| File name: | asdw.exe |
| Full analysis: | https://app.any.run/tasks/346f9bbe-270d-41d6-8e0f-af8e14ae6dff |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | June 01, 2025, 23:34:59 |
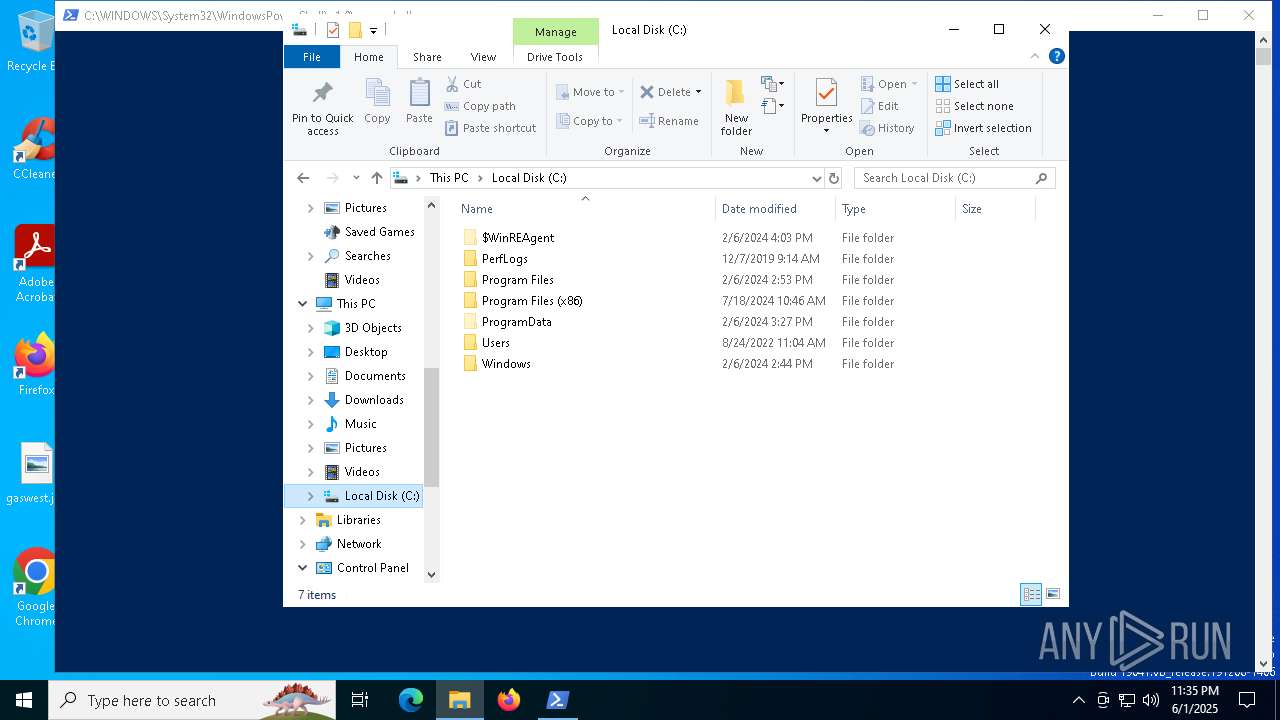
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 273DEECED80114C614F7816DD9EC10E3 |
| SHA1: | 3E7560F804CDA031C5A391A27BE87A24F89CF3EA |
| SHA256: | F12437C44AD0E58F9969D86B1DDD694CC184CAD3AF191E168CC4D01C6790B59F |
| SSDEEP: | 98304:0jWY/H8uBJNEDdtacygggWjCz0ss5iuMhw251nGTgSdEV6mSsCTnLmv5LbJ4eNwZ:kBuB |
MALICIOUS
TROX has been detected
- asdw.exe (PID: 8012)
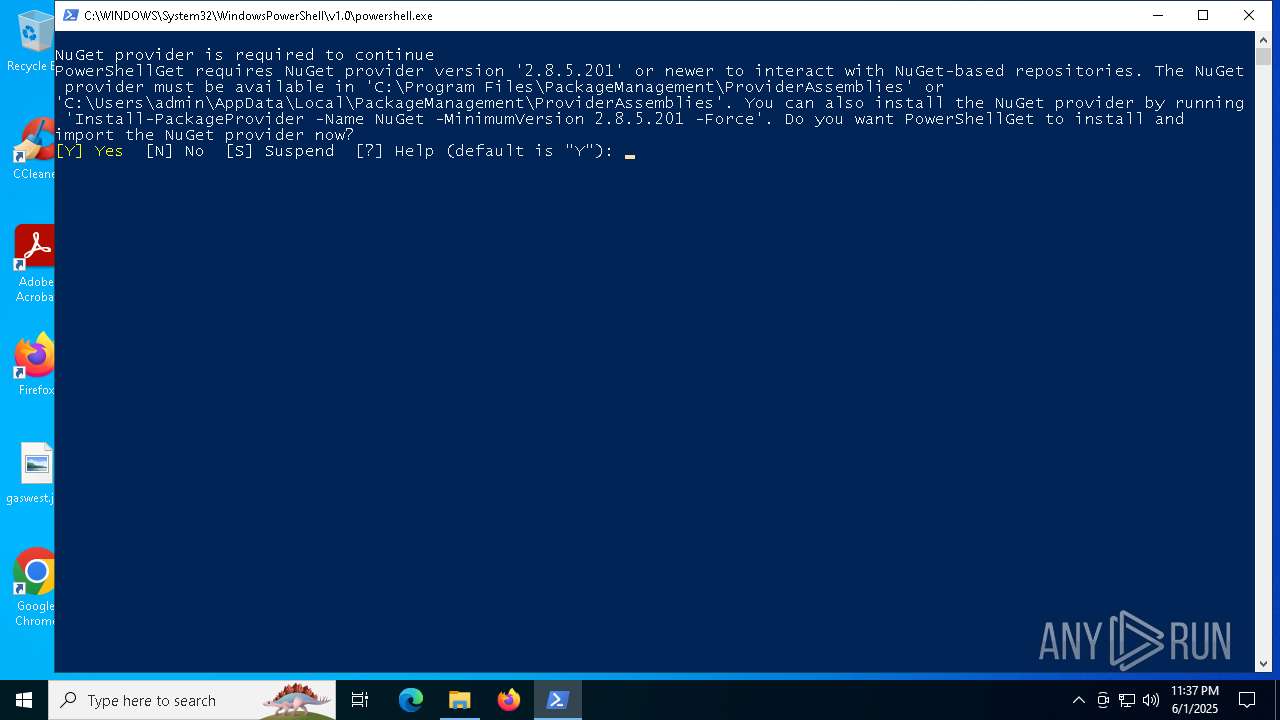
Bypass execution policy to execute commands
- powershell.exe (PID: 2616)
Changes powershell execution policy (Bypass)
- amp.exe (PID: 3208)
SUSPICIOUS
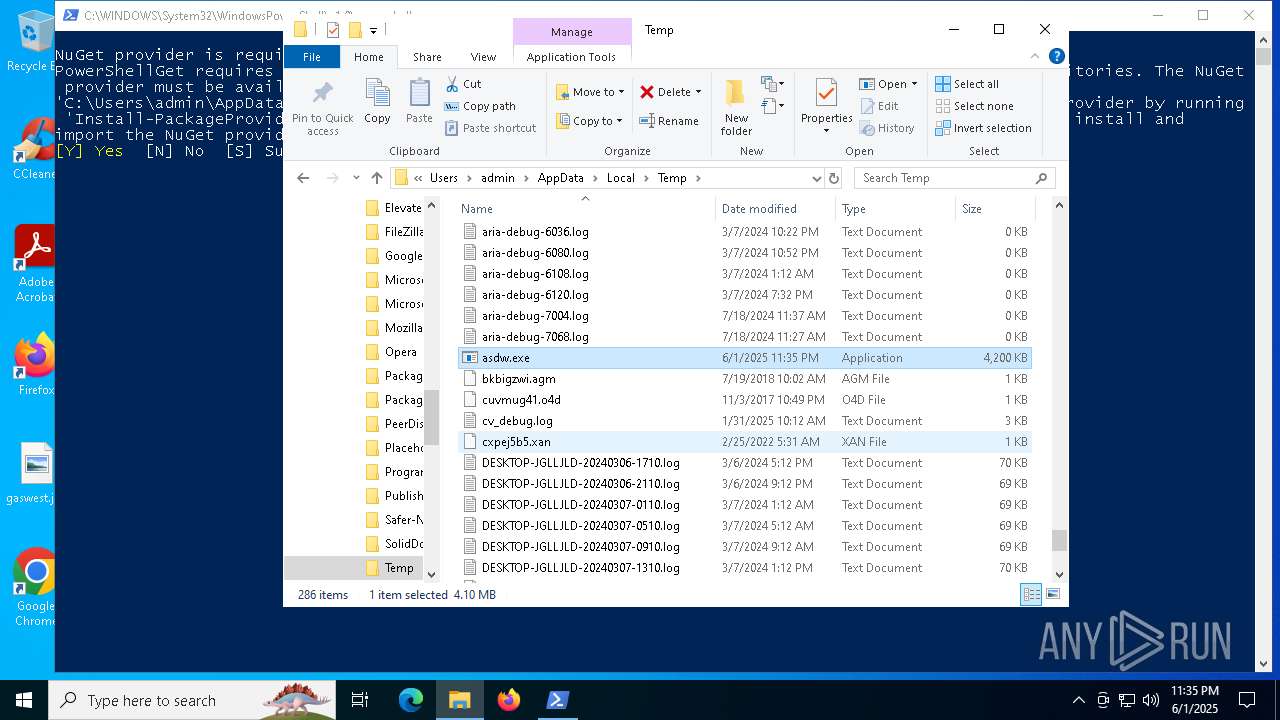
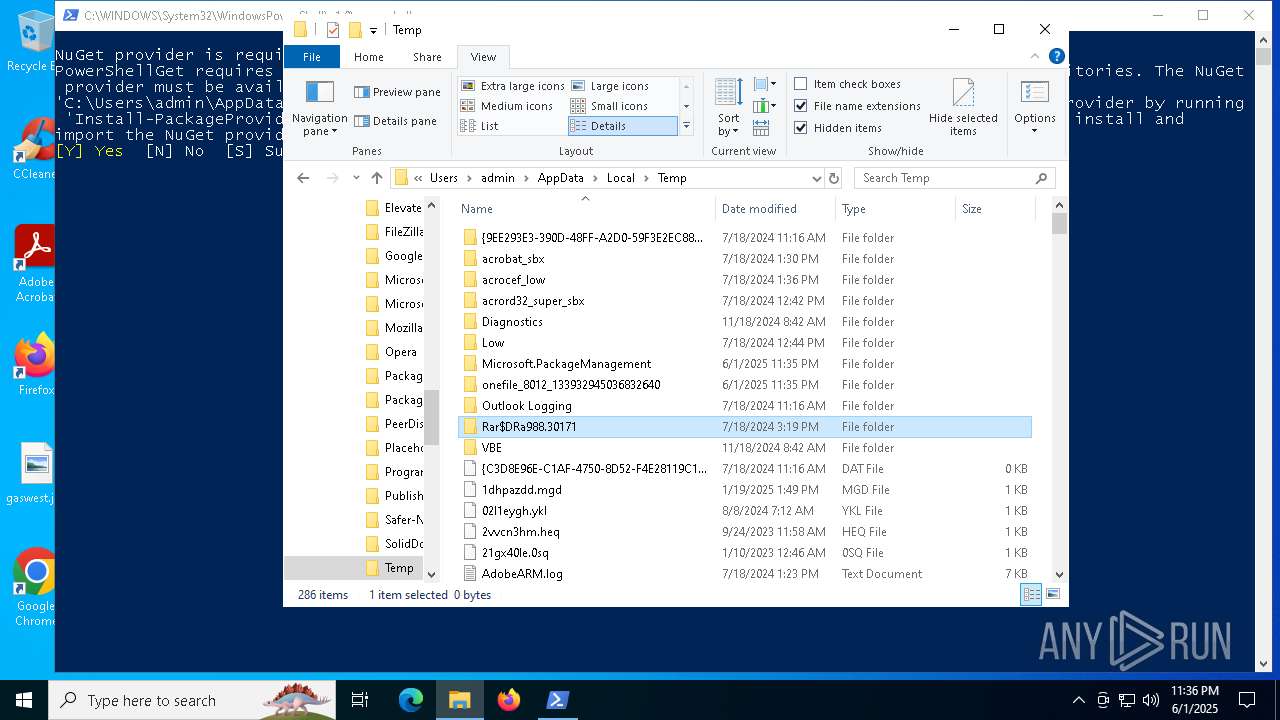
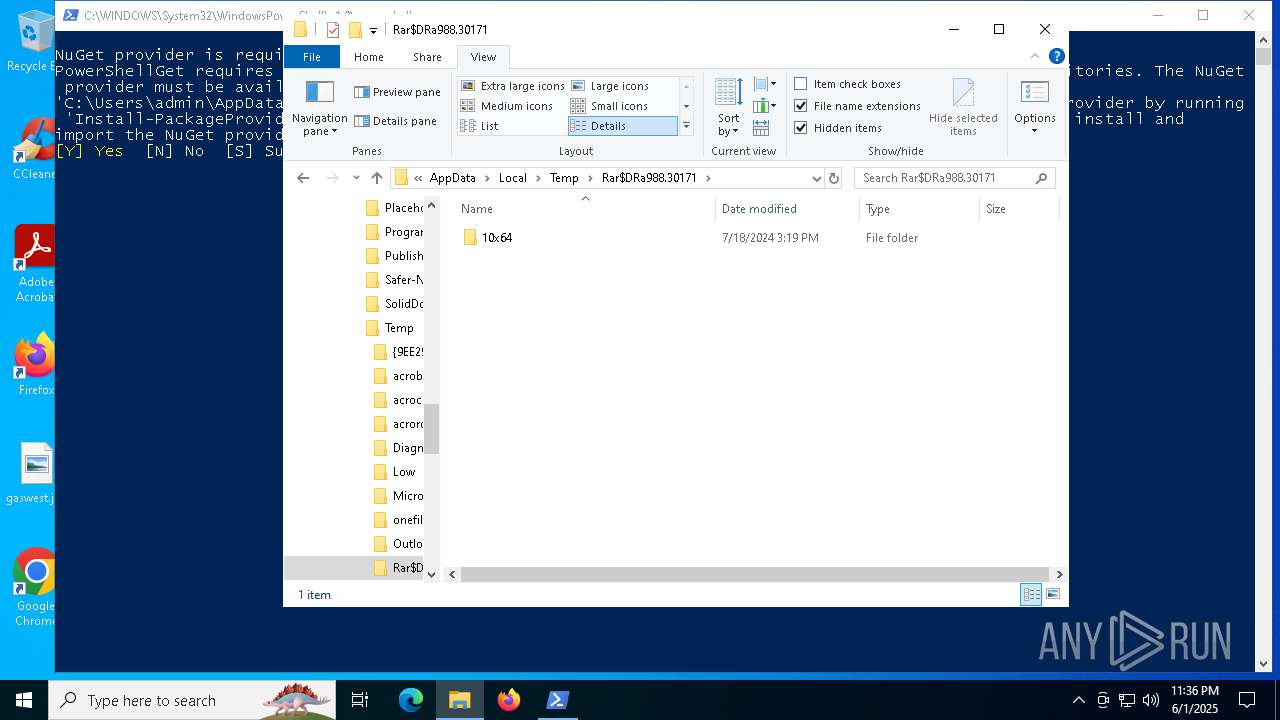
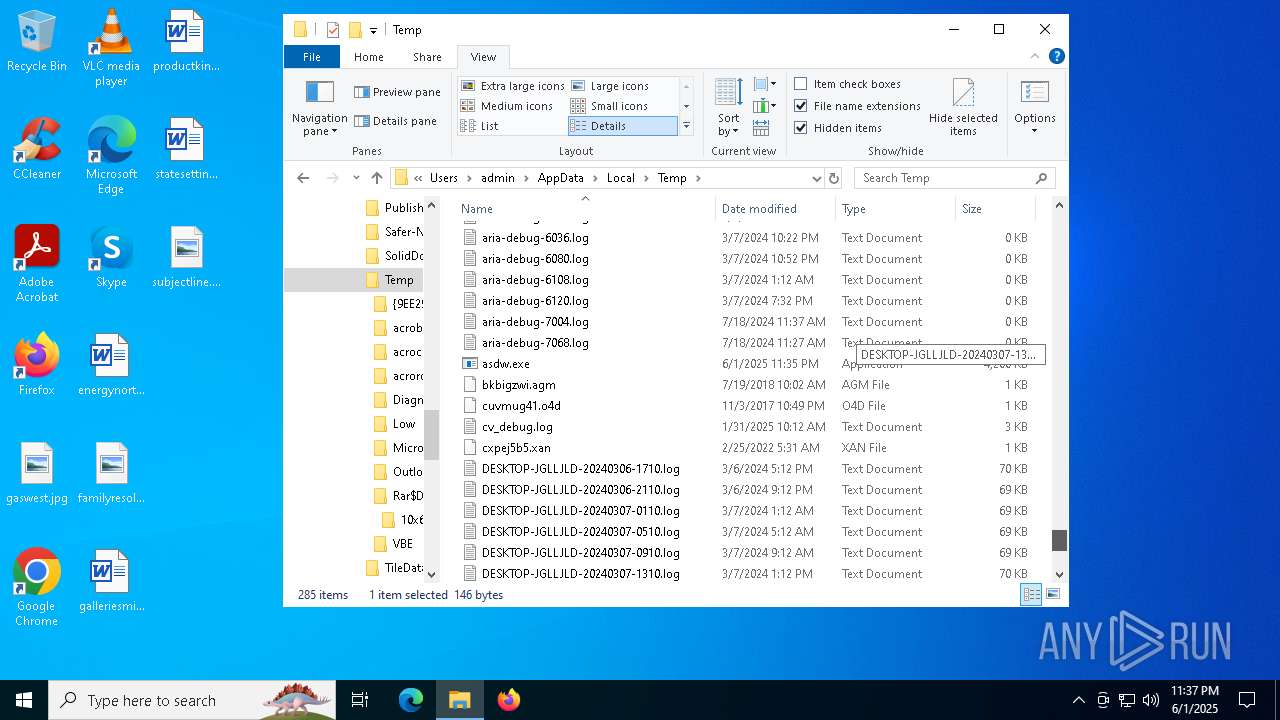
Executable content was dropped or overwritten
- asdw.exe (PID: 8012)
- csc.exe (PID: 7036)
- powershell.exe (PID: 2616)
Loads Python modules
- amp.exe (PID: 3208)
Process drops python dynamic module
- asdw.exe (PID: 8012)
Process drops legitimate windows executable
- asdw.exe (PID: 8012)
- powershell.exe (PID: 2616)
The process drops C-runtime libraries
- asdw.exe (PID: 8012)
CSC.EXE is used to compile C# code
- csc.exe (PID: 7036)
Starts POWERSHELL.EXE for commands execution
- amp.exe (PID: 3208)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 2616)
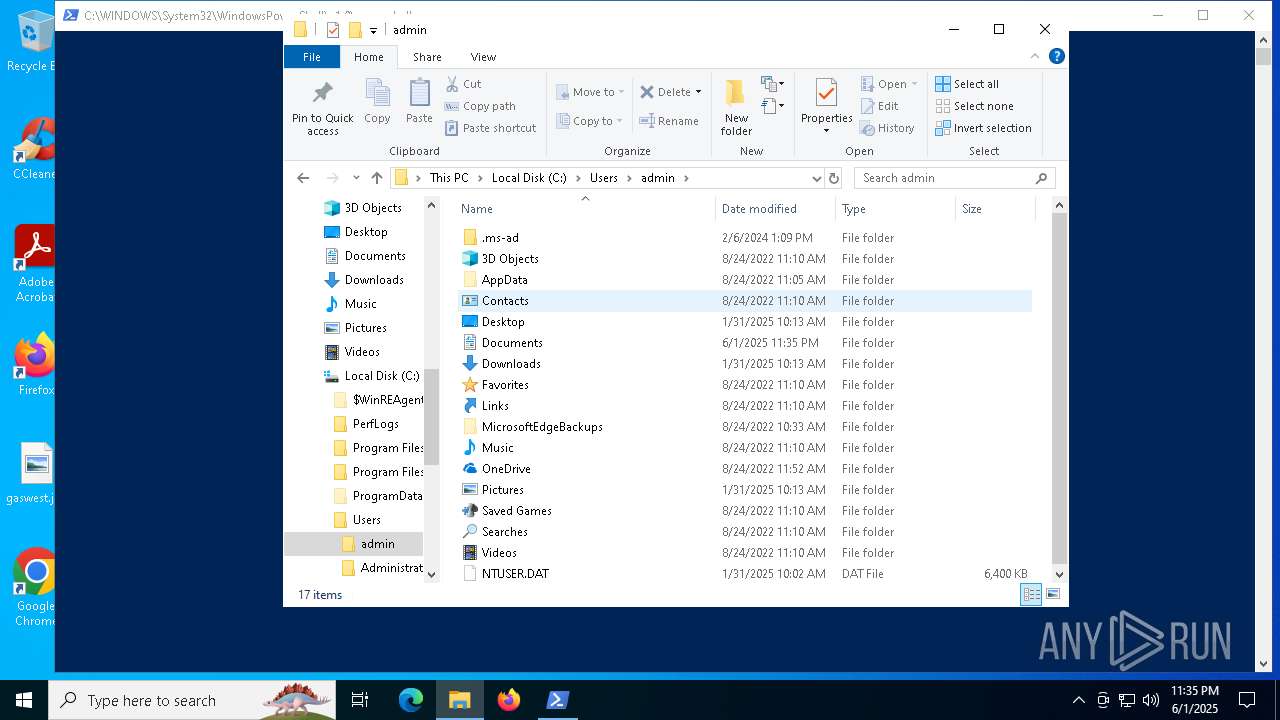
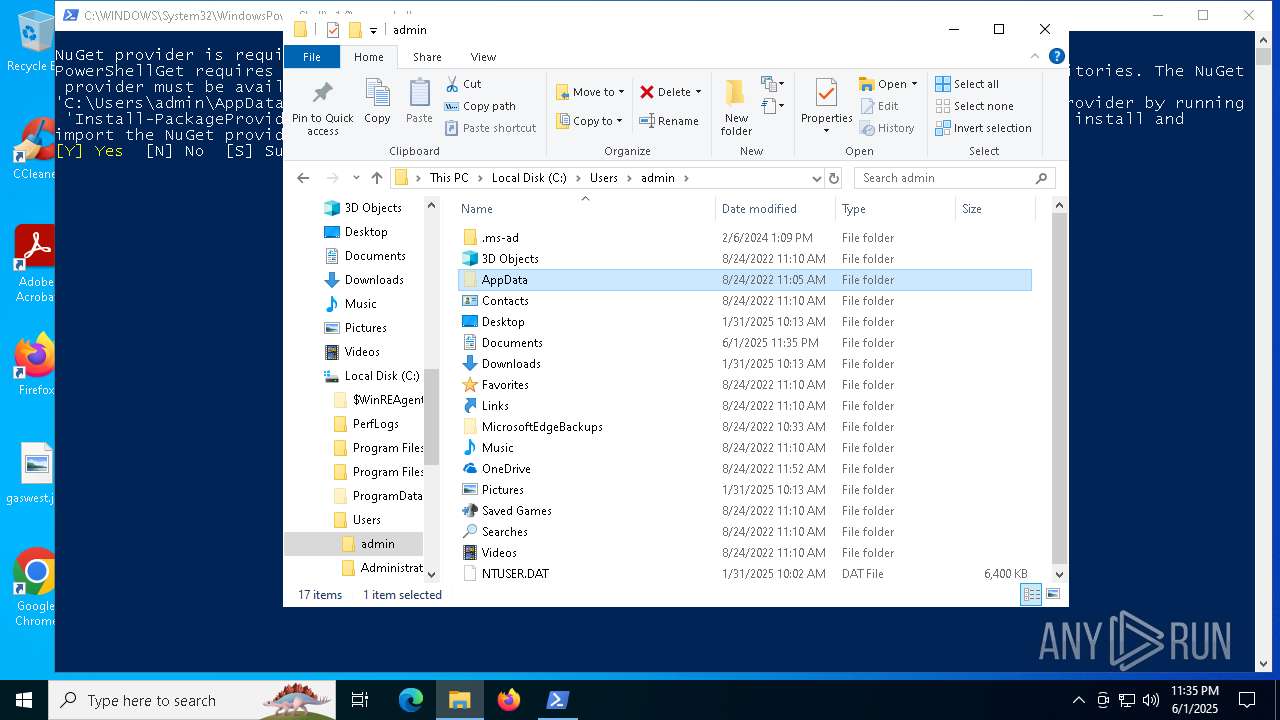
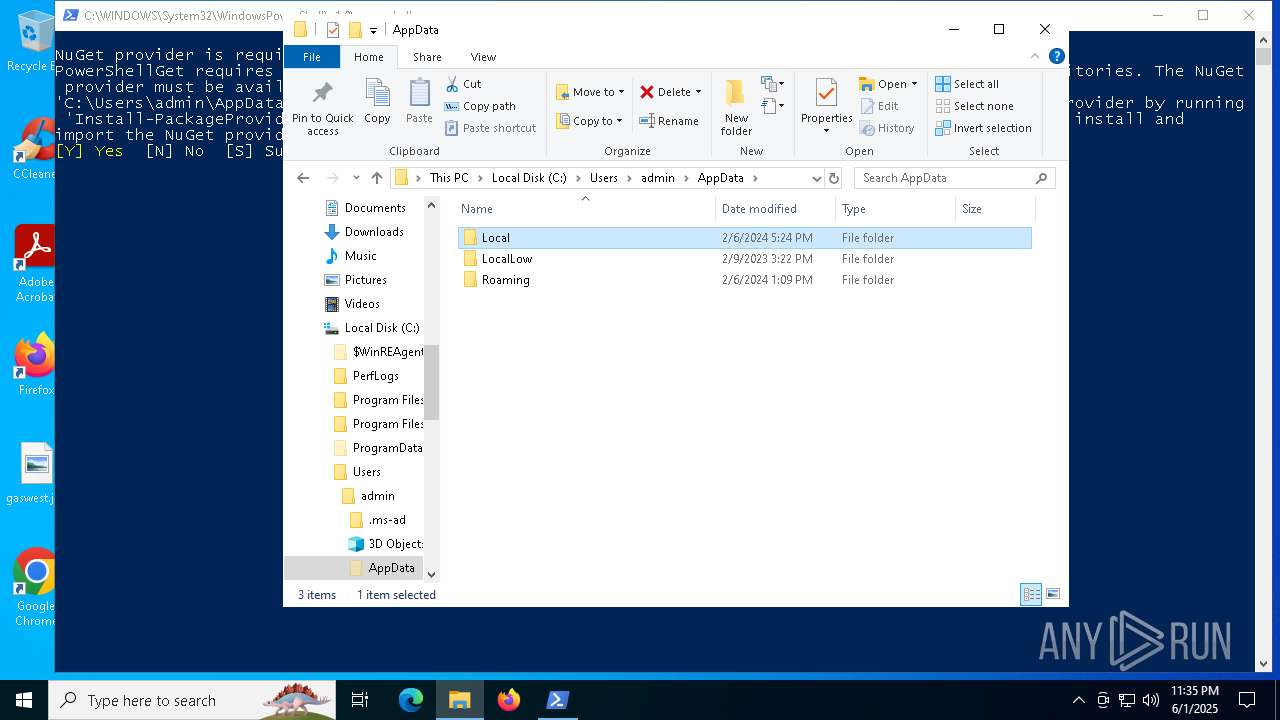
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 2616)
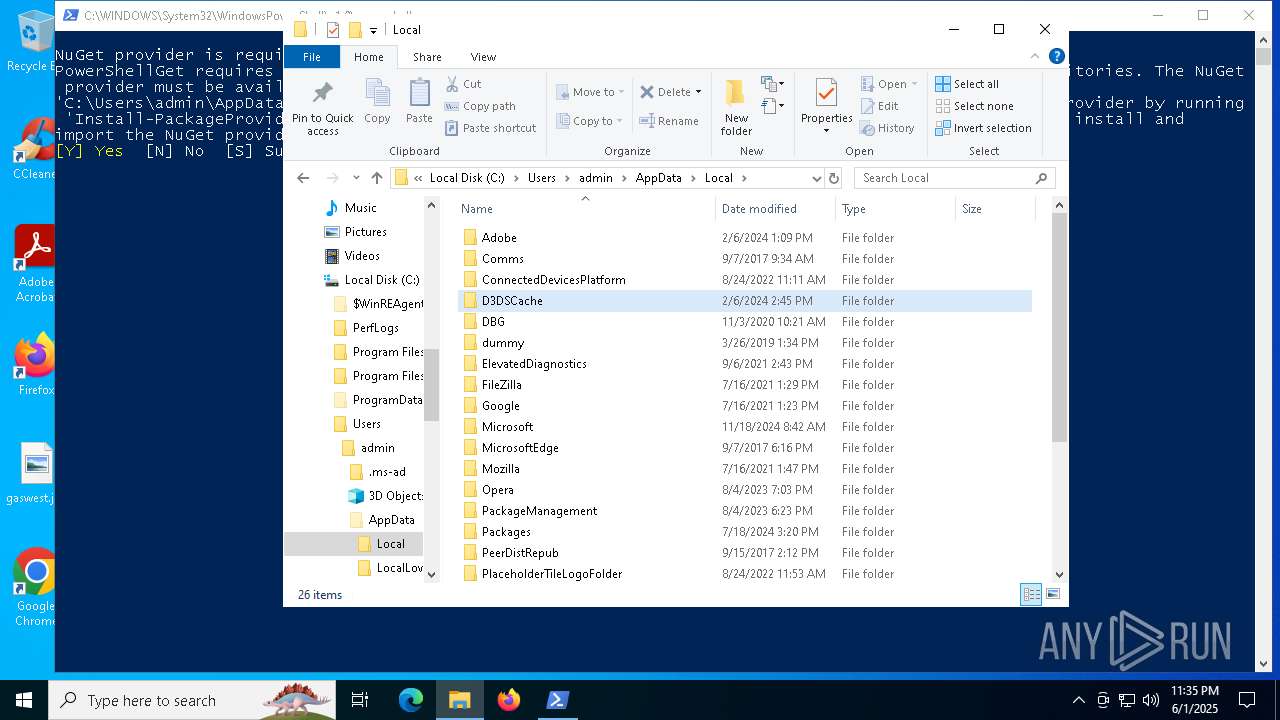
Installs module (POWERSHELL)
- powershell.exe (PID: 2616)
INFO
Checks supported languages
- asdw.exe (PID: 8012)
- amp.exe (PID: 3208)
- csc.exe (PID: 7036)
- cvtres.exe (PID: 2504)
The sample compiled with english language support
- asdw.exe (PID: 8012)
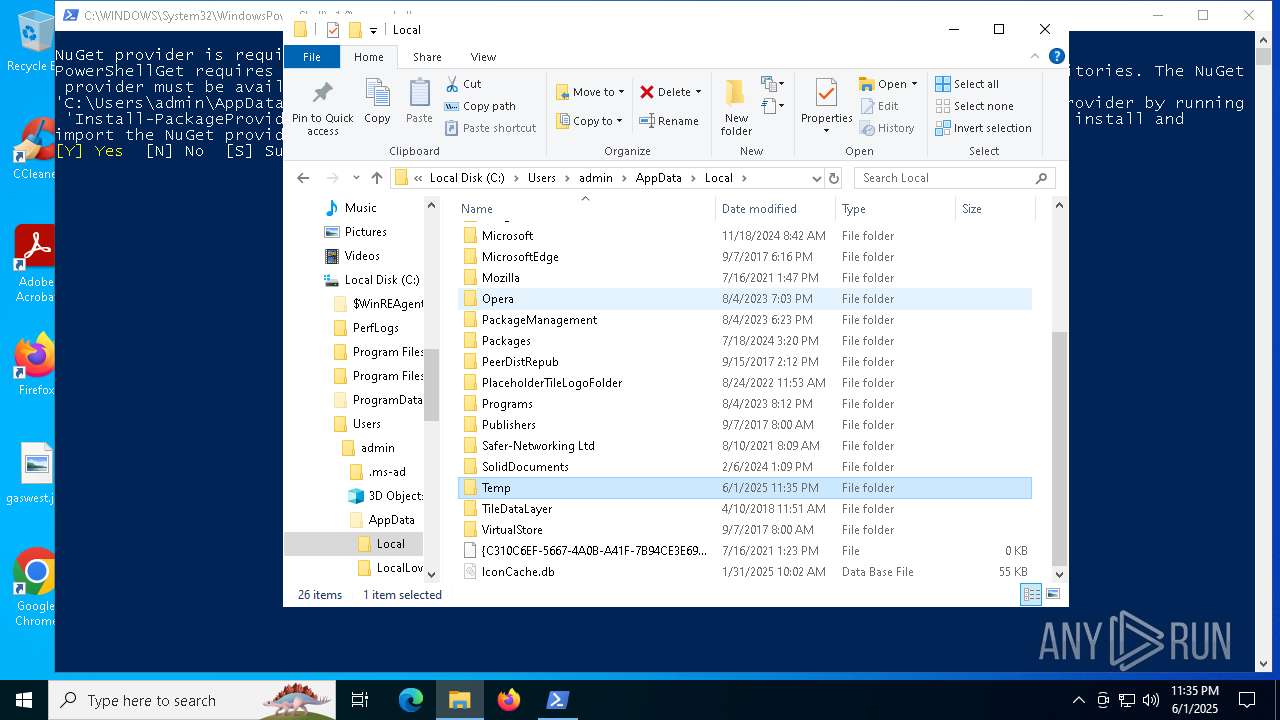
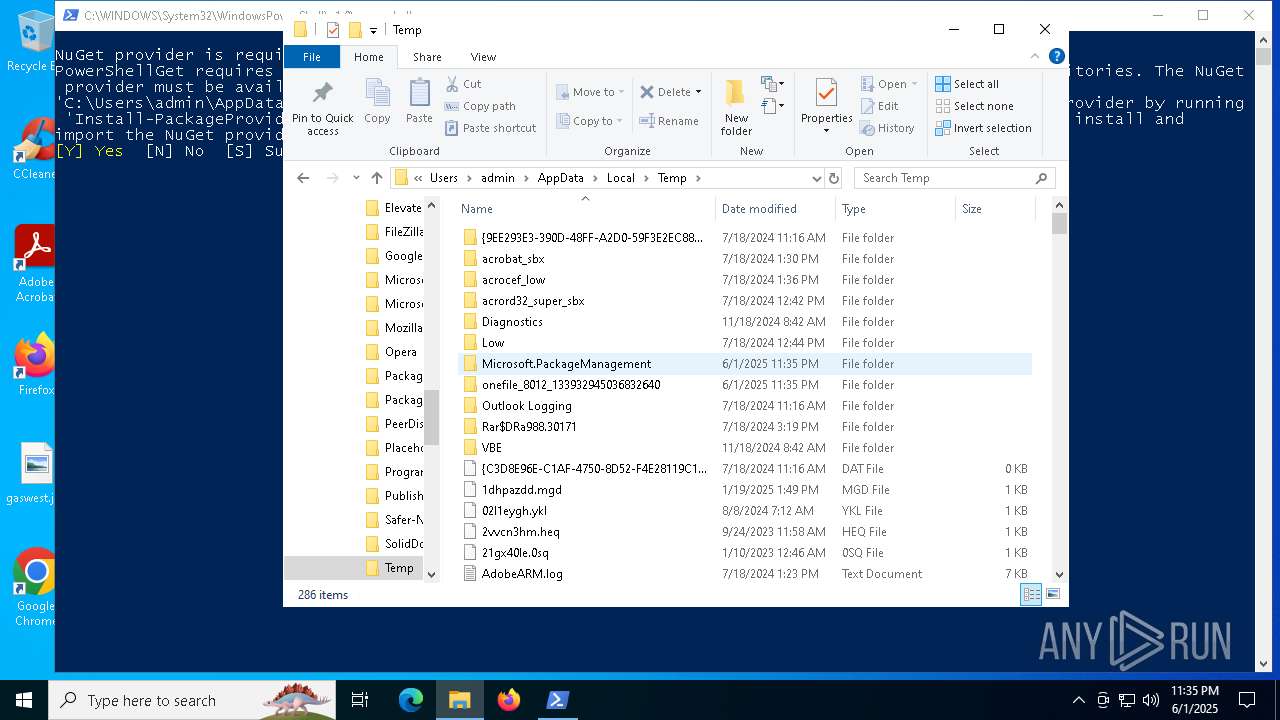
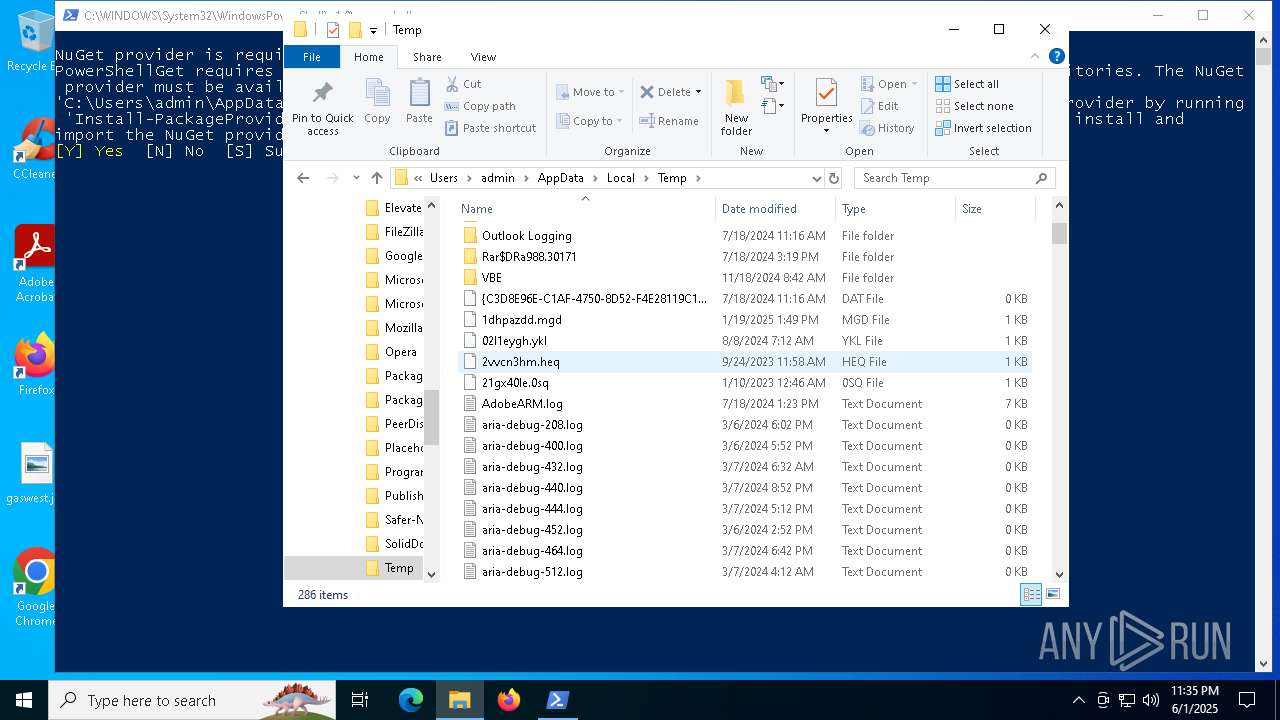
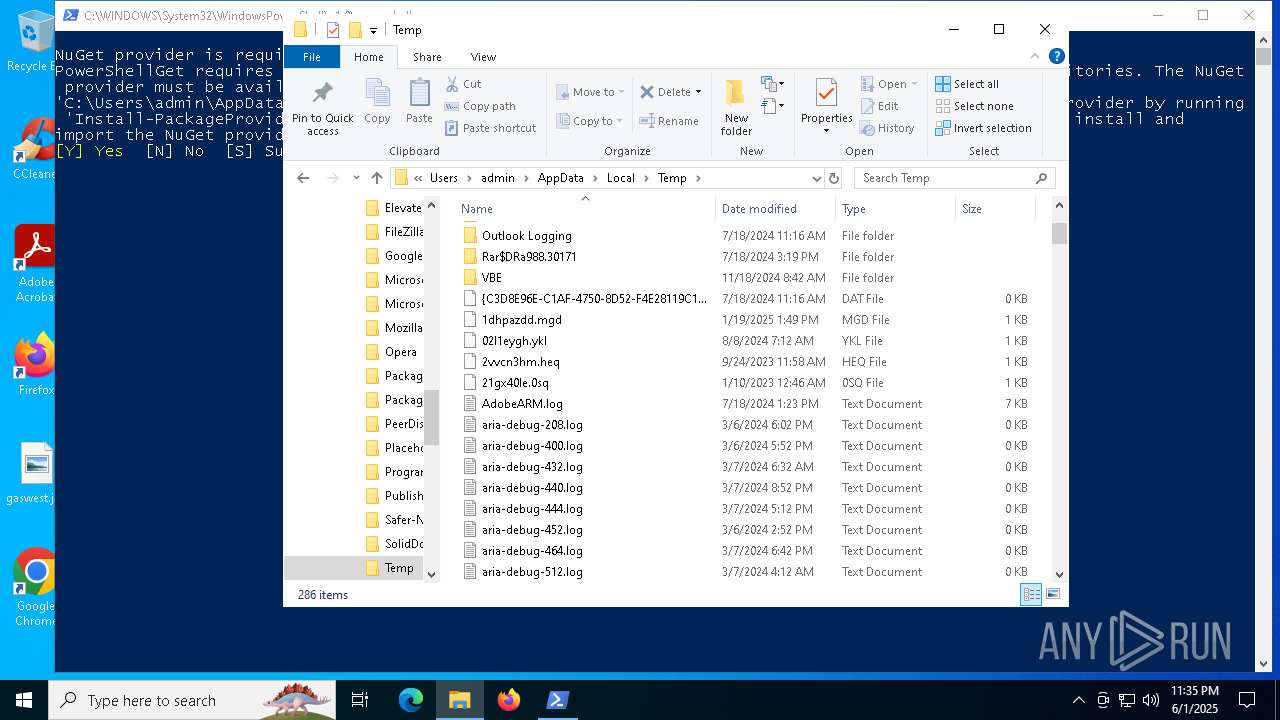
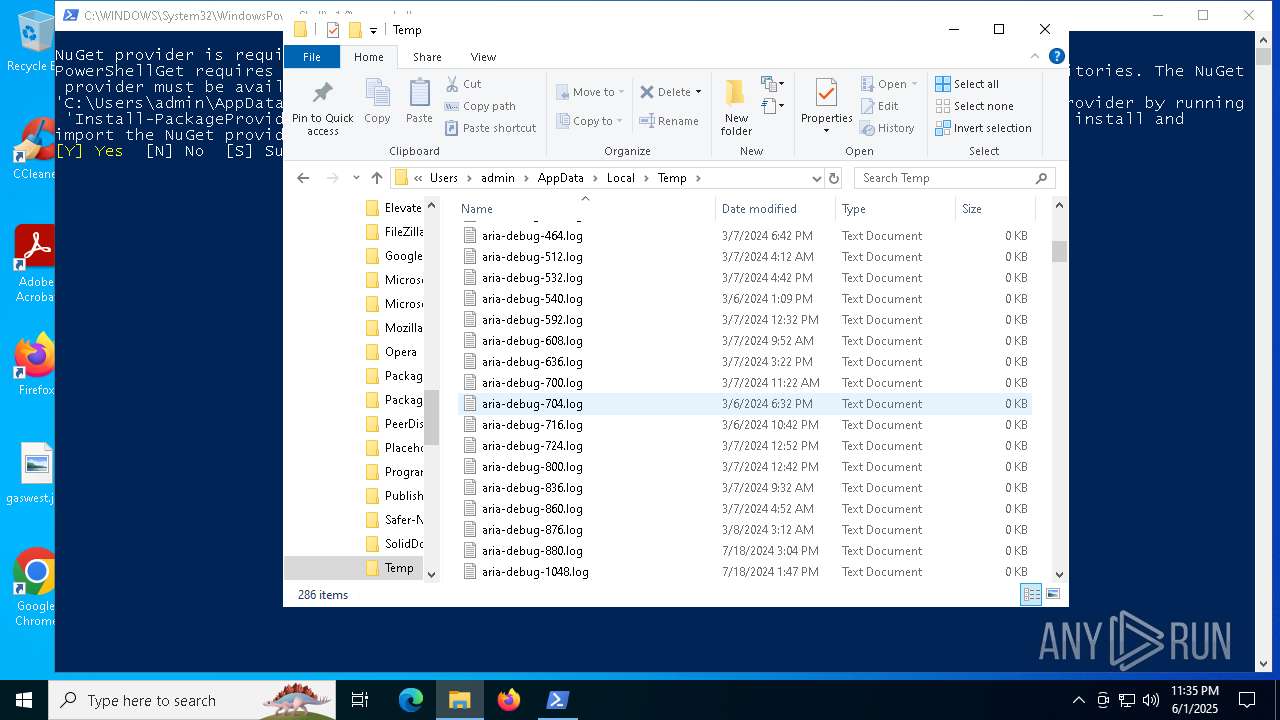
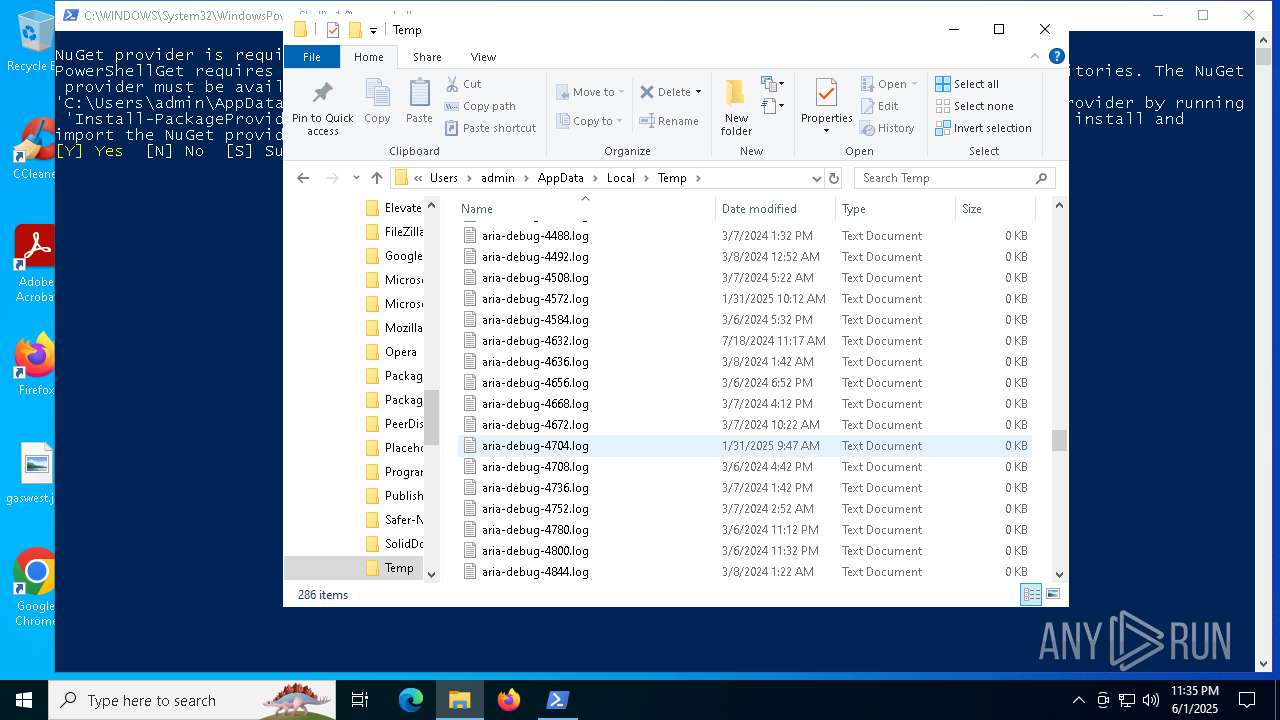
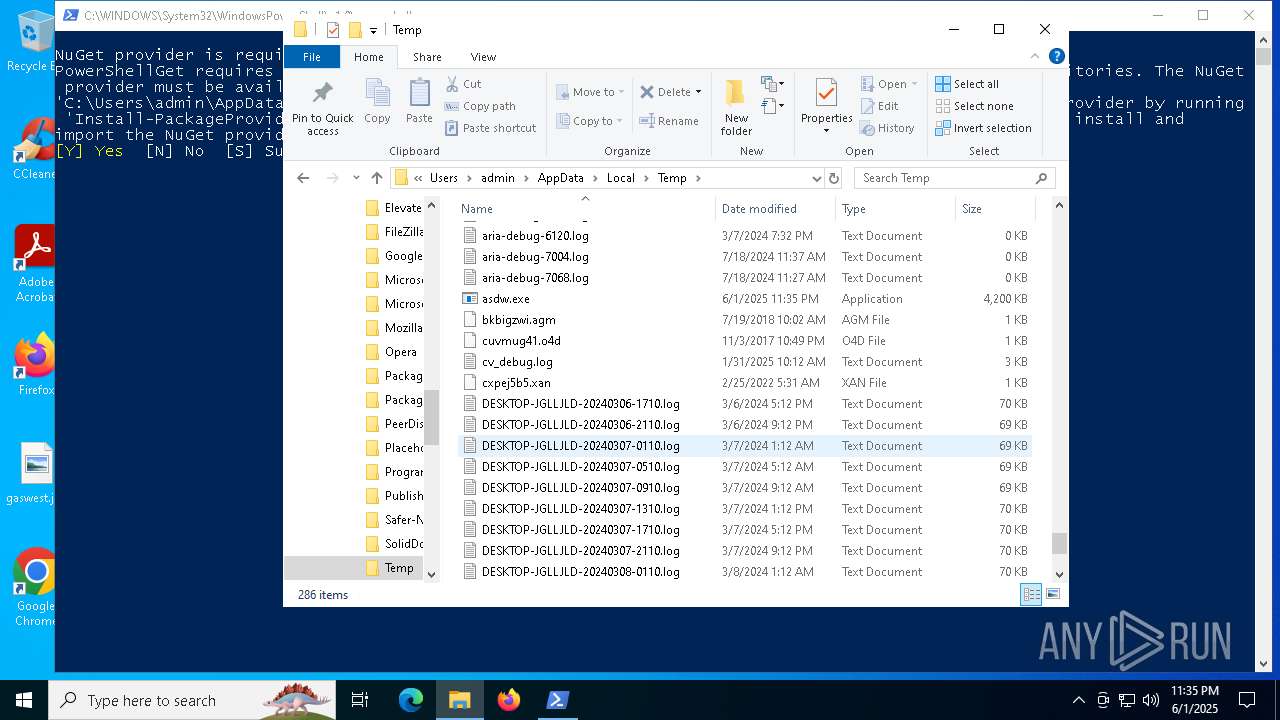
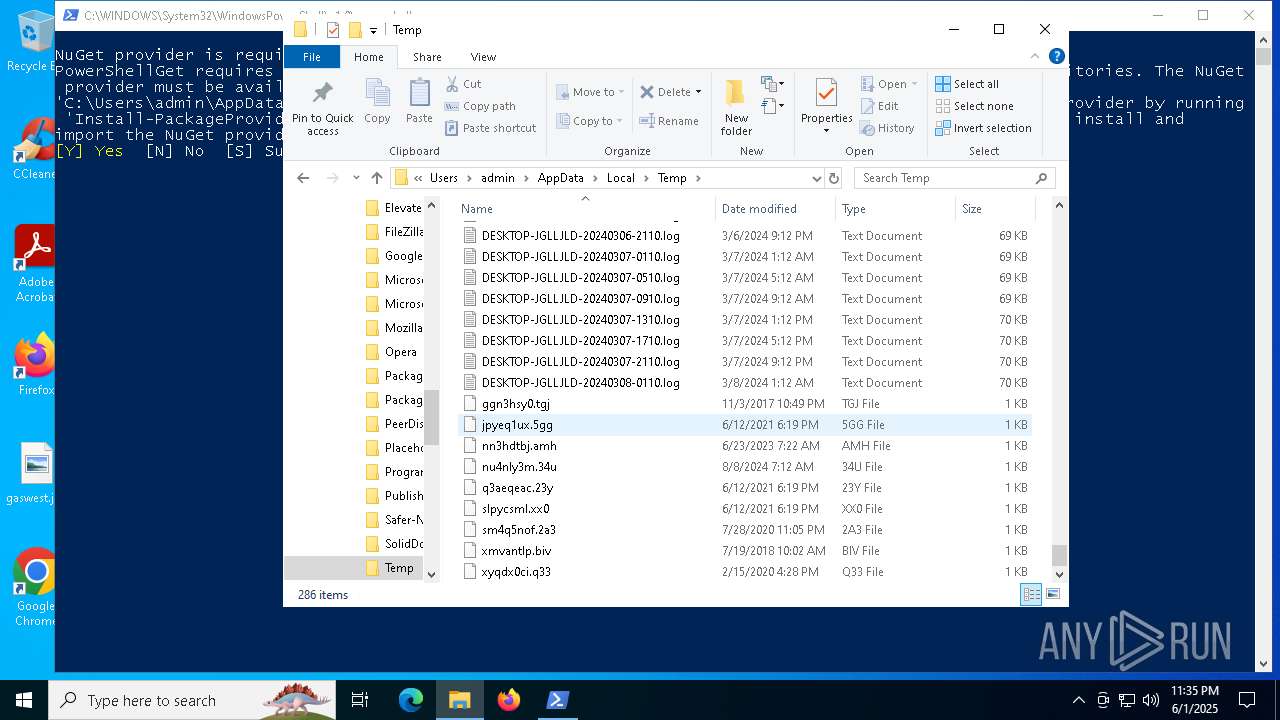
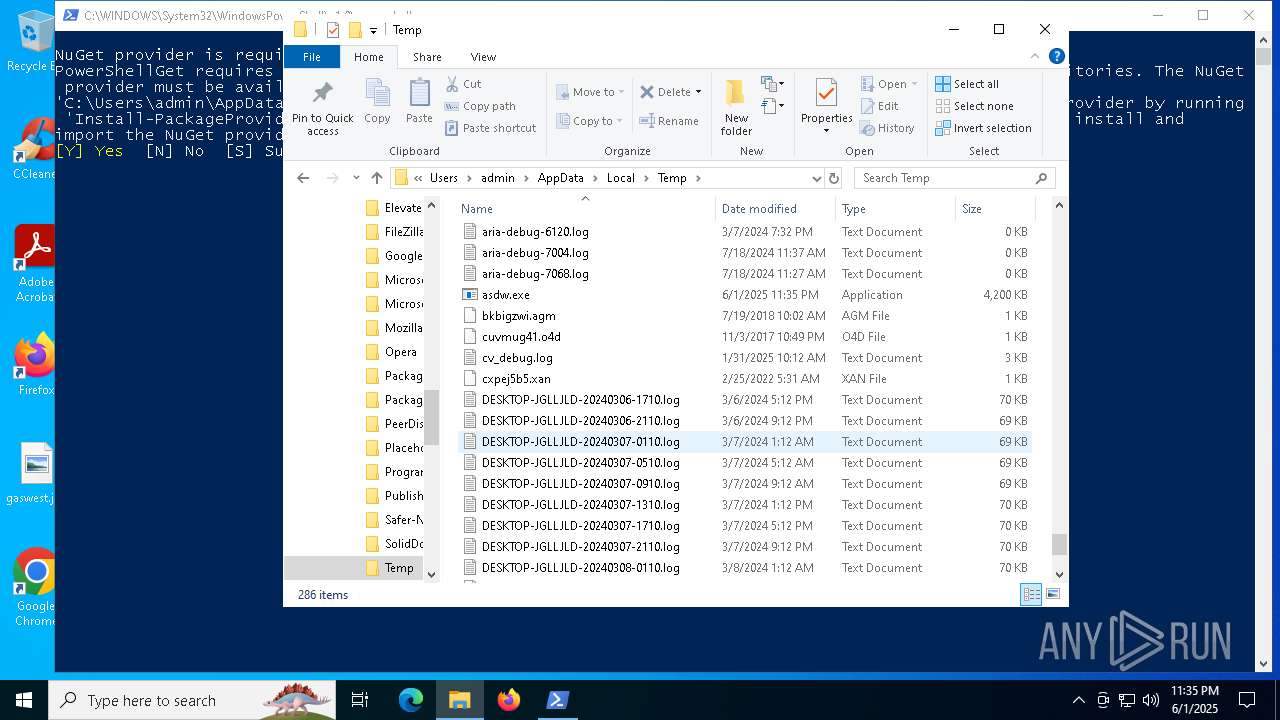
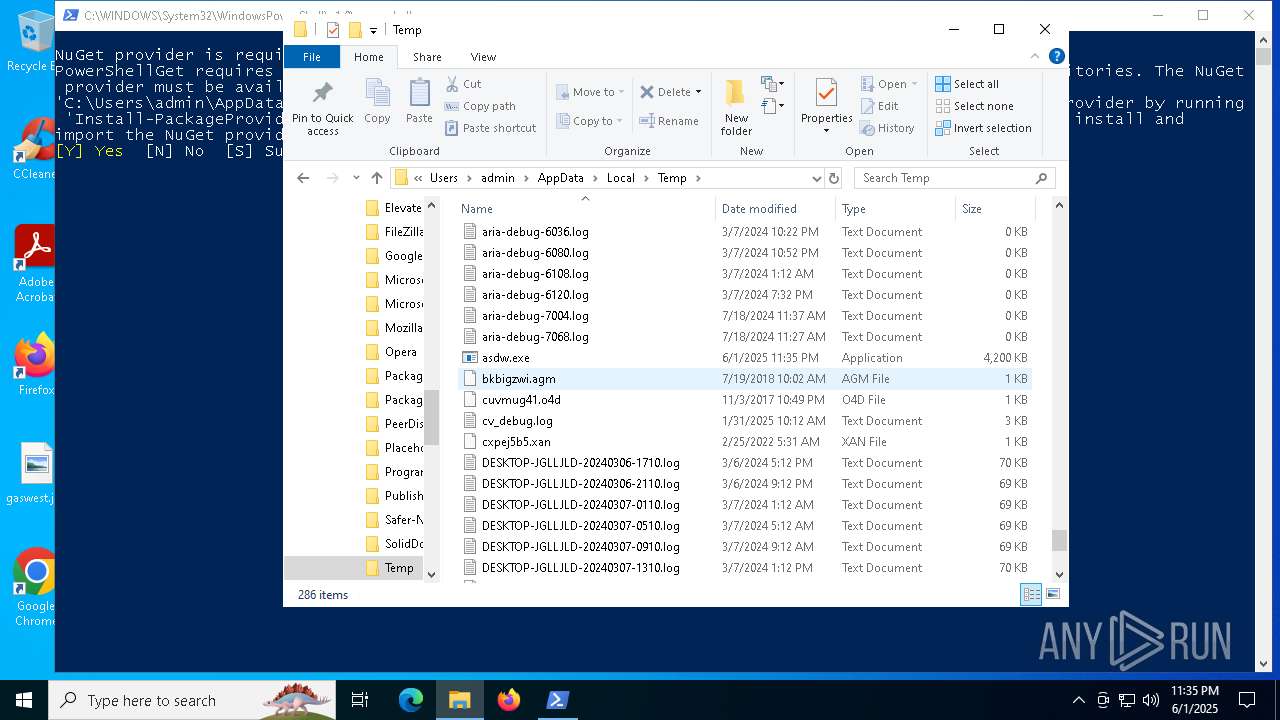
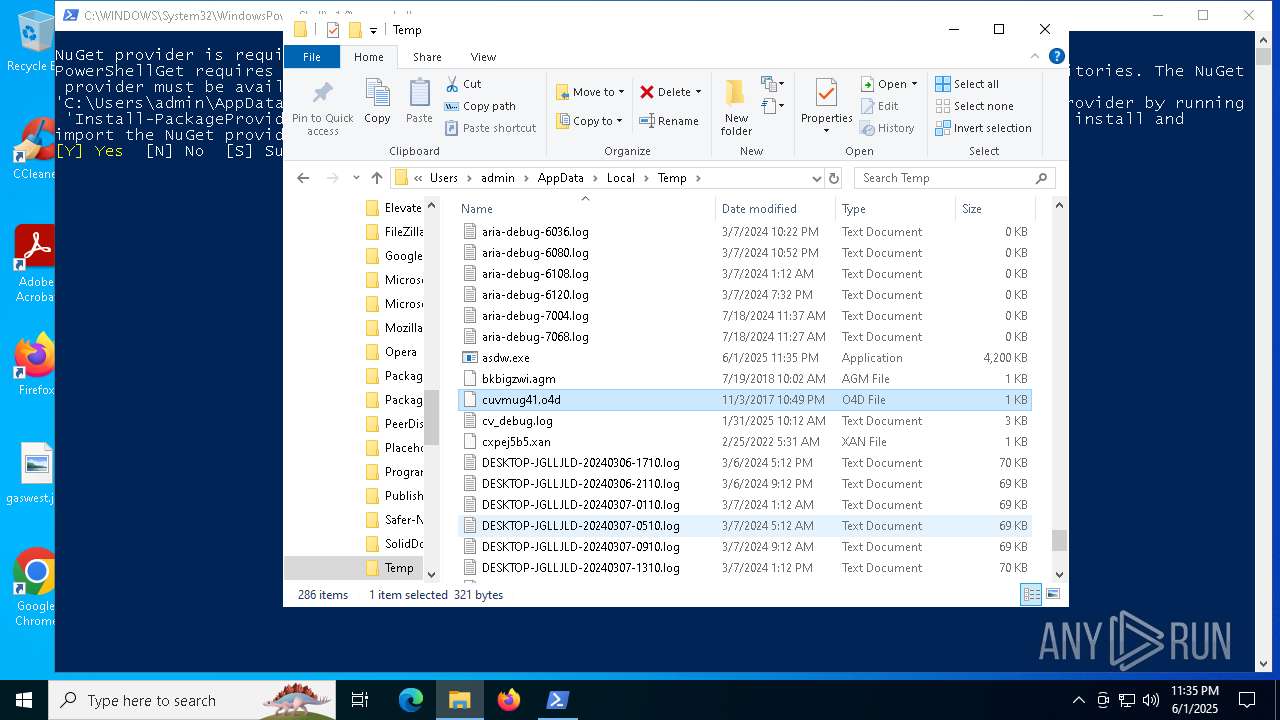
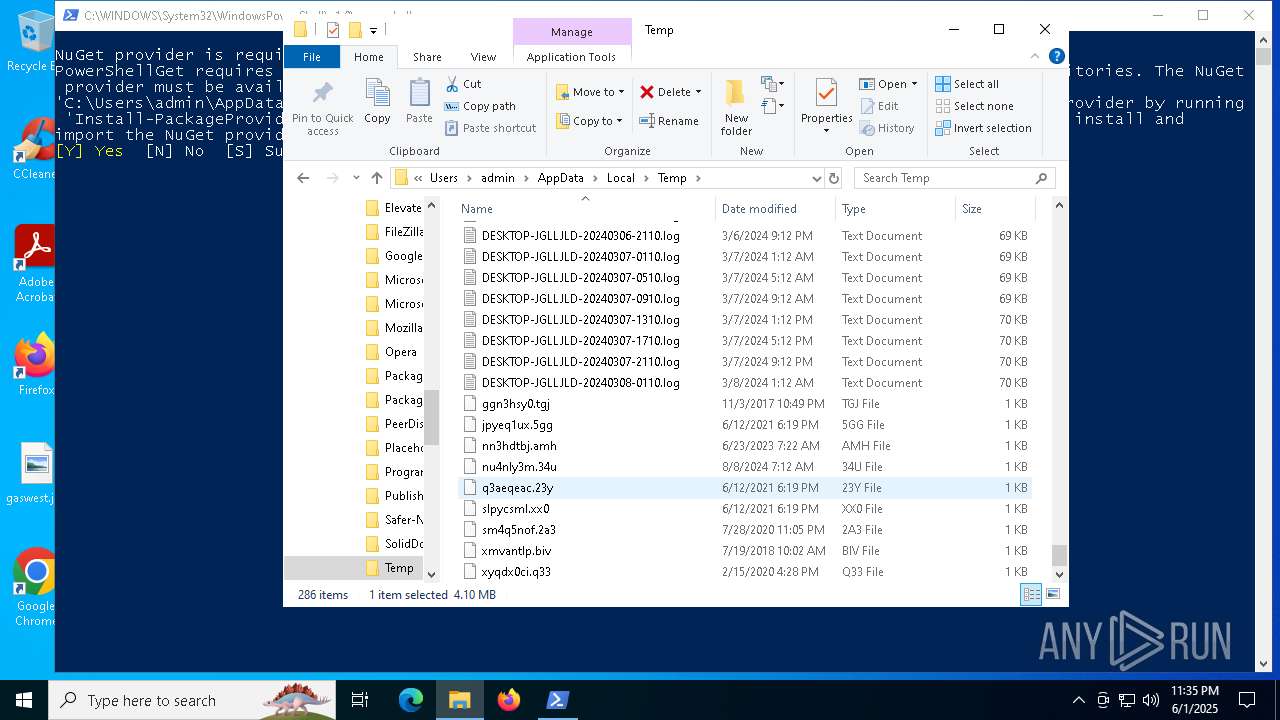
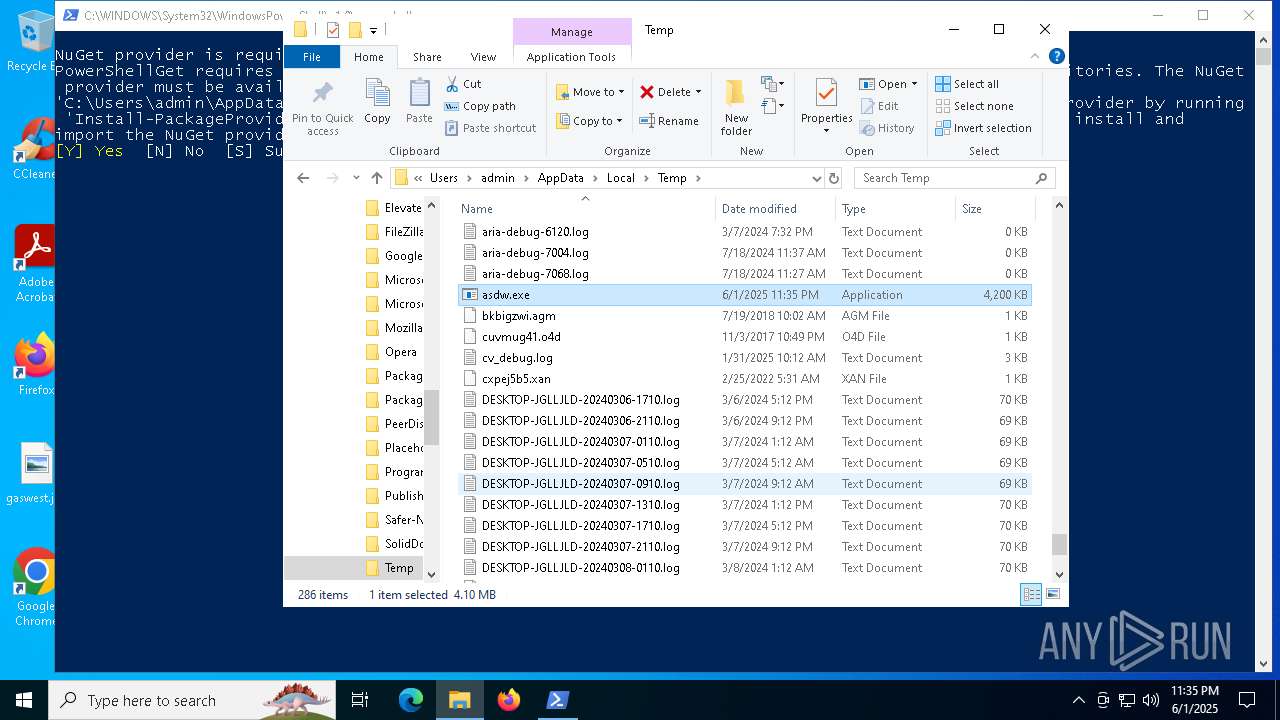
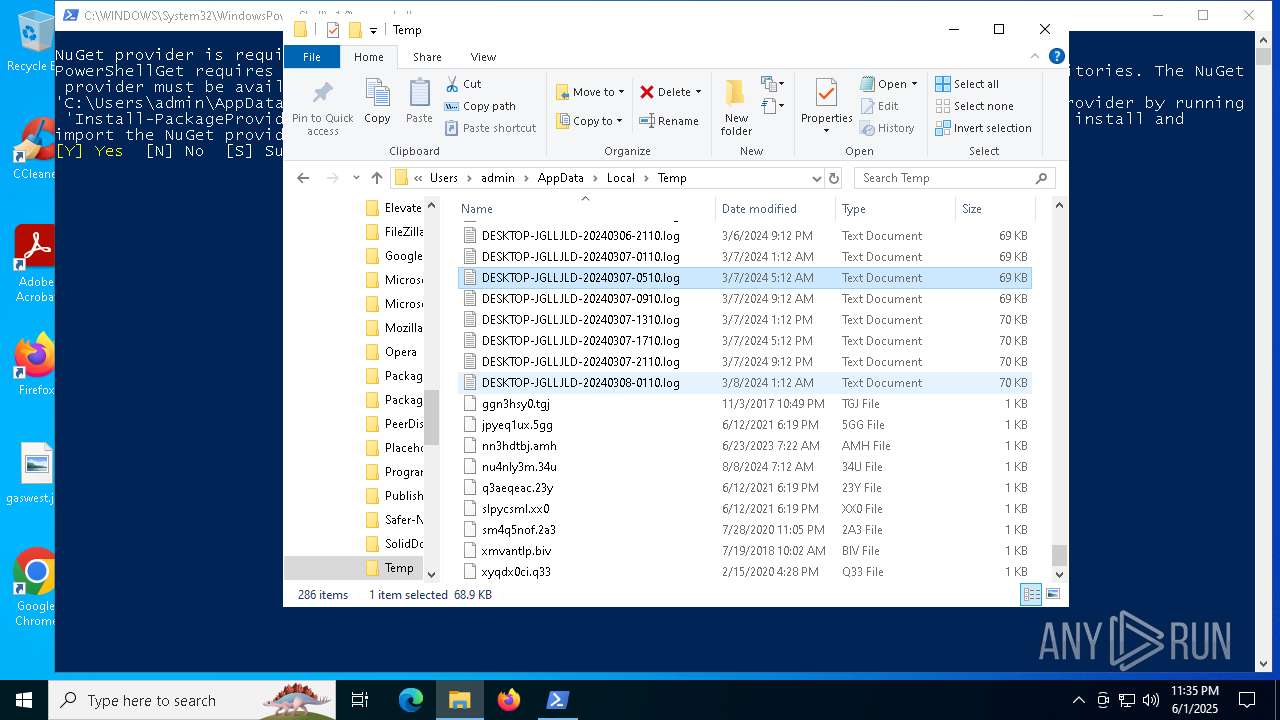
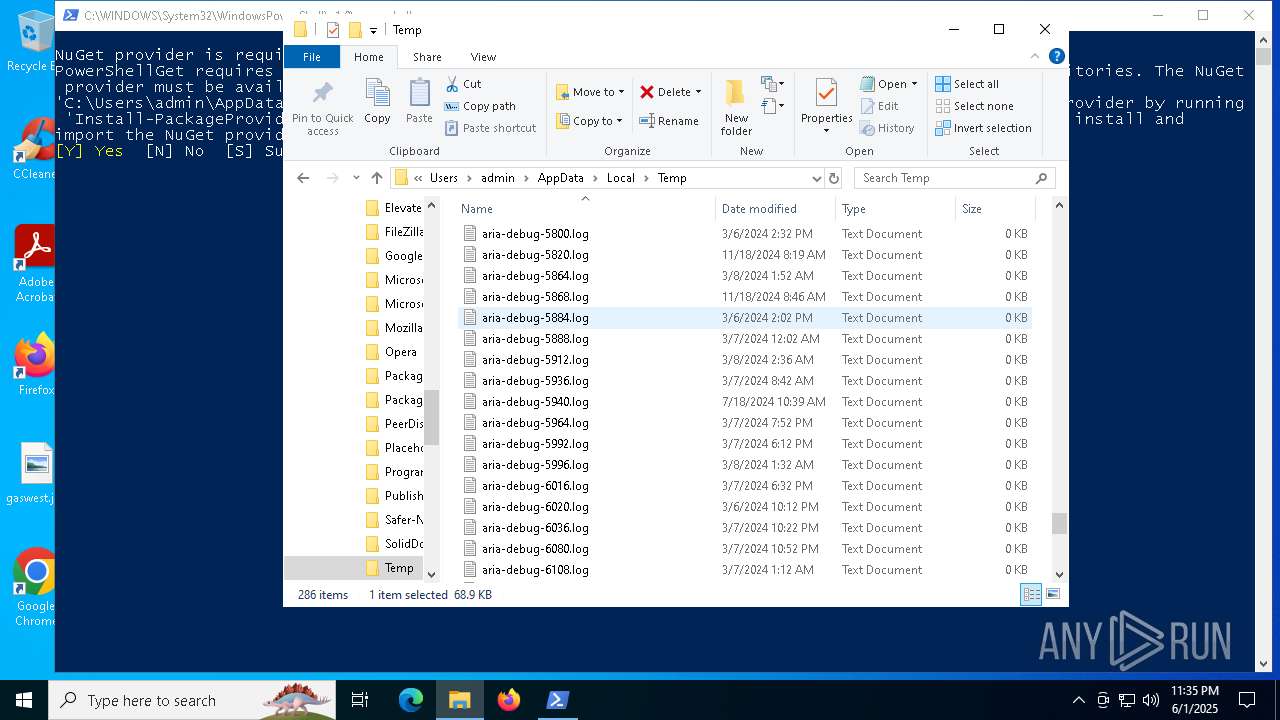
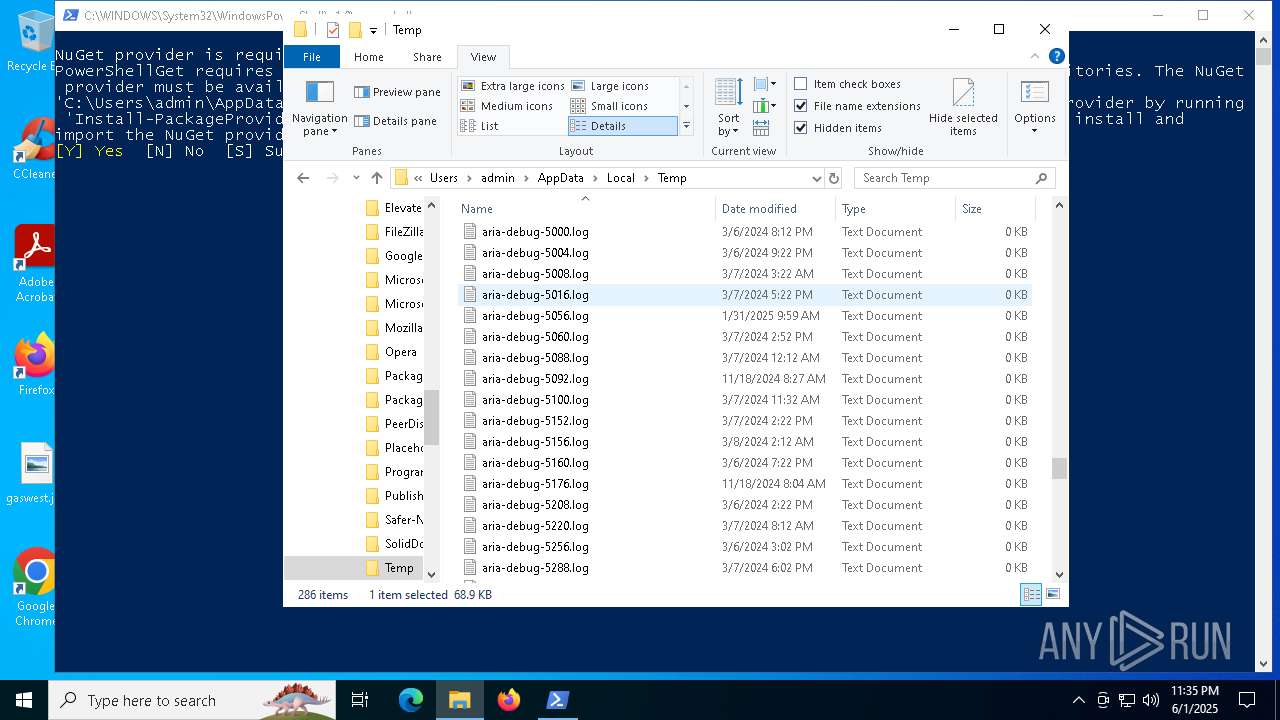
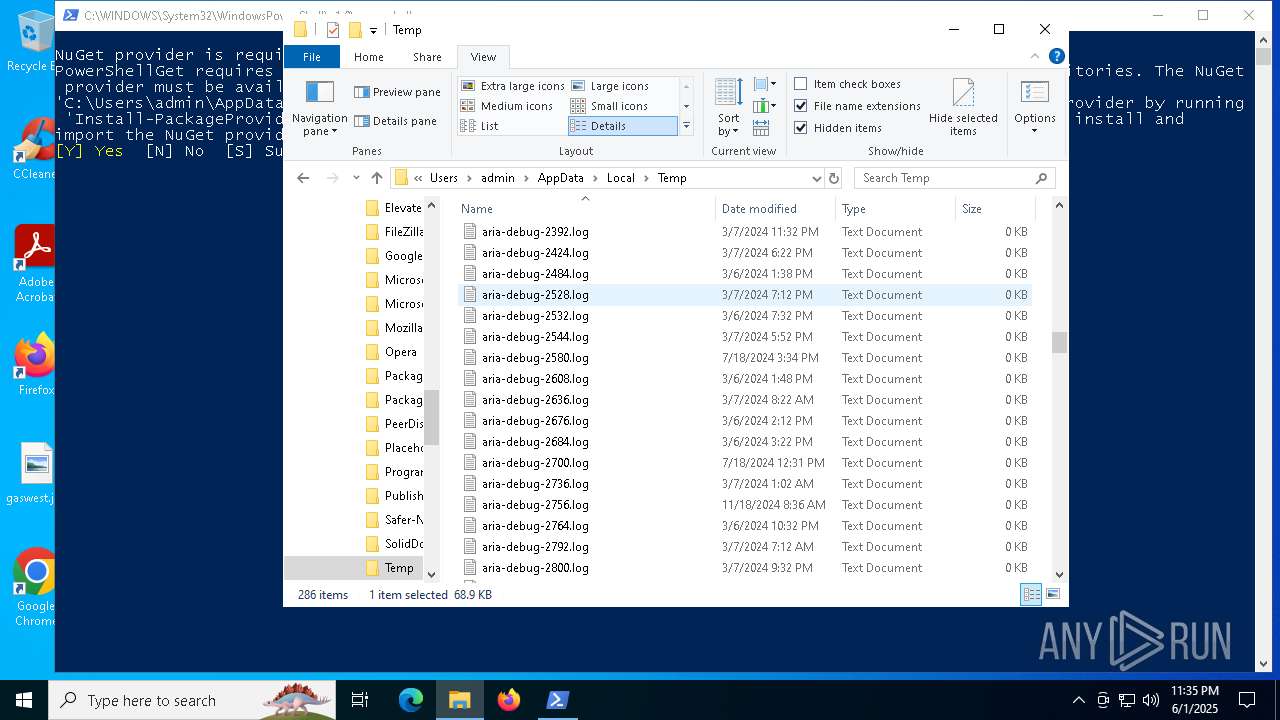
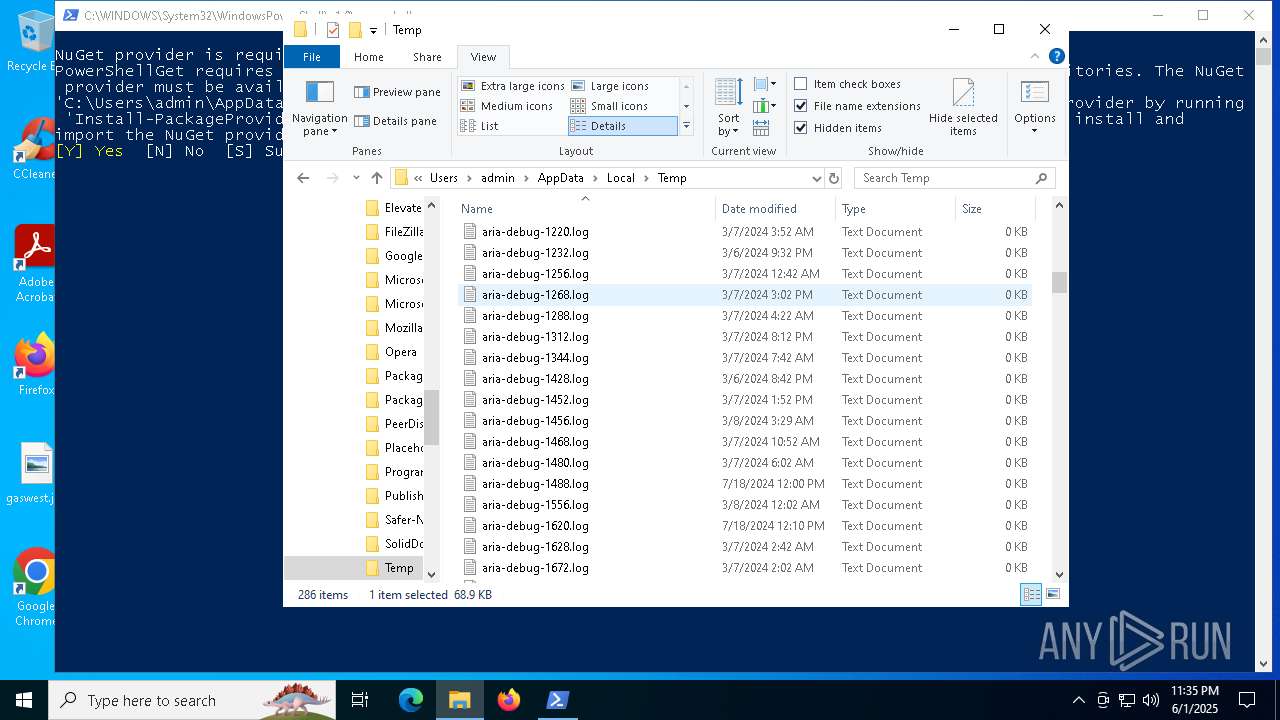
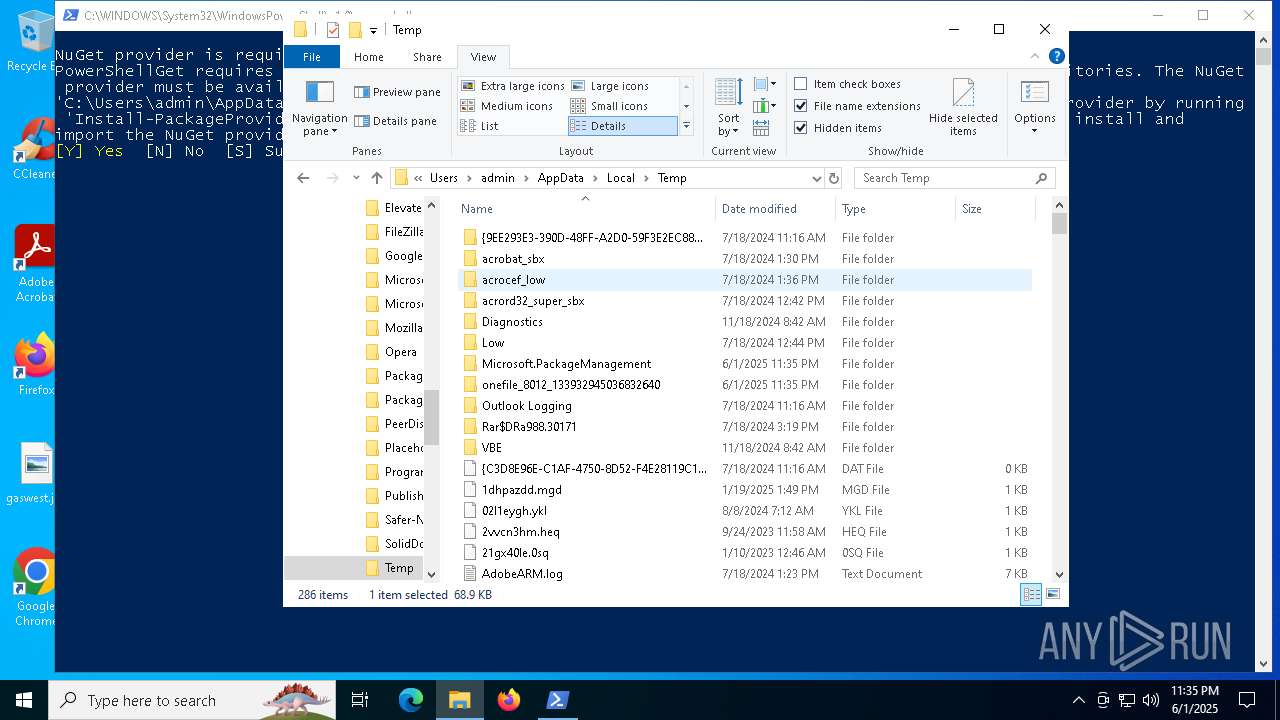
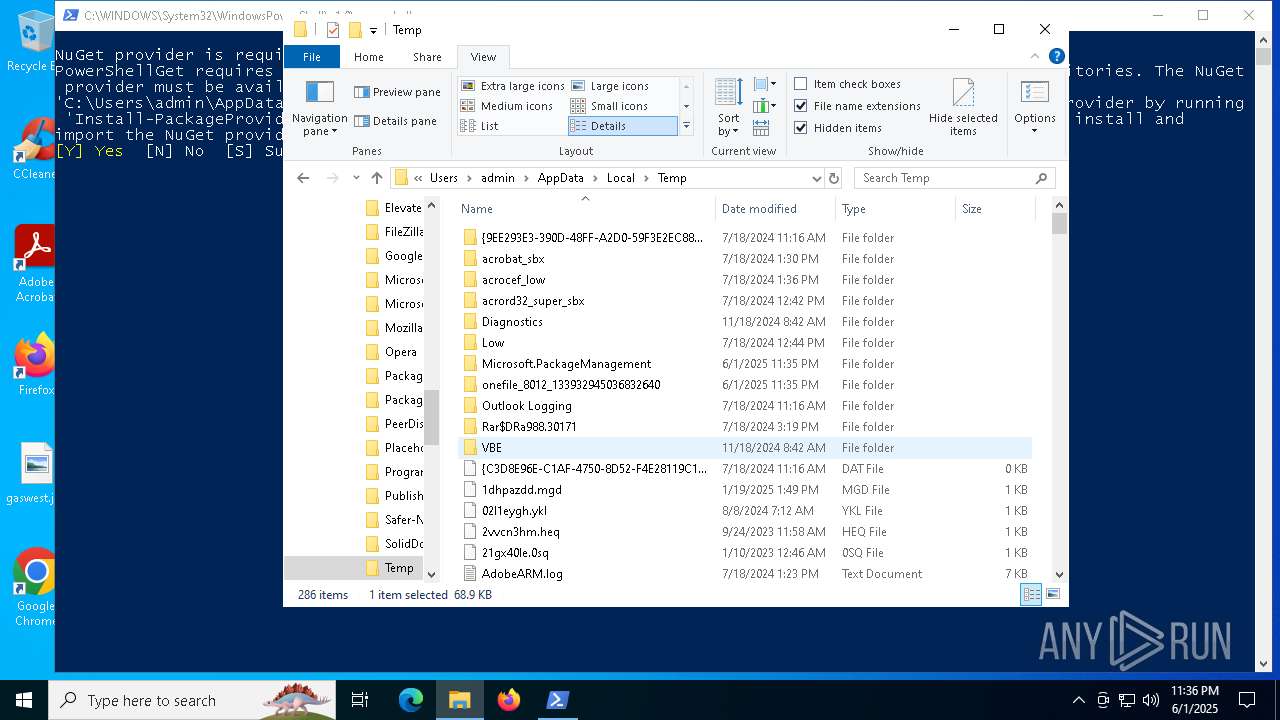
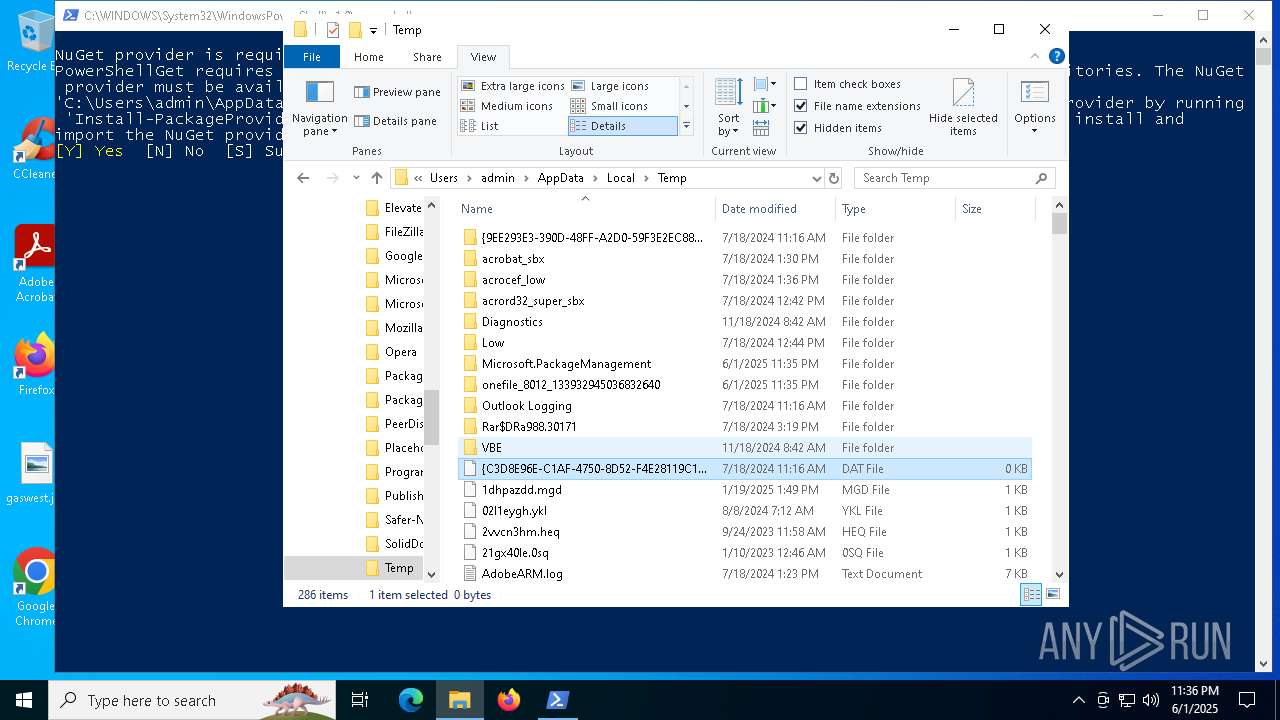
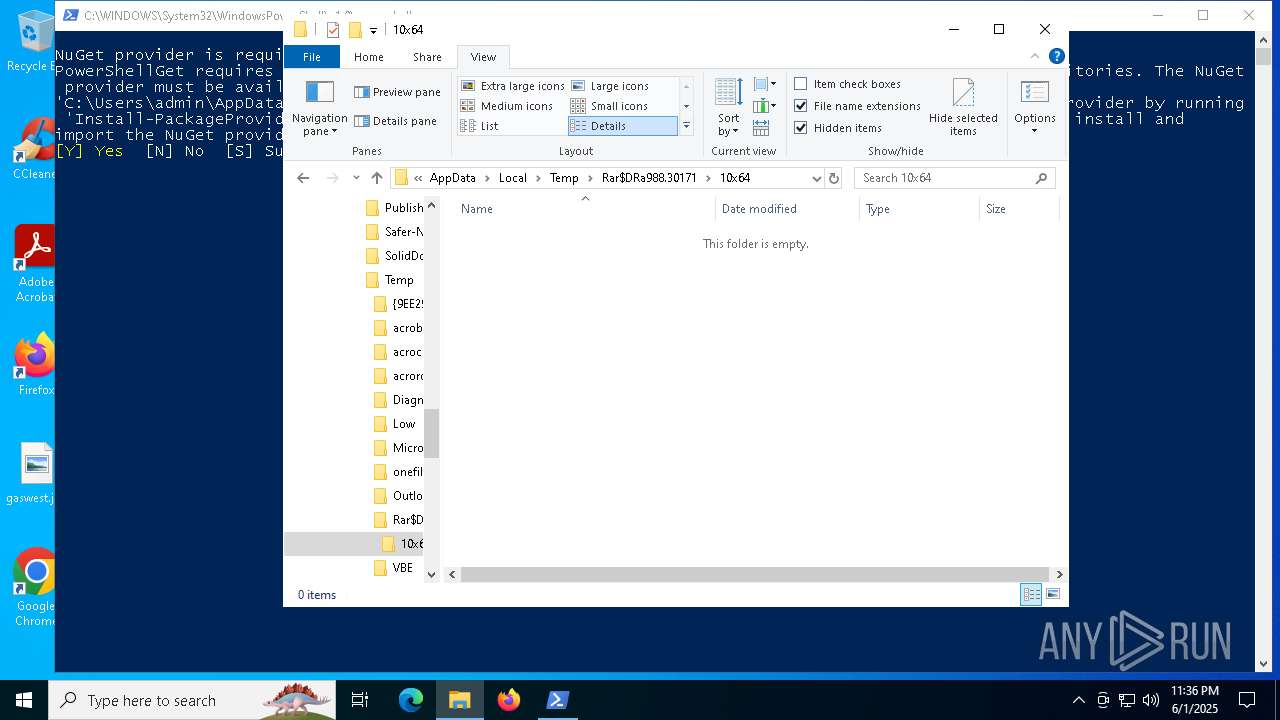
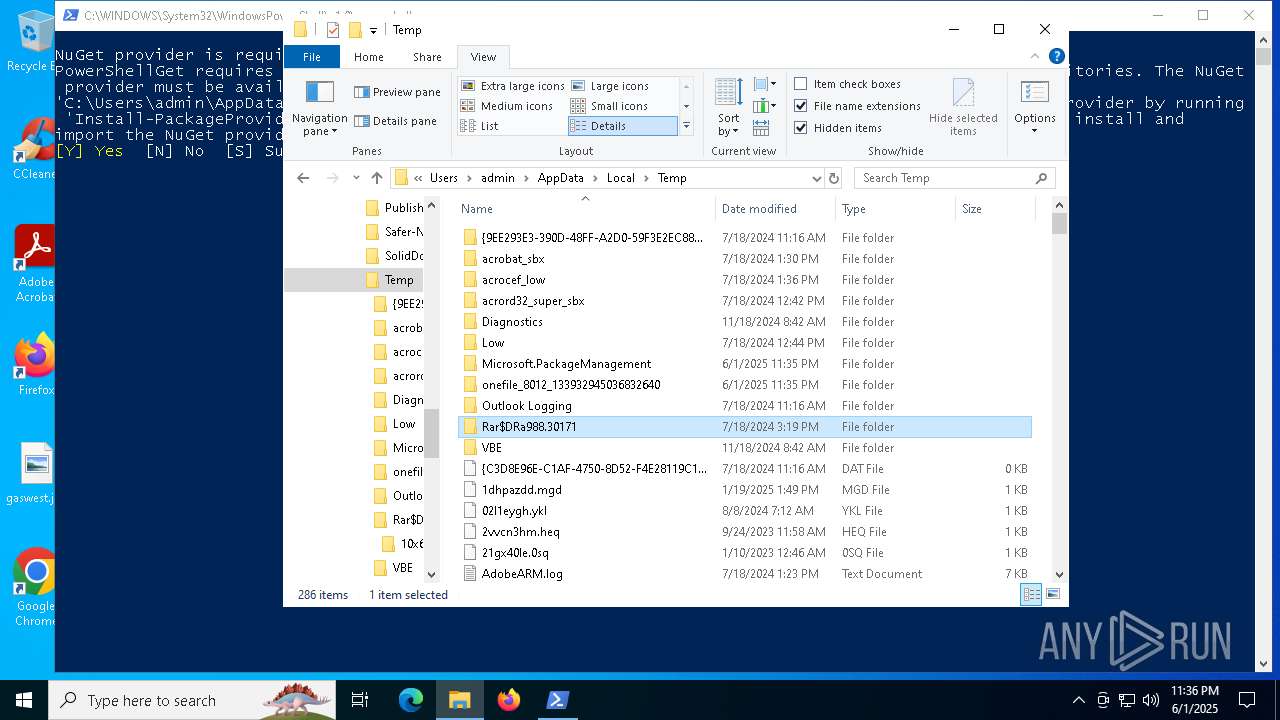
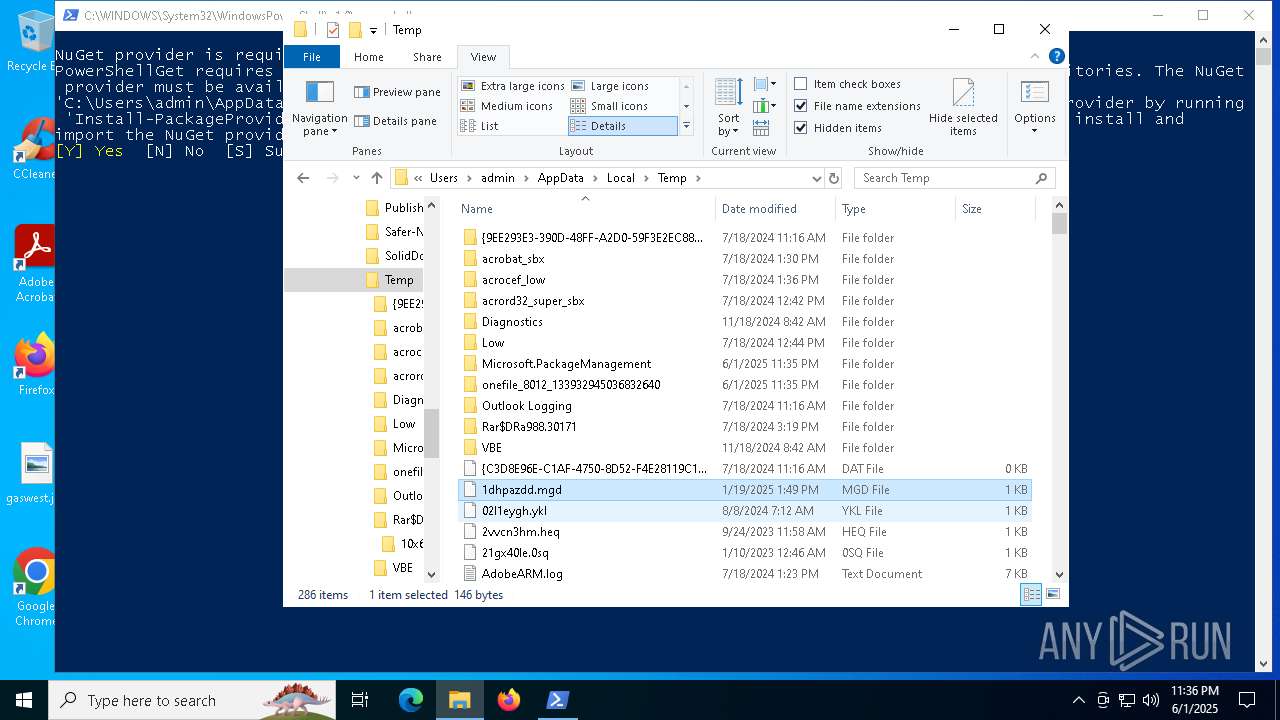
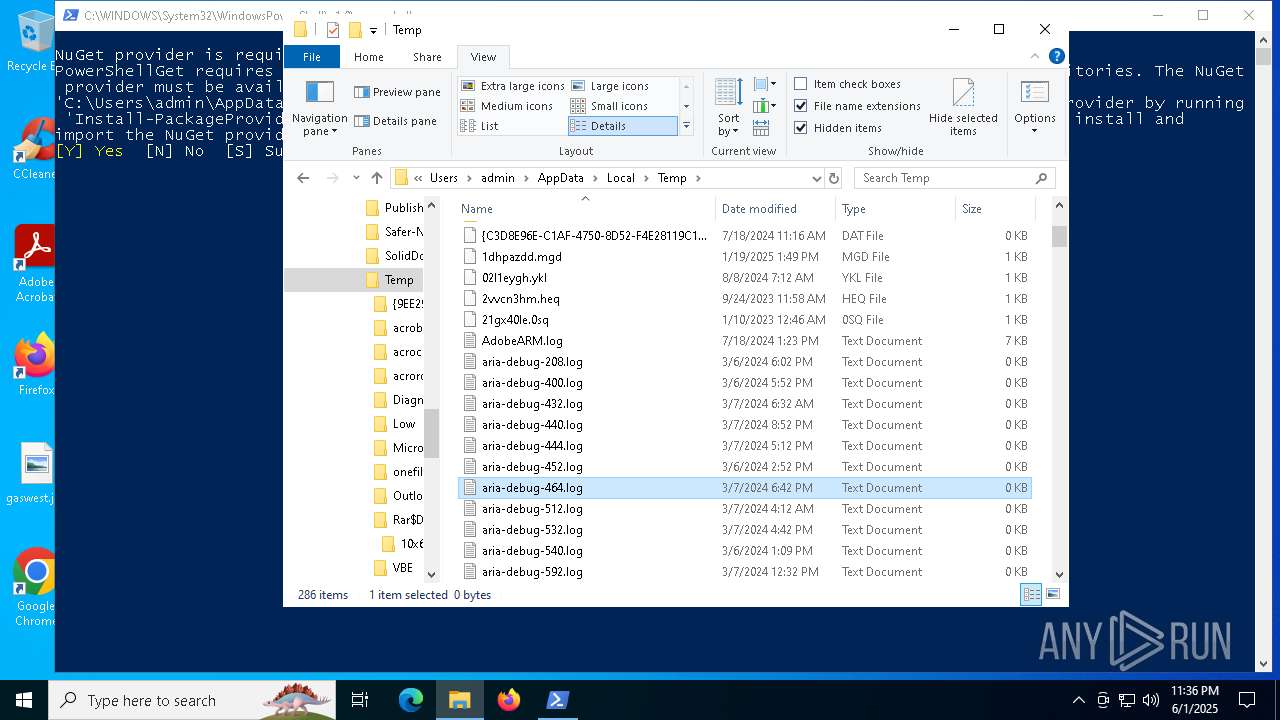
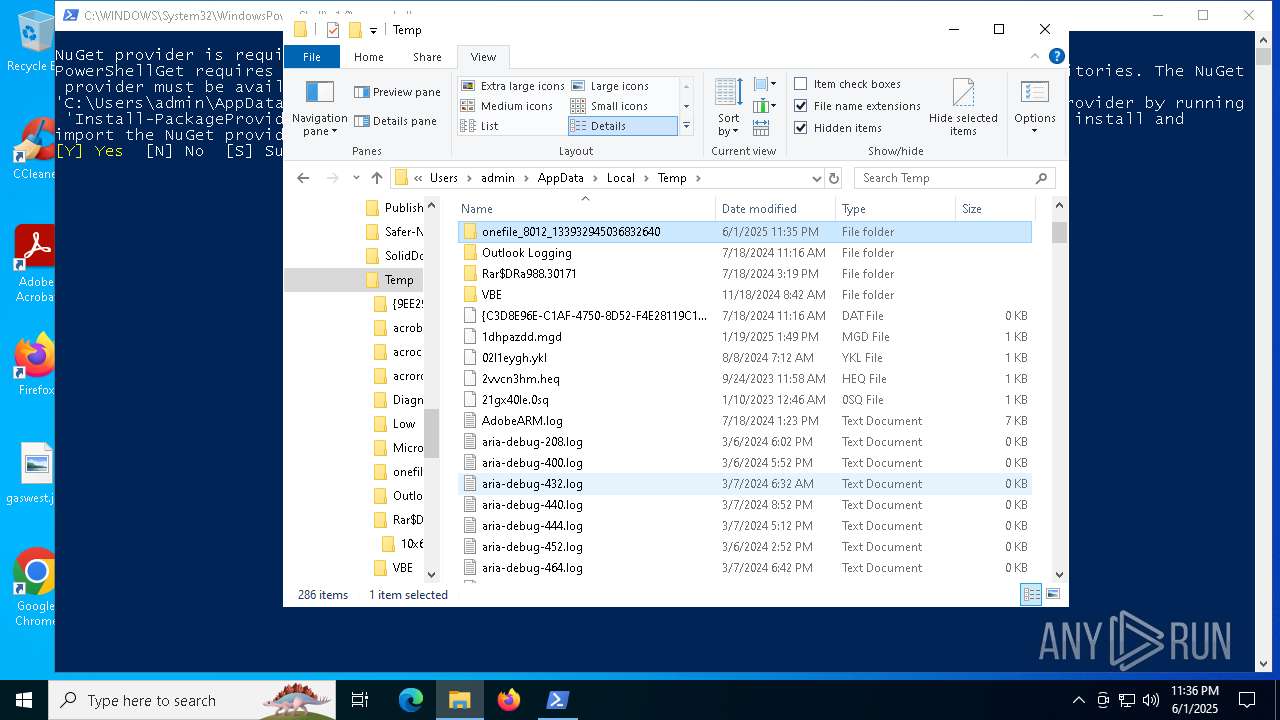
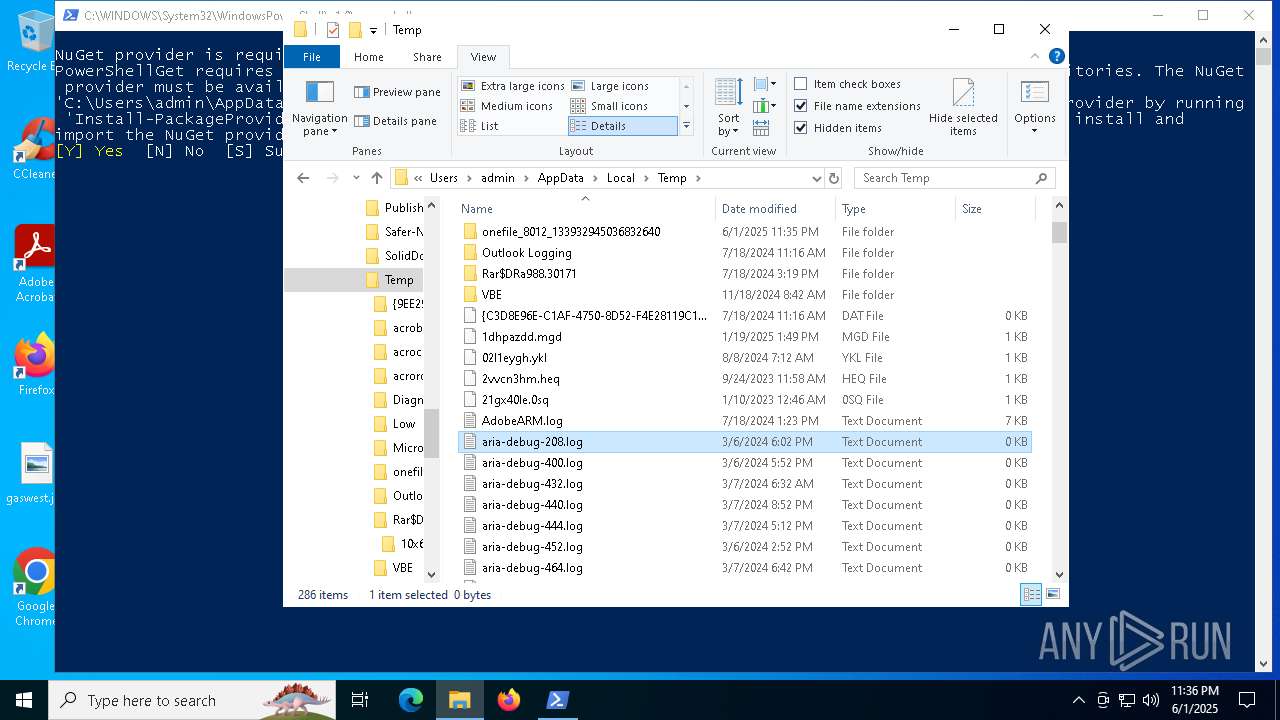
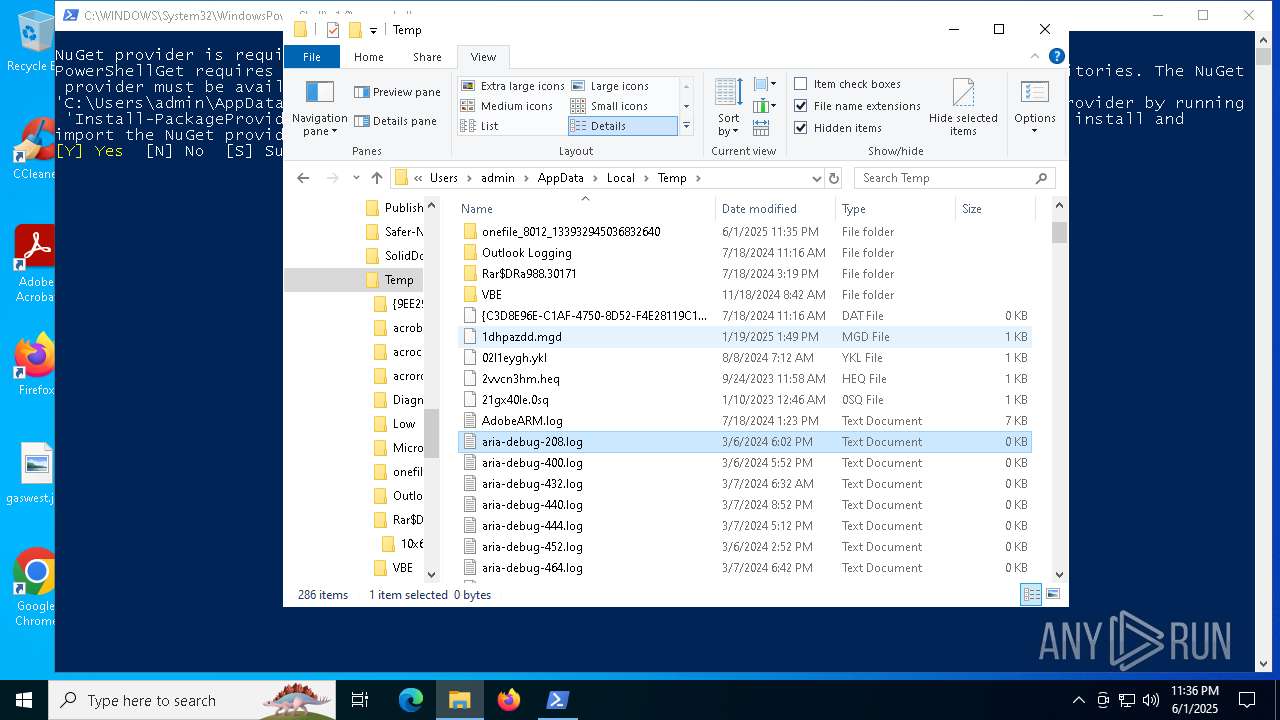
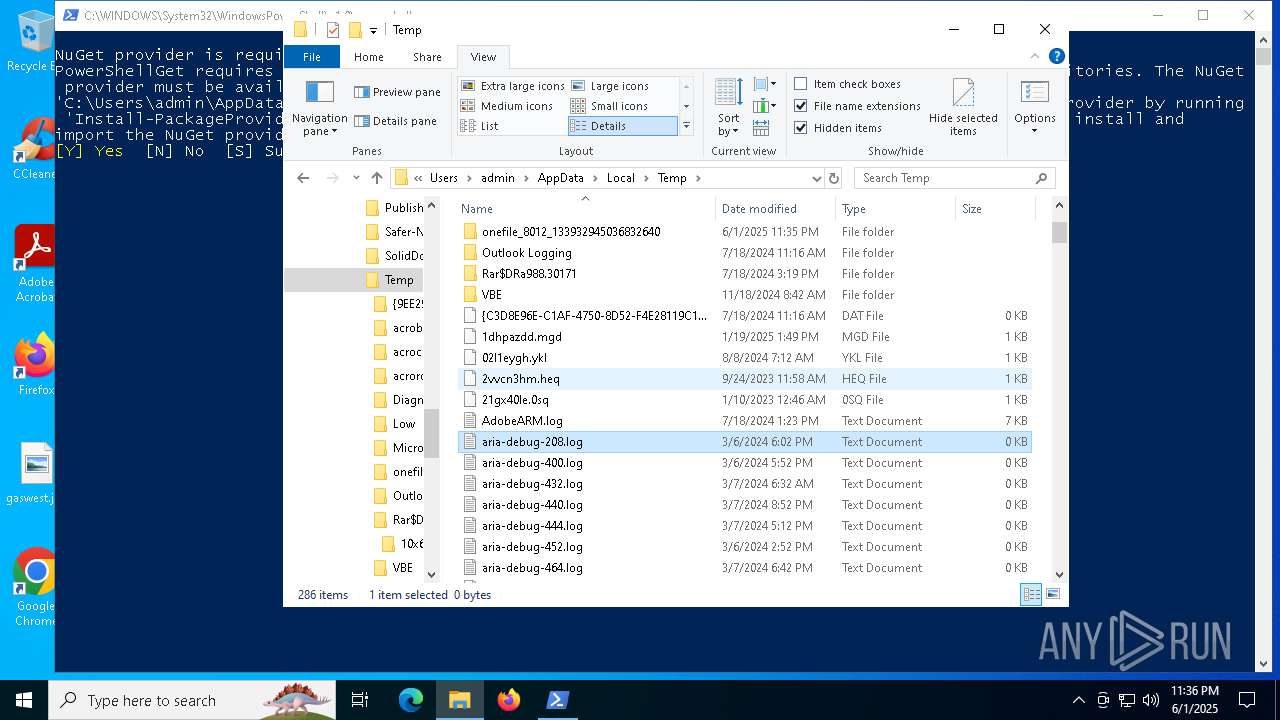
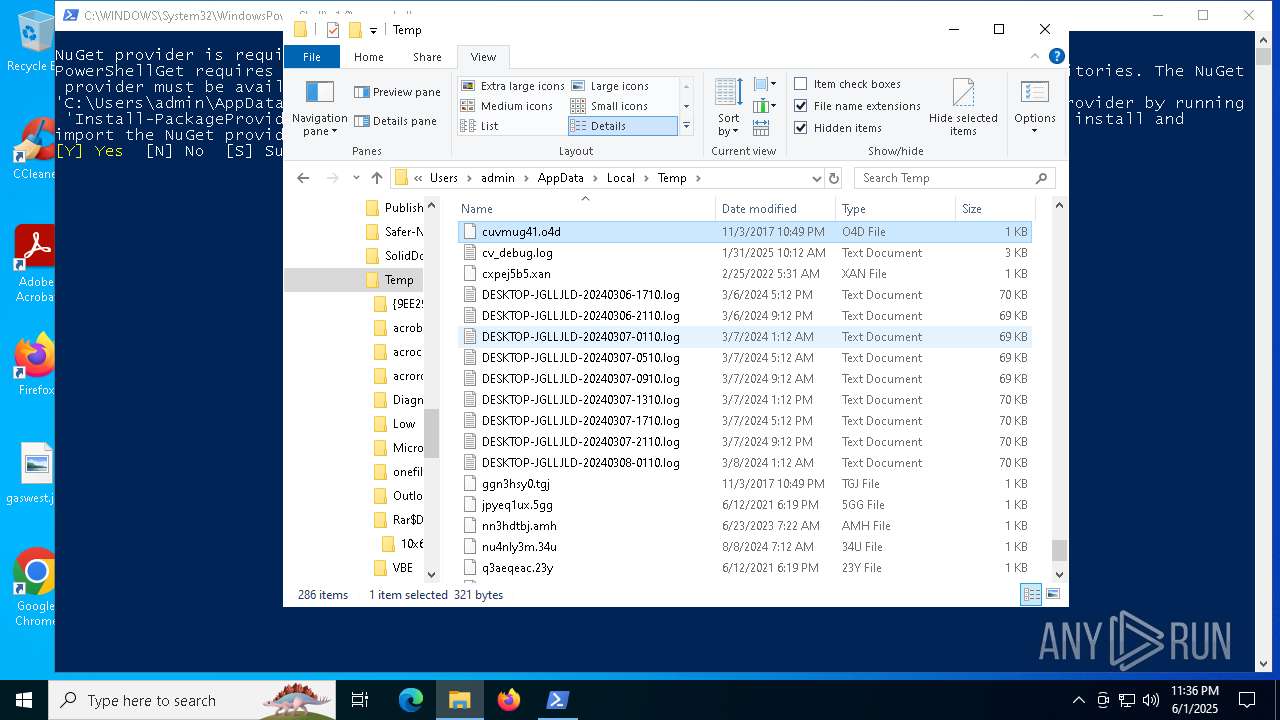
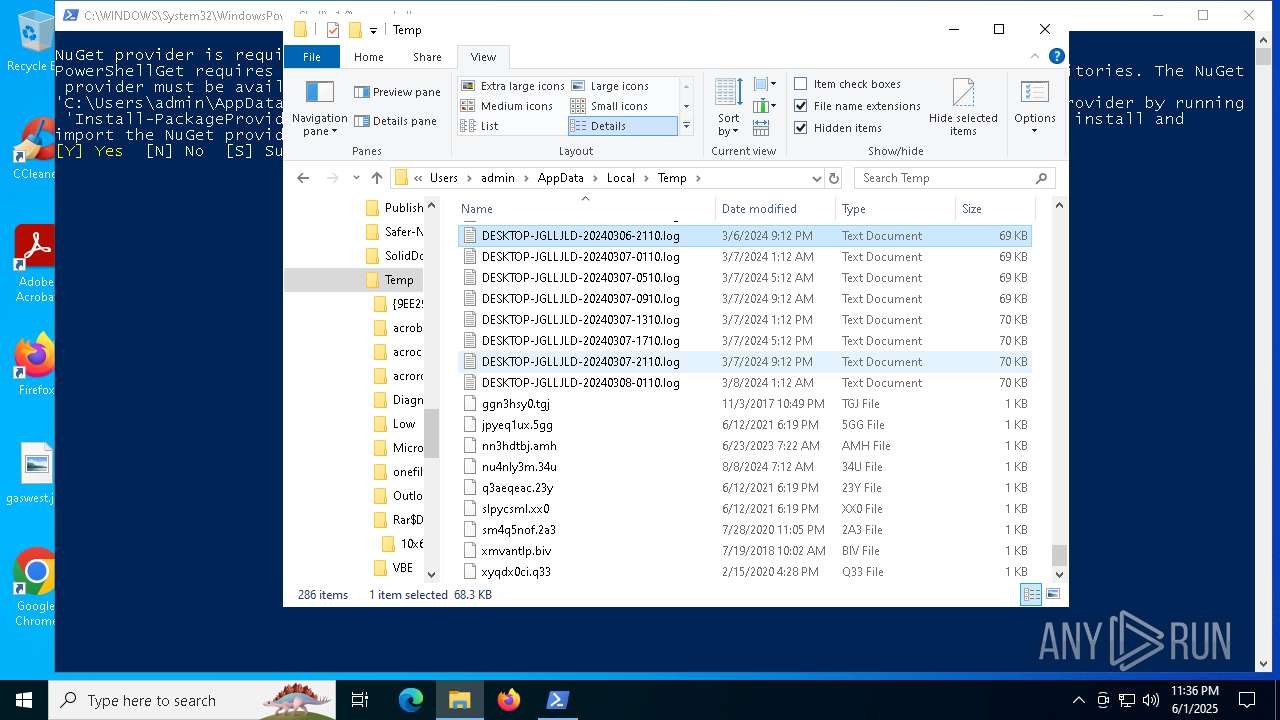
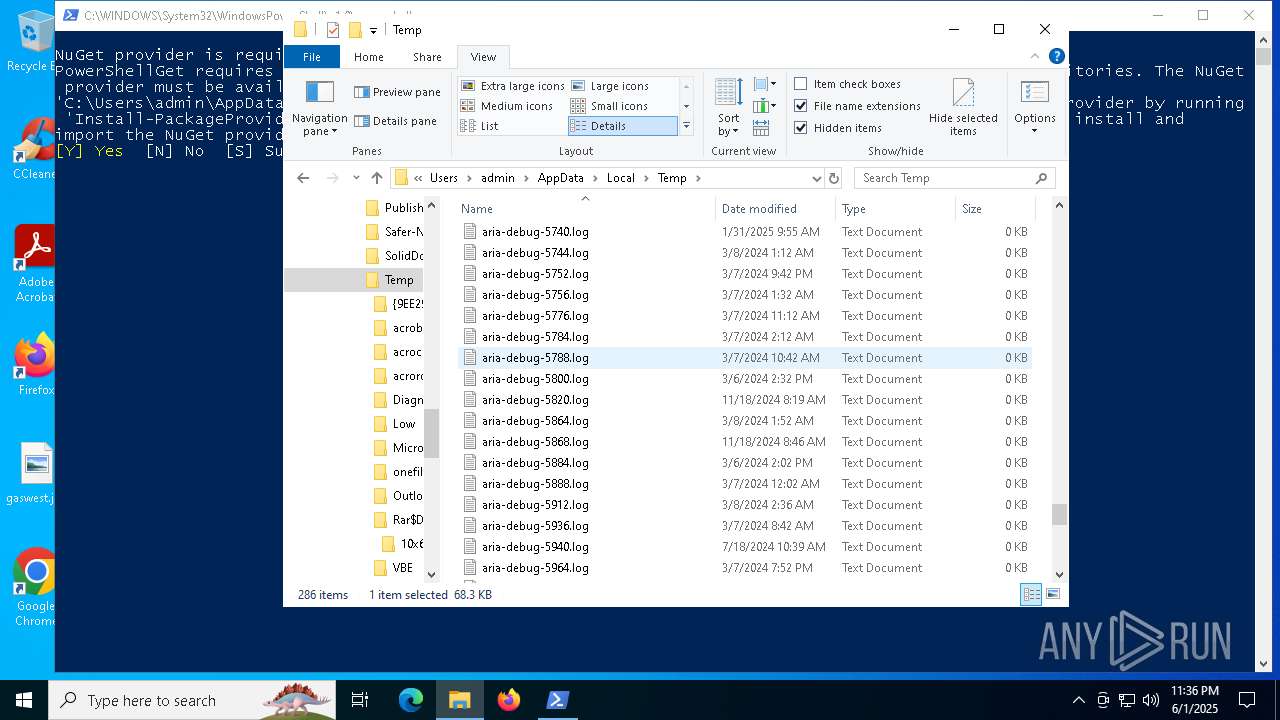
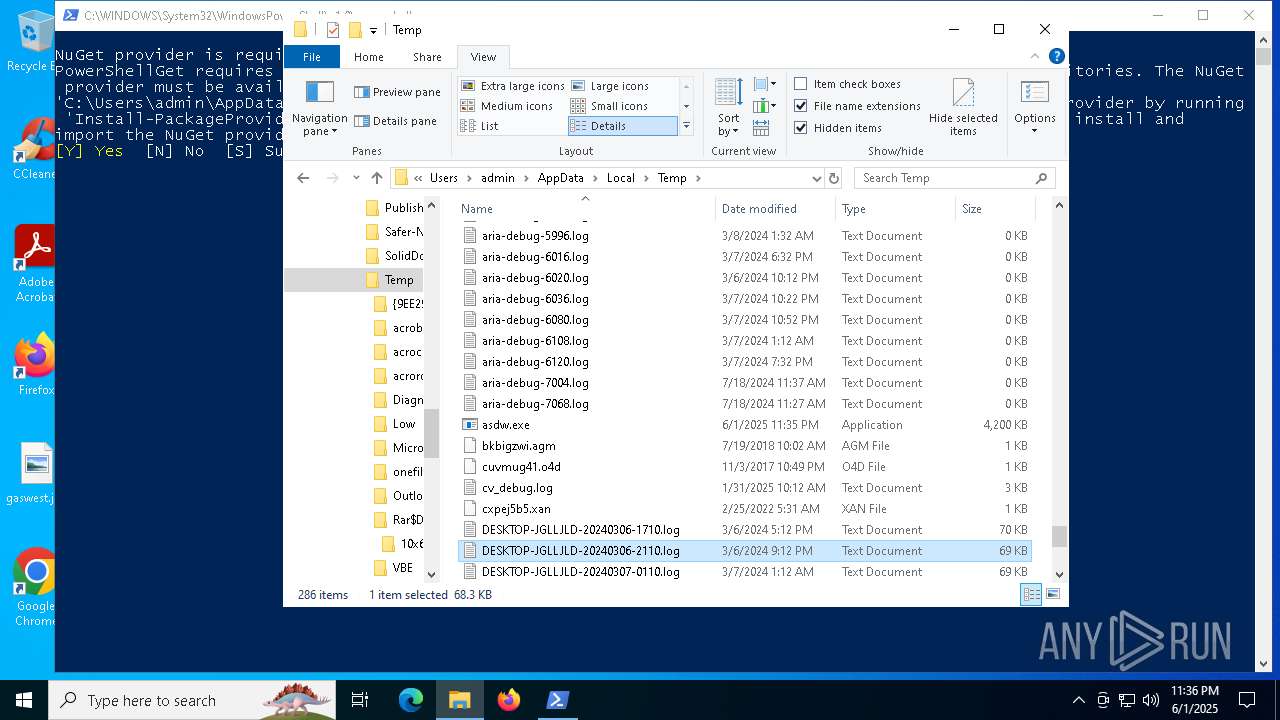
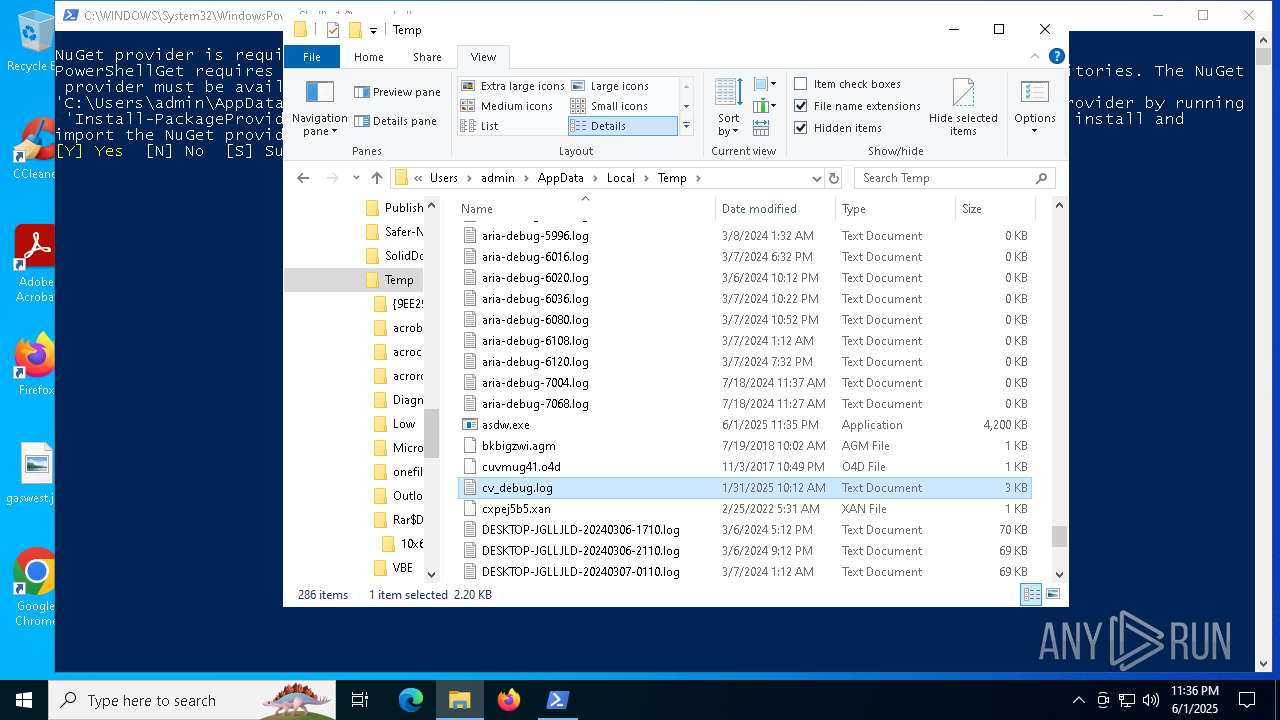
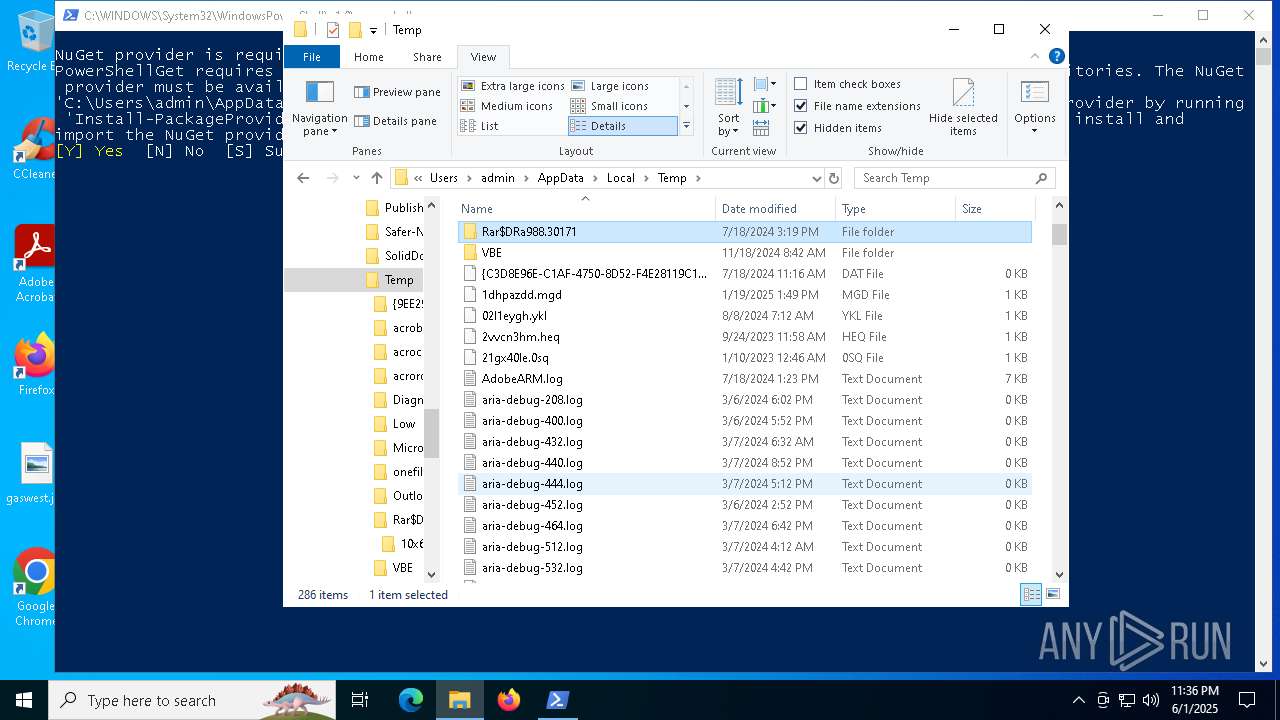
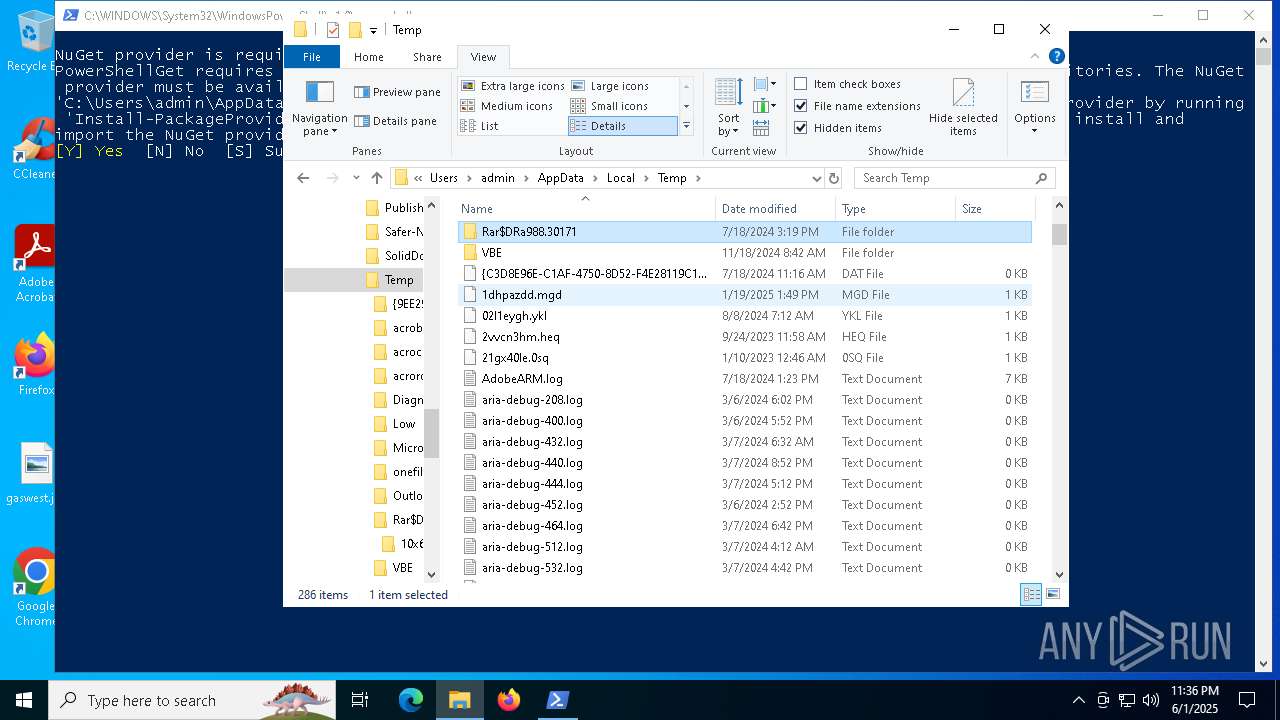
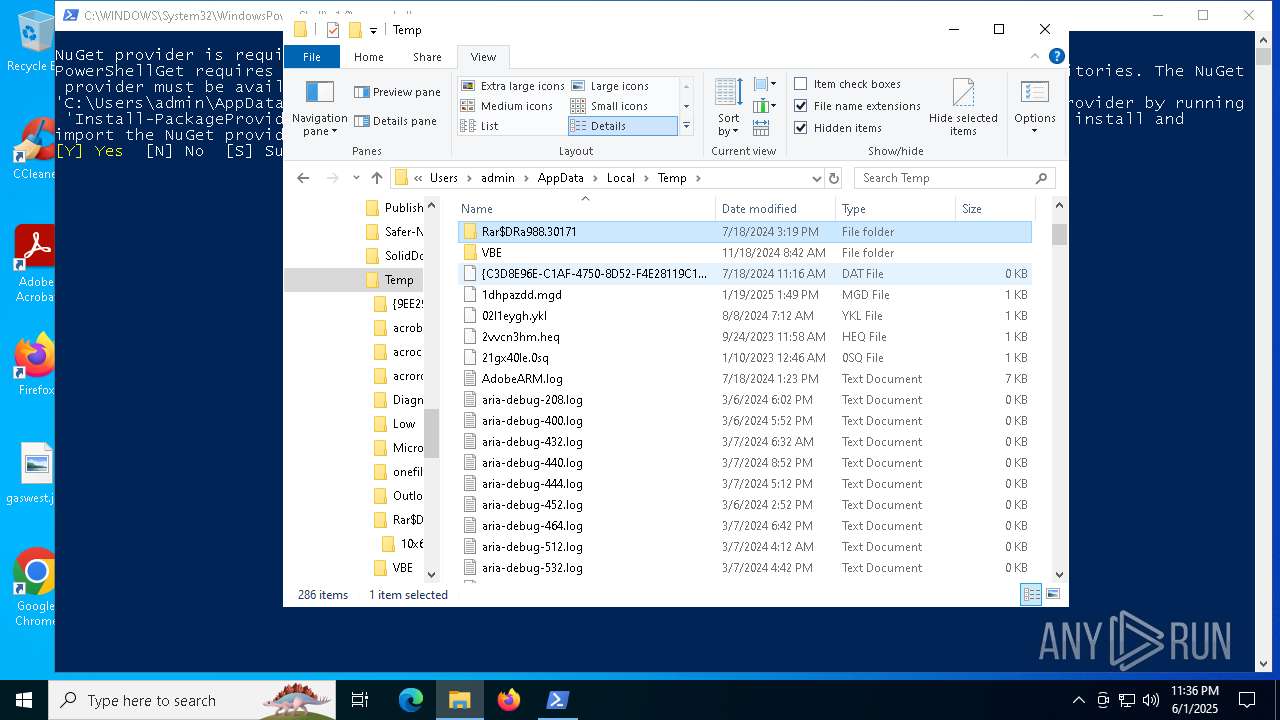
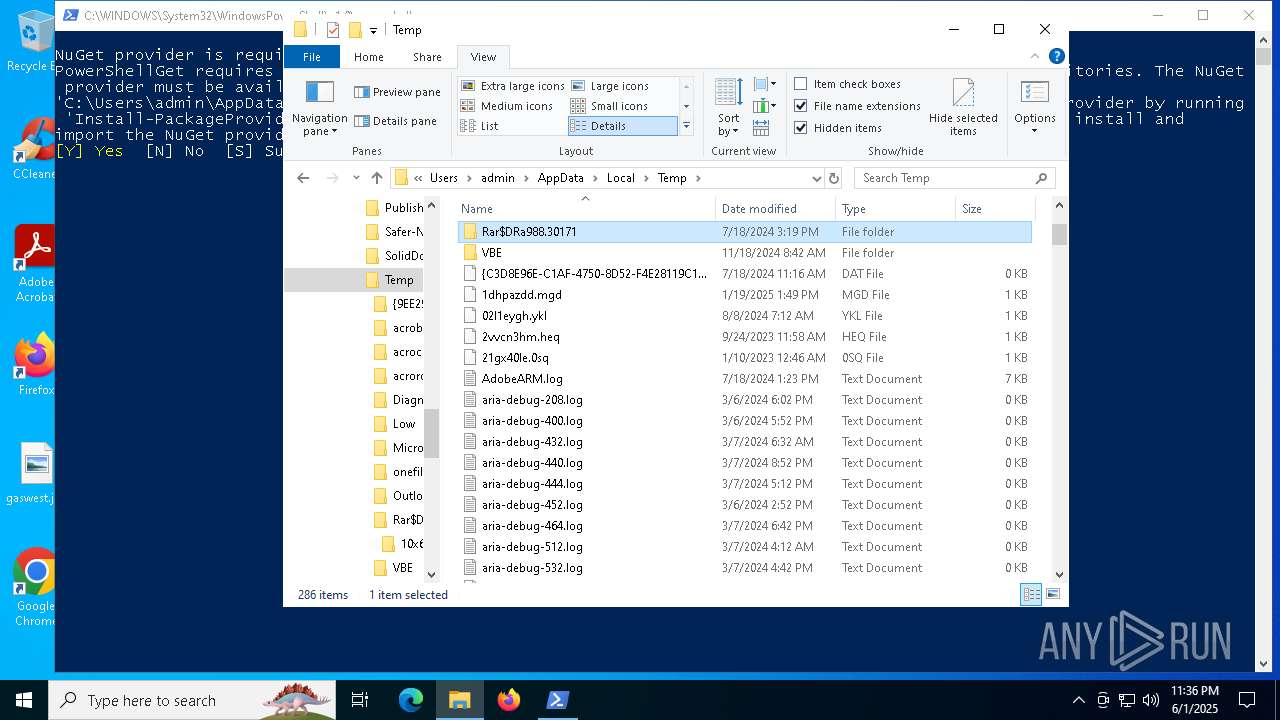
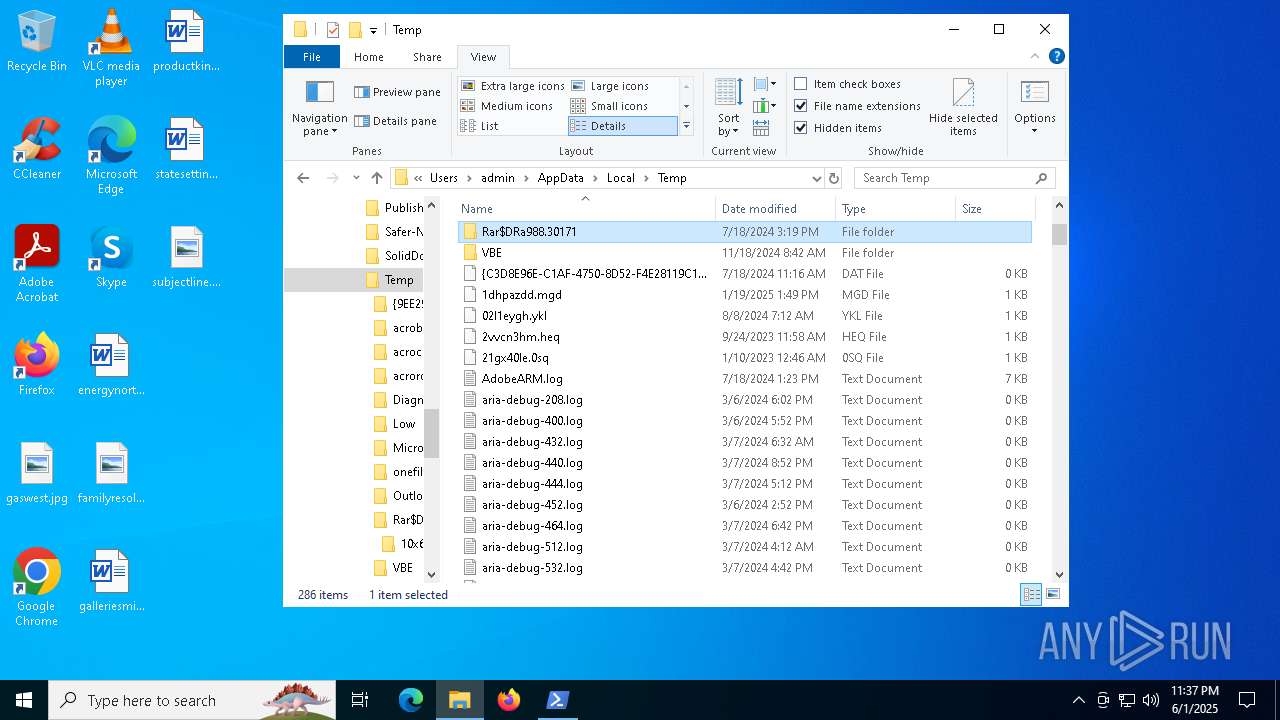
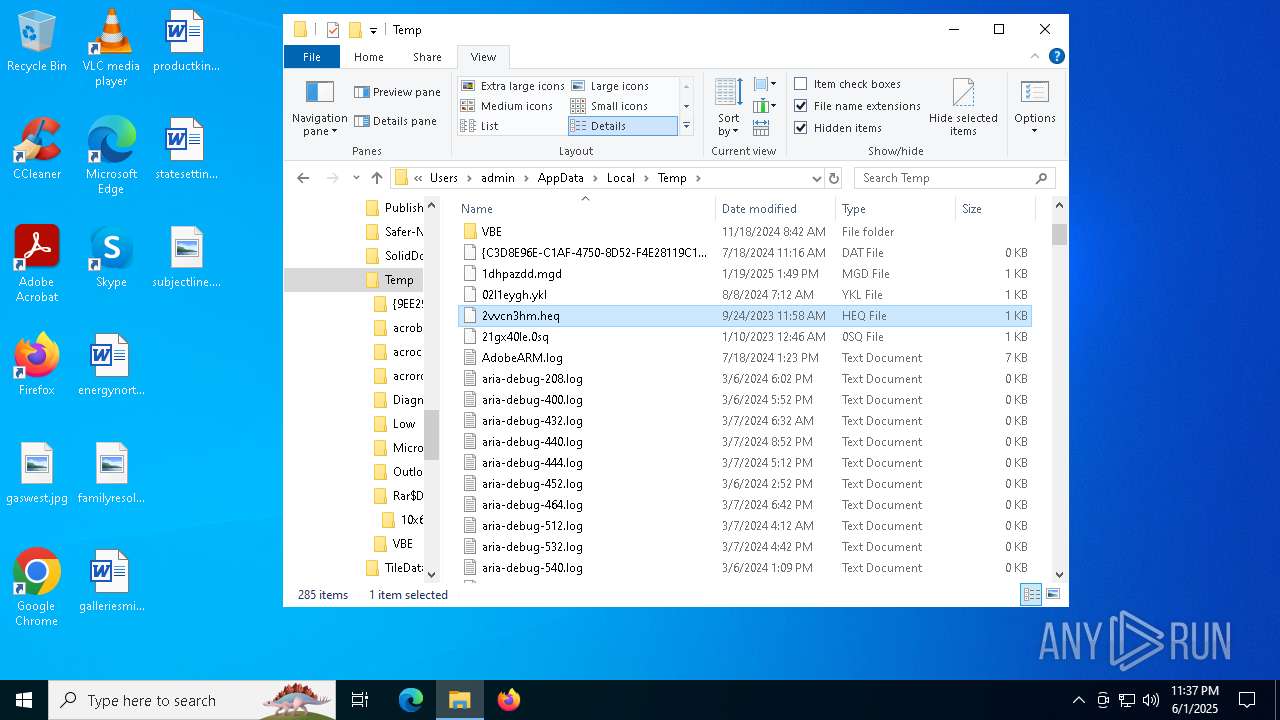
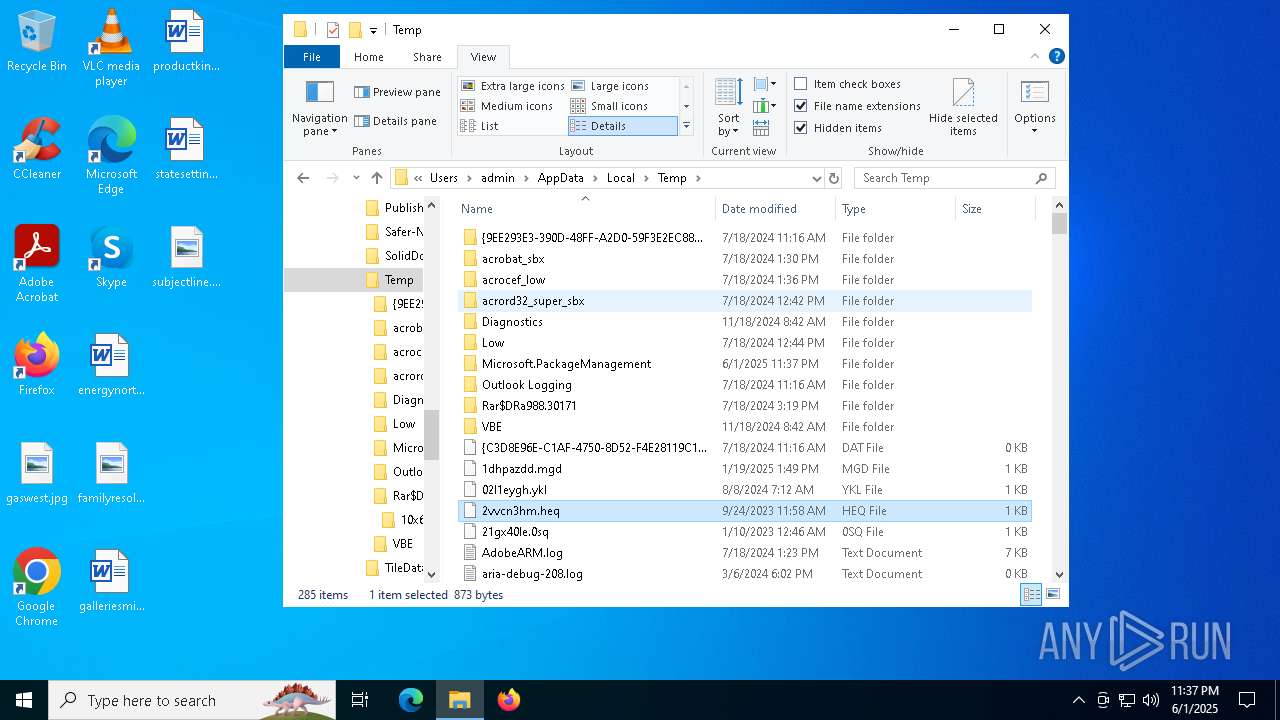
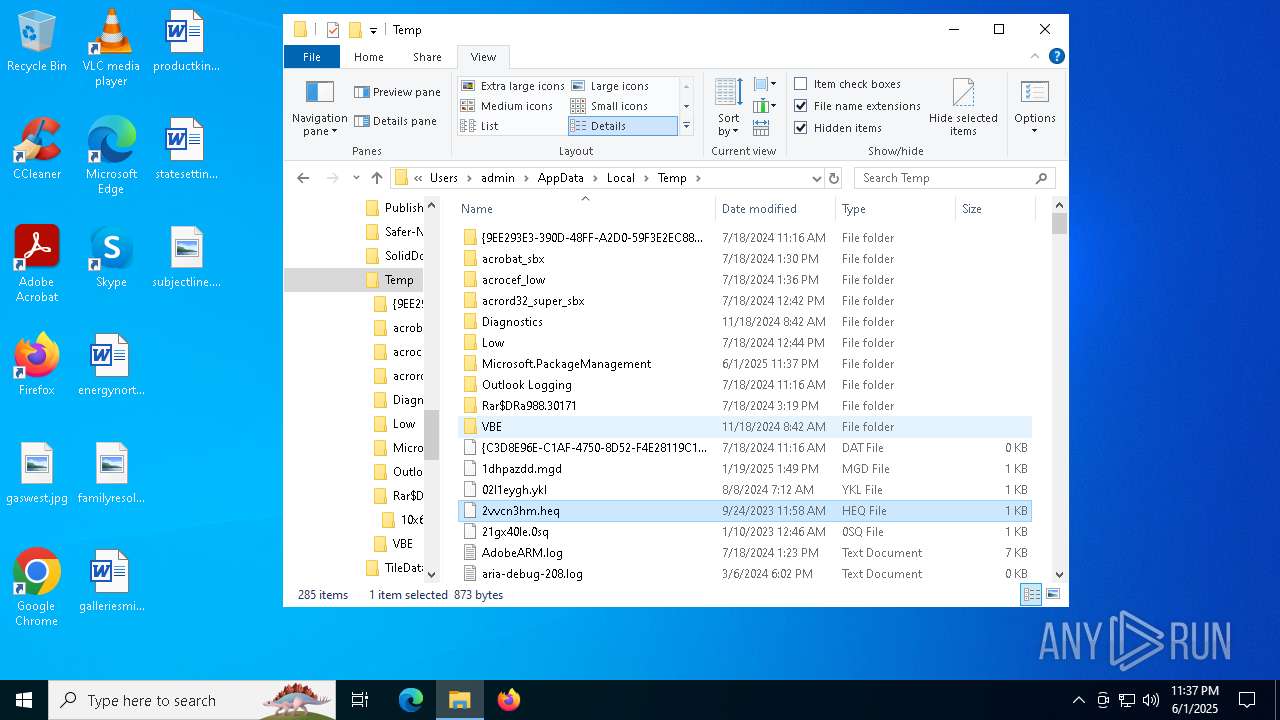
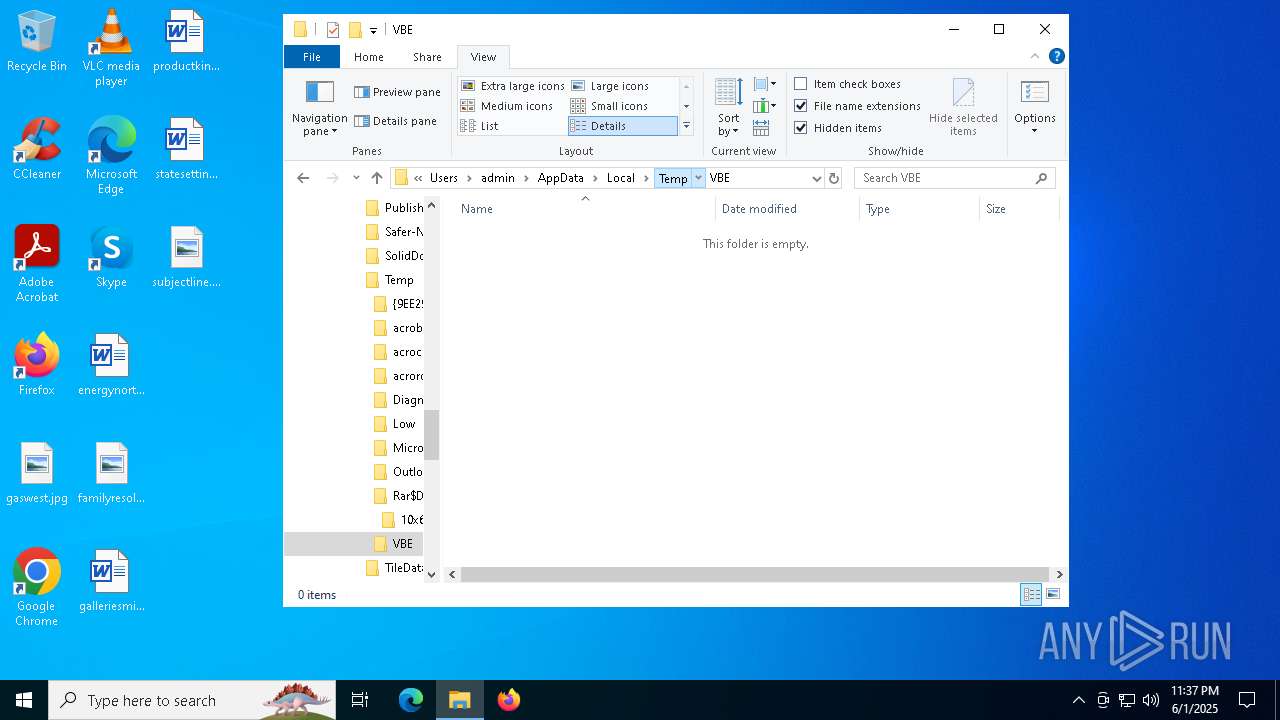
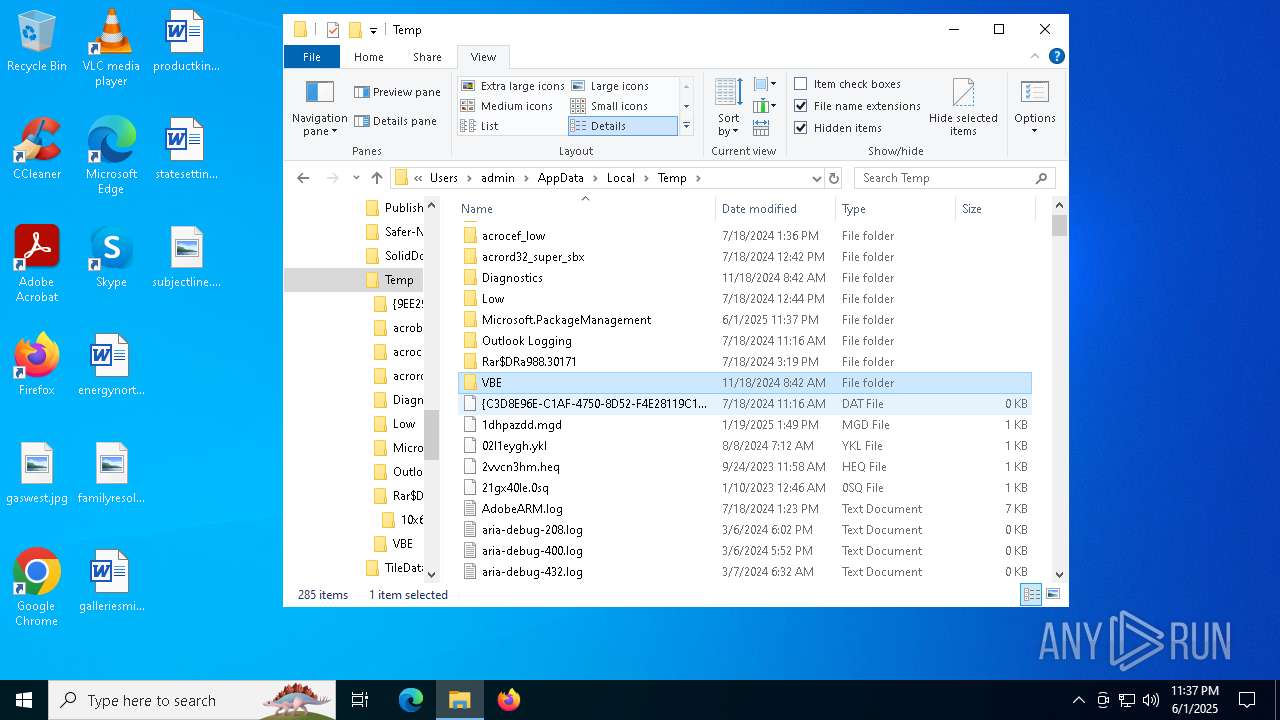
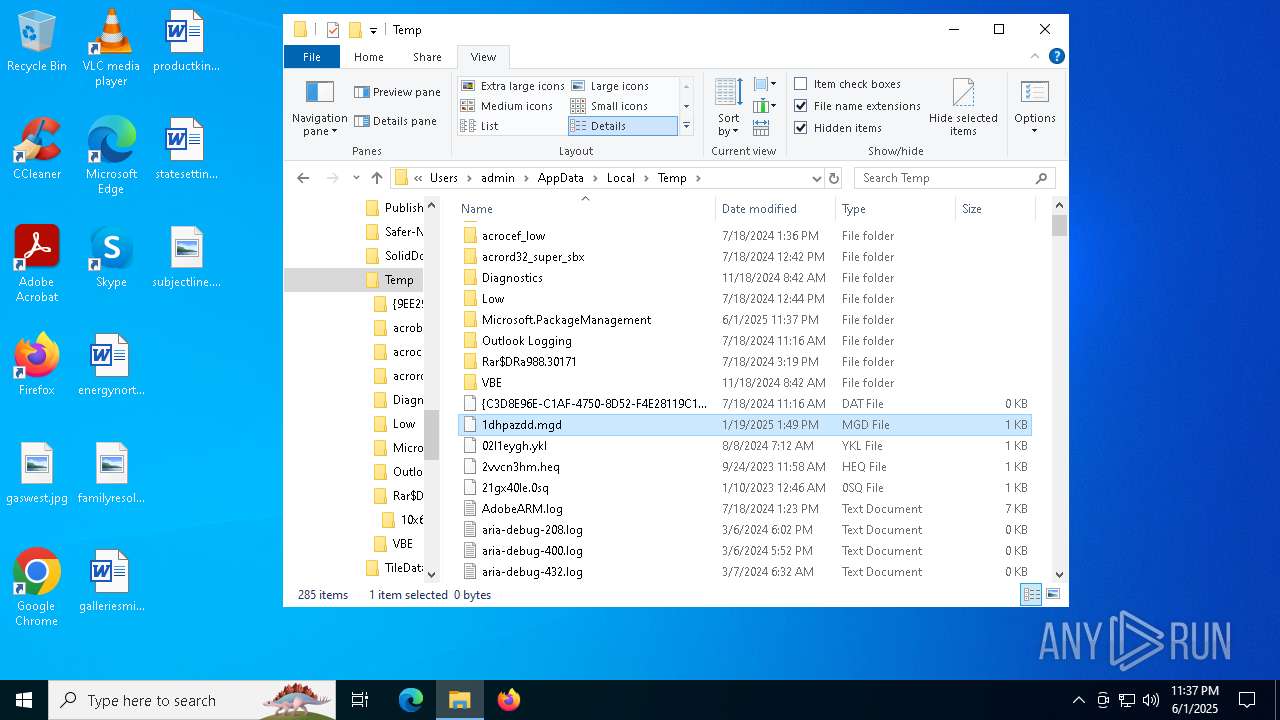
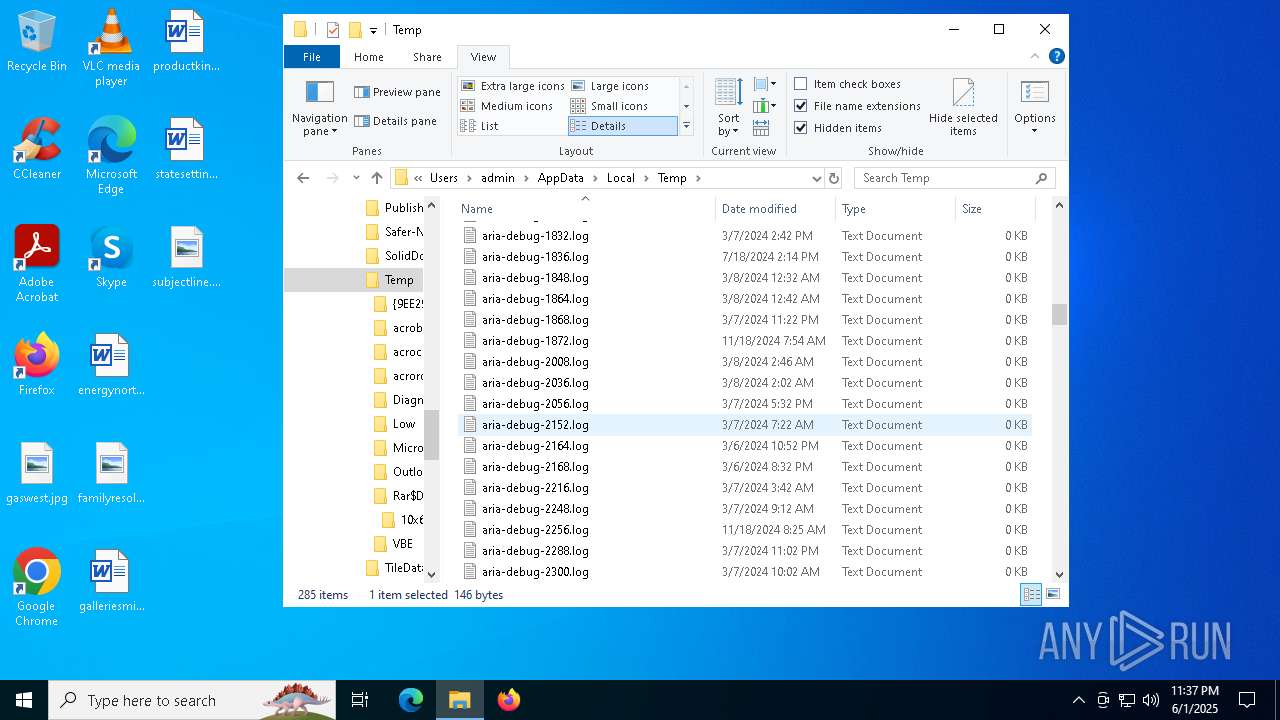
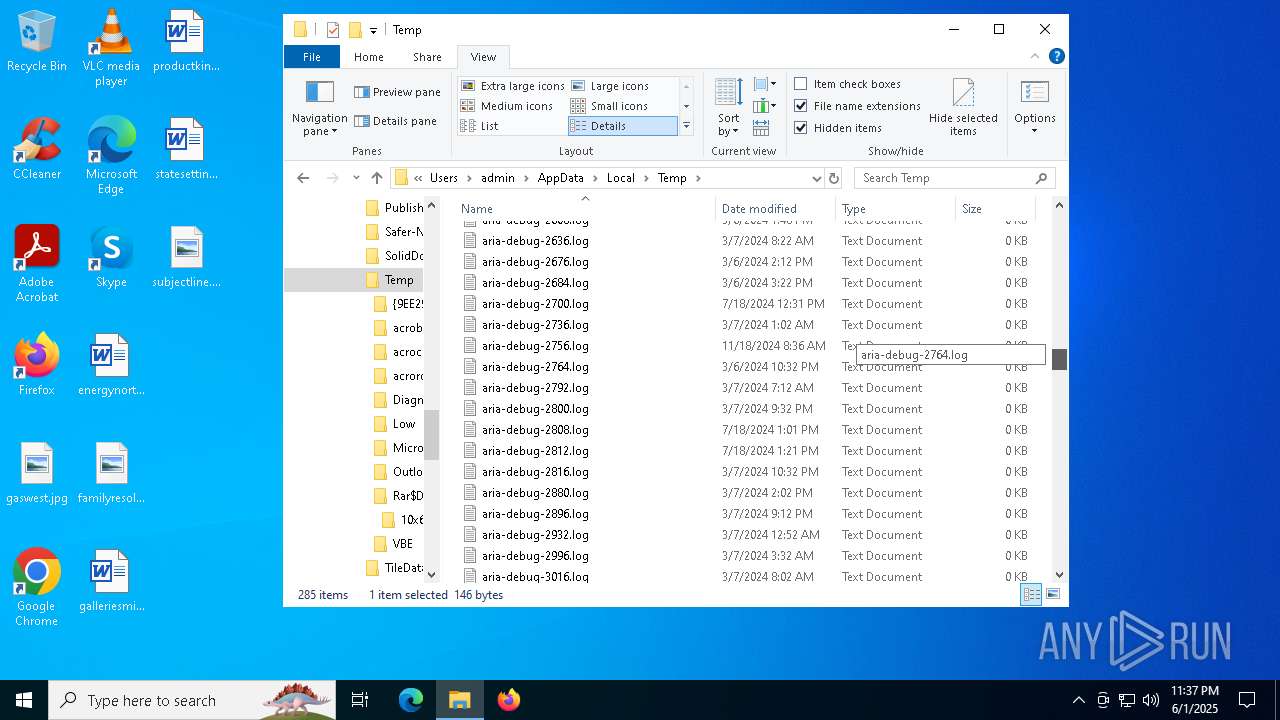
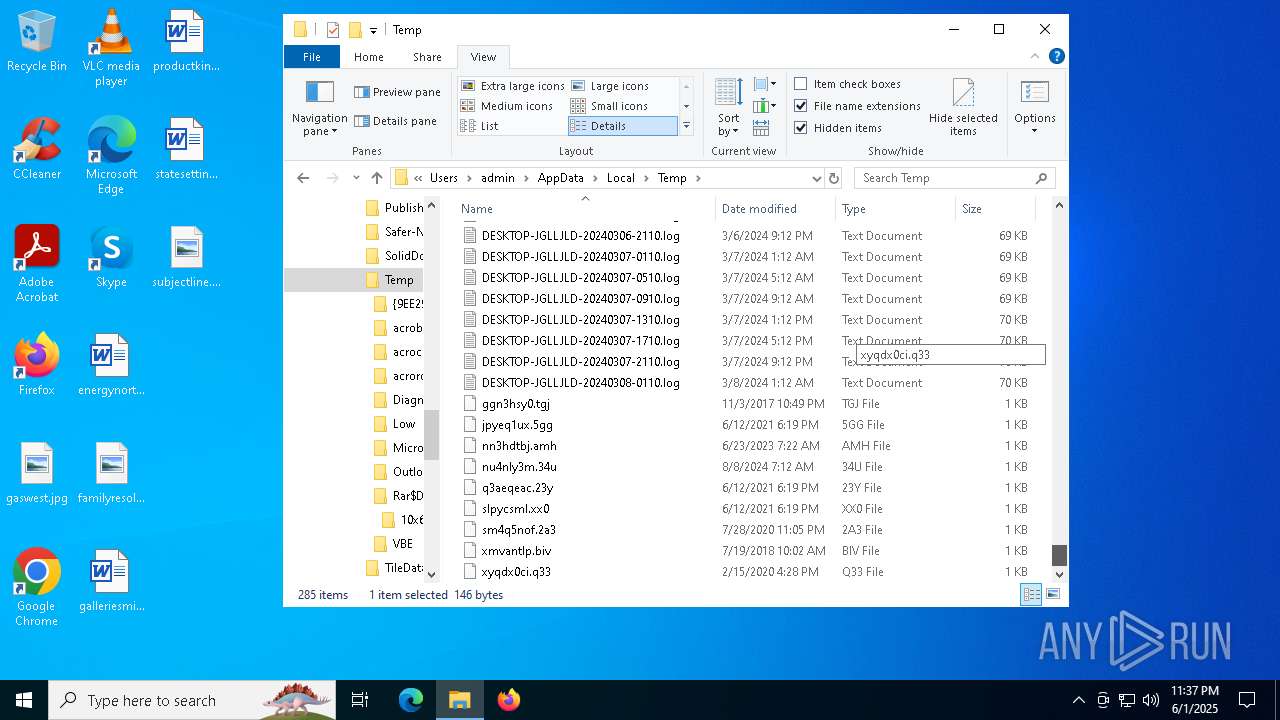
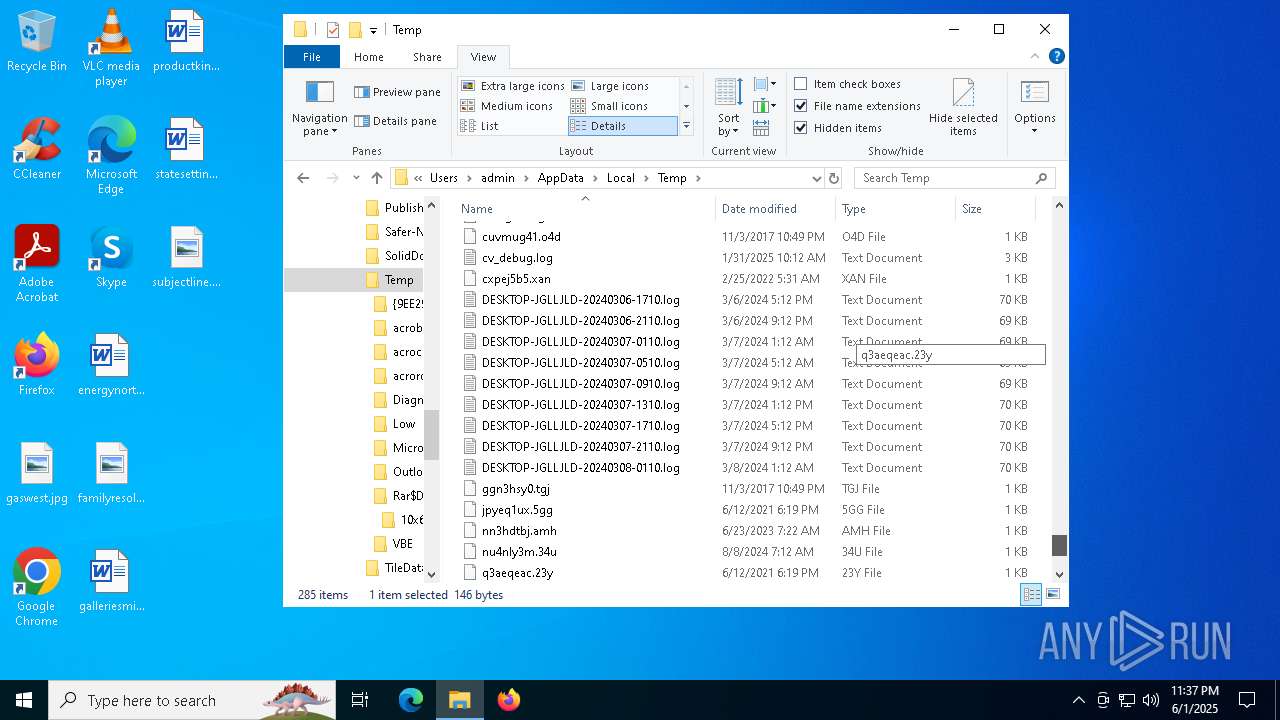
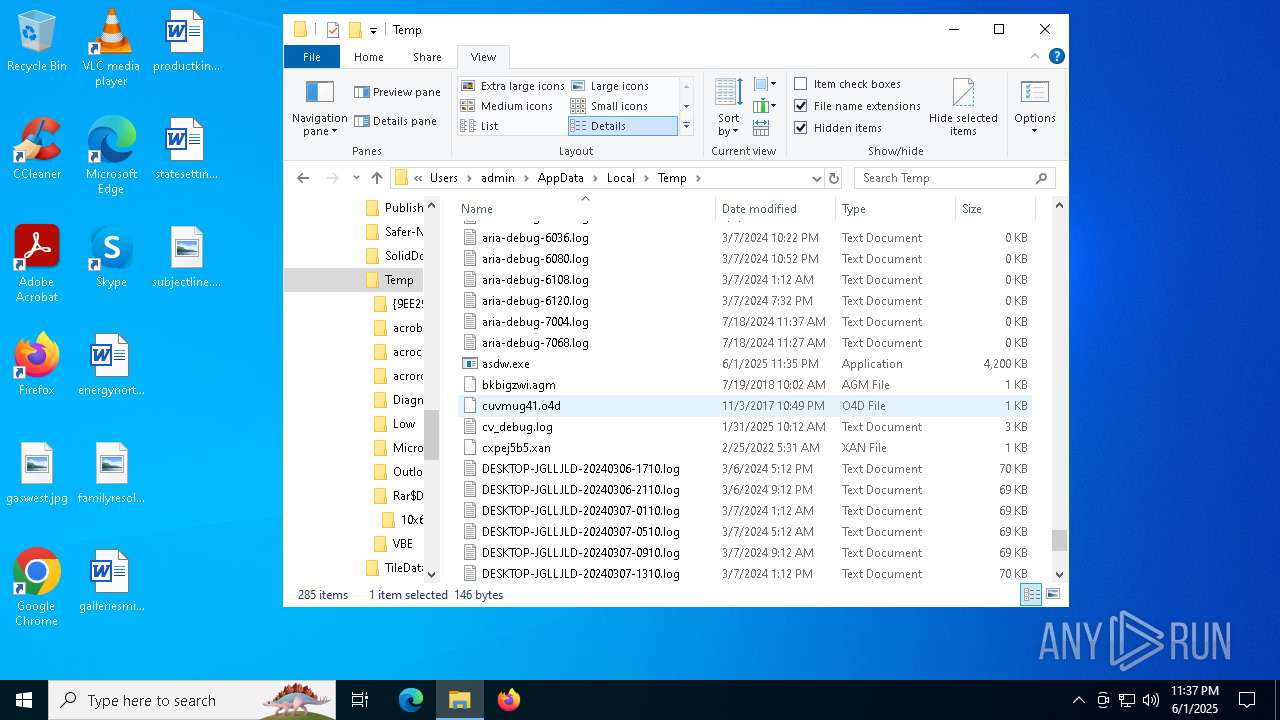
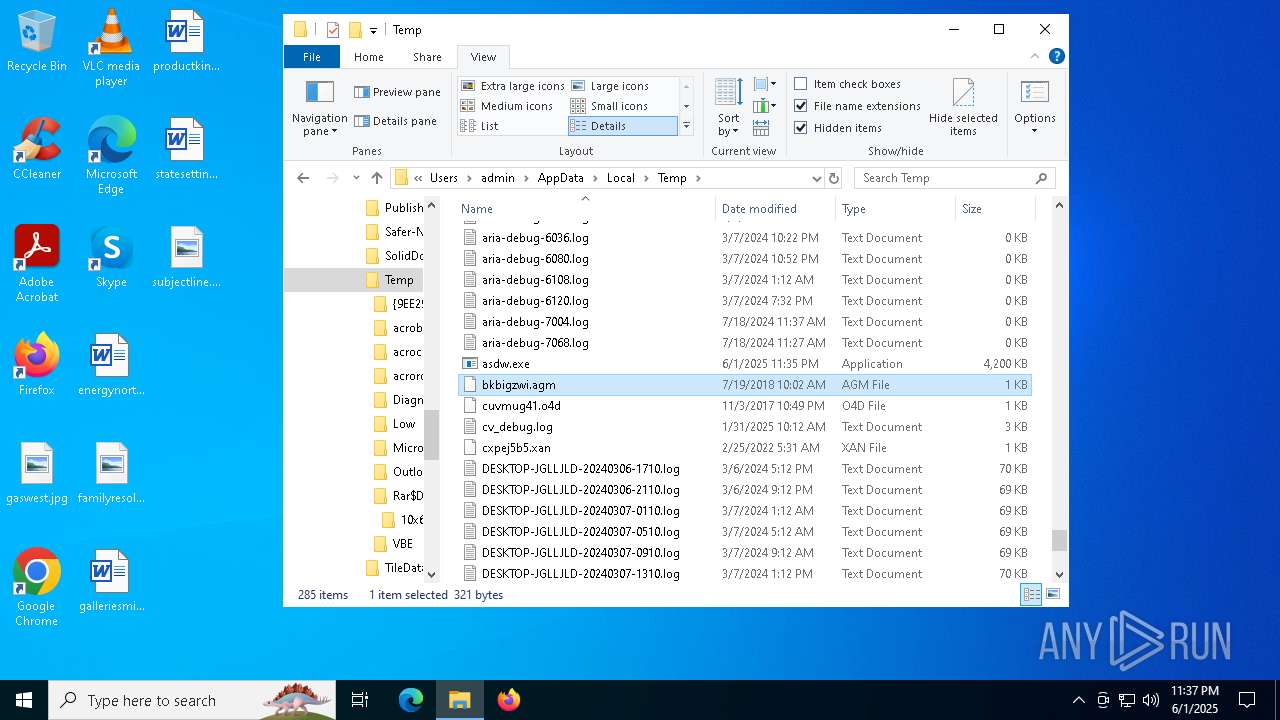
Create files in a temporary directory
- asdw.exe (PID: 8012)
- csc.exe (PID: 7036)
- cvtres.exe (PID: 2504)
Reads the machine GUID from the registry
- csc.exe (PID: 7036)
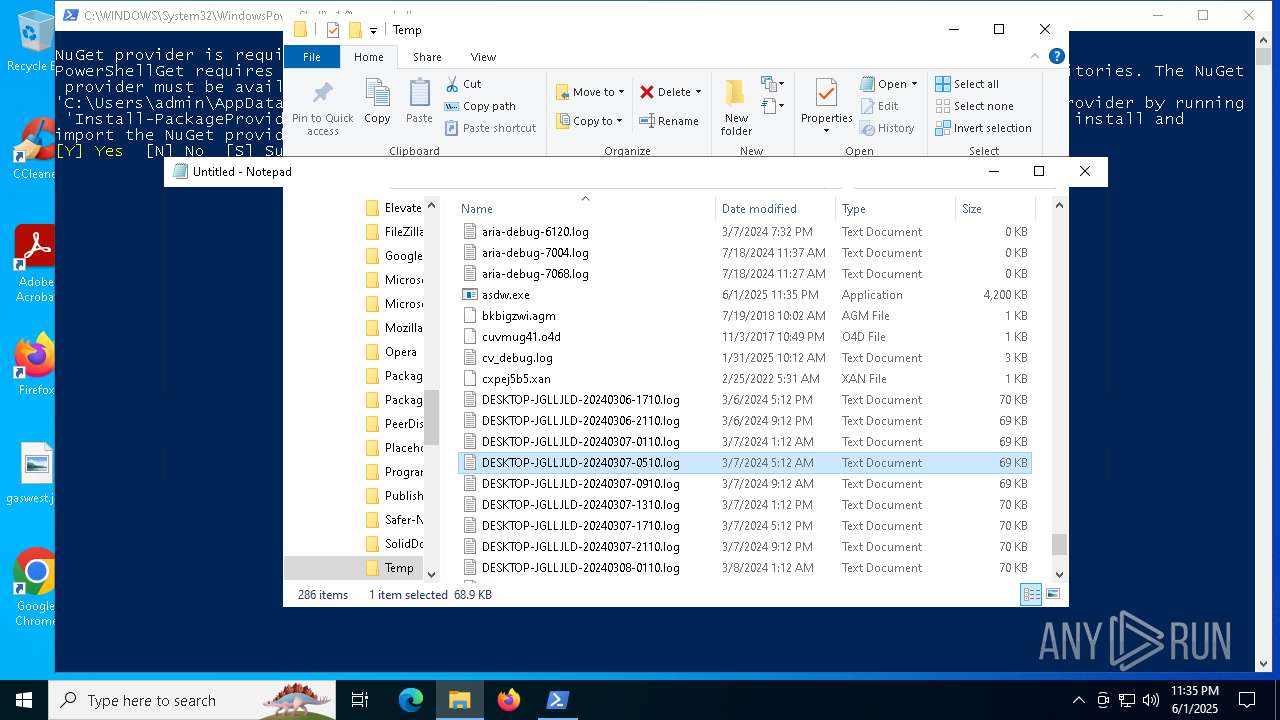
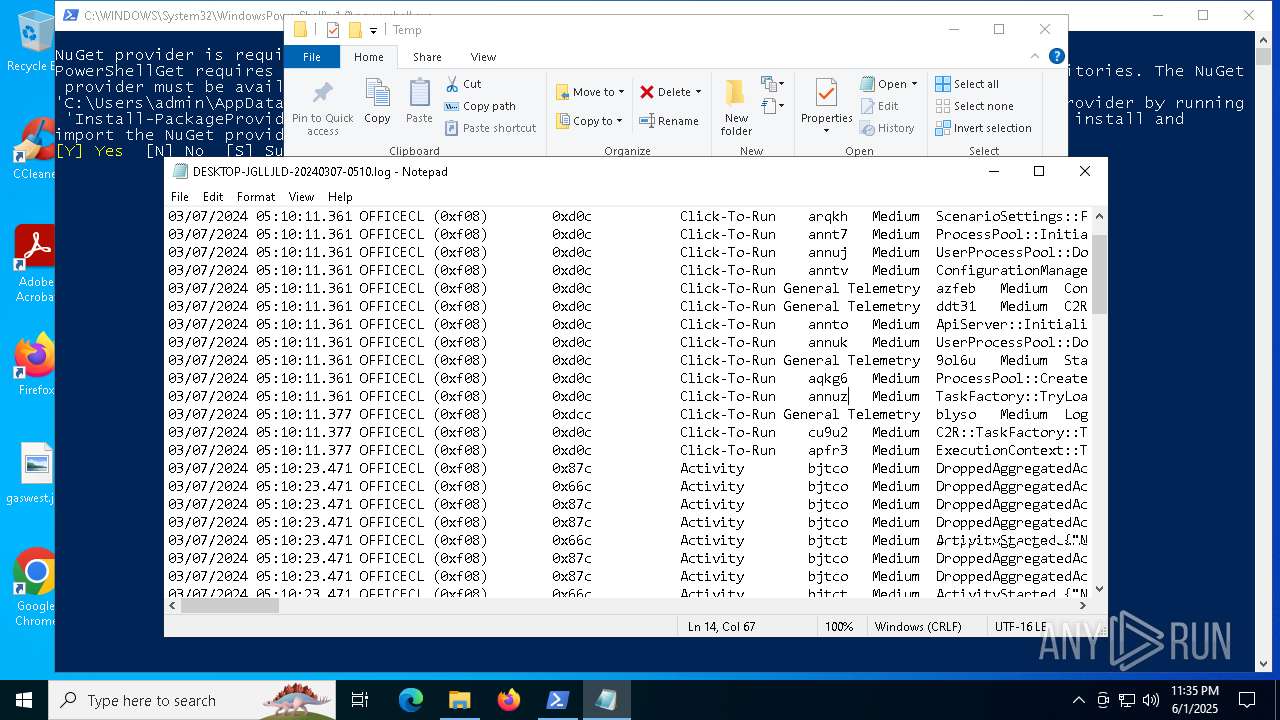
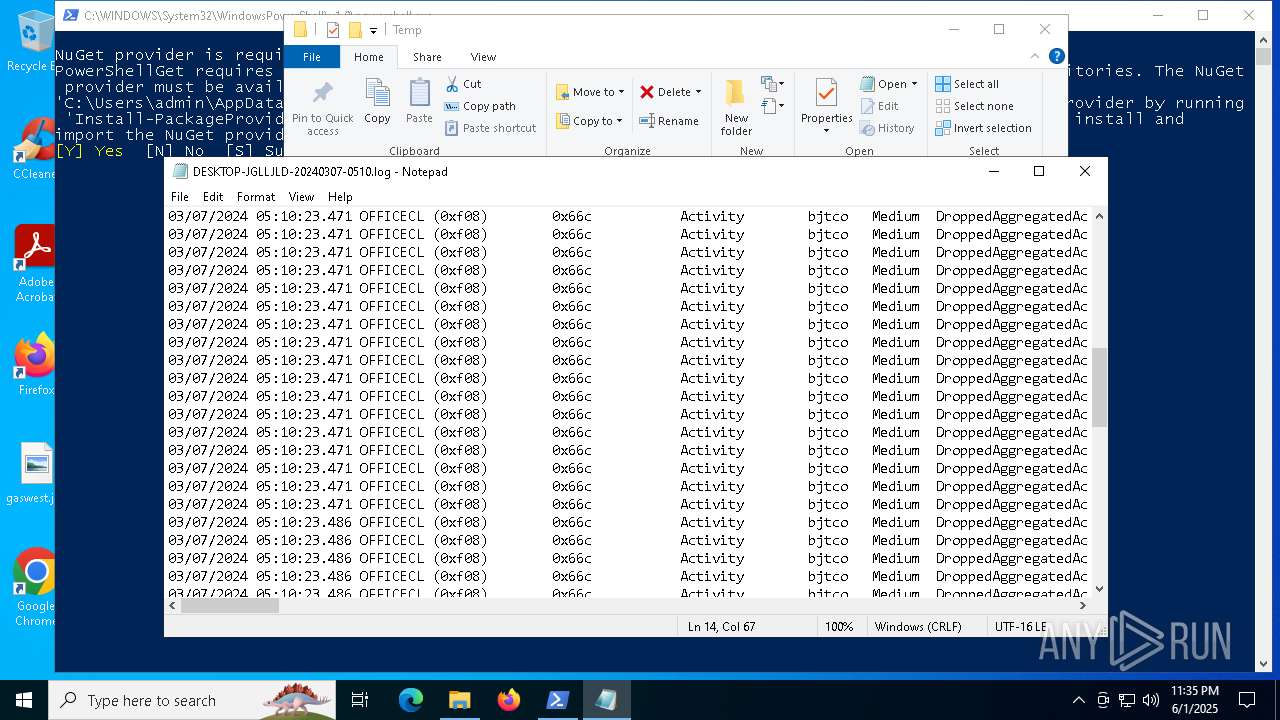
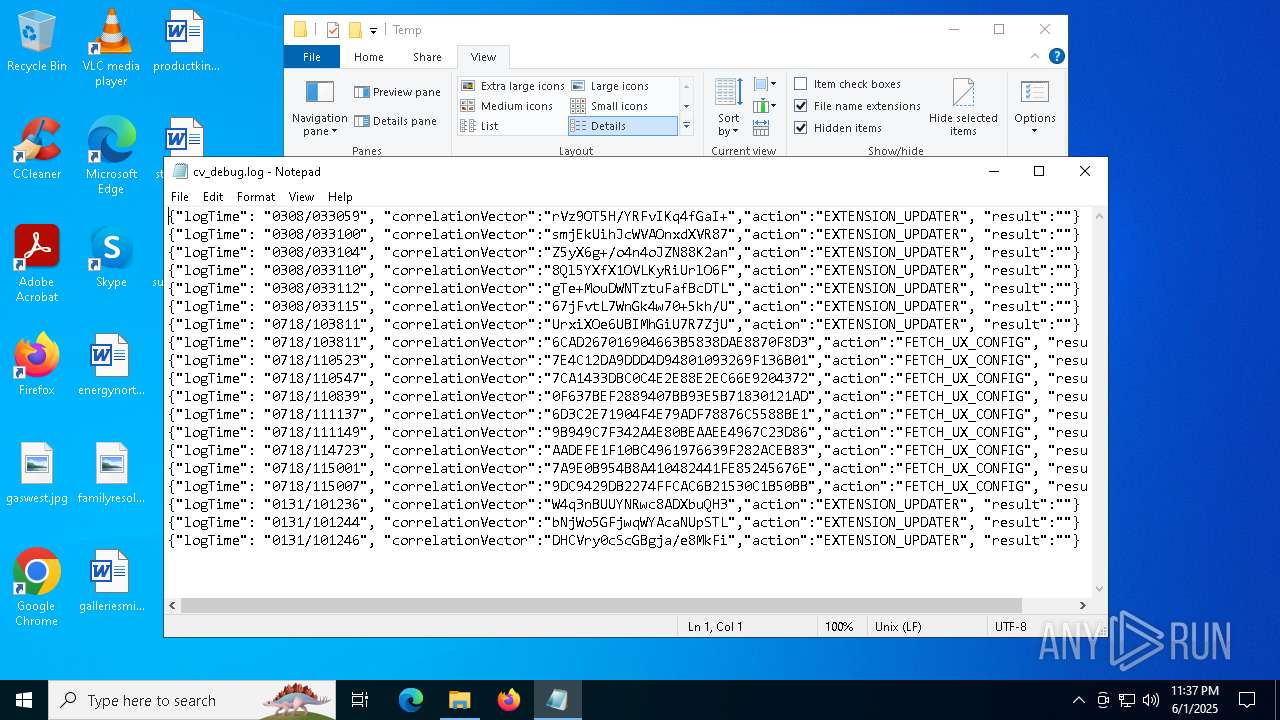
Manual execution by a user
- notepad.exe (PID: 7904)
- notepad.exe (PID: 7268)
Disables trace logs
- powershell.exe (PID: 2616)
Checks proxy server information
- powershell.exe (PID: 2616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:01 22:37:05+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.44 |
| CodeSize: | 126976 |
| InitializedDataSize: | 4172800 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xba74 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
142
Monitored processes
12
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2504 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES46D.tmp" "c:\Users\admin\AppData\Local\Temp\CSCFA3E4DCF79A248D19989B92DFDBDA86E.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
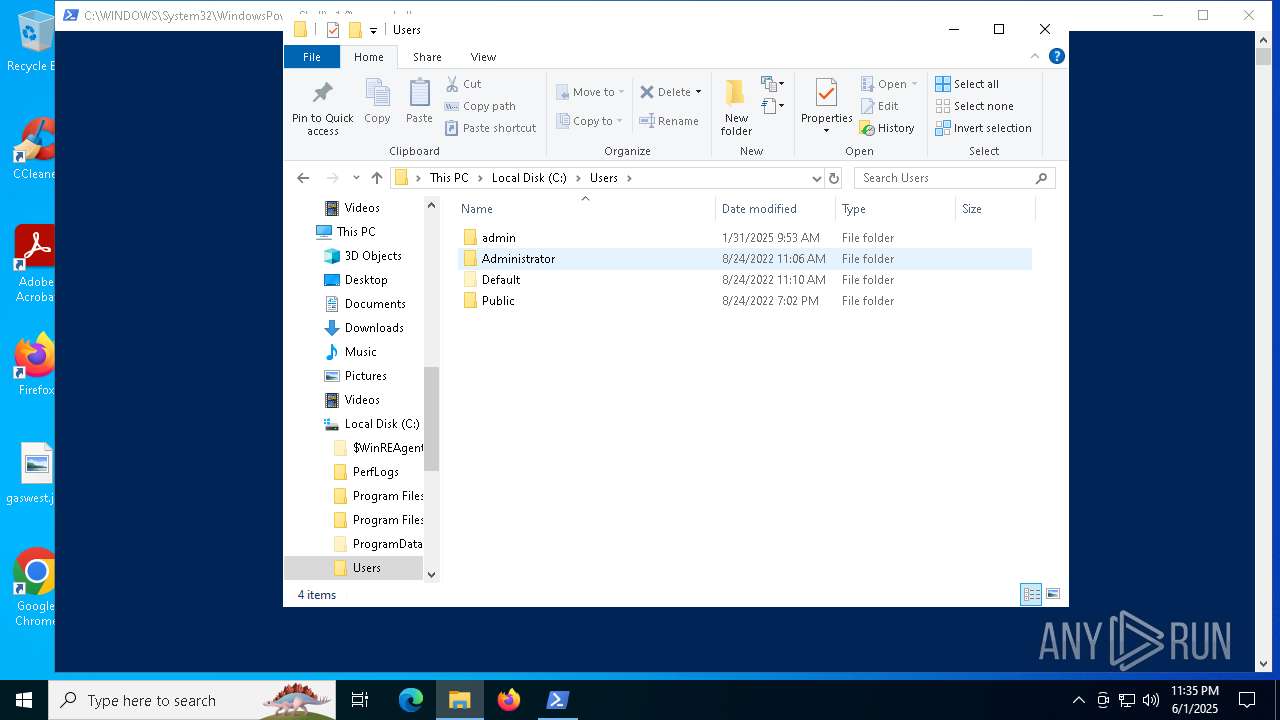
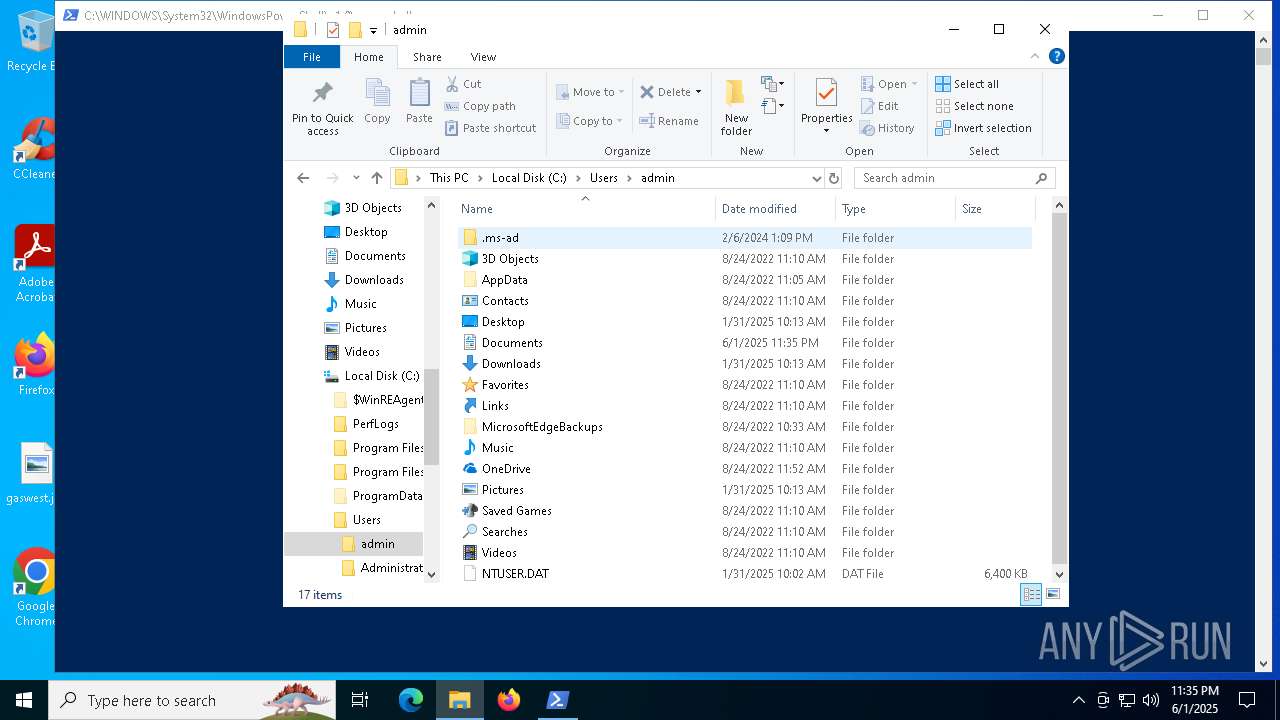
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 2616 | powershell.exe -ExecutionPolicy ByPass -Command "if (-not (Get-Module -ListAvailable -Name ps2exe)) { Install-Module -Name ps2exe -Force -Scope CurrentUser }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | amp.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2652 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3208 | "C:\Users\admin\AppData\Local\Temp\asdw.exe" | C:\Users\admin\AppData\Local\Temp\onefile_8012_133932945036832640\amp.exe | — | asdw.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3884 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6980 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7036 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\oflceh0a.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 7268 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\cv_debug.log | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7904 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\DESKTOP-JGLLJLD-20240307-0510.log | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7940 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
42 549
Read events
42 549
Write events
0
Delete events
0
Modification events
Executable files
8
Suspicious files
4
Text files
30
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8012 | asdw.exe | C:\Users\admin\AppData\Local\Temp\onefile_8012_133932945036832640\ucrtbase.dll | executable | |
MD5:3B337C2D41069B0A1E43E30F891C3813 | SHA256:C04DAEBA7E7C4B711D33993AB4C51A2E087F98F4211AEA0DCB3A216656BA0AB7 | |||
| 8012 | asdw.exe | C:\Users\admin\AppData\Local\Temp\onefile_8012_133932945036832640\python311.dll | executable | |
MD5:5A5DD7CAD8028097842B0AFEF45BFBCF | SHA256:A811C7516F531F1515D10743AE78004DD627EBA0DC2D3BC0D2E033B2722043CE | |||
| 7036 | csc.exe | C:\Users\admin\AppData\Local\Temp\oflceh0a.out | text | |
MD5:A42F7D963A2532776C6CFCBAE1020630 | SHA256:CE480A8312A6EB6F366D4F6B0A908155373A41FBF6D240B2F693A03D29170B6B | |||
| 2616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Microsoft.PackageManagement\52vyxfy4.jxc | xml | |
MD5:59146FA8BBC0DEFDEA515CDE5D5CCB59 | SHA256:6CC5CA22678B2300286AC6451FD66A3245F0153013430D899448DFC2A1E51291 | |||
| 7036 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCFA3E4DCF79A248D19989B92DFDBDA86E.TMP | binary | |
MD5:684BC0880DC0C2763DE89B0A31D7A6B4 | SHA256:E4B92D6A5359AFCBAB7304262EB8EBAF1B80FB634A1F4C56377DBDE4057FFE82 | |||
| 2616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1fdng2pi.qfi.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Microsoft.PackageManagement\eaefoytb.jeh | xml | |
MD5:D35B8C04DA801DE749B12D5DA8A0B9A0 | SHA256:9CB8C56FA40380069256C24AB816BFD0E08201E16B654BD76D0EC0608DC1CCE1 | |||
| 2616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\oflceh0a.cmdline | text | |
MD5:C811D01EA002A47B37A3ABDD3BEE378A | SHA256:06FCEA106EACE3EB06E126203362C1629F072C1E320CF84B3FA0090DFC67A279 | |||
| 2616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Microsoft.PackageManagement\0zoeckcm.awj | xml | |
MD5:26C50195ABBFDE6611A4CAEE3585960B | SHA256:B2915EDDDBD8029336C3933115B8D8E9471FB63039177901606C5D101770E059 | |||
| 2616 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_502auo2w.1hy.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
36
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7728 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6960 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7728 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1180 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6960 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6960 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2924 | SearchApp.exe | 92.123.104.38:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2924 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
onegetcdn.azureedge.net |
| whitelisted |
th.bing.com |
| whitelisted |
login.live.com |
| whitelisted |