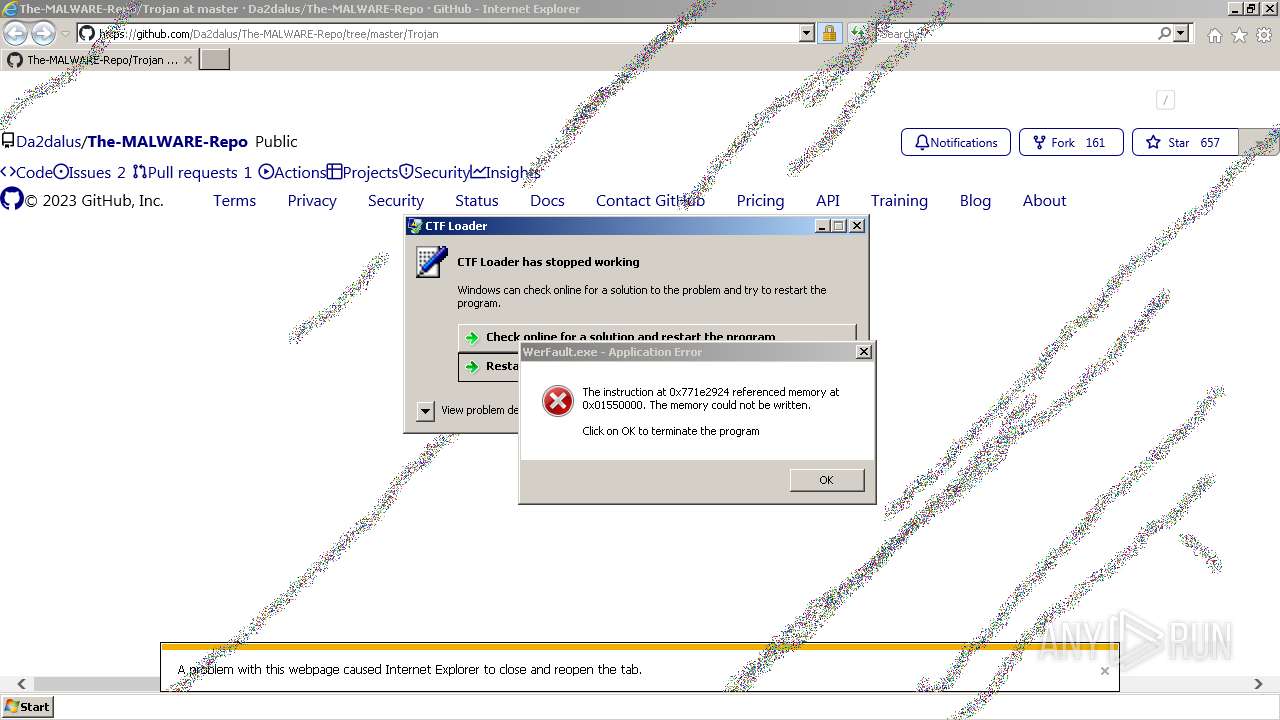
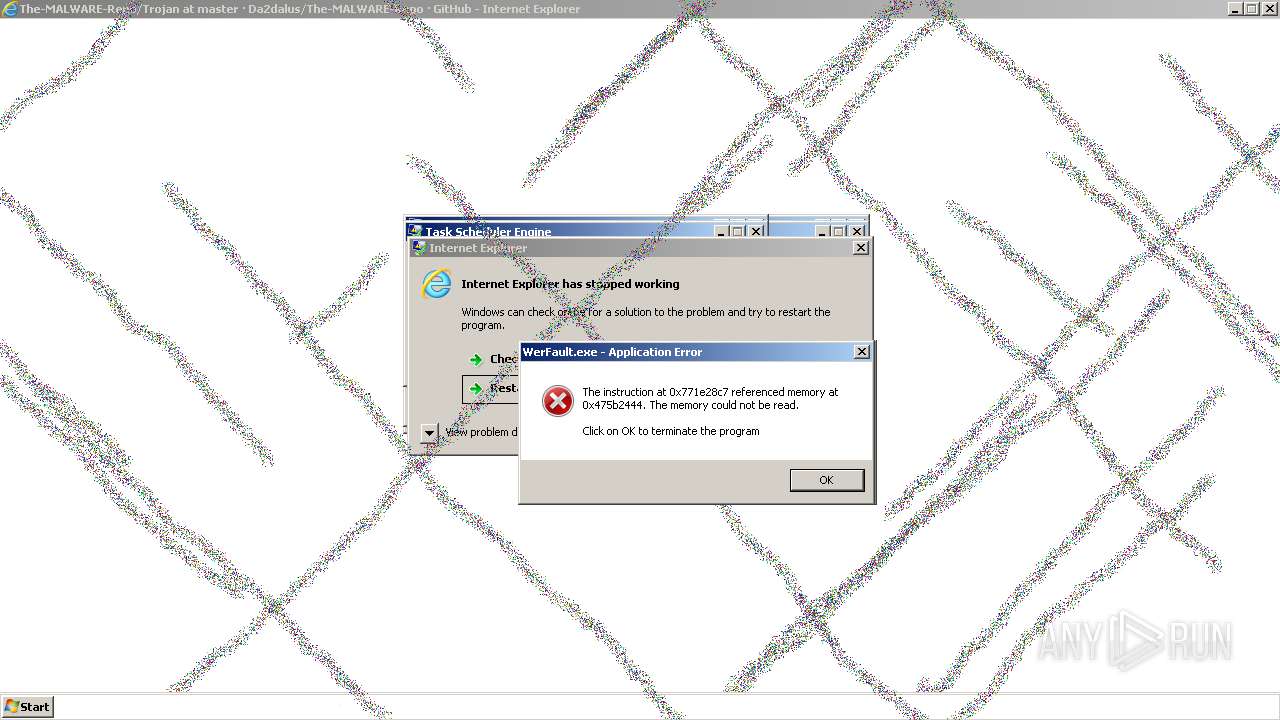
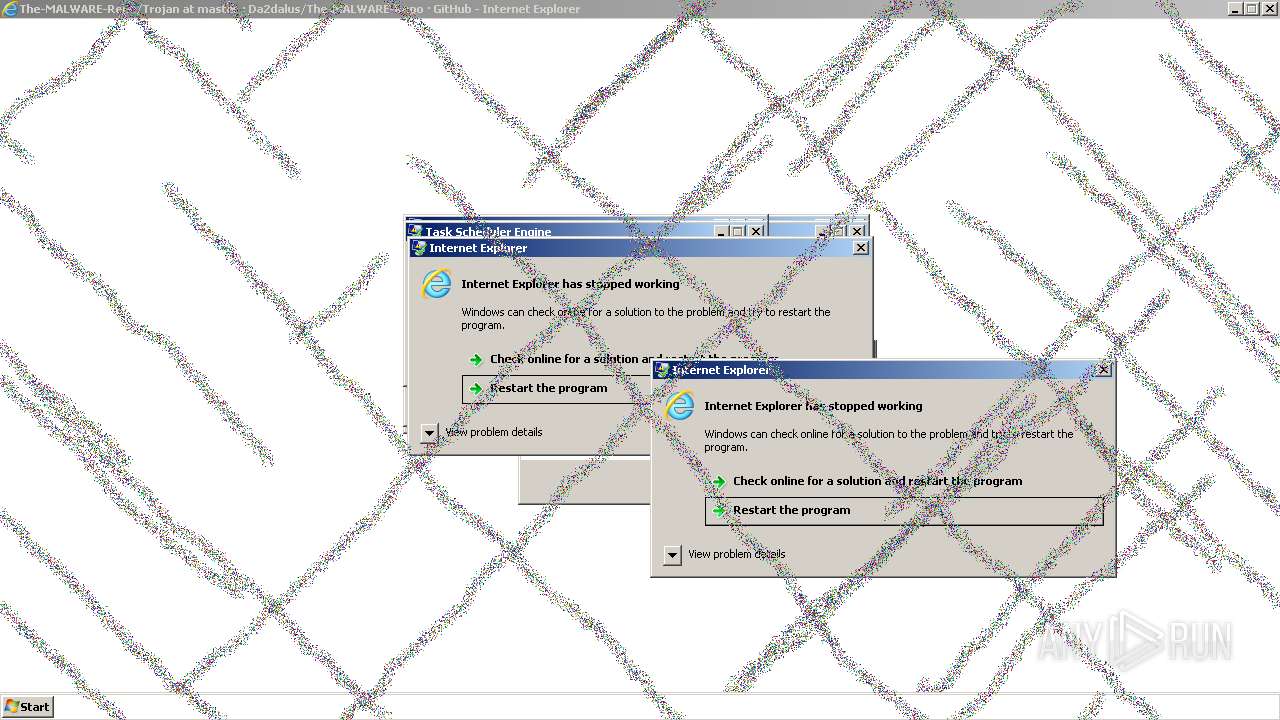
Application launched itself
- iexplore.exe (PID: 2708)
- msedge.exe (PID: 3640)
Checks supported languages
- wmpnscfg.exe (PID: 3380)
- VeryFun.exe (PID: 2176)
- wmpnscfg.exe (PID: 2760)
Reads the computer name
- wmpnscfg.exe (PID: 3380)
- VeryFun.exe (PID: 2176)
- wmpnscfg.exe (PID: 2760)
Manual execution by a user
- wmpnscfg.exe (PID: 3380)
- msedge.exe (PID: 3640)
- wmpnscfg.exe (PID: 2760)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3380)
- wmpnscfg.exe (PID: 2760)
Drops the executable file immediately after the start
- msedge.exe (PID: 2484)
- msedge.exe (PID: 3640)
The process uses the downloaded file
- msedge.exe (PID: 4080)
- msedge.exe (PID: 3640)
Reads mouse settings
- VeryFun.exe (PID: 2176)
- cmd.exe (PID: 2836)
- cmd.exe (PID: 1160)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 3132)
- cmd.exe (PID: 824)
- cmd.exe (PID: 968)
- cmd.exe (PID: 1832)
Checks transactions between databases Windows and Oracle
- cmd.exe (PID: 2836)
Reads Windows Product ID
- cmd.exe (PID: 2836)
Checks proxy server information
- cmd.exe (PID: 2836)
Checks Windows language
- cmd.exe (PID: 2836)
Reads the time zone
- cmd.exe (PID: 2836)
Reads Internet Explorer settings
- cmd.exe (PID: 2836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
128
Monitored processes
40
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4924 --field-trial-handle=920,i,6320601284984290045,1156710550915226141,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 644 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1236 --field-trial-handle=920,i,6320601284984290045,1156710550915226141,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --mojo-platform-channel-handle=3684 --field-trial-handle=920,i,6320601284984290045,1156710550915226141,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 4294930433 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 824 | "C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | VeryFun.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 968 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --instant-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2324 --field-trial-handle=920,i,6320601284984290045,1156710550915226141,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 968 | "C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | VeryFun.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4192 --field-trial-handle=920,i,6320601284984290045,1156710550915226141,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1160 | "C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | VeryFun.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3728 --field-trial-handle=920,i,6320601284984290045,1156710550915226141,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1832 | "C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | VeryFun.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
698 218
Read events
587 943
Write events
110 266
Delete events
9
Modification events
| (PID) Process: | (2708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000059010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2708) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
39
Suspicious files
1 117
Text files
166
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:C73A666F0190528846F31EE8F7E49F8F | SHA256:1B2B5896DC29FB35845FB1731A0AD6043AFC487499CFF5D09F6D4634CBD271A5 | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\50CD3D75D026C82E2E718570BD6F44D0_D222662A57BAA60D2F5EA0D2CC7B2F1C | binary | |
MD5:CE64B6538B48F9FC9FB02B75C3C06262 | SHA256:D97B6BB4FF18AA896A1971676684B7B23DC90CE598EA8236B8CF79553F741E4D | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:6C404A1EEE7B662F521765422362942D | SHA256:50ACD6891F67FCF9238B8980B894CFE9298614F1B405F5A86EEA9CB0CB7EC060 | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\QV0UMK71.txt | text | |
MD5:F152FD3E62073708EED0C753FBC068E3 | SHA256:90ED14020676C233702FA94C355EF2824FDFF477EF8A0AA6CF12626CCB2392E7 | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\1PL3OVQL.txt | text | |
MD5:E015765B71C71C2CDA74A289FB14A69F | SHA256:03F2D13D1A82FFECC8BA7C4F33DB8B376913A56C97E4EB524CB8F25158641258 | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:8D1FA3C50320F2651979BD7E70EAAF45 | SHA256:2D3BD862E5B45DB984083C2C69401E537671D4FF0D71CAA0BCC5A48BC4A18176 | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Trojan[1].htm | html | |
MD5:D01DB81699C8ADAA80A8D084928FD5D9 | SHA256:464D1600D53877FE82E34CCDA6A3E961BA18D0993BD3A2158D5E6A79B00B107C | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | binary | |
MD5:9674F79292E38391BE75E499FD9E89D6 | SHA256:B9E5271DE35684BD5E6C1C48BE950298E8AC1881F316AB2BDC0F3466C9136A7E | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3128 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\light-b92e9647318f[1].css | text | |
MD5:83DB2201DBE88660B6997830E7A61482 | SHA256:8F34F8C29F319A8D8AE2F087BE8954DFC22710EF7E8F3D99E872FD9BAE9E0ECA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
91
DNS requests
115
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3128 | iexplore.exe | GET | 200 | 8.248.135.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6e023fc7dc32a6b0 | unknown | compressed | 4.66 Kb | unknown |
3128 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAzQqL7GMs%2FmReygqbCE%2Bxw%3D | unknown | binary | 313 b | unknown |
3128 | iexplore.exe | GET | 200 | 8.248.135.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0e152650b56312b4 | unknown | compressed | 4.66 Kb | unknown |
3128 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 304 | 8.248.135.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?60b2f43ad8cf70d9 | unknown | — | — | unknown |
3128 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | binary | 471 b | unknown |
2708 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
2708 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 8.248.135.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?18478d18b79fc9a0 | unknown | compressed | 61.6 Kb | unknown |
2708 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3128 | iexplore.exe | 140.82.121.3:443 | github.com | GITHUB | US | unknown |
3128 | iexplore.exe | 8.248.135.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3128 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1080 | svchost.exe | 8.248.135.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
3128 | iexplore.exe | 185.199.108.154:443 | github.githubassets.com | FASTLY | US | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |
user-images.githubusercontent.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |