| File name: | VortexVPN.apk |
| Full analysis: | https://app.any.run/tasks/1ce83086-d43b-498e-acbc-fa77b25dcb71 |
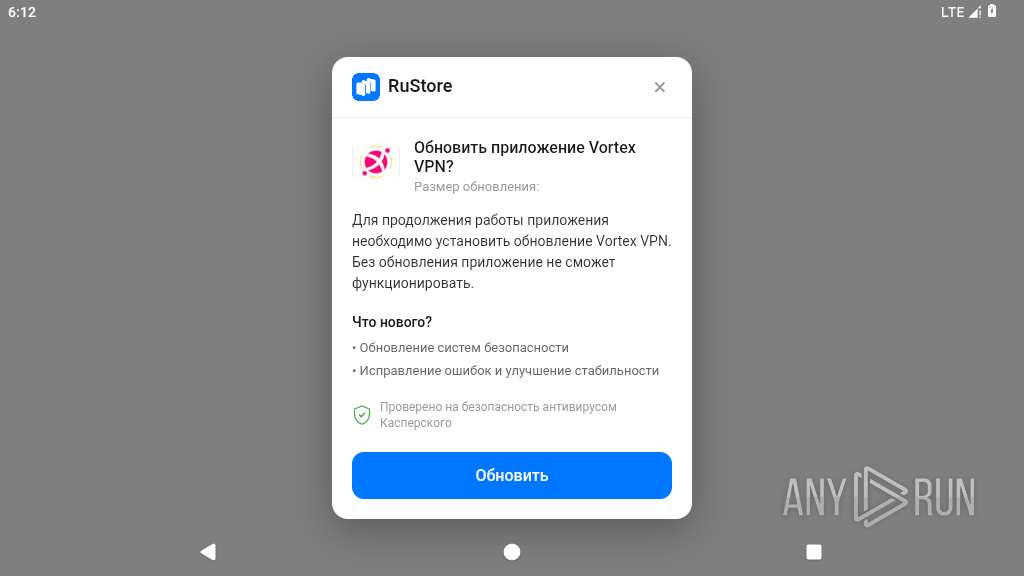
| Verdict: | Malicious activity |
| Analysis date: | March 20, 2026, 06:12:13 |
| OS: | Android 14 |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with gradle app-metadata.properties, with APK Signing Block |
| MD5: | D7E5D99232DEB1B26C0255E0312E8586 |
| SHA1: | 3E3EF9C0114AD4AE09244444A739B207EEF2B7AB |
| SHA256: | F17AB64094C2DE186C66CFBFC769E34828CAD2BA88D4E8149AE327FD7047487F |
| SSDEEP: | 98304:6yo6pdzi2qq9AaVqu7hC3HdmeK+HfpHjZ1opEe0DRBr4FaNRzBZjNO4QyS8a9dU5:vY8/E07LfeL |
MALICIOUS
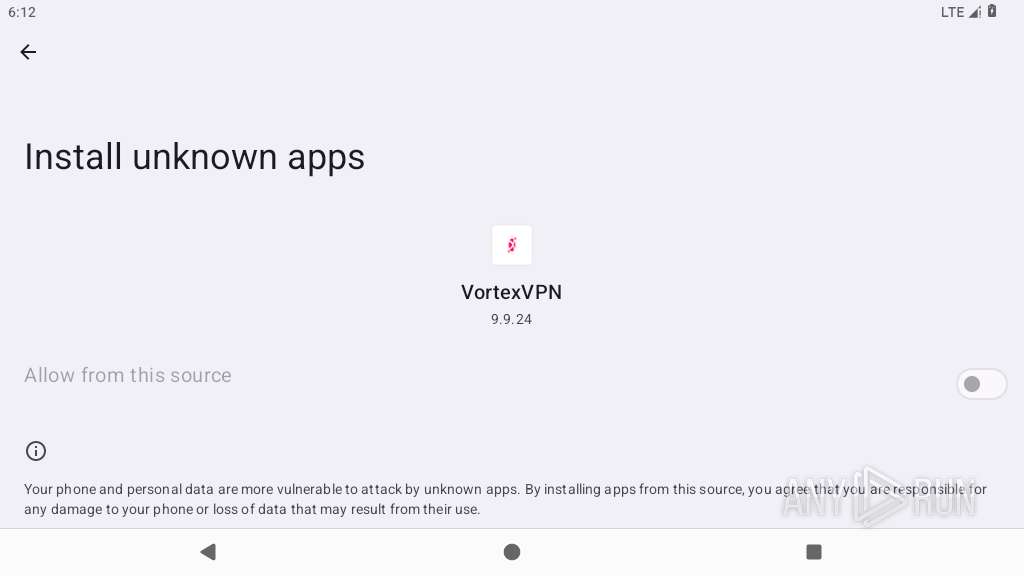
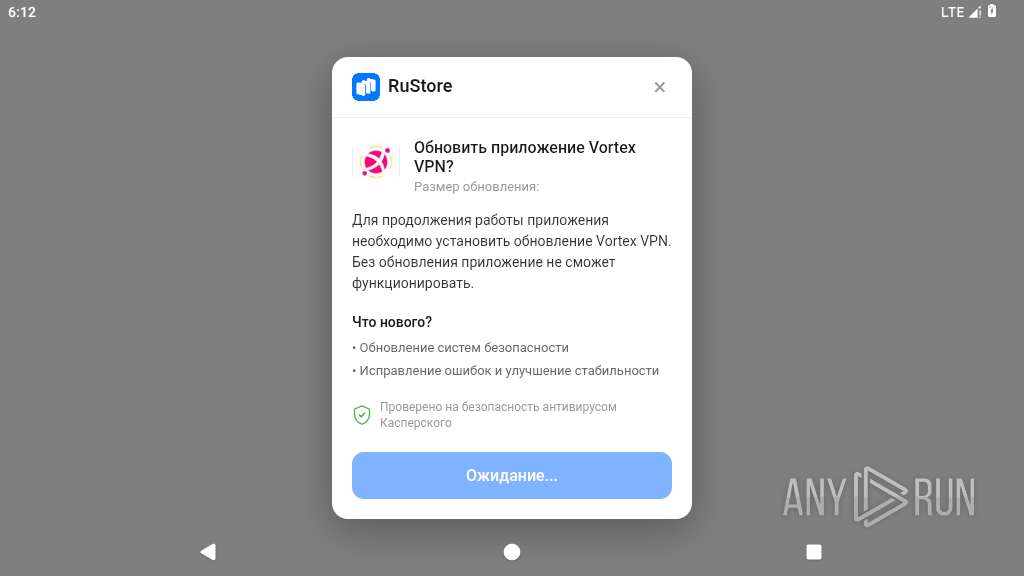
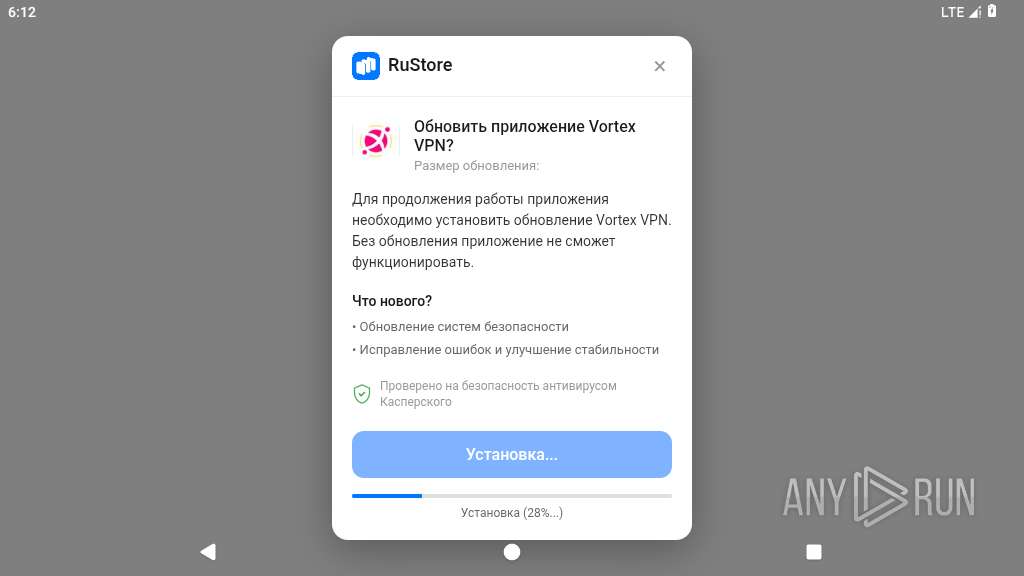
Initiates background APK installation
- app_process64 (PID: 4012)
SUSPICIOUS
Launches a new activity
- app_process64 (PID: 4012)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 4012)
- app_process64 (PID: 4257)
Starts a service
- app_process64 (PID: 4012)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 4257)
Accesses system-level resources
- app_process64 (PID: 4257)
Monitors changes in clipboard content
- app_process64 (PID: 4257)
Checks exemption from battery optimization
- app_process64 (PID: 4257)
Abuses foreground service for persistence
- app_process64 (PID: 4257)
Acquires a wake lock to keep the device awake
- app_process64 (PID: 4257)
Creates a WakeLock to manage power state
- app_process64 (PID: 4257)
Gets data of saved accounts
- app_process64 (PID: 4257)
Retrieves the MCC and MNC of the SIM card operator
- app_process64 (PID: 4257)
Creates new saved account
- app_process64 (PID: 4257)
INFO
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 4012)
- app_process64 (PID: 4257)
Stores data using SQLite database
- app_process64 (PID: 4257)
Retrieves the value of a secure system setting
- app_process64 (PID: 4257)
Loads a native library into the application
- app_process64 (PID: 4257)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 4257)
Returns elapsed time since boot
- app_process64 (PID: 4257)
Dynamically registers broadcast event listeners
- app_process64 (PID: 4257)
Handles throwable exceptions in the app
- app_process64 (PID: 4257)
Verifies presence of SIM card
- app_process64 (PID: 4257)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jar | | | Java Archive (78.3) |
|---|---|---|
| .zip | | | ZIP compressed archive (21.6) |
EXIF
ZIP
| ZipRequiredVersion: | - |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1981:01:01 01:01:02 |
| ZipCRC: | 0x254e4b1a |
| ZipCompressedSize: | 52 |
| ZipUncompressedSize: | 56 |
| ZipFileName: | META-INF/com/android/build/gradle/app-metadata.properties |
Total processes
137
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 4012 | io.vall8w4i.bjmknq | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4046 | com.android.webview:webview_service | /system/bin/app_process32 | — | app_process32 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4063 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4243 | /apex/com.android.art/bin/artd | /apex/com.android.art/bin/artd | — | init |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4250 | /apex/com.android.art/bin/dex2oat32 --zip-fd=6 --zip-location=/data/app/~~2bPB3OkVJ0V5cwfLsjfhKA==/eu.k0b4ou.g2n7414-5nCCWv2Q2ZDCsbybP7RPVQ==/base.apk --oat-fd=7 --oat-location=/data/app/~~2bPB3OkVJ0V5cwfLsjfhKA==/eu.k0b4ou.g2n7414-5nCCWv2Q2ZDCsbybP7RPVQ==/oat/arm64/base.odex --output-vdex-fd=8 --swap-fd=9 --class-loader-context=PCL[] --classpath-dir=/data/app/~~2bPB3OkVJ0V5cwfLsjfhKA==/eu.k0b4ou.g2n7414-5nCCWv2Q2ZDCsbybP7RPVQ== --instruction-set=arm64 --instruction-set-features=default --instruction-set-variant=cortex-a53 --compiler-filter=verify --compilation-reason=install --compact-dex-level=none --max-image-block-size=524288 --resolve-startup-const-strings=true --generate-mini-debug-info --runtime-arg -Xtarget-sdk-version:35 --runtime-arg -Xhidden-api-policy:enabled --runtime-arg -Xms64m --runtime-arg -Xmx512m --comments=app-version-name:2.0.32,app-version-code:430,art-version:340090000 | /apex/com.android.art/bin/dex2oat32 | — | artd |
User: artd Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4257 | eu.k0b4ou.g2n7414 | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4296 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
42
Text files
48
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4012 | app_process64 | /data/data/io.vall8w4i.bjmknq/app_webview/last-exit-info | text | |
MD5:— | SHA256:— | |||
| 4012 | app_process64 | /data/data/io.vall8w4i.bjmknq/shared_prefs/WebViewChromiumPrefs.xml | xml | |
MD5:— | SHA256:— | |||
| 4012 | app_process64 | /data/data/io.vall8w4i.bjmknq/app_webview/Default/Web Data-journal | binary | |
MD5:— | SHA256:— | |||
| 4012 | app_process64 | /data/data/io.vall8w4i.bjmknq/app_webview/Default/Shared Dictionary/cache/index | binary | |
MD5:— | SHA256:— | |||
| 4012 | app_process64 | /data/data/io.vall8w4i.bjmknq/cache/WebView/Default/HTTP Cache/Code Cache/wasm/index | binary | |
MD5:— | SHA256:— | |||
| 4012 | app_process64 | /data/data/io.vall8w4i.bjmknq/cache/WebView/Default/HTTP Cache/Code Cache/js/index | binary | |
MD5:— | SHA256:— | |||
| 4012 | app_process64 | /data/data/io.vall8w4i.bjmknq/app_webview/Default/Local Storage/leveldb/MANIFEST-000001 | binary | |
MD5:— | SHA256:— | |||
| 4012 | app_process64 | /data/data/io.vall8w4i.bjmknq/app_webview/Default/Local Storage/leveldb/000001.dbtmp | text | |
MD5:— | SHA256:— | |||
| 4012 | app_process64 | /data/data/io.vall8w4i.bjmknq/app_webview/Default/Local Storage/leveldb/CURRENT | text | |
MD5:— | SHA256:— | |||
| 4012 | app_process64 | /data/data/io.vall8w4i.bjmknq/cache/WebView/Default/HTTP Cache/Code Cache/js/index-dir/temp-index | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
27
DNS requests
6
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1921 | app_process64 | GET | 404 | 142.251.140.163:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
1921 | app_process64 | GET | 404 | 142.251.140.163:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
1921 | app_process64 | GET | 404 | 216.239.32.223:80 | http://play.googleapis.com/generate_204 | unknown | — | — | whitelisted |
1921 | app_process64 | GET | 404 | 142.251.140.163:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
1921 | app_process64 | GET | 404 | 142.251.151.119:443 | https://www.google.com/generate_204 | unknown | xml | 341 b | whitelisted |
1921 | app_process64 | GET | 404 | 142.251.150.119:80 | http://www.google.com/gen_204 | unknown | — | — | whitelisted |
4257 | app_process64 | GET | 404 | 172.217.16.206:443 | https://play.google.com/favicon.ico | unknown | xml | 341 b | whitelisted |
1921 | app_process64 | GET | 404 | 142.251.152.119:443 | https://www.google.com/generate_204 | unknown | xml | 341 b | whitelisted |
1921 | app_process64 | GET | 404 | 216.239.34.223:80 | http://play.googleapis.com/generate_204 | unknown | — | — | whitelisted |
1921 | app_process64 | GET | 404 | 142.251.150.119:443 | https://www.google.com/generate_204 | unknown | xml | 341 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 142.251.156.119:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 216.58.206.35:80 | — | GOOGLE | US | whitelisted |
— | — | 142.251.157.119:443 | www.google.com | GOOGLE | US | whitelisted |
452 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
1921 | app_process64 | 142.251.140.163:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
1921 | app_process64 | 142.251.151.119:443 | www.google.com | GOOGLE | US | whitelisted |
1921 | app_process64 | 216.239.32.223:80 | play.googleapis.com | GOOGLE | US | whitelisted |
1921 | app_process64 | 142.251.152.119:443 | www.google.com | GOOGLE | US | whitelisted |
1921 | app_process64 | 142.251.150.119:80 | www.google.com | GOOGLE | US | whitelisted |
4257 | app_process64 | 172.217.16.206:443 | play.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
google.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
play.googleapis.com |
| whitelisted |
play.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1921 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
1921 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
1921 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
1921 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
1921 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |