| File name: | StuxNet.exe |
| Full analysis: | https://app.any.run/tasks/d16b4b0e-295e-4843-ab22-195883f1309c |
| Verdict: | No threats detected |
| Analysis date: | September 28, 2019, 16:13:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7349B044311060E6BE61DC5FA5A2AC05 |
| SHA1: | F2974D9B8AE4F7B9B455C272C6F0F1780337EF11 |
| SHA256: | F184624C9AF9A5E8D6959001FD515D68A401502D48EB7FA597EA73920022151D |
| SSDEEP: | 49152:FOZ99sqrLxCg/PwX4lw5cqkRr6gSjw+8qKQRE0UhDTgrA:FMrtCgC4lwzk96gQ8qKQRERpTT |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- StuxNet.exe (PID: 3484)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:30 08:00:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 168960 |
| InitializedDataSize: | 53248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27796 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 18.6.0.0 |
| ProductVersionNumber: | 18.6.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z SFX |
| FileVersion: | 18.06 |
| InternalName: | 7z.sfx |
| LegalCopyright: | Copyright (c) 1999-2018 Igor Pavlov |
| OriginalFileName: | 7z.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 18.06 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Dec-2018 07:00:00 |
| Detected languages: |
|
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z SFX |
| FileVersion: | 18.06 |
| InternalName: | 7z.sfx |
| LegalCopyright: | Copyright (c) 1999-2018 Igor Pavlov |
| OriginalFilename: | 7z.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 18.06 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Dec-2018 07:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000293C5 | 0x00029400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67536 |
.rdata | 0x0002B000 | 0x000064F8 | 0x00006600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.44213 |
.data | 0x00032000 | 0x0000453C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.40447 |
.sxdata | 0x00037000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_INFO, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00038000 | 0x00002090 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.16388 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.42985 | 688 | UNKNOWN | English - United States | RT_VERSION |
2 | 1.68942 | 296 | UNKNOWN | English - United States | RT_ICON |
26 | 1.80688 | 62 | UNKNOWN | English - United States | RT_STRING |
28 | 1.93734 | 66 | UNKNOWN | English - United States | RT_STRING |
29 | 2.18408 | 96 | UNKNOWN | English - United States | RT_STRING |
64 | 1.20724 | 48 | UNKNOWN | English - United States | RT_STRING |
97 | 3.34731 | 1088 | UNKNOWN | English - United States | RT_DIALOG |
188 | 3.1595 | 524 | UNKNOWN | English - United States | RT_STRING |
189 | 2.80372 | 228 | UNKNOWN | English - United States | RT_STRING |
207 | 1.43775 | 52 | UNKNOWN | English - United States | RT_STRING |
Imports
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
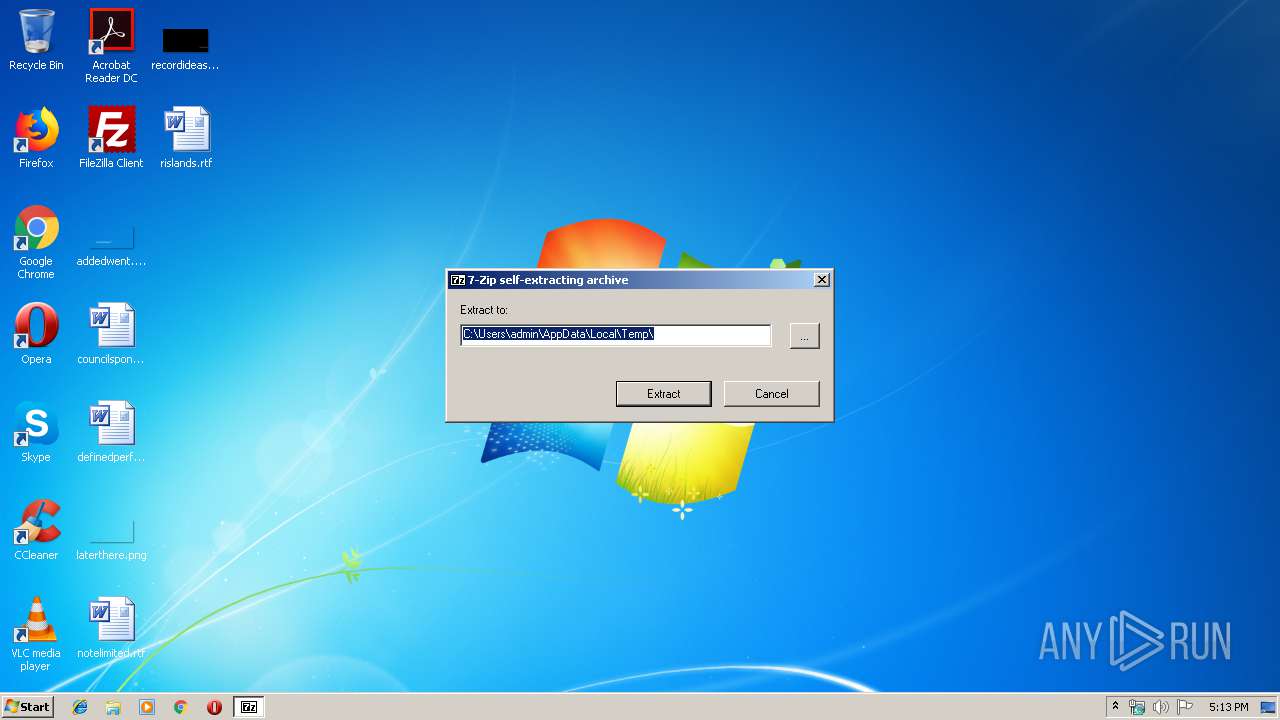
| 3484 | "C:\Users\admin\AppData\Local\Temp\StuxNet.exe" | C:\Users\admin\AppData\Local\Temp\StuxNet.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z SFX Exit code: 0 Version: 18.06 Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
17
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3484 | StuxNet.exe | C:\Users\admin\AppData\Local\Temp\Copy of Shortcut to.lnk | lnk | |
MD5:984C857CA2979AF776647061C8AE3ACC | SHA256:801E3B6D84862163A735502F93B9663BE53CCBDD7F12B0707336FECBA3A829A2 | |||
| 3484 | StuxNet.exe | C:\Users\admin\AppData\Local\Temp\~WTR4141.tmp | executable | |
MD5:4589EF6876E9C8C05DCF4DB00A54887B | SHA256:6BCF88251C876EF00B2F32CF97456A3E306C2A263D487B0A50216C6E3CC07C6A | |||
| 3484 | StuxNet.exe | C:\Users\admin\AppData\Local\Temp\1635ec04f069ccc8331d01fdf31132a4bc8f6fd3830ac94739df95ee093c555c.sys | executable | |
MD5:F8153747BAE8B4AE48837EE17172151E | SHA256:1635EC04F069CCC8331D01FDF31132A4BC8F6FD3830AC94739DF95EE093C555C | |||
| 3484 | StuxNet.exe | C:\Users\admin\AppData\Local\Temp\suckme.lnk | lnk | |
MD5:15DB99383D46D790812E83DF6196F4FD | SHA256:2D41FD5E315F7ECD4C4E20DFD1B21E23FBC273B1F4082F7FBA8D4B28A9D33BD9 | |||
| 3484 | StuxNet.exe | C:\Users\admin\AppData\Local\Temp\70f8789b03e38d07584f57581363afa848dd5c3a197f2483c6dfa4f3e7f78b9b.dll | executable | |
MD5:37FC7C5D89F1E5A96F54318DF1A2B905 | SHA256:70F8789B03E38D07584F57581363AFA848DD5C3A197F2483C6DFA4F3E7F78B9B | |||
| 3484 | StuxNet.exe | C:\Users\admin\AppData\Local\Temp\dropper.exe | executable | |
MD5:74DDC49A7C121A61B8D06C03F92D0C13 | SHA256:743E16B3EF4D39FC11C5E8EC890DCD29F034A6ECA51BE4F7FCA6E23E60DBD7A1 | |||
| 3484 | StuxNet.exe | C:\Users\admin\AppData\Local\Temp\63e6b8136058d7a06dfff4034b4ab17a261cdf398e63868a601f77ddd1b32802.dll | executable | |
MD5:1E17D81979271CFA44D471430FE123A5 | SHA256:63E6B8136058D7A06DFFF4034B4AB17A261CDF398E63868A601F77DDD1B32802 | |||
| 3484 | StuxNet.exe | C:\Users\admin\AppData\Local\Temp\dll.dll | executable | |
MD5:D24F522D4C40C33CB92F226A255C5BD0 | SHA256:9E392277F62206098CF794DDEBAFD2817483CFD57EC03C2E05E7C3C81E72F562 | |||
| 3484 | StuxNet.exe | C:\Users\admin\AppData\Local\Temp\maindll.decrypted.unpacked.dll | executable | |
MD5:68EB6D3ADC49DA0A79AFF2202BBB3BEA | SHA256:4C3D7B38339D7B8ADF73EAF85F0EB9FAB4420585C6AB6950EBD360428AF11712 | |||
| 3484 | StuxNet.exe | C:\Users\admin\AppData\Local\Temp\0d8c2bcb575378f6a88d17b5f6ce70e794a264cdc8556c8e812f0b5f9c709198.sys | executable | |
MD5:CC1DB5360109DE3B857654297D262CA1 | SHA256:0D8C2BCB575378F6A88D17B5F6CE70E794A264CDC8556C8E812F0B5F9C709198 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report