| URL: | https://nam10.safelinks.protection.outlook.com/?url=http%3A%2F%2Fi.ms00.net%2Fsubscribe%3Fserver_action%3DUnsubscribe%26list%3Dplainid%26sublist%3D*%26msgid%3D1596653605.57962%26email_address%3Dmarco.coderoni%2540ansys.com&data=02%7C01%7Cdhara.gohel%40ansys.com%7Cb44b23c9757a4ec4396a08d83a55607b%7C34c6ce6715b84eff80e952da8be89706%7C0%7C0%7C637323485676158423&sdata=n6O1hF273NzsrfFhOGINgWlHcVdG3dhfvVjuCN13lkw%3D&reserved=0 |
| Full analysis: | https://app.any.run/tasks/de3e43ec-c454-4ee5-856c-c8598fc10ede |
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2020, 01:50:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 43319F26CC7DF7AE59AB90F77330ECE7 |
| SHA1: | 29FF95439193442DD68F0BCEA8EE3C1860666FB2 |
| SHA256: | F19273DCC61B59274909B751E812A70F8611DD94132C8755BC6EF3B4D1A77F76 |
| SSDEEP: | 6:2aD9V9iRXPNHszaDL0j/RCGkRxzOLUJTTA03HXNGYDg/MOrnWZ3liGnep3vioSm:2G9qVsWX0DRexKMMw3NGY0Z0dIfioSm |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2476)
- chrome.exe (PID: 1940)
Application launched itself
- chrome.exe (PID: 2476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
14
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,3877235429142306322,4886563849547066883,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6344935805585303868 --mojo-platform-channel-handle=3548 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,3877235429142306322,4886563849547066883,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9982997677354312452 --mojo-platform-channel-handle=1152 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,3877235429142306322,4886563849547066883,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3959355968547664264 --mojo-platform-channel-handle=3160 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,3877235429142306322,4886563849547066883,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18075278806708127423 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,3877235429142306322,4886563849547066883,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3969841069333960083 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2556 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,3877235429142306322,4886563849547066883,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3713395735809987588 --mojo-platform-channel-handle=3140 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,3877235429142306322,4886563849547066883,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=18371146317454483870 --mojo-platform-channel-handle=1560 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://nam10.safelinks.protection.outlook.com/?url=http%3A%2F%2Fi.ms00.net%2Fsubscribe%3Fserver_action%3DUnsubscribe%26list%3Dplainid%26sublist%3D*%26msgid%3D1596653605.57962%26email_address%3Dmarco.coderoni%2540ansys.com&data=02%7C01%7Cdhara.gohel%40ansys.com%7Cb44b23c9757a4ec4396a08d83a55607b%7C34c6ce6715b84eff80e952da8be89706%7C0%7C0%7C637323485676158423&sdata=n6O1hF273NzsrfFhOGINgWlHcVdG3dhfvVjuCN13lkw%3D&reserved=0" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,3877235429142306322,4886563849547066883,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17241543539481663574 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2456 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
606
Read events
521
Write events
80
Delete events
5
Modification events
| (PID) Process: | (2476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2612) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2476-13241238666534500 |
Value: 259 | |||
| (PID) Process: | (2476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2476) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2476) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
6
Text files
59
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5156c08c-10c5-44d3-860c-22164c51a82e.tmp | — | |
MD5:— | SHA256:— | |||
| 2476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF18f018.TMP | text | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | gmc | |
MD5:B6D81B360A5672D80C27430F39153E2C | SHA256:30E14955EBF1352266DC2FF8067E68104607E750ABB9D3B36582B8AF909FCB58 | |||
| 2476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF18f0f2.TMP | text | |
MD5:— | SHA256:— | |||
| 2476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF18f0c4.TMP | text | |
MD5:— | SHA256:— | |||
| 2476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2476 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
15
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1940 | chrome.exe | GET | 200 | 216.39.113.141:80 | http://i.ms00.net/favicon.ico | US | image | 2.46 Kb | whitelisted |
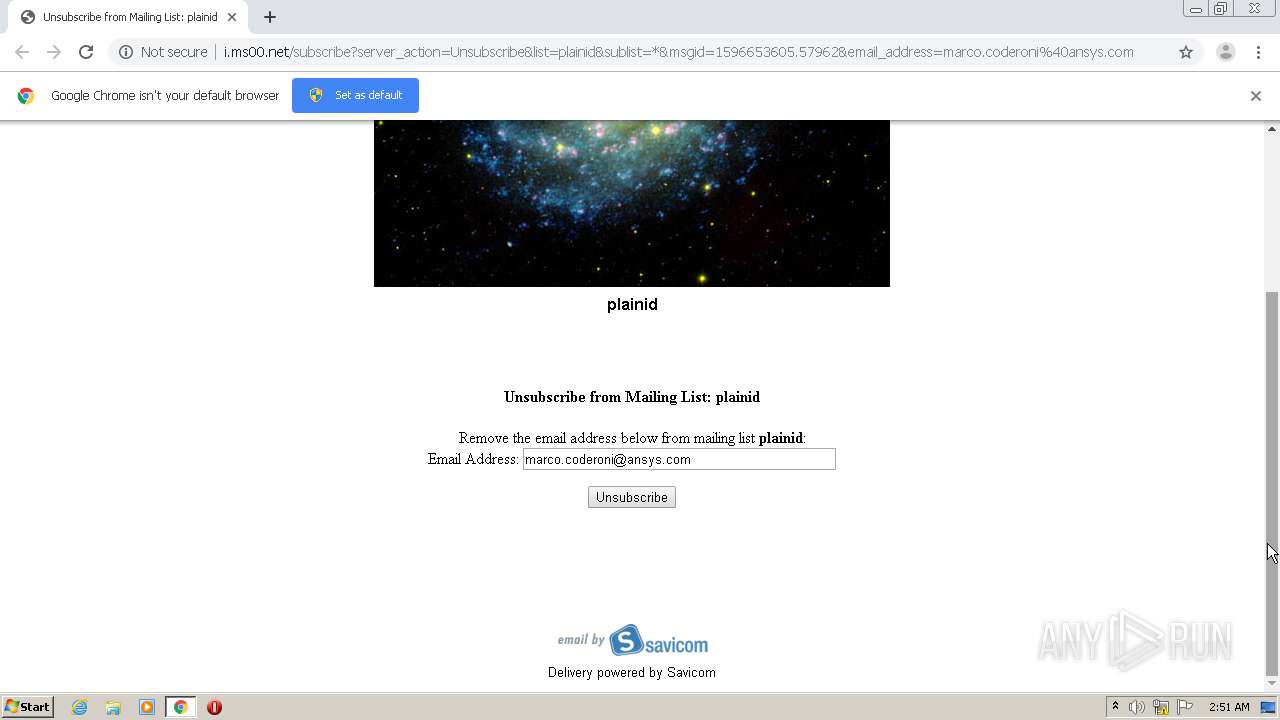
1940 | chrome.exe | GET | 200 | 216.39.113.141:80 | http://i.ms00.net/subscribe?server_action=Unsubscribe&list=plainid&sublist=*&msgid=1596653605.57962&email_address=marco.coderoni%40ansys.com | US | html | 1.91 Kb | whitelisted |
1940 | chrome.exe | GET | 200 | 216.39.113.141:80 | http://i.ms00.net/grafx/poweredby_small.png | US | image | 2.46 Kb | whitelisted |
1940 | chrome.exe | GET | 200 | 216.39.113.143:80 | http://g.pm0.net/plainid/images/galaxy.jpg | US | image | 57.5 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1940 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1940 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
1940 | chrome.exe | 216.39.113.141:80 | i.ms00.net | Unitedlayer, Inc. | US | unknown |
1940 | chrome.exe | 172.217.18.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
1940 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
1940 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1940 | chrome.exe | 216.39.113.143:80 | g.pm0.net | Unitedlayer, Inc. | US | unknown |
1940 | chrome.exe | 104.47.70.28:443 | nam10.safelinks.protection.outlook.com | Microsoft Corporation | US | suspicious |
1940 | chrome.exe | 104.47.55.28:443 | nam10.safelinks.protection.outlook.com | Microsoft Corporation | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
nam10.safelinks.protection.outlook.com |
| whitelisted |
accounts.google.com |
| shared |
i.ms00.net |
| whitelisted |
g.pm0.net |
| malicious |
clients1.google.com |
| whitelisted |
www.savicom.com |
| unknown |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |