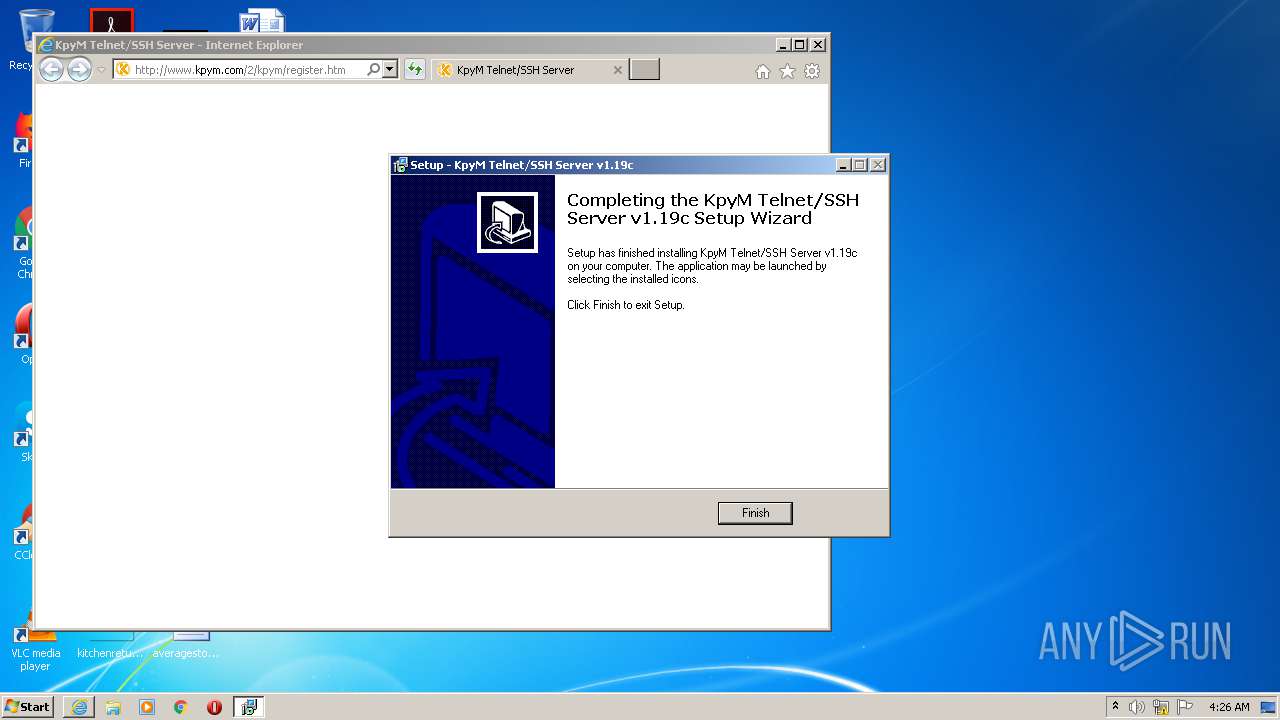
| File name: | kts119c.exe |
| Full analysis: | https://app.any.run/tasks/a0296855-b3f8-4b4b-93aa-e542671d250e |
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2020, 03:25:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 06A9F7C7B9E31994B91EE44A0145A155 |
| SHA1: | 705D8059D0B66C648B3625FF9535E41DA569664E |
| SHA256: | F19F6B2F89448EB497D1BE4C1EA057DC2D23A2516D9E668FB52A6B6AA4F65BE5 |
| SSDEEP: | 49152:v23OPF9QRwFRYXzKIOPF9QRwFQaE+945maV:u3RwDYD3RwuaE+KP |
MALICIOUS
Application was dropped or rewritten from another process
- daemon.exe (PID: 320)
- fixscut.exe (PID: 2384)
- daemon.exe (PID: 2632)
- daemon.exe (PID: 2252)
- daemon.exe (PID: 3832)
Loads dropped or rewritten executable
- daemon.exe (PID: 3832)
- daemon.exe (PID: 2252)
- daemon.exe (PID: 2632)
- daemon.exe (PID: 320)
SUSPICIOUS
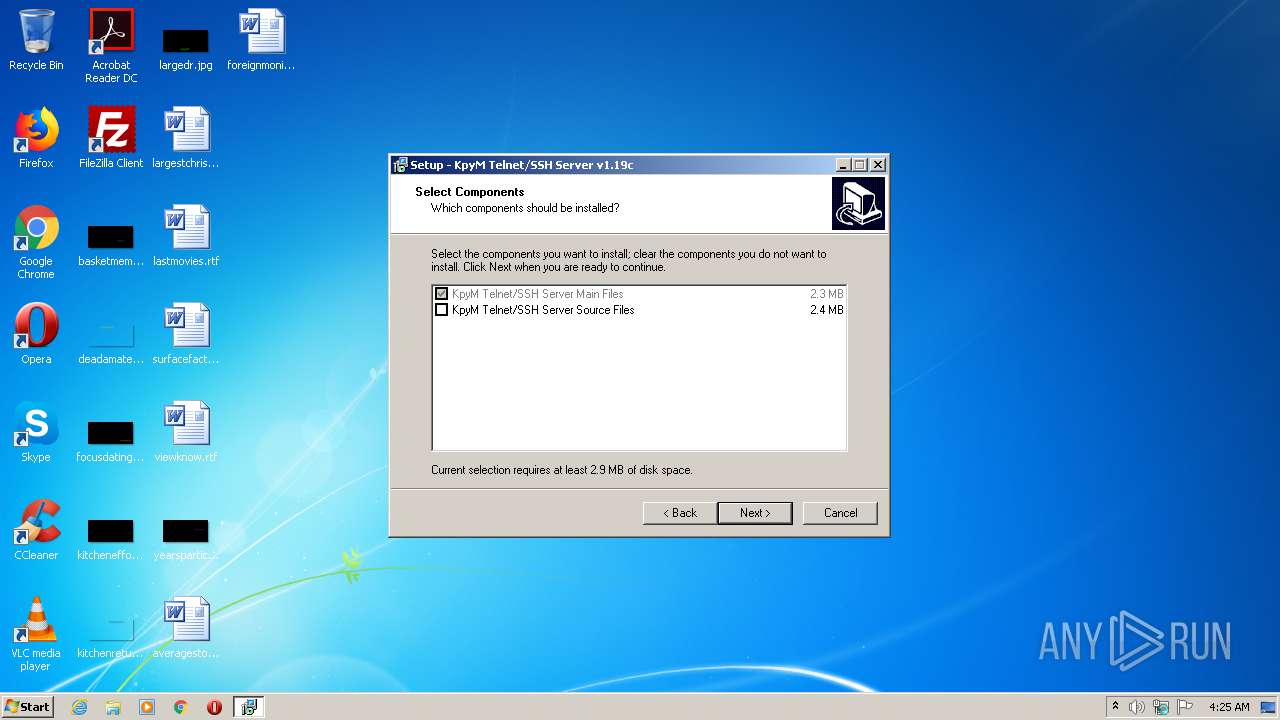
Executable content was dropped or overwritten
- kts119c.exe (PID: 1216)
- kts119c.exe (PID: 620)
- kts119c.tmp (PID: 976)
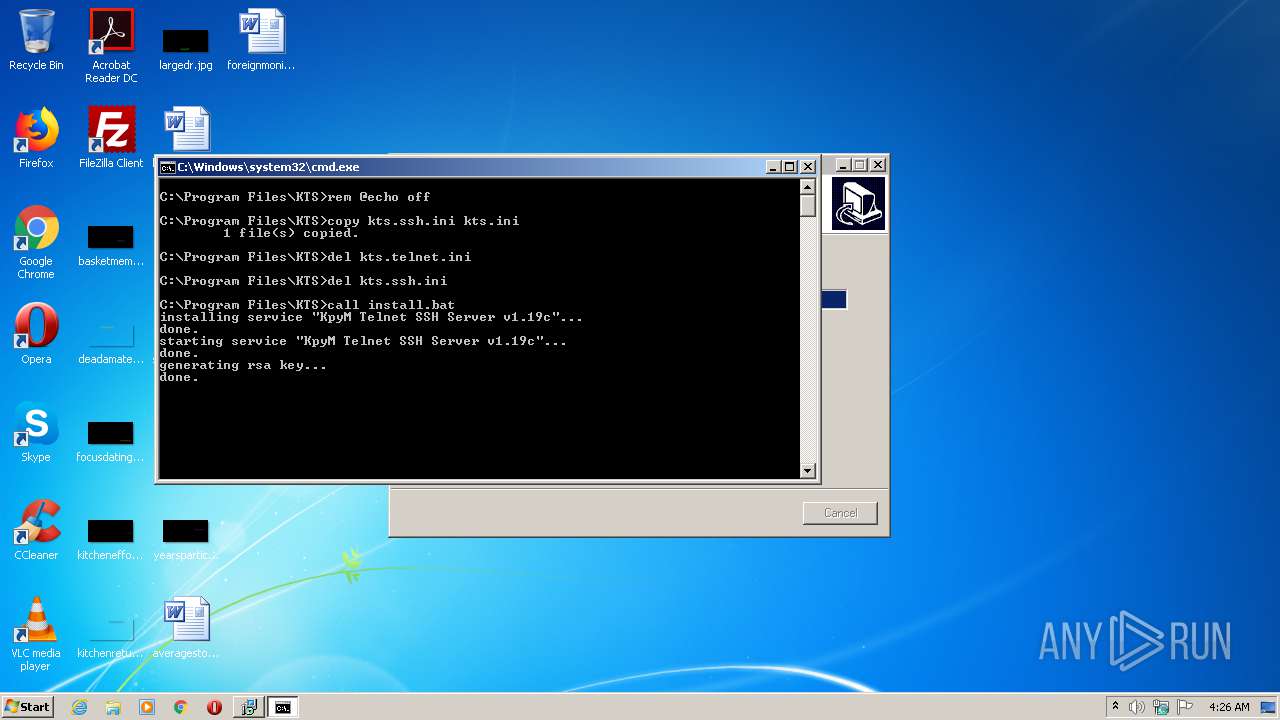
Starts CMD.EXE for commands execution
- kts119c.tmp (PID: 976)
Creates files in the program directory
- cmd.exe (PID: 1688)
- daemon.exe (PID: 320)
- daemon.exe (PID: 2252)
- iexplore.exe (PID: 588)
Executed as Windows Service
- daemon.exe (PID: 320)
Executed via COM
- iexplore.exe (PID: 3988)
INFO
Application was dropped or rewritten from another process
- kts119c.tmp (PID: 976)
- kts119c.tmp (PID: 2644)
Creates a software uninstall entry
- kts119c.tmp (PID: 976)
Loads dropped or rewritten executable
- kts119c.tmp (PID: 976)
Creates files in the program directory
- kts119c.tmp (PID: 976)
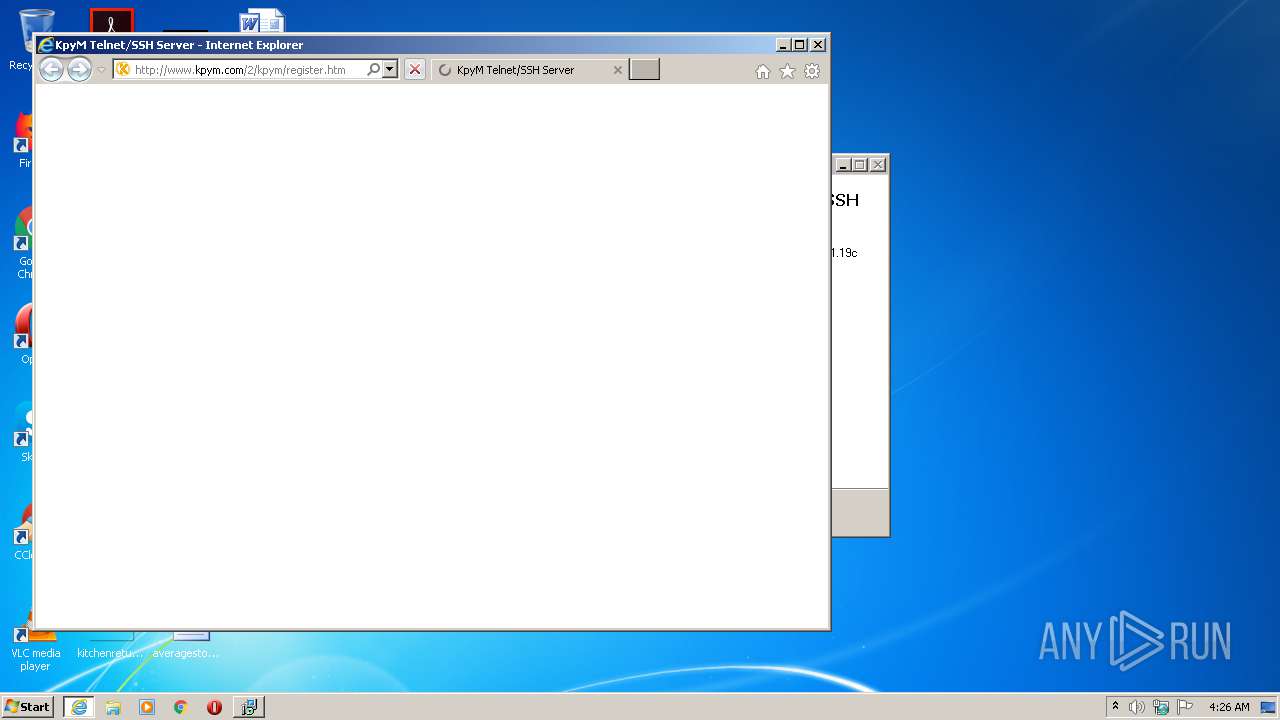
Changes internet zones settings
- iexplore.exe (PID: 3988)
Reads Internet Cache Settings
- iexplore.exe (PID: 588)
- iexplore.exe (PID: 3988)
Reads internet explorer settings
- iexplore.exe (PID: 588)
Creates files in the user directory
- iexplore.exe (PID: 588)
Reads settings of System Certificates
- iexplore.exe (PID: 588)
Changes settings of System certificates
- iexplore.exe (PID: 588)
Adds / modifies Windows certificates
- iexplore.exe (PID: 588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37376 |
| InitializedDataSize: | 17408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9a58 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
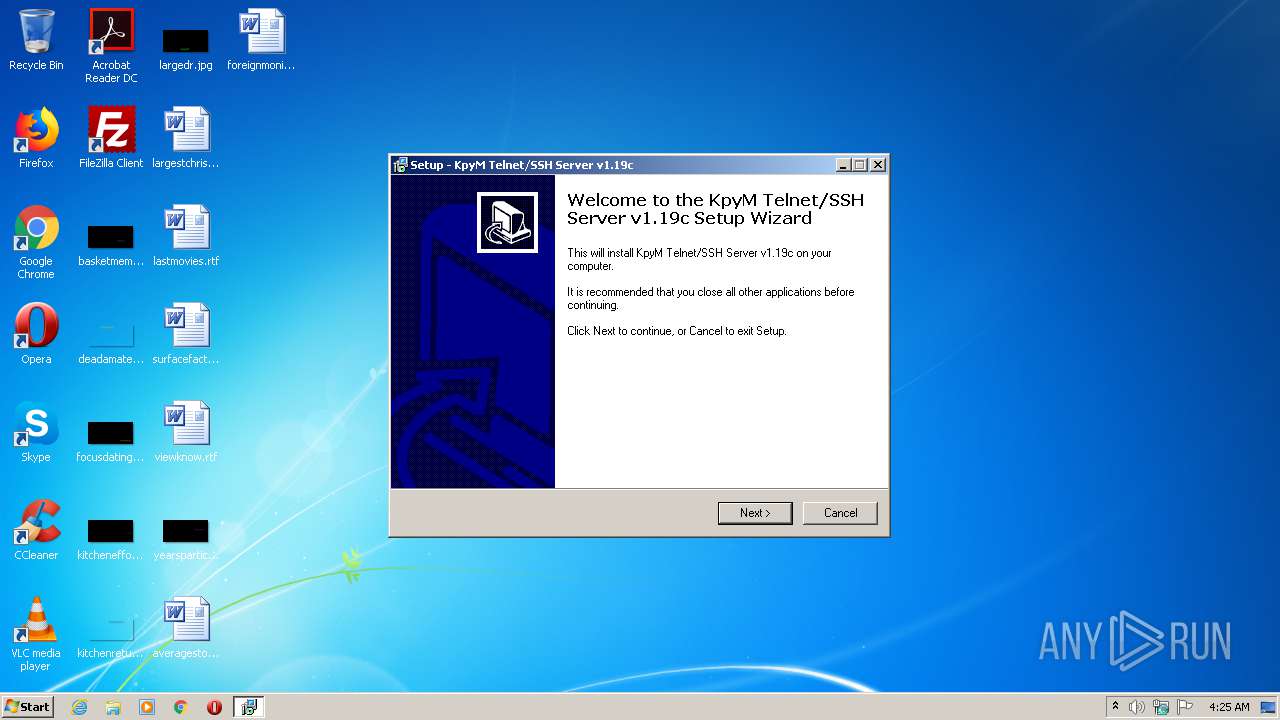
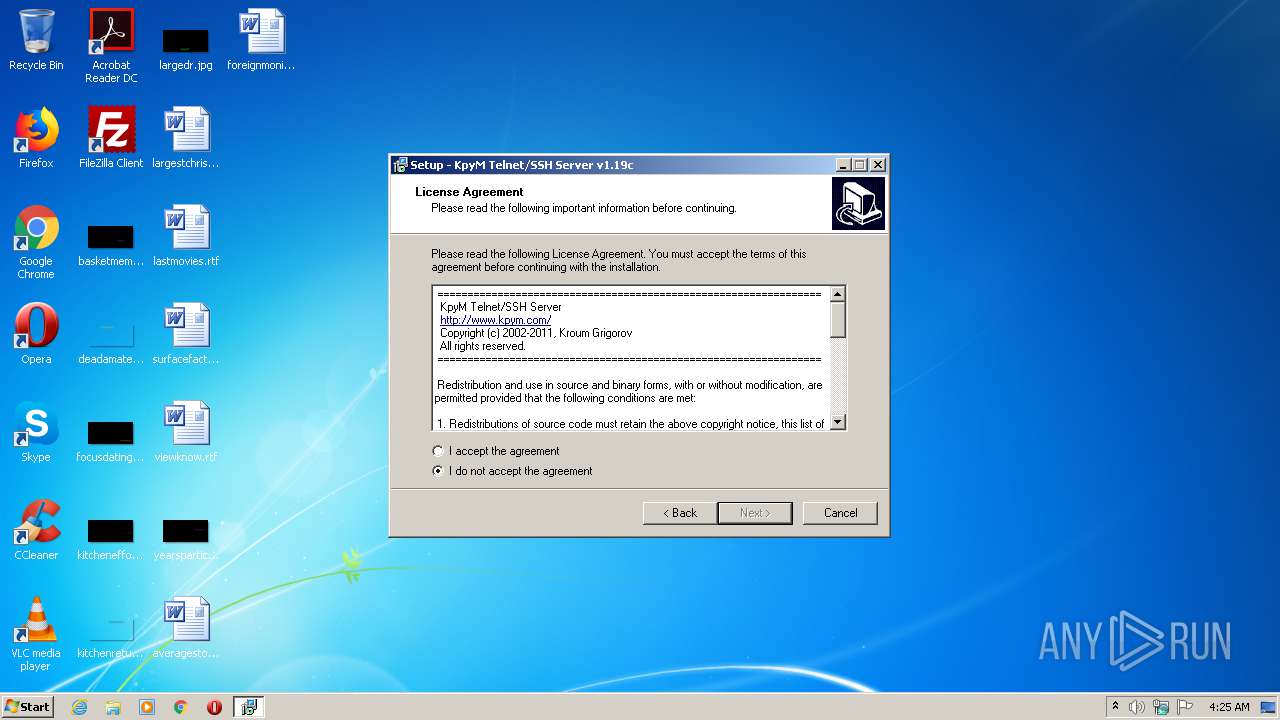
| FileDescription: | KpyM Telnet/SSH Server v1.19c Setup |
| FileVersion: | |
| LegalCopyright: | Copyright (c) 2002-2011 Kroum Grigorov |
| ProductName: | KpyM Telnet/SSH Server v1.19c |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | KpyM Telnet/SSH Server v1.19c Setup |
| FileVersion: | - |
| LegalCopyright: | Copyright (c) 2002-2011 Kroum Grigorov |
| ProductName: | KpyM Telnet/SSH Server v1.19c |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009174 | 0x00009200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56625 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.73508 |
BSS | 0x0000C000 | 0x00000E48 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00002A00 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.50649 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.94378 | 1150 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
51
Monitored processes
13
Malicious processes
0
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\KTS\daemon.exe" | C:\Program Files\KTS\daemon.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Kroum Grigorov Integrity Level: SYSTEM Description: KpyM Telnet/SSH Server - daemon.exe Exit code: 0 Version: 1,19,0,3 Modules
| |||||||||||||||
| 524 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\KTS\fixscut.bat"" | C:\Windows\system32\cmd.exe | — | kts119c.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 588 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3988 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 620 | "C:\Users\admin\AppData\Local\Temp\kts119c.exe" | C:\Users\admin\AppData\Local\Temp\kts119c.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: KpyM Telnet/SSH Server v1.19c Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 976 | "C:\Users\admin\AppData\Local\Temp\is-ETGSK.tmp\kts119c.tmp" /SL5="$30132,1490739,53248,C:\Users\admin\AppData\Local\Temp\kts119c.exe" /SPAWNWND=$50130 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\is-ETGSK.tmp\kts119c.tmp | kts119c.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.49.0.0 Modules
| |||||||||||||||
| 1216 | "C:\Users\admin\AppData\Local\Temp\kts119c.exe" /SPAWNWND=$50130 /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\kts119c.exe | kts119c.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: KpyM Telnet/SSH Server v1.19c Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1688 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\KTS\install.once.bat" ssh" | C:\Windows\system32\cmd.exe | — | kts119c.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2252 | daemon.exe -rsakey | C:\Program Files\KTS\daemon.exe | — | cmd.exe | |||||||||||
User: admin Company: Kroum Grigorov Integrity Level: HIGH Description: KpyM Telnet/SSH Server - daemon.exe Exit code: 0 Version: 1,19,0,3 Modules
| |||||||||||||||
| 2384 | fixscut.exe | C:\Program Files\KTS\fixscut.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2632 | daemon.exe -install | C:\Program Files\KTS\daemon.exe | — | cmd.exe | |||||||||||
User: admin Company: Kroum Grigorov Integrity Level: HIGH Description: KpyM Telnet/SSH Server - daemon.exe Exit code: 0 Version: 1,19,0,3 Modules
| |||||||||||||||
Total events
3 187
Read events
1 475
Write events
1 712
Delete events
0
Modification events
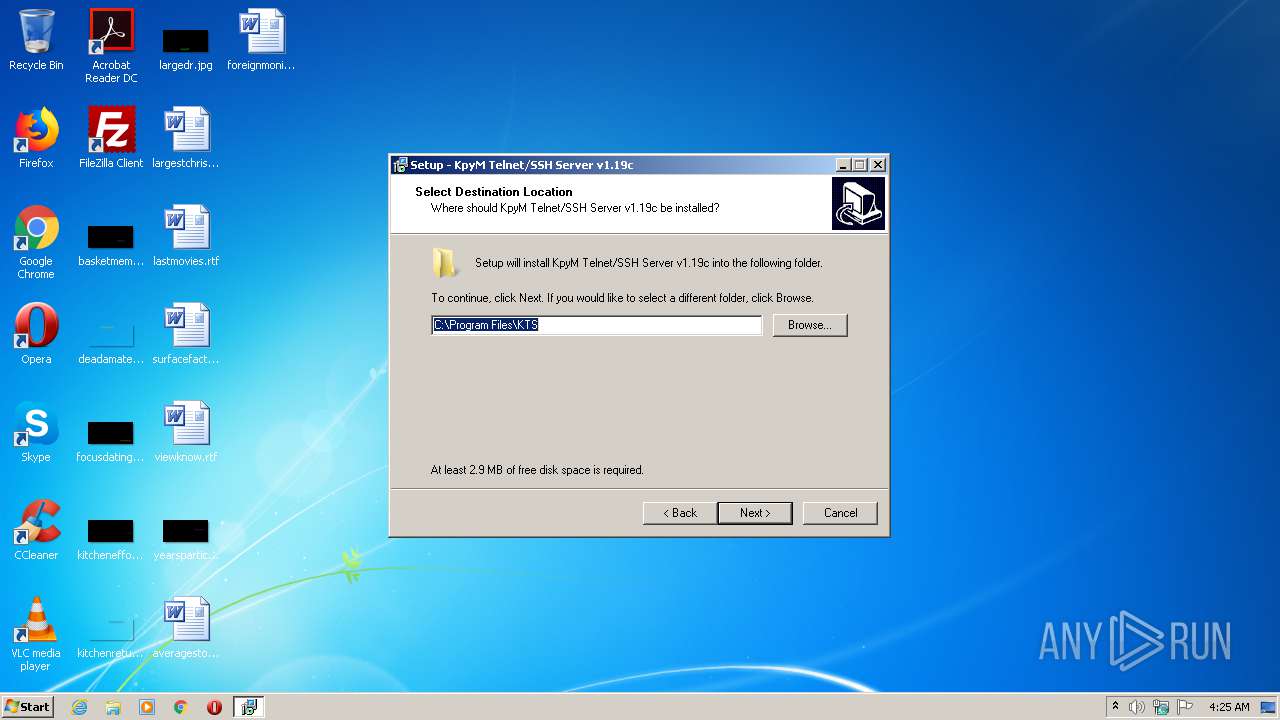
| (PID) Process: | (976) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.2.3 | |||
| (PID) Process: | (976) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\KTS | |||
| (PID) Process: | (976) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\KTS\ | |||
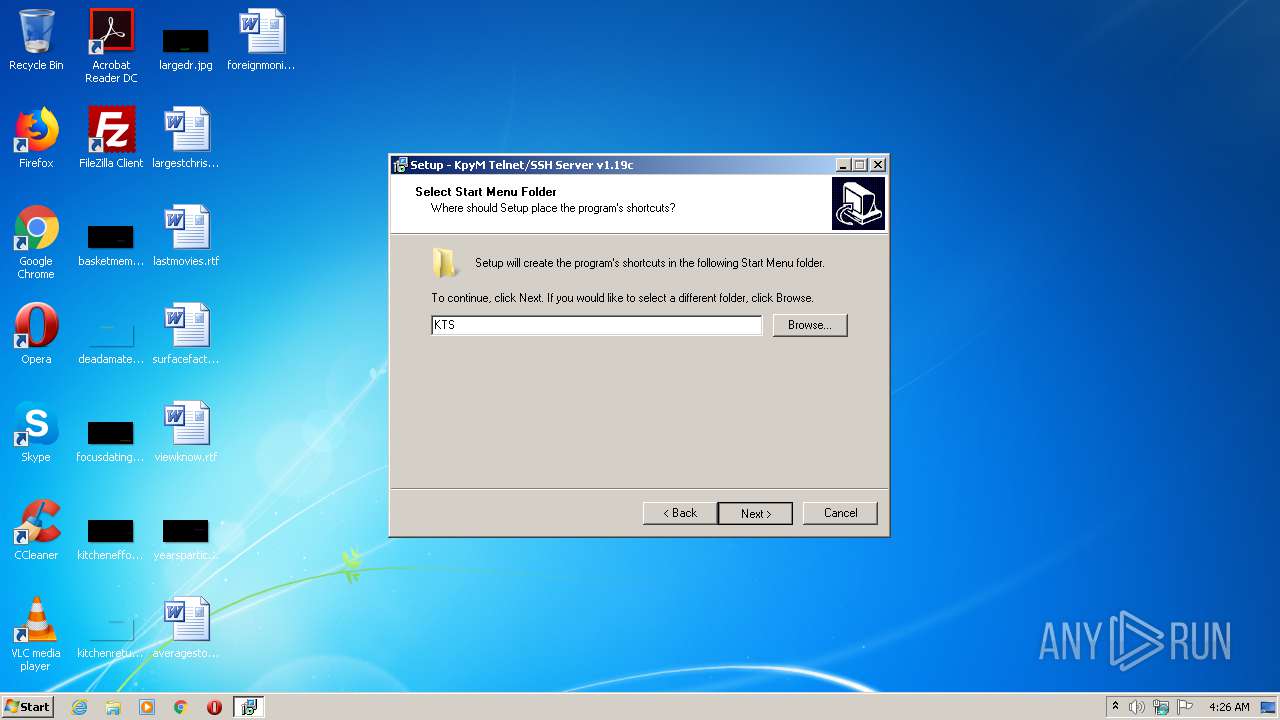
| (PID) Process: | (976) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: KTS | |||
| (PID) Process: | (976) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (976) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | Inno Setup: Setup Type |
Value: main | |||
| (PID) Process: | (976) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | Inno Setup: Selected Components |
Value: main,source | |||
| (PID) Process: | (976) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Components |
Value: | |||
| (PID) Process: | (976) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | DisplayName |
Value: KpyM Telnet/SSH Server v1.19c | |||
| (PID) Process: | (976) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\KTS\unins000.exe" | |||
Executable files
11
Suspicious files
20
Text files
112
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 976 | kts119c.tmp | C:\Program Files\KTS\is-NTFI4.tmp | — | |
MD5:— | SHA256:— | |||
| 976 | kts119c.tmp | C:\Program Files\KTS\is-H8784.tmp | — | |
MD5:— | SHA256:— | |||
| 976 | kts119c.tmp | C:\Program Files\KTS\is-MENKB.tmp | — | |
MD5:— | SHA256:— | |||
| 976 | kts119c.tmp | C:\Program Files\KTS\is-D9J8J.tmp | — | |
MD5:— | SHA256:— | |||
| 976 | kts119c.tmp | C:\Program Files\KTS\is-4IM25.tmp | — | |
MD5:— | SHA256:— | |||
| 976 | kts119c.tmp | C:\Program Files\KTS\is-3A776.tmp | — | |
MD5:— | SHA256:— | |||
| 976 | kts119c.tmp | C:\Program Files\KTS\is-CVKQM.tmp | — | |
MD5:— | SHA256:— | |||
| 976 | kts119c.tmp | C:\Program Files\KTS\is-3BNVE.tmp | — | |
MD5:— | SHA256:— | |||
| 976 | kts119c.tmp | C:\Program Files\KTS\is-7OB7A.tmp | — | |
MD5:— | SHA256:— | |||
| 976 | kts119c.tmp | C:\Program Files\KTS\is-S04VV.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
27
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
588 | iexplore.exe | GET | 200 | 193.107.69.123:80 | http://www.kpym.com/favicon.ico | BG | image | 1.37 Kb | suspicious |
588 | iexplore.exe | GET | 200 | 193.107.69.123:80 | http://www.kpym.com/2/kpym/kpym.css | BG | text | 91 b | suspicious |
588 | iexplore.exe | GET | 200 | 193.107.69.123:80 | http://www.kpym.com/2/kpym/register.htm | BG | html | 3.54 Kb | suspicious |
588 | iexplore.exe | GET | 302 | 172.217.16.196:80 | http://www.google.com/coop/cse/brand?form=cse-search-box&lang=en | US | html | 266 b | malicious |
588 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
588 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
588 | iexplore.exe | GET | 200 | 193.107.69.123:80 | http://www.kpym.com/2/shared/bg_mid.gif | BG | image | 196 b | suspicious |
588 | iexplore.exe | GET | 200 | 172.217.16.130:80 | http://pagead2.googlesyndication.com/pagead/show_ads.js | US | text | 29.6 Kb | whitelisted |
588 | iexplore.exe | GET | 200 | 193.107.69.123:80 | http://www.kpym.com/2/shared/logo_kpym.gif | BG | image | 8.44 Kb | suspicious |
588 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEB74UHKEp3vsAgAAAABqDTk%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
588 | iexplore.exe | 216.58.208.46:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
588 | iexplore.exe | 172.217.16.196:80 | www.google.com | Google Inc. | US | whitelisted |
588 | iexplore.exe | 193.107.69.123:80 | www.kpym.com | SuperHosting.BG Ltd. | BG | suspicious |
3988 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
588 | iexplore.exe | 172.217.16.130:80 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
588 | iexplore.exe | 216.58.207.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
588 | iexplore.exe | 172.217.16.130:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
588 | iexplore.exe | 172.217.16.162:443 | adservice.google.it | Google Inc. | US | whitelisted |
588 | iexplore.exe | 216.58.205.238:443 | cse.google.com | Google Inc. | US | whitelisted |
588 | iexplore.exe | 172.217.22.66:443 | adservice.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kpym.com |
| suspicious |
www.google-analytics.com |
| whitelisted |
www.google.com |
| malicious |
pagead2.googlesyndication.com |
| whitelisted |
cse.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
adservice.google.it |
| whitelisted |
adservice.google.com |
| whitelisted |