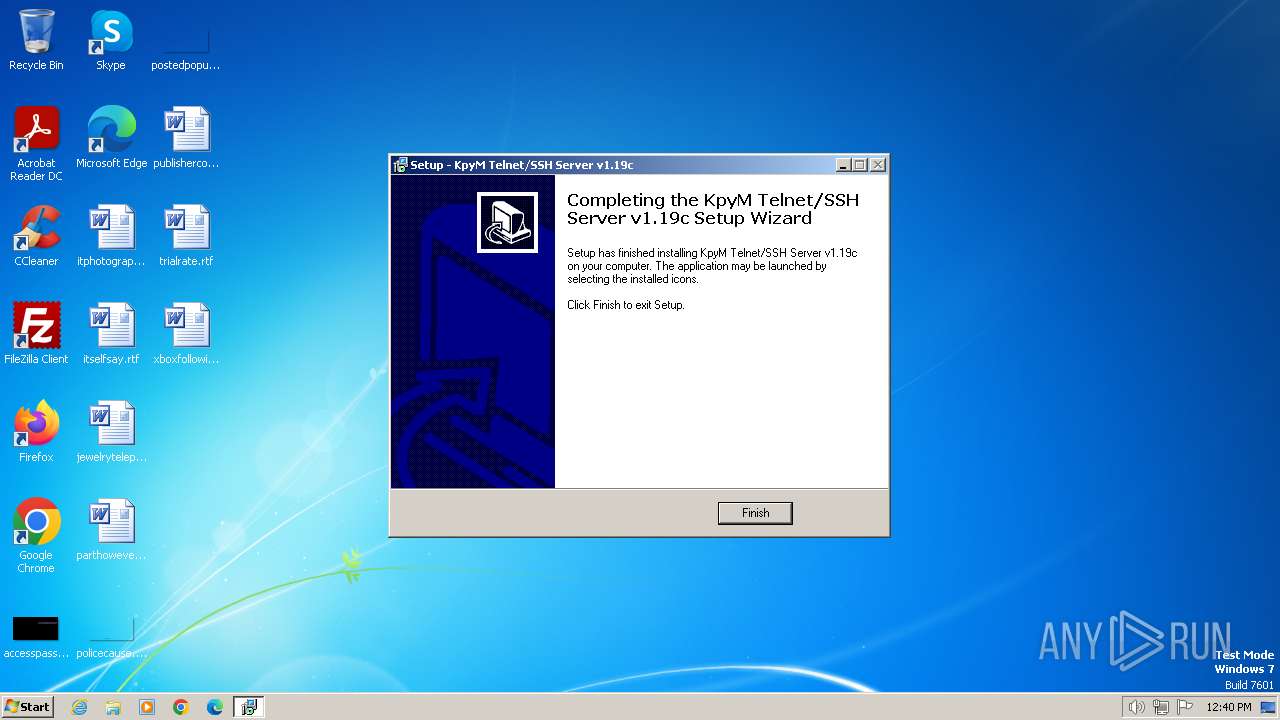
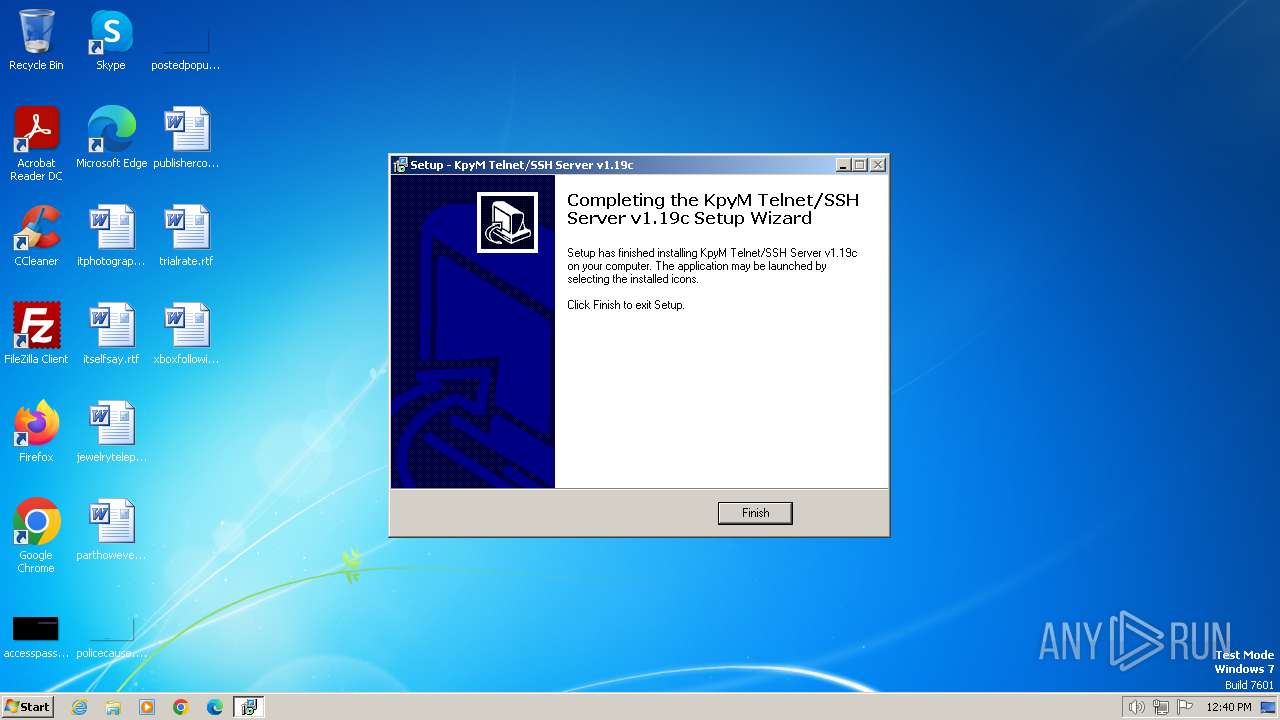
| File name: | kts119c.exe |
| Full analysis: | https://app.any.run/tasks/3285036e-0d62-4967-a73e-d89a471e0371 |
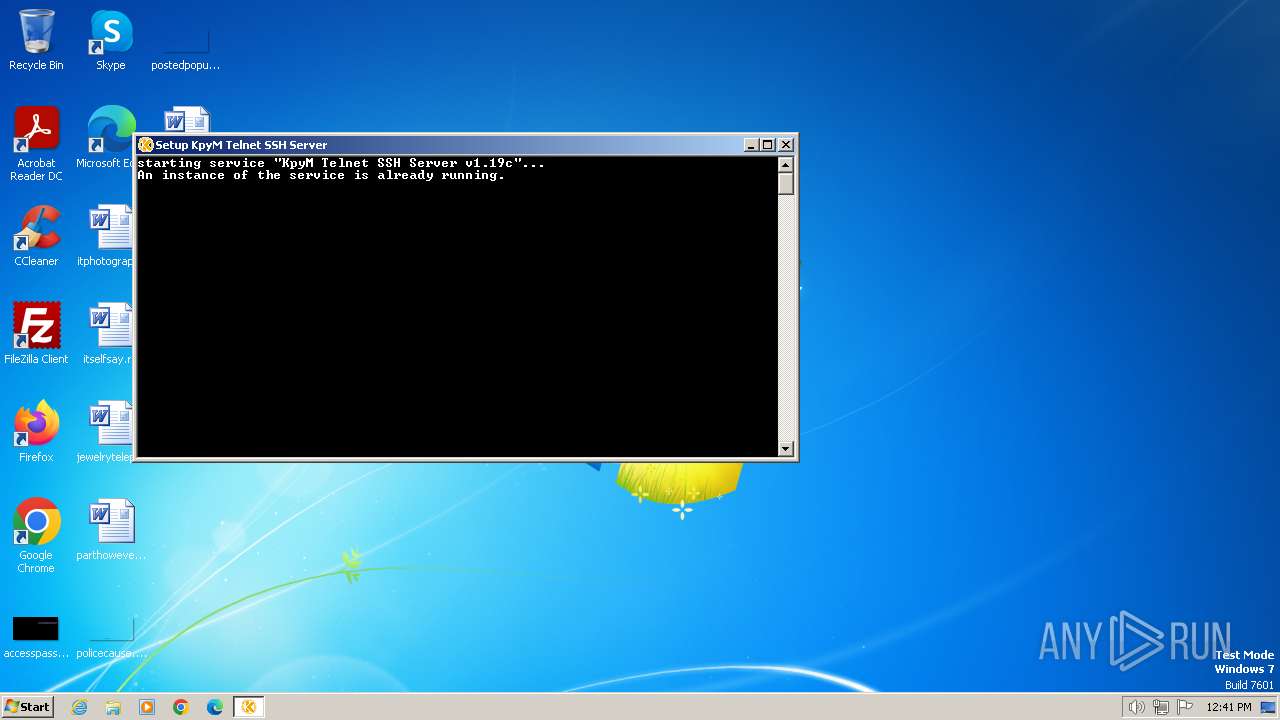
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2024, 12:39:31 |
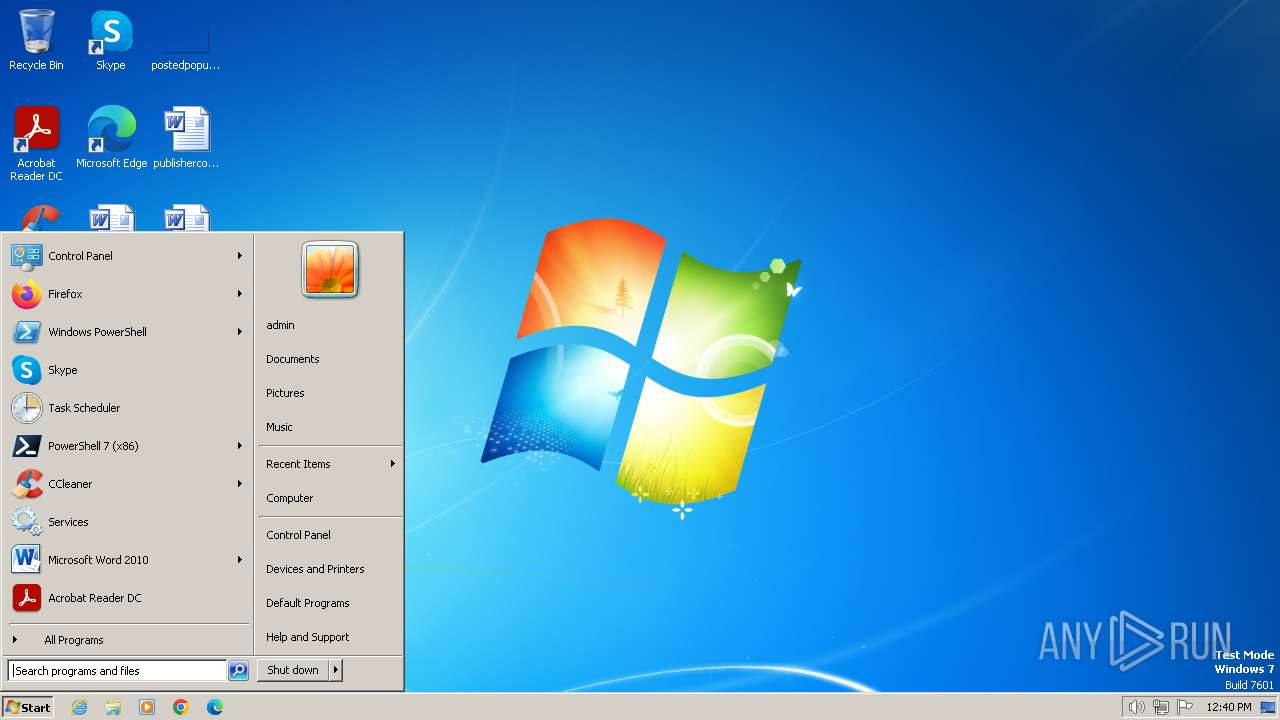
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 06A9F7C7B9E31994B91EE44A0145A155 |
| SHA1: | 705D8059D0B66C648B3625FF9535E41DA569664E |
| SHA256: | F19F6B2F89448EB497D1BE4C1EA057DC2D23A2516D9E668FB52A6B6AA4F65BE5 |
| SSDEEP: | 49152:v23OPF9QRwFRYXzKIOPF9QRwFQaE+945maV:u3RwDYD3RwuaE+KP |
MALICIOUS
Drops the executable file immediately after the start
- kts119c.exe (PID: 2472)
- kts119c.exe (PID: 1776)
- kts119c.tmp (PID: 2964)
SUSPICIOUS
Executable content was dropped or overwritten
- kts119c.exe (PID: 2472)
- kts119c.exe (PID: 1776)
- kts119c.tmp (PID: 2964)
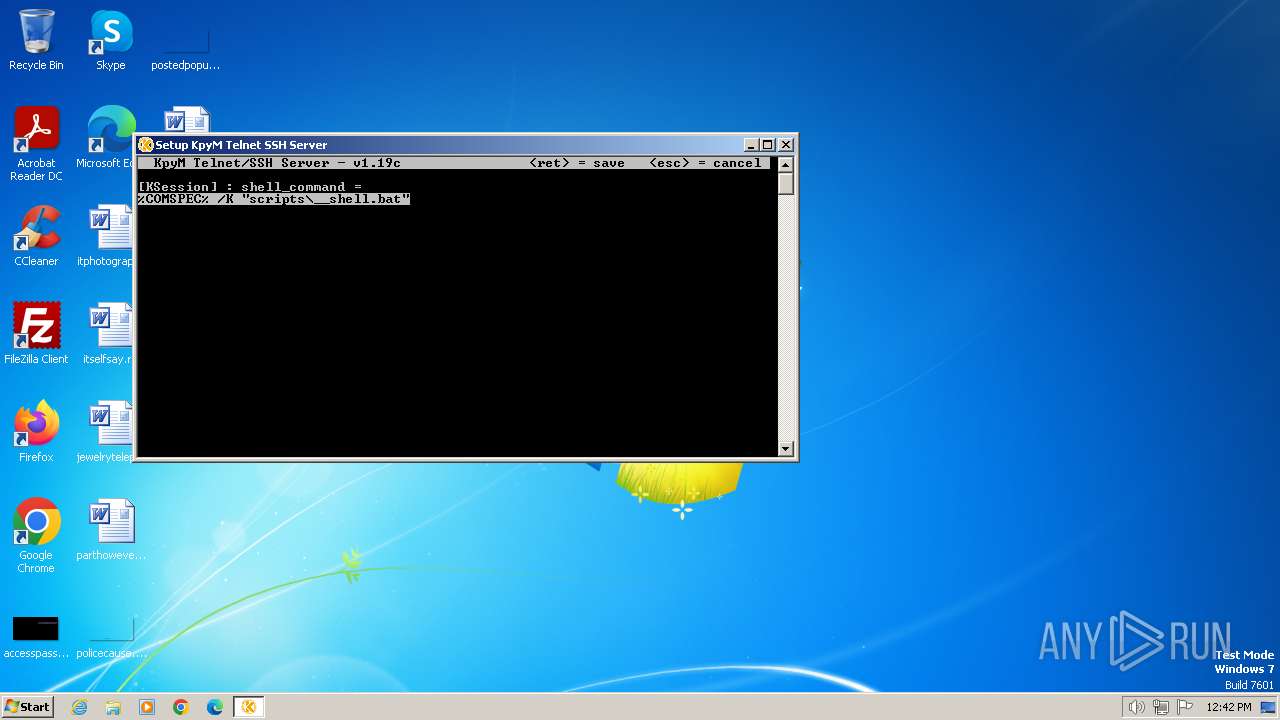
Starts CMD.EXE for commands execution
- kts119c.tmp (PID: 2964)
- daemon.exe (PID: 748)
Reads the Windows owner or organization settings
- kts119c.tmp (PID: 2964)
Executing commands from a ".bat" file
- kts119c.tmp (PID: 2964)
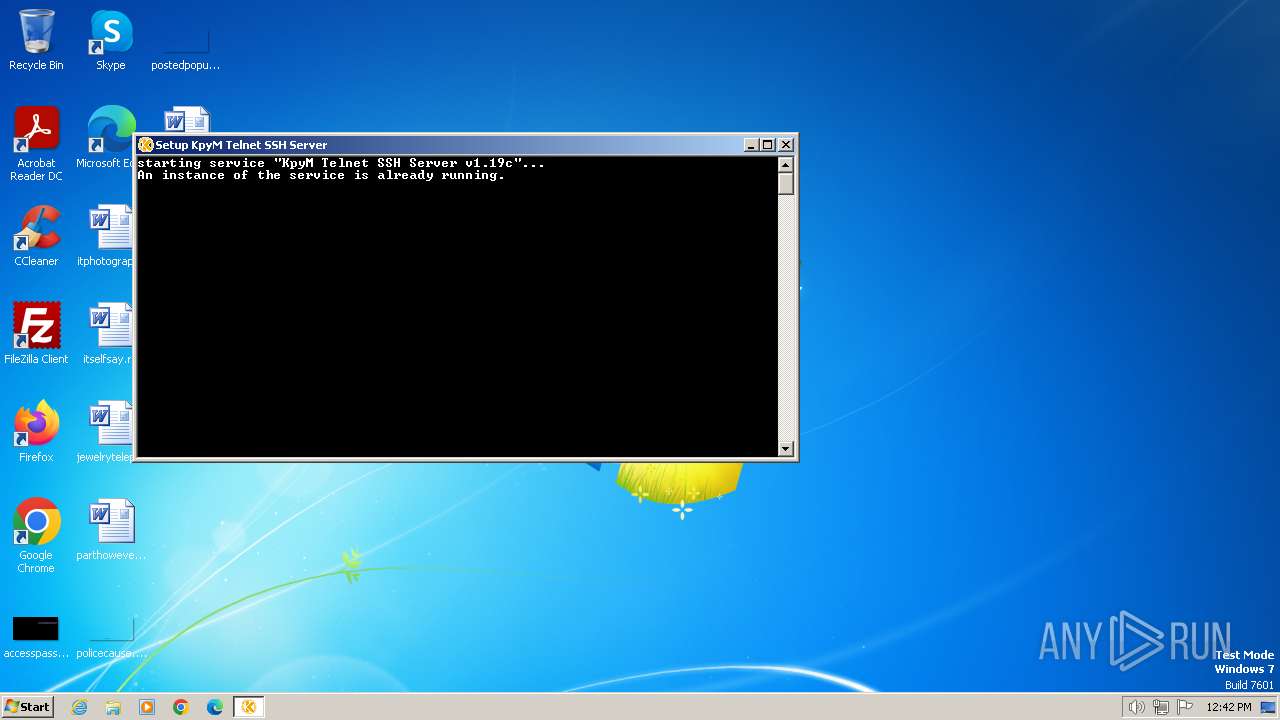
Executes as Windows Service
- daemon.exe (PID: 3092)
Reads the Internet Settings
- cmd.exe (PID: 4008)
Process drops legitimate windows executable
- kts119c.tmp (PID: 2964)
INFO
Checks supported languages
- kts119c.tmp (PID: 3672)
- kts119c.exe (PID: 2472)
- kts119c.exe (PID: 1776)
- fixscut.exe (PID: 864)
- daemon.exe (PID: 3092)
- daemon.exe (PID: 3960)
- daemon.exe (PID: 2580)
- daemon.exe (PID: 2232)
- daemon.exe (PID: 748)
- kts119c.tmp (PID: 2964)
Reads the computer name
- kts119c.tmp (PID: 3672)
- daemon.exe (PID: 3092)
- daemon.exe (PID: 3960)
- daemon.exe (PID: 2580)
- fixscut.exe (PID: 864)
- daemon.exe (PID: 2232)
- daemon.exe (PID: 748)
- kts119c.tmp (PID: 2964)
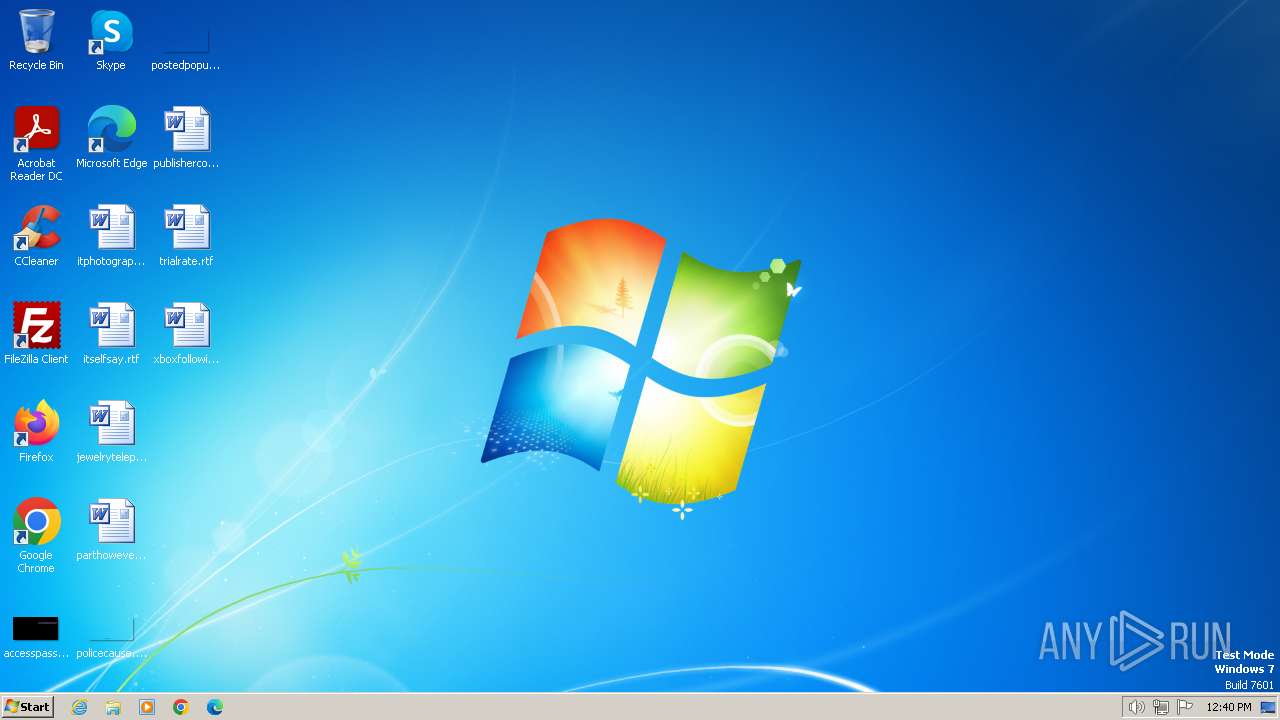
Create files in a temporary directory
- kts119c.exe (PID: 2472)
- kts119c.exe (PID: 1776)
- kts119c.tmp (PID: 2964)
Creates files in the program directory
- cmd.exe (PID: 4008)
- daemon.exe (PID: 3092)
- daemon.exe (PID: 748)
- daemon.exe (PID: 3960)
- kts119c.tmp (PID: 2964)
Creates a software uninstall entry
- kts119c.tmp (PID: 2964)
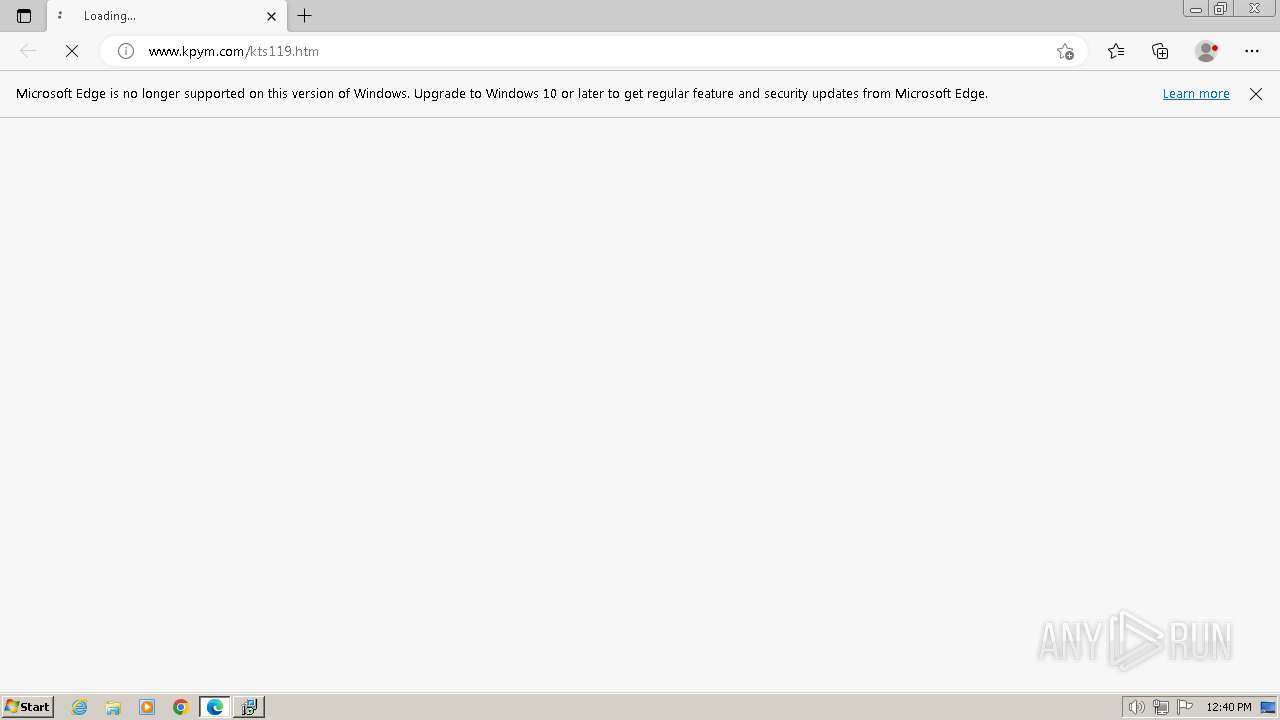
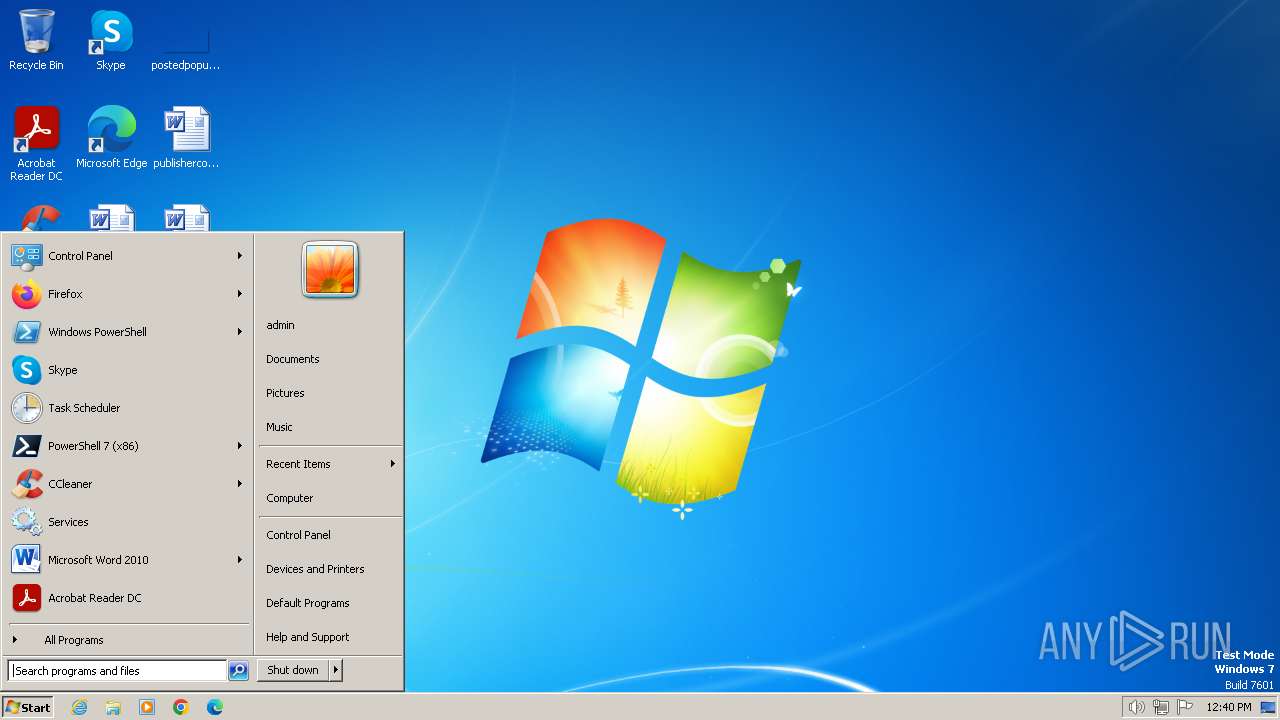
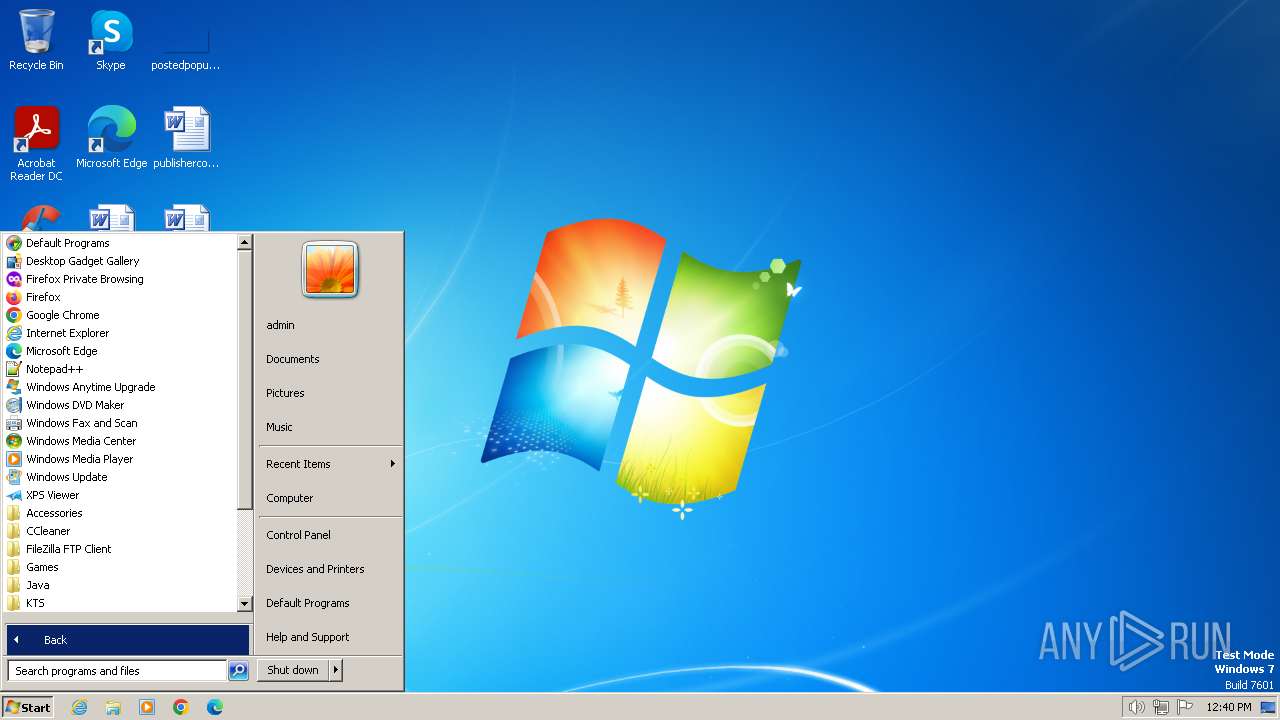
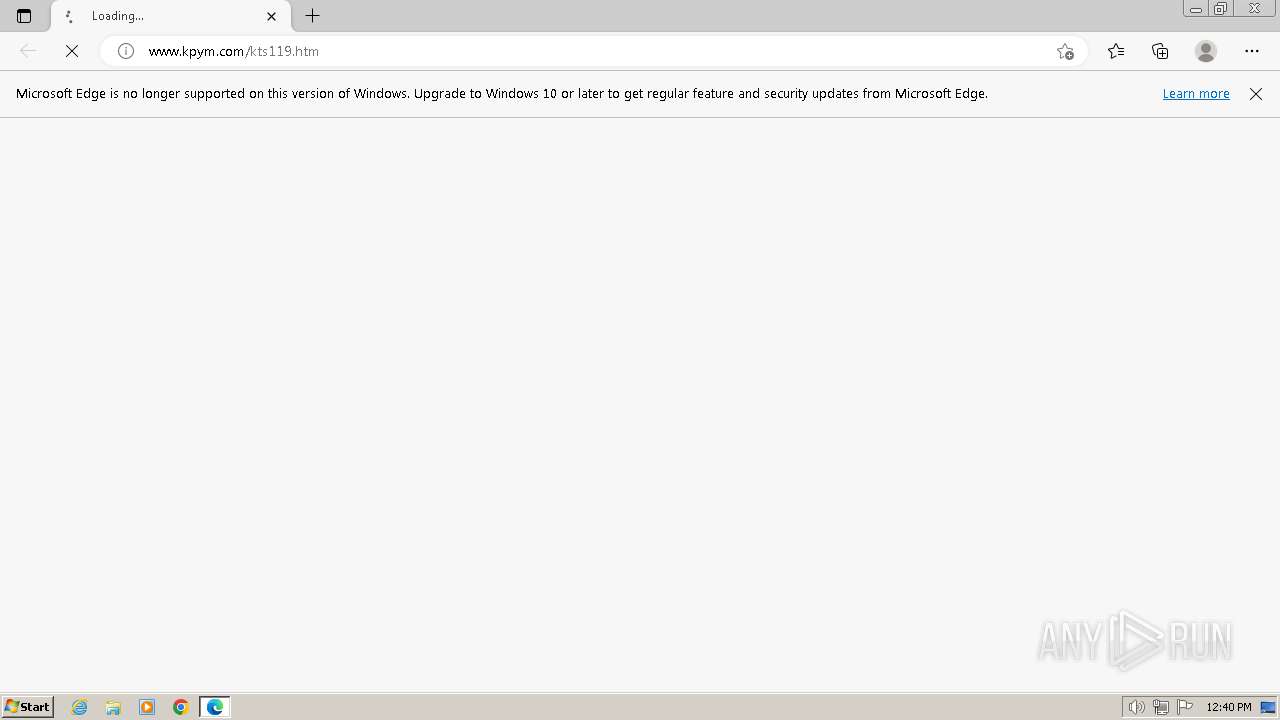
Manual execution by a user
- msedge.exe (PID: 2432)
- msedge.exe (PID: 3440)
- daemon.exe (PID: 2072)
- daemon.exe (PID: 748)
Application launched itself
- msedge.exe (PID: 2432)
- msedge.exe (PID: 2420)
- msedge.exe (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37376 |
| InitializedDataSize: | 17408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9a58 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
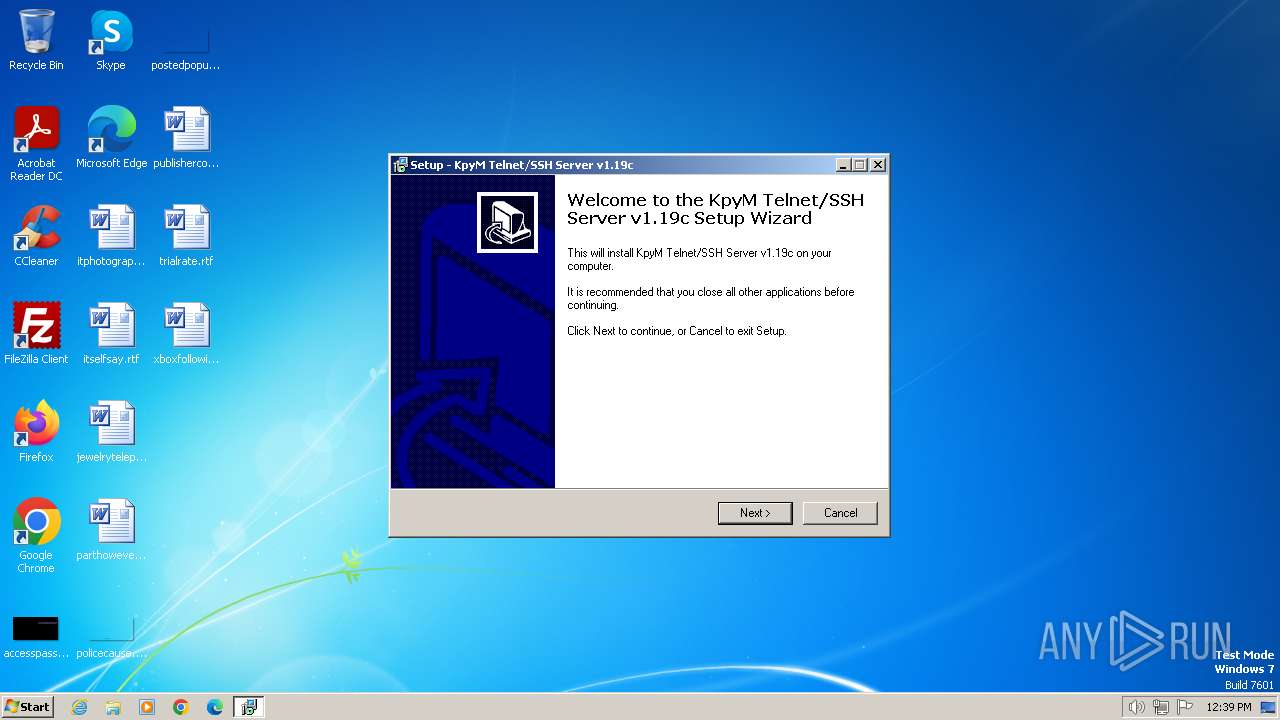
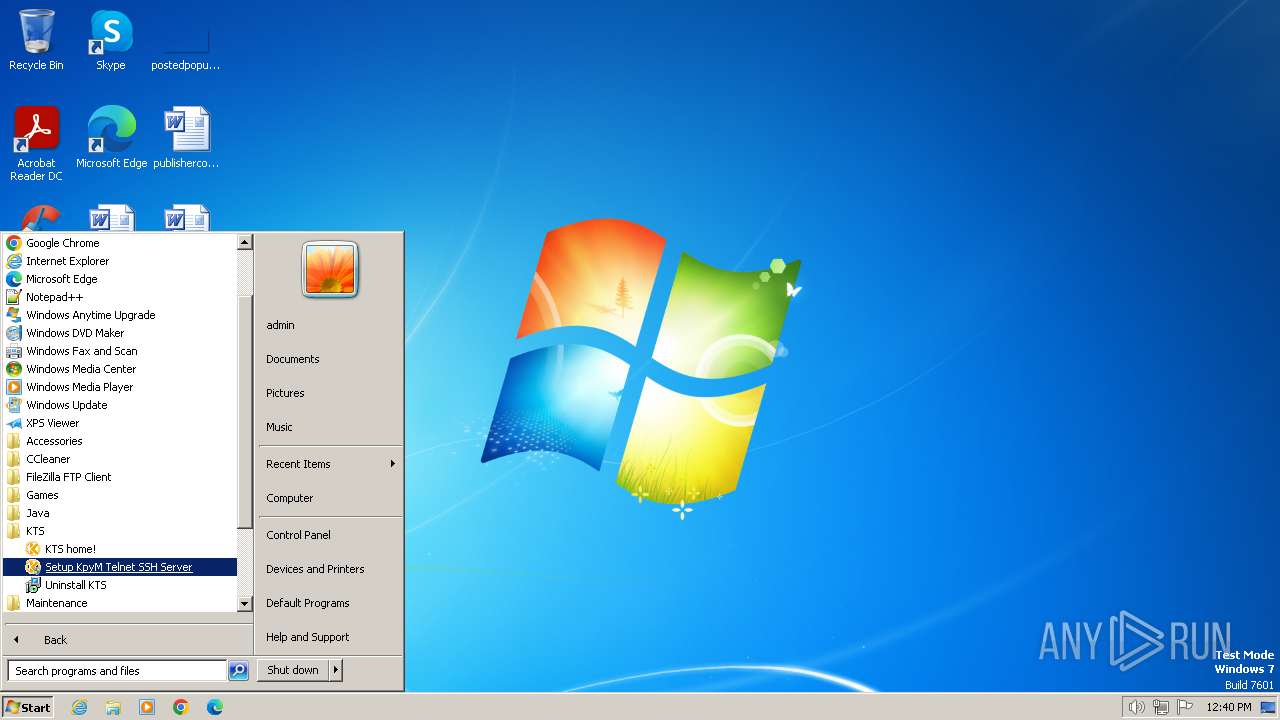
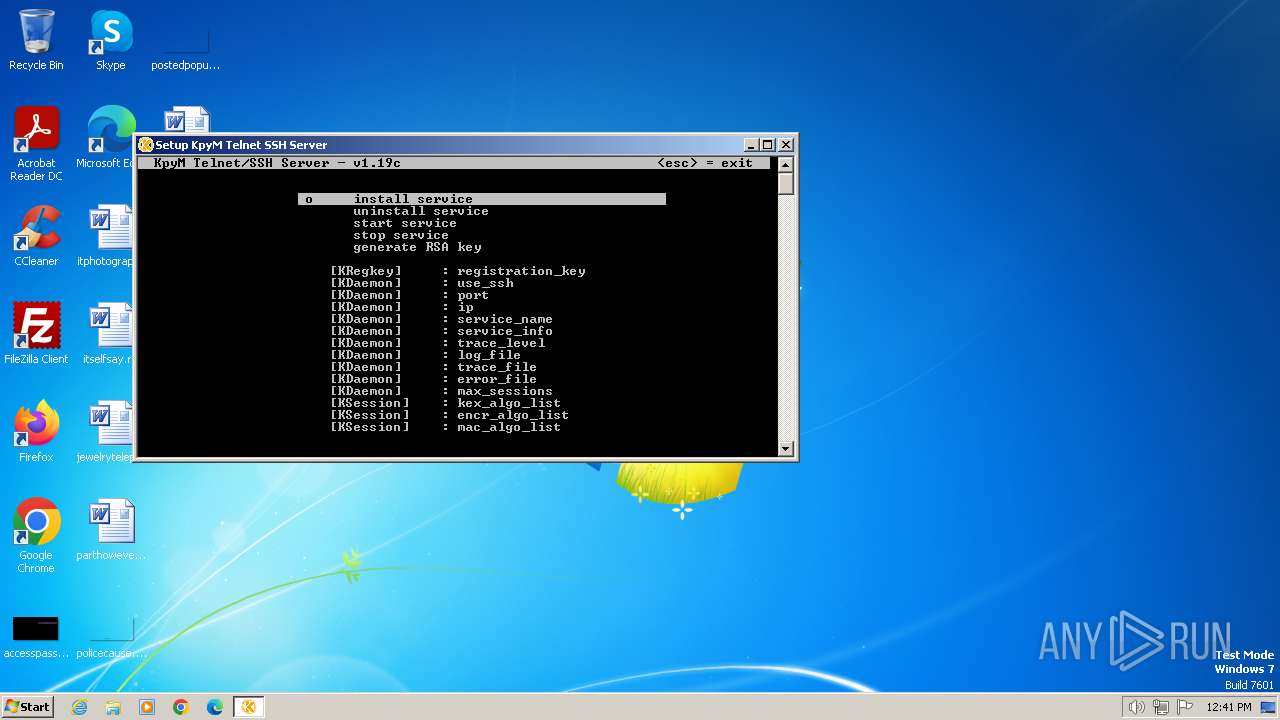
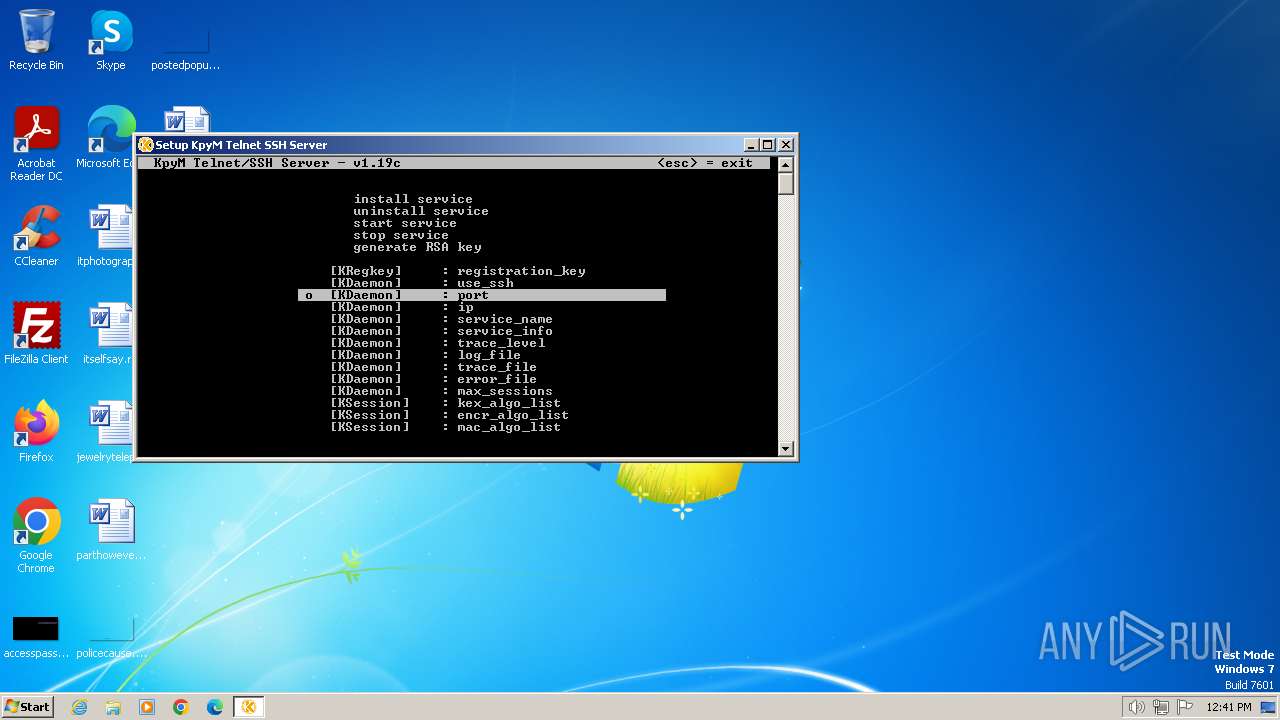
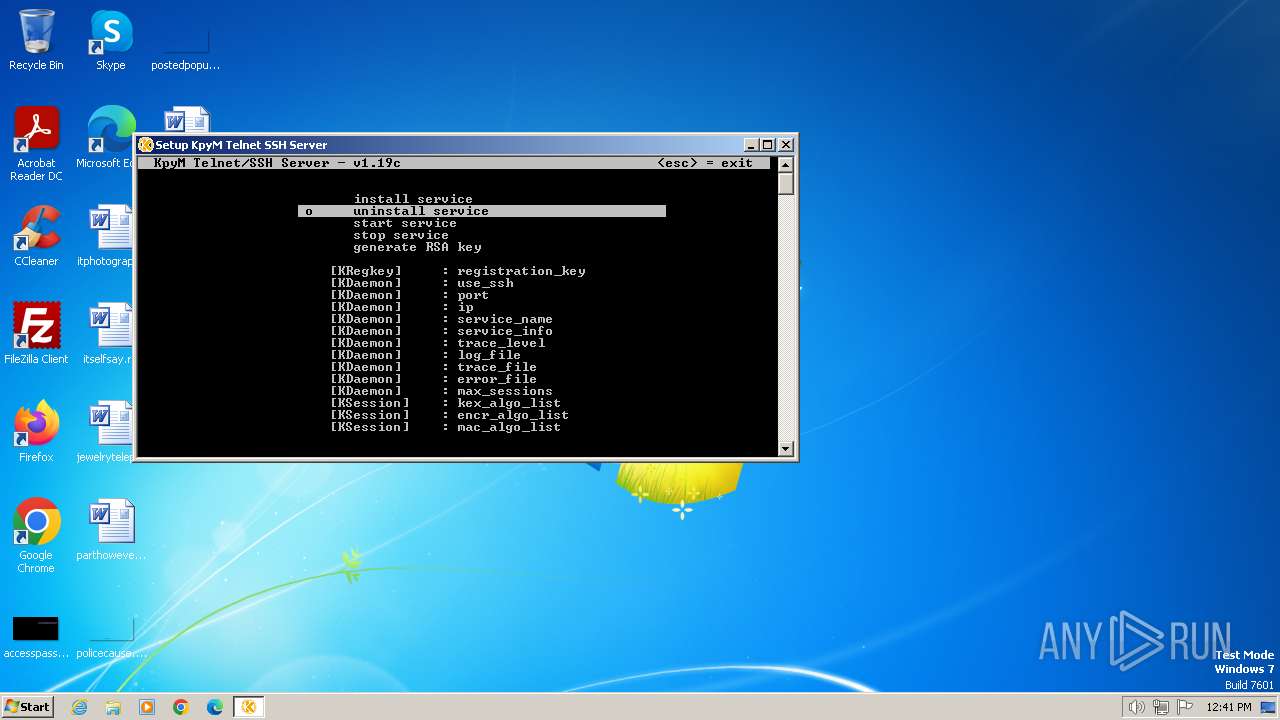
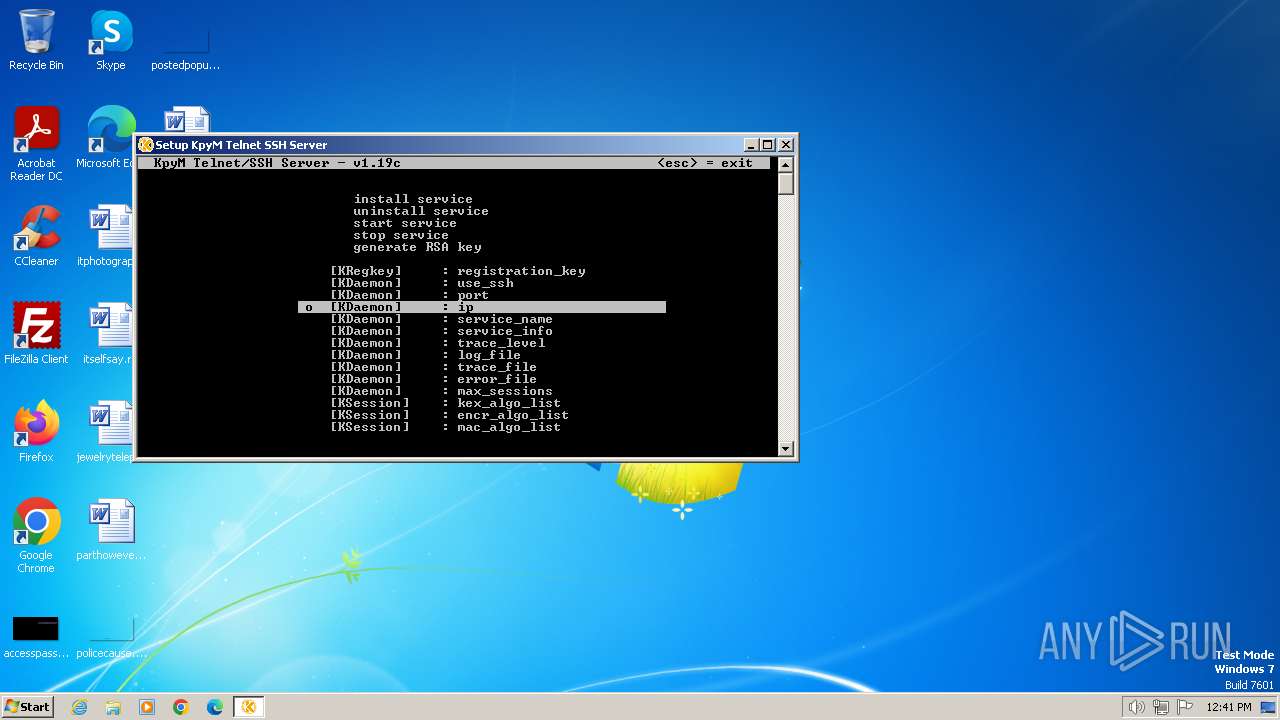
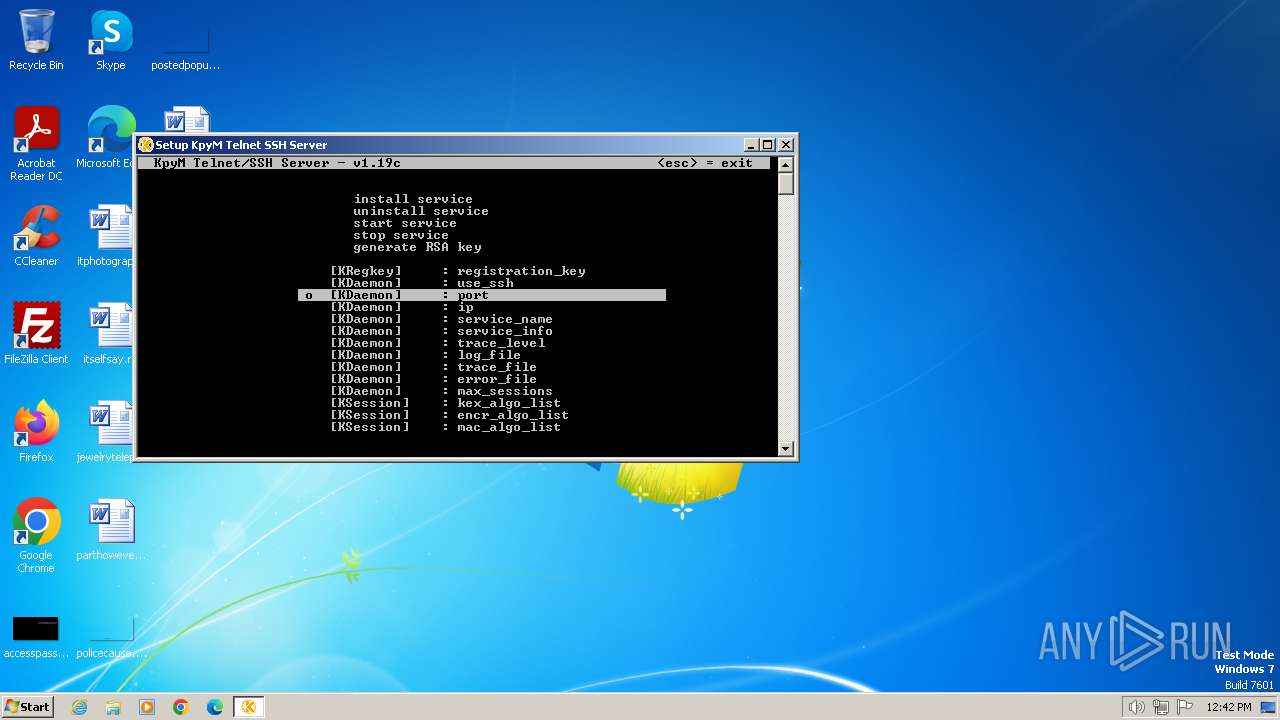
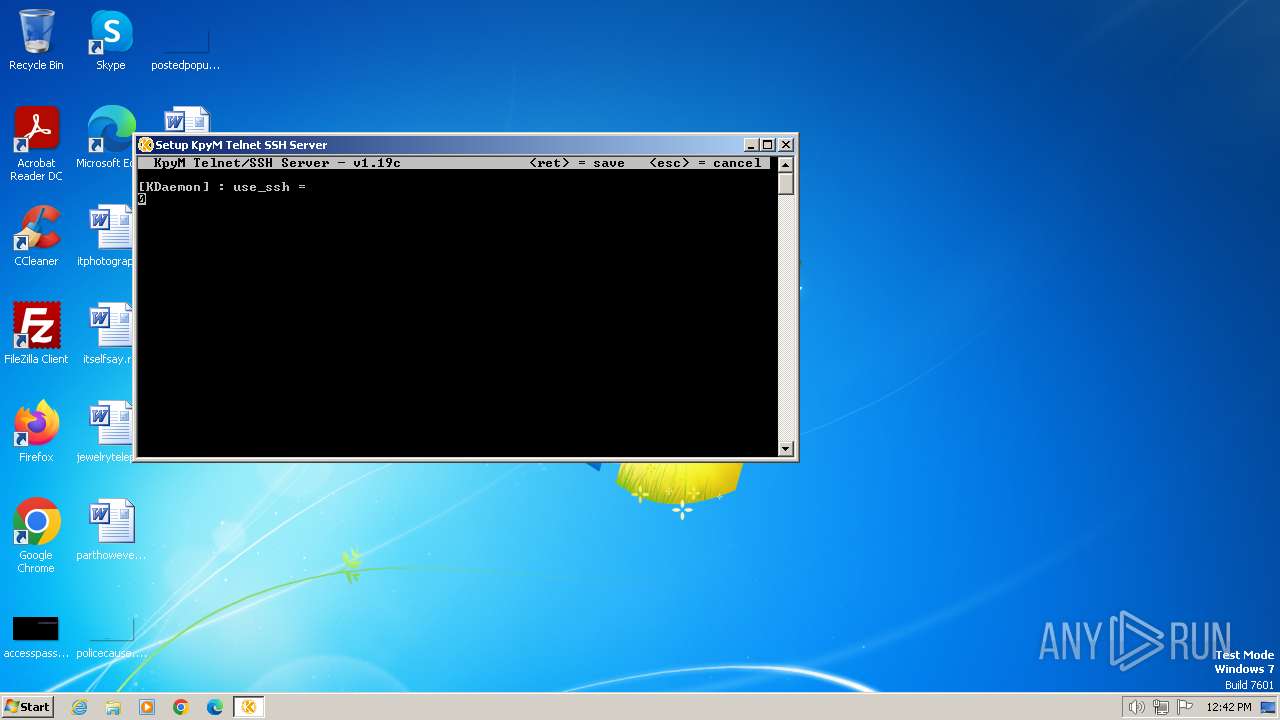
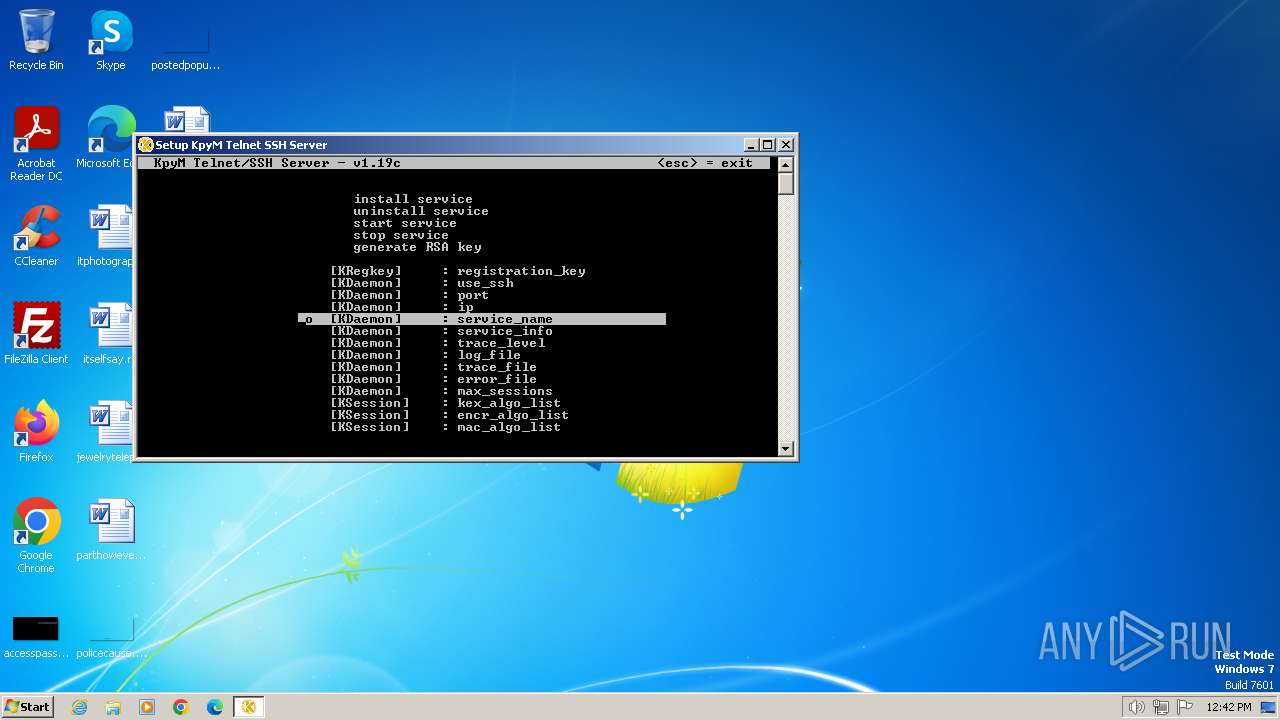
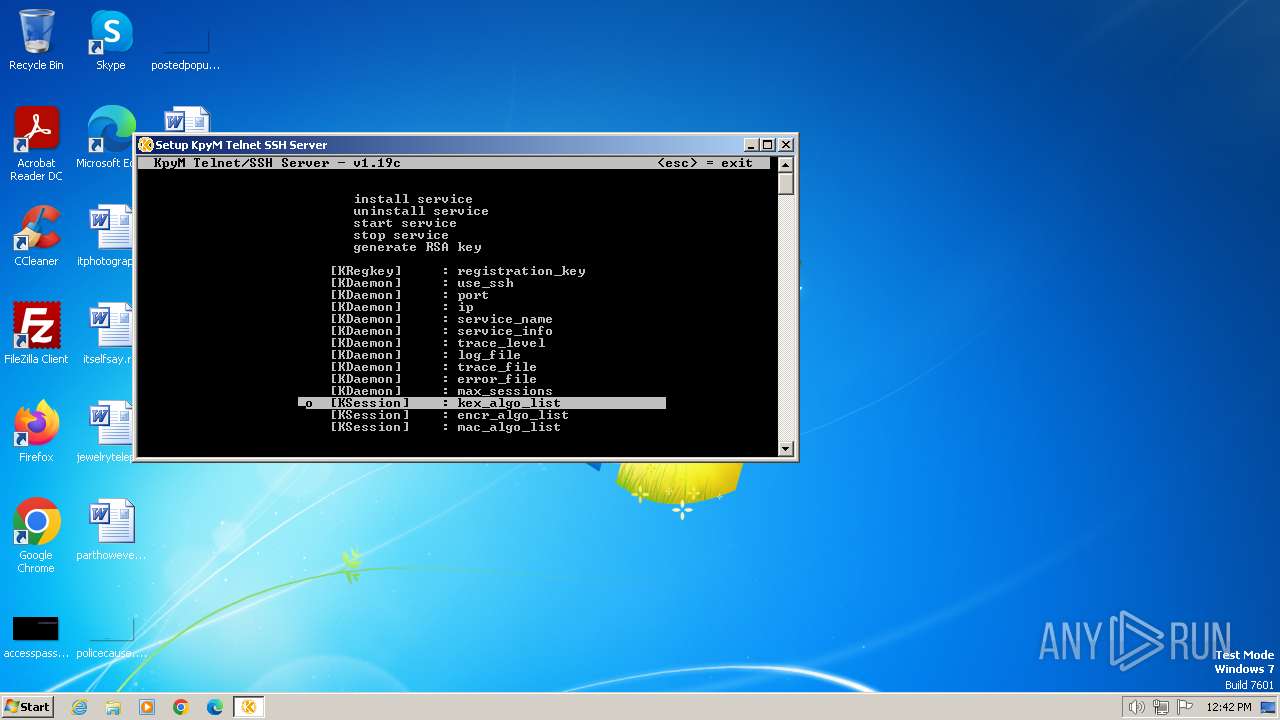
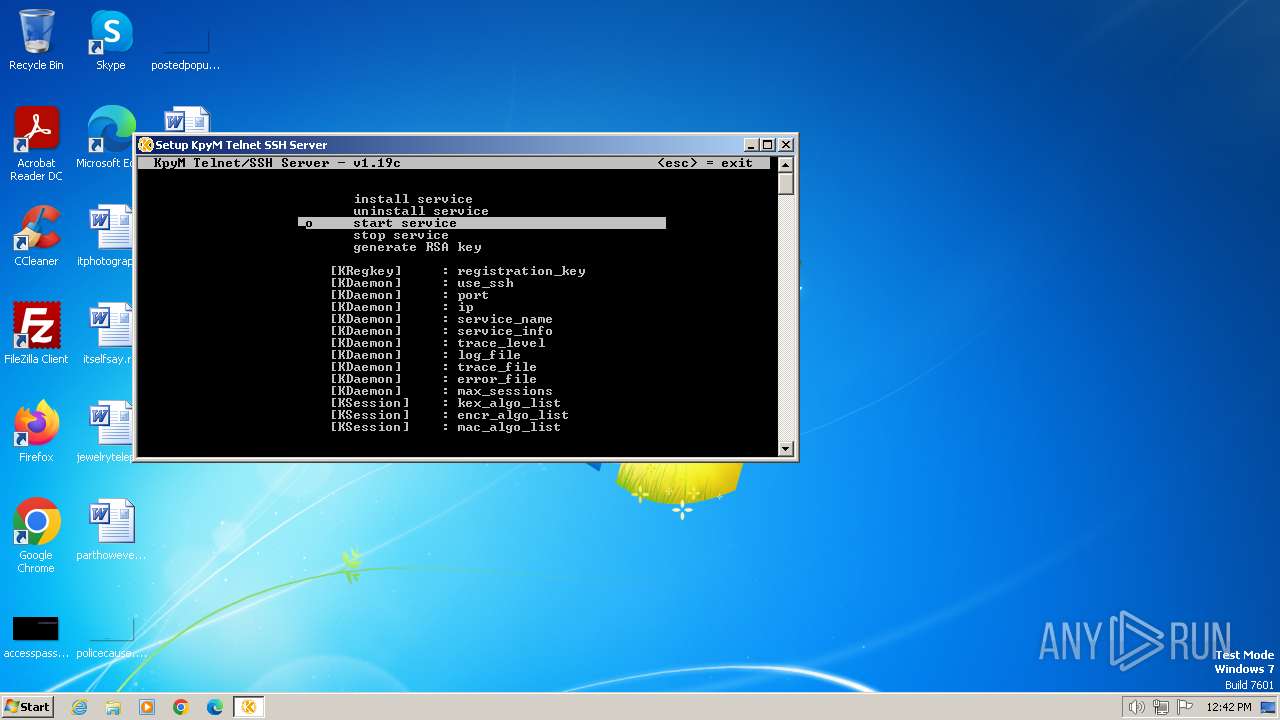
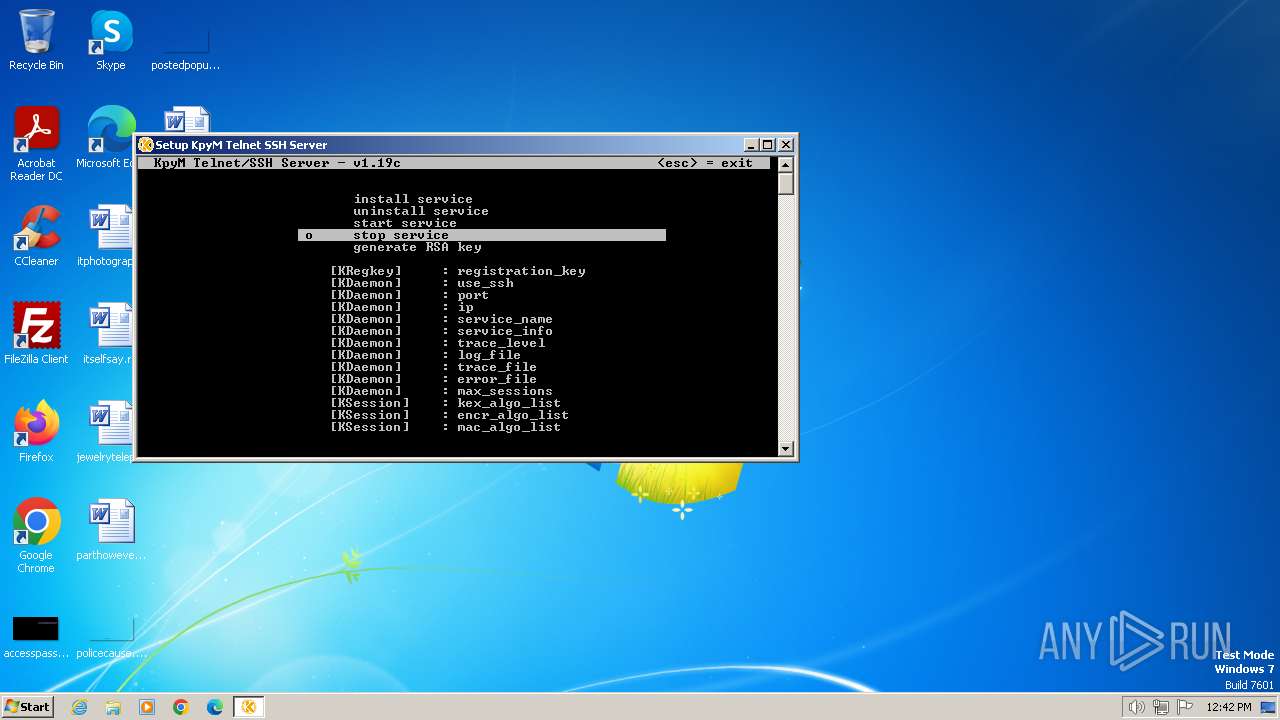
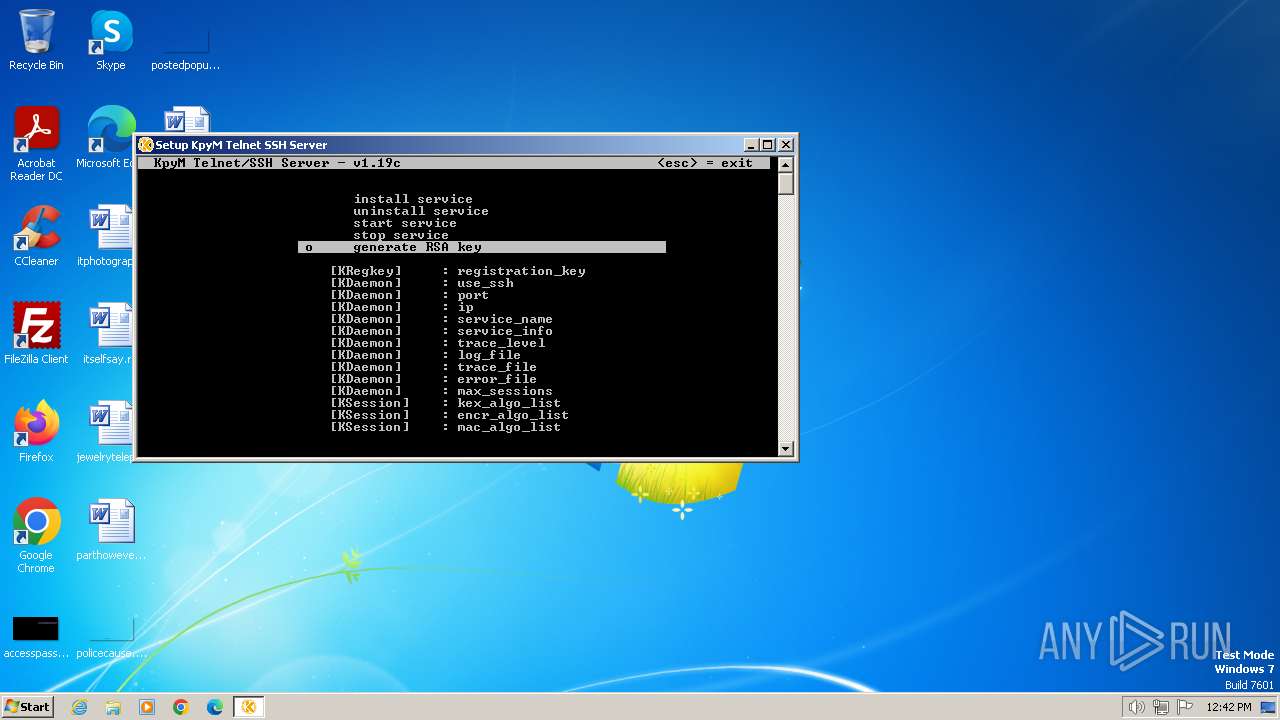
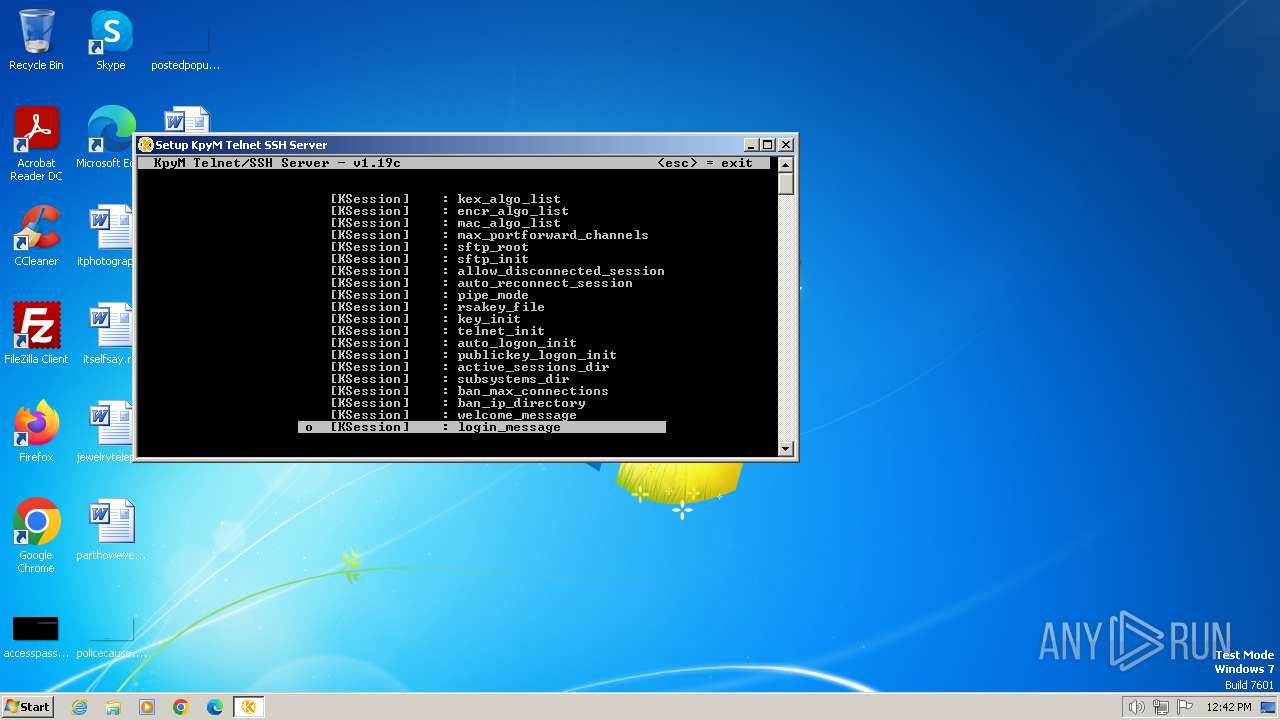
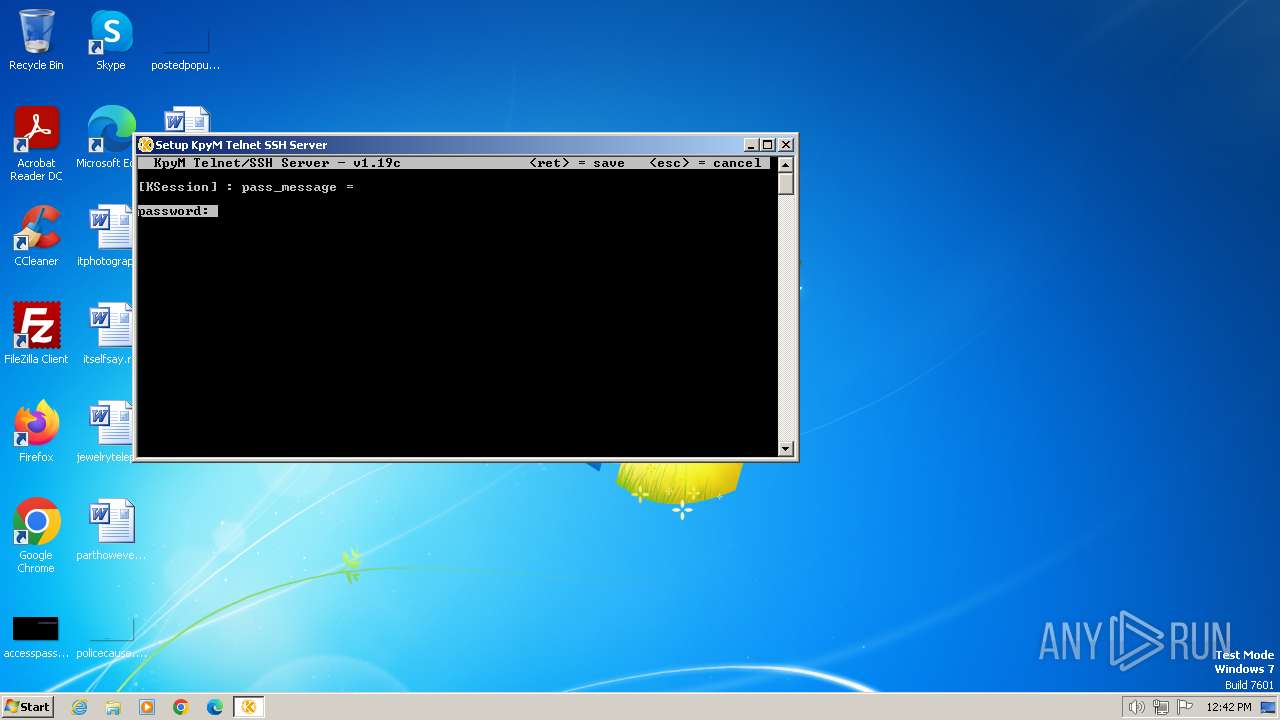
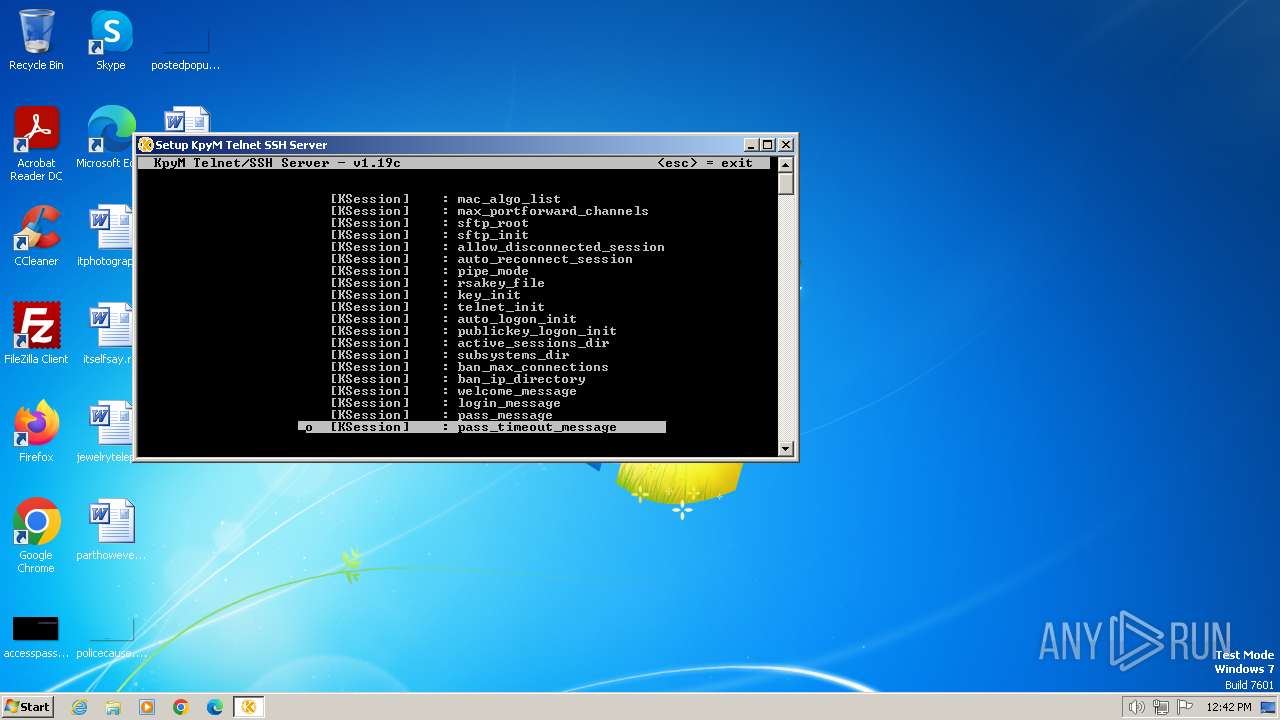
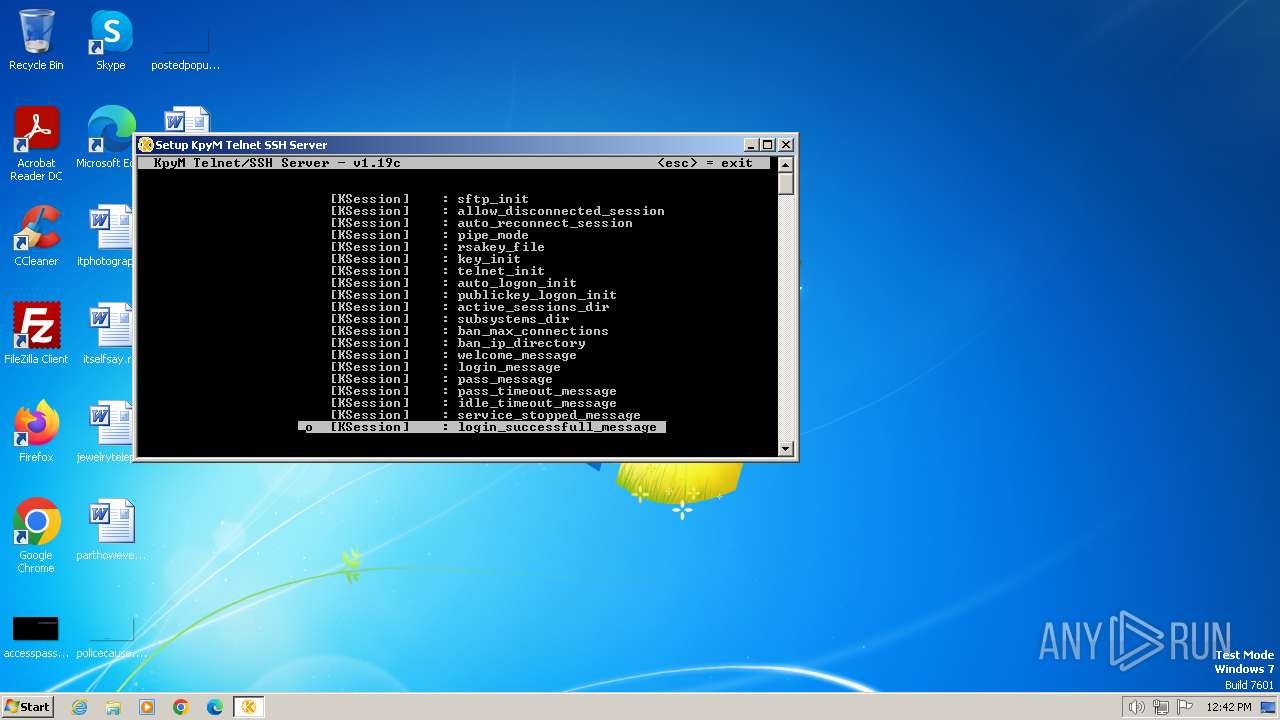
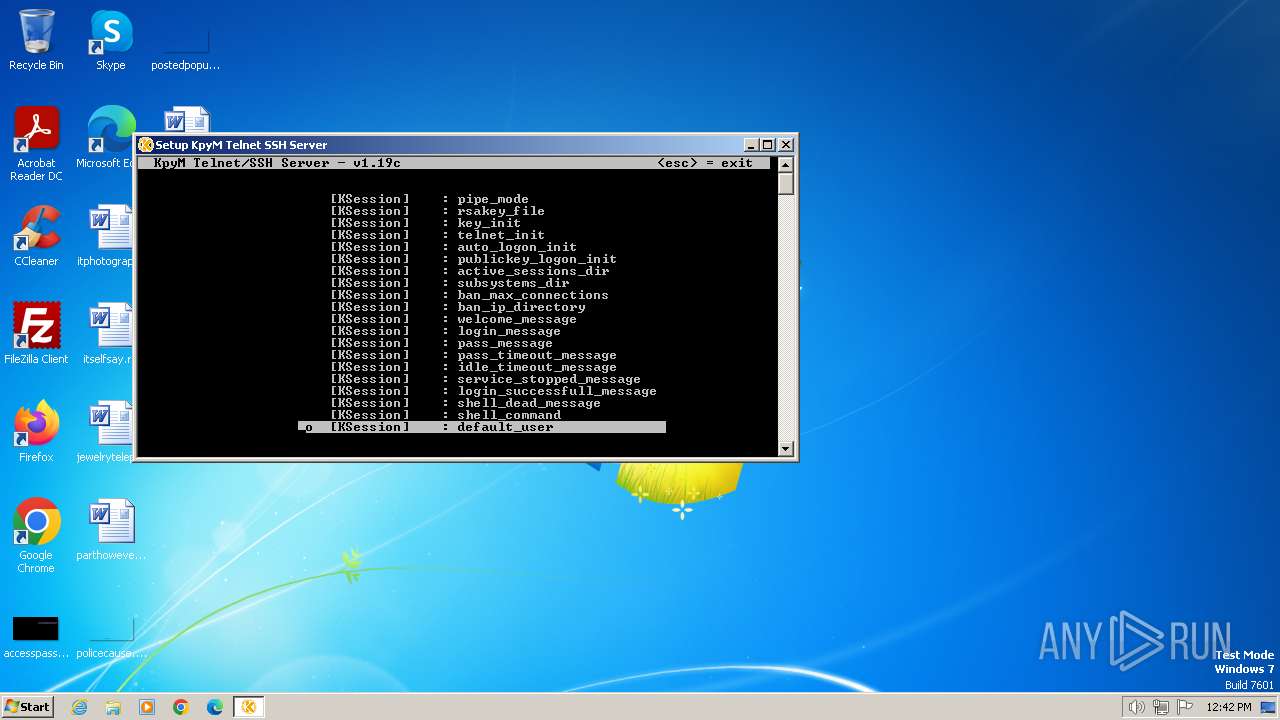
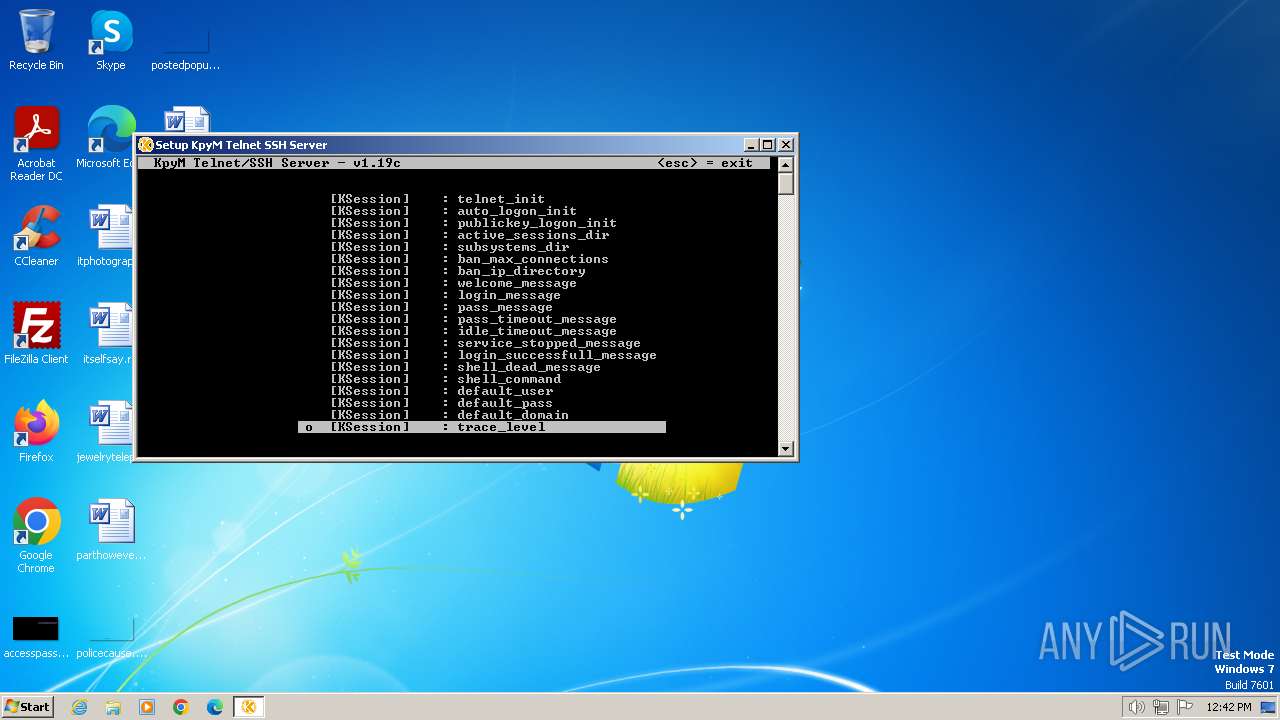
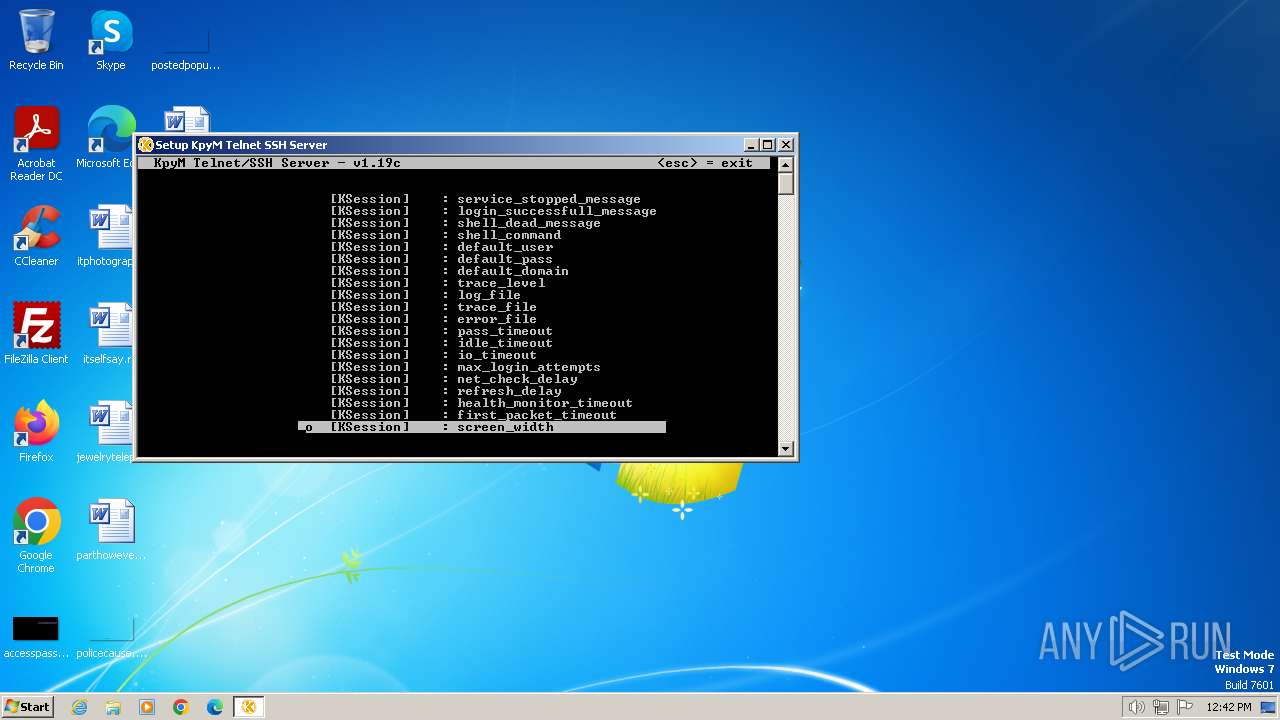
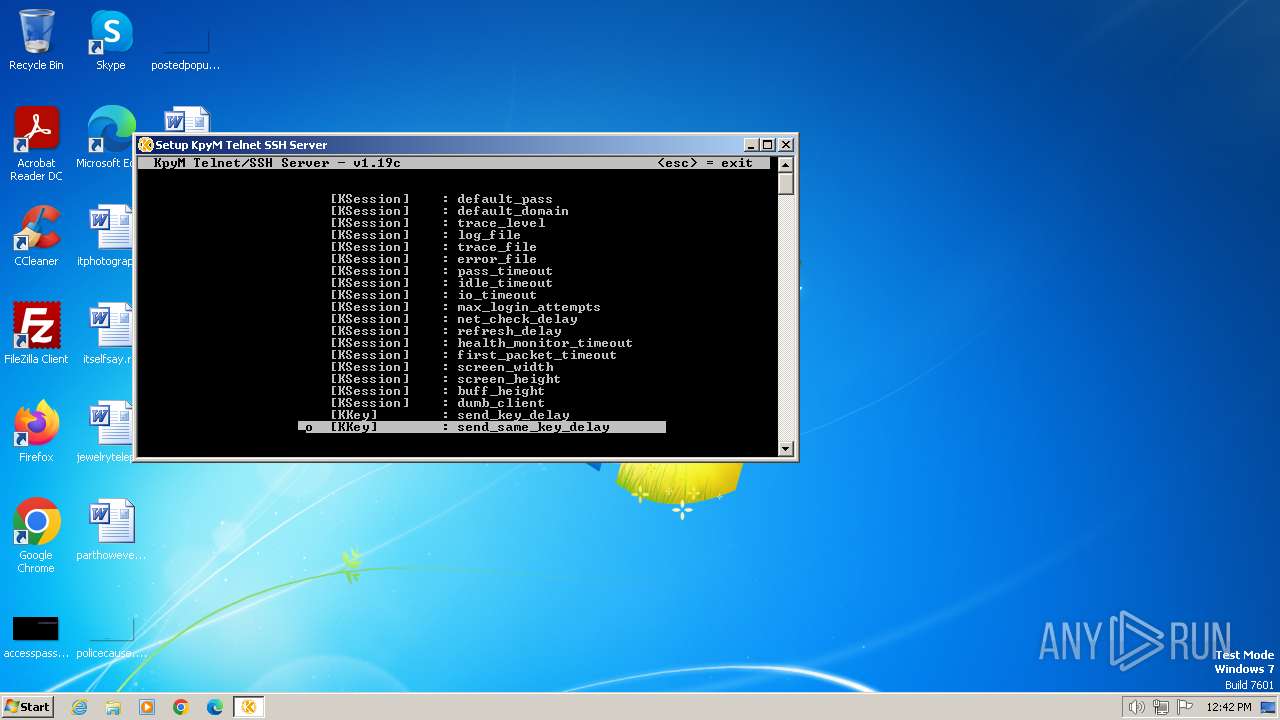
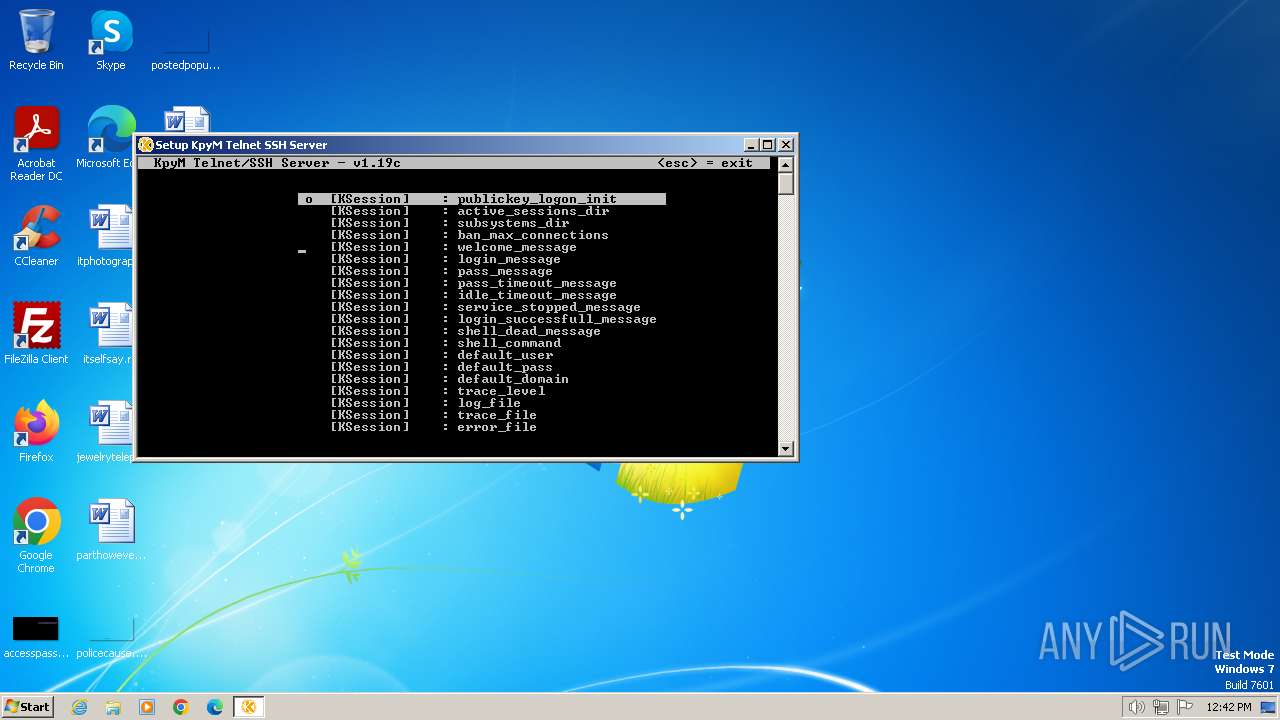
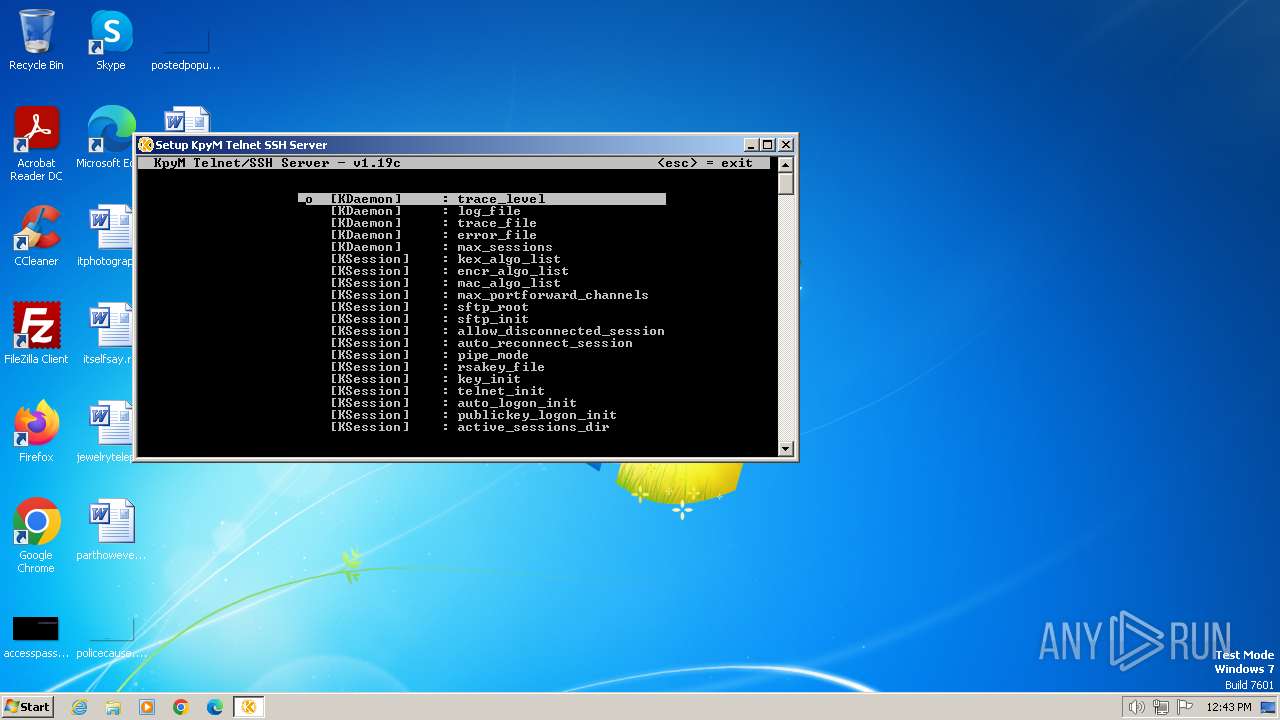
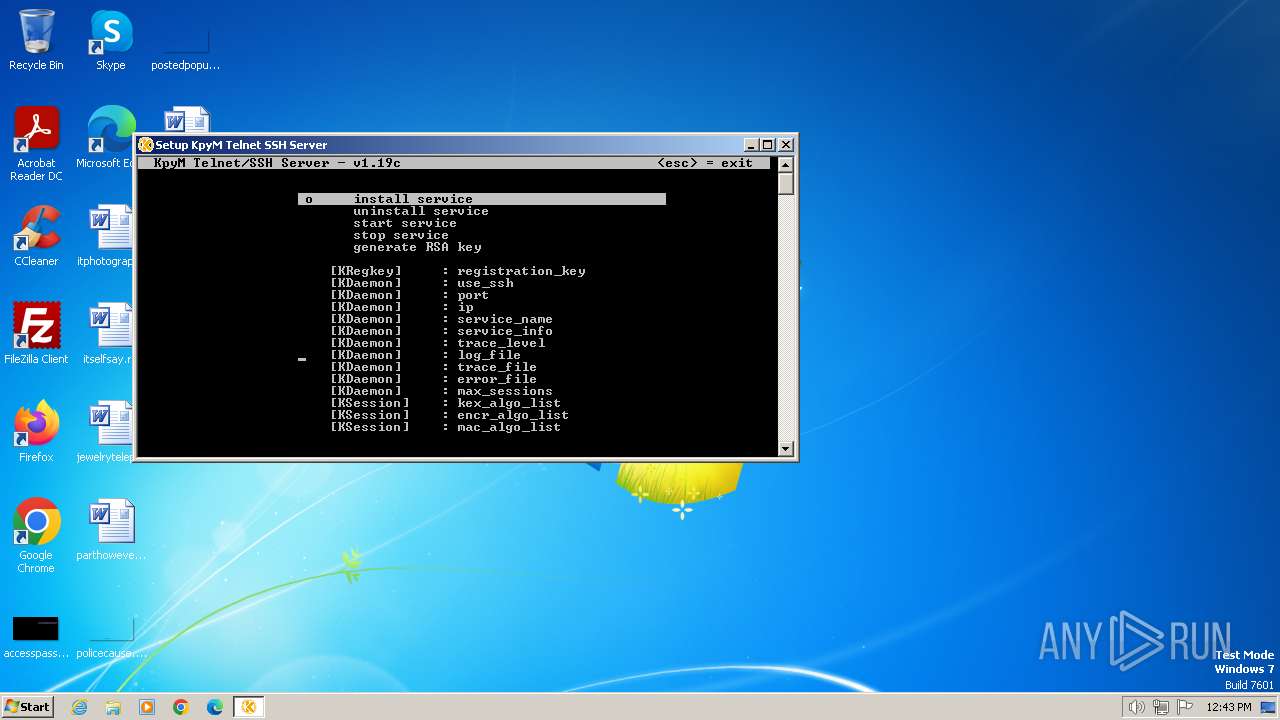
| FileDescription: | KpyM Telnet/SSH Server v1.19c Setup |
| FileVersion: | |
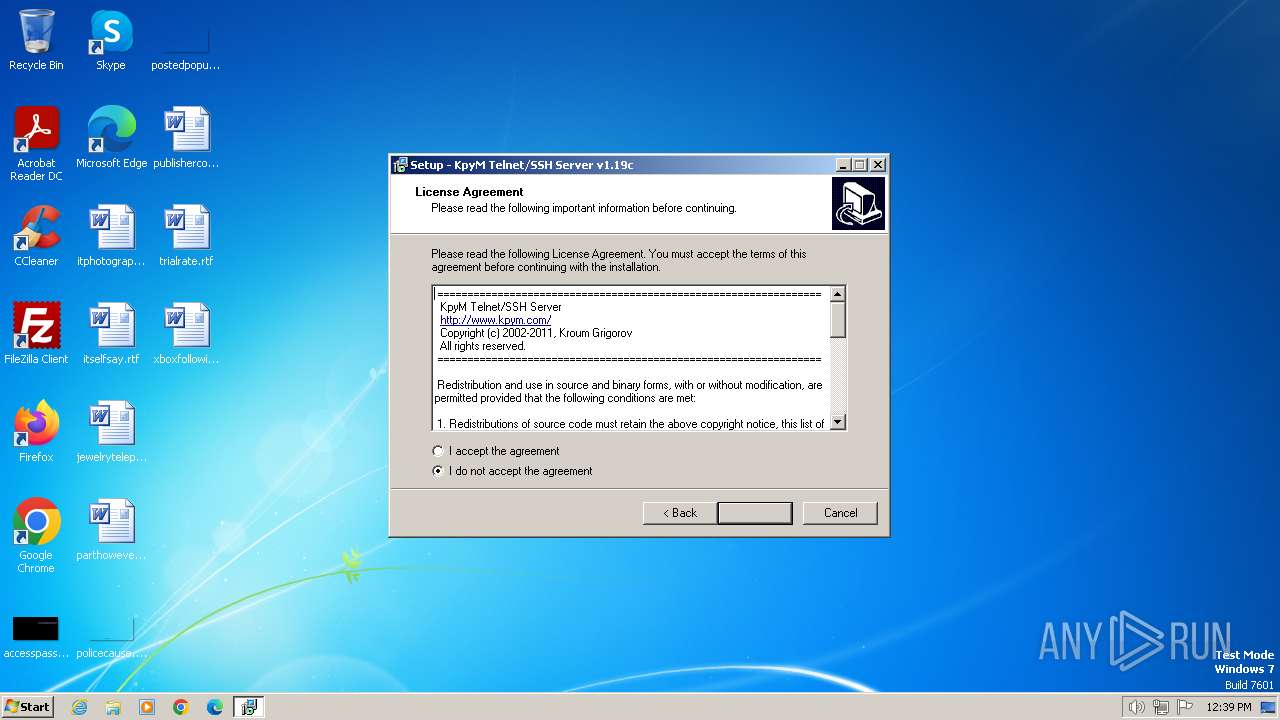
| LegalCopyright: | Copyright (c) 2002-2011 Kroum Grigorov |
| ProductName: | KpyM Telnet/SSH Server v1.19c |
| ProductVersion: |
Total processes
102
Monitored processes
58
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3700 --field-trial-handle=1320,i,14531531701970950101,14290256369283594077,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 748 | "C:\Program Files\KTS\daemon.exe" -setup | C:\Program Files\KTS\daemon.exe | explorer.exe | ||||||||||||
User: admin Company: Kroum Grigorov Integrity Level: HIGH Description: KpyM Telnet/SSH Server - daemon.exe Exit code: 0 Version: 1,19,0,3 Modules
| |||||||||||||||
| 848 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | daemon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 864 | fixscut.exe | C:\Program Files\KTS\fixscut.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 896 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | daemon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 952 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | daemon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1464 --field-trial-handle=1320,i,14531531701970950101,14290256369283594077,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1036 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | daemon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1172 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | daemon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1380 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | daemon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
15 606
Read events
15 500
Write events
96
Delete events
10
Modification events
| (PID) Process: | (2964) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.2.3 | |||
| (PID) Process: | (2964) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\KTS | |||
| (PID) Process: | (2964) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\KTS\ | |||
| (PID) Process: | (2964) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
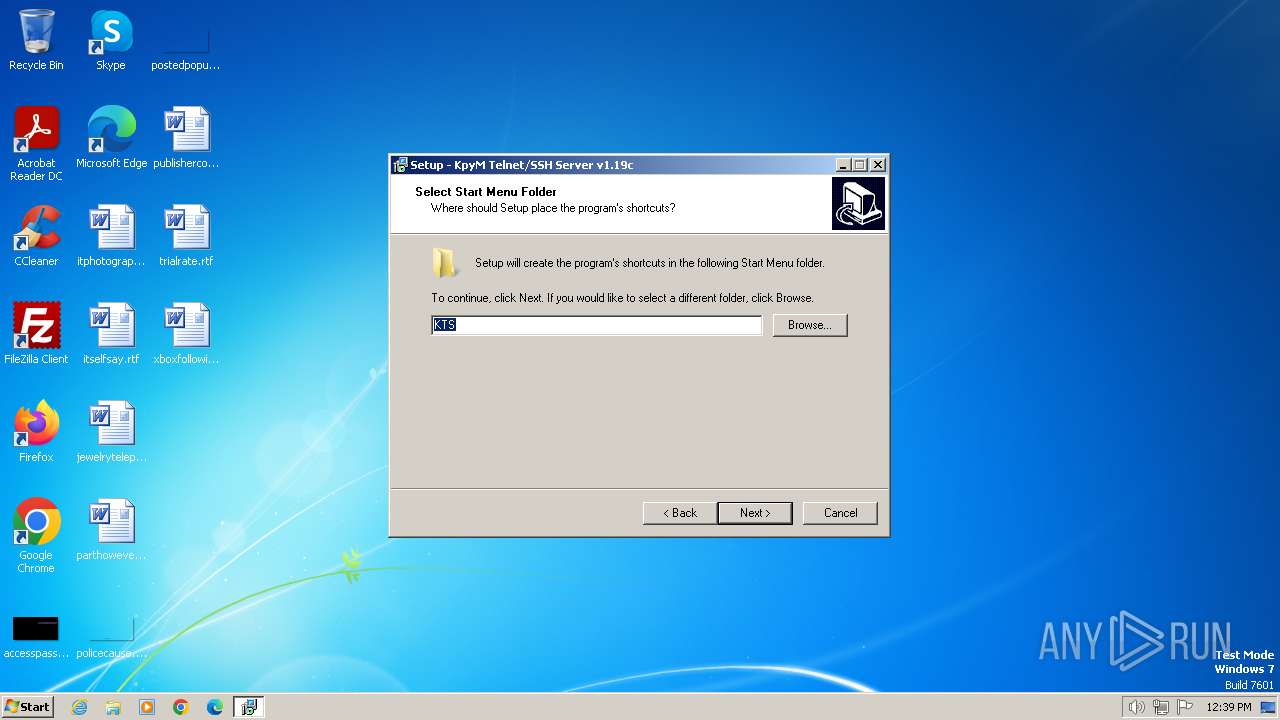
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: KTS | |||
| (PID) Process: | (2964) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (2964) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | Inno Setup: Setup Type |
Value: main | |||
| (PID) Process: | (2964) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
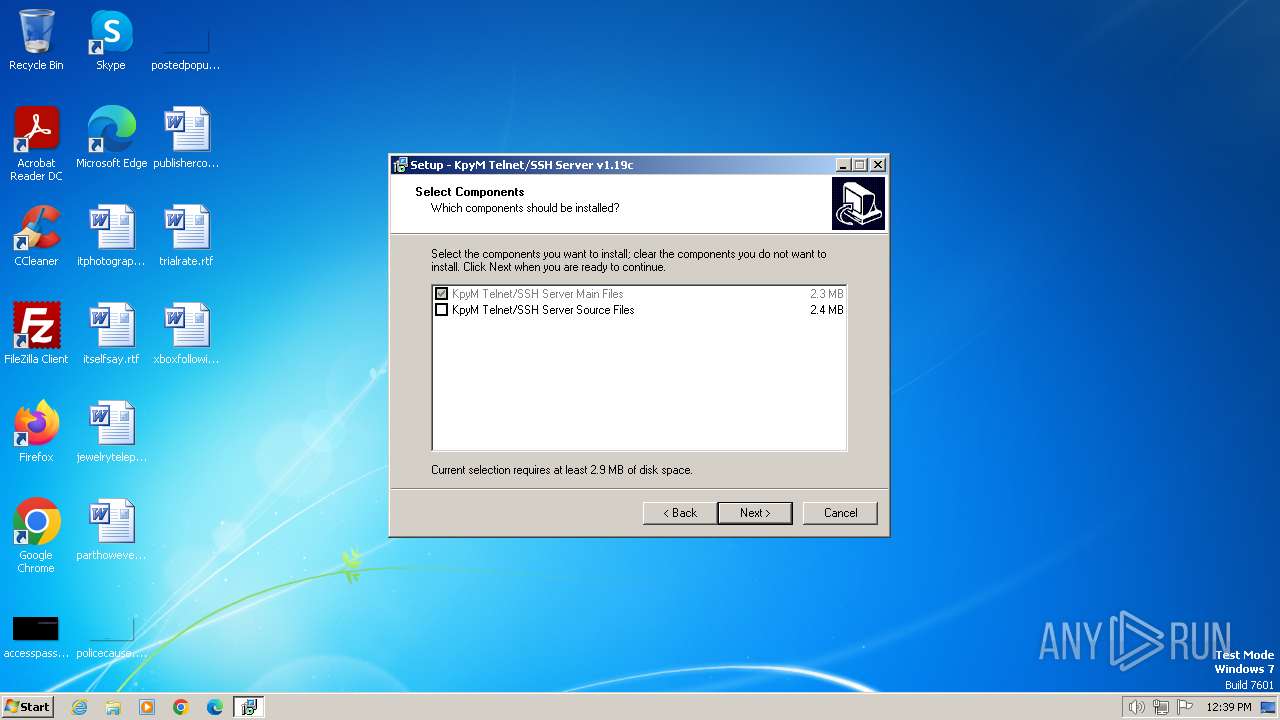
| Operation: | write | Name: | Inno Setup: Selected Components |
Value: main,source | |||
| (PID) Process: | (2964) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Components |
Value: | |||
| (PID) Process: | (2964) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | DisplayName |
Value: KpyM Telnet/SSH Server v1.19c | |||
| (PID) Process: | (2964) kts119c.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KpyM Telnet/SSH Server v1.19c_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\KTS\unins000.exe" | |||
Executable files
21
Suspicious files
41
Text files
266
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1776 | kts119c.exe | C:\Users\admin\AppData\Local\Temp\is-3133E.tmp\kts119c.tmp | executable | |
MD5:52950AC9E2B481453082F096120E355A | SHA256:25FBC88C7C967266F041AE4D47C2EAE0B96086F9E440CCA10729103AEE7EF6CD | |||
| 2964 | kts119c.tmp | C:\Program Files\KTS\is-59UL3.tmp | executable | |
MD5:DEADF995CEB95A073F9454B68414F607 | SHA256:46AAFF6630BC6C5D66B2BBF22FC5B7E59D6EEFE9BE622FCE7643FC3BA7143874 | |||
| 2964 | kts119c.tmp | C:\Program Files\KTS\is-8MQBN.tmp | text | |
MD5:979EC79BF19A5513B5C15DF9256CB4DB | SHA256:D9AF2F57B220244372C64F8C31C38D2ECB7D19570282967873DABF89669046F5 | |||
| 2964 | kts119c.tmp | C:\Program Files\KTS\unins000.exe | executable | |
MD5:DEADF995CEB95A073F9454B68414F607 | SHA256:46AAFF6630BC6C5D66B2BBF22FC5B7E59D6EEFE9BE622FCE7643FC3BA7143874 | |||
| 2964 | kts119c.tmp | C:\Program Files\KTS\is-F1NFH.tmp | executable | |
MD5:8C8983D282E9D6D3609988B0A2DEE242 | SHA256:1F9B8D992C73C47E369D821C251CDC53E56CC211872DFC2E89B8001E3906535E | |||
| 2964 | kts119c.tmp | C:\Program Files\KTS\auto_logon.ini | text | |
MD5:979EC79BF19A5513B5C15DF9256CB4DB | SHA256:D9AF2F57B220244372C64F8C31C38D2ECB7D19570282967873DABF89669046F5 | |||
| 2964 | kts119c.tmp | C:\Program Files\KTS\cl32.dll | executable | |
MD5:EE26B99466569836B5B9D267A2C05C73 | SHA256:9E59AA89BA674BE76AF6BCCEB8BDD51552AEB18BCB15316E9D3B145EEA451D29 | |||
| 2472 | kts119c.exe | C:\Users\admin\AppData\Local\Temp\is-8RMKR.tmp\kts119c.tmp | executable | |
MD5:52950AC9E2B481453082F096120E355A | SHA256:25FBC88C7C967266F041AE4D47C2EAE0B96086F9E440CCA10729103AEE7EF6CD | |||
| 2964 | kts119c.tmp | C:\Users\admin\AppData\Local\Temp\is-HBF71.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:C594B792B9C556EA62A30DE541D2FB03 | SHA256:5DCC1E0A197922907BCA2C4369F778BD07EE4B1BBBDF633E987A028A314D548E | |||
| 2964 | kts119c.tmp | C:\Users\admin\AppData\Local\Temp\is-HBF71.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
19
DNS requests
16
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2248 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2432 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
2248 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2248 | msedge.exe | 193.107.69.123:80 | www.kpym.com | SuperHosting.BG Ltd. | BG | unknown |
2432 | msedge.exe | 224.0.0.251:5353 | — | — | — | unknown |
2248 | msedge.exe | 2.17.162.14:443 | www.bing.com | Akamai International B.V. | BR | unknown |
2248 | msedge.exe | 152.199.21.175:443 | msedgeextensions.sf.tlu.dl.delivery.mp.microsoft.com | EDGECAST | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.kpym.com |
| unknown |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.bing.com |
| whitelisted |
msedgeextensions.sf.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |