| File name: | Air.Explorer.Pro.v2.5.5.exe |
| Full analysis: | https://app.any.run/tasks/5aa0dc1e-554c-40af-9f71-92ed617d0b86 |
| Verdict: | Malicious activity |
| Analysis date: | July 20, 2019, 03:07:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CAAFA0D2453961405EF5DD0D55713397 |
| SHA1: | EF87FB31349DA0CE151F0013255BF9B1966FDDD5 |
| SHA256: | F16A48A74DEE7C95F7CD1E9311C523A77D653FFE8B6644DBDB49AE6216DF7CB7 |
| SSDEEP: | 98304:lsYIsEWlKfXpVRZmx/KjNl4CDJx0PMsLgVYcO:lsYXEWls5Zm8l4CNxiMmOYcO |
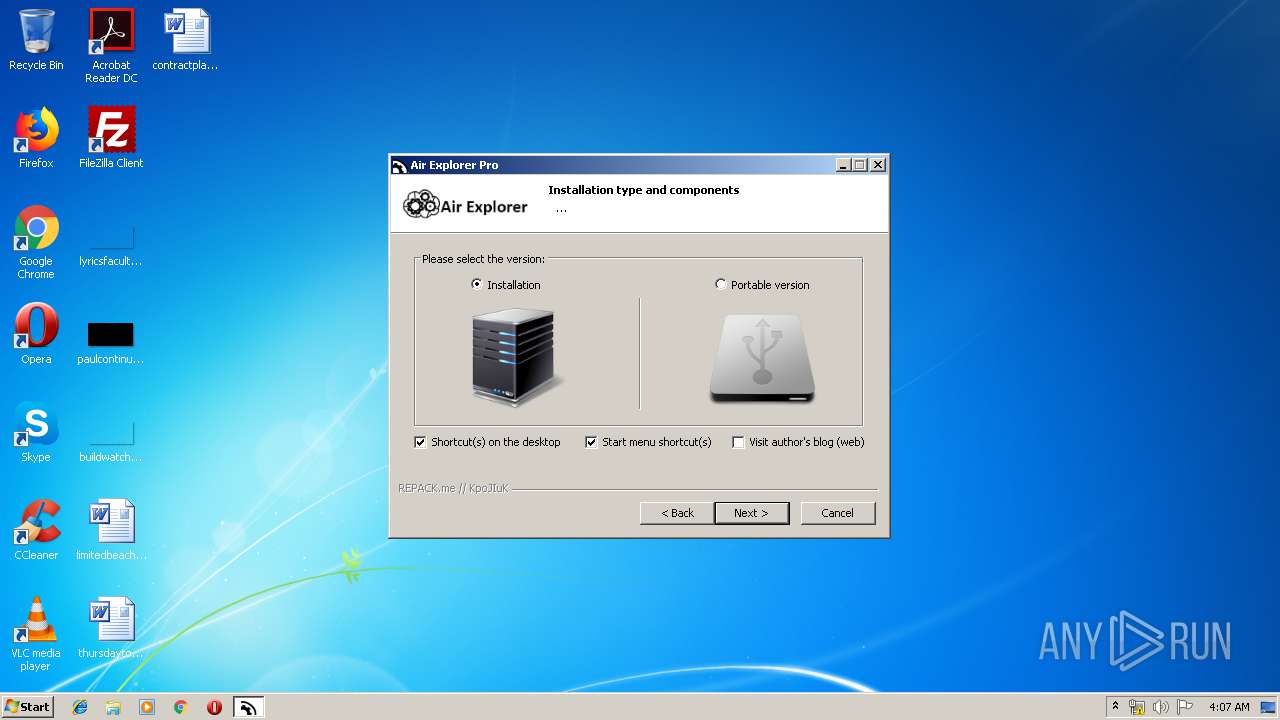
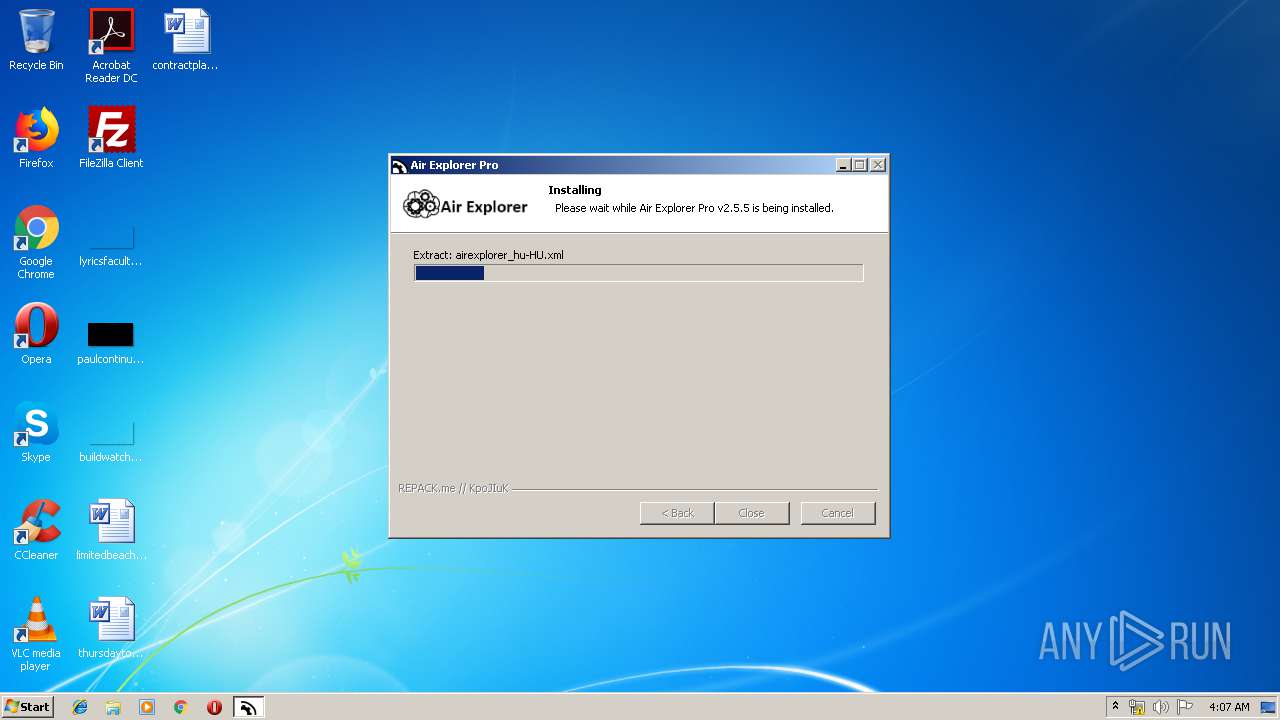
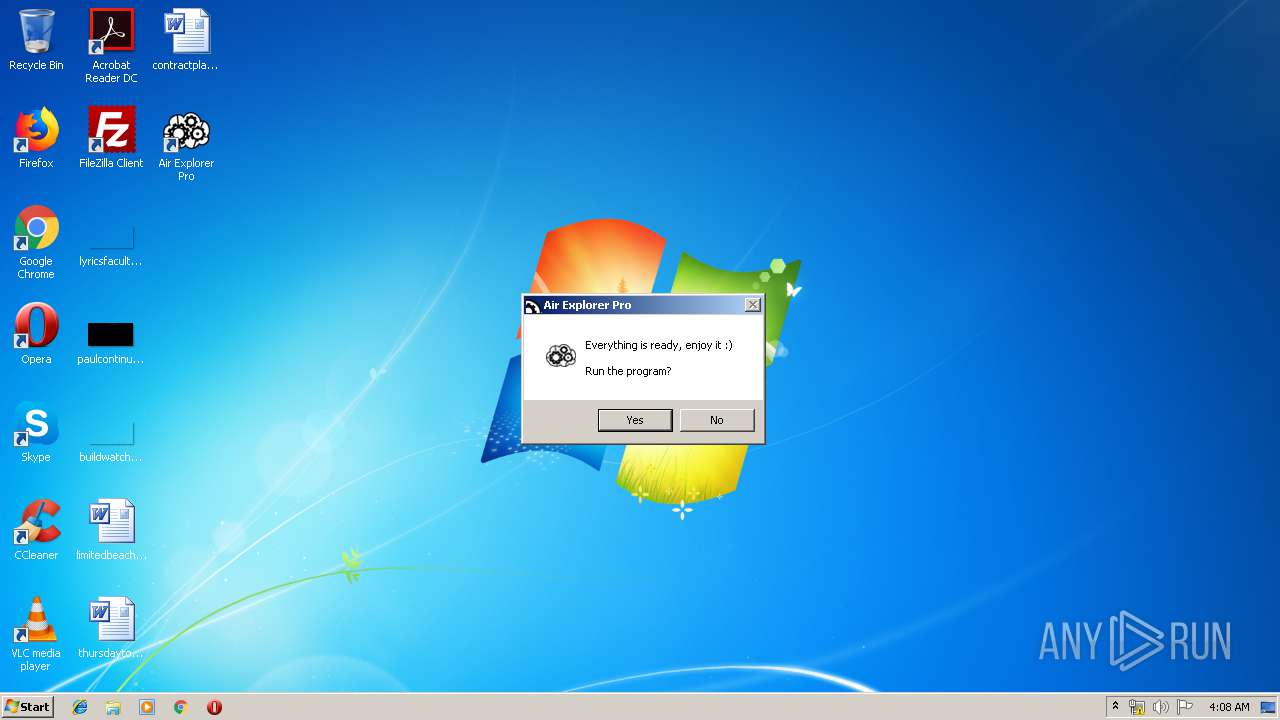
MALICIOUS
Loads dropped or rewritten executable
- Air.Explorer.Pro.v2.5.5.exe (PID: 2284)
- hiru.exe (PID: 2916)
- AirExplorer.exe (PID: 760)
Application was dropped or rewritten from another process
- ns377A.tmp (PID: 540)
- dec.exe (PID: 2380)
- ns3901.tmp (PID: 2400)
- hiru.exe (PID: 3760)
- hiru.exe (PID: 2916)
- AirExplorer.exe (PID: 760)
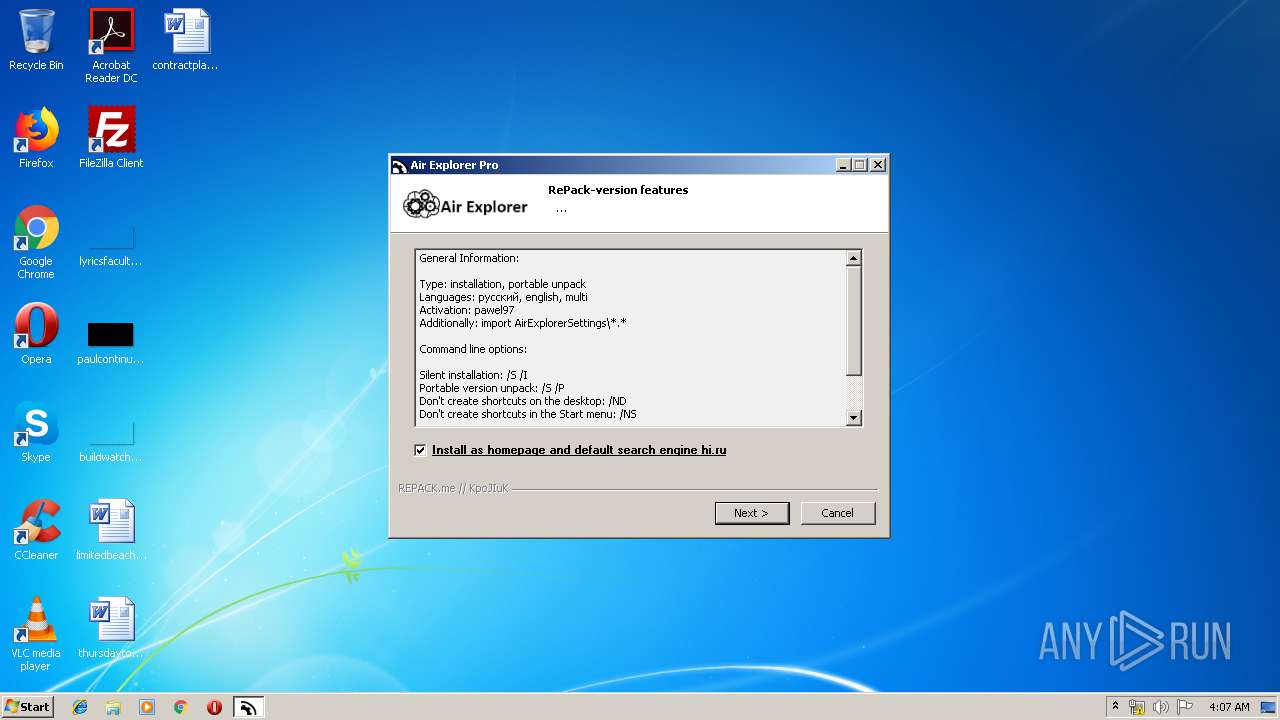
SUSPICIOUS
Creates files in the program directory
- Air.Explorer.Pro.v2.5.5.exe (PID: 2284)
- hiru.exe (PID: 2916)
Uses IPCONFIG.EXE to discover IP address
- ns377A.tmp (PID: 540)
Creates a software uninstall entry
- Air.Explorer.Pro.v2.5.5.exe (PID: 2284)
- hiru.exe (PID: 2916)
Creates files in the user directory
- Air.Explorer.Pro.v2.5.5.exe (PID: 2284)
Executable content was dropped or overwritten
- Air.Explorer.Pro.v2.5.5.exe (PID: 2284)
- dec.exe (PID: 2380)
- hiru.exe (PID: 3760)
- hiru.exe (PID: 2916)
Starts application with an unusual extension
- Air.Explorer.Pro.v2.5.5.exe (PID: 2284)
Starts CMD.EXE for commands execution
- Air.Explorer.Pro.v2.5.5.exe (PID: 2284)
Changes IE settings (feature browser emulation)
- AirExplorer.exe (PID: 760)
Reads internet explorer settings
- AirExplorer.exe (PID: 760)
INFO
Dropped object may contain Bitcoin addresses
- Air.Explorer.Pro.v2.5.5.exe (PID: 2284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:19:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28672 |
| InitializedDataSize: | 445952 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x39e3 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.5.5.0 |
| ProductVersionNumber: | 2.5.5.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | airexplorer.net |
| FileDescription: | Air Explorer Pro v2.5.5 |
| FileVersion: | 2.5.5.0 |
| LegalCopyright: | © airexplorer.net |
| ProductName: | Air Explorer Pro v2.5.5 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:19:59 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | airexplorer.net |
| FileDescription: | Air Explorer Pro v2.5.5 |
| FileVersion: | 2.5.5.0 |
| LegalCopyright: | © airexplorer.net |
| ProductName: | Air Explorer Pro v2.5.5 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:19:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006F10 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49816 |
.rdata | 0x00008000 | 0x00002A92 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39389 |
.data | 0x0000B000 | 0x00067EBC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.47278 |
.ndata | 0x00073000 | 0x000E9000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0015C000 | 0x0000F1C8 | 0x0000F200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.26616 |
.reloc | 0x0016C000 | 0x00000F8A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 7.92997 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22222 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.79597 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 3.44834 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 4.38074 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 4.43602 | 2440 | UNKNOWN | English - United States | RT_ICON |
6 | 2.51392 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.97856 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
51
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | "C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\ns377A.tmp" ipconfig /flushdns | C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\ns377A.tmp | — | Air.Explorer.Pro.v2.5.5.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Air Explorer Pro\AirExplorer.exe" | C:\Program Files\Air Explorer Pro\AirExplorer.exe | — | Air.Explorer.Pro.v2.5.5.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Air Explorer Exit code: 0 Version: 2.5.5.0 Modules
| |||||||||||||||
| 2284 | "C:\Users\admin\AppData\Local\Temp\Air.Explorer.Pro.v2.5.5.exe" | C:\Users\admin\AppData\Local\Temp\Air.Explorer.Pro.v2.5.5.exe | explorer.exe | ||||||||||||
User: admin Company: airexplorer.net Integrity Level: HIGH Description: Air Explorer Pro v2.5.5 Exit code: 0 Version: 2.5.5.0 Modules
| |||||||||||||||
| 2380 | "C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\dec.exe" hiru exe | C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\dec.exe | ns3901.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2400 | "C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\ns3901.tmp" "C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\dec.exe" hiru exe | C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\ns3901.tmp | — | Air.Explorer.Pro.v2.5.5.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2484 | cmd.exe /c "C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\hiru.exe" -p390775 | C:\Windows\system32\cmd.exe | — | Air.Explorer.Pro.v2.5.5.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1000 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2488 | ipconfig /flushdns | C:\Windows\system32\ipconfig.exe | — | ns377A.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2916 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\hiru.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX0\hiru.exe | hiru.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3520 | "C:\Users\admin\AppData\Local\Temp\Air.Explorer.Pro.v2.5.5.exe" | C:\Users\admin\AppData\Local\Temp\Air.Explorer.Pro.v2.5.5.exe | — | explorer.exe | |||||||||||
User: admin Company: airexplorer.net Integrity Level: MEDIUM Description: Air Explorer Pro v2.5.5 Exit code: 3221226540 Version: 2.5.5.0 Modules
| |||||||||||||||
| 3760 | C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\hiru.exe -p390775 | C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\hiru.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1000 Modules
| |||||||||||||||
Total events
1 174
Read events
1 131
Write events
43
Delete events
0
Modification events
| (PID) Process: | (2284) Air.Explorer.Pro.v2.5.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2284) Air.Explorer.Pro.v2.5.5.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2284) Air.Explorer.Pro.v2.5.5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Air Explorer Pro |
| Operation: | write | Name: | DisplayName |
Value: Air Explorer Pro | |||
| (PID) Process: | (2284) Air.Explorer.Pro.v2.5.5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Air Explorer Pro |
| Operation: | write | Name: | Publisher |
Value: airexplorer.net | |||
| (PID) Process: | (2284) Air.Explorer.Pro.v2.5.5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Air Explorer Pro |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Air Explorer Pro\Uninstall.exe | |||
| (PID) Process: | (2284) Air.Explorer.Pro.v2.5.5.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Air Explorer Pro |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Air Explorer Pro\AirExplorer.exe | |||
| (PID) Process: | (3760) hiru.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3760) hiru.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2916) hiru.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Chrome\Extensions\imhlianhlhdicjchlbmbfaefhhjencbe |
| Operation: | write | Name: | version |
Value: 0.4 | |||
| (PID) Process: | (2916) hiru.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Chrome\Extensions\imhlianhlhdicjchlbmbfaefhhjencbe |
| Operation: | write | Name: | update_url |
Value: https://clients2.google.com/service/update2/crx | |||
Executable files
43
Suspicious files
0
Text files
44
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2284 | Air.Explorer.Pro.v2.5.5.exe | C:\Program Files\Air Explorer Pro\AirExplorerCmd.exe | executable | |
MD5:— | SHA256:— | |||
| 2284 | Air.Explorer.Pro.v2.5.5.exe | C:\Program Files\Air Explorer Pro\KRBTabControl.dll | executable | |
MD5:— | SHA256:— | |||
| 2284 | Air.Explorer.Pro.v2.5.5.exe | C:\Program Files\Air Explorer Pro\AirExplorer.exe | executable | |
MD5:— | SHA256:— | |||
| 2284 | Air.Explorer.Pro.v2.5.5.exe | C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\newadvsplash.dll | executable | |
MD5:55A723E125AFBC9B3A41D46F41749068 | SHA256:0A70CC4B93D87ECD93E538CFBED7C9A4B8B5C6F1042C6069757BDA0D1279ED06 | |||
| 2284 | Air.Explorer.Pro.v2.5.5.exe | C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\repackme.gif | image | |
MD5:23D3840ADB8F4F1EFC083A1F7E640191 | SHA256:82A1454402156D74F4F23C992D5D772B665546208EFF44790871B8DCB36D2304 | |||
| 2284 | Air.Explorer.Pro.v2.5.5.exe | C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\LangDLL.dll | executable | |
MD5:A1CD3F159EF78D9ACE162F067B544FD9 | SHA256:47B9E251C9C90F43E3524965AECC07BD53C8E09C5B9F9862B44C306667E2B0B6 | |||
| 2284 | Air.Explorer.Pro.v2.5.5.exe | C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\modern-header.bmp | image | |
MD5:FCE32CFF69894E582054E47A7E5E075E | SHA256:AA7E095F977B17FD27FF4A58EAA679A56117D1D3BD0E2B69292AE42227278866 | |||
| 2284 | Air.Explorer.Pro.v2.5.5.exe | C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\1.bmp | image | |
MD5:DEC435FEBCB6AFA7D48712C6B7B7F797 | SHA256:CF0BF3E2326C6D6C60C0EB72F23D2F57E02C50B1C08012EC0F3490AD7992F85A | |||
| 2284 | Air.Explorer.Pro.v2.5.5.exe | C:\Program Files\Air Explorer Pro\BouncyCastle.Crypto.dll | executable | |
MD5:CC986FA07D3A886E7F5343E6A4DA90FA | SHA256:8063AC472E4D34D086AC22B003D2027137B367652F92C111E6076FF98D1C8580 | |||
| 2284 | Air.Explorer.Pro.v2.5.5.exe | C:\Users\admin\AppData\Local\Temp\nsuFC44.tmp\System.dll | executable | |
MD5:BF712F32249029466FA86756F5546950 | SHA256:7851CB12FA4131F1FEE5DE390D650EF65CAC561279F1CFE70AD16CC9780210AF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report