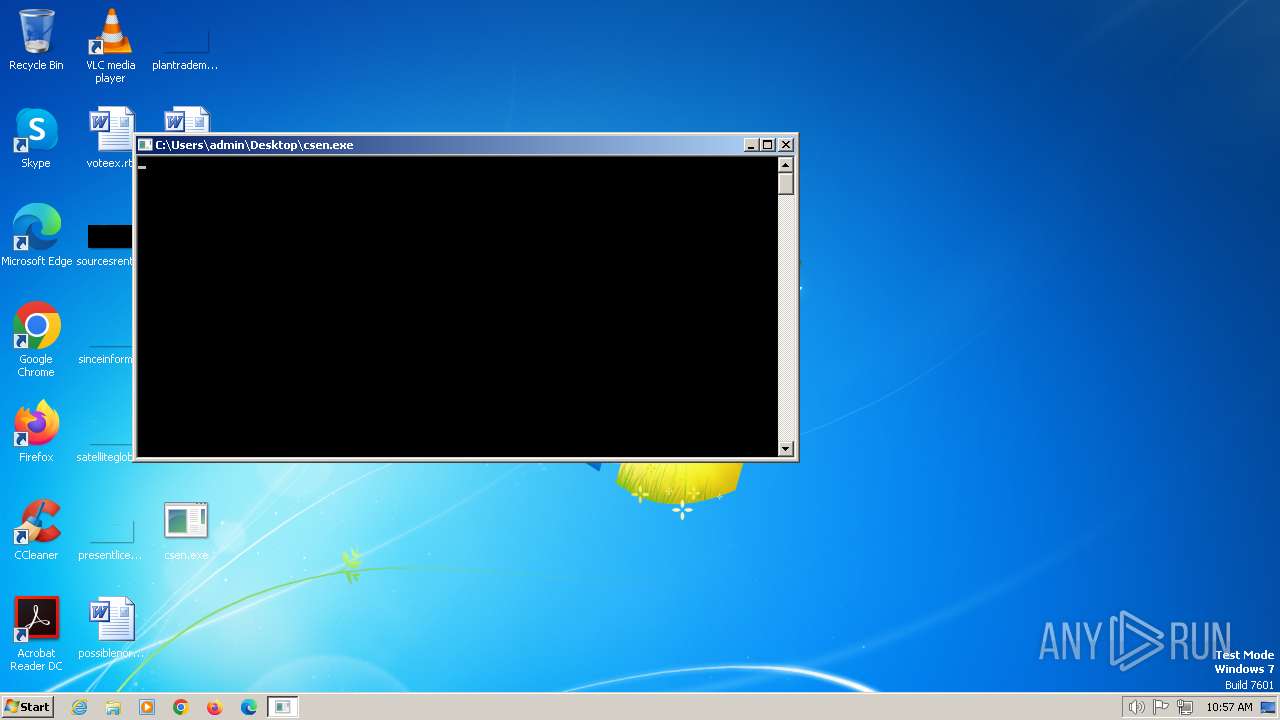
| File name: | csen.exe |
| Full analysis: | https://app.any.run/tasks/e2d0af9e-3938-4855-a6e3-5aef8df98404 |
| Verdict: | Malicious activity |
| Analysis date: | January 04, 2024, 10:13:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64 (stripped to external PDB), for MS Windows |
| MD5: | 1C0048C5CD6F36DFD30EF63E2310B461 |
| SHA1: | 9E7C0847F4CC8C7EA53AF93F03203D77E8120F81 |
| SHA256: | F1605C2CC5F8FA6CE3FD4781FCA899FDB83A77B6F0FE49E6F8F479F90E6ACC1A |
| SSDEEP: | 98304:gej4Coxks+I00YV/nLtmaOhDcsc+LjRsMagXaCErtymtZSCJFbSKbmL:k88 |
MALICIOUS
Creates a writable file in the system directory
- taskhost.exe (PID: 1364)
- powercfg.exe (PID: 2844)
Runs injected code in another process
- powercfg.exe (PID: 2844)
- rundll32.exe (PID: 896)
SUSPICIOUS
Reads settings of System Certificates
- csen.exe (PID: 2544)
Searches for installed software
- rundll32.exe (PID: 896)
Reads Microsoft Outlook installation path
- powercfg.exe (PID: 2844)
INFO
Reads the machine GUID from the registry
- csen.exe (PID: 2544)
Checks supported languages
- csen.exe (PID: 2544)
Reads the computer name
- csen.exe (PID: 2544)
Drops the executable file immediately after the start
- csen.exe (PID: 2544)
Application was injected by another process
- svchost.exe (PID: 600)
- svchost.exe (PID: 352)
- svchost.exe (PID: 864)
Executes as Windows Service
- powercfg.exe (PID: 2844)
- taskhost.exe (PID: 1364)
- rundll32.exe (PID: 896)
- VSSVC.exe (PID: 308)
- lpremove.exe (PID: 712)
Checks for external IP
- csen.exe (PID: 2544)
Creates files in the program directory
- powercfg.exe (PID: 2844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 3 |
| CodeSize: | 3262464 |
| InitializedDataSize: | 257024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x64a60 |
| OSVersion: | 6.1 |
| ImageVersion: | 1 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows command line |
Total processes
256
Monitored processes
9
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 352 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 600 | C:\Windows\system32\svchost.exe -k DcomLaunch | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 712 | C:\Windows\system32\lpremove.exe | C:\Windows\System32\lpremove.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: MUI Language pack cleanup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 896 | C:\Windows\system32\rundll32.exe /d srrstr.dll,ExecuteScheduledSPPCreation | C:\Windows\System32\rundll32.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1364 | "taskhost.exe" | C:\Windows\System32\taskhost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2544 | "C:\Users\admin\Desktop\csen.exe" -key=929c97c5-3344-498c-bc7c-27252d79af80 "-ua=win32#6.1.7601 SP1#1.1.2" | C:\Users\admin\Desktop\csen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2844 | C:\Windows\System32\powercfg.exe -energy -auto | C:\Windows\System32\powercfg.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 097
Read events
7 031
Write events
66
Delete events
0
Modification events
| (PID) Process: | (2544) csen.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\15A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (352) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MICROSOFT\WINDOWS NT\CURRENTVERSION\NetworkList\Nla\Cache\Intranet |
| Operation: | write | Name: | {00E51A5A-6FF0-414A-B358-C7EB6484BAF5} |
Value: 525400363EFF | |||
| (PID) Process: | (2844) powercfg.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2844) powercfg.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2844) powercfg.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2844) powercfg.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (712) lpremove.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MUI\Settings |
| Operation: | write | Name: | NextSQMCollection |
Value: 109F74A707F7D901 | |||
| (PID) Process: | (896) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000008904860955B0D901A8030000E0070000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (896) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000E366880955B0D901A8030000E0070000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (896) rundll32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000E366880955B0D901A8030000E0070000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
27
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2844 | powercfg.exe | C:\ProgramData\Microsoft\Windows\Power Efficiency Diagnostics\energy-ntkl.etl | — | |
MD5:— | SHA256:— | |||
| 896 | rundll32.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 352 | svchost.exe | C:\Windows\system32\CatRoot2\{F750E6C3-38EE-11D1-85E5-00C04FC295EE}\catdb | — | |
MD5:— | SHA256:— | |||
| 896 | rundll32.exe | C:\System Volume Information\SPP\SppCbsHiveStore\{cd42efe1-f6f1-427c-b004-033192c625a4}{15ADAA32-56F8-4385-830D-EA09F8A8AA81} | — | |
MD5:— | SHA256:— | |||
| 896 | rundll32.exe | C:\System Volume Information\SPP\SppCbsHiveStore\{cd42efe1-f6f1-427c-b004-033192c625a4}{1D75D4F4-7926-4209-AC6A-D5823F8DD966} | — | |
MD5:— | SHA256:— | |||
| 896 | rundll32.exe | C:\System Volume Information\SPP\SppCbsHiveStore\{cd42efe1-f6f1-427c-b004-033192c625a4}{C39E91F9-0C48-48F0-87B1-4650A59D0527} | — | |
MD5:— | SHA256:— | |||
| 896 | rundll32.exe | C:\System Volume Information\SPP\SppCbsHiveStore\{cd42efe1-f6f1-427c-b004-033192c625a4}{2C420892-08B1-42EC-9711-9B715FC5929F} | — | |
MD5:— | SHA256:— | |||
| 864 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | binary | |
MD5:89C909374B5AAF65CF1DFF14A2268B7A | SHA256:2987B7748413376D5B38E25D4D288967693218C4B51CE5F5D7B688B3D564A4BD | |||
| 352 | svchost.exe | C:\Windows\system32\CatRoot2\edb.chk | binary | |
MD5:9F0B62522D88789DEF2489EE8FC45C5C | SHA256:0B34FFE5D2CA520C7D1A4F90142383853A2257054CF81BA3E1D62D0CD1CAB091 | |||
| 352 | svchost.exe | C:\Windows\system32\CatRoot2\edb.log | binary | |
MD5:1628A5F6AA463CD534D9E48D9DED9F45 | SHA256:65034600358992F26A0ADE25F160684A5B0229A46E03085B6707499B235603B1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
22
DNS requests
17
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2544 | csen.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/?fields=61439 | unknown | binary | 289 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
352 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2544 | csen.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
1220 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
2544 | csen.exe | 188.114.96.3:443 | coinsurf.com | CLOUDFLARENET | NL | unknown |
2544 | csen.exe | 195.181.165.170:5051 | — | — | — | unknown |
2544 | csen.exe | 184.30.216.156:443 | ssl.zdf.de | AKAMAI-AS | DE | unknown |
2544 | csen.exe | 54.246.79.9:443 | www.netflix.com | AMAZON-02 | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2544 | csen.exe | 54.74.73.31:443 | www.netflix.com | AMAZON-02 | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| shared |
coinsurf.com |
| unknown |
ssl.zdf.de |
| unknown |
www.netflix.com |
| whitelisted |
teredo.ipv6.microsoft.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2544 | csen.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2544 | csen.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
2544 | csen.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |