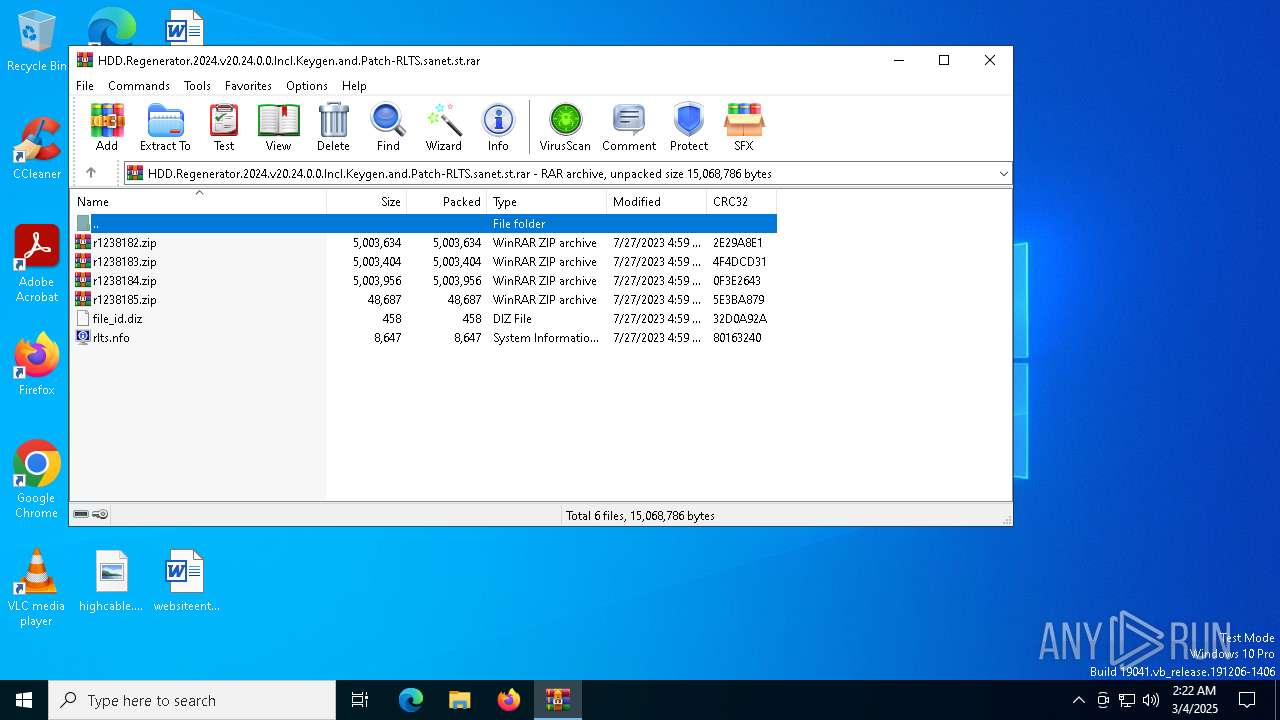
| File name: | HDD.Regenerator.2024.v20.24.0.0.Incl.Keygen.and.Patch-RLTS.sanet.st.rar |
| Full analysis: | https://app.any.run/tasks/b7112a16-8e76-4b02-9350-b58743b159eb |
| Verdict: | Malicious activity |
| Analysis date: | March 04, 2025, 02:22:33 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2CB0D4F56C472421A639522D6D3E714E |
| SHA1: | 52410AA630E02B9B97AD53A92281C18E099D6725 |
| SHA256: | F19E21A4A3A84E4C89A08F042897D7C8997F7B0B105B5BB19A570BEAE97BA446 |
| SSDEEP: | 98304:ISng7bnQXFjEG5JHECafDttHNHelkzo85AhuiAYvMrQJ6MdCxIv92LedhgclZCYQ:6sNESt9LaZyn1JXVYW46ICC |
MALICIOUS
No malicious indicators.SUSPICIOUS
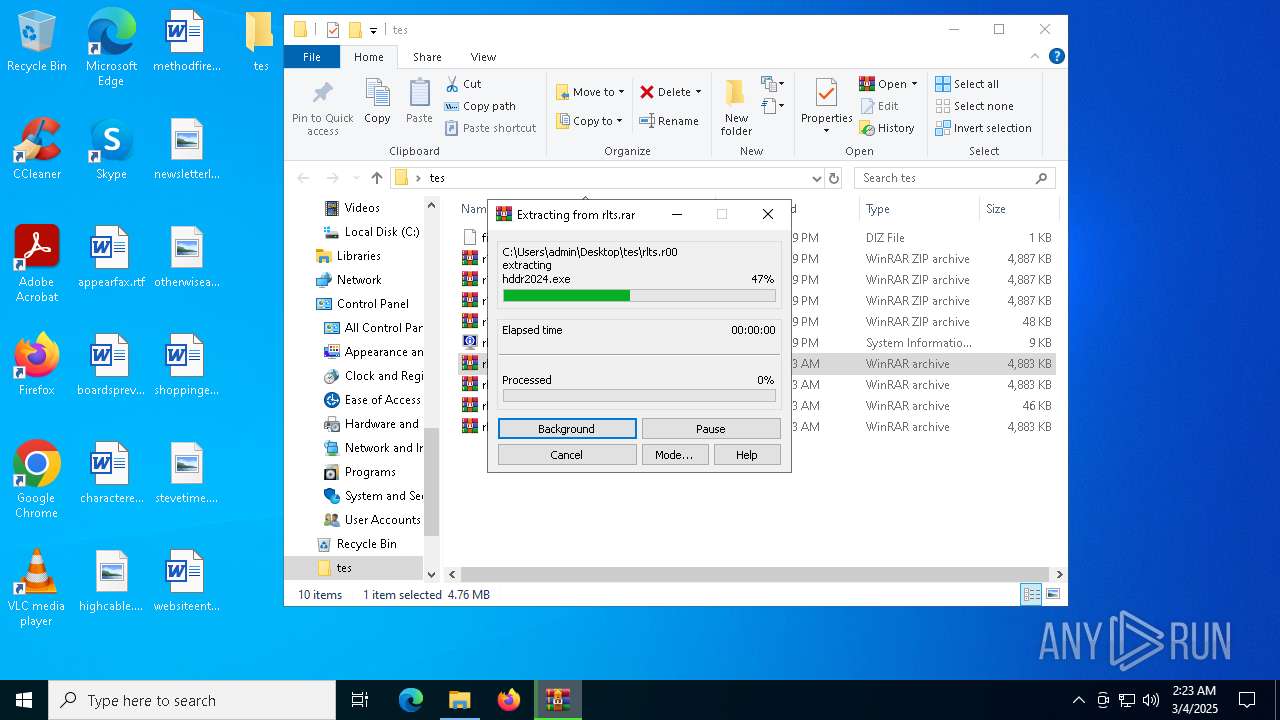
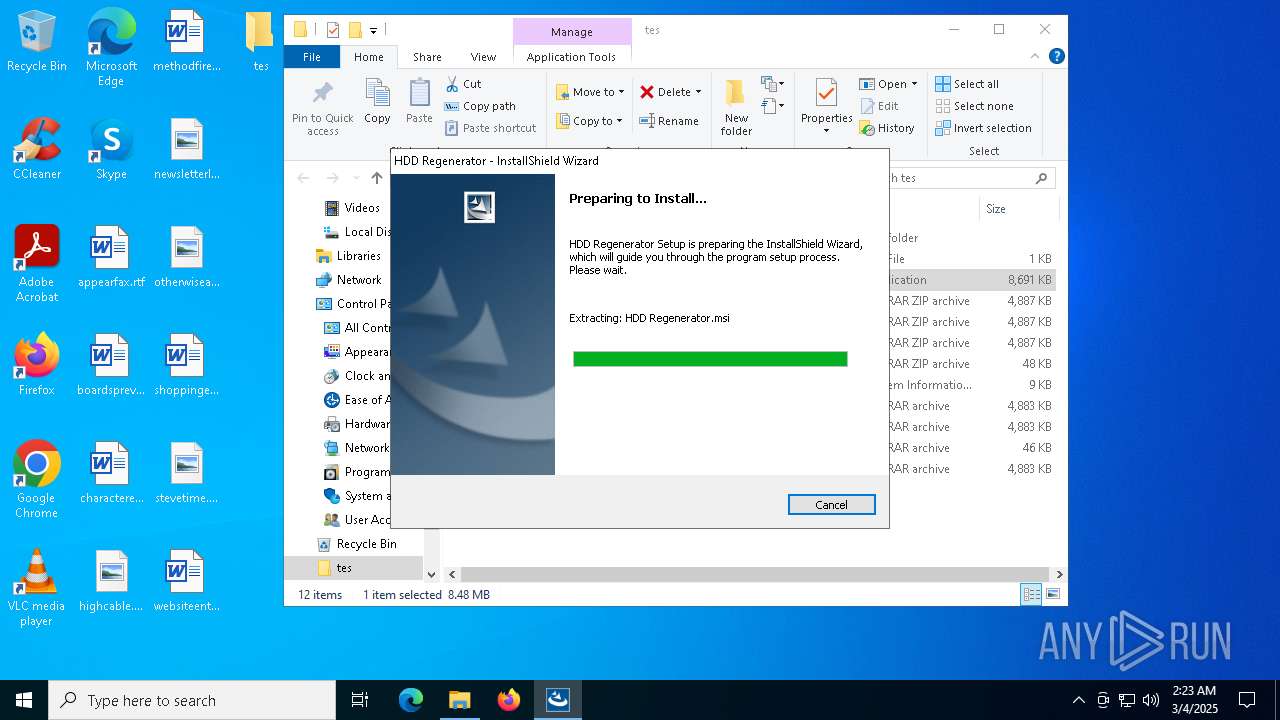
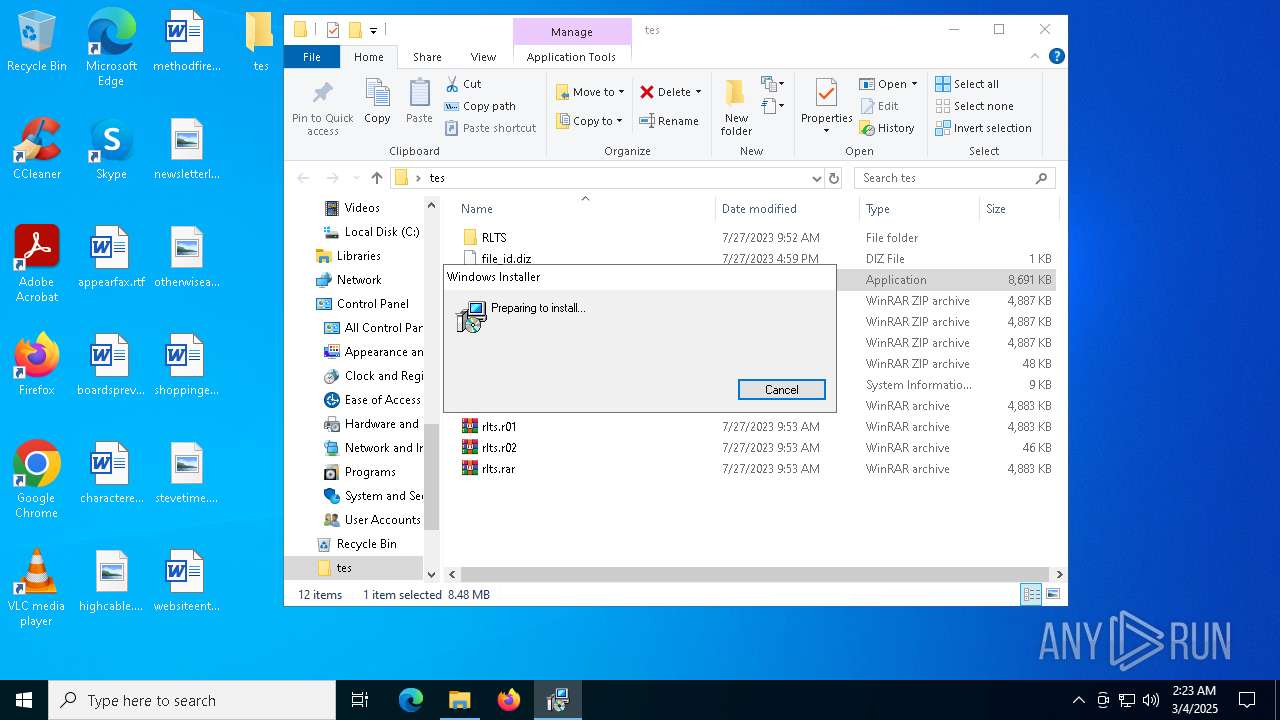
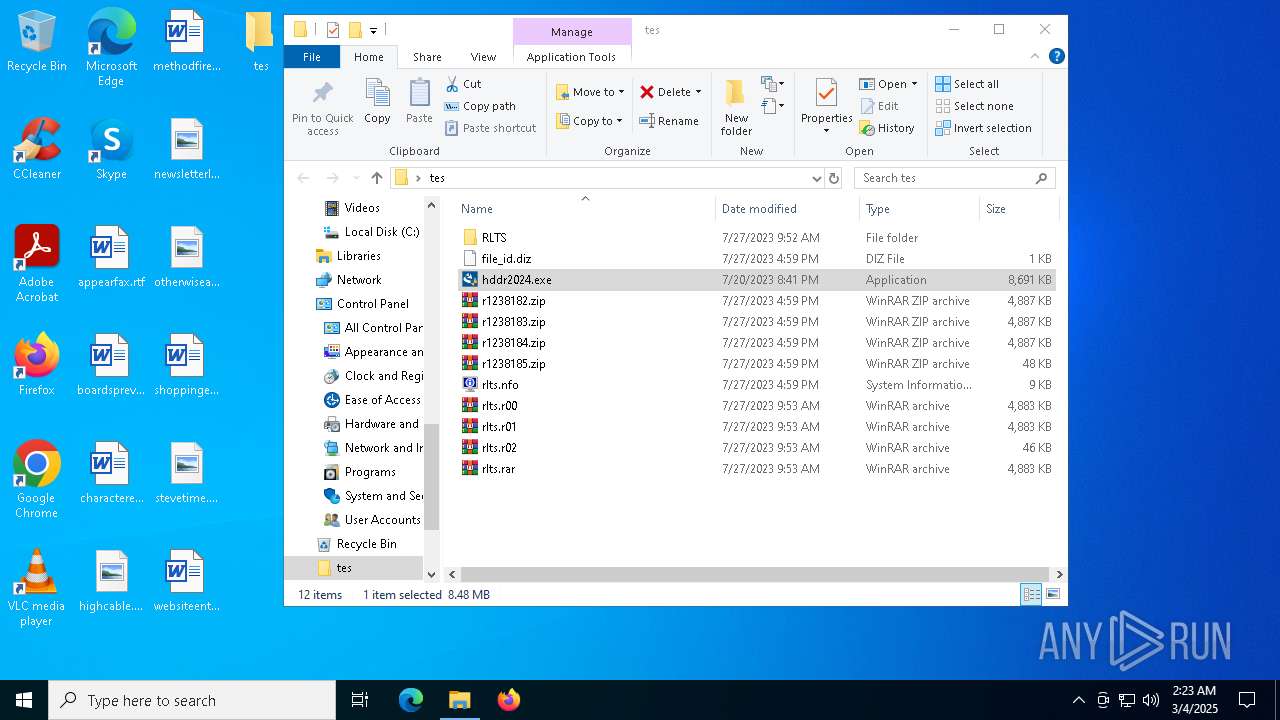
Executable content was dropped or overwritten
- hddr2024.exe (PID: 5776)
Starts itself from another location
- hddr2024.exe (PID: 5776)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 4220)
There is functionality for taking screenshot (YARA)
- hddr2024.exe (PID: 5776)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 1040)
- BackgroundTransferHost.exe (PID: 728)
- BackgroundTransferHost.exe (PID: 1272)
- BackgroundTransferHost.exe (PID: 6668)
- BackgroundTransferHost.exe (PID: 728)
- msiexec.exe (PID: 968)
The sample compiled with english language support
- WinRAR.exe (PID: 5164)
- WinRAR.exe (PID: 5260)
- msiexec.exe (PID: 968)
- hddr2024.exe (PID: 5776)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 1272)
- msiexec.exe (PID: 968)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 1272)
- msiexec.exe (PID: 968)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 1272)
- msiexec.exe (PID: 968)
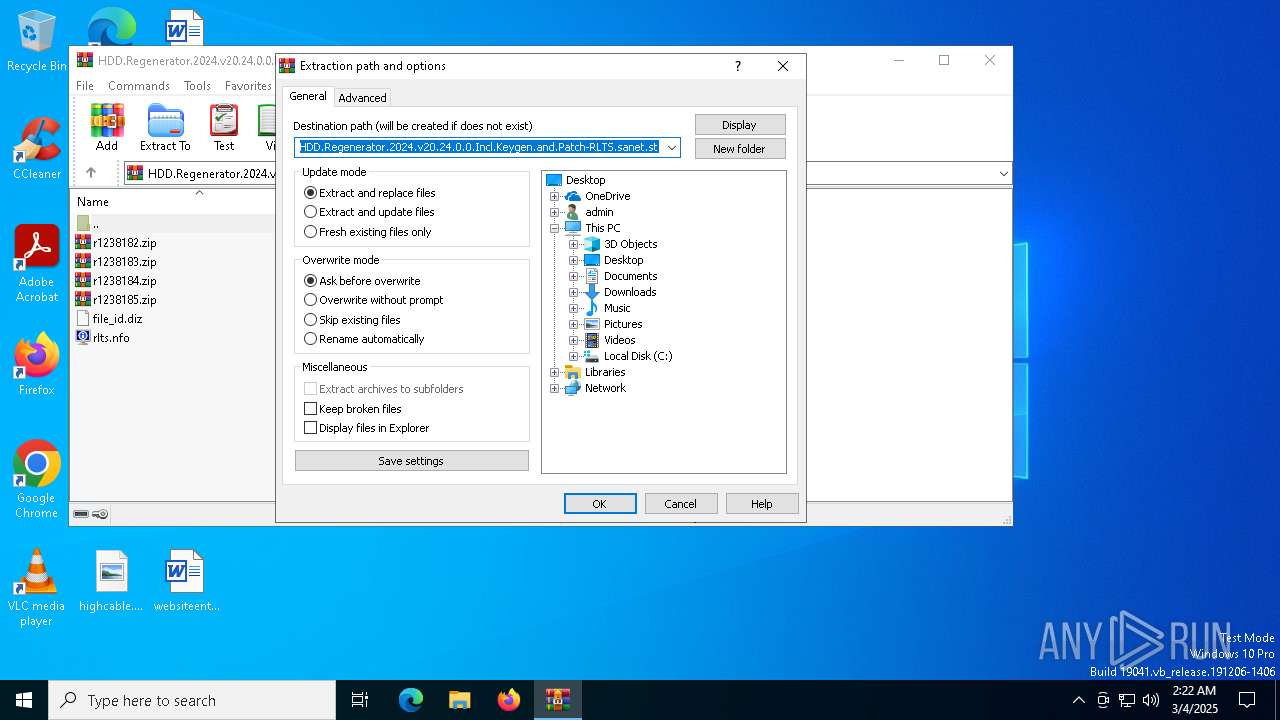
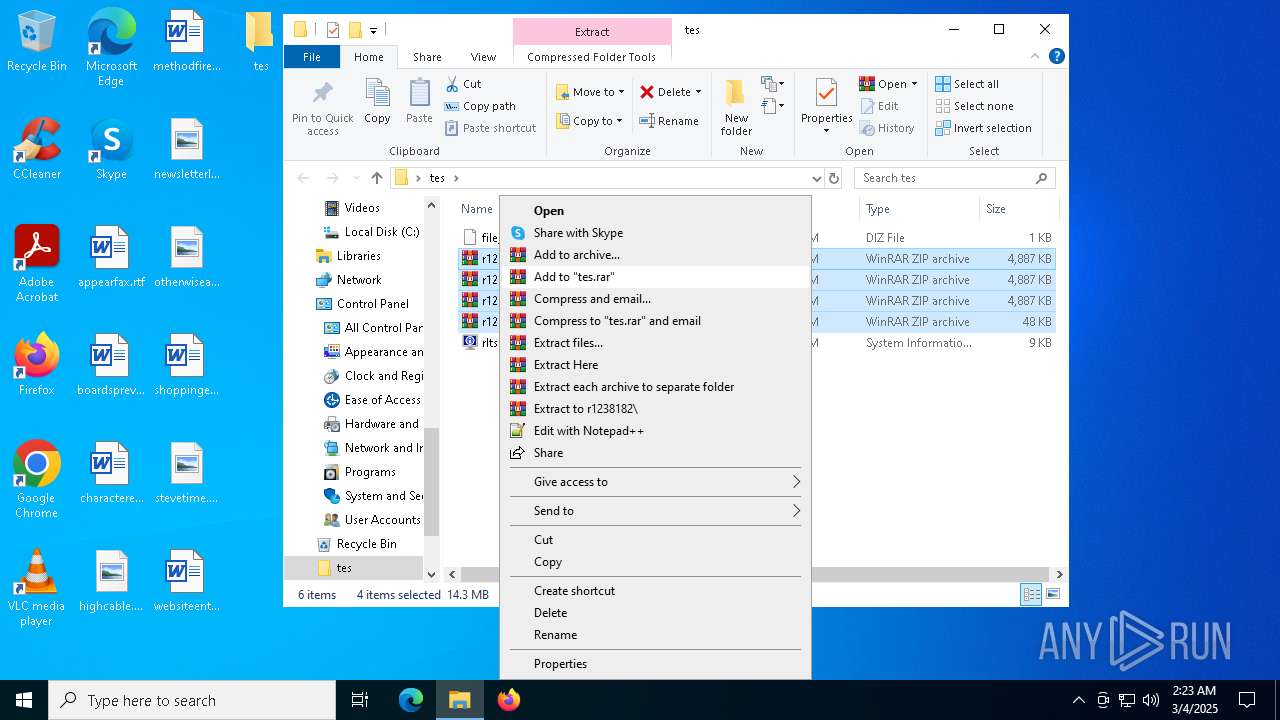
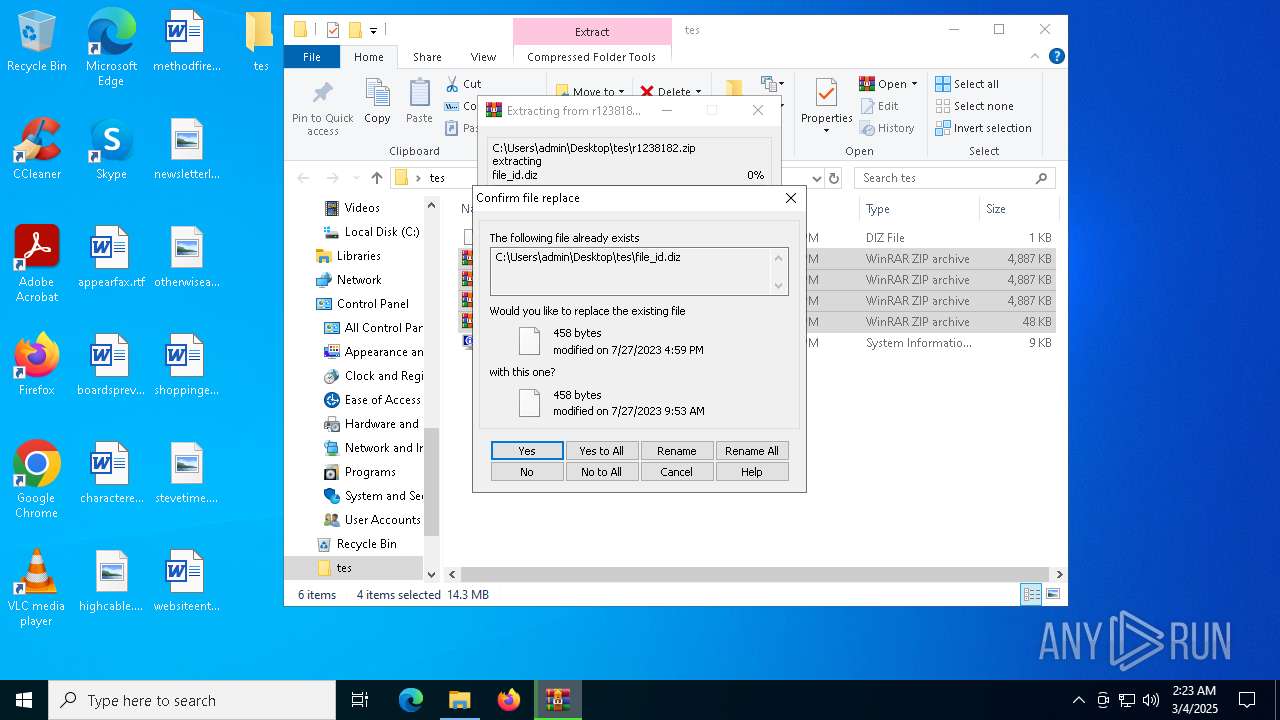
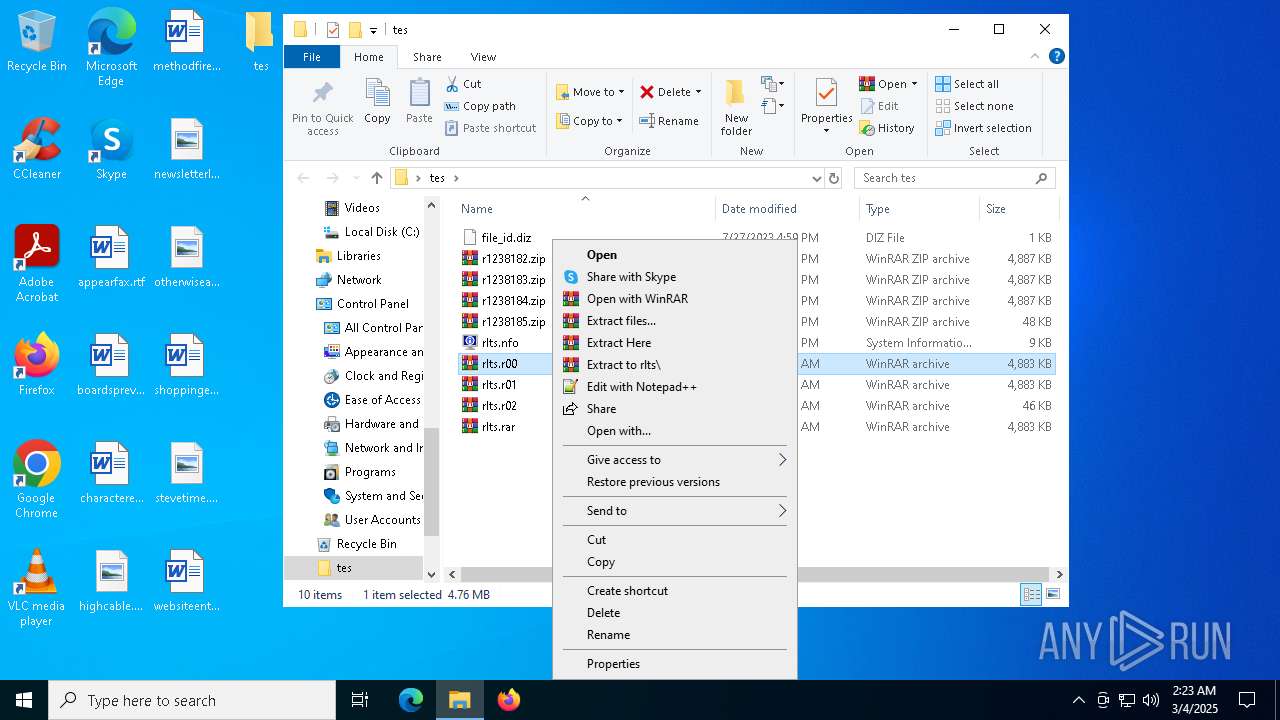
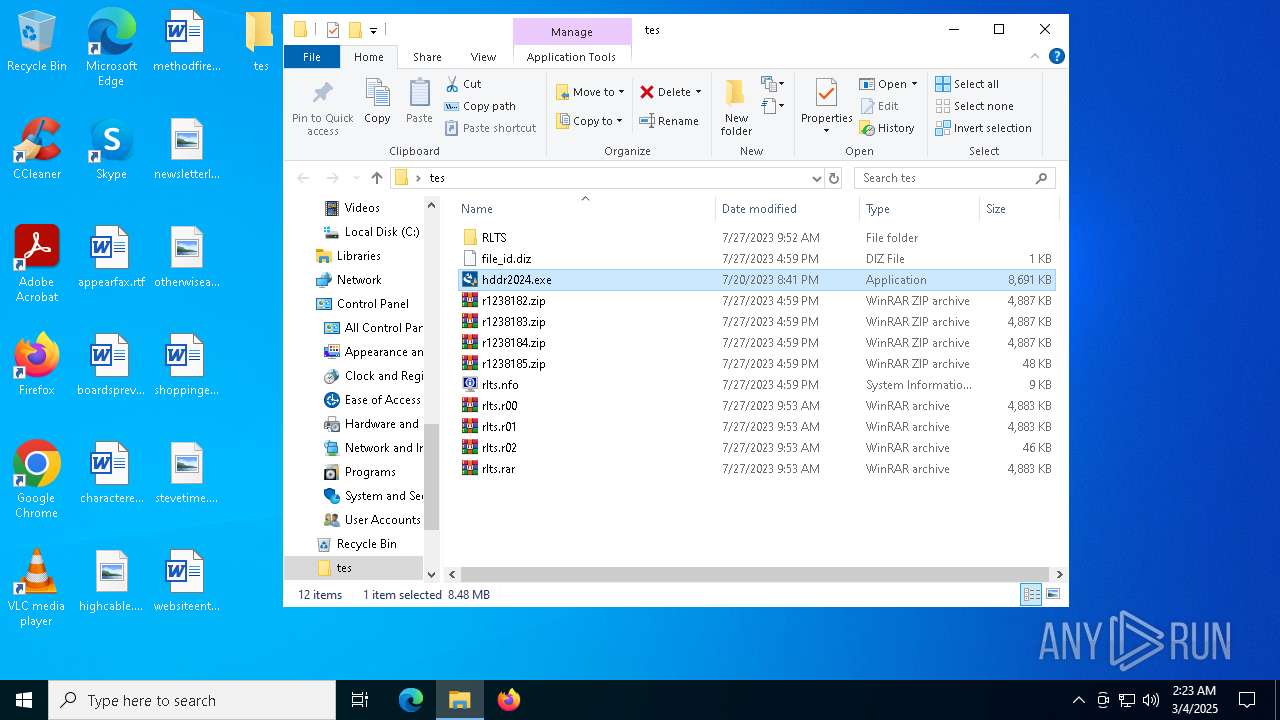
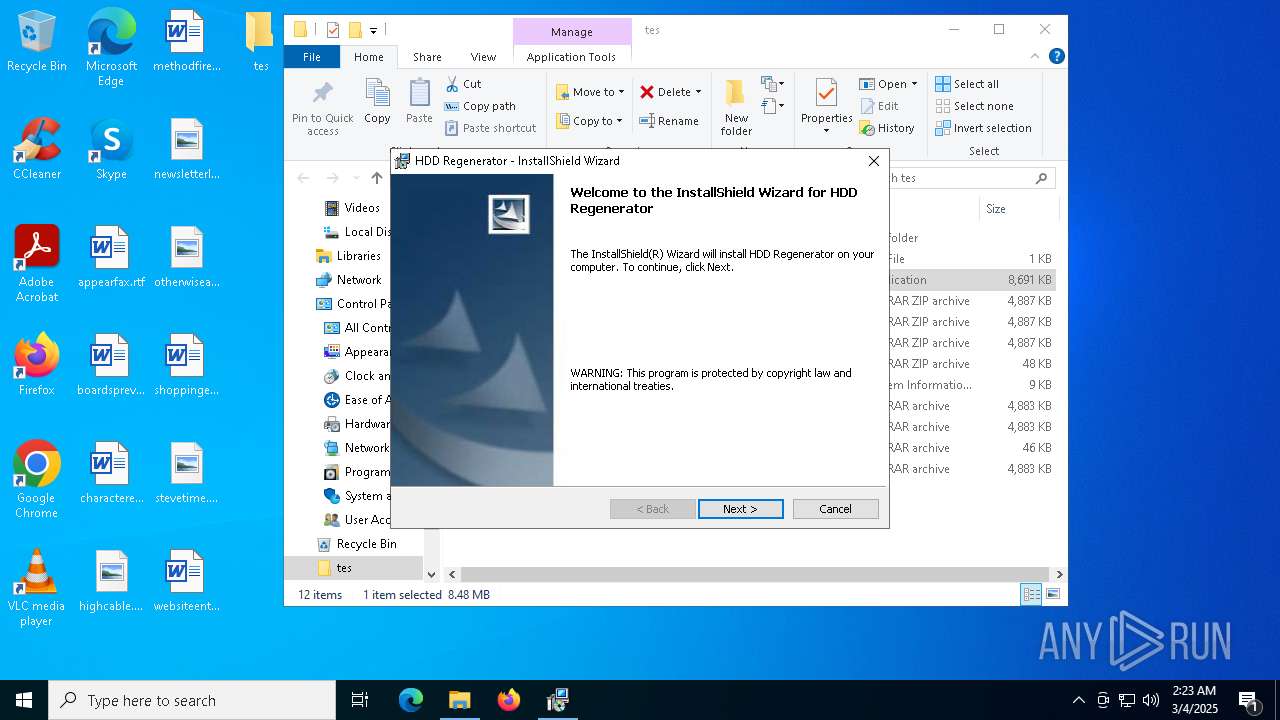
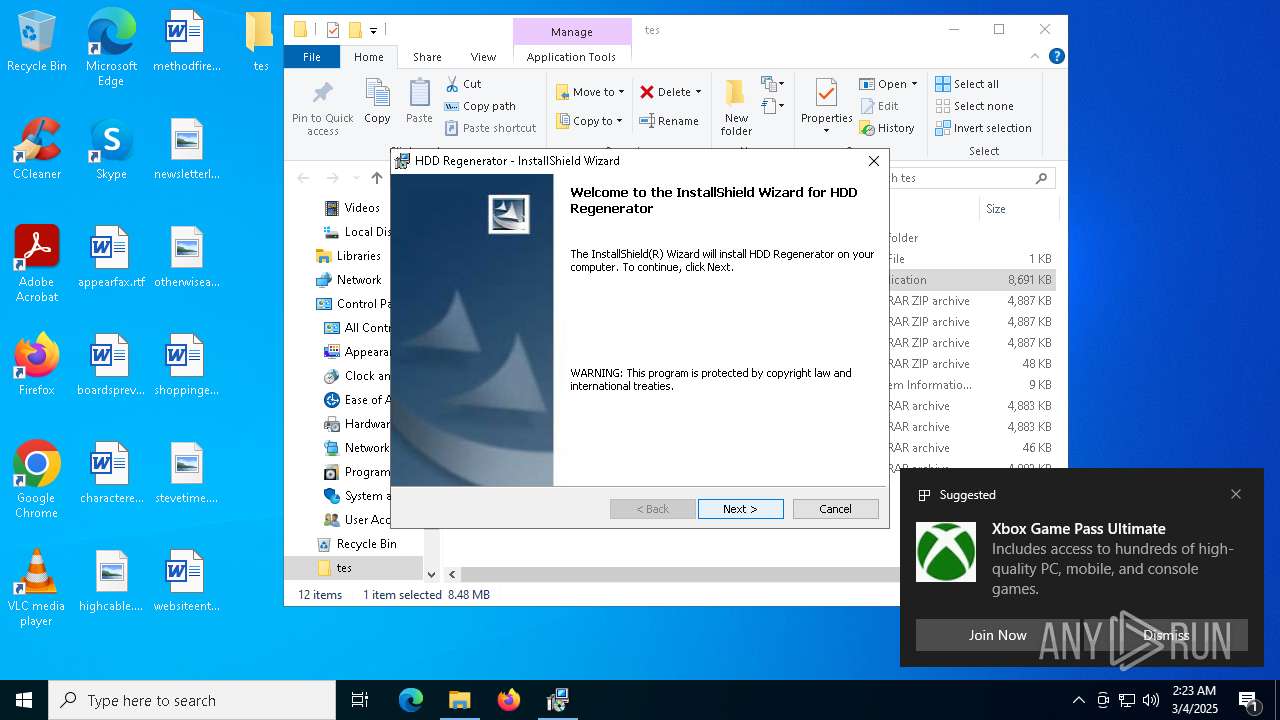
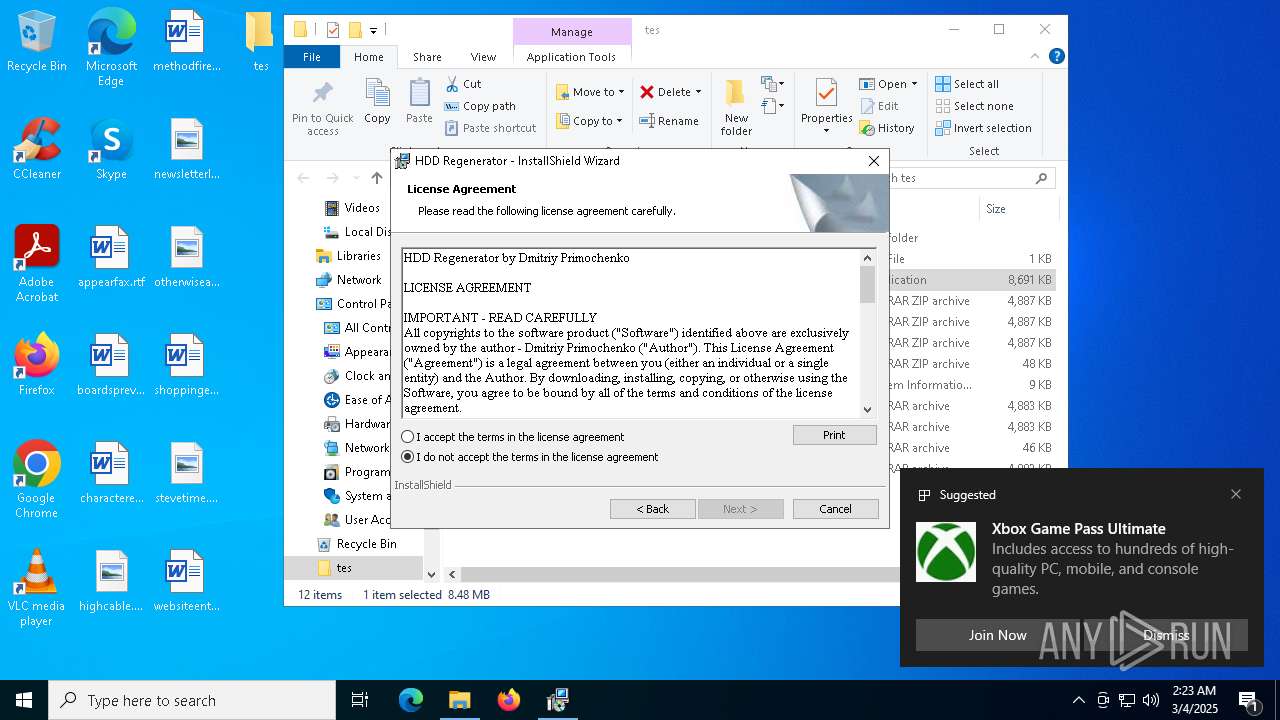
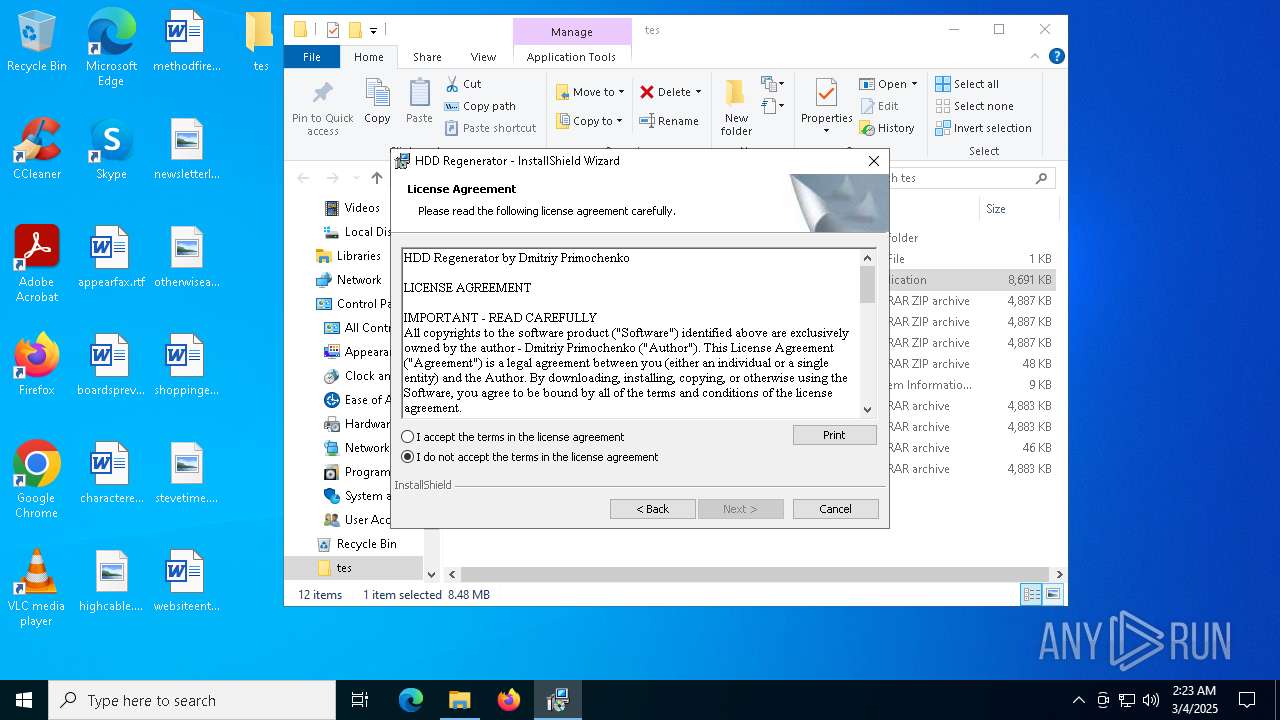
Manual execution by a user
- WinRAR.exe (PID: 6068)
- hddr2024.exe (PID: 5776)
- WinRAR.exe (PID: 5260)
- hddr2024.exe (PID: 2096)
Create files in a temporary directory
- hddr2024.exe (PID: 5776)
- hddr2024.exe (PID: 6512)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5260)
- msiexec.exe (PID: 968)
Reads the computer name
- hddr2024.exe (PID: 5776)
- hddr2024.exe (PID: 6512)
- msiexec.exe (PID: 4400)
- msiexec.exe (PID: 5352)
- ShellExperienceHost.exe (PID: 4220)
Checks supported languages
- hddr2024.exe (PID: 6512)
- msiexec.exe (PID: 4400)
- msiexec.exe (PID: 5352)
- hddr2024.exe (PID: 5776)
- ShellExperienceHost.exe (PID: 4220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 458 |
| UncompressedSize: | 458 |
| OperatingSystem: | Win32 |
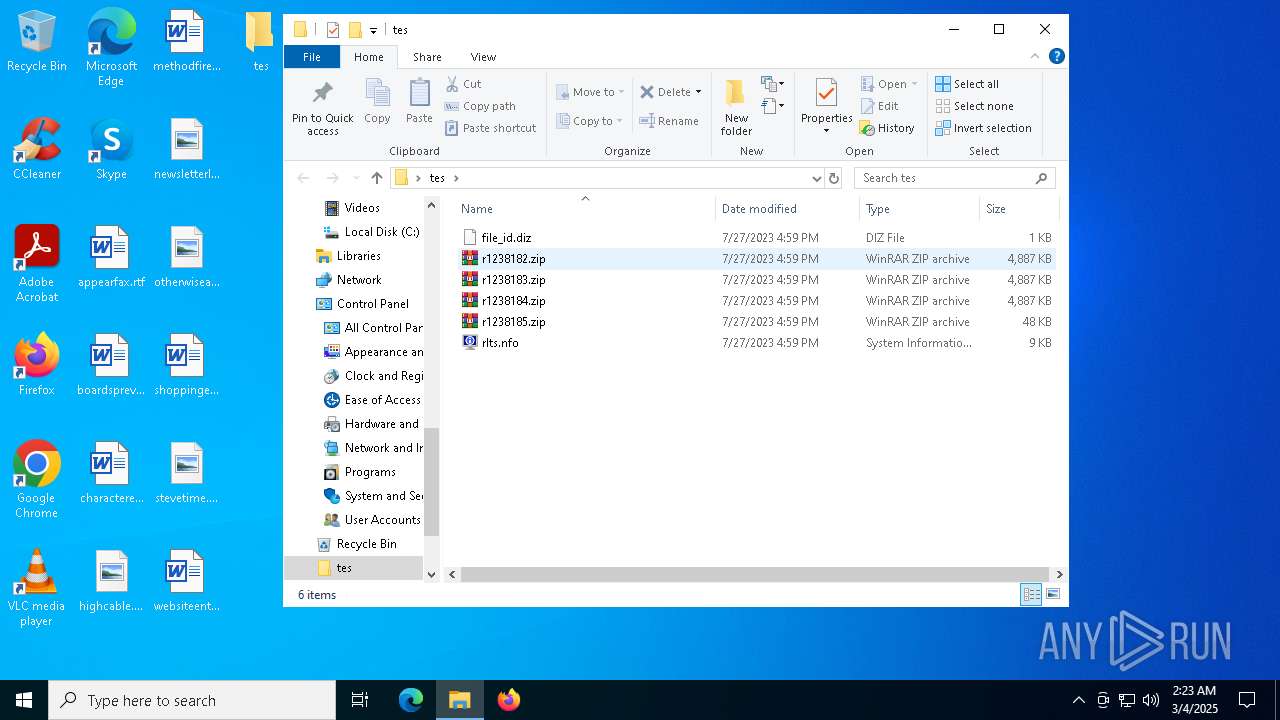
| ArchivedFileName: | file_id.diz |
Total processes
154
Monitored processes
17
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | "C:\WINDOWS\system32\MSIEXEC.EXE" /i "C:\Users\admin\AppData\Local\Temp\{6A19A9C4-DA9E-48C1-BA99-65060662A30B}\HDD Regenerator.msi" SETUPEXEDIR="C:\Users\admin\Desktop\tes" SETUPEXENAME="hddr2024.exe" | C:\Windows\SysWOW64\msiexec.exe | hddr2024.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | "C:\Users\admin\Desktop\tes\hddr2024.exe" | C:\Users\admin\Desktop\tes\hddr2024.exe | — | explorer.exe | |||||||||||
User: admin Company: Abstradrome Integrity Level: MEDIUM Description: Setup Launcher Unicode Exit code: 3221226540 Version: 20.24.0000 Modules
| |||||||||||||||
| 4220 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4400 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4740 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5164 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\HDD.Regenerator.2024.v20.24.0.0.Incl.Keygen.and.Patch-RLTS.sanet.st.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
12 475
Read events
12 400
Write events
56
Delete events
19
Modification events
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\HDD.Regenerator.2024.v20.24.0.0.Incl.Keygen.and.Patch-RLTS.sanet.st.rar | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (728) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (728) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
5
Suspicious files
17
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1272 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\91df8773-16e5-4f70-8746-f4ba00dd32ee.down_data | — | |
MD5:— | SHA256:— | |||
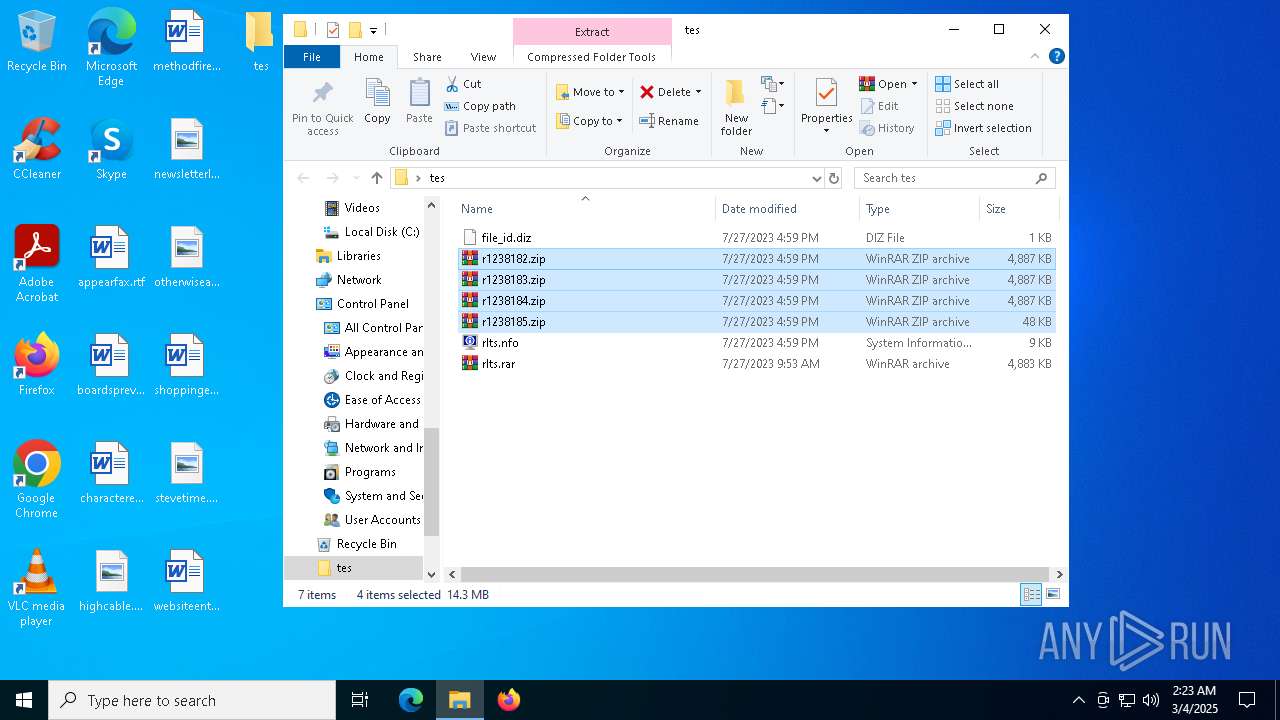
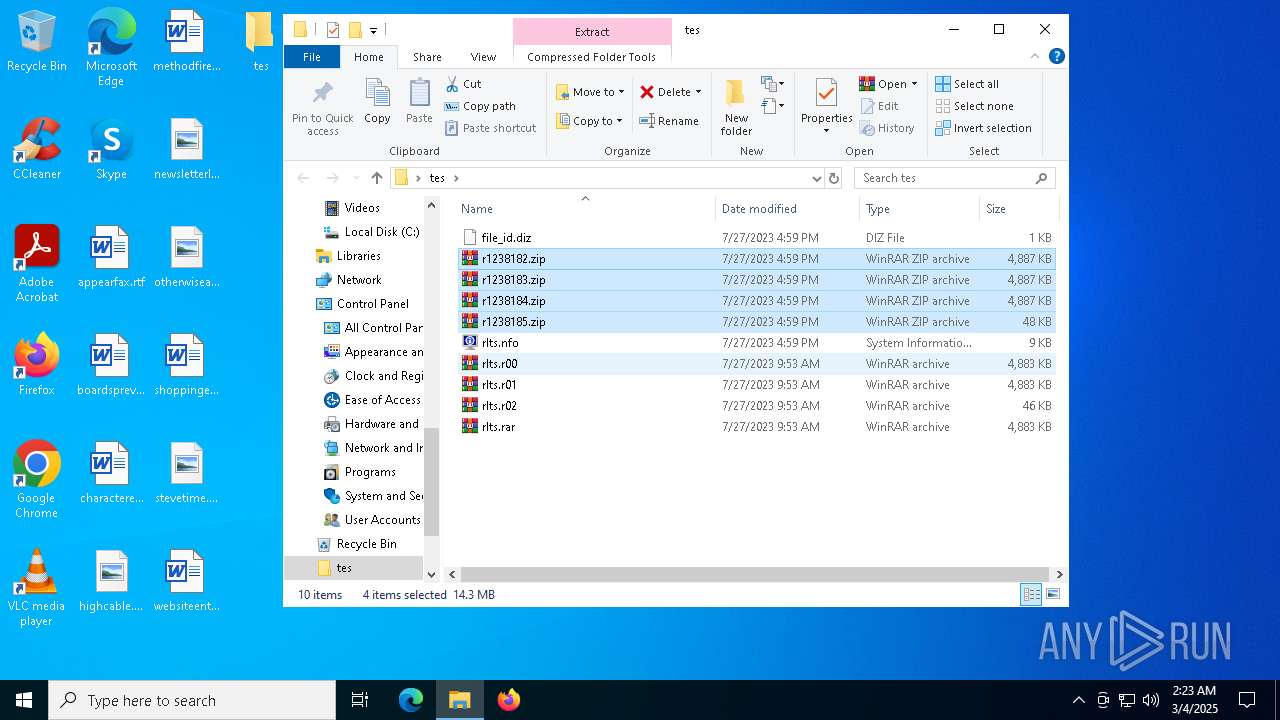
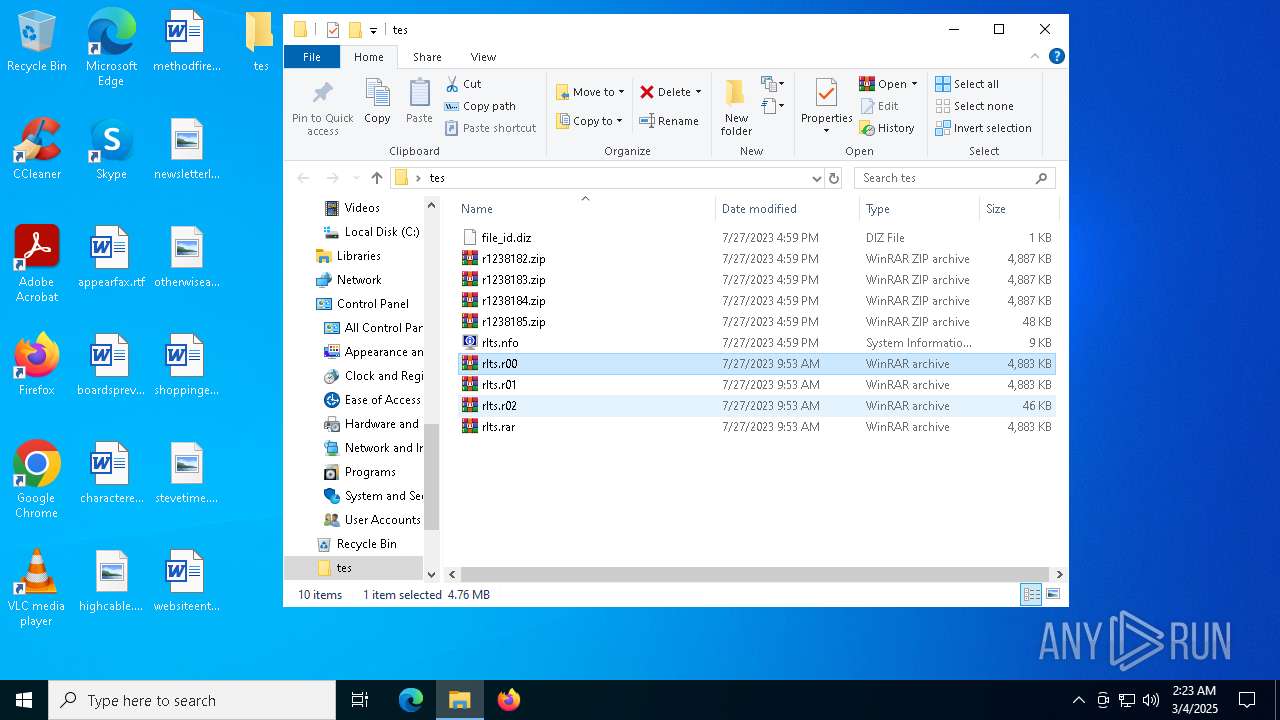
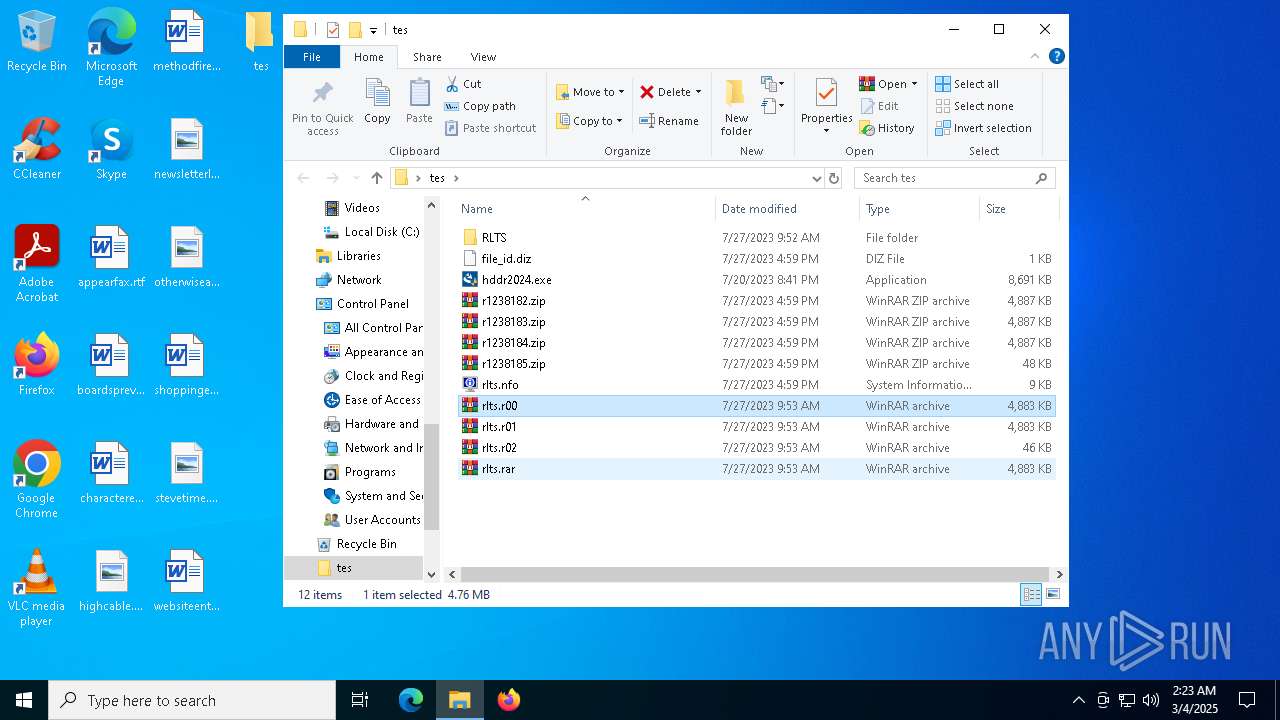
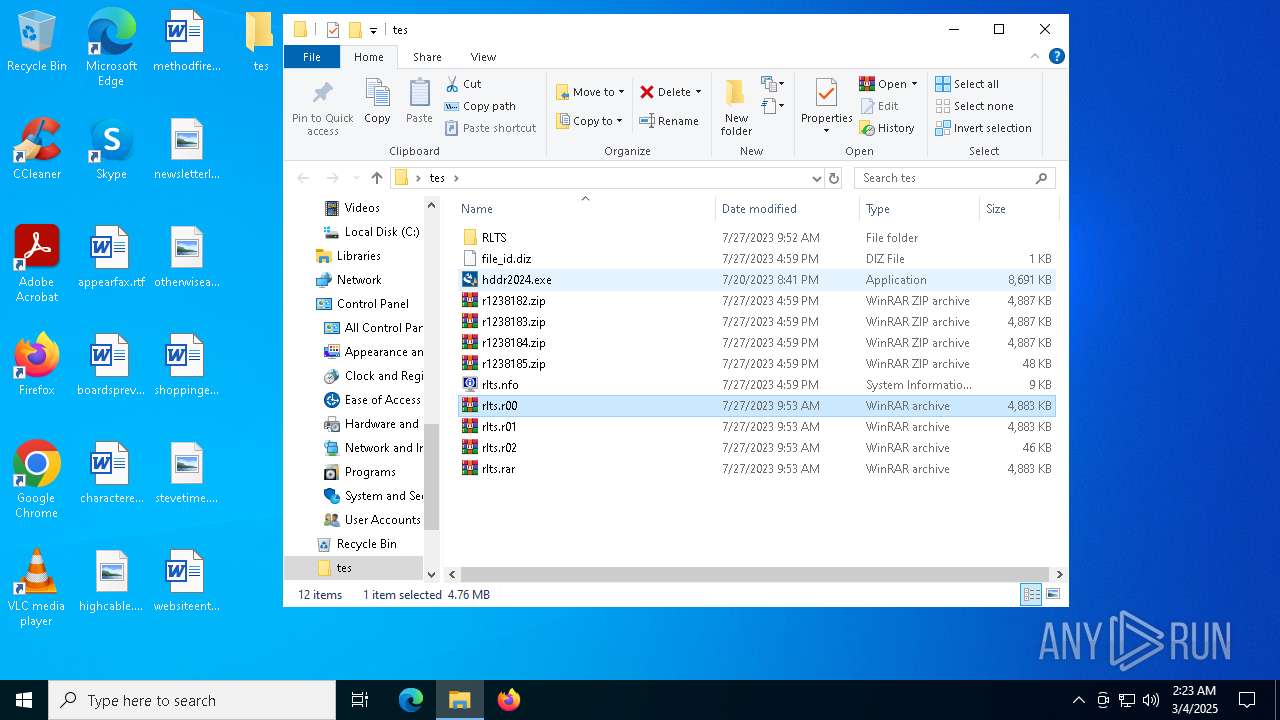
| 6068 | WinRAR.exe | C:\Users\admin\Desktop\tes\rlts.rar | — | |
MD5:— | SHA256:— | |||
| 6068 | WinRAR.exe | C:\Users\admin\Desktop\tes\rlts.r00 | — | |
MD5:— | SHA256:— | |||
| 6068 | WinRAR.exe | C:\Users\admin\Desktop\tes\rlts.r01 | — | |
MD5:— | SHA256:— | |||
| 5260 | WinRAR.exe | C:\Users\admin\Desktop\tes\RLTS\RLTS_deluxe.png | — | |
MD5:— | SHA256:— | |||
| 1272 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:996DA96F7B324AF393887F84E28588CF | SHA256:1C50F1B776319E2A94A083CC14276F5E0BA1F37A8AB6E56A4CBD07D926E72F73 | |||
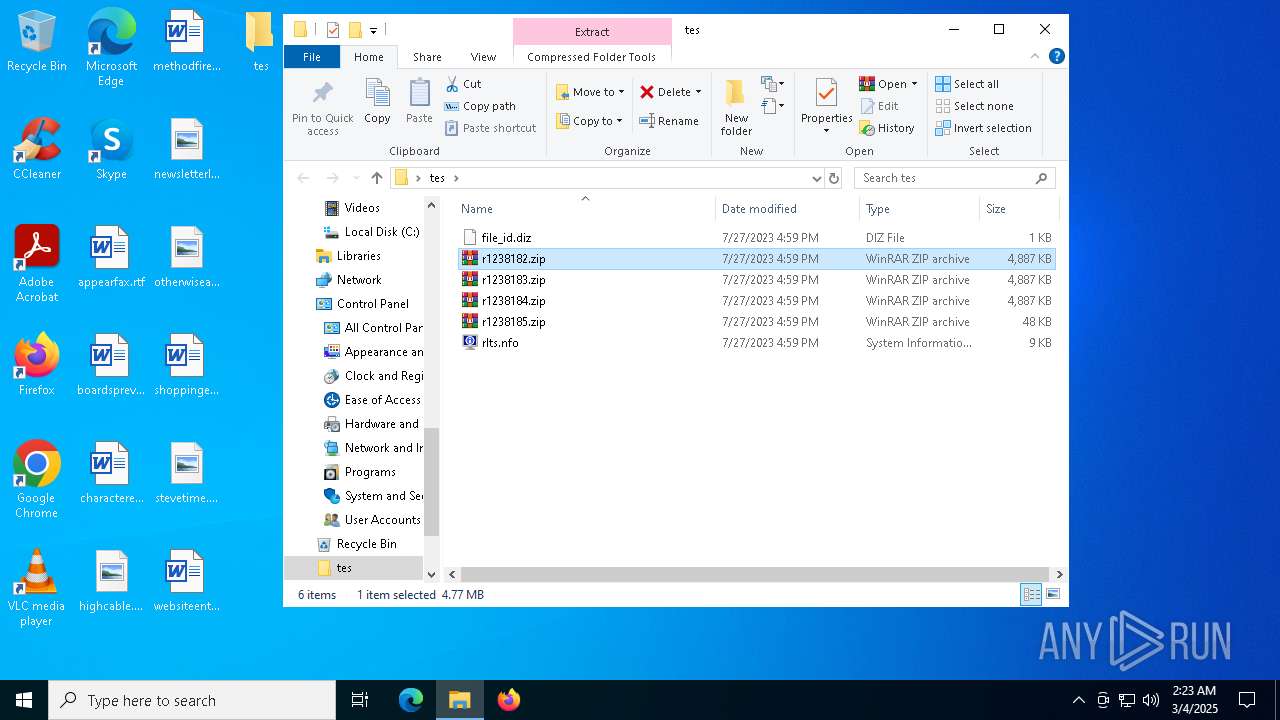
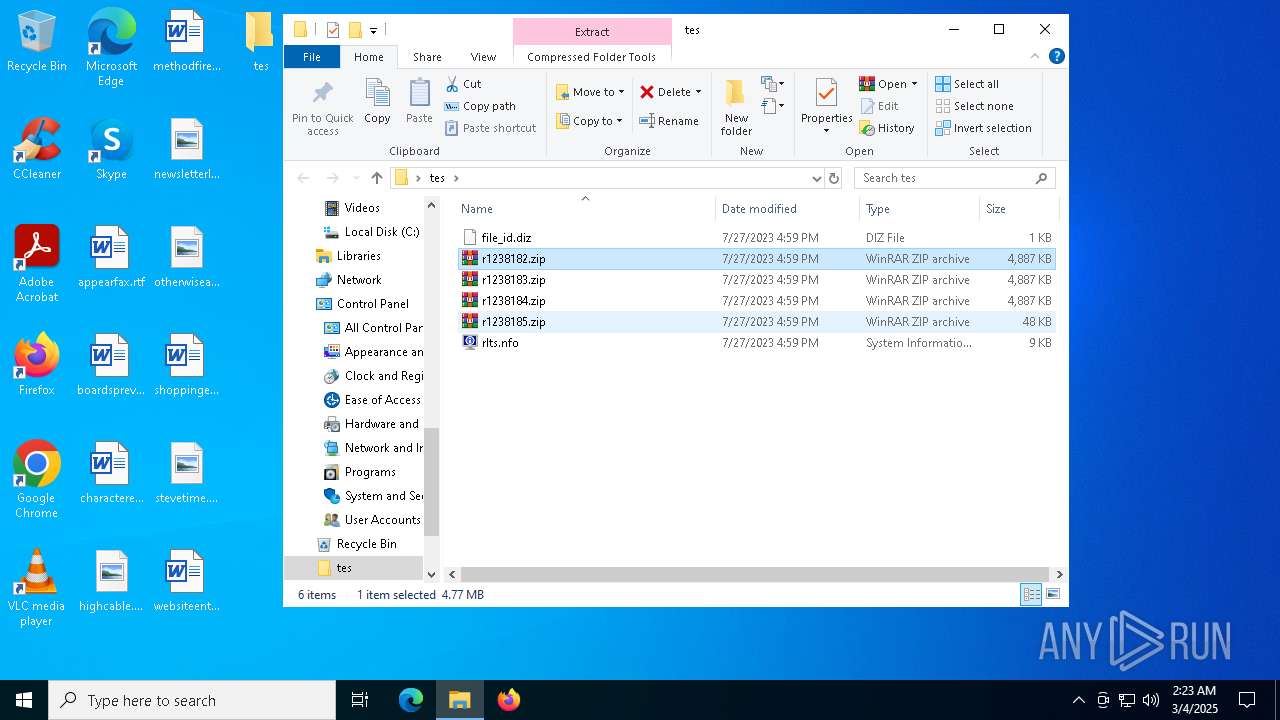
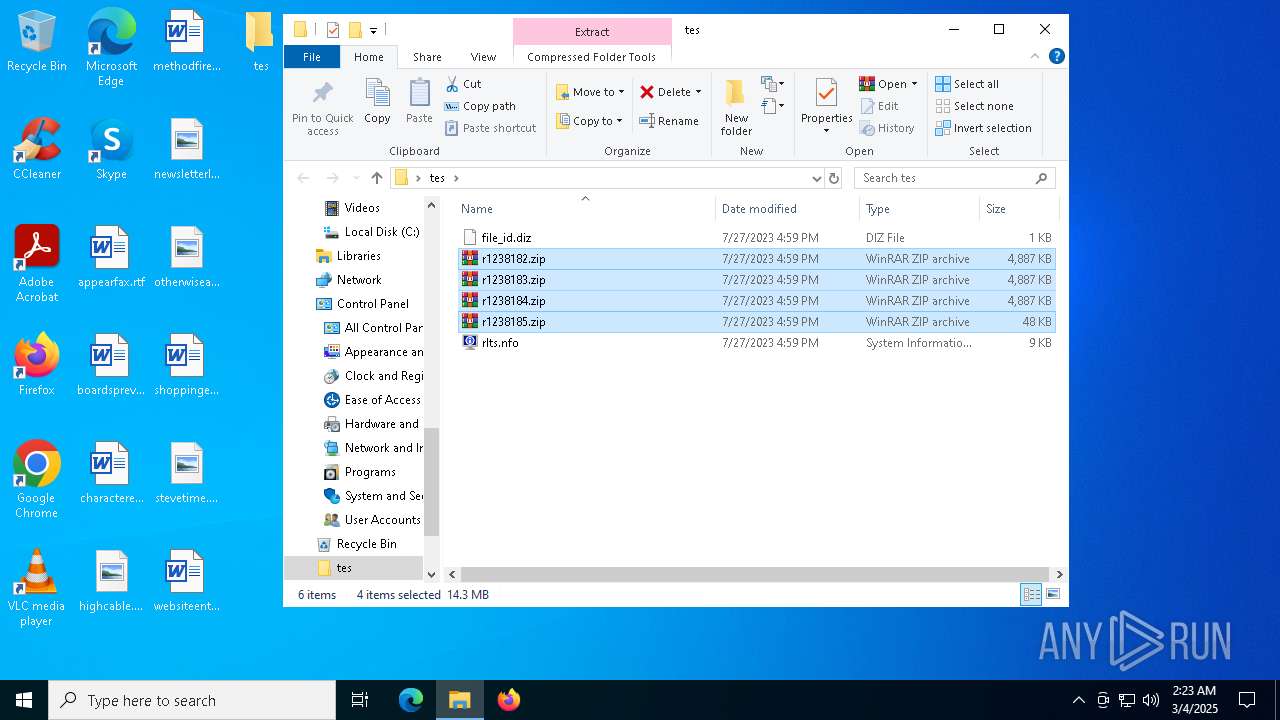
| 5164 | WinRAR.exe | C:\Users\admin\Desktop\tes\r1238185.zip | compressed | |
MD5:4EBFE3332EB7AE75F92DF3AAF03256E4 | SHA256:7FD2F1E1831DBC6DD780F200BECAECC9A699D02128384B7745510AFA072D8289 | |||
| 1272 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\5bc55330-6580-4125-9cfb-12a3622c6fc3.up_meta_secure | binary | |
MD5:220559EBA2226376992ADE955E2B77B4 | SHA256:FDD7121CFE99AF6579DB192E8ED0B8281A586609A286F2569BE667A9C5609078 | |||
| 5164 | WinRAR.exe | C:\Users\admin\Desktop\tes\r1238182.zip | compressed | |
MD5:ABF1F9DB12CAEE06CD2B1255BC65CED3 | SHA256:2299AFB6EDD7E83DD51B58B5F62D302A3E72CCB2EA321F08AC14A11D1B5A04C2 | |||
| 5164 | WinRAR.exe | C:\Users\admin\Desktop\tes\r1238183.zip | compressed | |
MD5:9D1DE714689D61D5D4C698D578E58BE6 | SHA256:2F99236101C52F5CDFEA178AC0D71EA5774EA2CC4CBC083933F79710FDFAE22F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
25
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6272 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5800 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5800 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
968 | msiexec.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGEJFcIpBz28BuO60qVQ%3D | unknown | — | — | whitelisted |
968 | msiexec.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/gsgccr45codesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTLuA3ygnKW%2F7xuSx%2F09F%2BhHVuEUQQU2rONwCSQo2t30wygWd0hZ2R2C3gCDEJCV9JceldyRuYC4Q%3D%3D | unknown | — | — | whitelisted |
1272 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
968 | msiexec.exe | GET | 200 | 151.101.130.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgOhtwj4VKsGchDZBEc%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6272 | backgroundTaskHost.exe | 20.74.47.205:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6272 | backgroundTaskHost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1272 | BackgroundTransferHost.exe | 2.19.96.120:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |