| File name: | 19f51d90e7ea70a6376a2918c0f0d56f4299bcde.doc |
| Full analysis: | https://app.any.run/tasks/1d54d6c3-4df8-4f55-9eb6-e0d3370ac077 |
| Verdict: | Malicious activity |
| Analysis date: | January 26, 2022, 10:34:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: John Tear, Template: Normal.dotm, Last Saved By: John Tear, Revision Number: 73, Name of Creating Application: Microsoft Office Word, Total Editing Time: 01:08:00, Create Time/Date: Mon Oct 25 19:49:00 2021, Last Saved Time/Date: Mon Oct 25 21:01:00 2021, Number of Pages: 1, Number of Words: 8, Number of Characters: 50, Security: 0 |
| MD5: | 20C9739AEF69BFDD9A4CCFD767B6B346 |
| SHA1: | 19F51D90E7EA70A6376A2918C0F0D56F4299BCDE |
| SHA256: | F169B4A701EDD1A771AFF13F4A2AB9606EEDCD8EEA231D5B76C95D0143D2452F |
| SSDEEP: | 24576:iaL0UTXIa5LcZLBl4wfghAN4ybPmisZ3xq2A9DeOsg:nNhAN4DxuD |
MALICIOUS
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2368)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2368)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2368)
SUSPICIOUS
Reads the date of Windows installation
- WINWORD.EXE (PID: 2368)
Reads default file associations for system extensions
- WINWORD.EXE (PID: 2368)
Checks supported languages
- cmd.exe (PID: 1228)
- cmd.exe (PID: 3444)
- cmd.exe (PID: 352)
- cmd.exe (PID: 2336)
- cmd.exe (PID: 2532)
Application launched itself
- cmd.exe (PID: 1228)
- cmd.exe (PID: 352)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1228)
- cmd.exe (PID: 352)
Creates files in the Windows directory
- WINWORD.EXE (PID: 2368)
INFO
Reads the computer name
- WINWORD.EXE (PID: 2368)
Checks supported languages
- WINWORD.EXE (PID: 2368)
- NOTEPAD.EXE (PID: 3316)
- find.exe (PID: 3408)
Reads Microsoft Outlook installation path
- WINWORD.EXE (PID: 2368)
Creates files in the user directory
- WINWORD.EXE (PID: 2368)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserType: | Microsoft Word 97-2003 Document |
|---|---|
| CompObjUserTypeLen: | 32 |
| HeadingPairs: |
|
| TitleOfParts: | - |
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| ScaleCrop: | No |
| AppVersion: | 16 |
| CharCountWithSpaces: | 57 |
| Paragraphs: | 1 |
| Lines: | 1 |
| Company: | - |
| CodePage: | Windows Latin 1 (Western European) |
| Security: | None |
| Characters: | 50 |
| Words: | 8 |
| Pages: | 1 |
| ModifyDate: | 2021:10:25 20:01:00 |
| CreateDate: | 2021:10:25 18:49:00 |
| TotalEditTime: | 1.1 hours |
| Software: | Microsoft Office Word |
| RevisionNumber: | 73 |
| LastModifiedBy: | John Tear |
| Template: | Normal.dotm |
| Comments: | - |
| Keywords: | - |
| Author: | John Tear |
| Subject: | - |
| Title: | - |
Total processes
48
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\system32\cmd.exe /S /D /c" FOR /F %i in ('find "shell.txt"') do copy "%i" C:\windows\tasks\" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1228 | cmd.exe /c dir C:\Users\admin\AppData\Local\Temp\ /s /b | for /f %i in ('find "shell.txt"') do copy "%i" C:\windows\tasks\ | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2336 | C:\Windows\system32\cmd.exe /c find "shell.txt" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\19f51d90e7ea70a6376a2918c0f0d56f4299bcde.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2532 | cmd.exe /c move /Y C:\windows\tasks\shell.txt C:\windows\tasks\shell.exe | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
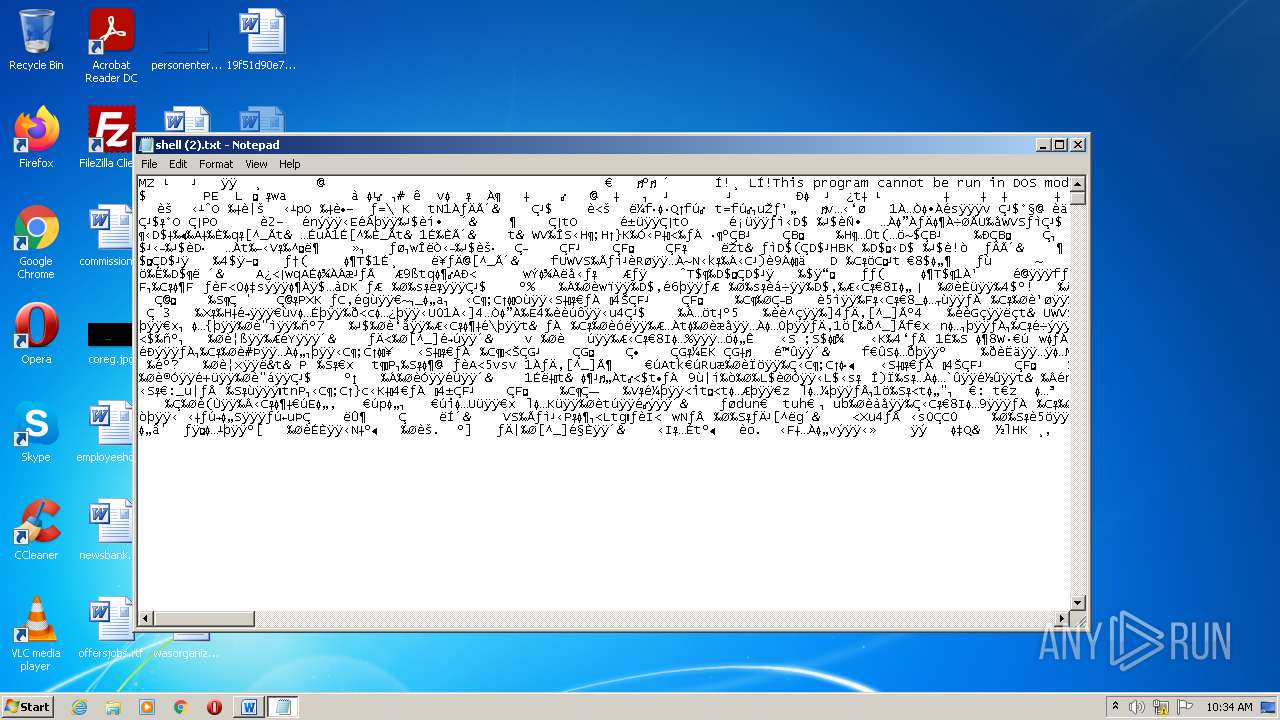
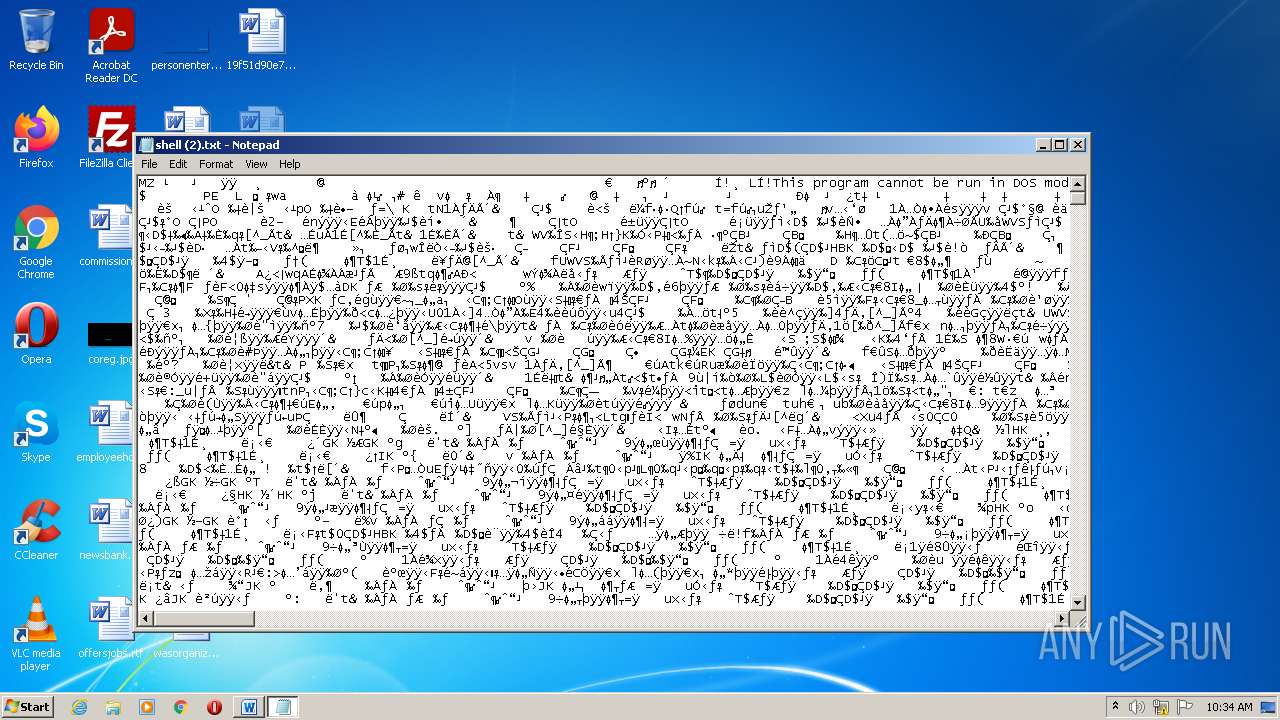
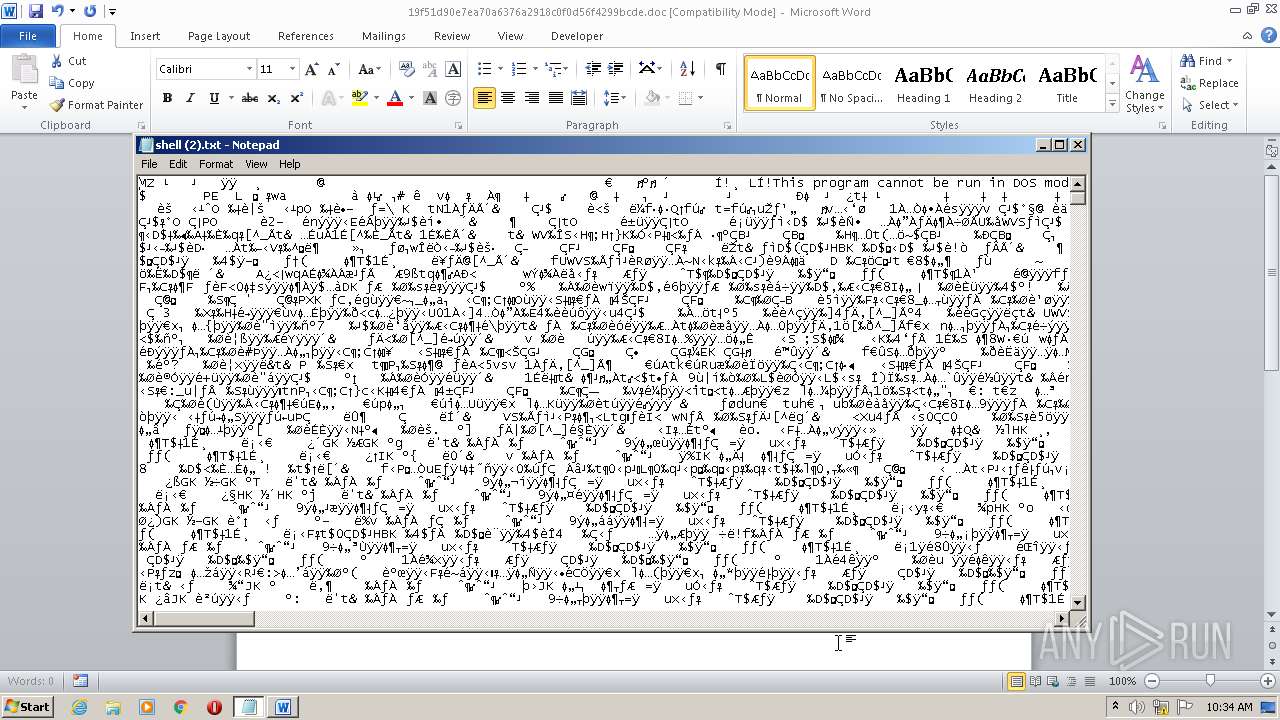
| 3316 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\shell (2).txt | C:\Windows\system32\NOTEPAD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3408 | find "shell.txt" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3444 | C:\Windows\system32\cmd.exe /S /D /c" dir C:\Users\admin\AppData\Local\Temp\ /s /b " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
4 136
Read events
3 335
Write events
649
Delete events
152
Modification events
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | c.= |
Value: 632E3D0040090000010000000000000000000000 | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
1
Suspicious files
0
Text files
5
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREA53.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\Desktop\~$f51d90e7ea70a6376a2918c0f0d56f4299bcde.doc | pgc | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\19f51d90e7ea70a6376a2918c0f0d56f4299bcde.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2ADC049E.emf | emf | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\shell (2).txt:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CD26B410.wmf | image | |
MD5:— | SHA256:— | |||
| 2368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\shell (2).txt | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.2:53 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |