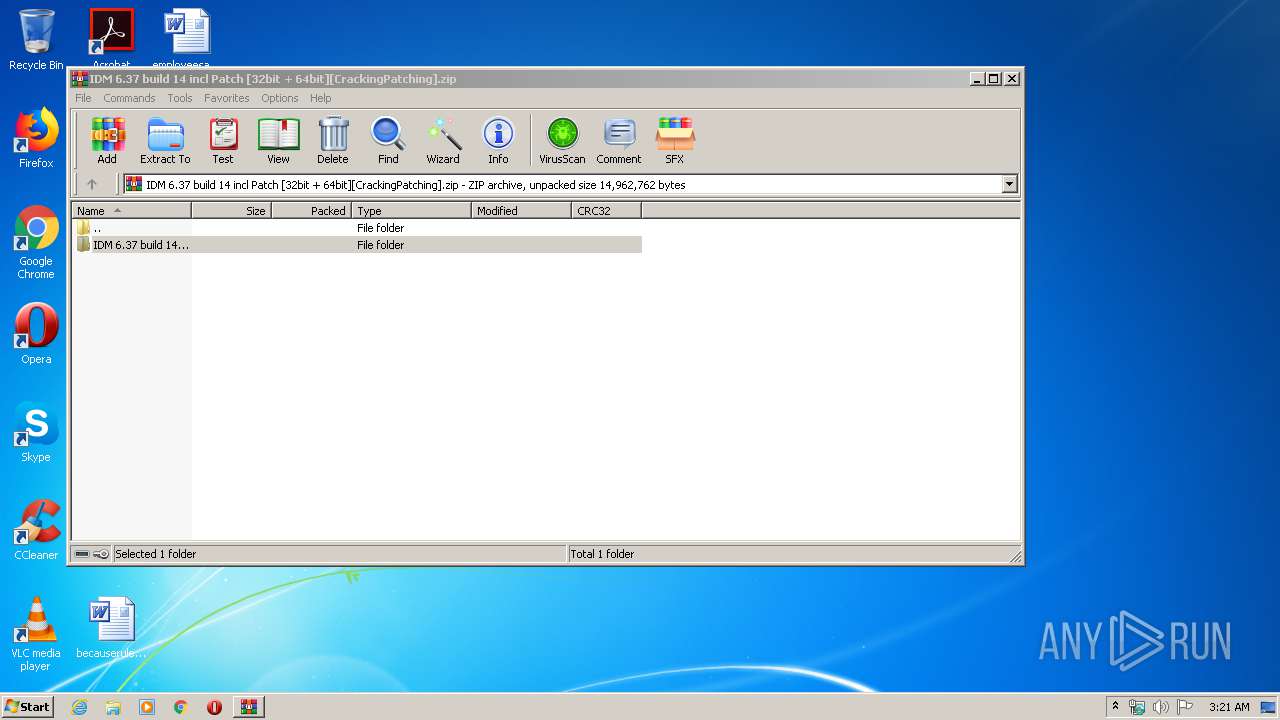
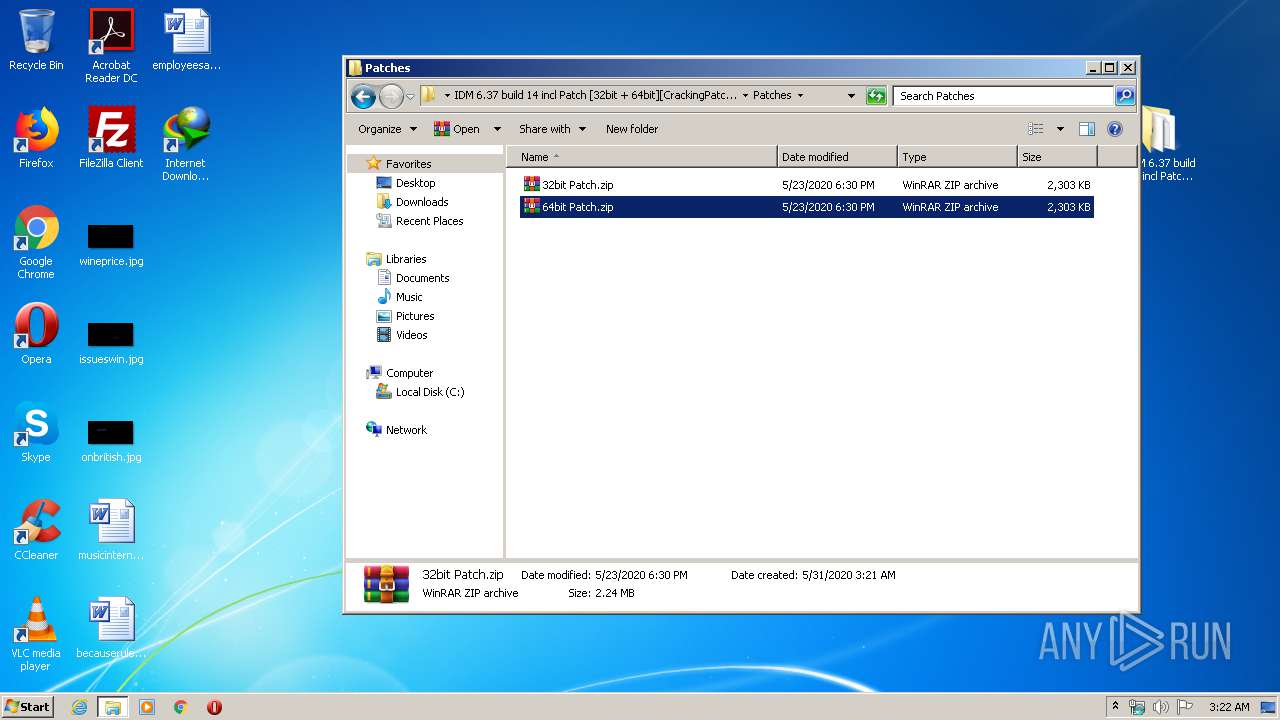
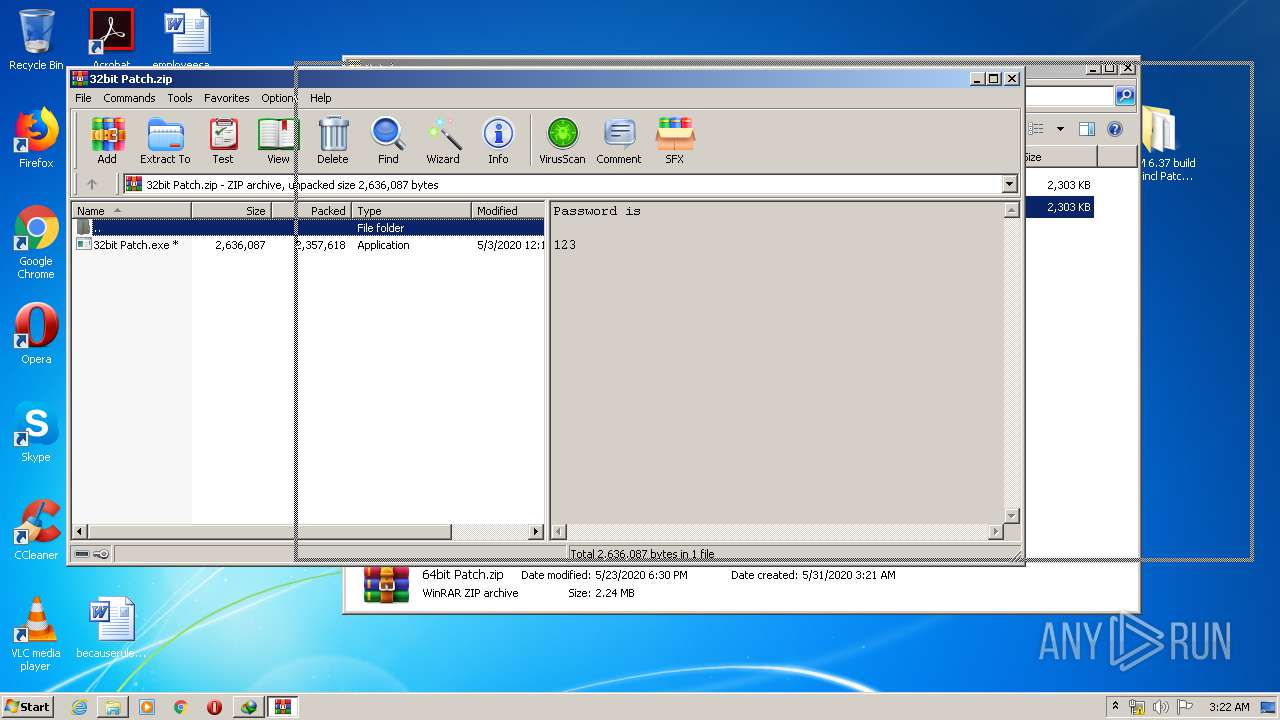
| File name: | IDM 6.37 build 14 incl Patch [32bit + 64bit][CrackingPatching].zip |
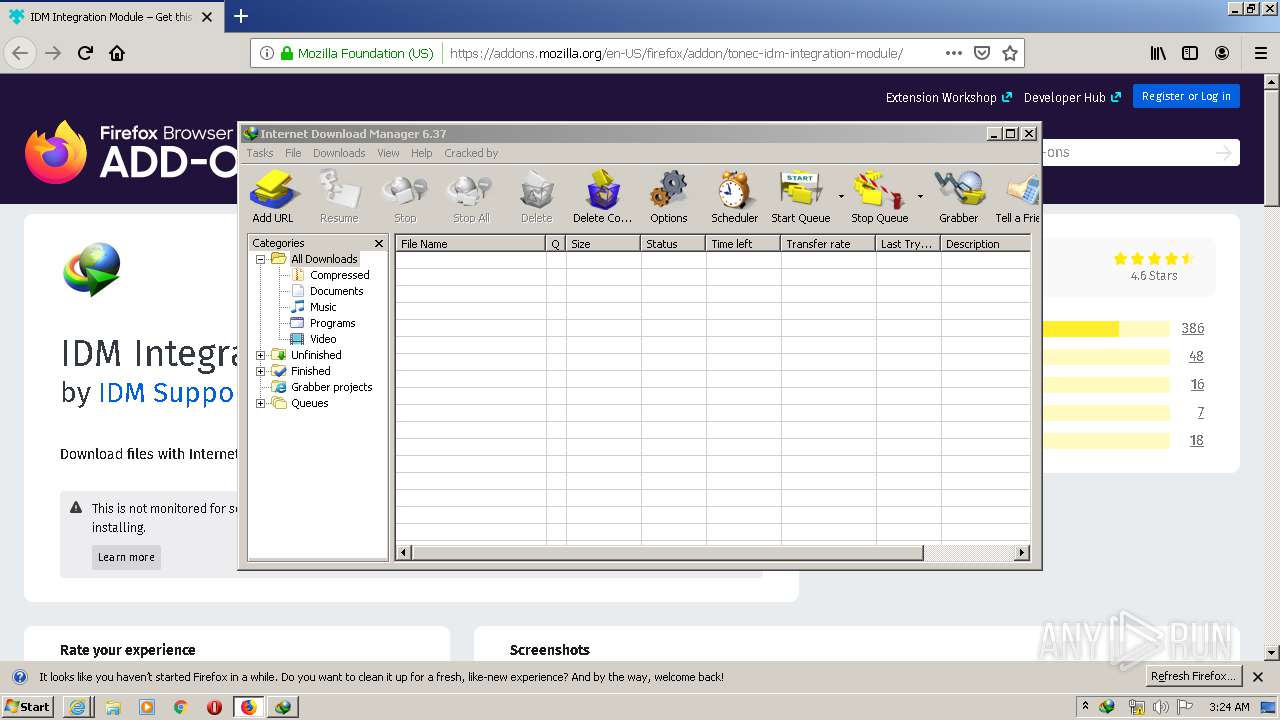
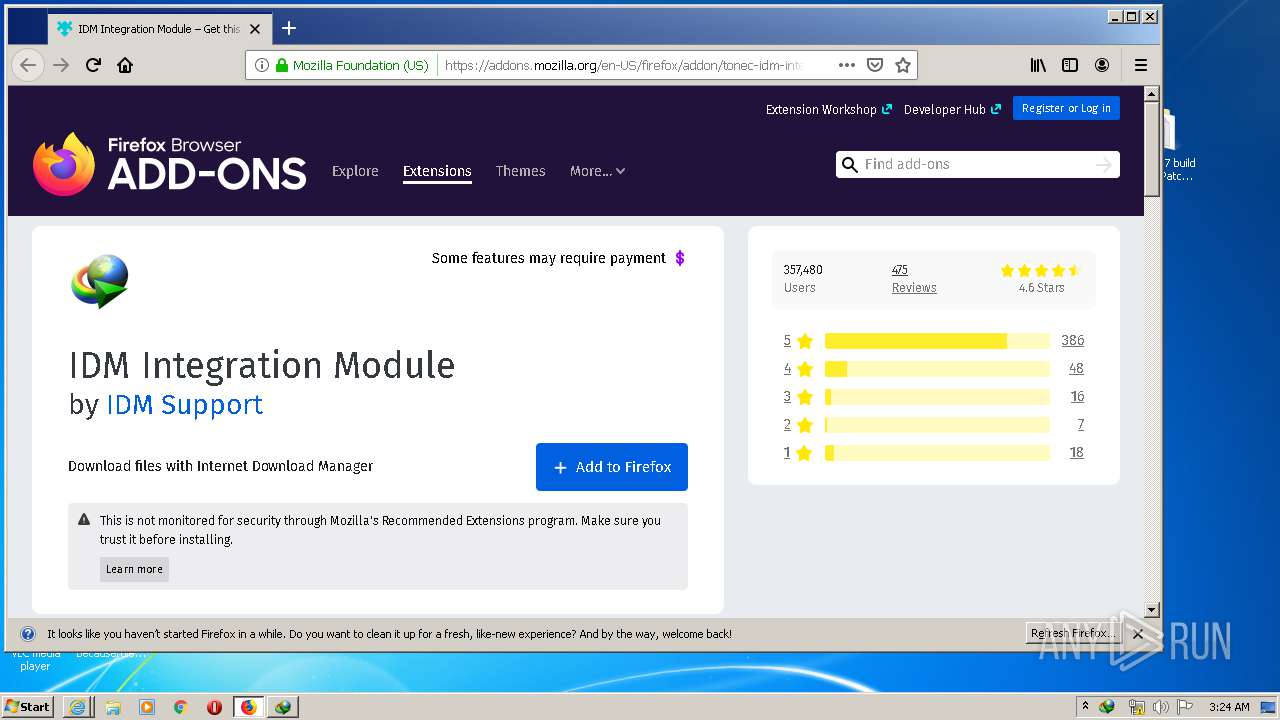
| Full analysis: | https://app.any.run/tasks/bcf500eb-d079-4390-ade9-08faeee9e62d |
| Verdict: | Malicious activity |
| Analysis date: | May 31, 2020, 02:21:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | C166FA1EF56470AC380B27337034BAEB |
| SHA1: | 1678D75571B0162495A2CC184DBA058F4B08F153 |
| SHA256: | F112EC8F880FC52AE1B4F395A1C1BB2CB4038EA3E7BA7655A974312FBB2210E1 |
| SSDEEP: | 393216:OpYZmFIAwoenYanntB3M3qwzum5Rrf8Bn5A5+b:OpYZ2IVxnnCDRj8Hb |
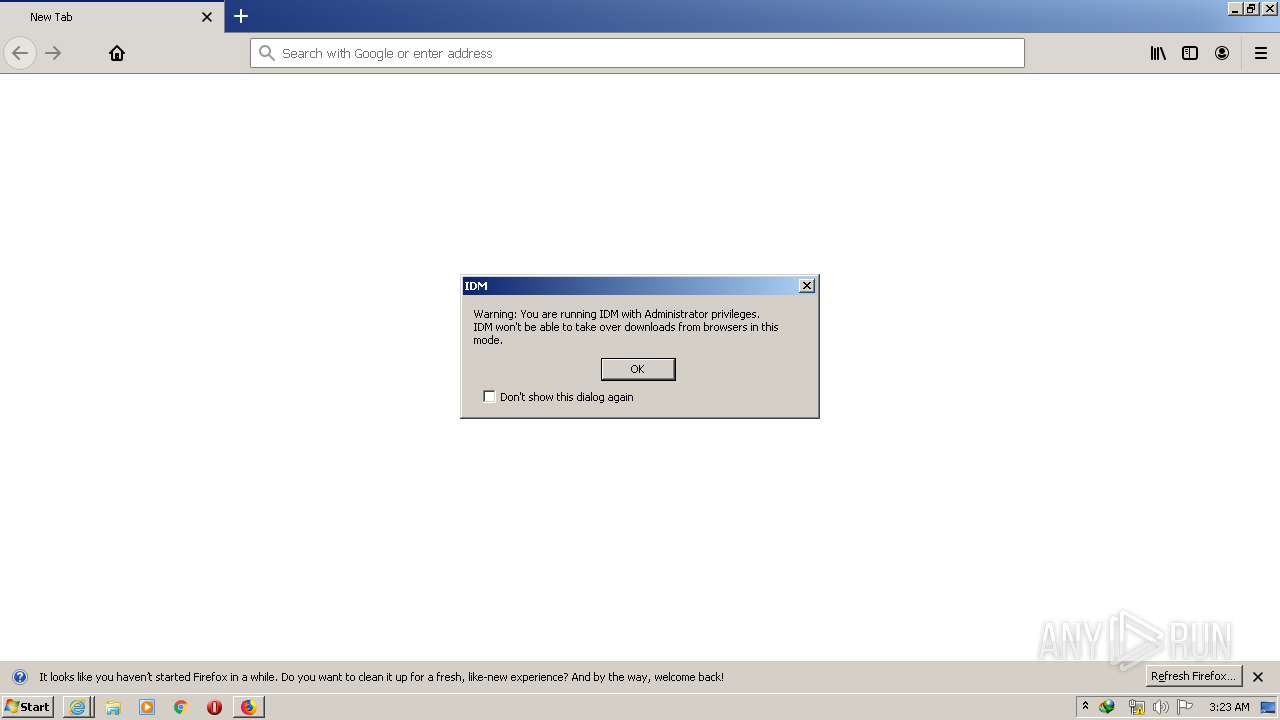
MALICIOUS
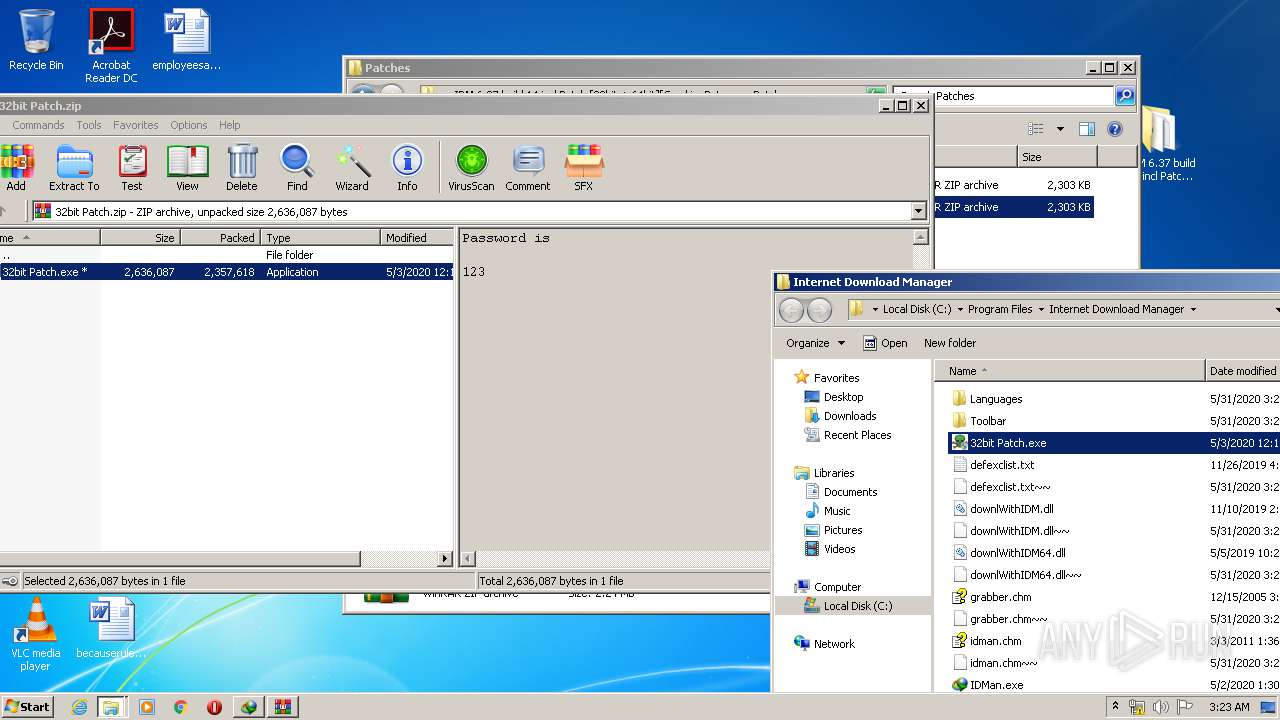
Application was dropped or rewritten from another process
- 32bit Patch.exe (PID: 1092)
- 32bit Patch.exe (PID: 3968)
- IDMan.exe (PID: 2476)
Changes the autorun value in the registry
- rundll32.exe (PID: 2912)
- IDMan.exe (PID: 2476)
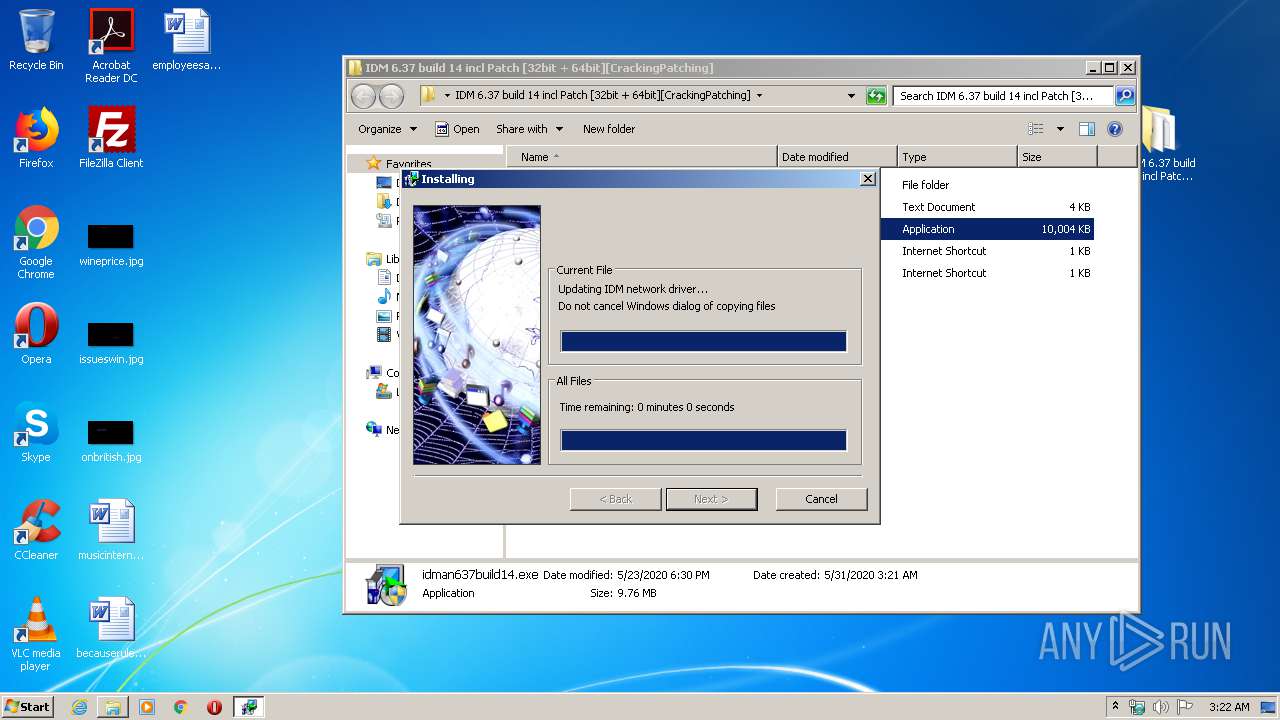
Starts NET.EXE for service management
- Uninstall.exe (PID: 2700)
Changes settings of System certificates
- IDMan.exe (PID: 1456)
SUSPICIOUS
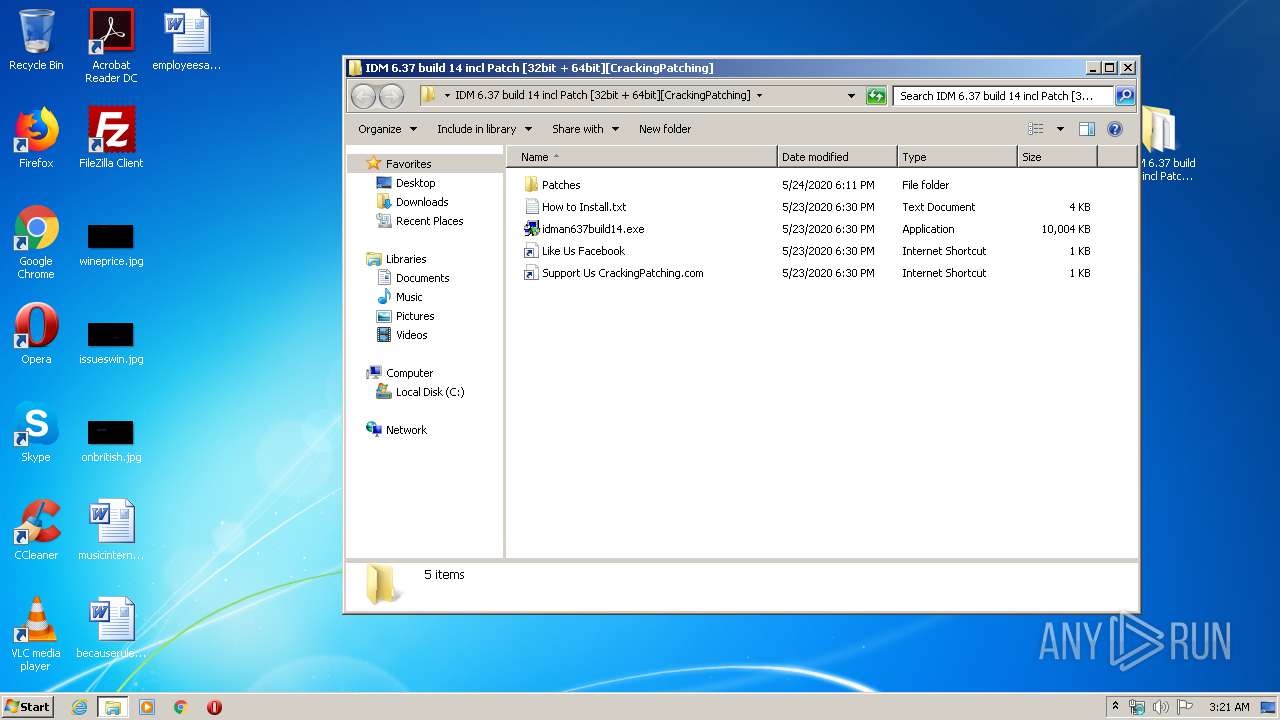
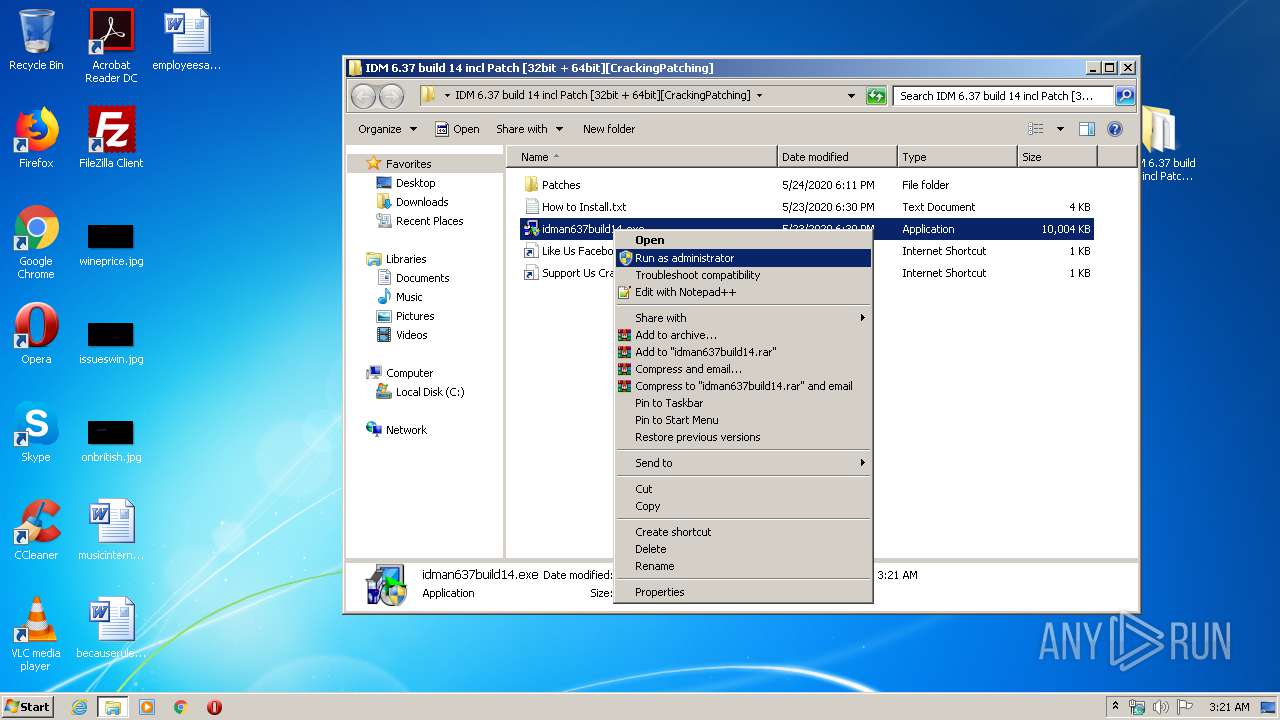
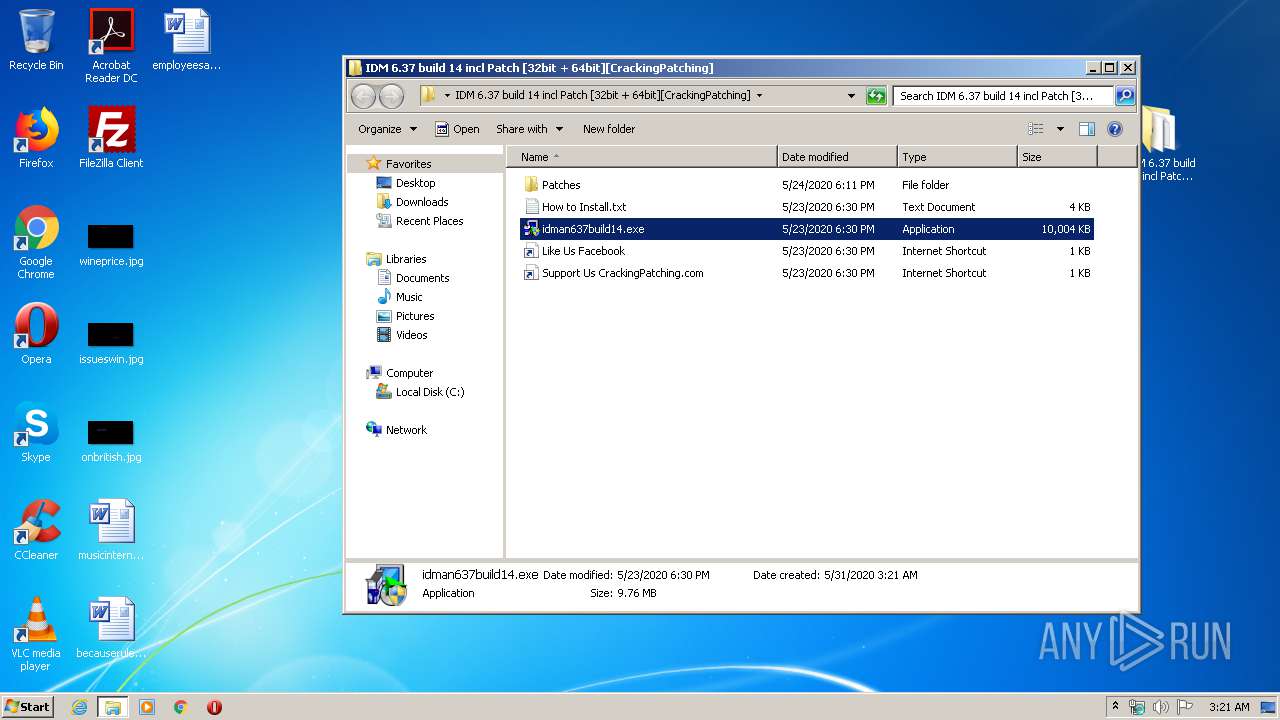
Starts application with an unusual extension
- idman637build14.exe (PID: 3028)
Executed via COM
- DllHost.exe (PID: 3280)
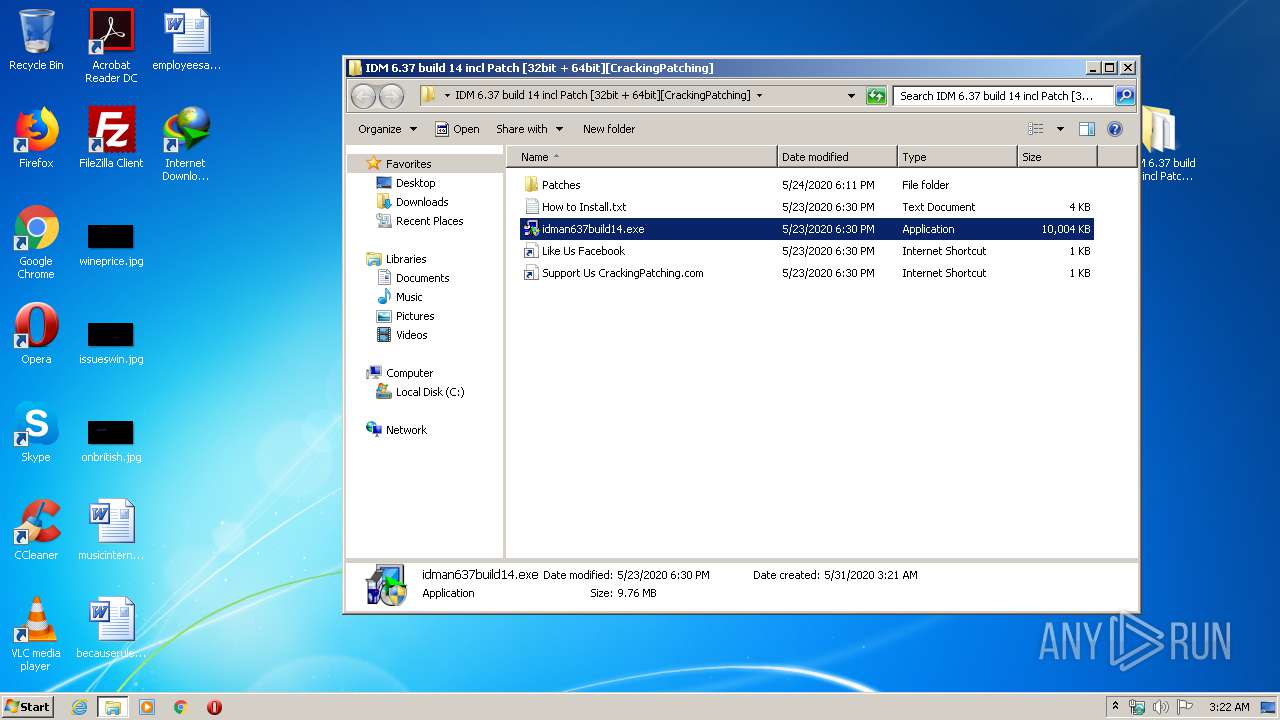
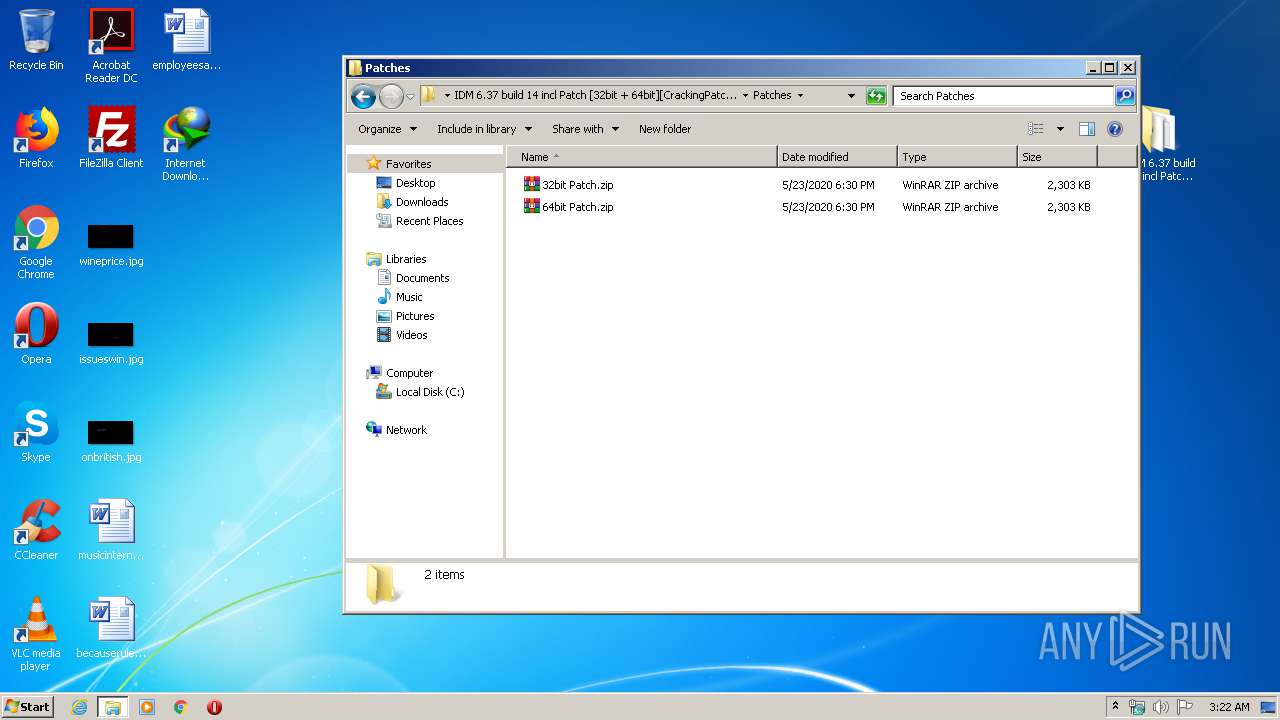
Executable content was dropped or overwritten
- DllHost.exe (PID: 3280)
- WinRAR.exe (PID: 1872)
- 32bit Patch.exe (PID: 1092)
- IDMan.exe (PID: 2476)
- rundll32.exe (PID: 2912)
Creates COM task schedule object
- IDMan.exe (PID: 1456)
- IDM1.tmp (PID: 448)
- IDMan.exe (PID: 2476)
- Uninstall.exe (PID: 2700)
Creates a software uninstall entry
- IDM1.tmp (PID: 448)
- 32bit Patch.exe (PID: 1092)
Creates files in the user directory
- IDMan.exe (PID: 1456)
- IDM1.tmp (PID: 448)
- IDMan.exe (PID: 2476)
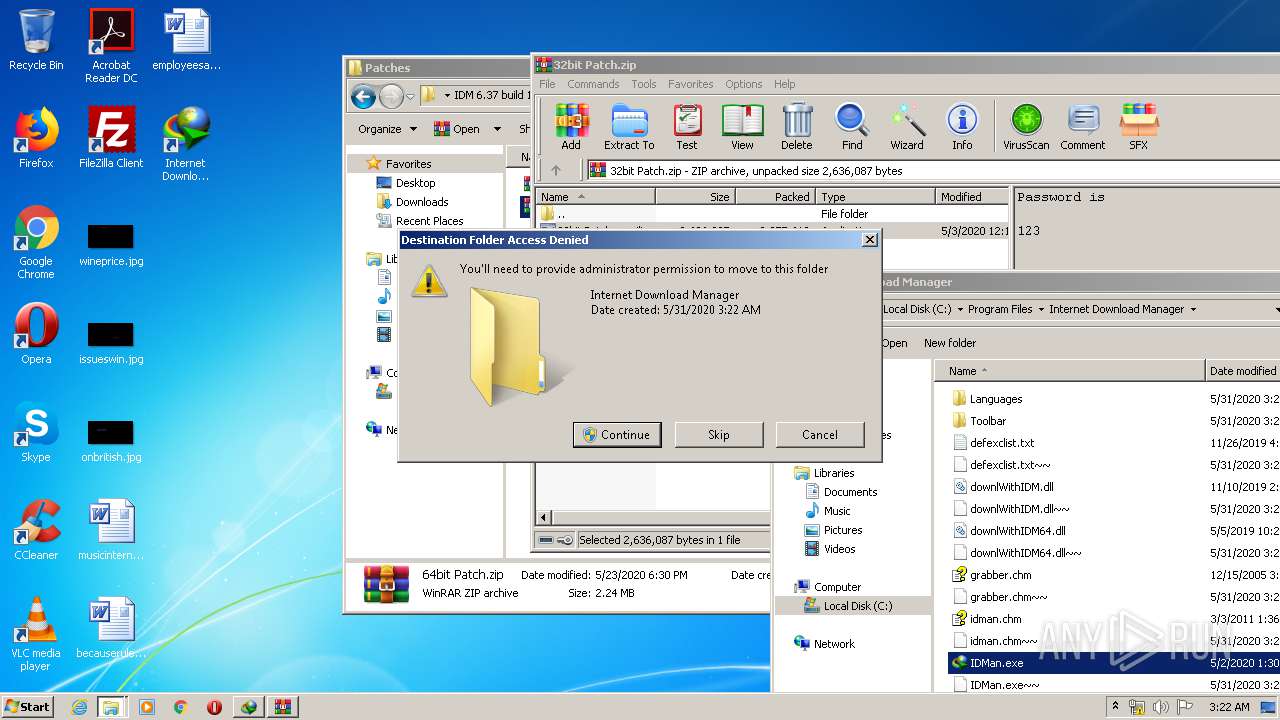
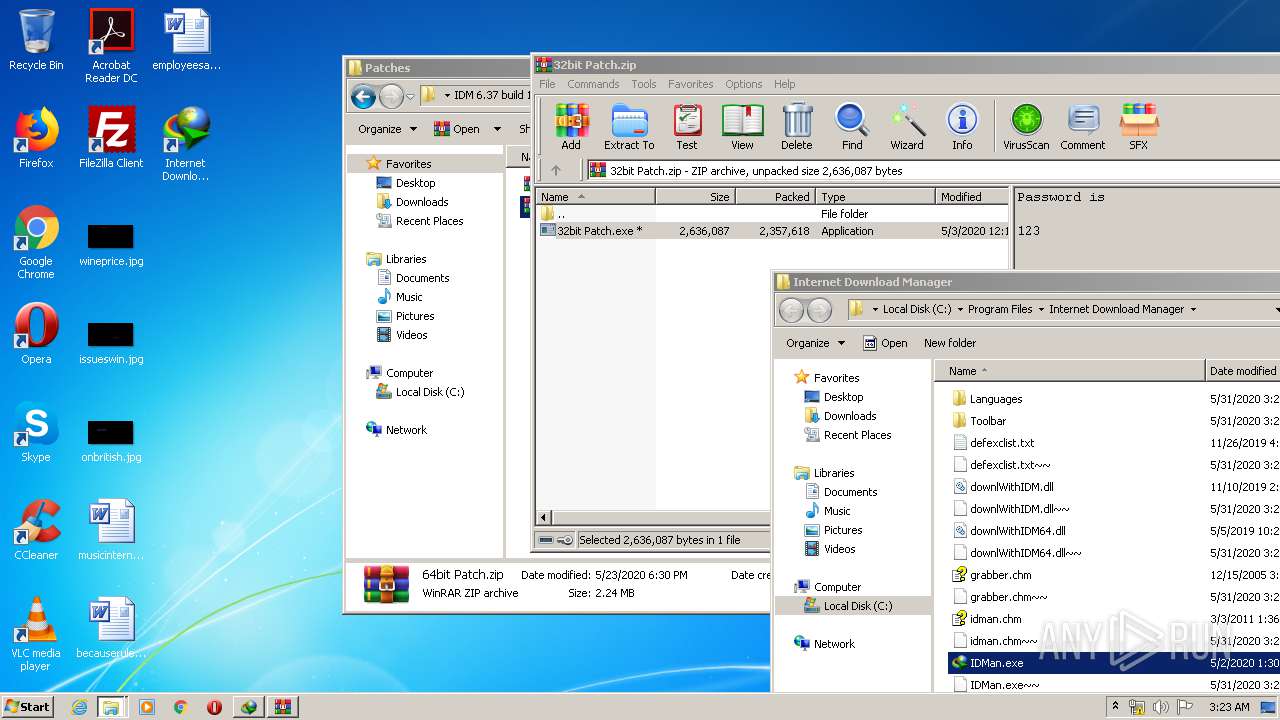
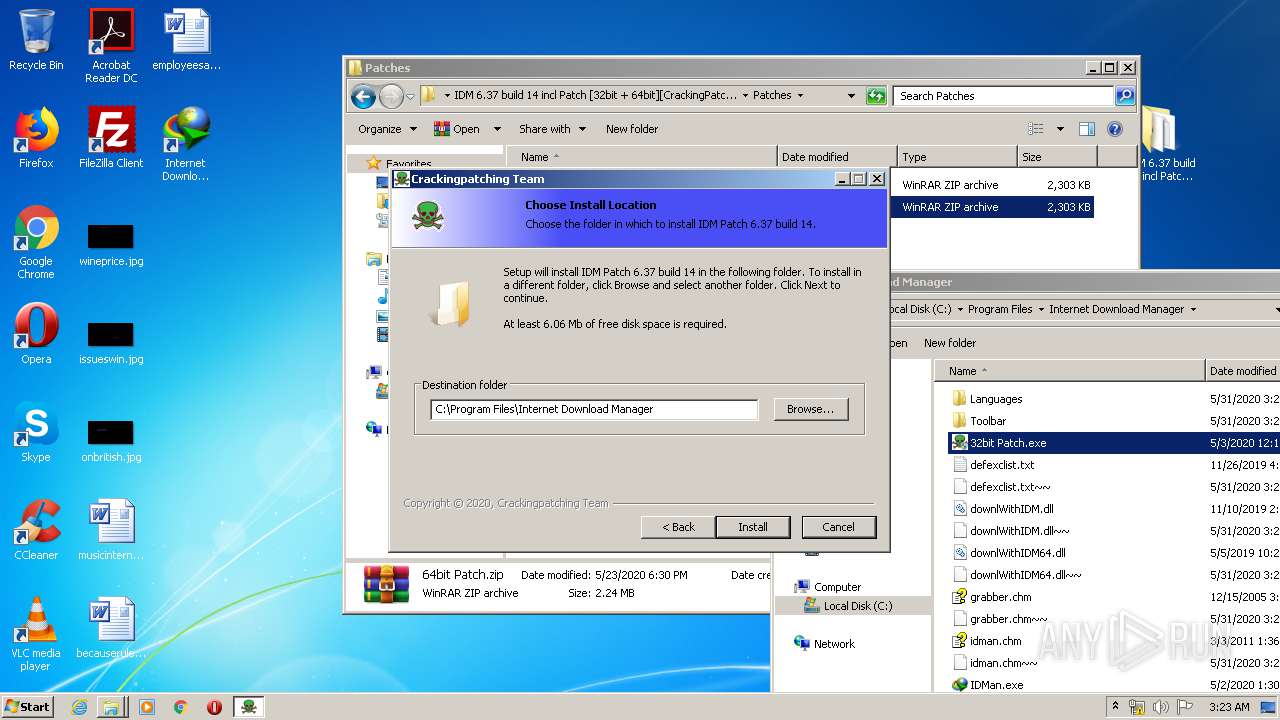
Creates files in the program directory
- 32bit Patch.exe (PID: 1092)
- IDM1.tmp (PID: 448)
- IDMan.exe (PID: 2476)
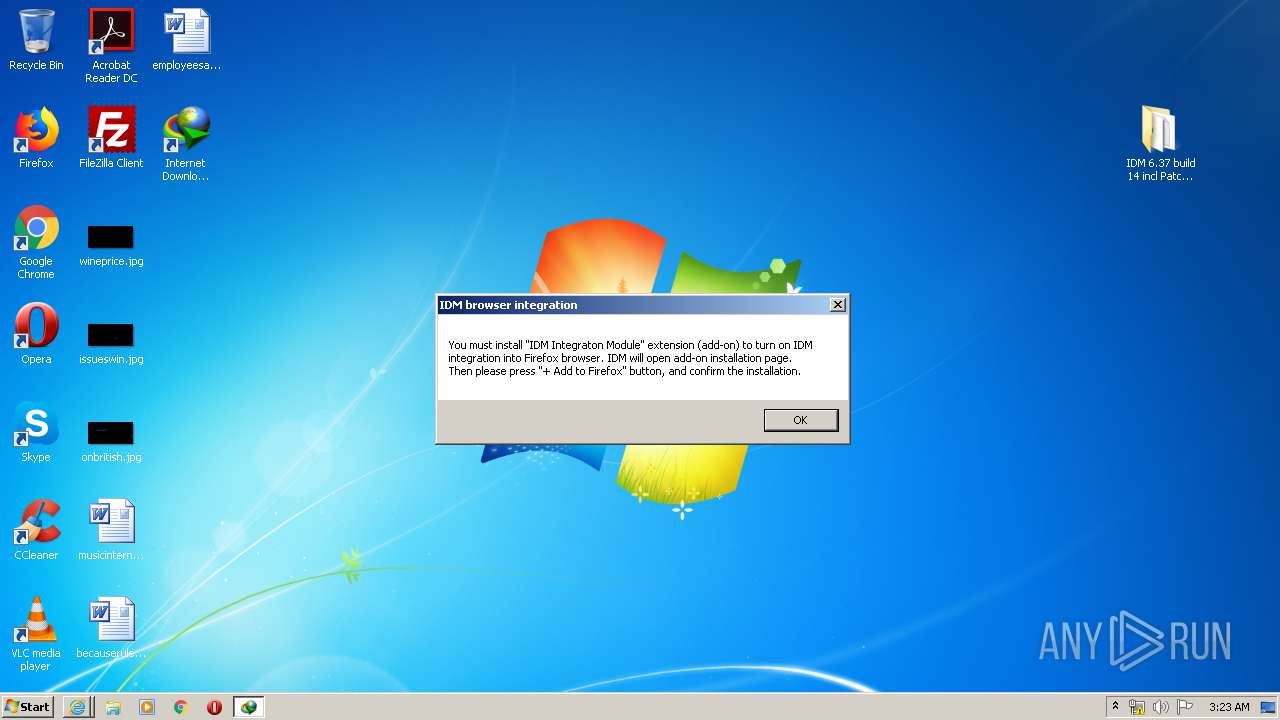
- firefox.exe (PID: 1492)
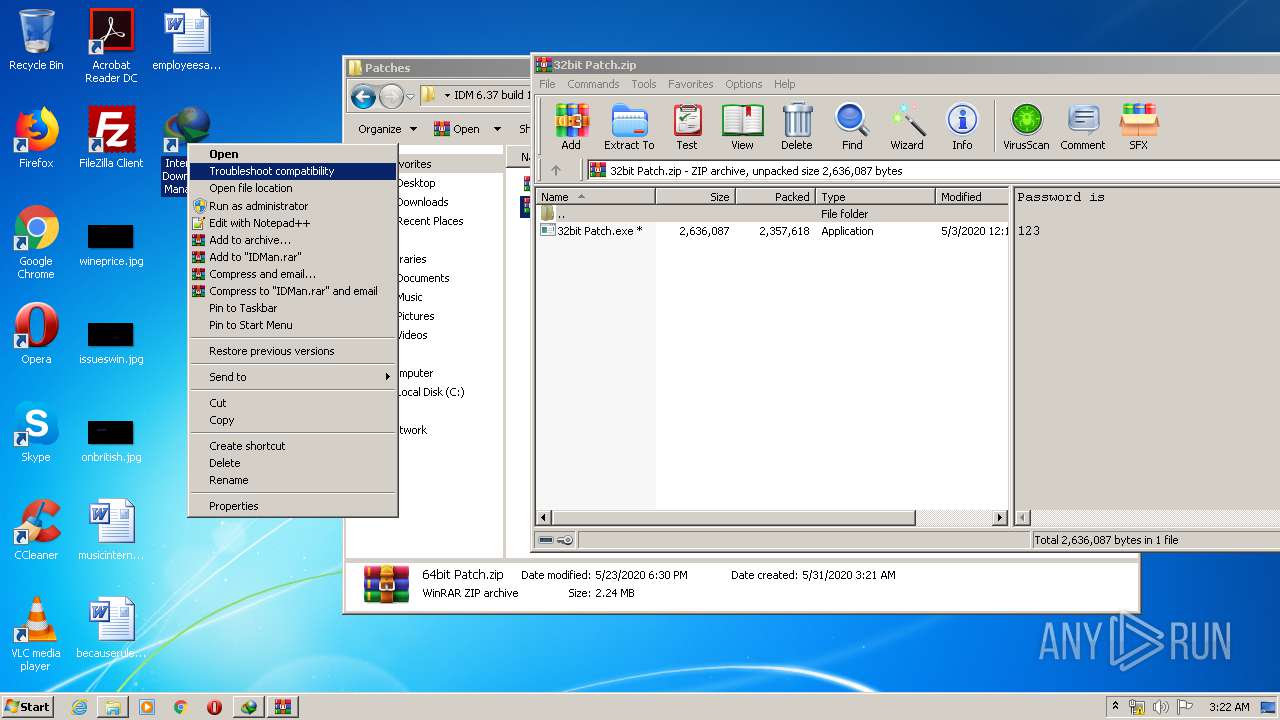
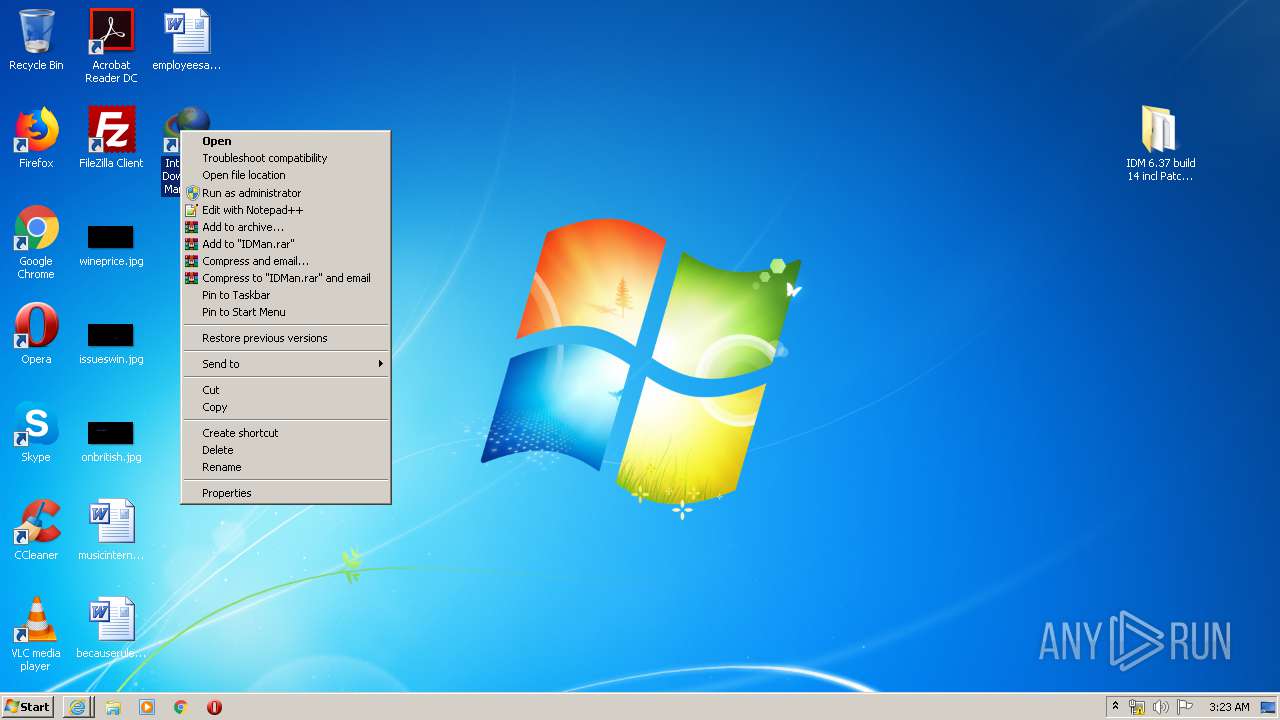
Starts Internet Explorer
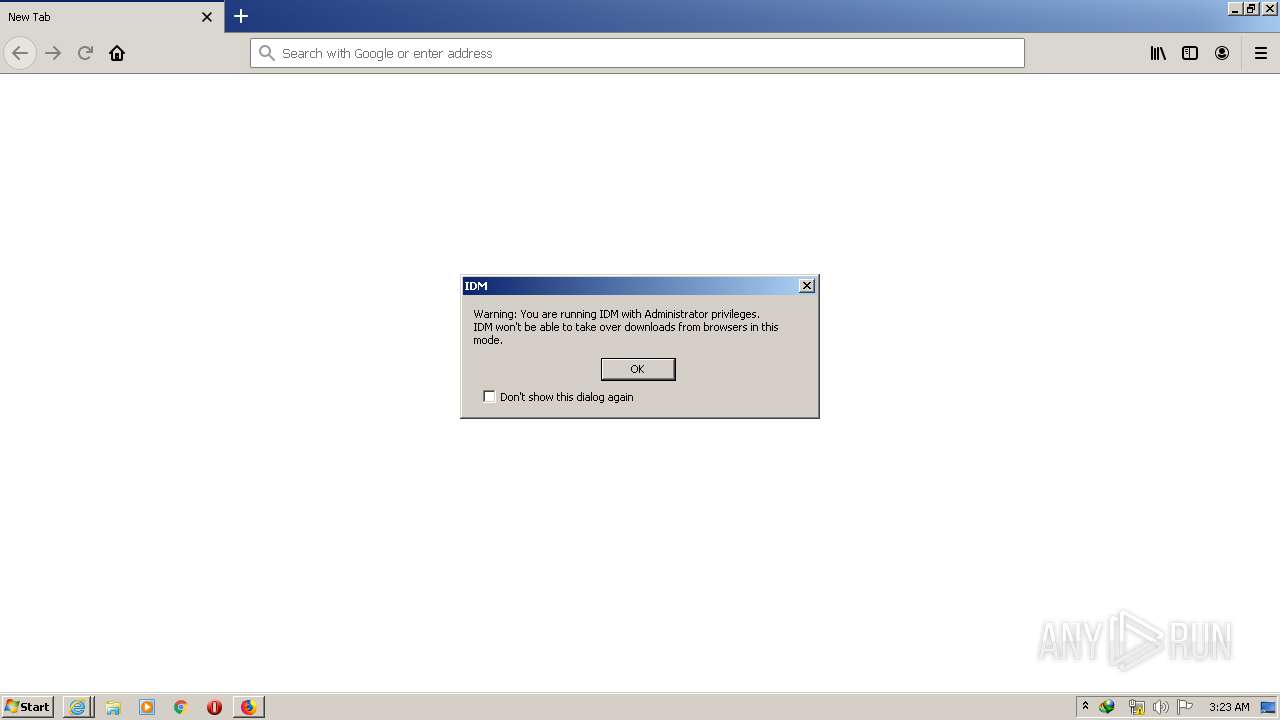
- 32bit Patch.exe (PID: 1092)
Uses RUNDLL32.EXE to load library
- Uninstall.exe (PID: 2700)
Removes files from Windows directory
- rundll32.exe (PID: 2912)
Creates files in the Windows directory
- rundll32.exe (PID: 2912)
Creates files in the driver directory
- rundll32.exe (PID: 2912)
Creates or modifies windows services
- Uninstall.exe (PID: 2700)
Adds / modifies Windows certificates
- IDMan.exe (PID: 1456)
INFO
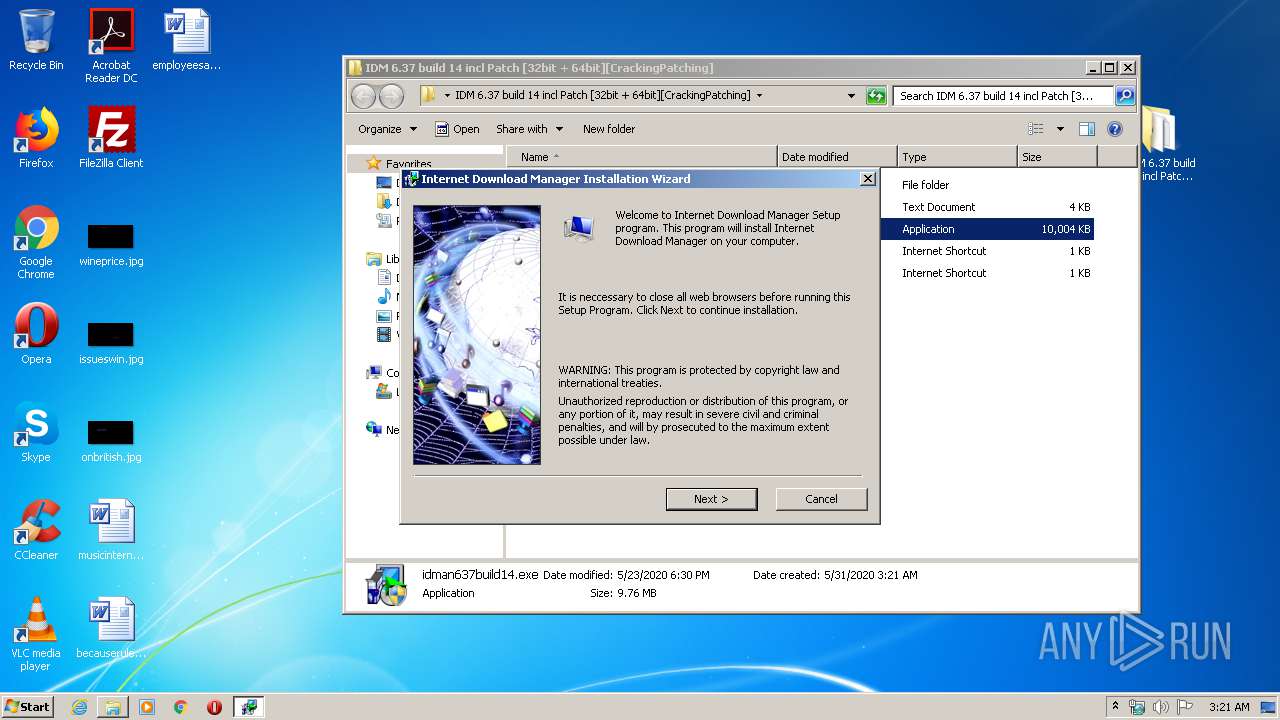
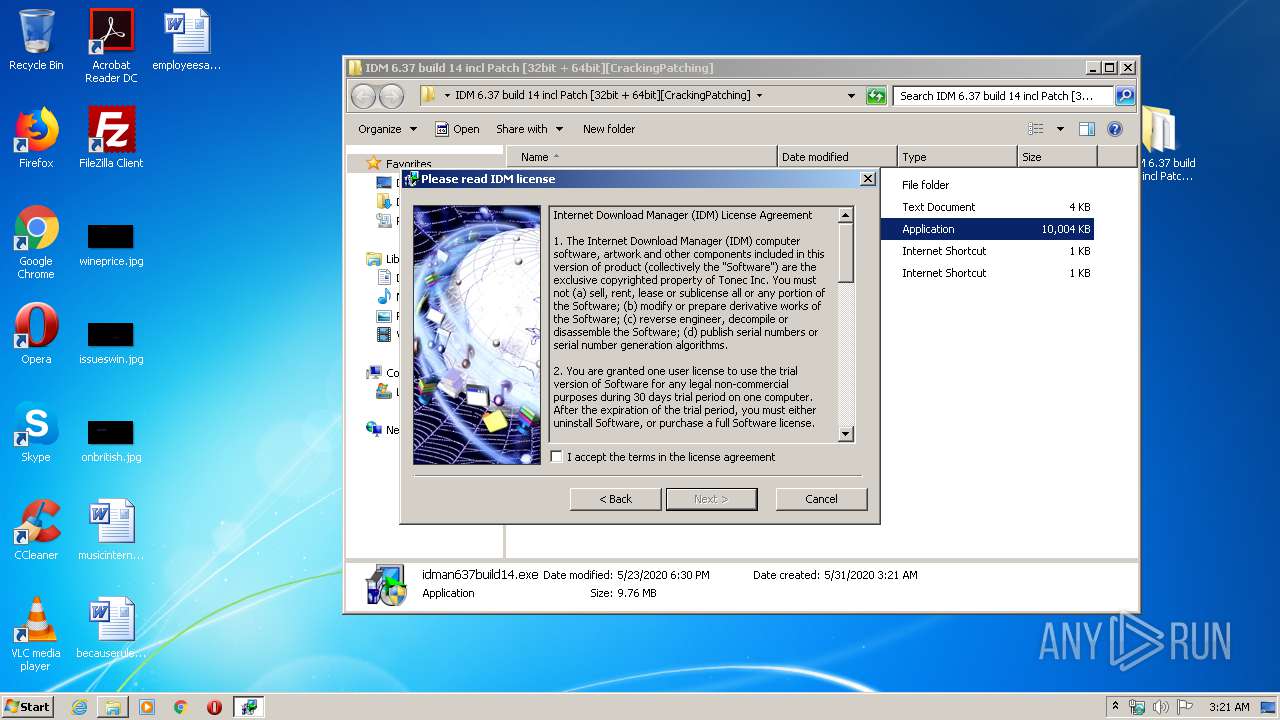
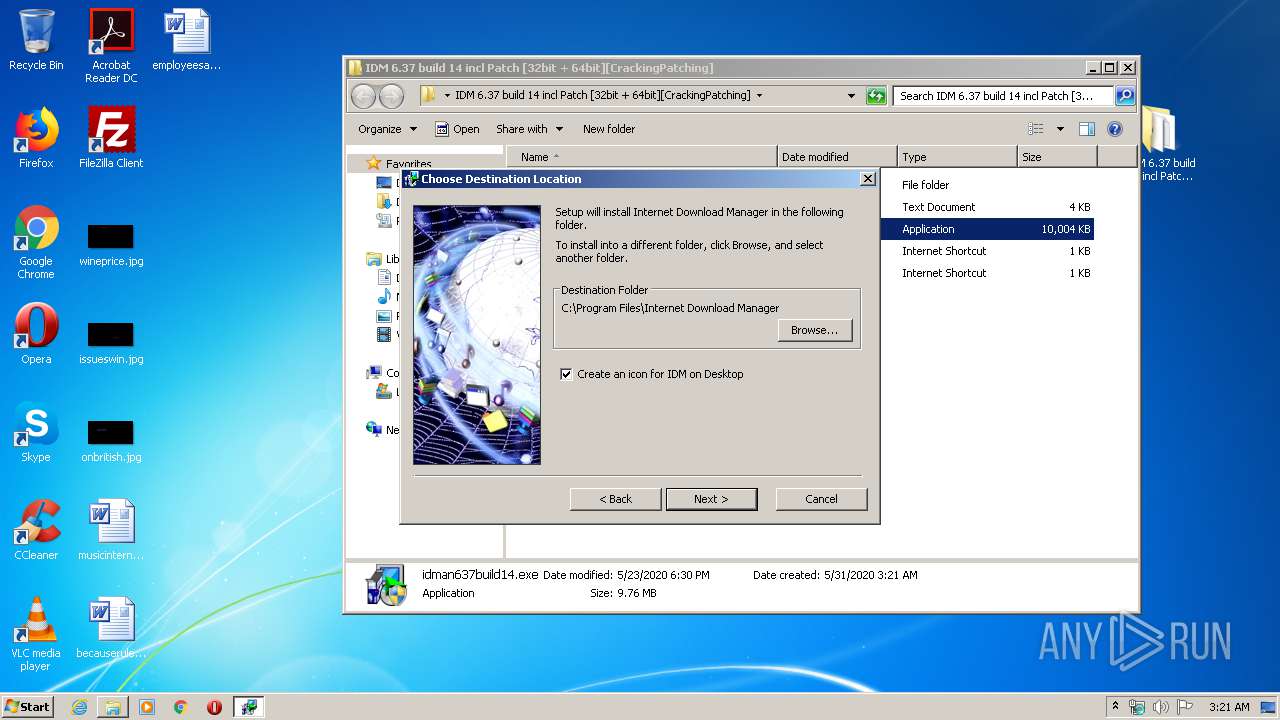
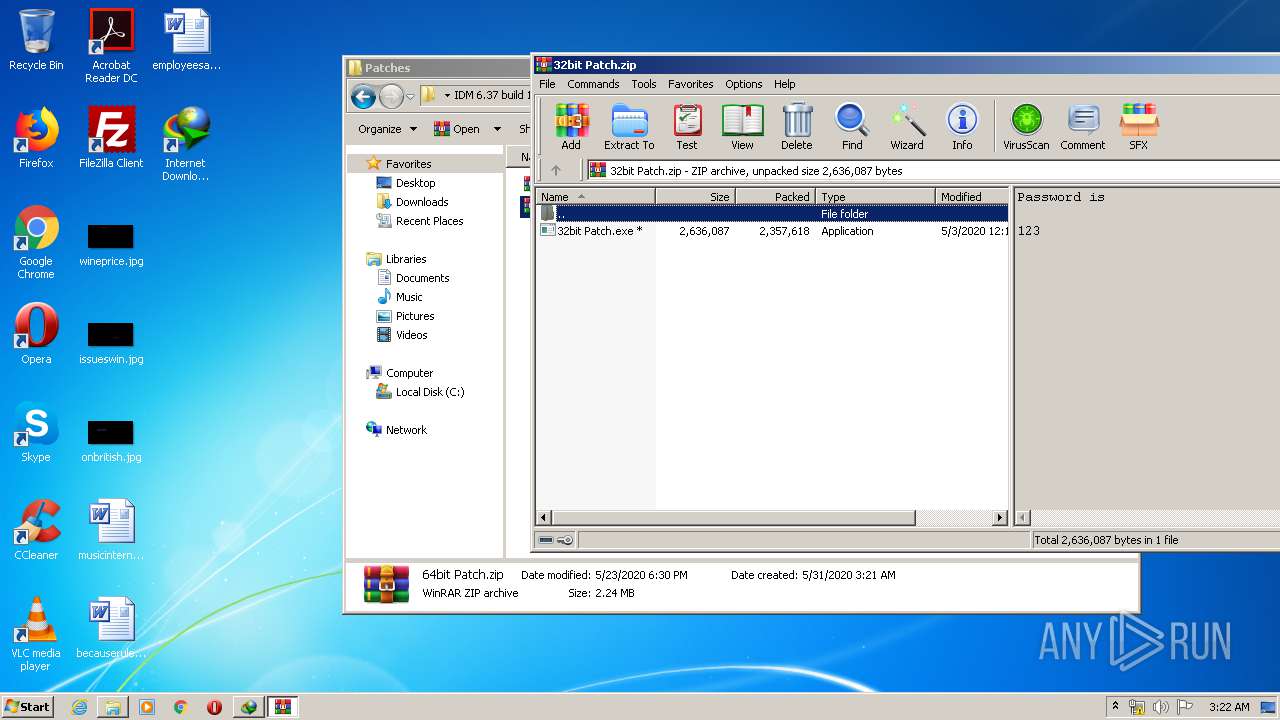
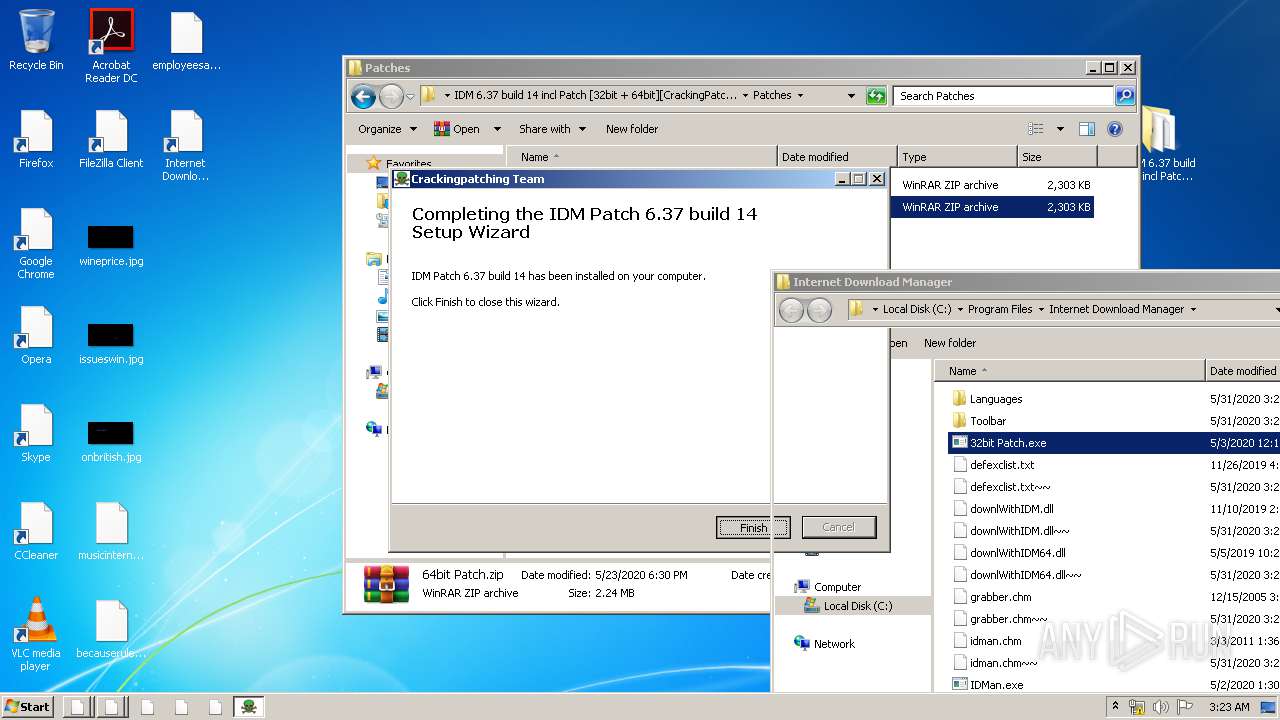
Manual execution by user
- idman637build14.exe (PID: 3028)
- 32bit Patch.exe (PID: 3968)
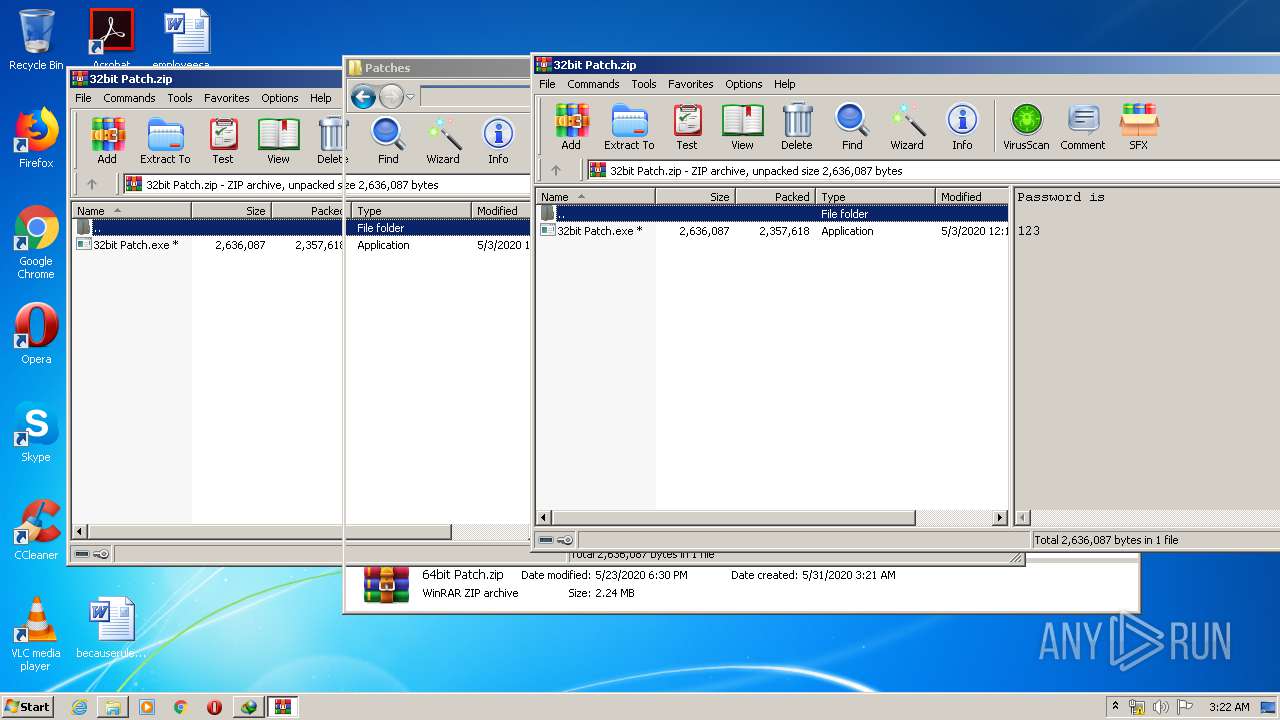
- WinRAR.exe (PID: 2680)
- 32bit Patch.exe (PID: 1092)
- WinRAR.exe (PID: 1872)
- IDMan.exe (PID: 2476)
- firefox.exe (PID: 2640)
Reads Internet Cache Settings
- iexplore.exe (PID: 3944)
- iexplore.exe (PID: 3800)
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 2240)
- firefox.exe (PID: 1492)
- pingsender.exe (PID: 3760)
Changes internet zones settings
- iexplore.exe (PID: 3944)
- iexplore.exe (PID: 2240)
Changes settings of System certificates
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 3800)
Reads settings of System Certificates
- IDMan.exe (PID: 1456)
- iexplore.exe (PID: 3800)
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 3944)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 3800)
Creates files in the user directory
- iexplore.exe (PID: 3800)
- iexplore.exe (PID: 3748)
- firefox.exe (PID: 1492)
Reads internet explorer settings
- iexplore.exe (PID: 3800)
- iexplore.exe (PID: 3748)
Dropped object may contain Bitcoin addresses
- IDMan.exe (PID: 2476)
- firefox.exe (PID: 1492)
Application launched itself
- firefox.exe (PID: 1492)
Reads CPU info
- firefox.exe (PID: 1492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
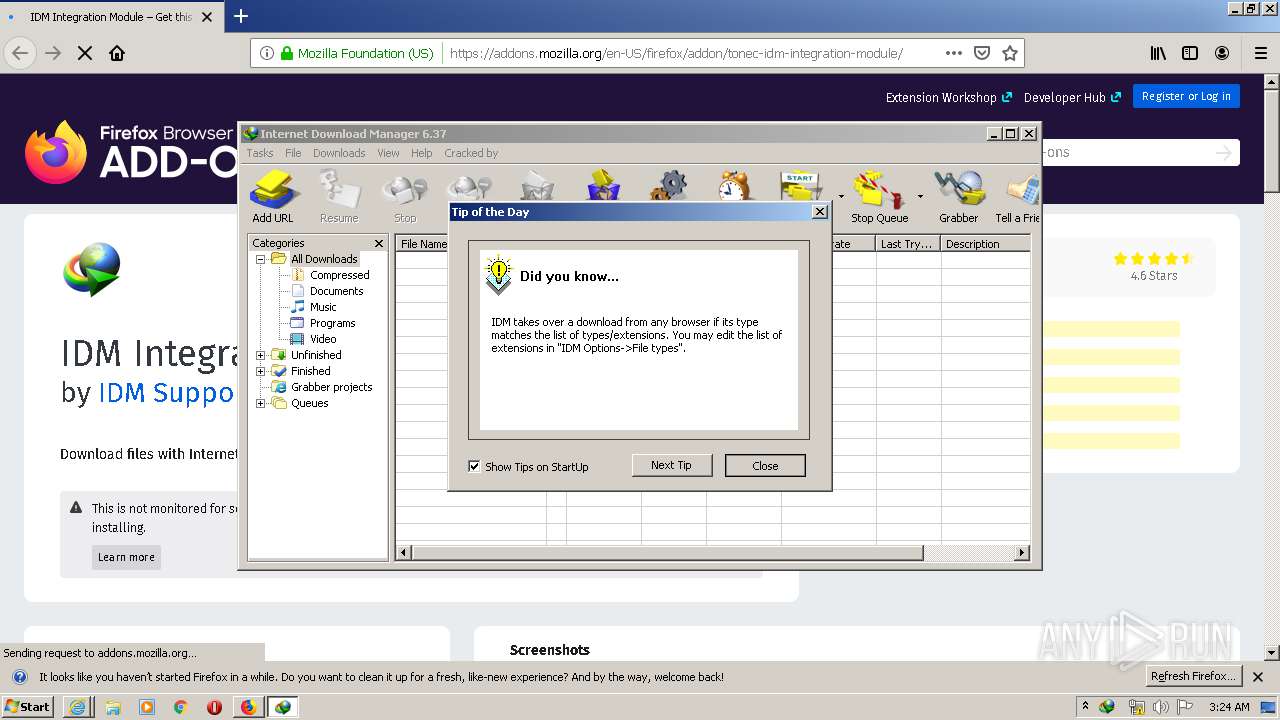
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:05:23 18:30:11 |
| ZipCRC: | 0x2a3d36ca |
| ZipCompressedSize: | 1357 |
| ZipUncompressedSize: | 3526 |
| ZipFileName: | IDM 6.37 build 14 incl Patch [32bit + 64bit][CrackingPatching]/How to Install.txt |
Total processes
91
Monitored processes
30
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
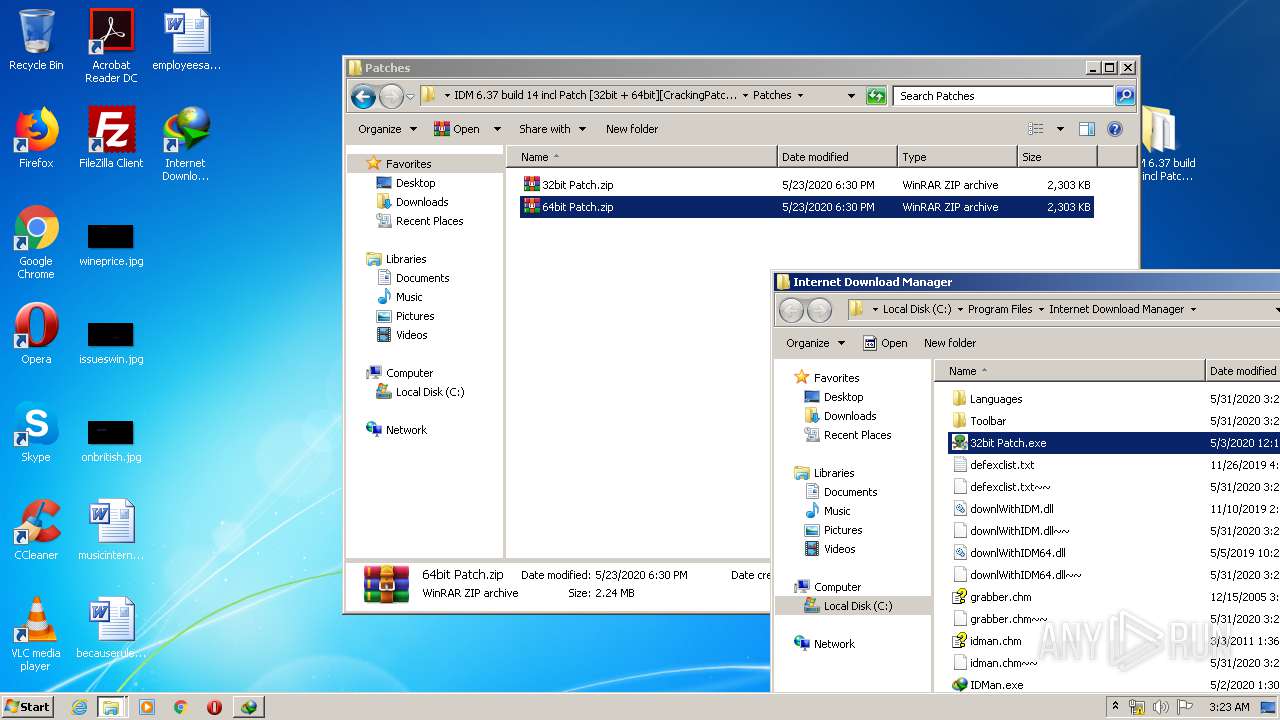
| 324 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\IDM 6.37 build 14 incl Patch [32bit + 64bit][CrackingPatching].zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 448 | "C:\Users\admin\AppData\Local\Temp\IDM_Setup_Temp\IDM1.tmp" -d "C:\Users\admin\AppData\Local\Temp\IDM_Setup_Temp\" | C:\Users\admin\AppData\Local\Temp\IDM_Setup_Temp\IDM1.tmp | — | idman637build14.exe | |||||||||||
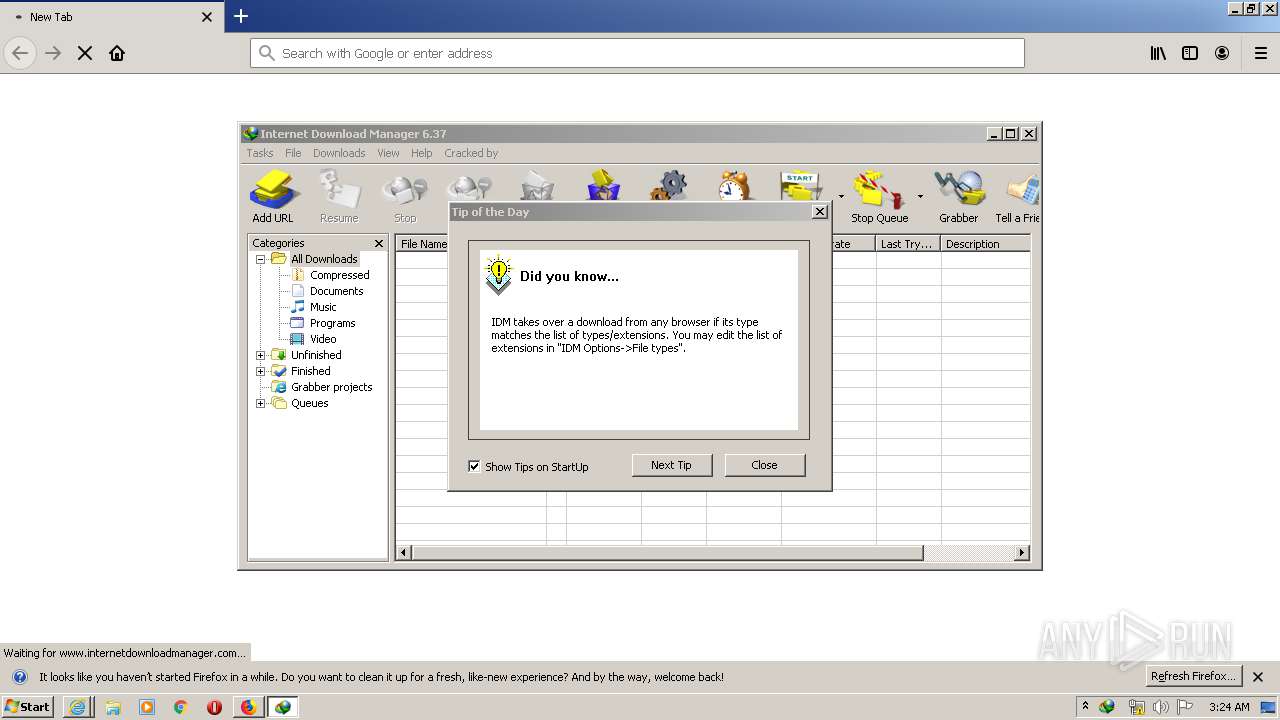
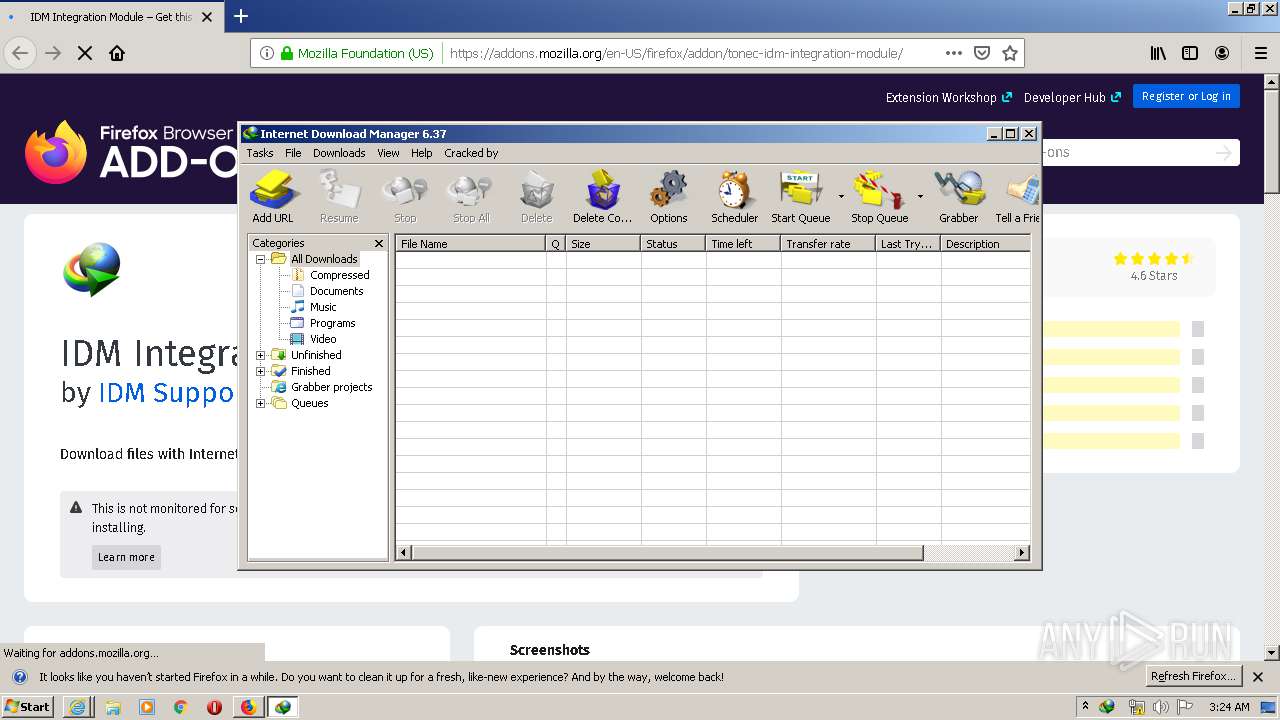
User: admin Company: Tonec Inc. Integrity Level: HIGH Description: Internet Download Manager installer Exit code: 0 Version: 6, 37, 11, 1 Modules
| |||||||||||||||
| 540 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1492.20.1869922418\1382694194" -childID 3 -isForBrowser -prefsHandle 3740 -prefMapHandle 3752 -prefsLen 7299 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1492 "\\.\pipe\gecko-crash-server-pipe.1492" 3764 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
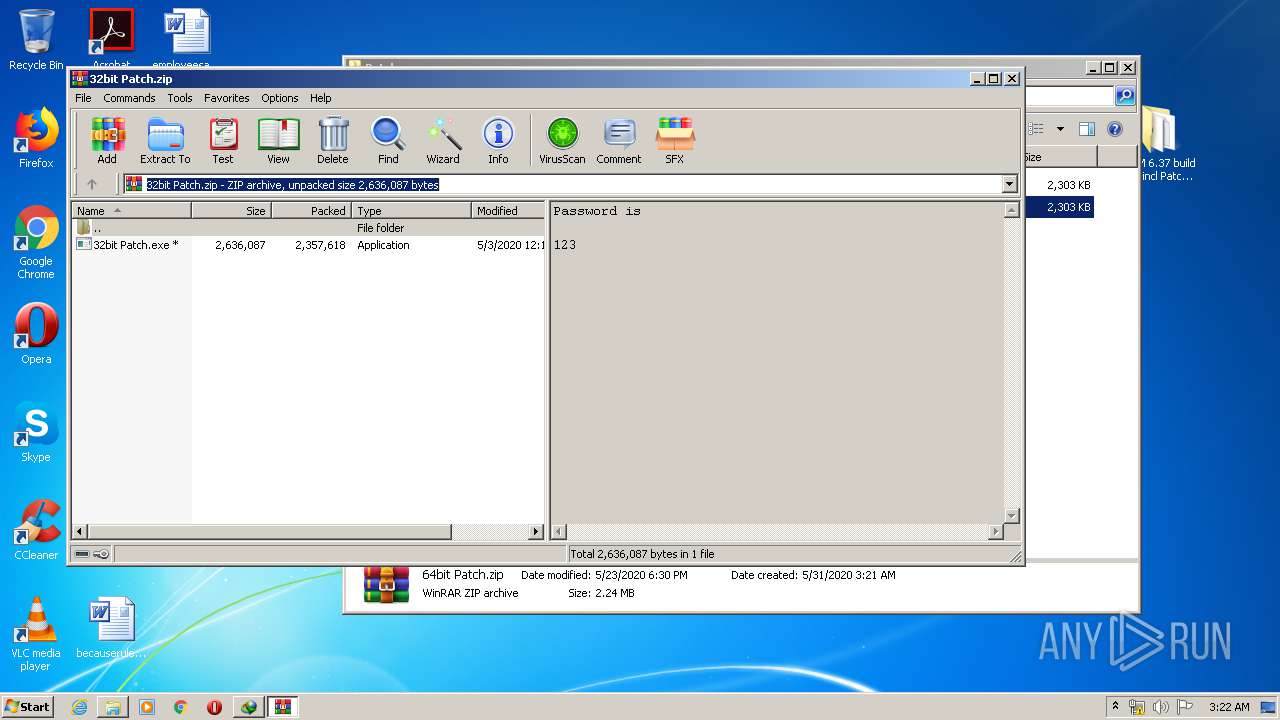
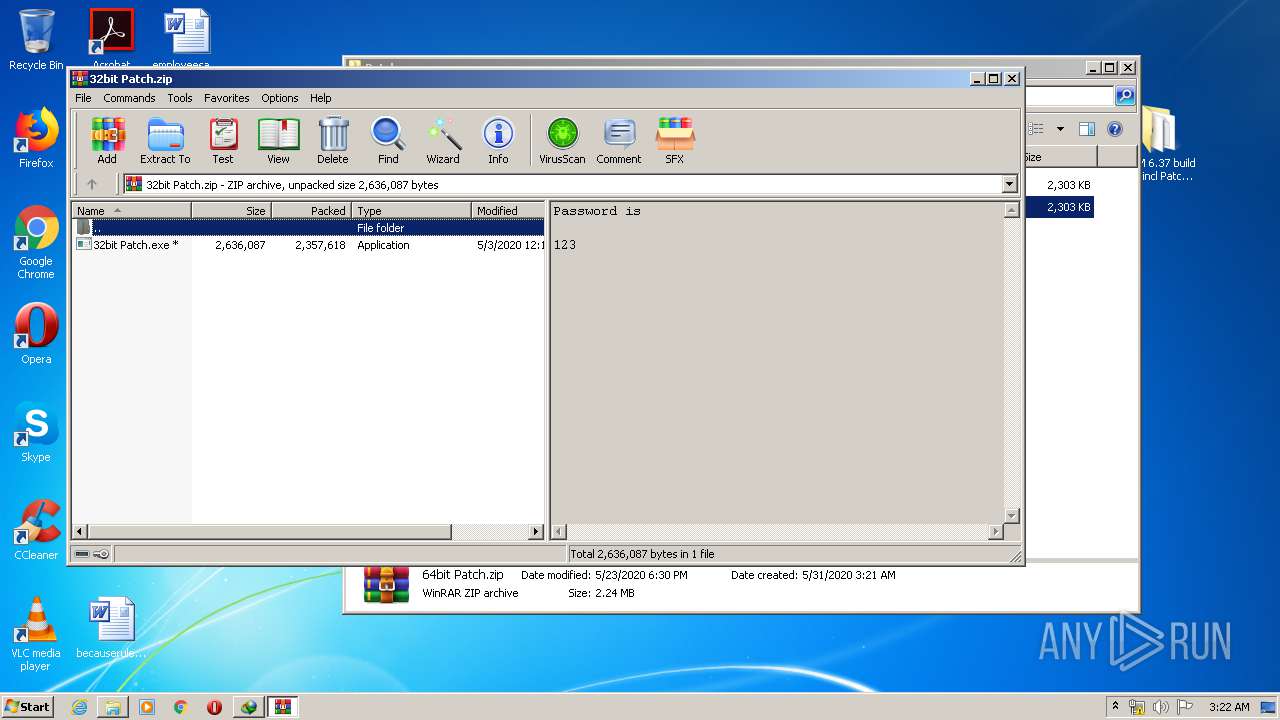
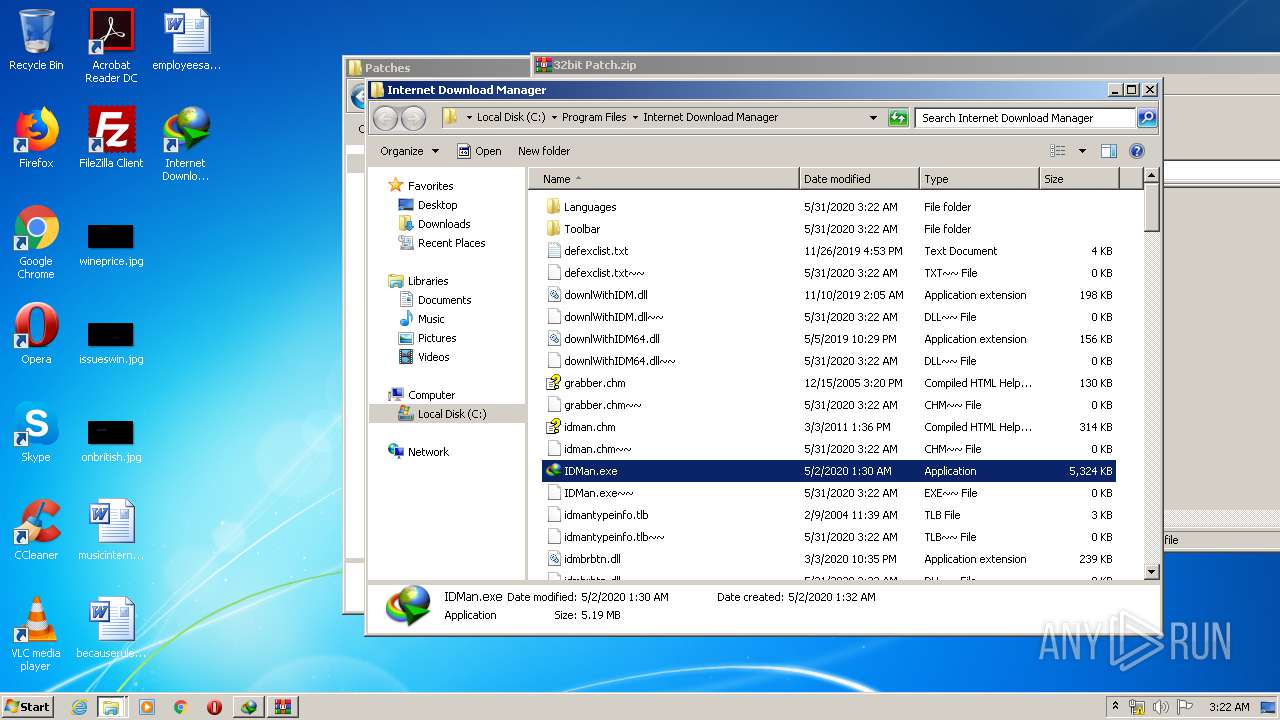
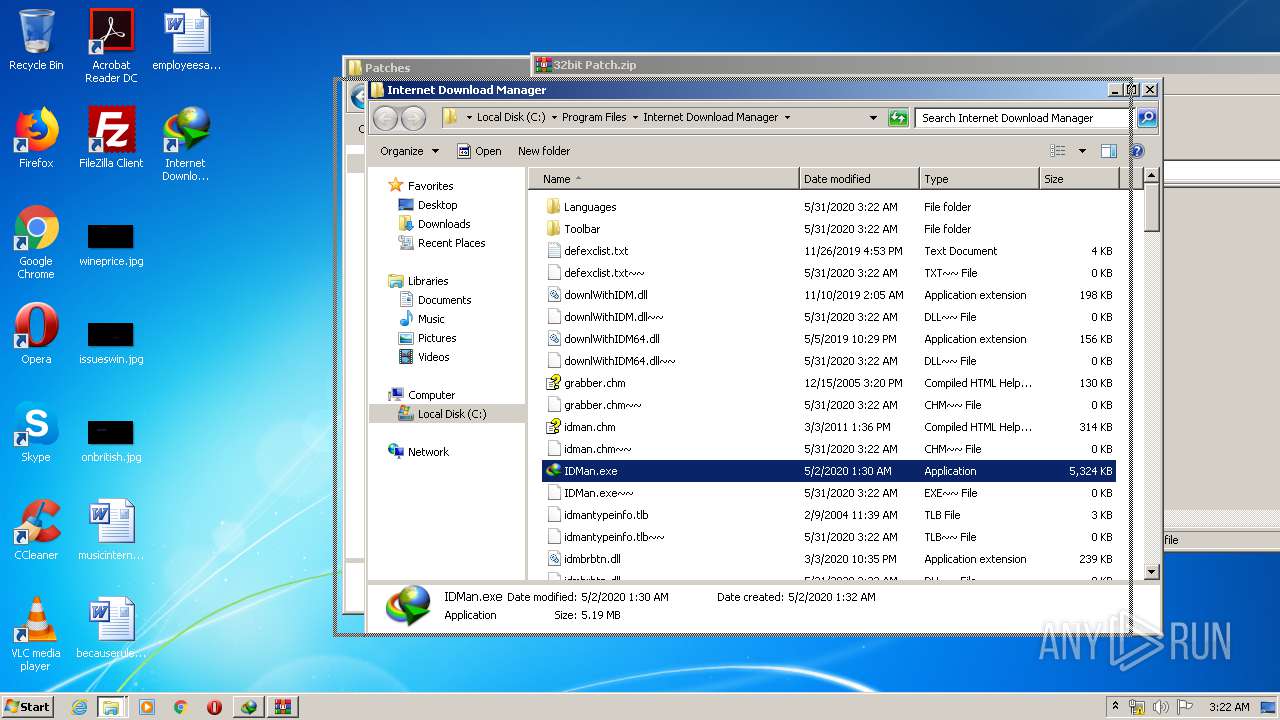
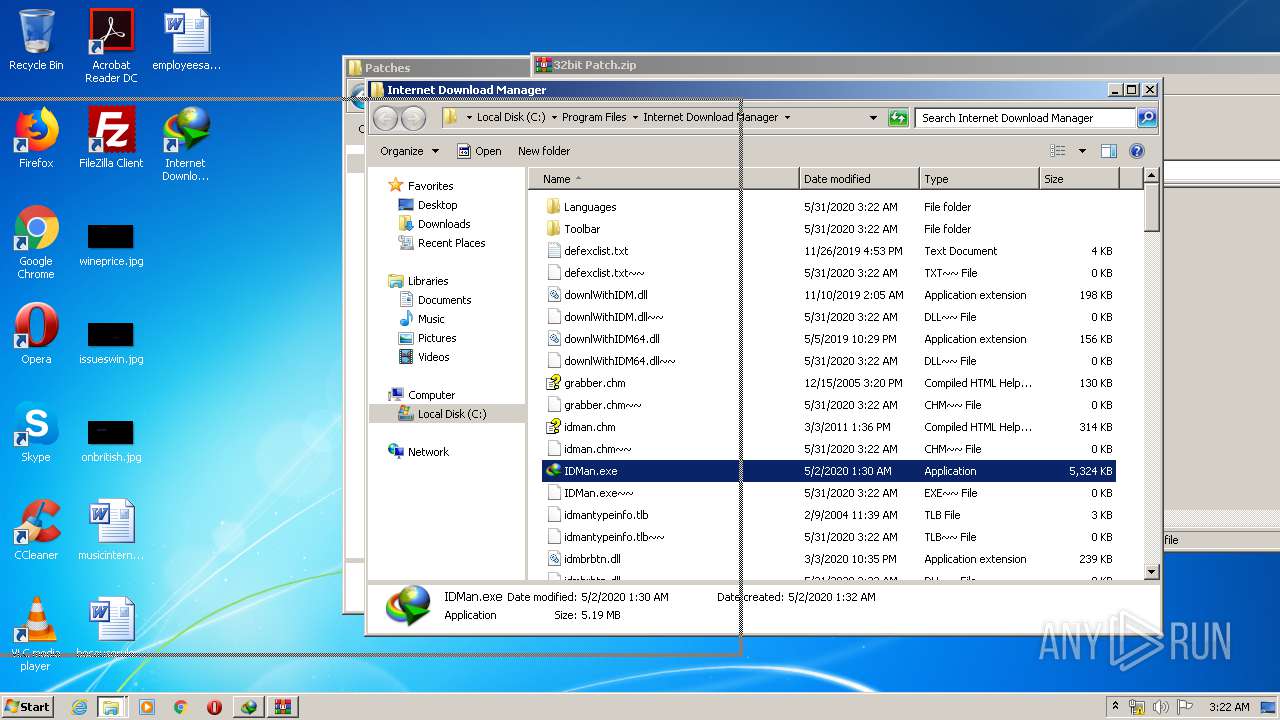
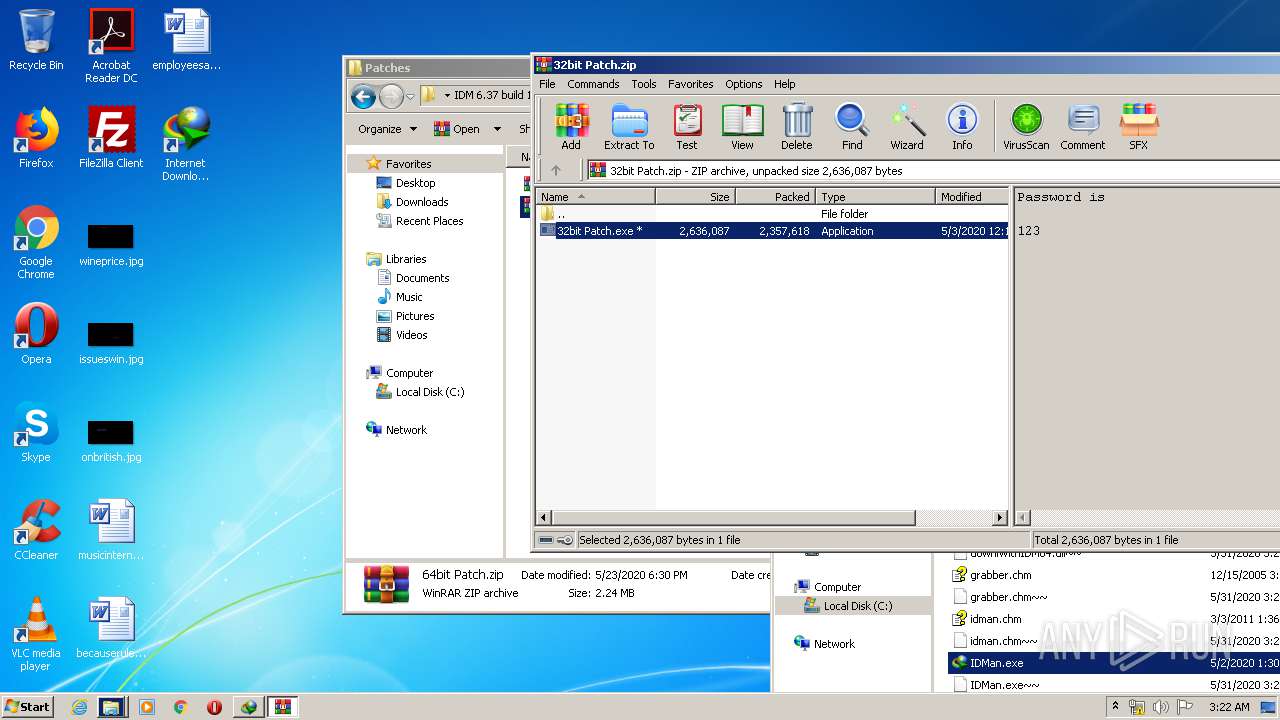
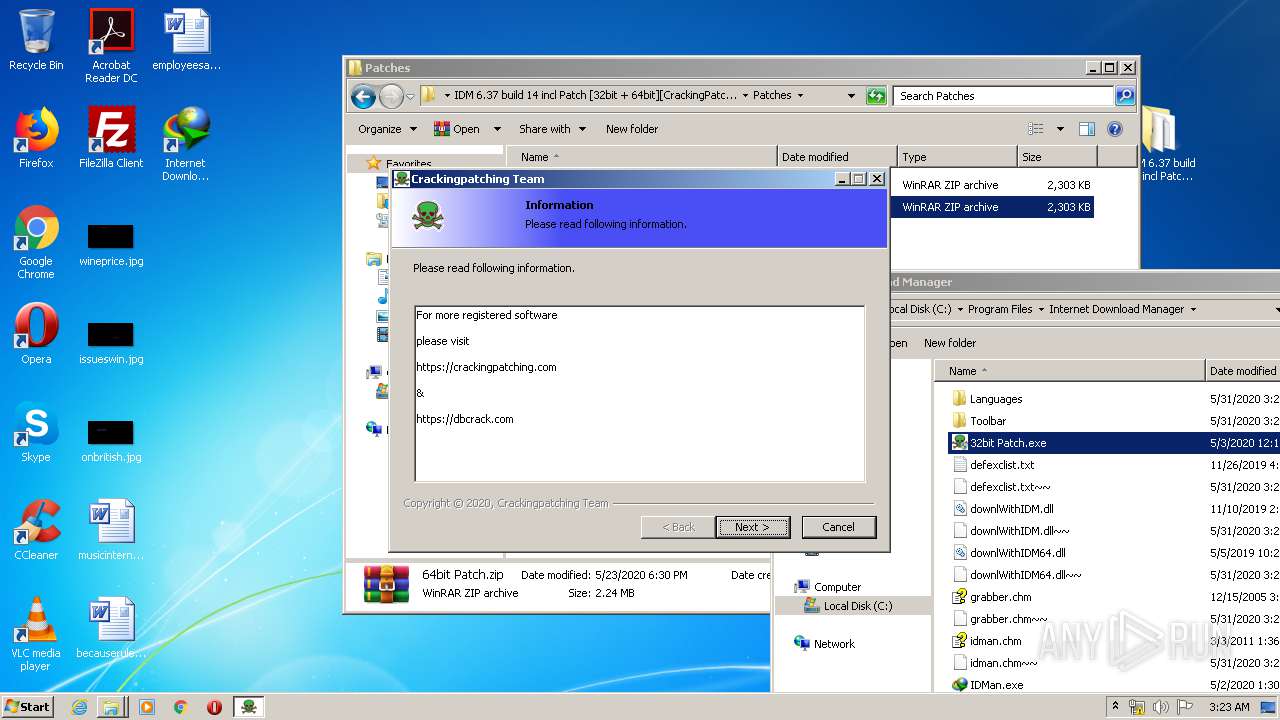
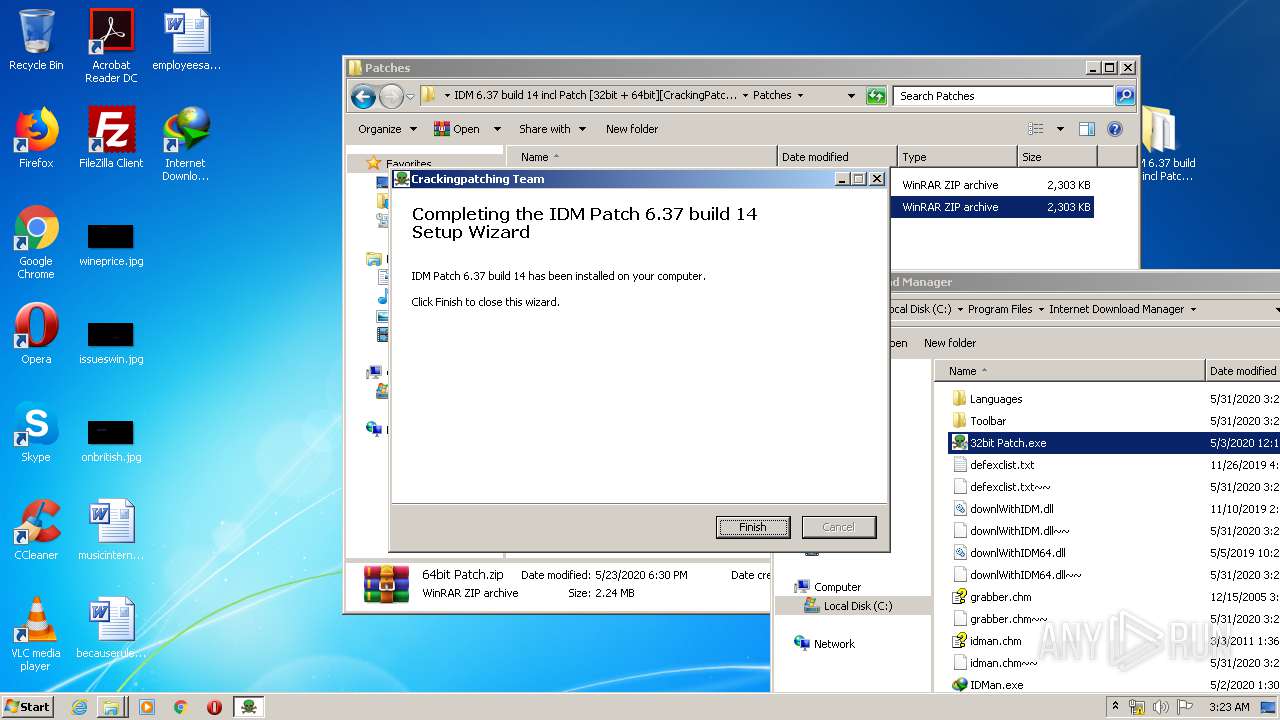
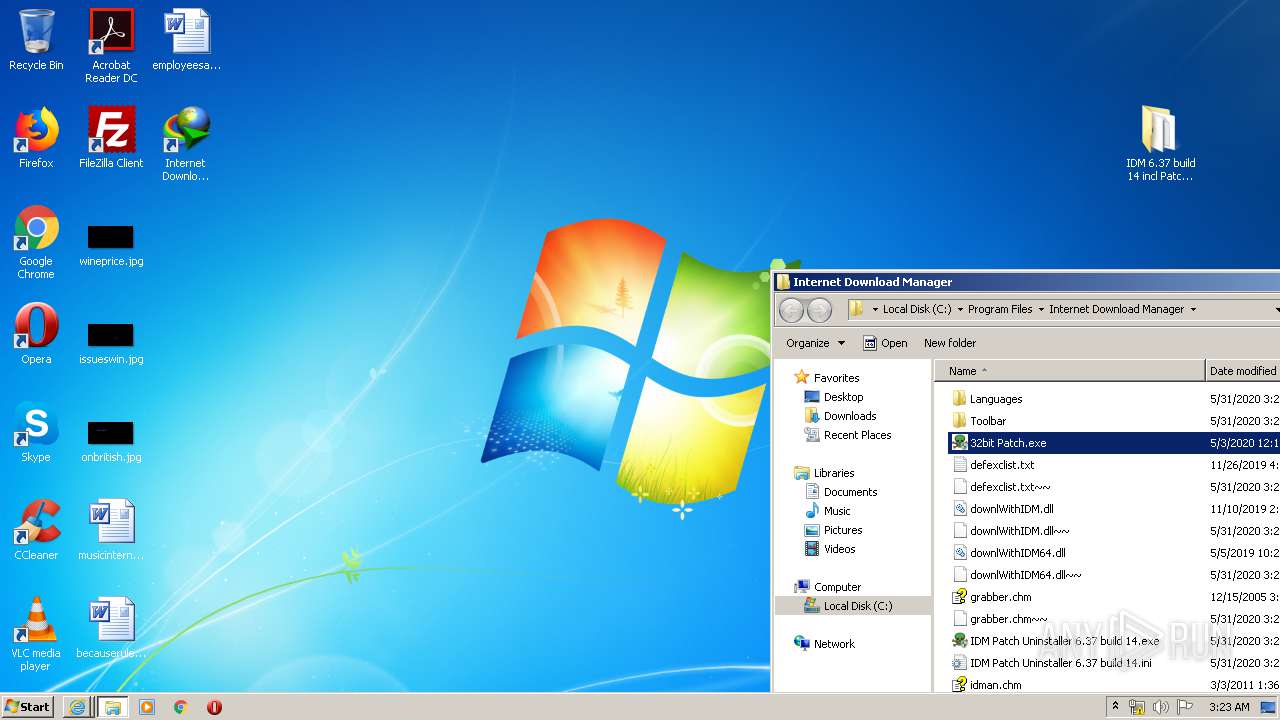
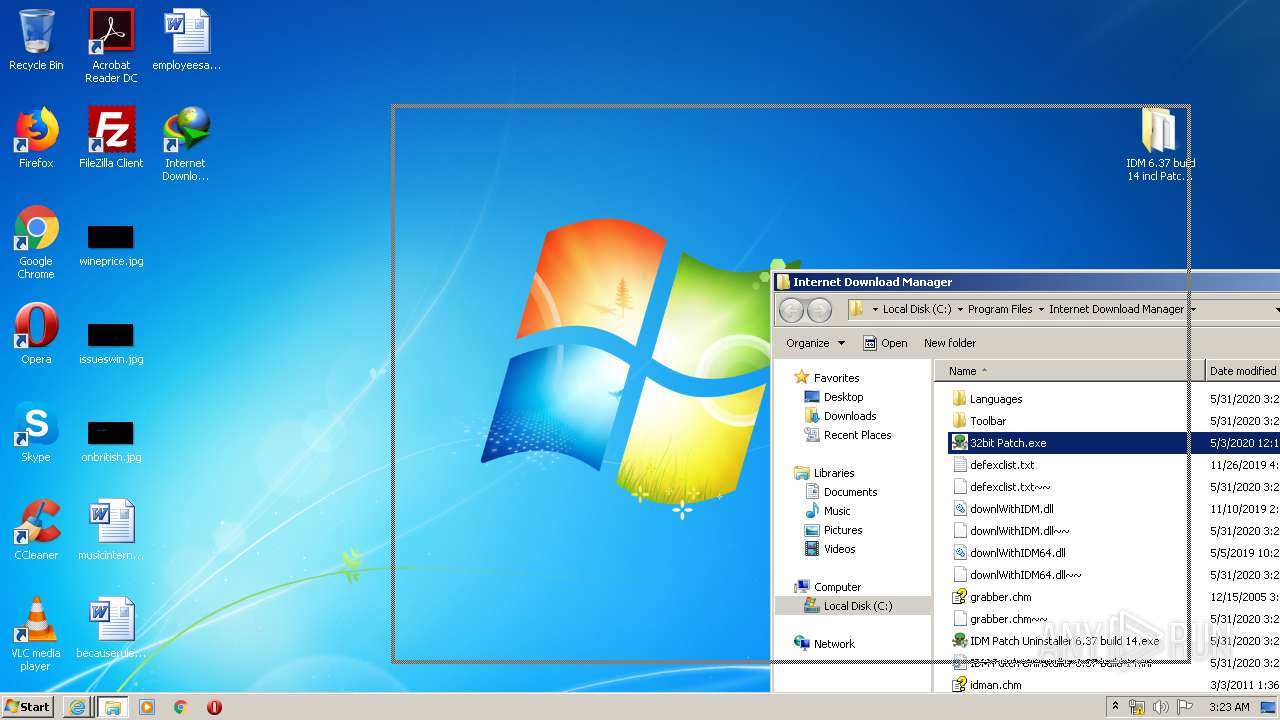
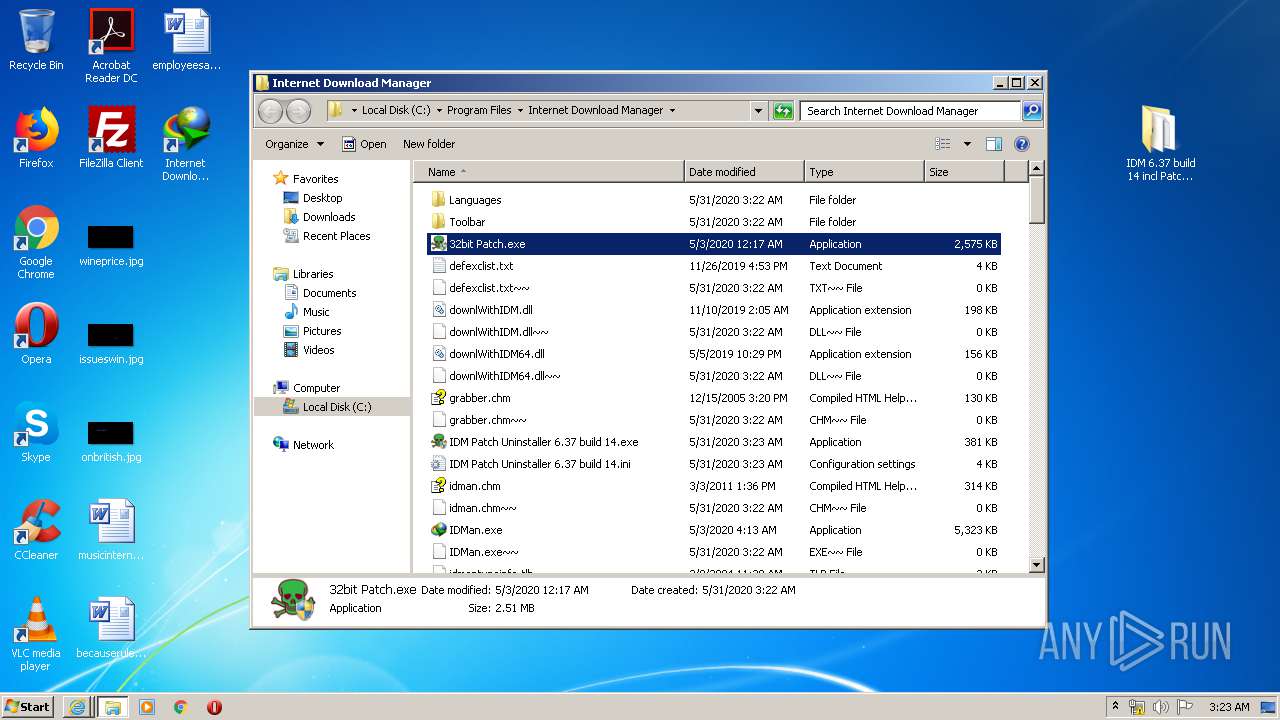
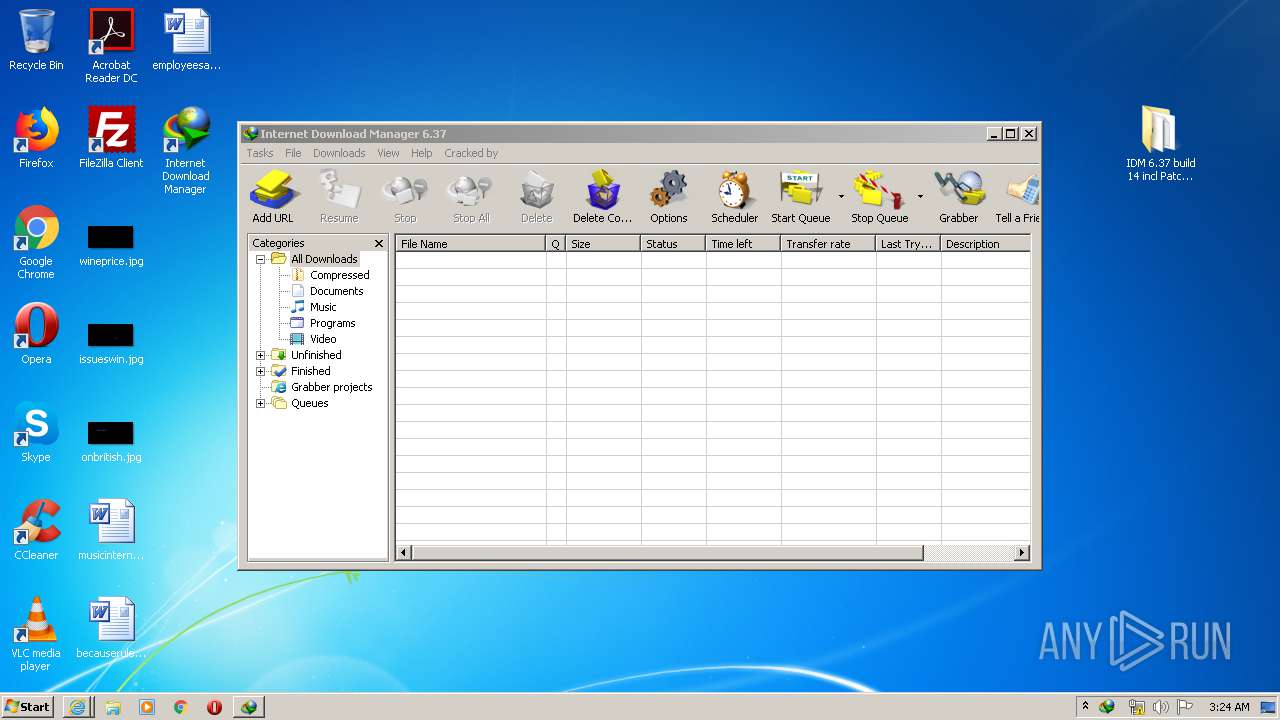
| 1092 | "C:\Program Files\Internet Download Manager\32bit Patch.exe" | C:\Program Files\Internet Download Manager\32bit Patch.exe | explorer.exe | ||||||||||||
User: admin Company: Crackingpatching.com Team Integrity Level: HIGH Description: IDM Patch 6.37 build 14 6.37 build 14 Installation Exit code: 0 Version: 6.37 build 14 Modules
| |||||||||||||||
| 1392 | "C:\Windows\System32\net.exe" start IDMWFP | C:\Windows\System32\net.exe | — | Uninstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Internet Download Manager\IDMan.exe" /rtr | C:\Program Files\Internet Download Manager\IDMan.exe | — | IDM1.tmp | |||||||||||
User: admin Company: Tonec Inc. Integrity Level: HIGH Description: Internet Download Manager (IDM) Exit code: 259 Version: 6, 37, 14, 2 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Mozilla Firefox\firefox.exe" http://www.internetdownloadmanager.com/support/installffextfrommozillasite.html | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
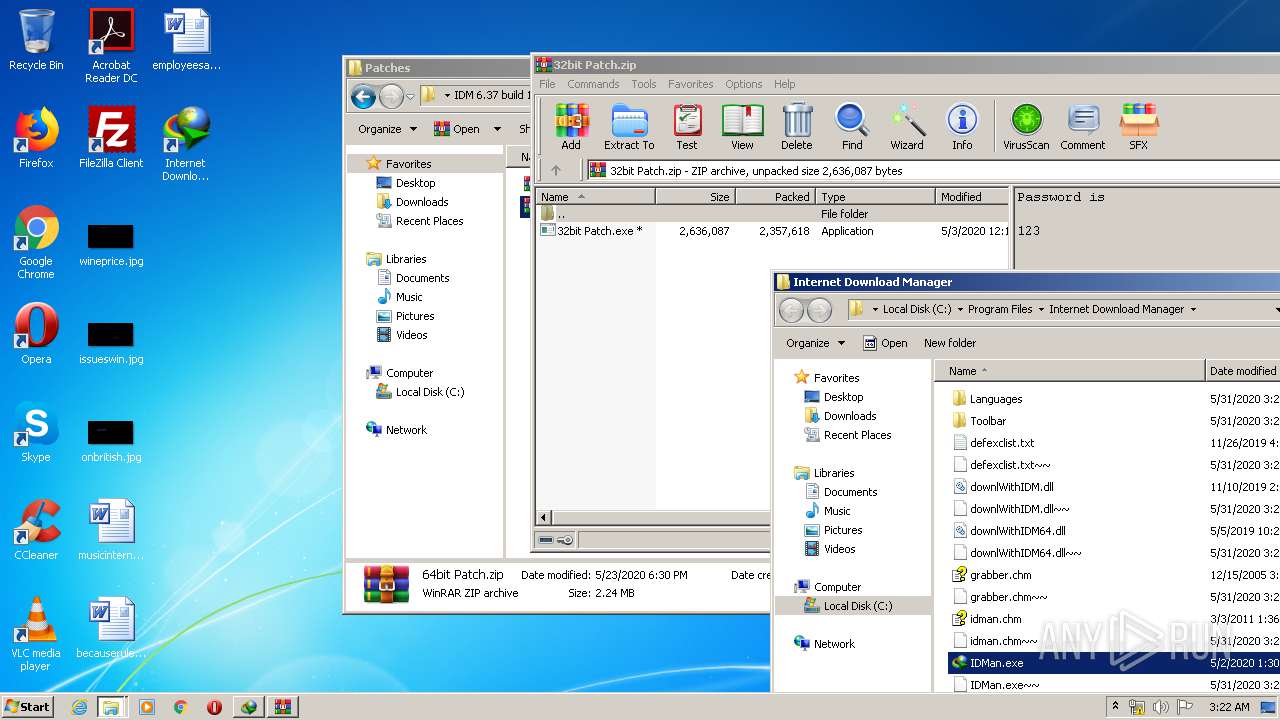
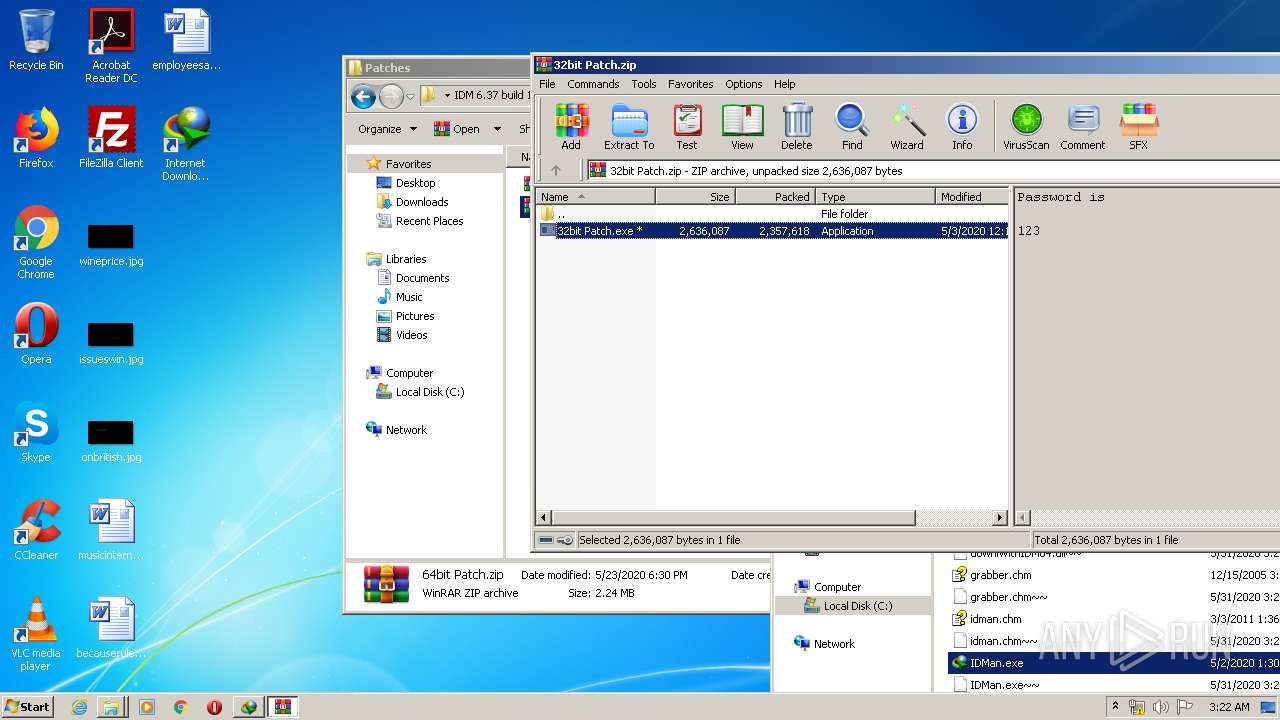
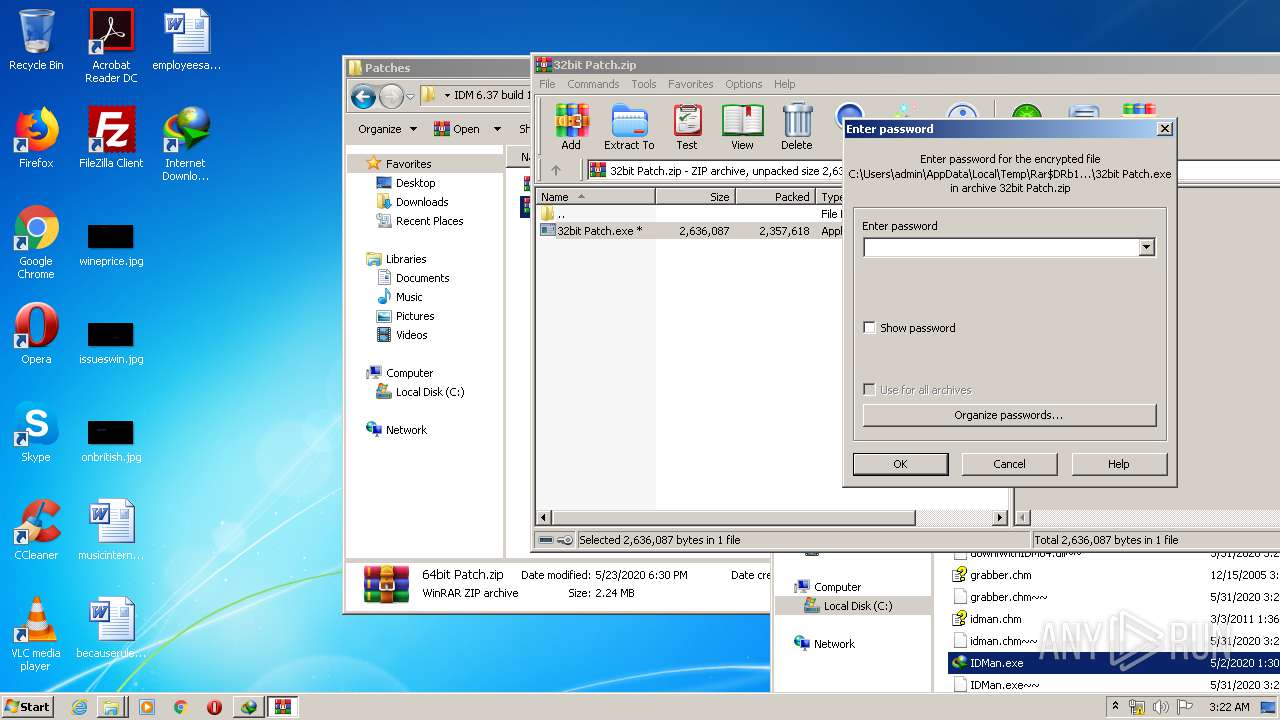
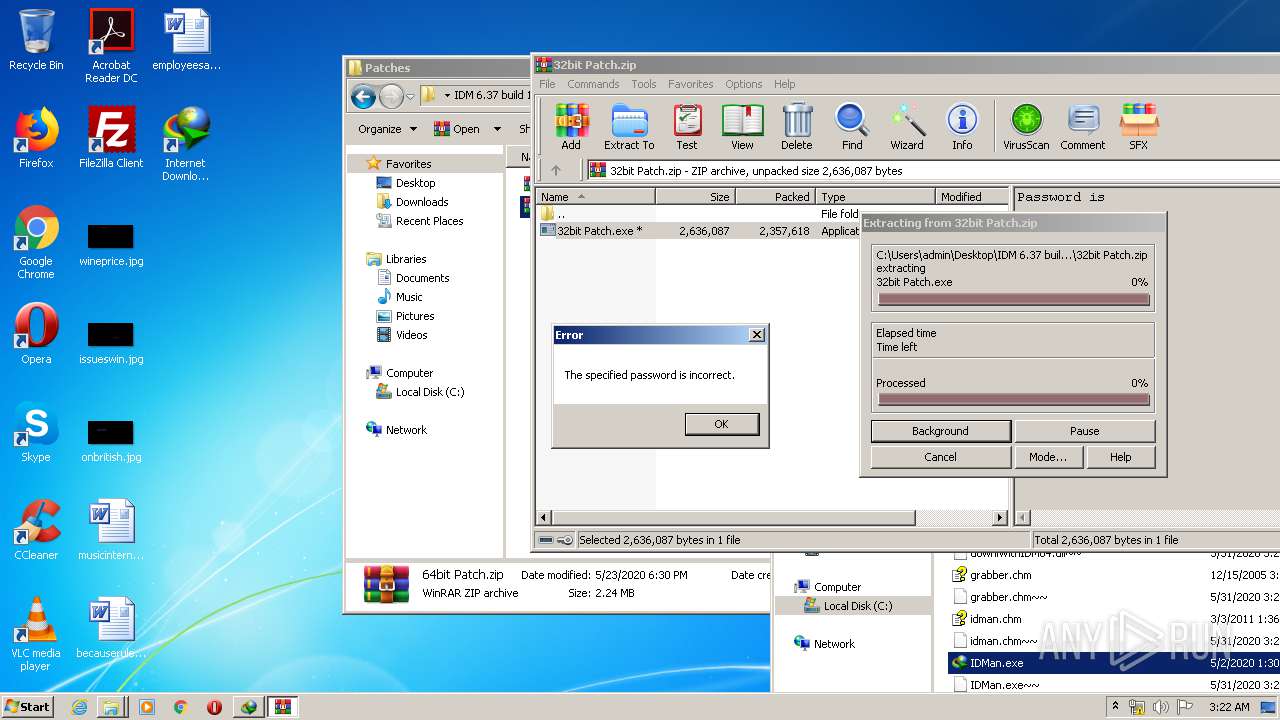
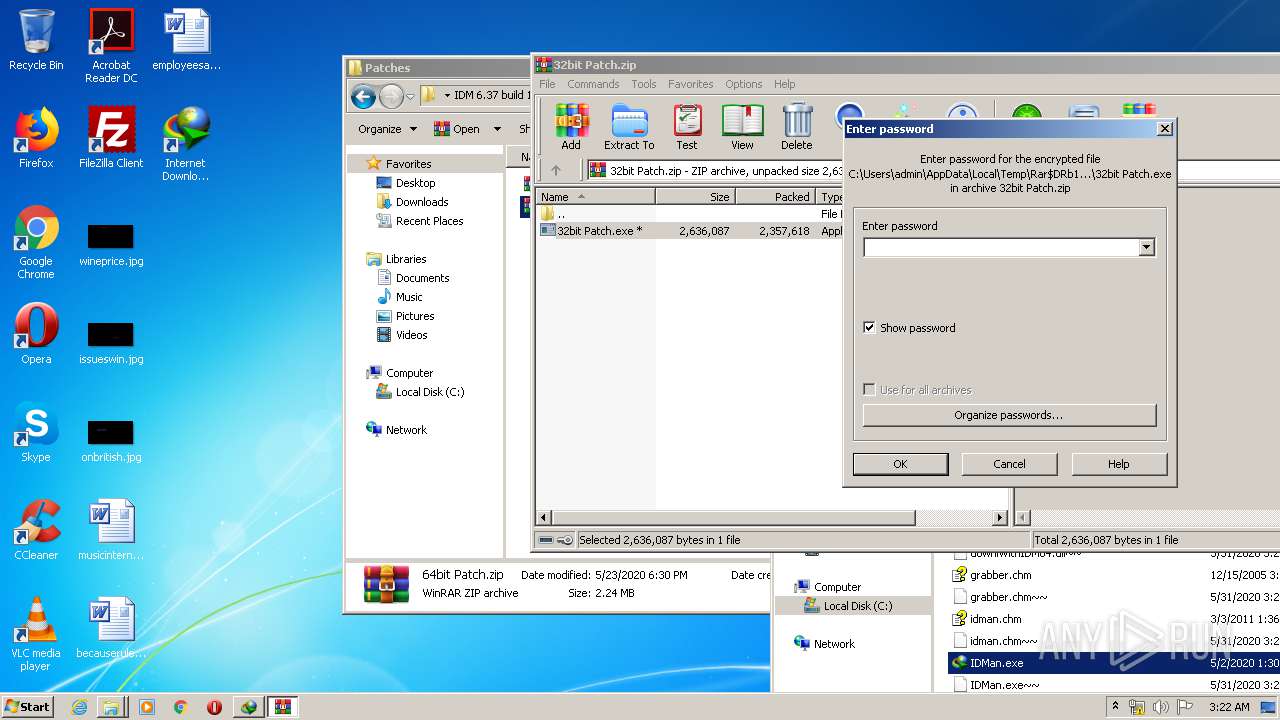
| 1872 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\IDM 6.37 build 14 incl Patch [32bit + 64bit][CrackingPatching]\Patches\32bit Patch.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Internet Explorer\iexplore.exe" https://crackingpatching.com/2019/08/idm-crack.html | C:\Program Files\Internet Explorer\iexplore.exe | 32bit Patch.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2424 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="1492.3.551001859\1672998570" -childID 1 -isForBrowser -prefsHandle 1336 -prefMapHandle 852 -prefsLen 1 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 1492 "\\.\pipe\gecko-crash-server-pipe.1492" 844 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
Total events
5 348
Read events
2 909
Write events
2 321
Delete events
118
Modification events
| (PID) Process: | (324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (324) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (324) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\IDM 6.37 build 14 incl Patch [32bit + 64bit][CrackingPatching].zip | |||
| (PID) Process: | (324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (324) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
16
Suspicious files
379
Text files
230
Unknown types
134
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa324.2553\IDM 6.37 build 14 incl Patch [32bit + 64bit][CrackingPatching]\idman637build14.exe | — | |
MD5:— | SHA256:— | |||
| 324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa324.2553\IDM 6.37 build 14 incl Patch [32bit + 64bit][CrackingPatching]\Like Us Facebook.URL | — | |
MD5:— | SHA256:— | |||
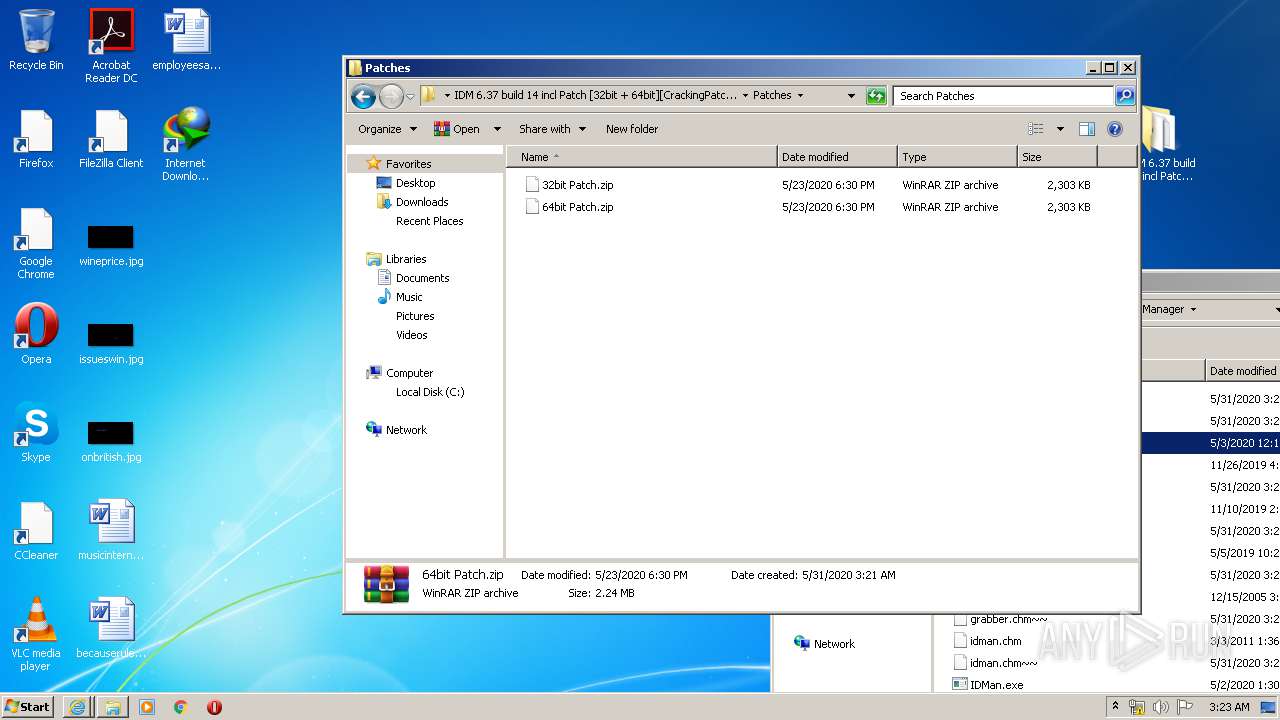
| 324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa324.2553\IDM 6.37 build 14 incl Patch [32bit + 64bit][CrackingPatching]\Patches\32bit Patch.zip | — | |
MD5:— | SHA256:— | |||
| 324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa324.2553\IDM 6.37 build 14 incl Patch [32bit + 64bit][CrackingPatching]\Patches\64bit Patch.zip | — | |
MD5:— | SHA256:— | |||
| 324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa324.2553\IDM 6.37 build 14 incl Patch [32bit + 64bit][CrackingPatching]\Support Us CrackingPatching.com.URL | — | |
MD5:— | SHA256:— | |||
| 448 | IDM1.tmp | C:\Users\admin\AppData\Local\Temp\~DF1C46E770A5FDC770.TMP | — | |
MD5:— | SHA256:— | |||
| 324 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa324.2553\IDM 6.37 build 14 incl Patch [32bit + 64bit][CrackingPatching]\How to Install.txt | text | |
MD5:— | SHA256:— | |||
| 448 | IDM1.tmp | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Internet Download Manager\Uninstall IDM.lnk | lnk | |
MD5:— | SHA256:— | |||
| 448 | IDM1.tmp | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Internet Download Manager\Grabber Help.lnk | lnk | |
MD5:— | SHA256:— | |||
| 448 | IDM1.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Internet Download Manager\IDM Help.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
121
TCP/UDP connections
175
DNS requests
127
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3748 | iexplore.exe | GET | 304 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | — | — | whitelisted |
3748 | iexplore.exe | GET | 304 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | — | — | whitelisted |
3748 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3748 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3748 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3748 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
3800 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3800 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3800 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3748 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3748 | iexplore.exe | 104.18.57.24:443 | crackingpatching.com | Cloudflare Inc | US | shared |
3800 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3800 | iexplore.exe | 216.58.207.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3748 | iexplore.exe | 216.58.212.162:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
3800 | iexplore.exe | 104.18.57.24:443 | crackingpatching.com | Cloudflare Inc | US | shared |
3748 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3800 | iexplore.exe | 192.0.77.37:443 | c0.wp.com | Automattic, Inc | US | suspicious |
3800 | iexplore.exe | 192.0.77.2:443 | i1.wp.com | Automattic, Inc | US | suspicious |
3800 | iexplore.exe | 157.240.20.19:443 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crackingpatching.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
c0.wp.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
i1.wp.com |
| whitelisted |
i2.wp.com |
| whitelisted |
i0.wp.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |