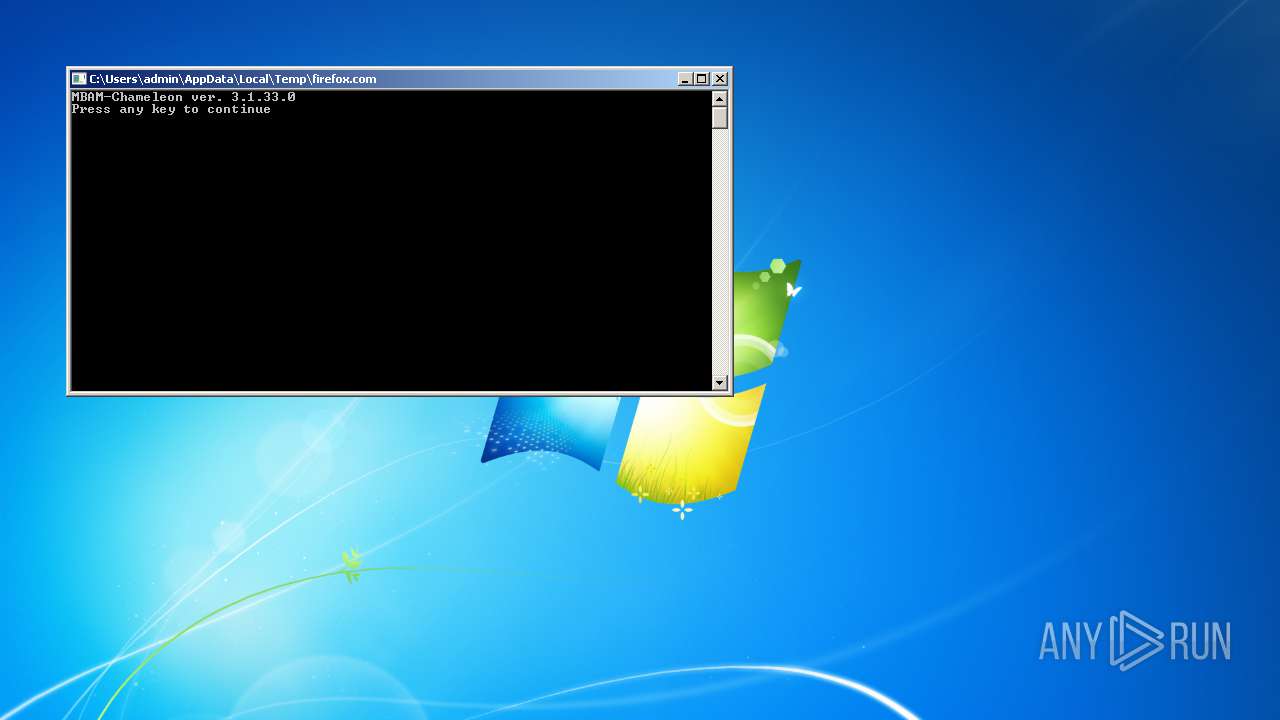
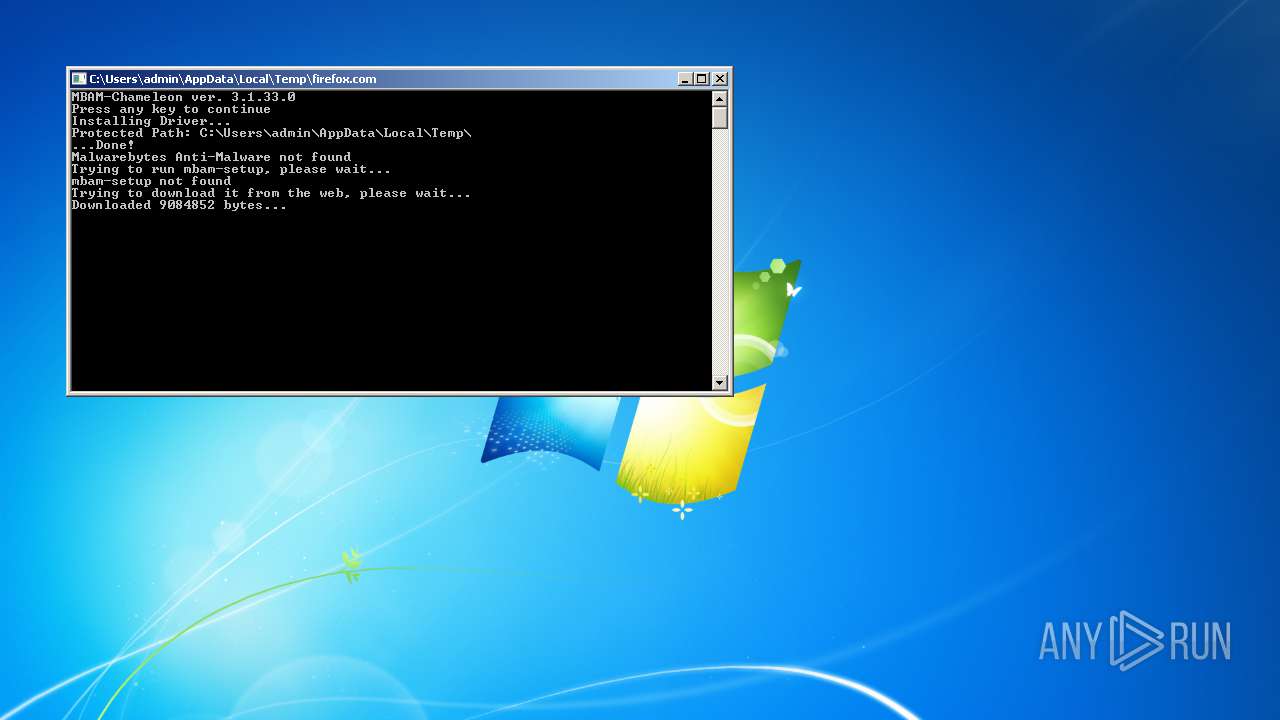
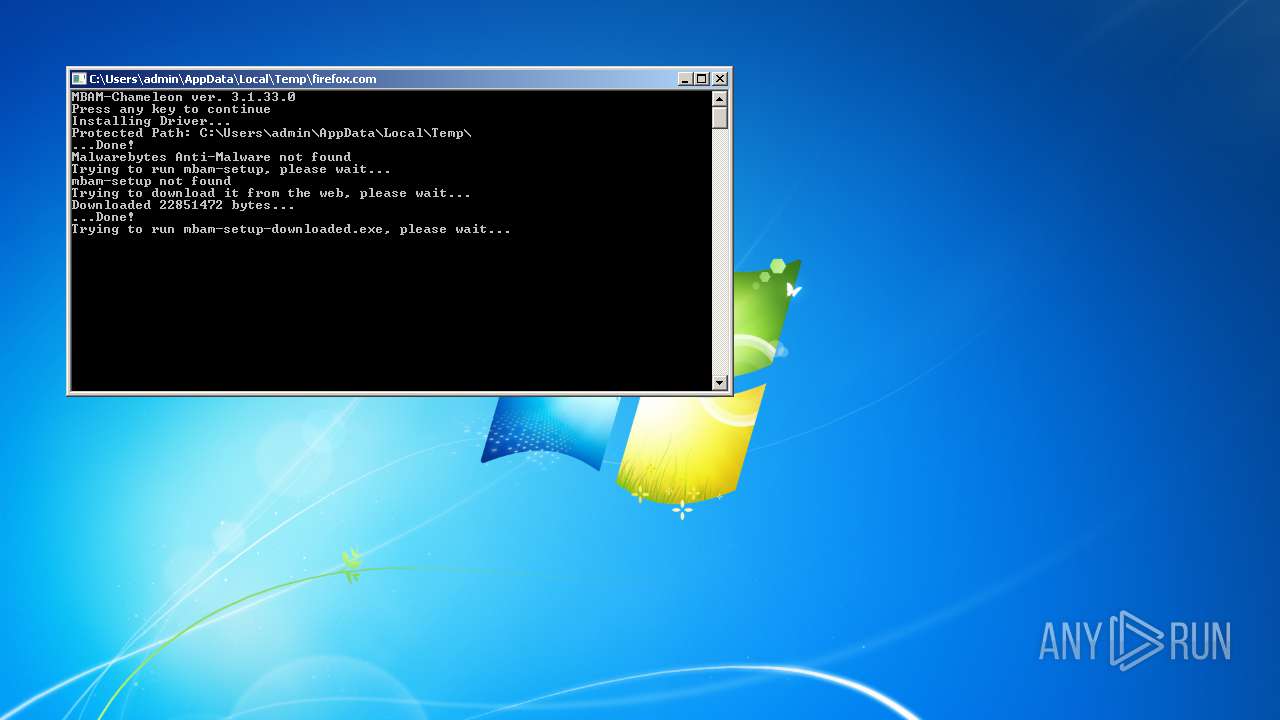
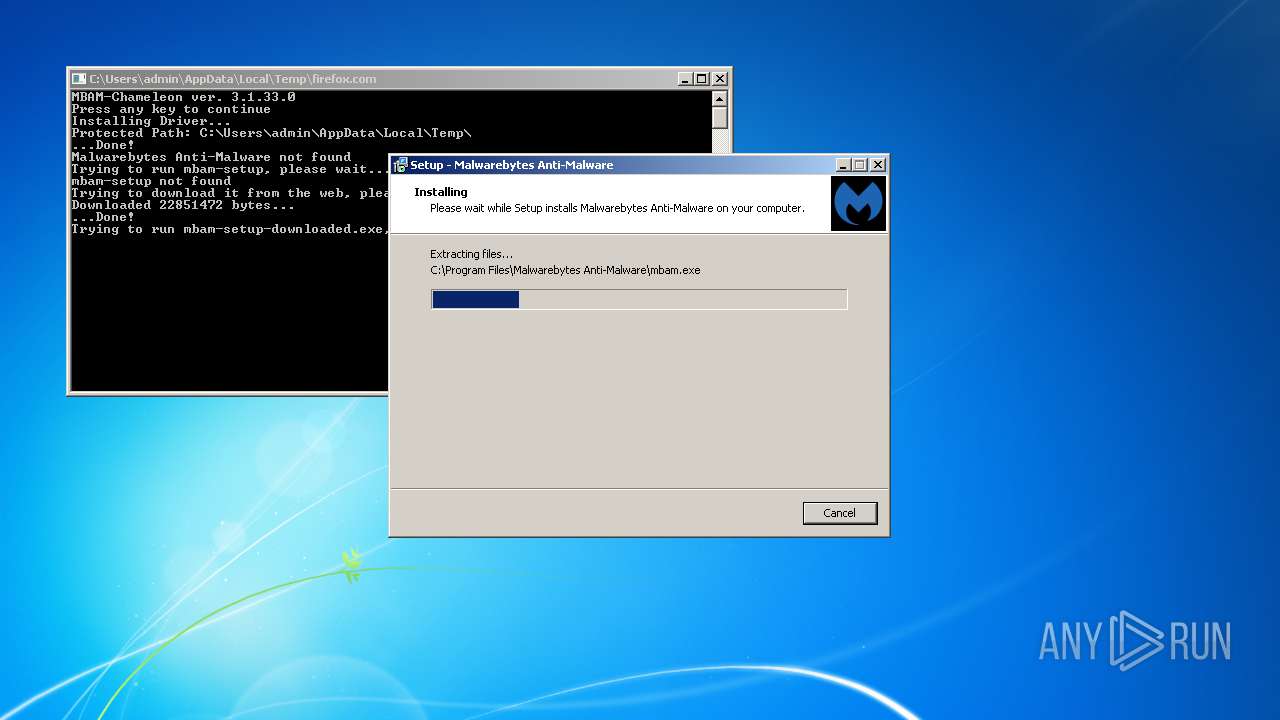
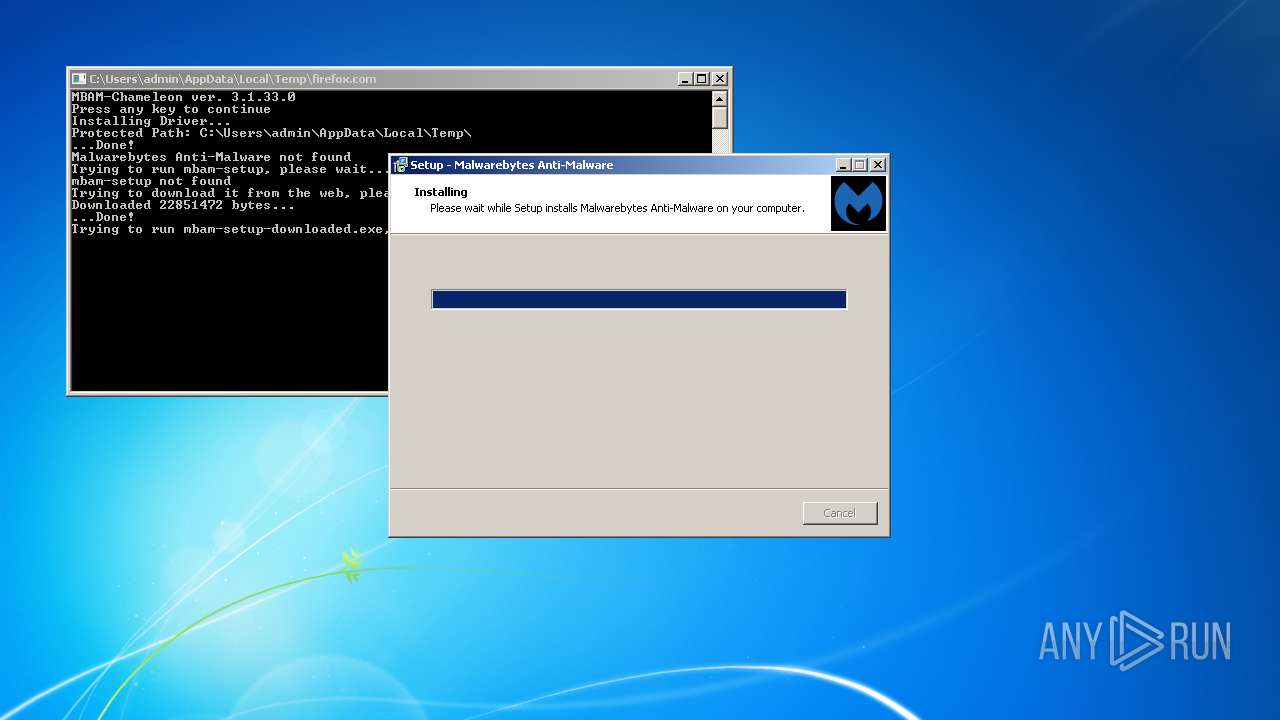
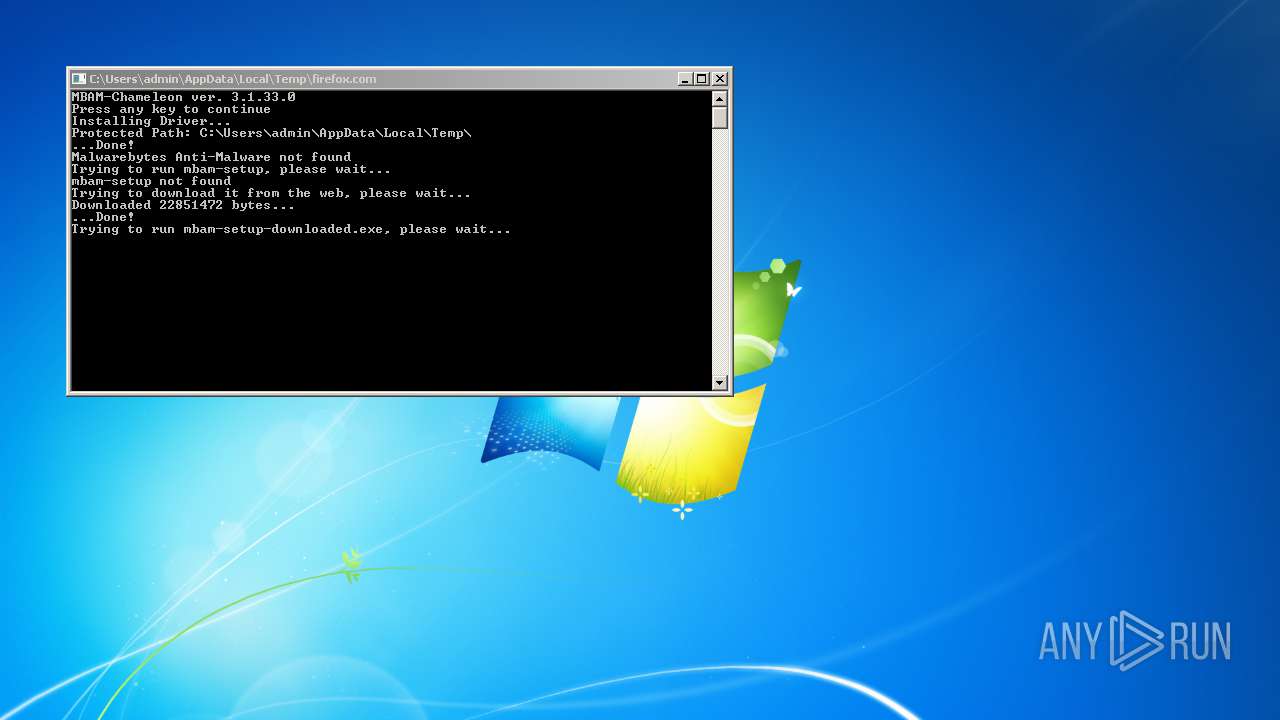
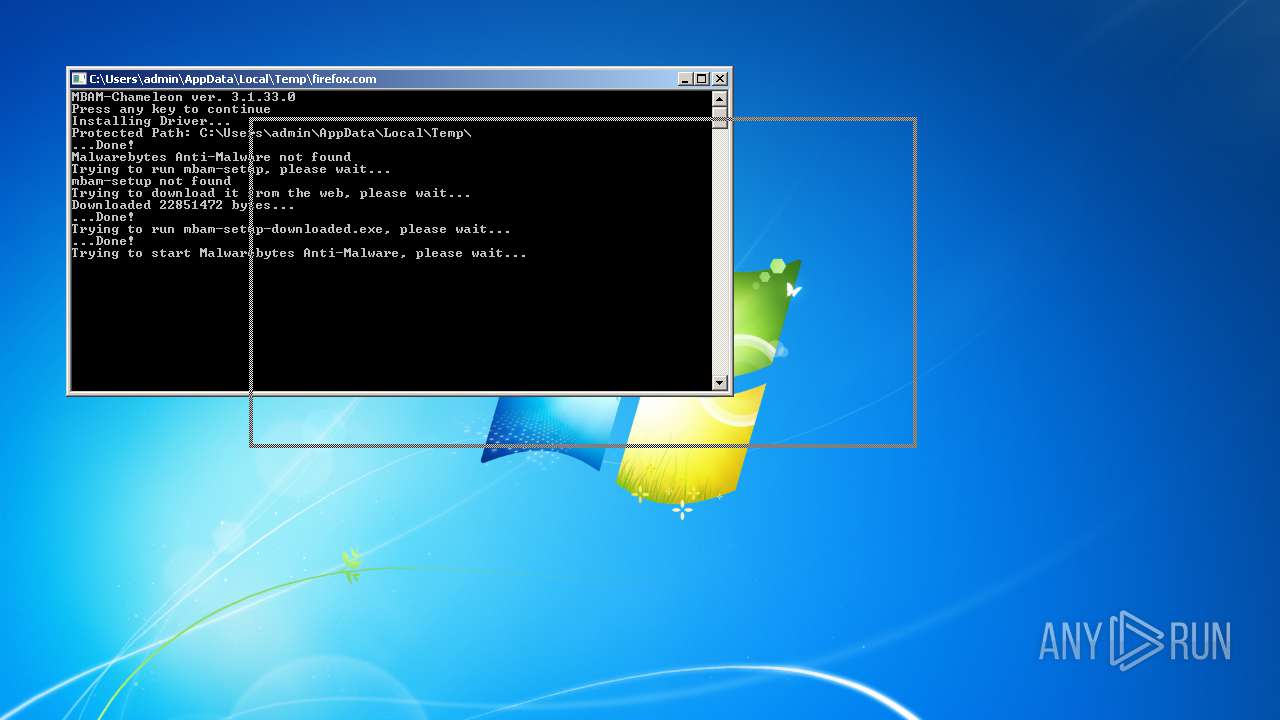
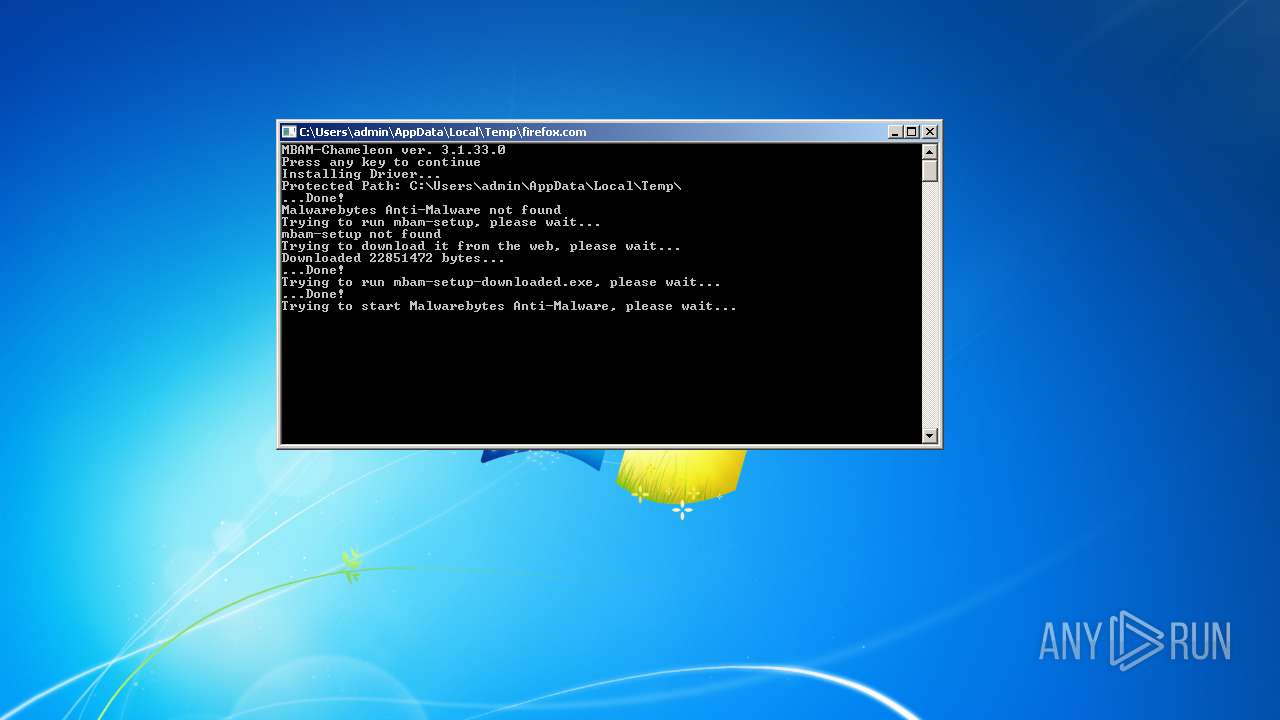
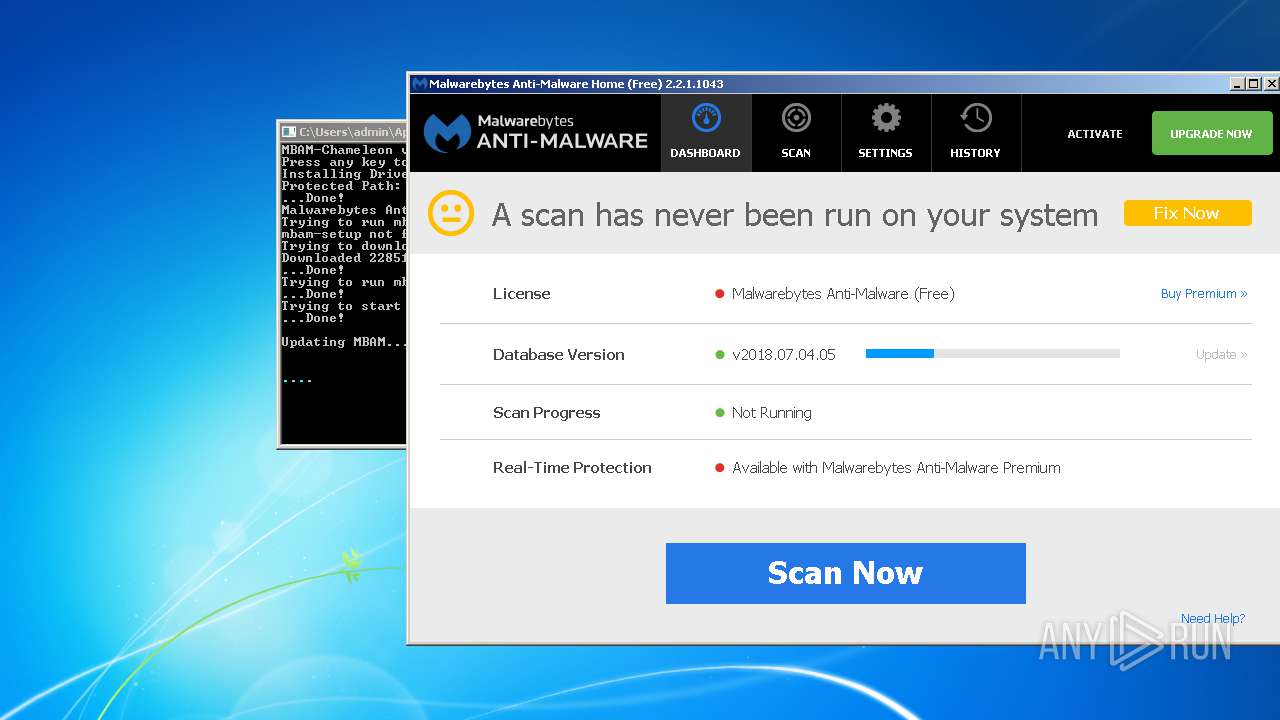
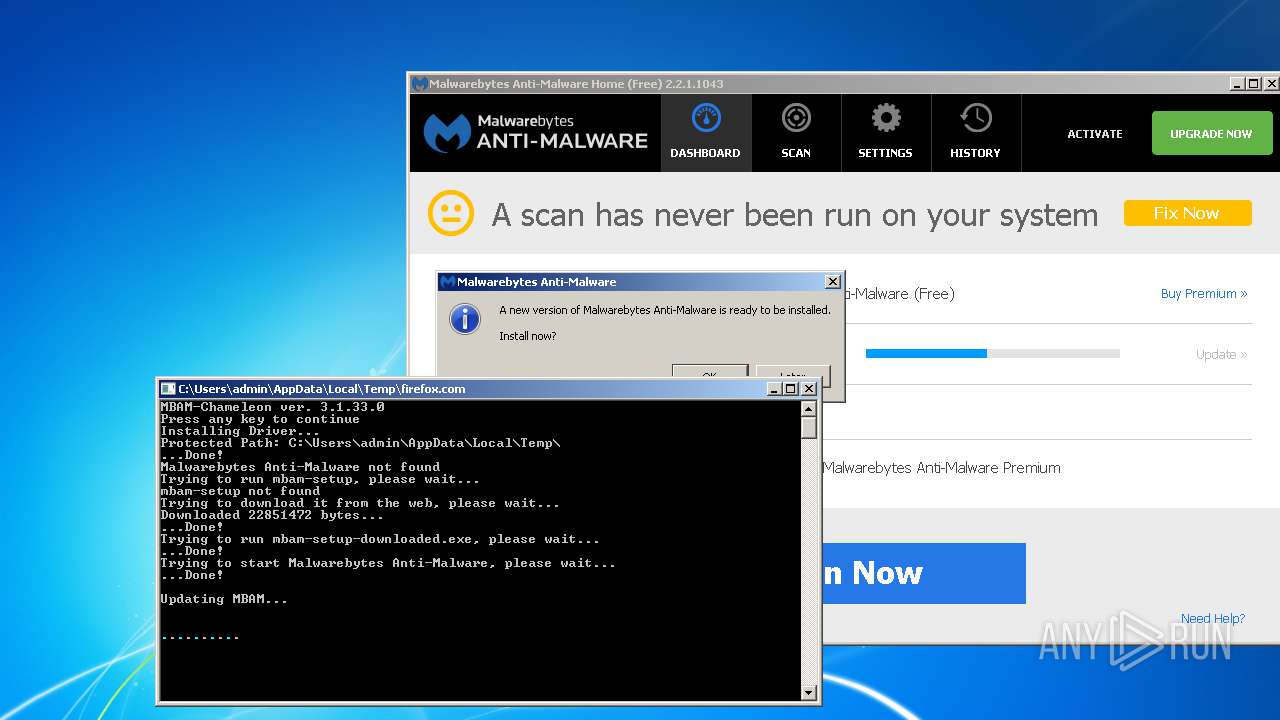
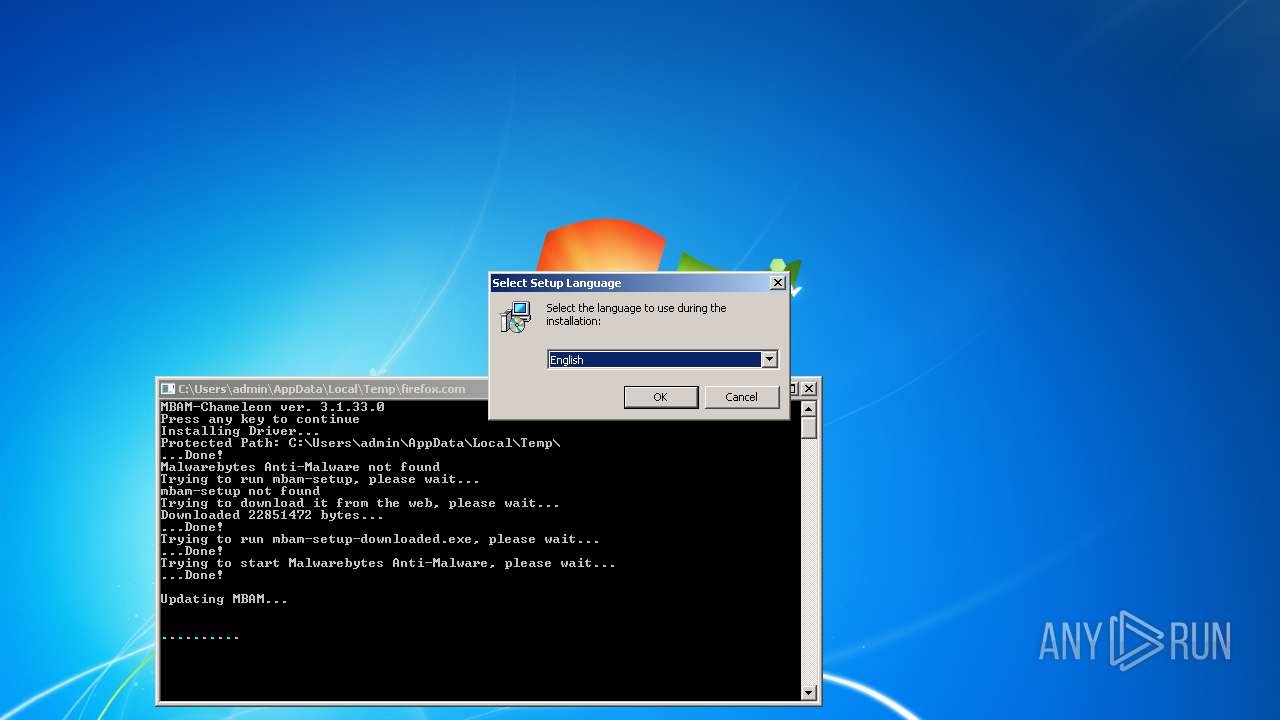
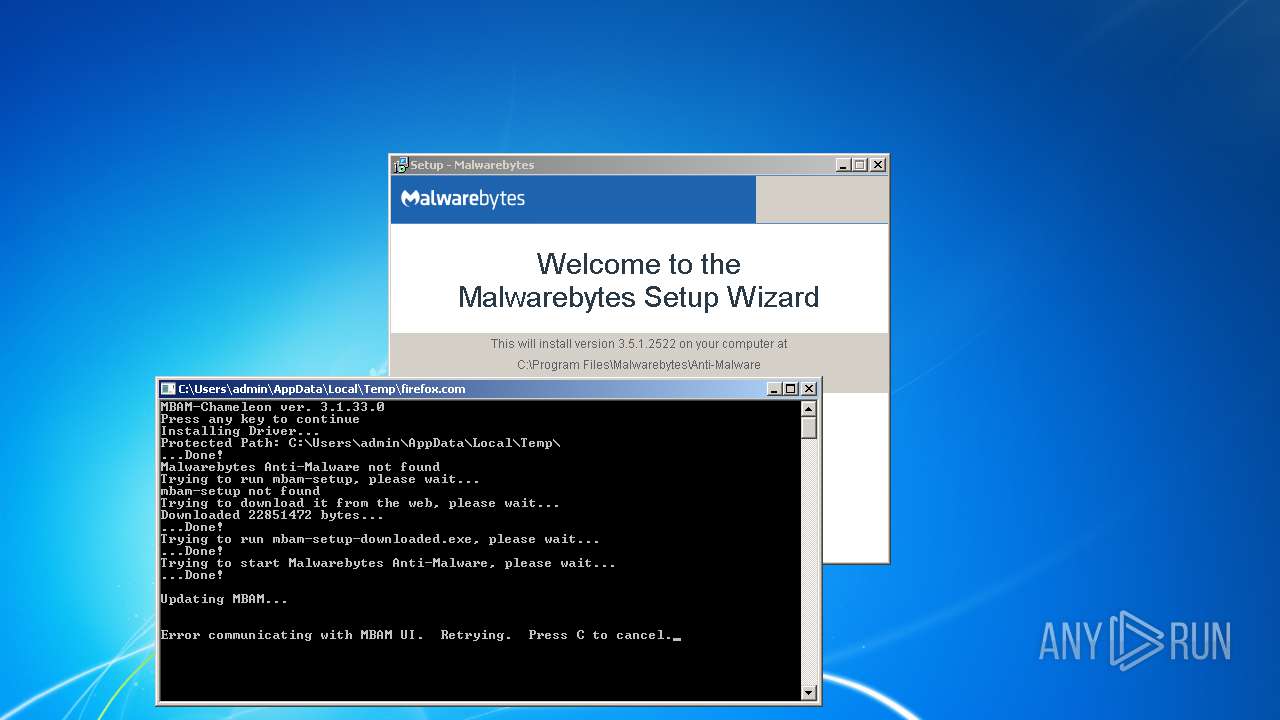
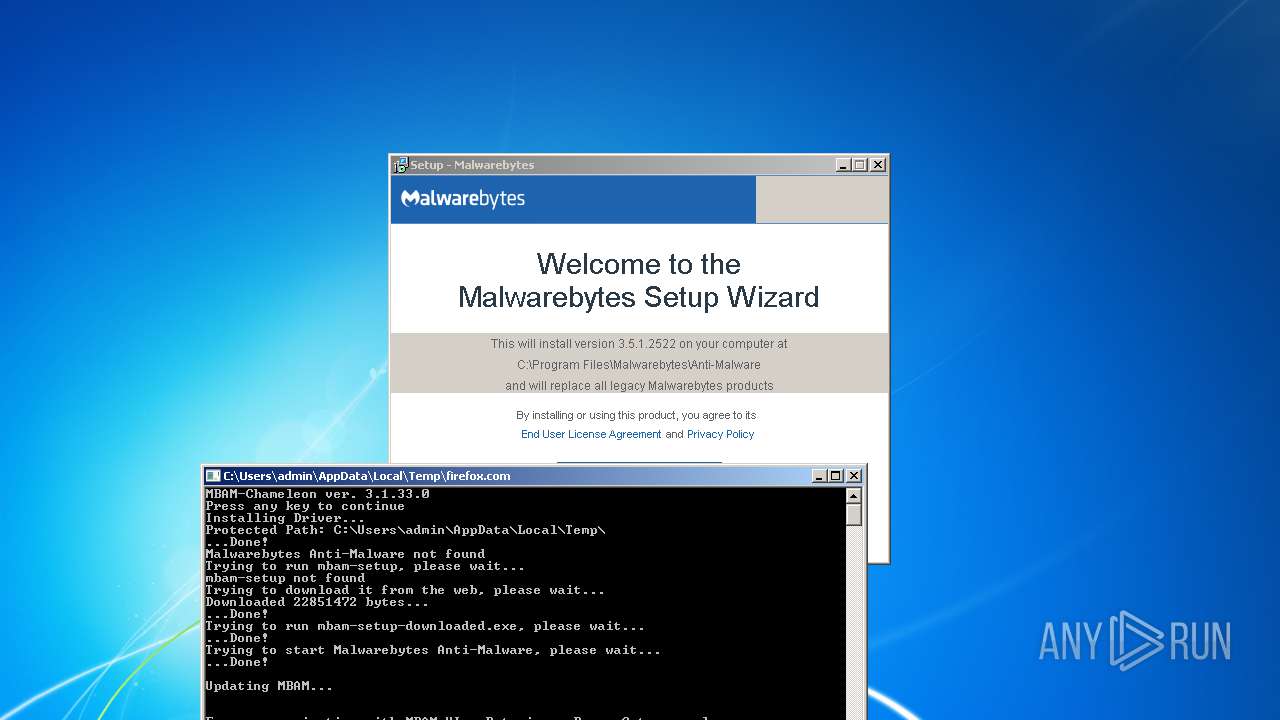
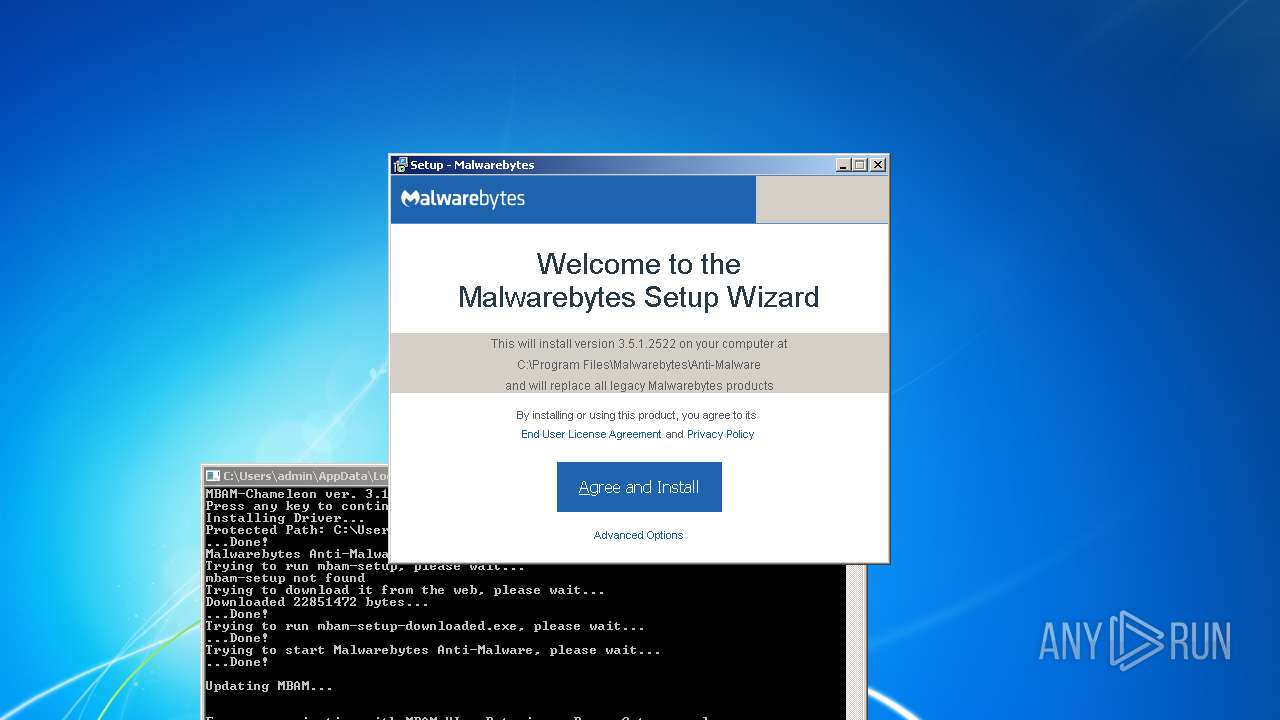
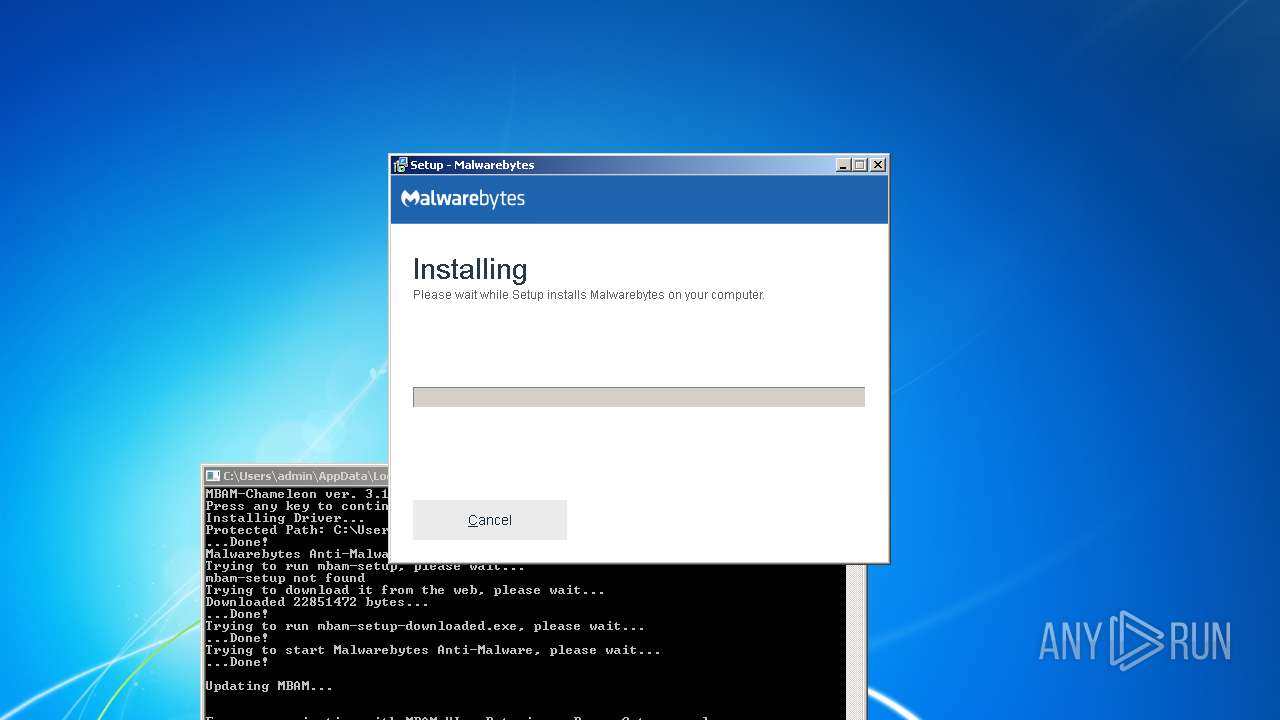
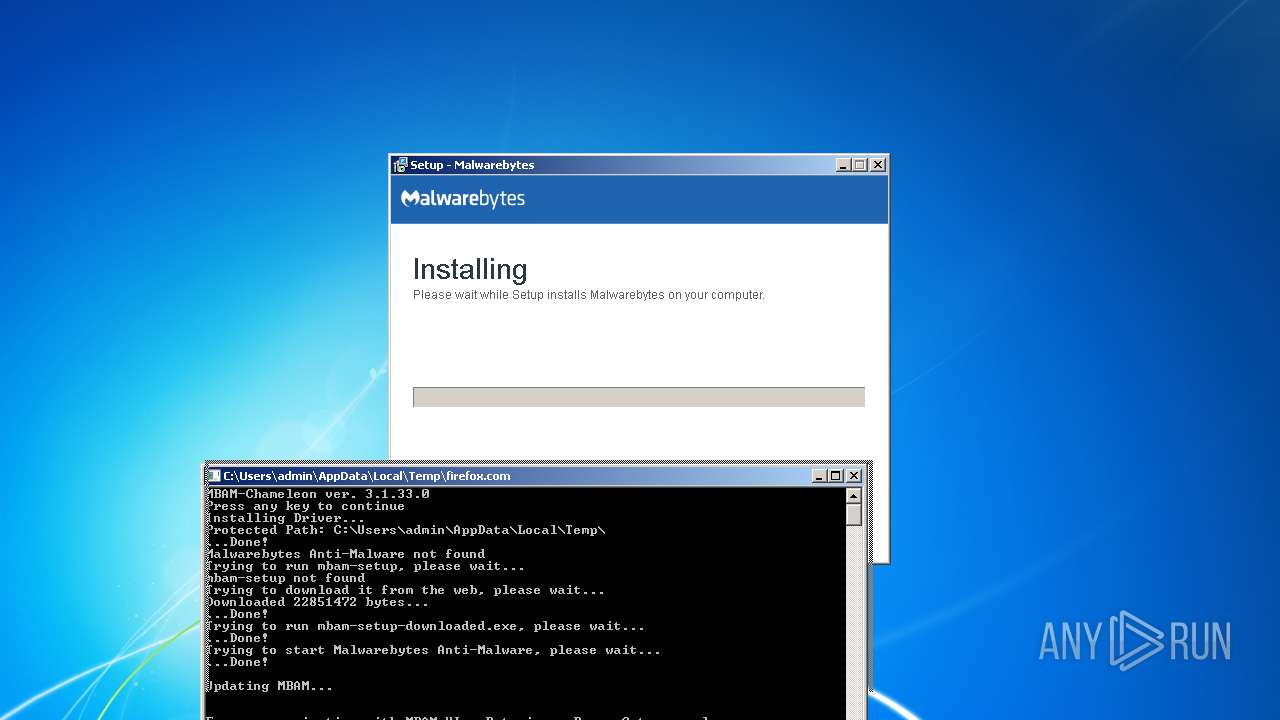
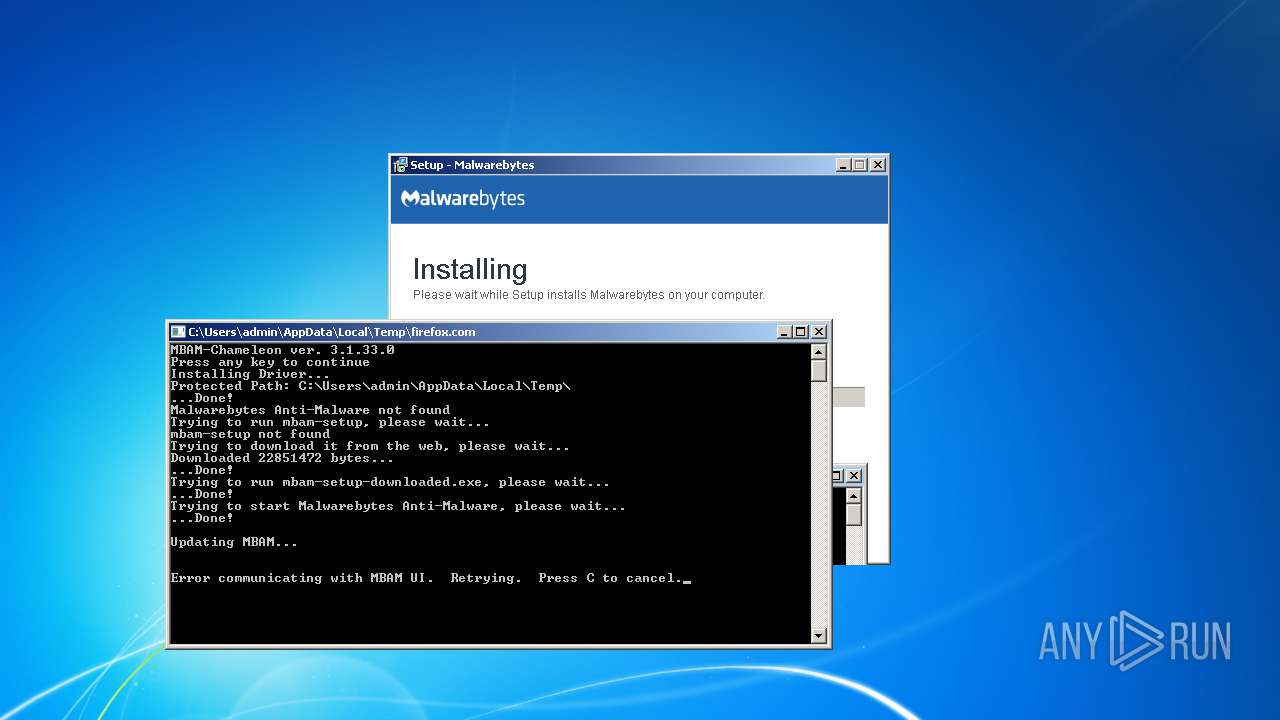
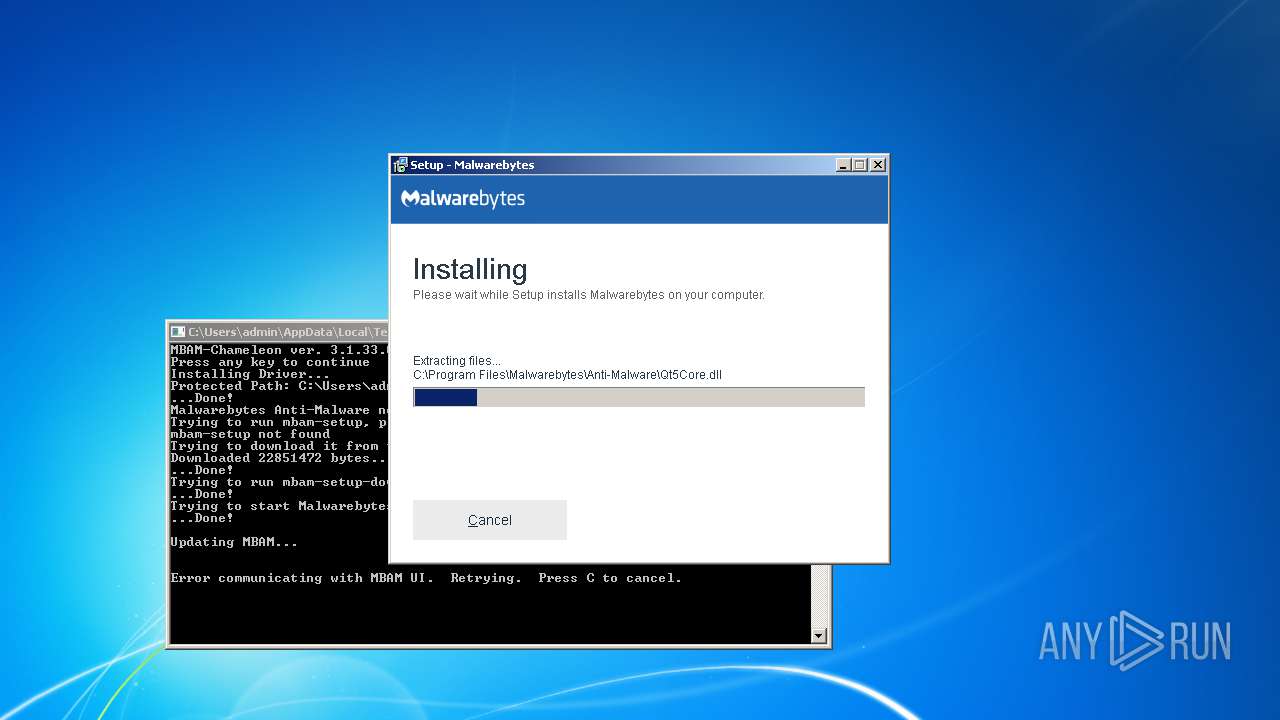
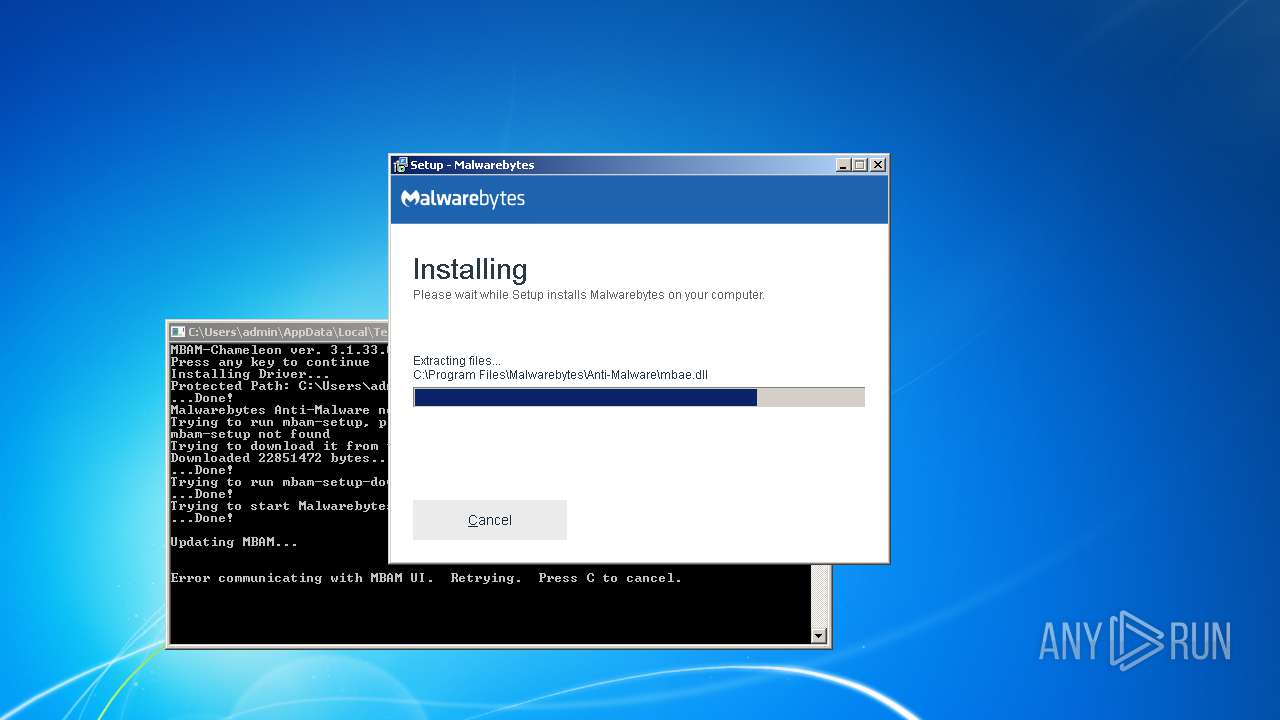
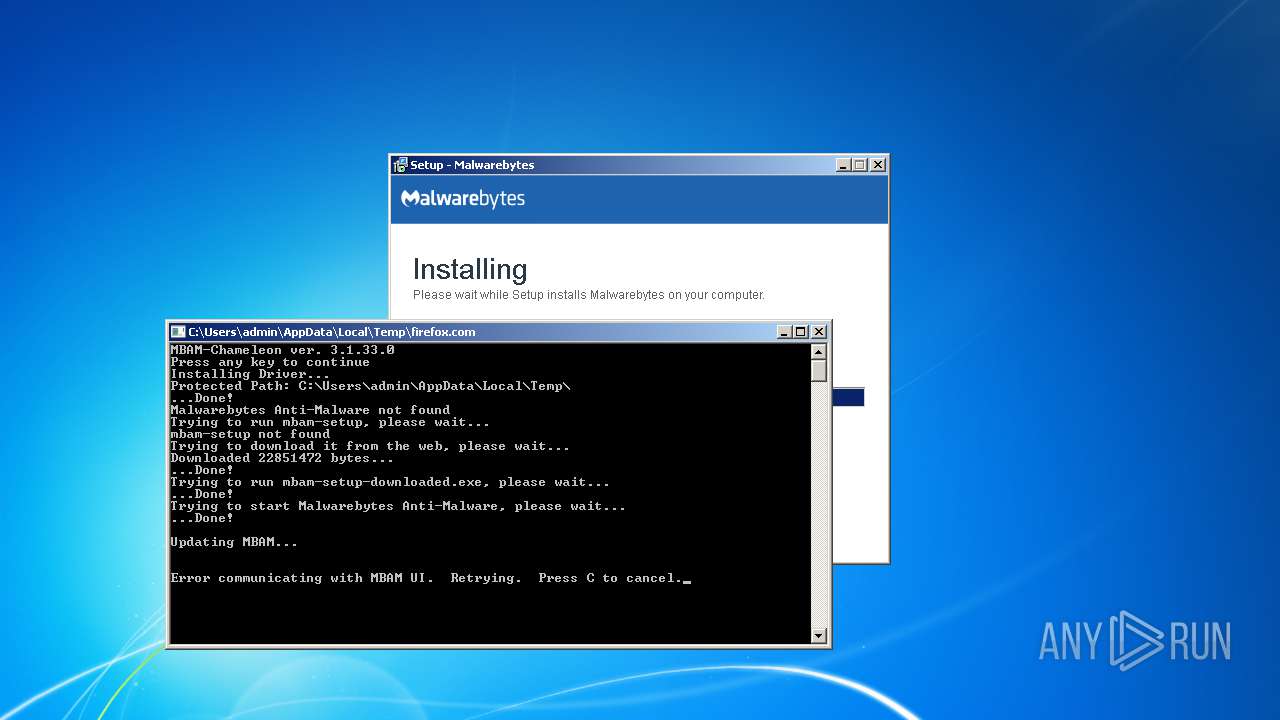
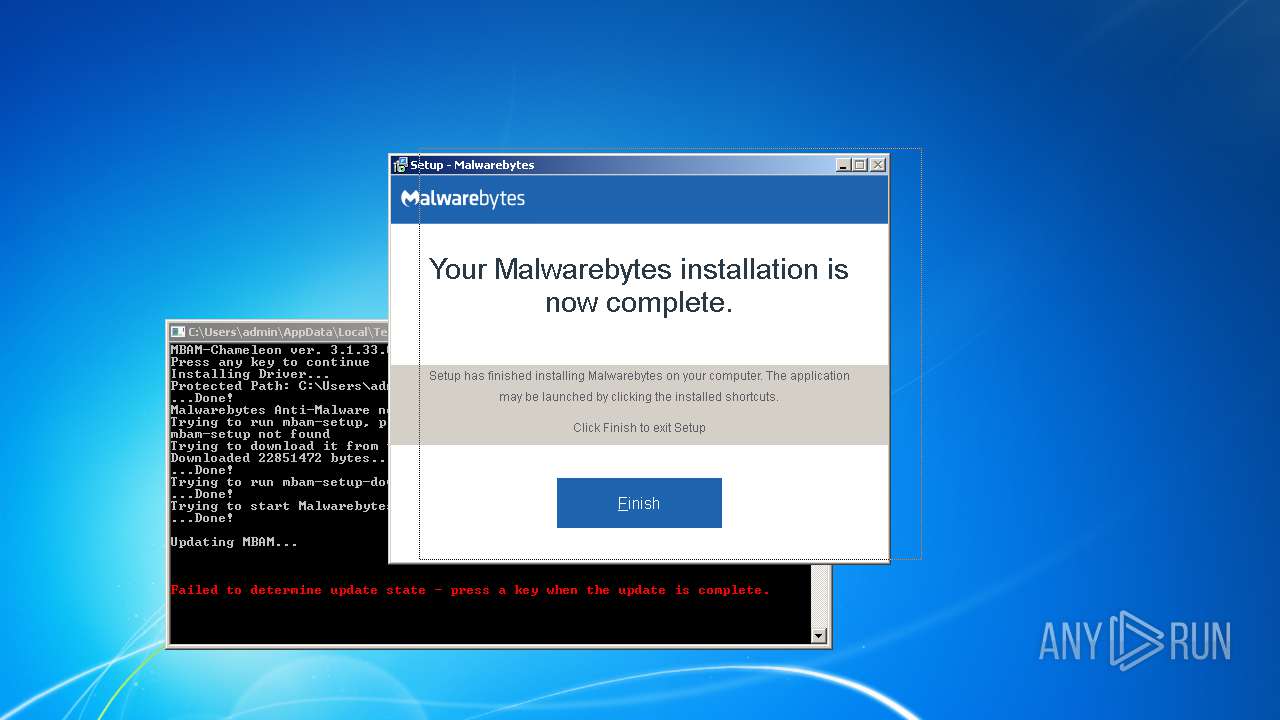
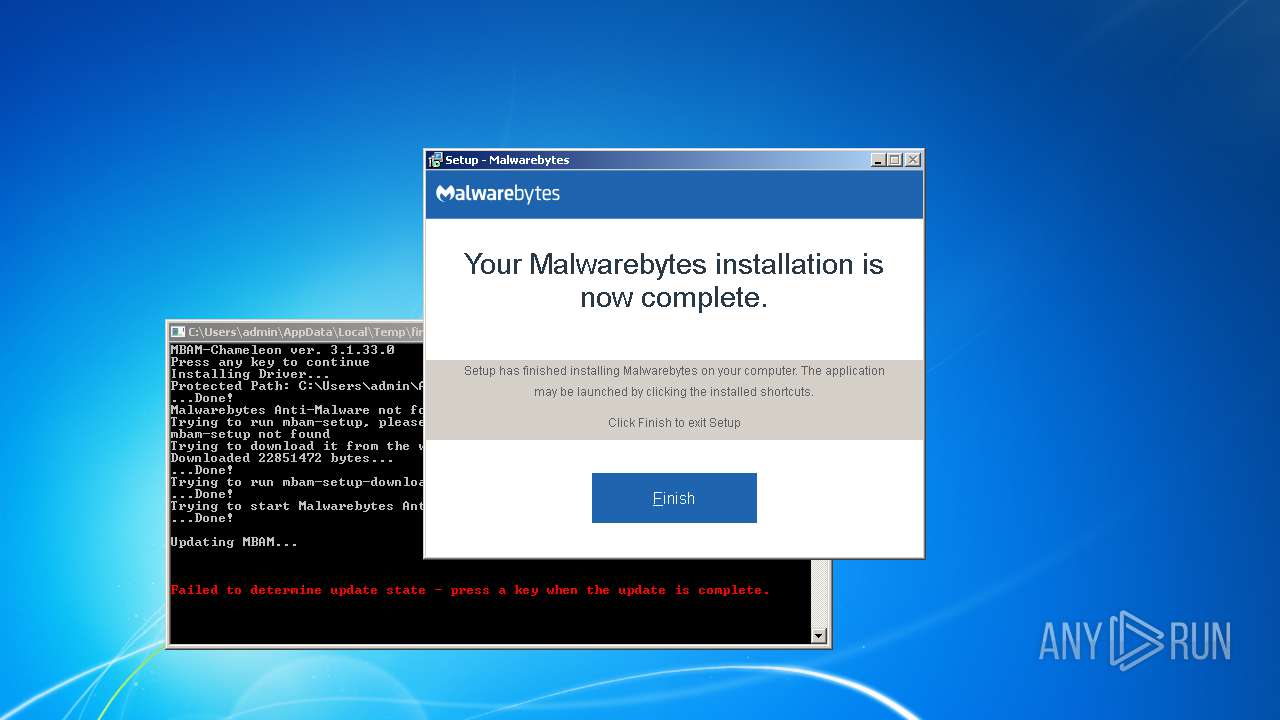
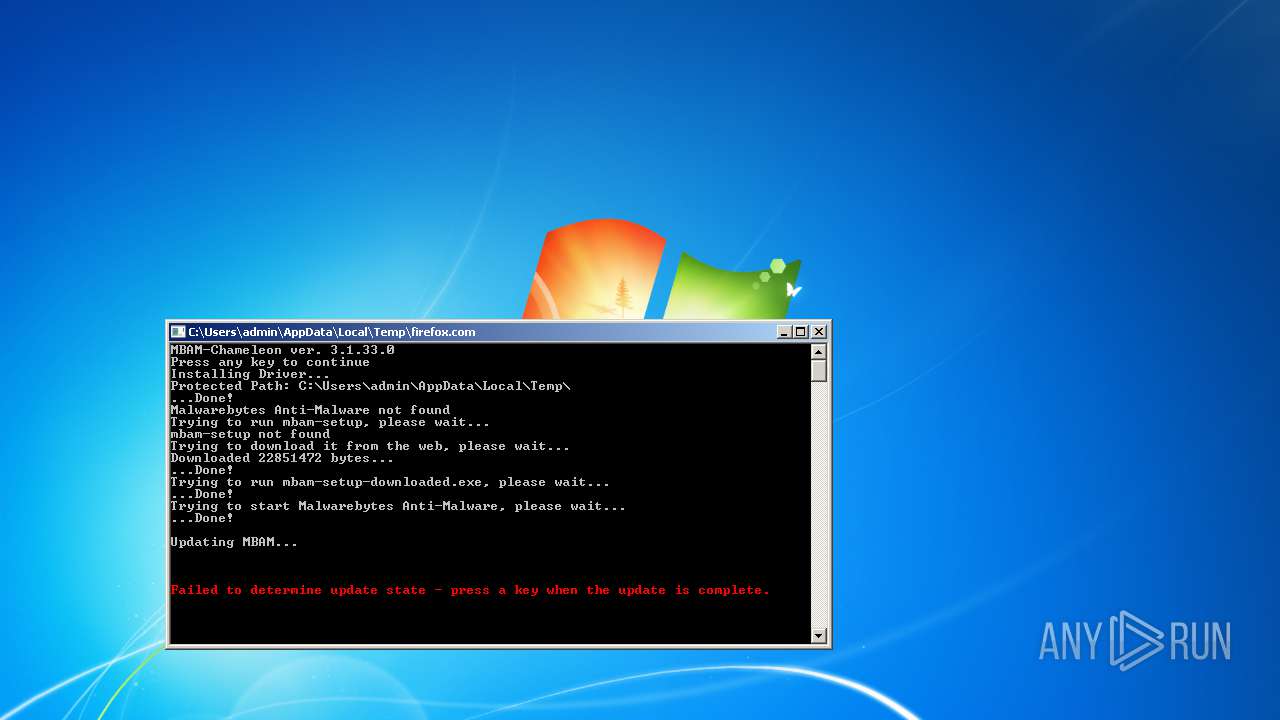
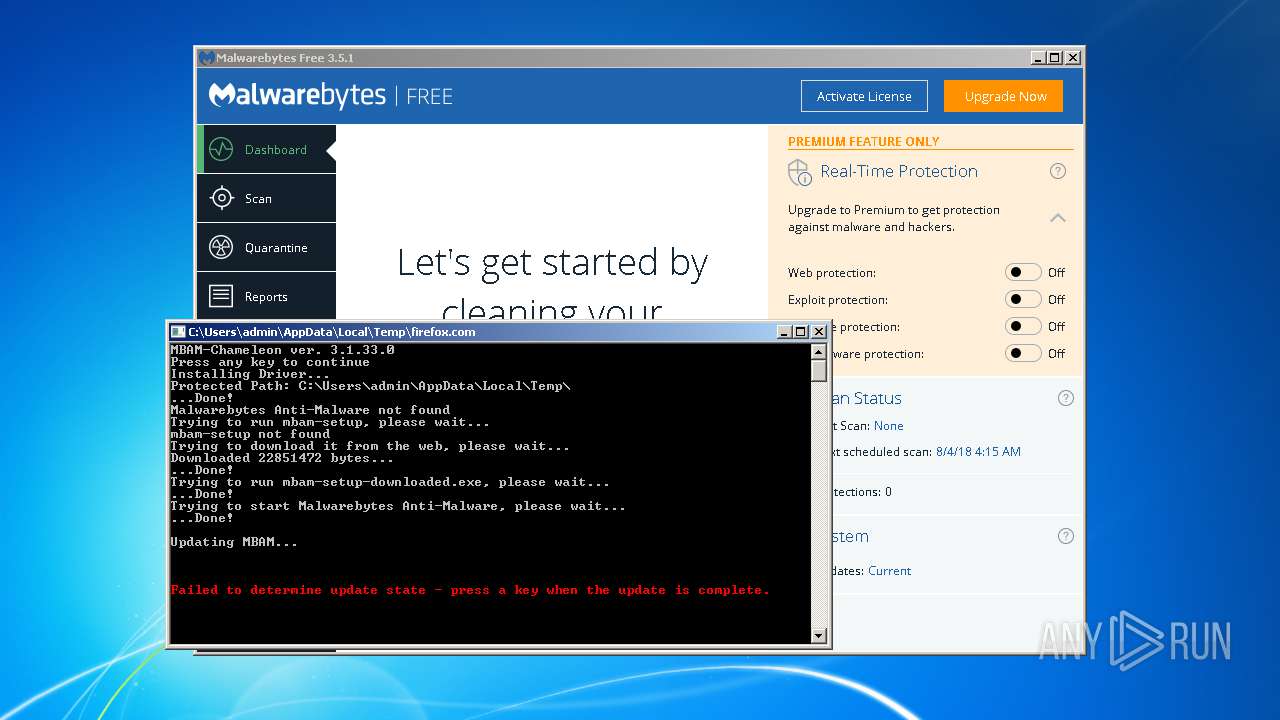
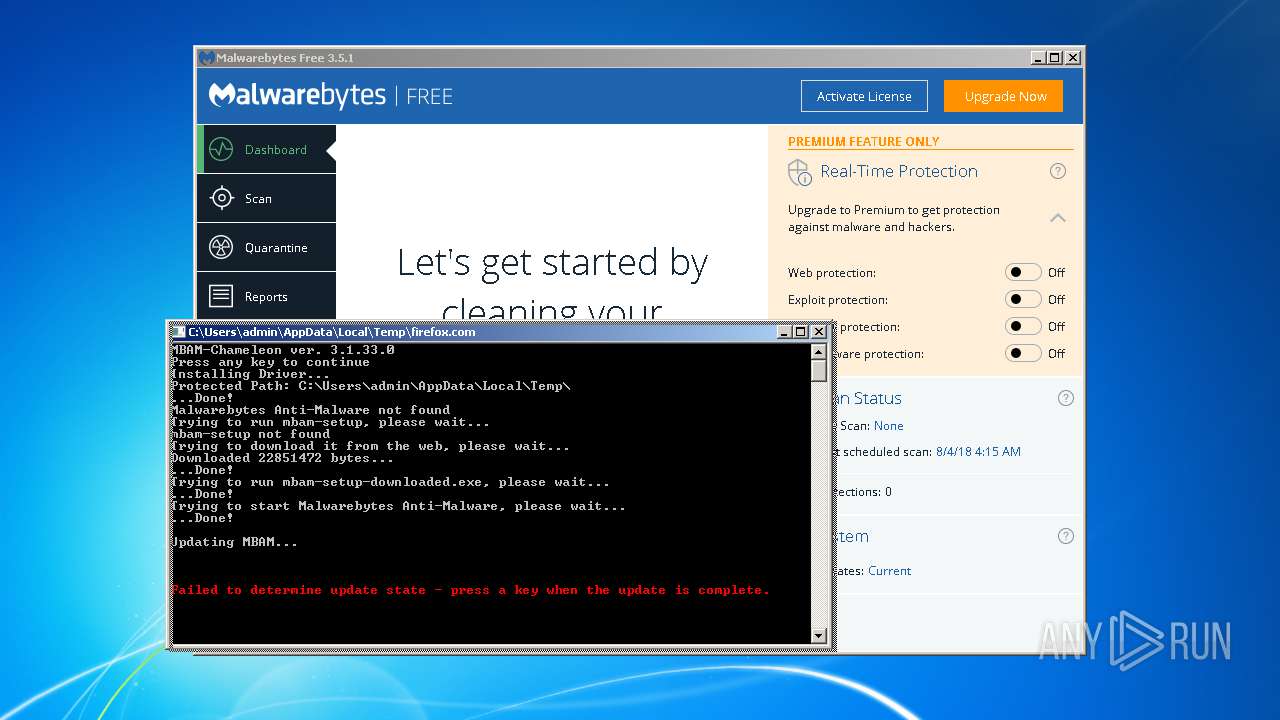
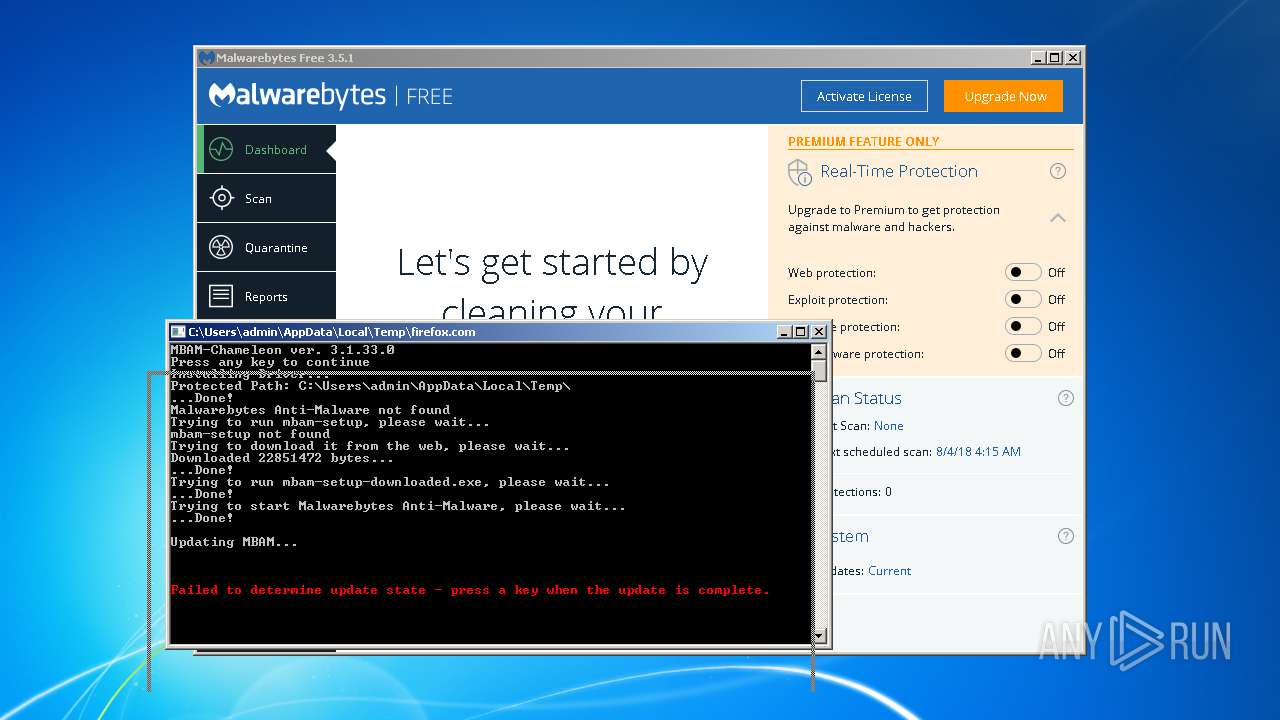
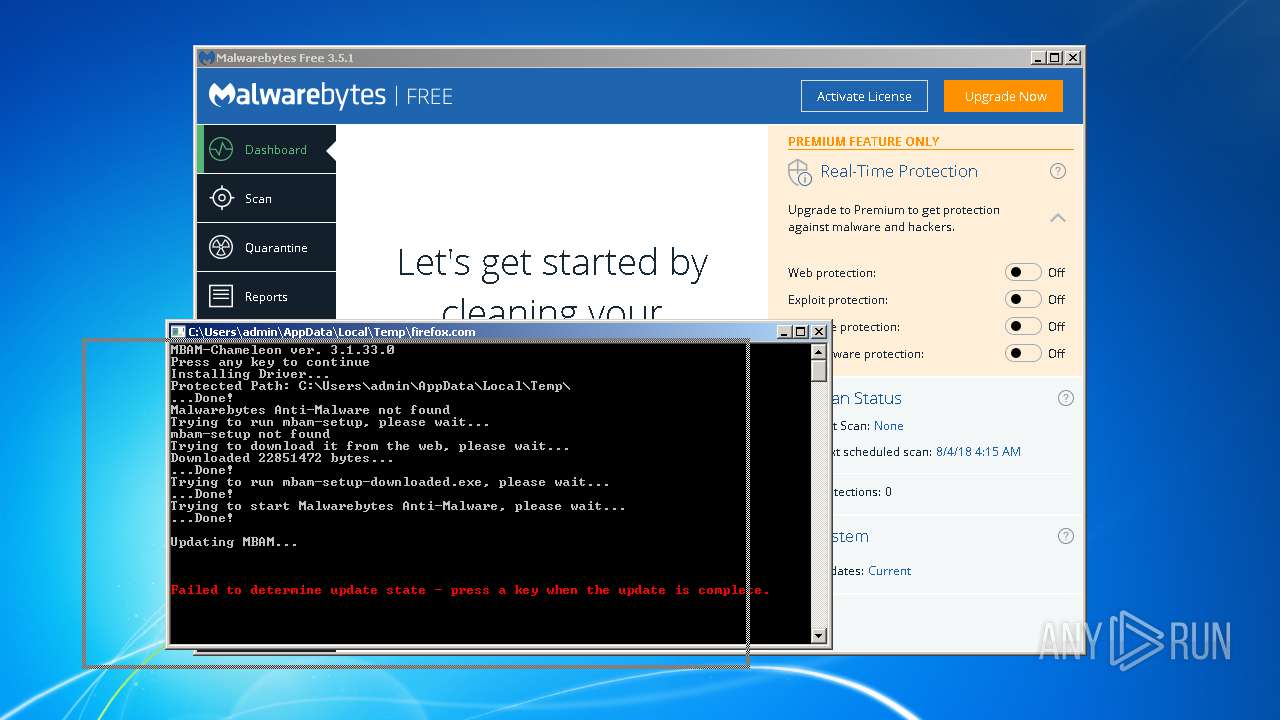
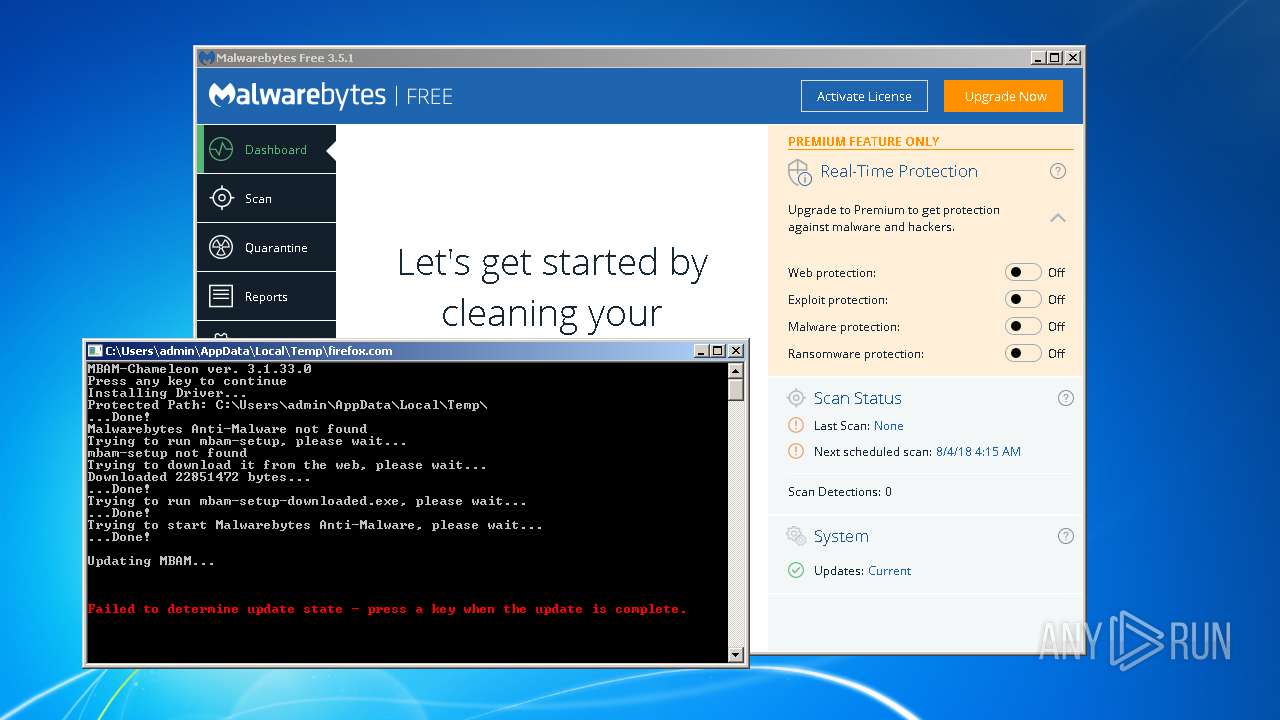
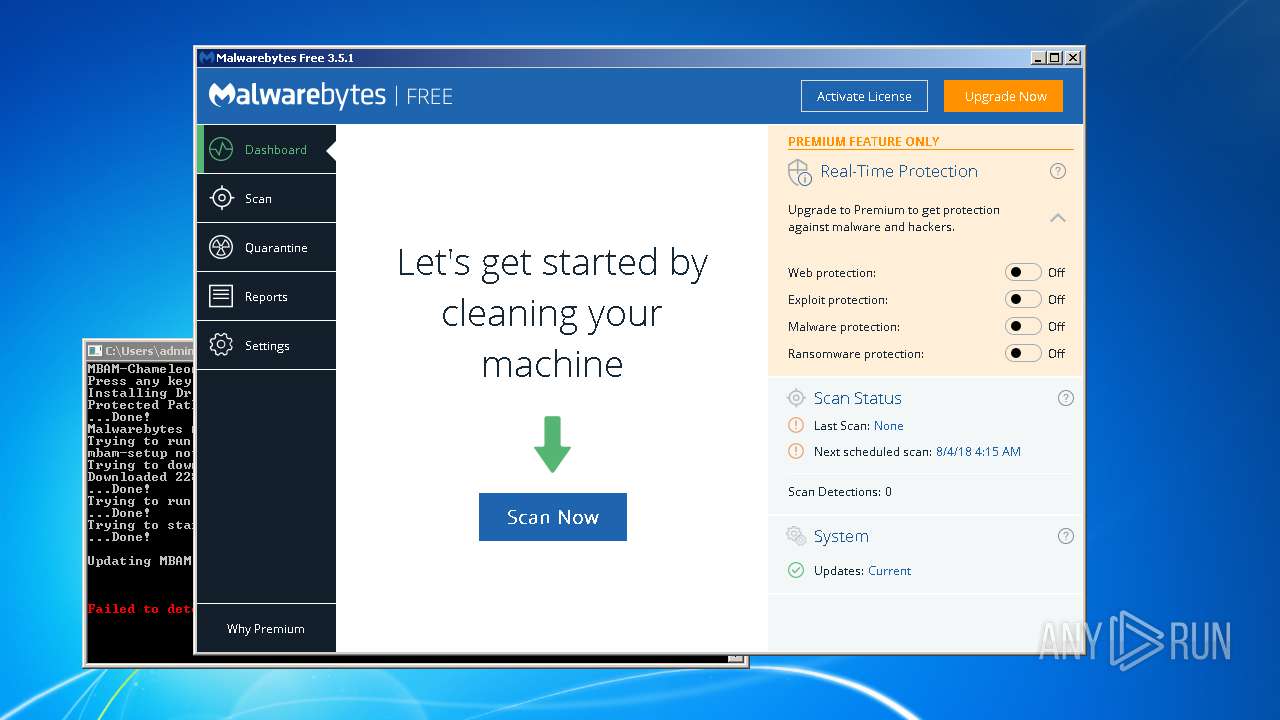
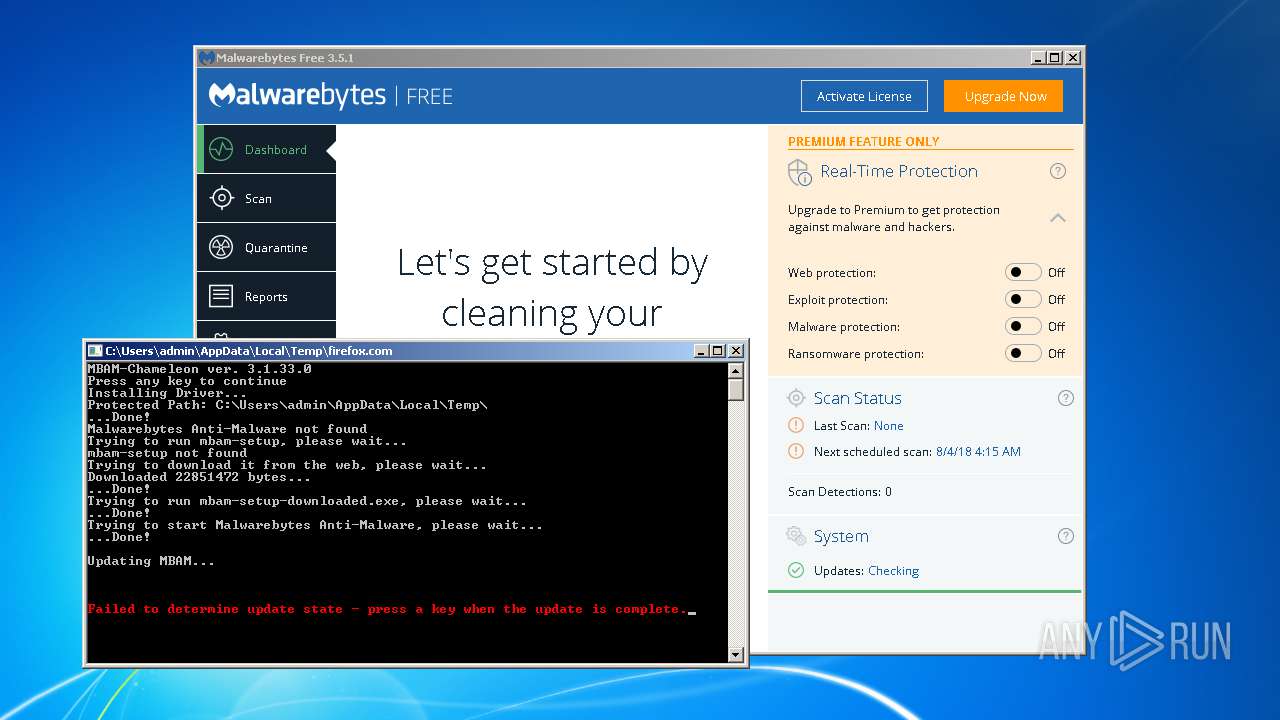
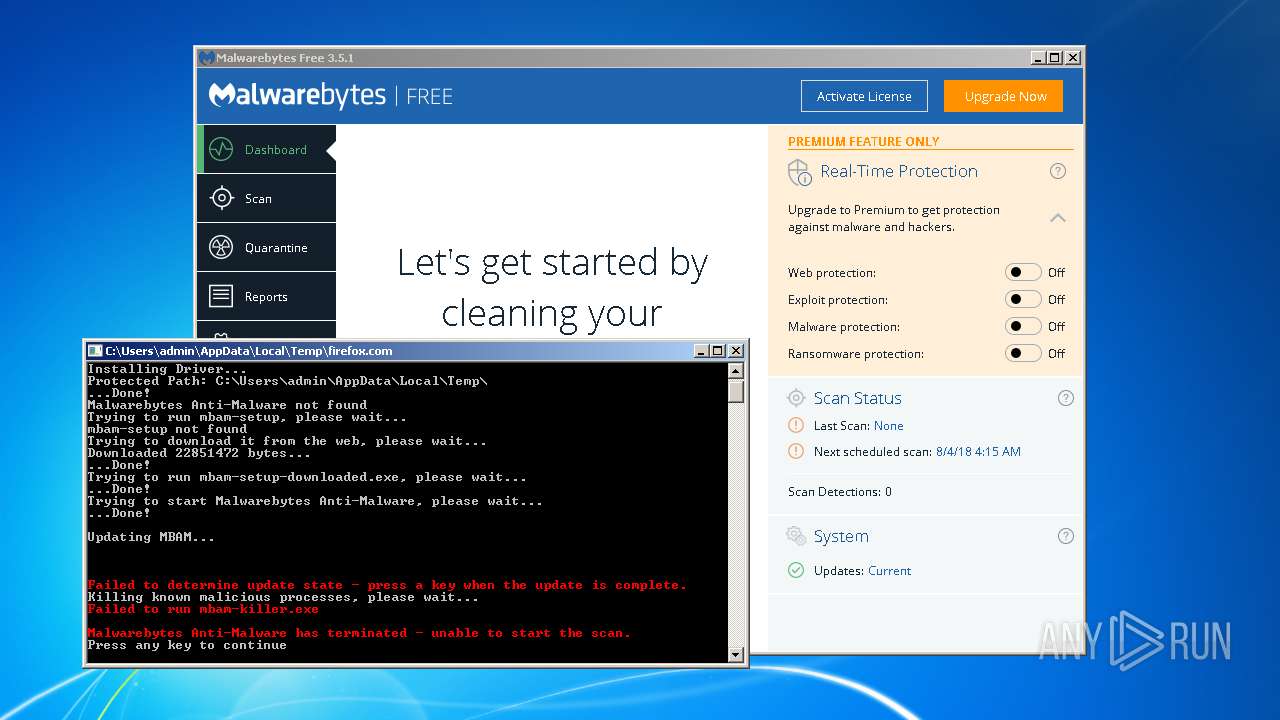
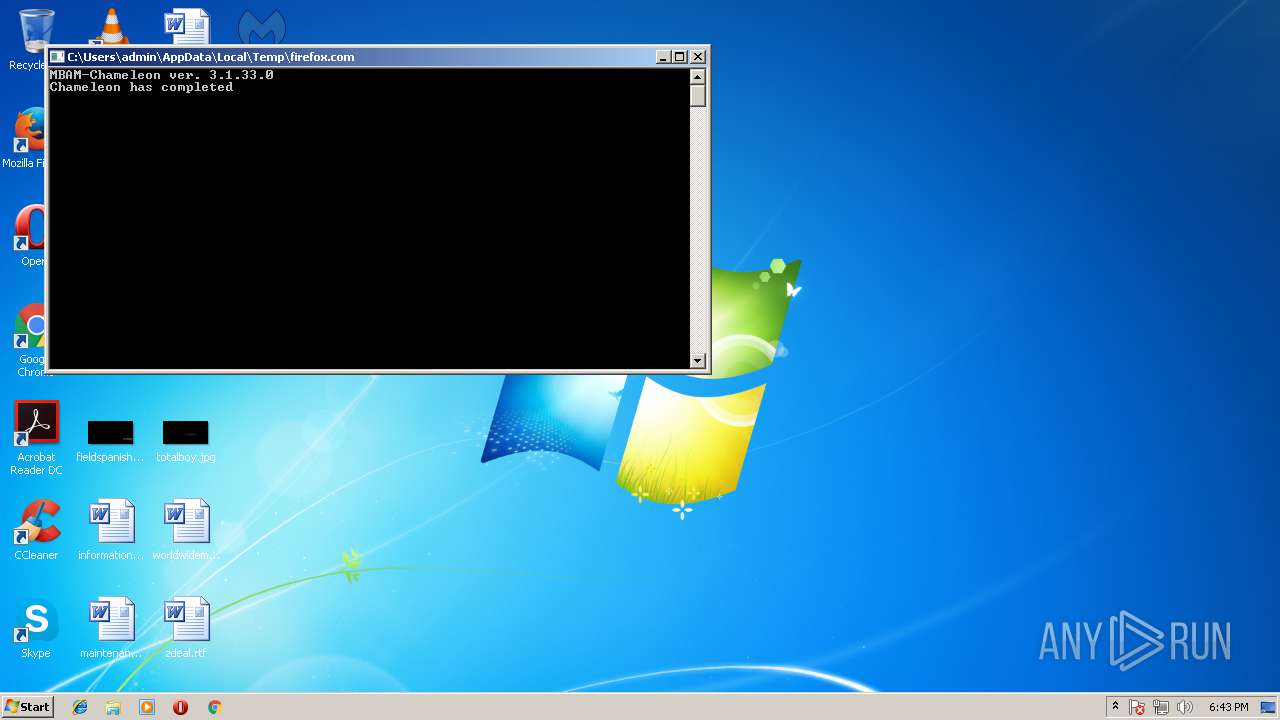
| File name: | firefox.com |
| Full analysis: | https://app.any.run/tasks/626bbd1d-dcf8-42ee-b4a4-1a124bdd525b |
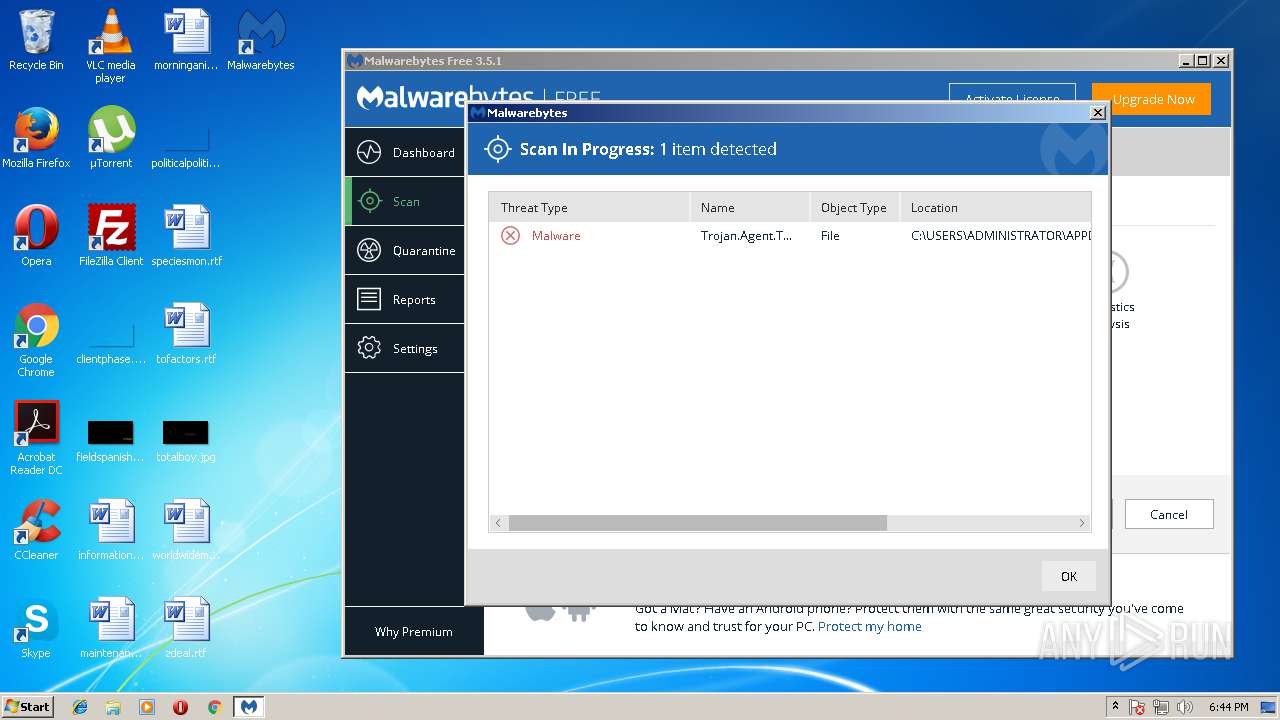
| Verdict: | Malicious activity |
| Analysis date: | July 04, 2018, 17:39:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | DE6CDB4C2EE6C510768D2F04F5A4EAC3 |
| SHA1: | A99B631EF2DD8BEBD9308453E00FE686DBA4C9F2 |
| SHA256: | F10BA92A426EEF3AD51C83BA3DFC63A5B3601529297025D4A2E5DCCD6D9C9158 |
| SSDEEP: | 24576:h4fPiyLlfLAmdxIypY+GhR+ECbreGpDPa/b2y9TfushDNcgEXL7M01cBNZxSu:hlmd3dZeGSBzxSu |
MALICIOUS
Changes settings of System certificates
- firefox.com (PID: 688)
- certutil.exe (PID: 3520)
- certutil.exe (PID: 2644)
- mbam.exe (PID: 3044)
Registers / Runs the DLL via REGSVR32.EXE
- mbam-setup-downloaded.tmp (PID: 996)
- _iu14D2N.tmp (PID: 3352)
Application was dropped or rewritten from another process
- mbam-setup-downloaded.exe (PID: 1208)
- mbam.exe (PID: 3044)
- mbamresearch.exe (PID: 384)
- _iu14D2N.tmp (PID: 3352)
- unins000.exe (PID: 1488)
- mbamservice.exe (PID: 1672)
- mbamservice.exe (PID: 1456)
- mbam.exe (PID: 3236)
- mbamtray.exe (PID: 848)
- mbam.exe (PID: 2996)
Loads dropped or rewritten executable
- mbam.exe (PID: 3044)
- regsvr32.exe (PID: 1424)
- _iu14D2N.tmp (PID: 3352)
- regsvr32.exe (PID: 3248)
- mbamservice.exe (PID: 1456)
- mbamtray.exe (PID: 848)
- mbam.exe (PID: 3236)
- mbam.exe (PID: 2996)
SUSPICIOUS
Application launched itself
- firefox.com (PID: 3376)
Creates files in the Windows directory
- firefox.com (PID: 688)
- mbam-setup-downloaded.tmp (PID: 996)
- mbam.exe (PID: 3044)
- mbam-setup.tmp (PID: 2564)
- certutil.exe (PID: 3520)
- certutil.exe (PID: 2644)
- mbamservice.exe (PID: 1456)
Starts application with an unusual extension
- firefox.com (PID: 3376)
- unins000.exe (PID: 1488)
Creates files in the driver directory
- firefox.com (PID: 688)
- mbam-setup-downloaded.tmp (PID: 996)
- mbam.exe (PID: 3044)
- mbam-setup.tmp (PID: 2564)
- mbamservice.exe (PID: 1456)
Creates or modifies windows services
- firefox.com (PID: 688)
- mbam-setup-downloaded.tmp (PID: 996)
- mbam.exe (PID: 3044)
- _iu14D2N.tmp (PID: 3352)
- mbamservice.exe (PID: 1672)
- mbamservice.exe (PID: 1456)
Adds / modifies Windows certificates
- firefox.com (PID: 688)
- mbam.exe (PID: 3044)
Removes files from Windows directory
- mbam-setup-downloaded.tmp (PID: 996)
- _iu14D2N.tmp (PID: 3352)
- certutil.exe (PID: 3520)
- certutil.exe (PID: 2644)
- mbamservice.exe (PID: 1456)
Executable content was dropped or overwritten
- mbam-setup-downloaded.exe (PID: 1208)
- mbam-setup-downloaded.tmp (PID: 996)
- mbam.exe (PID: 3044)
- firefox.com (PID: 688)
- mbam-setup.exe (PID: 1332)
- unins000.exe (PID: 1488)
- mbam-setup.tmp (PID: 2564)
- _iu14D2N.tmp (PID: 3352)
- mbamservice.exe (PID: 1456)
Changes IE settings (feature browser emulation)
- mbam.exe (PID: 3044)
- mbam-setup.tmp (PID: 2564)
Creates files in the program directory
- mbam.exe (PID: 3044)
- mbamservice.exe (PID: 1456)
Reads Windows owner settings
- mbam-setup.tmp (PID: 2564)
Reads the Windows organization settings
- mbam-setup.tmp (PID: 2564)
Uses TASKKILL.EXE to kill process
- _iu14D2N.tmp (PID: 3352)
Modifies the open verb of a shell class
- mbam-setup.tmp (PID: 2564)
Creates COM task schedule object
- regsvr32.exe (PID: 1424)
- mbamservice.exe (PID: 1456)
Searches for installed software
- mbam-setup.tmp (PID: 2564)
Creates files in the user directory
- mbam.exe (PID: 3236)
- mbam.exe (PID: 2996)
INFO
Dropped object may contain URL's
- mbam-setup-downloaded.exe (PID: 1208)
- mbam.exe (PID: 3044)
- firefox.com (PID: 688)
- unins000.exe (PID: 1488)
- mbam-setup-downloaded.tmp (PID: 996)
- mbamservice.exe (PID: 1456)
- mbam-setup.tmp (PID: 2564)
Dropped object may contain Bitcoin addresses
- mbam-setup-downloaded.tmp (PID: 996)
- mbam-setup.tmp (PID: 2564)
- mbamservice.exe (PID: 1456)
Creates a software uninstall entry
- mbam-setup-downloaded.tmp (PID: 996)
- mbam-setup.tmp (PID: 2564)
Loads dropped or rewritten executable
- mbam-setup-downloaded.tmp (PID: 996)
- mbam-setup.tmp (PID: 2564)
Application was dropped or rewritten from another process
- mbam-setup-downloaded.tmp (PID: 996)
- mbam-setup.tmp (PID: 2564)
Creates files in the program directory
- mbam-setup-downloaded.tmp (PID: 996)
- mbam-setup.tmp (PID: 2564)
Reads settings of System Certificates
- mbamservice.exe (PID: 1456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:05:05 01:07:42+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 419328 |
| InitializedDataSize: | 543232 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x476fb |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows command line |
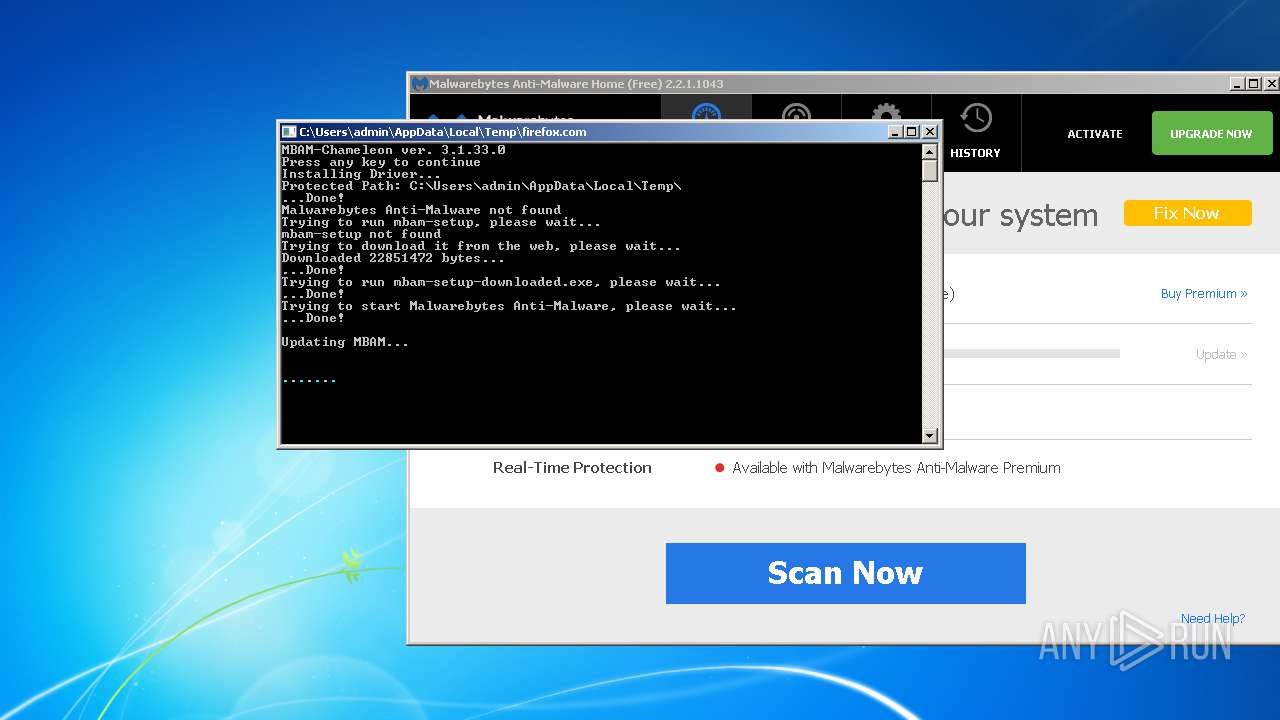
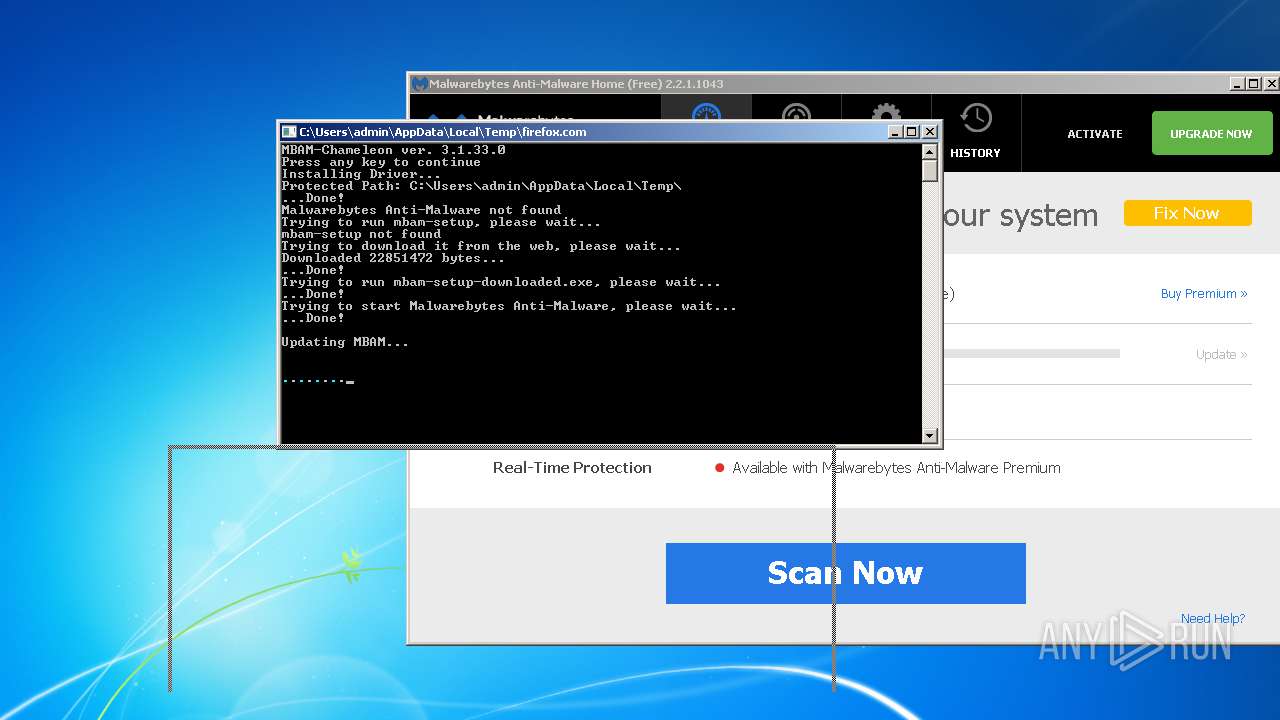
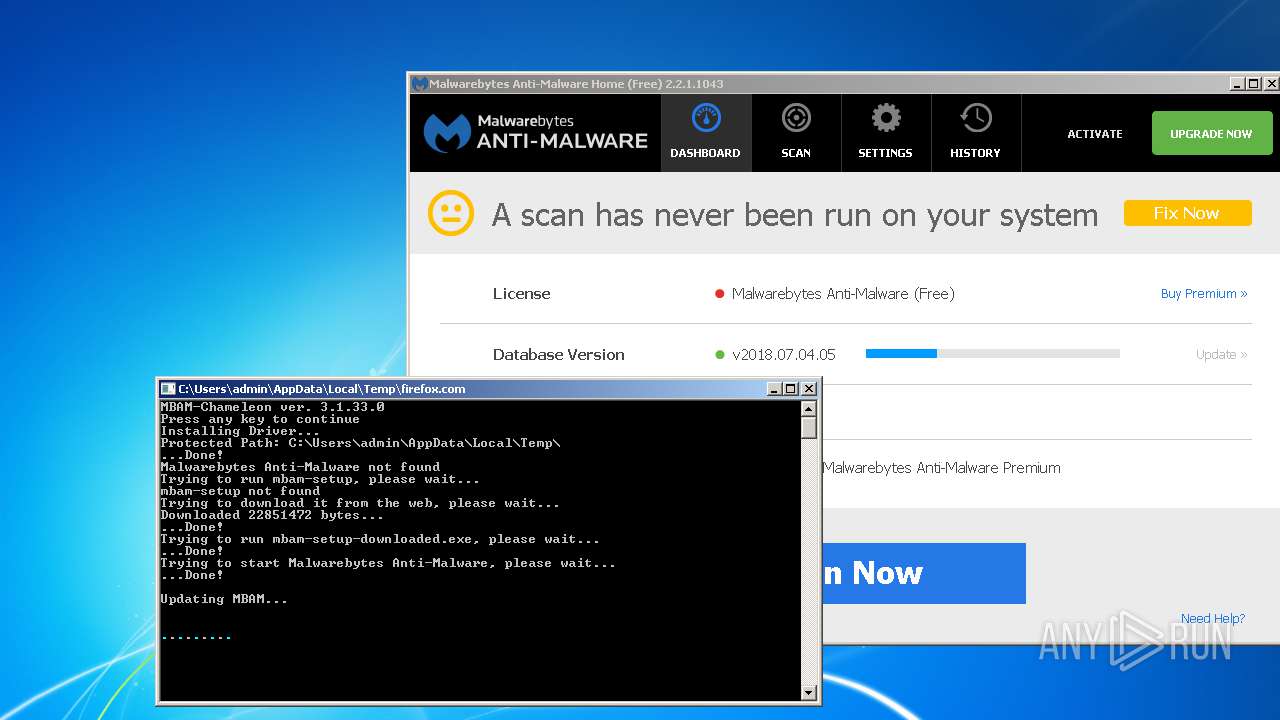
| FileVersionNumber: | 3.1.33.0 |
| ProductVersionNumber: | 3.1.33.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | MalwareBytes |
| FileDescription: | Chameleon |
| FileVersion: | 3.1.33.0 |
| InternalName: | mbam-chameleon.exe |
| LegalCopyright: | Copyright (C) 2013 |
| OriginalFileName: | mbam-chameleon.exe |
| ProductName: | Malwarebytes Anti-Malware |
| ProductVersion: | 3.1.33.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 04-May-2016 23:07:42 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | MalwareBytes |
| FileDescription: | Chameleon |
| FileVersion: | 3.1.33.0 |
| InternalName: | mbam-chameleon.exe |
| LegalCopyright: | Copyright (C) 2013 |
| OriginalFilename: | mbam-chameleon.exe |
| ProductName: | Malwarebytes Anti-Malware |
| ProductVersion: | 3.1.33.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 04-May-2016 23:07:42 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00066441 | 0x00066600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50354 |
.rdata | 0x00068000 | 0x00017242 | 0x00017400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.3601 |
.data | 0x00080000 | 0x00005C64 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.05864 |
.rsrc | 0x00086000 | 0x0005FC58 | 0x0005FE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.741 |
.reloc | 0x000E6000 | 0x000079E8 | 0x00007A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.51271 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.15783 | 857 | UNKNOWN | English - United States | RT_MANIFEST |
105 | 6.77003 | 126336 | UNKNOWN | English - United States | MBAM_WATCHDOG_DRIVER |
106 | 6.45845 | 140672 | UNKNOWN | English - United States | MBAM_WATCHDOG_DRIVER |
107 | 6.74458 | 123264 | UNKNOWN | English - United States | MBAM_WATCHDOG_DRIVER |
Imports
ADVAPI32.dll |
KERNEL32.dll |
NETAPI32.dll |
PSAPI.DLL |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
VERSION.dll |
WININET.dll |
WINTRUST.dll |
Total processes
71
Monitored processes
22
Malicious processes
15
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 384 | mbamresearch.exe | C:\Program Files\Malwarebytes Anti-Malware\mbamresearch.exe | — | mbam.exe | |||||||||||
User: admin Company: Malwarebytes Integrity Level: HIGH Description: Malwarebytes Anti-Malware Exit code: 2 Version: 1.0.0 Modules
| |||||||||||||||
| 688 | C:\Users\admin\AppData\Local\Temp\firefox.com /x qfdgl | C:\Users\admin\AppData\Local\Temp\firefox.com | firefox.com | ||||||||||||
User: admin Company: MalwareBytes Integrity Level: HIGH Description: Chameleon Exit code: 0 Version: 3.1.33.0 Modules
| |||||||||||||||
| 848 | "C:\Program Files\Malwarebytes\Anti-Malware\mbamtray.exe" | C:\Program Files\Malwarebytes\Anti-Malware\mbamtray.exe | mbamservice.exe | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: MEDIUM Description: Malwarebytes Tray Application Exit code: 0 Version: 3.0.0.1490 Modules
| |||||||||||||||
| 996 | "C:\Users\admin\AppData\Local\Temp\is-6VUHI.tmp\mbam-setup-downloaded.tmp" /SL5="$1401A4,22449202,56832,C:\Users\admin\AppData\Local\Temp\mbam-setup-downloaded.exe" /silent /noreboot | C:\Users\admin\AppData\Local\Temp\is-6VUHI.tmp\mbam-setup-downloaded.tmp | mbam-setup-downloaded.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1208 | "mbam-setup-downloaded.exe" /silent /noreboot | C:\Users\admin\AppData\Local\Temp\mbam-setup-downloaded.exe | firefox.com | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: HIGH Description: Malwarebytes Anti-Malware Exit code: 0 Version: 2.2.1.1043 Modules
| |||||||||||||||
| 1332 | "C:\ProgramData\Malwarebytes\Malwarebytes Anti-Malware\mbam-setup.exe" | C:\ProgramData\Malwarebytes\Malwarebytes Anti-Malware\mbam-setup.exe | mbam.exe | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: HIGH Description: Malwarebytes Exit code: 0 Version: 3.5.1.2522 Modules
| |||||||||||||||
| 1424 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\Malwarebytes Anti-Malware\mbamext.dll" | C:\Windows\system32\regsvr32.exe | — | mbam-setup-downloaded.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1456 | "C:\Program Files\Malwarebytes\Anti-Malware\mbamservice.exe" | C:\Program Files\Malwarebytes\Anti-Malware\mbamservice.exe | services.exe | ||||||||||||
User: SYSTEM Company: Malwarebytes Integrity Level: SYSTEM Description: Malwarebytes Service Exit code: 0 Version: 3.1.0.667 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Malwarebytes Anti-Malware\unins000.exe" /VERYSILENT /NORESTART /LOG | C:\Program Files\Malwarebytes Anti-Malware\unins000.exe | mbam-setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Malwarebytes\Anti-Malware\mbamservice.exe" /service | C:\Program Files\Malwarebytes\Anti-Malware\mbamservice.exe | — | mbam-setup.tmp | |||||||||||
User: admin Company: Malwarebytes Integrity Level: HIGH Description: Malwarebytes Service Exit code: 0 Version: 3.1.0.667 Modules
| |||||||||||||||
Total events
3 157
Read events
1 266
Write events
1 844
Delete events
47
Modification events
| (PID) Process: | (688) firefox.com | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\mbamchameleon\Instances |
| Operation: | write | Name: | DefaultInstance |
Value: mbamchameleon Instance | |||
| (PID) Process: | (688) firefox.com | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\mbamchameleon\Instances\mbamchameleon Instance |
| Operation: | write | Name: | Altitude |
Value: 400900 | |||
| (PID) Process: | (688) firefox.com | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\mbamchameleon\Instances\mbamchameleon Instance |
| Operation: | write | Name: | Flags |
Value: 0 | |||
| (PID) Process: | (688) firefox.com | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\mbamchameleon |
| Operation: | write | Name: | Protected |
Value: C:\Users\admin\AppData\Local\Temp\ | |||
| (PID) Process: | (688) firefox.com | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\System\mbamchameleon |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Windows\system32\drivers\mbamchameleon.sys | |||
| (PID) Process: | (688) firefox.com | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\System\mbamchameleon |
| Operation: | write | Name: | TypesSupported |
Value: 7 | |||
| (PID) Process: | (688) firefox.com | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\mbamchameleon |
| Operation: | write | Name: | RefCount |
Value: 1 | |||
| (PID) Process: | (688) firefox.com | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (688) firefox.com | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000070000000010000000000000000000000000000000000000000000000400C35B347C7D301000000000000000000000000020000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001C00000000000000000000000000000000000000000000000000000000000000170000000000000000000000000000000000FFFFC0A8640B000000000000000002000000C0A801640000000000000000000000000000000000000000000000000C00000C37D0000010A73800D8703600000000000000000000000000000000000000000000000000000000000000000000000000000000000000000081F800009000230090002300380023000000000000702C000A00000000000000F8412C00 | |||
| (PID) Process: | (688) firefox.com | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
152
Suspicious files
123
Text files
132
Unknown types
72
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 996 | mbam-setup-downloaded.tmp | C:\Program Files\Malwarebytes Anti-Malware\is-5B2FI.tmp | — | |
MD5:— | SHA256:— | |||
| 996 | mbam-setup-downloaded.tmp | C:\Windows\system32\drivers\is-1BKKN.tmp | — | |
MD5:— | SHA256:— | |||
| 996 | mbam-setup-downloaded.tmp | C:\Windows\system32\drivers\is-86KIN.tmp | — | |
MD5:— | SHA256:— | |||
| 996 | mbam-setup-downloaded.tmp | C:\Windows\system32\drivers\is-TILU1.tmp | — | |
MD5:— | SHA256:— | |||
| 996 | mbam-setup-downloaded.tmp | C:\Program Files\Malwarebytes Anti-Malware\is-J5D0R.tmp | — | |
MD5:— | SHA256:— | |||
| 996 | mbam-setup-downloaded.tmp | C:\Program Files\Malwarebytes Anti-Malware\is-J5Q27.tmp | — | |
MD5:— | SHA256:— | |||
| 996 | mbam-setup-downloaded.tmp | C:\Program Files\Malwarebytes Anti-Malware\is-OH39A.tmp | — | |
MD5:— | SHA256:— | |||
| 996 | mbam-setup-downloaded.tmp | C:\Program Files\Malwarebytes Anti-Malware\is-Q01E0.tmp | — | |
MD5:— | SHA256:— | |||
| 996 | mbam-setup-downloaded.tmp | C:\Program Files\Malwarebytes Anti-Malware\is-84GBM.tmp | — | |
MD5:— | SHA256:— | |||
| 996 | mbam-setup-downloaded.tmp | C:\Program Files\Malwarebytes Anti-Malware\is-J9RVA.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
244
DNS requests
15
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
688 | firefox.com | 2.18.233.58:443 | links.malwarebytes.org | Akamai International B.V. | — | whitelisted |
3044 | mbam.exe | 50.19.28.216:443 | keystone.mwbsys.com | Amazon.com, Inc. | US | unknown |
3044 | mbam.exe | 54.85.91.182:443 | keystone.mwbsys.com | Amazon.com, Inc. | US | unknown |
3044 | mbam.exe | 2.18.233.58:443 | links.malwarebytes.org | Akamai International B.V. | — | whitelisted |
3044 | mbam.exe | 54.148.177.165:443 | stats.mbamupdates.com | Amazon.com, Inc. | US | unknown |
3044 | mbam.exe | 52.0.161.176:443 | sirius.mwbsys.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
links.malwarebytes.org |
| malicious |
data-cdn.mbamupdates.com |
| whitelisted |
keystone.mwbsys.com |
| unknown |
sirius.mwbsys.com |
| suspicious |
cdn.mwbsys.com |
| whitelisted |
stats.mbamupdates.com |
| unknown |
bactem.mwbsys.com |
| unknown |
Threats
Process | Message |
|---|---|
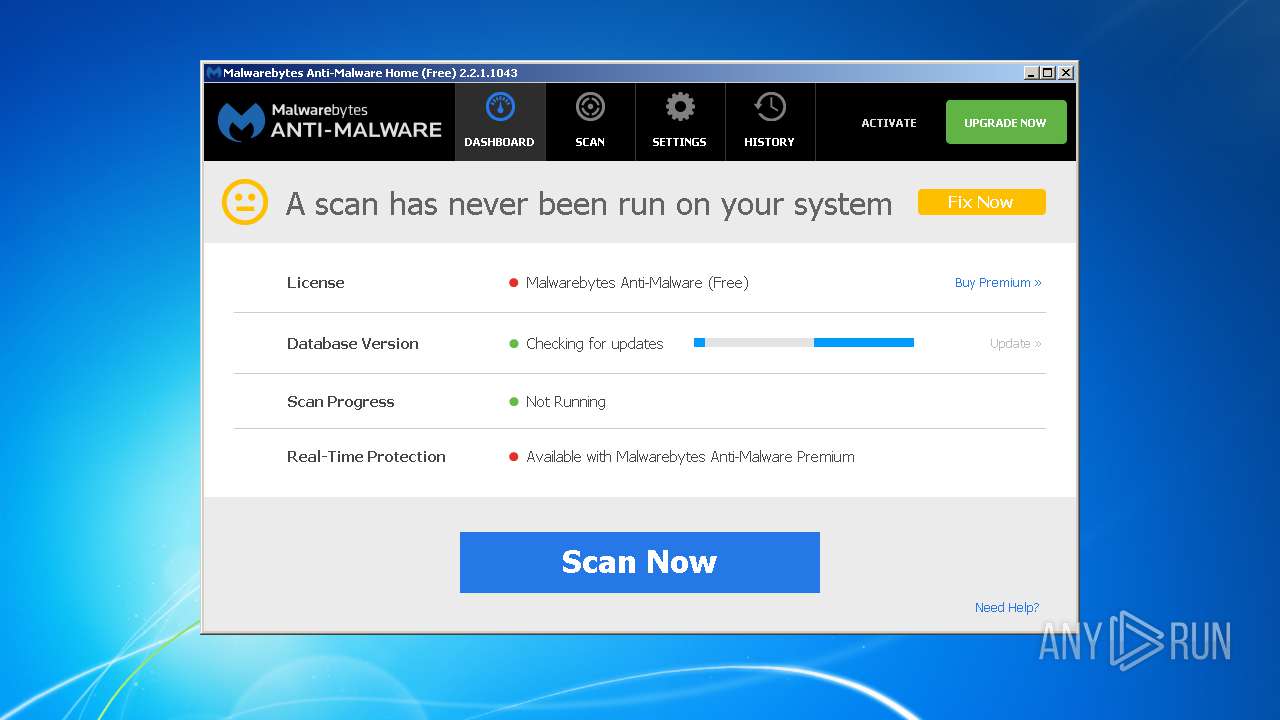
mbam.exe | Manual: LogUpdate [Rootkit Database, 2016.2.8.1 -> 2018.7.4.5]
|
mbam.exe | Manual: LogUpdate [Remediation Database, 2016.2.12.1 -> 2018.1.20.1]
|
mbam.exe | Manual: LogUpdate [IP Database, 2016.2.8.1 -> 2018.7.4.5]
|
mbam.exe | Manual: LogUpdate [Domain Database, 2016.2.16.8 -> 2018.7.4.5]
|
mbam.exe | Manual: LogUpdate [Malware Database, 2016.2.16.6 -> 2018.7.4.5]
|
mbam.exe | Manual: LogUpdate [program, 2.2.1.1043 -> 3.5.1.0]
|
mbamtray.exe | QAxBase::setControl: requested control {F36AD0D0-B5F0-4C69-AF08-603D177FEF0E} could not be instantiated
|
mbamtray.exe | QAxBase: Error calling IDispatch member GetLastActiveScanner: Exception thrown by server
|
mbamtray.exe | Code : 16389
|
mbamtray.exe | Source :
|