| download: | honda-element-camper |
| Full analysis: | https://app.any.run/tasks/3b5b00e5-4a5f-4b2b-b7c0-bf961d01da33 |
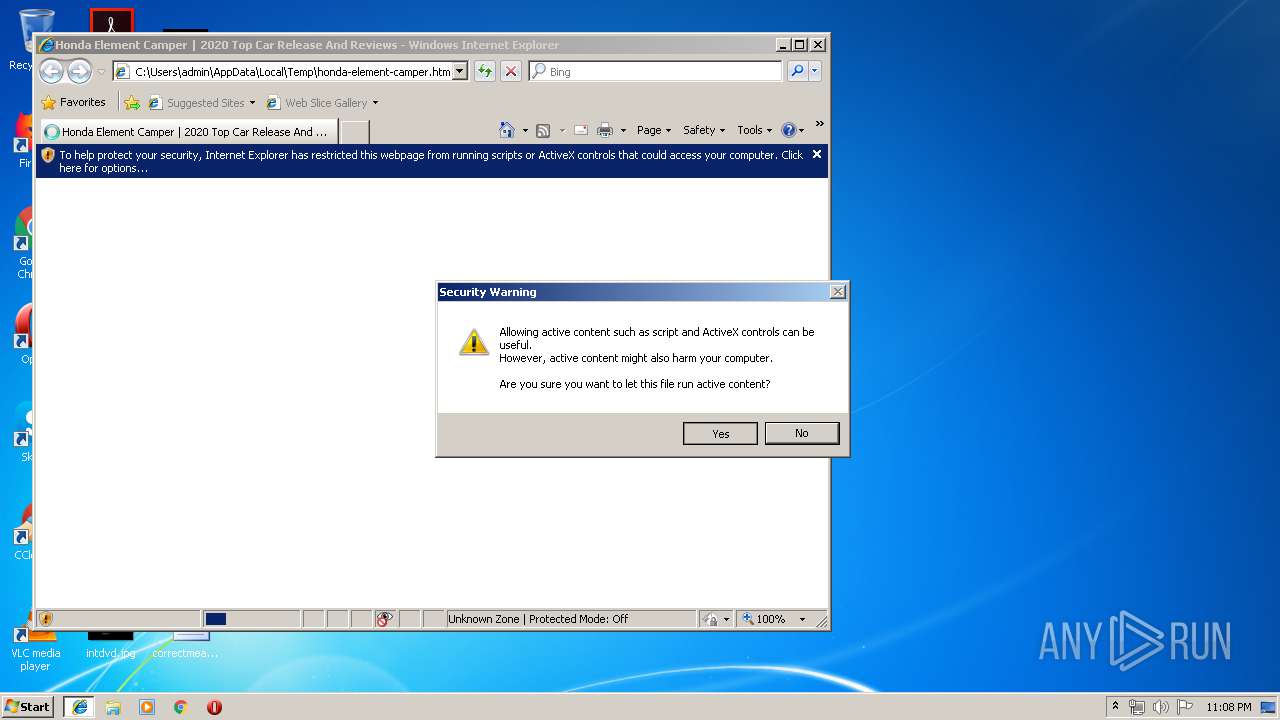
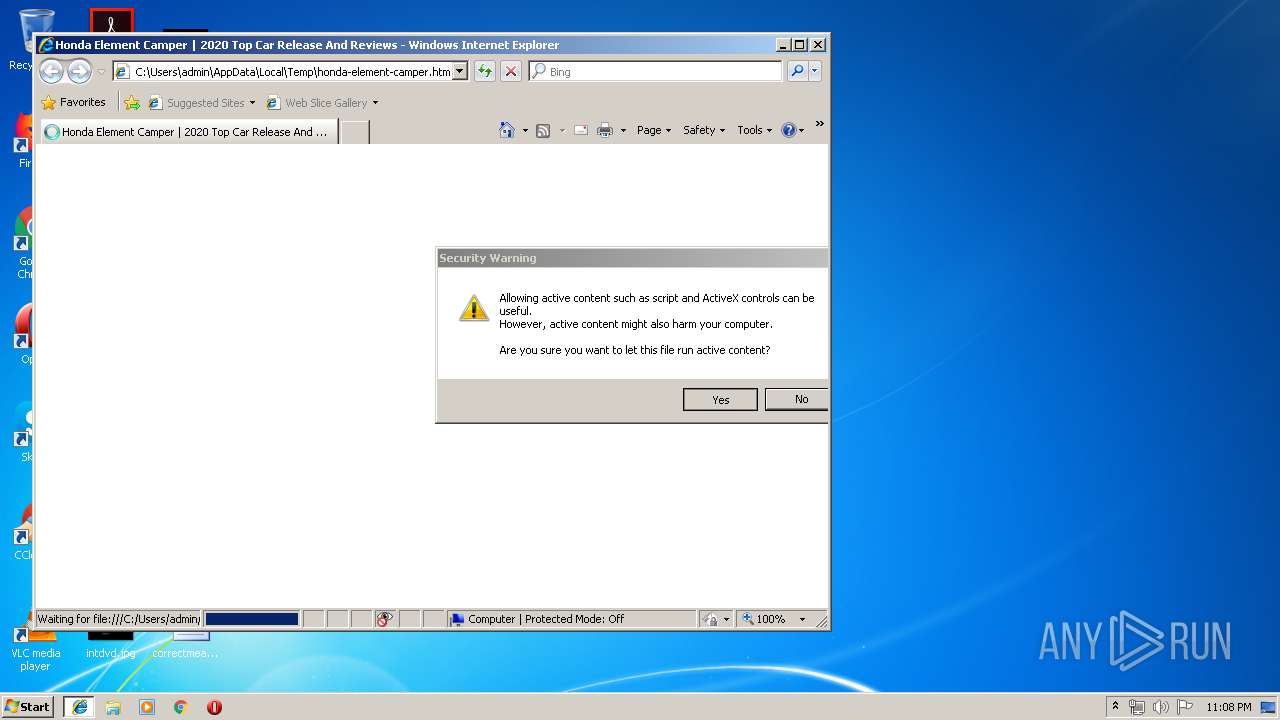
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 22:07:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 7A42823EE2421A8C4A639BCE7ECB63D8 |
| SHA1: | C8F237D2607E5C127067AE1F7E56F6677918E0FB |
| SHA256: | F17CE7B288847AFEAE5BEAA7501D46F7B115B7172E5C5F031027E86D9E2A99B7 |
| SSDEEP: | 768:ubRD+rewzRXsidu4wsFWe1A6fAa1koepQ4eYjrD:ubRoewzRXsbe1A6fAa1vepQ4eYjrD |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
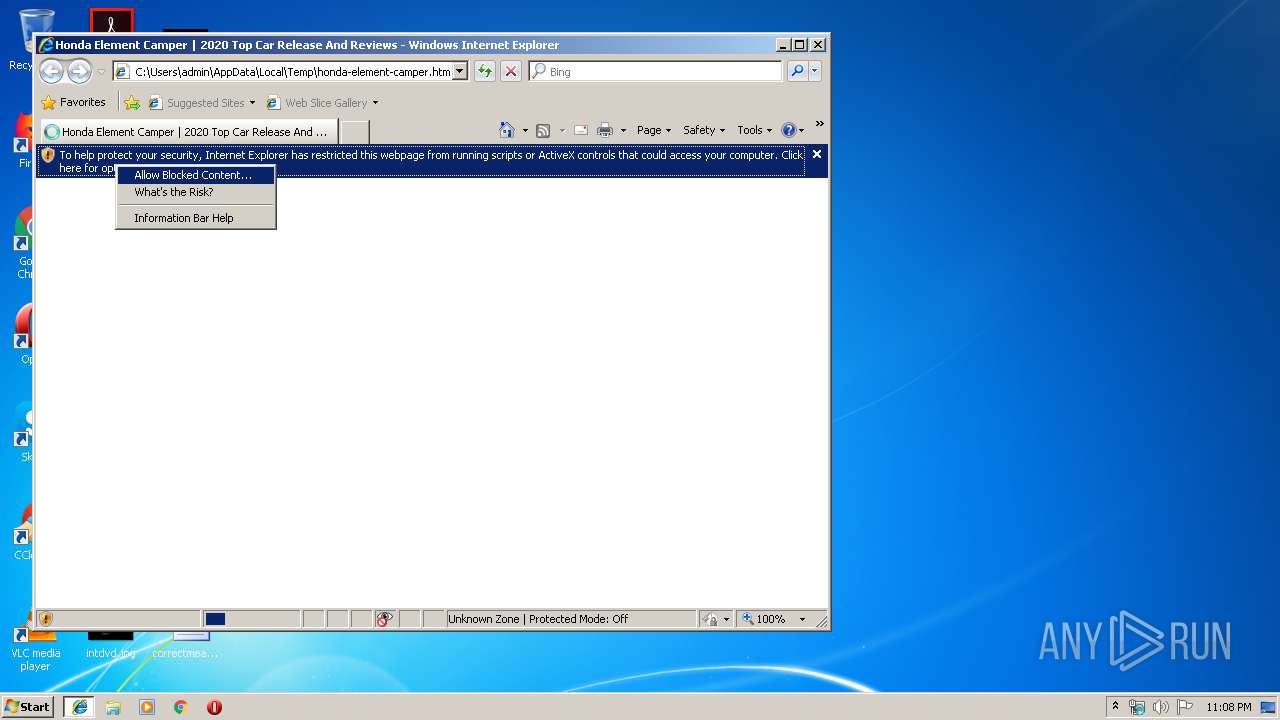
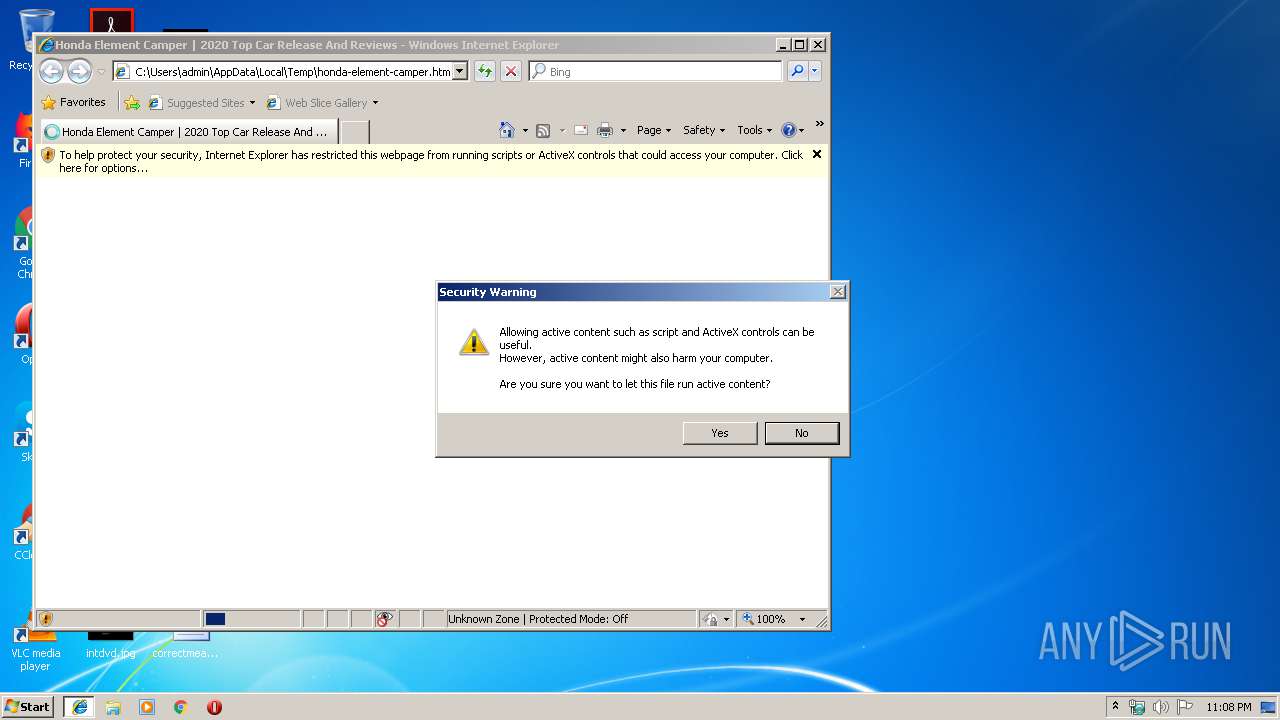
Application launched itself
- iexplore.exe (PID: 2176)
Creates files in the user directory
- iexplore.exe (PID: 3372)
Changes internet zones settings
- iexplore.exe (PID: 2176)
Reads internet explorer settings
- iexplore.exe (PID: 3372)
Changes settings of System certificates
- iexplore.exe (PID: 3372)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3372)
Reads Internet Cache Settings
- iexplore.exe (PID: 3372)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| msvalidate01: | B99EF5669E083C15B72DF375B3609739 |
|---|---|
| viewport: | width=device-width, initial-scale=1, user-scalable=0 |
| Description: | Honda Element Camper – Bed #3DThursday #3DPrinting. Amy Makes Stuff shares: I finally finished the 2D drawings and 3D model of my Honda Element Camper Bed. For background, this earlier post give a full tour of the camper and some of the design goals I was trying to balance. While this design provides all the details that tailor it for an ... |
| Keywords: | honda element camper, honda element camper for sale, honda element camper top, honda element camper kit, honda element camper conversion for sale, honda element camper van, honda element camper build, honda element camper conversions, honda element camper plans, honda element camper tent |
| Title: | Honda Element Camper | 2020 Top Car Release And Reviews |
| Generator: | WordPress 4.7.14 |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2176 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\honda-element-camper.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3372 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2176 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
382
Read events
290
Write events
87
Delete events
5
Modification events
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {12105235-EECF-11E9-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2176) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070A0001000E00160007003700F901 | |||
Executable files
0
Suspicious files
5
Text files
31
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2176 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2176 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarA57.tmp | — | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab1CC7.tmp | — | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\dashicons.min[1].css | text | |
MD5:CF3C0E8F26FE2025A0F22138FFE30D53 | SHA256:5C68CF1F0DCA577BF260A647A1E73410FAE9B838E3DA448412DF4B142E4FC123 | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar1CC8.tmp | — | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\seo-breadcrumbs-styles[1].css | text | |
MD5:14F65206633A23125E6BE01DD6671B42 | SHA256:64EBE8D577AF8C3DA0E0F29F84C59407B5CD28420C54F663CFC2423D120C80F6 | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\transit-bed[1].jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
91
DNS requests
25
Threats
41
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3372 | iexplore.exe | GET | 200 | 205.186.160.223:80 | http://www.bermstyle.com/wp-content/uploads/2016/05/outside-van-rainmaker-6937.jpg | US | image | 593 Kb | unknown |
3372 | iexplore.exe | GET | 200 | 205.186.160.223:80 | http://www.bermstyle.com/wp-content/uploads/2017/01/5thelement-camping-1500x877.jpg | US | image | 155 Kb | unknown |
3372 | iexplore.exe | GET | 200 | 104.31.71.107:80 | http://newsflashinformation.xyz/wp-content/themes/newsflashinformationxyz/fonts/fontawesome-webfont.eot? | US | eot | 96.6 Kb | suspicious |
3372 | iexplore.exe | GET | 200 | 104.31.71.107:80 | http://newsflashinformation.xyz/wp-content/plugins/seo-breadcrumbs/css/seo-breadcrumbs-styles.css?ver=4.7.14 | US | text | 1.36 Kb | suspicious |
3372 | iexplore.exe | GET | 200 | 104.31.71.107:80 | http://newsflashinformation.xyz/wp-content/themes/newsflashinformationxyz/js/jquery.fitvids.js?ver=1.1 | US | html | 1.29 Kb | suspicious |
3372 | iexplore.exe | GET | 301 | 93.114.86.104:80 | http://expeditionportal.com/media/2017/01/Snow-FifthElementCamping.com-Copy.jpg | GB | html | 1.12 Kb | whitelisted |
2176 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3372 | iexplore.exe | GET | 200 | 104.31.71.107:80 | http://newsflashinformation.xyz/wp-content/themes/newsflashinformationxyz/js/scripts.js?ver=20190515 | US | text | 589 b | suspicious |
3372 | iexplore.exe | GET | 200 | 92.122.213.201:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/B51C067CEE2B0C3DF855AB2D92F4FE39D4E70F0E.crt | unknown | der | 993 b | whitelisted |
3372 | iexplore.exe | GET | 200 | 104.31.71.107:80 | http://newsflashinformation.xyz/wp-includes/js/wp-embed.min.js?ver=4.7.14 | US | text | 751 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3372 | iexplore.exe | 104.31.71.107:80 | newsflashinformation.xyz | Cloudflare Inc | US | suspicious |
3372 | iexplore.exe | 172.217.21.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2176 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3372 | iexplore.exe | 216.58.208.54:443 | i.ytimg.com | Google Inc. | US | whitelisted |
3372 | iexplore.exe | 216.58.205.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3372 | iexplore.exe | 93.114.86.104:80 | expeditionportal.com | NetConnex Broadband Ltd. | GB | unknown |
3372 | iexplore.exe | 93.189.38.30:443 | www.coches.com | Propelin Consulting S.L.U. | ES | unknown |
3372 | iexplore.exe | 192.0.77.2:443 | i0.wp.com | Automattic, Inc | US | suspicious |
3372 | iexplore.exe | 104.18.15.176:443 | s-media-cache-ak0.pinimg.com | Cloudflare Inc | US | shared |
3372 | iexplore.exe | 91.250.68.242:443 | www.crosli.de | Host Europe GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
newsflashinformation.xyz |
| suspicious |
fonts.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
dns.msftncsi.com |
| shared |
fonts.gstatic.com |
| whitelisted |
4.bp.blogspot.com |
| whitelisted |
i.ytimg.com |
| whitelisted |
www.bermstyle.com |
| unknown |
expeditionportal.com |
| whitelisted |
www.thefirearmblog.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3372 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3372 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3372 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3372 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3372 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3372 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3372 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3372 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3372 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3372 | iexplore.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |