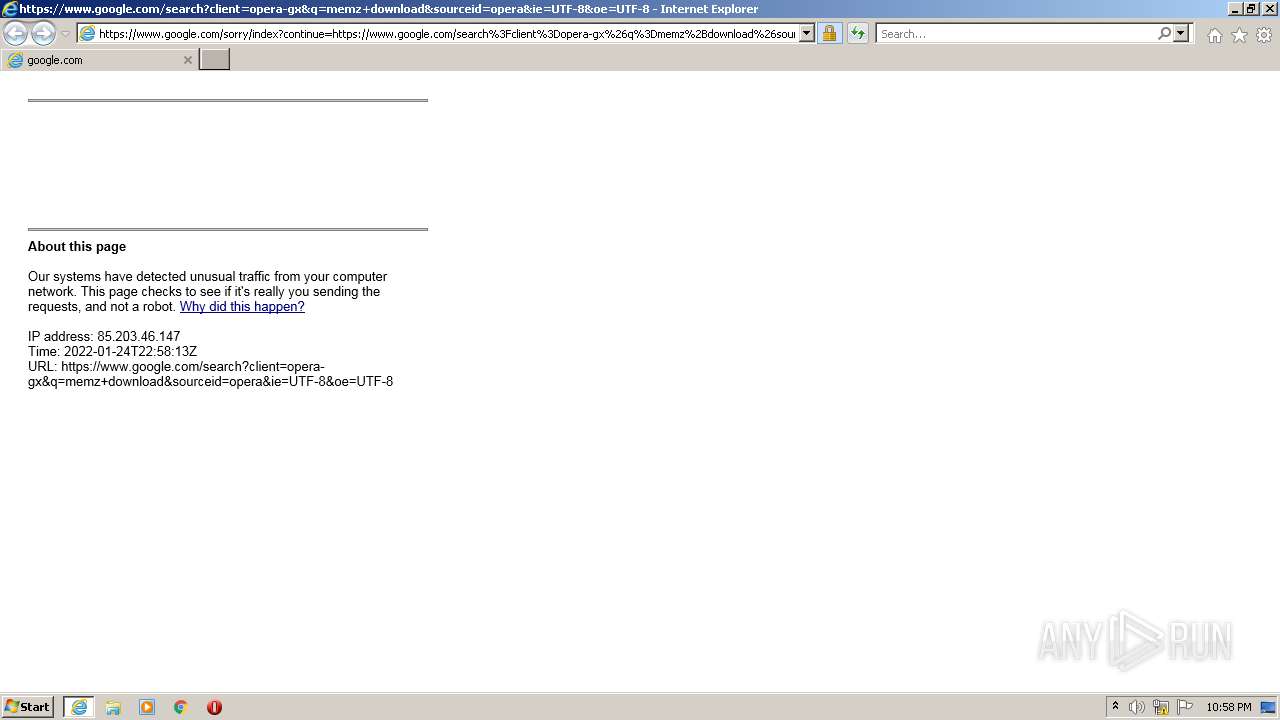
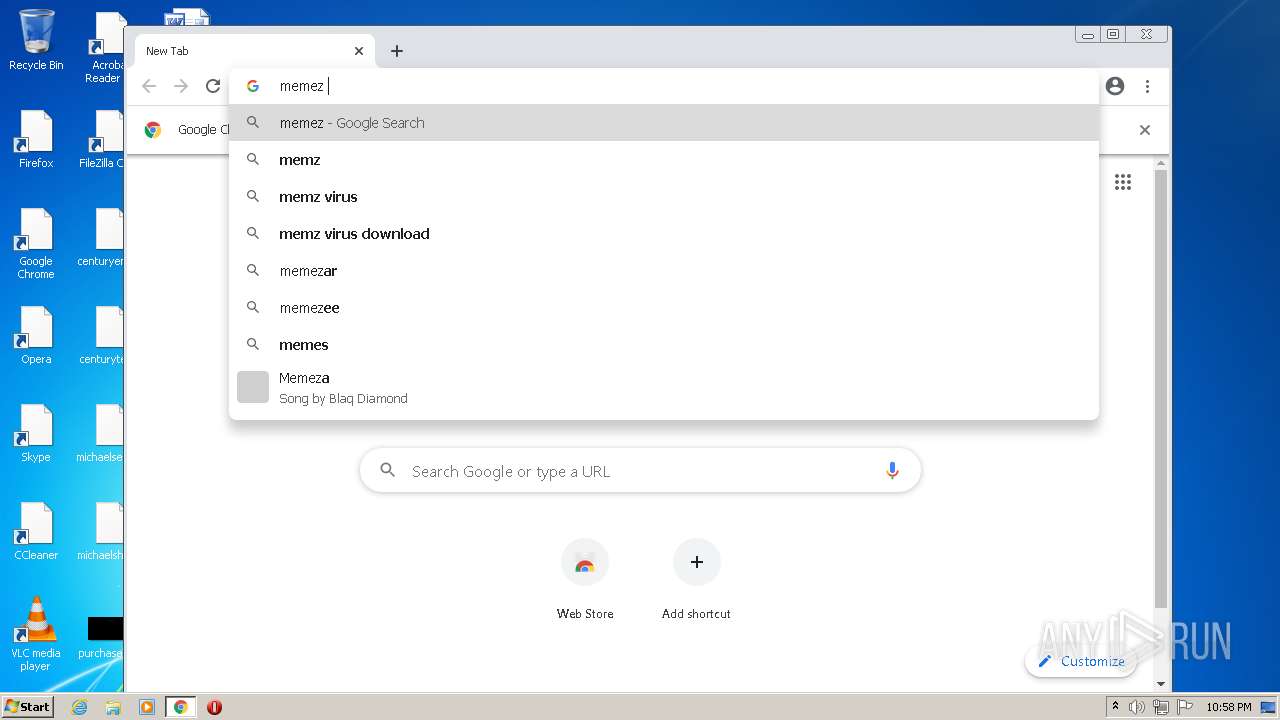
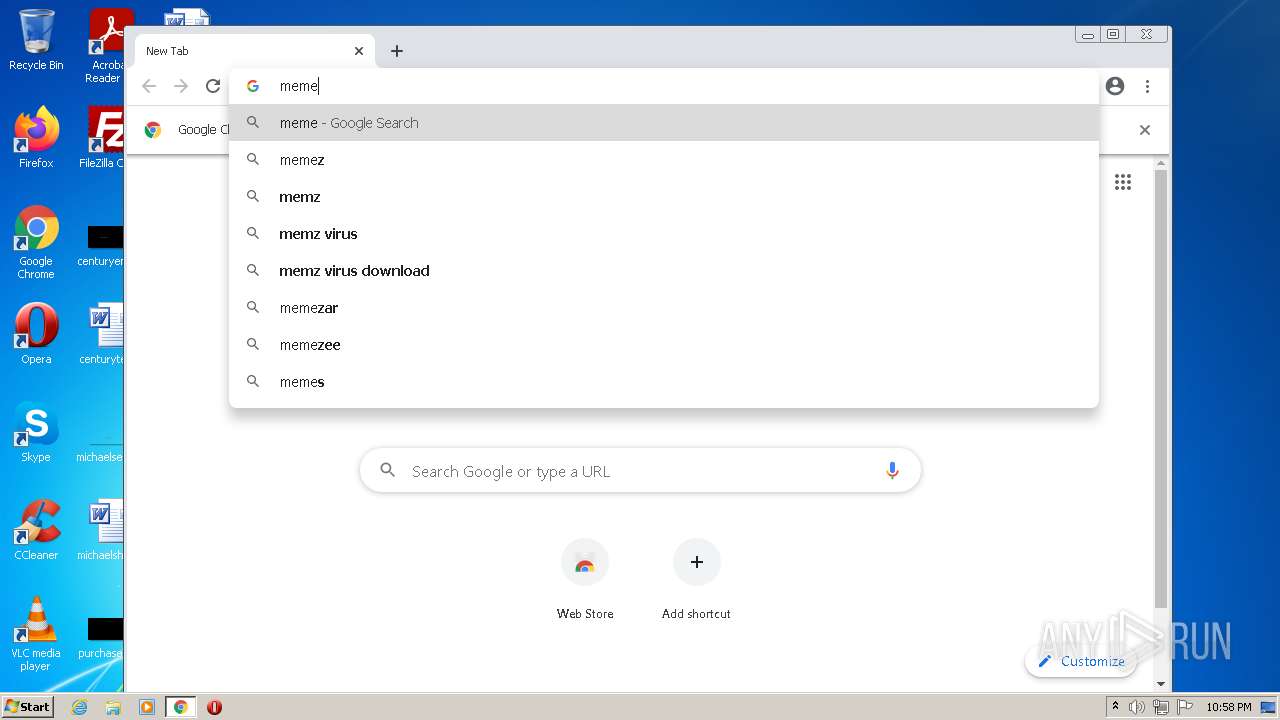
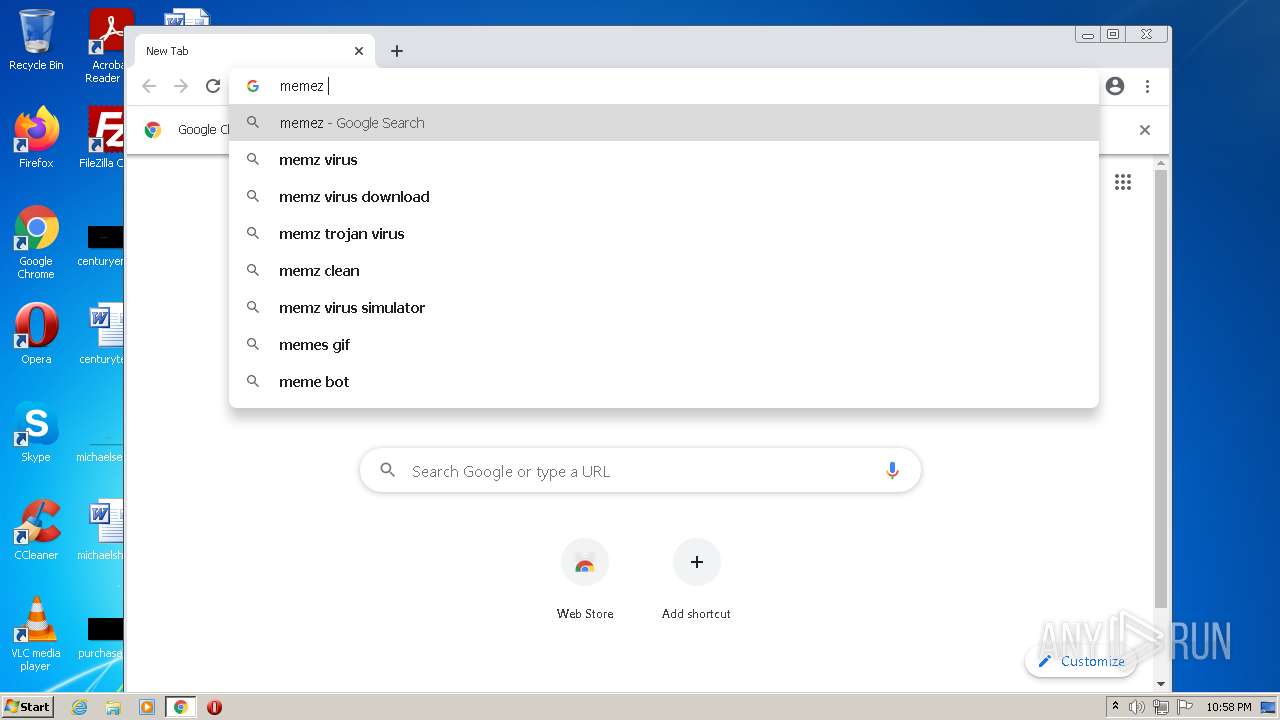
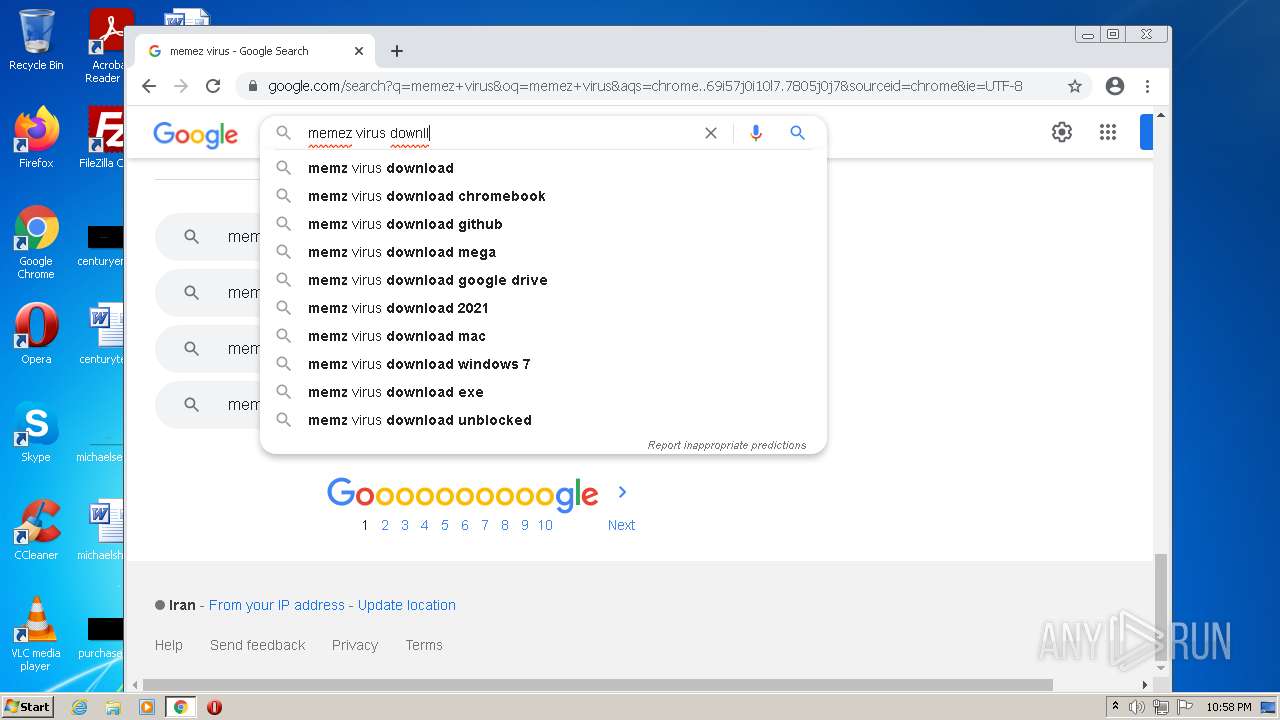
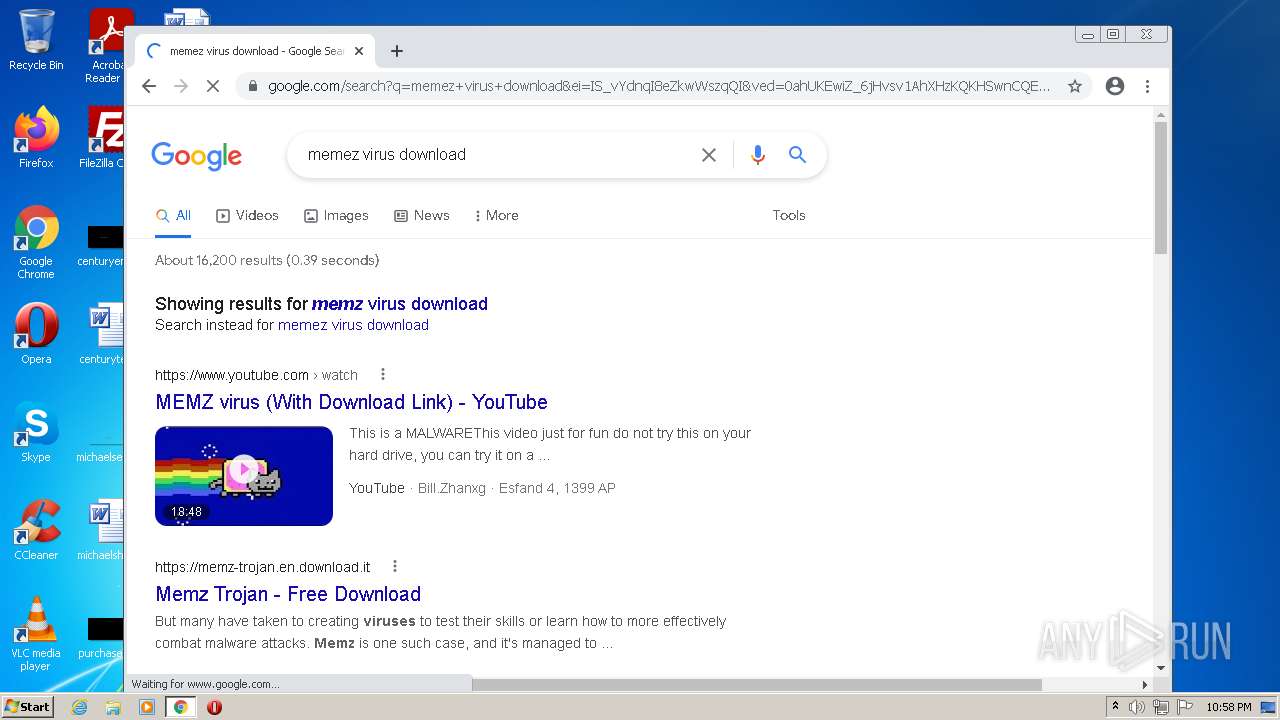
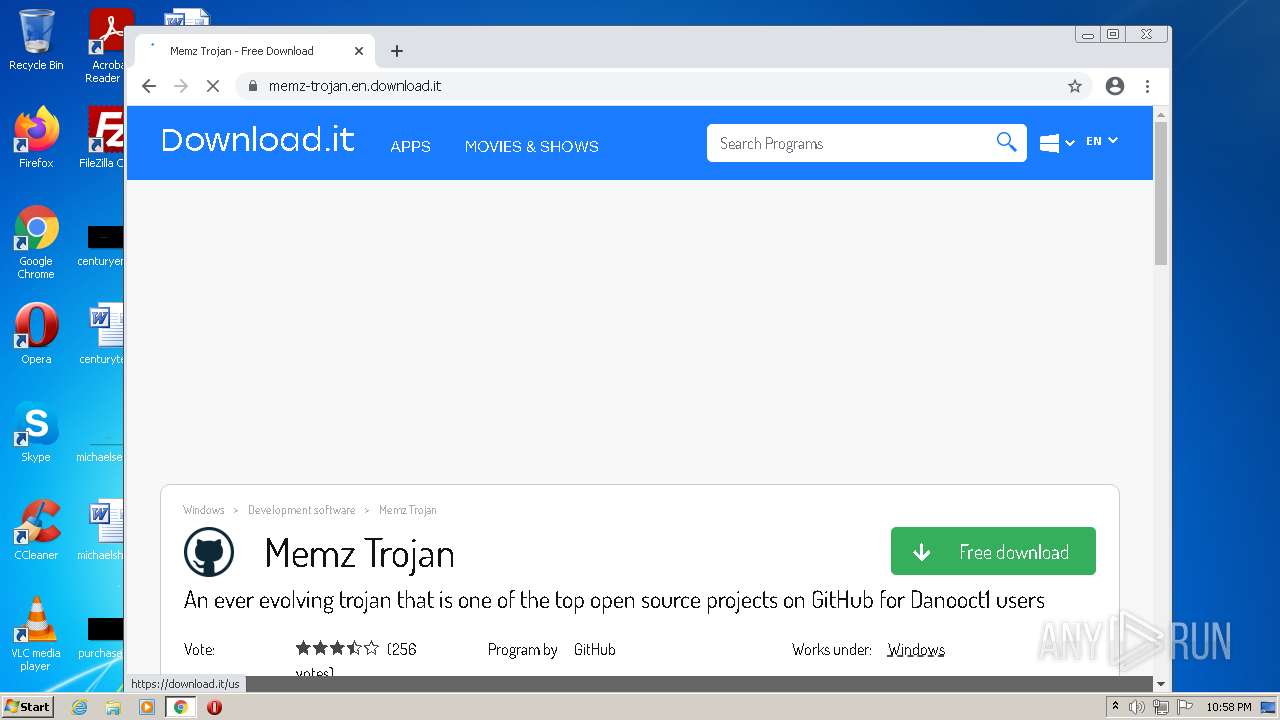
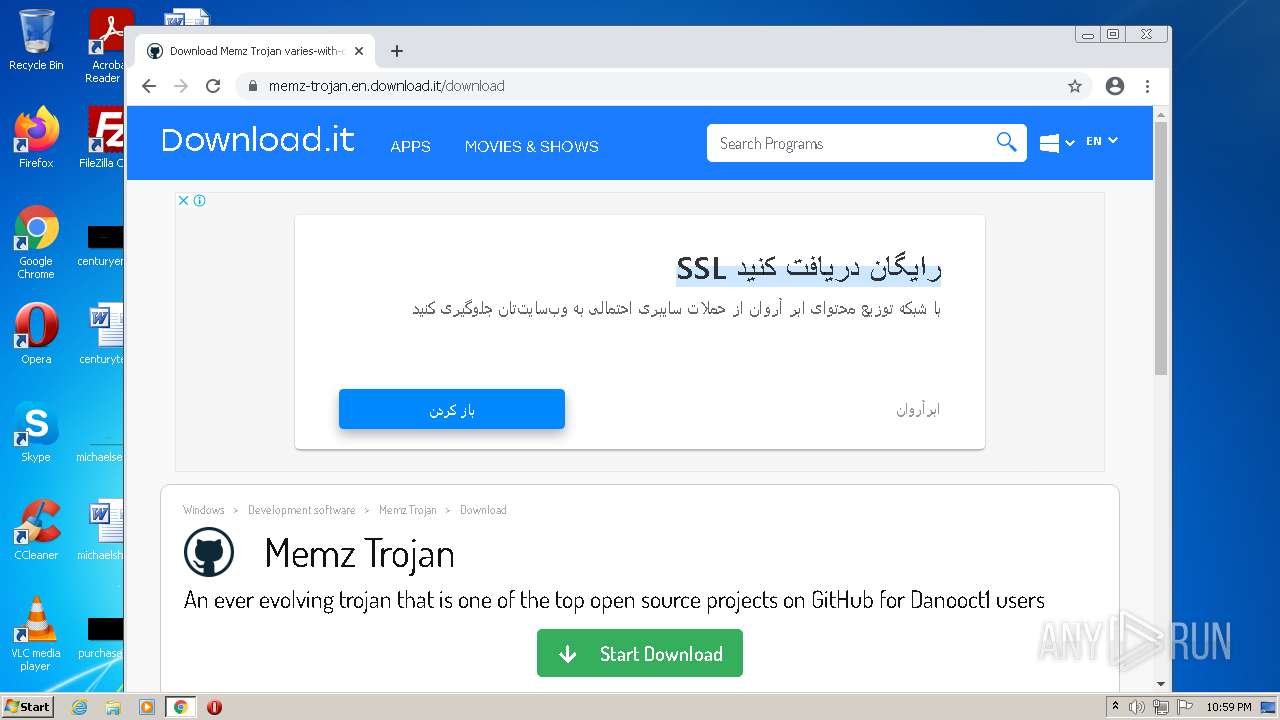
| URL: | https://www.google.com/search?client=opera-gx&q=memz+download&sourceid=opera&ie=UTF-8&oe=UTF-8 |
| Full analysis: | https://app.any.run/tasks/6cd62531-339c-408c-97fa-22b8011cfed0 |
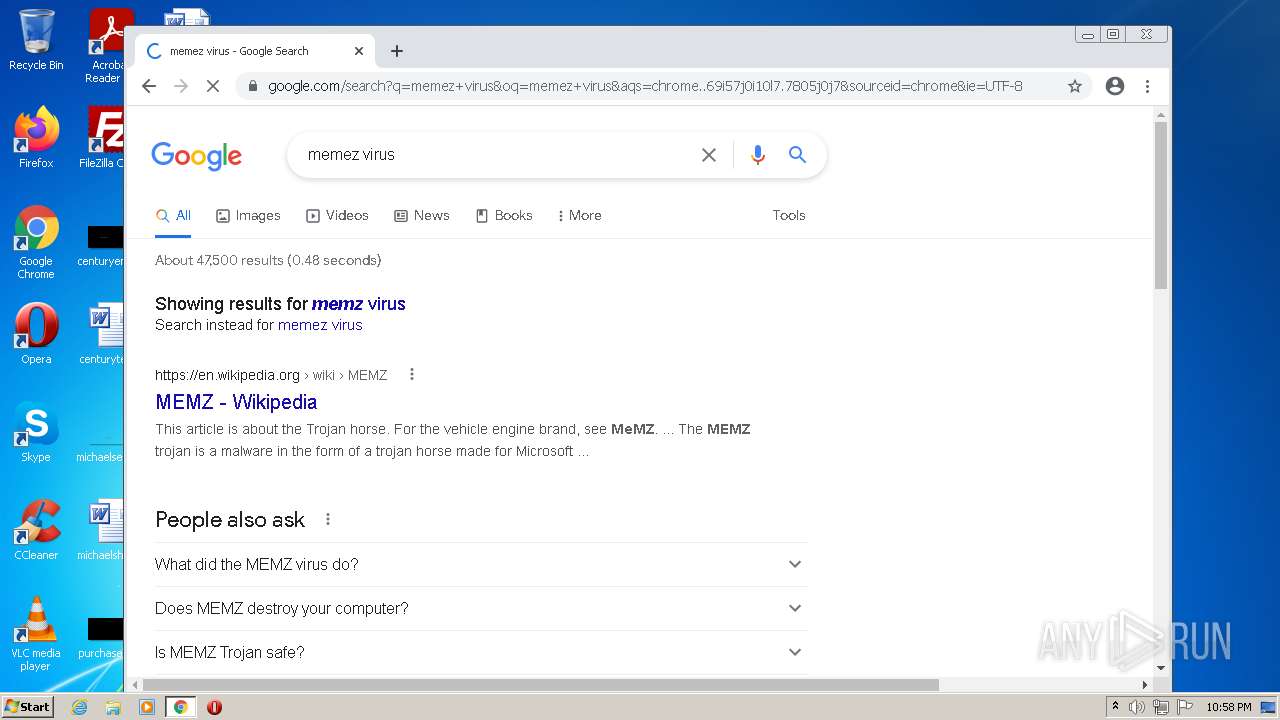
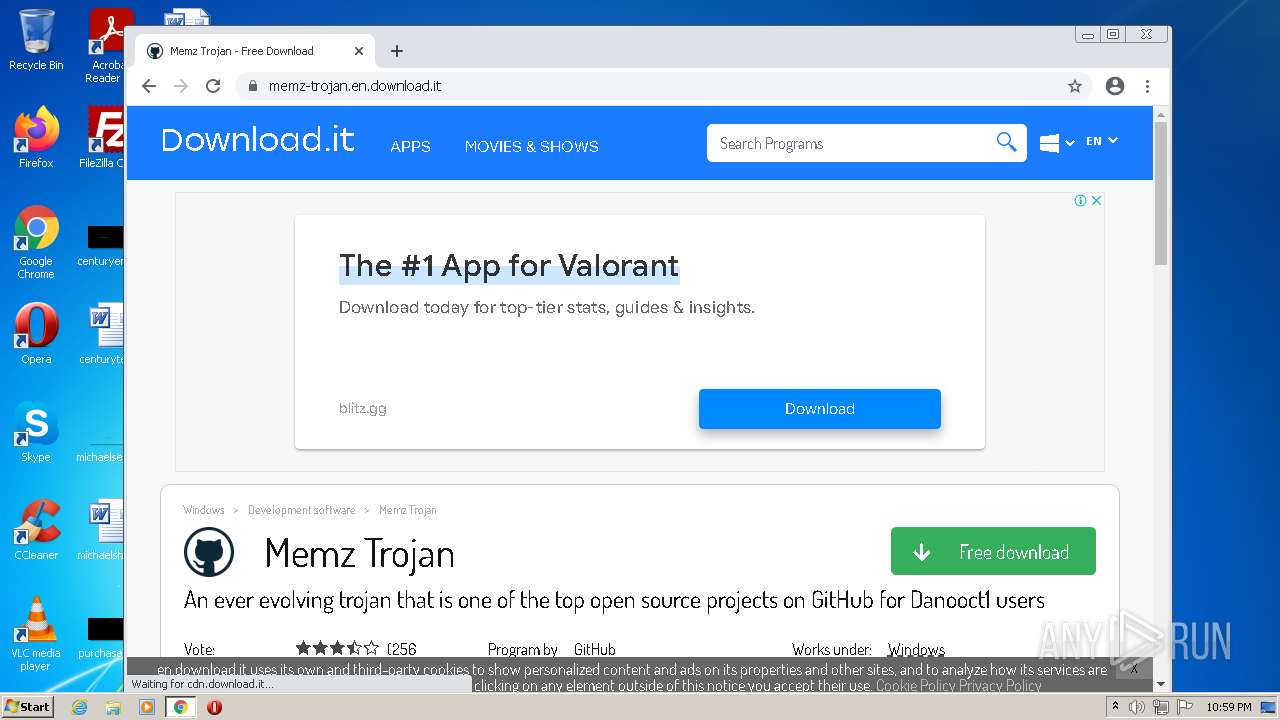
| Verdict: | Malicious activity |
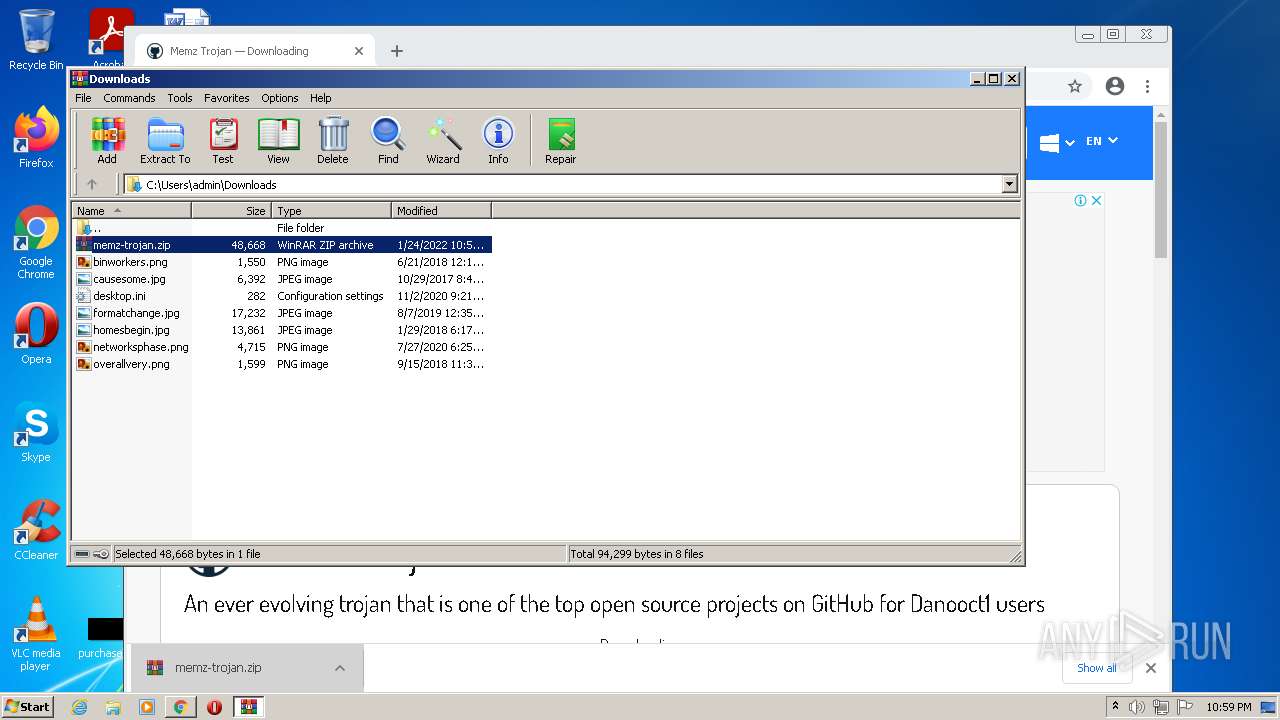
| Analysis date: | January 24, 2022, 22:58:08 |
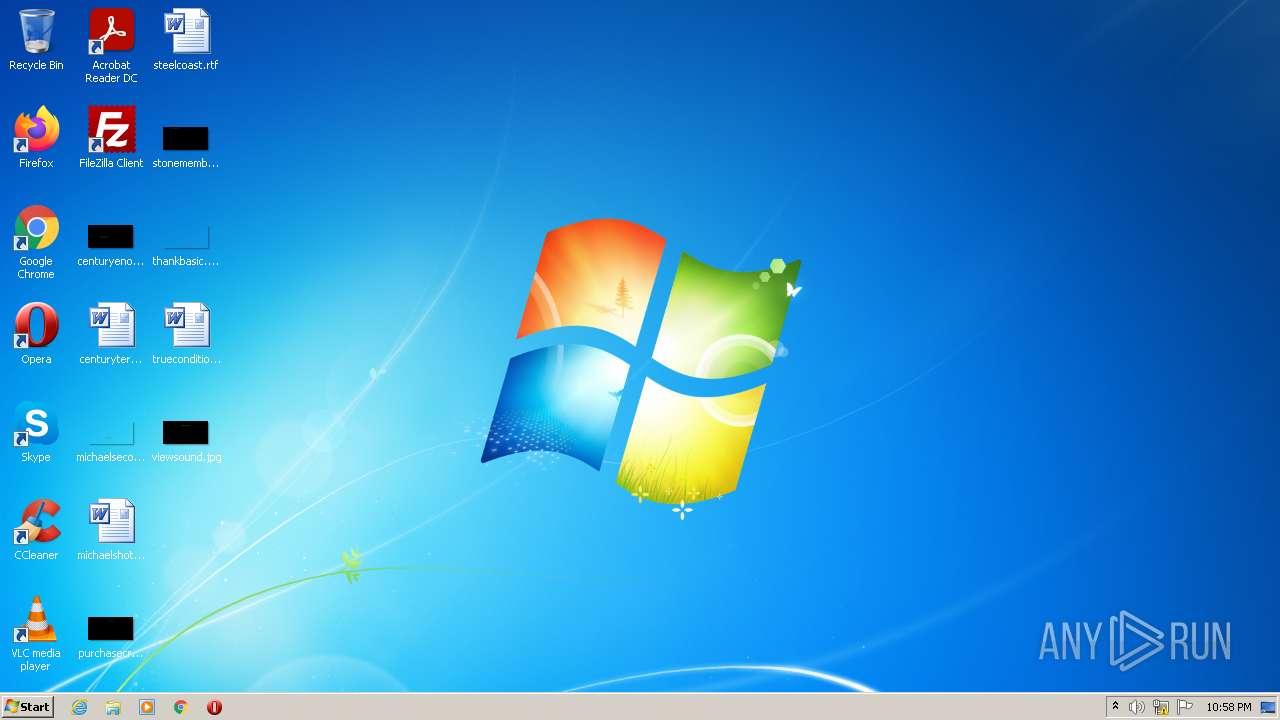
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
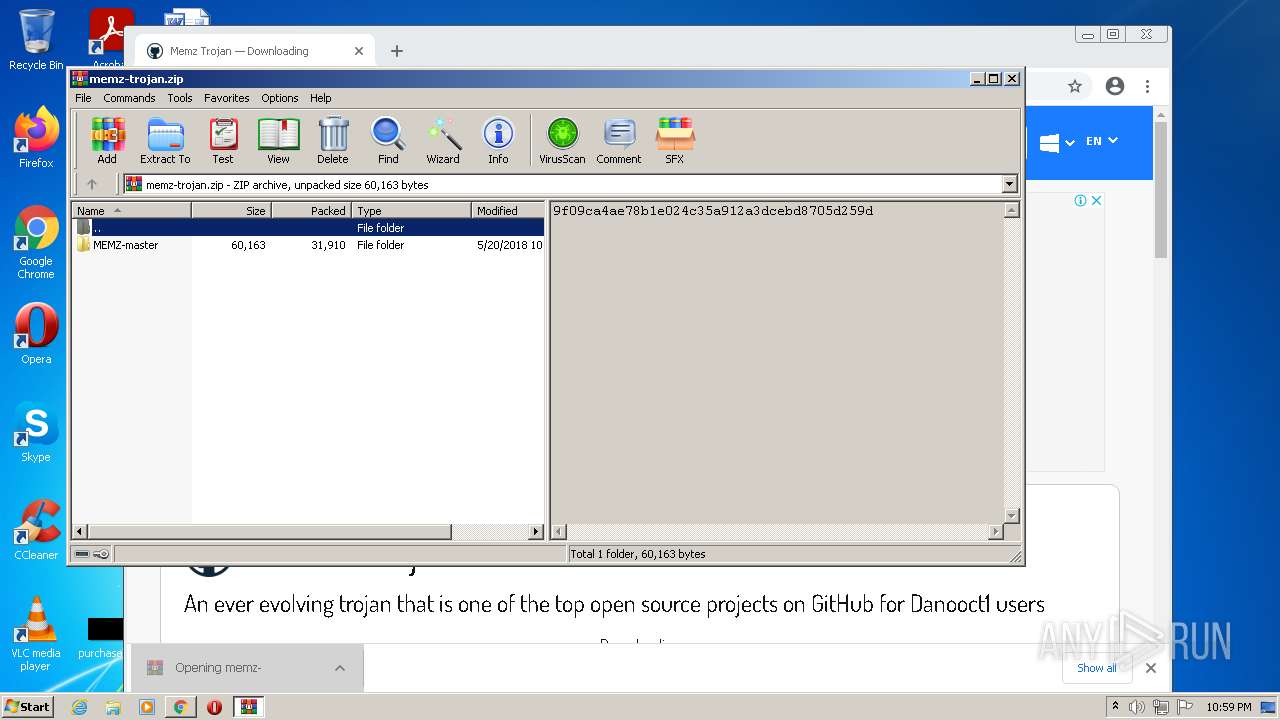
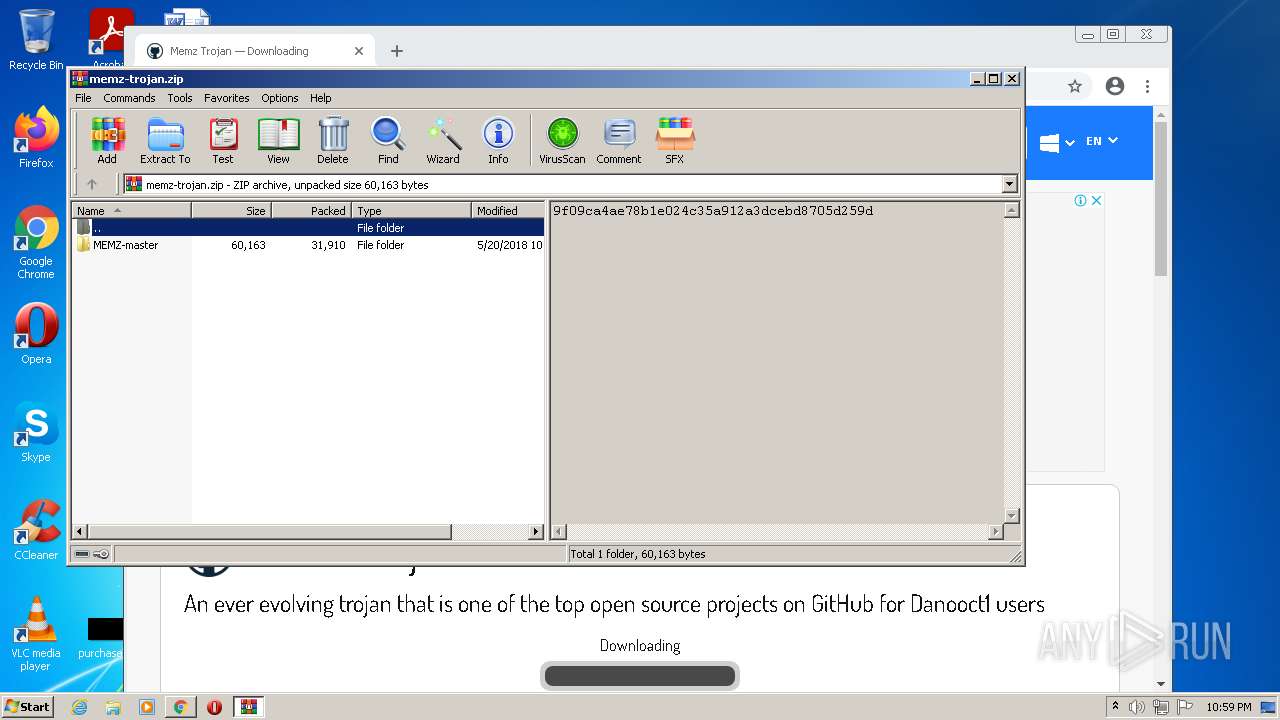
| MD5: | 715C417684780CDC72C7D4142F4B9570 |
| SHA1: | F6DB9A429E4461D75AAF634F3AA4BCCB9185183E |
| SHA256: | F1A57A1469E18406EEB7A774E92FBBB7FFA83BA947D56C0ECFFD02EB2C01BBCC |
| SSDEEP: | 3:N8DSLIwAEXG7CqSeIYqOvNFA9KlDMgIJk:2OLIwBGeqbIYqOvNbMN2 |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 3308)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3492)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3704)
Reads the computer name
- WinRAR.exe (PID: 1496)
Checks supported languages
- WinRAR.exe (PID: 1496)
Executable content was dropped or overwritten
- chrome.exe (PID: 3308)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 3308)
INFO
Reads the computer name
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 2916)
- chrome.exe (PID: 2504)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 2392)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 2228)
- chrome.exe (PID: 1468)
Checks Windows Trust Settings
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 2916)
Reads internet explorer settings
- iexplore.exe (PID: 3492)
Changes internet zones settings
- iexplore.exe (PID: 2916)
Reads settings of System Certificates
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 3492)
- chrome.exe (PID: 2540)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2916)
Application launched itself
- chrome.exe (PID: 3704)
- iexplore.exe (PID: 2916)
Checks supported languages
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 3492)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 3828)
- chrome.exe (PID: 2068)
- chrome.exe (PID: 2504)
- chrome.exe (PID: 3208)
- chrome.exe (PID: 3332)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 2392)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 2980)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 3312)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 3572)
- chrome.exe (PID: 3644)
- chrome.exe (PID: 2824)
- chrome.exe (PID: 2820)
- chrome.exe (PID: 3520)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 320)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 4060)
- chrome.exe (PID: 1728)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 872)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 3124)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 3296)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 288)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 3220)
- chrome.exe (PID: 2228)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 3872)
- chrome.exe (PID: 1468)
- chrome.exe (PID: 3952)
- chrome.exe (PID: 3308)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 3584)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 3380)
Creates files in the user directory
- iexplore.exe (PID: 3492)
Changes settings of System certificates
- iexplore.exe (PID: 2916)
Manual execution by user
- chrome.exe (PID: 3704)
Reads the date of Windows installation
- iexplore.exe (PID: 2916)
- chrome.exe (PID: 2228)
Reads the hosts file
- chrome.exe (PID: 2540)
- chrome.exe (PID: 3704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
48
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,6023520822971068325,17482402013386732789,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,6023520822971068325,17482402013386732789,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3312 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,6023520822971068325,17482402013386732789,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2024 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,6023520822971068325,17482402013386732789,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3760 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
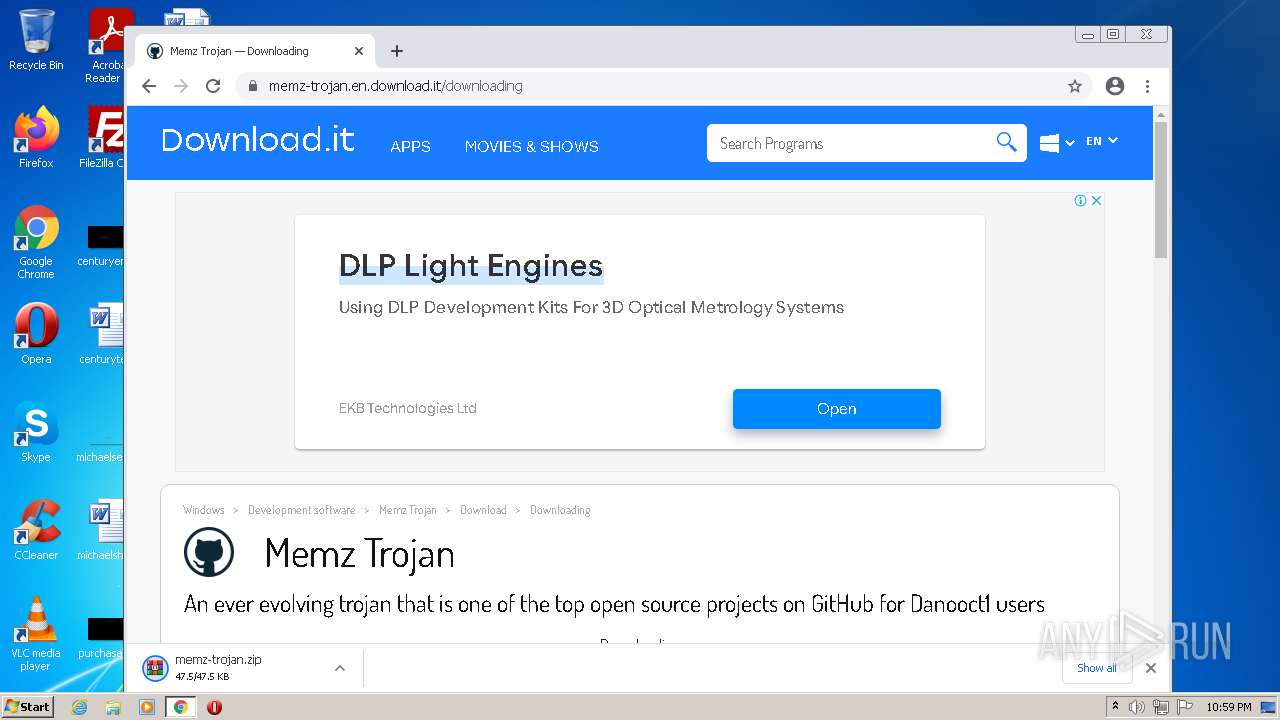
| 1496 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\memz-trojan.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,6023520822971068325,17482402013386732789,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,6023520822971068325,17482402013386732789,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,6023520822971068325,17482402013386732789,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2968 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,6023520822971068325,17482402013386732789,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3924 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,6023520822971068325,17482402013386732789,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3844 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
31 576
Read events
31 245
Write events
319
Delete events
12
Modification events
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937461 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937461 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
249
Text files
160
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\api[1].js | text | |
MD5:— | SHA256:— | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\TCZXRM3Q.txt | text | |
MD5:— | SHA256:— | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07644E38ED7C9F37D11EEC6D4335E02_CF98E93287B57910F3C2F3AE8F983EDC | der | |
MD5:— | SHA256:— | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:— | SHA256:— | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E87CE99F124623F95572A696C80EFCAF_F23AE0988B5AEC53578C63EE6A32AAF8 | binary | |
MD5:— | SHA256:— | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E87CE99F124623F95572A696C80EFCAF_F23AE0988B5AEC53578C63EE6A32AAF8 | der | |
MD5:— | SHA256:— | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\recaptcha__en[1].js | text | |
MD5:— | SHA256:— | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\anchor[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
89
DNS requests
65
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
884 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
884 | svchost.exe | HEAD | 200 | 173.194.183.199:80 | http://r2---sn-aigl6nl7.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.46.147&mm=28&mn=sn-aigl6nl7&ms=nvh&mt=1643064989&mv=m&mvi=2&pl=25&rmhost=r3---sn-aigl6nl7.gvt1.com&shardbypass=yes&smhost=r3---sn-aigl6n76.gvt1.com | US | — | — | whitelisted |
3492 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3492 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3492 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEH4wYrandiOsCgAAAAErgCs%3D | US | der | 471 b | whitelisted |
2540 | chrome.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 593 b | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.186.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 614 b | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.97.71:80 | http://r2---sn-aigzrnld.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.46.147&mm=28&mn=sn-aigzrnld&ms=nvh&mt=1643064748&mv=m&mvi=2&pl=25&rmhost=r3---sn-aigzrnld.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | binary | 5.63 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.97.71:80 | http://r2---sn-aigzrnld.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.46.147&mm=28&mn=sn-aigzrnld&ms=nvh&mt=1643064748&mv=m&mvi=2&pl=25&rmhost=r3---sn-aigzrnld.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | binary | 9.45 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3492 | iexplore.exe | 142.250.186.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3492 | iexplore.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3492 | iexplore.exe | 2.16.106.171:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2540 | chrome.exe | 142.250.185.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2916 | iexplore.exe | 142.250.185.164:443 | www.google.com | Google Inc. | US | whitelisted |
3492 | iexplore.exe | 142.250.186.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2916 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2540 | chrome.exe | 142.250.185.164:443 | www.google.com | Google Inc. | US | whitelisted |
2540 | chrome.exe | 142.250.185.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2540 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |