| File name: | Setup_Install_Game.exe |
| Full analysis: | https://app.any.run/tasks/e6e02f30-438e-4ec6-b2e1-115612d3ff69 |
| Verdict: | Suspicious activity |
| Analysis date: | November 15, 2019, 19:54:02 |
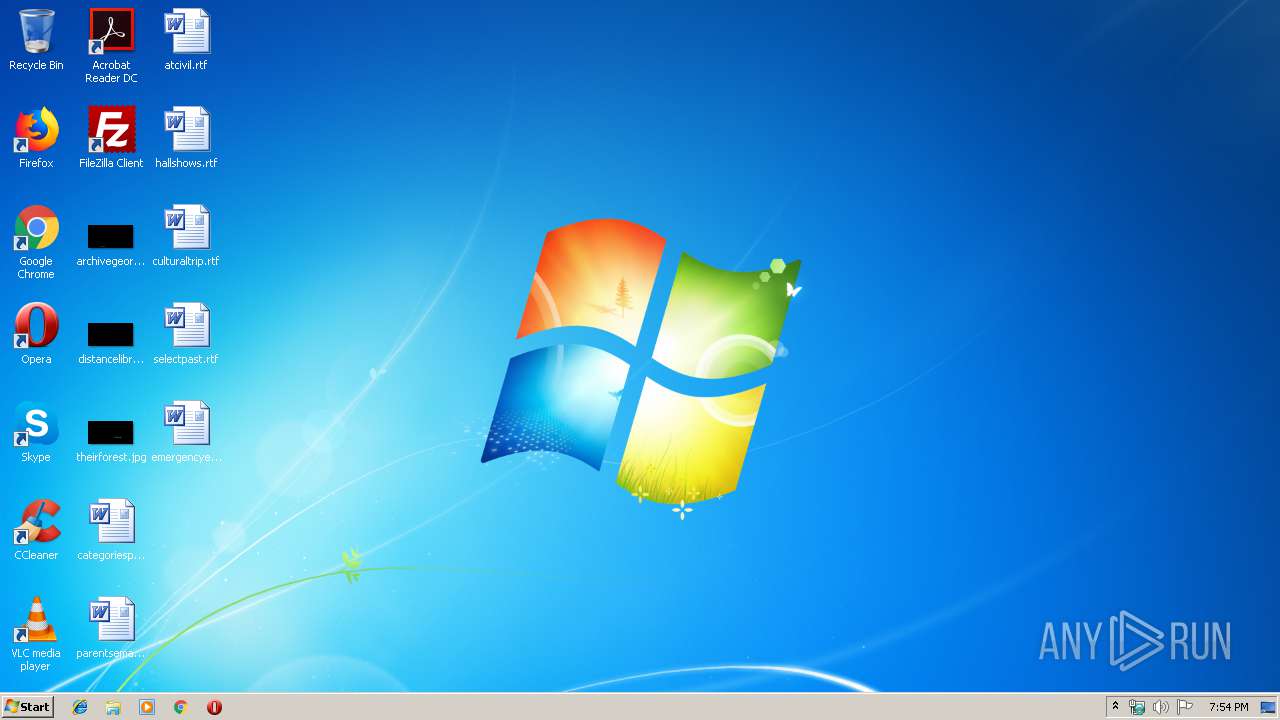
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0B8B06CFC697CC05E83D0B0A36CAC687 |
| SHA1: | AEE48B10684A57F9F968C832D05D0ABEEBF7C81B |
| SHA256: | F188F06FF03E467B87CB9D2EE3577164F09F7C98938846D99BED07F8CA21F025 |
| SSDEEP: | 6144:zeLSd2W+LBuWknzSNASXP8T6enmSvxR4JBc7kxwVOJxNzBehLmNdHkCPl4FvYKuS:6SgynzSXPRlVxNzch65a8UMMnW0L |
MALICIOUS
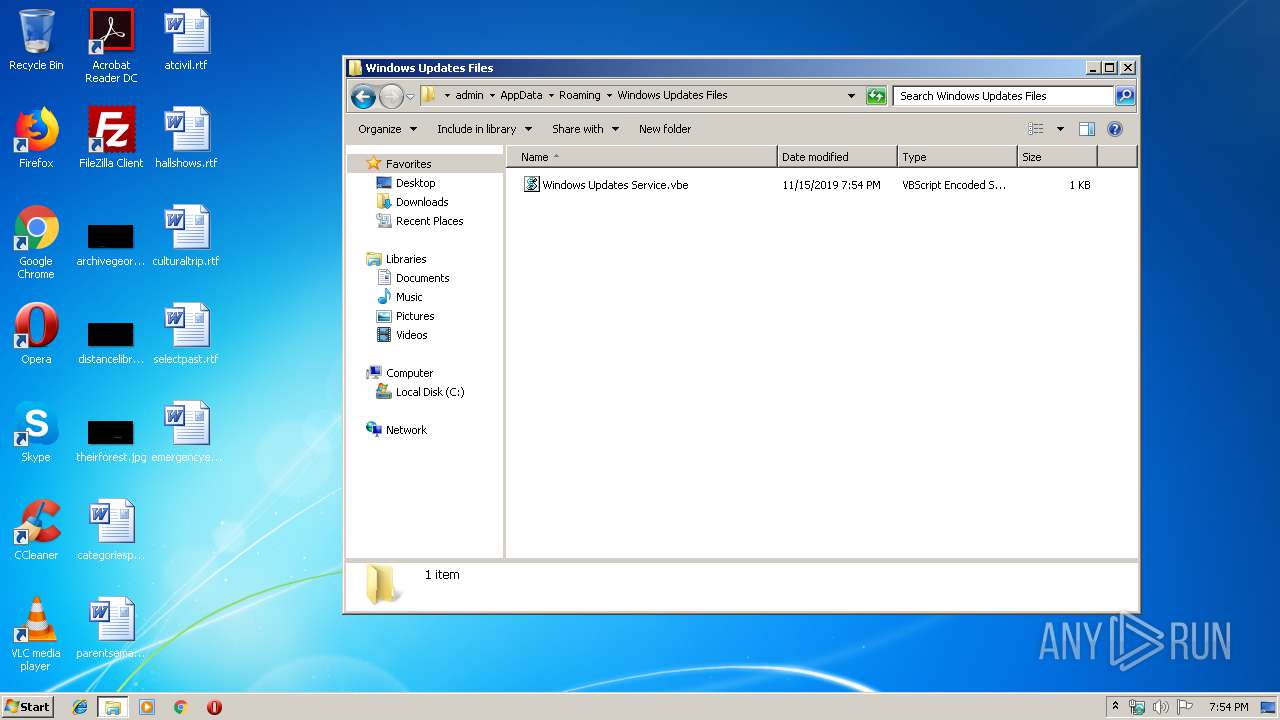
Changes the autorun value in the registry
- reg.exe (PID: 592)
SUSPICIOUS
Executes scripts
- Setup_Install_Game.exe (PID: 3872)
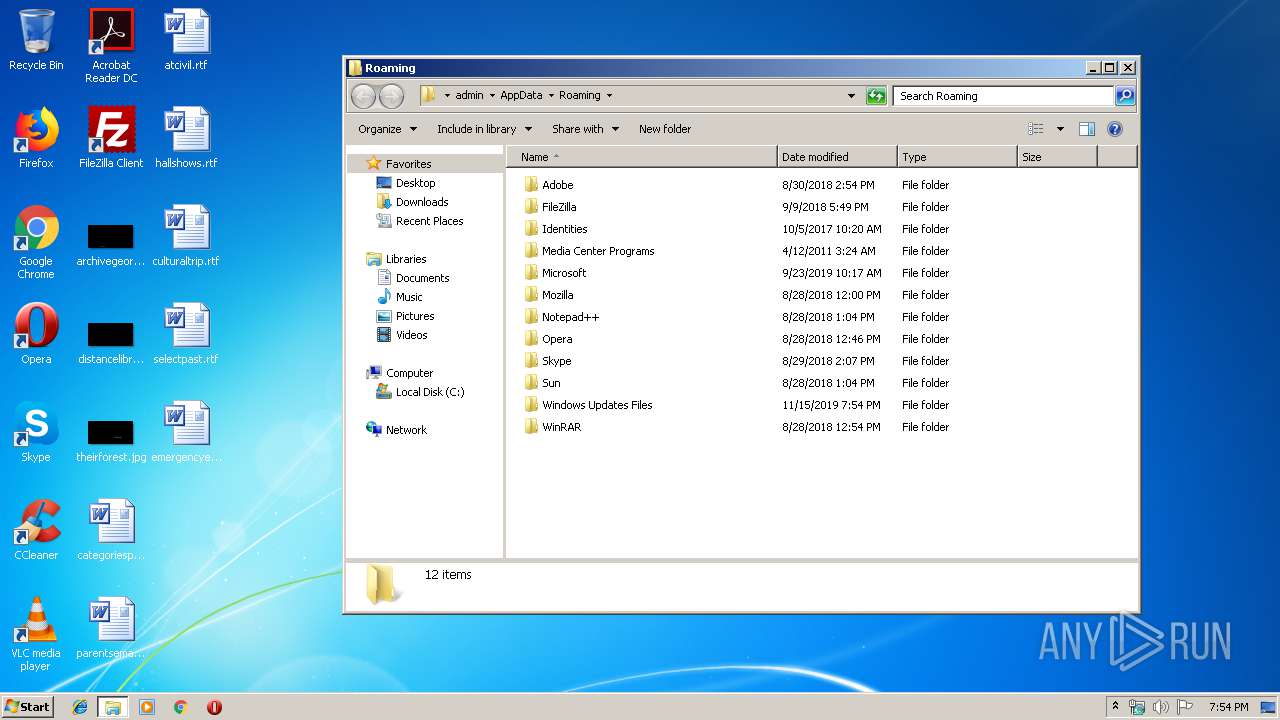
Creates files in the user directory
- Setup_Install_Game.exe (PID: 3872)
- WScript.exe (PID: 3084)
Uses REG.EXE to modify Windows registry
- Setup_Install_Game.exe (PID: 3872)
INFO
Connects to unusual port
- chrome.exe (PID: 3620)
Application launched itself
- chrome.exe (PID: 1248)
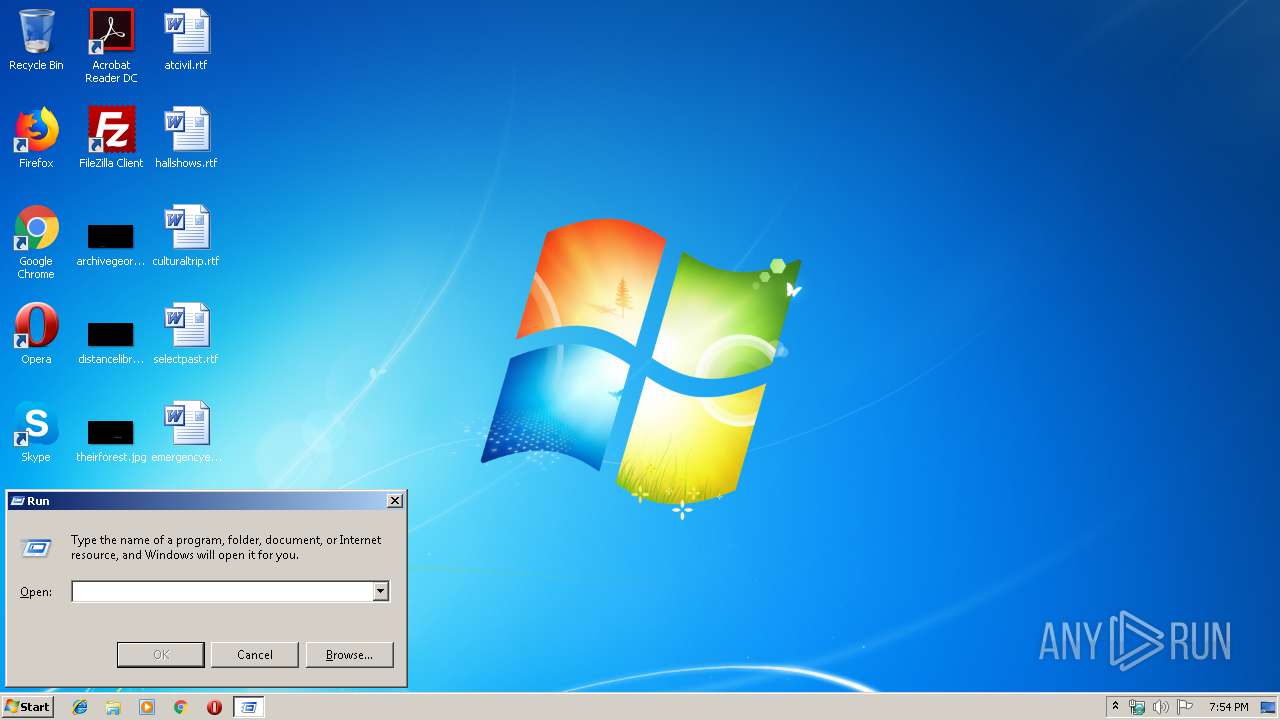
Manual execution by user
- WScript.exe (PID: 3900)
Reads the hosts file
- chrome.exe (PID: 3620)
- chrome.exe (PID: 1248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:23 15:51:01+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 281600 |
| InitializedDataSize: | 235520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2b6dc |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileVersion: | 1, 0, 0, 0 |
| ProductVersion: | 1, 0, 0, 0 |
| LegalCopyright: | Copyright (C) 2019 |
| FileDescription: | Setup v1.0 |
| ProductName: | Setup |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Jan-2019 14:51:01 |
| Detected languages: |
|
| Debug artifacts: |
|
| FileVersion: | 1, 0, 0, 0 |
| ProductVersion: | 1, 0, 0, 0 |
| LegalCopyright: | Copyright (C) 2019 |
| FileDescription: | Setup v1.0 |
| ProductName: | Setup |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000130 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 23-Jan-2019 14:51:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00044A25 | 0x00044C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59028 |
.rdata | 0x00046000 | 0x00016E2C | 0x00017000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.67603 |
.data | 0x0005D000 | 0x00004A04 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.73415 |
.gfids | 0x00062000 | 0x00000BAC | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.97169 |
.giats | 0x00063000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0407808 |
.tls | 0x00064000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00065000 | 0x0001B294 | 0x0001B400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.61702 |
.reloc | 0x00081000 | 0x00004570 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56661 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.73611 | 309 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 5.63311 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 6.13066 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.87666 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 4.93029 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 2.19502 | 72 | Latin 1 / Western European | French - France | RT_STRING |
128 | 2.80283 | 76 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
129 | 7.8763 | 10040 | Latin 1 / Western European | UNKNOWN | RT_BITMAP |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WINSPOOL.DRV |
ole32.dll |
Total processes
52
Monitored processes
13
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --use-gl=swiftshader-webgl --field-trial-handle=892,2365748962430828427,12274768742784675898,131072 --disable-databases --disable-gpu-compositing --lang=en-US --headless --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15789674912520093436 --renderer-client-id=3 --mojo-platform-channel-handle=1420 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 592 | "C:\Windows\System32\reg.exe" add "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /v "Windows Updates Service" /t REG_EXPAND_SZ /d "C:\Users\admin\AppData\Roaming\Windows Updates Files\Windows Updates Service.vbe" /f | C:\Windows\System32\reg.exe | Setup_Install_Game.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 920 | "C:\Users\admin\AppData\Local\Temp\Setup_Install_Game.exe" | C:\Users\admin\AppData\Local\Temp\Setup_Install_Game.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --headless --disable-gpu --remote-debugging-port=9222 http://www.google.com.911739932166205.window-updates-service.com | C:\Program Files\Google\Chrome\Application\chrome.exe | — | WScript.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\Temp --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod= --annotation=ver= --initial-client-data=0x148,0x14c,0x150,0x140,0x154,0x6d526390,0x6d5263a0,0x6d5263ac | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1244 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6d90a9d0,0x6d90a9e0,0x6d90a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3084 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\Windows Updates Files\encode.vbs" "C:\Users\admin\AppData\Roaming\Windows Updates Files\Windows Updates Service.vbs" | C:\Windows\System32\WScript.exe | — | Setup_Install_Game.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3316 | "C:\Windows\System32\PING.EXE" -n 1 -w 300 www.google.com.911739932166205.window-updates-service.com | C:\Windows\System32\PING.EXE | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=892,2365748962430828427,12274768742784675898,131072 --lang=en-US --service-sandbox-type=network --use-gl=swiftshader-webgl --headless --service-request-channel-token=16810489856367788483 --mojo-platform-channel-handle=1296 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
519
Read events
493
Write events
26
Delete events
0
Modification events
| (PID) Process: | (592) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Windows Updates Service |
Value: C:\Users\admin\AppData\Roaming\Windows Updates Files\Windows Updates Service.vbe | |||
| (PID) Process: | (3872) Setup_Install_Game.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3872) Setup_Install_Game.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3900) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3900) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1248) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
0
Suspicious files
4
Text files
2
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3872 | Setup_Install_Game.exe | C:\Users\admin\AppData\Roaming\Windows Updates Files\Windows Updates Service.vbs | text | |
MD5:1FF80D3357AA26B40DC20D5AFFF68CDC | SHA256:A60B9536B92CDED92F73FB644C1A76DED42C112D65BA866DD3A9D18228C08036 | |||
| 3084 | WScript.exe | C:\Users\admin\AppData\Roaming\Windows Updates Files\Windows Updates Service.vbe | vbe | |
MD5:5156EBC3C9846C72B9D826FE5750F721 | SHA256:9026FBD9D2D469F190C1C43A3E0A434BA2B20B012F4E862A33AB15D78AFD6AA6 | |||
| 1756 | chrome.exe | C:\Users\admin\AppData\Local\Temp\settings.dat | binary | |
MD5:A09C2BA58B7DAA2E7CE363C67155F9FB | SHA256:4288E1315343E7F3183DD2062D2CB60F82C58FACB258AA582826526D7F8078EE | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Temp\settings.dat | binary | |
MD5:A09C2BA58B7DAA2E7CE363C67155F9FB | SHA256:4288E1315343E7F3183DD2062D2CB60F82C58FACB258AA582826526D7F8078EE | |||
| 2620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:B59113C2DCD2D346F31A64F231162ADA | SHA256:1D97C69AEA85D3B06787458EA47576B192CE5C5DB9940E5EAA514FF977CE2DC2 | |||
| 1248 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3872 | Setup_Install_Game.exe | C:\Users\admin\AppData\Roaming\Windows Updates Files\encode.vbs | text | |
MD5:A9F3E70D2F5A77660D981C7821CA0574 | SHA256:EFBA151D6BB488059B8F513AD33A09C76BC56323431F148B3CC454F46C8AE264 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3620 | chrome.exe | GET | 200 | 80.86.87.6:80 | http://www.google.com.911739932166205.window-updates-service.com/ | DE | html | 42.7 Kb | unknown |
3620 | chrome.exe | GET | 200 | 80.86.87.6:80 | http://www.google.com.911739932166205.window-updates-service.com/wp-content/cache/autoptimize/js/autoptimize_eaa24614893be1323f03a8e1c58ec0b5.js | DE | text | 40.4 Kb | unknown |
3620 | chrome.exe | GET | 200 | 80.86.87.7:80 | http://www.7368876578257677.windows-updates-service.com/webmr.js | DE | text | 64.4 Kb | unknown |
3620 | chrome.exe | GET | 200 | 80.86.87.6:80 | http://www.google.com.911739932166205.window-updates-service.com/wp-content/plugins/wp-content-copy-protector/images/warning.png | DE | image | 483 b | unknown |
3620 | chrome.exe | GET | 200 | 80.86.87.7:80 | http://www.7368876578257677.windows-updates-service.com/ | DE | html | 176 b | unknown |
3620 | chrome.exe | GET | 404 | 51.68.180.217:80 | http://51.68.180.217/tracker.js | GB | html | 564 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3620 | chrome.exe | 80.86.87.6:80 | www.google.com.911739932166205.window-updates-service.com | Host Europe GmbH | DE | unknown |
3620 | chrome.exe | 80.86.87.7:80 | www.7368876578257677.windows-updates-service.com | Host Europe GmbH | DE | unknown |
3620 | chrome.exe | 51.68.180.217:80 | — | — | GB | unknown |
3620 | chrome.exe | 217.172.190.220:8181 | www.google.fast-dns-host.com | Host Europe GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com.911739932166205.window-updates-service.com |
| unknown |
www.7368876578257677.windows-updates-service.com |
| unknown |
www.google.fast-dns-host.com |
| unknown |