| File name: | 1.exe |
| Full analysis: | https://app.any.run/tasks/e4942815-3f68-4516-8f8f-fa3aa04a631b |
| Verdict: | Malicious activity |
| Analysis date: | August 21, 2023, 14:13:24 |
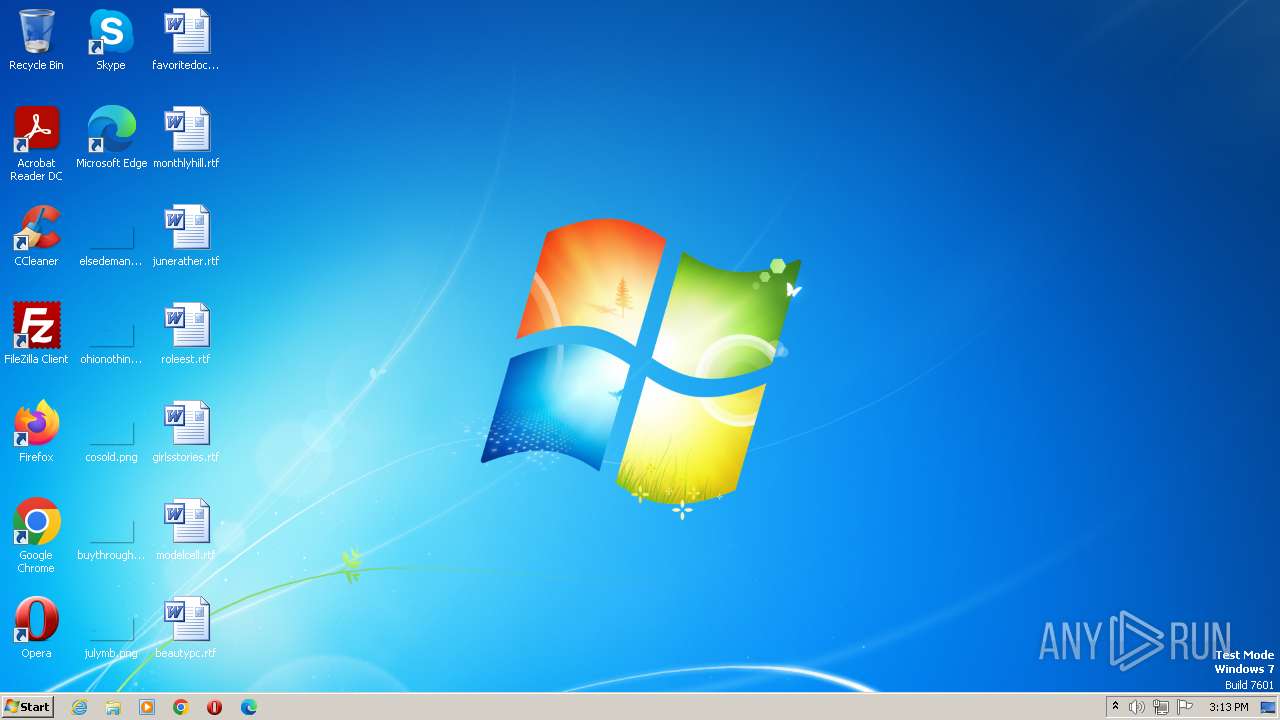
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 195172EB3F7A763AD8DB8496065B6FD2 |
| SHA1: | 057AFD7AC15715427BD459267A3607E0E671C767 |
| SHA256: | F1428AF9DD631AF5870AF8E79DE25CDD8B5197B940CE34CC490BFDC8FA4F0953 |
| SSDEEP: | 12288:Z0hiVxinJv/UxrrdyvGq5MoQnKgWv9Ne3wdO4:Z0hiHUJqrrdeGqeP29Nec |
MALICIOUS
Loads dropped or rewritten executable
- 1.exe (PID: 3492)
SUSPICIOUS
Searches for installed software
- 1.exe (PID: 3492)
Executable content was dropped or overwritten
- 1.exe (PID: 3492)
The process creates files with name similar to system file names
- 1.exe (PID: 3492)
INFO
Reads the computer name
- 1.exe (PID: 3492)
- wmpnscfg.exe (PID: 3412)
Checks supported languages
- 1.exe (PID: 3492)
- wmpnscfg.exe (PID: 3412)
Manual execution by a user
- wmpnscfg.exe (PID: 3412)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3412)
Create files in a temporary directory
- 1.exe (PID: 3492)
Creates files or folders in the user directory
- 1.exe (PID: 3492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductVersion: | 3.0.0.0 |
|---|---|
| ProductName: | splashed toptrnere |
| LegalTrademarks: | vareudbud |
| LegalCopyright: | irrision basisforskningsprogram marmorets |
| Comments: | vernonia osteopaths |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 3.0.0.0 |
| FileVersionNumber: | 3.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x34a5 |
| UninitializedDataSize: | 2048 |
| InitializedDataSize: | 141824 |
| CodeSize: | 26112 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2018:01:30 03:57:41+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:41 |
| Detected languages: |
|
| Comments: | vernonia osteopaths |
| LegalCopyright: | irrision basisforskningsprogram marmorets |
| LegalTrademarks: | vareudbud |
| ProductName: | splashed toptrnere |
| ProductVersion: | 3.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006409 | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41622 |
.rdata | 0x00008000 | 0x0000138E | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14383 |
.data | 0x0000A000 | 0x00020358 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.0044 |
.ndata | 0x0002B000 | 0x00023000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0004E000 | 0x0002EA68 | 0x0002EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.60016 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2992 | 830 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.59514 | 38056 | UNKNOWN | English - United States | RT_ICON |
3 | 5.04853 | 19496 | UNKNOWN | English - United States | RT_ICON |
4 | 5.73096 | 16936 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18973 | 11432 | UNKNOWN | English - United States | RT_ICON |
6 | 5.72423 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 5.45091 | 5672 | UNKNOWN | English - United States | RT_ICON |
8 | 5.91128 | 4264 | UNKNOWN | English - United States | RT_ICON |
9 | 5.51286 | 3752 | UNKNOWN | English - United States | RT_ICON |
10 | 5.99294 | 2440 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3412 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3492 | "C:\Users\admin\AppData\Local\Temp\1.exe" | C:\Users\admin\AppData\Local\Temp\1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 010
Read events
1 007
Write events
0
Delete events
3
Modification events
| (PID) Process: | (3412) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{82A9E474-3AF7-4D31-9E36-A96F045939D3}\{A73C7236-7191-42F3-9BF4-15E1DB4244C2} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3412) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{82A9E474-3AF7-4D31-9E36-A96F045939D3} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3412) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{0080F5FA-3DF4-41FB-9BD0-10B0D7A00E09} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
1
Suspicious files
2
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3492 | 1.exe | C:\Users\admin\AppData\Local\Temp\Sara.lnk | lnk | |
MD5:C850AA5706C5AC04967787C04C60D403 | SHA256:E2125C1A7B25B619A318F89C9659E8CA38F3D442B23E901FA1F0220823E8831B | |||
| 3492 | 1.exe | C:\Users\admin\AppData\Roaming\Bannerfrerens\Arno\semipurposive.Kla | binary | |
MD5:03F55616C144BA8920021666DC5B76F5 | SHA256:CAB8FFF2BC87C288BA1B11C97140A7AEE098945E7839F3D1CE4509B5AA430C3D | |||
| 3492 | 1.exe | C:\Users\admin\AppData\Local\Temp\nss9832.tmp\System.dll | executable | |
MD5:75ED96254FBF894E42058062B4B4F0D1 | SHA256:A632D74332B3F08F834C732A103DAFEB09A540823A2217CA7F49159755E8F1D7 | |||
| 3492 | 1.exe | C:\Users\admin\AppData\Roaming\Bannerfrerens\Arno\Mangelsygdommes\Finalismes\metasymboler.for | binary | |
MD5:25AEB217C520C021BC71BC02AC3A4FC7 | SHA256:5638E07F7E245B6D2FDD6F0135D82FE7D97F6ED972DEB79247F695061B5A63CA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |