| File name: | xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe |
| Full analysis: | https://app.any.run/tasks/143dac19-87e4-4ecf-b755-ce4ffebd165b |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | February 24, 2026, 02:41:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 0BF814FF7DA8AC61D3BA49E35C2F1B17 |
| SHA1: | 6782F3286A8779D51159F226195B3BA884FEA784 |
| SHA256: | F137A03A5AD245D3F0291C31587C1E2B1BA31396C0A12FC138EB15DEDEC2C8CD |
| SSDEEP: | 98304:xAfJsY3g+hna1iRRJx2gMSqqhV4btbwM+CQxxWhF7aq13xMT7aet1tE1l0i9P3w/:z+v |
MALICIOUS
UAC/LUA settings modification
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 6544)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
- conhost.exe (PID: 8916)
- conhost.exe (PID: 2364)
- conhost.exe (PID: 6172)
- conhost.exe (PID: 7748)
- conhost.exe (PID: 1908)
- conhost.exe (PID: 5044)
- conhost.exe (PID: 5676)
- conhost.exe (PID: 6852)
- conhost.exe (PID: 7244)
Changes the autorun value in the registry
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
Changes Windows Defender settings
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
Adds path to the Windows Defender exclusion list
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
DCRAT mutex has been found
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
- conhost.exe (PID: 8916)
- conhost.exe (PID: 2364)
- conhost.exe (PID: 6172)
- conhost.exe (PID: 7748)
- conhost.exe (PID: 1908)
- conhost.exe (PID: 5044)
- conhost.exe (PID: 5676)
- conhost.exe (PID: 6852)
- conhost.exe (PID: 7244)
DCRAT has been detected (YARA)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 5308)
- wscript.exe (PID: 7036)
- wscript.exe (PID: 6516)
- wscript.exe (PID: 8820)
- wscript.exe (PID: 6664)
- wscript.exe (PID: 7104)
- wscript.exe (PID: 2788)
- wscript.exe (PID: 3232)
- wscript.exe (PID: 6352)
- wscript.exe (PID: 7600)
- wscript.exe (PID: 3032)
- wscript.exe (PID: 7272)
- wscript.exe (PID: 4552)
- wscript.exe (PID: 7544)
- wscript.exe (PID: 4128)
- wscript.exe (PID: 6332)
Deletes a file (SCRIPT)
- wscript.exe (PID: 5308)
- wscript.exe (PID: 6516)
- wscript.exe (PID: 6664)
- wscript.exe (PID: 3232)
- wscript.exe (PID: 7600)
- wscript.exe (PID: 3032)
- wscript.exe (PID: 4552)
- wscript.exe (PID: 6332)
SUSPICIOUS
Starts CMD.EXE for commands execution
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 6544)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
Executed via WMI
- schtasks.exe (PID: 5768)
- schtasks.exe (PID: 6784)
- schtasks.exe (PID: 6500)
- schtasks.exe (PID: 8152)
- schtasks.exe (PID: 1344)
- schtasks.exe (PID: 9004)
- schtasks.exe (PID: 8264)
- schtasks.exe (PID: 8660)
- schtasks.exe (PID: 4280)
- schtasks.exe (PID: 3176)
- schtasks.exe (PID: 9188)
- schtasks.exe (PID: 6172)
- schtasks.exe (PID: 6348)
- schtasks.exe (PID: 1916)
- schtasks.exe (PID: 2096)
- schtasks.exe (PID: 8728)
- schtasks.exe (PID: 1856)
- schtasks.exe (PID: 8180)
- schtasks.exe (PID: 8676)
- schtasks.exe (PID: 8624)
- schtasks.exe (PID: 6056)
- schtasks.exe (PID: 864)
- schtasks.exe (PID: 6360)
- schtasks.exe (PID: 8912)
- schtasks.exe (PID: 1512)
- schtasks.exe (PID: 3636)
- schtasks.exe (PID: 3332)
- schtasks.exe (PID: 4796)
- schtasks.exe (PID: 7288)
- schtasks.exe (PID: 3208)
- schtasks.exe (PID: 4700)
- schtasks.exe (PID: 4288)
- schtasks.exe (PID: 7272)
- schtasks.exe (PID: 6644)
- schtasks.exe (PID: 2868)
- schtasks.exe (PID: 4828)
- schtasks.exe (PID: 3096)
- schtasks.exe (PID: 4352)
- schtasks.exe (PID: 8692)
- schtasks.exe (PID: 8844)
- schtasks.exe (PID: 1632)
- schtasks.exe (PID: 7924)
- schtasks.exe (PID: 6208)
- schtasks.exe (PID: 9112)
- schtasks.exe (PID: 2496)
- schtasks.exe (PID: 7988)
- schtasks.exe (PID: 7104)
- schtasks.exe (PID: 8740)
- schtasks.exe (PID: 7640)
- schtasks.exe (PID: 6444)
- schtasks.exe (PID: 5424)
- schtasks.exe (PID: 8800)
- schtasks.exe (PID: 7824)
- schtasks.exe (PID: 7920)
- schtasks.exe (PID: 8576)
- schtasks.exe (PID: 5308)
- schtasks.exe (PID: 8044)
- schtasks.exe (PID: 1672)
- schtasks.exe (PID: 4024)
- schtasks.exe (PID: 6608)
The process creates files with name similar to system file names
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
Creates scheduled task with highest privileges
- schtasks.exe (PID: 6784)
- schtasks.exe (PID: 6500)
- schtasks.exe (PID: 8152)
- schtasks.exe (PID: 1344)
- schtasks.exe (PID: 8660)
- schtasks.exe (PID: 4280)
- schtasks.exe (PID: 6172)
- schtasks.exe (PID: 1916)
- schtasks.exe (PID: 9188)
- schtasks.exe (PID: 1856)
- schtasks.exe (PID: 2096)
- schtasks.exe (PID: 864)
- schtasks.exe (PID: 8180)
- schtasks.exe (PID: 8624)
- schtasks.exe (PID: 3636)
- schtasks.exe (PID: 3332)
- schtasks.exe (PID: 4796)
- schtasks.exe (PID: 3208)
- schtasks.exe (PID: 7288)
- schtasks.exe (PID: 4700)
- schtasks.exe (PID: 4288)
- schtasks.exe (PID: 6360)
- schtasks.exe (PID: 3096)
- schtasks.exe (PID: 4352)
- schtasks.exe (PID: 8844)
- schtasks.exe (PID: 4828)
- schtasks.exe (PID: 6644)
- schtasks.exe (PID: 7924)
- schtasks.exe (PID: 9112)
- schtasks.exe (PID: 2496)
- schtasks.exe (PID: 8740)
- schtasks.exe (PID: 8800)
- schtasks.exe (PID: 7640)
- schtasks.exe (PID: 5424)
- schtasks.exe (PID: 7104)
- schtasks.exe (PID: 4024)
- schtasks.exe (PID: 8576)
- schtasks.exe (PID: 1672)
- schtasks.exe (PID: 6608)
- schtasks.exe (PID: 5308)
Executable content was dropped or overwritten
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
- conhost.exe (PID: 8916)
Starts POWERSHELL.EXE for commands execution
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
Script adds exclusion path to Windows Defender
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
Executing commands from a ".bat" file
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 7104)
- w32tm.exe (PID: 7672)
Starts itself from another location
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 5308)
- wscript.exe (PID: 7036)
- wscript.exe (PID: 8820)
- wscript.exe (PID: 6516)
- wscript.exe (PID: 6664)
- wscript.exe (PID: 7104)
- wscript.exe (PID: 2788)
- wscript.exe (PID: 3232)
- wscript.exe (PID: 7600)
- wscript.exe (PID: 6352)
- wscript.exe (PID: 3032)
- wscript.exe (PID: 7272)
- wscript.exe (PID: 7544)
- wscript.exe (PID: 4552)
- wscript.exe (PID: 4128)
- wscript.exe (PID: 6332)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 5308)
- wscript.exe (PID: 6516)
- wscript.exe (PID: 6664)
- wscript.exe (PID: 3232)
- wscript.exe (PID: 7600)
- wscript.exe (PID: 3032)
- wscript.exe (PID: 4552)
- wscript.exe (PID: 6332)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 5308)
- wscript.exe (PID: 6516)
- wscript.exe (PID: 6664)
- wscript.exe (PID: 3232)
- wscript.exe (PID: 7600)
- wscript.exe (PID: 3032)
- wscript.exe (PID: 4552)
- wscript.exe (PID: 6332)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 5308)
- wscript.exe (PID: 6516)
- wscript.exe (PID: 6664)
- wscript.exe (PID: 3232)
- wscript.exe (PID: 7600)
- wscript.exe (PID: 3032)
- wscript.exe (PID: 4552)
- wscript.exe (PID: 6332)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5308)
- wscript.exe (PID: 6516)
- wscript.exe (PID: 6664)
- wscript.exe (PID: 3232)
- wscript.exe (PID: 7600)
- wscript.exe (PID: 3032)
- wscript.exe (PID: 4552)
- wscript.exe (PID: 6332)
The process executes VB scripts
- wscript.exe (PID: 6516)
- wscript.exe (PID: 7104)
- wscript.exe (PID: 6352)
- wscript.exe (PID: 3032)
INFO
Reads the computer name
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 6544)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- winlogon.exe (PID: 8232)
- winlogon.exe (PID: 4828)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
- slui.exe (PID: 3508)
- smss.exe (PID: 4188)
- uhssvc.exe (PID: 4516)
- conhost.exe (PID: 8632)
- slui.exe (PID: 1824)
- Memory Compression.exe (PID: 7708)
- WmiPrvSE.exe (PID: 3212)
- conhost.exe (PID: 8080)
- System.exe (PID: 7932)
- slui.exe (PID: 4088)
- TextInputHost.exe (PID: 148)
- smss.exe (PID: 1760)
- uhssvc.exe (PID: 1492)
- System.exe (PID: 1084)
- conhost.exe (PID: 8488)
- winrshost.exe (PID: 7164)
- Memory Compression.exe (PID: 8844)
- slui.exe (PID: 6848)
- csrss.exe (PID: 1512)
- conhost.exe (PID: 5484)
- winrshost.exe (PID: 3536)
- winrshost.exe (PID: 3168)
- WmiPrvSE.exe (PID: 4784)
- slui.exe (PID: 8232)
- conhost.exe (PID: 6336)
- csrss.exe (PID: 2684)
- winrshost.exe (PID: 2228)
- conhost.exe (PID: 8408)
- slui.exe (PID: 4060)
- TextInputHost.exe (PID: 864)
- conhost.exe (PID: 8916)
- conhost.exe (PID: 2364)
- conhost.exe (PID: 6172)
- conhost.exe (PID: 7748)
- conhost.exe (PID: 1908)
- conhost.exe (PID: 5044)
- conhost.exe (PID: 5676)
- conhost.exe (PID: 6852)
- conhost.exe (PID: 7244)
Checks supported languages
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 6544)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- winlogon.exe (PID: 8232)
- winlogon.exe (PID: 4828)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
- smss.exe (PID: 4188)
- slui.exe (PID: 3508)
- uhssvc.exe (PID: 4516)
- conhost.exe (PID: 8632)
- Memory Compression.exe (PID: 7708)
- slui.exe (PID: 1824)
- WmiPrvSE.exe (PID: 3212)
- smss.exe (PID: 1760)
- conhost.exe (PID: 8080)
- System.exe (PID: 7932)
- slui.exe (PID: 4088)
- uhssvc.exe (PID: 1492)
- TextInputHost.exe (PID: 148)
- conhost.exe (PID: 8488)
- winrshost.exe (PID: 7164)
- System.exe (PID: 1084)
- csrss.exe (PID: 1512)
- conhost.exe (PID: 5484)
- winrshost.exe (PID: 3536)
- Memory Compression.exe (PID: 8844)
- slui.exe (PID: 6848)
- slui.exe (PID: 8232)
- winrshost.exe (PID: 3168)
- conhost.exe (PID: 6336)
- WmiPrvSE.exe (PID: 4784)
- slui.exe (PID: 4060)
- winrshost.exe (PID: 2228)
- conhost.exe (PID: 8408)
- TextInputHost.exe (PID: 864)
- csrss.exe (PID: 2684)
- conhost.exe (PID: 8916)
- conhost.exe (PID: 2364)
- conhost.exe (PID: 6172)
- conhost.exe (PID: 7748)
- conhost.exe (PID: 1908)
- conhost.exe (PID: 5044)
- conhost.exe (PID: 5676)
- conhost.exe (PID: 6852)
- conhost.exe (PID: 7244)
The sample compiled with english language support
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 6544)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
- conhost.exe (PID: 8916)
Reads the machine GUID from the registry
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 6544)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- winlogon.exe (PID: 8232)
- winlogon.exe (PID: 4828)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
- slui.exe (PID: 3508)
- smss.exe (PID: 4188)
- uhssvc.exe (PID: 4516)
- conhost.exe (PID: 8632)
- Memory Compression.exe (PID: 7708)
- slui.exe (PID: 1824)
- WmiPrvSE.exe (PID: 3212)
- slui.exe (PID: 4088)
- conhost.exe (PID: 8080)
- TextInputHost.exe (PID: 148)
- smss.exe (PID: 1760)
- System.exe (PID: 7932)
- conhost.exe (PID: 8488)
- winrshost.exe (PID: 7164)
- uhssvc.exe (PID: 1492)
- System.exe (PID: 1084)
- conhost.exe (PID: 5484)
- winrshost.exe (PID: 3536)
- Memory Compression.exe (PID: 8844)
- csrss.exe (PID: 1512)
- slui.exe (PID: 6848)
- conhost.exe (PID: 6336)
- winrshost.exe (PID: 3168)
- slui.exe (PID: 8232)
- winrshost.exe (PID: 2228)
- conhost.exe (PID: 8408)
- slui.exe (PID: 4060)
- WmiPrvSE.exe (PID: 4784)
- csrss.exe (PID: 2684)
- TextInputHost.exe (PID: 864)
- conhost.exe (PID: 8916)
- conhost.exe (PID: 2364)
- conhost.exe (PID: 6172)
- conhost.exe (PID: 7748)
- conhost.exe (PID: 1908)
- conhost.exe (PID: 5044)
- conhost.exe (PID: 5676)
- conhost.exe (PID: 6852)
- conhost.exe (PID: 7244)
Reads security settings of Internet Explorer
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 6544)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
- conhost.exe (PID: 8916)
- conhost.exe (PID: 2364)
- conhost.exe (PID: 6172)
- conhost.exe (PID: 7748)
- conhost.exe (PID: 1908)
- conhost.exe (PID: 5044)
- conhost.exe (PID: 5676)
- conhost.exe (PID: 6852)
- conhost.exe (PID: 7244)
Process checks whether UAC notifications are on
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 6544)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
- conhost.exe (PID: 8916)
- conhost.exe (PID: 2364)
- conhost.exe (PID: 6172)
- conhost.exe (PID: 7748)
- conhost.exe (PID: 1908)
- conhost.exe (PID: 5044)
- conhost.exe (PID: 5676)
- conhost.exe (PID: 6852)
- conhost.exe (PID: 7244)
Process checks computer location settings
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 6544)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
- conhost.exe (PID: 8916)
- conhost.exe (PID: 2364)
- conhost.exe (PID: 6172)
- conhost.exe (PID: 7748)
- conhost.exe (PID: 1908)
- conhost.exe (PID: 5044)
- conhost.exe (PID: 5676)
- conhost.exe (PID: 6852)
Launching a file from a Registry key
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
Creates files in the program directory
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
Manual execution by a user
- winlogon.exe (PID: 8232)
- winlogon.exe (PID: 4828)
- slui.exe (PID: 3508)
- smss.exe (PID: 4188)
- uhssvc.exe (PID: 4516)
- conhost.exe (PID: 8632)
- Memory Compression.exe (PID: 7708)
- slui.exe (PID: 1824)
- WmiPrvSE.exe (PID: 3212)
- smss.exe (PID: 1760)
- slui.exe (PID: 4088)
- TextInputHost.exe (PID: 148)
- conhost.exe (PID: 8080)
- System.exe (PID: 7932)
- conhost.exe (PID: 8488)
- winrshost.exe (PID: 7164)
- System.exe (PID: 1084)
- csrss.exe (PID: 1512)
- uhssvc.exe (PID: 1492)
- winrshost.exe (PID: 3536)
- Memory Compression.exe (PID: 8844)
- slui.exe (PID: 6848)
- slui.exe (PID: 8232)
- conhost.exe (PID: 5484)
- winrshost.exe (PID: 3168)
- WmiPrvSE.exe (PID: 4784)
- slui.exe (PID: 4060)
- conhost.exe (PID: 6336)
- winrshost.exe (PID: 2228)
- TextInputHost.exe (PID: 864)
- conhost.exe (PID: 8408)
- csrss.exe (PID: 2684)
Create files in a temporary directory
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- conhost.exe (PID: 8916)
- conhost.exe (PID: 2364)
- conhost.exe (PID: 6172)
- conhost.exe (PID: 7748)
- conhost.exe (PID: 1908)
- conhost.exe (PID: 5044)
- conhost.exe (PID: 5676)
- conhost.exe (PID: 6852)
- conhost.exe (PID: 7244)
Drops script file
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 8368)
- powershell.exe (PID: 7304)
- powershell.exe (PID: 7340)
- cmd.exe (PID: 7104)
- powershell.exe (PID: 2328)
- powershell.exe (PID: 5664)
- powershell.exe (PID: 4800)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 6908)
- powershell.exe (PID: 2372)
- powershell.exe (PID: 6208)
- powershell.exe (PID: 4552)
- powershell.exe (PID: 5676)
- powershell.exe (PID: 5588)
- powershell.exe (PID: 6848)
- powershell.exe (PID: 7076)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 2896)
- powershell.exe (PID: 7432)
- powershell.exe (PID: 2780)
- powershell.exe (PID: 492)
- powershell.exe (PID: 5184)
- powershell.exe (PID: 2864)
- powershell.exe (PID: 1156)
- powershell.exe (PID: 6516)
- powershell.exe (PID: 1944)
- powershell.exe (PID: 7492)
- powershell.exe (PID: 3020)
- wscript.exe (PID: 5308)
- wscript.exe (PID: 7036)
- conhost.exe (PID: 8916)
- wscript.exe (PID: 6516)
- wscript.exe (PID: 8820)
- conhost.exe (PID: 2364)
- conhost.exe (PID: 6172)
- wscript.exe (PID: 7104)
- wscript.exe (PID: 6664)
- conhost.exe (PID: 7748)
- wscript.exe (PID: 3232)
- wscript.exe (PID: 2788)
- wscript.exe (PID: 7600)
- wscript.exe (PID: 6352)
- conhost.exe (PID: 1908)
- conhost.exe (PID: 5044)
- wscript.exe (PID: 3032)
- wscript.exe (PID: 7272)
- conhost.exe (PID: 5676)
- wscript.exe (PID: 4552)
- wscript.exe (PID: 7544)
- conhost.exe (PID: 6852)
- wscript.exe (PID: 6332)
- wscript.exe (PID: 4128)
- conhost.exe (PID: 7244)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2328)
- powershell.exe (PID: 7304)
- powershell.exe (PID: 5664)
- powershell.exe (PID: 5588)
- powershell.exe (PID: 4552)
- powershell.exe (PID: 5676)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 6848)
- powershell.exe (PID: 6908)
- powershell.exe (PID: 7340)
- powershell.exe (PID: 2372)
- powershell.exe (PID: 6208)
- powershell.exe (PID: 4800)
- powershell.exe (PID: 6516)
- powershell.exe (PID: 7492)
- powershell.exe (PID: 492)
- powershell.exe (PID: 7432)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 2896)
- powershell.exe (PID: 7076)
- powershell.exe (PID: 3020)
- powershell.exe (PID: 1944)
- powershell.exe (PID: 2864)
- powershell.exe (PID: 5184)
- powershell.exe (PID: 1156)
- powershell.exe (PID: 2780)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4800)
- powershell.exe (PID: 6208)
- powershell.exe (PID: 5664)
- powershell.exe (PID: 2328)
- powershell.exe (PID: 6908)
- powershell.exe (PID: 7304)
- powershell.exe (PID: 7340)
- powershell.exe (PID: 2372)
- powershell.exe (PID: 6848)
- powershell.exe (PID: 5676)
- powershell.exe (PID: 4552)
- powershell.exe (PID: 5588)
- powershell.exe (PID: 1324)
- powershell.exe (PID: 6516)
- powershell.exe (PID: 492)
- powershell.exe (PID: 2564)
- powershell.exe (PID: 1156)
- powershell.exe (PID: 2780)
- powershell.exe (PID: 3020)
- powershell.exe (PID: 7492)
- powershell.exe (PID: 7076)
- powershell.exe (PID: 2864)
- powershell.exe (PID: 5184)
- powershell.exe (PID: 2896)
- powershell.exe (PID: 7432)
- powershell.exe (PID: 1944)
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
Potential library load (Base64 Encoded 'LoadLibrary')
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
Found Base64 encoded reference to WMI classes (YARA)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
Potential dynamic function import (Base64 Encoded 'GetProcAddress')
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
There is functionality for taking screenshot (YARA)
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
.NET Reactor protector has been detected
- xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe (PID: 7672)
Disables trace logs
- conhost.exe (PID: 8916)
- conhost.exe (PID: 2364)
- conhost.exe (PID: 6172)
- conhost.exe (PID: 7748)
- conhost.exe (PID: 1908)
- conhost.exe (PID: 5044)
- conhost.exe (PID: 5676)
- conhost.exe (PID: 6852)
- conhost.exe (PID: 7244)
Checks proxy server information
- conhost.exe (PID: 8916)
- conhost.exe (PID: 2364)
- conhost.exe (PID: 6172)
- conhost.exe (PID: 7748)
- conhost.exe (PID: 1908)
- conhost.exe (PID: 5044)
- conhost.exe (PID: 5676)
- conhost.exe (PID: 6852)
- conhost.exe (PID: 7244)
- slui.exe (PID: 5392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
DcRat
(PID) Process(7672) xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe
C2 (1)http://batyatj6.beget.tech/a4f88cb8.php
Options
PluginConfigs
ebf1c8a624aad5a504024645c9bfb8dac03df9a9
systemattrTrue
hiddenattrTrue
cleariconTrue
randomversioninfoTrue
2d421f511019ab10b4005cadf6e8fab088ff728d
customexts
zcashFalse
exodusFalse
electrumFalse
moneroFalse
ethereumFalse
bytecoinFalse
litecoincoreFalse
dashcoreFalse
bitcoincoreFalse
atomicFalse
armoryFalse
binanceFalse
metamaskTrue
tronlinkTrue
roninTrue
binancewebTrue
phantomTrue
tonTrue
yoroiTrue
extscanschemeCurrent User
5a5179f1dd43b9144a917e744c408409444d73dd
HighlightedWindowslogin;bank;transfer;pay;secure payment;crypto
SaveScheme0
SavePeriod15
AutoStartTrue
ProcessKiller
processesmbsetup
kts21
avast_
antivirus
mcafee
bitdefender
360ts
avira_
ns-esd
nortonsecurity
windowseset
avast
kaspersky
drweb
antivirus
антивирус
norton security
grizzly
malwarebytes
bullguard
bitdefender
windows defender
защитник windows
360 total
mcafee
WindowsDefenderExcluder
workschemeSystem Drive
MutexscPm5u8iQSQ0SskS2aEg
Debugfalse
ServerConfigReplacementTable
1@
2,
5_
6(
9&
y~
i;
k!
d*
p
I-
R|
H>
o`
M.
Z#
N%
W)
C<
E^
T$
PluginConfigReplacementTable
0(
1;
2*
3.
4^
T
J%
U&
B#
Q)
D`
h$
V<
X_
Z@
k~
m!
n>
F,
t-
R|
GetWebcamsfalse
SleepTimeout5
InactivityTimeout2
CacheStorageRegistry
AutoRunFull
StealerConfig
savebrowsersdatatosinglefilefalse
ignorepartiallyemptydatatrue
cookiestrue
passwordstrue
formstrue
cctrue
historytrue
telegramtrue
steamtrue
discordtrue
filezillatrue
screenshottrue
clipboardtrue
sysinfotrue
searchpath%SystemDrive% - Slow
StealerEnabledtrue
StealerOptionsfalse
SelfDeletefalse
Plugins (15)TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDALdiv2IAAAAAAAAAAOAAIiALAQgAAEYBAAAGAAAAAAAAnmUBAAAgAAAAgAEAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADAAQAAAgAA4rEBAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAG16FmEAAAAAAAAAAOAAAiELAQsAAAgAAAAGAAAAAAAAviYAAAAgAAAAQAAAAAAAEAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAACAAAAAAgAAAAAAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAGW2kWEAAAAAAAAAAOAAIiALAQgAAJAAAAAIAAAAAAAAzq8AAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAAAAAAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDABDFxWIAAAAAAAAAAOAAIiALAQgAAPoAAAAGAAAAAAAAbhgBAAAgAAAAIAEAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAABgAQAAAgAAdI8BAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAHf1pWEAAAAAAAAAAOAAAiELAQsAAAYAAAAGAAAAAAAAniQAAAAgAAAAQAAAAAAAEAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAACAAAAAAgAAAAAAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAG+fi2IAAAAAAAAAAOAAAiELAQgAAJIAAAAGAAAAAAAAbrEAAAAgAAAAwAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAAAQAAAgAA7/UAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDANIylmEAAAAAAAAAAOAAAiELAQgAADoAAAAGAAAAAAAArlgAAAAgAAAAYAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAACgAAAAAgAAAAAAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAMZzT2IAAAAAAAAAAOAAAiELAQgAAE4AAAAGAAAAAAAAbmwAAAAgAAAAgAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADAAAAAAgAAs5AAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAM1Ro2IAAAAAAAAAAOAAAiELAQgAAKwAAAAGAAAAAAAA/skAAAAgAAAA4AAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAAAgAQAAAgAAp3sBAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAGi6/WEAAAAAAAAAAOAAAiELAQgAAFwAAAAGAAAAAAAAbnsAAAAgAAAAgAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADAAAAAAgAAAAAAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAHlZ42EAAAAAAAAAAOAAAiELAQgAAFoAAAAGAAAAAAAATnkAAAAgAAAAgAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADAAAAAAgAAgCIBAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDADgl2mEAAAAAAAAAAOAAAiELAQgAADoAAAAGAAAAAAAATlgAAAAgAAAAYAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAACgAAAAAgAAbt8AAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDALbDE2EAAAAAAAAAAOAAAiELAQsAAAgAAAAGAAAAAAAAviYAAAAgAAAAQAAAAAAAEAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAACAAAAAAgAAAAAAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAAL3tWEAAAAAAAAAAOAAIiALAQgAAFAAAAAGAAAAAAAA/m4AAAAgAAAAgAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADAAAAAAgAAAAAAAAMAQIUA...
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAgAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAABQRQAATAEDAMsjhWIAAAAAAAAAAOAAAiELAQgAAFIAAAAGAAAAAAAAHnEAAAAgAAAAgAAAAABAAAAgAAAAAgAABAAAAAAAAAAEAAAAAAAAAADAAAAAAgAAo98AAAMAQIUA...
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:07:13 22:47:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 104448 |
| InitializedDataSize: | 1668096 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcd2f |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.15.2.0 |
| ProductVersionNumber: | 5.15.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileVersion: | 5.15.2.0 |
| OriginalFileName: | libGLESv2.dll |
| ProductName: | libGLESv2 |
| ProductVersion: | 5.15.2.0 |
Total processes
325
Monitored processes
179
Malicious processes
30
Suspicious processes
48
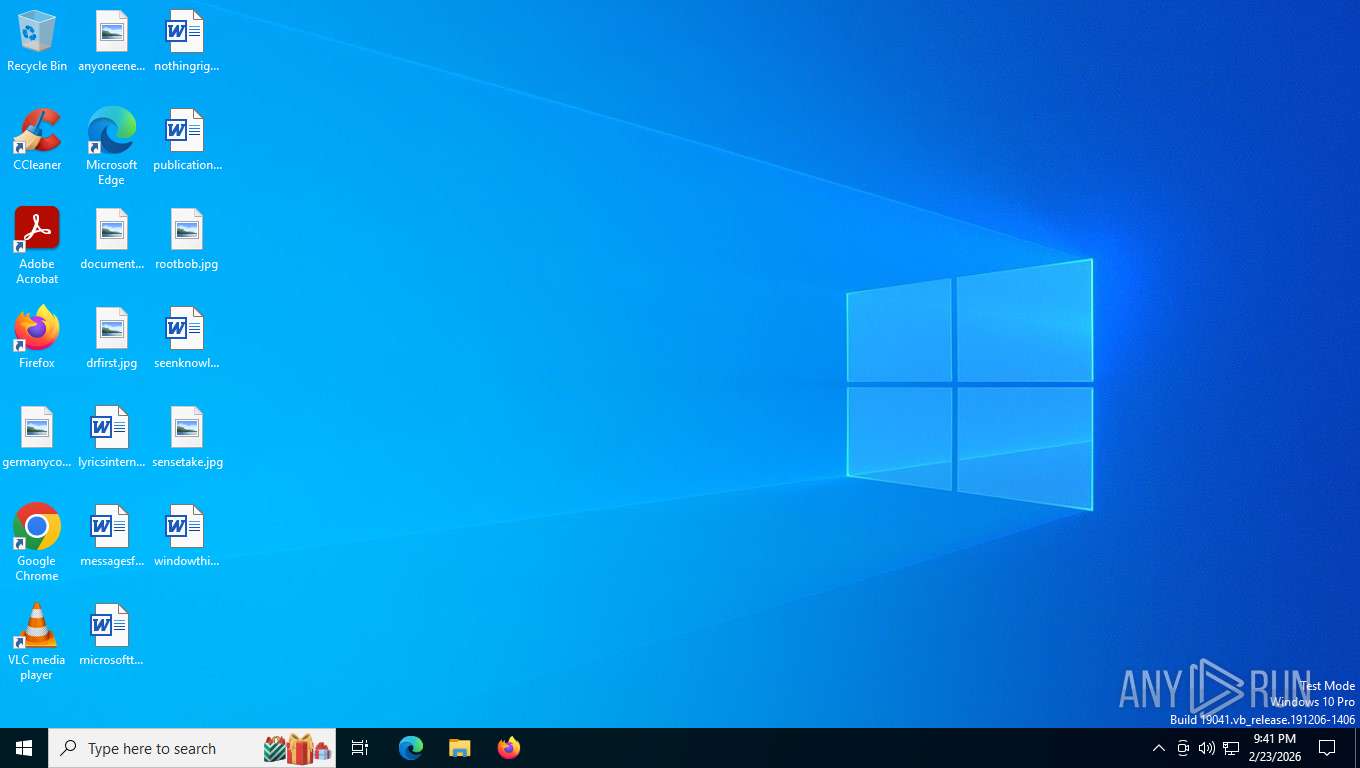
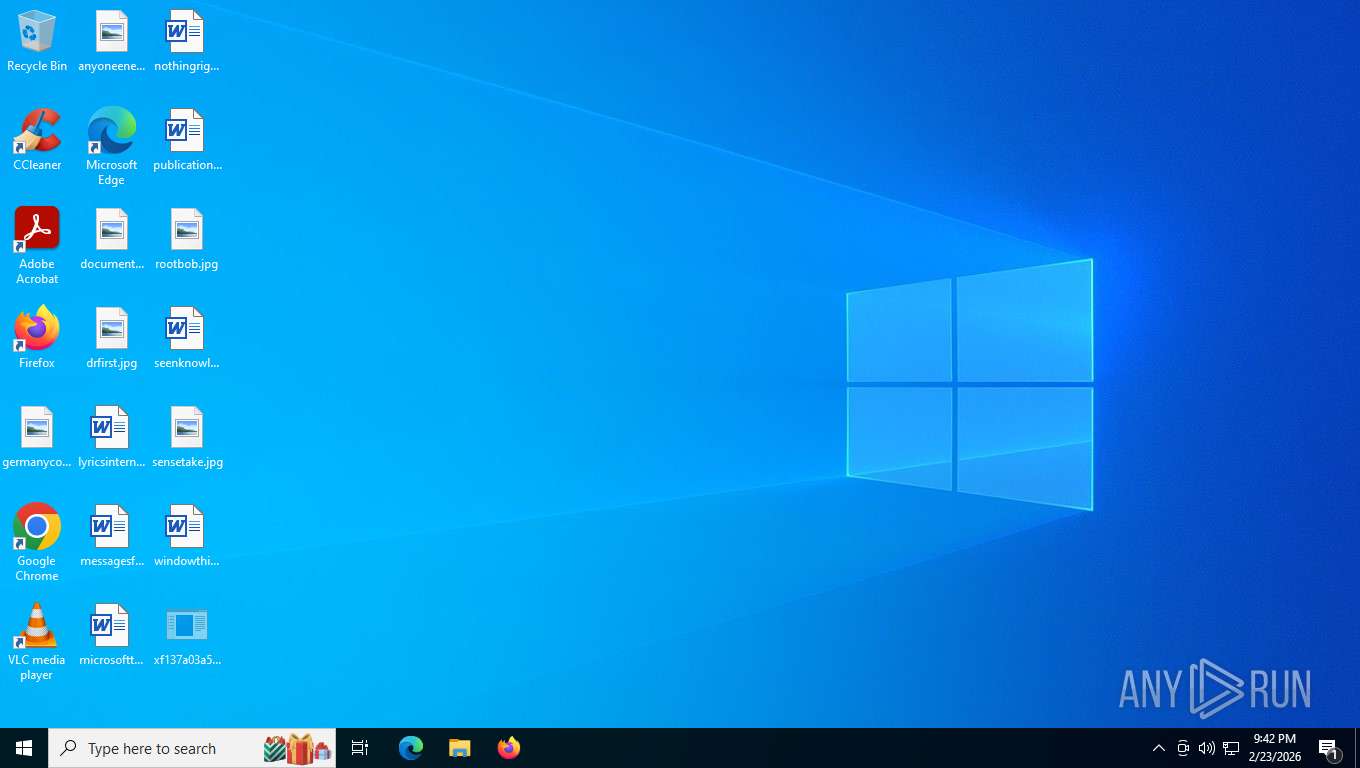
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Program Files\Windows Mail\en-US\TextInputHost.exe" | C:\Program Files\Windows Mail\en-US\TextInputHost.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.15.2.0 Modules
| |||||||||||||||
| 492 | "powershell" -Command Add-MpPreference -ExclusionPath 'C:/Windows/' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 552 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | schtasks.exe /create /tn "sluis" /sc MINUTE /mo 14 /tr "'C:\Windows\Installer\{420AE50D-8B07-4845-8592-3BECCD71DE80}\slui.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | "C:\Program Files\Windows Mail\en-US\TextInputHost.exe" | C:\Program Files\Windows Mail\en-US\TextInputHost.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.15.2.0 Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Microsoft Office\root\Office16\FPA_FA000000064\System.exe" | C:\Program Files\Microsoft Office\root\Office16\FPA_FA000000064\System.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 5.15.2.0 Modules
| |||||||||||||||
| 1156 | "powershell" -Command Add-MpPreference -ExclusionPath 'C:/' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "powershell" -Command Add-MpPreference -ExclusionPath 'C:/found.000/' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1344 | schtasks.exe /create /tn "winlogonw" /sc MINUTE /mo 6 /tr "'C:\Program Files (x86)\Microsoft\EdgeUpdate\Install\{2D098B61-807D-4808-BCF8-B8EA9C81B412}\winlogon.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
166 307
Read events
166 182
Write events
125
Delete events
0
Modification events
| (PID) Process: | (6544) xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (8368) xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (8368) xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
| (PID) Process: | (8368) xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | PromptOnSecureDesktop |
Value: 0 | |||
| (PID) Process: | (8368) xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | StartMenuExperienceHost |
Value: "C:\found.000\dir_00000002.chk\StartMenuExperienceHost.exe" | |||
| (PID) Process: | (8368) xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | StartMenuExperienceHost |
Value: "C:\found.000\dir_00000002.chk\StartMenuExperienceHost.exe" | |||
| (PID) Process: | (8368) xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | winlogon |
Value: "C:\Program Files (x86)\Microsoft\EdgeUpdate\Install\{2D098B61-807D-4808-BCF8-B8EA9C81B412}\winlogon.exe" | |||
| (PID) Process: | (8368) xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | winlogon |
Value: "C:\Program Files (x86)\Microsoft\EdgeUpdate\Install\{2D098B61-807D-4808-BCF8-B8EA9C81B412}\winlogon.exe" | |||
| (PID) Process: | (8368) xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000000000000000000000 | |||
| (PID) Process: | (8368) xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\18331a31f20a7b6fcdb841aef9e9c4760bf533f8 |
| Operation: | write | Name: | 539bf7534690e9c69b5832ad5f180b0d49182e69 |
Value: WyJDOlxcVXNlcnNcXGFkbWluXFxEZXNrdG9wXFx4ZjEzN2EwM2E1YWQyNDVkM2YwMjkxYzMxNTg3YzFlMmIxYmEzMTM5NmMwYTEyZmMxMzhlYjE1ZGVkZWMyYzhjZC5leGUiLCJDOlxcZm91bmQuMDAwXFxkaXJfMDAwMDAwMDIuY2hrXFxTdGFydE1lbnVFeHBlcmllbmNlSG9zdC5leGUiLCJDOlxcUHJvZ3JhbSBGaWxlcyAoeDg2KVxcTWljcm9zb2Z0XFxFZGdlVXBkYXRlXFxJbnN0YWxsXFx7MkQwOThCNjEtODA3RC00ODA4LUJDRjgtQjhFQTlDODFCNDEyfVxcd2lubG9nb24uZXhlIl0= | |||
Executable files
22
Suspicious files
0
Text files
0
Unknown types
150
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8368 | xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | — | ||
MD5:— | SHA256:— | |||
| 8368 | xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | C:\found.000\dir_00000002.chk\RCX71F4.tmp | binary | |
MD5:99B83A1CFA03748CDFE8BDD9040FA95C | SHA256:F1E2DB2750316B2E323E4D17560E27441D8E04B42171F94C950355E3314F1E2E | |||
| 8368 | xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | C:\Program Files (x86)\Microsoft\EdgeUpdate\Install\{2D098B61-807D-4808-BCF8-B8EA9C81B412}\winlogon.exe | executable | |
MD5:0BF814FF7DA8AC61D3BA49E35C2F1B17 | SHA256:F137A03A5AD245D3F0291C31587C1E2B1BA31396C0A12FC138EB15DEDEC2C8CD | |||
| 8368 | xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | C:\Program Files (x86)\Microsoft\EdgeUpdate\Install\{2D098B61-807D-4808-BCF8-B8EA9C81B412}\cc11b995f2a76d | binary | |
MD5:2881E7F47AD762095BEABB0A7AD37406 | SHA256:80BD5030BE3BA38DAE9C3DCD7112B0E52B173D78EA8EA9241BF72D8C338E84A8 | |||
| 8368 | xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | C:\Program Files (x86)\Microsoft\EdgeUpdate\Install\{2D098B61-807D-4808-BCF8-B8EA9C81B412}\RCX74F3.tmp | binary | |
MD5:20102C9DAA877B27797F31FDF56B083F | SHA256:A6033F61511817EFD27EE32D1CA2EA86ABF205780215C3538482277E067901C2 | |||
| 8368 | xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | C:\Users\admin\AppData\Local\Temp\5NgynF79py.bat | binary | |
MD5:FCAE15F4B512ECADBCBA7EB84A1EE112 | SHA256:364509AA0E7CDA9A046DA1840C6ADEBD171BBB2427B24D06F5E3661F28FD5C63 | |||
| 8368 | xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | C:\Users\admin\Desktop\RCX6FD0.tmp | binary | |
MD5:3DC7906AE5BBA782649EB685F1F0F62F | SHA256:02B18E7383862C1EDEF58B39E0BC43FC82C9B2370830B2A1C56B3C470F32B3D8 | |||
| 7304 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bjurtmic.egt.ps1 | binary | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8368 | xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | C:\Users\admin\AppData\Local\Temp\AxUrIXgib8 | binary | |
MD5:5B64A8821A915C054ECD5117498371DE | SHA256:774345DF9E44928282CA00651AB1BF868AE0CC8ABCD0C412F8EE2AE879E41283 | |||
| 8368 | xf137a03a5ad245d3f0291c31587c1e2b1ba31396c0a12fc138eb15dedec2c8cd.exe | C:\found.000\dir_00000002.chk\RCX7272.tmp | binary | |
MD5:99B83A1CFA03748CDFE8BDD9040FA95C | SHA256:F1E2DB2750316B2E323E4D17560E27441D8E04B42171F94C950355E3314F1E2E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
55
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1672 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
9080 | svchost.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1672 | SIHClient.exe | GET | 200 | 135.232.92.97:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
9080 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8628 | RUXIMICS.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
356 | svchost.exe | POST | 200 | 20.190.159.71:443 | https://login.live.com/RST2.srf | unknown | — | 11.1 Kb | whitelisted |
1672 | SIHClient.exe | GET | 200 | 135.232.92.137:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.160.14:443 | https://login.live.com/RST2.srf | unknown | binary | 11.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 184.86.251.27:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 92.123.104.59:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
9080 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8628 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
9080 | svchost.exe | 2.16.164.49:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |