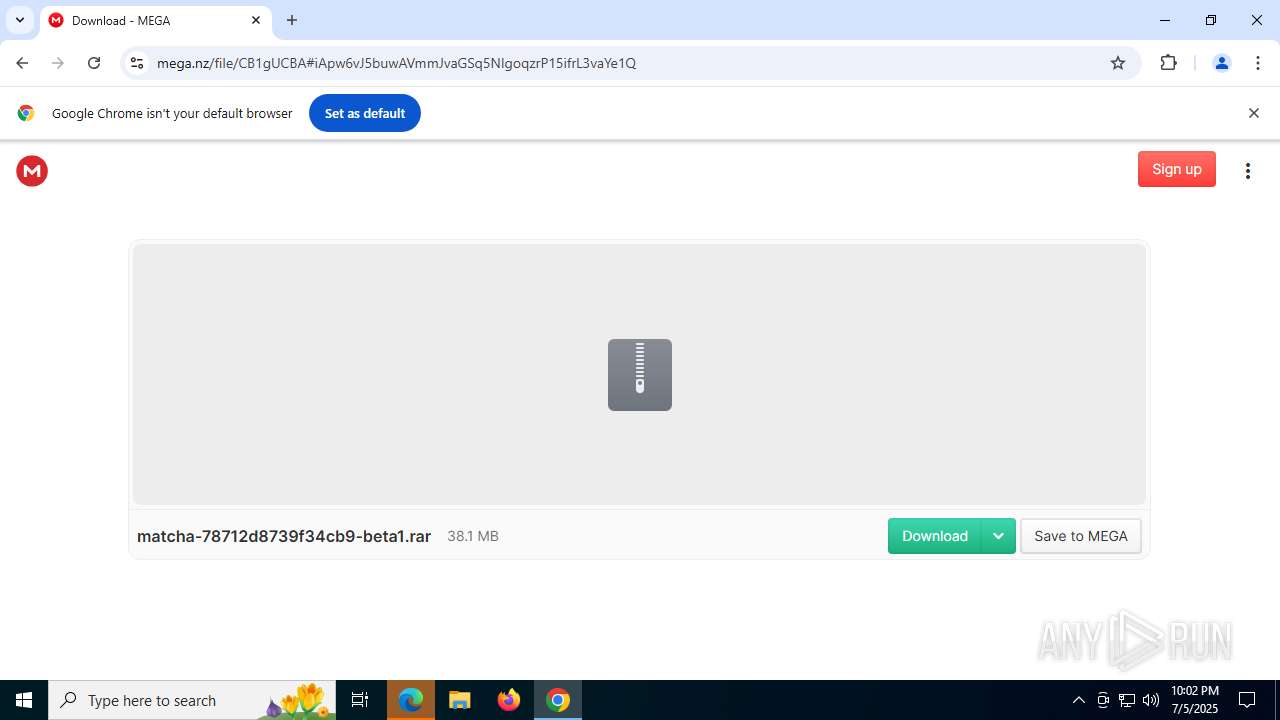
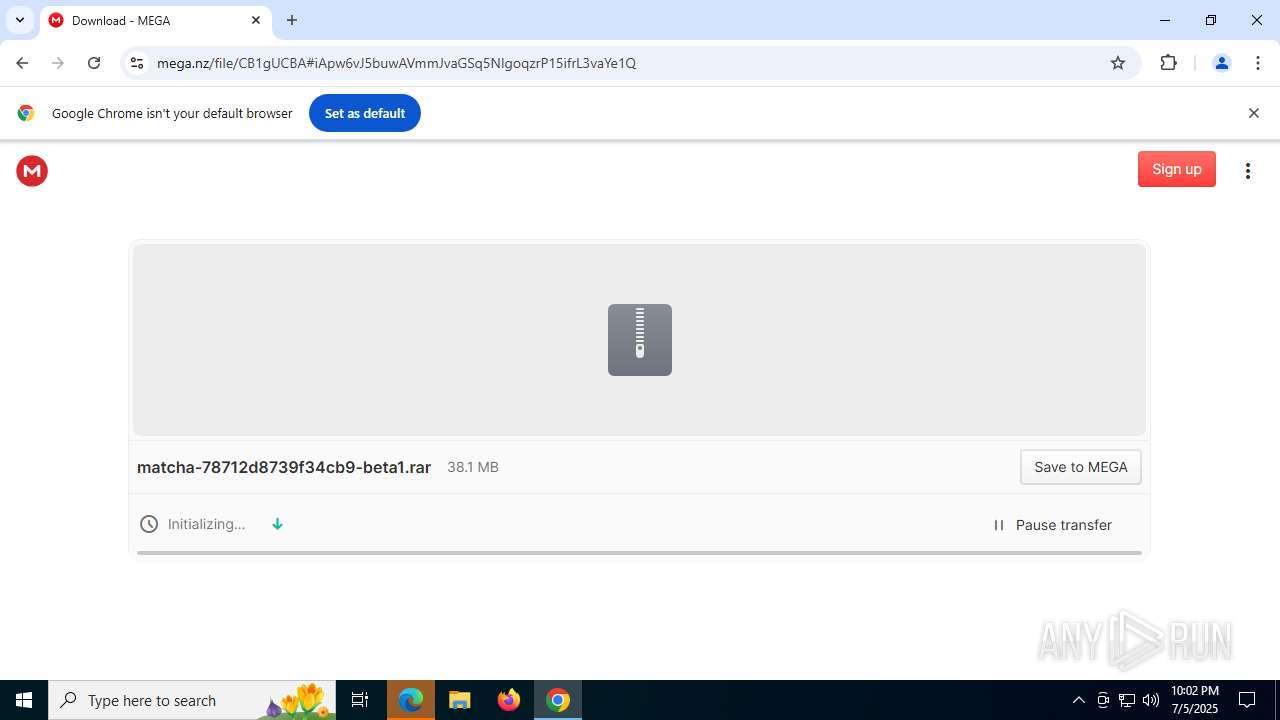
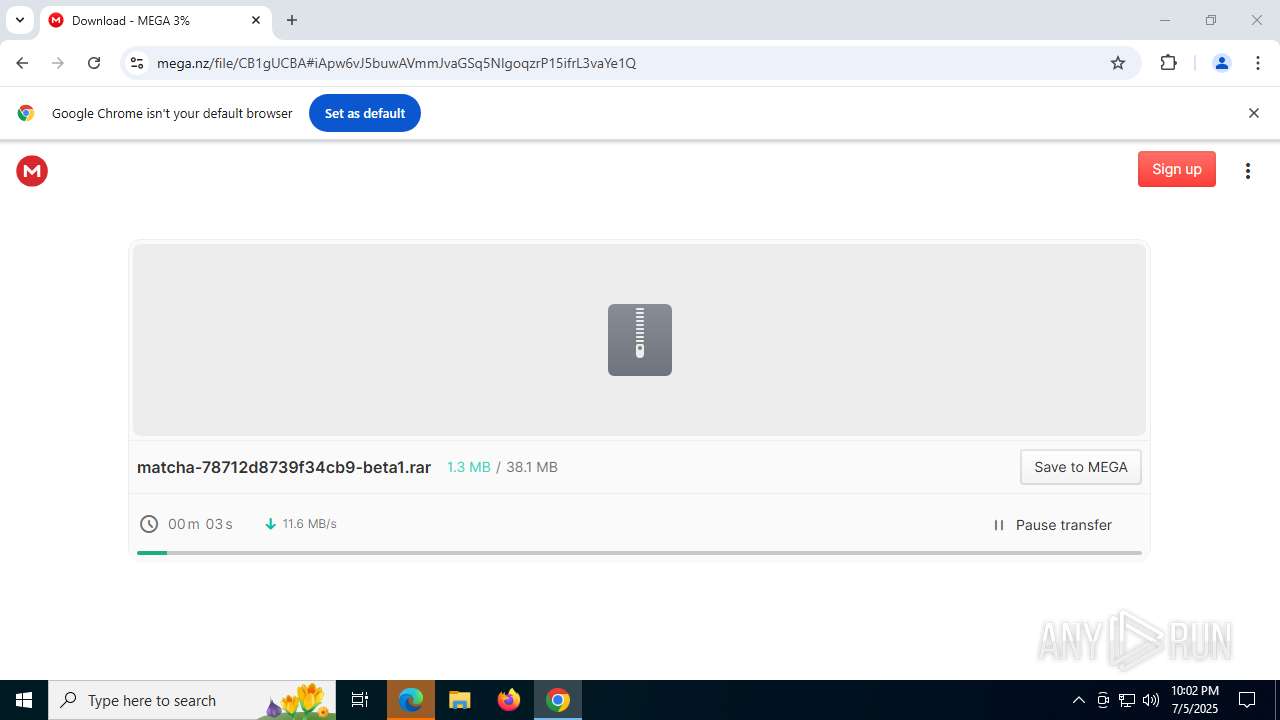
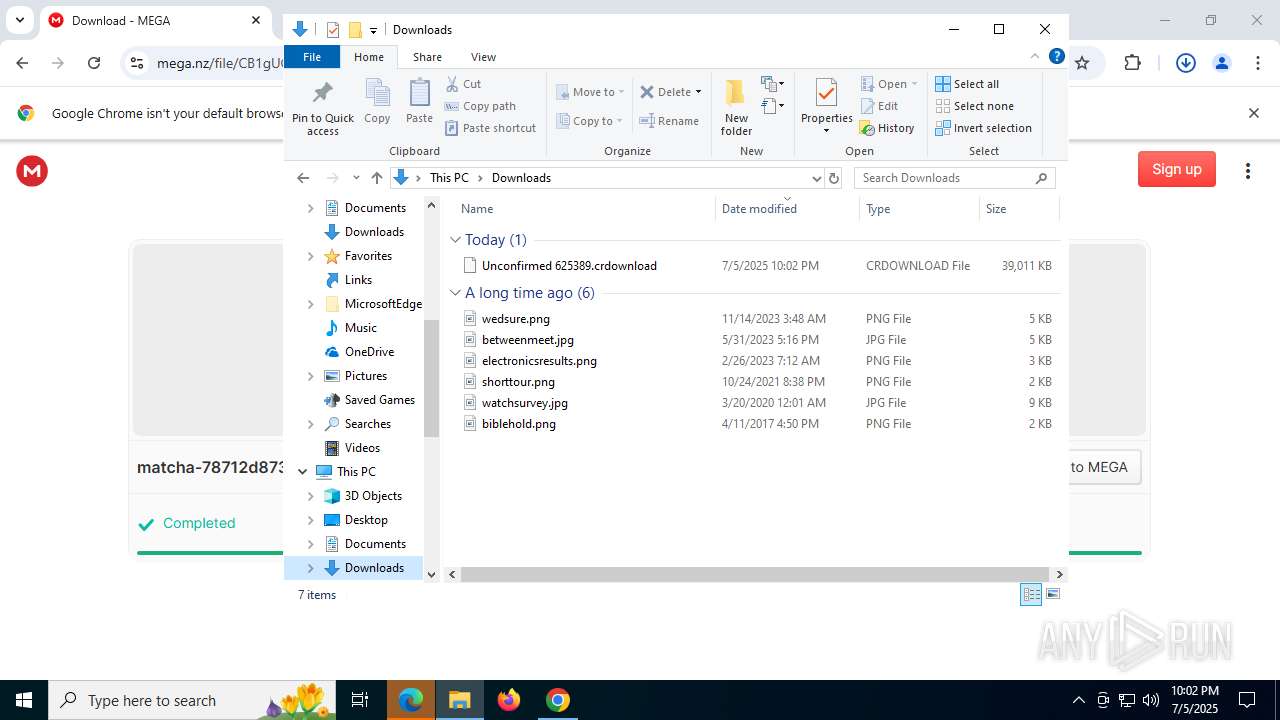
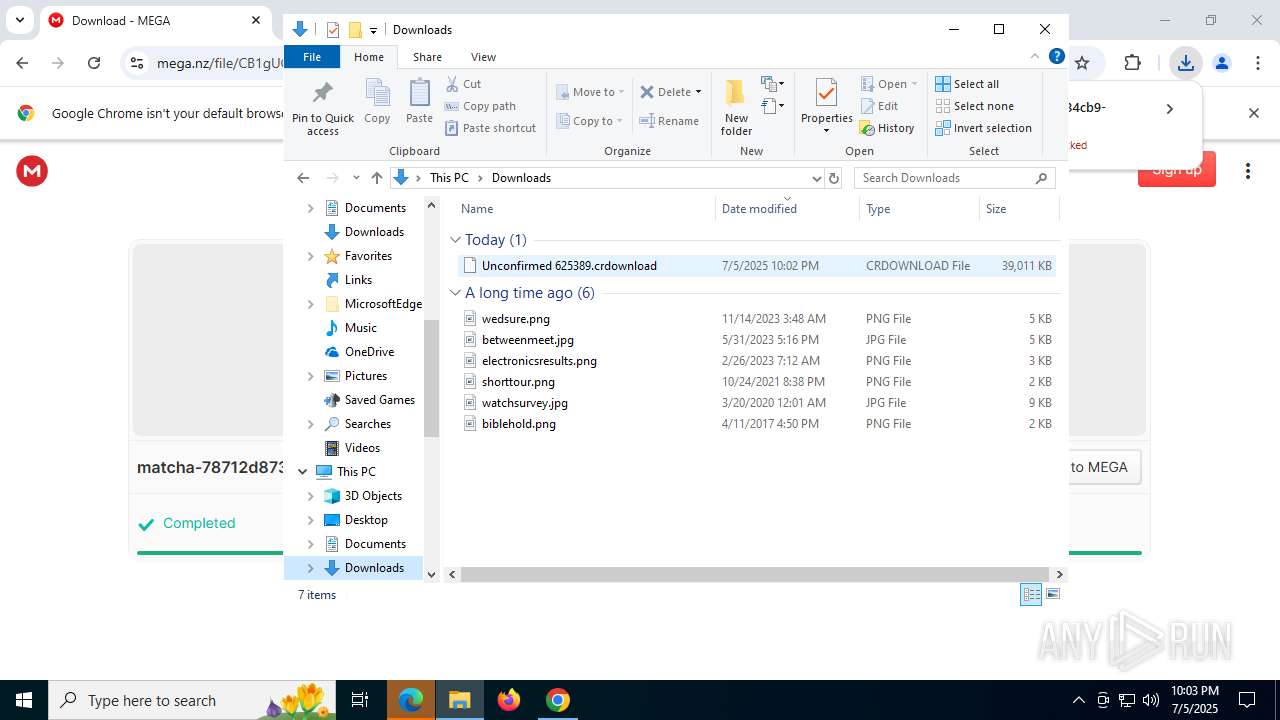
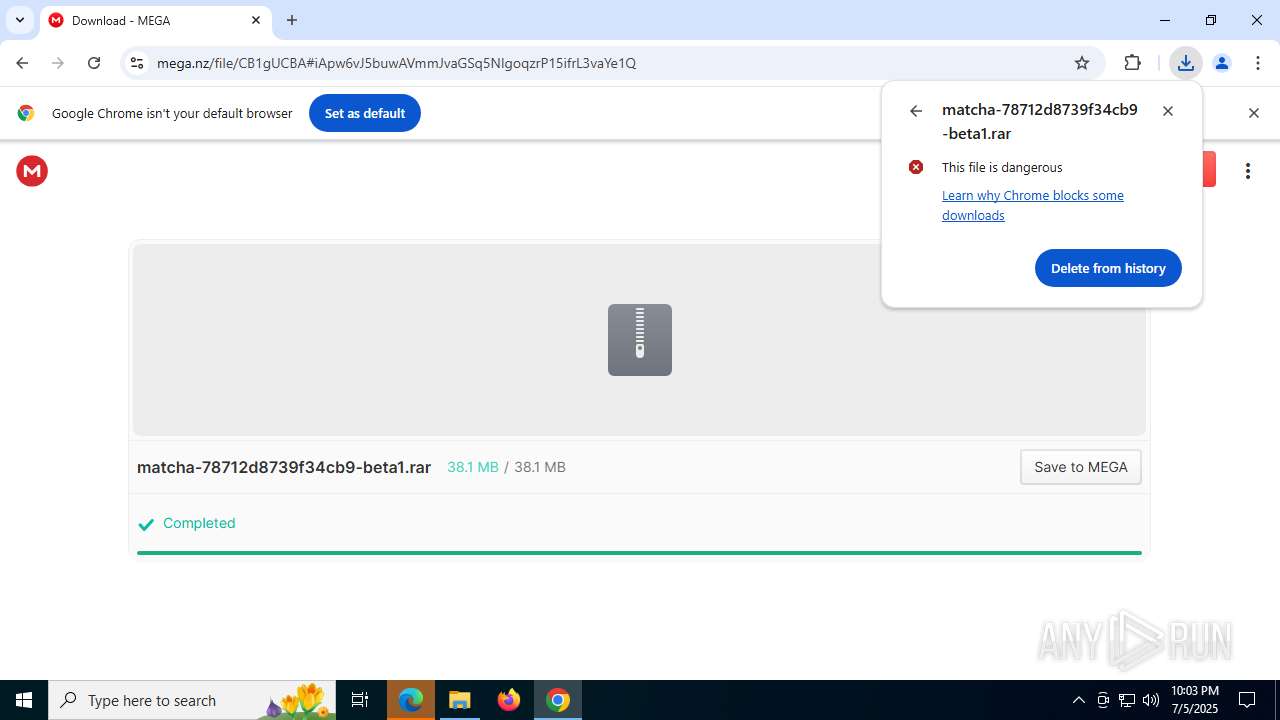
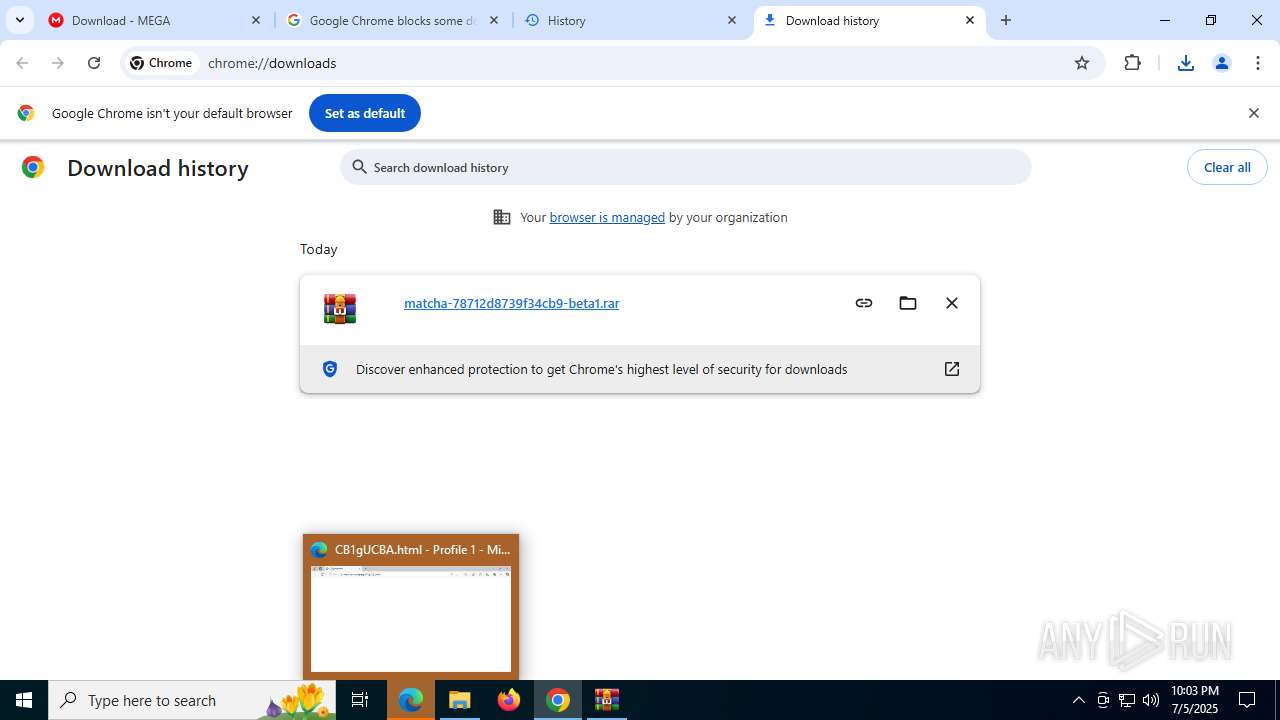
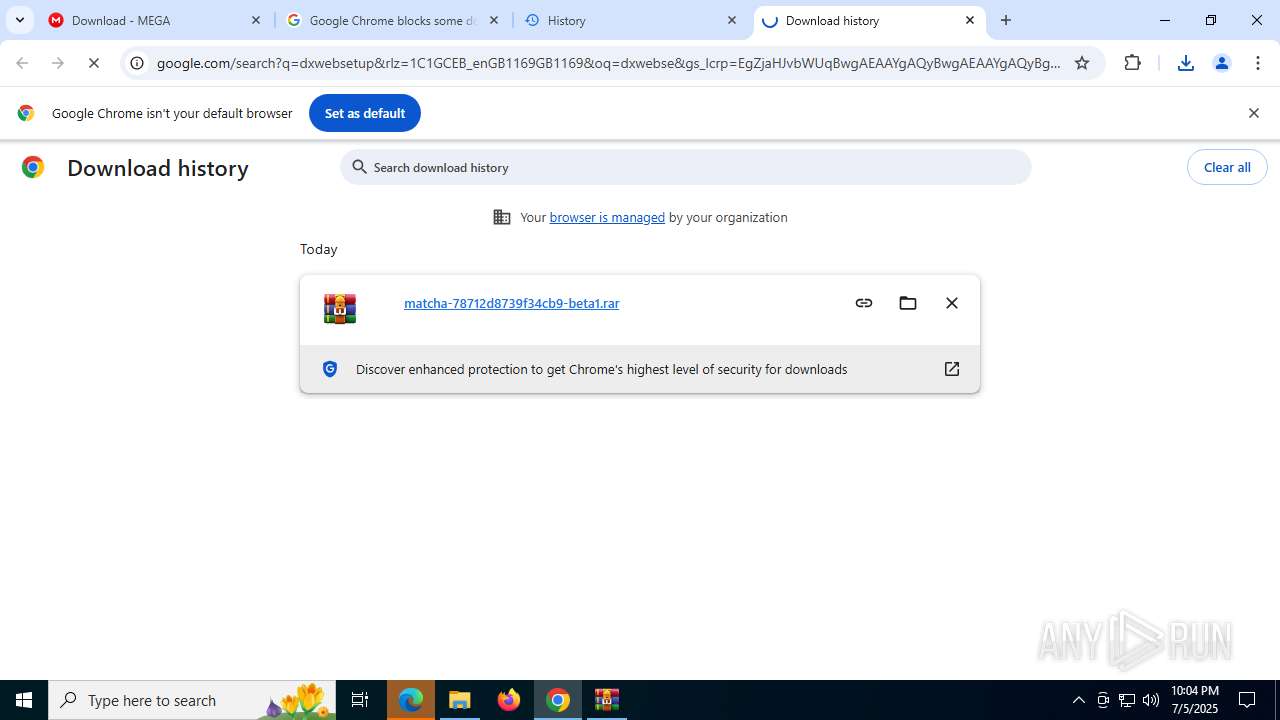
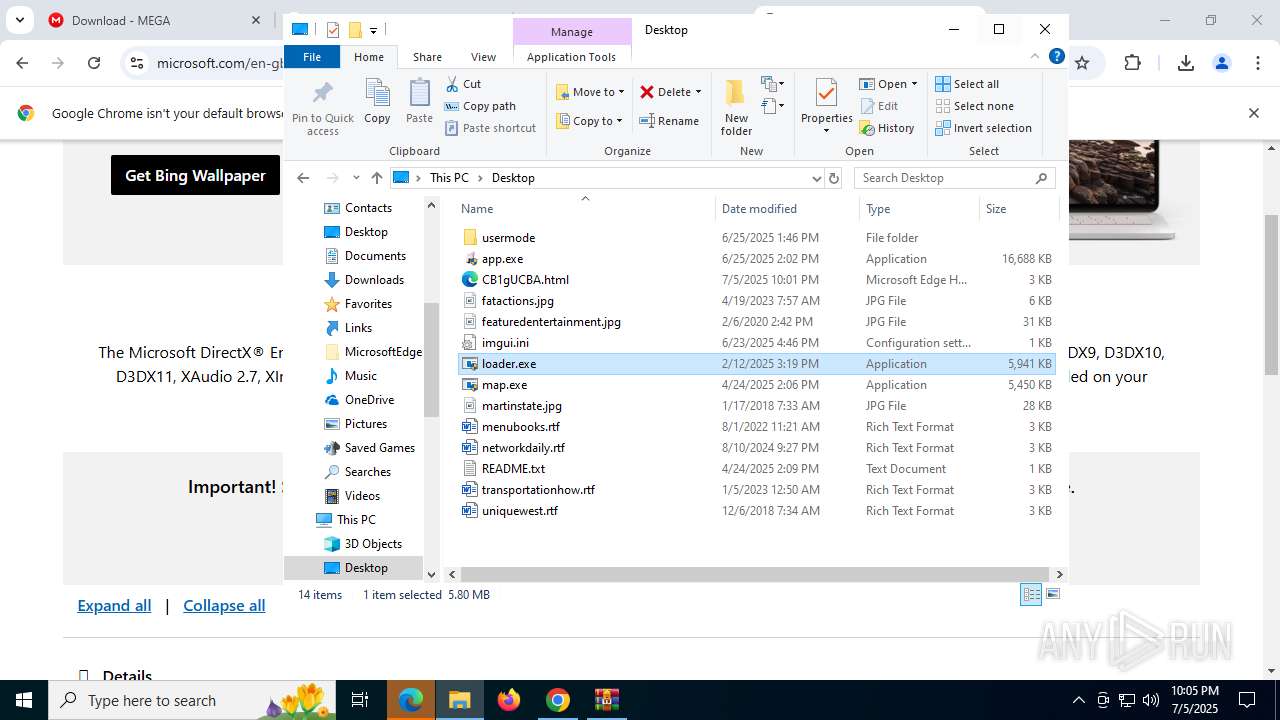
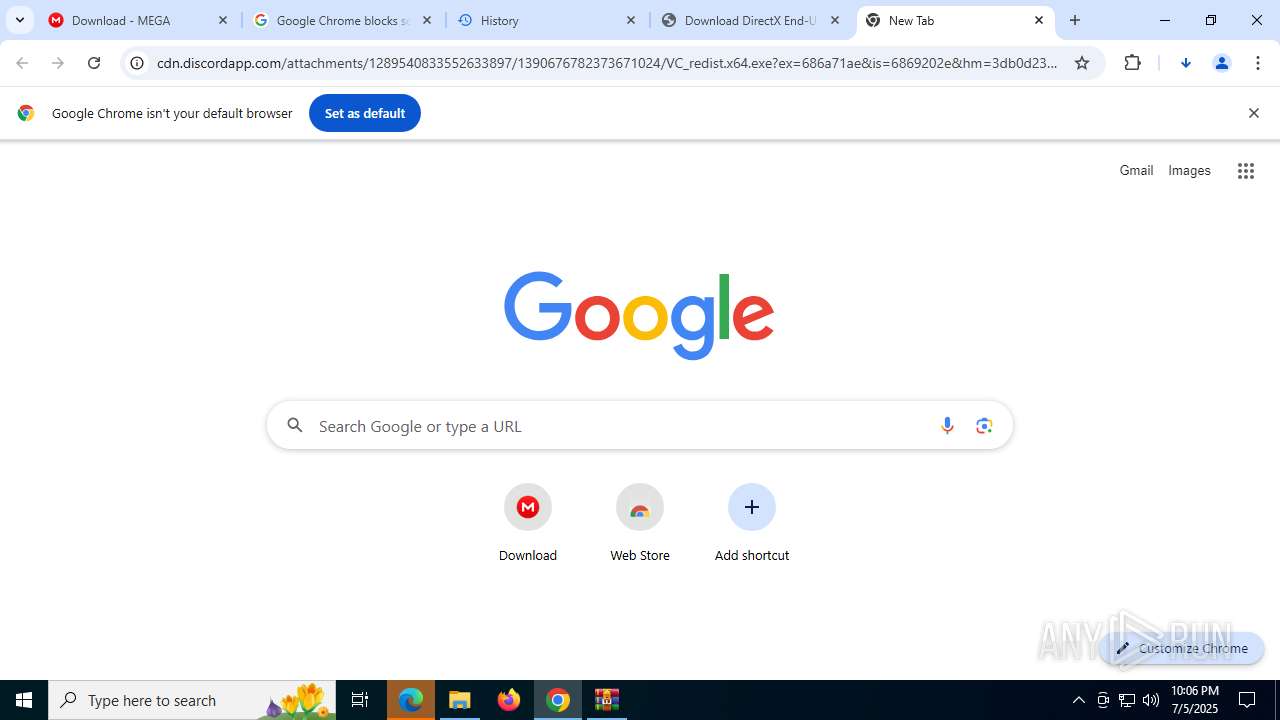
| download: | /file/CB1gUCBA |
| Full analysis: | https://app.any.run/tasks/2764bbf9-a74a-4972-9de9-07f99d166643 |
| Verdict: | Malicious activity |
| Analysis date: | July 05, 2025, 22:01:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text |
| MD5: | EE6EA5E10117799DCDEEF2F17D24F465 |
| SHA1: | 9FD629C50637AB3C378D4B821BFBDCA01C4C3B21 |
| SHA256: | F193CF8098AEB5A23CE79E92D4D4CC545B7ED80A0F792B331021DC77D970098B |
| SSDEEP: | 48:/VvlymuqrI4LVs2Jf8NrIU3P3msU/FUjG:/jHf8B8sU/FUjG |
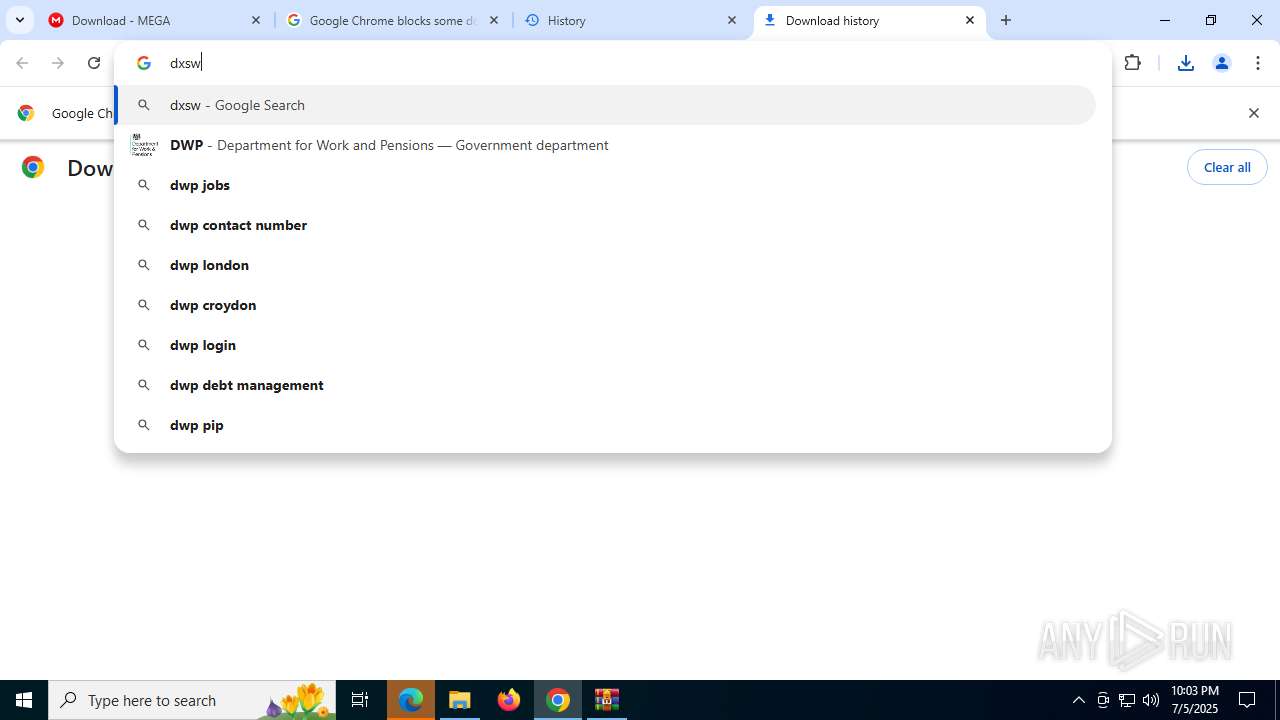
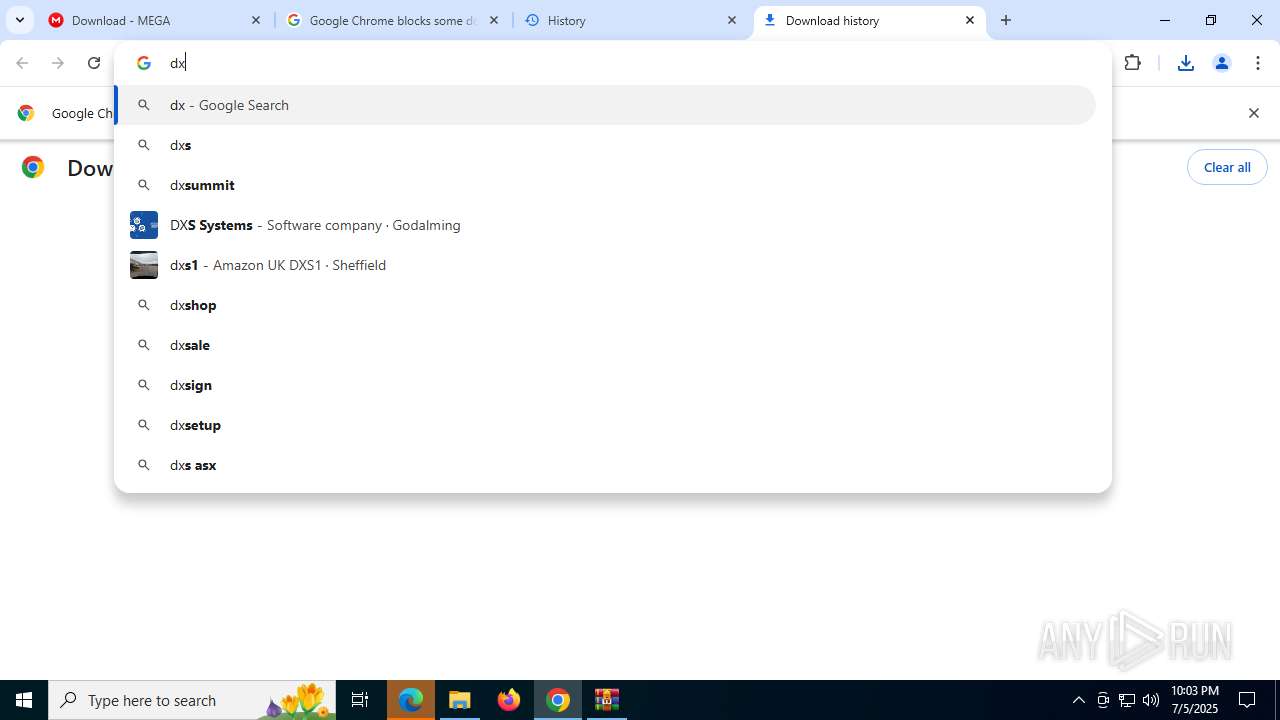
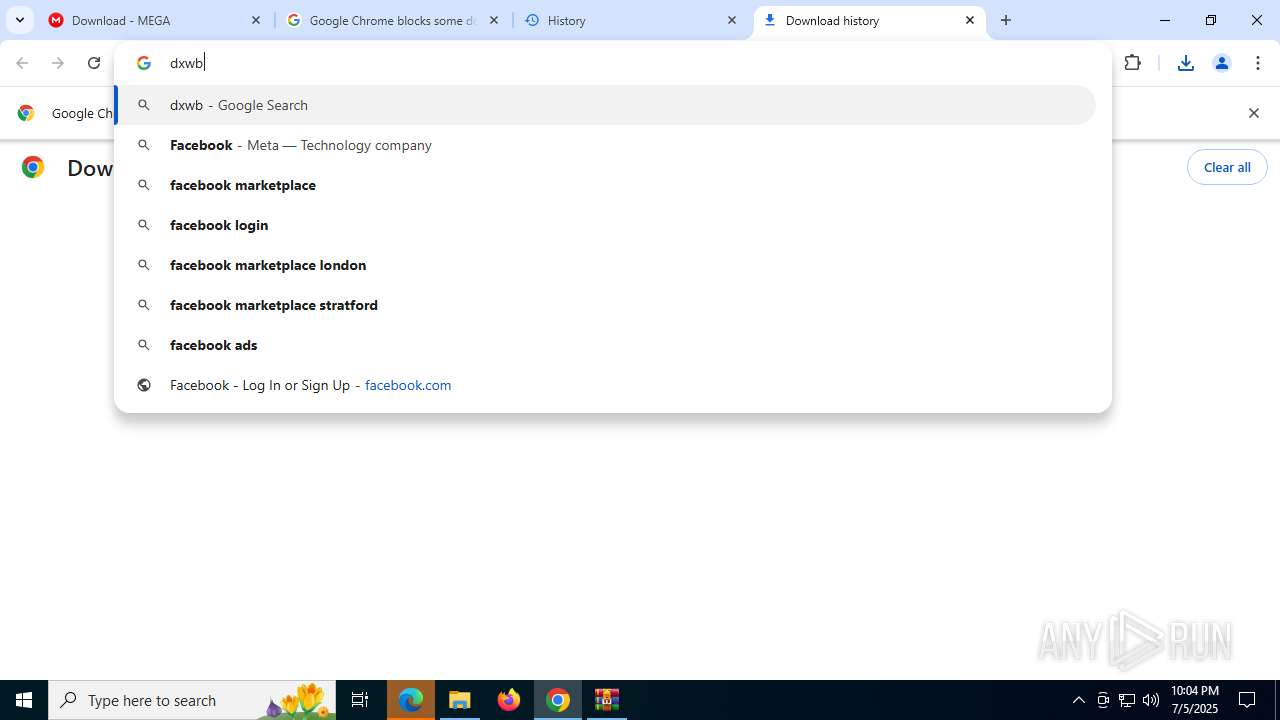
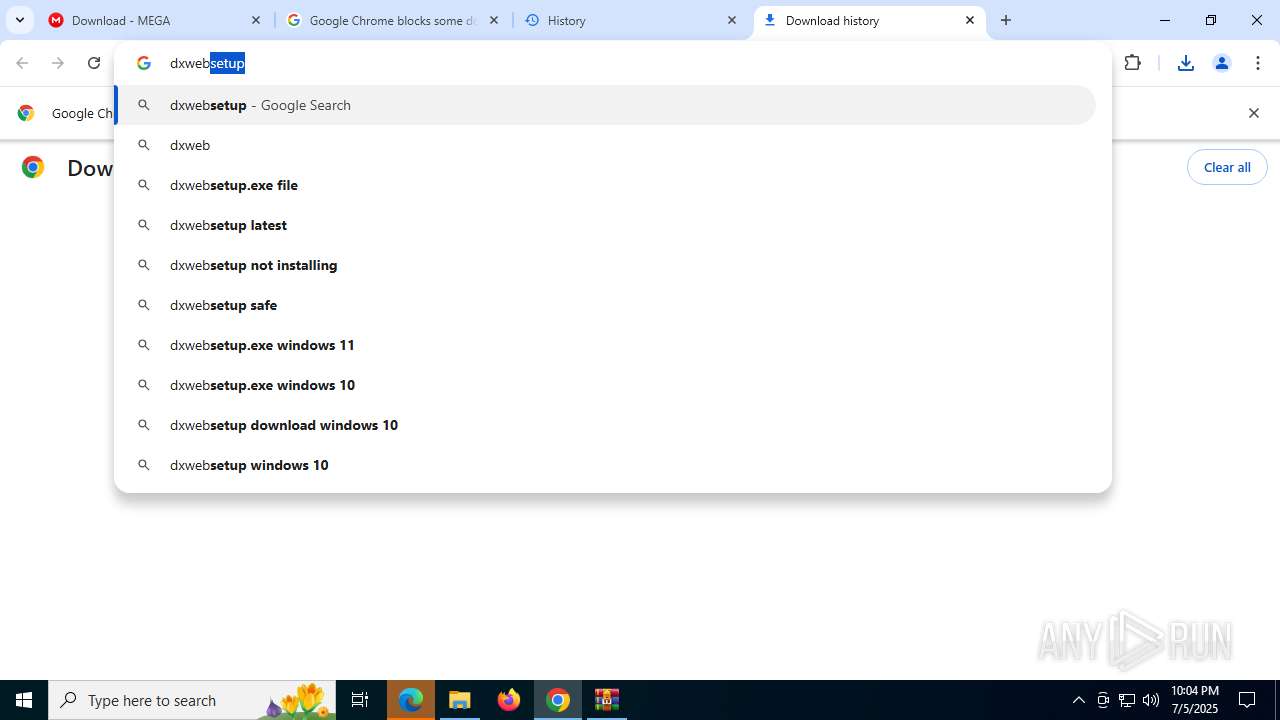
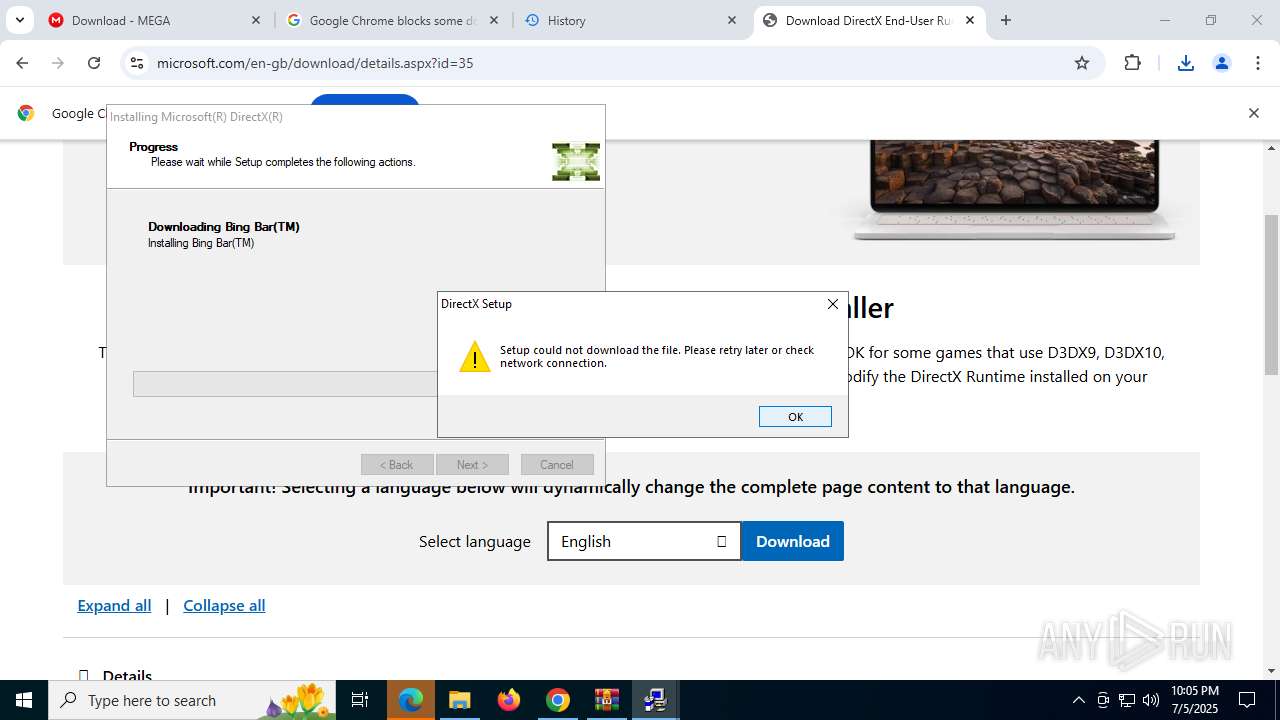
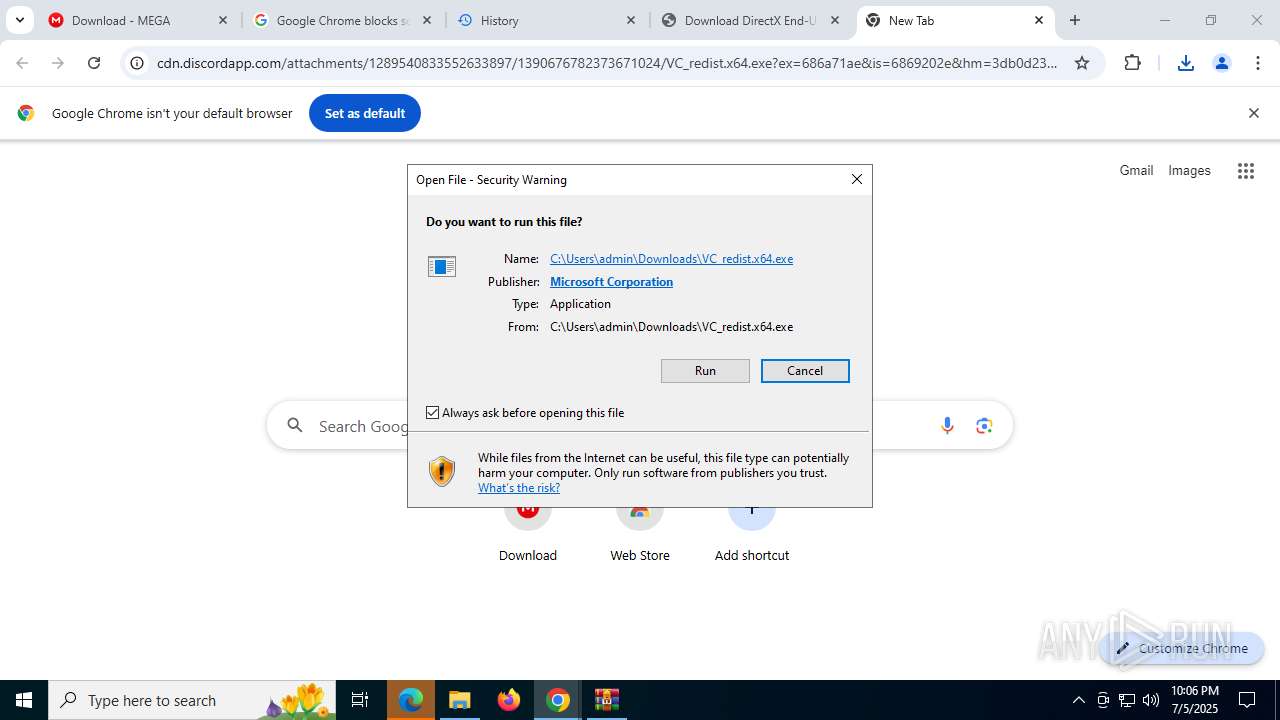
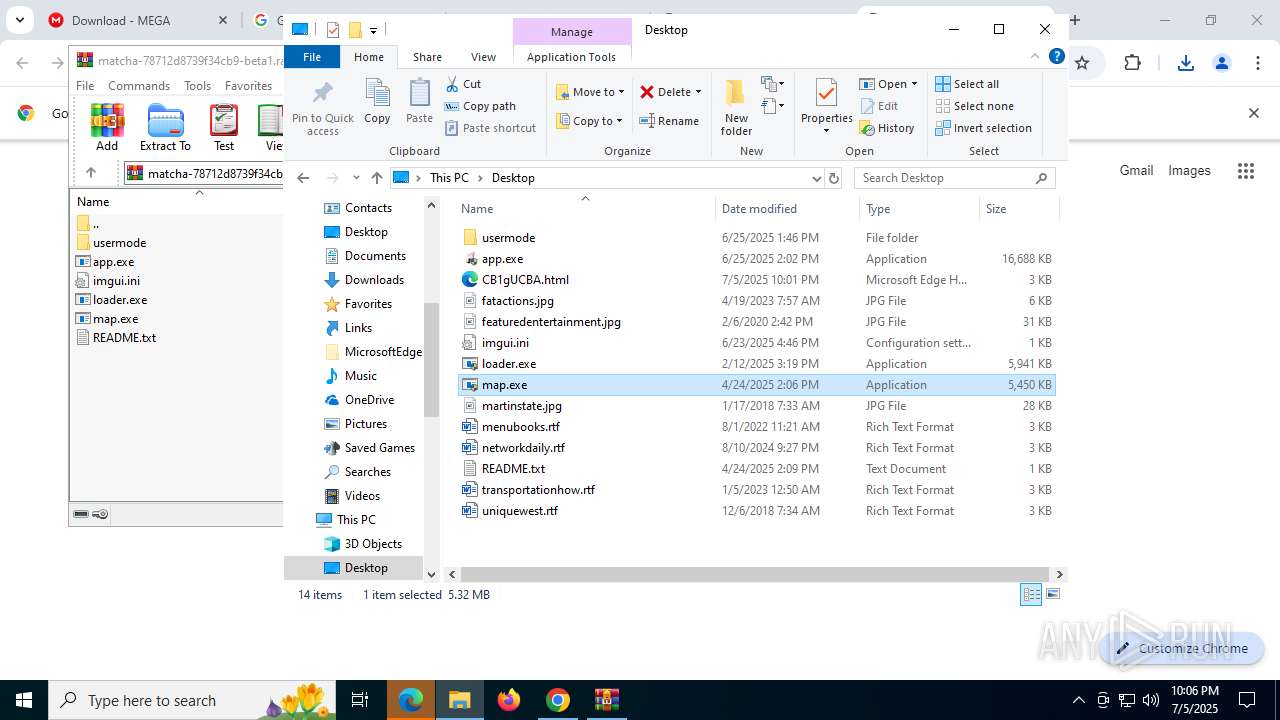
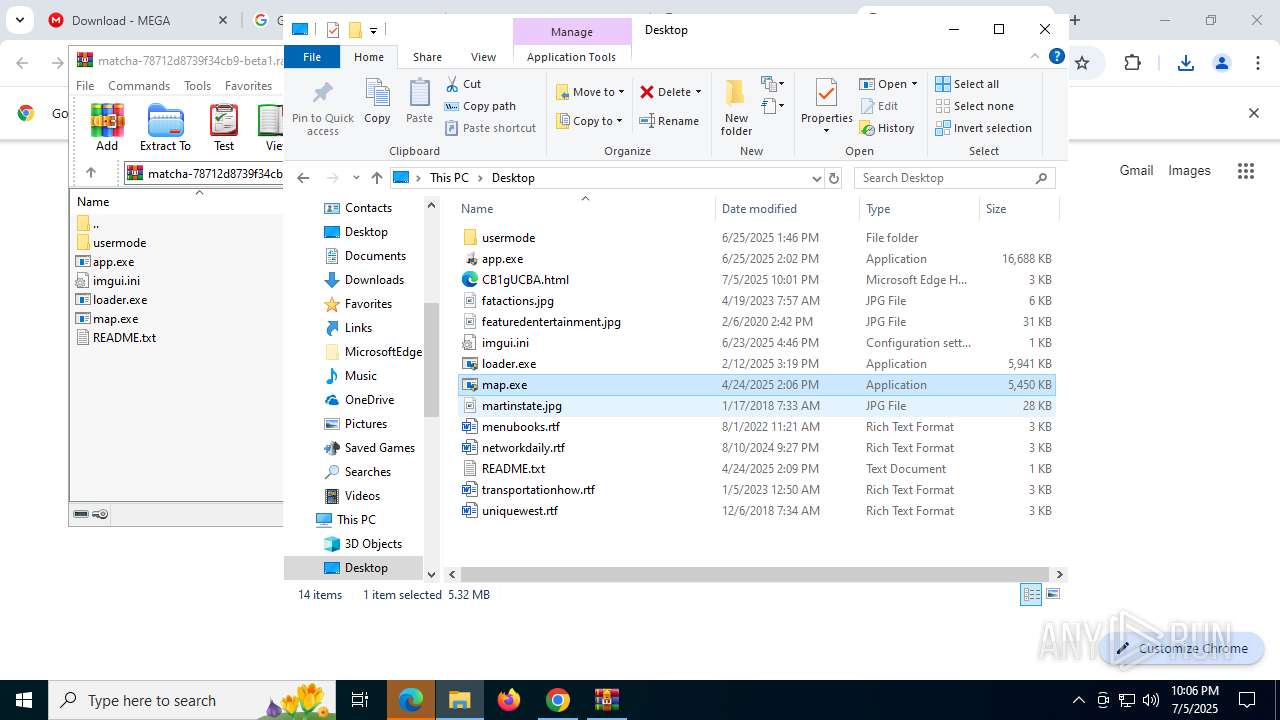
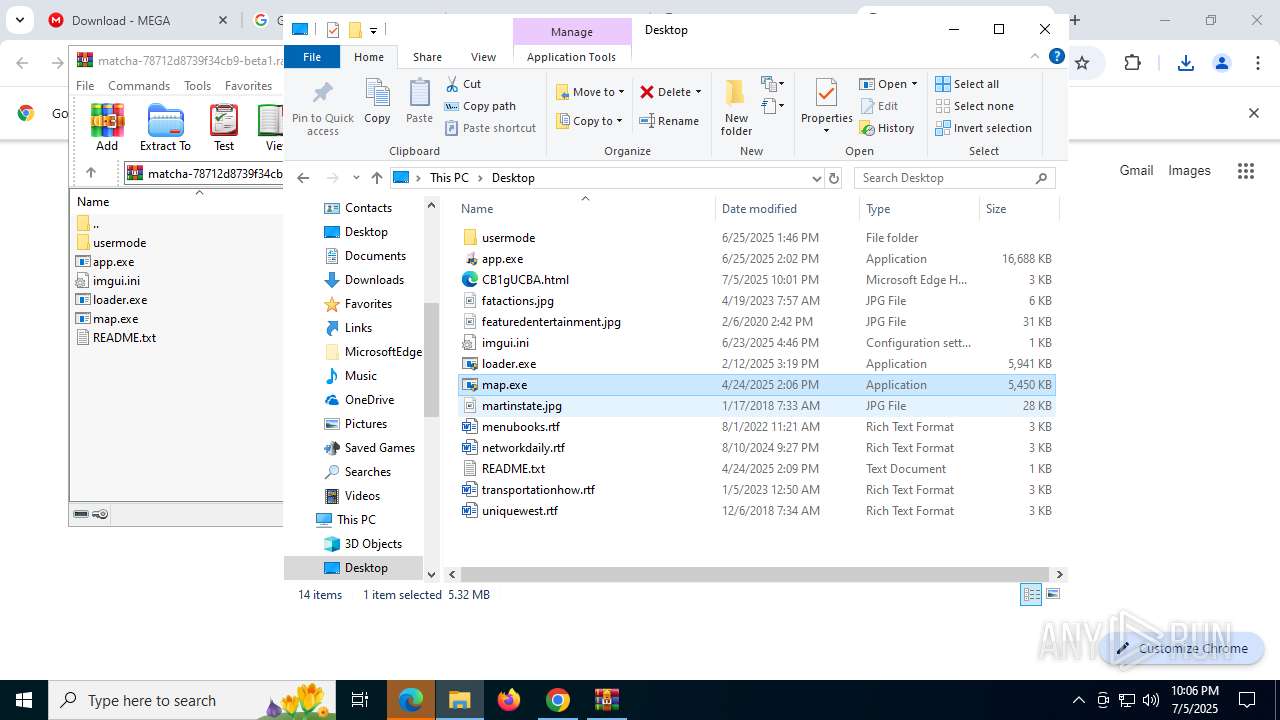
MALICIOUS
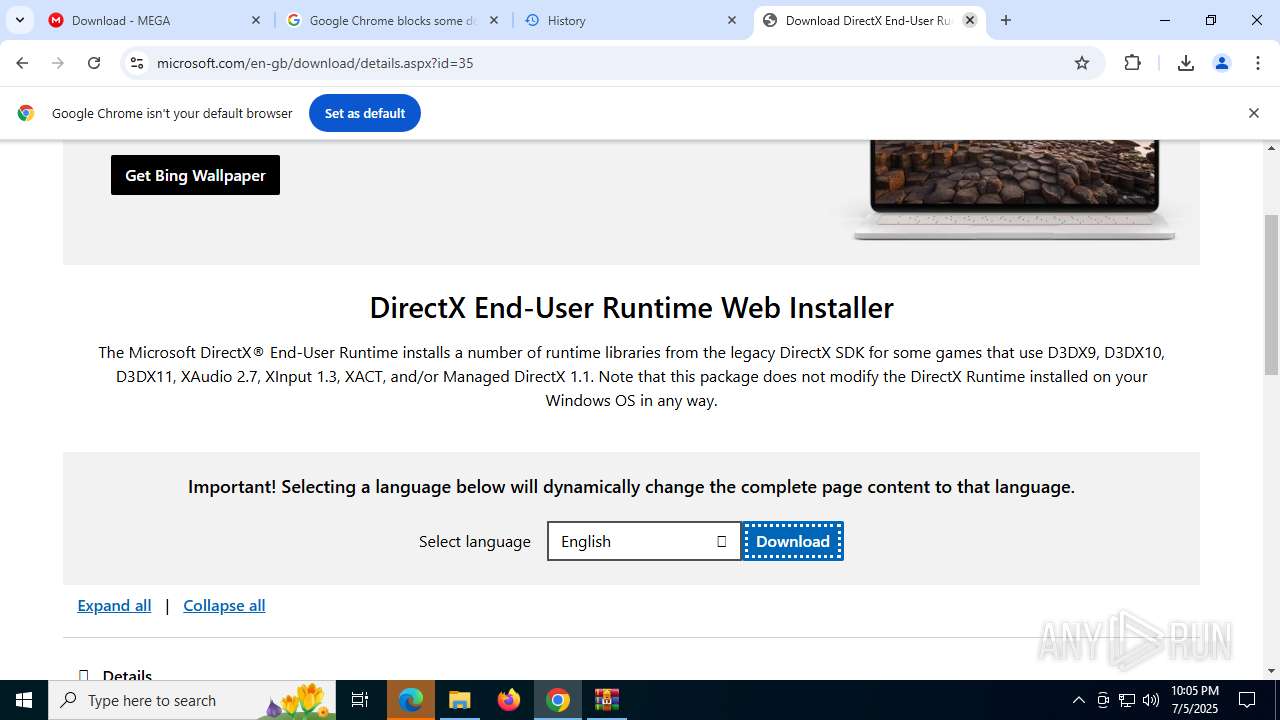
Changes the autorun value in the registry
- dxwebsetup.exe (PID: 5456)
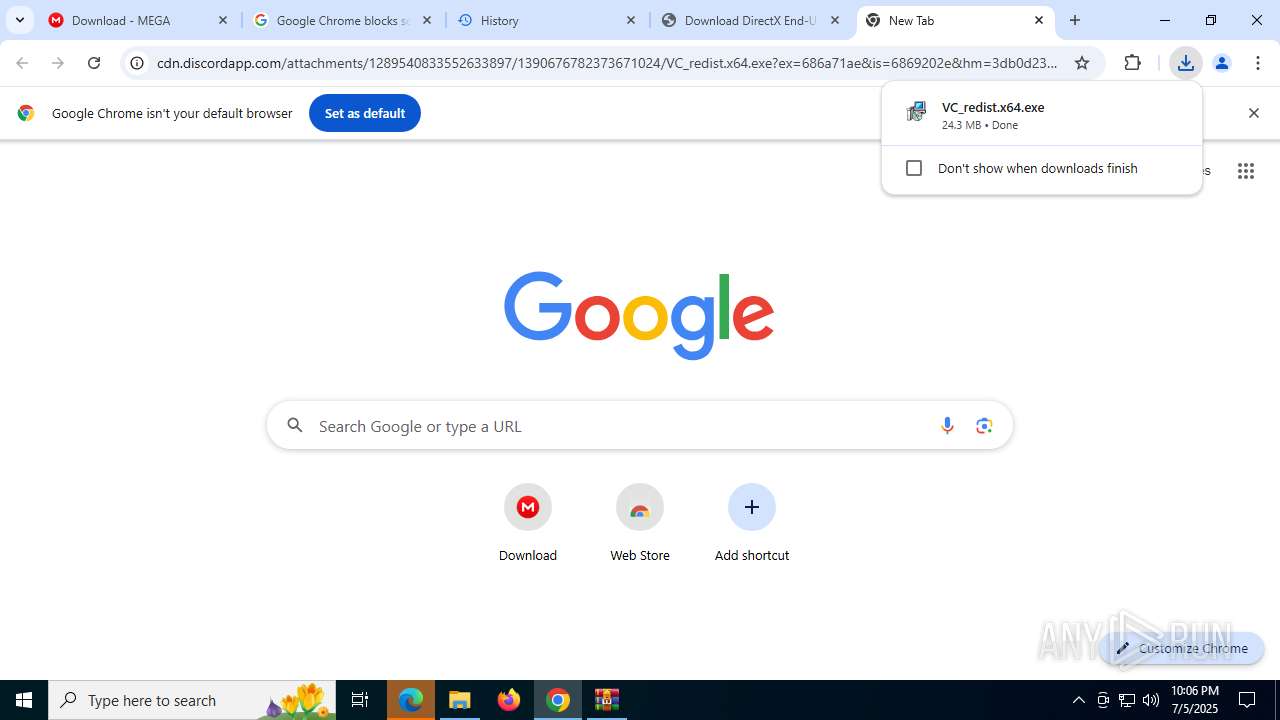
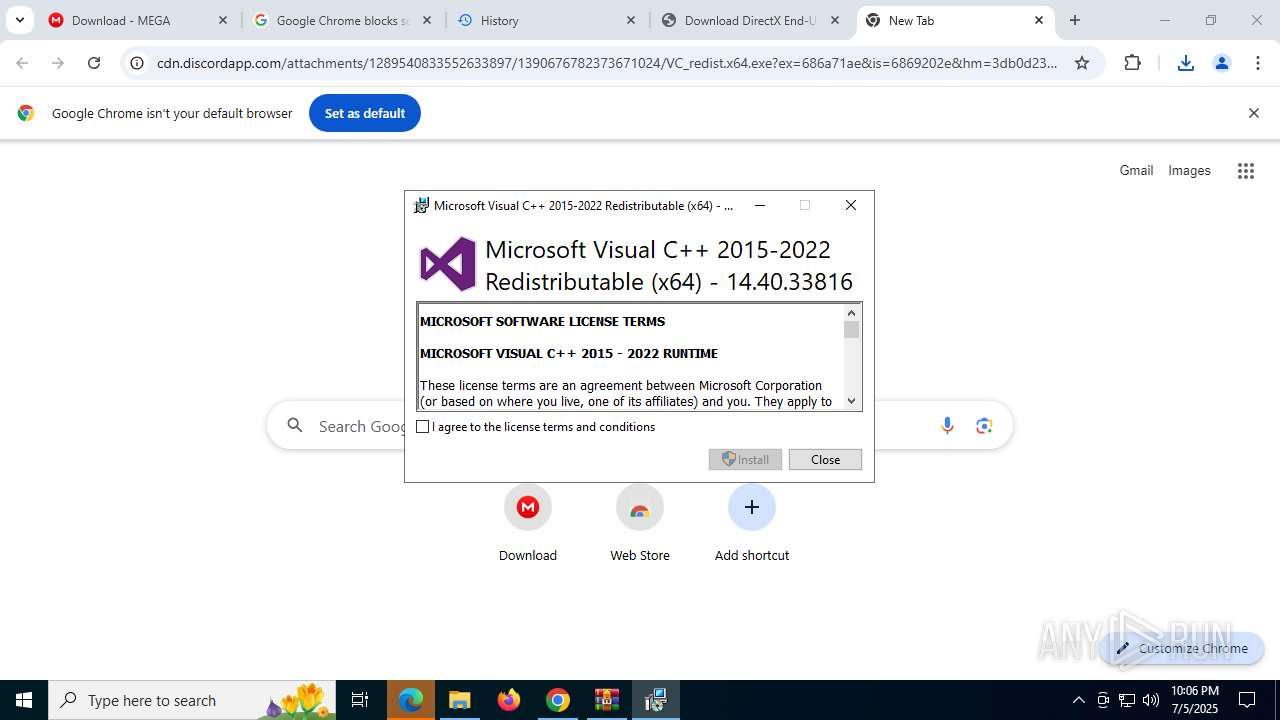
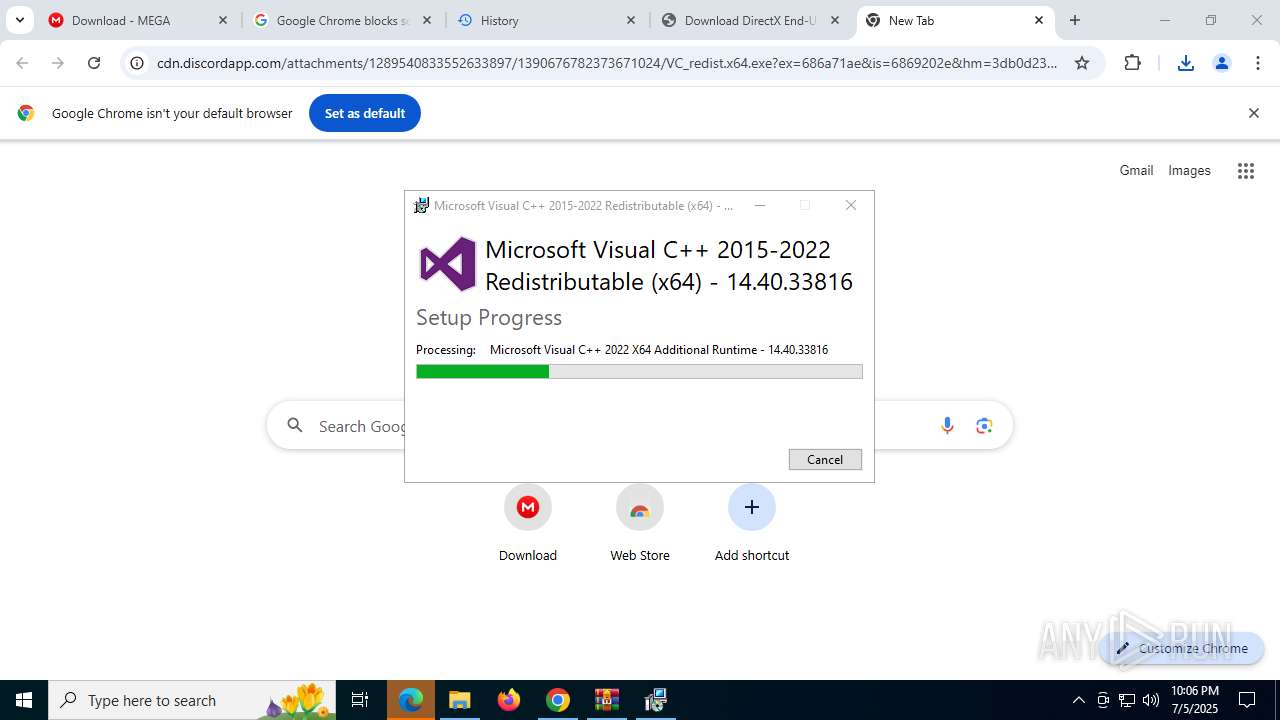
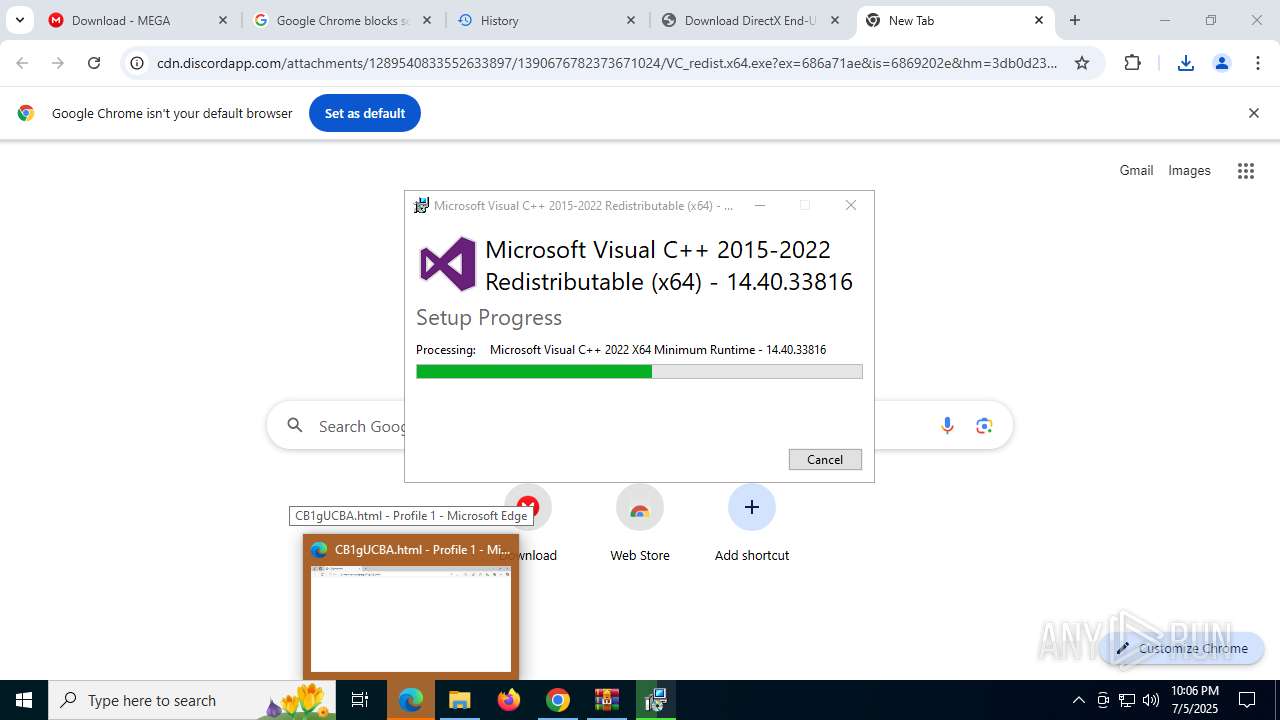
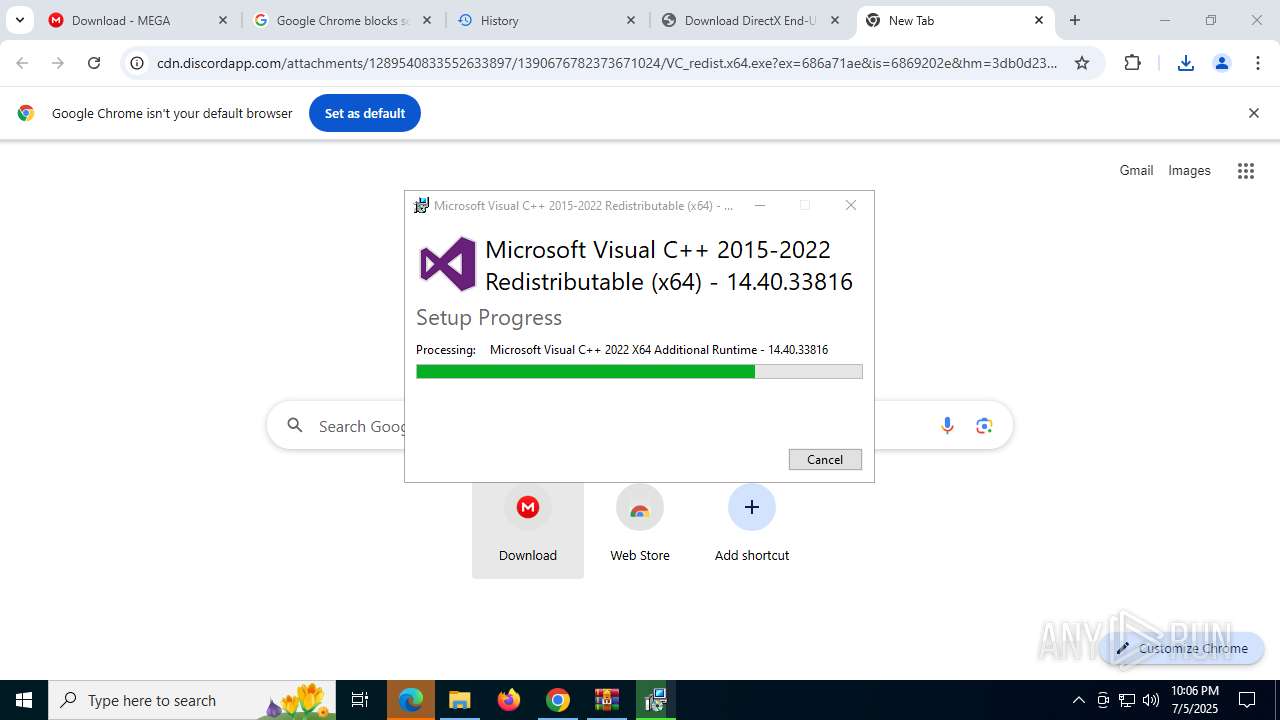
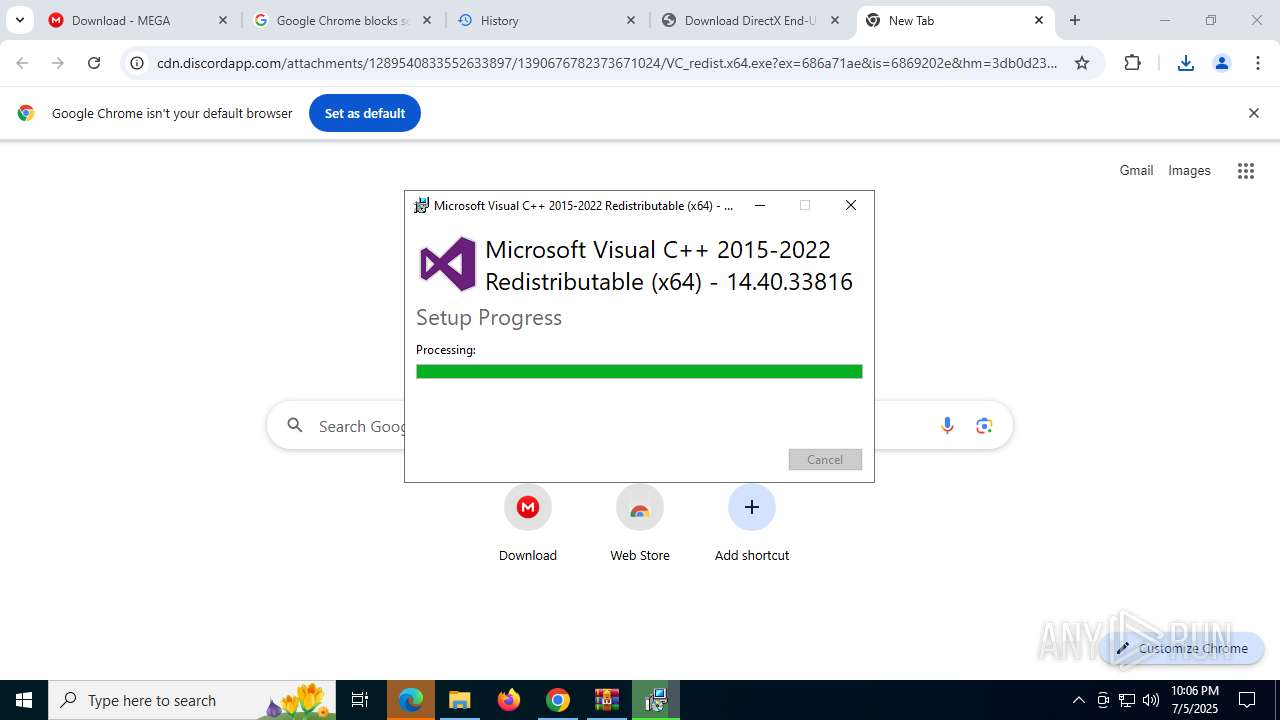
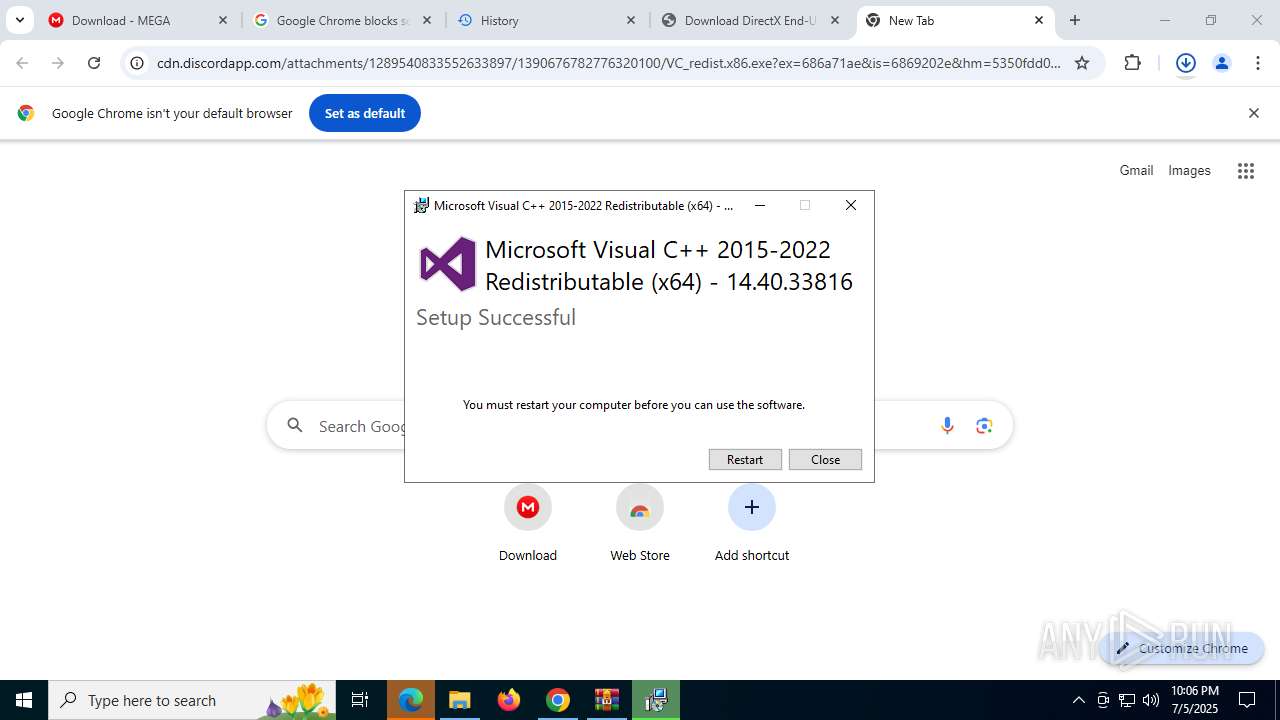
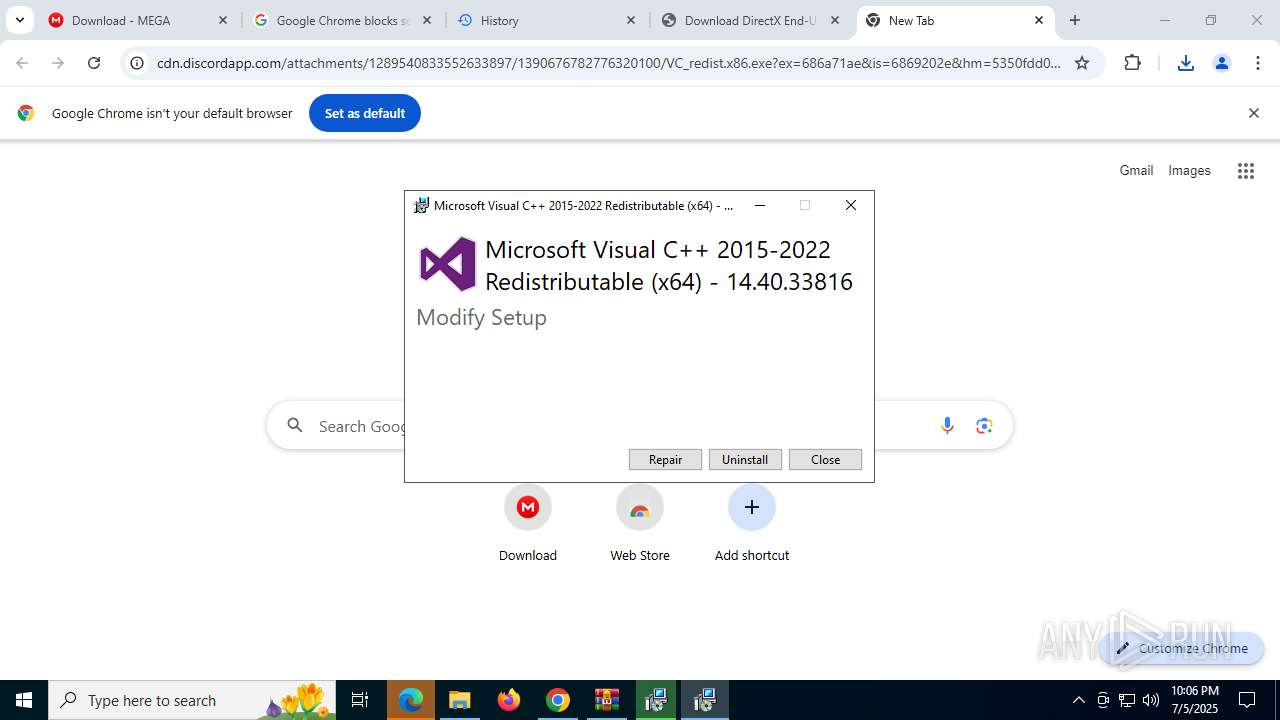
- VC_redist.x64.exe (PID: 3504)
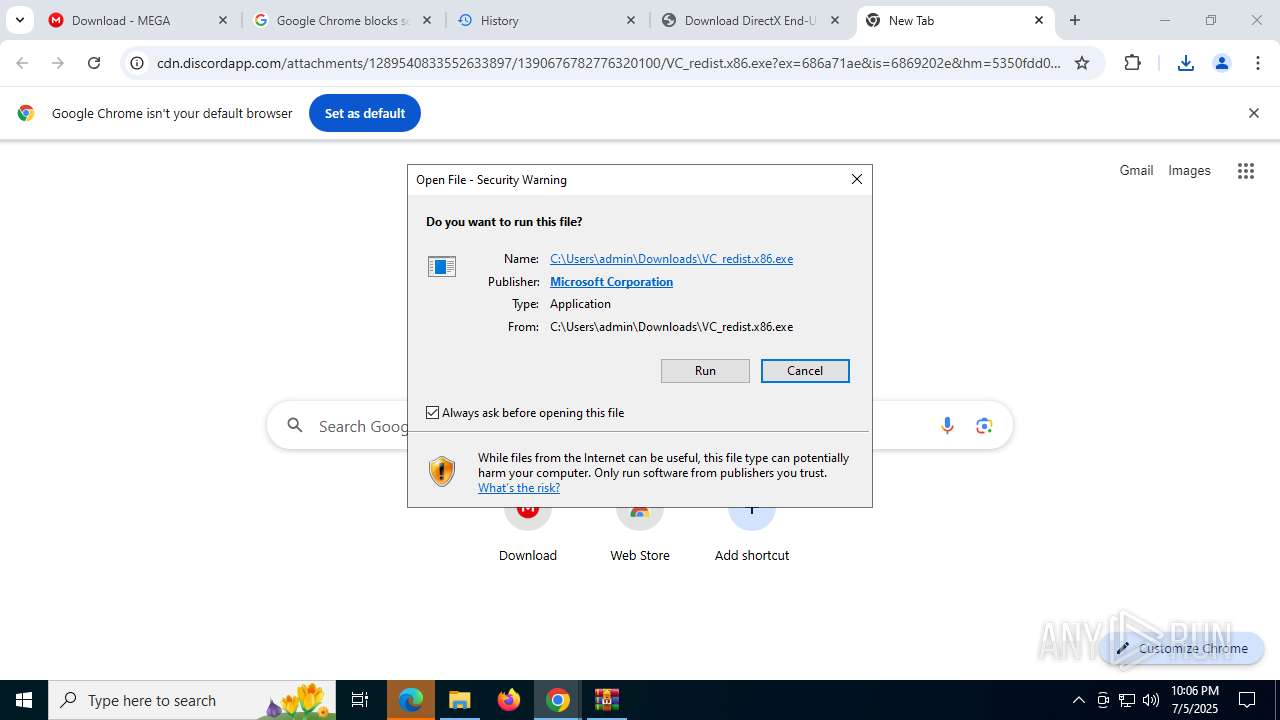
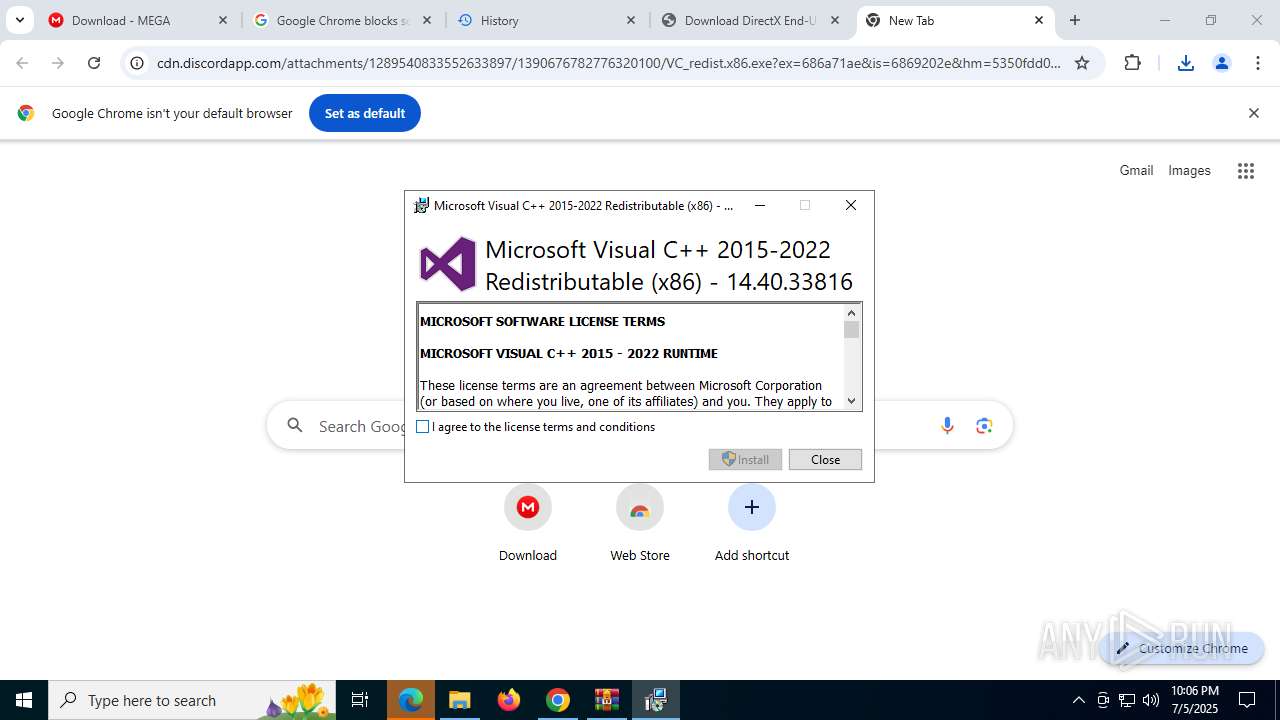
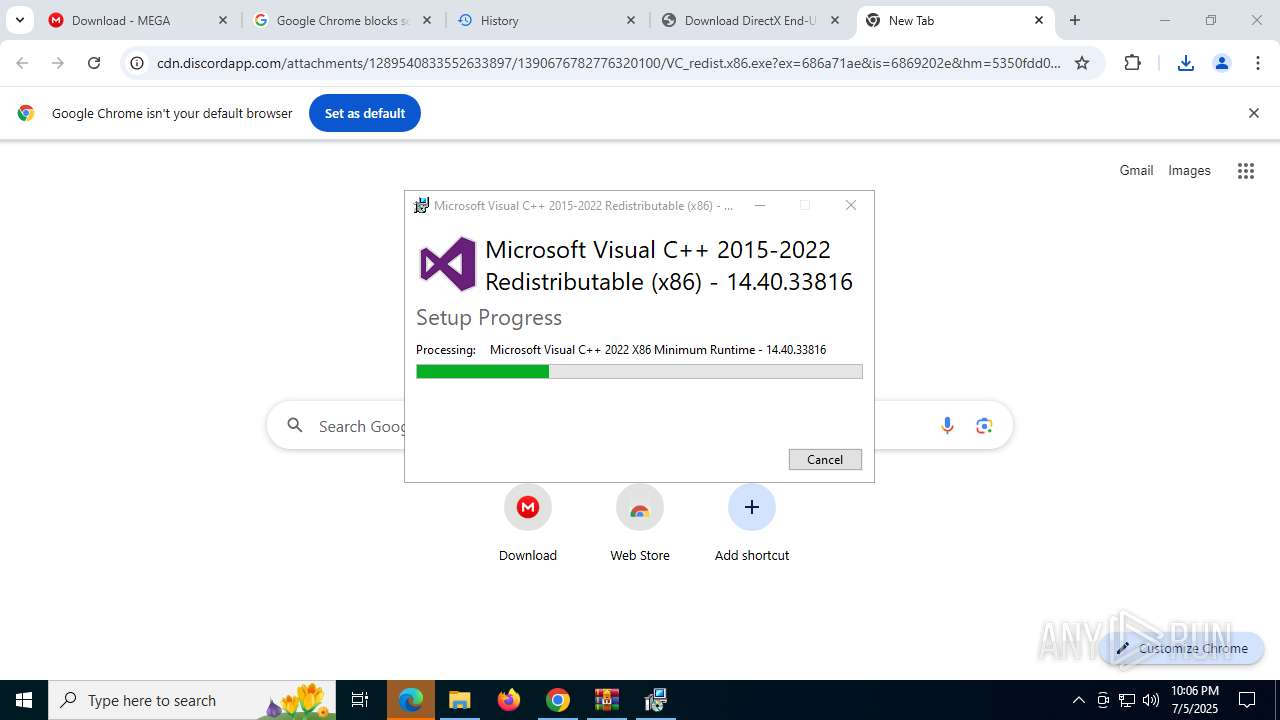
- VC_redist.x86.exe (PID: 7416)
Executing a file with an untrusted certificate
- infinst.exe (PID: 7368)
- infinst.exe (PID: 2296)
- infinst.exe (PID: 6756)
- infinst.exe (PID: 7220)
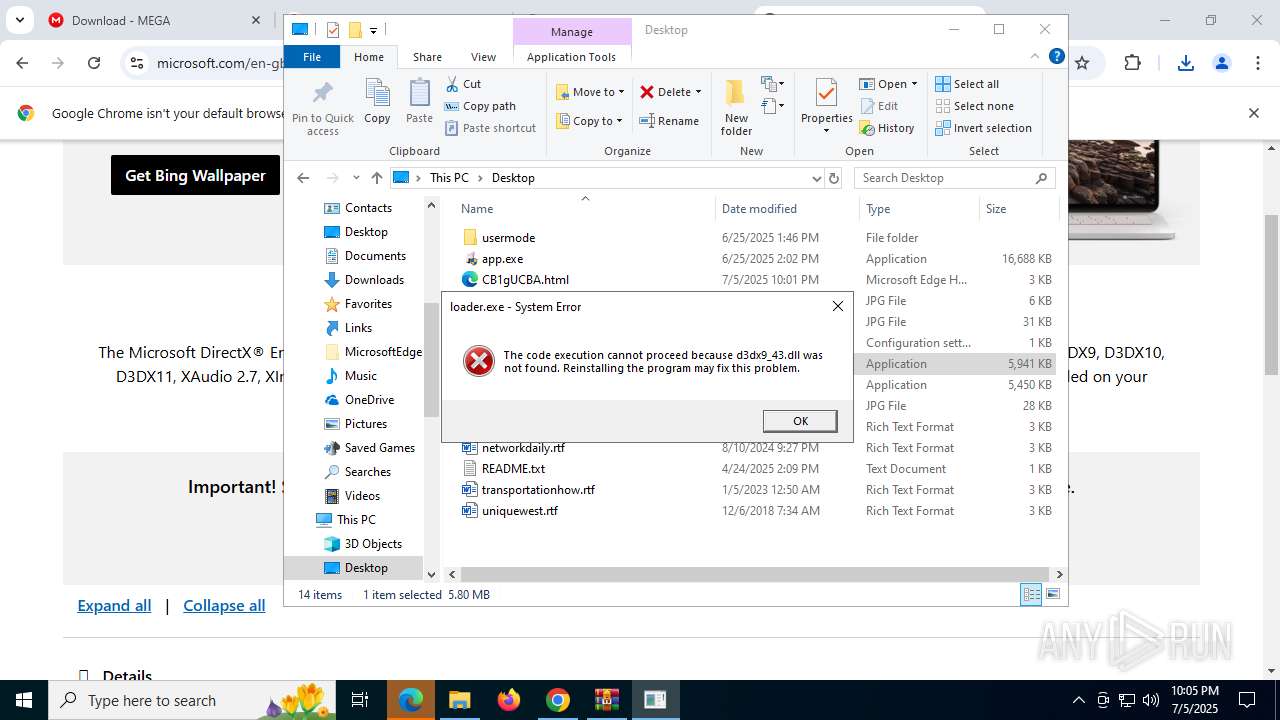
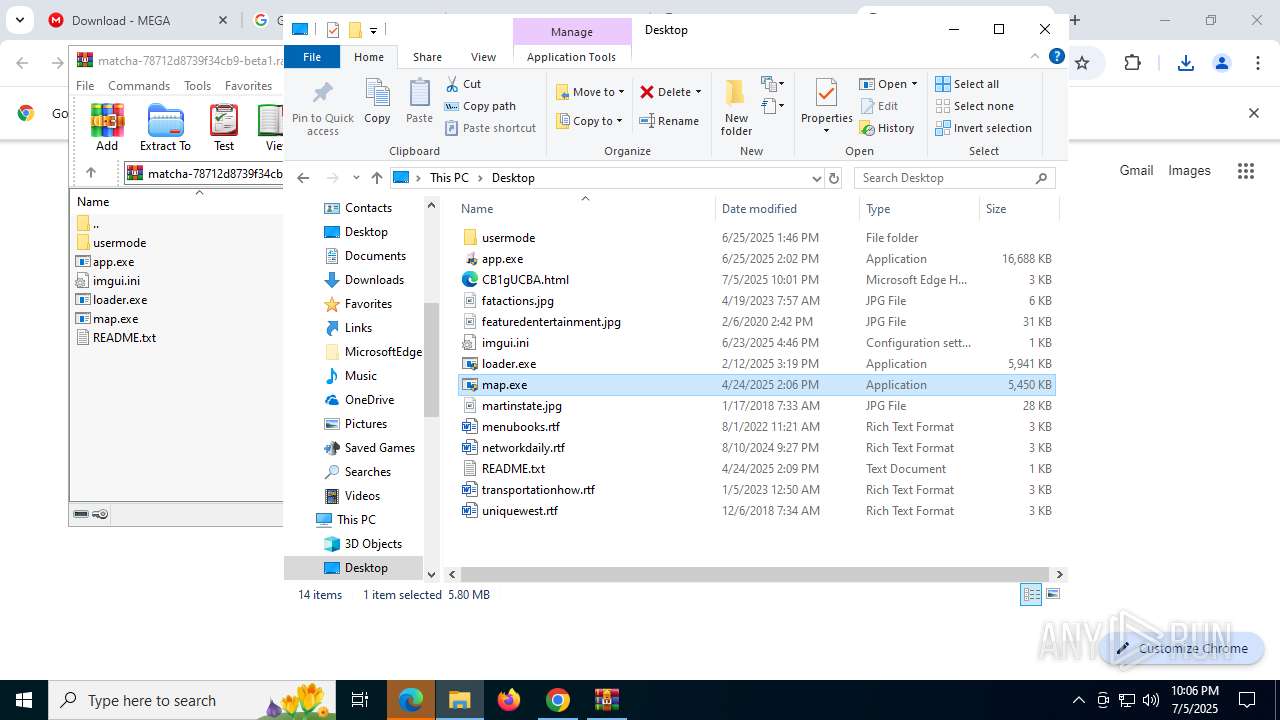
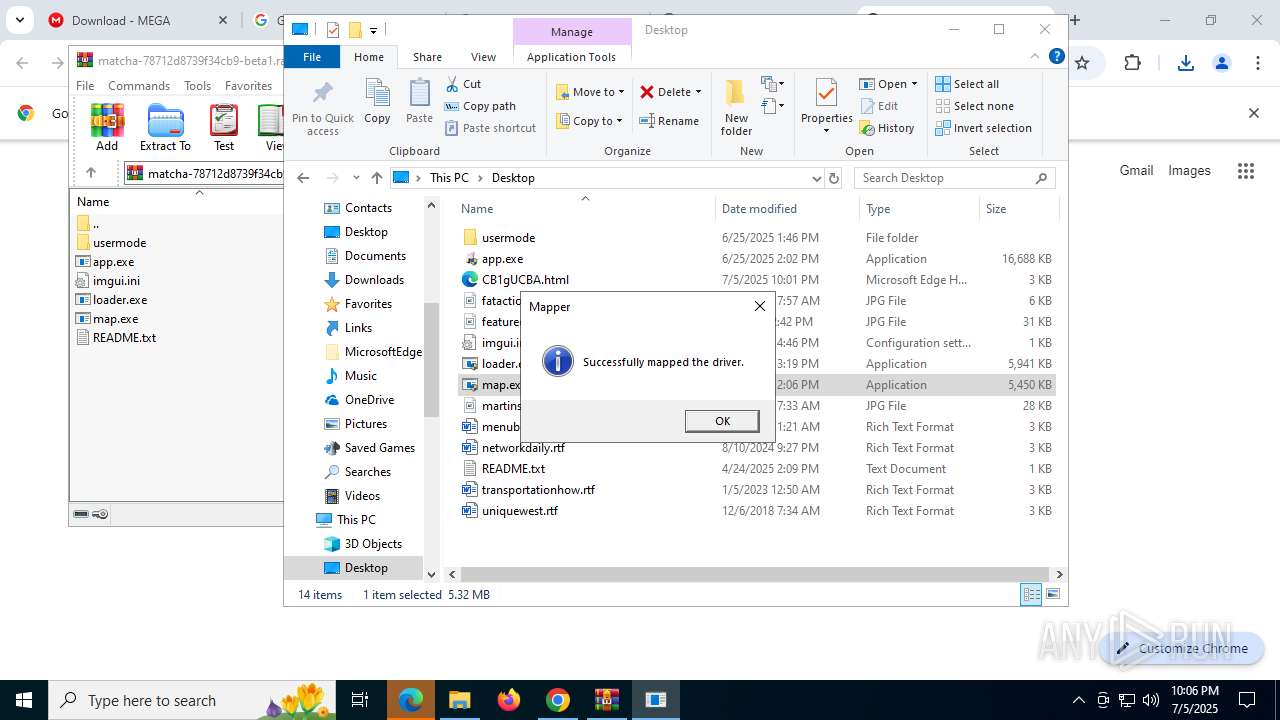
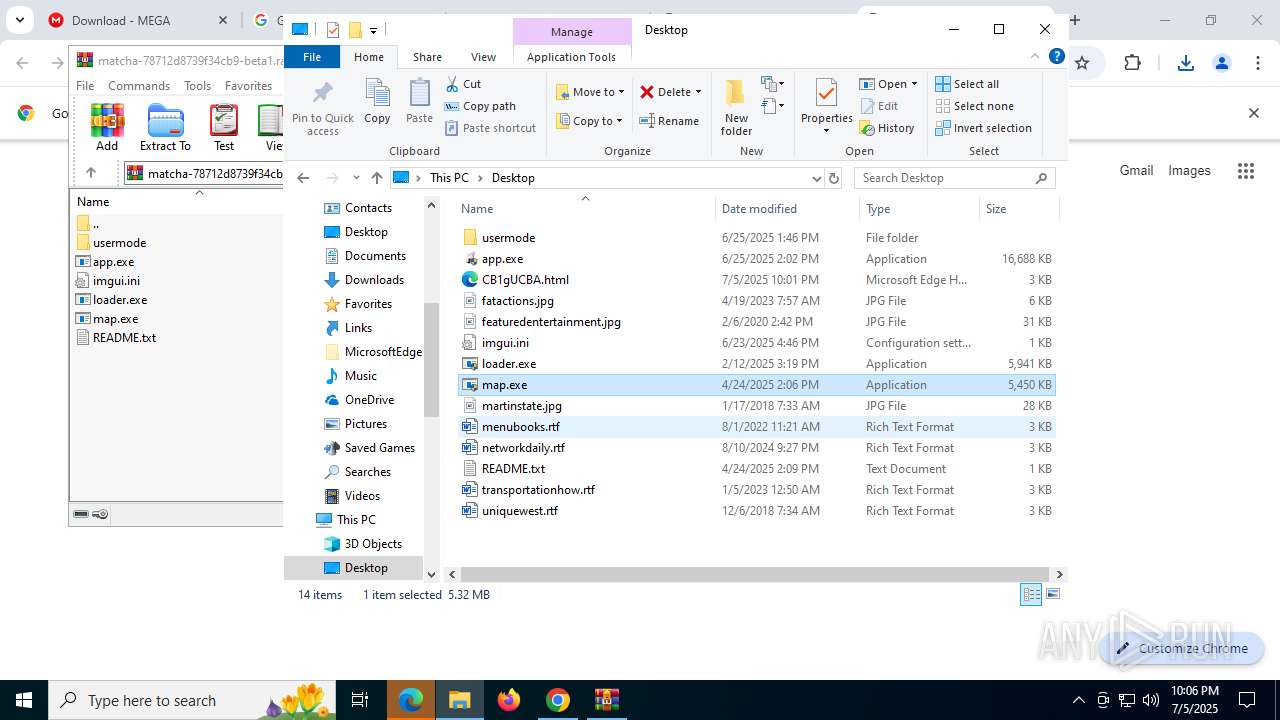
Vulnerable driver has been detected
- map.exe (PID: 5276)
- map.exe (PID: 4372)
SUSPICIOUS
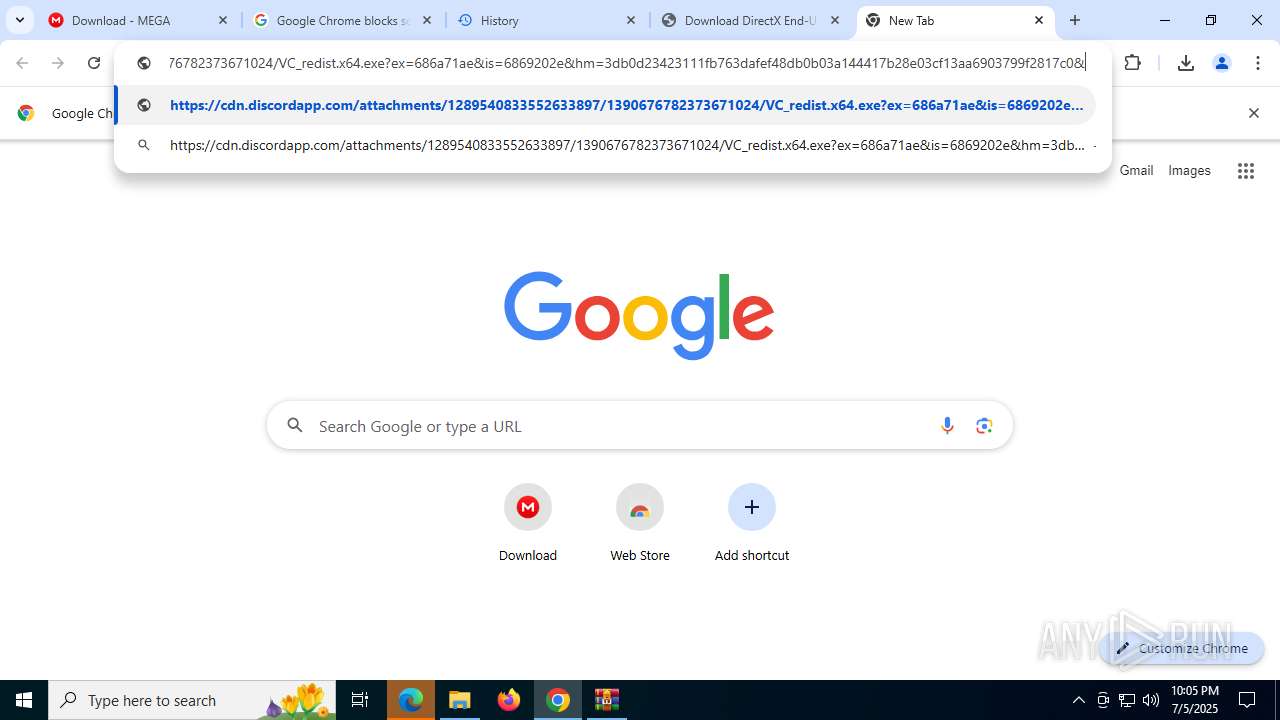
Process drops legitimate windows executable
- chrome.exe (PID: 7704)
- chrome.exe (PID: 2612)
- dxwsetup.exe (PID: 7016)
- dxwebsetup.exe (PID: 5456)
- infinst.exe (PID: 7368)
- infinst.exe (PID: 2296)
- infinst.exe (PID: 6756)
- infinst.exe (PID: 7220)
- VC_redist.x64.exe (PID: 8124)
- VC_redist.x64.exe (PID: 7324)
- VC_redist.x64.exe (PID: 3504)
- msiexec.exe (PID: 7332)
- VC_redist.x64.exe (PID: 6652)
- VC_redist.x86.exe (PID: 7440)
- VC_redist.x86.exe (PID: 6004)
- VC_redist.x86.exe (PID: 7416)
- VC_redist.x86.exe (PID: 1148)
Starts a Microsoft application from unusual location
- dxwsetup.exe (PID: 7016)
- VC_redist.x64.exe (PID: 7324)
- VC_redist.x64.exe (PID: 3504)
- VC_redist.x86.exe (PID: 7440)
- VC_redist.x86.exe (PID: 7416)
Executable content was dropped or overwritten
- dxwebsetup.exe (PID: 5456)
- dxwsetup.exe (PID: 7016)
- infinst.exe (PID: 7368)
- infinst.exe (PID: 2296)
- infinst.exe (PID: 6756)
- infinst.exe (PID: 7220)
- VC_redist.x64.exe (PID: 8124)
- VC_redist.x64.exe (PID: 7324)
- VC_redist.x64.exe (PID: 3504)
- VC_redist.x64.exe (PID: 436)
- VC_redist.x64.exe (PID: 6652)
- VC_redist.x86.exe (PID: 6004)
- VC_redist.x86.exe (PID: 7440)
- VC_redist.x86.exe (PID: 7416)
- VC_redist.x86.exe (PID: 7408)
- VC_redist.x86.exe (PID: 7372)
- VC_redist.x64.exe (PID: 6948)
- VC_redist.x86.exe (PID: 1148)
- map.exe (PID: 5276)
- map.exe (PID: 4372)
Reads security settings of Internet Explorer
- dxwsetup.exe (PID: 7016)
- VC_redist.x64.exe (PID: 7324)
- VC_redist.x64.exe (PID: 436)
- VC_redist.x86.exe (PID: 7440)
- VC_redist.x86.exe (PID: 7372)
Executes as Windows Service
- VSSVC.exe (PID: 6876)
Searches for installed software
- dllhost.exe (PID: 7180)
- VC_redist.x64.exe (PID: 7324)
- VC_redist.x64.exe (PID: 436)
- VC_redist.x86.exe (PID: 7440)
- VC_redist.x86.exe (PID: 5172)
- VC_redist.x86.exe (PID: 7416)
- VC_redist.x86.exe (PID: 7372)
- VC_redist.x86.exe (PID: 1148)
- VC_redist.x64.exe (PID: 6600)
- VC_redist.x86.exe (PID: 7408)
- VC_redist.x64.exe (PID: 6948)
- VC_redist.x64.exe (PID: 6652)
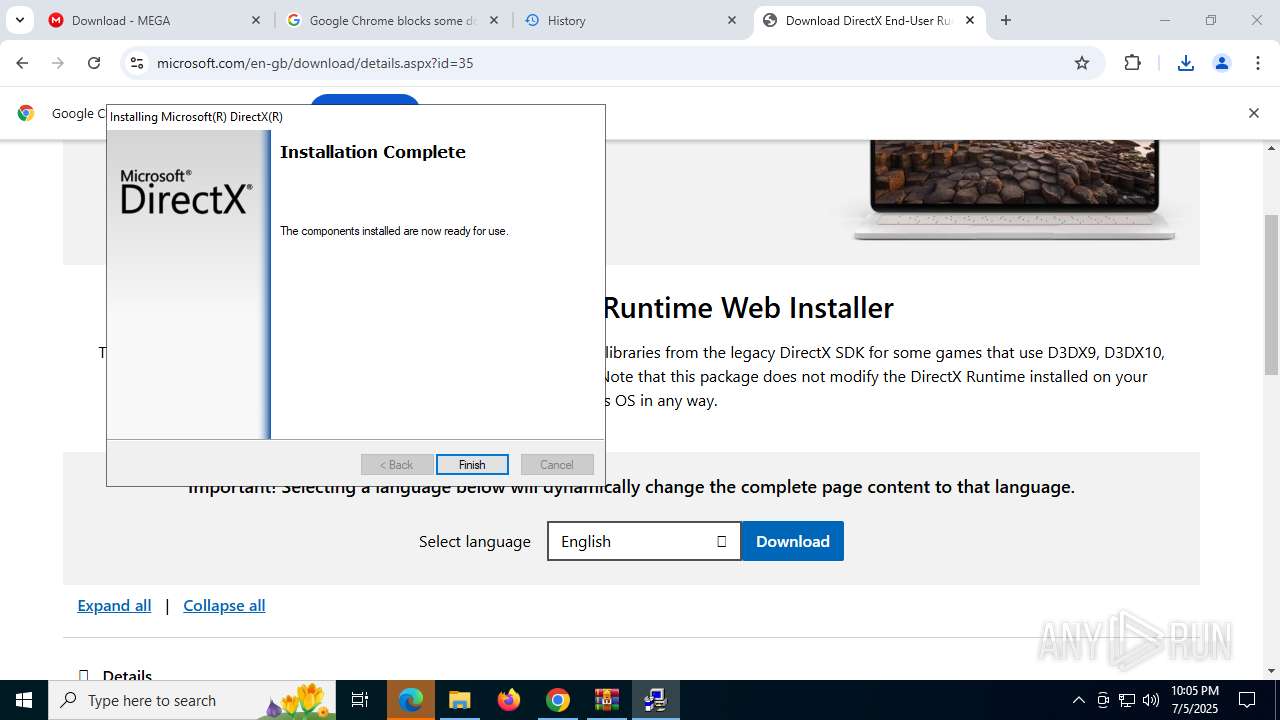
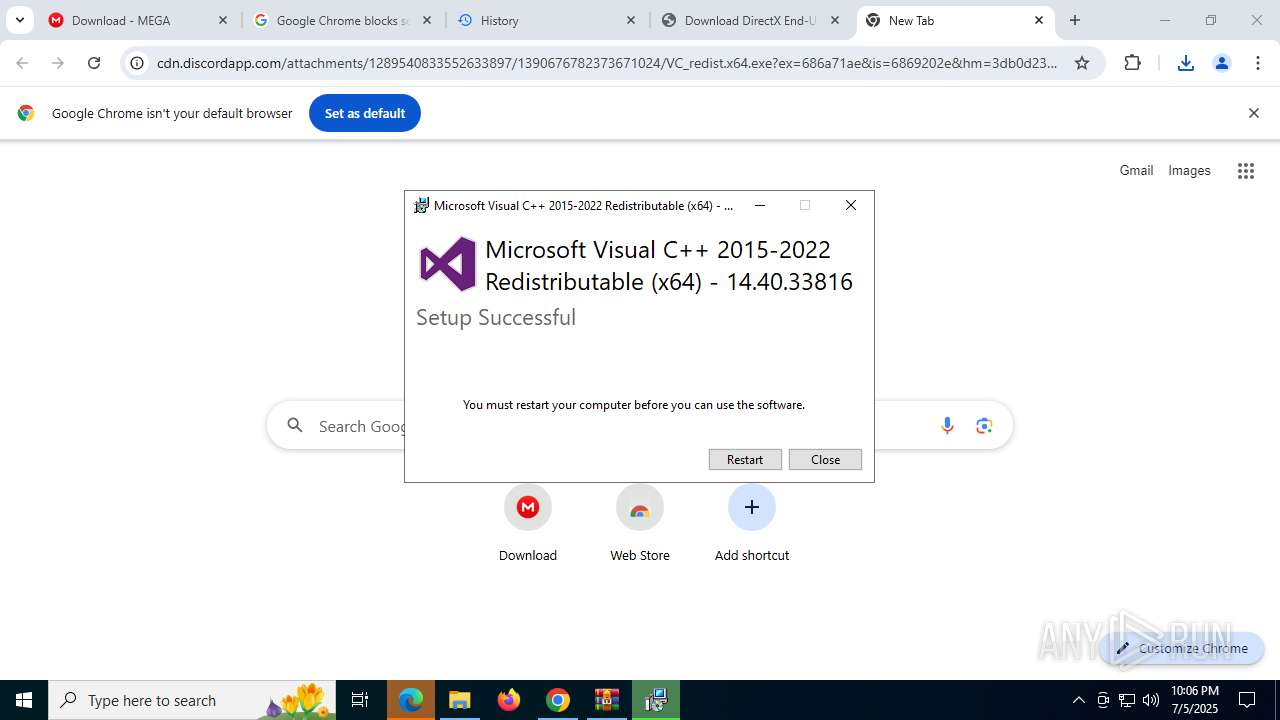
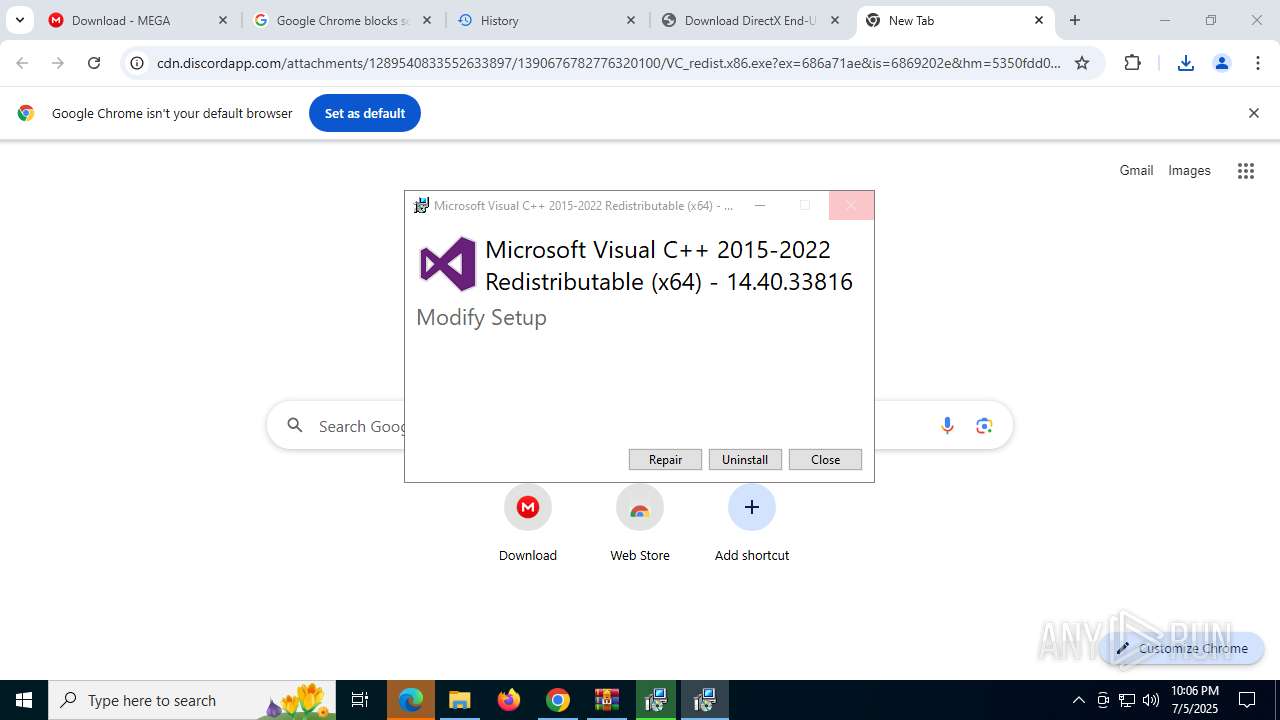
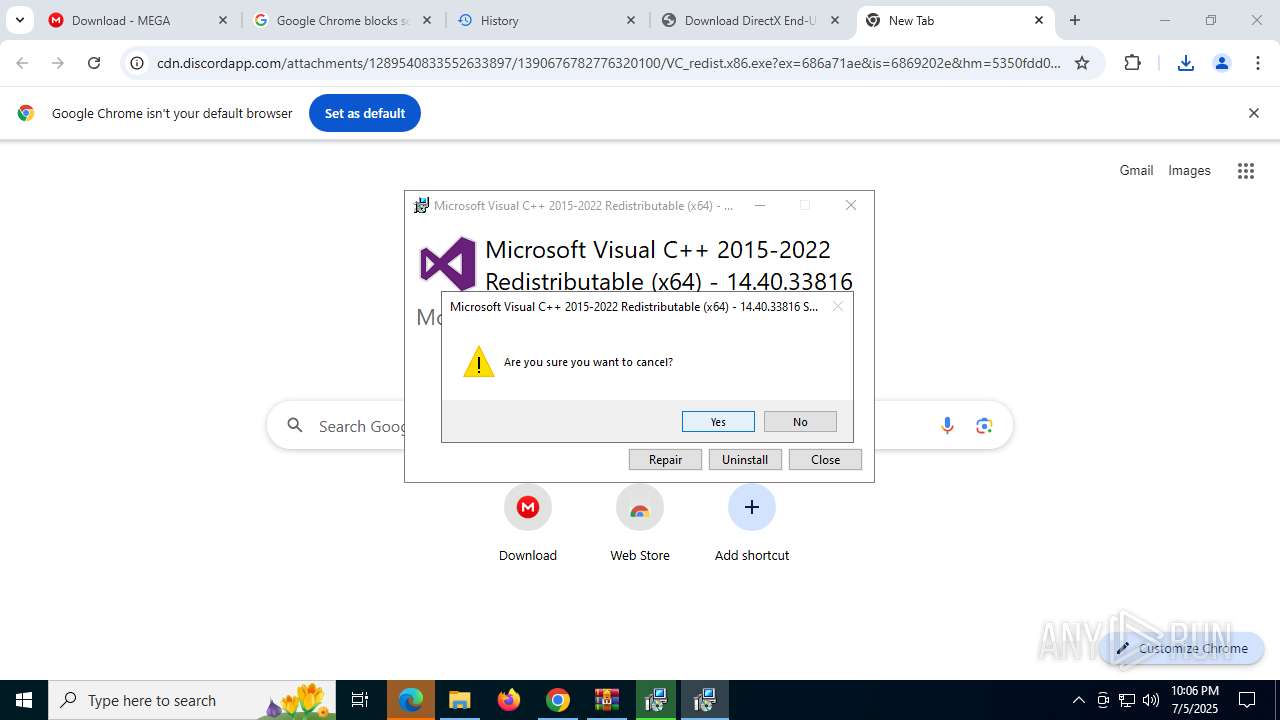
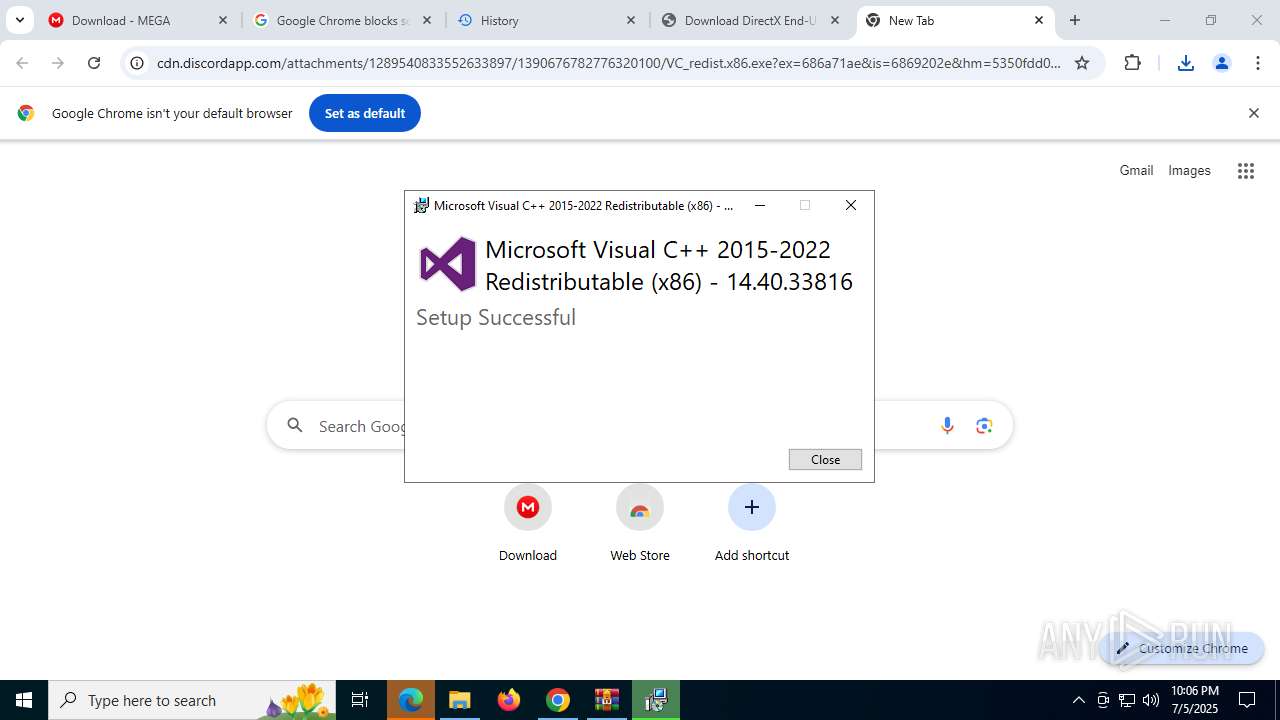
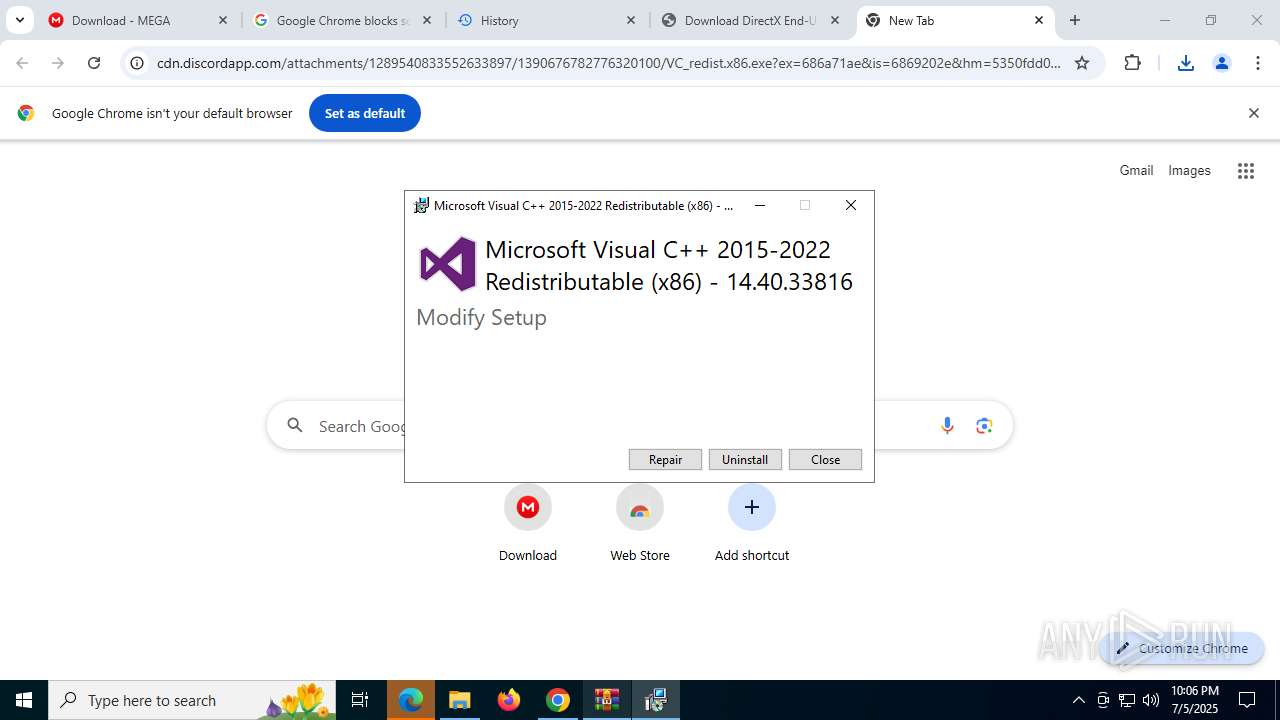
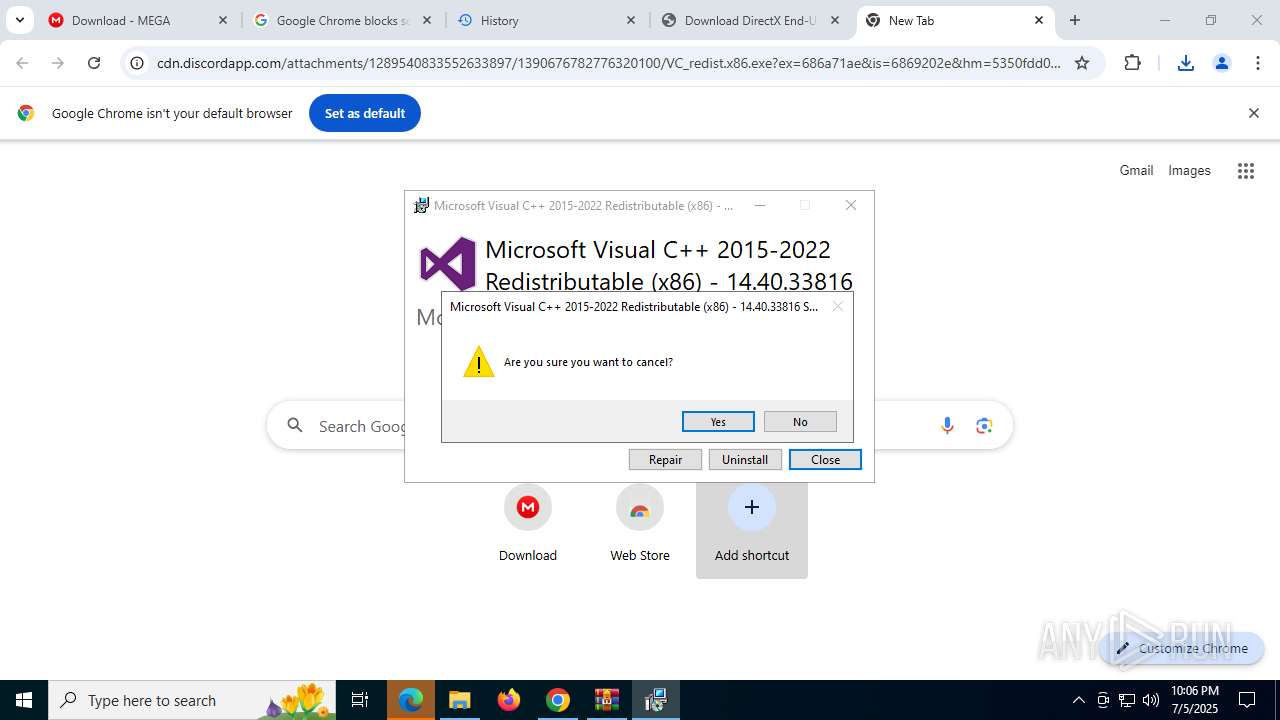
Creates a software uninstall entry
- VC_redist.x64.exe (PID: 3504)
- VC_redist.x86.exe (PID: 7416)
The process drops C-runtime libraries
- msiexec.exe (PID: 7332)
Application launched itself
- VC_redist.x64.exe (PID: 436)
- VC_redist.x64.exe (PID: 8000)
- VC_redist.x86.exe (PID: 5172)
- VC_redist.x86.exe (PID: 5924)
- VC_redist.x86.exe (PID: 3724)
- VC_redist.x64.exe (PID: 6600)
- VC_redist.x64.exe (PID: 3900)
- VC_redist.x86.exe (PID: 7372)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7332)
The process checks if it is being run in the virtual environment
- msiexec.exe (PID: 7332)
Starts itself from another location
- VC_redist.x64.exe (PID: 7324)
- VC_redist.x86.exe (PID: 7440)
Creates or modifies Windows services
- map.exe (PID: 5276)
- map.exe (PID: 4372)
INFO
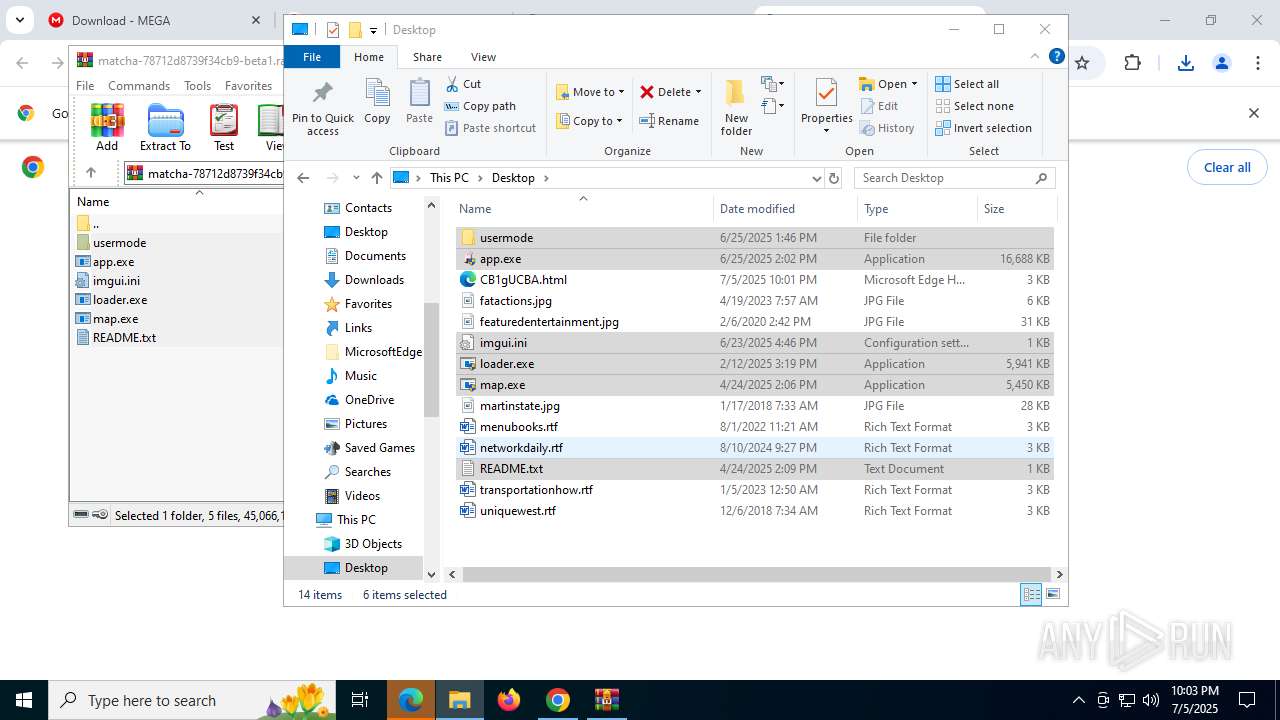
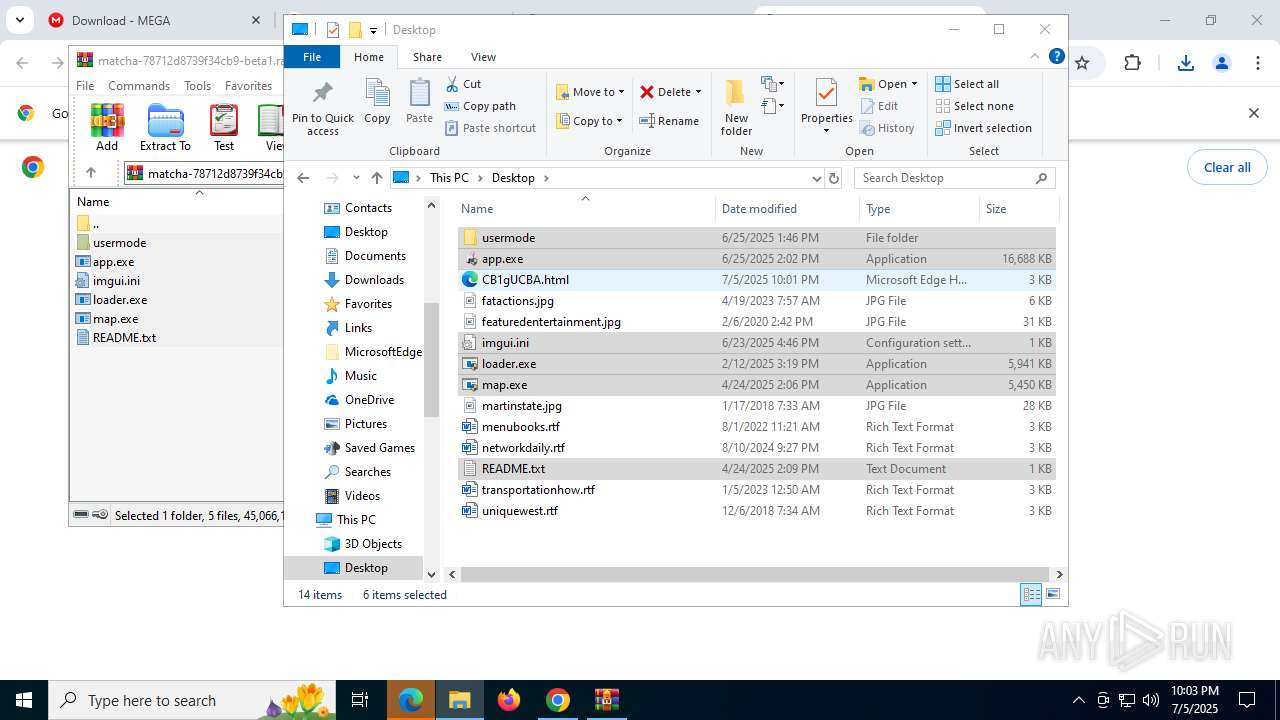
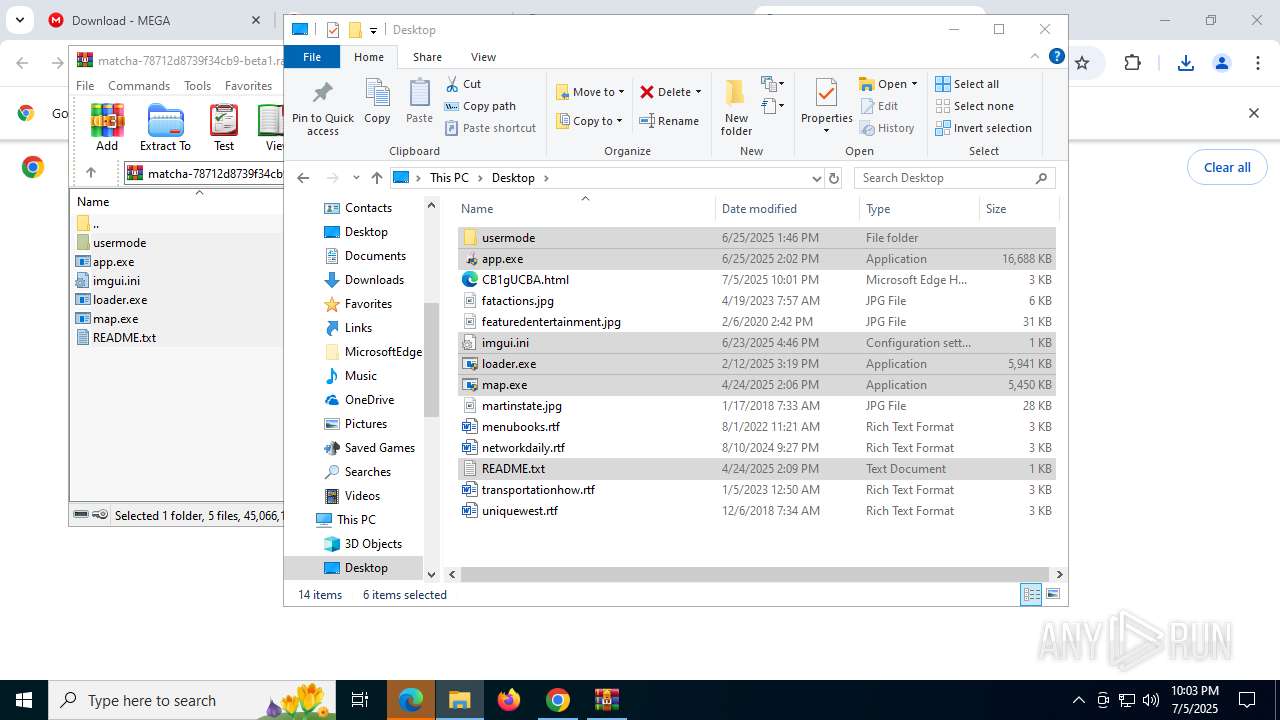
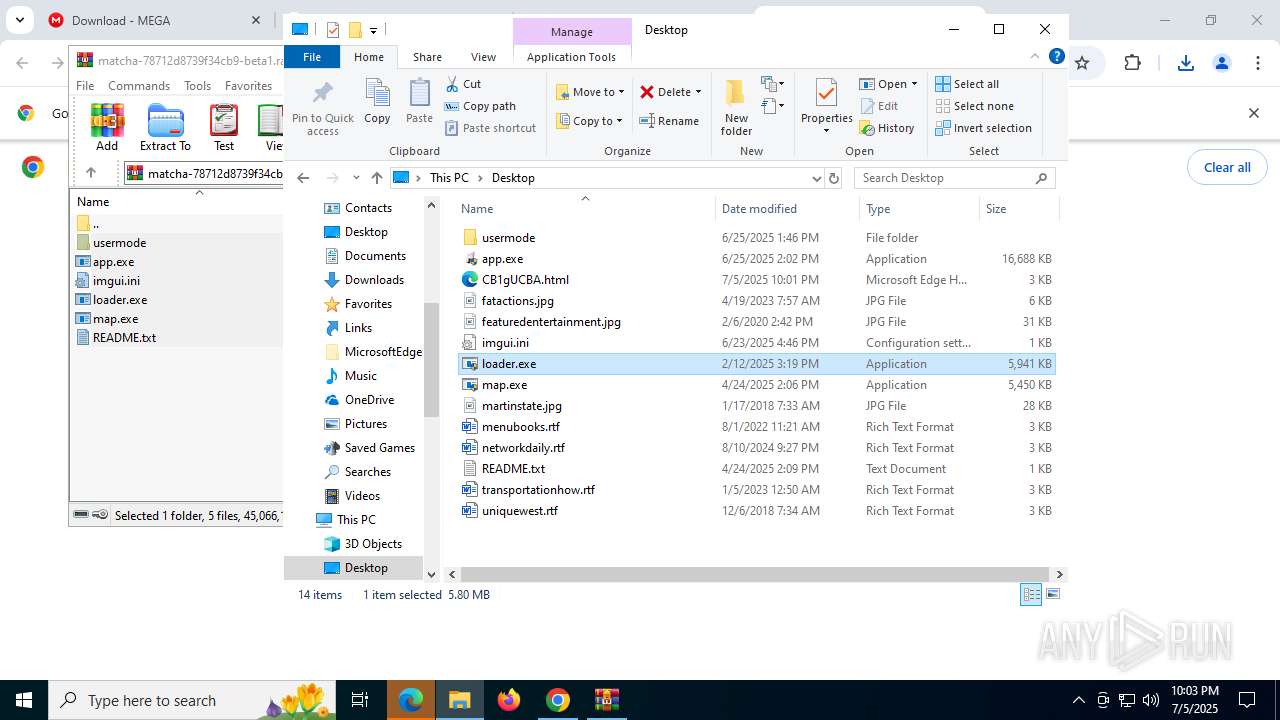
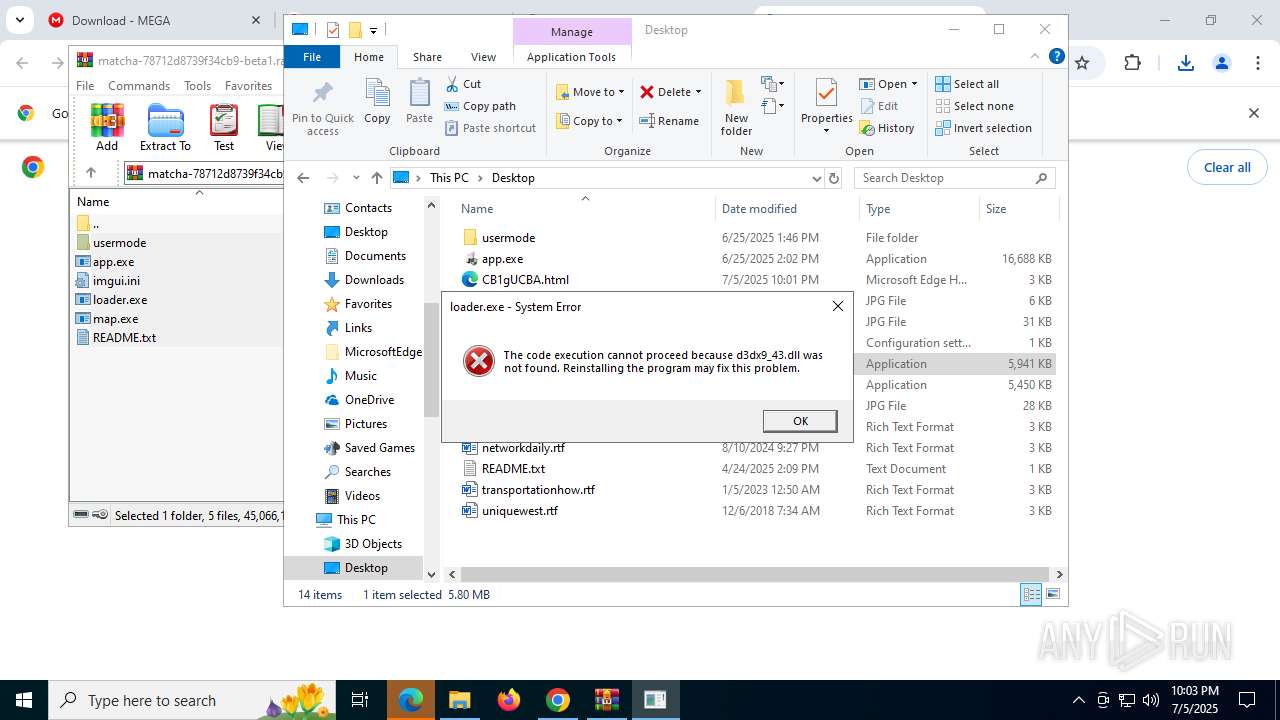
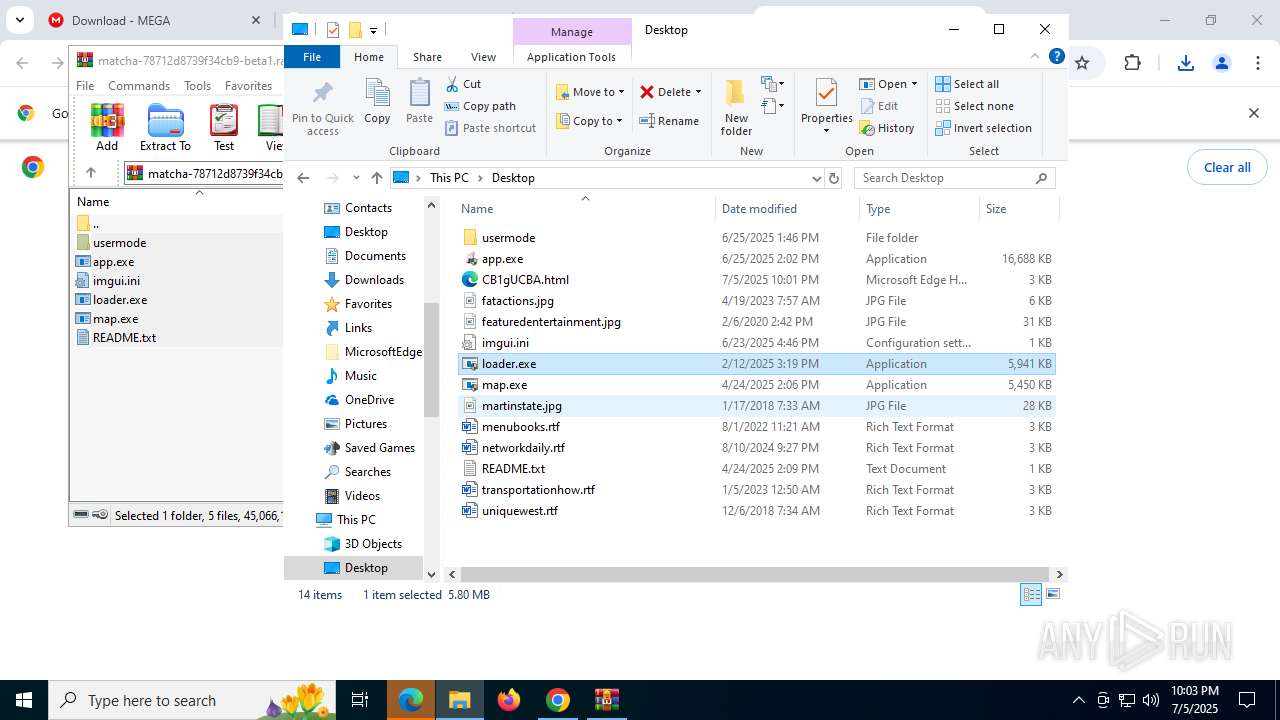
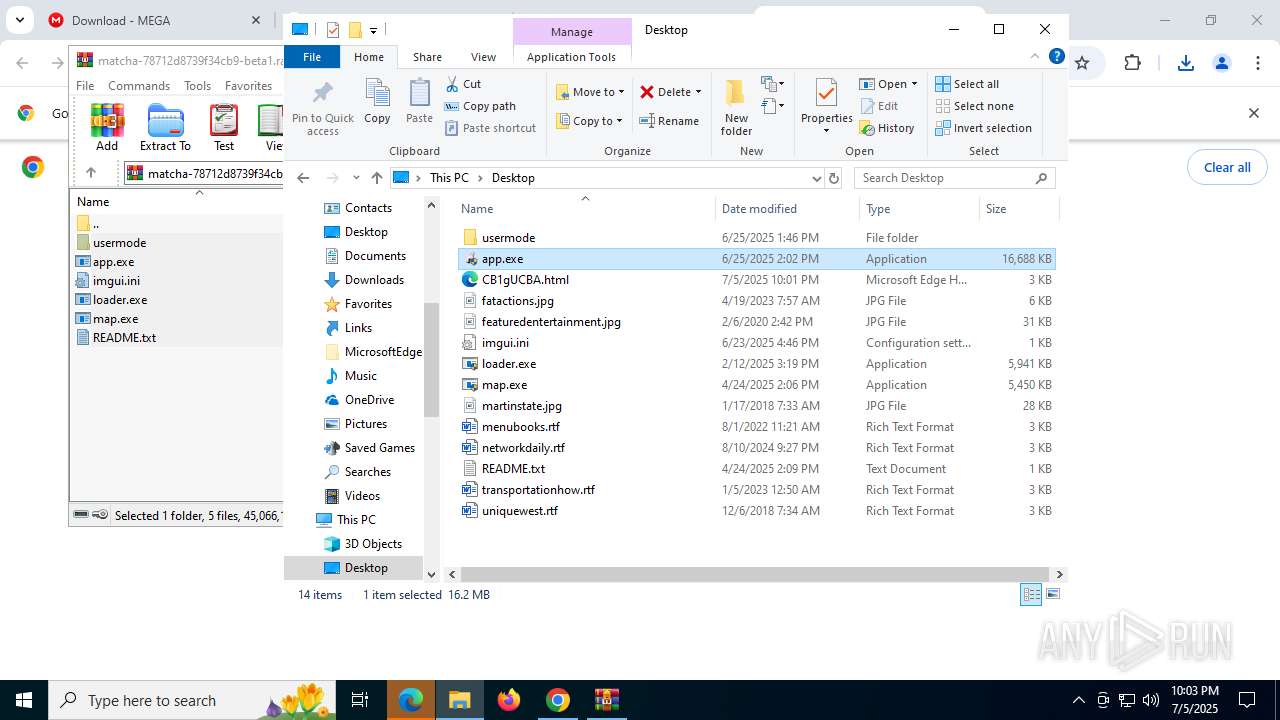
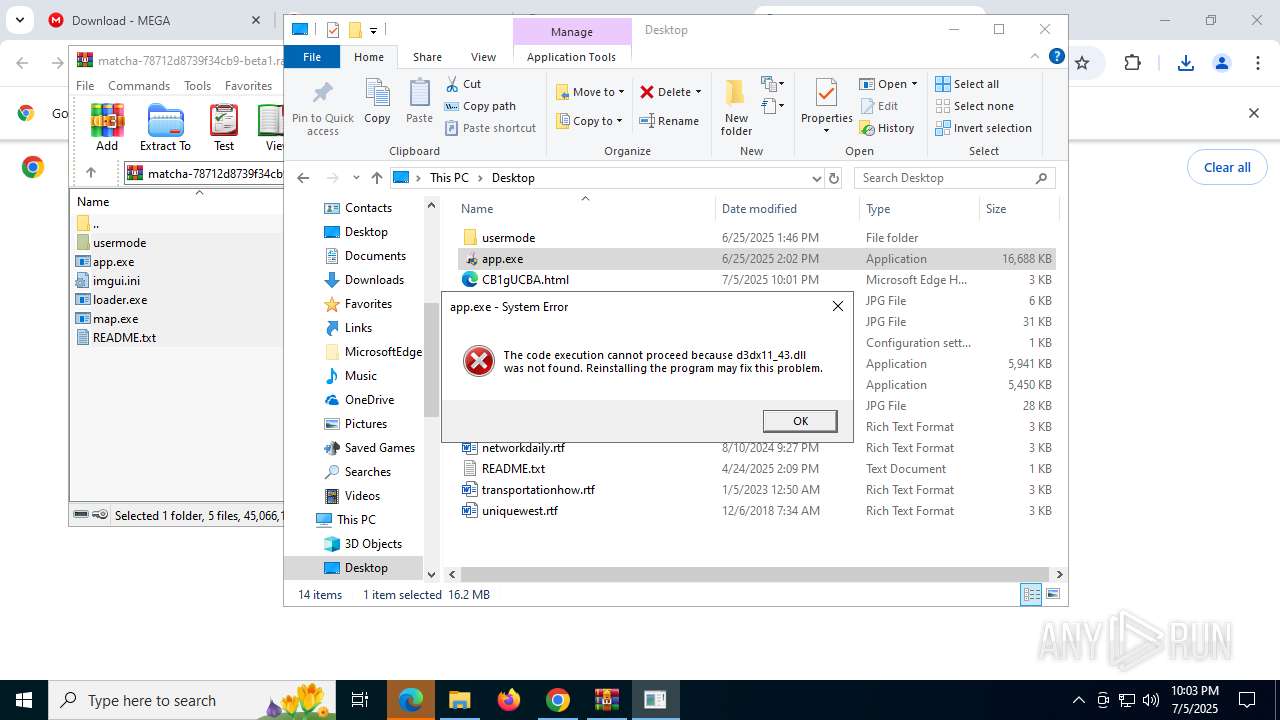
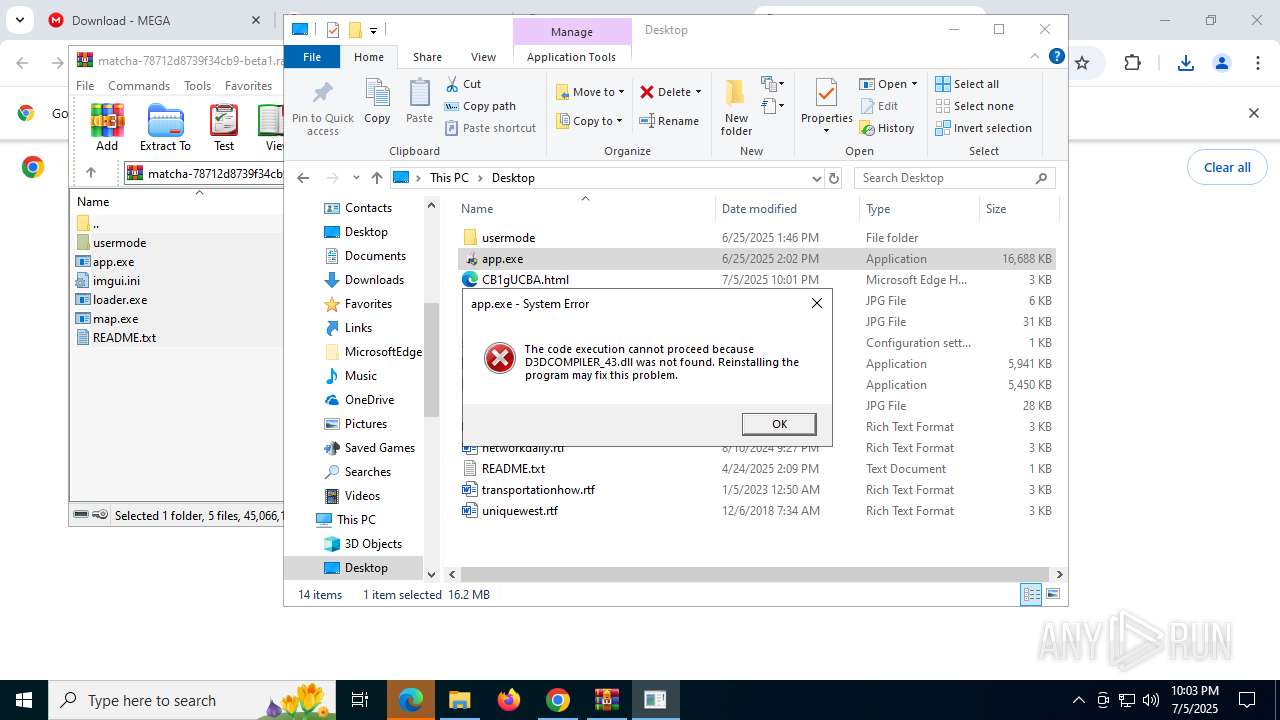
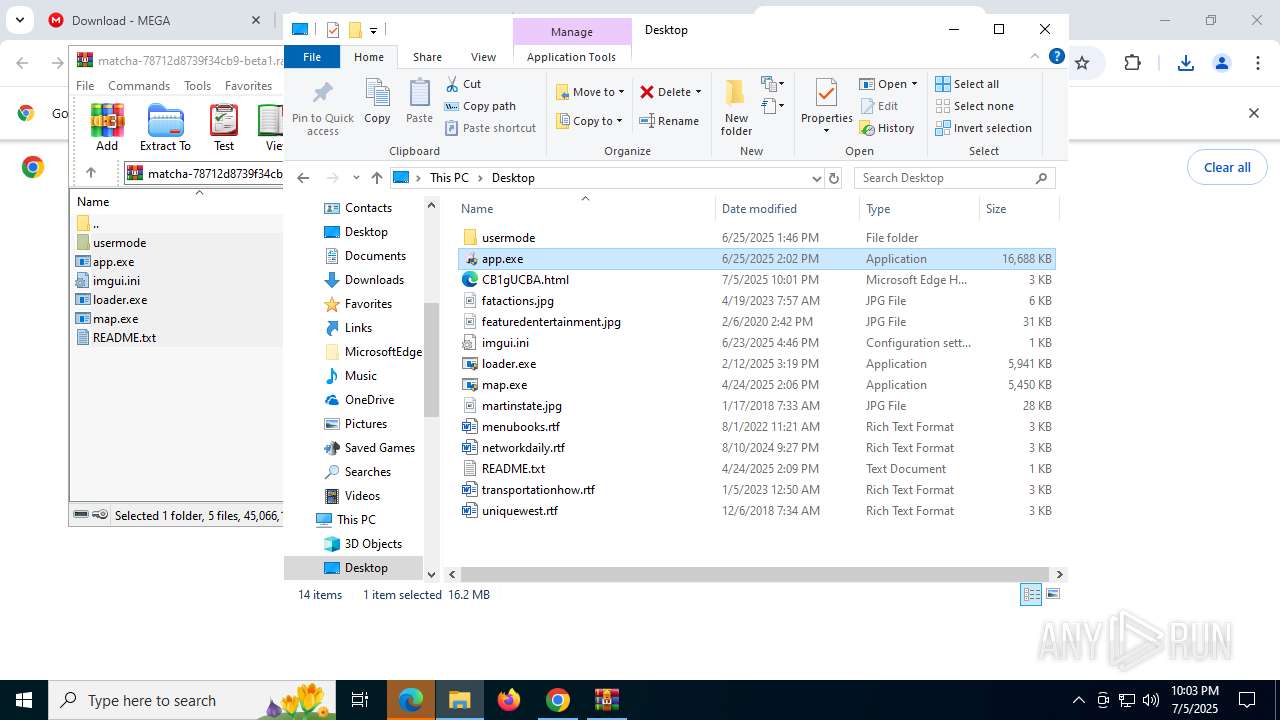
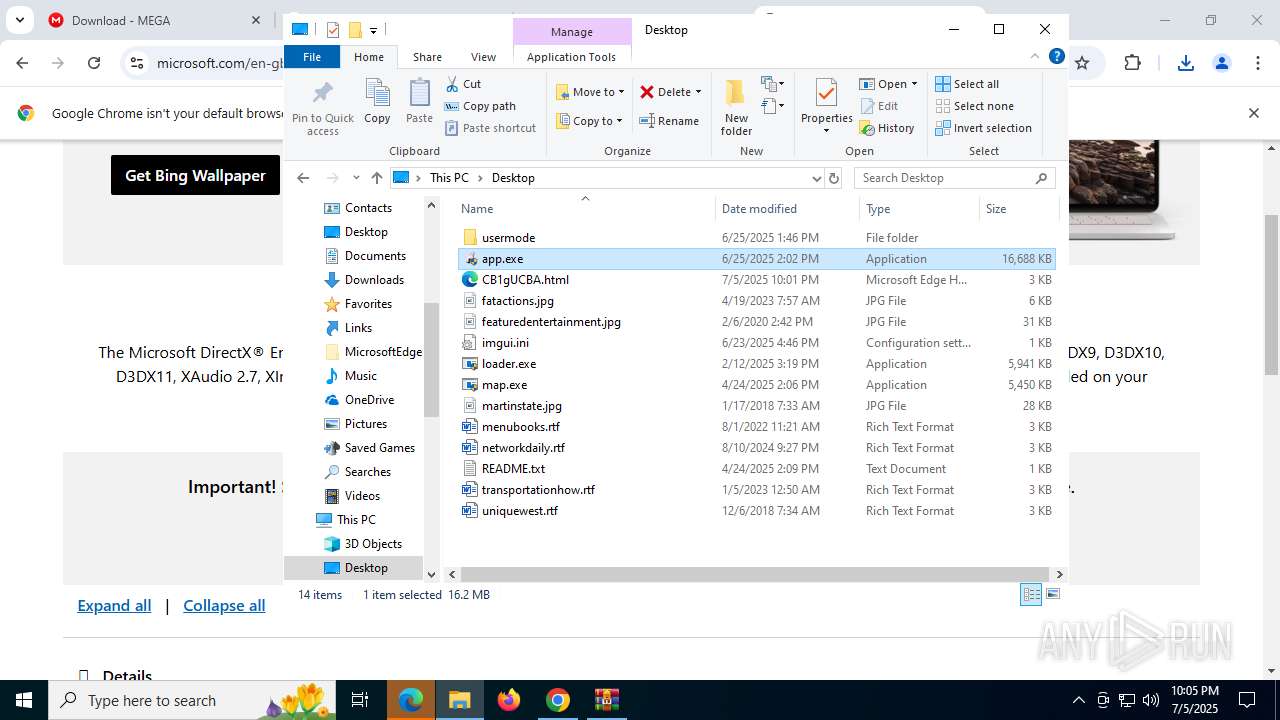
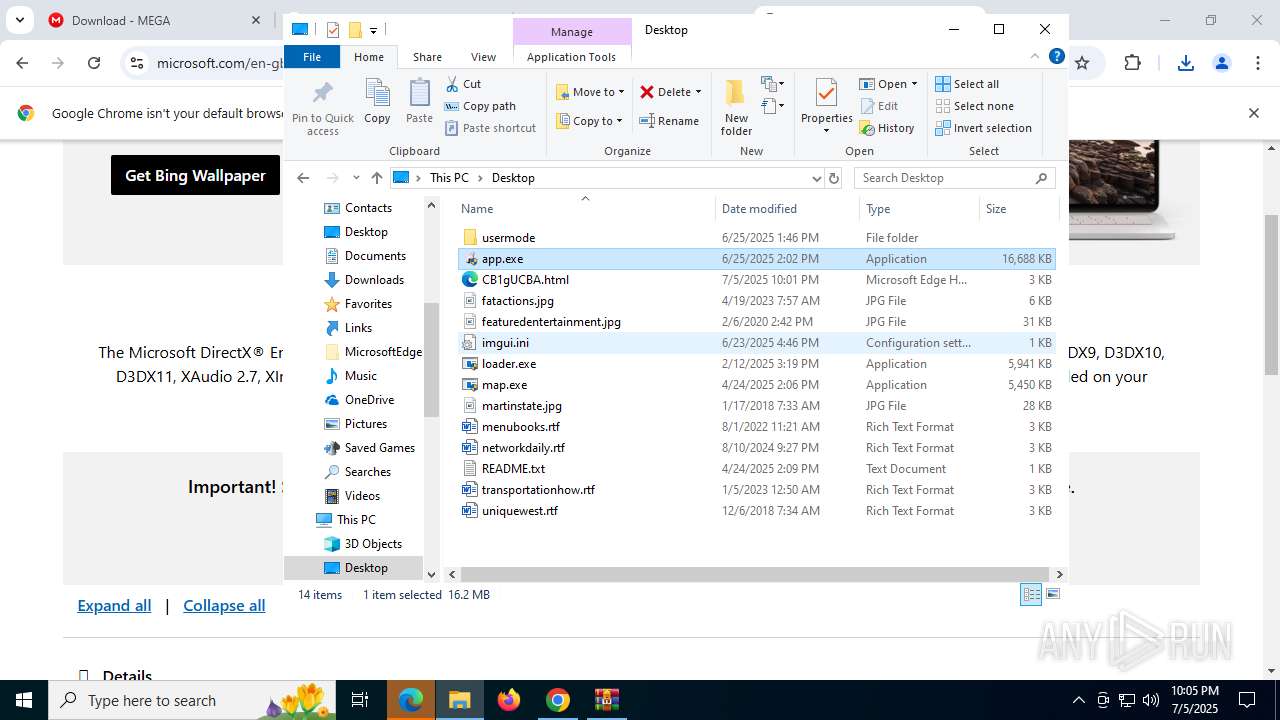
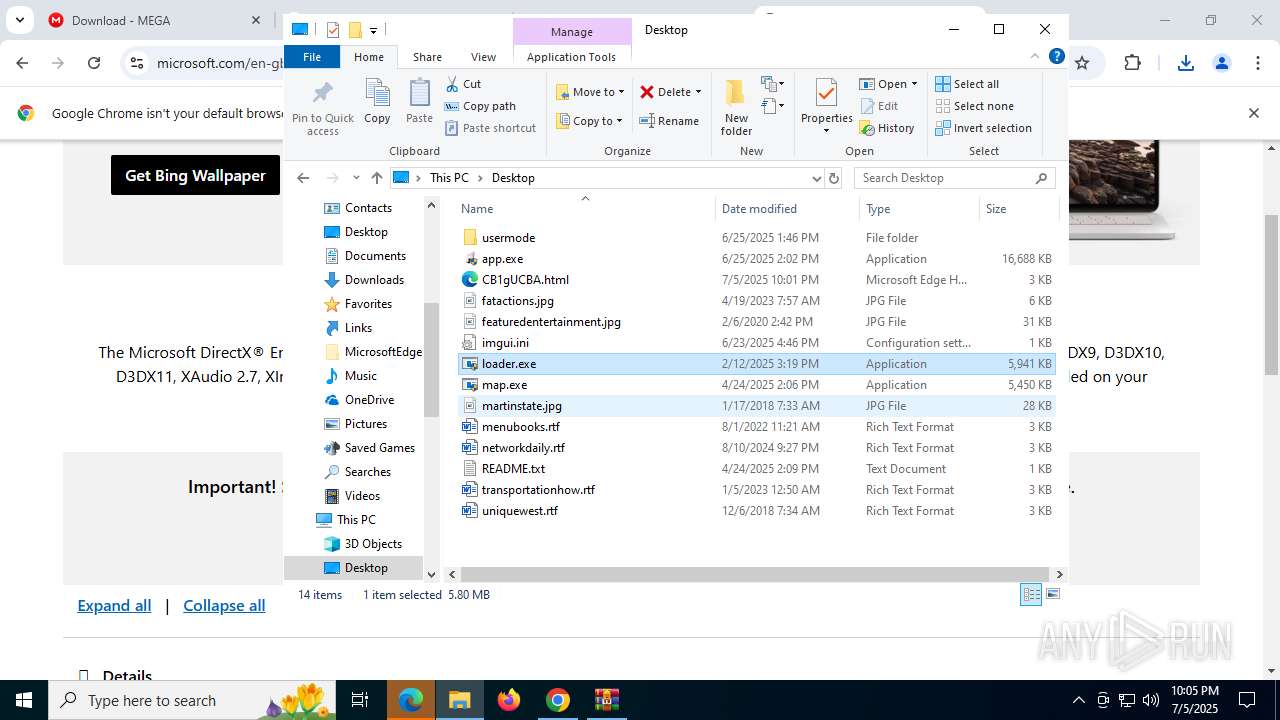
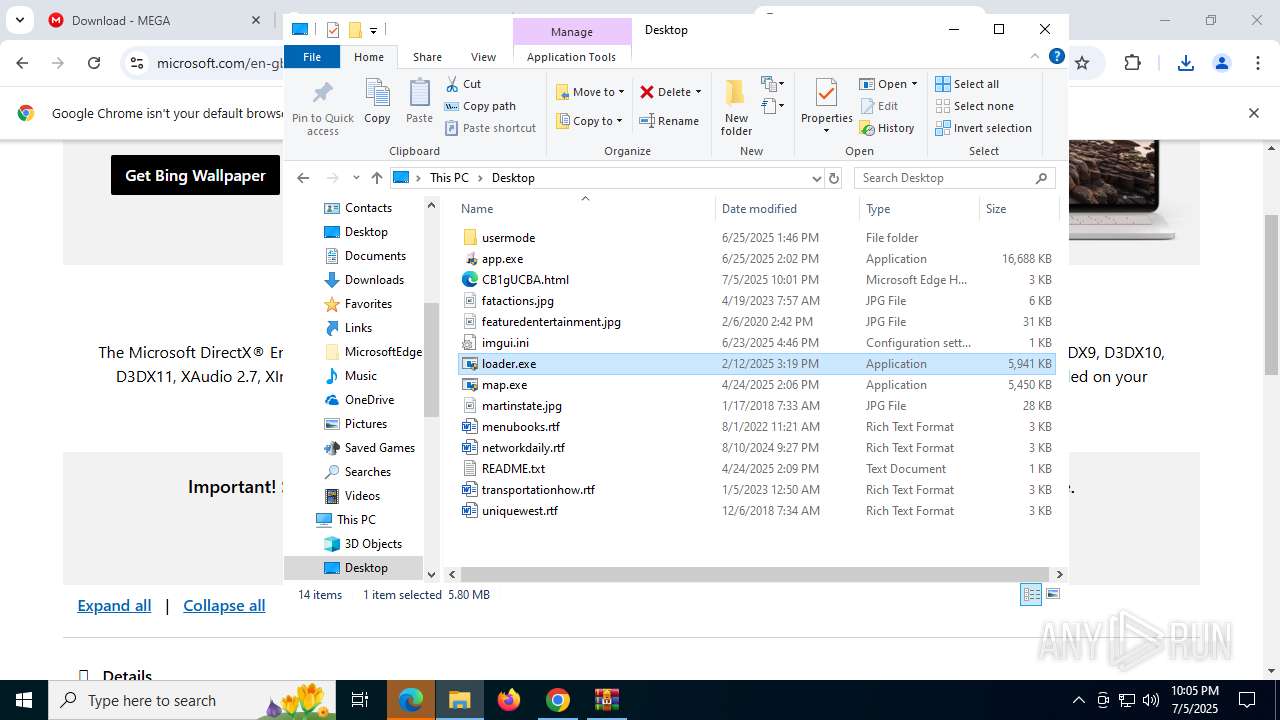
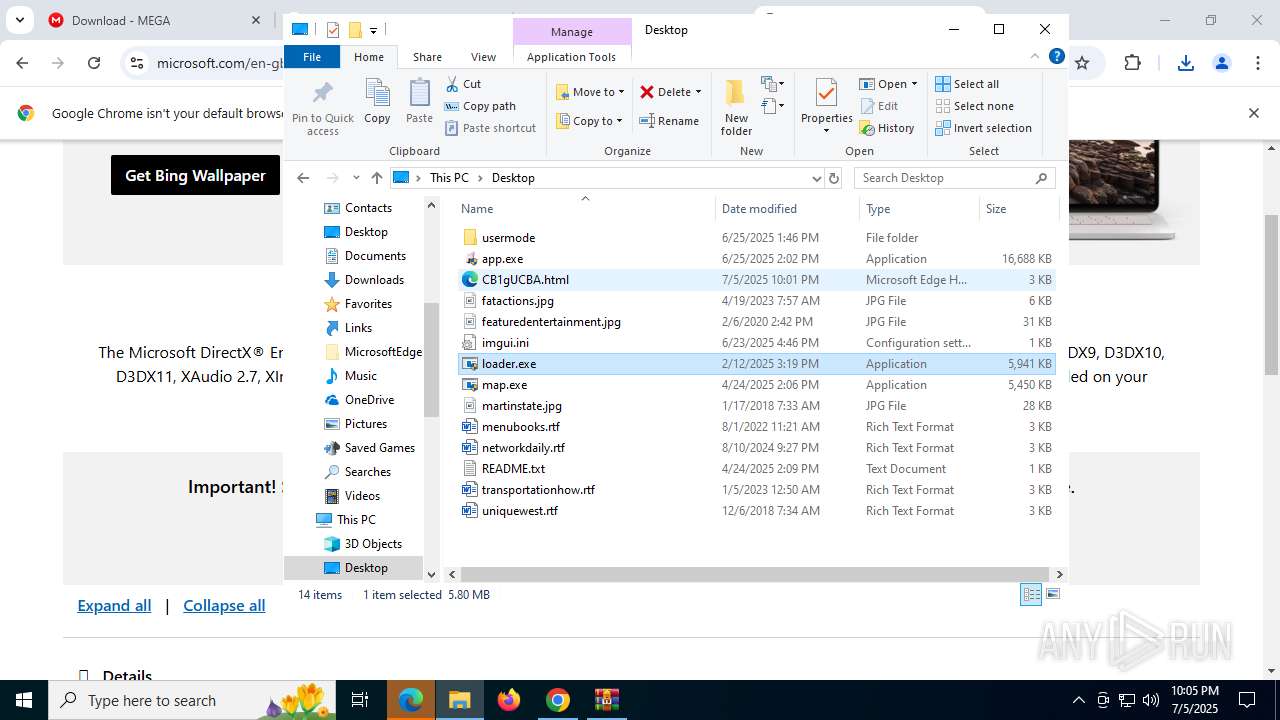
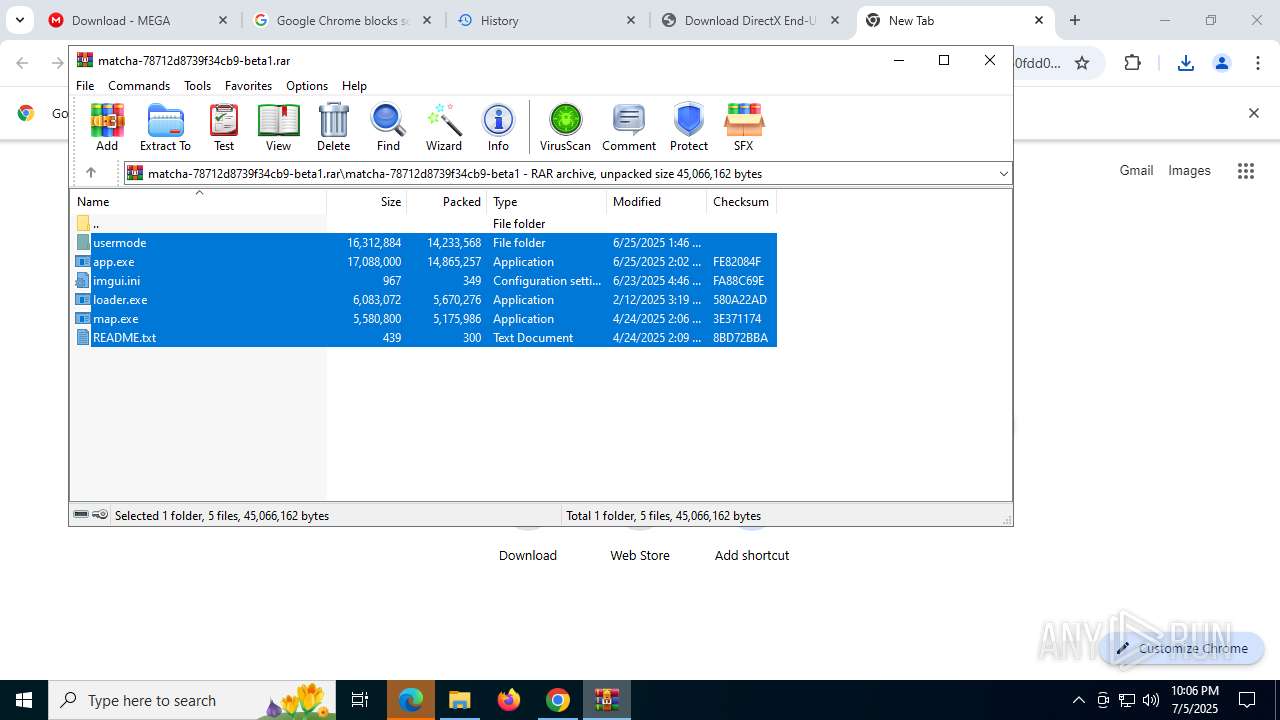
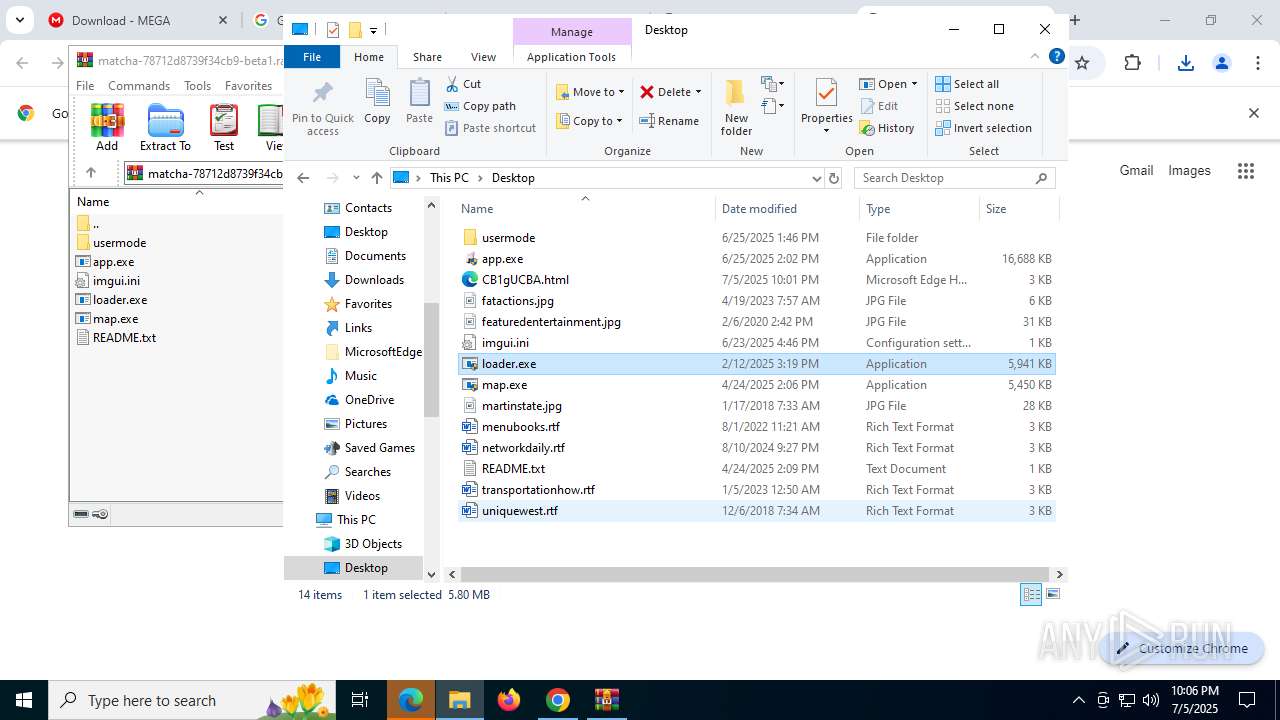
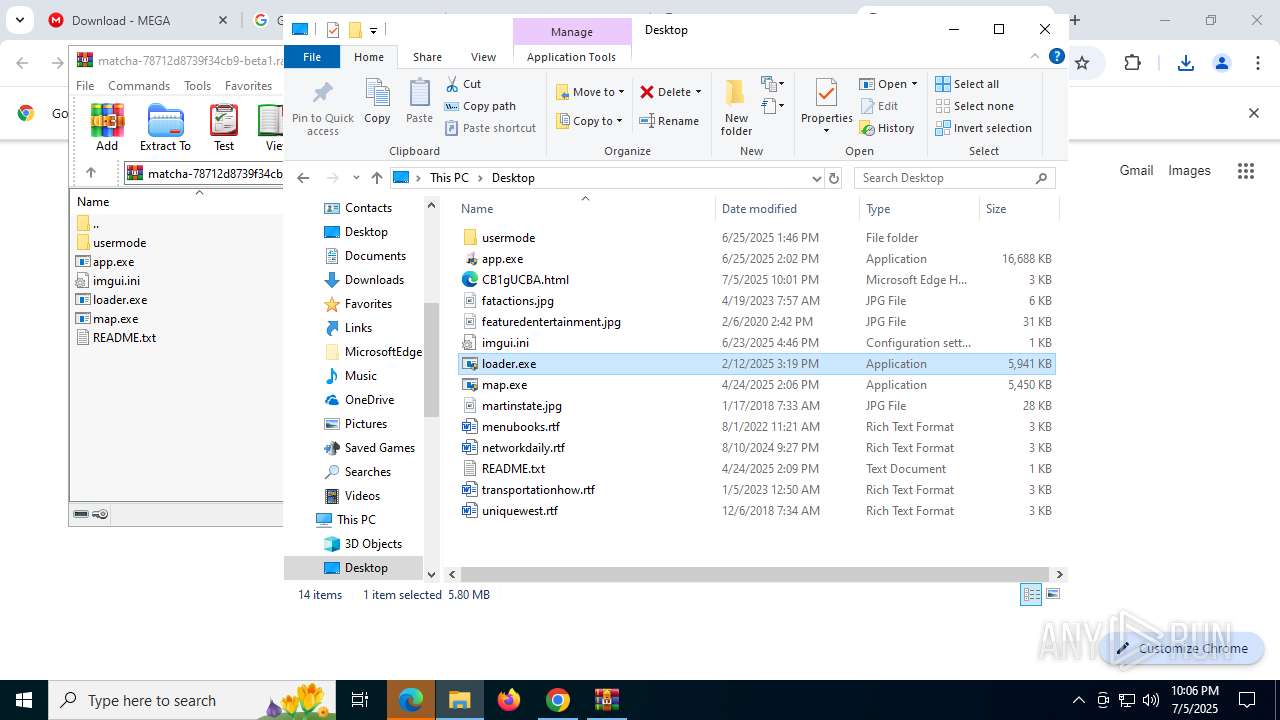
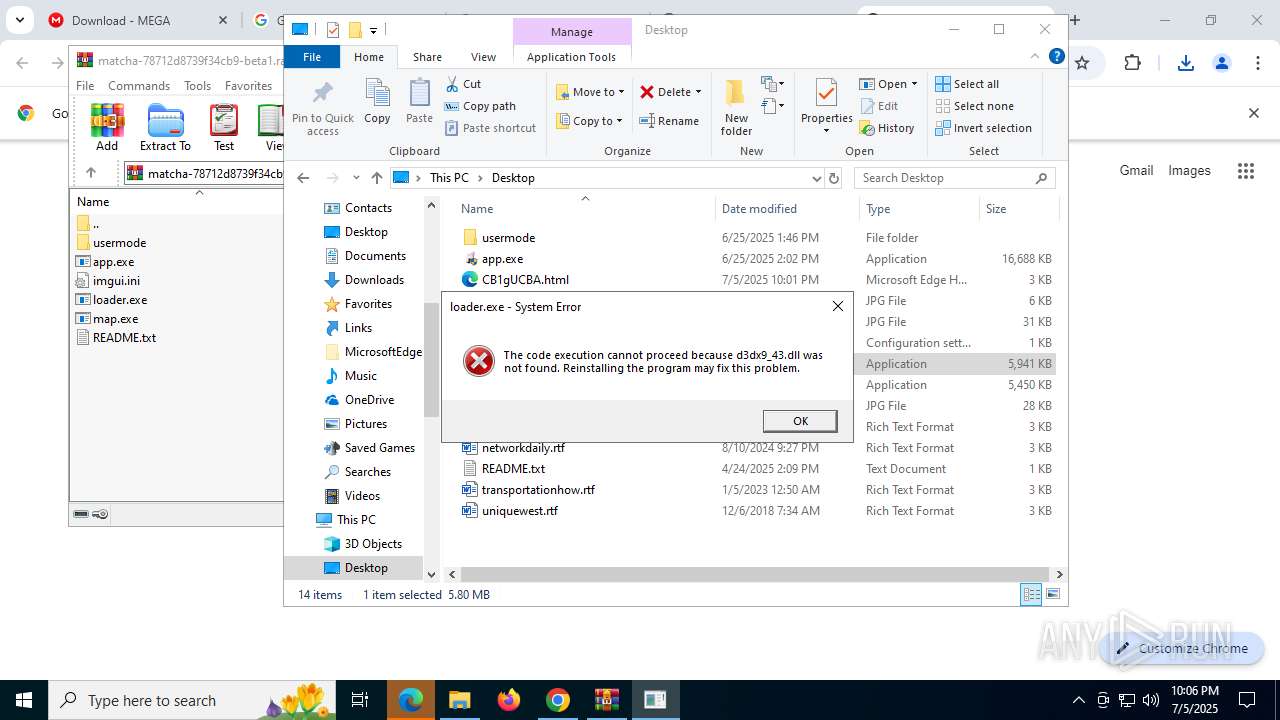
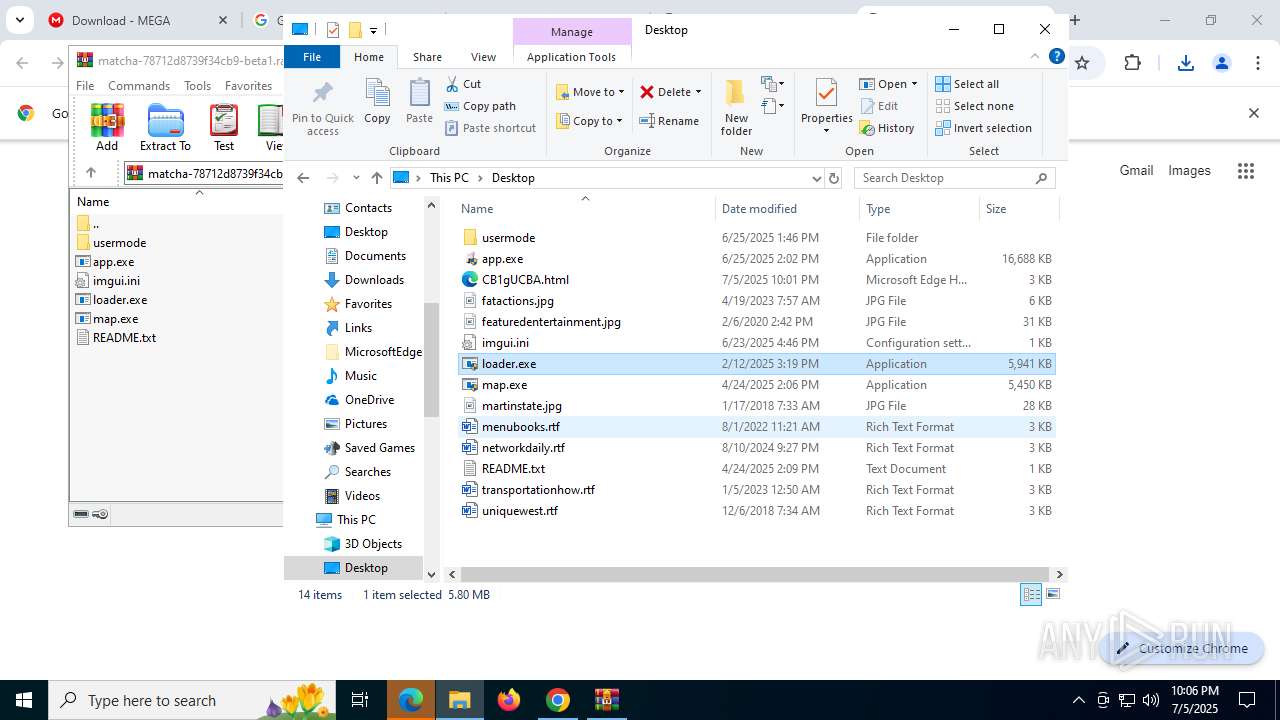
Manual execution by a user
- chrome.exe (PID: 2612)
- loader.exe (PID: 8008)
- loader.exe (PID: 1080)
- app.exe (PID: 7828)
- app.exe (PID: 3836)
- rundll32.exe (PID: 5436)
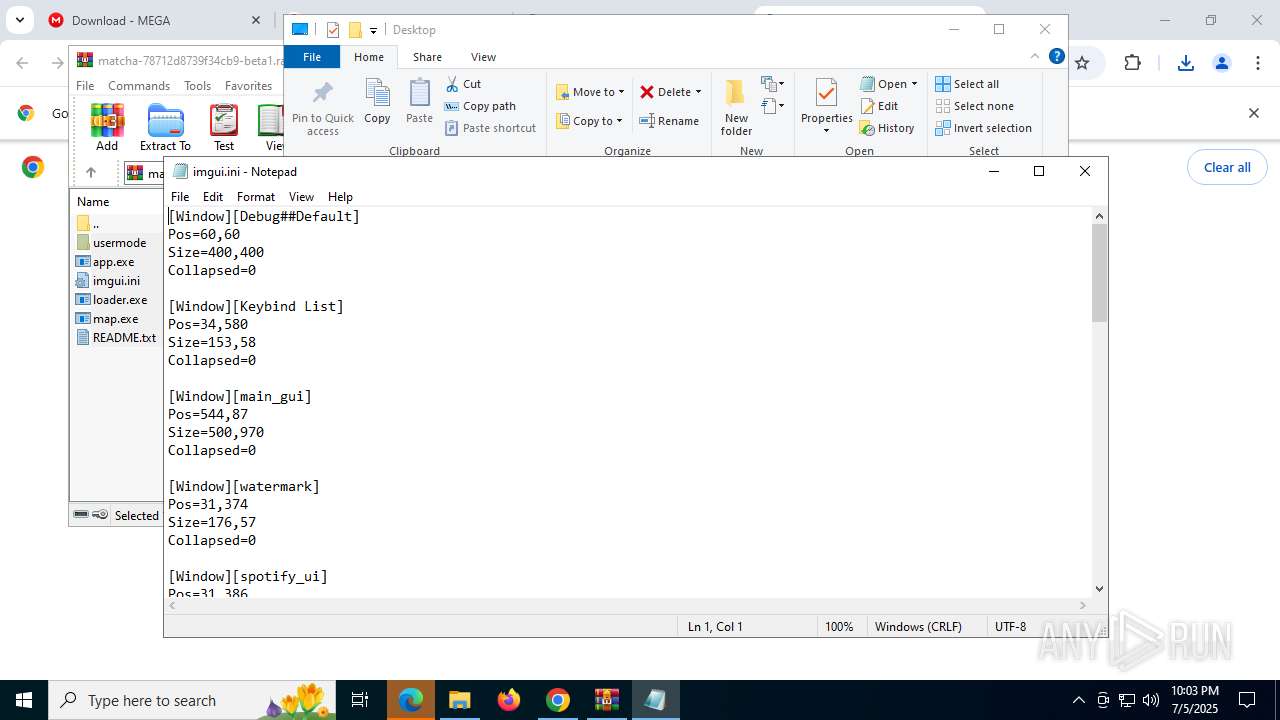
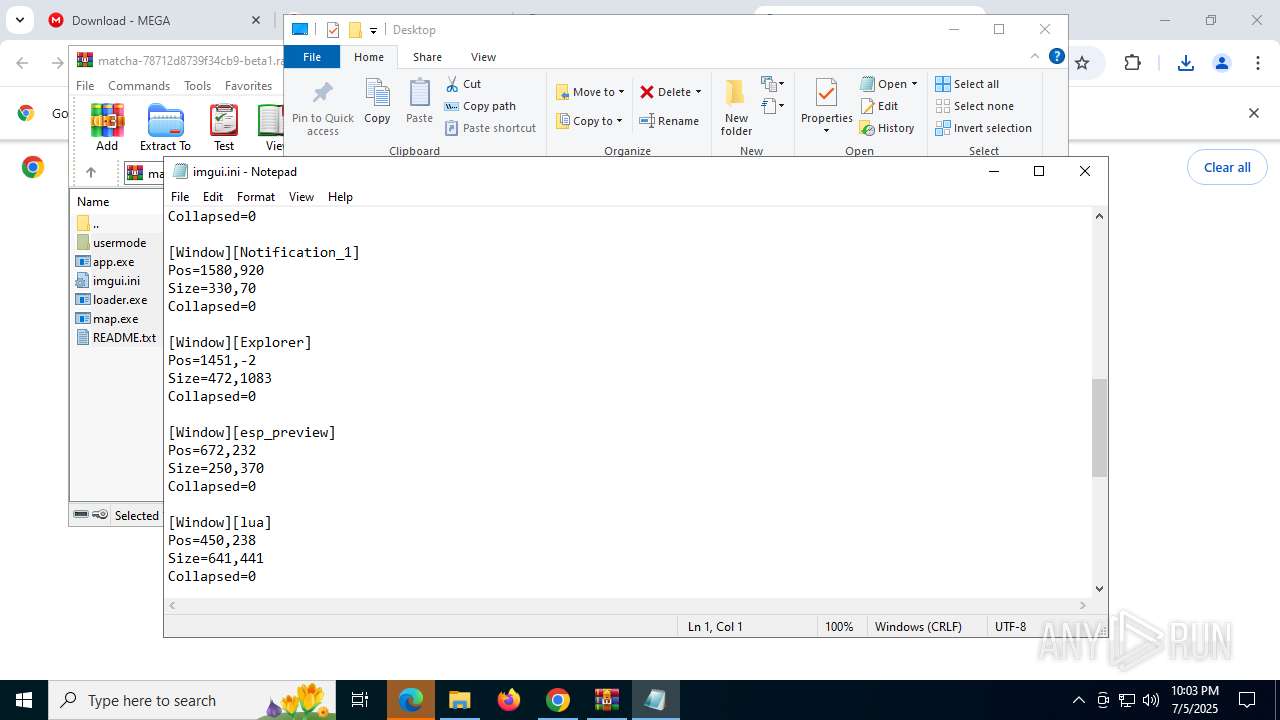
- notepad.exe (PID: 4560)
- loader.exe (PID: 2508)
- loader.exe (PID: 6668)
- loader.exe (PID: 6492)
- loader.exe (PID: 2800)
- VC_redist.x86.exe (PID: 5172)
- VC_redist.x64.exe (PID: 6600)
- loader.exe (PID: 5884)
- map.exe (PID: 5276)
- map.exe (PID: 2996)
- loader.exe (PID: 6068)
- map.exe (PID: 7996)
- map.exe (PID: 4372)
Application launched itself
- msedge.exe (PID: 4324)
- chrome.exe (PID: 2612)
Checks supported languages
- identity_helper.exe (PID: 7520)
- dxwebsetup.exe (PID: 5456)
- dxwsetup.exe (PID: 7016)
- infinst.exe (PID: 2296)
- infinst.exe (PID: 7368)
- infinst.exe (PID: 6756)
- infinst.exe (PID: 7220)
- VC_redist.x64.exe (PID: 8124)
- VC_redist.x64.exe (PID: 7324)
- VC_redist.x64.exe (PID: 3504)
- msiexec.exe (PID: 7332)
- VC_redist.x64.exe (PID: 8000)
- VC_redist.x64.exe (PID: 436)
- VC_redist.x64.exe (PID: 6652)
- VC_redist.x86.exe (PID: 6004)
- VC_redist.x86.exe (PID: 7440)
- VC_redist.x86.exe (PID: 7416)
- VC_redist.x86.exe (PID: 5172)
- VC_redist.x86.exe (PID: 7408)
- VC_redist.x86.exe (PID: 3724)
- VC_redist.x86.exe (PID: 7372)
- VC_redist.x86.exe (PID: 5924)
- VC_redist.x86.exe (PID: 1148)
- VC_redist.x64.exe (PID: 6600)
- VC_redist.x64.exe (PID: 3900)
- VC_redist.x64.exe (PID: 6948)
- map.exe (PID: 5276)
- map.exe (PID: 4372)
Reads Environment values
- identity_helper.exe (PID: 7520)
Reads the computer name
- identity_helper.exe (PID: 7520)
- dxwsetup.exe (PID: 7016)
- VC_redist.x64.exe (PID: 7324)
- VC_redist.x64.exe (PID: 3504)
- msiexec.exe (PID: 7332)
- VC_redist.x64.exe (PID: 436)
- VC_redist.x86.exe (PID: 7440)
- VC_redist.x86.exe (PID: 7416)
- VC_redist.x86.exe (PID: 7372)
- VC_redist.x86.exe (PID: 1148)
- VC_redist.x64.exe (PID: 6948)
- VC_redist.x86.exe (PID: 7408)
- map.exe (PID: 5276)
- map.exe (PID: 4372)
- VC_redist.x64.exe (PID: 6652)
Reads Microsoft Office registry keys
- chrome.exe (PID: 2612)
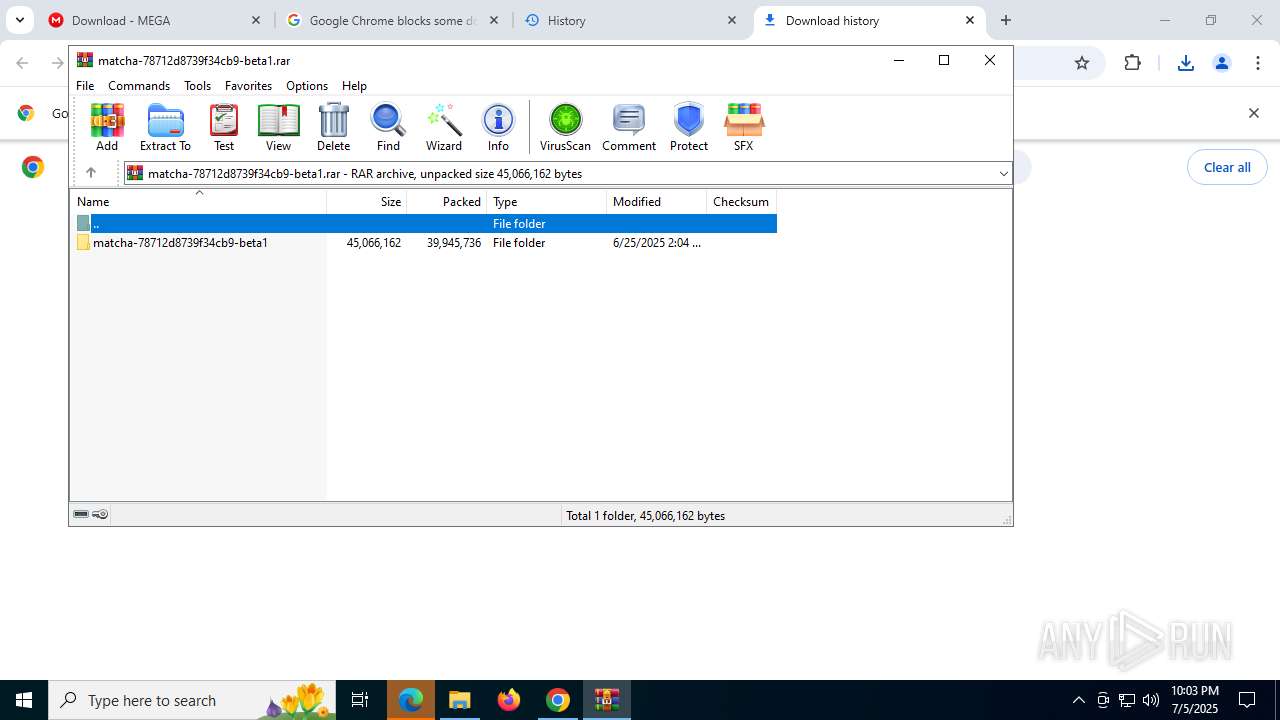
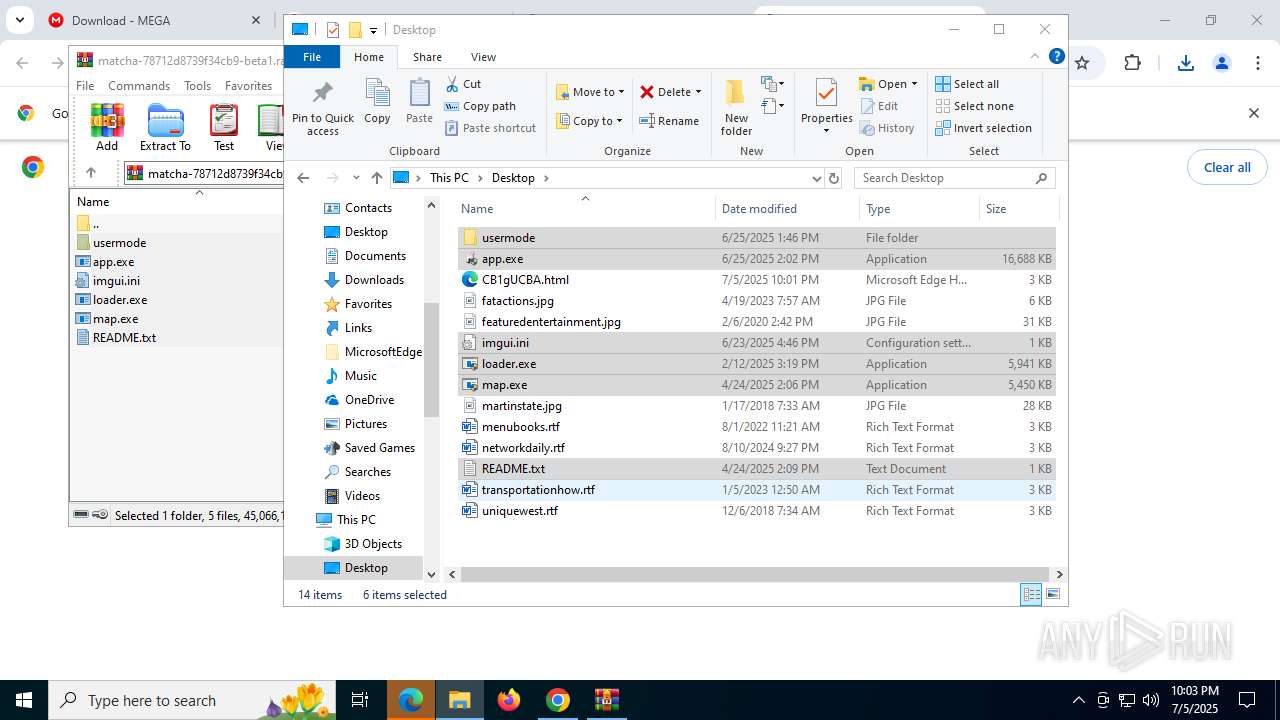
Executable content was dropped or overwritten
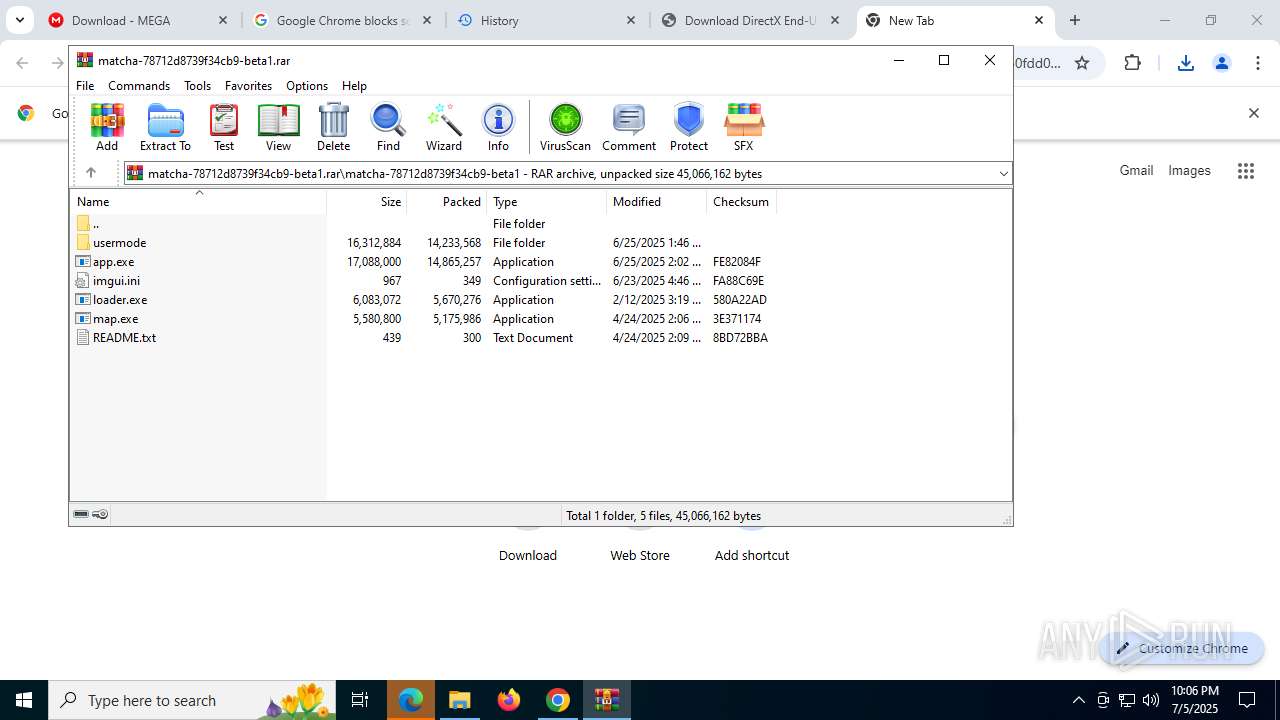
- WinRAR.exe (PID: 8028)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 7704)
- msiexec.exe (PID: 7332)
Reads security settings of Internet Explorer
- notepad.exe (PID: 4560)
Reads the software policy settings
- slui.exe (PID: 7392)
- dxwsetup.exe (PID: 7016)
- msiexec.exe (PID: 7332)
The sample compiled with english language support
- chrome.exe (PID: 2612)
- dxwebsetup.exe (PID: 5456)
- dxwsetup.exe (PID: 7016)
- chrome.exe (PID: 7704)
- infinst.exe (PID: 2296)
- infinst.exe (PID: 7368)
- infinst.exe (PID: 6756)
- infinst.exe (PID: 7220)
- VC_redist.x64.exe (PID: 7324)
- VC_redist.x64.exe (PID: 3504)
- msiexec.exe (PID: 7332)
- VC_redist.x64.exe (PID: 436)
- VC_redist.x64.exe (PID: 6652)
- VC_redist.x64.exe (PID: 8124)
- VC_redist.x86.exe (PID: 6004)
- VC_redist.x86.exe (PID: 7440)
- VC_redist.x86.exe (PID: 7416)
- VC_redist.x86.exe (PID: 7408)
- VC_redist.x86.exe (PID: 7372)
- VC_redist.x86.exe (PID: 1148)
- VC_redist.x64.exe (PID: 6948)
- map.exe (PID: 5276)
- map.exe (PID: 4372)
Create files in a temporary directory
- dxwebsetup.exe (PID: 5456)
- dxwsetup.exe (PID: 7016)
- VC_redist.x64.exe (PID: 8124)
- VC_redist.x64.exe (PID: 7324)
- VC_redist.x64.exe (PID: 3504)
- VC_redist.x86.exe (PID: 6004)
- VC_redist.x86.exe (PID: 7440)
- VC_redist.x86.exe (PID: 7416)
- VC_redist.x86.exe (PID: 7408)
- VC_redist.x86.exe (PID: 7372)
- VC_redist.x64.exe (PID: 6948)
- VC_redist.x64.exe (PID: 436)
- map.exe (PID: 4372)
- map.exe (PID: 5276)
Launching a file from a Registry key
- dxwebsetup.exe (PID: 5456)
- VC_redist.x64.exe (PID: 3504)
- VC_redist.x86.exe (PID: 7416)
Checks proxy server information
- slui.exe (PID: 7392)
- dxwsetup.exe (PID: 7016)
Reads the machine GUID from the registry
- dxwsetup.exe (PID: 7016)
- VC_redist.x64.exe (PID: 3504)
- msiexec.exe (PID: 7332)
- VC_redist.x86.exe (PID: 7416)
Creates files or folders in the user directory
- dxwsetup.exe (PID: 7016)
Manages system restore points
- SrTasks.exe (PID: 504)
Process checks computer location settings
- VC_redist.x64.exe (PID: 7324)
- VC_redist.x86.exe (PID: 7440)
- VC_redist.x86.exe (PID: 7372)
- VC_redist.x64.exe (PID: 436)
Creates files in the program directory
- VC_redist.x64.exe (PID: 3504)
- VC_redist.x86.exe (PID: 7416)
Creates a software uninstall entry
- msiexec.exe (PID: 7332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| ContentType: | text/html, charset=UTF-8 |
|---|---|
| Referrer: | strict-origin-when-cross-origin |
Total processes
284
Monitored processes
124
Malicious processes
23
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --string-annotations --field-trial-handle=7404,i,15243910148804955315,15894146645259690070,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=7784 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 360 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5436,i,6537067093000401792,3189939801640770536,262144 --variations-seed-version --mojo-platform-channel-handle=4960 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=7560,i,15243910148804955315,15894146645259690070,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=7352 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 436 | "C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe" -burn.clean.room="C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe" -burn.filehandle.attached=508 -burn.filehandle.self=528 -uninstall -quiet -burn.related.upgrade -burn.ancestors={77169412-f642-45e7-b533-0c6f48de12f9} -burn.filehandle.self=1192 -burn.embedded BurnPipe.{782CDB09-BBB5-490D-AA8C-D88D74C5AFDF} {A31752FC-6998-4BDC-925A-4B558441D7EE} 3504 | C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe | VC_redist.x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
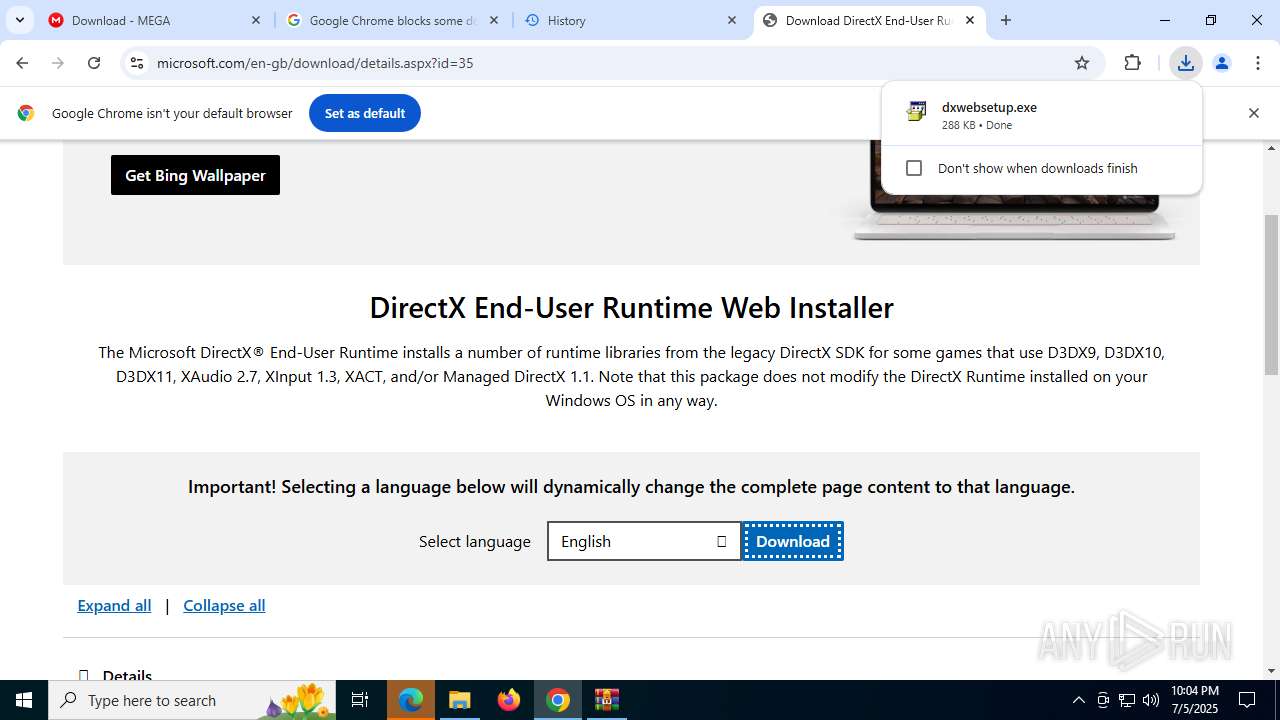
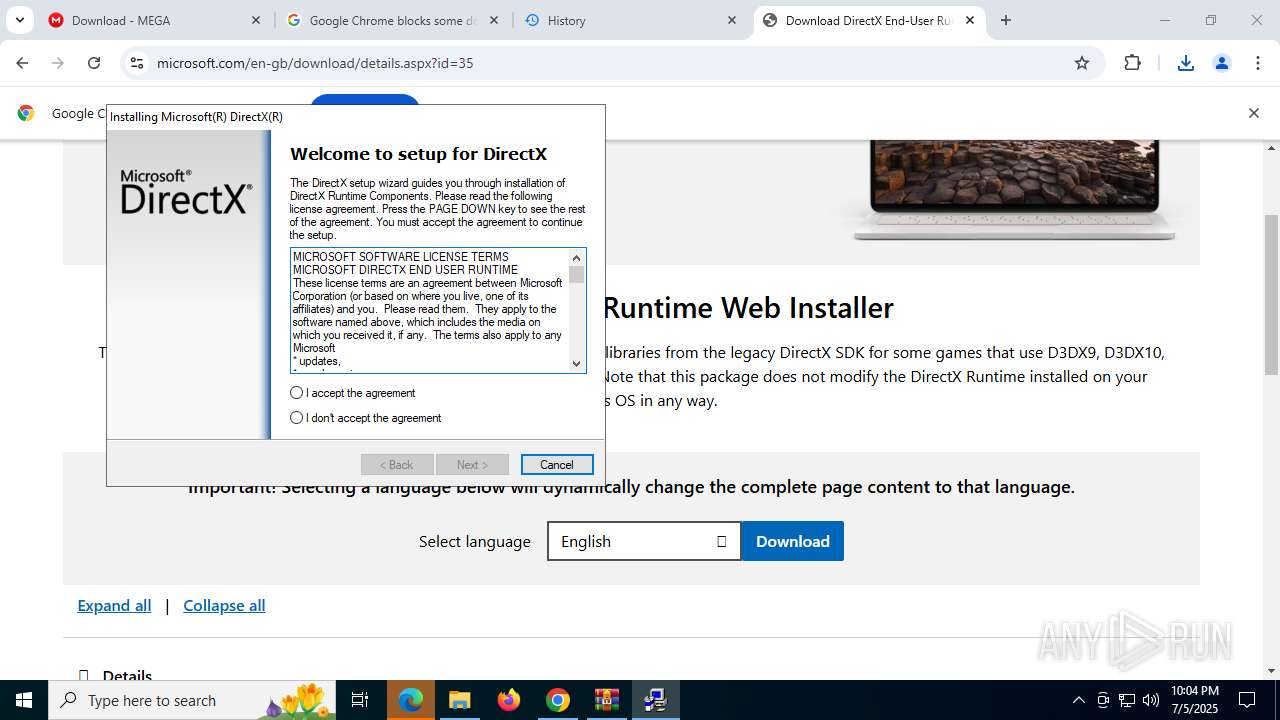
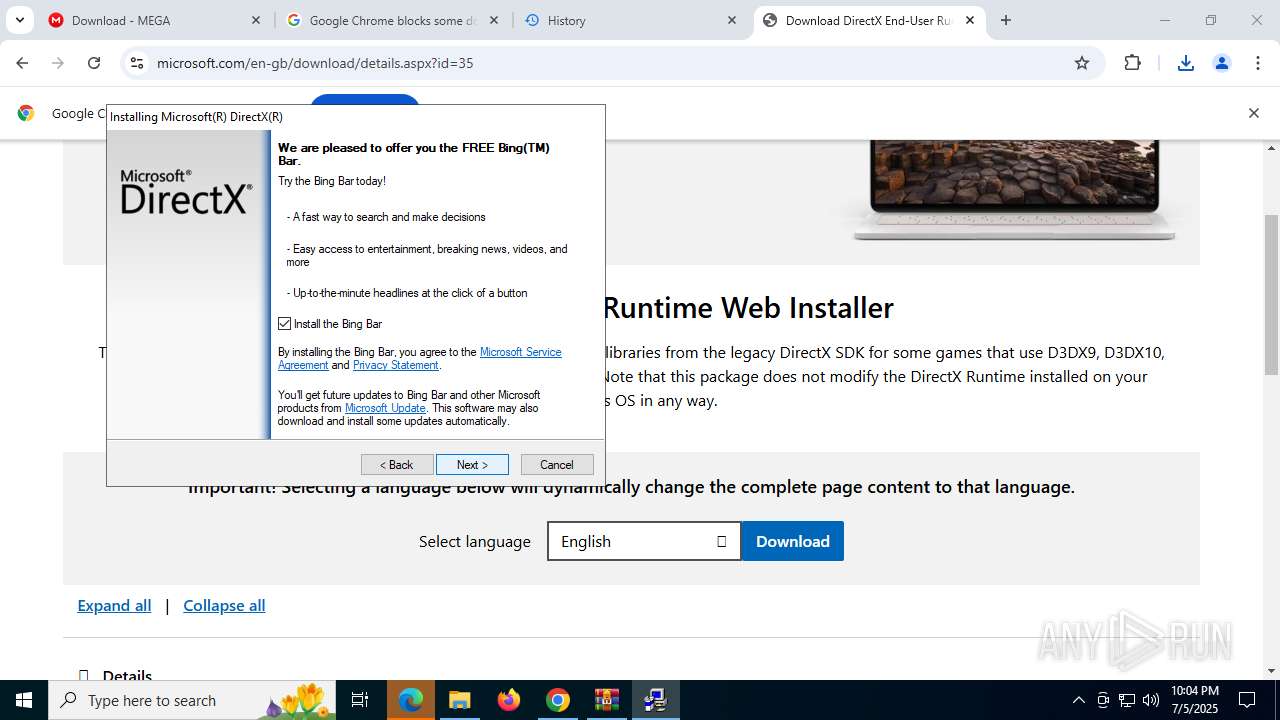
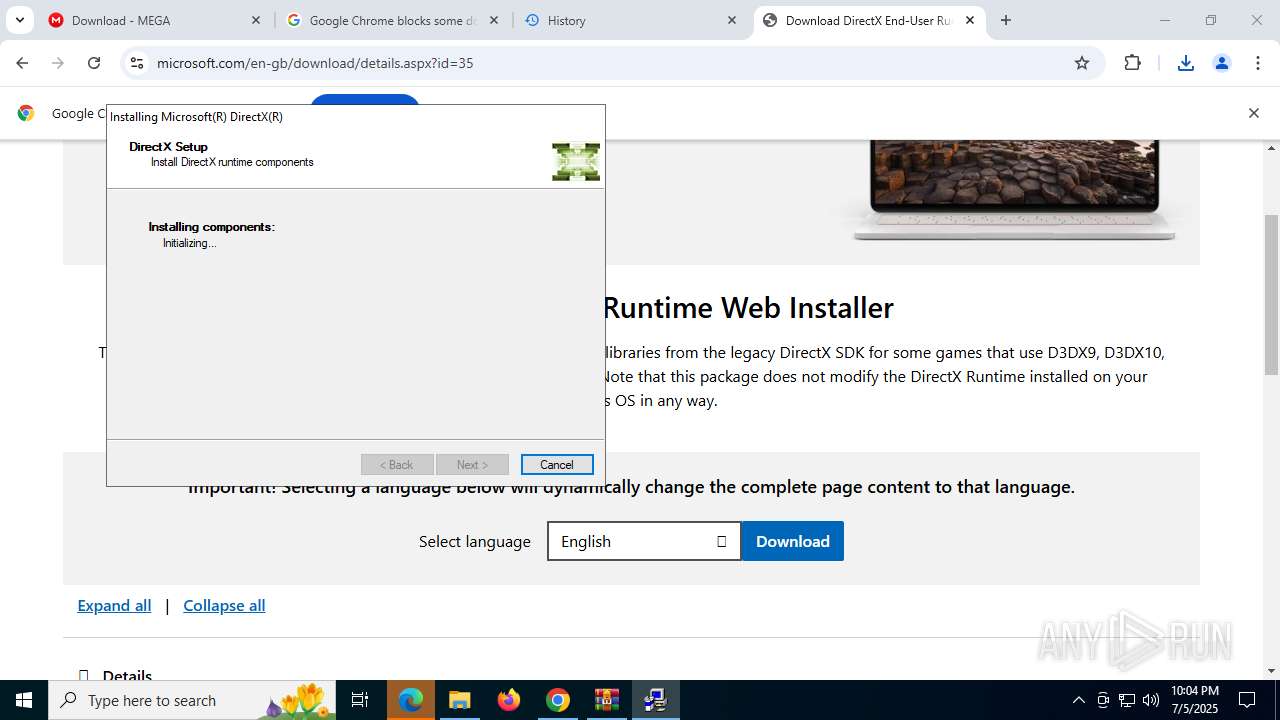
| 504 | "C:\Users\admin\Downloads\dxwebsetup.exe" | C:\Users\admin\Downloads\dxwebsetup.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DirectX 9.0 Web setup Exit code: 3221226540 Version: 9.29.1974.0 Modules
| |||||||||||||||
| 504 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=6768,i,15243910148804955315,15894146645259690070,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=7012 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
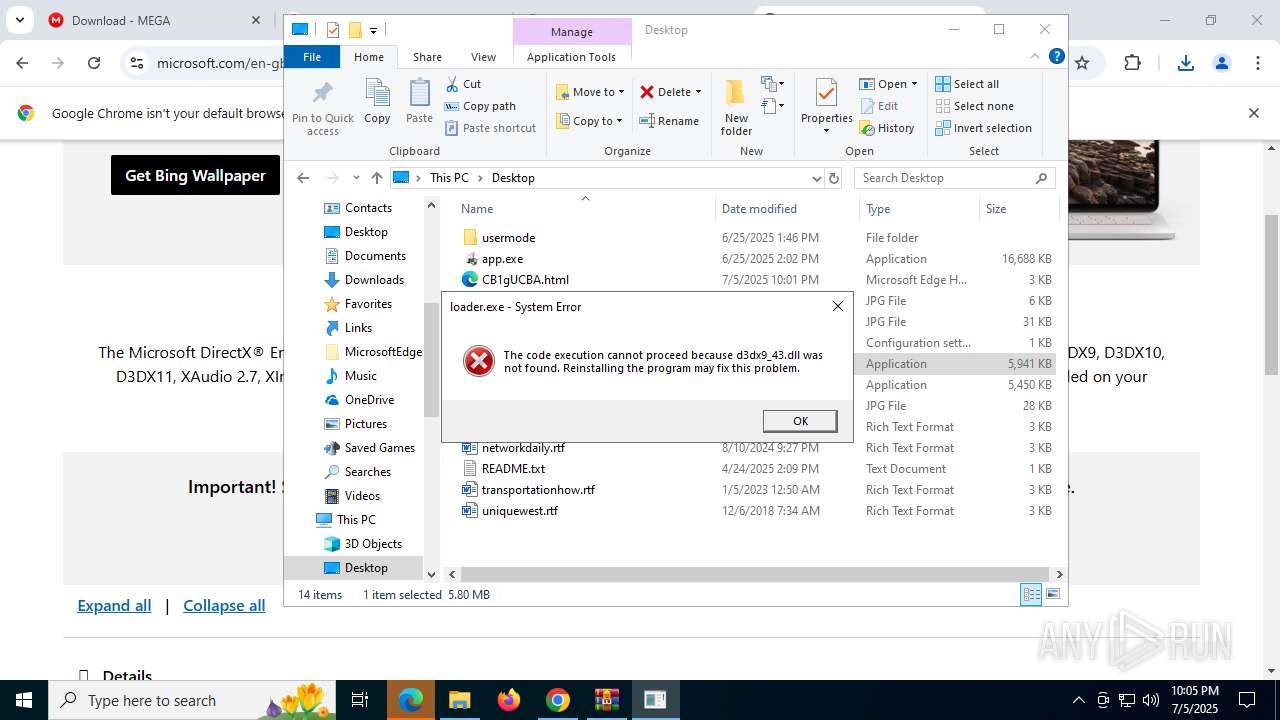
| 1080 | "C:\Users\admin\Desktop\loader.exe" | C:\Users\admin\Desktop\loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225781 Modules
| |||||||||||||||
| 1148 | "C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe" -q -burn.elevated BurnPipe.{E490BC6F-DB38-41AA-8BD7-3929683A7DB4} {DFA3A810-B87D-4DA5-962A-EA9F5F593E5F} 7372 | C:\ProgramData\Package Cache\{410c0ee1-00bb-41b6-9772-e12c2828b02f}\VC_redist.x86.exe | VC_redist.x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x86) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 1612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5364,i,6537067093000401792,3189939801640770536,262144 --variations-seed-version --mojo-platform-channel-handle=3624 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
42 462
Read events
40 707
Write events
1 123
Delete events
632
Modification events
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3100) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (4324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2612) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
229
Suspicious files
1 019
Text files
306
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17638c.TMP | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17638c.TMP | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF17639c.TMP | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF17638c.TMP | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1763ab.TMP | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF17638c.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
85
TCP/UDP connections
228
DNS requests
257
Threats
40
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1964 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4444 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:fNNPpa98-2mZCVlP74s8RmMPYjnF3wY6clnAJKMLyaw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5552 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5552 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8076 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751984814&P2=404&P3=2&P4=R7R1BFKV2u6lNtudUQ4LuK4AjptPHyQVGeghIiFiN9%2feBnpaFJe6wGvwp7JYRU3ixtwrvJoTkHqeRMezWT1Znw%3d%3d | unknown | — | — | whitelisted |
8076 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751984814&P2=404&P3=2&P4=R7R1BFKV2u6lNtudUQ4LuK4AjptPHyQVGeghIiFiN9%2feBnpaFJe6wGvwp7JYRU3ixtwrvJoTkHqeRMezWT1Znw%3d%3d | unknown | — | — | whitelisted |
8076 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
8076 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751984814&P2=404&P3=2&P4=R7R1BFKV2u6lNtudUQ4LuK4AjptPHyQVGeghIiFiN9%2feBnpaFJe6wGvwp7JYRU3ixtwrvJoTkHqeRMezWT1Znw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4680 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4444 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4444 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4444 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4444 | msedge.exe | 104.126.37.169:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
4444 | msedge.exe | 142.250.186.99:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
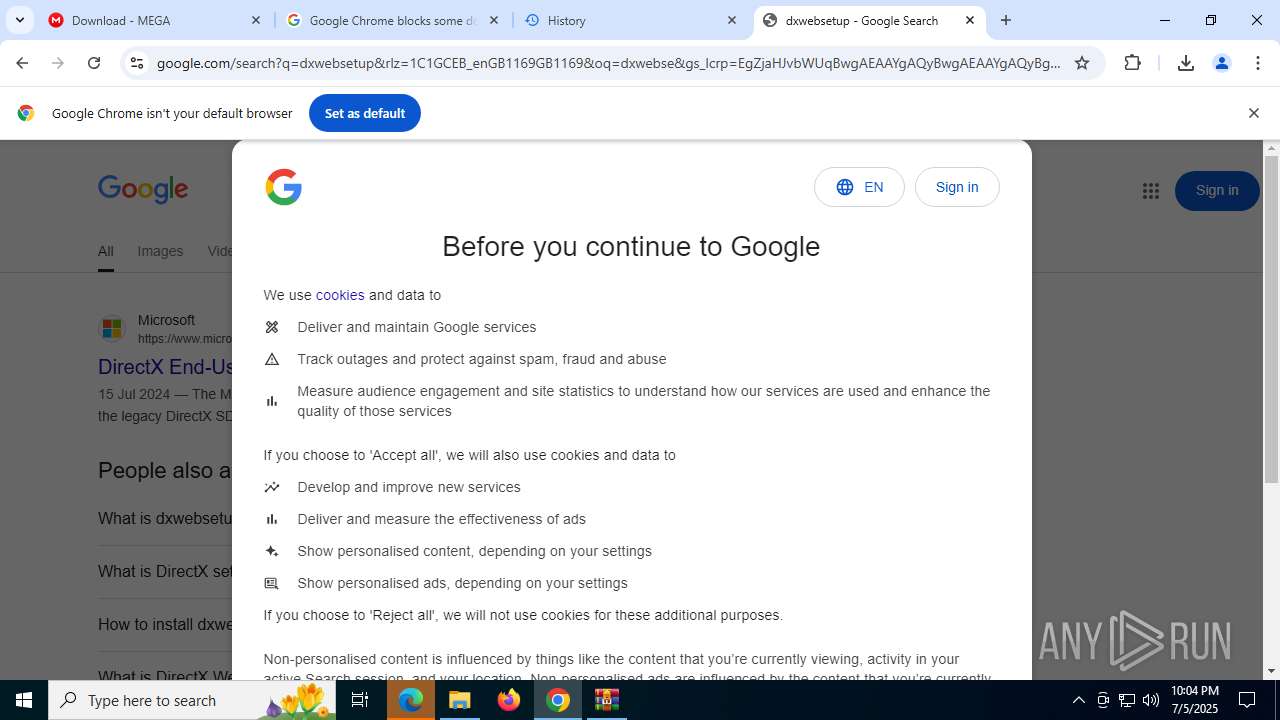
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
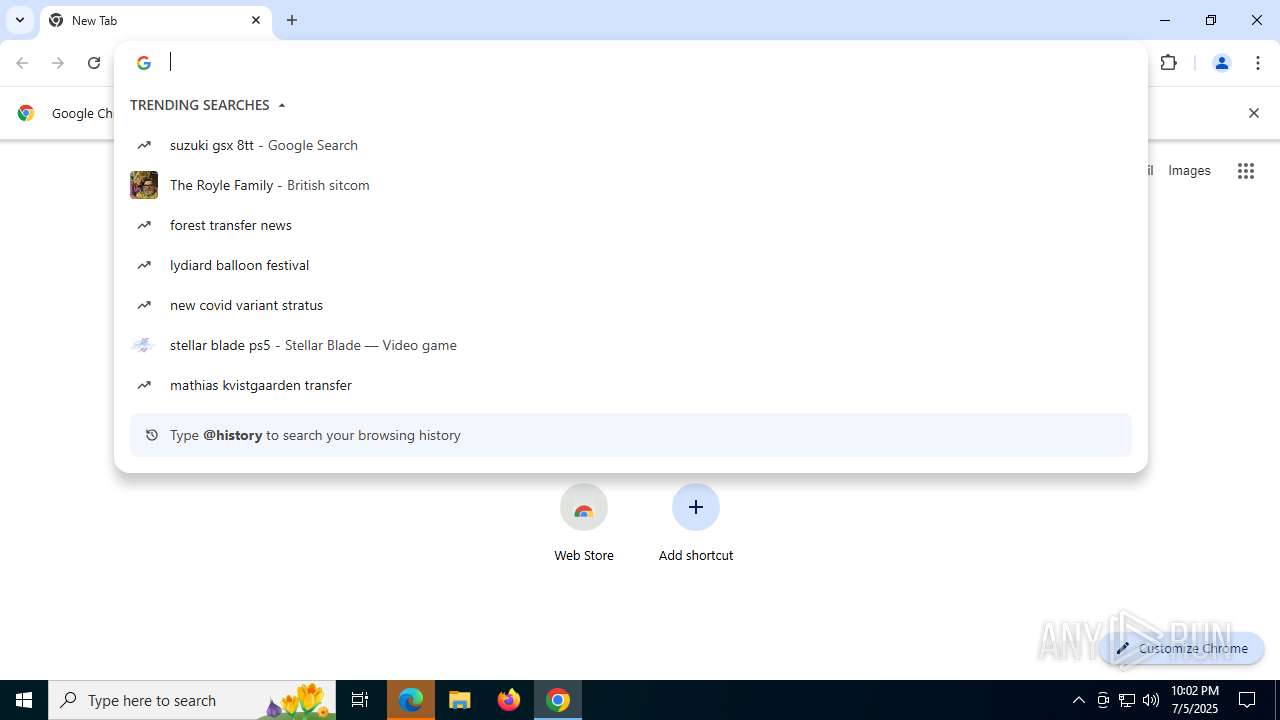
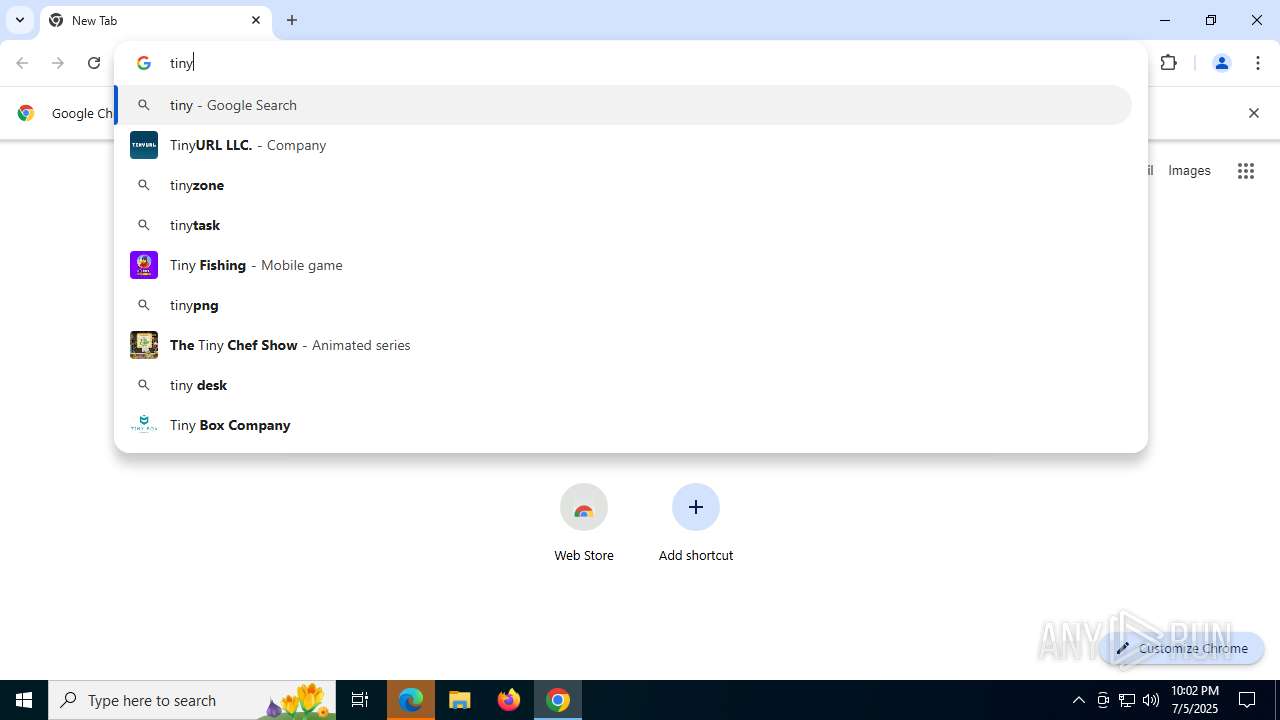
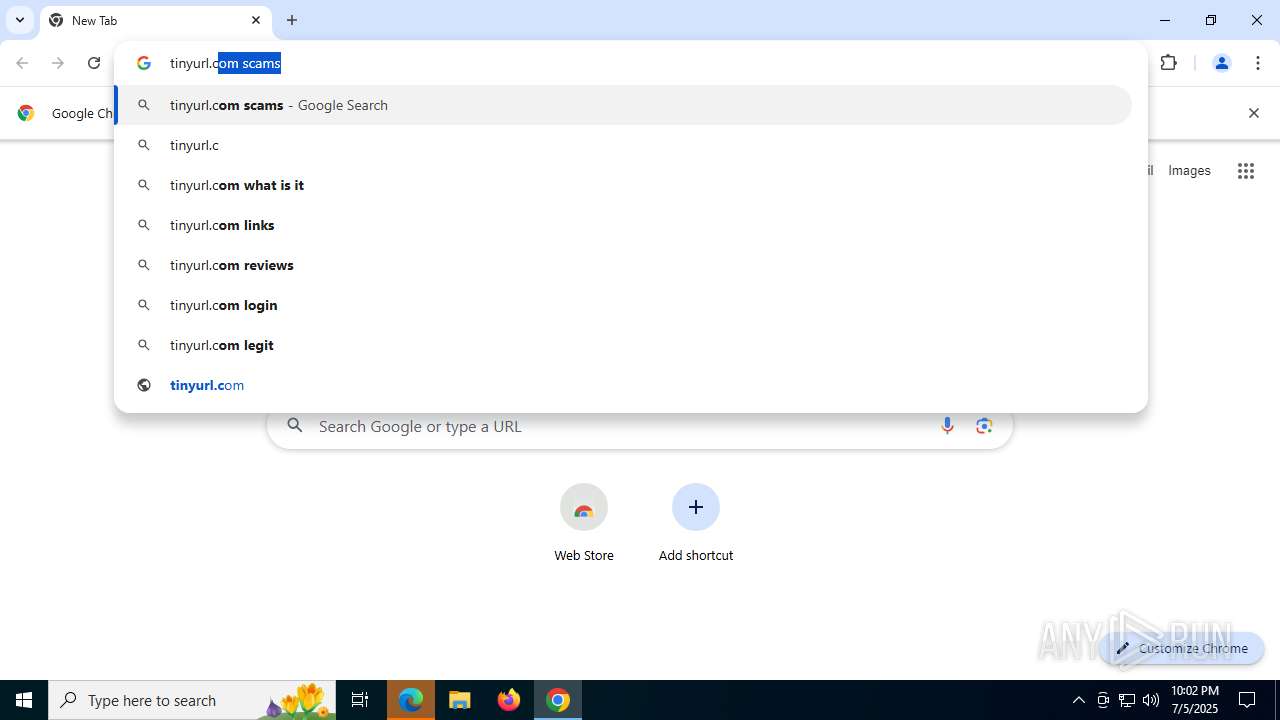
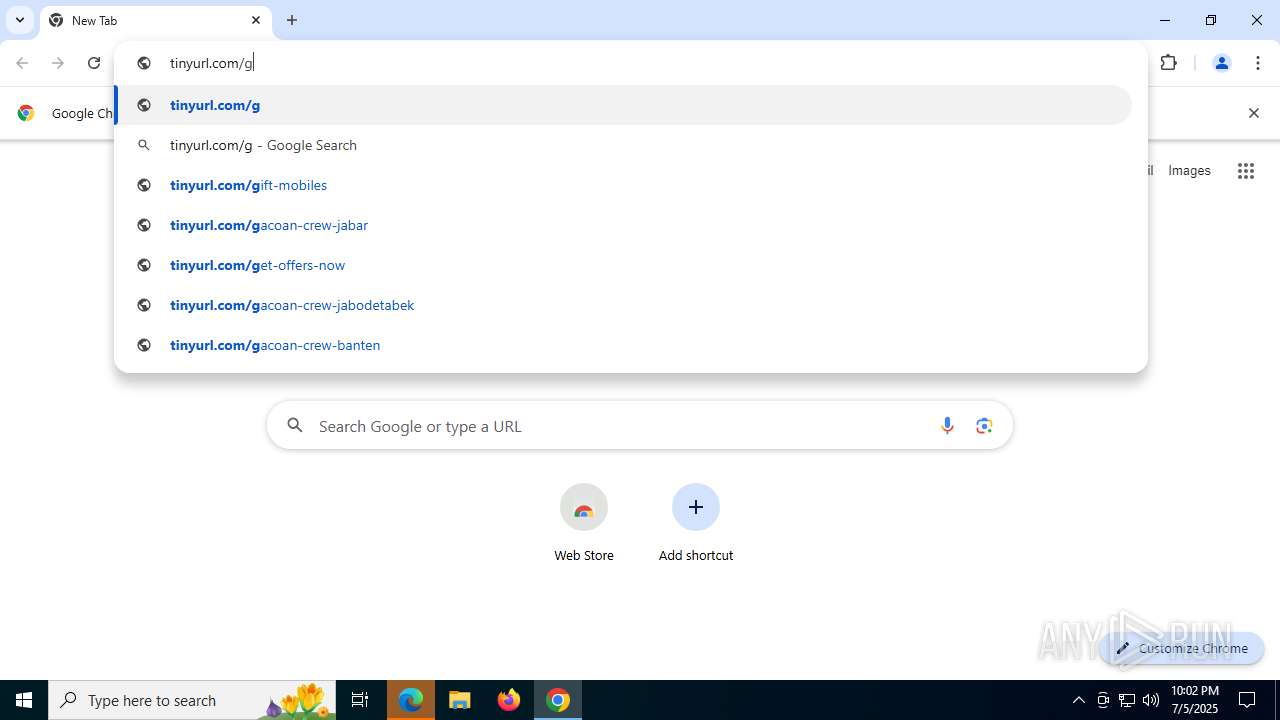
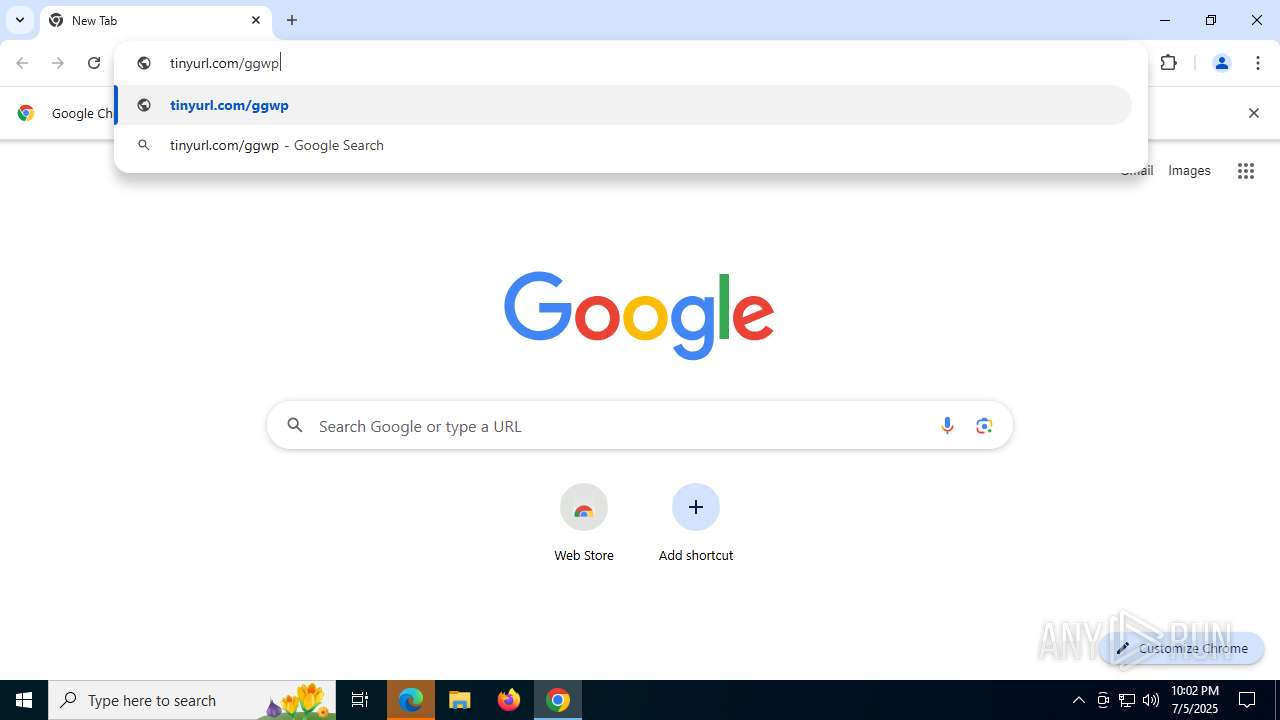
7704 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (tinyurl .com) |
7704 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (tinyurl .com) |
7704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] URL Shortener TinyURL (tinyurl .com) |
7704 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (tinyurl .com) |
7704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] URL Shortener TinyURL (tinyurl .com) |
7704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] URL Shortener TinyURL (tinyurl .com) |
7704 | chrome.exe | Misc activity | INFO [ANY.RUN] Possible short link service (tinyurl .com) |
7704 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] URL Shortener TinyURL (tinyurl .com) |
7704 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7704 | chrome.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
Process | Message |
|---|---|
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | Invalid parameter passed to C runtime function.
|
dxwsetup.exe | Invalid parameter passed to C runtime function.
|
dxwsetup.exe | DLL_PROCESS_DETACH |
dxwsetup.exe | DLL_PROCESS_DETACH |
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | DLL_PROCESS_DETACH |
dxwsetup.exe | DLL_PROCESS_DETACH |