| URL: | https://https.secure-links.bloemlight.com/XaVJmZVNLMGRLQkxCZ0tHNlVpdERJbWpNK1o0alpySkxUZTZTTG5NRnBlbU5vNjlZYWU2aWZGaFJJY2RPcmMvTWNWWnRRSlJtNG0wdHA1blNnbUFqZDJiSlBqdmZwQXR5UjVjZWl1b29RZTJqMHV1K1RaV2tVQVMyV1hlTm5TYWdEdW91MnM5SnBsSFdydTFzLzhFTWs4NURZK3hMclE2SE9kMms0dHJxcldsZGtFMnRqZ3Y2YnFRcDJSc3pEd2RIbURlZ3VRRWFOWE9YOUJDWENoaklxcmdqYlJYQi0tVVJTVjdMd3BjT0pQYTlQby0tZy9hRGs4VFB4MU9Wd0ladFRqbXFhdz09?cid=2905659352 |
| Full analysis: | https://app.any.run/tasks/a2b0fab0-b738-4353-a9a1-3e8f89093c55 |
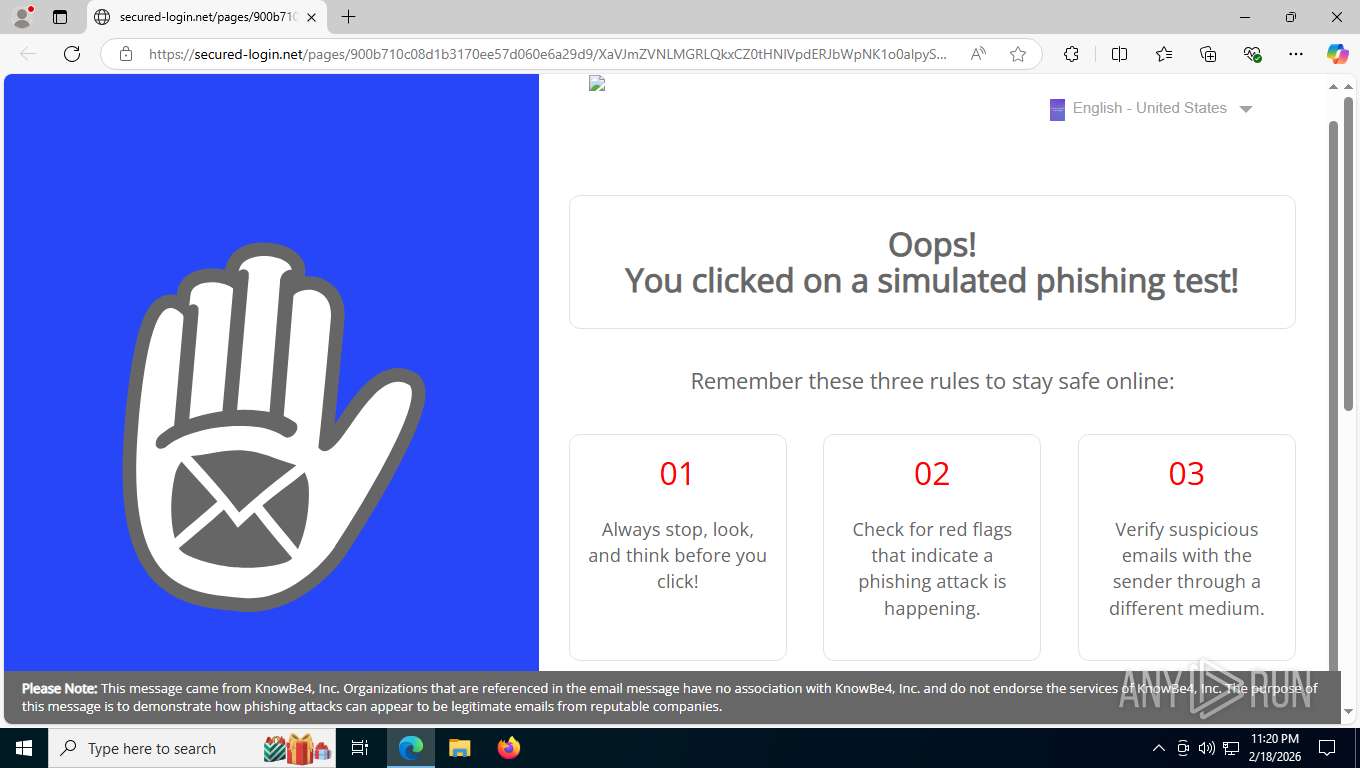
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2026, 04:20:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E0802B33763135F60FDBD347634CB181 |
| SHA1: | 7DC72F22E2DE0B130CADE1C826A899E1A3EA208D |
| SHA256: | F19D301426015FD0027AC0B4823559ECB1A35F7D2062C4FBBDF1DA6D301F97B8 |
| SSDEEP: | 6:2jaDRf/LyfmqUCQIzi/8P8SRqup1kSR1Jtg/RXCIxTsv5VThhTG1:2jyRfDyfDUCJb8SBpSSR1Xg/RVTUx32 |
MALICIOUS
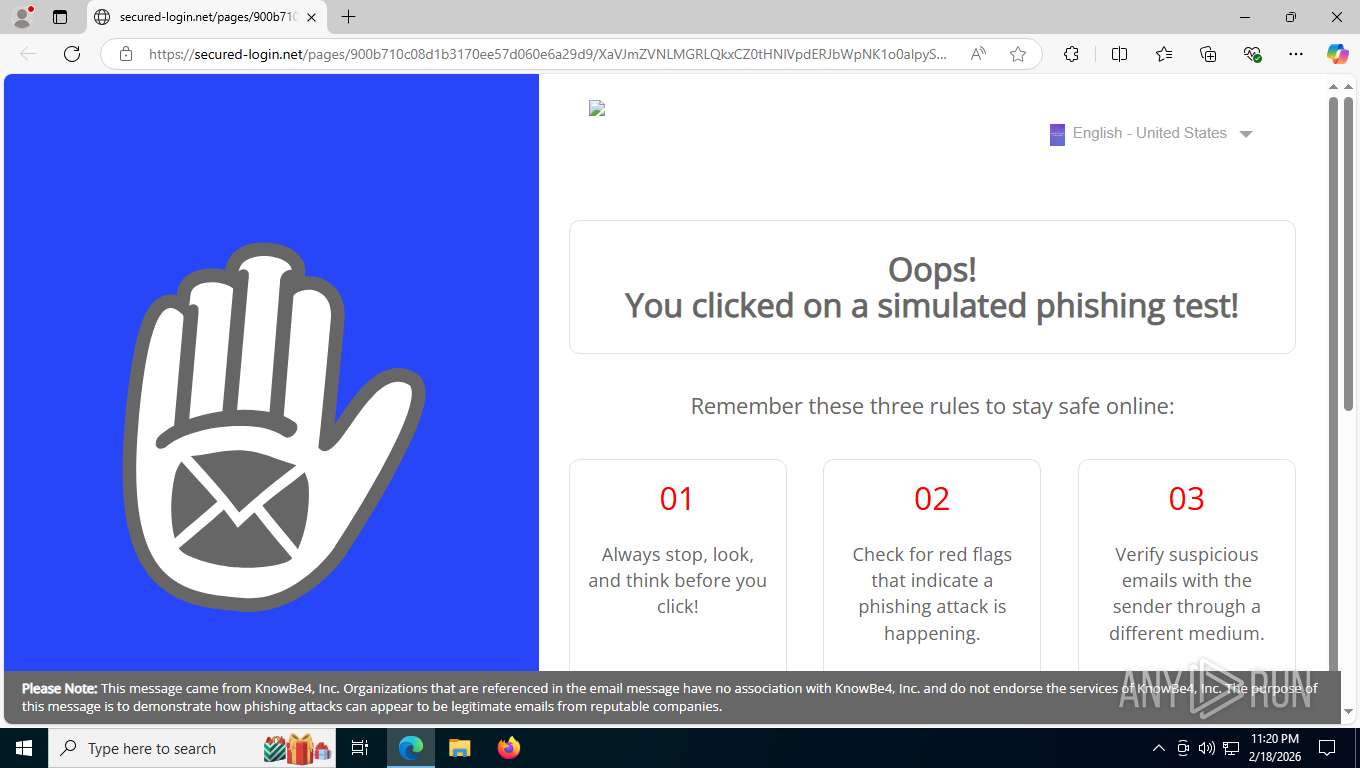
KNOWBE4 has been detected (SURICATA)
- msedge.exe (PID: 8120)
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 8120)
SUSPICIOUS
The process connected to a server suspected of theft
- msedge.exe (PID: 8120)
INFO
Checks supported languages
- identity_helper.exe (PID: 4516)
Reads the computer name
- identity_helper.exe (PID: 4516)
Drops script file
- msedge.exe (PID: 3652)
Reads Environment values
- identity_helper.exe (PID: 4516)
Application launched itself
- msedge.exe (PID: 3652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
169
Monitored processes
21
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1868 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3704,i,11620589701421276011,8174329420087343685,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3808 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3660,i,11620589701421276011,8174329420087343685,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3684 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2448 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3600,i,11620589701421276011,8174329420087343685,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3544 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3440 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3652 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --disable-features=HttpsUpgrades,HttpsFirstModeV2,HttpsOnlyMode,HttpsFirstBalancedMode --no-first-run --no-default-browser-check https://https.secure-links.bloemlight.com/XaVJmZVNLMGRLQkxCZ0tHNlVpdERJbWpNK1o0alpySkxUZTZTTG5NRnBlbU5vNjlZYWU2aWZGaFJJY2RPcmMvTWNWWnRRSlJtNG0wdHA1blNnbUFqZDJiSlBqdmZwQXR5UjVjZWl1b29RZTJqMHV1K1RaV2tVQVMyV1hlTm5TYWdEdW91MnM5SnBsSFdydTFzLzhFTWs4NURZK3hMclE2SE9kMms0dHJxcldsZGtFMnRqZ3Y2YnFRcDJSc3pEd2RIbURlZ3VRRWFOWE9YOUJDWENoaklxcmdqYlJYQi0tVVJTVjdMd3BjT0pQYTlQby0tZy9hRGs4VFB4MU9Wd0ladFRqbXFhdz09?cid=2905659352 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 4516 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6320,i,11620589701421276011,8174329420087343685,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6384 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5784,i,11620589701421276011,8174329420087343685,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5780 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5716 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=4108,i,11620589701421276011,8174329420087343685,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3560 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 5992 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6320,i,11620589701421276011,8174329420087343685,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6384 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 6172 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5796,i,11620589701421276011,8174329420087343685,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5912 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
557
Read events
557
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
11
Text files
42
Unknown types
80
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e532f.TMP | — | |
MD5:— | SHA256:— | |||
| 3652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e533e.TMP | — | |
MD5:— | SHA256:— | |||
| 3652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e534e.TMP | — | |
MD5:— | SHA256:— | |||
| 3652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e534e.TMP | — | |
MD5:— | SHA256:— | |||
| 3652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e535d.TMP | — | |
MD5:— | SHA256:— | |||
| 3652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3652 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e535d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
94
TCP/UDP connections
81
DNS requests
66
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | unknown | — | — | whitelisted |
8120 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:MT8oPM1v8pZPWSBY3aOljUNMU8JDPyidCCaPE3YM5L4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
8120 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 295 b | whitelisted |
8120 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | text | 25 b | whitelisted |
8120 | msedge.exe | GET | 200 | 13.107.213.38:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | unknown | binary | 82 b | whitelisted |
8120 | msedge.exe | GET | 200 | 52.123.243.88:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | unknown | binary | 4.47 Kb | whitelisted |
8120 | msedge.exe | GET | 200 | 18.215.216.36:443 | https://https.secure-links.bloemlight.com/XaVJmZVNLMGRLQkxCZ0tHNlVpdERJbWpNK1o0alpySkxUZTZTTG5NRnBlbU5vNjlZYWU2aWZGaFJJY2RPcmMvTWNWWnRRSlJtNG0wdHA1blNnbUFqZDJiSlBqdmZwQXR5UjVjZWl1b29RZTJqMHV1K1RaV2tVQVMyV1hlTm5TYWdEdW91MnM5SnBsSFdydTFzLzhFTWs4NURZK3hMclE2SE9kMms0dHJxcldsZGtFMnRqZ3Y2YnFRcDJSc3pEd2RIbURlZ3VRRWFOWE9YOUJDWENoaklxcmdqYlJYQi0tVVJTVjdMd3BjT0pQYTlQby0tZy9hRGs4VFB4MU9Wd0ladFRqbXFhdz09?cid=2905659352 | unknown | binary | 521 b | unknown |
8120 | msedge.exe | GET | 200 | 100.28.31.195:443 | https://secured-login.net/pages/900b710c08d1b3170ee57d060e6a29d9/XaVJmZVNLMGRLQkxCZ0tHNlVpdERJbWpNK1o0alpySkxUZTZTTG5NRnBlbU5vNjlZYWU2aWZGaFJJY2RPcmMvTWNWWnRRSlJtNG0wdHA1blNnbUFqZDJiSlBqdmZwQXR5UjVjZWl1b29RZTJqMHV1K1RaV2tVQVMyV1hlTm5TYWdEdW91MnM5SnBsSFdydTFzLzhFTWs4NURZK3hMclE2SE9kMms0dHJxcldsZGtFMnRqZ3Y2YnFRcDJSc3pEd2RIbURlZ3VRRWFOWE9YOUJDWENoaklxcmdqYlJYQi0tVVJTVjdMd3BjT0pQYTlQby0tZy9hRGs4VFB4MU9Wd0ladFRqbXFhdz09 | unknown | binary | 109 Kb | unknown |
8120 | msedge.exe | GET | 200 | 52.123.243.88:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeRuntime%2CEdgeRuntimeConfig%2CEdgeDomainActions&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1771474843&lafgdate=0 | unknown | binary | 41.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
9088 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
9072 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 184.86.251.22:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5568 | SearchApp.exe | 184.86.251.27:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 184.86.251.27:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8120 | msedge.exe | Misc activity | ET INFO Observed DNS Query to KnowBe4 Simulated Phish Domain (bloemlight .com) |
8120 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] KnowBe4: Security Awareness Training (secured-login. net) |
8120 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] KnowBe4: Security Awareness Training (secured-login. net) |
8120 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
8120 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
8120 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
8120 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
8120 | msedge.exe | Successful Credential Theft Detected | ET INFO Observed KnowBe4/Popcorn Training Simulated Phish Landing Page M2 |
8120 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
8120 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |