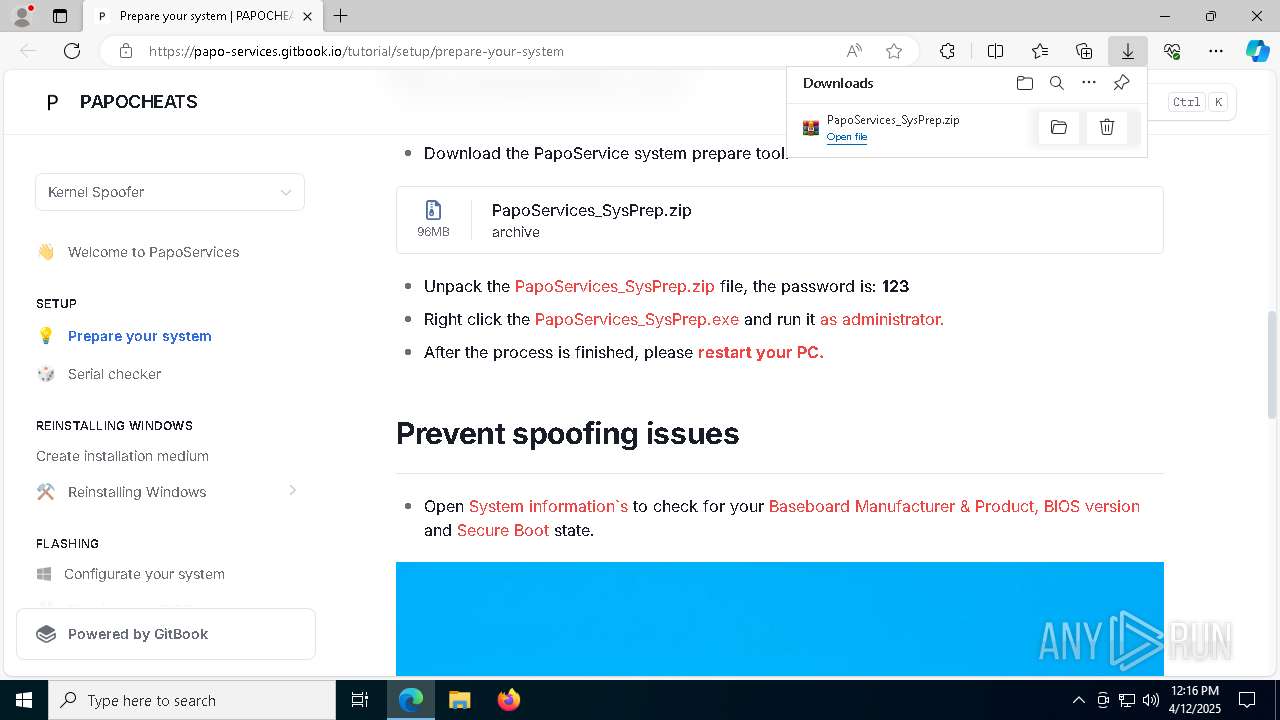
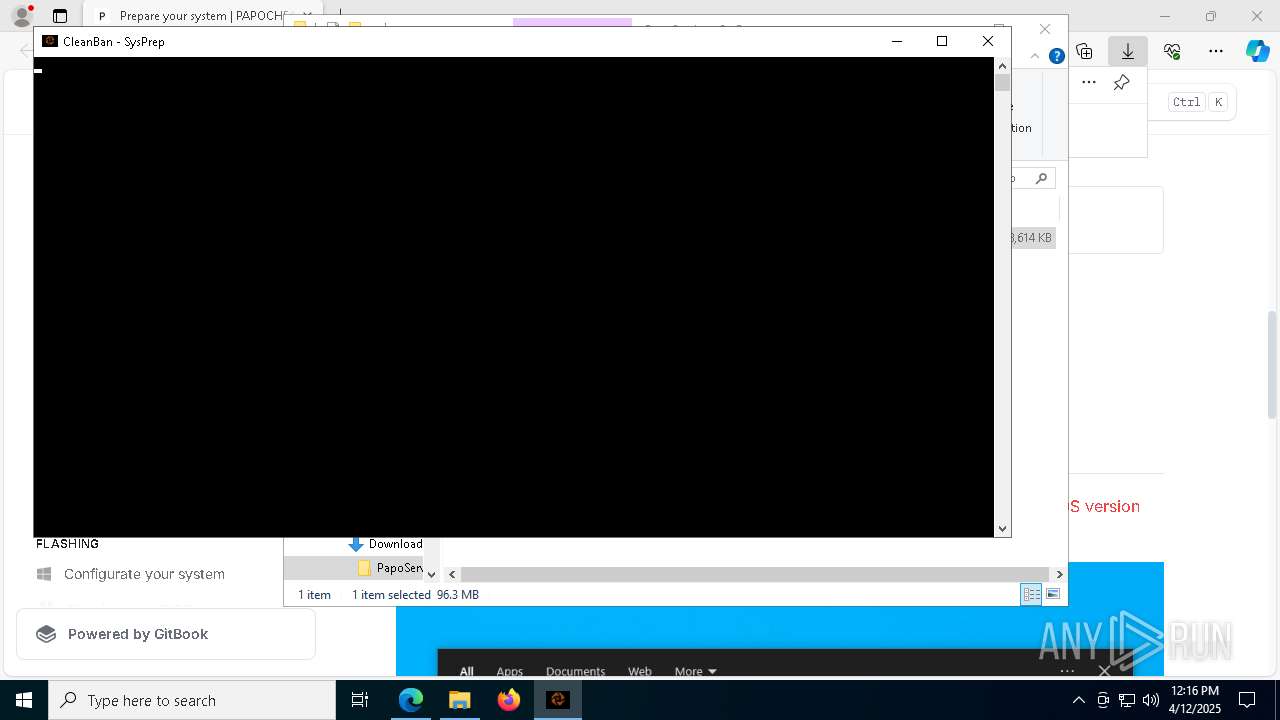
| URL: | https://papo-services.gitbook.io/tutorial/setup/prepare-your-system |
| Full analysis: | https://app.any.run/tasks/1a319f63-195f-481f-958c-1c92c2ee0bd5 |
| Verdict: | Malicious activity |
| Analysis date: | April 12, 2025, 12:15:37 |
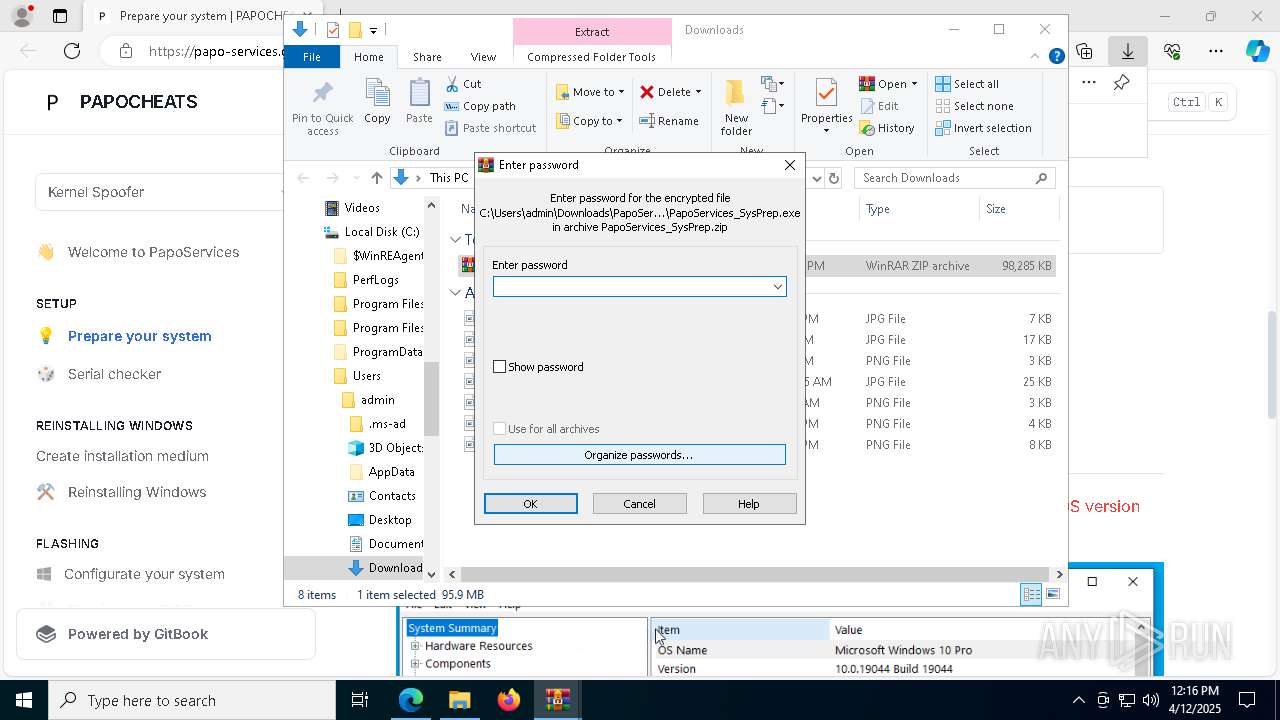
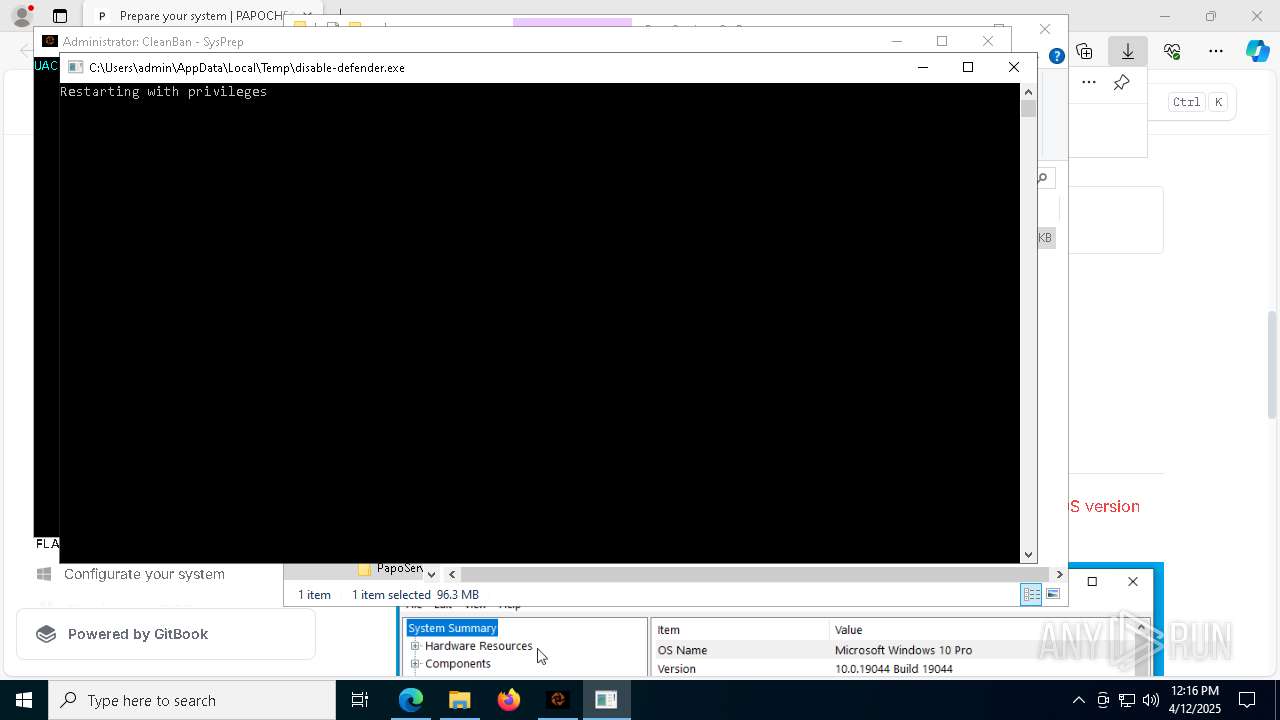
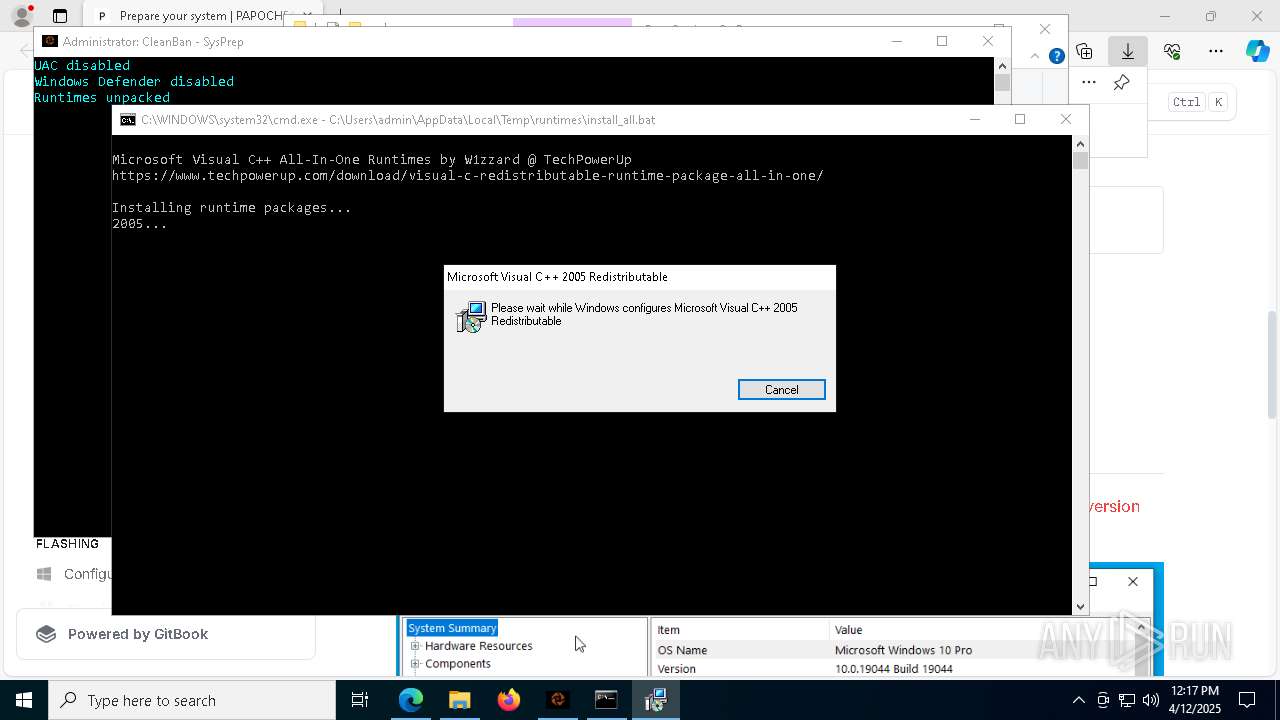
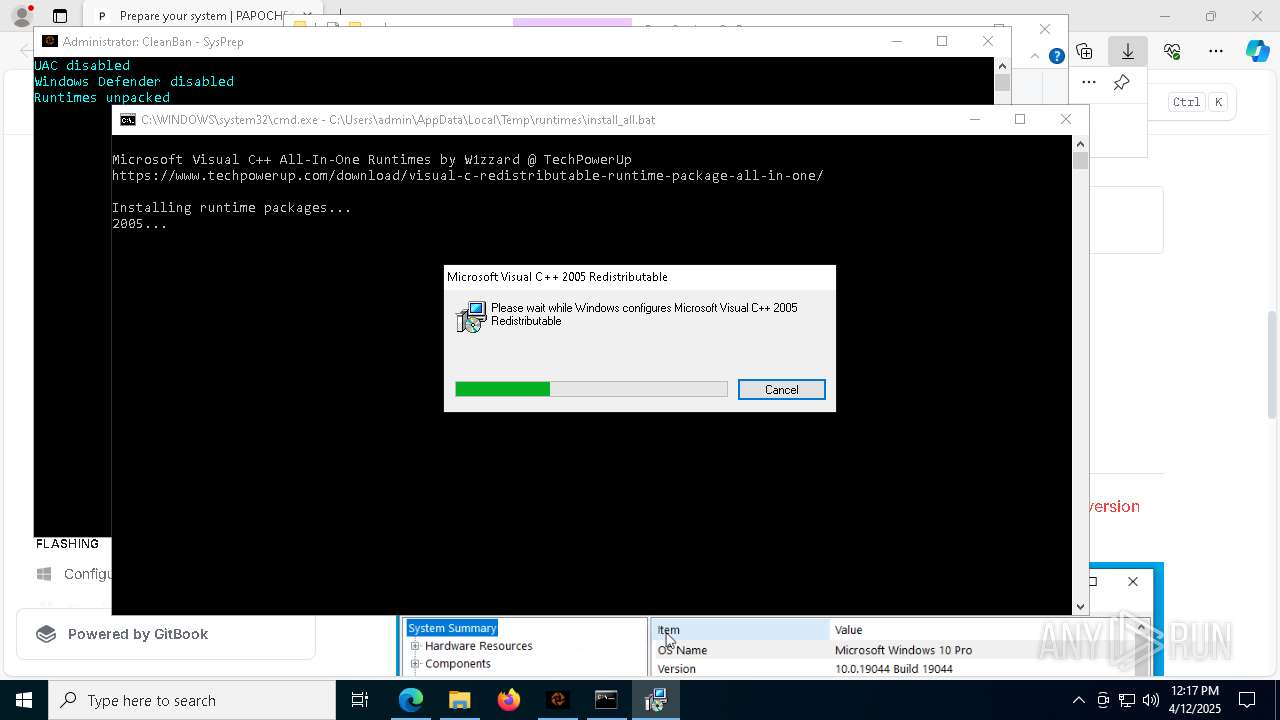
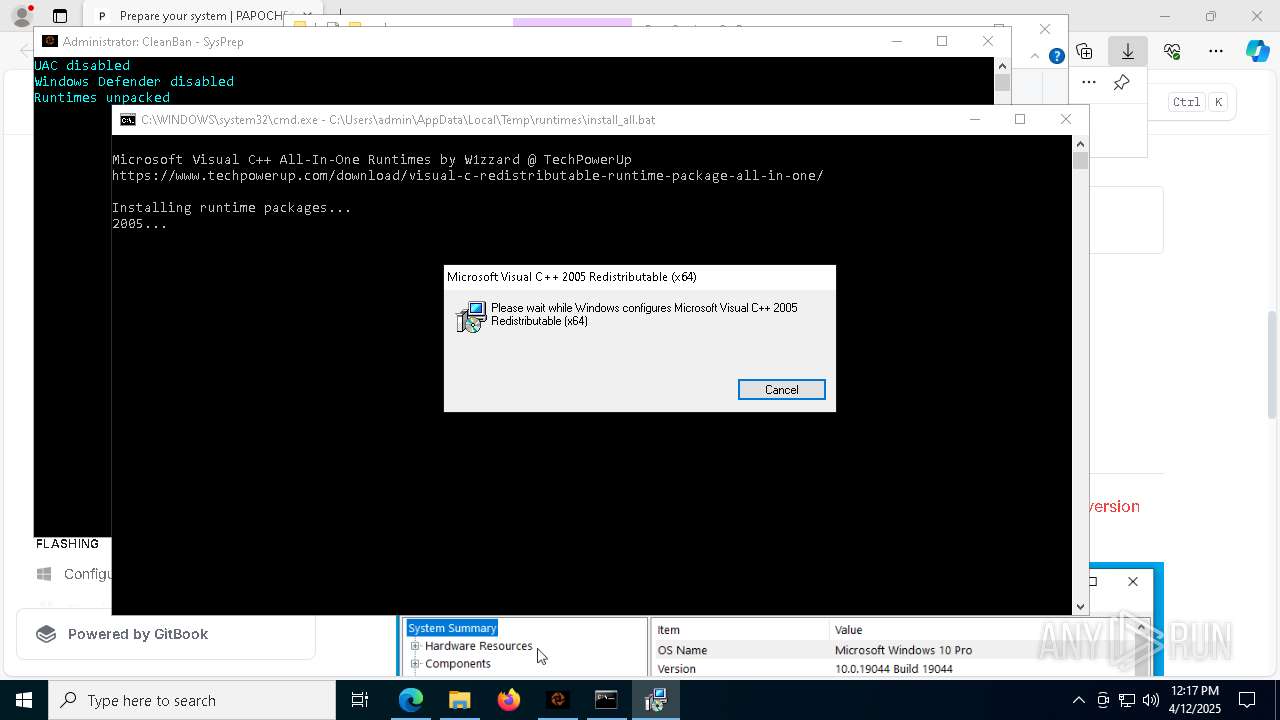
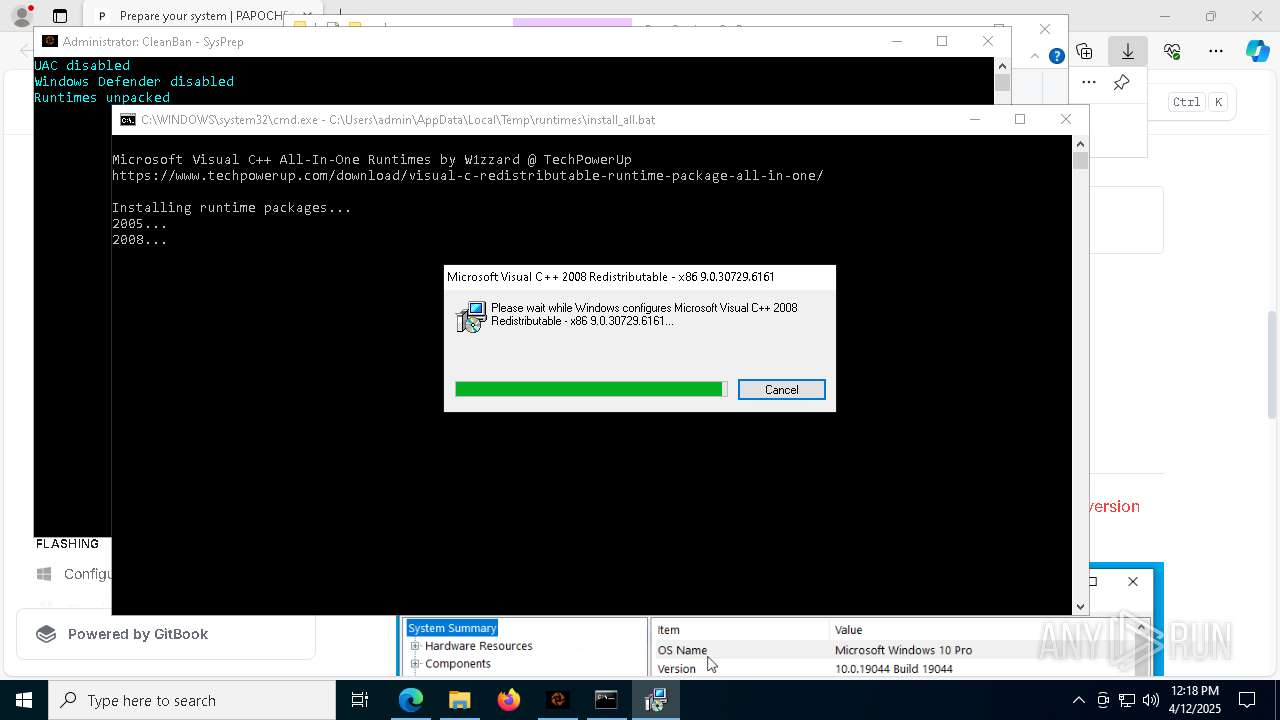
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 34961F8BBCC8BD2DC700B60B3F565F40 |
| SHA1: | 5A3BE7D701EF7C2FCB036C20E827C684A466F952 |
| SHA256: | F1674A8C428213FD96A62D241609DC011BA53B60812E3A31C2A2413E46B6F5D1 |
| SSDEEP: | 3:N8AgIHVILLQ1/ARAK9ULz:2Ao2ARApz |
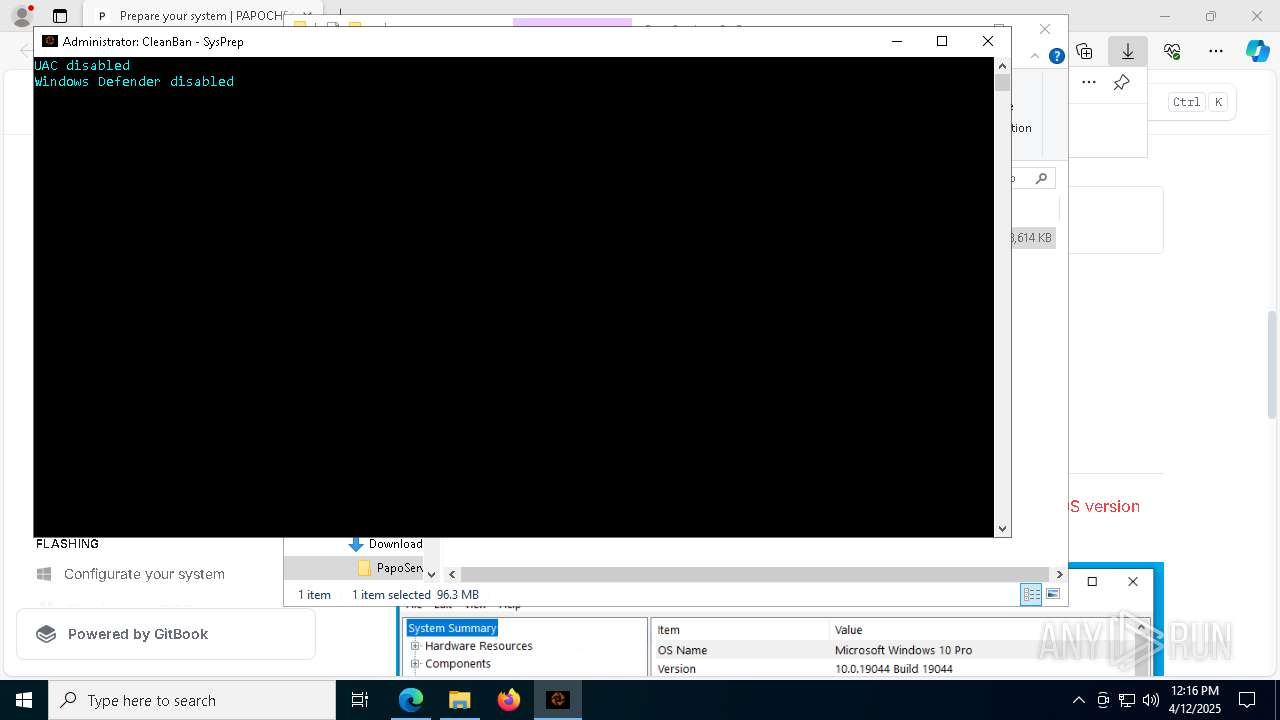
MALICIOUS
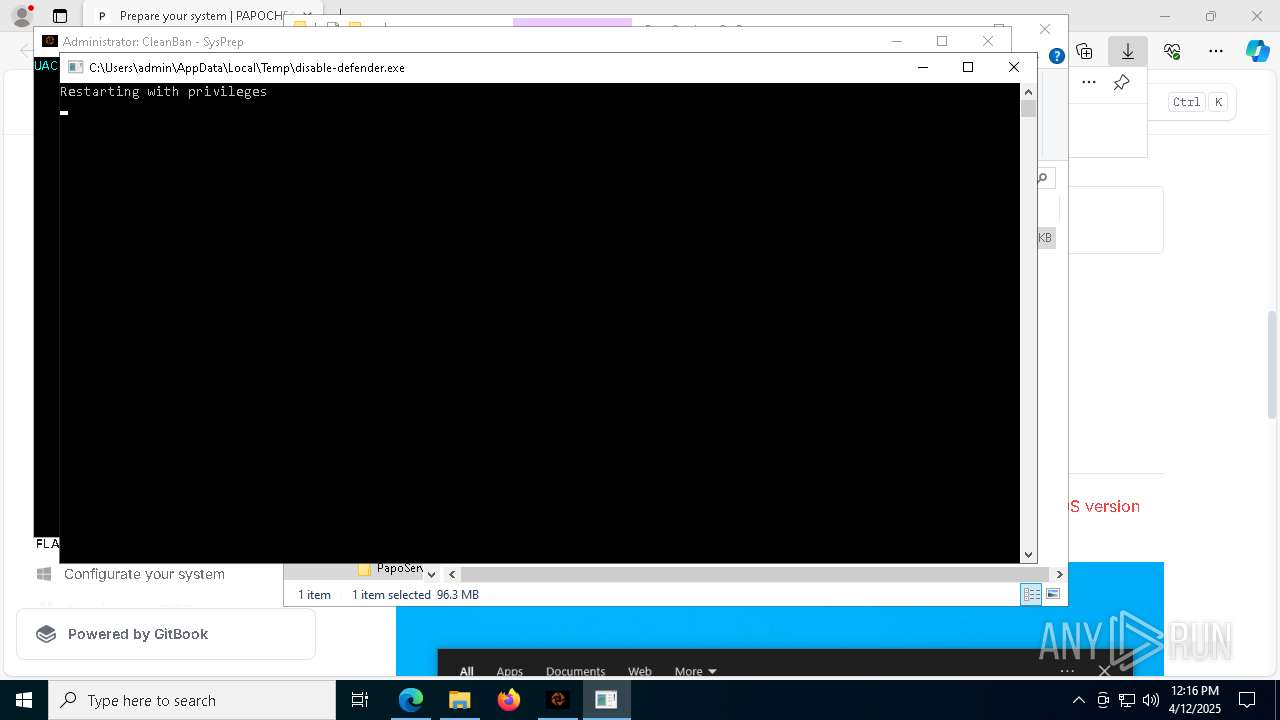
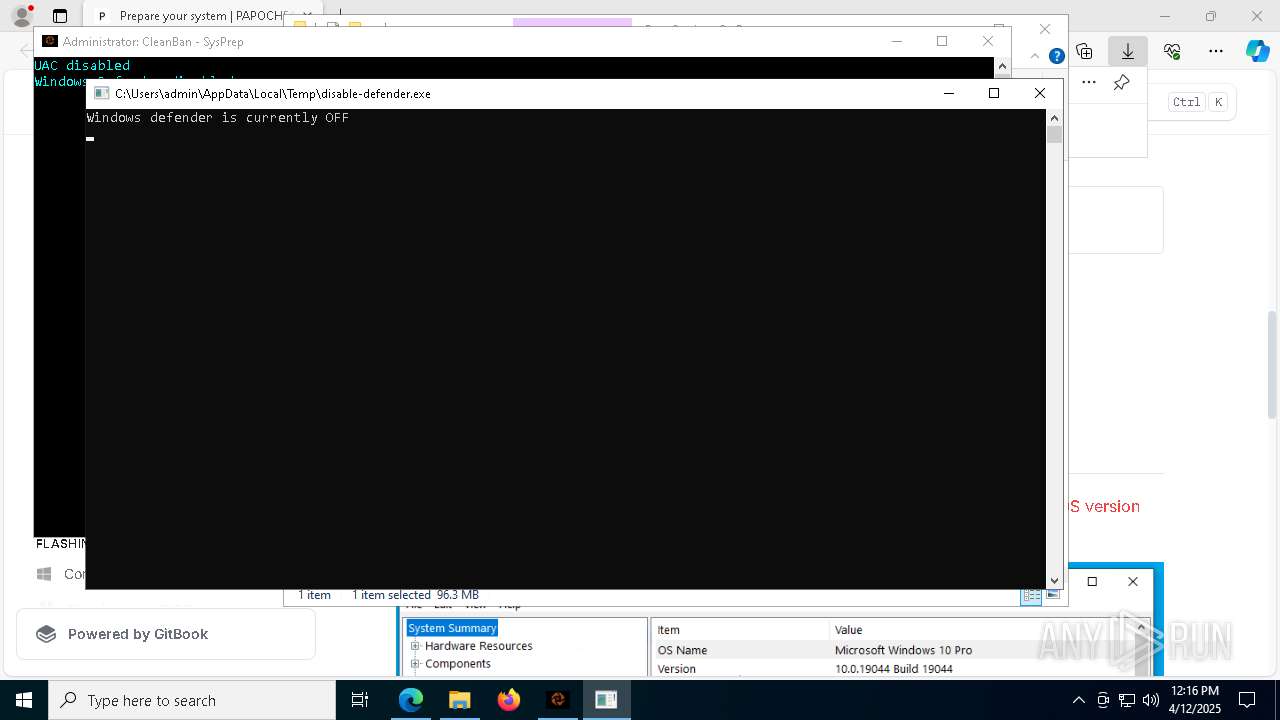
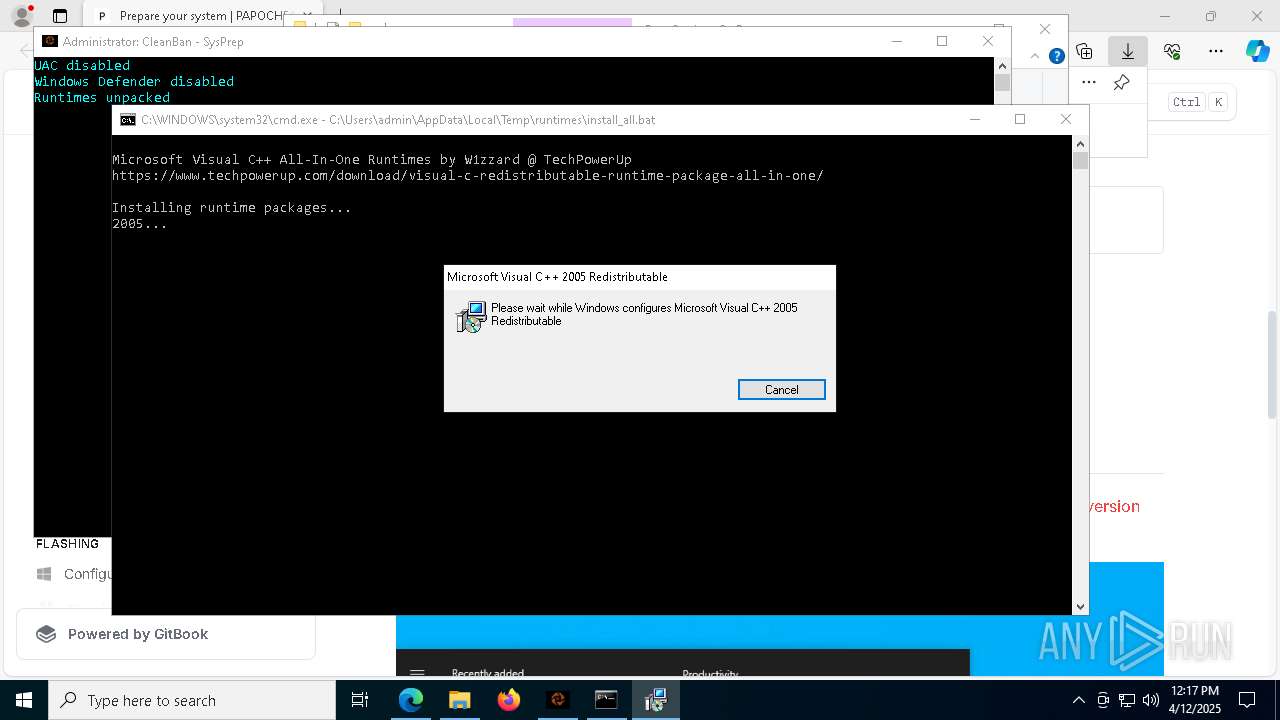
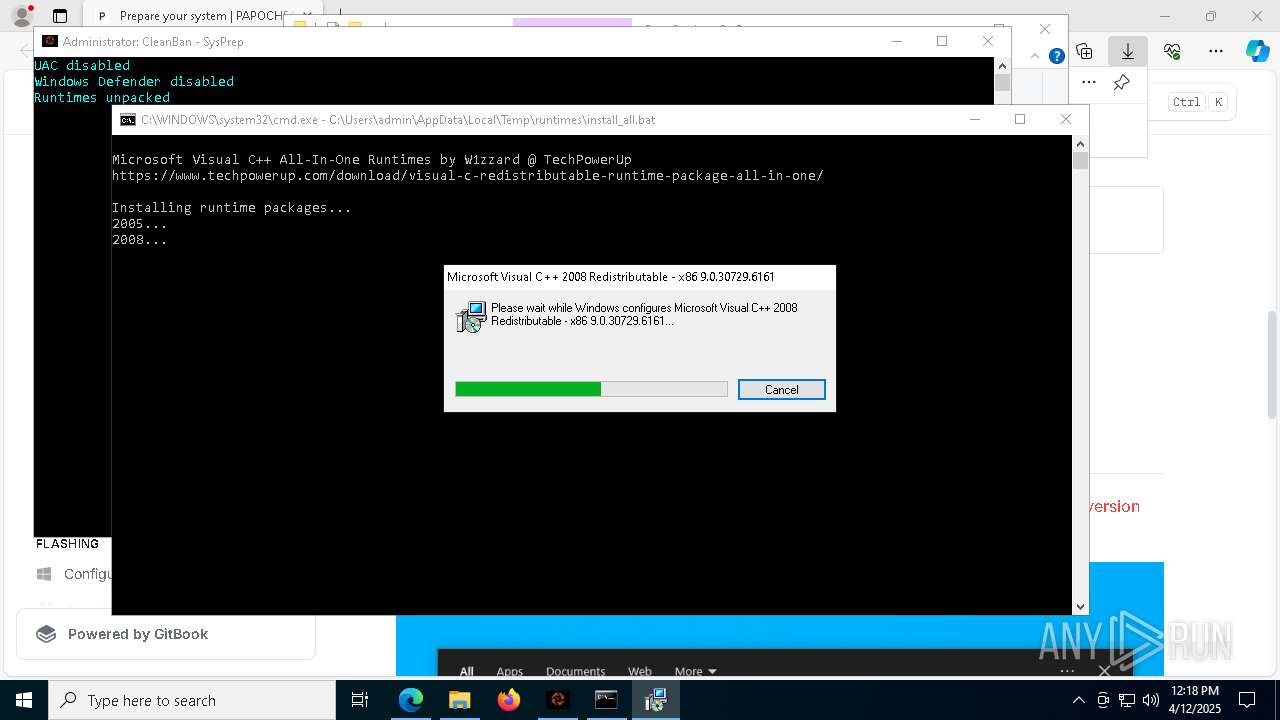
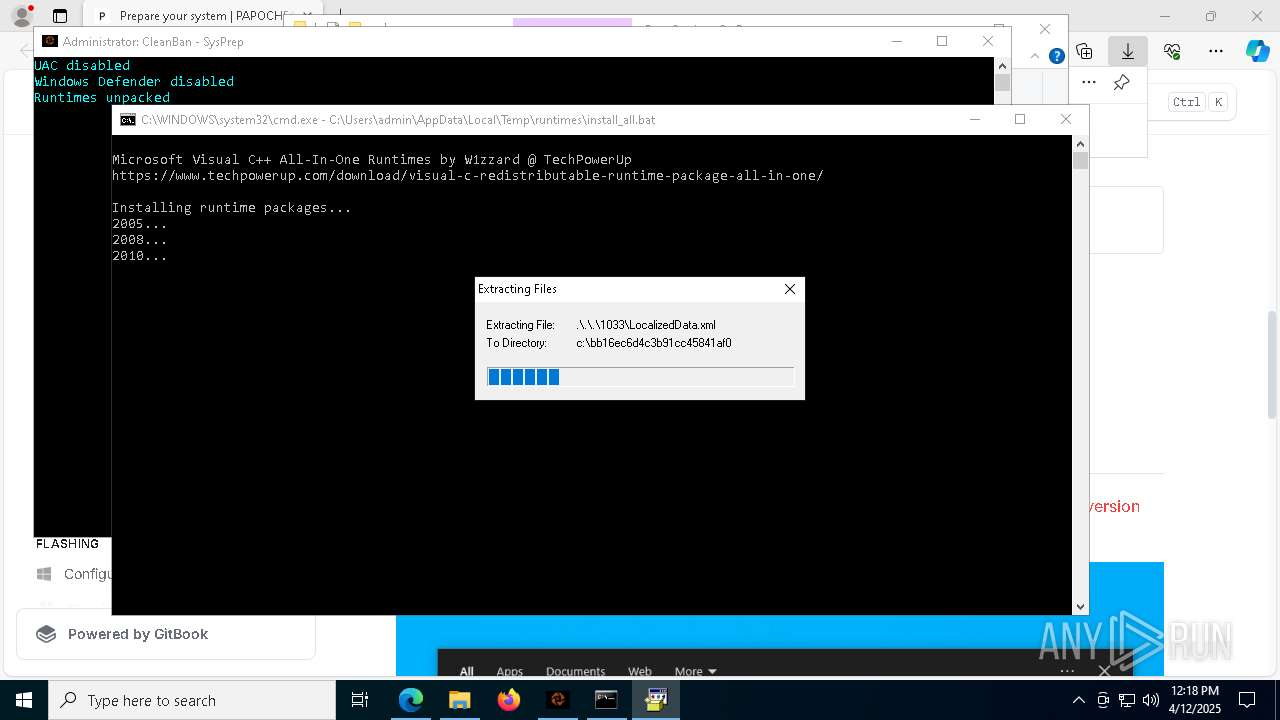
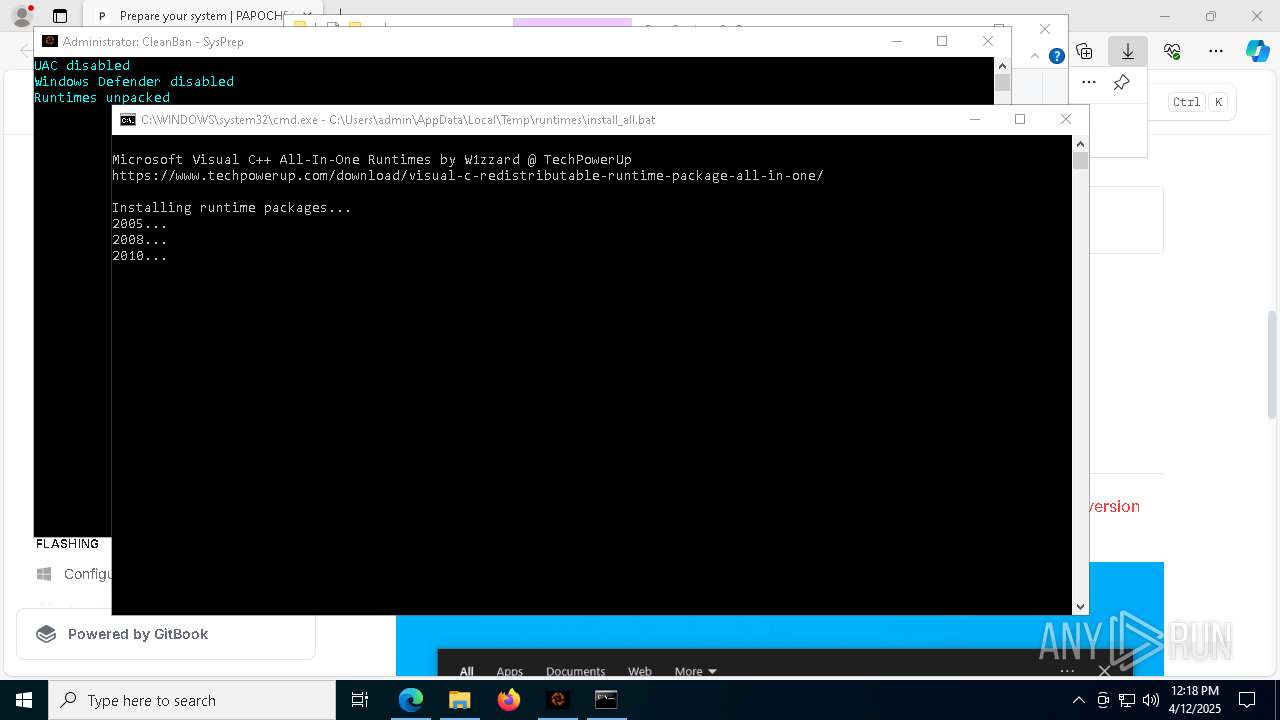
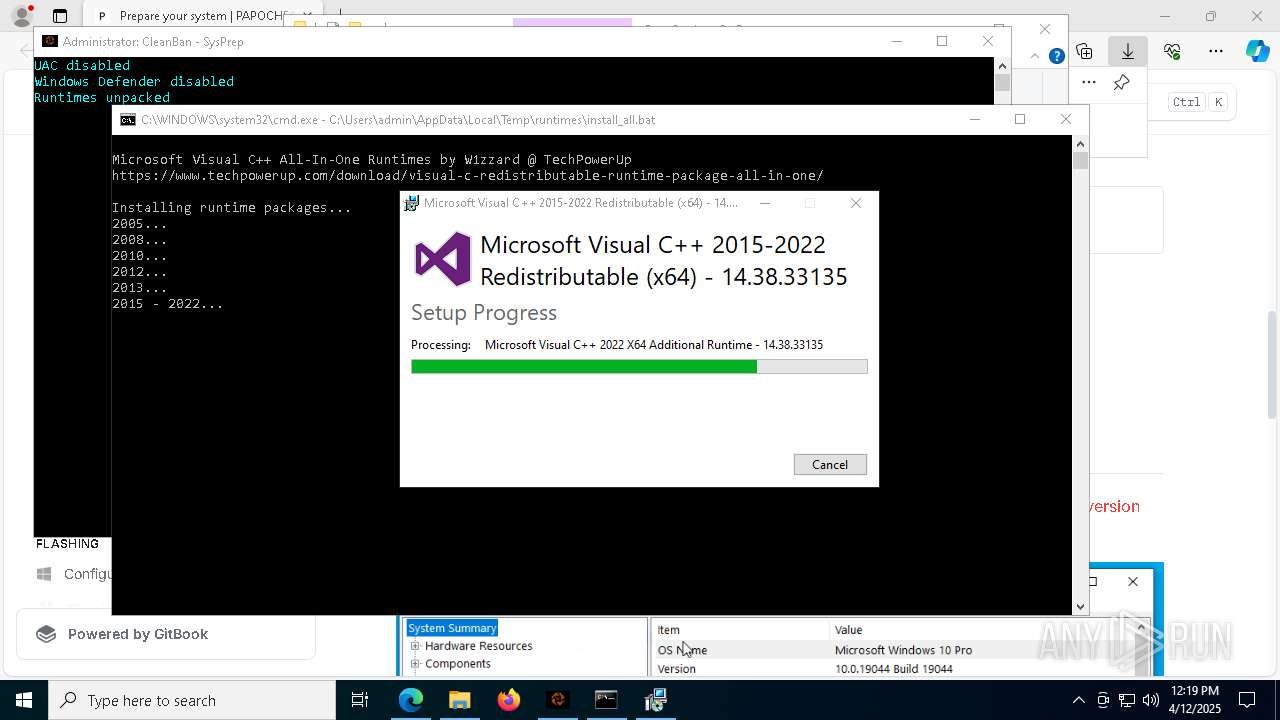
Disables Windows Defender
- disable-defender.exe (PID: 4776)
Creates or modifies Windows services
- disable-defender.exe (PID: 4776)
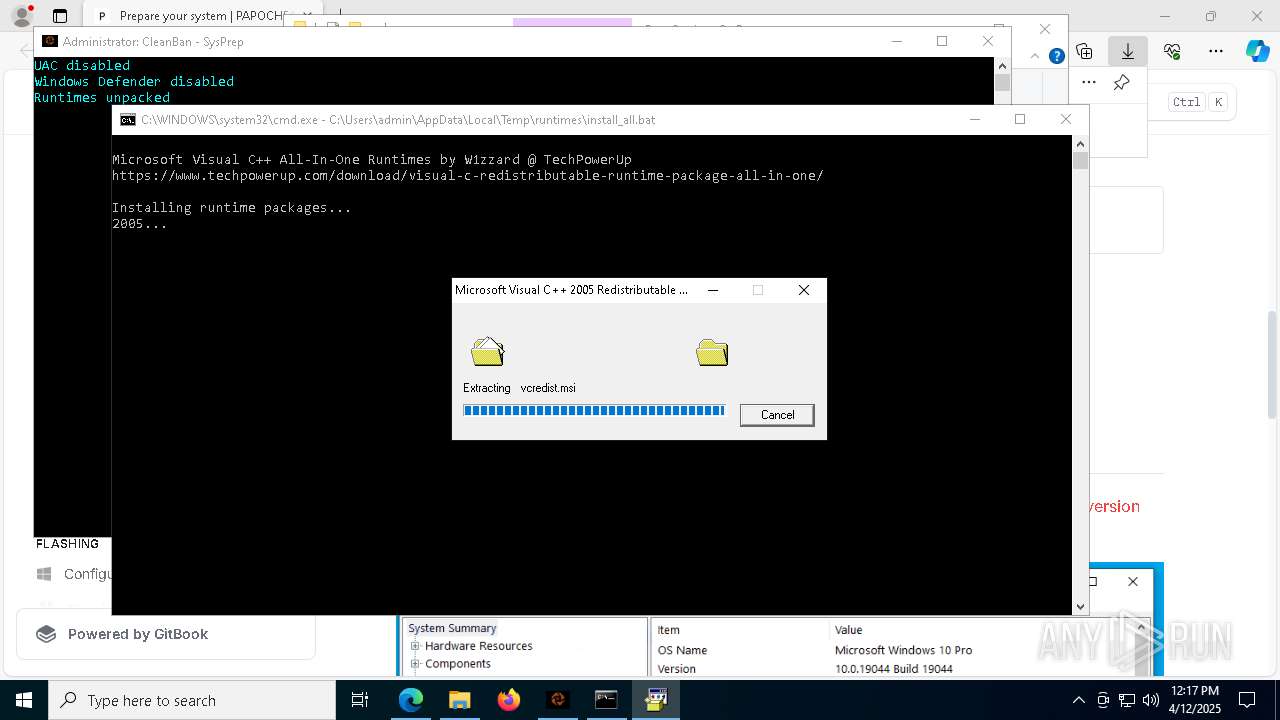
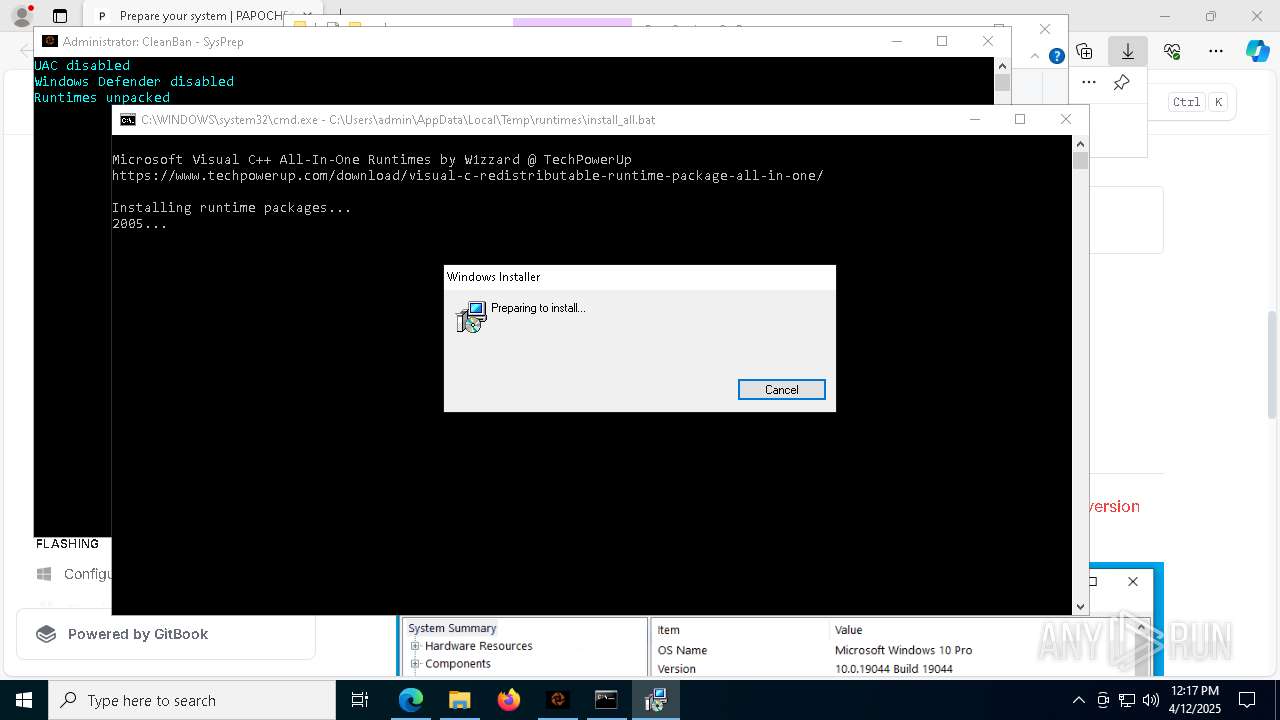
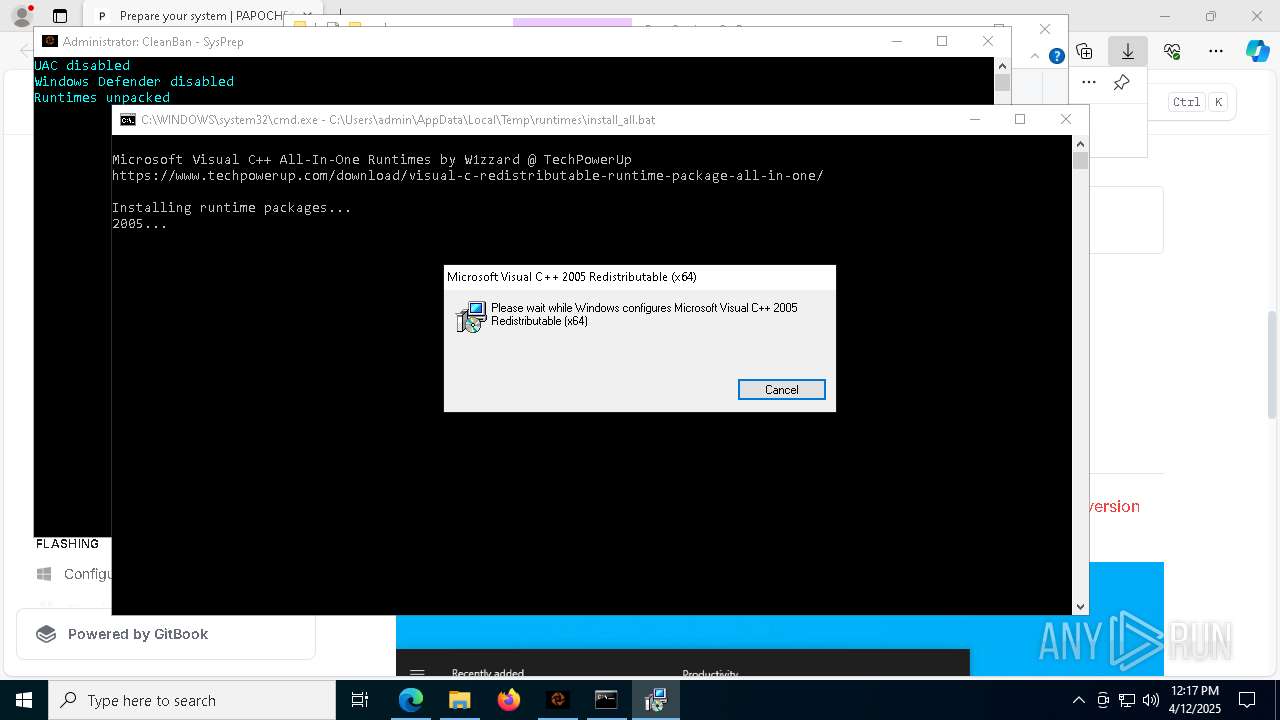
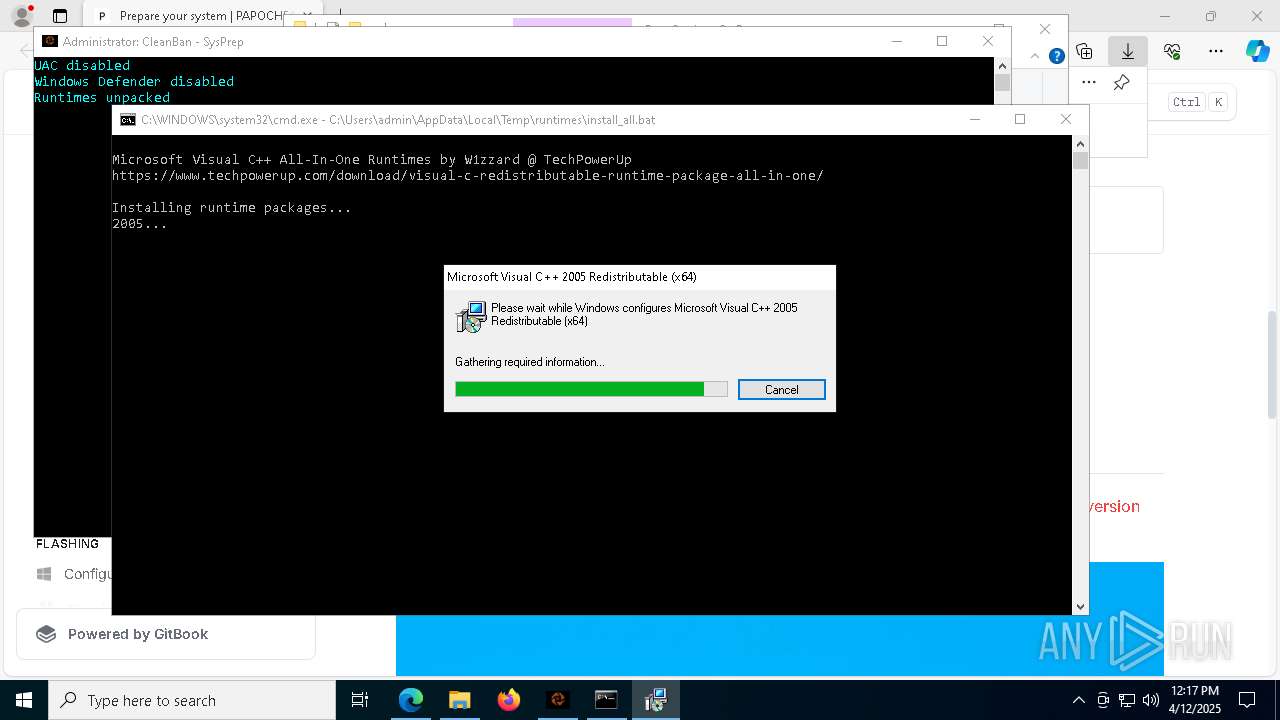
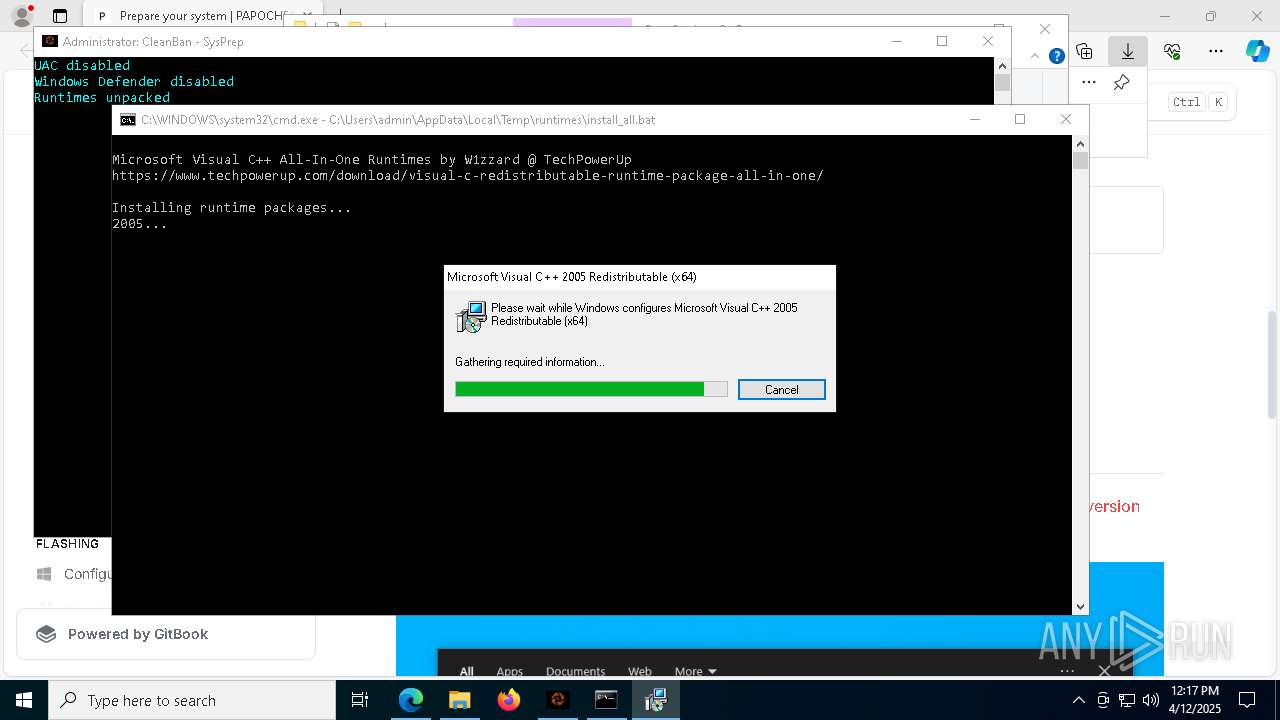
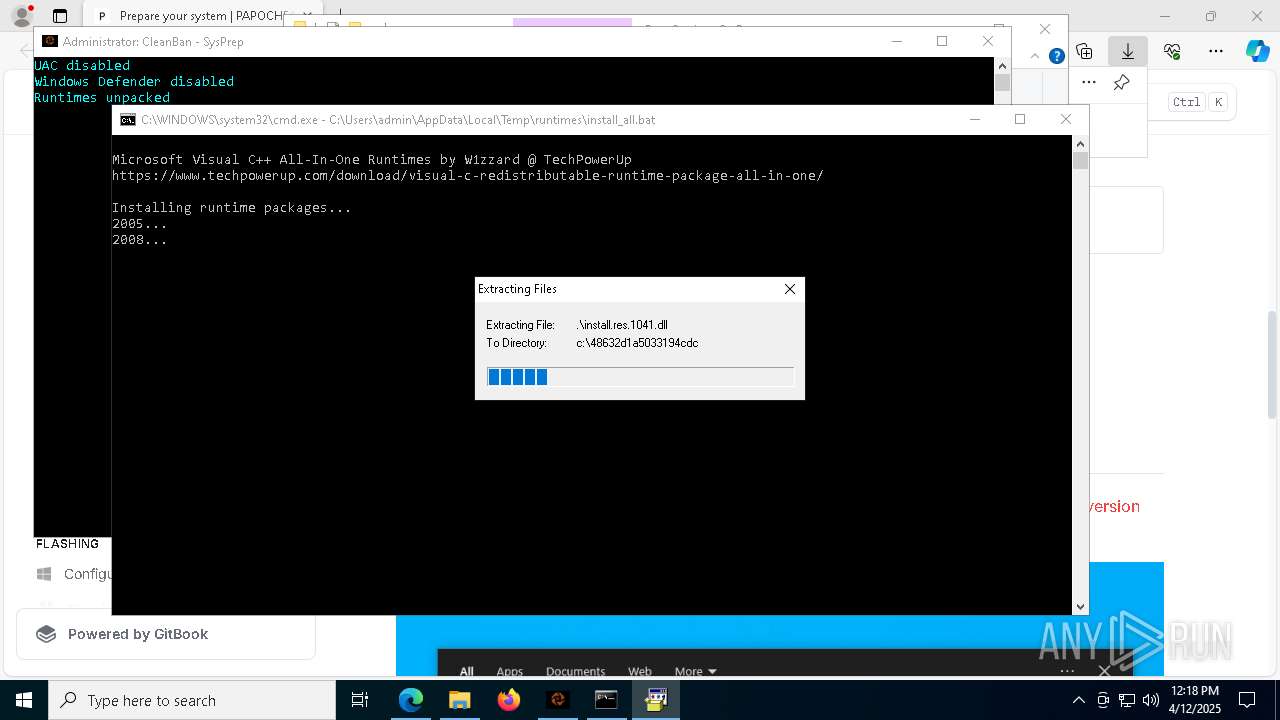
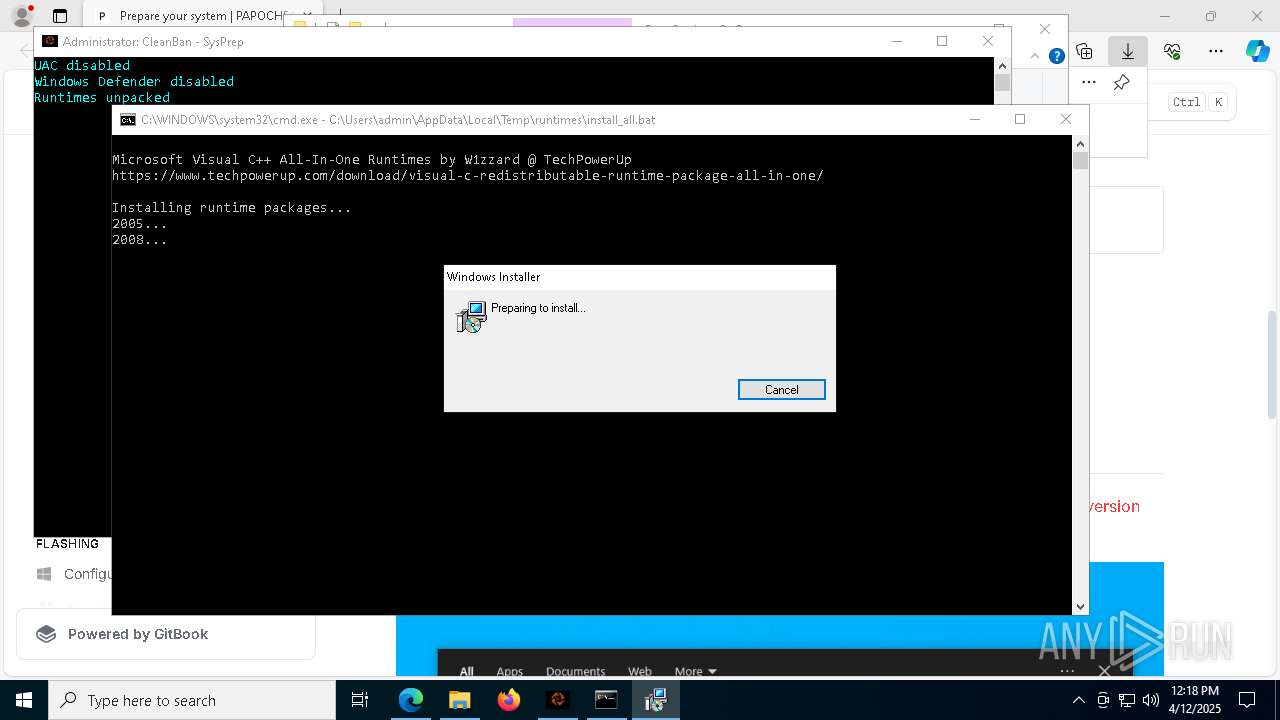
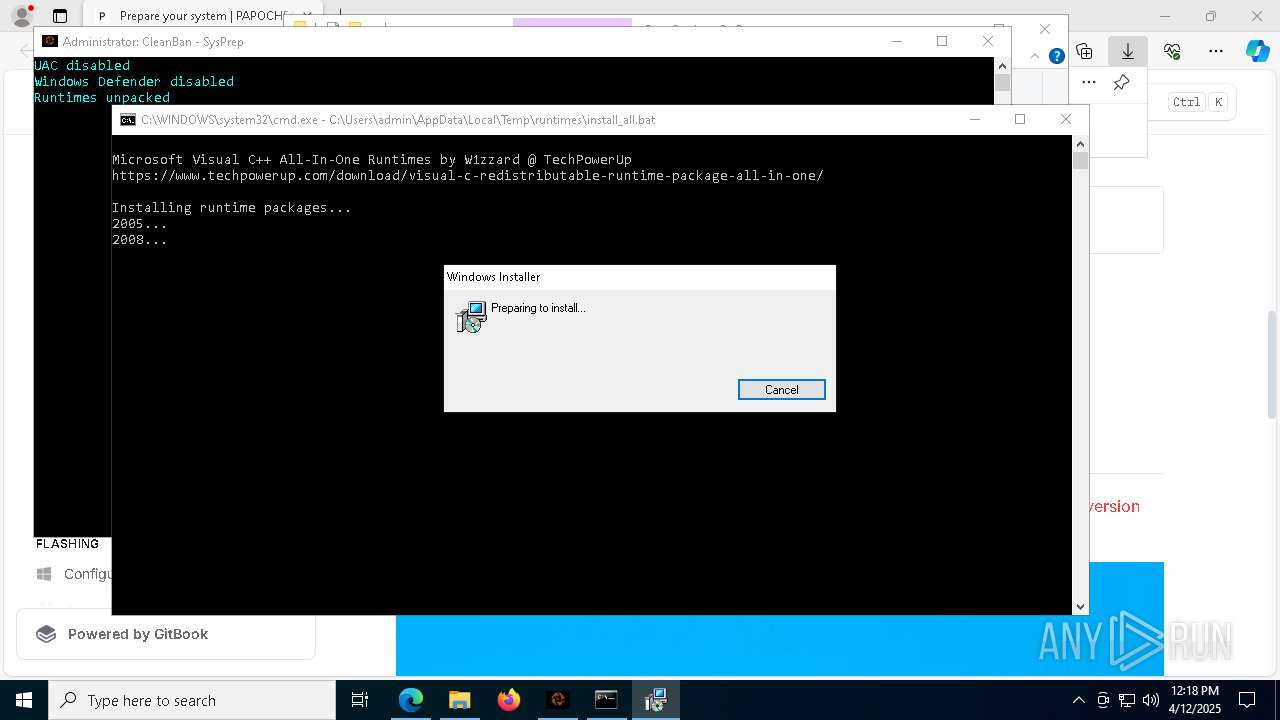
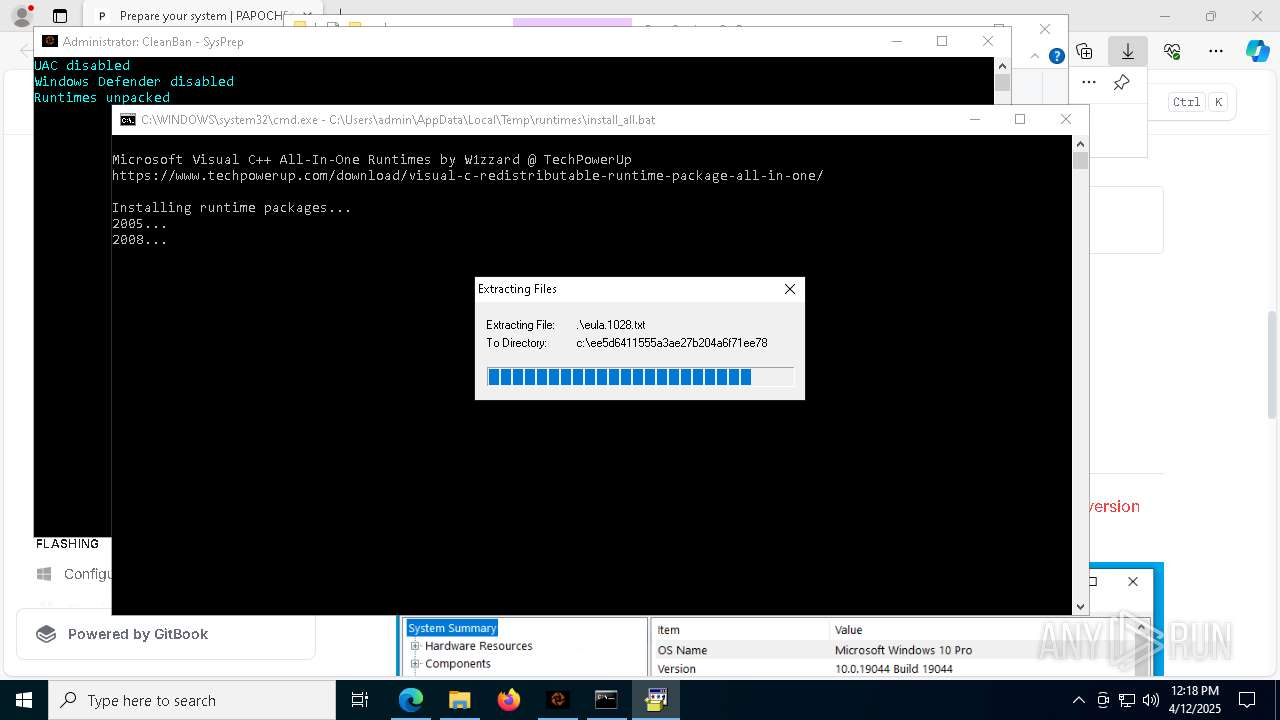
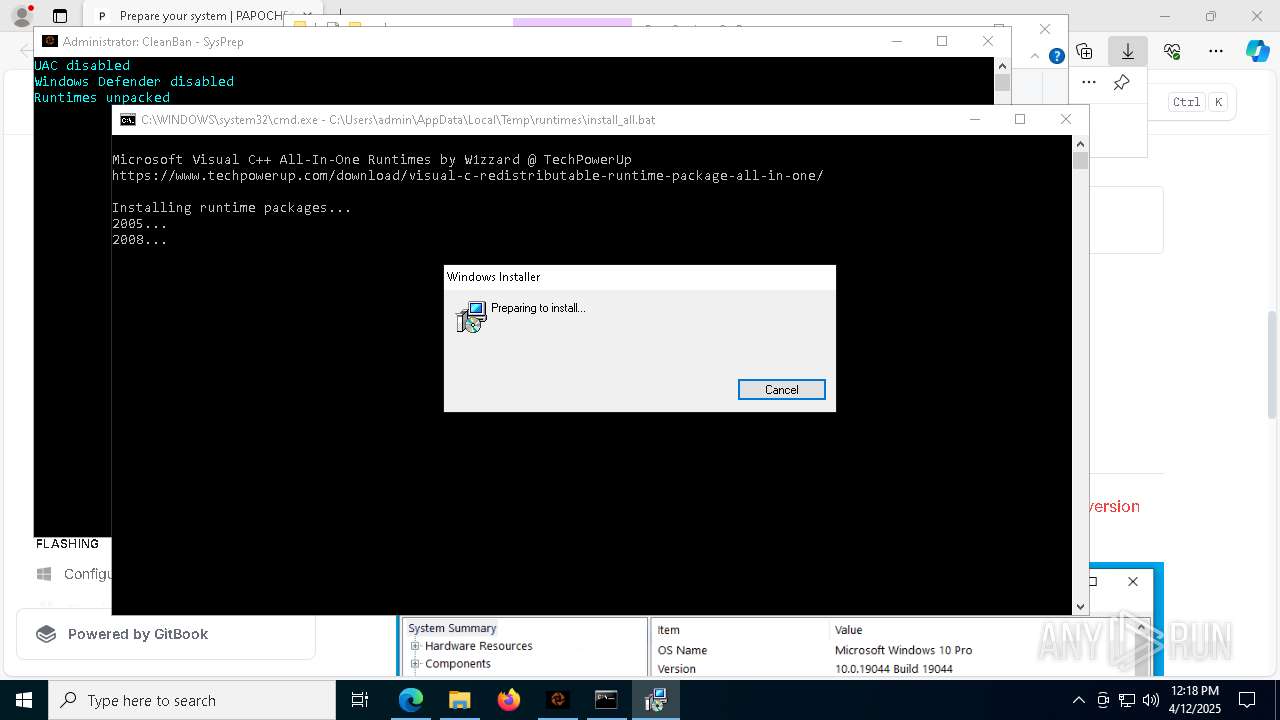
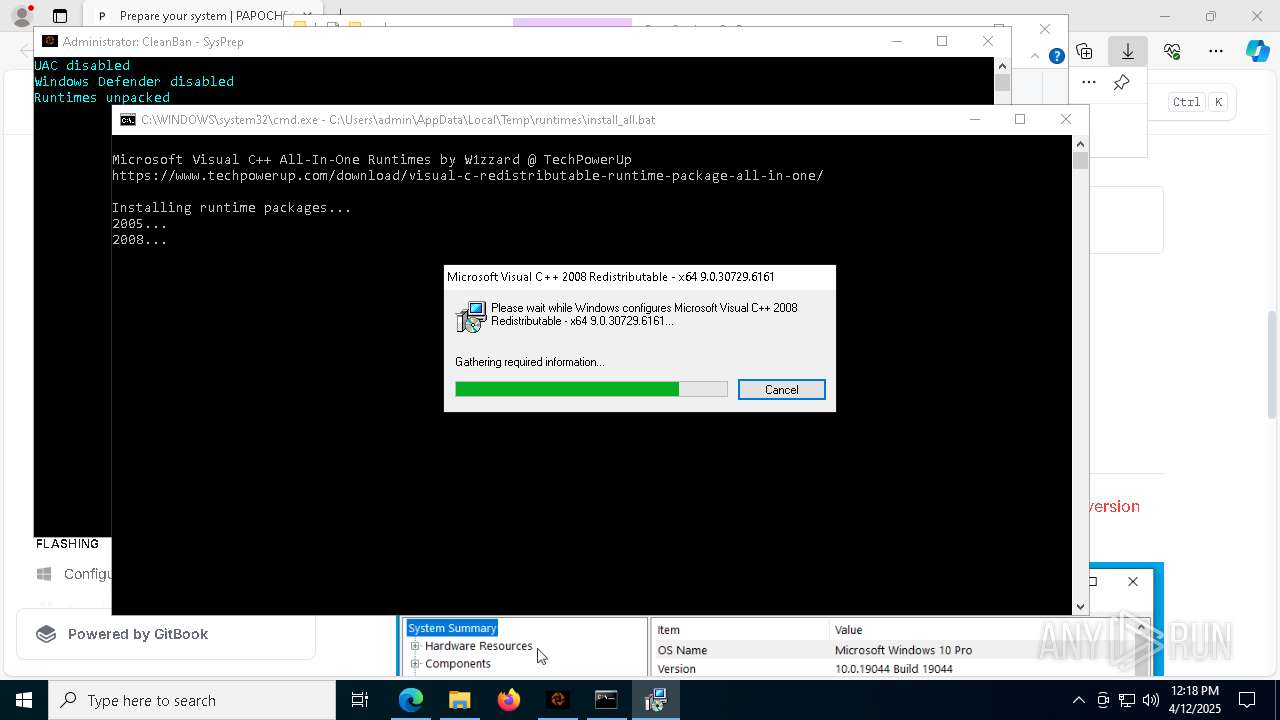
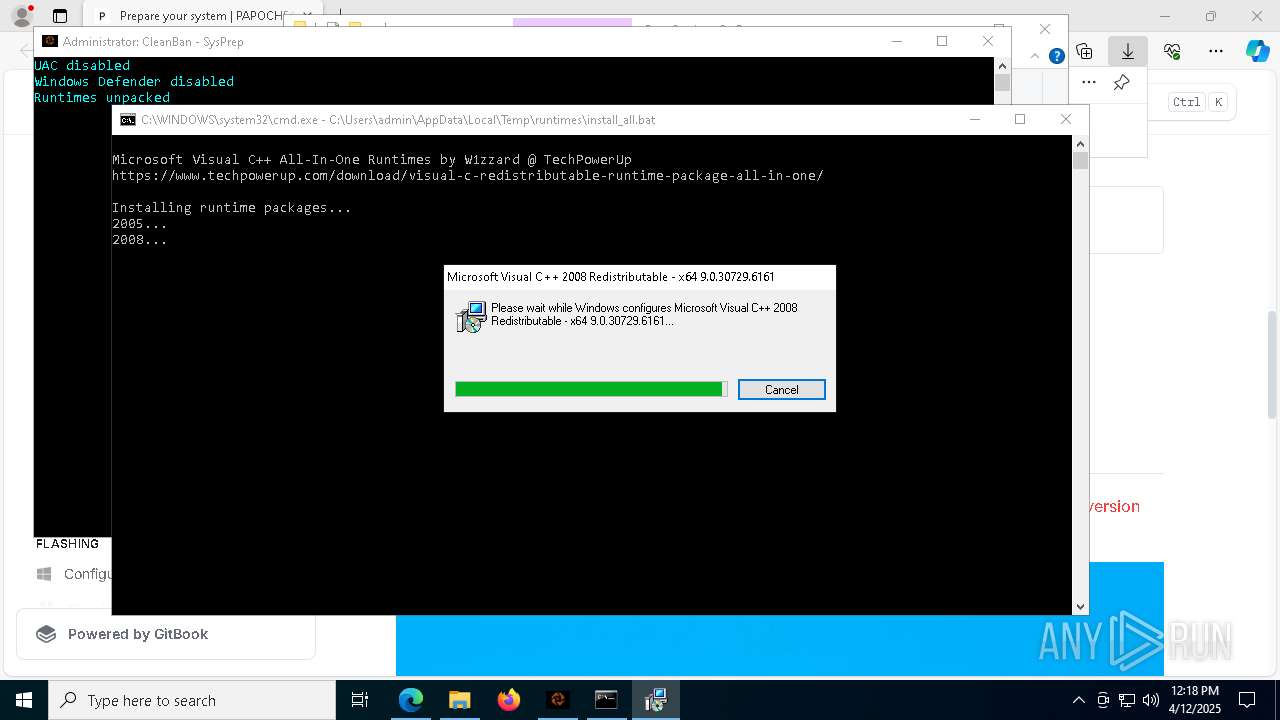
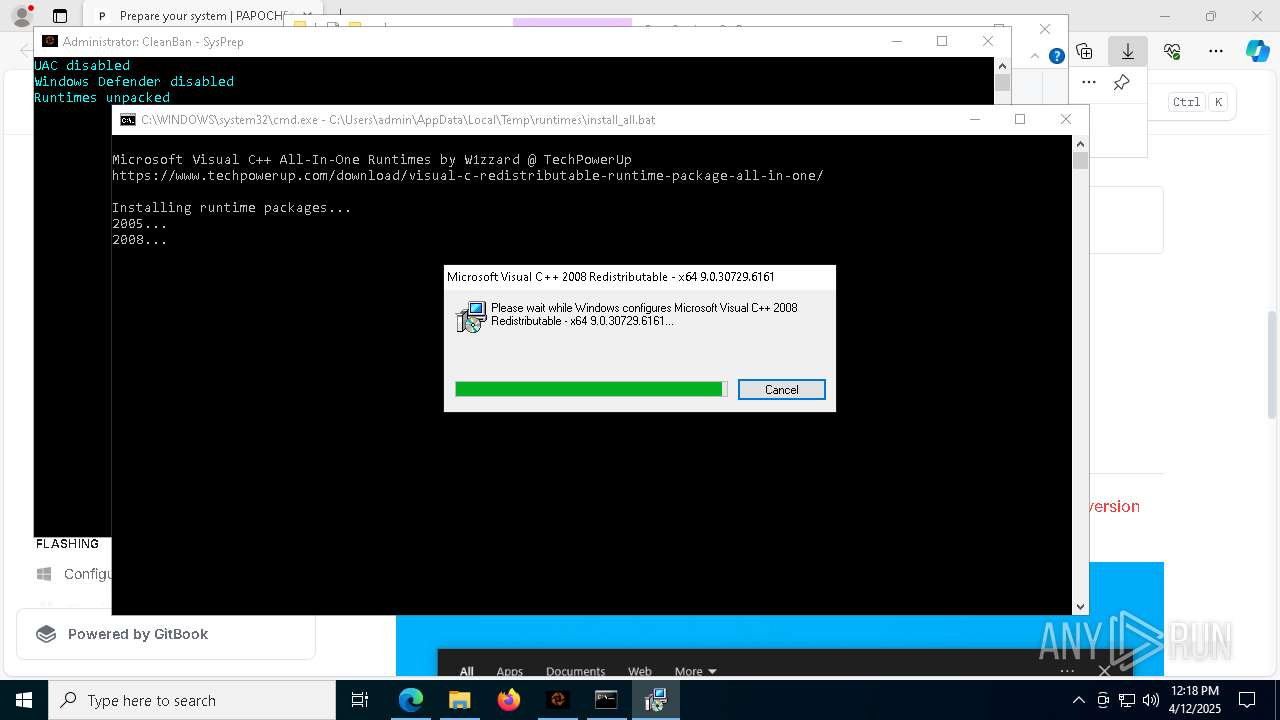
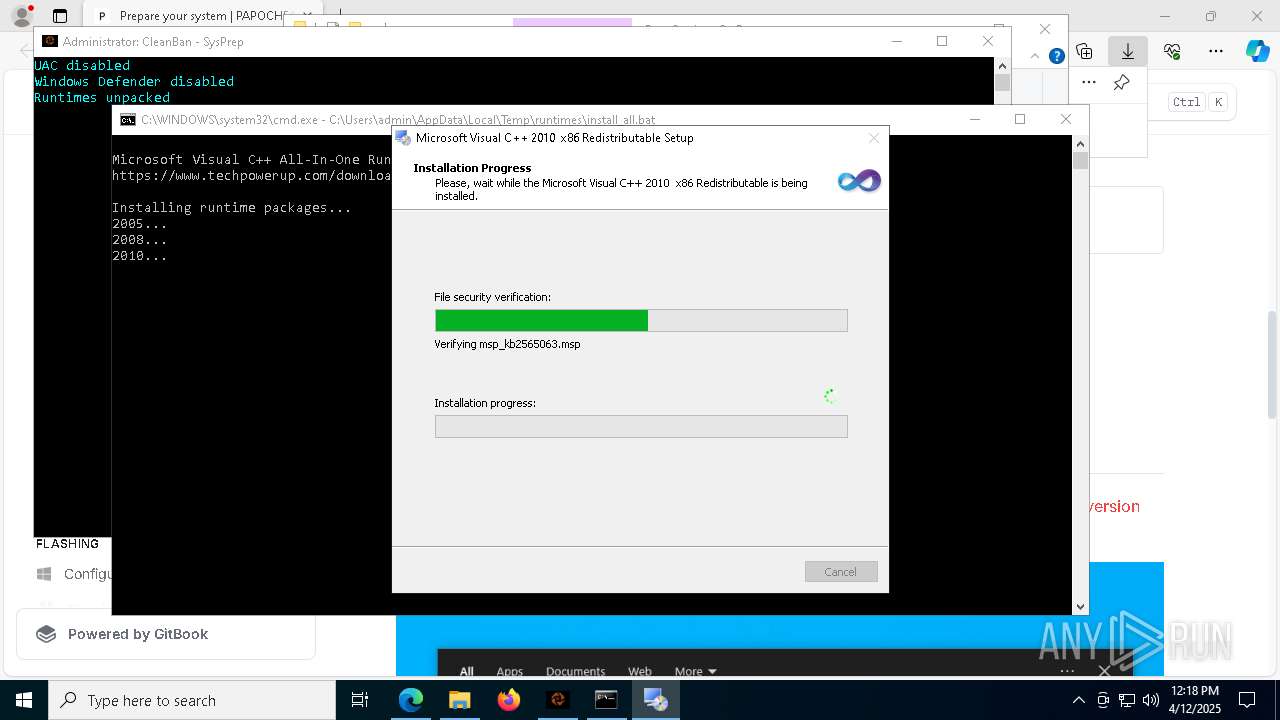
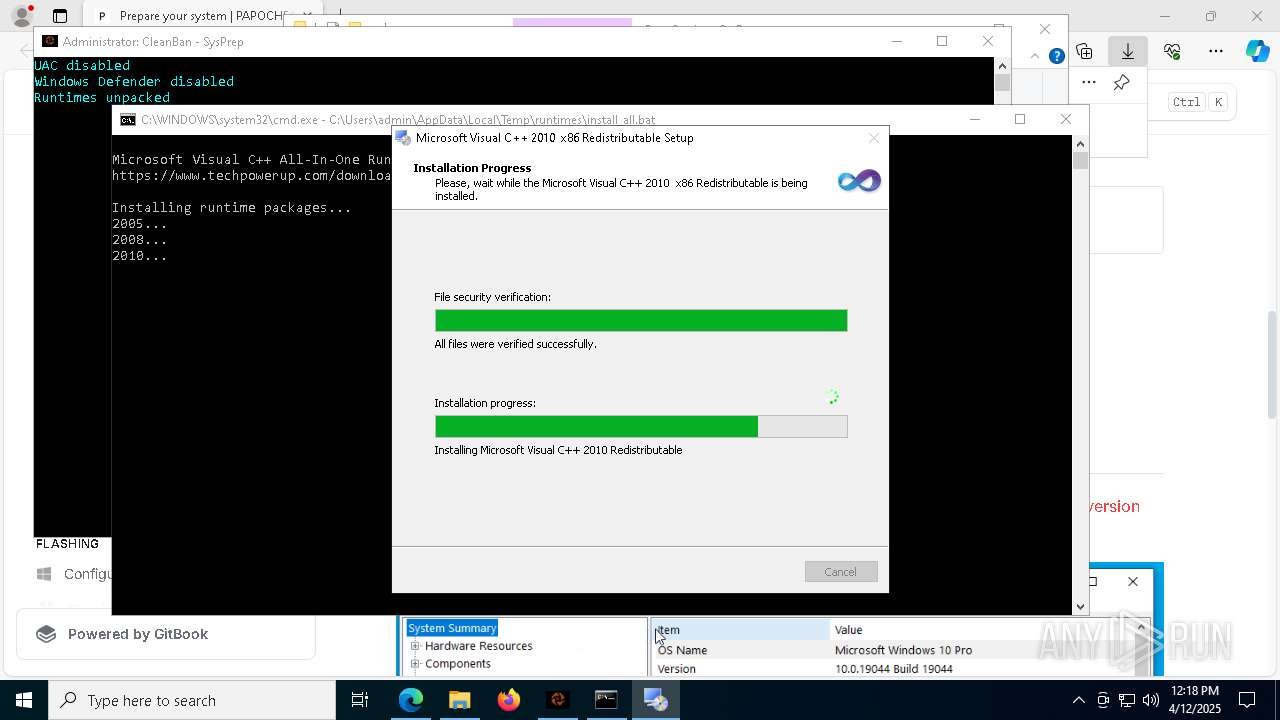
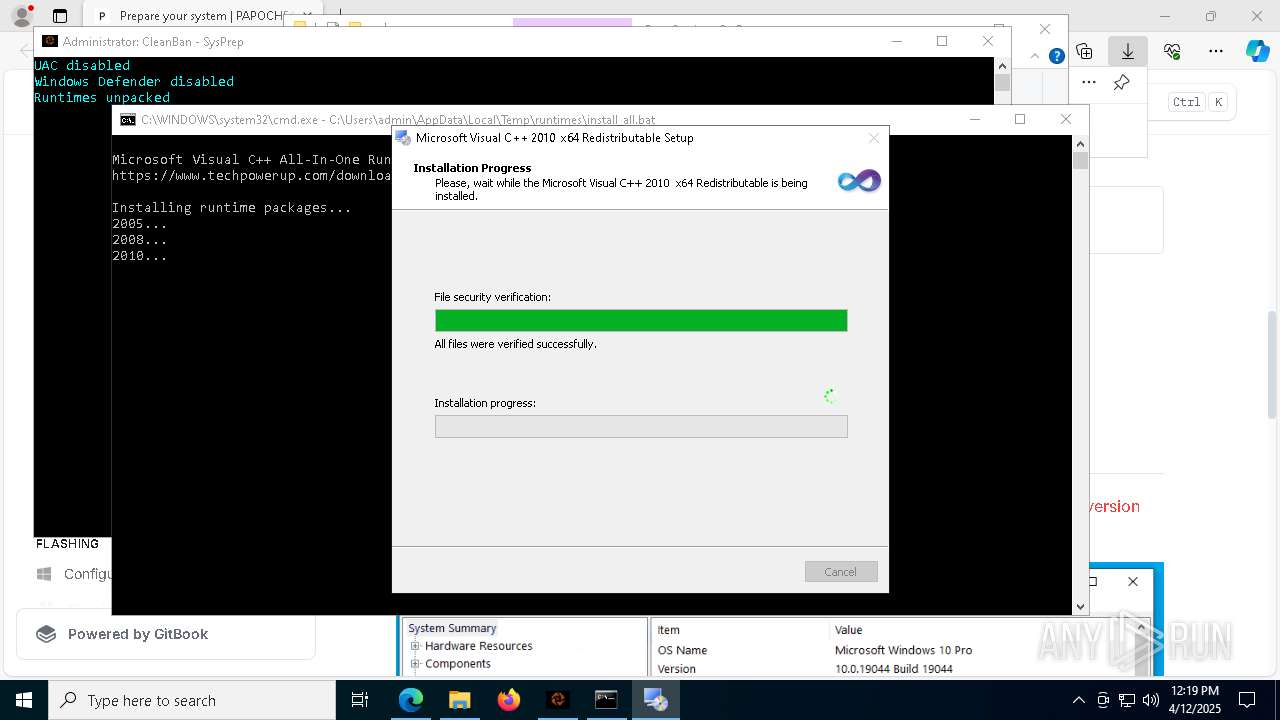
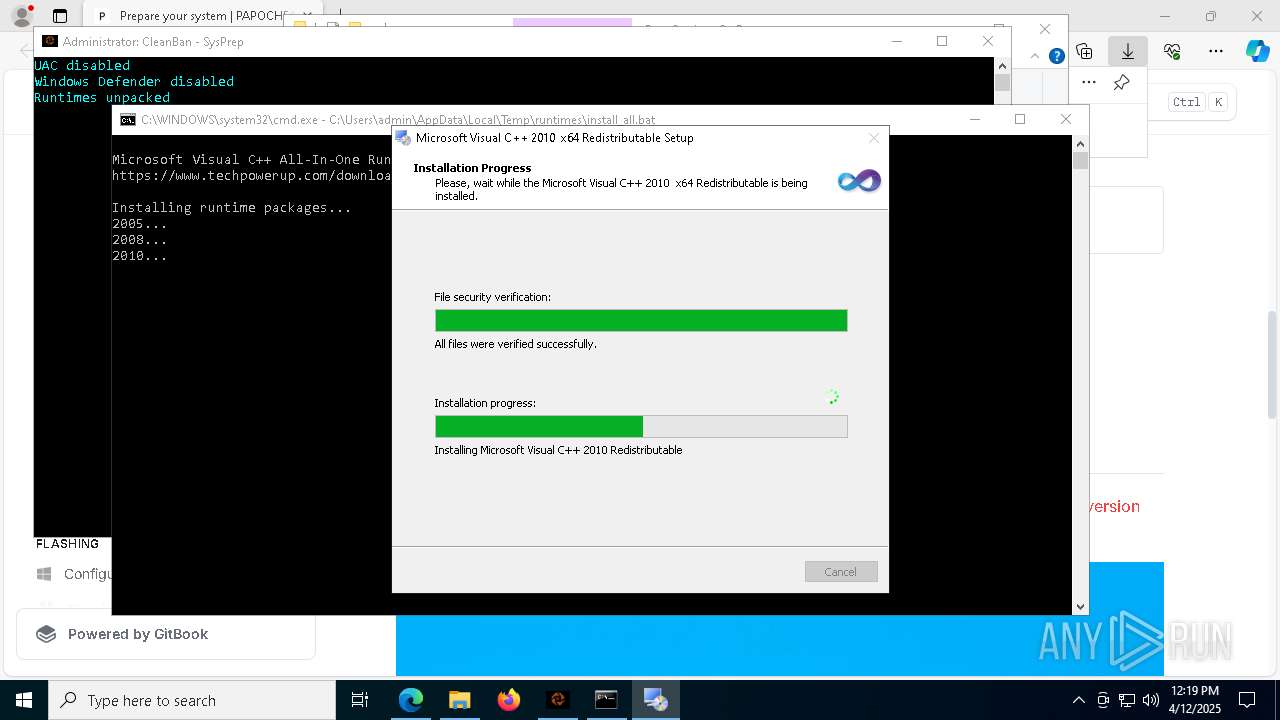
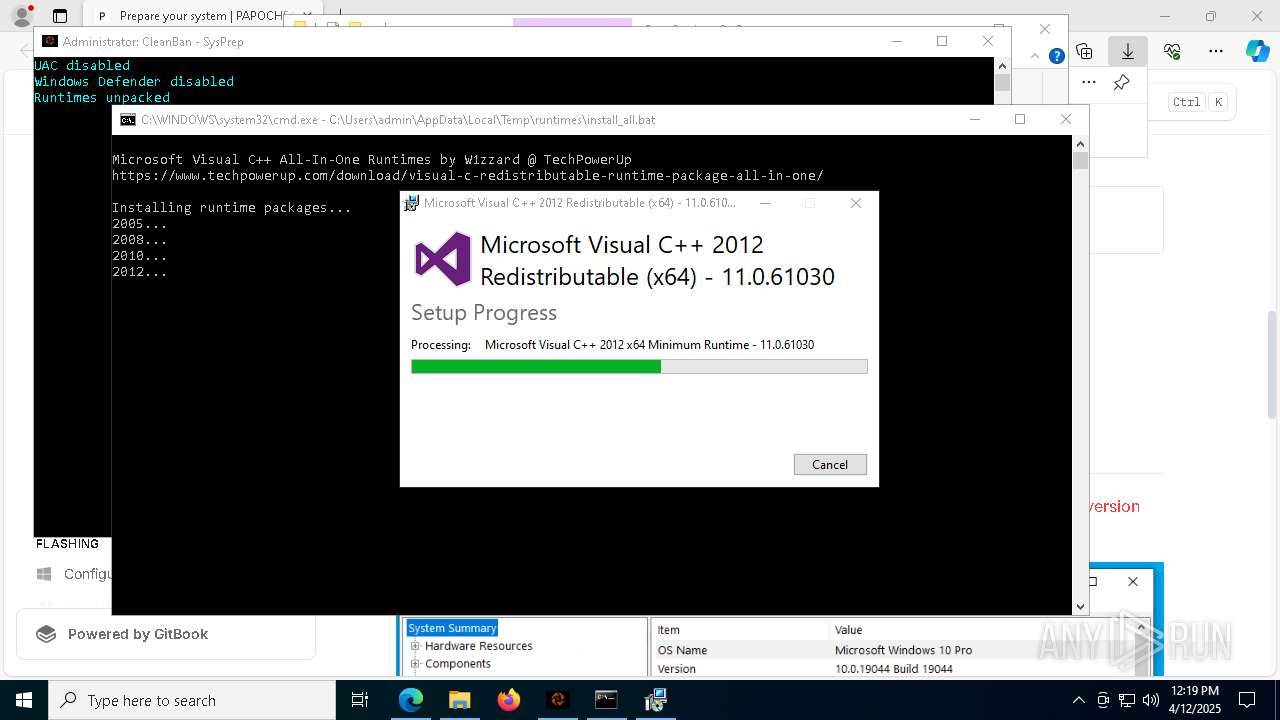
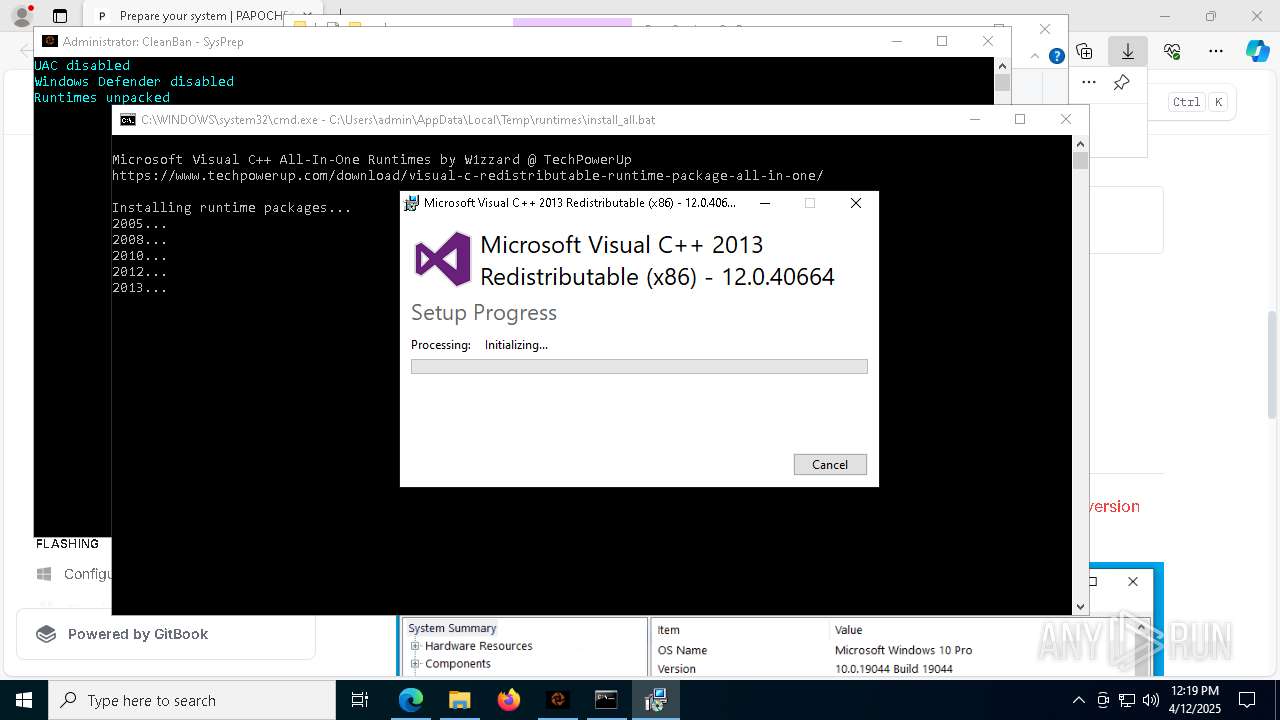
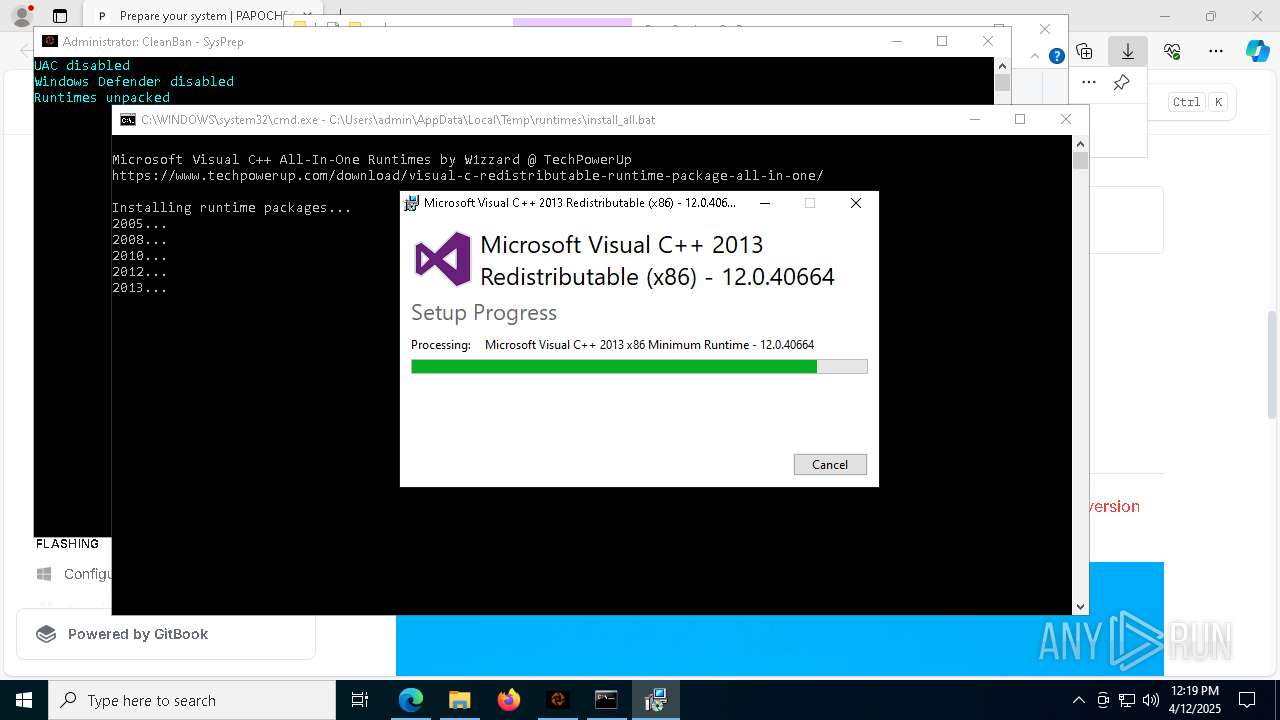
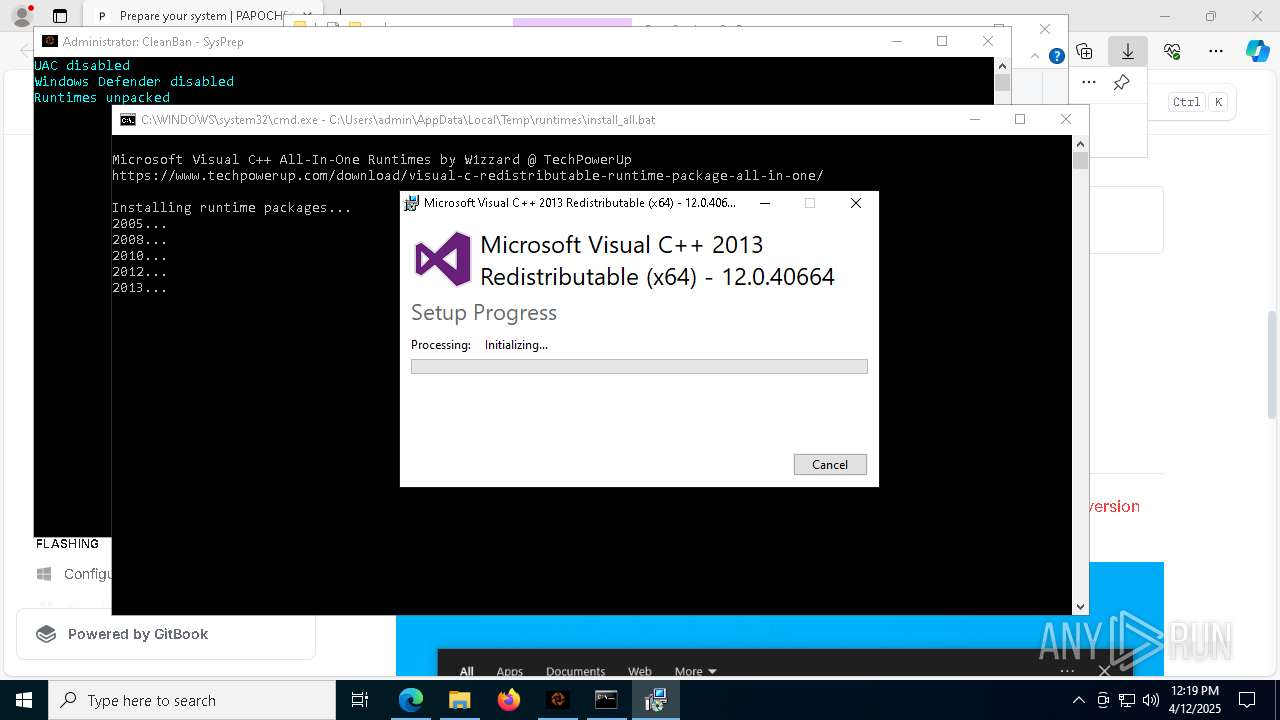
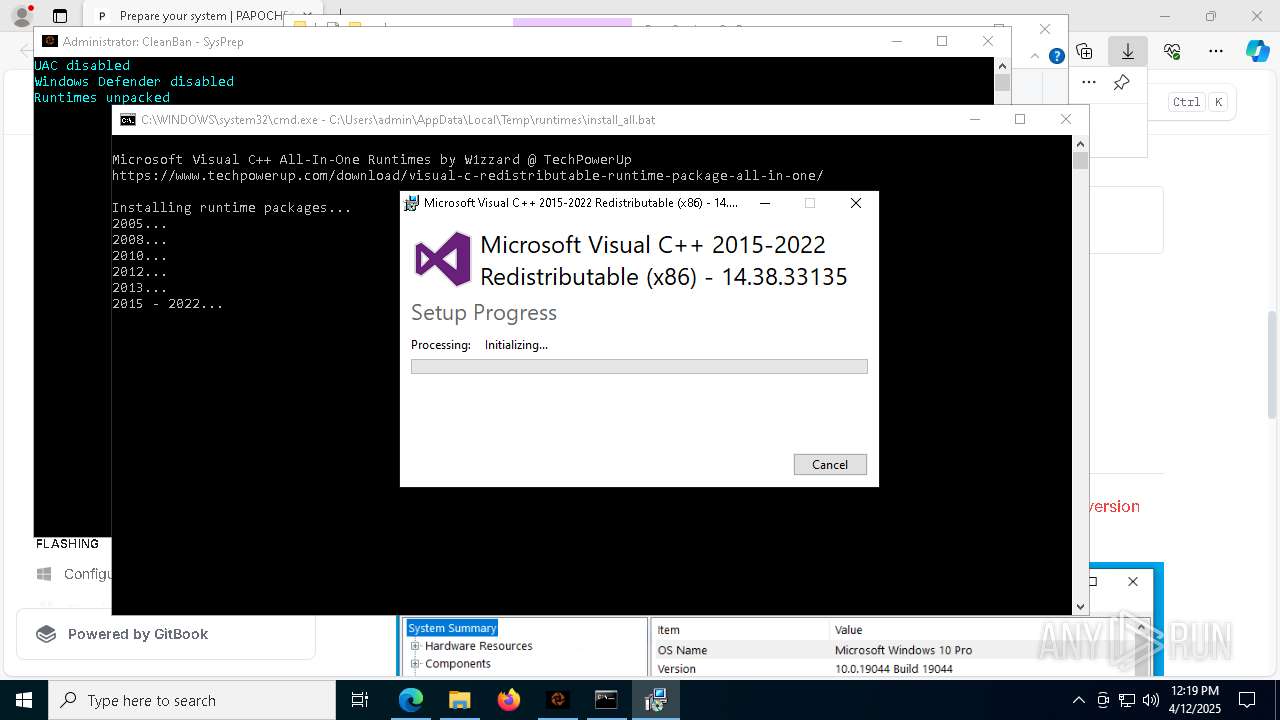
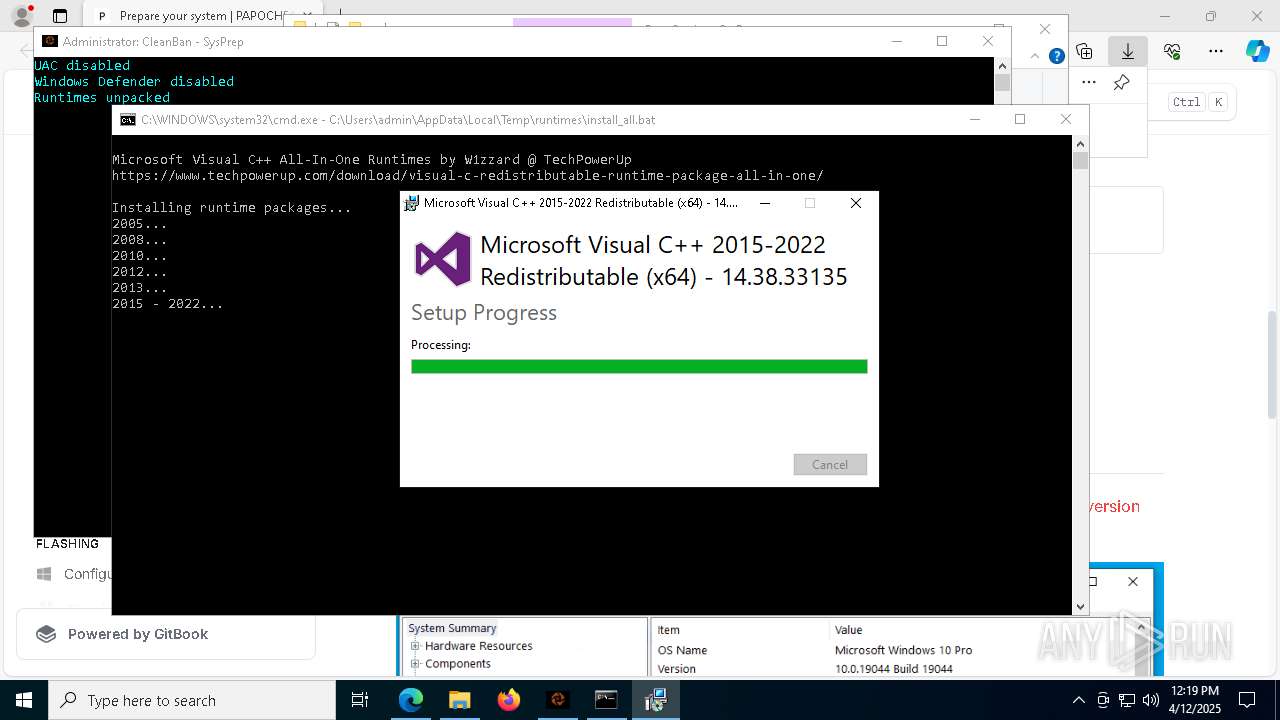
Executing a file with an untrusted certificate
- vcredist2005_x86.exe (PID: 1280)
- vcredist2005_x64.exe (PID: 2284)
- vcredist2008_x86.exe (PID: 8100)
- install.exe (PID: 6240)
- vcredist2008_x64.exe (PID: 3176)
- install.exe (PID: 2100)
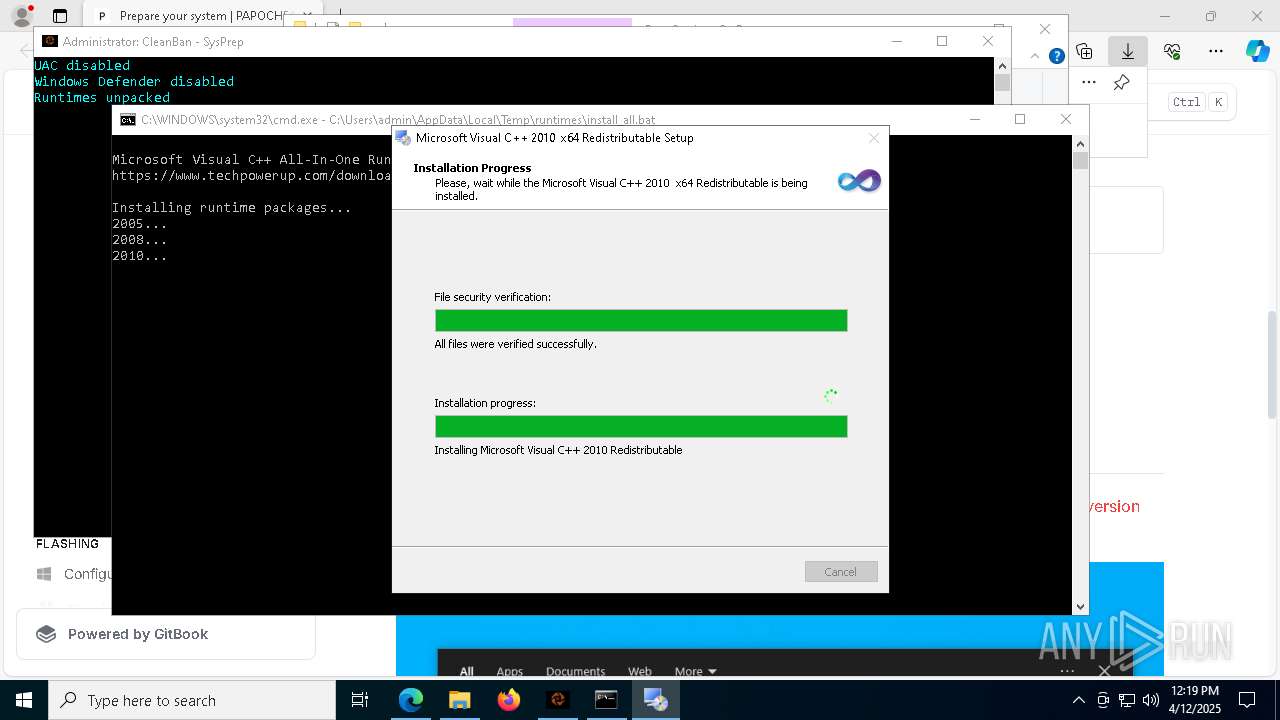
- vcredist2010_x86.exe (PID: 2852)
- Setup.exe (PID: 6436)
- vcredist2010_x64.exe (PID: 6824)
- Setup.exe (PID: 1328)
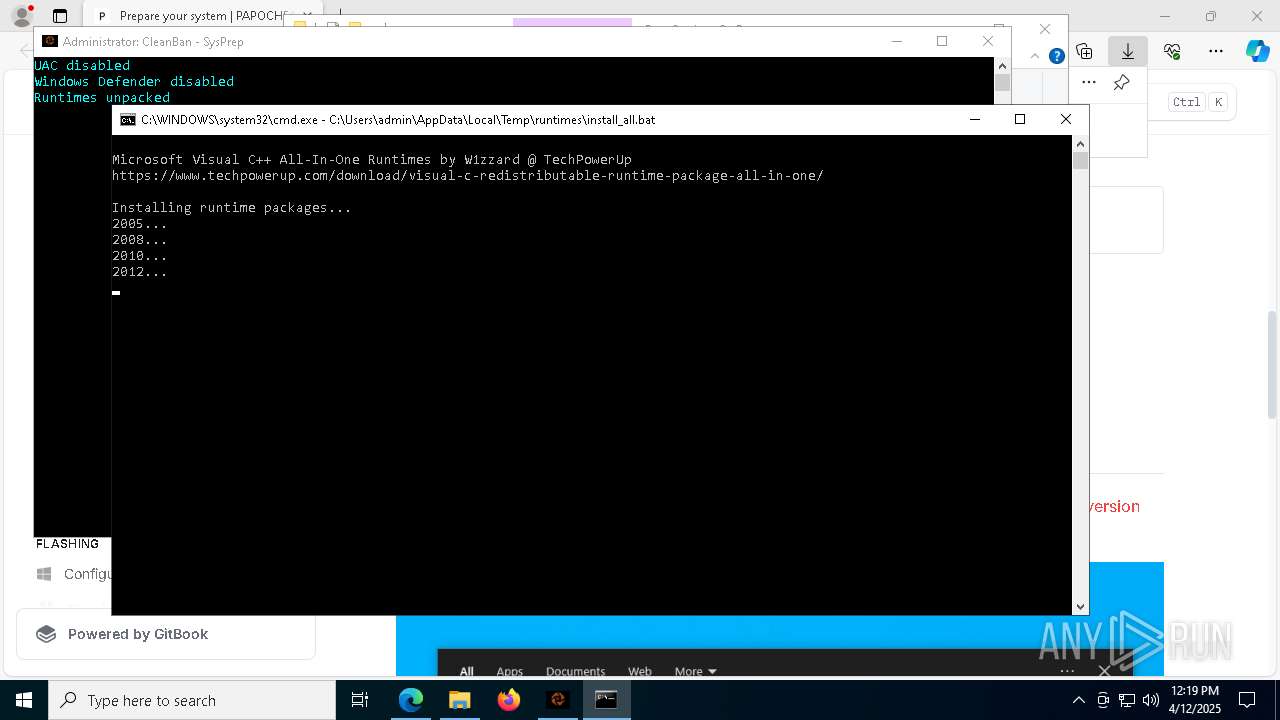
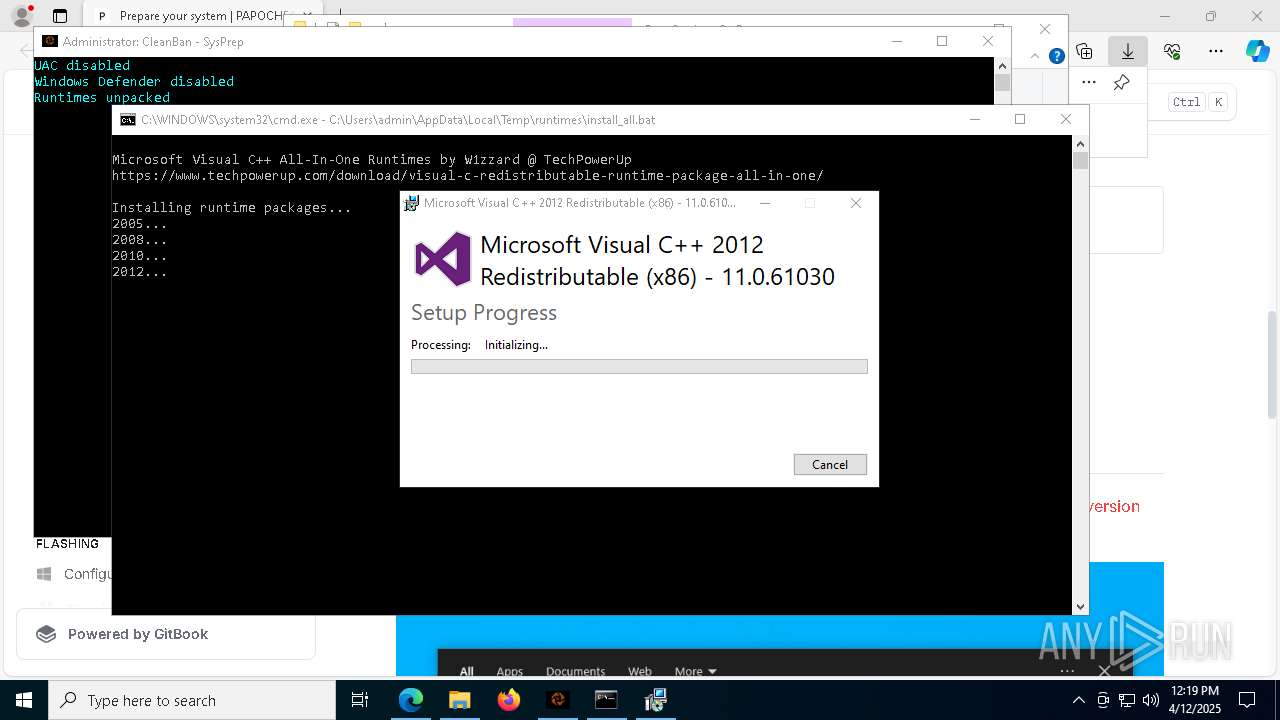
- vcredist2012_x86.exe (PID: 5232)
- vcredist2012_x86.exe (PID: 4308)
- vcredist2012_x64.exe (PID: 6740)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x86.exe (PID: 2772)
- vcredist2013_x64.exe (PID: 5936)
- vcredist2013_x64.exe (PID: 6620)
Changes the autorun value in the registry
- vcredist2005_x86.exe (PID: 1280)
- vcredist2005_x64.exe (PID: 2284)
- vcredist2012_x86.exe (PID: 5232)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x64.exe (PID: 5936)
- VC_redist.x86.exe (PID: 5232)
- VC_redist.x64.exe (PID: 7872)
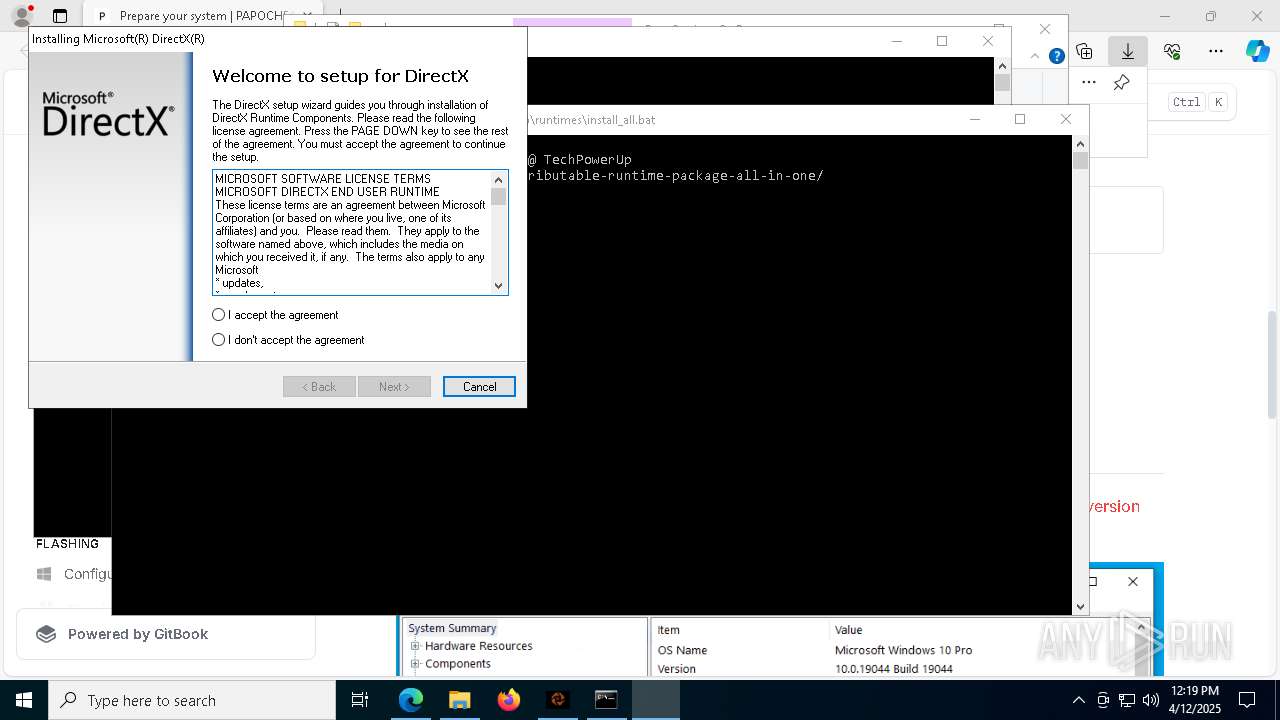
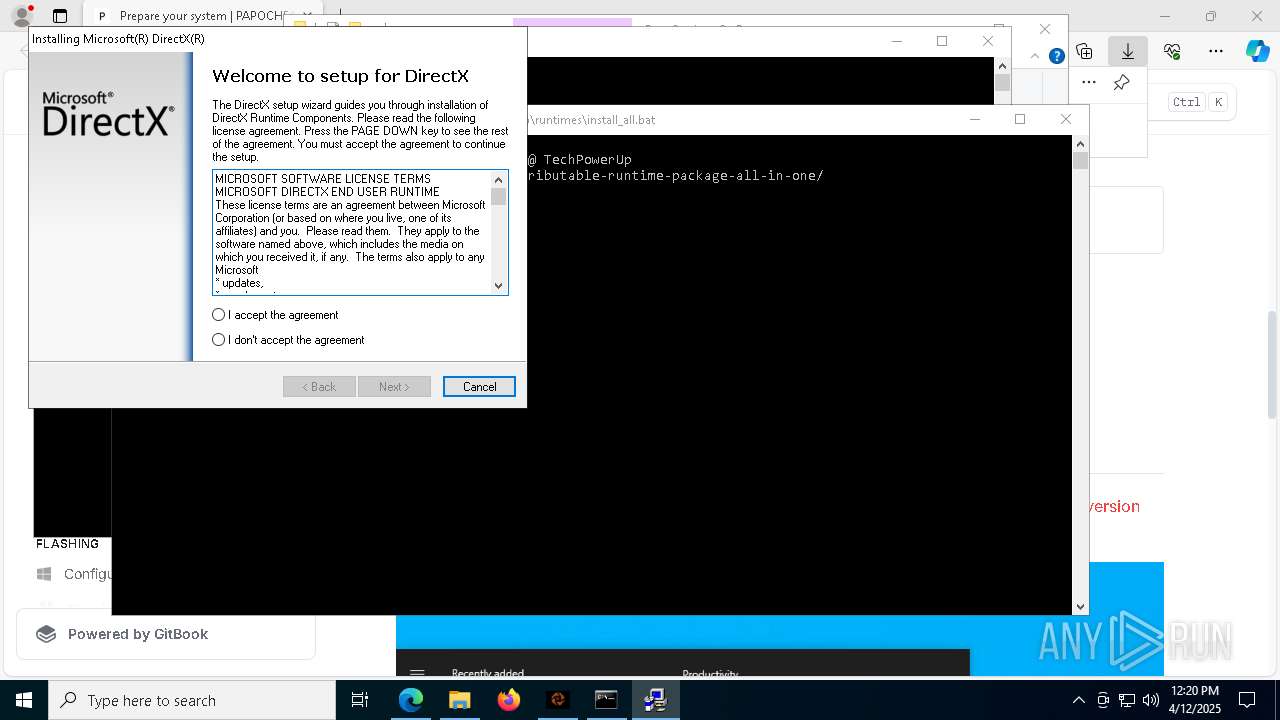
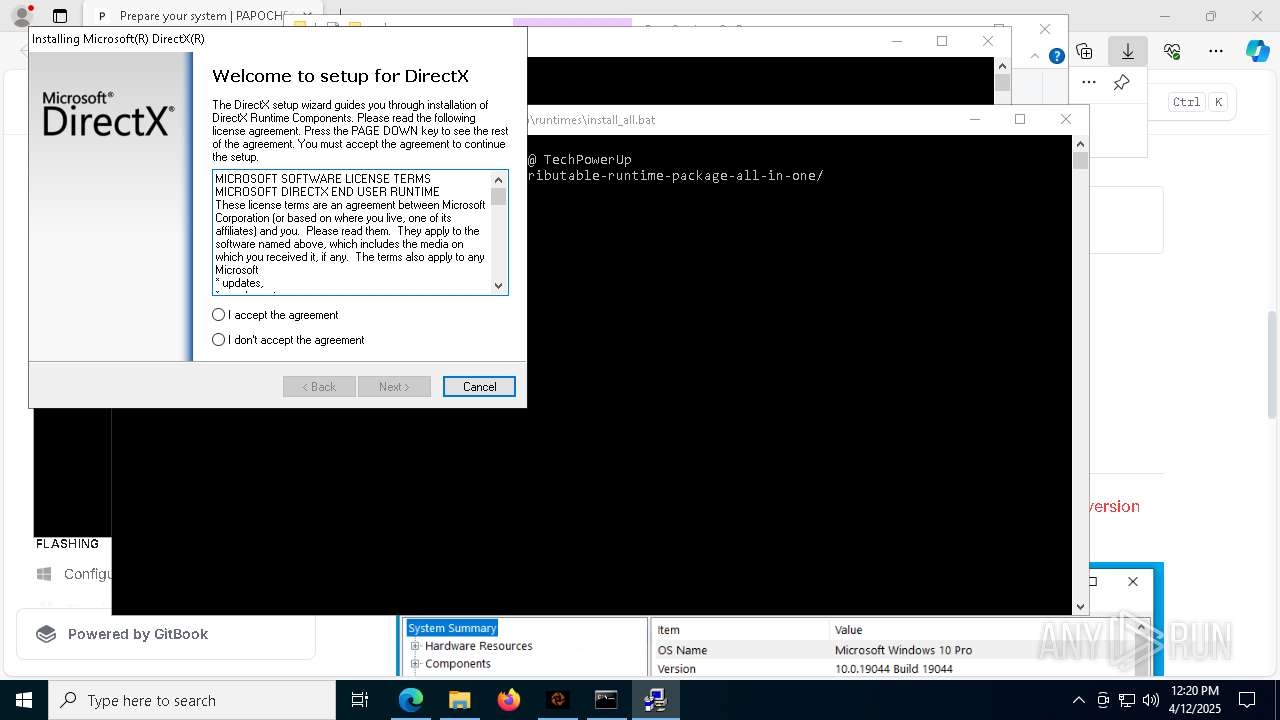
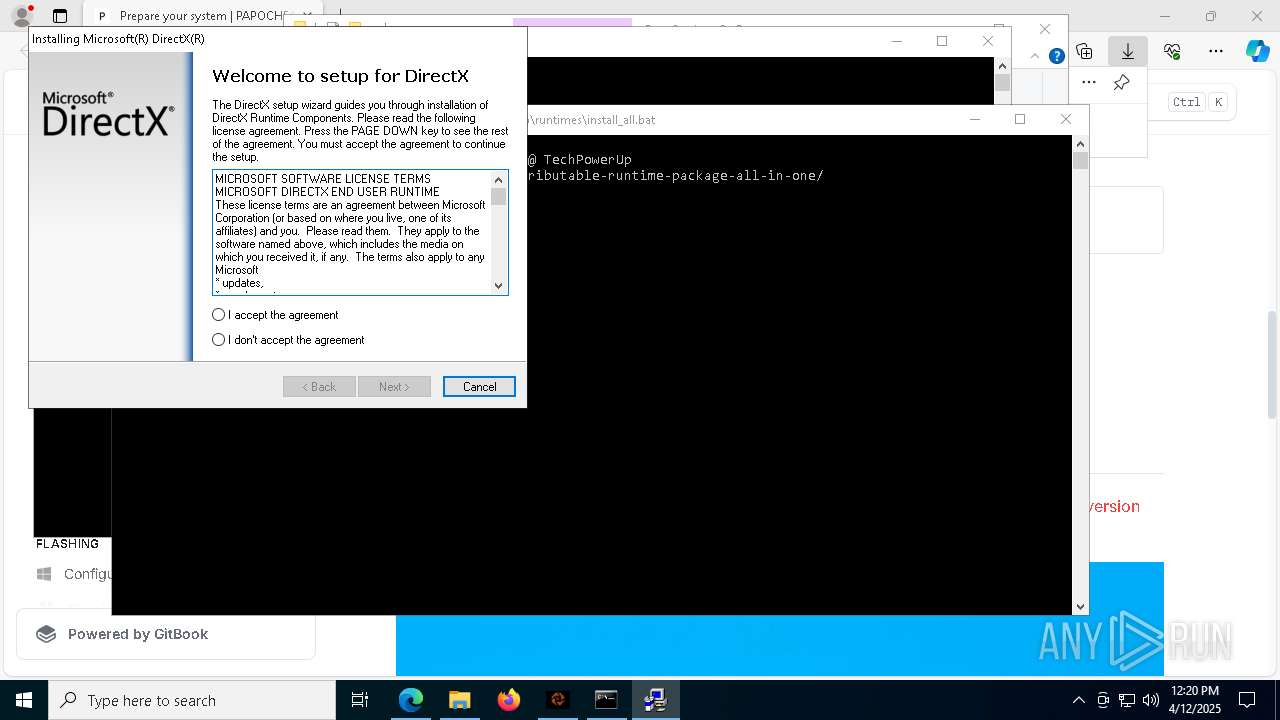
- dxwebsetup.exe (PID: 6108)
SUSPICIOUS
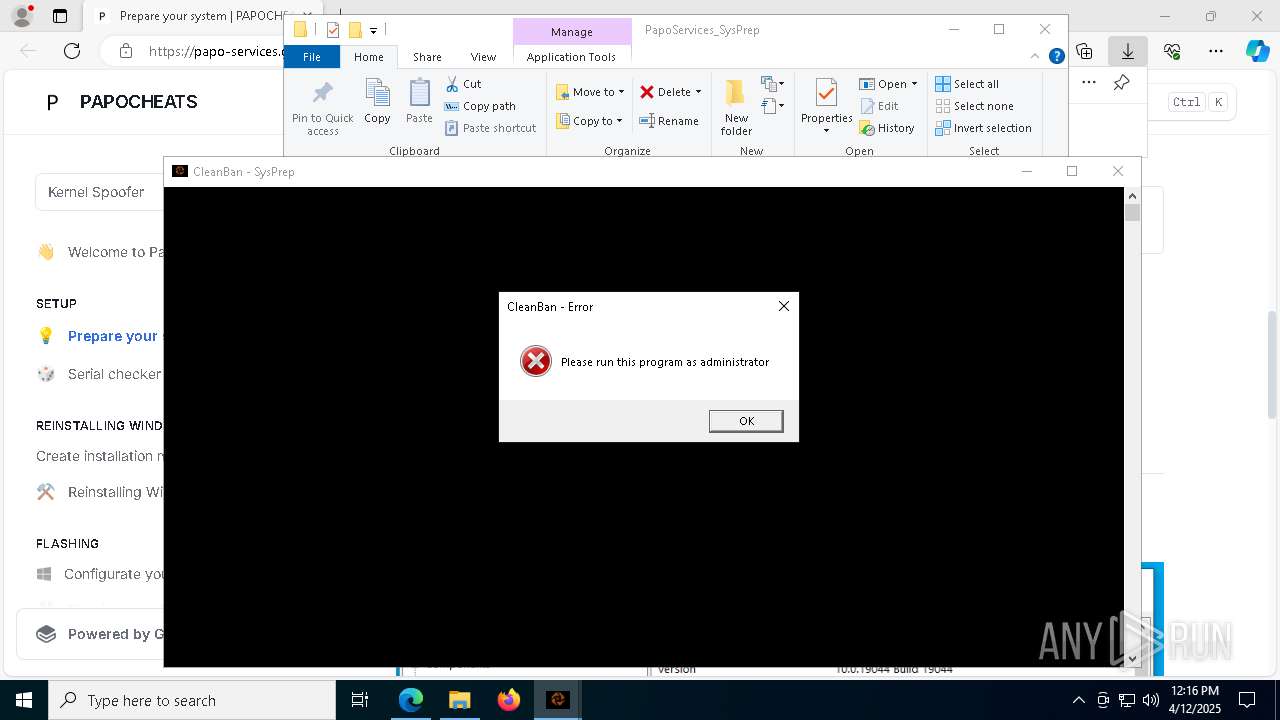
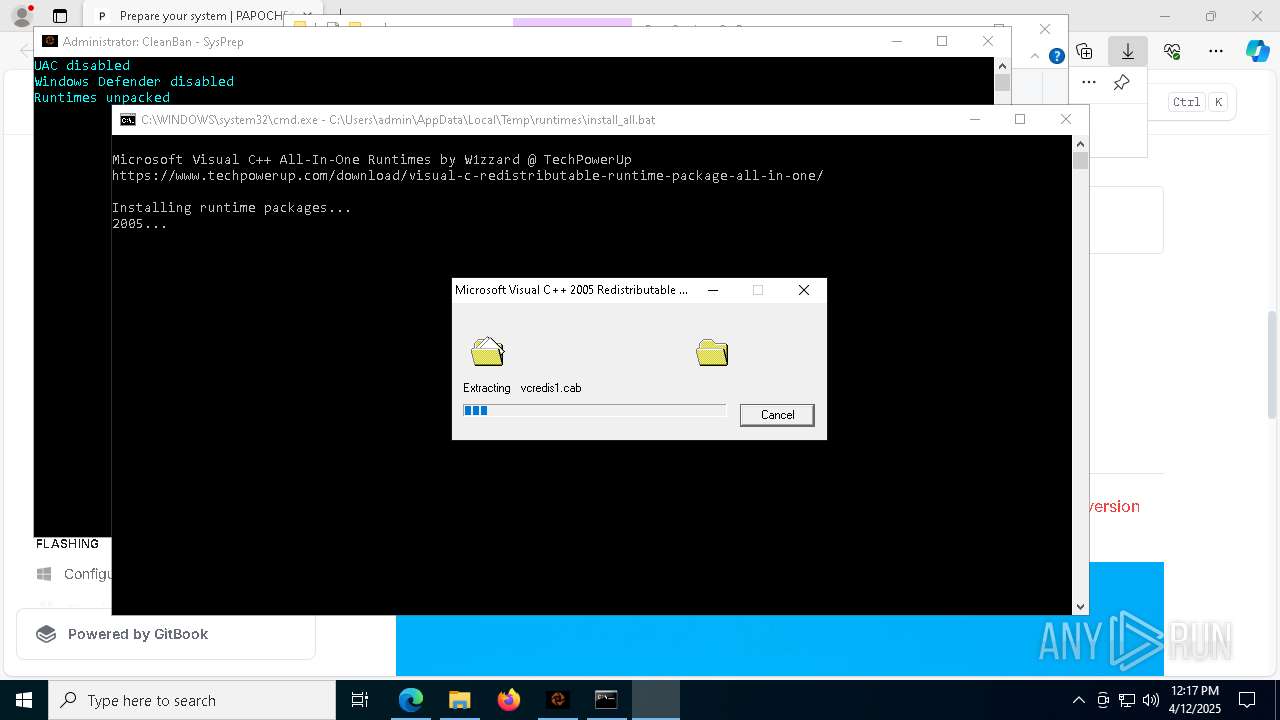
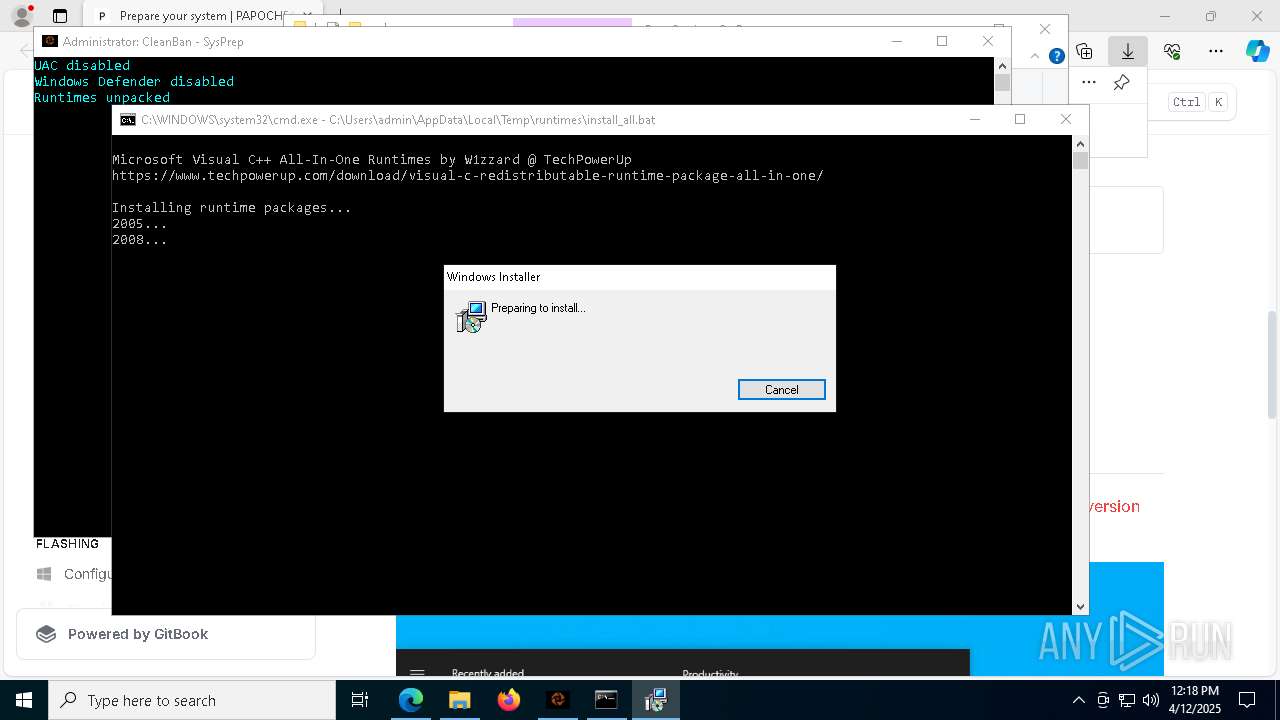
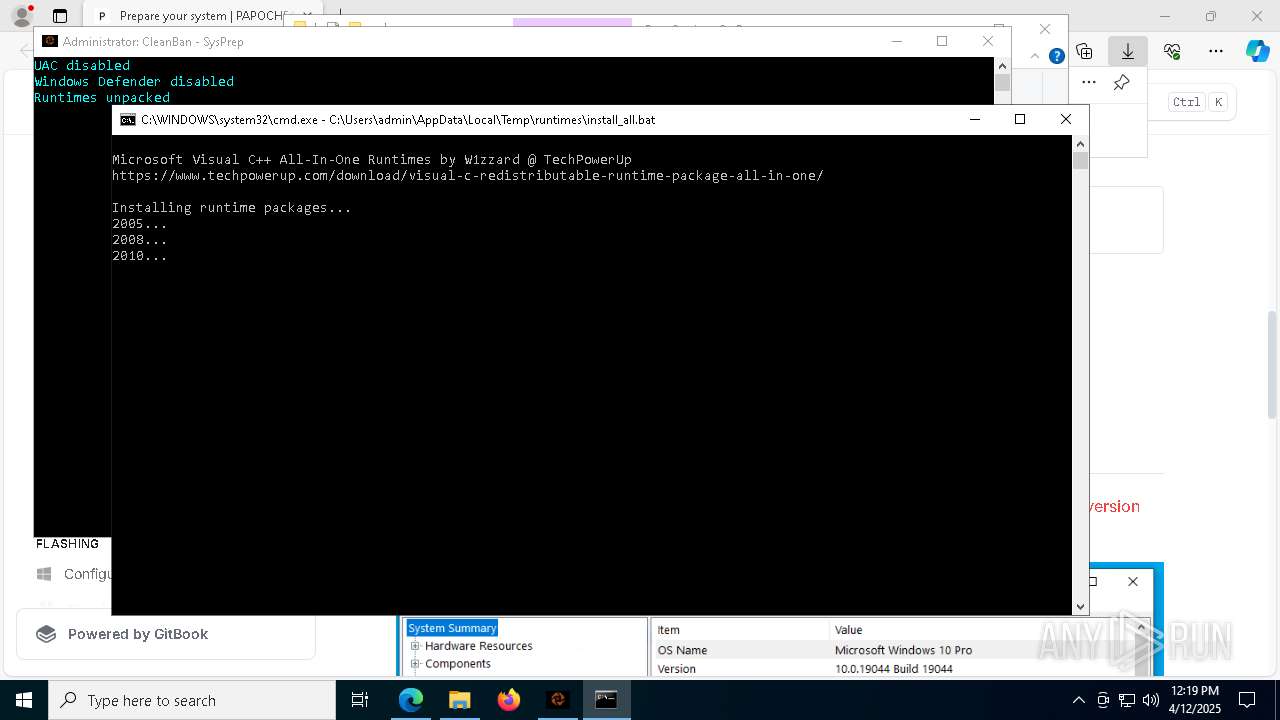
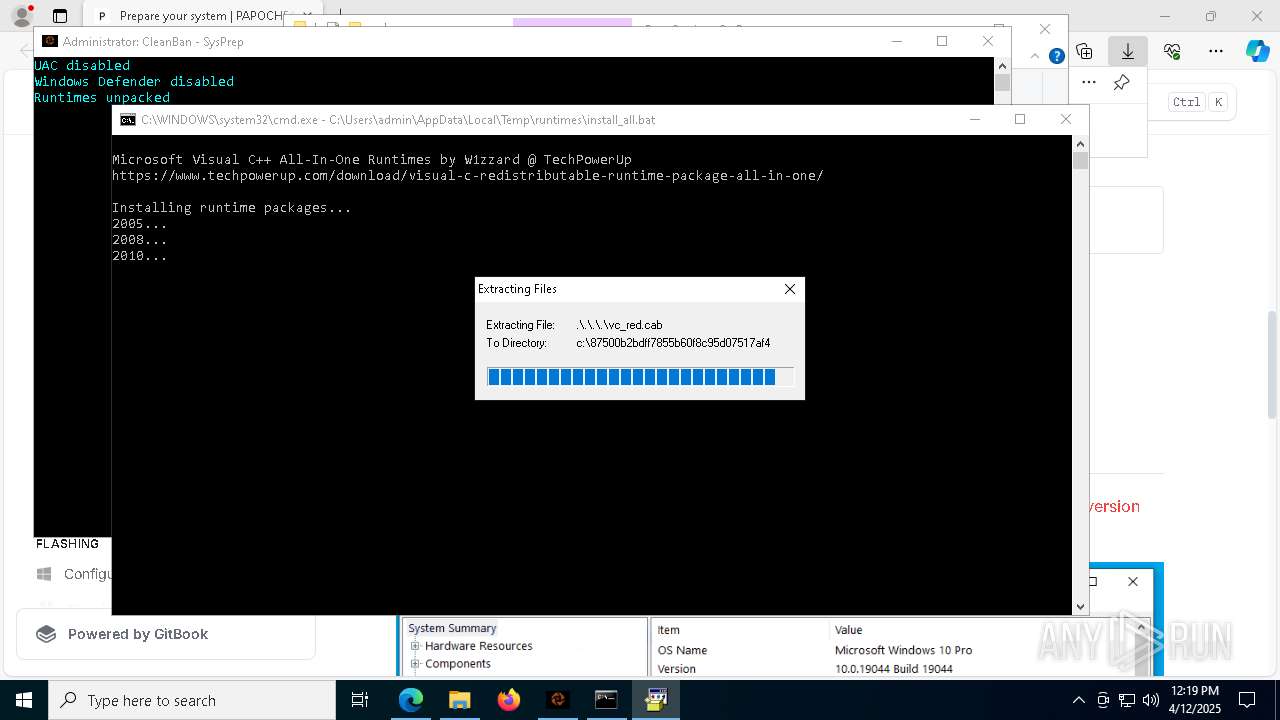
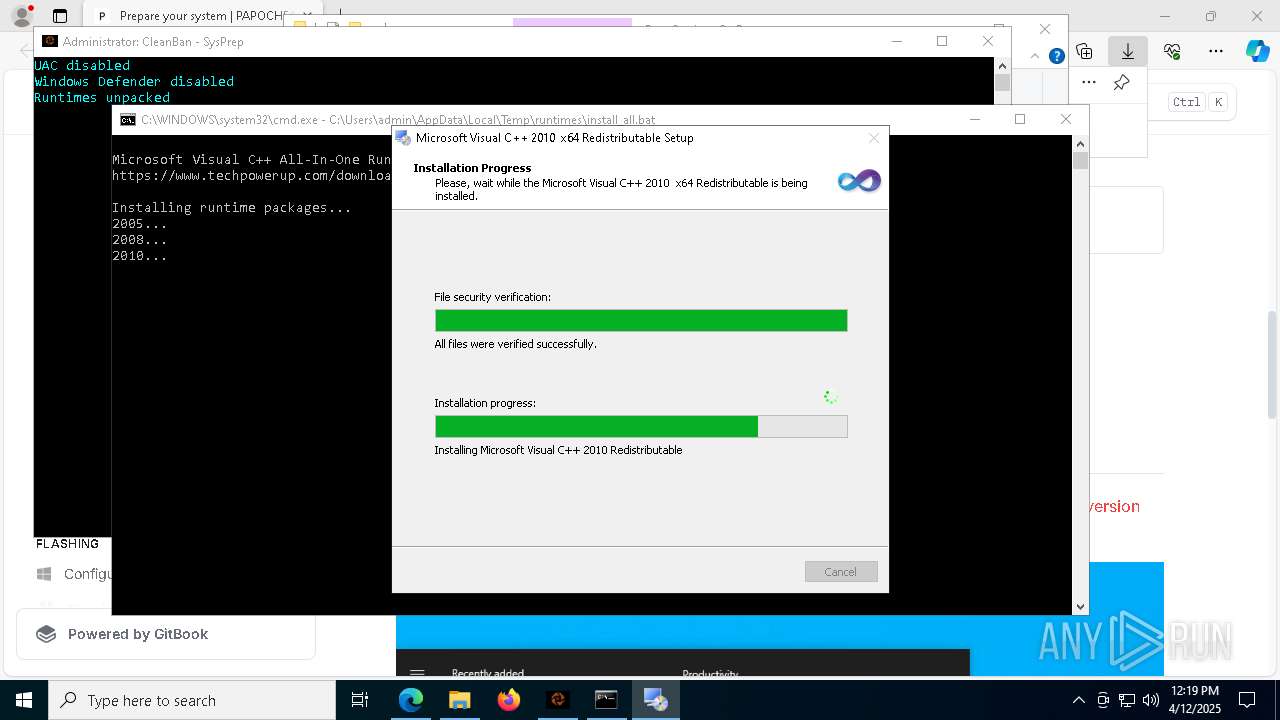
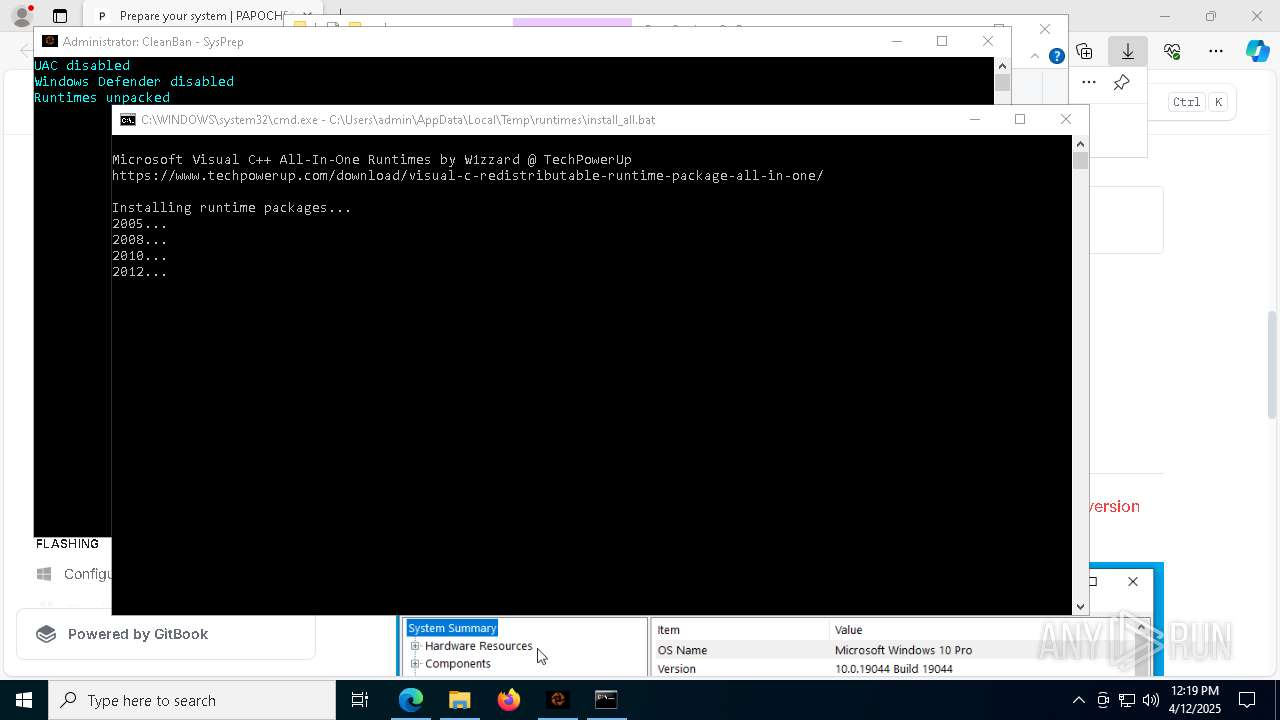
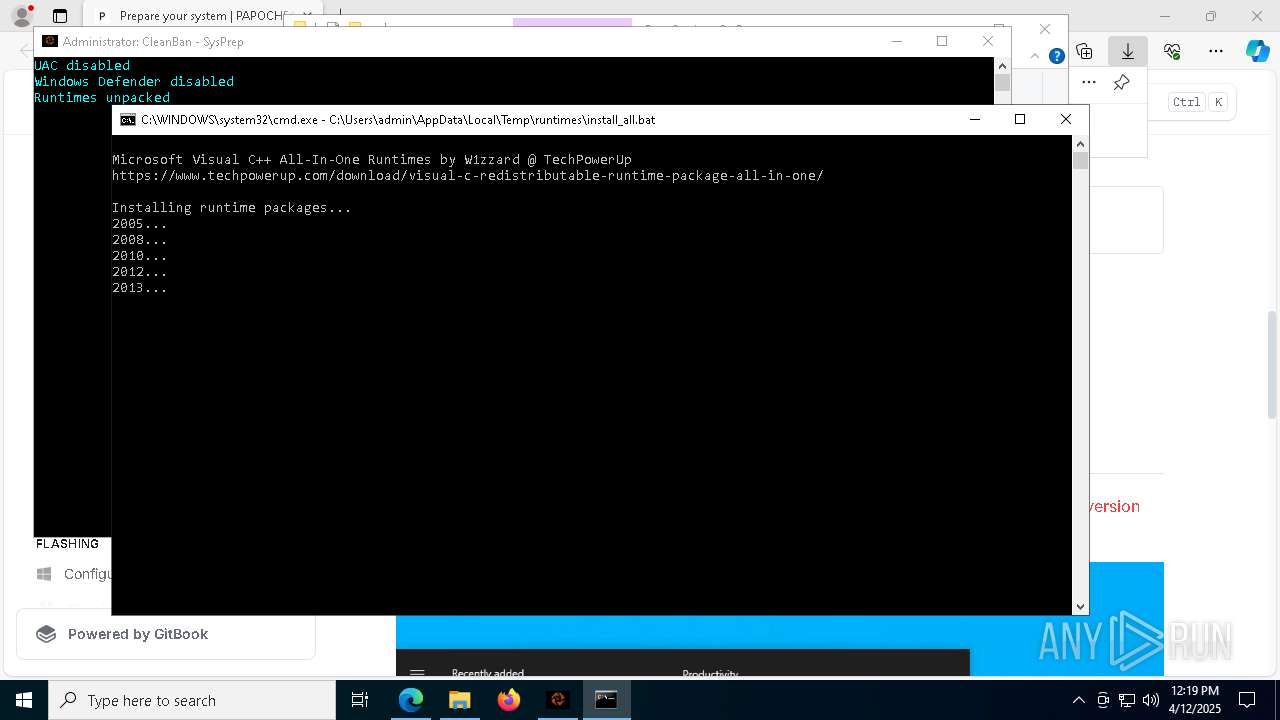
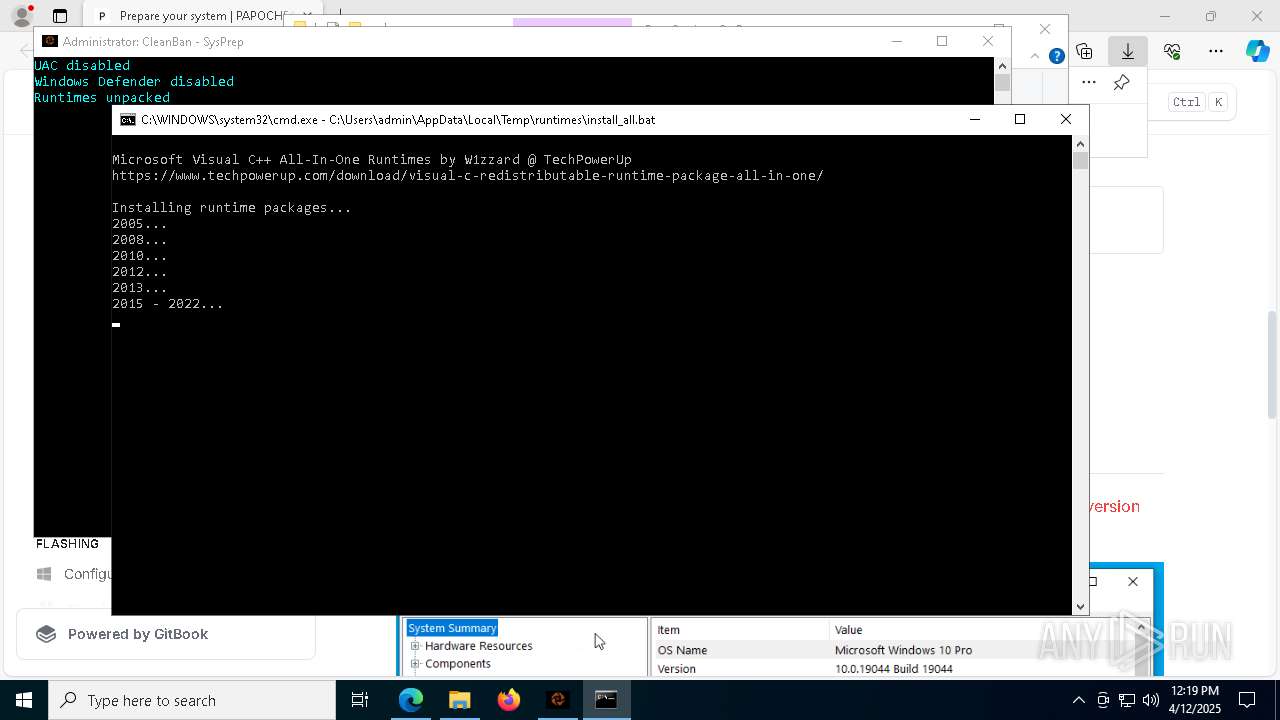
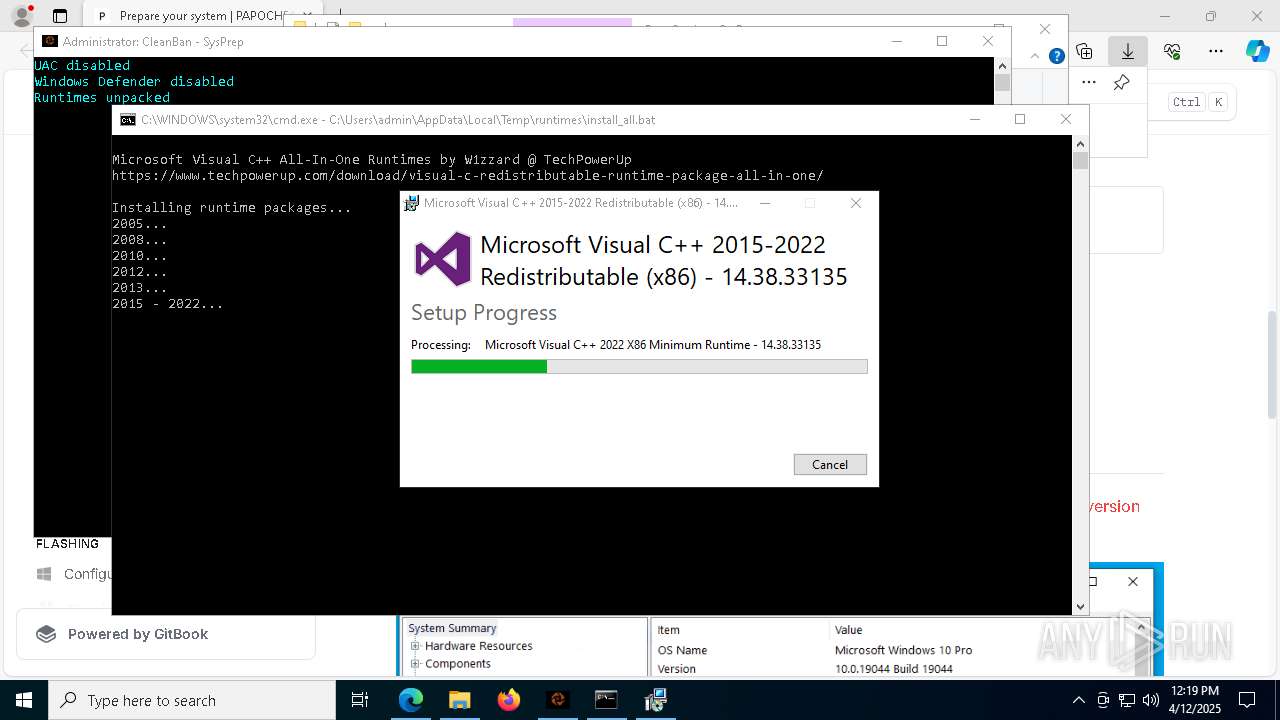
Starts CMD.EXE for commands execution
- PapoServices_SysPrep.exe (PID: 5960)
- cmd.exe (PID: 632)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8096)
The executable file from the user directory is run by the CMD process
- disable-defender.exe (PID: 5608)
- vcredist2005_x86.exe (PID: 1280)
- vcredist2005_x64.exe (PID: 2284)
- vcredist2008_x86.exe (PID: 8100)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2010_x86.exe (PID: 2852)
- vcredist2010_x64.exe (PID: 6824)
- vcredist2012_x86.exe (PID: 5232)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x64.exe (PID: 5936)
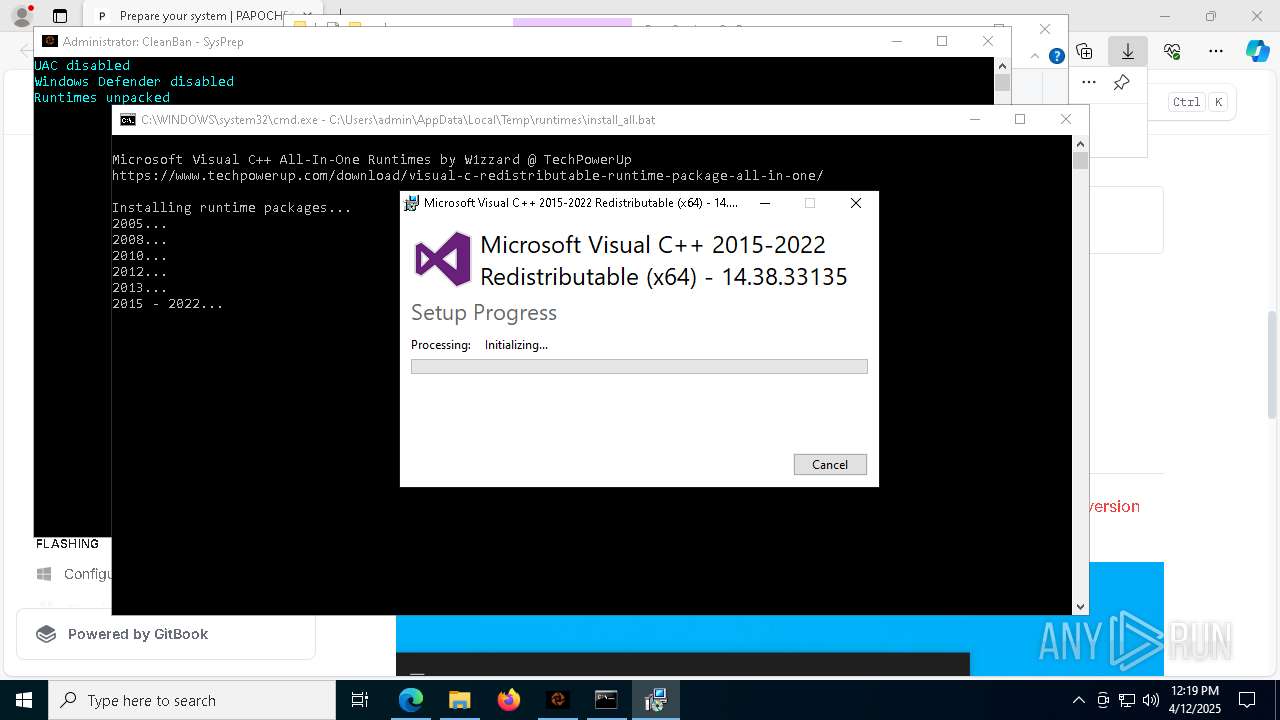
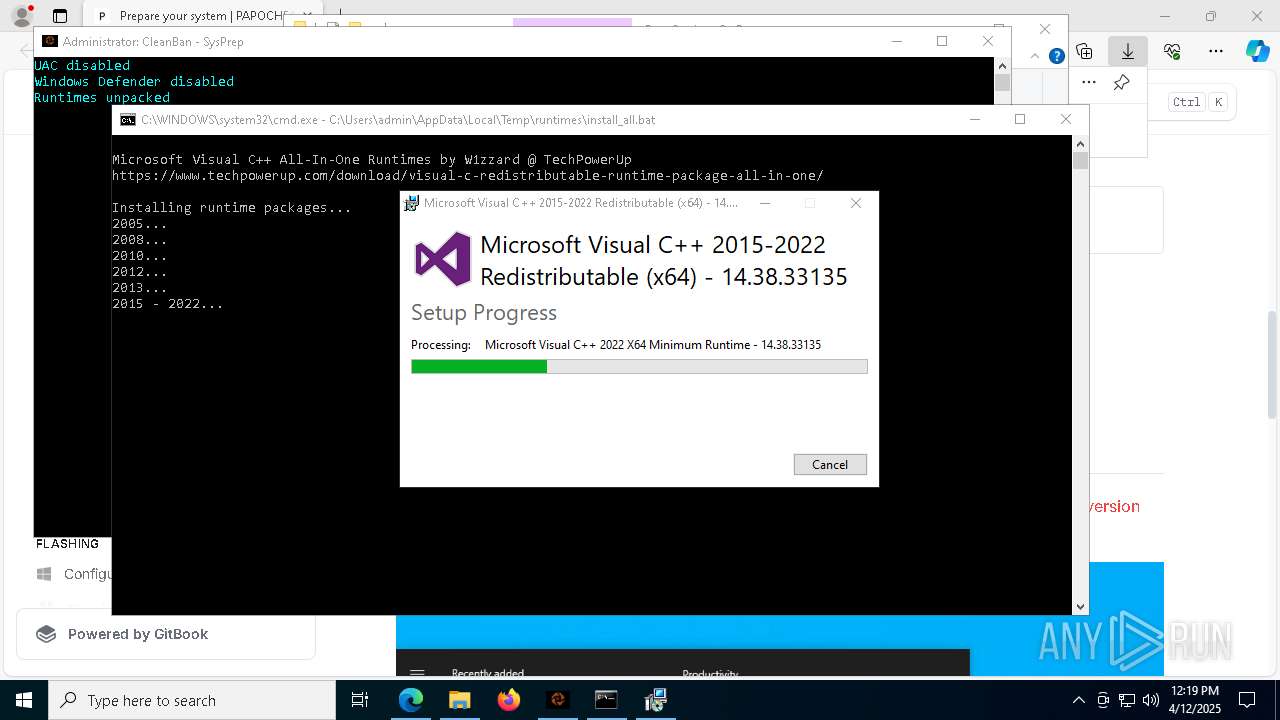
- vcredist2015_2017_2019_2022_x86.exe (PID: 5744)
- vcredist2015_2017_2019_2022_x64.exe (PID: 5364)
- dxwebsetup.exe (PID: 6108)
Found strings related to reading or modifying Windows Defender settings
- PapoServices_SysPrep.exe (PID: 5960)
Executable content was dropped or overwritten
- PapoServices_SysPrep.exe (PID: 5960)
- tar.exe (PID: 2240)
- vcredist2005_x86.exe (PID: 1280)
- TiWorker.exe (PID: 8020)
- vcredist2005_x64.exe (PID: 2284)
- vcredist2008_x86.exe (PID: 8100)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2010_x86.exe (PID: 2852)
- vcredist2010_x64.exe (PID: 6824)
- vcredist2012_x86.exe (PID: 5232)
- vcredist2012_x86.exe (PID: 4308)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2012_x64.exe (PID: 6740)
- vcredist2013_x86.exe (PID: 2772)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x64.exe (PID: 6620)
- vcredist2013_x64.exe (PID: 5936)
- vcredist2015_2017_2019_2022_x86.exe (PID: 5744)
- VC_redist.x86.exe (PID: 5232)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4844)
- VC_redist.x86.exe (PID: 7728)
- VC_redist.x86.exe (PID: 5344)
- vcredist2015_2017_2019_2022_x64.exe (PID: 5364)
- VC_redist.x64.exe (PID: 7872)
- vcredist2015_2017_2019_2022_x64.exe (PID: 516)
- VC_redist.x64.exe (PID: 660)
- VC_redist.x64.exe (PID: 6736)
- dxwebsetup.exe (PID: 6108)
- dxwsetup.exe (PID: 7660)
Application launched itself
- disable-defender.exe (PID: 5608)
- cmd.exe (PID: 632)
- vcredist2012_x86.exe (PID: 5232)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x64.exe (PID: 5936)
- VC_redist.x86.exe (PID: 6740)
- VC_redist.x86.exe (PID: 7728)
- VC_redist.x64.exe (PID: 5500)
- VC_redist.x64.exe (PID: 660)
Process drops legitimate windows executable
- tar.exe (PID: 2240)
- msiexec.exe (PID: 5280)
- TiWorker.exe (PID: 8020)
- vcredist2008_x86.exe (PID: 8100)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2010_x86.exe (PID: 2852)
- vcredist2010_x64.exe (PID: 6824)
- msiexec.exe (PID: 1628)
- vcredist2012_x86.exe (PID: 4308)
- vcredist2012_x86.exe (PID: 5232)
- msiexec.exe (PID: 4056)
- vcredist2012_x64.exe (PID: 6740)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2013_x86.exe (PID: 2772)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x64.exe (PID: 6620)
- vcredist2013_x64.exe (PID: 5936)
- vcredist2015_2017_2019_2022_x86.exe (PID: 5744)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4844)
- VC_redist.x86.exe (PID: 5232)
- VC_redist.x86.exe (PID: 5344)
- vcredist2015_2017_2019_2022_x64.exe (PID: 5364)
- vcredist2015_2017_2019_2022_x64.exe (PID: 516)
- VC_redist.x64.exe (PID: 7872)
- VC_redist.x64.exe (PID: 6736)
- dxwebsetup.exe (PID: 6108)
- dxwsetup.exe (PID: 7660)
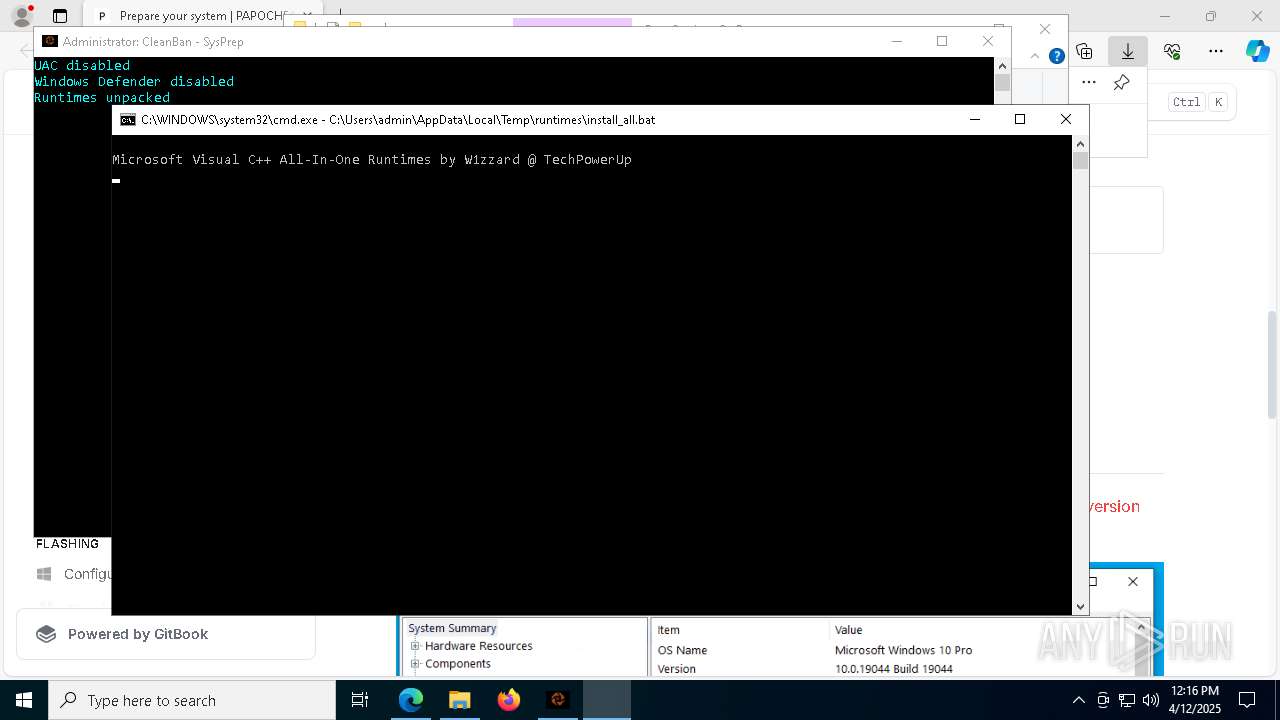
Executing commands from a ".bat" file
- cmd.exe (PID: 632)
- PapoServices_SysPrep.exe (PID: 5960)
Starts a Microsoft application from unusual location
- vcredist2005_x86.exe (PID: 1280)
- vcredist2005_x64.exe (PID: 2284)
- vcredist2008_x86.exe (PID: 8100)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2010_x86.exe (PID: 2852)
- vcredist2010_x64.exe (PID: 6824)
- vcredist2012_x86.exe (PID: 5232)
- vcredist2012_x86.exe (PID: 4308)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2012_x64.exe (PID: 6740)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x86.exe (PID: 2772)
- vcredist2013_x64.exe (PID: 6620)
- vcredist2013_x64.exe (PID: 5936)
- vcredist2015_2017_2019_2022_x86.exe (PID: 5744)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4844)
- VC_redist.x86.exe (PID: 5232)
- vcredist2015_2017_2019_2022_x64.exe (PID: 5364)
- vcredist2015_2017_2019_2022_x64.exe (PID: 516)
- VC_redist.x64.exe (PID: 7872)
- dxwebsetup.exe (PID: 6108)
- dxwsetup.exe (PID: 7660)
Executes as Windows Service
- VSSVC.exe (PID: 1764)
The process drops C-runtime libraries
- msiexec.exe (PID: 5280)
- TiWorker.exe (PID: 8020)
- vcredist2010_x86.exe (PID: 2852)
- msiexec.exe (PID: 1628)
- msiexec.exe (PID: 4056)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5280)
- msiexec.exe (PID: 1628)
- msiexec.exe (PID: 4056)
Creates file in the systems drive root
- vcredist2008_x86.exe (PID: 8100)
- vcredist2010_x86.exe (PID: 2852)
- vcredist2010_x64.exe (PID: 6824)
Reads security settings of Internet Explorer
- Setup.exe (PID: 6436)
- Setup.exe (PID: 1328)
- vcredist2012_x86.exe (PID: 5232)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x64.exe (PID: 5936)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4844)
- VC_redist.x86.exe (PID: 7728)
- vcredist2015_2017_2019_2022_x64.exe (PID: 516)
- VC_redist.x64.exe (PID: 660)
Searches for installed software
- vcredist2012_x86.exe (PID: 4308)
- vcredist2012_x86.exe (PID: 5232)
- vcredist2012_x64.exe (PID: 6740)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2013_x86.exe (PID: 2772)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x64.exe (PID: 5936)
- vcredist2013_x64.exe (PID: 6620)
- VC_redist.x86.exe (PID: 5232)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4844)
- VC_redist.x86.exe (PID: 5344)
- VC_redist.x86.exe (PID: 7728)
- vcredist2015_2017_2019_2022_x64.exe (PID: 516)
- VC_redist.x64.exe (PID: 7872)
- VC_redist.x64.exe (PID: 660)
- VC_redist.x64.exe (PID: 6736)
Creates a software uninstall entry
- vcredist2012_x86.exe (PID: 5232)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x64.exe (PID: 5936)
- VC_redist.x86.exe (PID: 5232)
- VC_redist.x64.exe (PID: 7872)
Starts itself from another location
- vcredist2015_2017_2019_2022_x86.exe (PID: 4844)
- vcredist2015_2017_2019_2022_x64.exe (PID: 516)
The process checks if it is being run in the virtual environment
- msiexec.exe (PID: 4056)
INFO
Application launched itself
- msedge.exe (PID: 5048)
Checks supported languages
- identity_helper.exe (PID: 4724)
- PapoServices_SysPrep.exe (PID: 1568)
- PapoServices_SysPrep.exe (PID: 5960)
- disable-defender.exe (PID: 5608)
- tar.exe (PID: 2240)
- disable-defender.exe (PID: 4776)
- vcredist2005_x86.exe (PID: 1280)
- msiexec.exe (PID: 5280)
- msiexec.exe (PID: 6072)
- msiexec.exe (PID: 2316)
- vcredist2005_x64.exe (PID: 2284)
- vcredist2008_x86.exe (PID: 8100)
- install.exe (PID: 6240)
- install.exe (PID: 2100)
- vcredist2010_x86.exe (PID: 2852)
- Setup.exe (PID: 6436)
- vcredist2010_x64.exe (PID: 6824)
- Setup.exe (PID: 1328)
- msiexec.exe (PID: 1628)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2012_x86.exe (PID: 5232)
- vcredist2012_x86.exe (PID: 4308)
- msiexec.exe (PID: 4056)
- vcredist2012_x64.exe (PID: 6740)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x86.exe (PID: 2772)
- vcredist2013_x64.exe (PID: 5936)
- vcredist2013_x64.exe (PID: 6620)
- vcredist2015_2017_2019_2022_x86.exe (PID: 5744)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4844)
- VC_redist.x86.exe (PID: 5232)
- VC_redist.x86.exe (PID: 6740)
- VC_redist.x86.exe (PID: 7728)
- VC_redist.x86.exe (PID: 5344)
- vcredist2015_2017_2019_2022_x64.exe (PID: 5364)
- vcredist2015_2017_2019_2022_x64.exe (PID: 516)
- VC_redist.x64.exe (PID: 7872)
- VC_redist.x64.exe (PID: 5500)
- VC_redist.x64.exe (PID: 660)
- VC_redist.x64.exe (PID: 6736)
- dxwebsetup.exe (PID: 6108)
- dxwsetup.exe (PID: 7660)
Reads the computer name
- identity_helper.exe (PID: 4724)
- PapoServices_SysPrep.exe (PID: 1568)
- disable-defender.exe (PID: 5608)
- disable-defender.exe (PID: 4776)
- vcredist2005_x86.exe (PID: 1280)
- msiexec.exe (PID: 5280)
- msiexec.exe (PID: 6072)
- vcredist2005_x64.exe (PID: 2284)
- msiexec.exe (PID: 2316)
- vcredist2008_x86.exe (PID: 8100)
- install.exe (PID: 6240)
- vcredist2008_x64.exe (PID: 3176)
- install.exe (PID: 2100)
- vcredist2010_x86.exe (PID: 2852)
- Setup.exe (PID: 6436)
- vcredist2010_x64.exe (PID: 6824)
- msiexec.exe (PID: 1628)
- Setup.exe (PID: 1328)
- vcredist2012_x86.exe (PID: 5232)
- vcredist2012_x86.exe (PID: 4308)
- msiexec.exe (PID: 4056)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2012_x64.exe (PID: 6740)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x86.exe (PID: 2772)
- vcredist2013_x64.exe (PID: 5936)
- vcredist2013_x64.exe (PID: 6620)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4844)
- VC_redist.x86.exe (PID: 5232)
- VC_redist.x86.exe (PID: 7728)
- VC_redist.x86.exe (PID: 5344)
- vcredist2015_2017_2019_2022_x64.exe (PID: 516)
- VC_redist.x64.exe (PID: 7872)
- VC_redist.x64.exe (PID: 660)
- VC_redist.x64.exe (PID: 6736)
- dxwsetup.exe (PID: 7660)
Reads Environment values
- identity_helper.exe (PID: 4724)
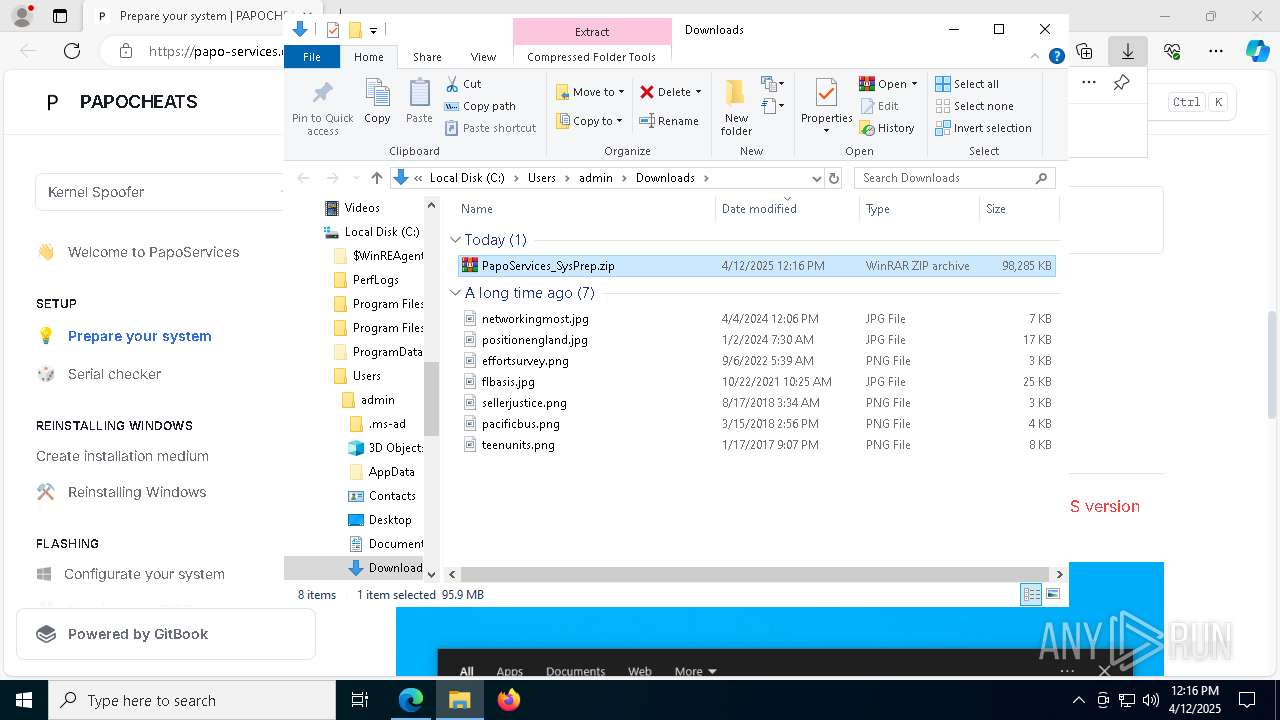
Autorun file from Downloads
- msedge.exe (PID: 5800)
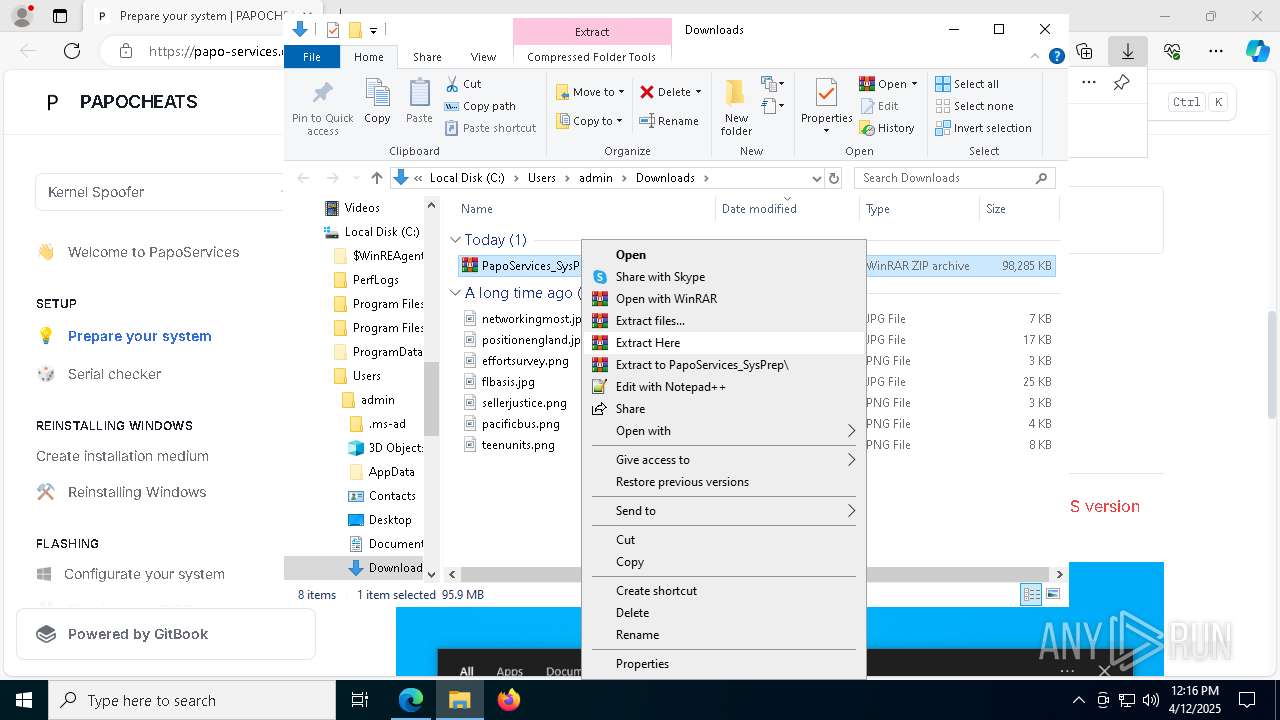
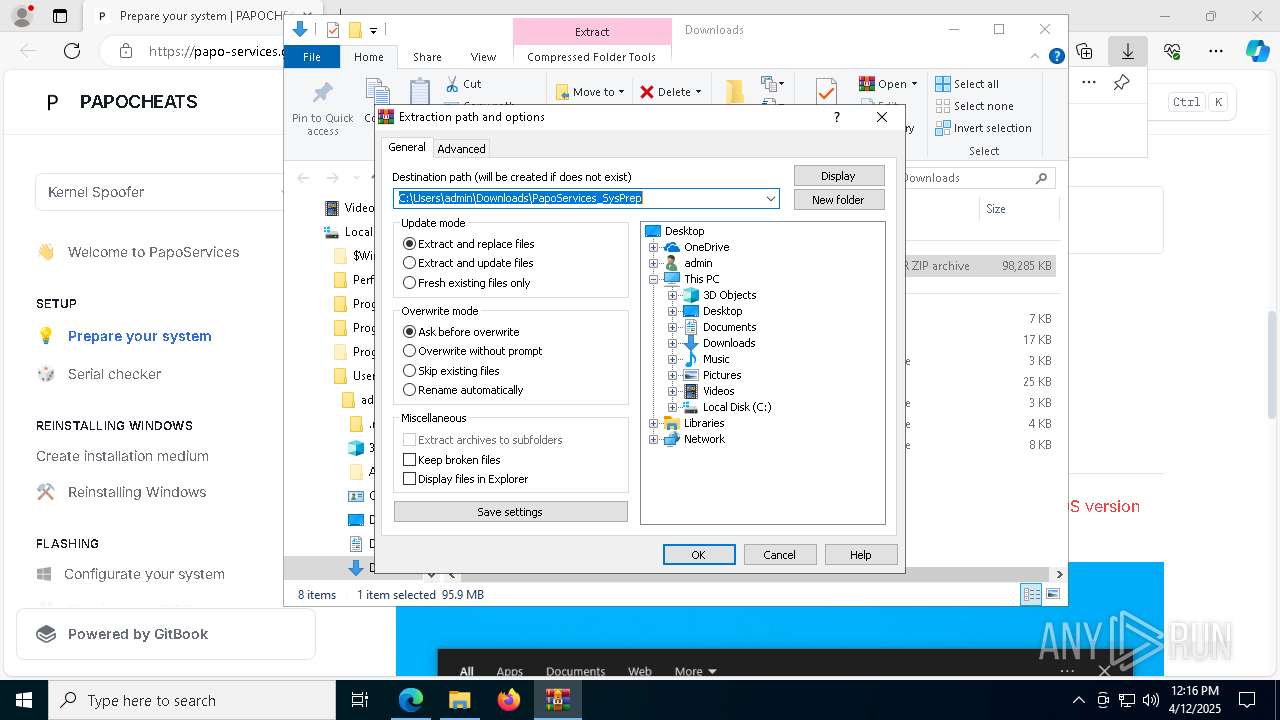
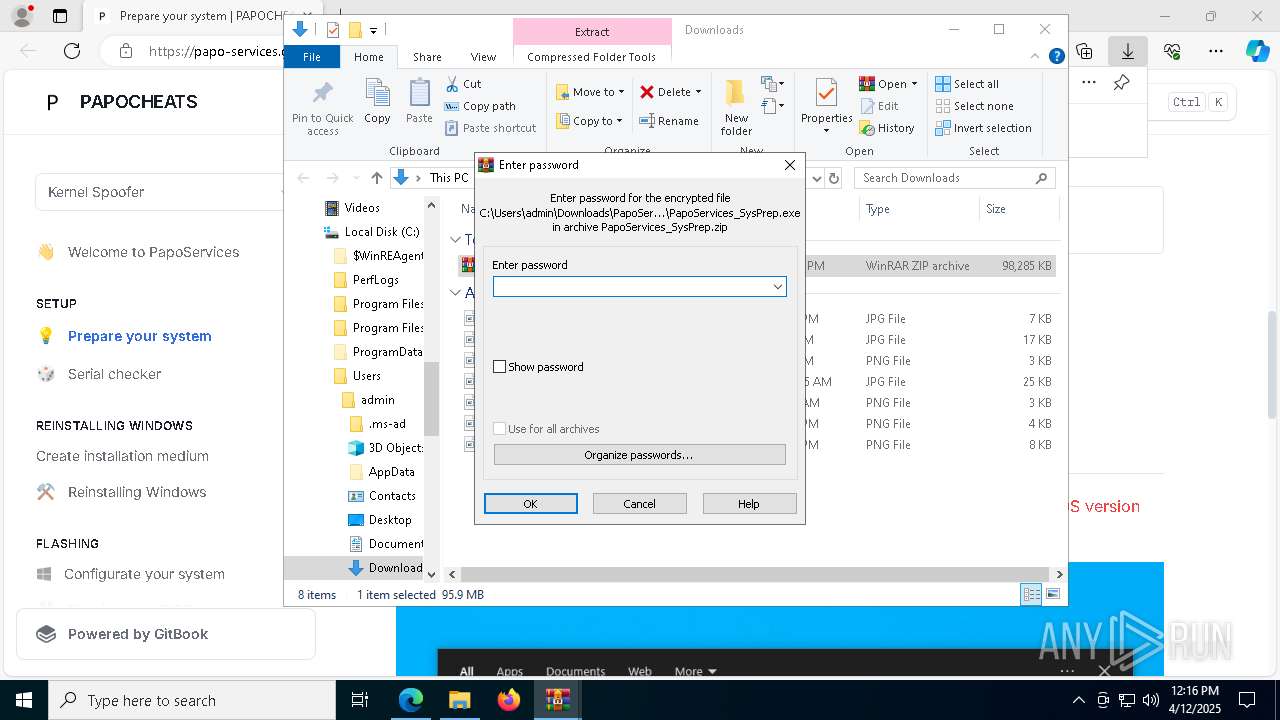
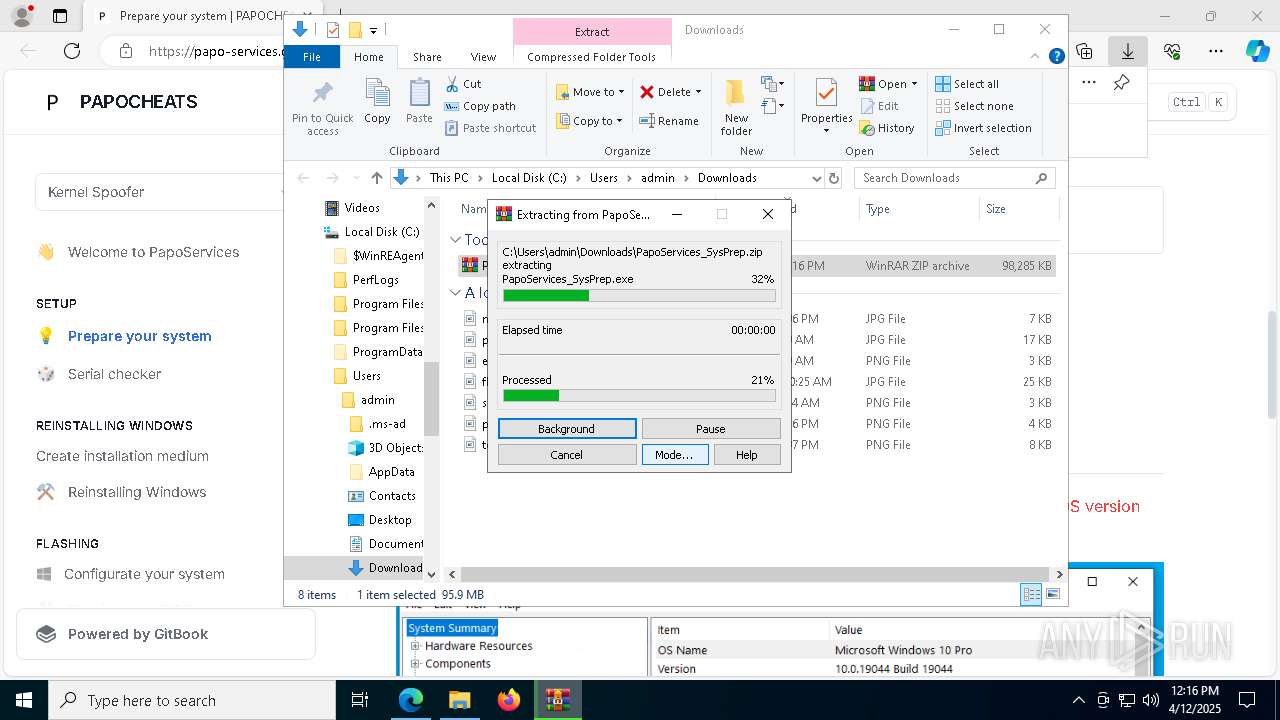
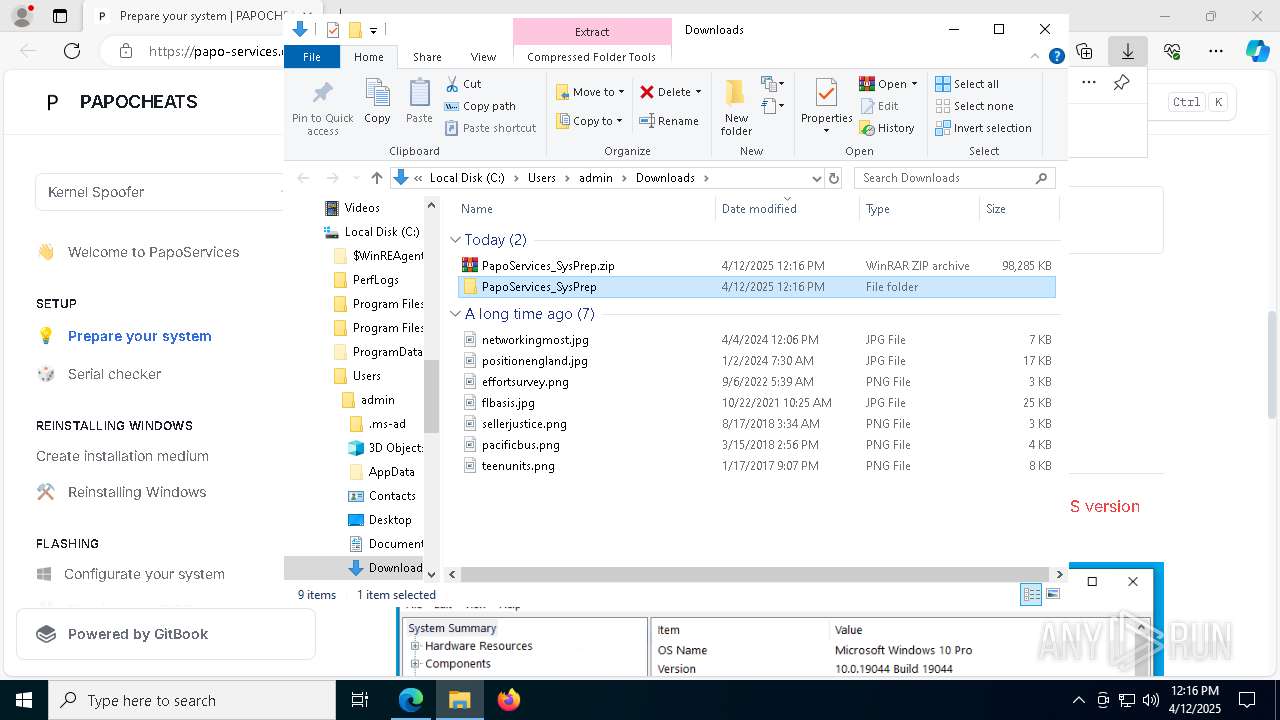
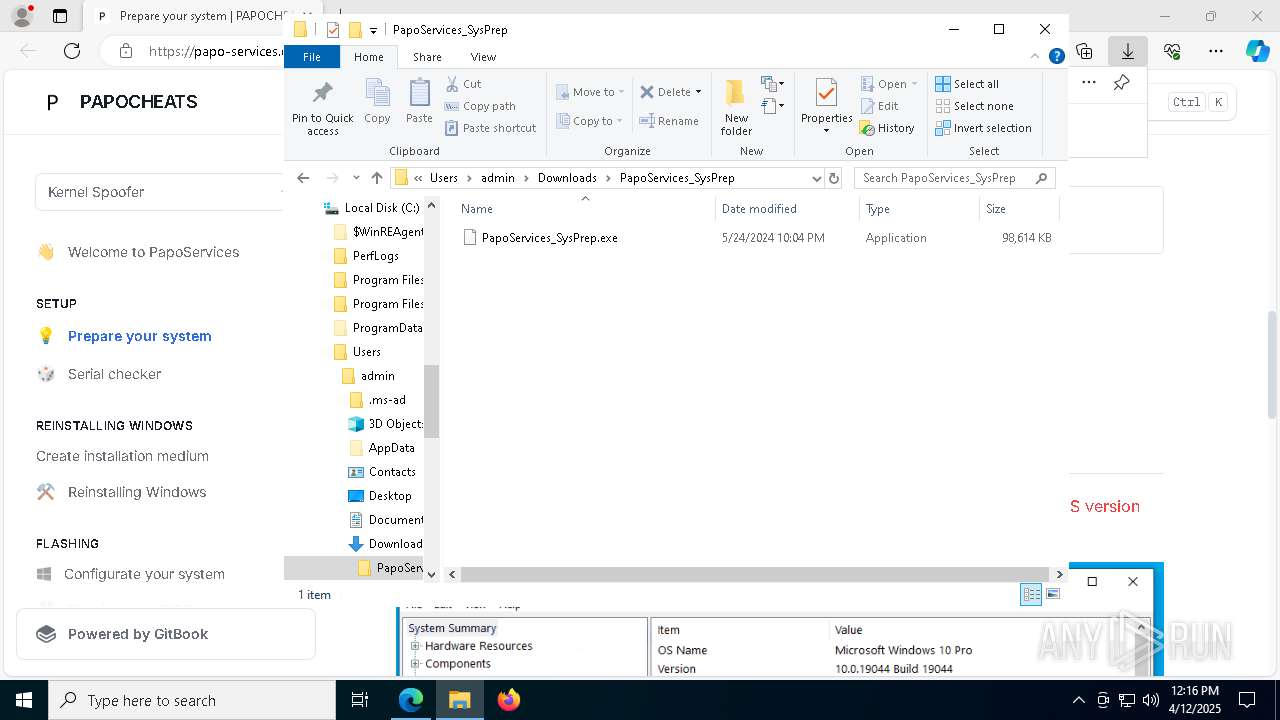
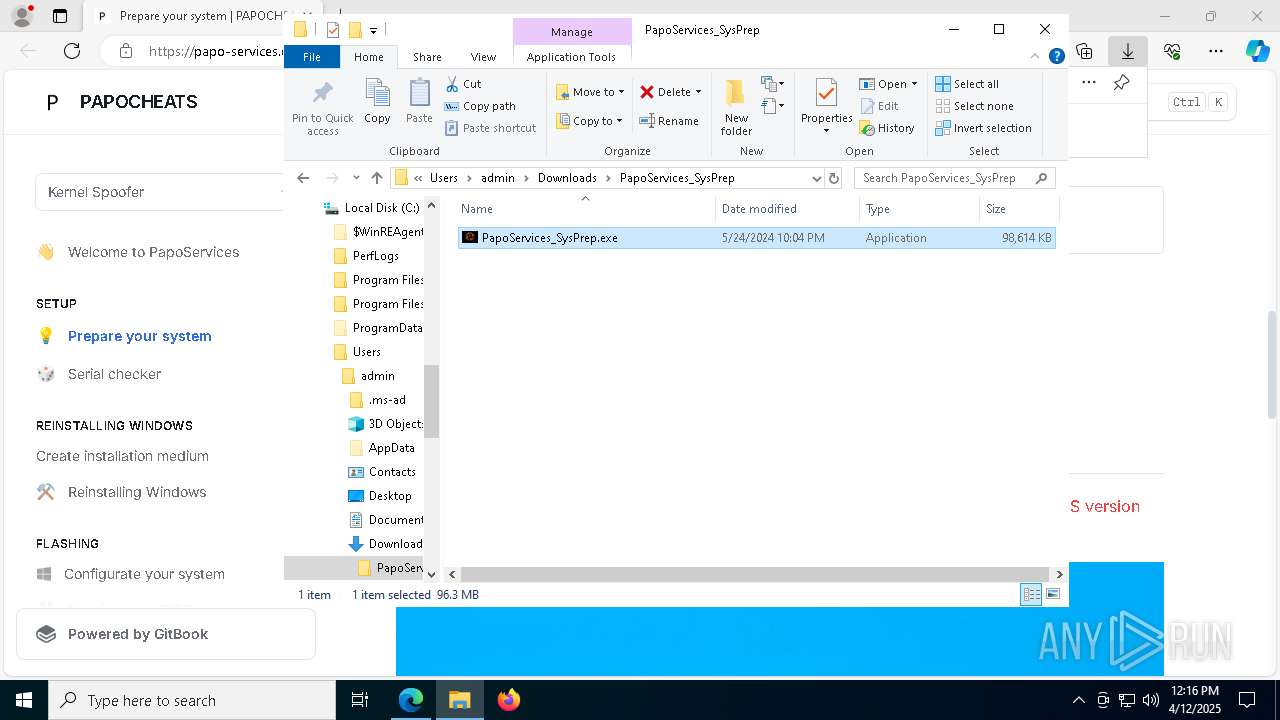
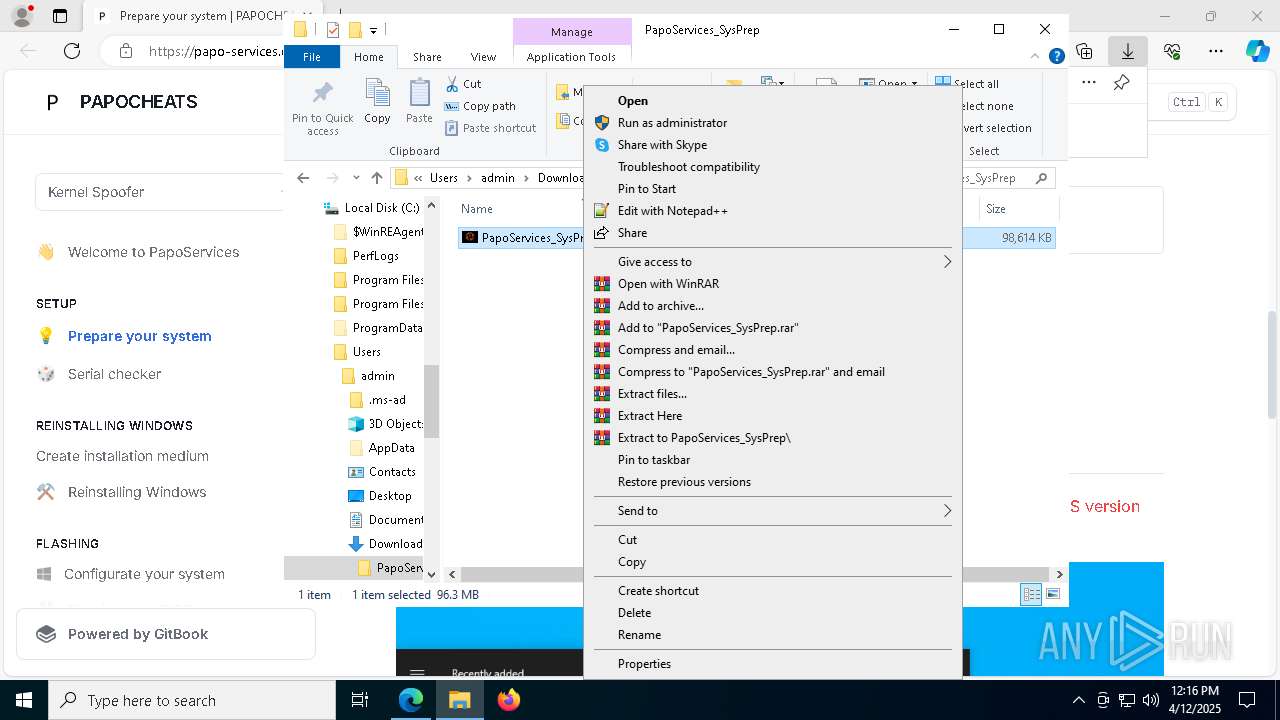
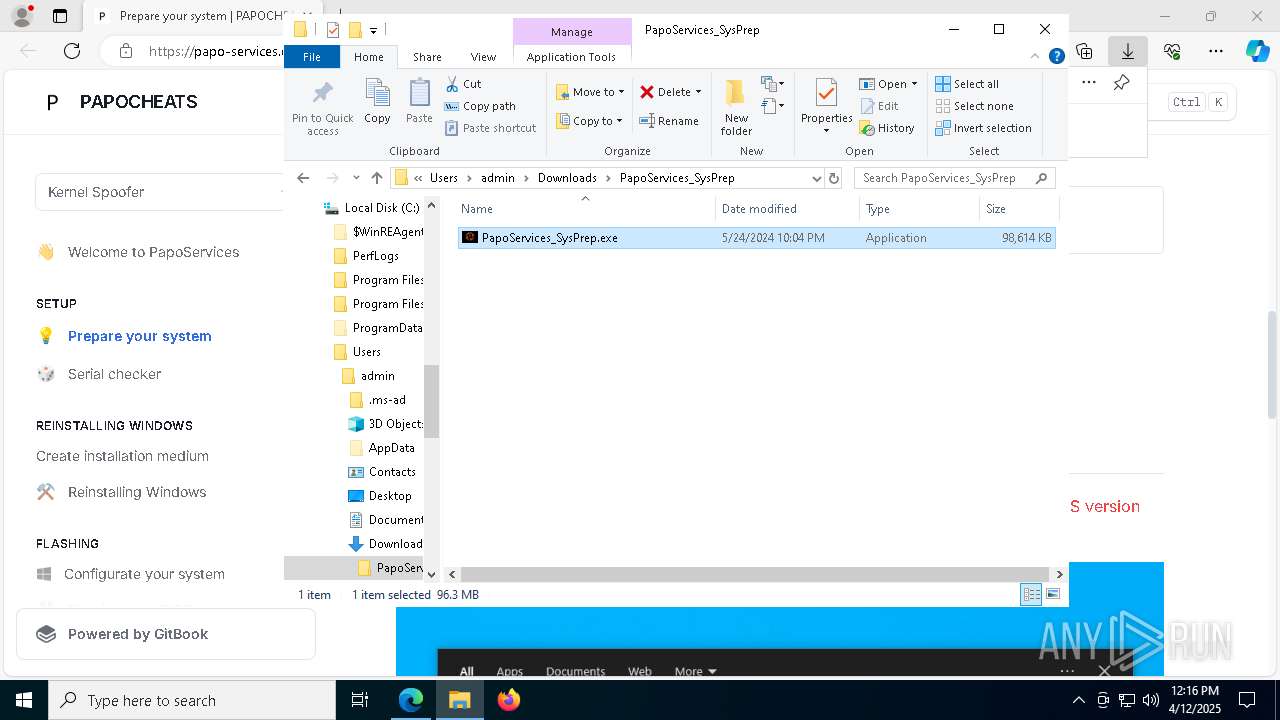
Manual execution by a user
- WinRAR.exe (PID: 5600)
- PapoServices_SysPrep.exe (PID: 1568)
- PapoServices_SysPrep.exe (PID: 5960)
Changes the registry key values via Powershell
- cmd.exe (PID: 8096)
Create files in a temporary directory
- PapoServices_SysPrep.exe (PID: 5960)
- tar.exe (PID: 2240)
- vcredist2005_x86.exe (PID: 1280)
- vcredist2005_x64.exe (PID: 2284)
- install.exe (PID: 2100)
- Setup.exe (PID: 6436)
- install.exe (PID: 6240)
- Setup.exe (PID: 1328)
- vcredist2012_x86.exe (PID: 4308)
- vcredist2012_x86.exe (PID: 5232)
- vcredist2012_x64.exe (PID: 6740)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2013_x86.exe (PID: 2772)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x64.exe (PID: 6620)
- vcredist2013_x64.exe (PID: 5936)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4844)
- VC_redist.x86.exe (PID: 5232)
- VC_redist.x86.exe (PID: 7728)
- vcredist2015_2017_2019_2022_x64.exe (PID: 516)
- VC_redist.x64.exe (PID: 7872)
- VC_redist.x64.exe (PID: 660)
- dxwebsetup.exe (PID: 6108)
Reads the software policy settings
- slui.exe (PID: 8184)
- msiexec.exe (PID: 6620)
- msiexec.exe (PID: 2596)
- slui.exe (PID: 1056)
- msiexec.exe (PID: 5280)
- Setup.exe (PID: 6436)
- Setup.exe (PID: 1328)
- msiexec.exe (PID: 1628)
- msiexec.exe (PID: 4056)
- vcredist2012_x86.exe (PID: 5232)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x64.exe (PID: 5936)
The sample compiled with english language support
- tar.exe (PID: 2240)
- msiexec.exe (PID: 5280)
- TiWorker.exe (PID: 8020)
- vcredist2008_x86.exe (PID: 8100)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2010_x86.exe (PID: 2852)
- vcredist2010_x64.exe (PID: 6824)
- msiexec.exe (PID: 1628)
- msedge.exe (PID: 5952)
- vcredist2012_x86.exe (PID: 4308)
- vcredist2012_x86.exe (PID: 5232)
- msiexec.exe (PID: 4056)
- vcredist2012_x64.exe (PID: 6740)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2013_x86.exe (PID: 2772)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x64.exe (PID: 6620)
- vcredist2013_x64.exe (PID: 5936)
- vcredist2015_2017_2019_2022_x86.exe (PID: 5744)
- vcredist2015_2017_2019_2022_x86.exe (PID: 4844)
- VC_redist.x86.exe (PID: 5232)
- VC_redist.x86.exe (PID: 7728)
- VC_redist.x86.exe (PID: 5344)
- vcredist2015_2017_2019_2022_x64.exe (PID: 5364)
- vcredist2015_2017_2019_2022_x64.exe (PID: 516)
- VC_redist.x64.exe (PID: 7872)
- VC_redist.x64.exe (PID: 660)
- VC_redist.x64.exe (PID: 6736)
- dxwebsetup.exe (PID: 6108)
- dxwsetup.exe (PID: 7660)
Checks proxy server information
- msiexec.exe (PID: 6620)
- slui.exe (PID: 1056)
- vcredist2012_x86.exe (PID: 5232)
- vcredist2013_x86.exe (PID: 4028)
Creates files or folders in the user directory
- msiexec.exe (PID: 6620)
- vcredist2012_x86.exe (PID: 5232)
- vcredist2013_x86.exe (PID: 4028)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6620)
- msiexec.exe (PID: 2596)
Manages system restore points
- SrTasks.exe (PID: 924)
- SrTasks.exe (PID: 4812)
- SrTasks.exe (PID: 7928)
- SrTasks.exe (PID: 7876)
Reads the machine GUID from the registry
- msiexec.exe (PID: 5280)
- vcredist2008_x86.exe (PID: 8100)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2010_x86.exe (PID: 2852)
- Setup.exe (PID: 6436)
- vcredist2010_x64.exe (PID: 6824)
- Setup.exe (PID: 1328)
- msiexec.exe (PID: 1628)
- vcredist2012_x86.exe (PID: 5232)
- msiexec.exe (PID: 4056)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x64.exe (PID: 5936)
- VC_redist.x86.exe (PID: 5232)
- VC_redist.x64.exe (PID: 7872)
The sample compiled with chinese language support
- msiexec.exe (PID: 5280)
- TiWorker.exe (PID: 8020)
- vcredist2008_x86.exe (PID: 8100)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2010_x86.exe (PID: 2852)
- vcredist2010_x64.exe (PID: 6824)
- msiexec.exe (PID: 1628)
- msiexec.exe (PID: 4056)
The sample compiled with spanish language support
- msiexec.exe (PID: 5280)
- TiWorker.exe (PID: 8020)
- vcredist2008_x86.exe (PID: 8100)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2010_x86.exe (PID: 2852)
- vcredist2010_x64.exe (PID: 6824)
- msiexec.exe (PID: 1628)
- msiexec.exe (PID: 4056)
The sample compiled with french language support
- msiexec.exe (PID: 5280)
- TiWorker.exe (PID: 8020)
- vcredist2008_x86.exe (PID: 8100)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2010_x86.exe (PID: 2852)
- vcredist2010_x64.exe (PID: 6824)
- msiexec.exe (PID: 1628)
- msiexec.exe (PID: 4056)
The sample compiled with Italian language support
- msiexec.exe (PID: 5280)
- TiWorker.exe (PID: 8020)
- vcredist2008_x86.exe (PID: 8100)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2010_x86.exe (PID: 2852)
- vcredist2010_x64.exe (PID: 6824)
- msiexec.exe (PID: 1628)
- msiexec.exe (PID: 4056)
The sample compiled with german language support
- msiexec.exe (PID: 5280)
- TiWorker.exe (PID: 8020)
- vcredist2008_x86.exe (PID: 8100)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2010_x86.exe (PID: 2852)
- vcredist2010_x64.exe (PID: 6824)
- msiexec.exe (PID: 1628)
- msiexec.exe (PID: 4056)
The sample compiled with japanese language support
- msiexec.exe (PID: 5280)
- TiWorker.exe (PID: 8020)
- vcredist2008_x86.exe (PID: 8100)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2010_x86.exe (PID: 2852)
- vcredist2010_x64.exe (PID: 6824)
- msiexec.exe (PID: 1628)
- msiexec.exe (PID: 4056)
The sample compiled with korean language support
- msiexec.exe (PID: 5280)
- TiWorker.exe (PID: 8020)
- vcredist2008_x86.exe (PID: 8100)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2010_x86.exe (PID: 2852)
- vcredist2010_x64.exe (PID: 6824)
- msiexec.exe (PID: 1628)
- msiexec.exe (PID: 4056)
Creates a software uninstall entry
- msiexec.exe (PID: 5280)
- msiexec.exe (PID: 1628)
- msiexec.exe (PID: 4056)
The sample compiled with russian language support
- TiWorker.exe (PID: 8020)
- msiexec.exe (PID: 5280)
- vcredist2008_x86.exe (PID: 8100)
- vcredist2008_x64.exe (PID: 3176)
- vcredist2010_x86.exe (PID: 2852)
- vcredist2010_x64.exe (PID: 6824)
- msiexec.exe (PID: 1628)
- msiexec.exe (PID: 4056)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5280)
- msiexec.exe (PID: 1628)
- msedge.exe (PID: 5952)
- msiexec.exe (PID: 4056)
Reads CPU info
- Setup.exe (PID: 6436)
- Setup.exe (PID: 1328)
Creates files in the program directory
- vcredist2012_x86.exe (PID: 5232)
- vcredist2012_x64.exe (PID: 4164)
- vcredist2013_x86.exe (PID: 4028)
- vcredist2013_x64.exe (PID: 5936)
- VC_redist.x86.exe (PID: 5232)
- VC_redist.x64.exe (PID: 7872)
Process checks computer location settings
- vcredist2015_2017_2019_2022_x86.exe (PID: 4844)
- VC_redist.x86.exe (PID: 7728)
- vcredist2015_2017_2019_2022_x64.exe (PID: 516)
- VC_redist.x64.exe (PID: 660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
277
Monitored processes
134
Malicious processes
33
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6132 --field-trial-handle=2628,i,9089678411840504173,7147987715053894809,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 516 | "C:\WINDOWS\Temp\{EFB749CB-93A1-4A96-83FF-3013D86BF430}\.cr\vcredist2015_2017_2019_2022_x64.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\runtimes\vcredist2015_2017_2019_2022_x64.exe" -burn.filehandle.attached=556 -burn.filehandle.self=576 /passive /norestart | C:\Windows\Temp\{EFB749CB-93A1-4A96-83FF-3013D86BF430}\.cr\vcredist2015_2017_2019_2022_x64.exe | vcredist2015_2017_2019_2022_x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.38.33135 Exit code: 3010 Version: 14.38.33135.0 Modules
| |||||||||||||||
| 632 | C:\WINDOWS\system32\cmd.exe /c start /wait C:\Users\admin\AppData\Local\Temp\runtimes\install_all.bat | C:\Windows\System32\cmd.exe | — | PapoServices_SysPrep.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe" -burn.clean.room="C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe" -burn.filehandle.attached=532 -burn.filehandle.self=552 -uninstall -quiet -burn.related.upgrade -burn.ancestors={c649ede4-f16a-4486-a117-dcc2f2a35165} -burn.filehandle.self=1208 -burn.embedded BurnPipe.{14864AF1-2108-4D32-B66C-7EB68D5374B6} {E6B9962C-B0AA-4B4C-B3A2-9580890F8EFD} 7872 | C:\ProgramData\Package Cache\{8bdfe669-9705-4184-9368-db9ce581e0e7}\VC_redist.x64.exe | VC_redist.x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2022 Redistributable (x64) - 14.36.32532 Exit code: 0 Version: 14.36.32532.0 Modules
| |||||||||||||||
| 668 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | PapoServices_SysPrep.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4436 --field-trial-handle=2628,i,9089678411840504173,7147987715053894809,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7140 --field-trial-handle=2628,i,9089678411840504173,7147987715053894809,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=900 --field-trial-handle=2628,i,9089678411840504173,7147987715053894809,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
100 745
Read events
92 636
Write events
6 783
Delete events
1 326
Modification events
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B555C60F2A912F00 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 98CFD30F2A912F00 | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2B85C0DC-6294-4711-8437-3BC77FEA3BA9} | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EFE8CF25-65CA-4E98-BC09-03CE42A7093A} | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BC0C1988-72AF-4C88-9E0B-08DB9A6DE7B5} | |||
| (PID) Process: | (5048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328332 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9F45CC8A-AED0-4490-AB7D-AD317E20D0D8} | |||
Executable files
703
Suspicious files
1 162
Text files
681
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c7d6.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c7f5.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c805.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c824.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c8a1.TMP | — | |
MD5:— | SHA256:— | |||
| 5048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
95
DNS requests
92
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1012 | SIHClient.exe | GET | — | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5116 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744952132&P2=404&P3=2&P4=MZ2NVcOPk648eQqGxqZ2ktWzyRzrvSYS3COFhzoSr4bWUsFx5xB0iqZb%2binmI9x9RQosLI8aQB0Yfi5cnTsPXg%3d%3d | unknown | — | — | whitelisted |
1012 | SIHClient.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5116 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744952132&P2=404&P3=2&P4=MZ2NVcOPk648eQqGxqZ2ktWzyRzrvSYS3COFhzoSr4bWUsFx5xB0iqZb%2binmI9x9RQosLI8aQB0Yfi5cnTsPXg%3d%3d | unknown | — | — | whitelisted |
5116 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744952132&P2=404&P3=2&P4=MZ2NVcOPk648eQqGxqZ2ktWzyRzrvSYS3COFhzoSr4bWUsFx5xB0iqZb%2binmI9x9RQosLI8aQB0Yfi5cnTsPXg%3d%3d | unknown | — | — | whitelisted |
5116 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744952132&P2=404&P3=2&P4=MZ2NVcOPk648eQqGxqZ2ktWzyRzrvSYS3COFhzoSr4bWUsFx5xB0iqZb%2binmI9x9RQosLI8aQB0Yfi5cnTsPXg%3d%3d | unknown | — | — | whitelisted |
5116 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744952132&P2=404&P3=2&P4=MZ2NVcOPk648eQqGxqZ2ktWzyRzrvSYS3COFhzoSr4bWUsFx5xB0iqZb%2binmI9x9RQosLI8aQB0Yfi5cnTsPXg%3d%3d | unknown | — | — | whitelisted |
5116 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1744952132&P2=404&P3=2&P4=MZ2NVcOPk648eQqGxqZ2ktWzyRzrvSYS3COFhzoSr4bWUsFx5xB0iqZb%2binmI9x9RQosLI8aQB0Yfi5cnTsPXg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7384 | msedge.exe | 172.64.147.209:443 | papo-services.gitbook.io | — | — | whitelisted |
5048 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7384 | msedge.exe | 104.18.41.89:443 | static.gitbook.com | — | — | shared |
7384 | msedge.exe | 172.64.146.167:443 | static.gitbook.com | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7384 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7384 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
papo-services.gitbook.io |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
static.gitbook.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7384 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Branch-based Git custom docs platform (.gitbook .io) |
7384 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Branch-based Git custom docs platform (.gitbook .io) |
7384 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Branch-based Git custom docs platform (.gitbook .io) |
7384 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Branch-based Git custom docs platform (.gitbook .io) |
7384 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Branch-based Git custom docs platform (.gitbook .io) |
7384 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Branch-based Git custom docs platform (.gitbook .io) |
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|