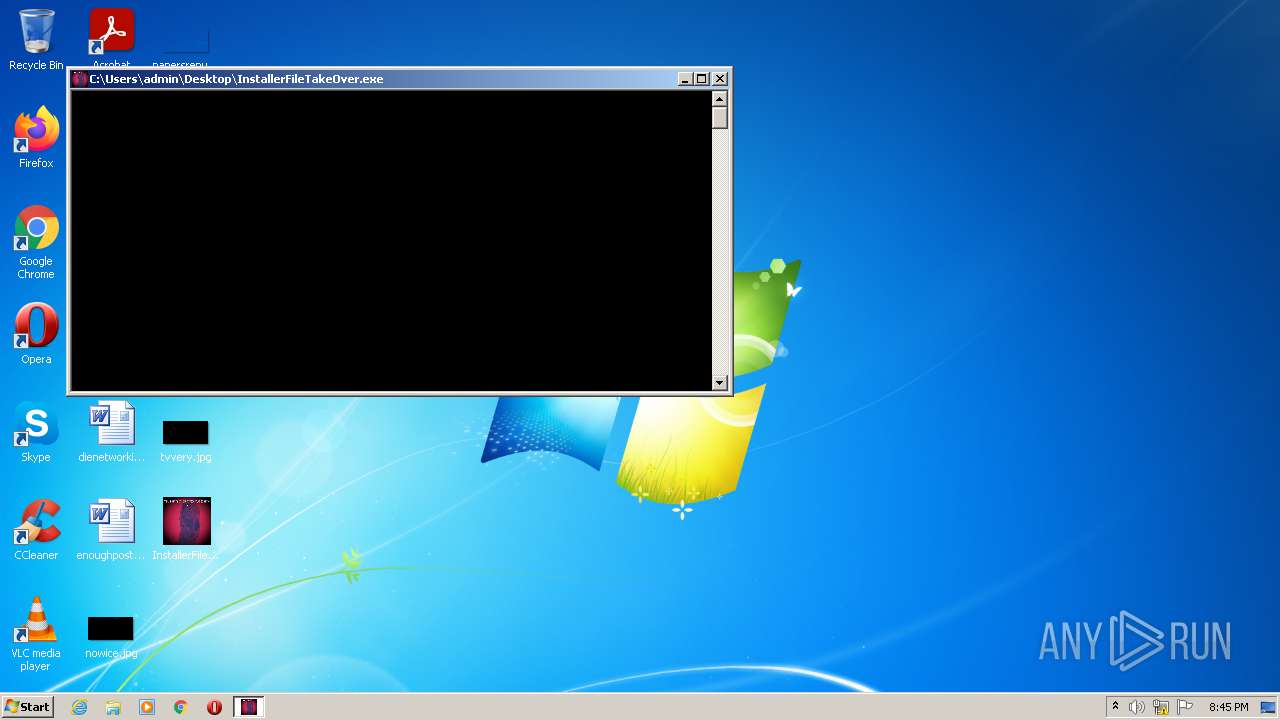
| File name: | InstallerFileTakeOver.exe |
| Full analysis: | https://app.any.run/tasks/074ac1c5-8d87-42f1-896d-cd77ba939eb8 |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2021, 20:45:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 9B95BAA91C2E92756DA970D7846B6C14 |
| SHA1: | 87E3BC6C690B4D881ABAAE8222575DDFDFD96EF9 |
| SHA256: | F181B8AE88F6C657C3EC3D1D5E8420FBF340C543B3D9292947AE035E3591B664 |
| SSDEEP: | 24576:OVPiOex8NeYD5swvEU7J8VlvfxAO4BOvKvzDL114R5UjZosXV:OVPiOPeYNEUl8VlvfxA0vW/LL4NiV |
MALICIOUS
Drops executable file immediately after starts
- msiexec.exe (PID: 760)
SUSPICIOUS
Reads Windows owner or organization settings
- msiexec.exe (PID: 760)
Reads the Windows organization settings
- msiexec.exe (PID: 760)
Executable content was dropped or overwritten
- msiexec.exe (PID: 760)
- InstallerFileTakeOver.exe (PID: 2824)
Checks supported languages
- InstallerFileTakeOver.exe (PID: 2824)
Reads the computer name
- InstallerFileTakeOver.exe (PID: 2824)
Executed as Windows Service
- msiexec.exe (PID: 760)
Drops a file that was compiled in debug mode
- msiexec.exe (PID: 760)
Drops a file with too old compile date
- msiexec.exe (PID: 760)
INFO
Checks supported languages
- msiexec.exe (PID: 760)
Reads the computer name
- msiexec.exe (PID: 760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:11:24 18:16:58+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 95232 |
| InitializedDataSize: | 1217024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x60bd |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 24-Nov-2021 17:16:58 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Nov-2021 17:16:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00017305 | 0x00017400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.61205 |
.rdata | 0x00019000 | 0x00007D9E | 0x00007E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18654 |
.data | 0x00021000 | 0x0000212C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.42062 |
.rsrc | 0x00024000 | 0x0011DD00 | 0x0011DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.13176 |
.reloc | 0x00142000 | 0x000013F4 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.6115 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
101 | 7.15028 | 1017856 | UNKNOWN | English - United Kingdom | MSI |
102 | 2.01924 | 20 | UNKNOWN | English - United Kingdom | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
SHLWAPI.dll |
msi.dll |
ole32.dll |
Total processes
37
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 760 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2824 | "C:\Users\admin\Desktop\InstallerFileTakeOver.exe" c:\windows\system.ini | C:\Users\admin\Desktop\InstallerFileTakeOver.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 187
Read events
2 166
Write events
8
Delete events
13
Modification events
| (PID) Process: | (760) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: F8020000809ACE4674E1D701 | |||
| (PID) Process: | (760) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 0E6D7BD237CFC9A7C8871971056CAA2C91CE0F79CA9FB8A16C563BA9D76C803D | |||
| (PID) Process: | (760) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (760) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\Temp\{79636F4B-1E66-4D4E-9E8D-2BF42D4CC8E8}\microsoft plz\notepad.exe | |||
| (PID) Process: | (760) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 8B7FBB4F2DECEC3140940121F98E6659AD8B7D361CF5D4C898E47A72269BE4DA | |||
| (PID) Process: | (760) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\InProgress |
| Operation: | write | Name: | (default) |
Value: C:\Windows\Installer\13e804.ipi | |||
| (PID) Process: | (760) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\13e805.rbs |
Value: 30925172 | |||
| (PID) Process: | (760) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\13e805.rbsLow |
Value: | |||
| (PID) Process: | (760) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | delete value | Name: | C:\Config.Msi\13e805.rbs |
Value: 30925172 | |||
| (PID) Process: | (760) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | delete value | Name: | C:\Config.Msi\13e805.rbsLow |
Value: | |||
Executable files
4
Suspicious files
11
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 760 | msiexec.exe | C:\Windows\Installer\13e804.ipi | binary | |
MD5:— | SHA256:— | |||
| 760 | msiexec.exe | C:\Windows\Installer\MSIE8CD.tmp | binary | |
MD5:— | SHA256:— | |||
| 760 | msiexec.exe | C:\Windows\Installer\SourceHash{A91D747A-3FDD-40F3-A235-16F0132127D4} | binary | |
MD5:— | SHA256:— | |||
| 760 | msiexec.exe | C:\Config.Msi\13e805.rbs | binary | |
MD5:— | SHA256:— | |||
| 760 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFA3CA66DE9F13AEB8.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2824 | InstallerFileTakeOver.exe | C:\Users\admin\AppData\Local\Temp\{79636F4B-1E66-4D4E-9E8D-2BF42D4CC8E8}\splwow64.exe | binary | |
MD5:— | SHA256:— | |||
| 2824 | InstallerFileTakeOver.exe | C:\Users\admin\AppData\Local\Temp\{79636F4B-1E66-4D4E-9E8D-2BF42D4CC8E8}\@AppHelpToast.png | binary | |
MD5:— | SHA256:— | |||
| 760 | msiexec.exe | C:\Config.Msi\13e806.rbf | binary | |
MD5:— | SHA256:— | |||
| 760 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF48203976699DAE7F.TMP | gmc | |
MD5:— | SHA256:— | |||
| 760 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{79636F4B-1E66-4D4E-9E8D-2BF42D4CC8E8}\splwow64.exe | executable | |
MD5:8E7AE69F0B9EC8A04285174BEBC8821E | SHA256:5CAFE00AABDA80896382613E2DC21ABDA160CE816DAF3BC7E2DE5D5E9A011830 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|