| download: | index.html |
| Full analysis: | https://app.any.run/tasks/3786c298-c286-47a4-a868-a8eb24adcf97 |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 21:10:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/xml |
| File info: | XML 1.0 document, ASCII text, with very long lines |
| MD5: | 7784F7EFA1CC623439171A310F0D8D79 |
| SHA1: | CFFB9FA9779BC27C1AFD74FA0821D59F97FC2AC7 |
| SHA256: | F176F1C9C75ACA6B86FBE919156AEFC06FDA945826F73B54400D85693683ABA1 |
| SSDEEP: | 384:2rLXGAxDgKnppbDUBIOREx+BstONg1txmWcU2MIYJBluDyxhKhcp:2rL2A+KTb2xg1tx2YJBlQcp |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 660)
- iexplore.exe (PID: 3800)
Changes internet zones settings
- iexplore.exe (PID: 660)
Application launched itself
- iexplore.exe (PID: 660)
- iexplore.exe (PID: 3384)
Reads internet explorer settings
- iexplore.exe (PID: 3680)
- iexplore.exe (PID: 3384)
Reads settings of System Certificates
- iexplore.exe (PID: 3384)
- iexplore.exe (PID: 660)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3384)
- iexplore.exe (PID: 660)
Changes settings of System certificates
- iexplore.exe (PID: 3384)
- iexplore.exe (PID: 660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xml | | | Generic XML (ASCII) (62.5) |
|---|---|---|
| .html | | | HyperText Markup Language (37.5) |
EXIF
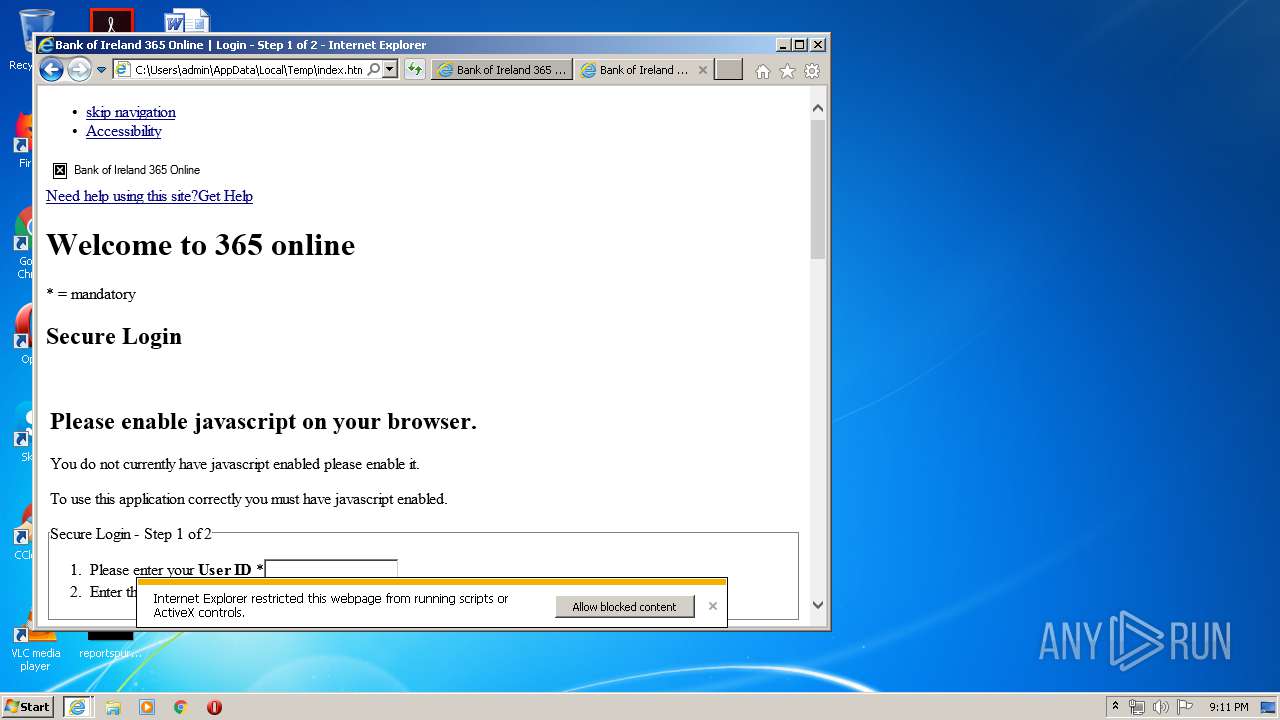
HTML
| ContentType: | text/html; charset=ISO-8859-1 |
|---|---|
| CacheControl: | must-revalidate |
| Expires: | - |
| Refresh: | 615; URL=/online365/spring/logout |
| viewport: | width=device-width, initial-scale=1.0 |
| HTTPEquivXUACompatible: | IE=EmulateIE8 |
| Keywords: | Bank of Ireland, 365 Online , login Step 1 of 2, |
| Description: | Bank of Ireland 365 Online, login Step 1 of 2 |
| Title: | Bank of Ireland 365 Online | Login - Step 1 of 2 |
Total processes
38
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3384 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:660 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3680 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:660 CREDAT:341002 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3800 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:660 CREDAT:464129 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
10 503
Read events
1 083
Write events
6 298
Delete events
3 122
Modification events
| (PID) Process: | (660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1760992008 | |||
| (PID) Process: | (660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30796027 | |||
| (PID) Process: | (660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 660 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\errorPageStrings[1] | text | |
MD5:— | SHA256:— | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\errorPageStrings[1] | text | |
MD5:— | SHA256:— | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\dnserrordiagoff[1] | html | |
MD5:47F581B112D58EDA23EA8B2E08CF0FF0 | SHA256:B1C947D00DB5FCE43314C56C663DBEAE0FFA13407C9C16225C17CCEFC3AFA928 | |||
| 660 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\favicon[1].ico | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\NewErrorPageTemplate[1] | text | |
MD5:CDF81E591D9CBFB47A7F97A2BCDB70B9 | SHA256:204D95C6FB161368C795BB63E538FE0B11F9E406494BB5758B3B0D60C5F651BD | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\dnserrordiagoff[2] | html | |
MD5:47F581B112D58EDA23EA8B2E08CF0FF0 | SHA256:B1C947D00DB5FCE43314C56C663DBEAE0FFA13407C9C16225C17CCEFC3AFA928 | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\NewErrorPageTemplate[1] | text | |
MD5:CDF81E591D9CBFB47A7F97A2BCDB70B9 | SHA256:204D95C6FB161368C795BB63E538FE0B11F9E406494BB5758B3B0D60C5F651BD | |||
| 3384 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\httpErrorPagesScripts[1] | text | |
MD5:3F57B781CB3EF114DD0B665151571B7B | SHA256:46E019FA34465F4ED096A9665D1827B54553931AD82E98BE01EDB1DDBC94D3AD | |||
| 3680 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\httpErrorPagesScripts[1] | text | |
MD5:3F57B781CB3EF114DD0B665151571B7B | SHA256:46E019FA34465F4ED096A9665D1827B54553931AD82E98BE01EDB1DDBC94D3AD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
18
DNS requests
8
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3384 | iexplore.exe | OPTIONS | 400 | 172.217.22.40:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
660 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3680 | iexplore.exe | OPTIONS | 400 | 172.217.22.40:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3680 | iexplore.exe | OPTIONS | 400 | 172.217.22.40:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3680 | iexplore.exe | OPTIONS | 400 | 172.217.22.40:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3384 | iexplore.exe | OPTIONS | 400 | 172.217.22.40:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3384 | iexplore.exe | OPTIONS | 400 | 172.217.22.40:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3384 | iexplore.exe | OPTIONS | 400 | 172.217.22.40:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3680 | iexplore.exe | OPTIONS | 400 | 172.217.22.40:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3680 | iexplore.exe | OPTIONS | 400 | 172.217.22.40:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
660 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4 | System | 172.217.22.40:139 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3384 | iexplore.exe | 172.217.22.40:80 | www.googletagmanager.com | Google Inc. | US | whitelisted |
660 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3384 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
660 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3680 | iexplore.exe | 172.217.22.40:80 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3384 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4 | System | 172.217.22.40:445 | www.googletagmanager.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.googletagmanager.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
20 ETPRO signatures available at the full report